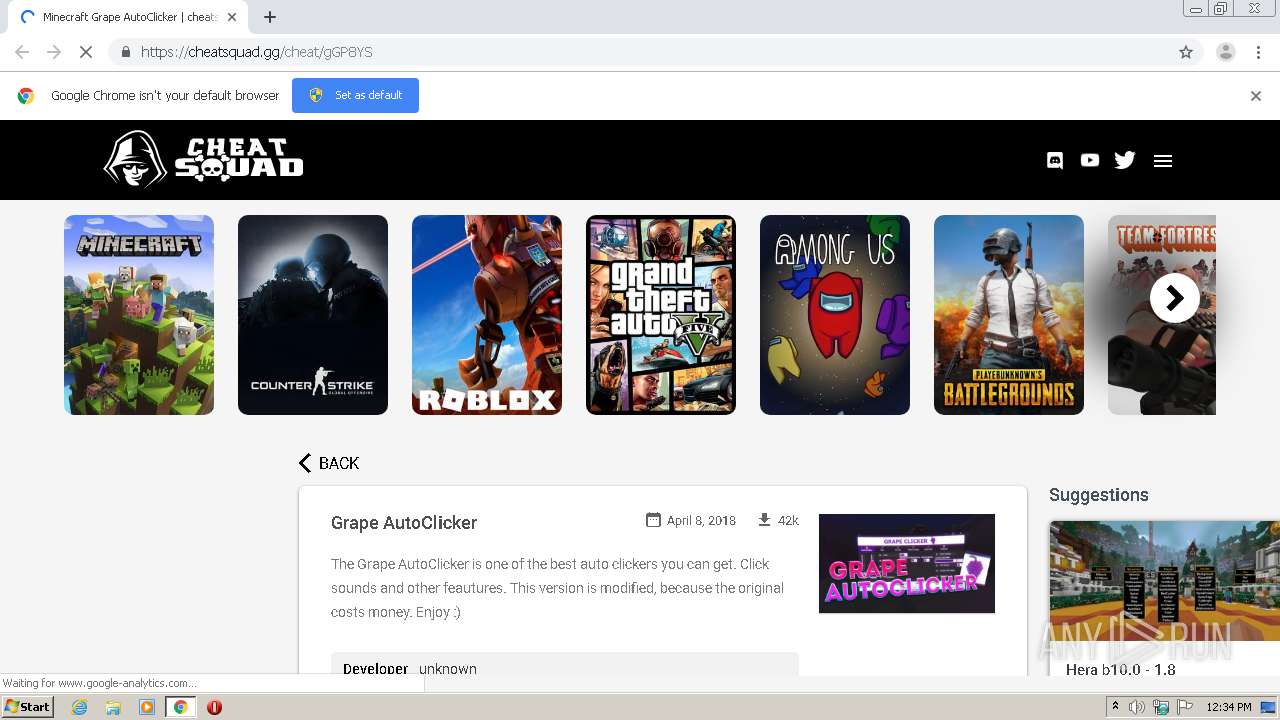
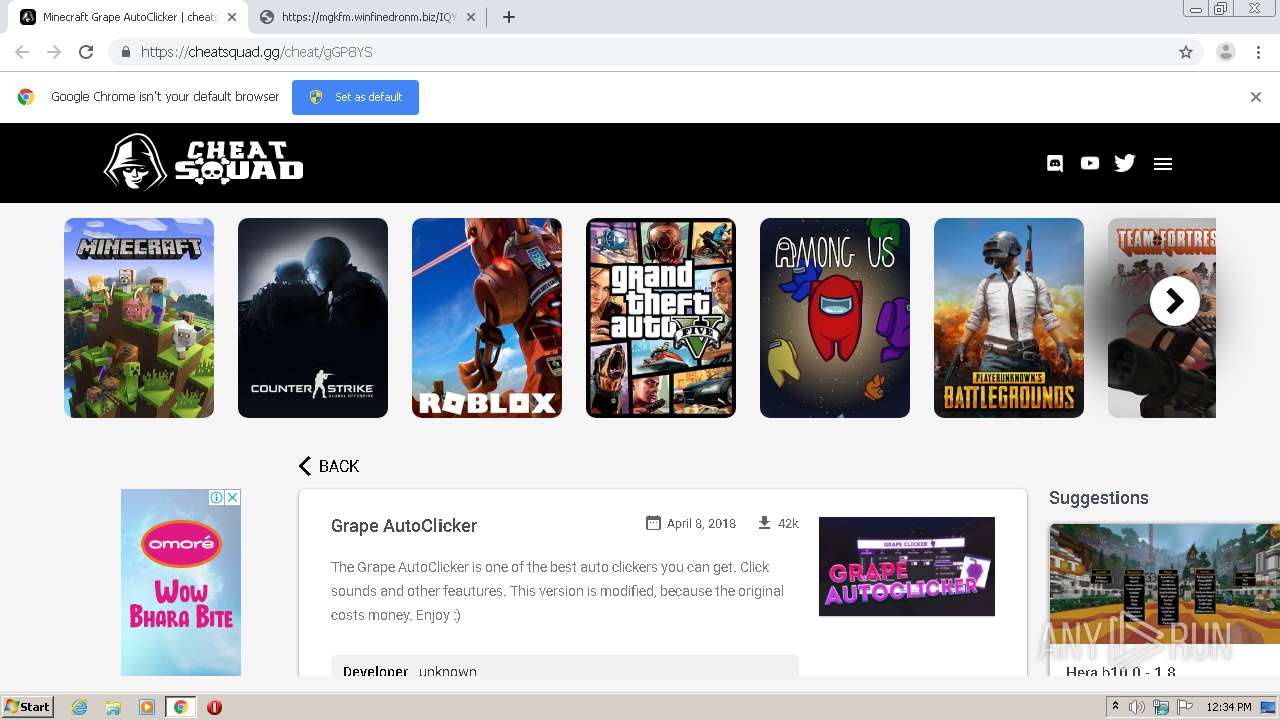
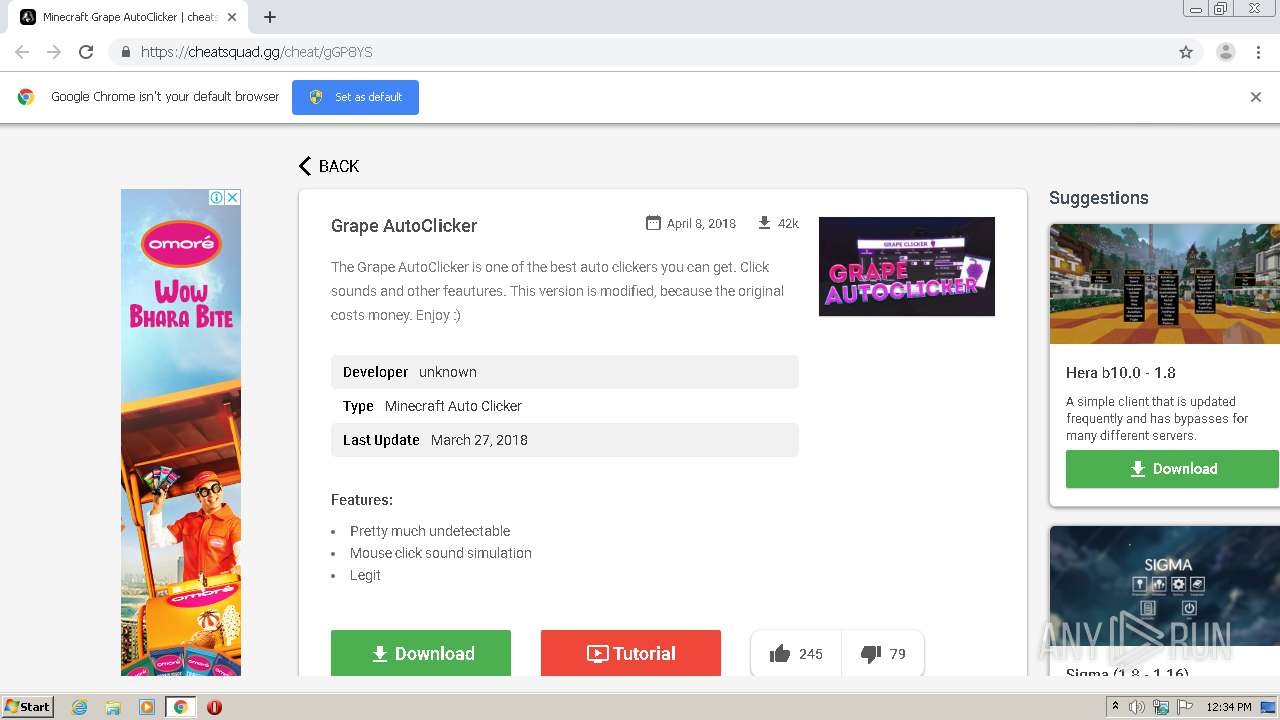
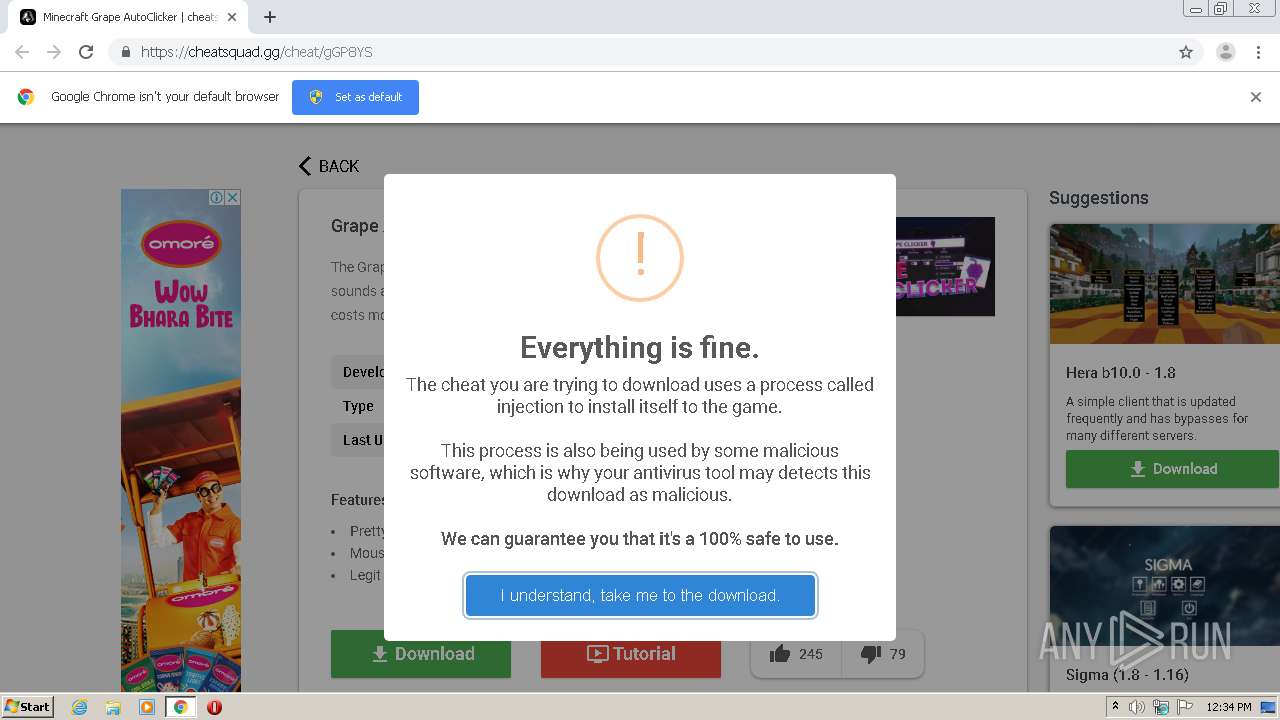
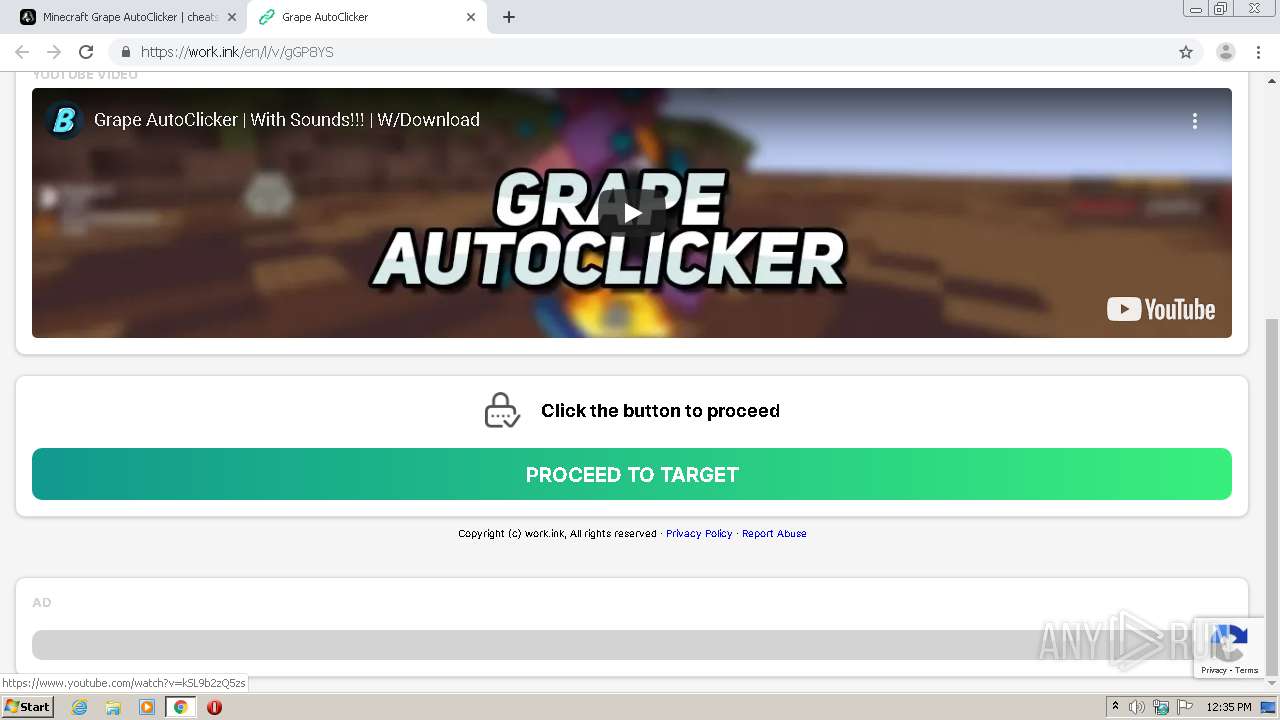
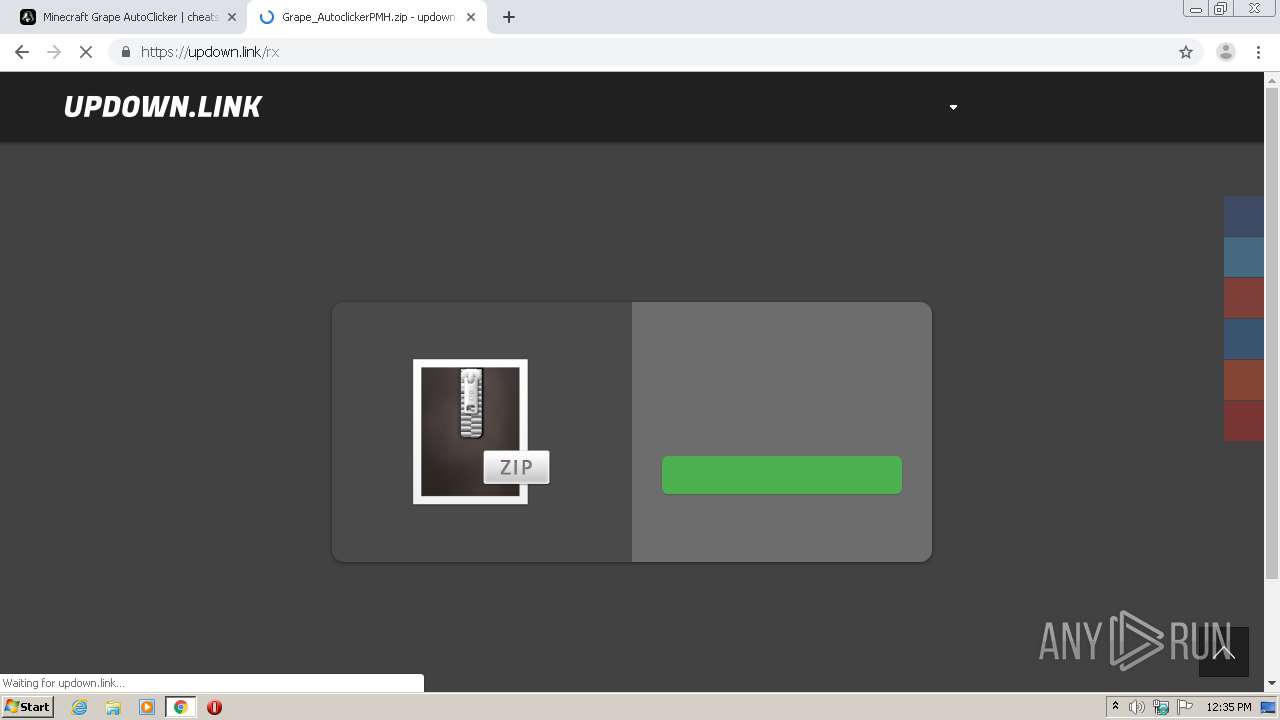
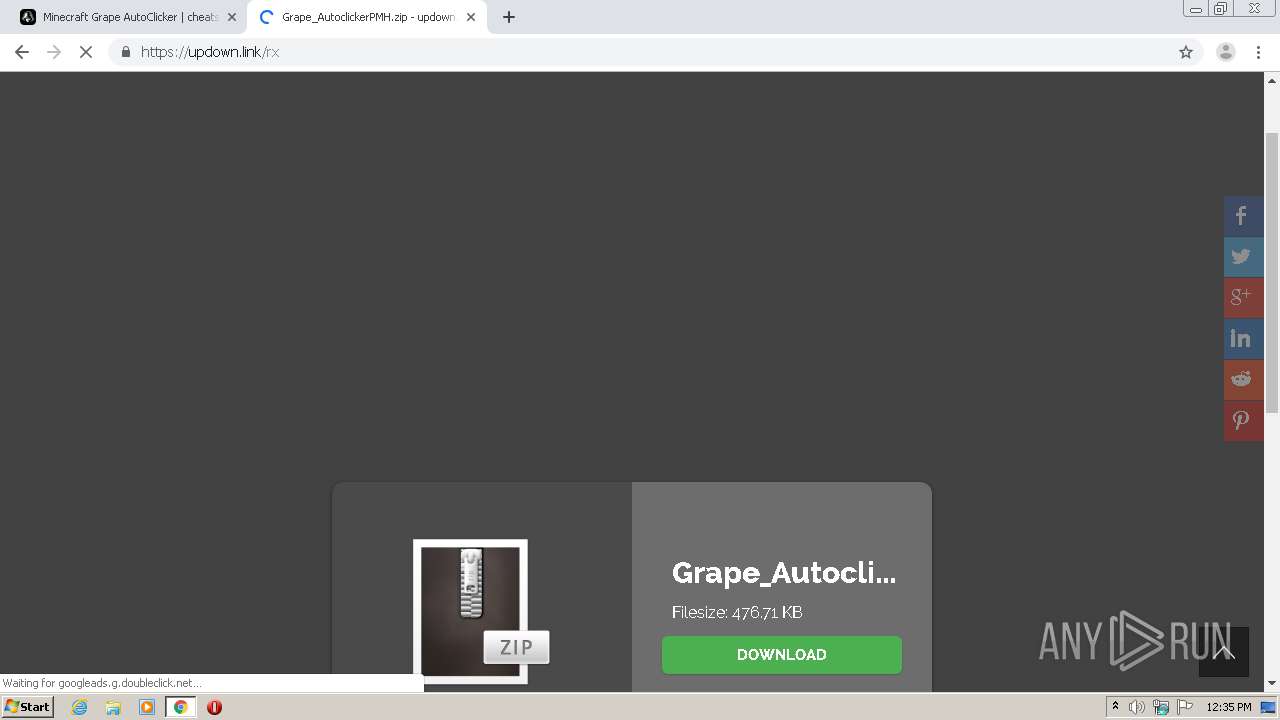
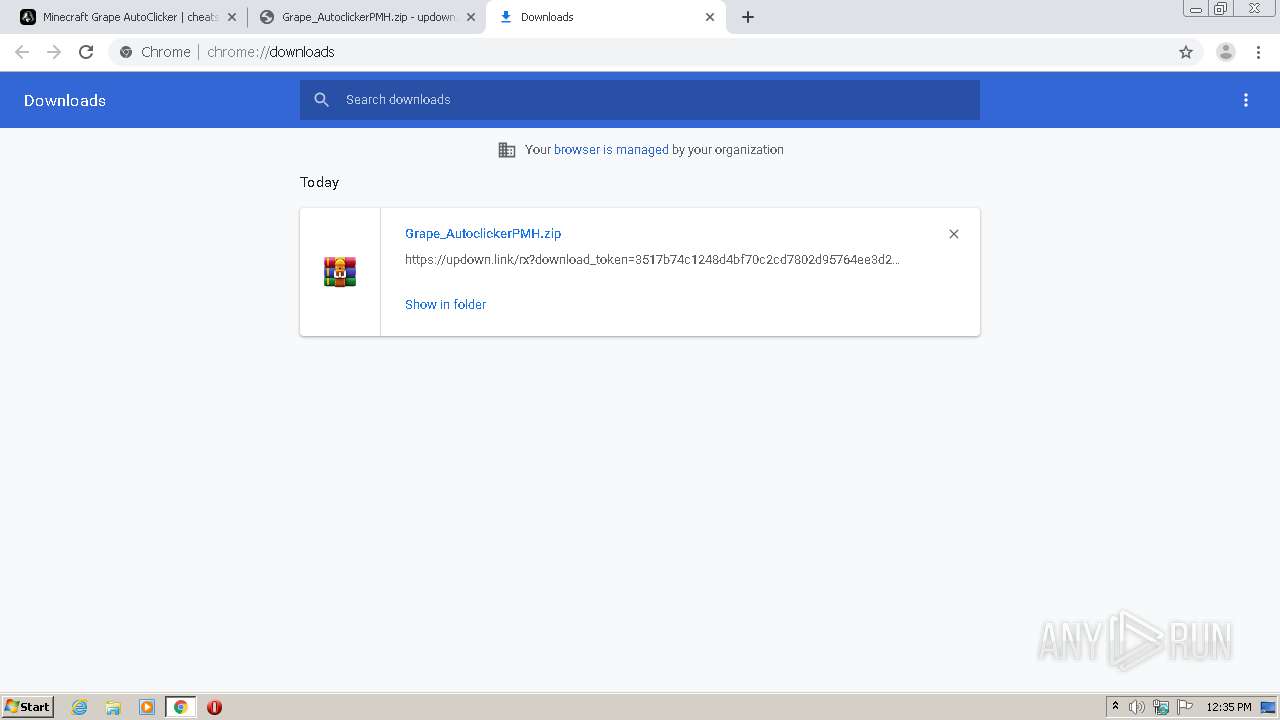
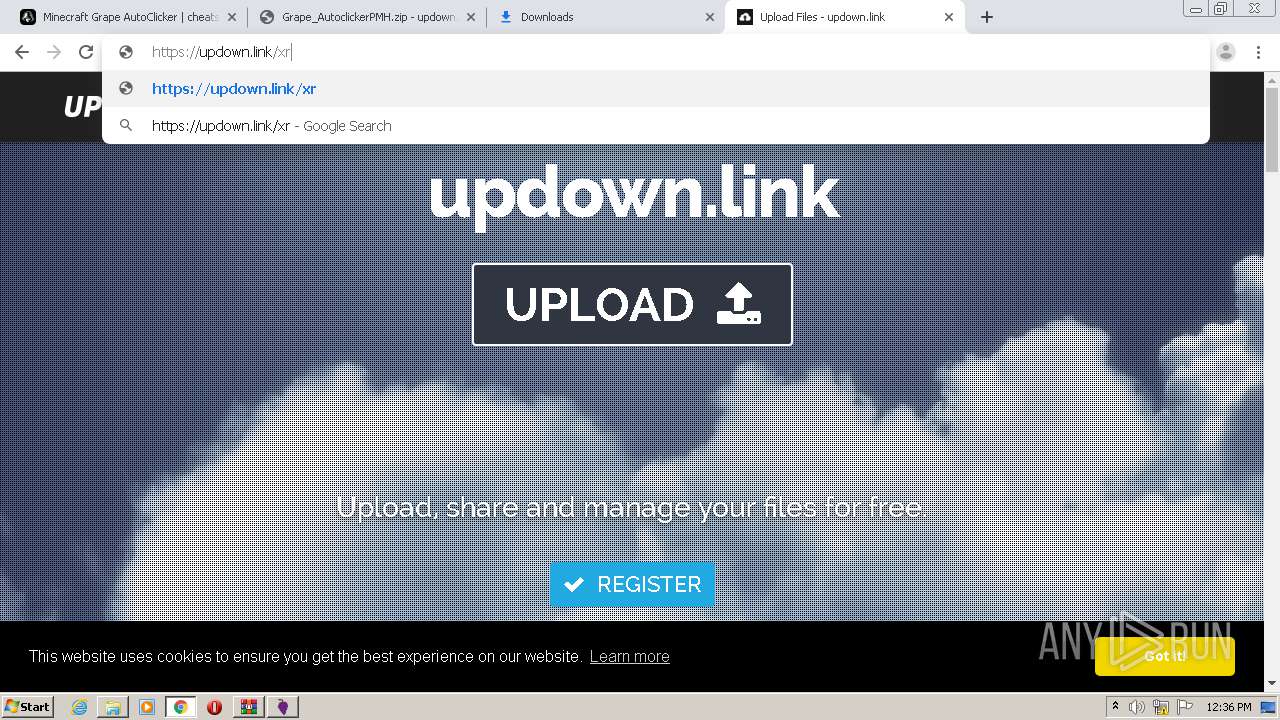
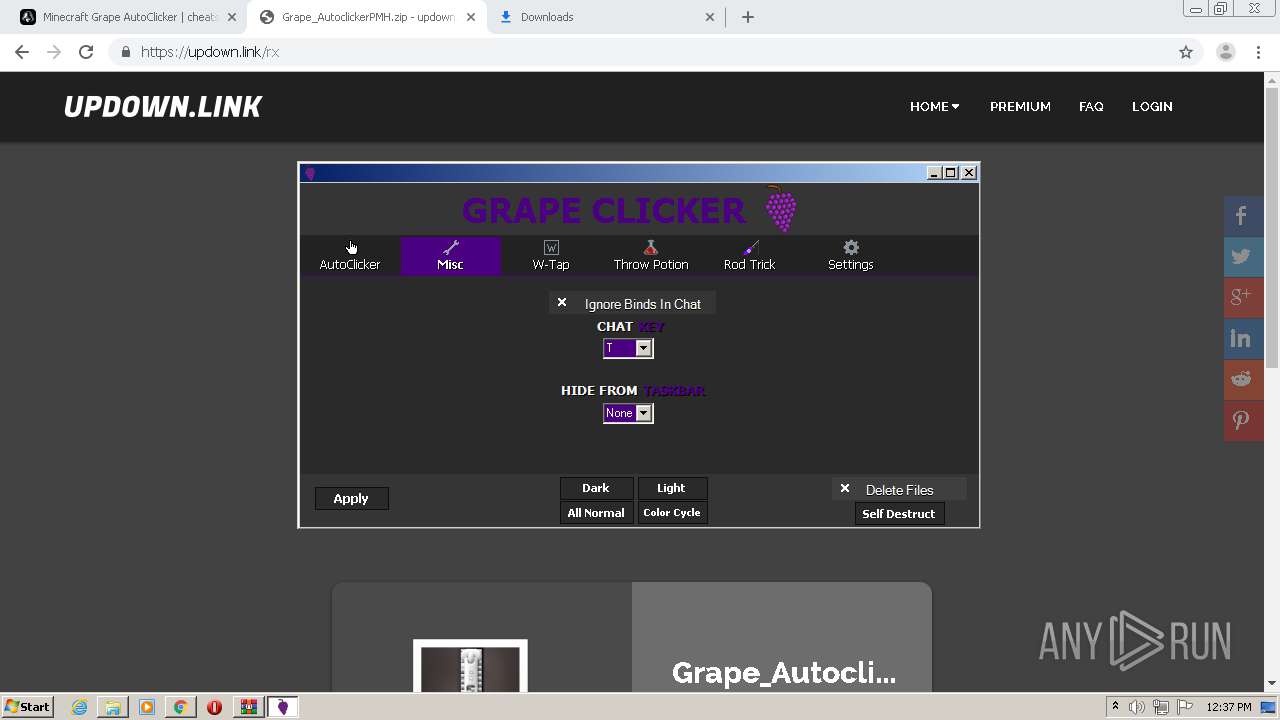
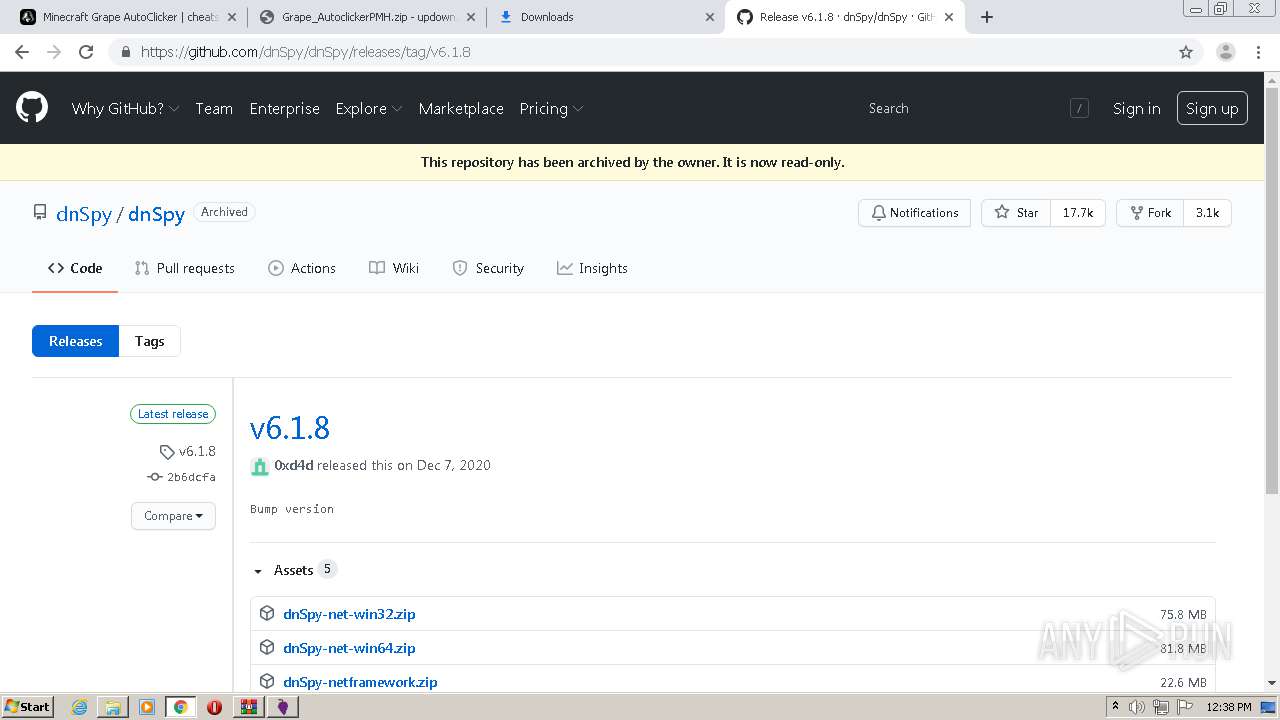
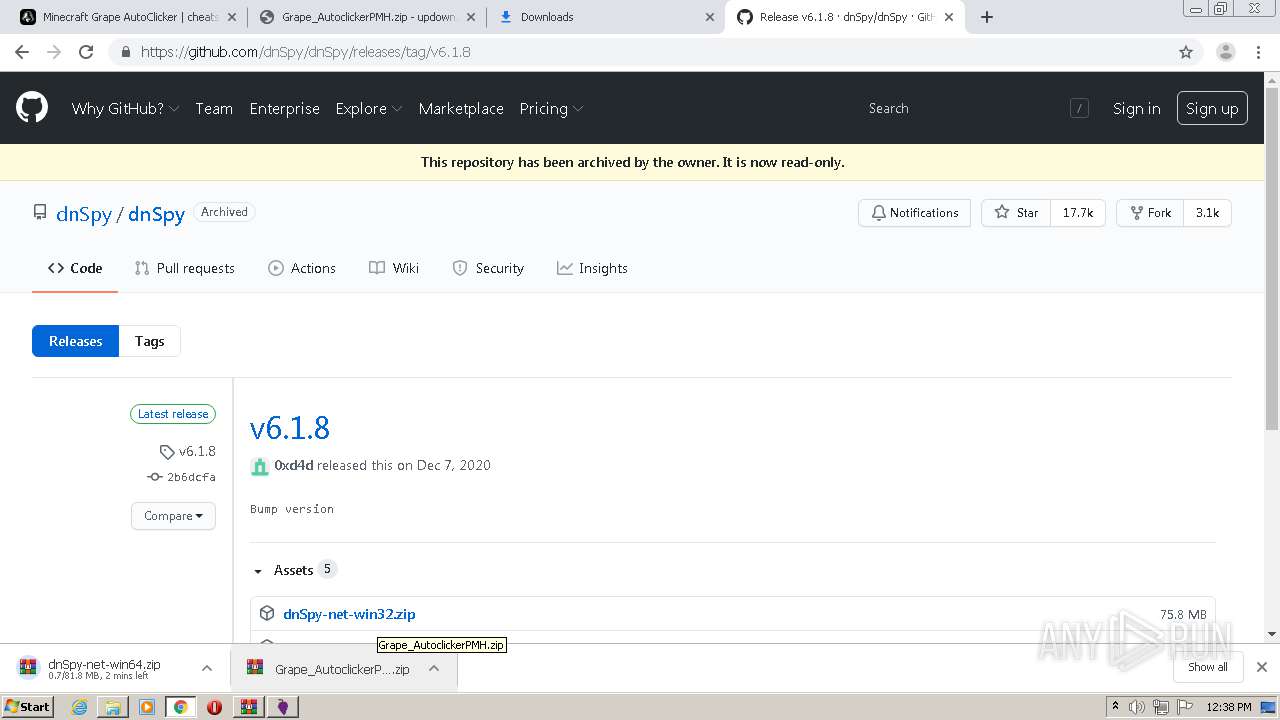
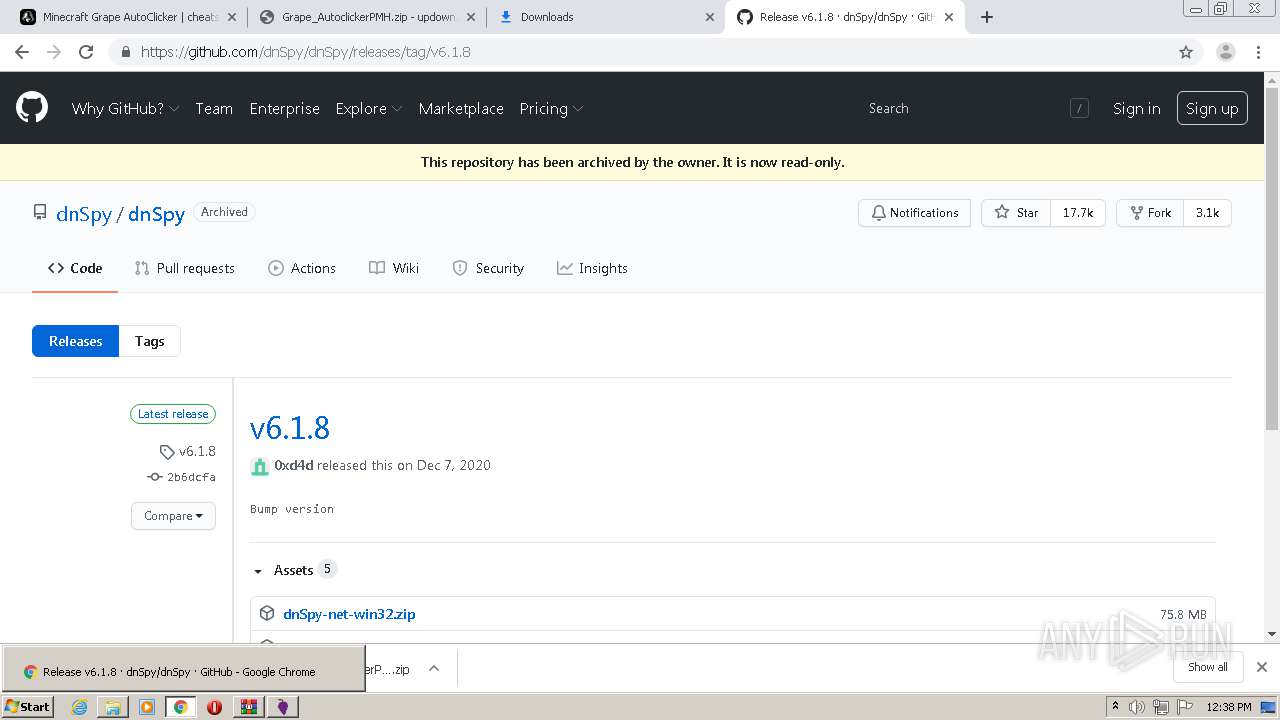
| URL: | https://cheatsquad.gg/cheat/gGP8YS |
| Full analysis: | https://app.any.run/tasks/f27e26c0-07f0-4596-8b5a-0bb4a48c2a8f |
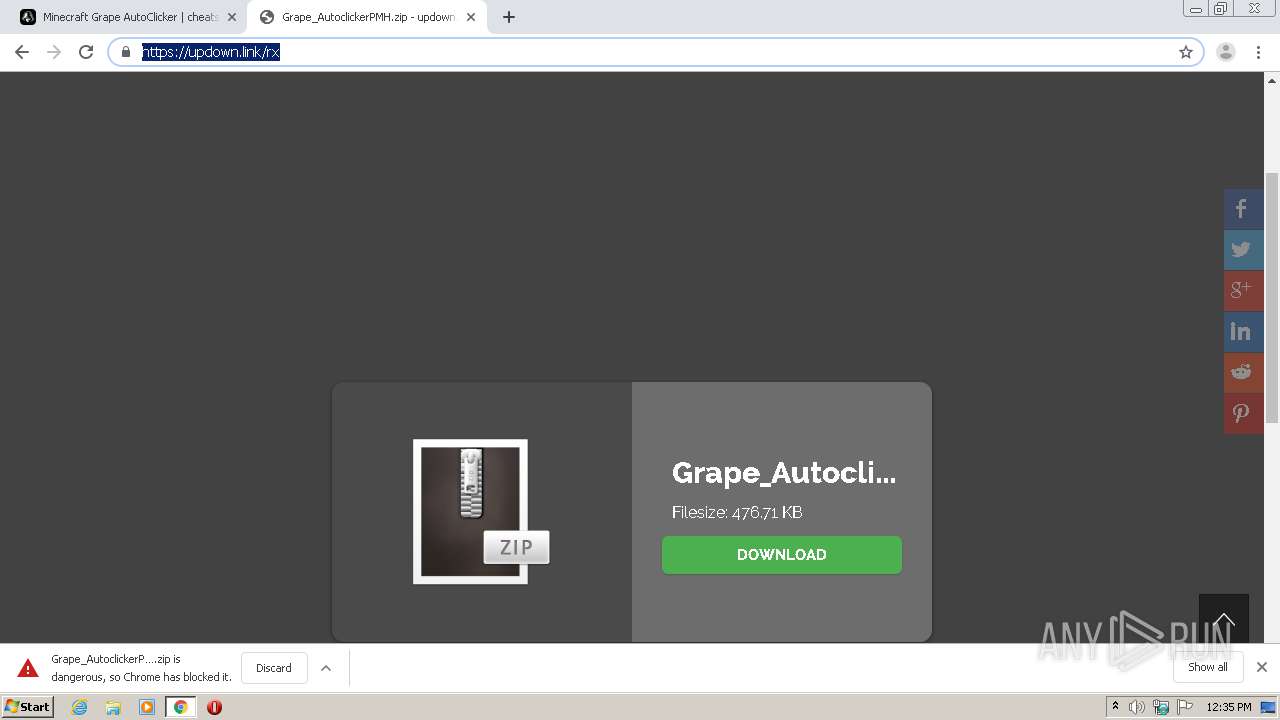
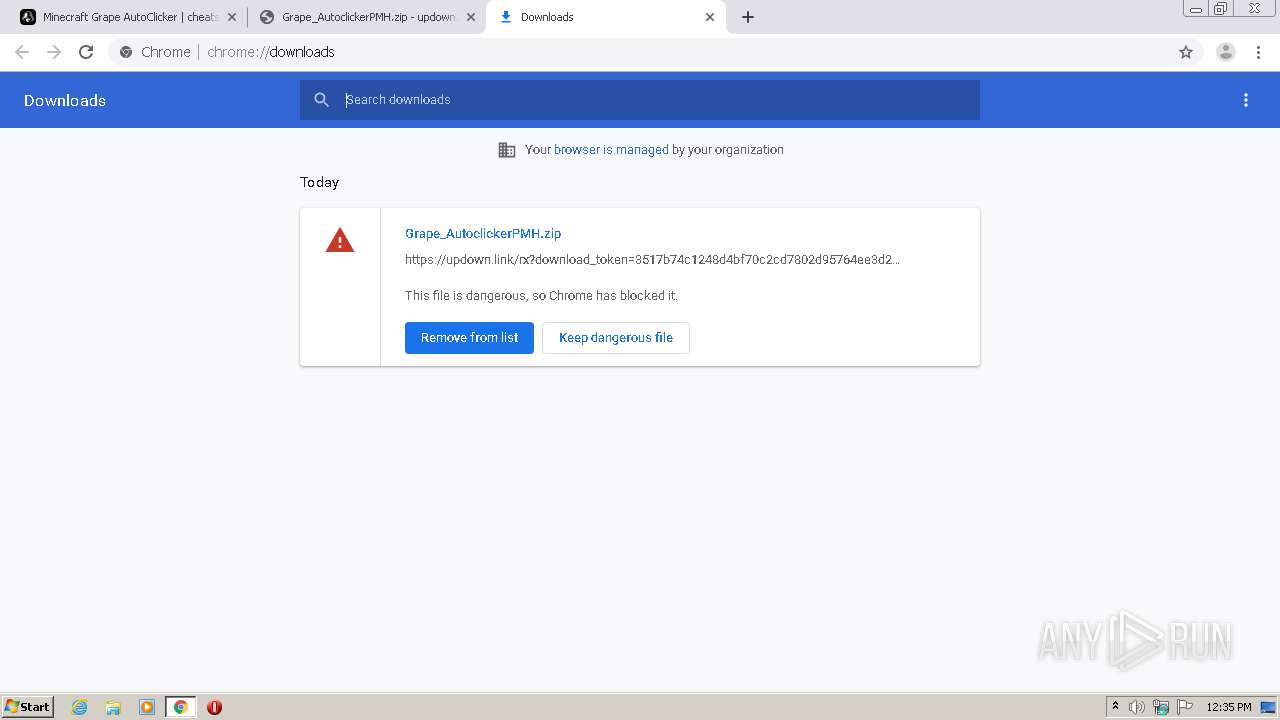
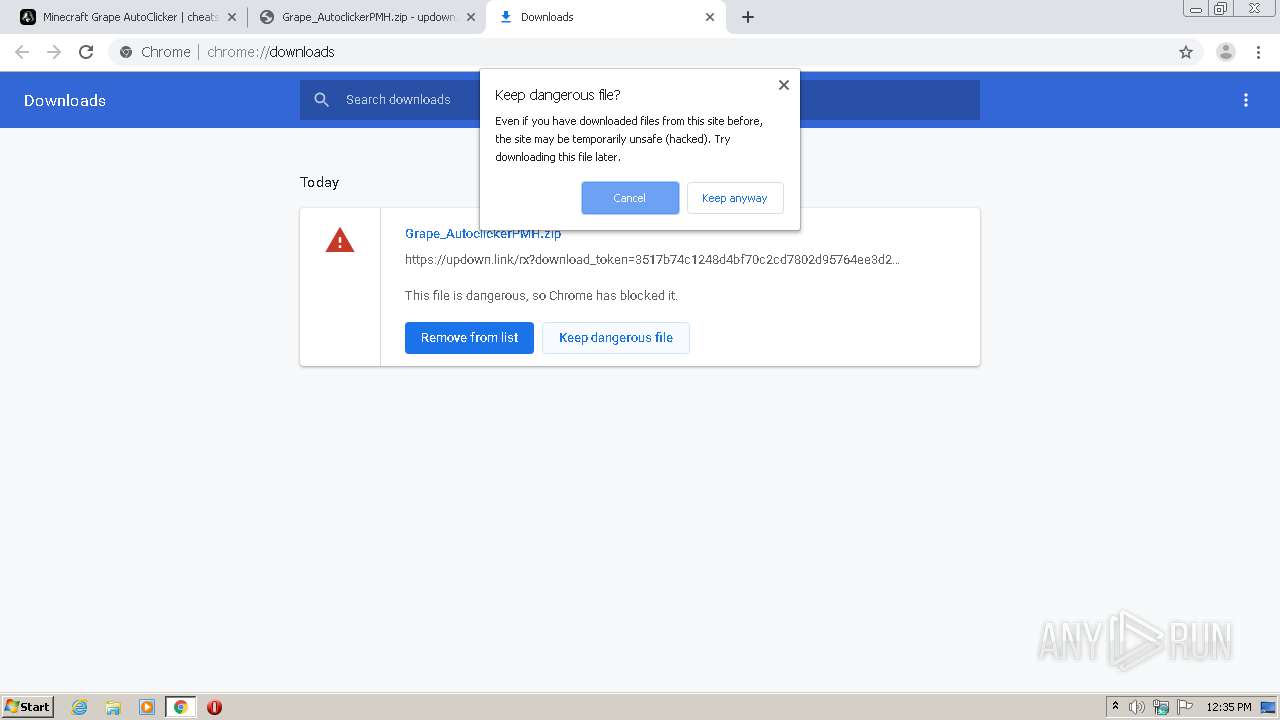
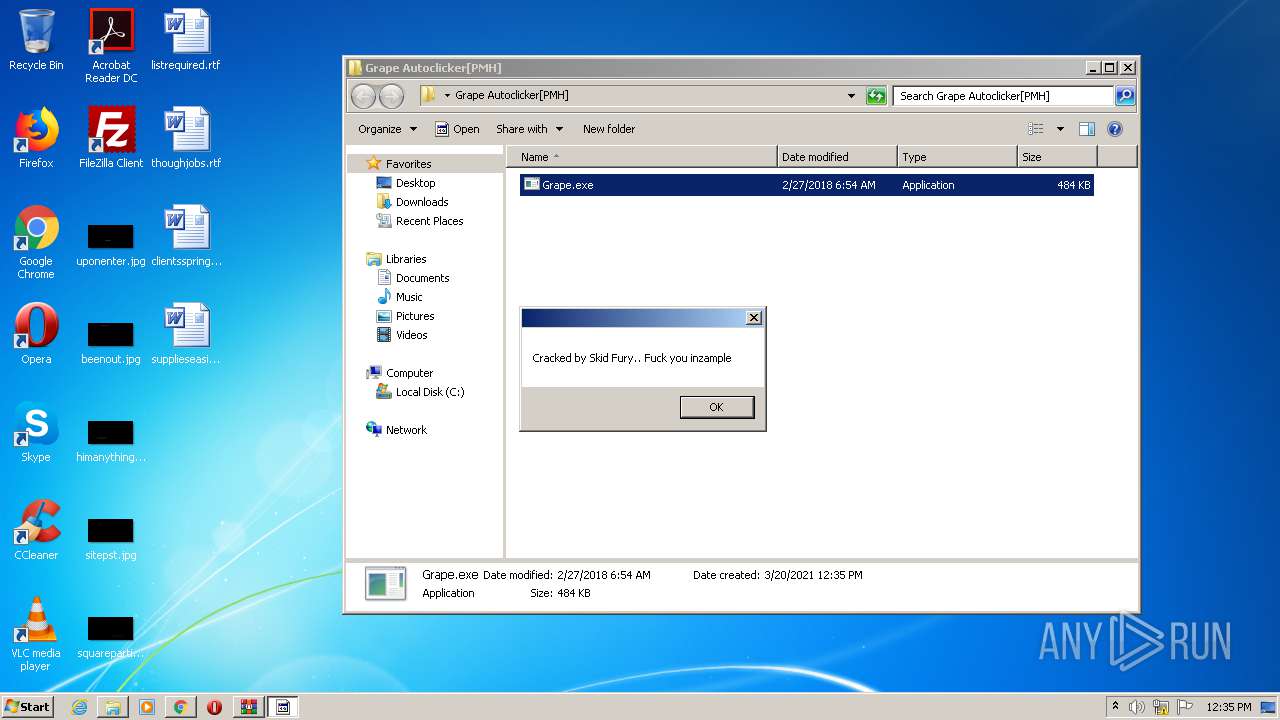
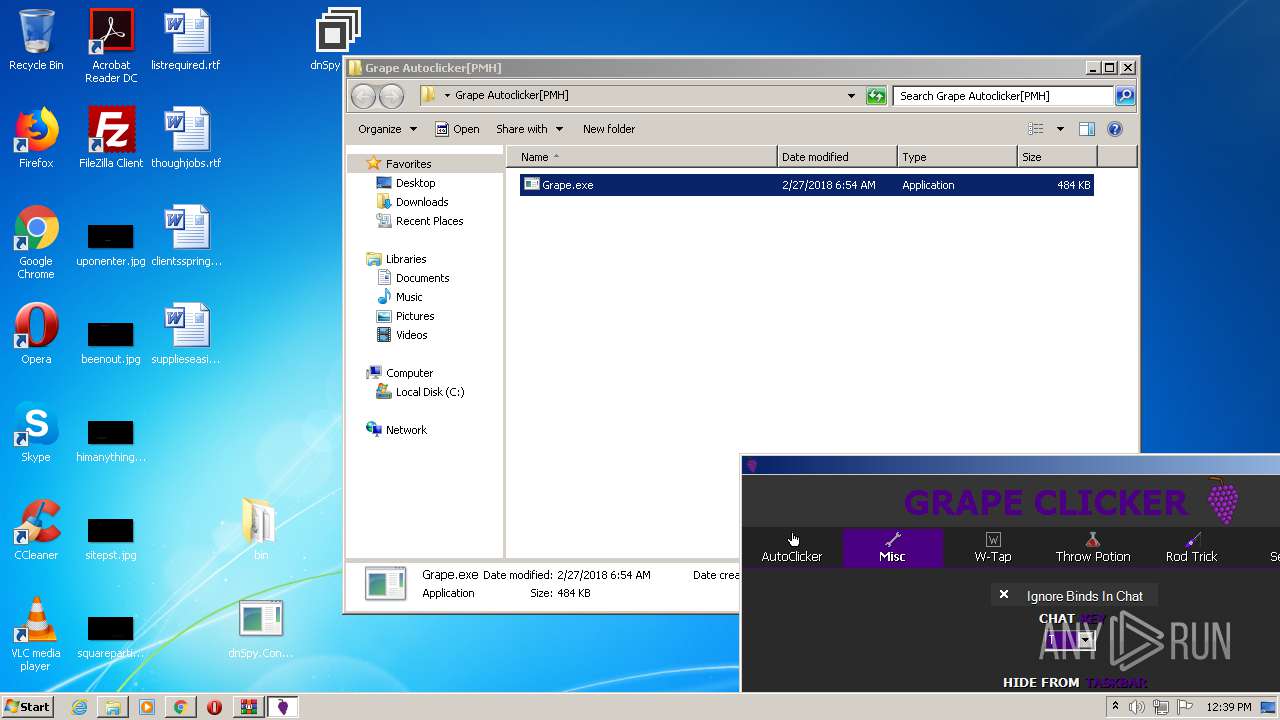
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2021, 12:34:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
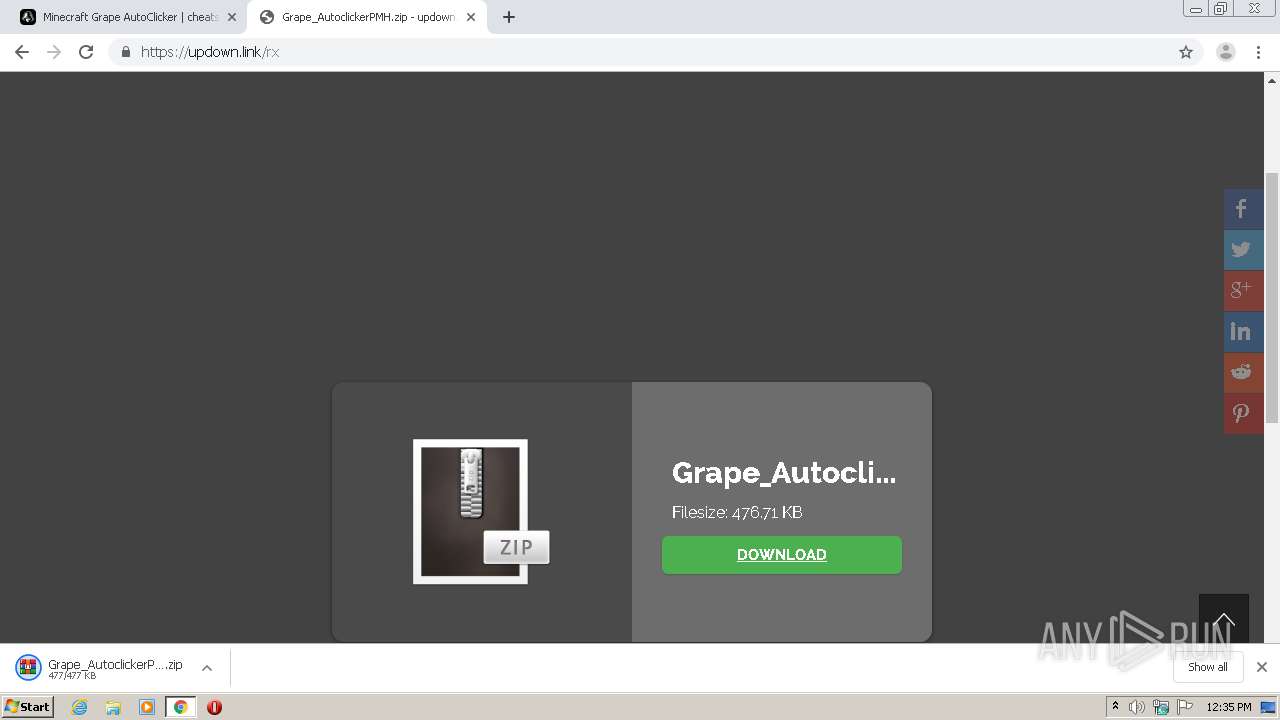
| MD5: | 6DBCEE5988D44A39EAEDA6AEC796A1D6 |
| SHA1: | 16D9C8F0087C58A474FF8BDDF77D5EE76FEC0504 |
| SHA256: | DF117C4F9E07DA9DA1DC979408D65A3B8FACD27412A962C0FFAB495BAE44B75C |
| SSDEEP: | 3:N8Q2URB2ORKCW+2n:2Q2U21CW+2n |
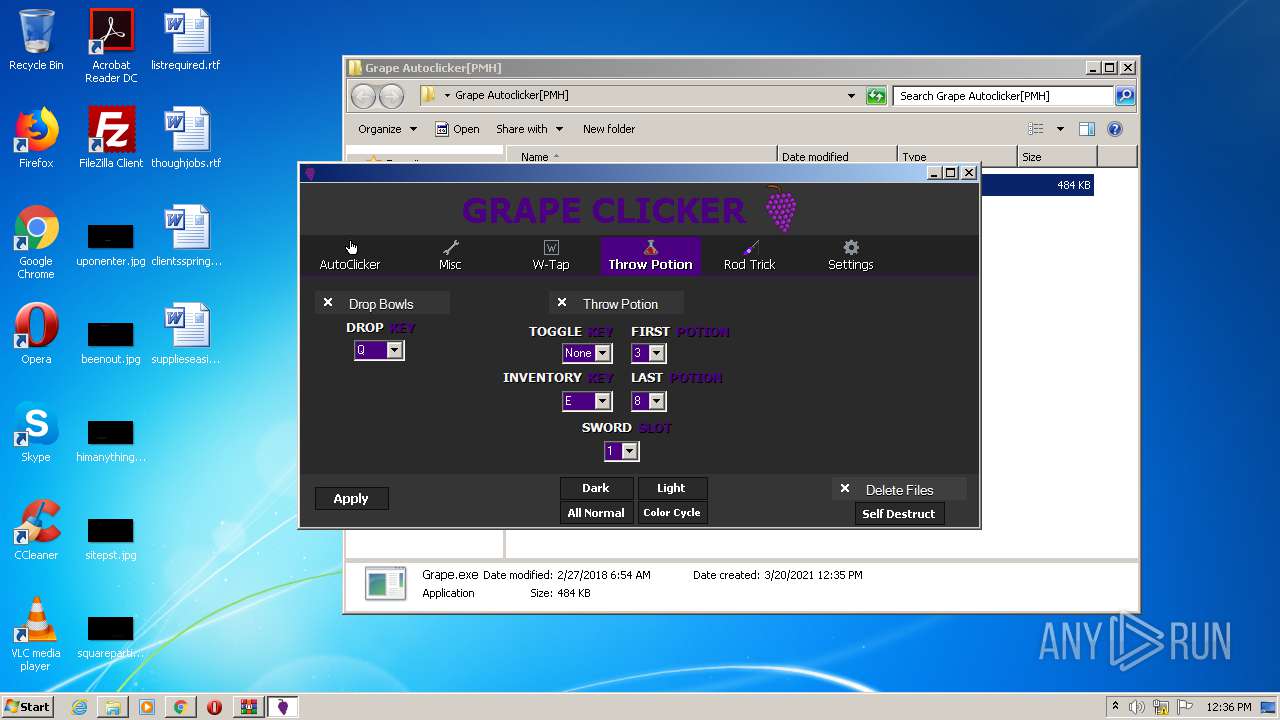
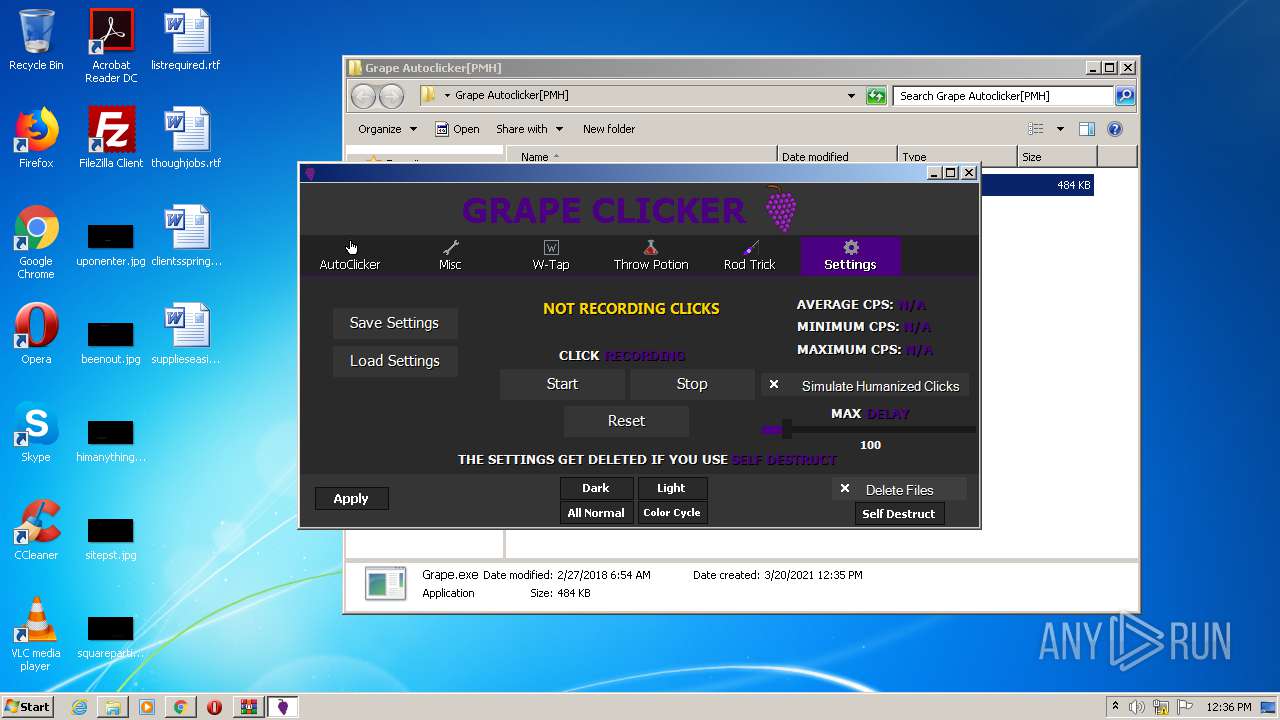
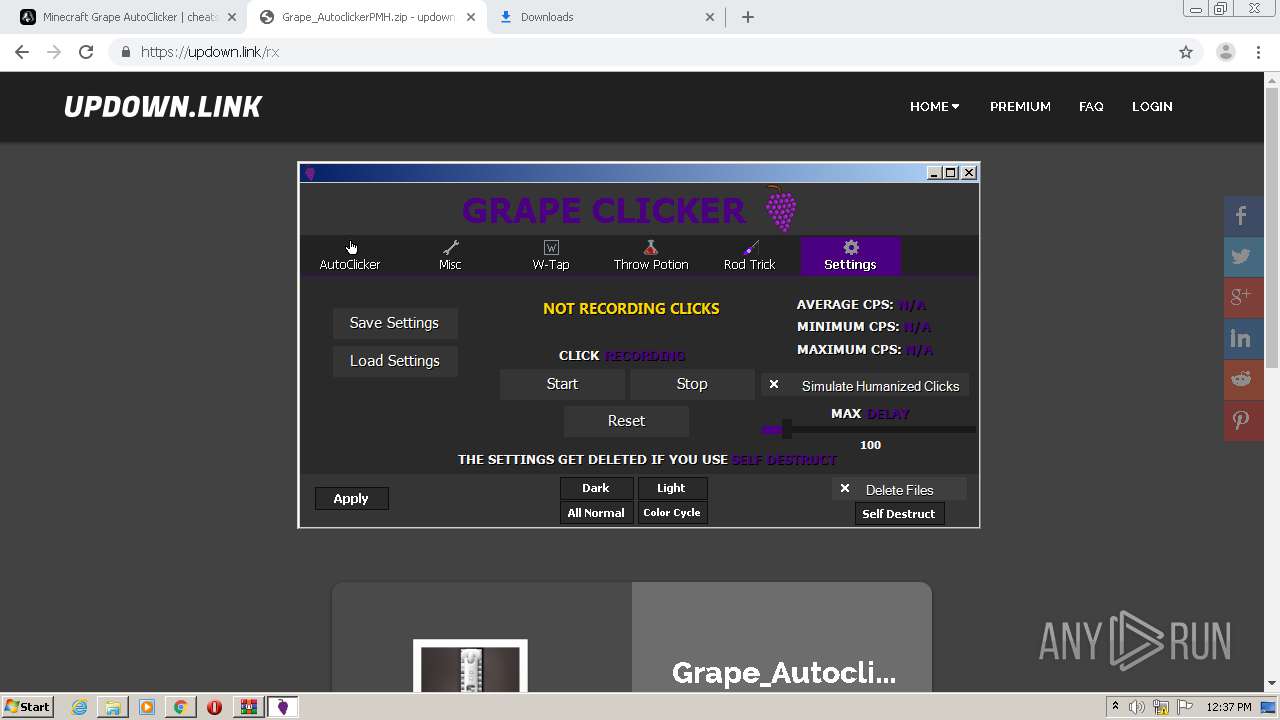
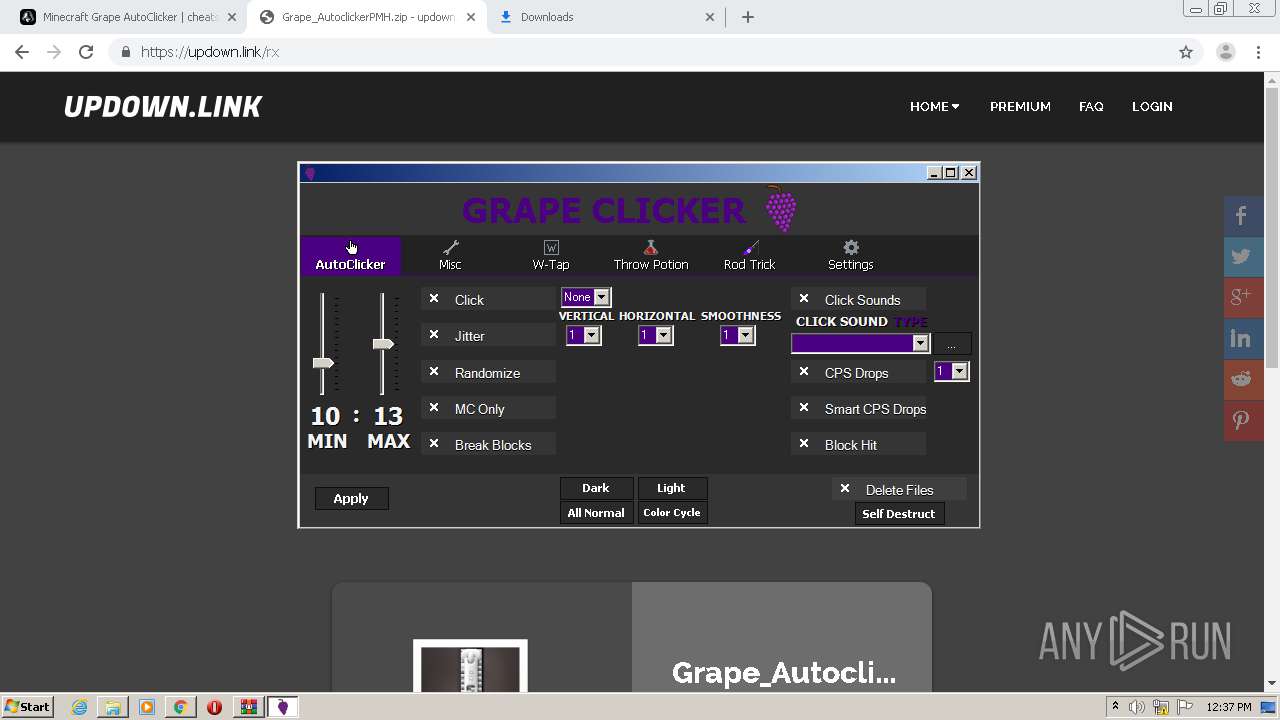
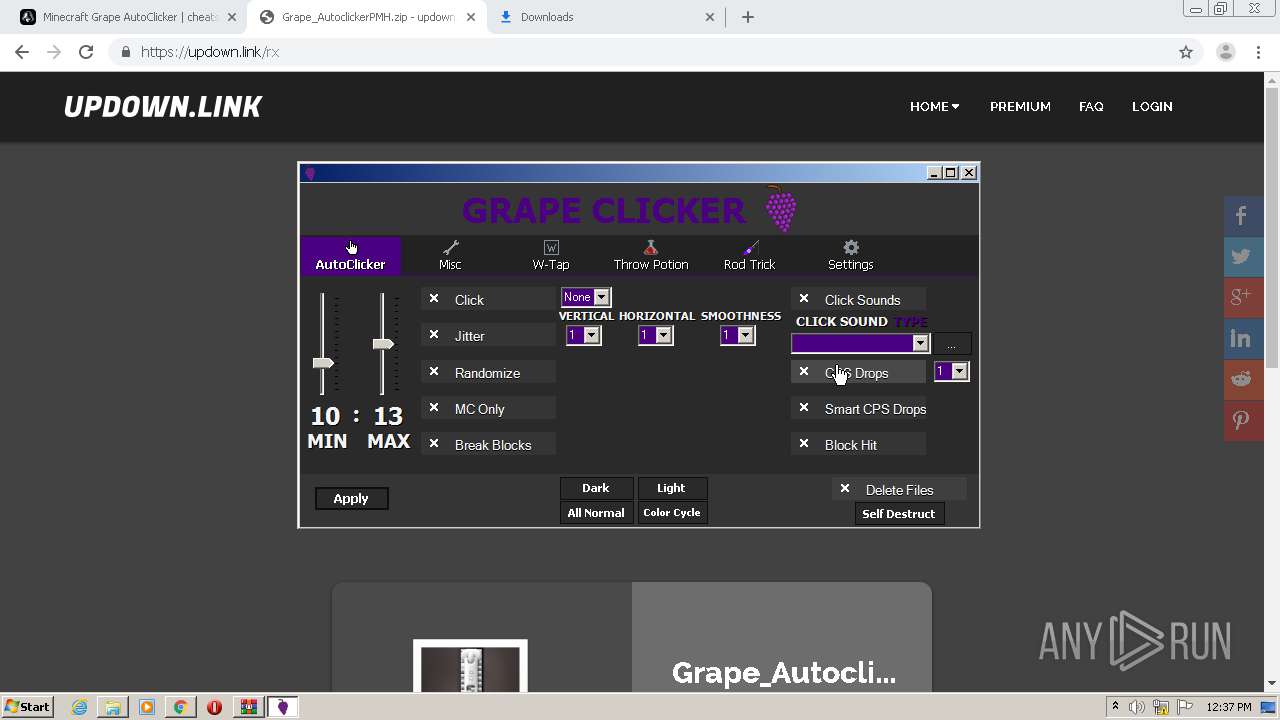
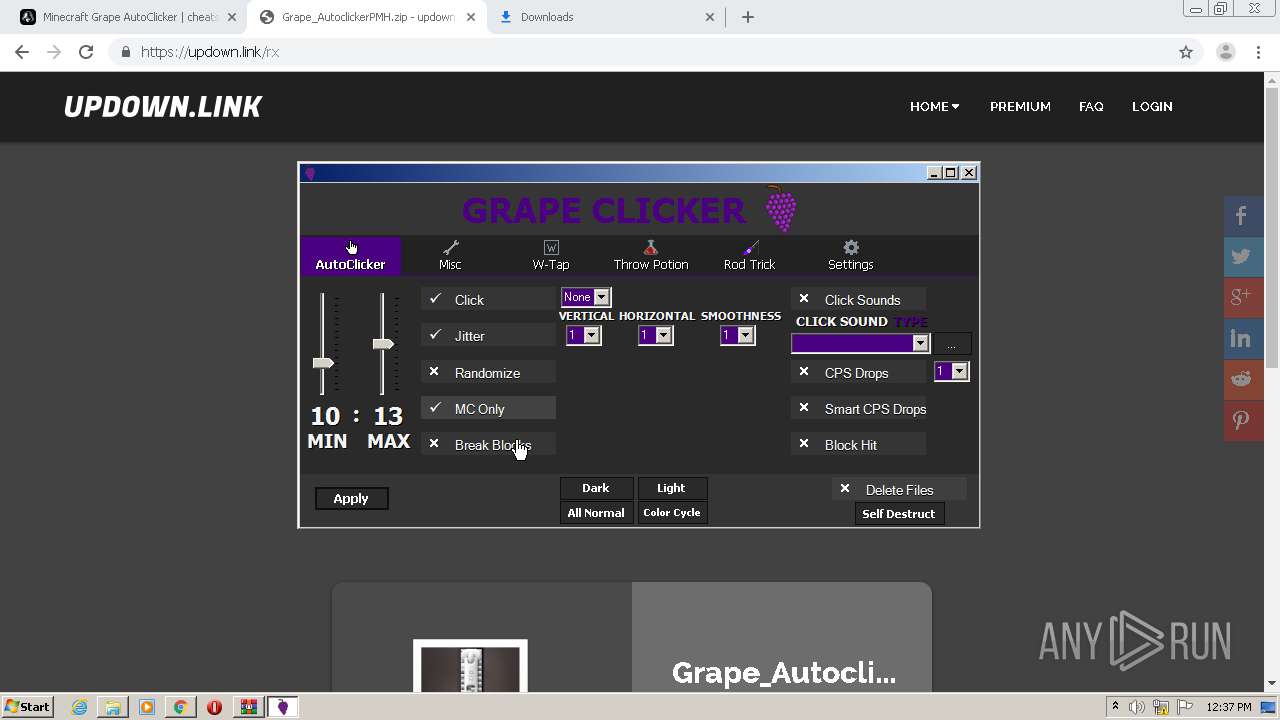
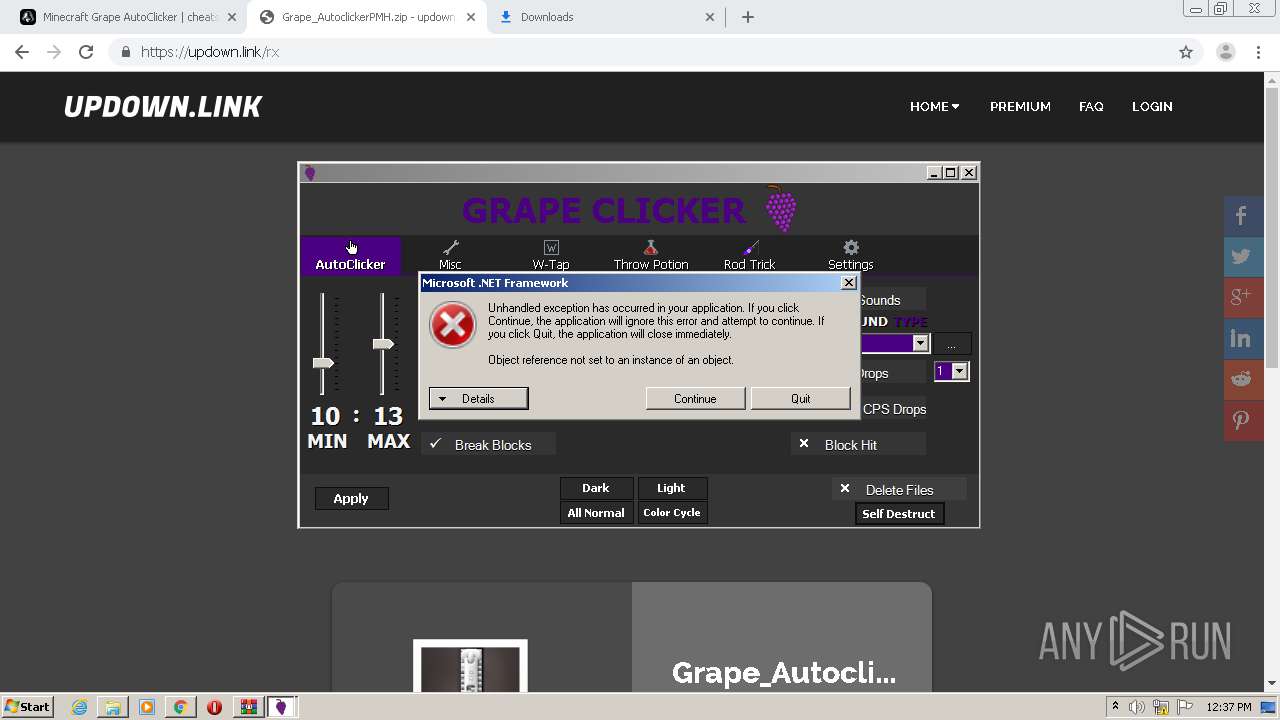
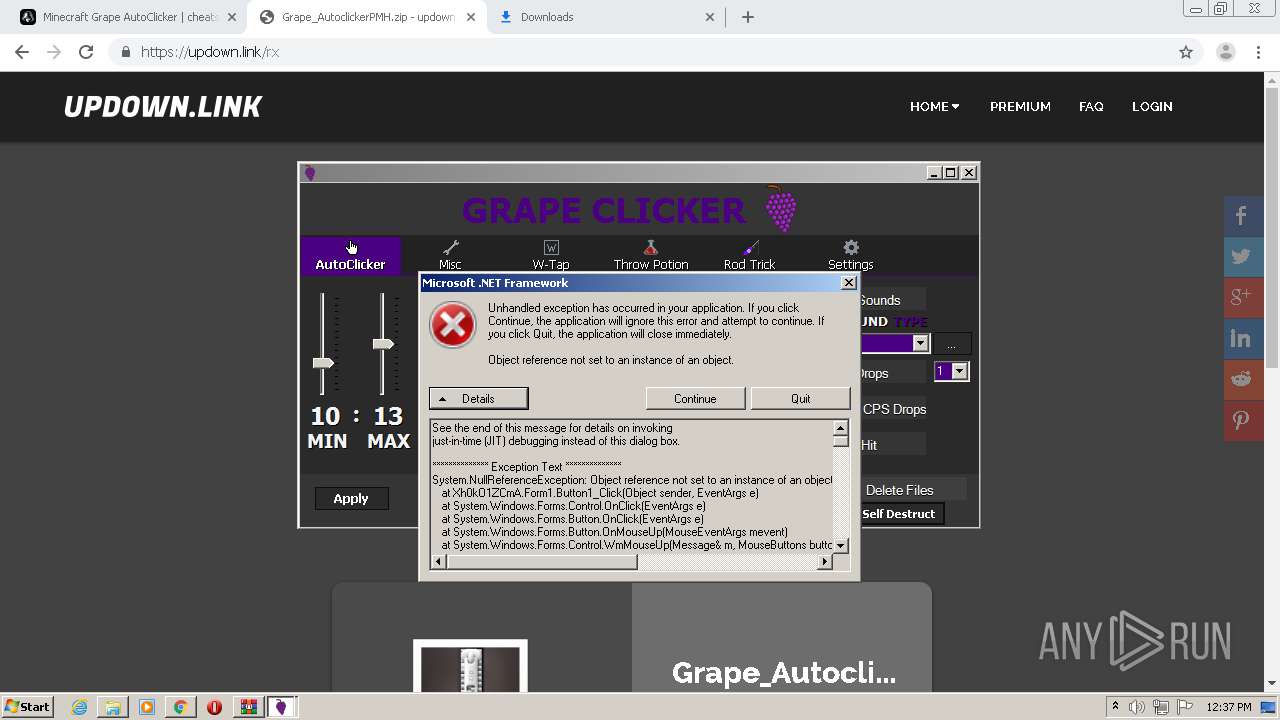
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3052)
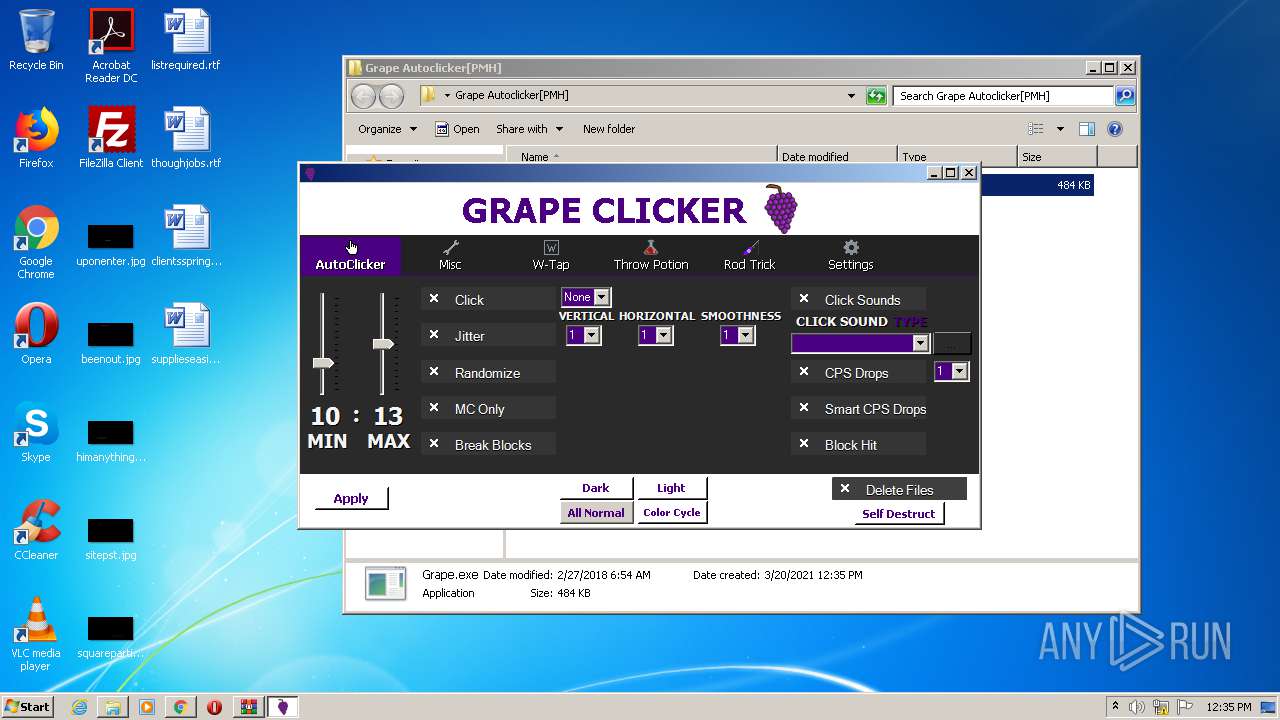
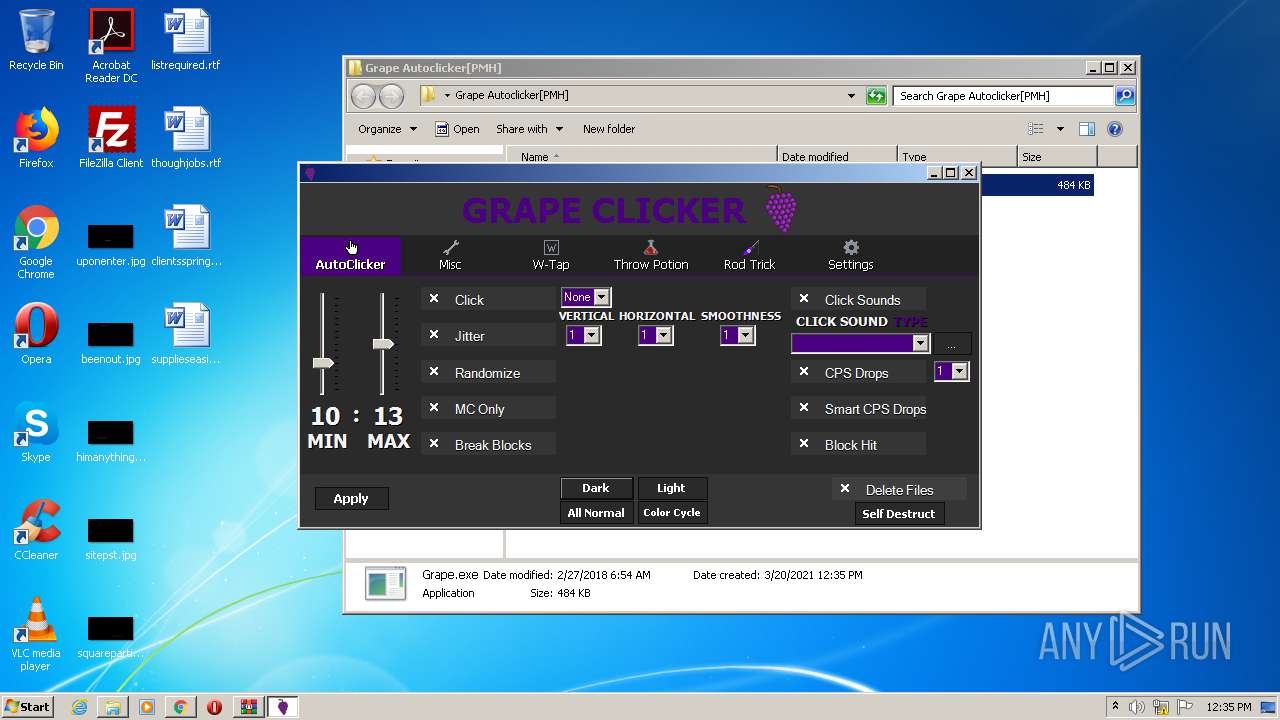
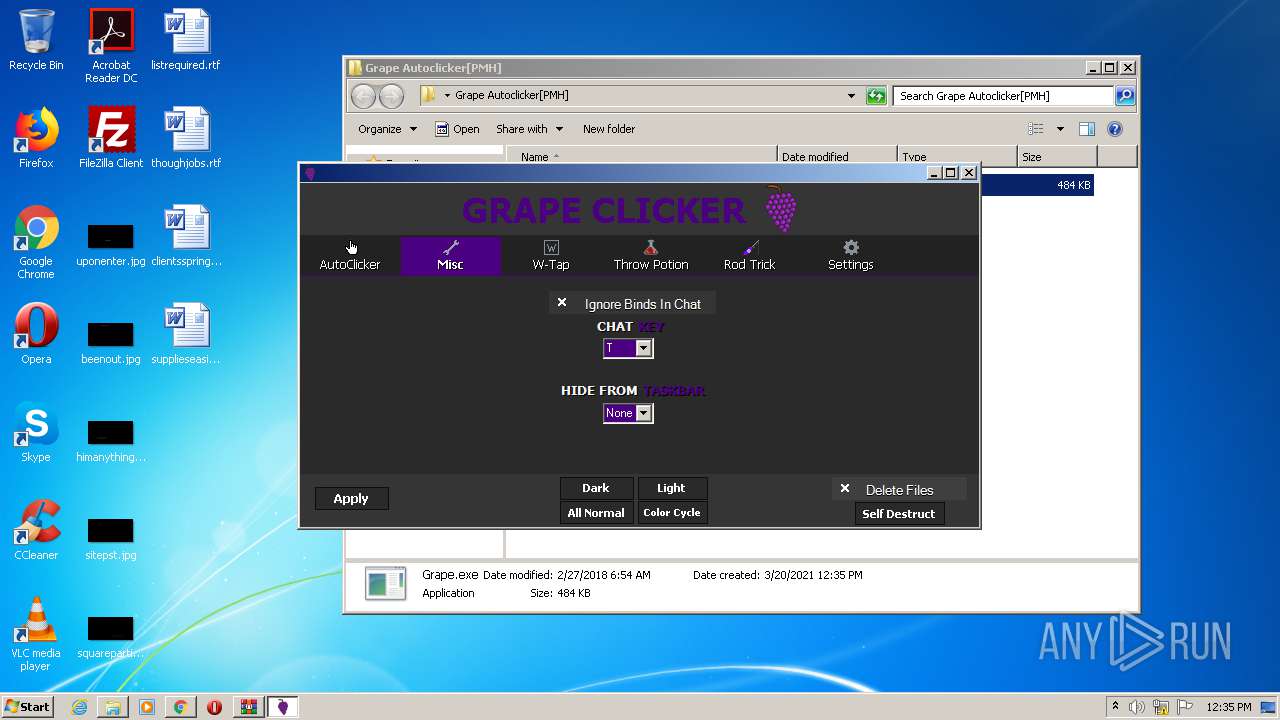
SUSPICIOUS
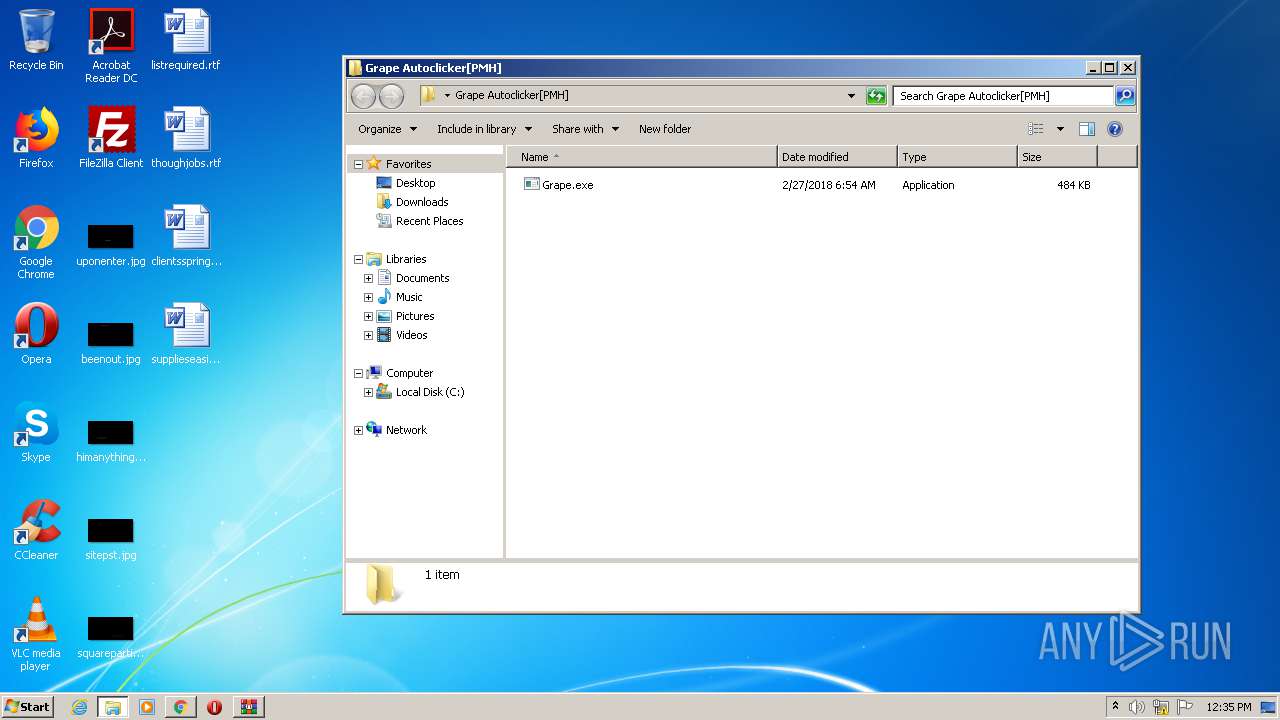
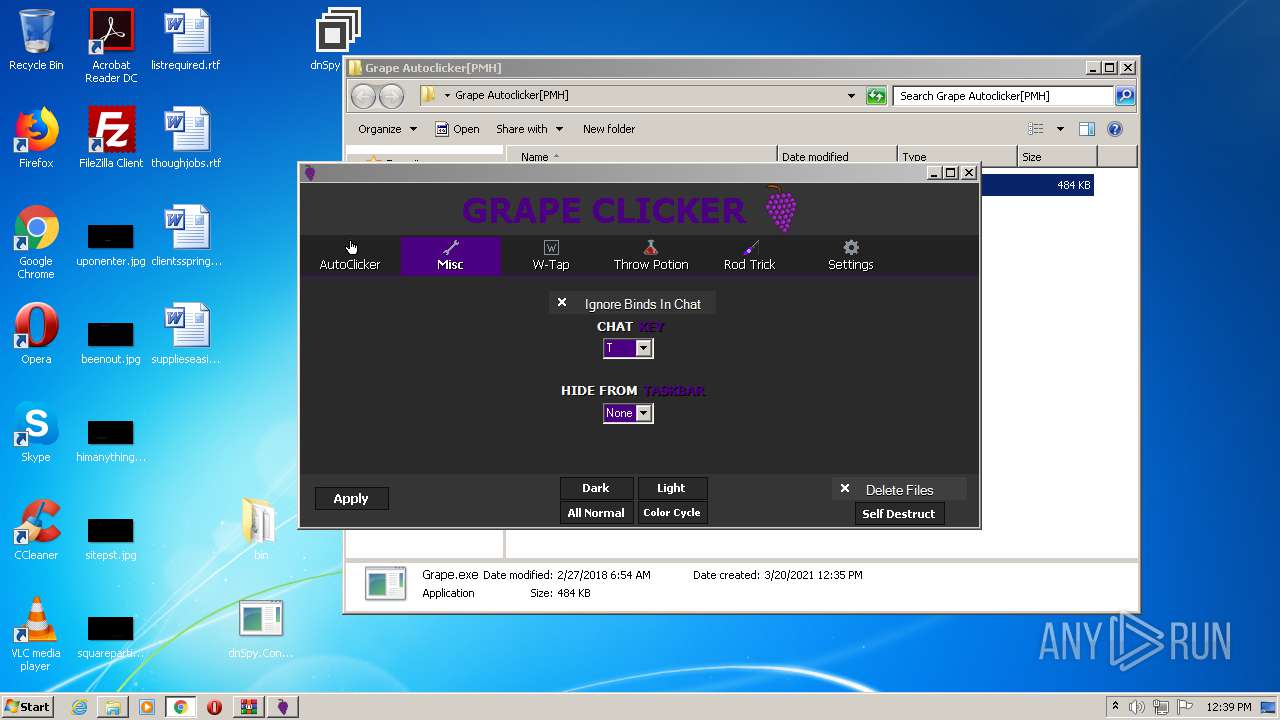
Starts CMD.EXE for commands execution
- Grape.exe (PID: 2444)
Starts CMD.EXE for self-deleting
- Grape.exe (PID: 2444)
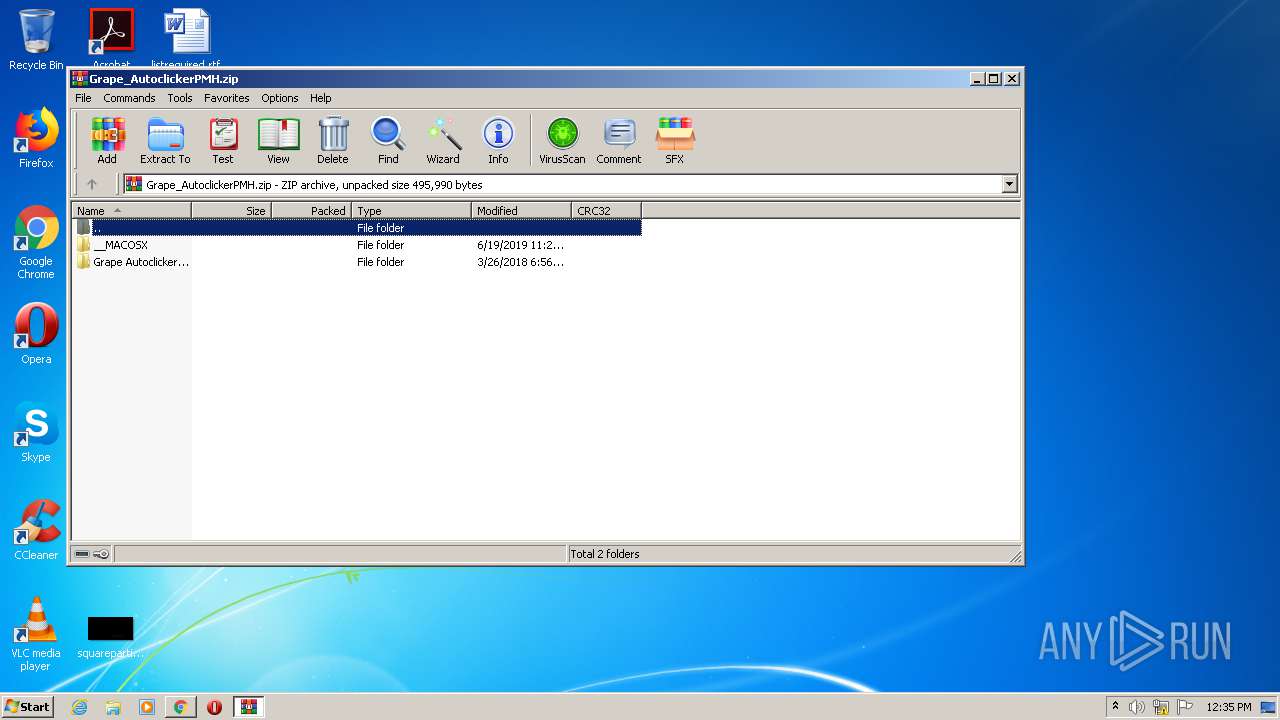
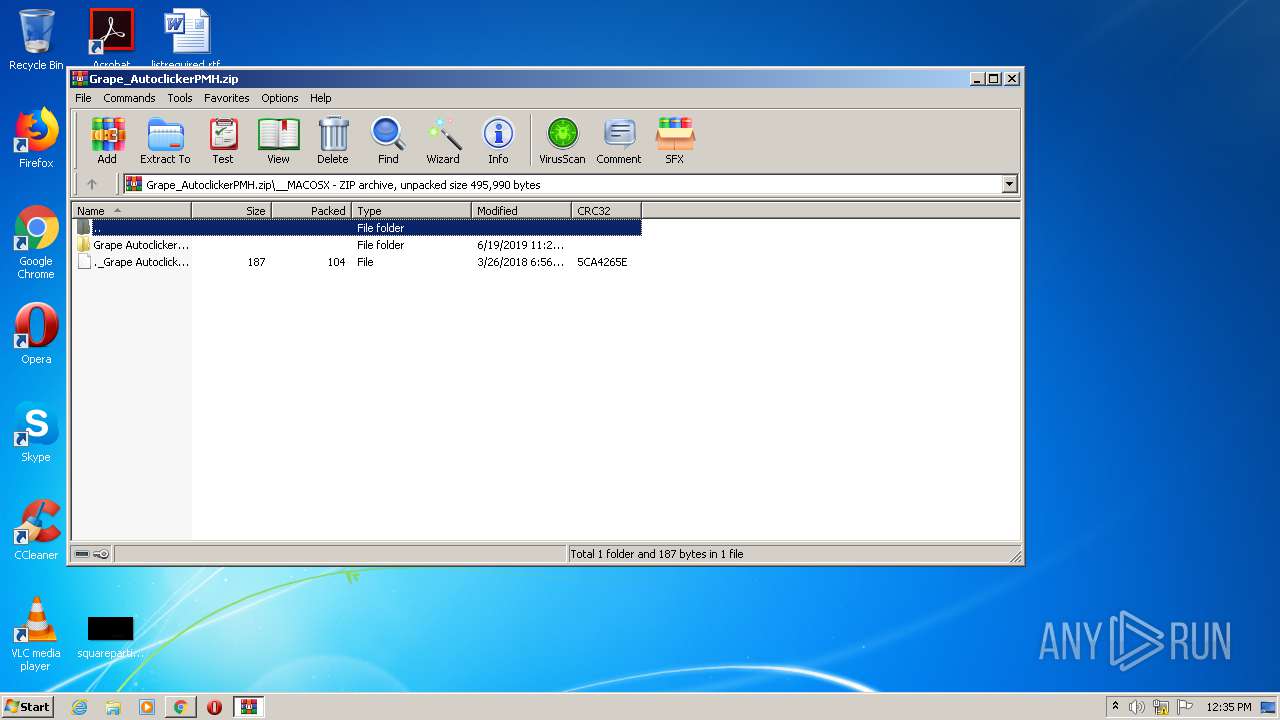
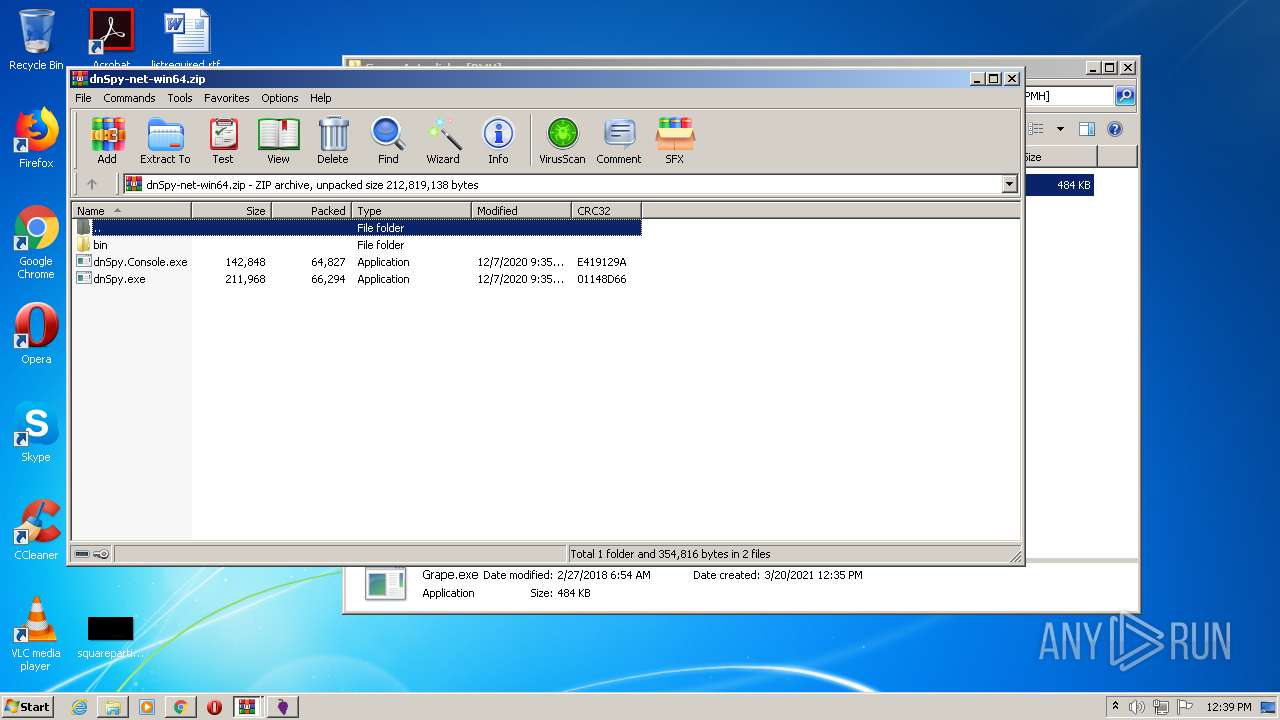
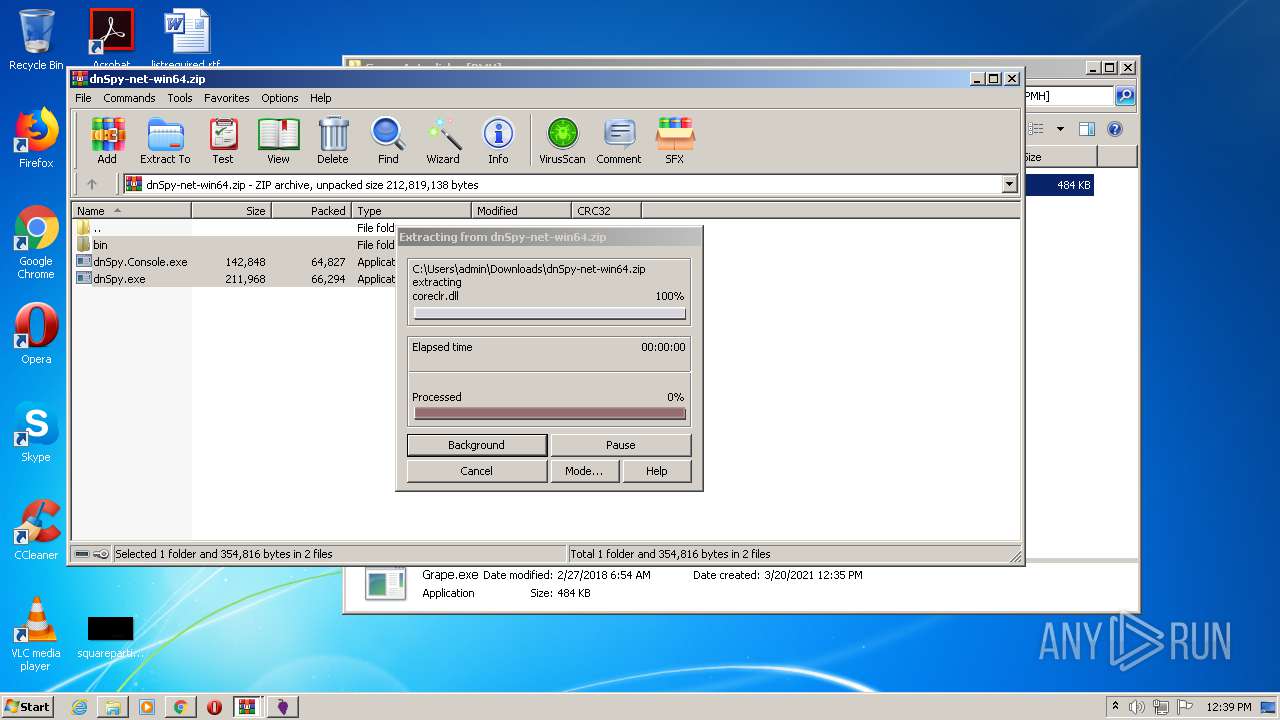
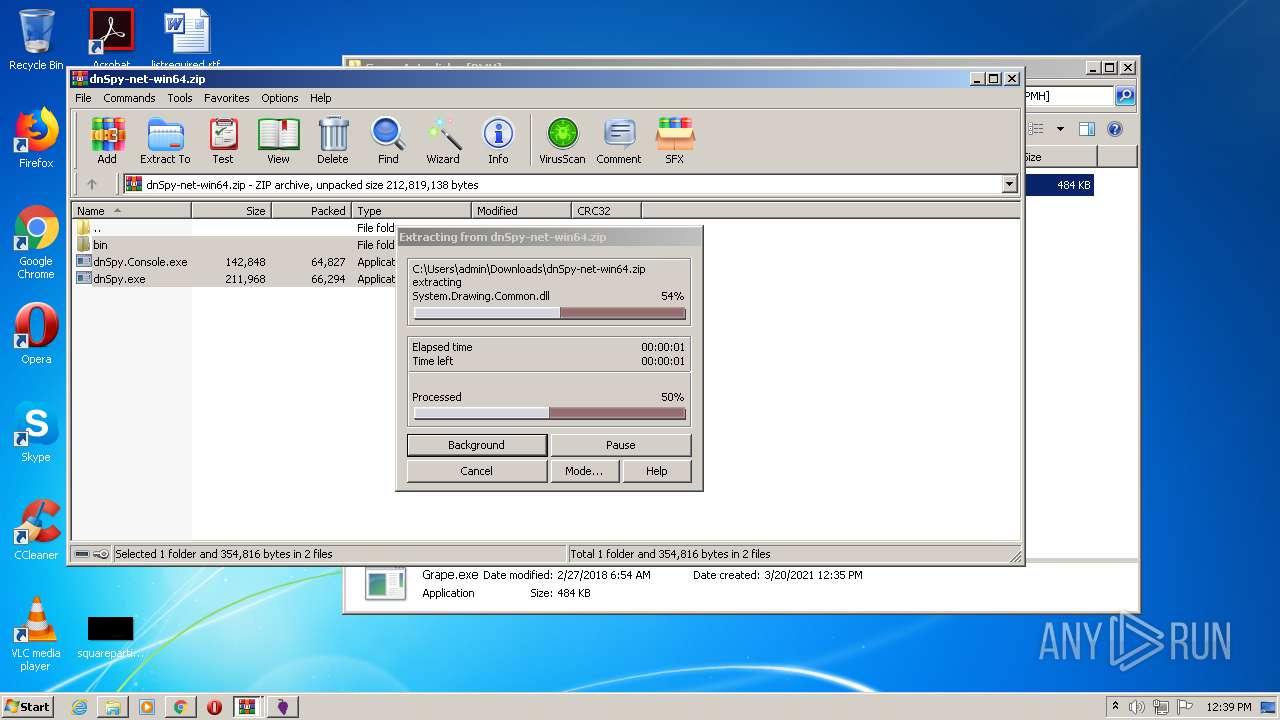
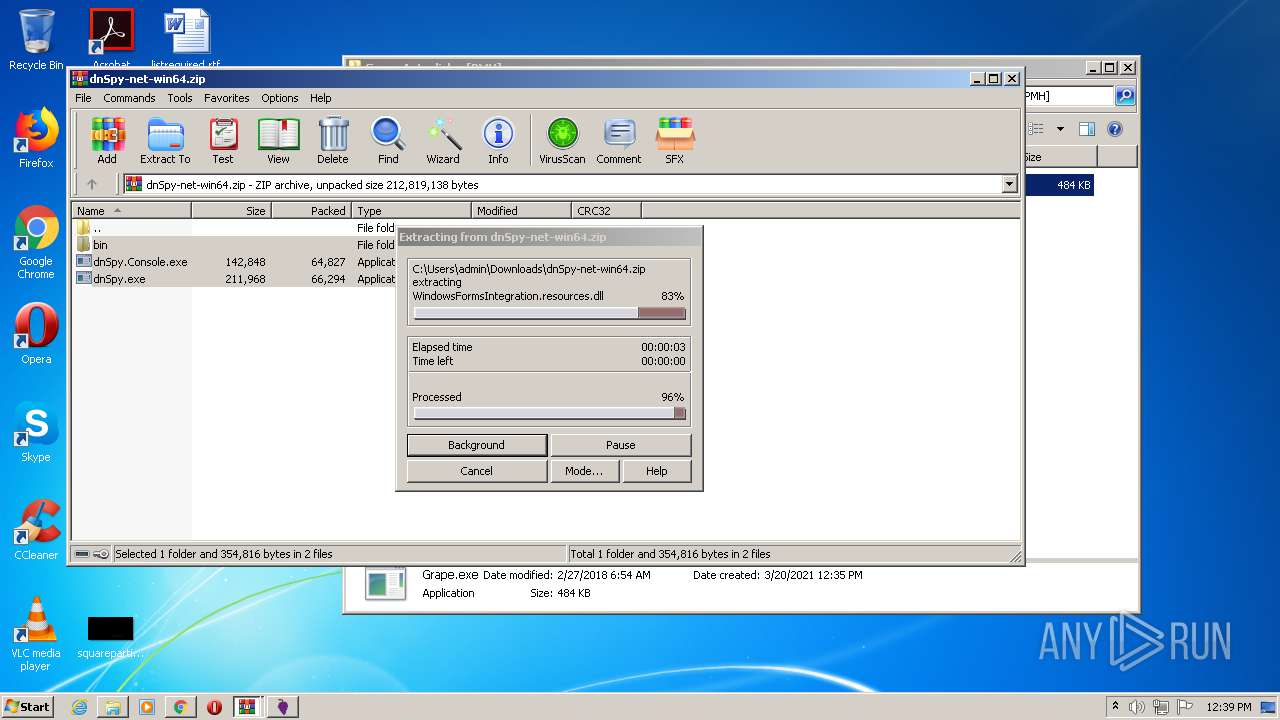
Drops a file with a compile date too recent
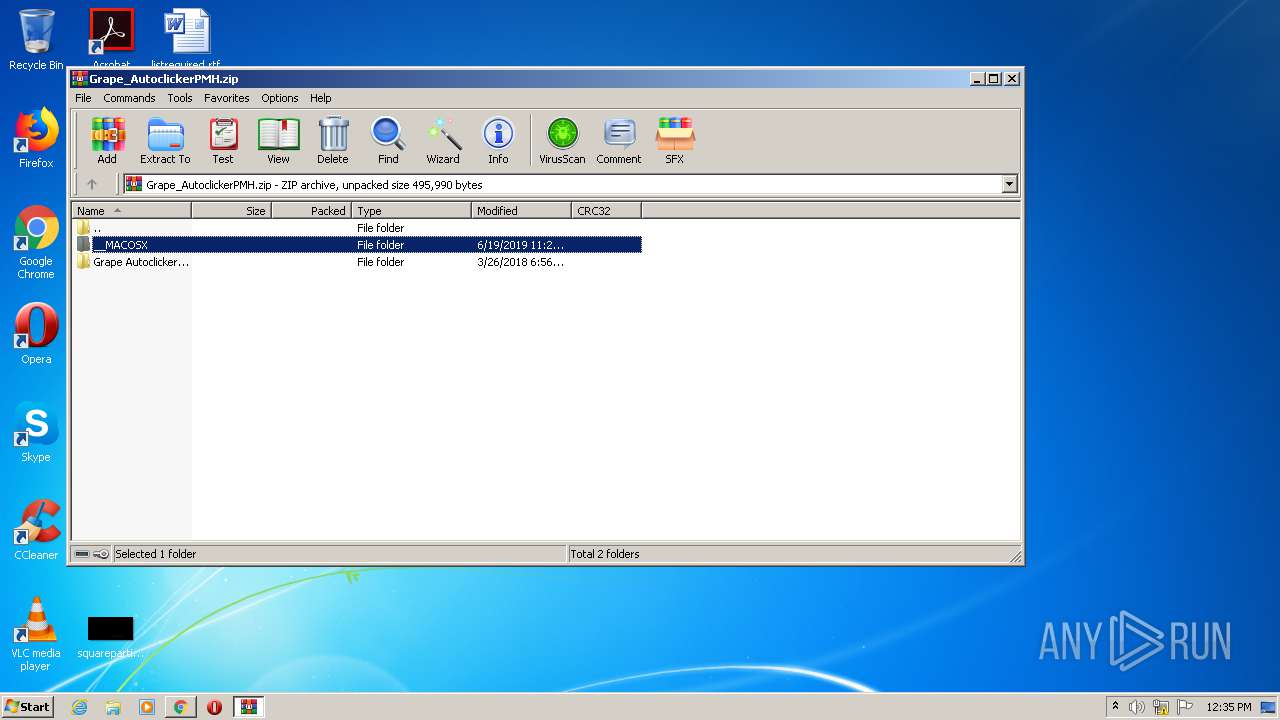
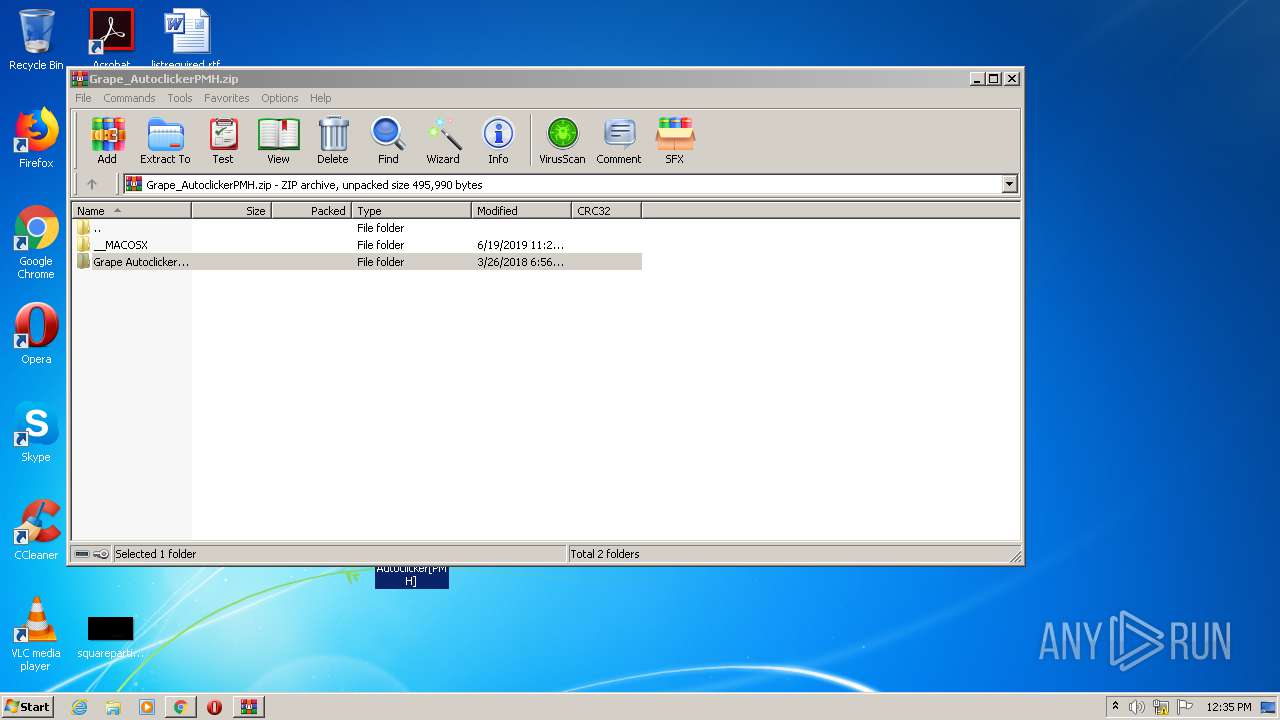
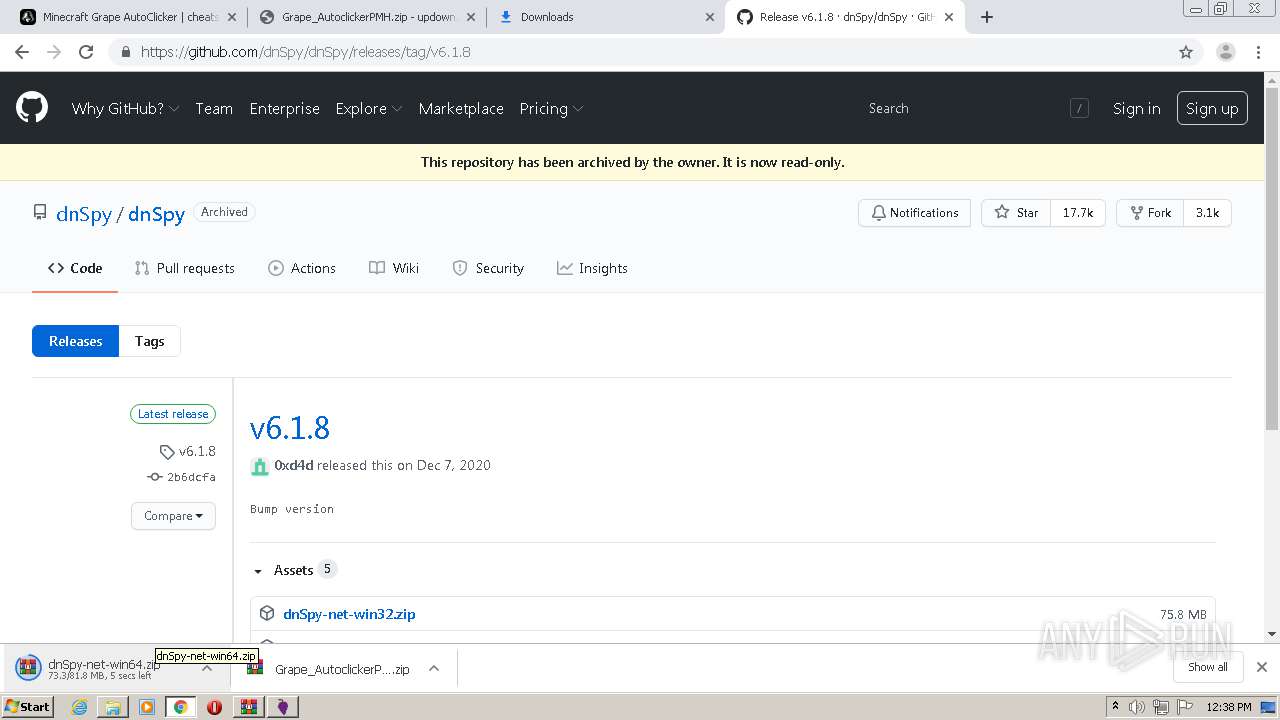
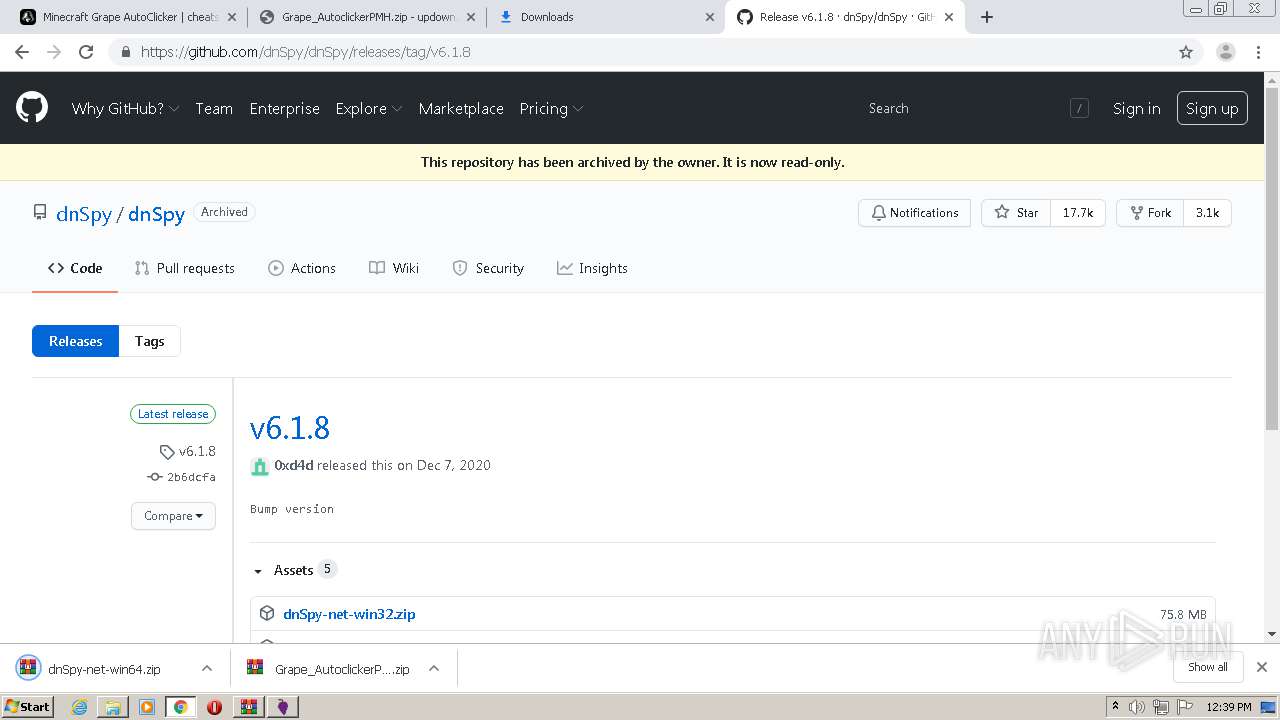
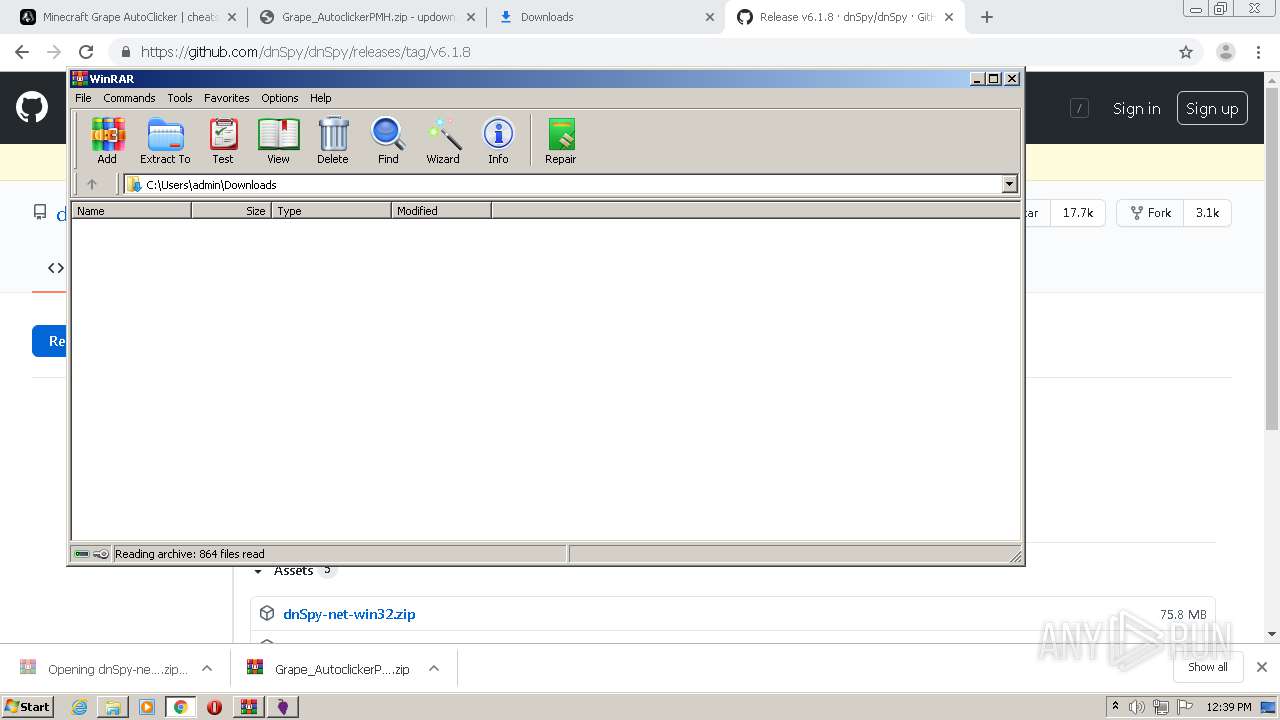
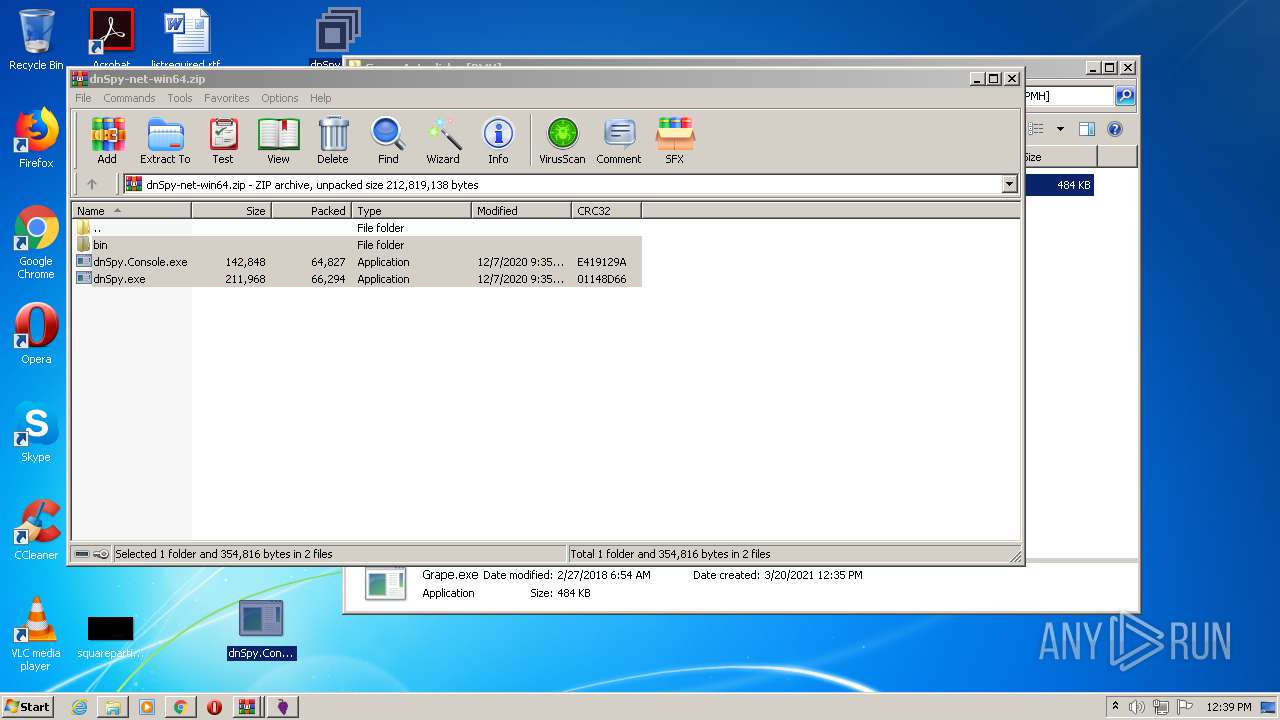
- WinRAR.exe (PID: 1708)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1708)
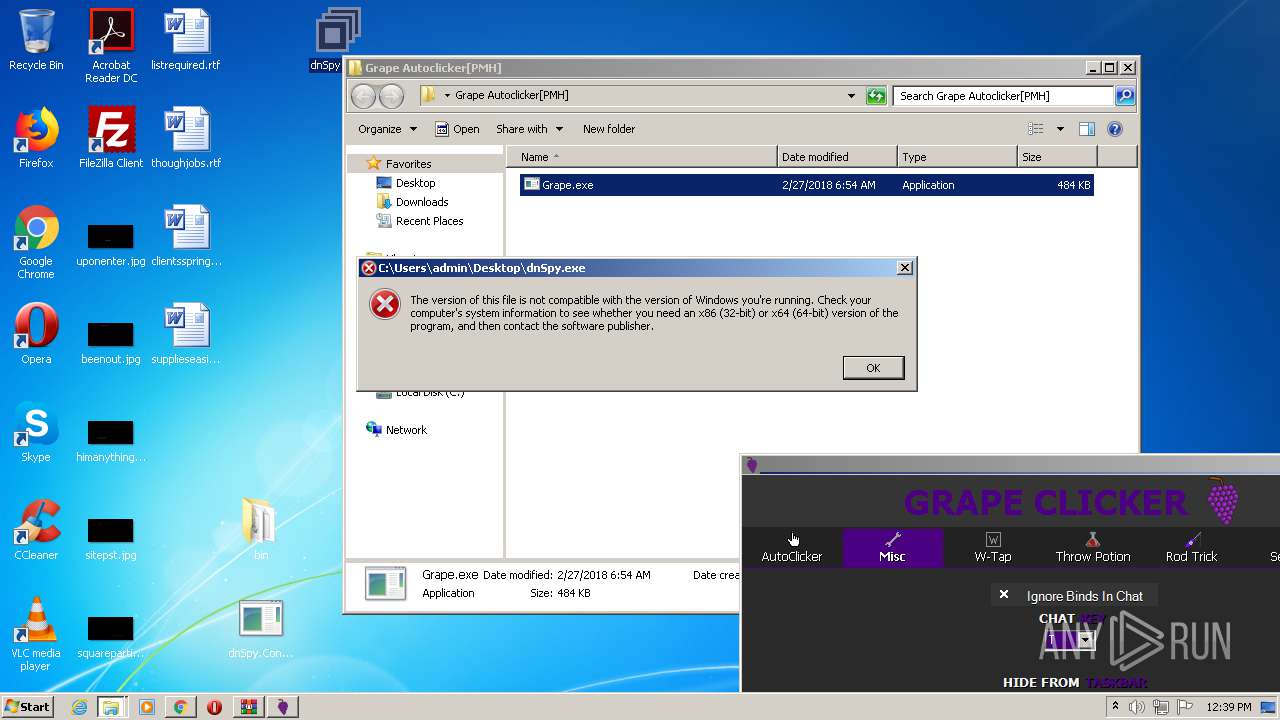
Drops a file with too old compile date
- WinRAR.exe (PID: 1708)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1708)
INFO
Reads the hosts file
- chrome.exe (PID: 2484)
- chrome.exe (PID: 2124)
Reads settings of System Certificates
- chrome.exe (PID: 2124)
Application launched itself
- chrome.exe (PID: 2484)
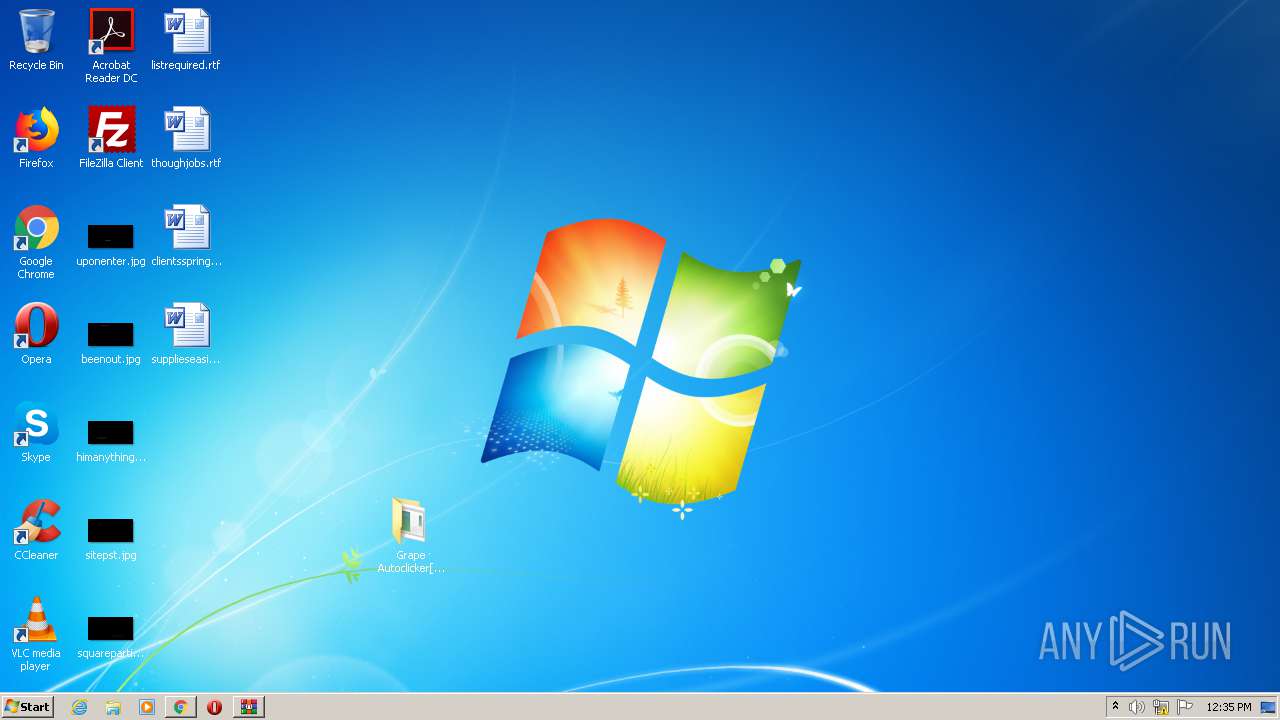
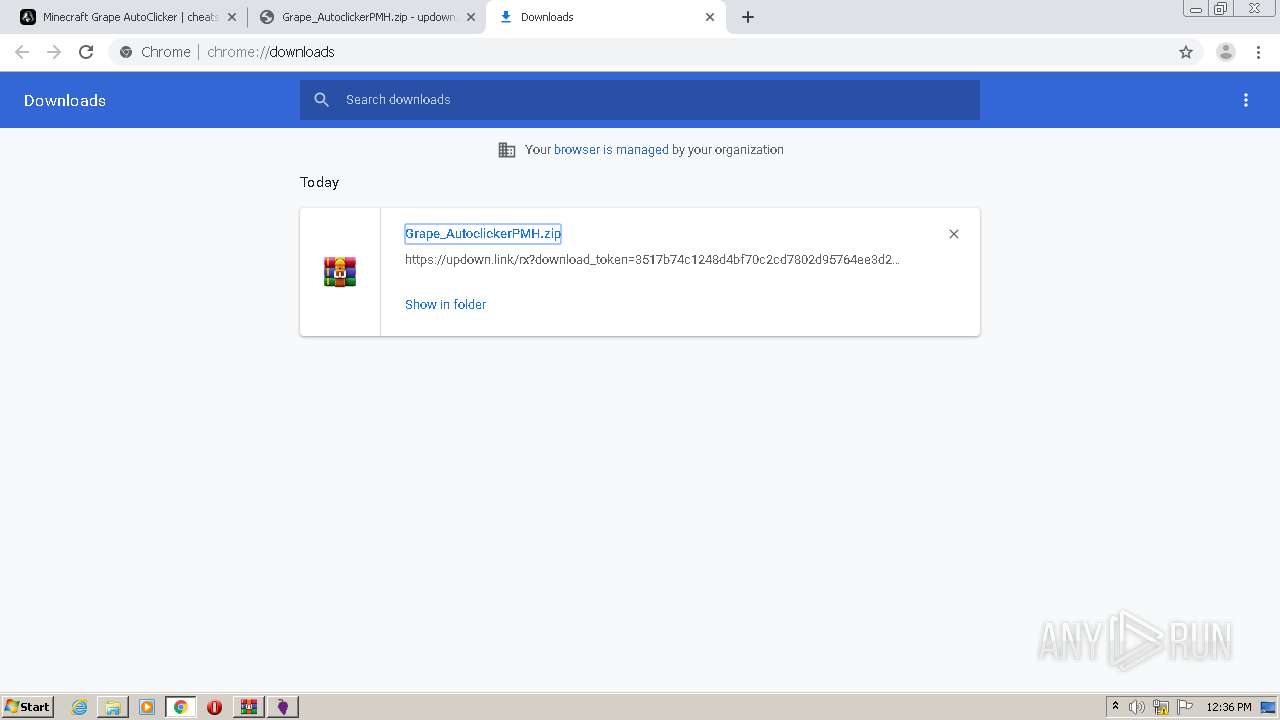
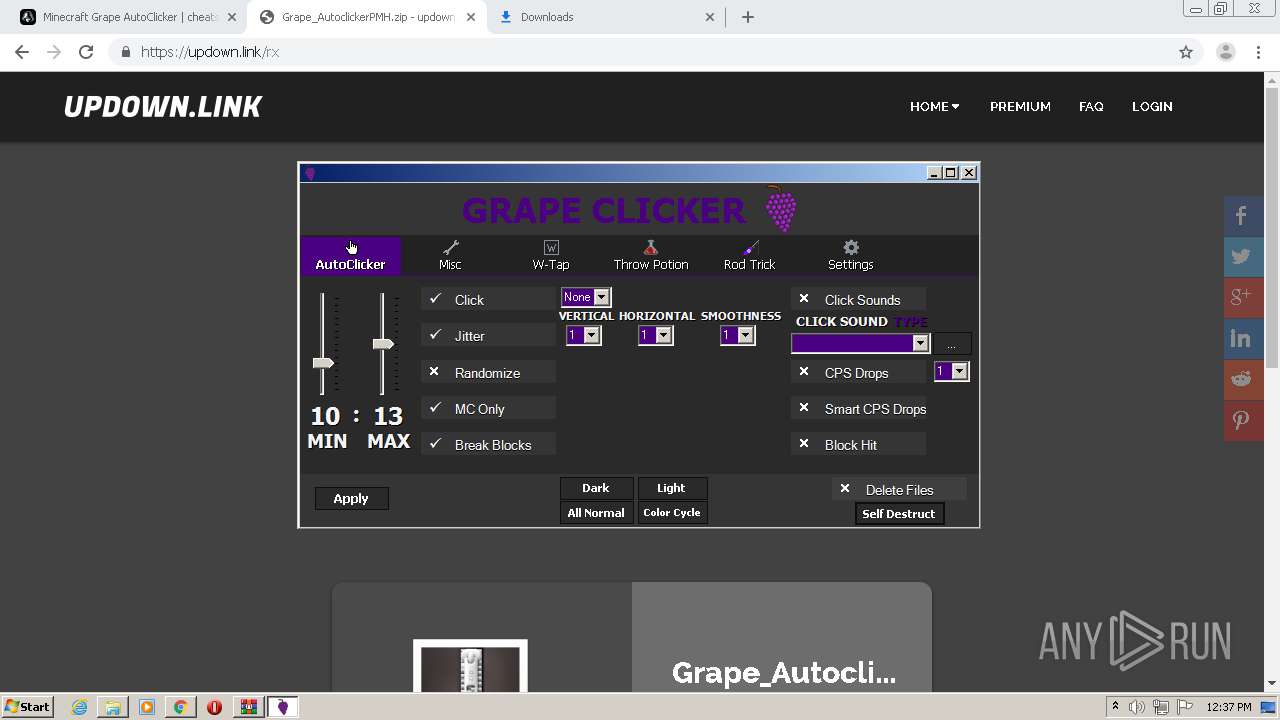
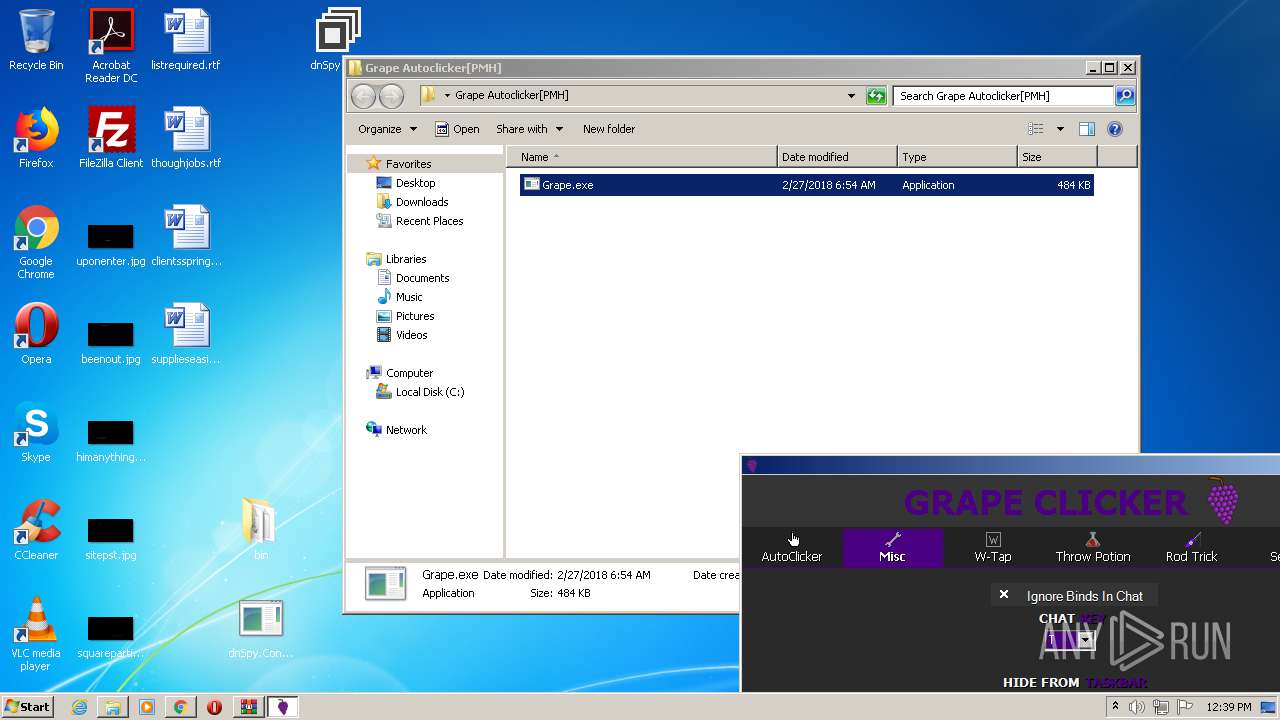
Manual execution by user
- Grape.exe (PID: 2444)
Creates files in the user directory
- chrome.exe (PID: 2484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
48
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7789704496287490232 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15913385972404394068 --mojo-platform-channel-handle=5012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6383867693801847206 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7780381539541944599 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11582705914278086008 --mojo-platform-channel-handle=3192 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Grape_AutoclickerPMH.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12716614895896718307 --mojo-platform-channel-handle=3652 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12792574130778846750 --mojo-platform-channel-handle=4968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8418949933932670709 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=563997983199146821 --mojo-platform-channel-handle=3764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 170
Read events
2 042
Write events
125
Delete events
3
Modification events
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2484-13260717283077750 |
Value: 259 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
139
Suspicious files
227
Text files
162
Unknown types
0
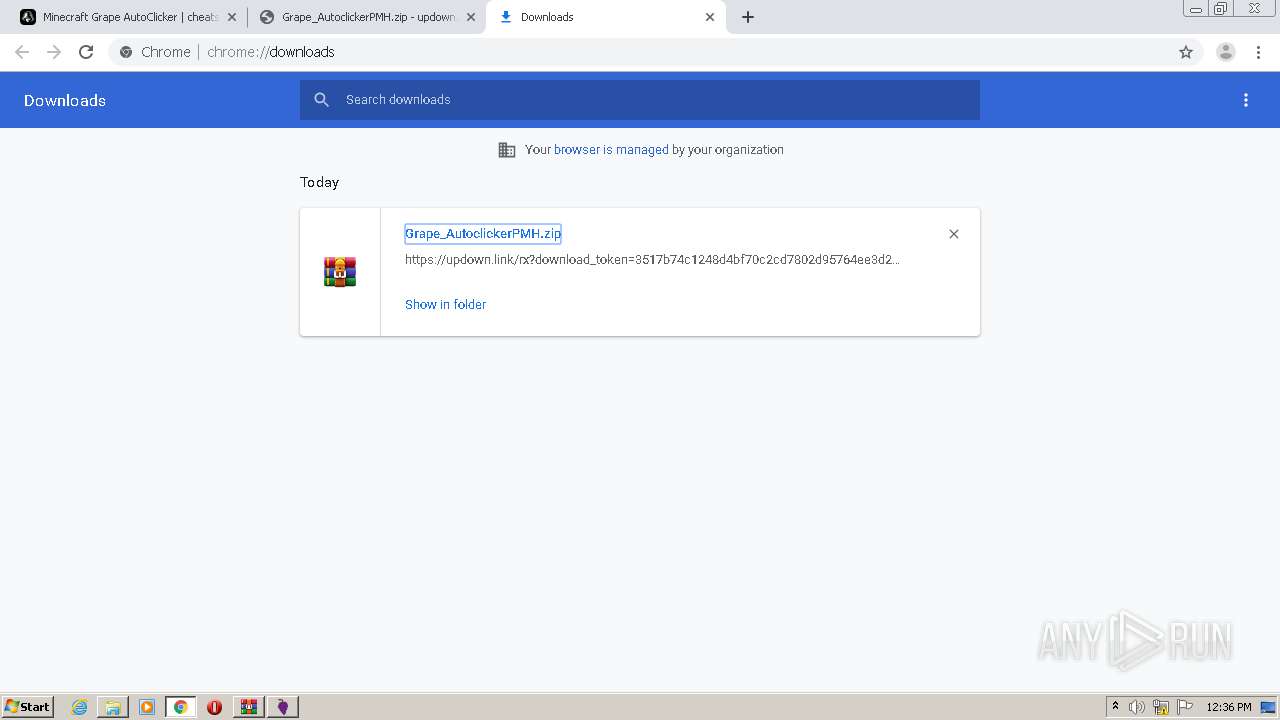
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6055EBE4-9B4.pma | — | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a4873784-427a-4fb3-9f46-85abb998c514.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF12c1a2.TMP | text | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2484 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12c481.TMP | — | |
MD5:— | SHA256:— | |||
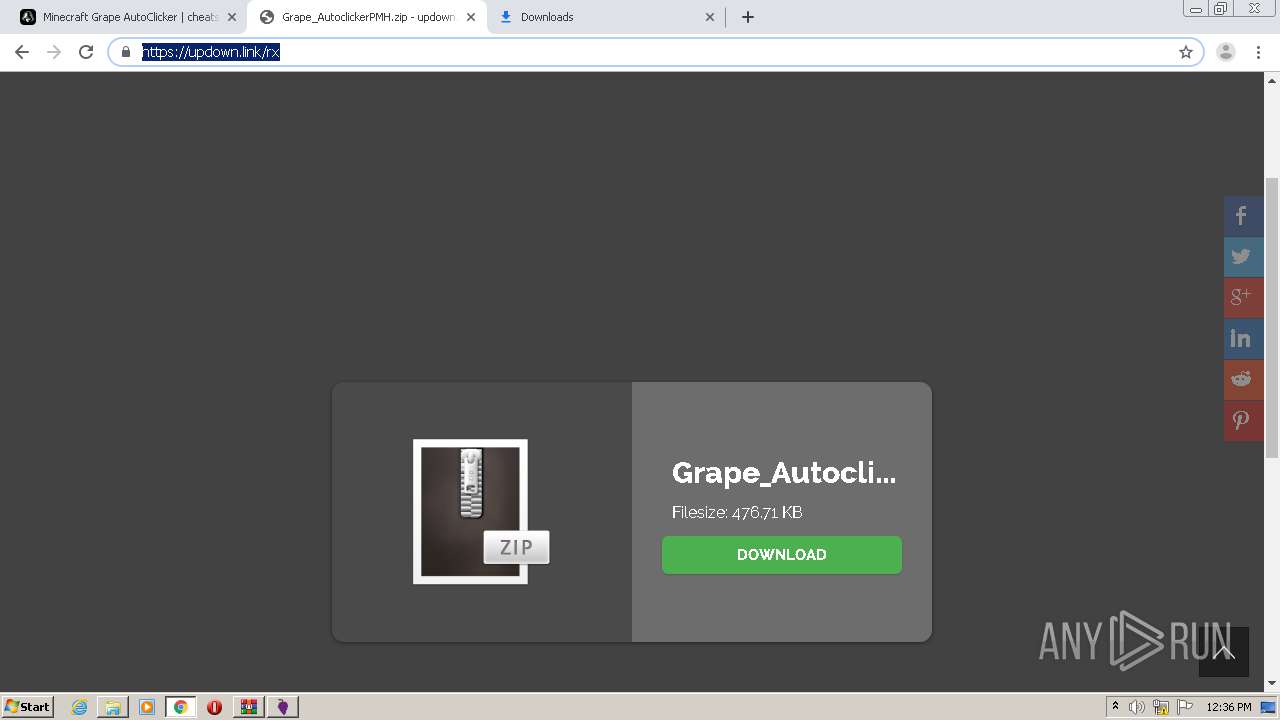
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
110
DNS requests
76
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
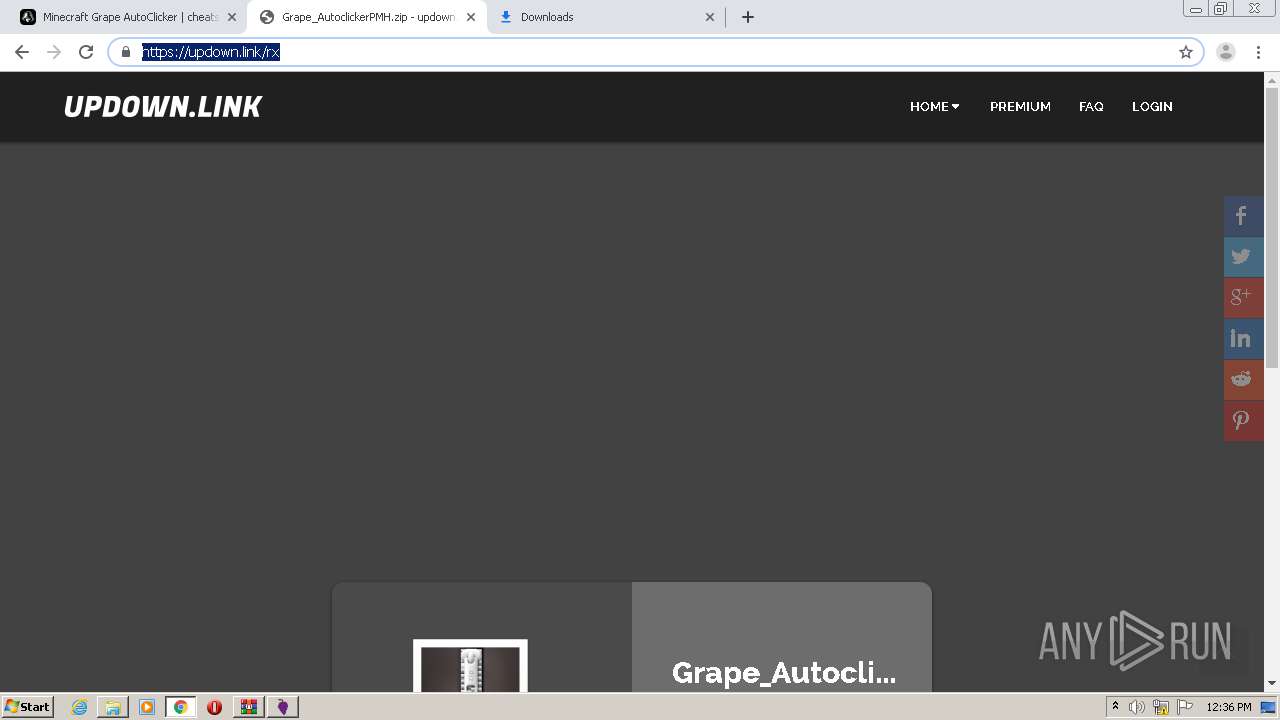
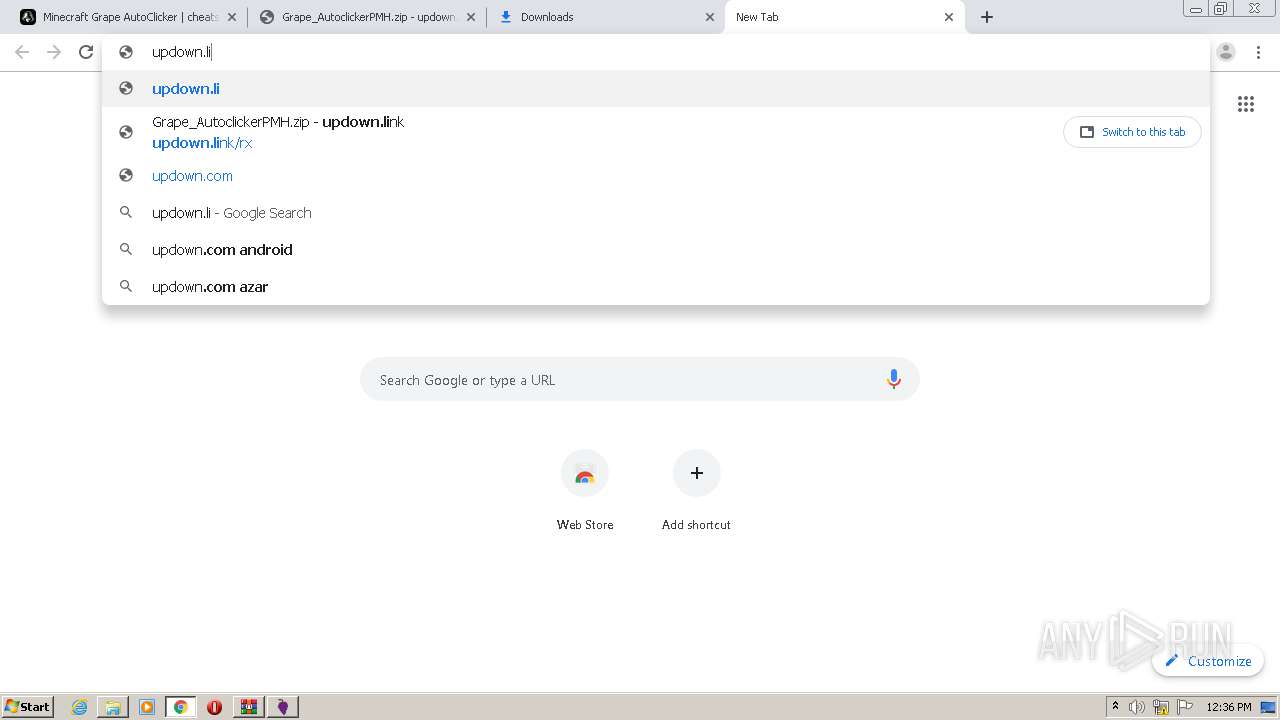
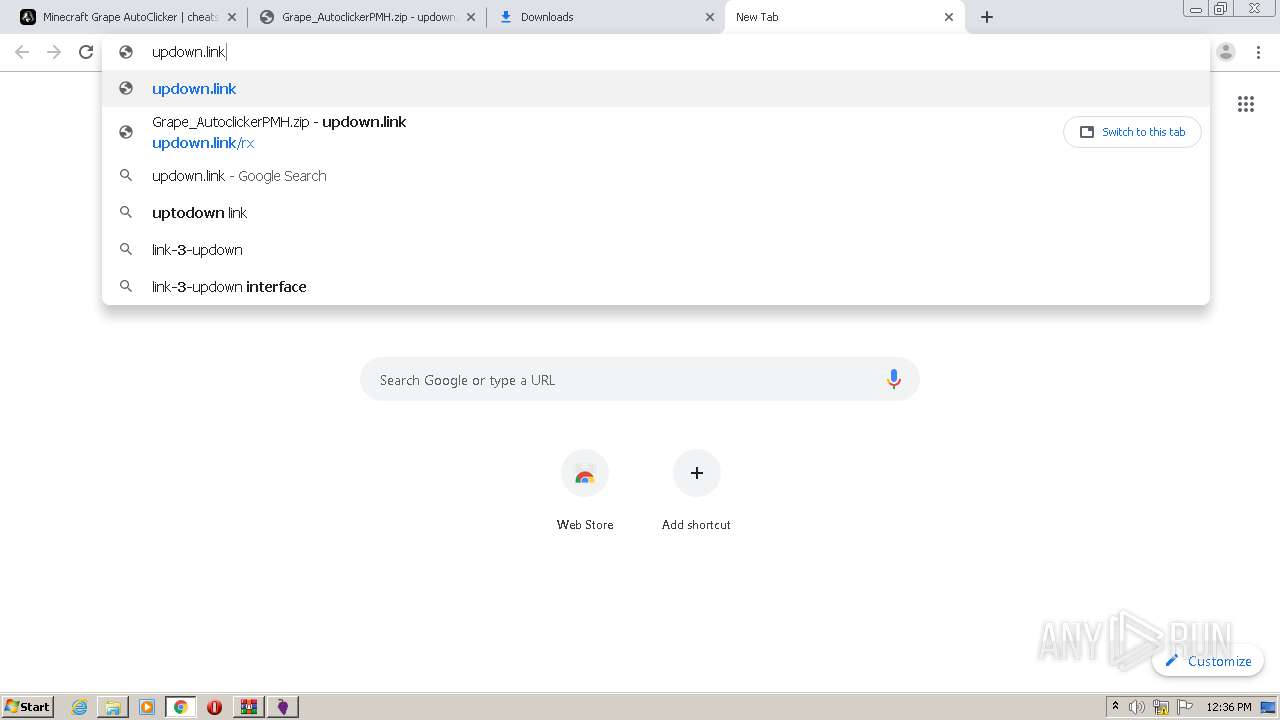
2124 | chrome.exe | GET | 301 | 104.21.63.42:80 | http://updown.link/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2124 | chrome.exe | 172.67.155.114:443 | cheatsquad.gg | — | US | unknown |
2124 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2124 | chrome.exe | 143.204.101.193:443 | dmmzkfd82wayn.cloudfront.net | — | US | malicious |
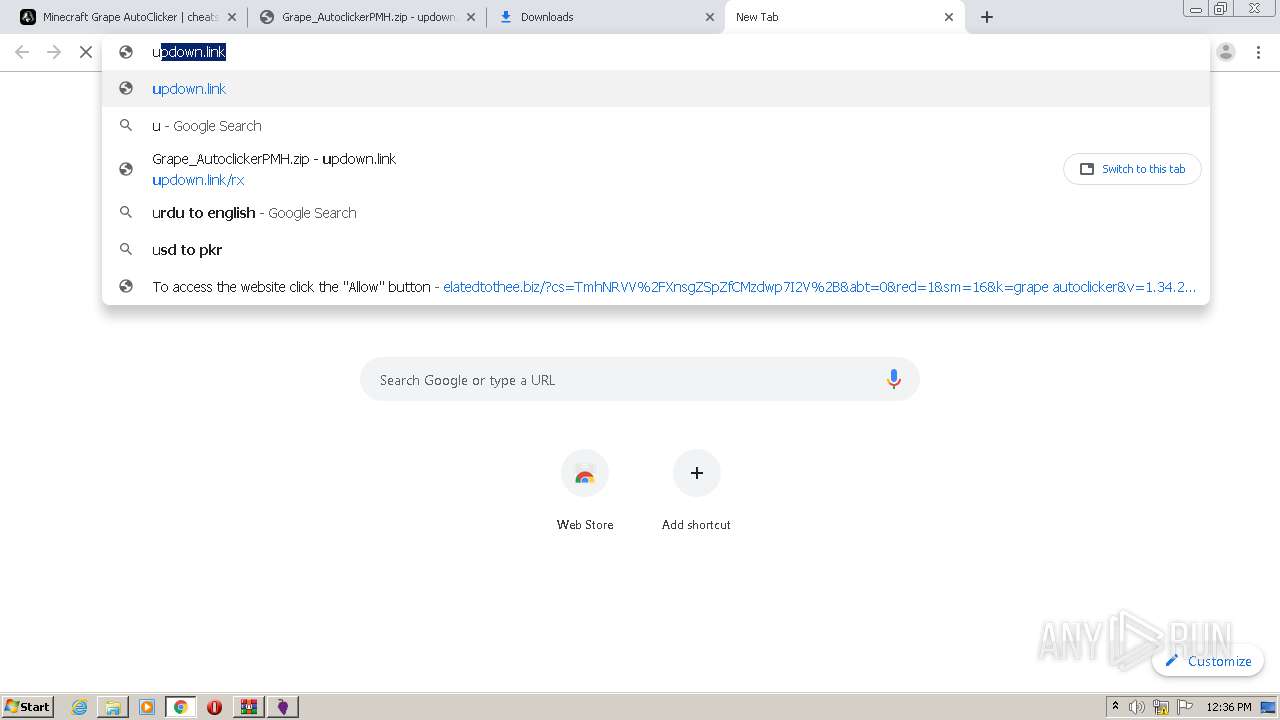
2124 | chrome.exe | 99.84.158.89:443 | elatedtothee.biz | AT&T Services, Inc. | US | suspicious |
2124 | chrome.exe | 142.250.185.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2124 | chrome.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2124 | chrome.exe | 13.32.21.112:443 | sioncenture.fun | Amazon.com, Inc. | US | suspicious |
2124 | chrome.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2124 | chrome.exe | 172.64.201.21:443 | freychang.fun | Cloudflare Inc | US | shared |
2124 | chrome.exe | 142.250.185.232:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cheatsquad.gg |
| malicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
dmmzkfd82wayn.cloudfront.net |
| whitelisted |
ajax.cloudflare.com |
| whitelisted |
i.imgur.com |
| malicious |
images.dmca.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
elatedtothee.biz |
| suspicious |
www.facebook.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |