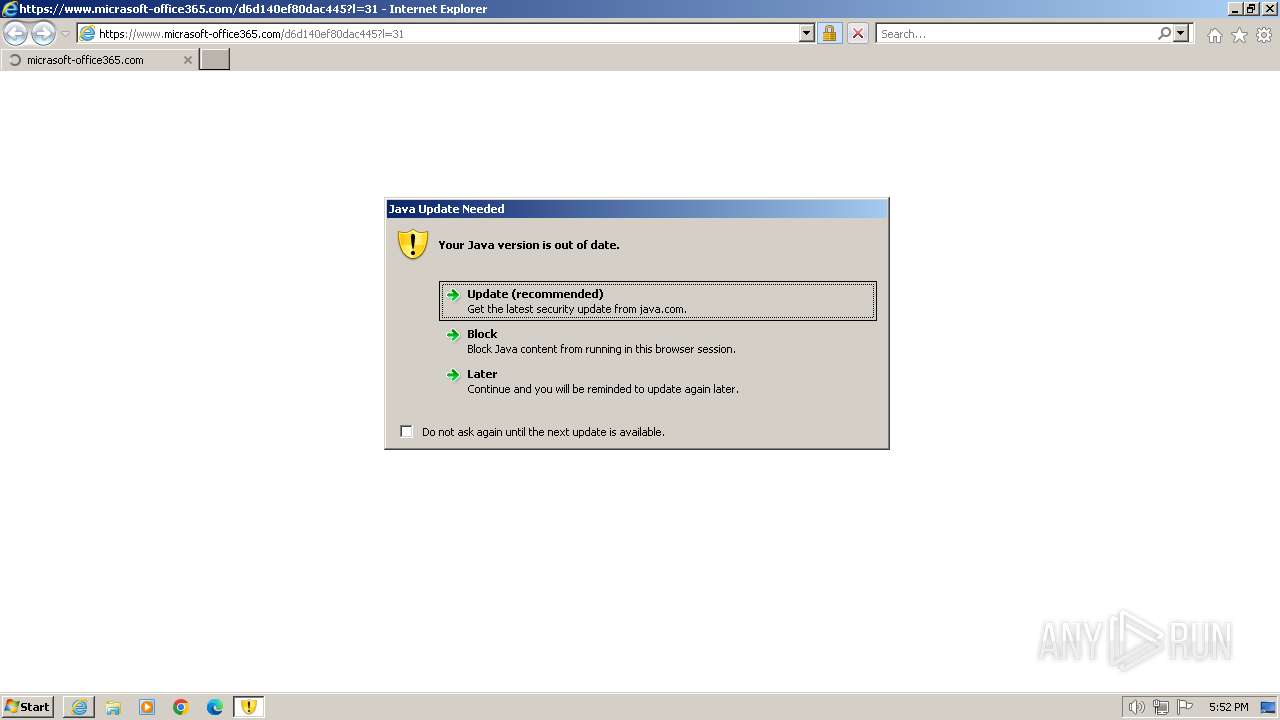
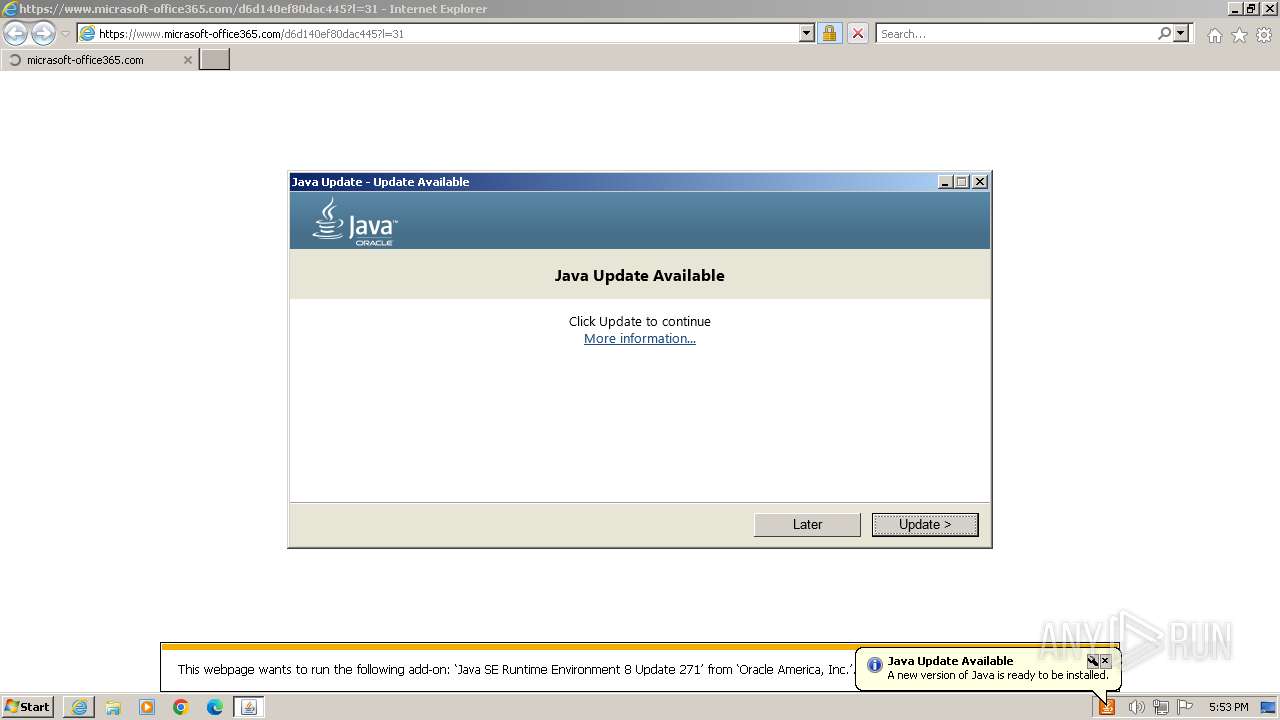
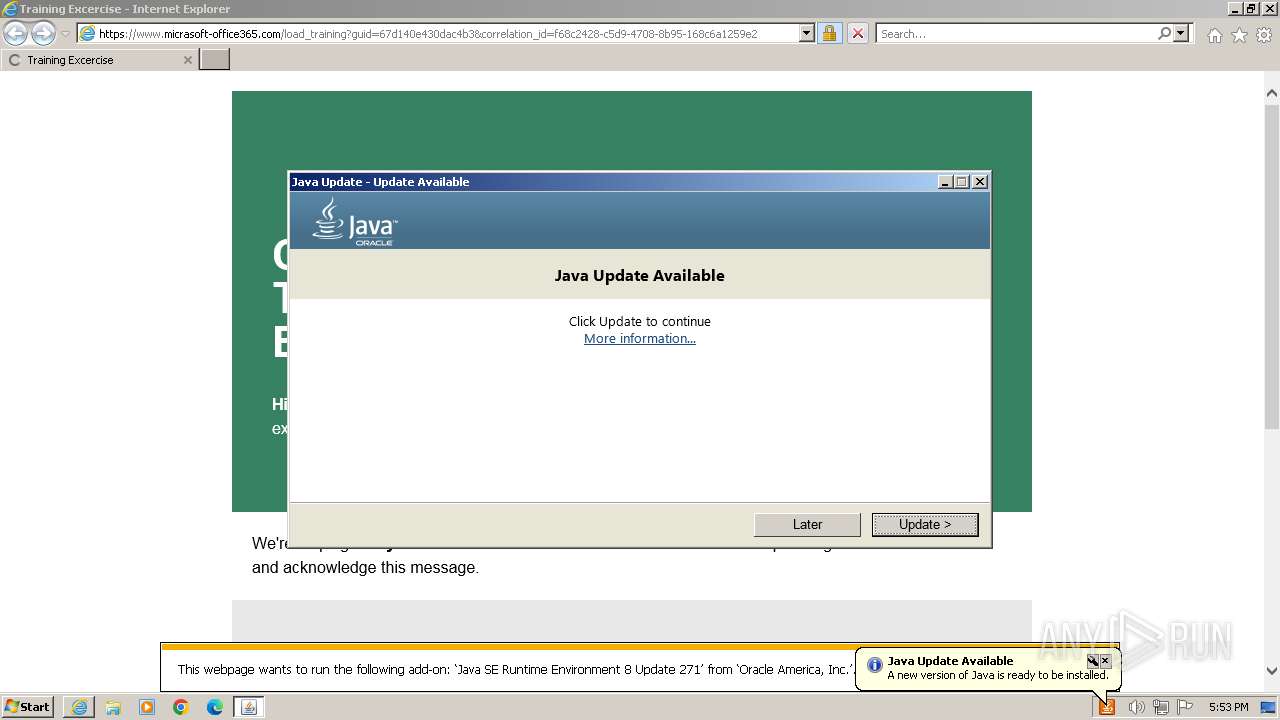
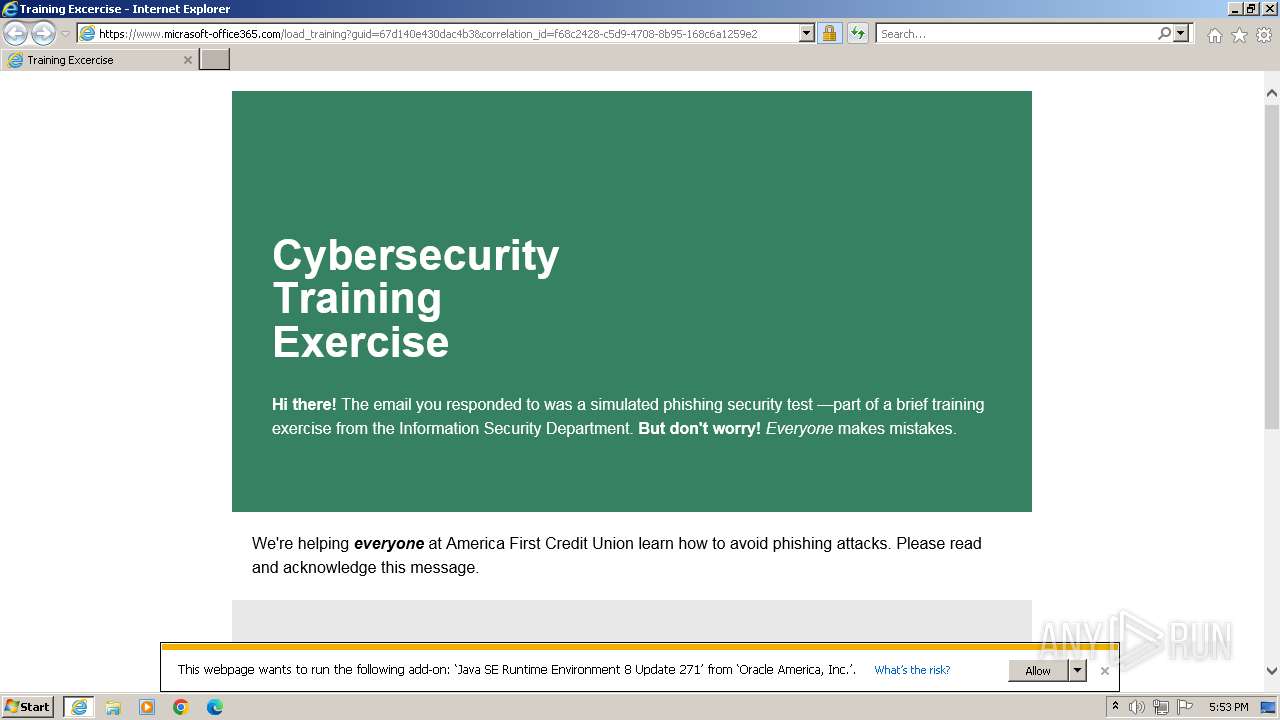
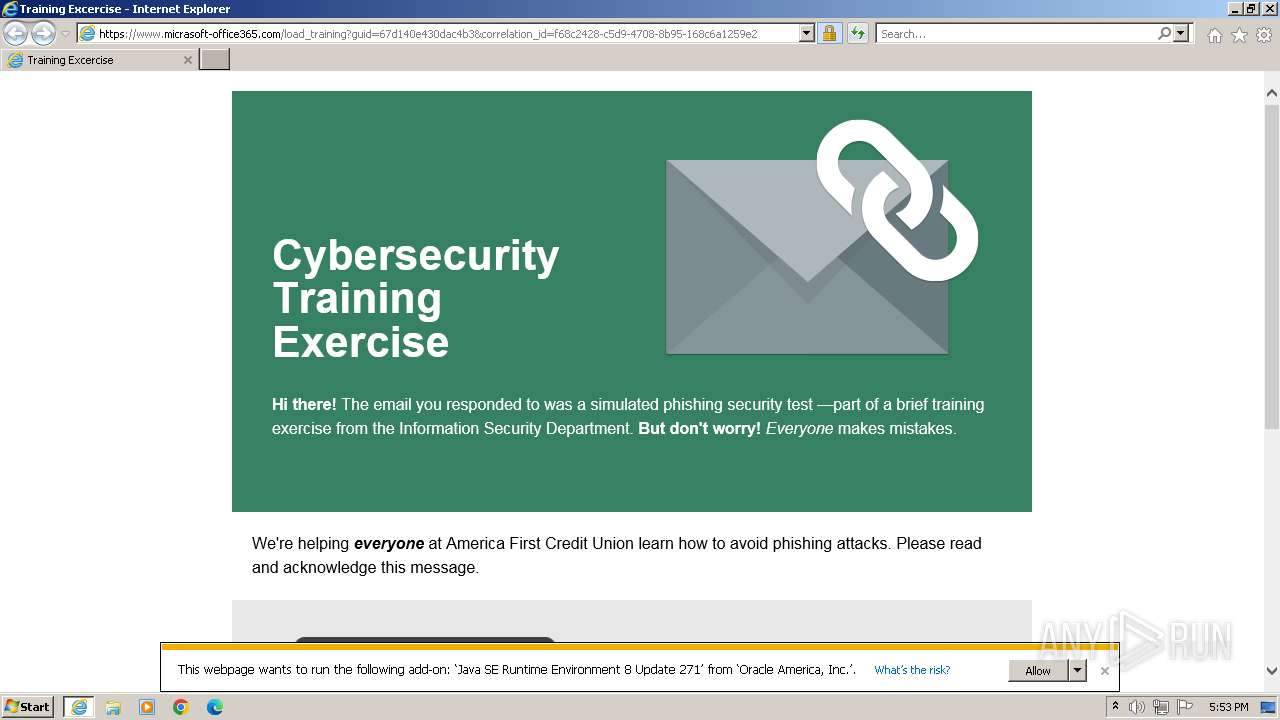
| URL: | https://www.micrasoft-office365.com/d6d140ef80dac445?l=31 |
| Full analysis: | https://app.any.run/tasks/b6371ca5-3f87-4c03-8df9-43ee21a64030 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2024, 17:52:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1C2611BBE50DCF6B32DA84301FF59526 |
| SHA1: | 035834075DF228B072582F12E2BB00E4900671C8 |
| SHA256: | DF37E655EF1993E7A67E0BE6E1BD32E7B551646A5231BD13657D5807741FCDD7 |
| SSDEEP: | 3:N8DSLXRFfH/QLGTKBTiRVqQG2aRU:2OLBFfHYL1d9RU |
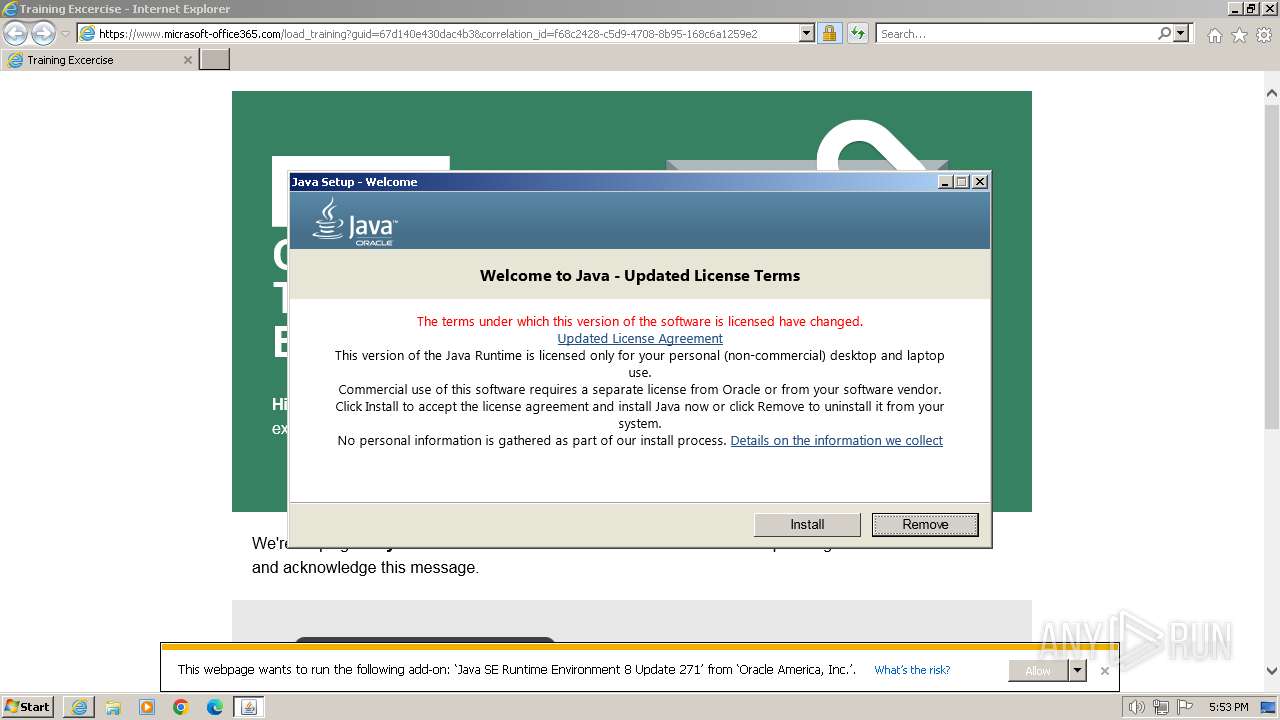
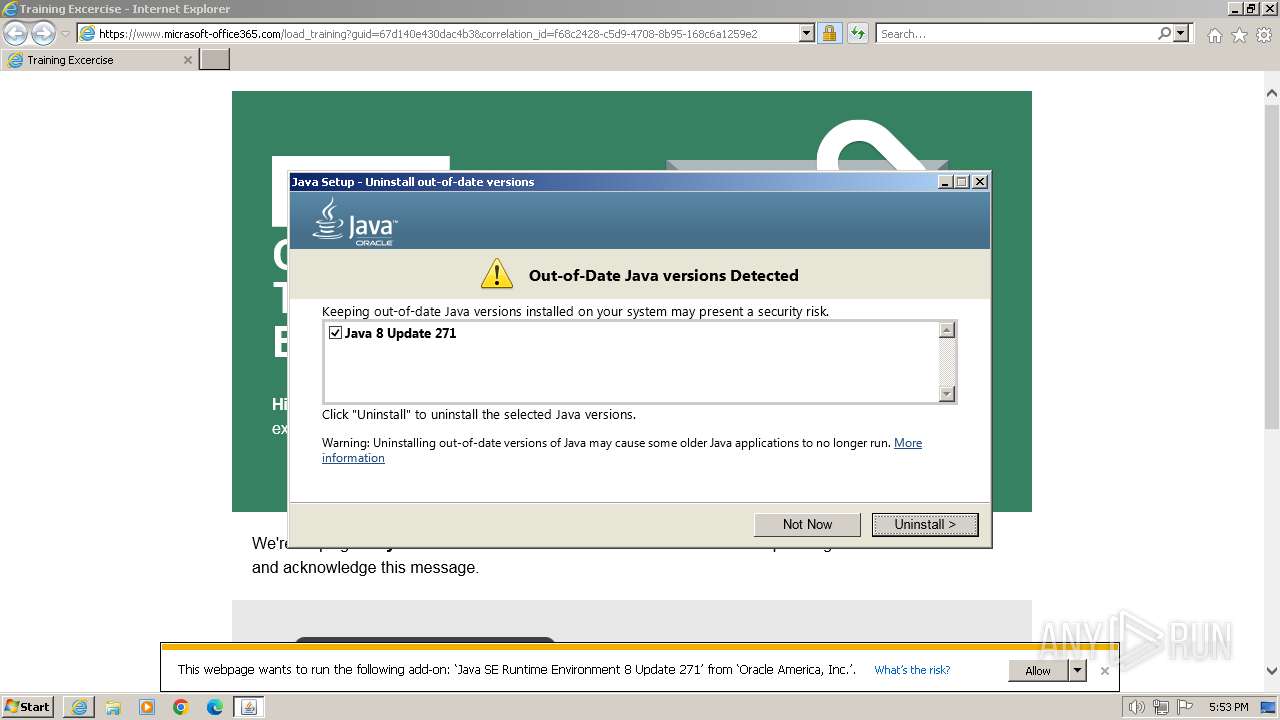
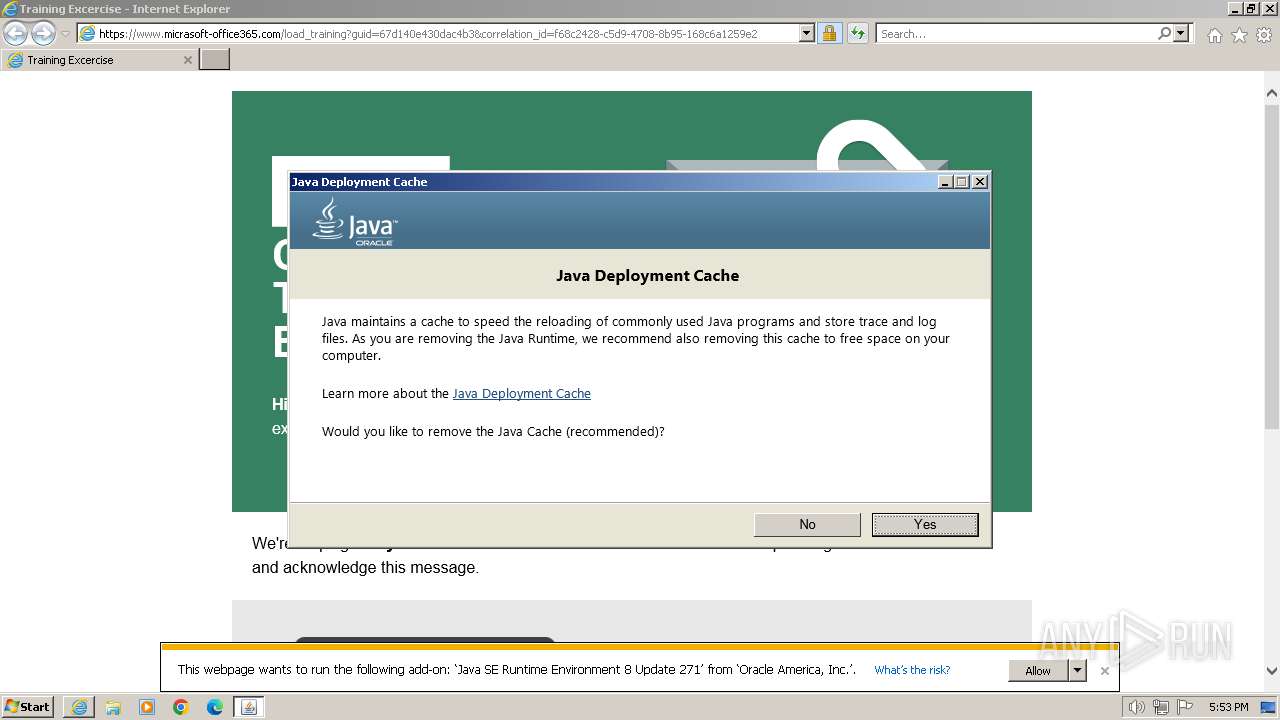
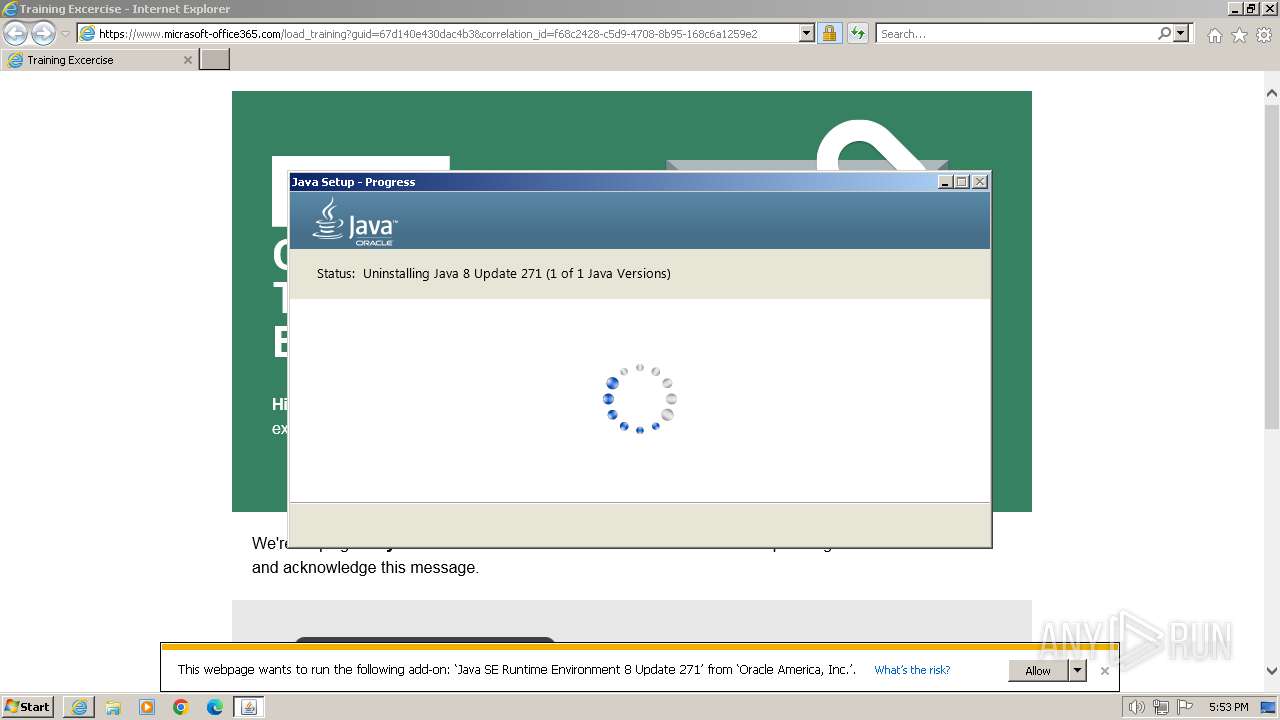
MALICIOUS
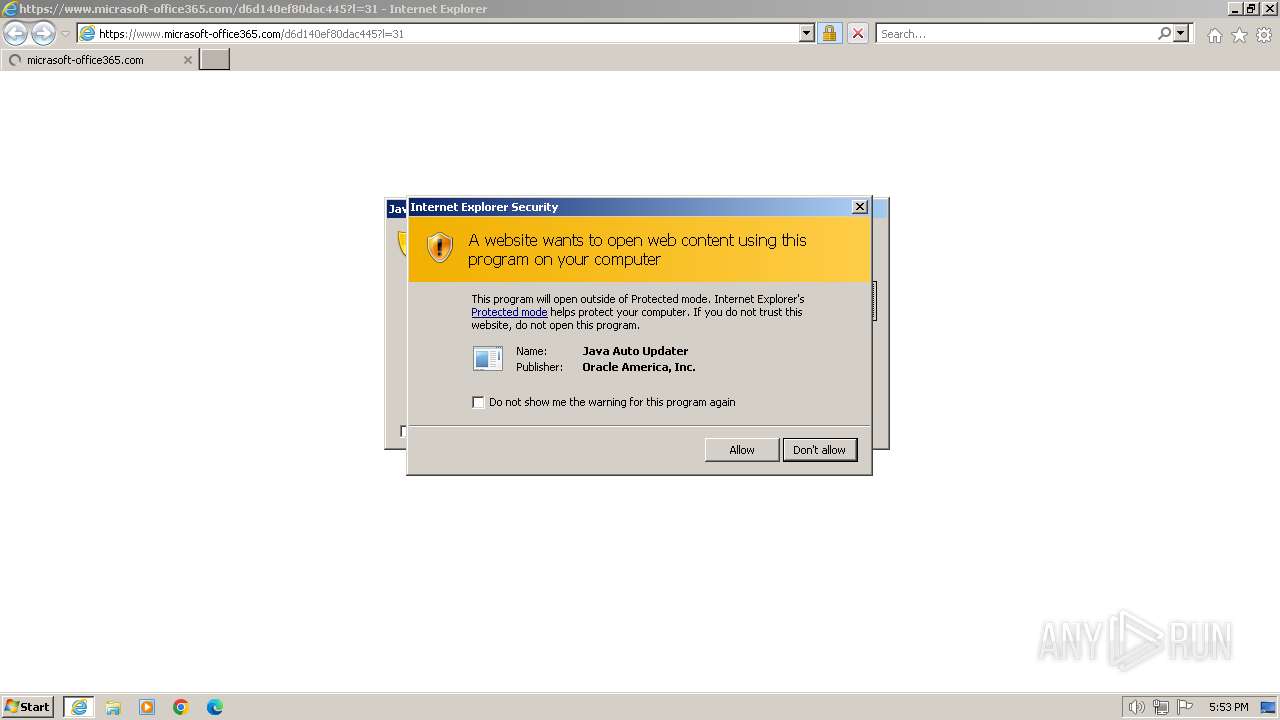
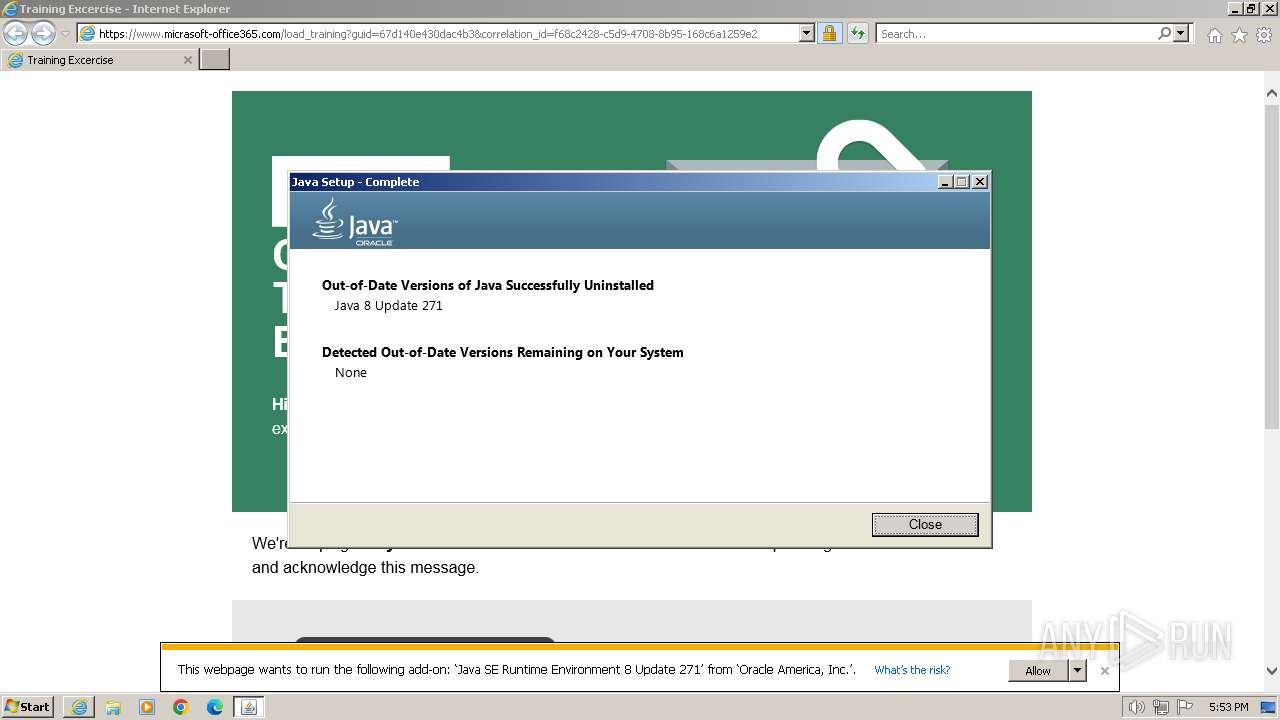
Drops the executable file immediately after the start
- jucheck.exe (PID: 2592)
- jre-8u401-windows-au.exe (PID: 3208)
- msiexec.exe (PID: 3352)
SUSPICIOUS
Checks for Java to be installed
- jp2launcher.exe (PID: 1592)
- javaw.exe (PID: 1928)
- javaw.exe (PID: 1560)
- javaw.exe (PID: 2328)
- jp2launcher.exe (PID: 1232)
- jucheck.exe (PID: 2592)
- msiexec.exe (PID: 3352)
Checks Windows Trust Settings
- jucheck.exe (PID: 2592)
- jre-8u401-windows-au.exe (PID: 3108)
Reads security settings of Internet Explorer
- jucheck.exe (PID: 2592)
- jre-8u401-windows-au.exe (PID: 3108)
Reads settings of System Certificates
- jucheck.exe (PID: 2592)
- jp2launcher.exe (PID: 1232)
- jre-8u401-windows-au.exe (PID: 3108)
Reads the Internet Settings
- jucheck.exe (PID: 2592)
- jp2launcher.exe (PID: 1232)
- jre-8u401-windows-au.exe (PID: 3108)
Executable content was dropped or overwritten
- jre-8u401-windows-au.exe (PID: 3208)
- jucheck.exe (PID: 2592)
Reads Microsoft Outlook installation path
- jucheck.exe (PID: 2592)
- jre-8u401-windows-au.exe (PID: 3108)
Reads Internet Explorer settings
- jucheck.exe (PID: 2592)
- jre-8u401-windows-au.exe (PID: 3108)
Reads Mozilla Firefox installation path
- MSI6CC1.tmp (PID: 3368)
The process drops C-runtime libraries
- msiexec.exe (PID: 3352)
Process drops legitimate windows executable
- msiexec.exe (PID: 3352)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3352)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 1832)
Application launched itself
- iexplore.exe (PID: 2044)
- msiexec.exe (PID: 3352)
Checks supported languages
- jp2launcher.exe (PID: 1592)
- wmpnscfg.exe (PID: 1832)
- javaw.exe (PID: 1928)
- javaw.exe (PID: 1560)
- javaw.exe (PID: 2328)
- jucheck.exe (PID: 2592)
- javaws.exe (PID: 452)
- jp2launcher.exe (PID: 1232)
- jre-8u401-windows-au.exe (PID: 3108)
- jre-8u401-windows-au.exe (PID: 3208)
- msiexec.exe (PID: 3352)
- MSI6CC1.tmp (PID: 3368)
- msiexec.exe (PID: 3452)
- msiexec.exe (PID: 3680)
- jaureg.exe (PID: 2784)
Reads the computer name
- wmpnscfg.exe (PID: 1832)
- javaw.exe (PID: 1928)
- javaw.exe (PID: 1560)
- javaw.exe (PID: 2328)
- jucheck.exe (PID: 2592)
- jp2launcher.exe (PID: 1232)
- jre-8u401-windows-au.exe (PID: 3208)
- jre-8u401-windows-au.exe (PID: 3108)
- msiexec.exe (PID: 3352)
- MSI6CC1.tmp (PID: 3368)
- msiexec.exe (PID: 3452)
- msiexec.exe (PID: 3680)
Creates files in the program directory
- javaw.exe (PID: 1928)
Create files in a temporary directory
- javaw.exe (PID: 1928)
- javaw.exe (PID: 1560)
- javaw.exe (PID: 2328)
- jp2launcher.exe (PID: 1232)
- jucheck.exe (PID: 2592)
- jre-8u401-windows-au.exe (PID: 3208)
- msiexec.exe (PID: 3352)
Connects to unusual port
- iexplore.exe (PID: 296)
Reads the machine GUID from the registry
- jucheck.exe (PID: 2592)
- jp2launcher.exe (PID: 1232)
- jre-8u401-windows-au.exe (PID: 3108)
- msiexec.exe (PID: 3352)
- msiexec.exe (PID: 3452)
- msiexec.exe (PID: 3680)
Checks proxy server information
- jucheck.exe (PID: 2592)
- jp2launcher.exe (PID: 1232)
- jre-8u401-windows-au.exe (PID: 3108)
Creates files or folders in the user directory
- jucheck.exe (PID: 2592)
- jp2launcher.exe (PID: 1232)
- jre-8u401-windows-au.exe (PID: 3108)
Reads CPU info
- msiexec.exe (PID: 3352)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3352)
Starts application with an unusual extension
- msiexec.exe (PID: 3352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
21
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2044 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 452 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" -J-Djdk.disableLastUsageTracking=true -SSVBaselineUpdate | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | jucheck.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxwbHVnaW4uamFyAC1EamRrLmRpc2FibGVMYXN0VXNhZ2VUcmFja2luZz10cnVlAC1Eam5scHguanZtPUM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcYmluXGphdmF3LmV4ZQAtRGpubHB4LnZtYXJncz1MVVJxWkdzdVpHbHpZV0pzWlV4aGMzUlZjMkZuWlZSeVlXTnJhVzVuUFhSeWRXVUE= -ma LVNTVkJhc2VsaW5lVXBkYXRlAC1ub3RXZWJKYXZh | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1705945980" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1576 | "C:\PROGRA~1\Java\JRE18~1.0_2\bin\jp2launcher.exe" -sjed | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 1592 | "C:\PROGRA~1\Java\JRE18~1.0_2\bin\jp2launcher.exe" -sjed | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 1 Version: 11.271.2.09 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.271.2" "update" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.micrasoft-office365.com/d6d140ef80dac445?l=31" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2312 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
45 443
Read events
32 457
Write events
430
Delete events
12 556
Modification events
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
159
Suspicious files
64
Text files
142
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:A5FF62B3F571F06C406CA36CA96AFA72 | SHA256:AEEAB8A0A8C519C181779D1AC9C0F4113F5F4578EA5EB1FB4FD4F7570A647689 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:5CA0BA71EAE873BF14AF2F16C728F8DF | SHA256:54A109F89FEC86A187B2C80233050879C5EC0BAA75E1955223FFAF180CBA6110 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_645BC4A49DCDC40FE5917FA45C6D4517 | binary | |
MD5:A56D6129E99089C30B3935BE59283B8E | SHA256:DDDDCF553A97628774C7F653072CCB8A026CCC0614EC902B90251CDD8F036854 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_645BC4A49DCDC40FE5917FA45C6D4517 | binary | |
MD5:5DBDA49076D60905055BE6038BE9B09E | SHA256:4B13E5C547449E2DAF67F5E243E8749EBC515443CBE9EA745C359BC133BFC835 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\83D863F495E7D991917B3ABB3E1EB382_4AFBAF1AC474E3E1A5B6CF643D7BBE05 | binary | |
MD5:FFC99EC625E8341D7733E8062978927A | SHA256:563DE64CA67A796326C24531B766C0E50090CD598C70BF1E94125C2D70F17193 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\83D863F495E7D991917B3ABB3E1EB382_4AFBAF1AC474E3E1A5B6CF643D7BBE05 | binary | |
MD5:255FA5167DC208F7ED94B7DD62CBF355 | SHA256:1DCCA459DD648109D2B738495EB4D169AA6B864017B622DDCBD876B13C2AA044 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:D71D7E4815ABB9F1B06B9DF80DE34EC3 | SHA256:C6CB133C2FCC6EE2E87C3BB4CB03ADCBC8A279389F9151073B4C5033E42F3167 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\all[1].js | text | |
MD5:097F74FC8F861ECE148262A652AB806A | SHA256:39B4614F1C87CF0CFD1BC3375642E95825CB2018E0318A36AAD766DDB5A8CBE9 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\d6d140ef80dac445[1].htm | html | |
MD5:8912A8ED81A6C8ACF7B6B85389A851E3 | SHA256:5B8F022F2934F04E83248B8DD0C1DD55C4A995FC5F0E8AA61526E2144F890FC6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
65
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
296 | iexplore.exe | GET | 200 | 184.24.77.207:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f6bf34dbb61e71d7 | unknown | compressed | 4.66 Kb | unknown |
296 | iexplore.exe | GET | 200 | 184.24.77.207:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?608cb4ab6d3f68d3 | unknown | compressed | 4.66 Kb | unknown |
296 | iexplore.exe | GET | 200 | 18.155.152.117:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
296 | iexplore.exe | GET | 200 | 18.155.156.218:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.49 Kb | unknown |
296 | iexplore.exe | GET | 200 | 18.155.156.218:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkzUBtJnwJkc3SmanzgxeYU%3D | unknown | binary | 1.37 Kb | unknown |
296 | iexplore.exe | GET | 200 | 54.230.54.227:80 | http://ocsp.r2m03.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQqHI%2BsdmapawQncL1rpCEZZ8gTSAQUVdkYX9IczAHhWLS%2Bq9lVQgHXLgICEA7FfHwauM2Iij3MwyyH4Z8%3D | unknown | binary | 471 b | unknown |
296 | iexplore.exe | GET | 200 | 18.155.156.218:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | binary | 1.37 Kb | unknown |
296 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
296 | iexplore.exe | GET | 200 | 54.230.54.227:80 | http://ocsp.r2m01.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBShdVEFnSEQ0gG5CBtzM48cPMe9XwQUgbgOY4qJEhjl%2Bjs7UJWf5uWQE4UCEAttUCKs5pZVb8wIJ%2BugwJo%3D | unknown | binary | 471 b | unknown |
2044 | iexplore.exe | GET | 304 | 184.24.77.207:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a85e8d0c2f0a71a5 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
296 | iexplore.exe | 52.201.60.166:443 | www.micrasoft-office365.com | AMAZON-AES | US | unknown |
296 | iexplore.exe | 184.24.77.207:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
296 | iexplore.exe | 18.155.152.117:80 | o.ss2.us | AMAZON-02 | US | unknown |
296 | iexplore.exe | 18.155.156.218:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | unknown |
296 | iexplore.exe | 54.230.54.227:80 | ocsp.r2m03.amazontrust.com | AMAZON-02 | US | unknown |
296 | iexplore.exe | 52.201.60.166:49153 | www.micrasoft-office365.com | AMAZON-AES | US | unknown |
296 | iexplore.exe | 3.5.2.181:443 | tslp.s3.amazonaws.com | AMAZON-AES | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.micrasoft-office365.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.r2m03.amazontrust.com |
| unknown |
tslp.s3.amazonaws.com |
| shared |
java.com |
| whitelisted |
d2wy8f7a9ursnm.cloudfront.net |
| shared |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
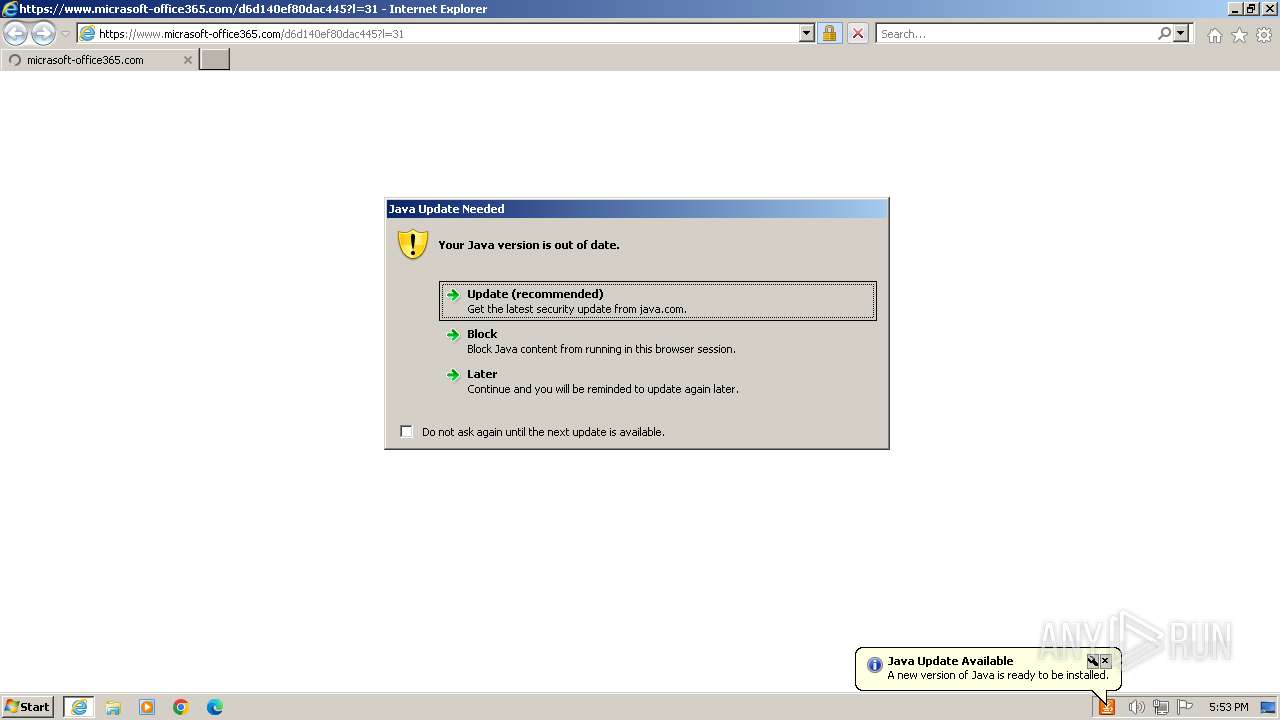
1232 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
1232 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |