| File name: | Xenos.exe |
| Full analysis: | https://app.any.run/tasks/fbbe58d7-8fd7-4dd3-9b57-e894ce418cf9 |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2024, 15:43:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4731B90DB56FC5DD654D59DECA1009E6 |
| SHA1: | 7C486D696813B1E0102F2FEB300E6C6A7610287C |
| SHA256: | DEF1C2F12307D598E42506A55F1A06ED5E652AF0D260AAC9572469429F10D04D |
| SSDEEP: | 24576:F6vLpf9LJiOm0xg2VkVtw099I98mzGokH/Ngwpsu+VfSVgPCS3tMrMyj3F9hIF1j:afJWVD99U8okH/NSVRSVE3tMx3FE1S0T |
MALICIOUS
Drops the executable file immediately after the start
- Xenos.exe (PID: 3660)
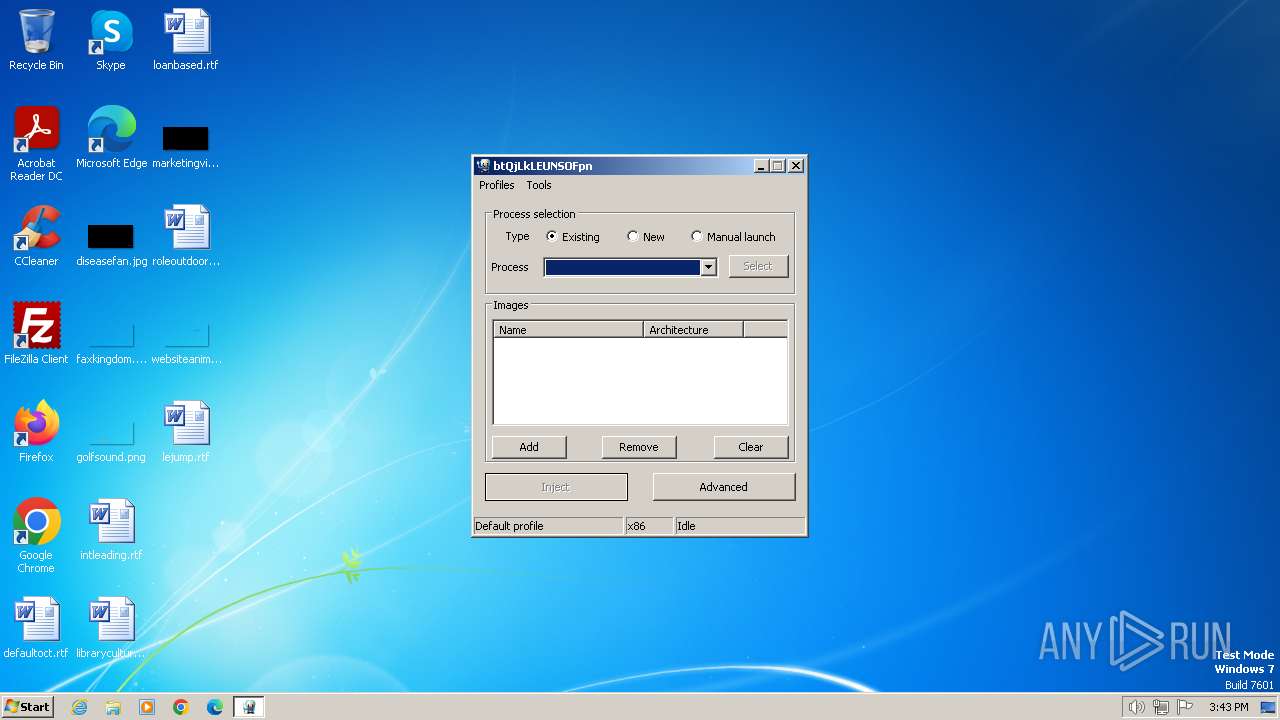
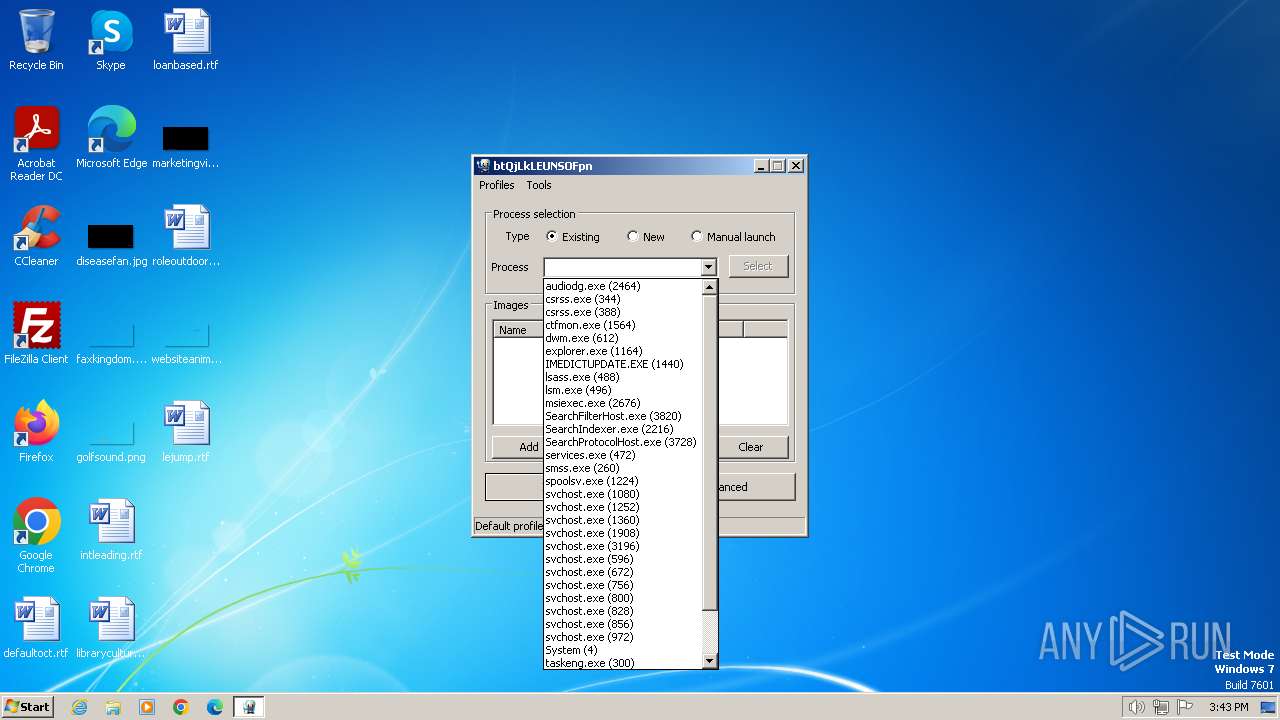
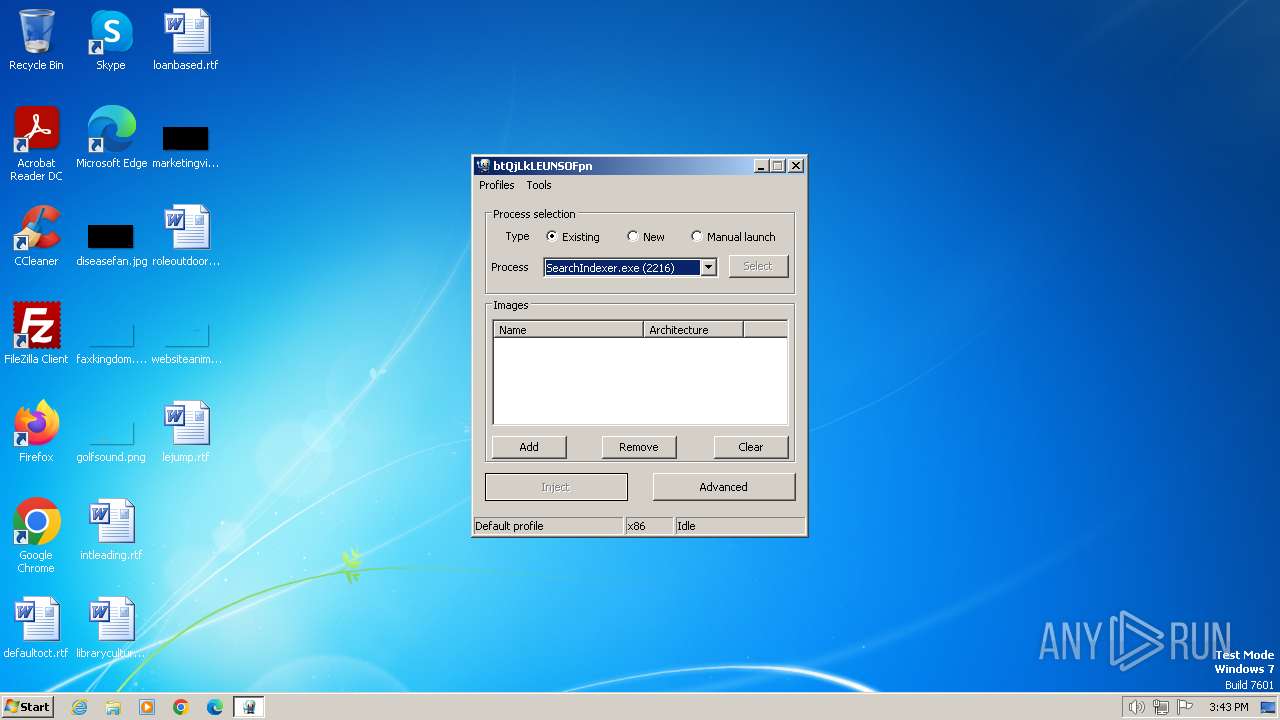
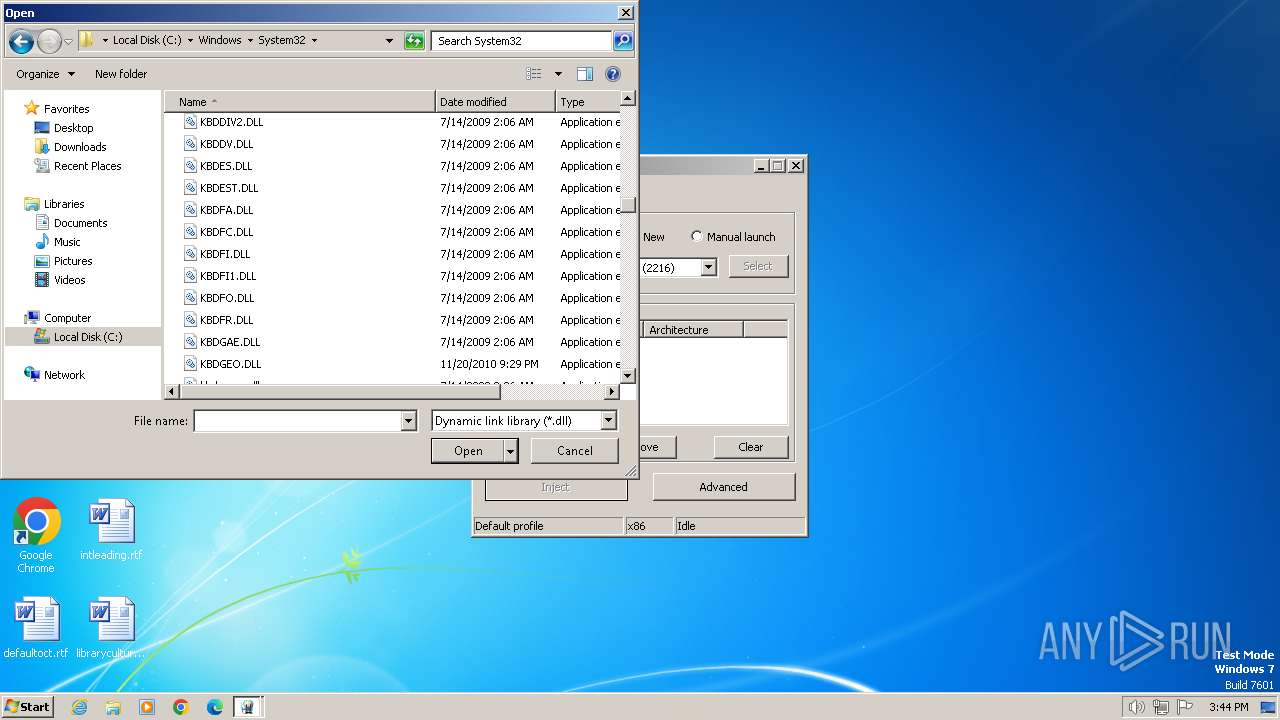
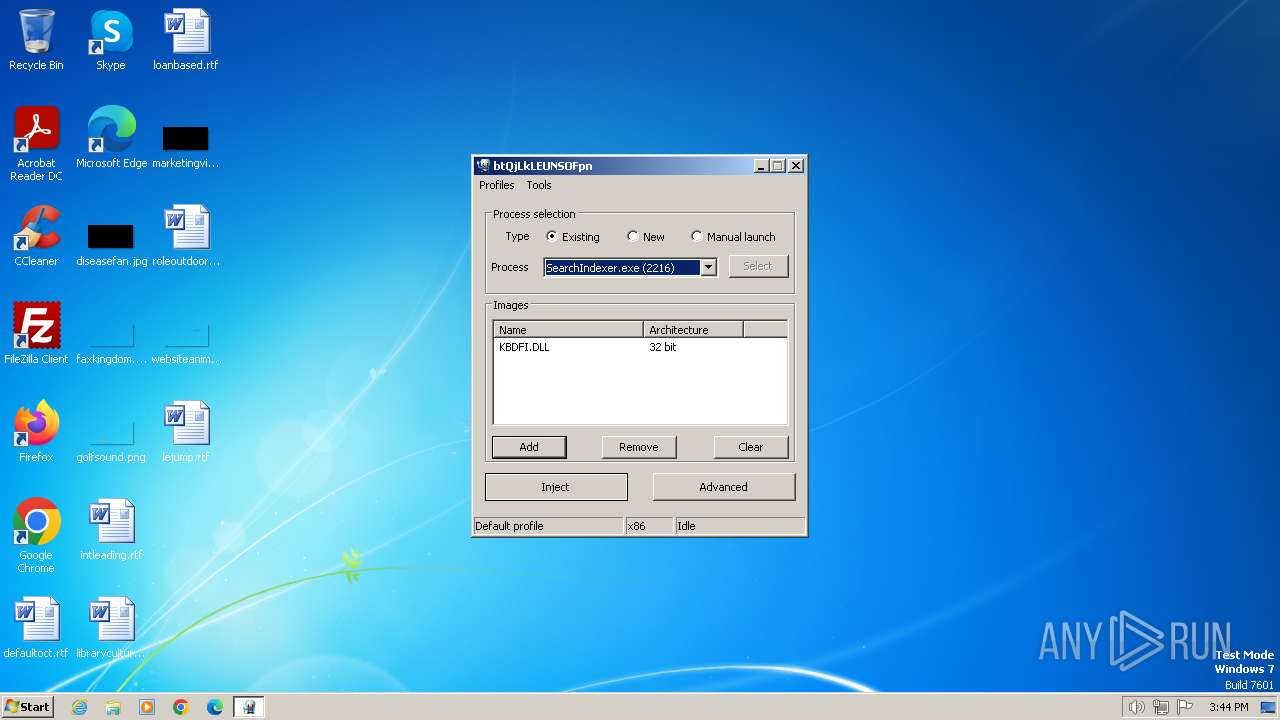
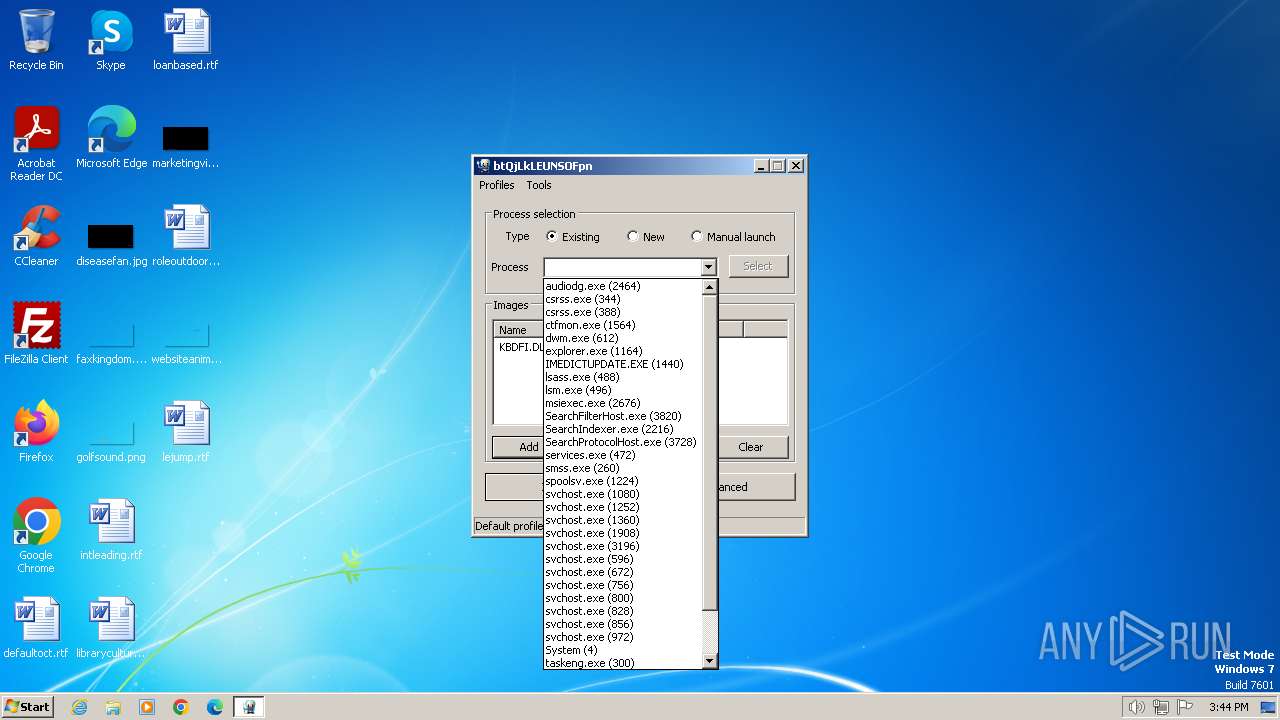
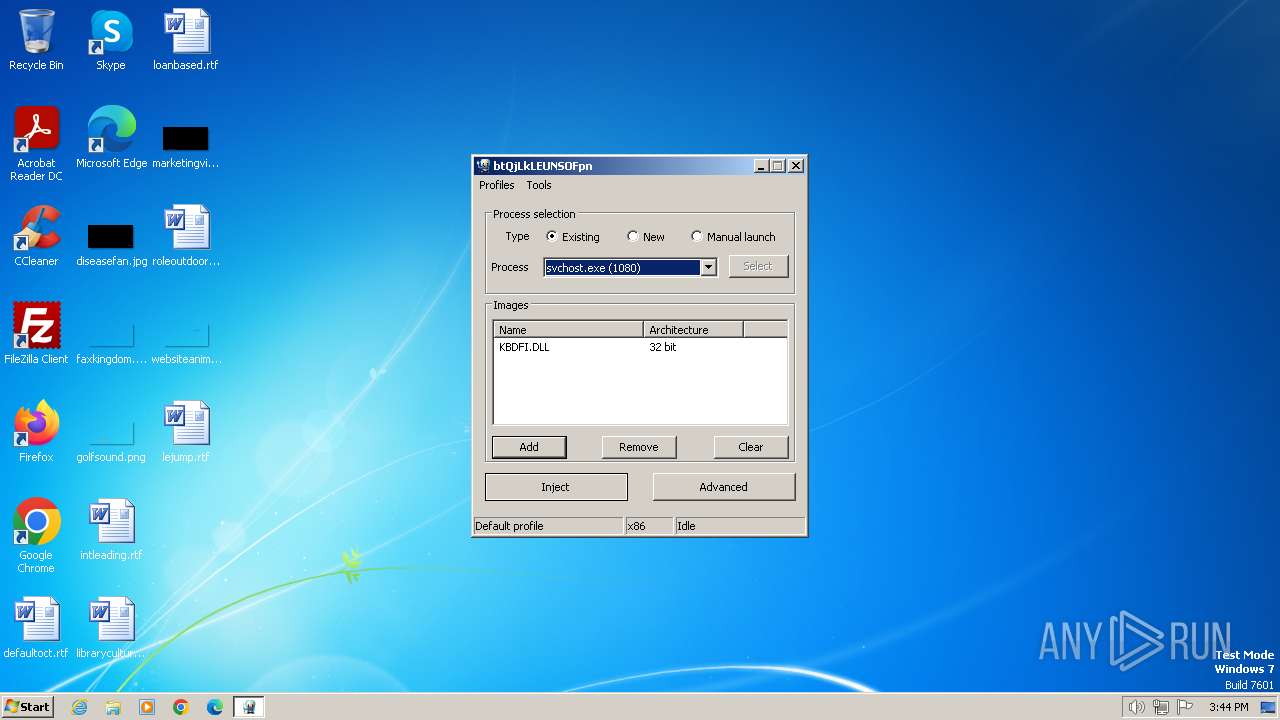
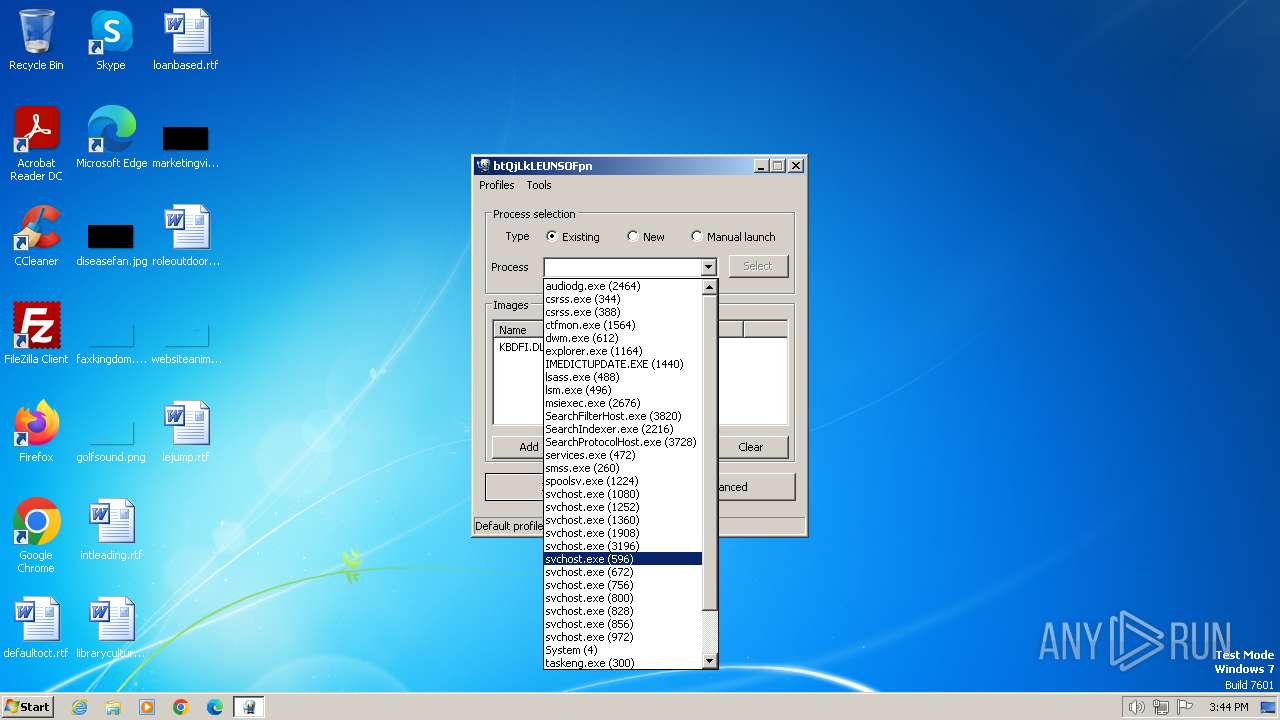
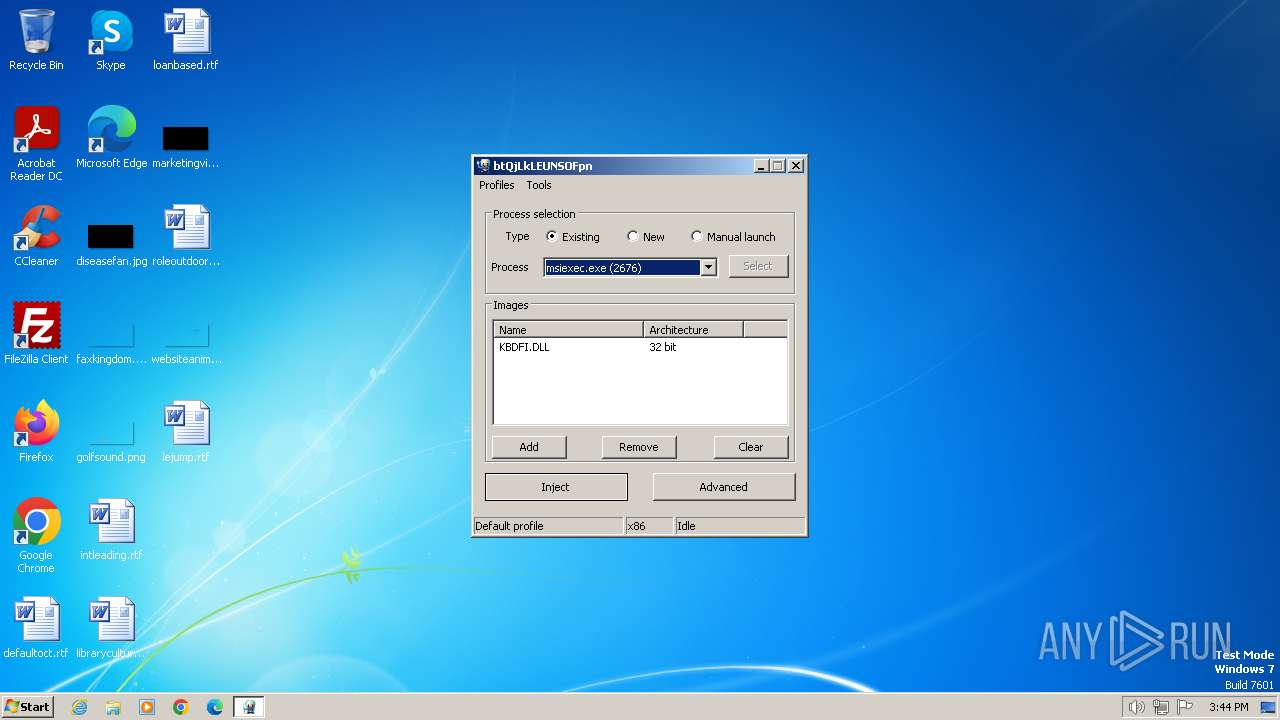
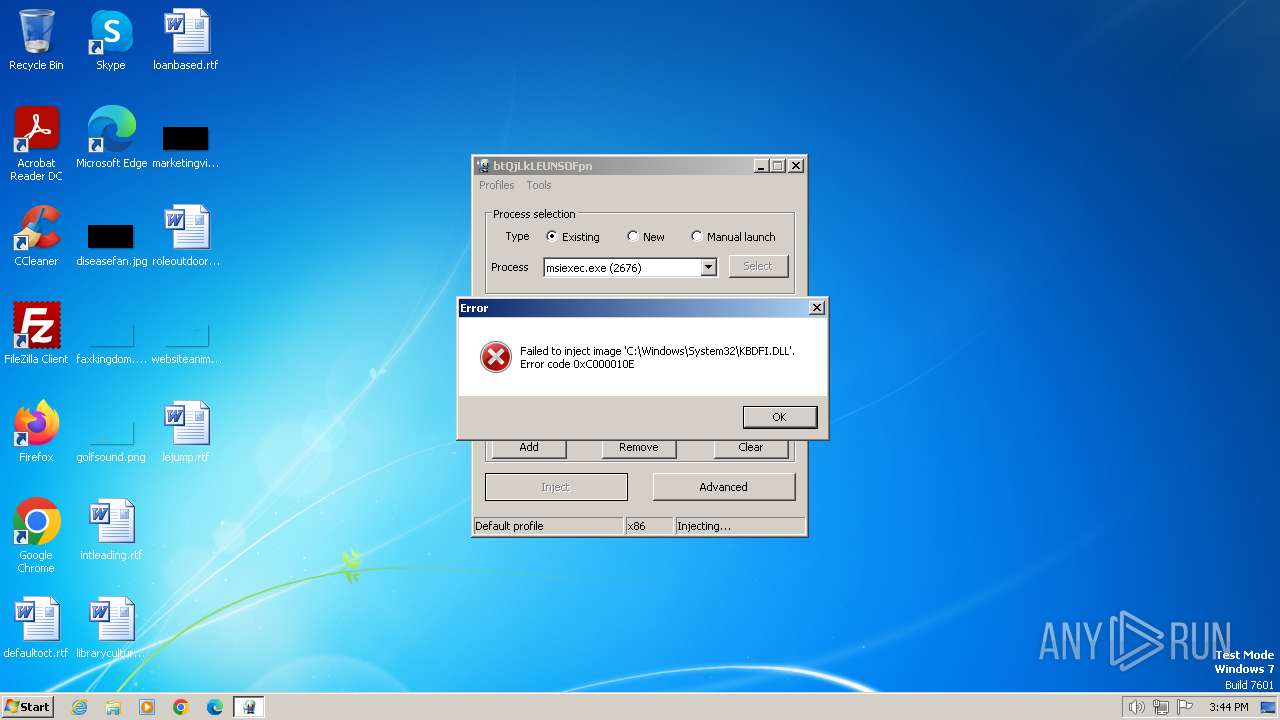
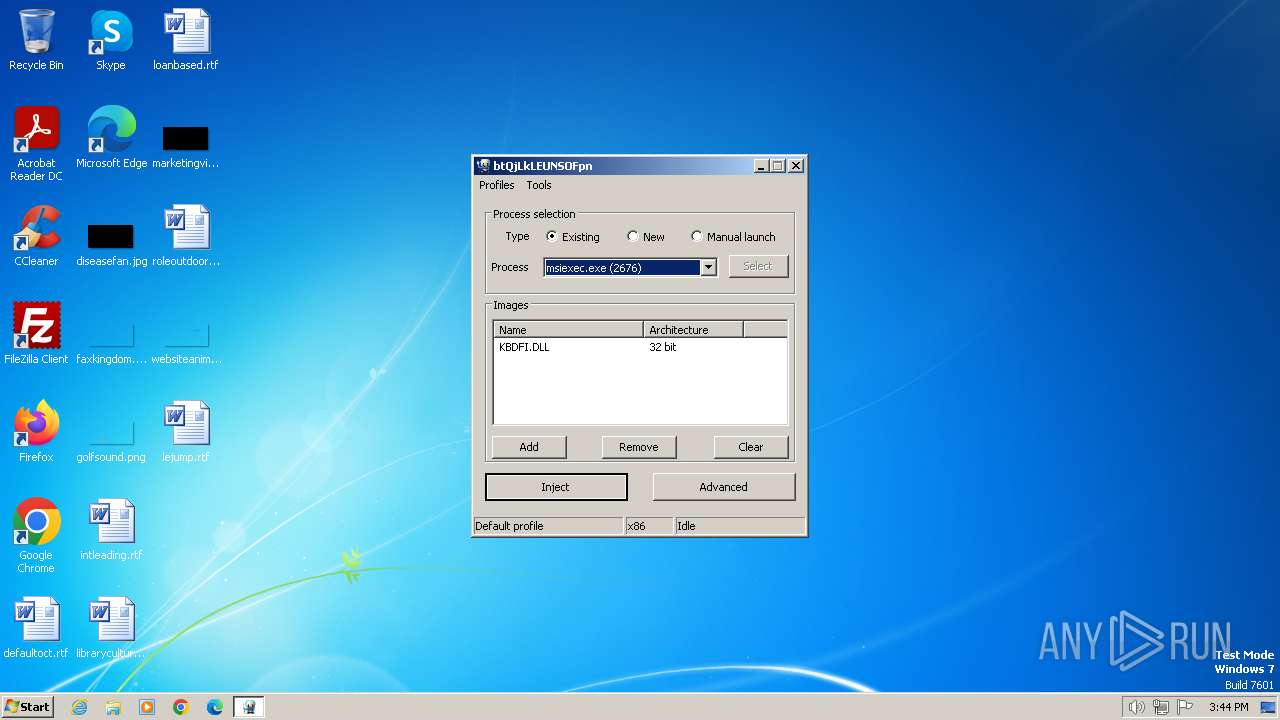
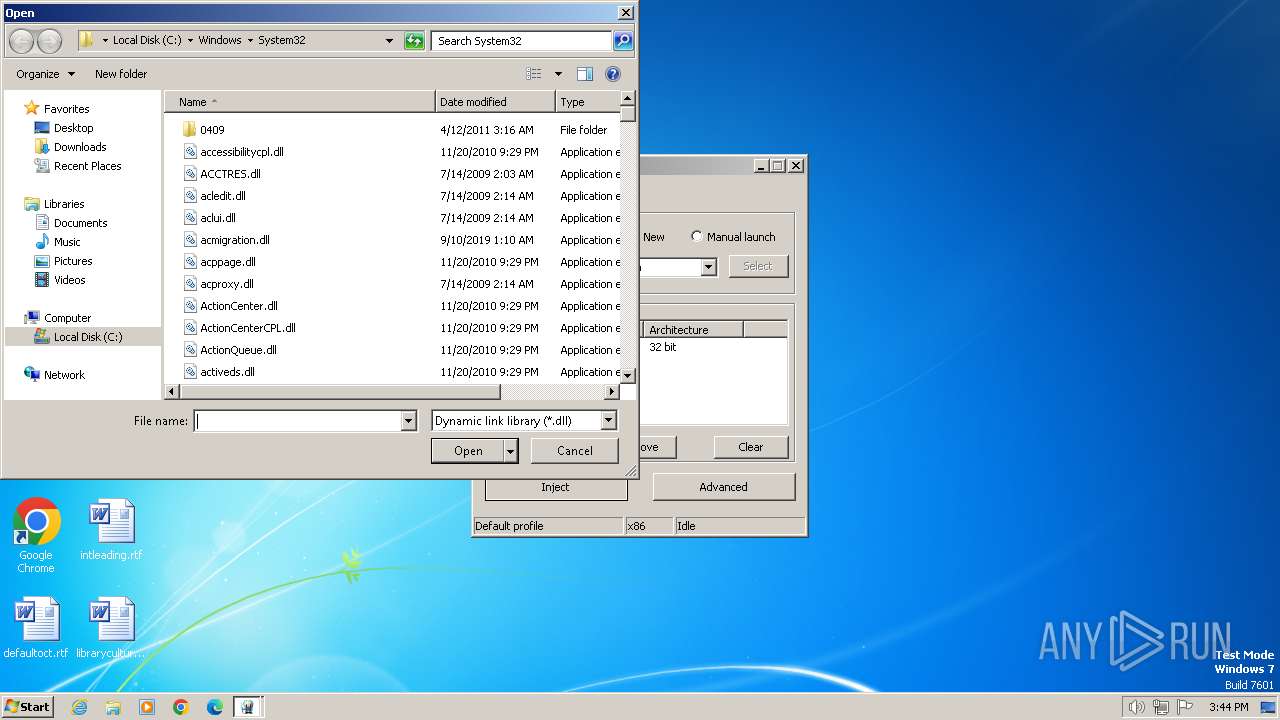
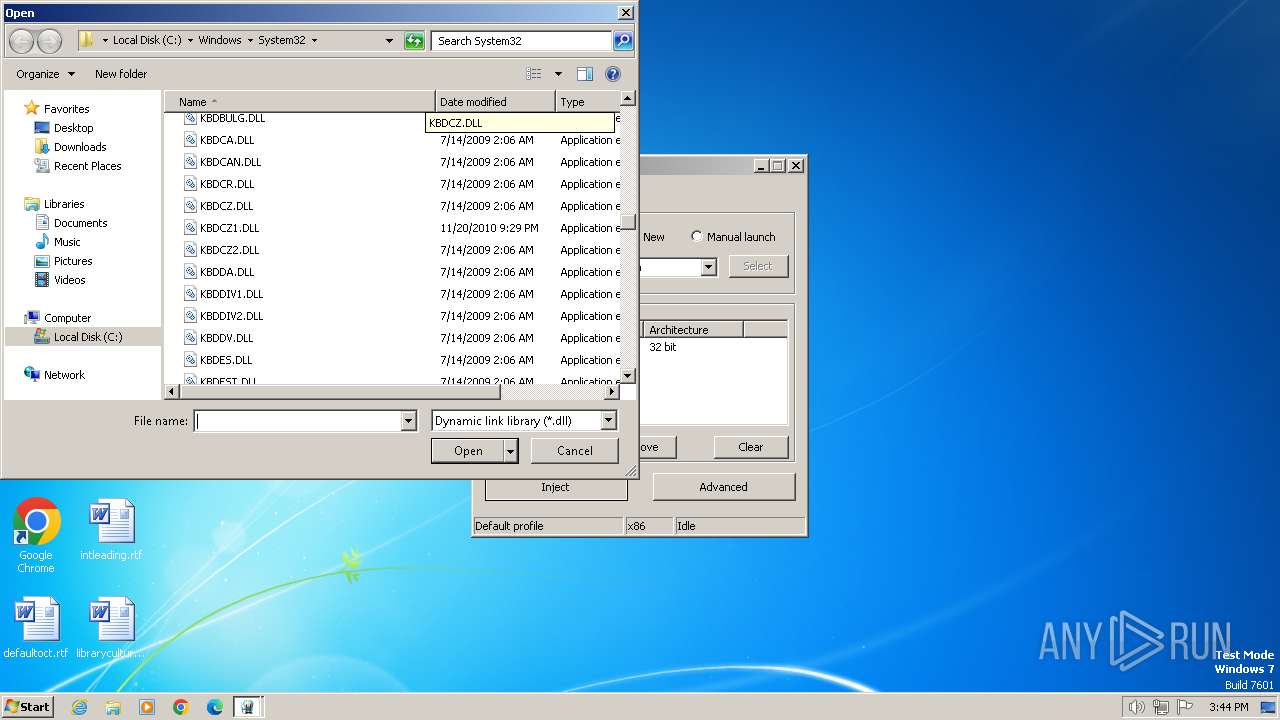
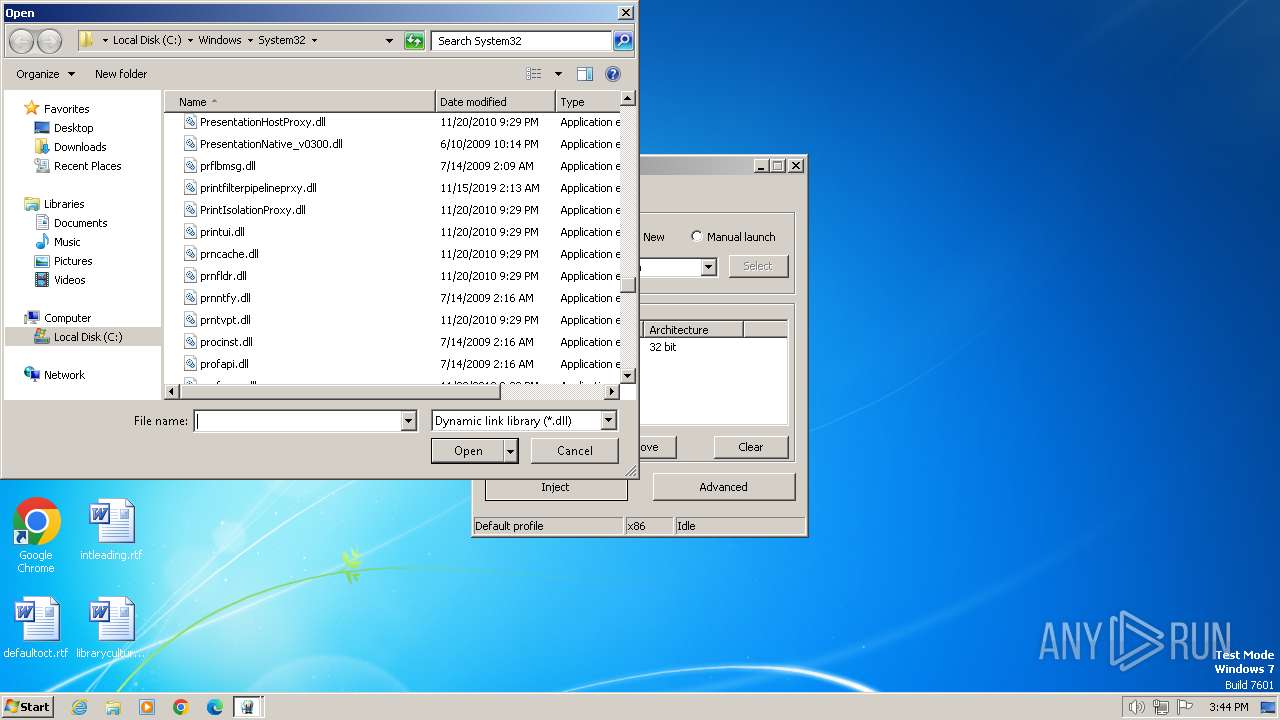
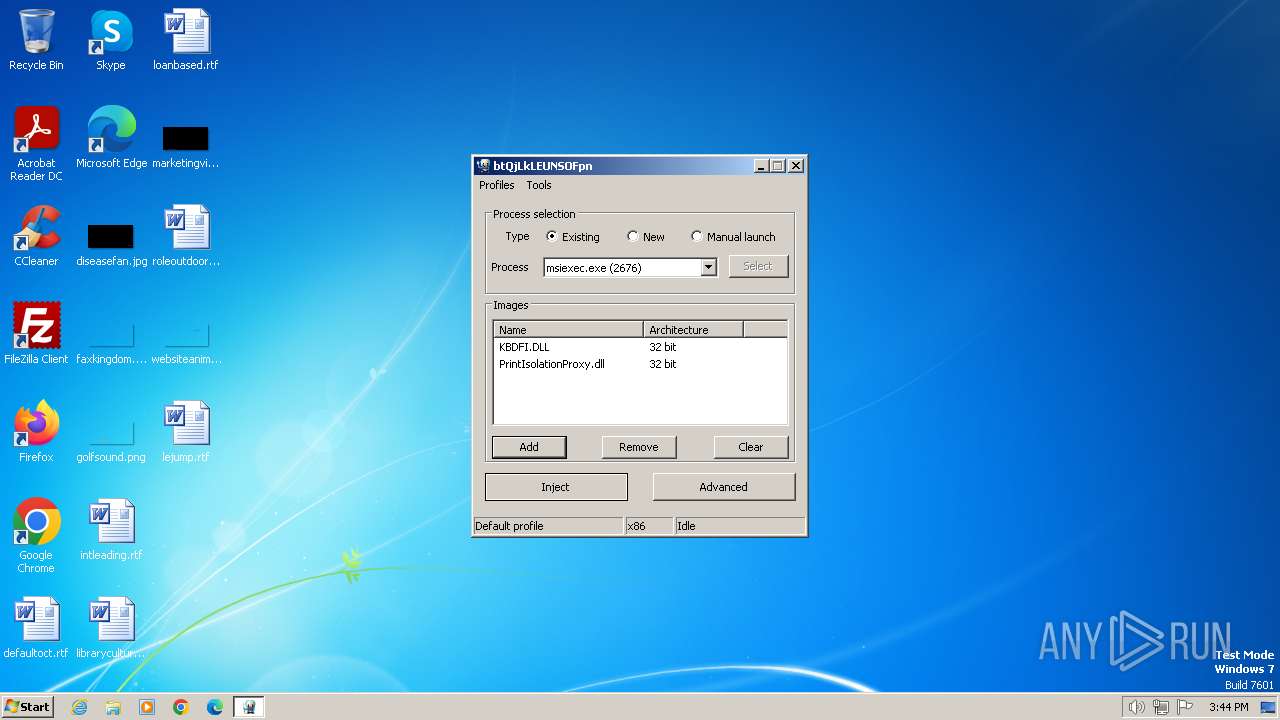
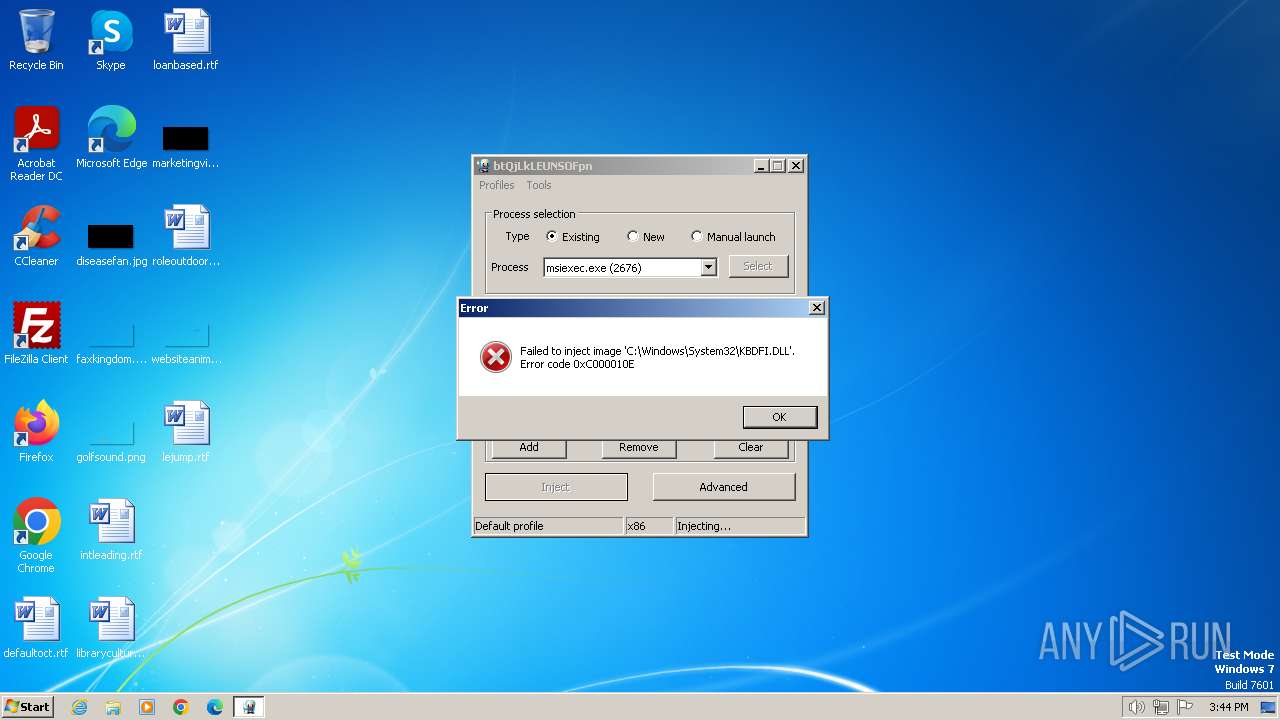
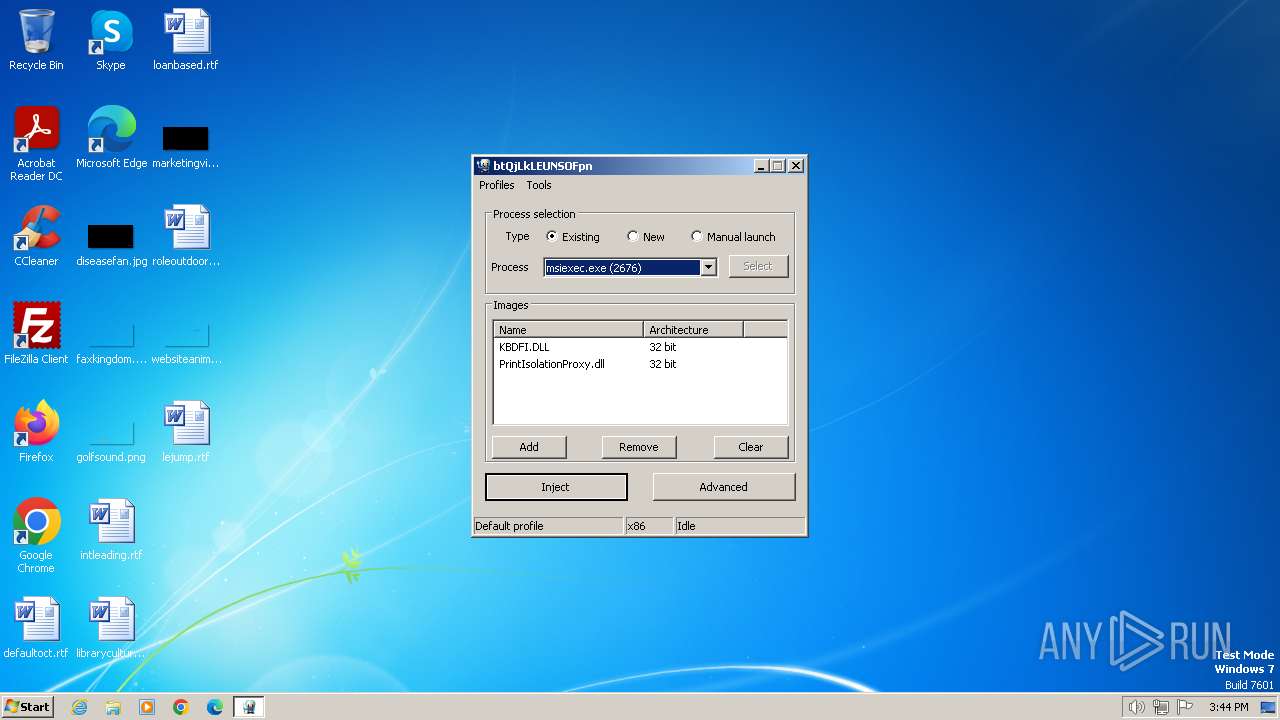
Runs injected code in another process
- Xenos.exe (PID: 3660)
Application was injected by another process
- svchost.exe (PID: 1080)
- msiexec.exe (PID: 2676)
SUSPICIOUS
Creates file in the systems drive root
- Xenos.exe (PID: 3660)
INFO
Checks supported languages
- Xenos.exe (PID: 3660)
- wmpnscfg.exe (PID: 1876)
Reads the computer name
- Xenos.exe (PID: 3660)
- wmpnscfg.exe (PID: 1876)
Reads the machine GUID from the registry
- Xenos.exe (PID: 3660)
Manual execution by a user
- wmpnscfg.exe (PID: 1876)
Create files in a temporary directory
- Xenos.exe (PID: 3660)
Reads Environment values
- Xenos.exe (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:21 11:01:11+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 652800 |
| InitializedDataSize: | 529408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5f40d |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.2.0 |
| ProductVersionNumber: | 2.3.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Process default |
| CharacterSet: | Unicode |
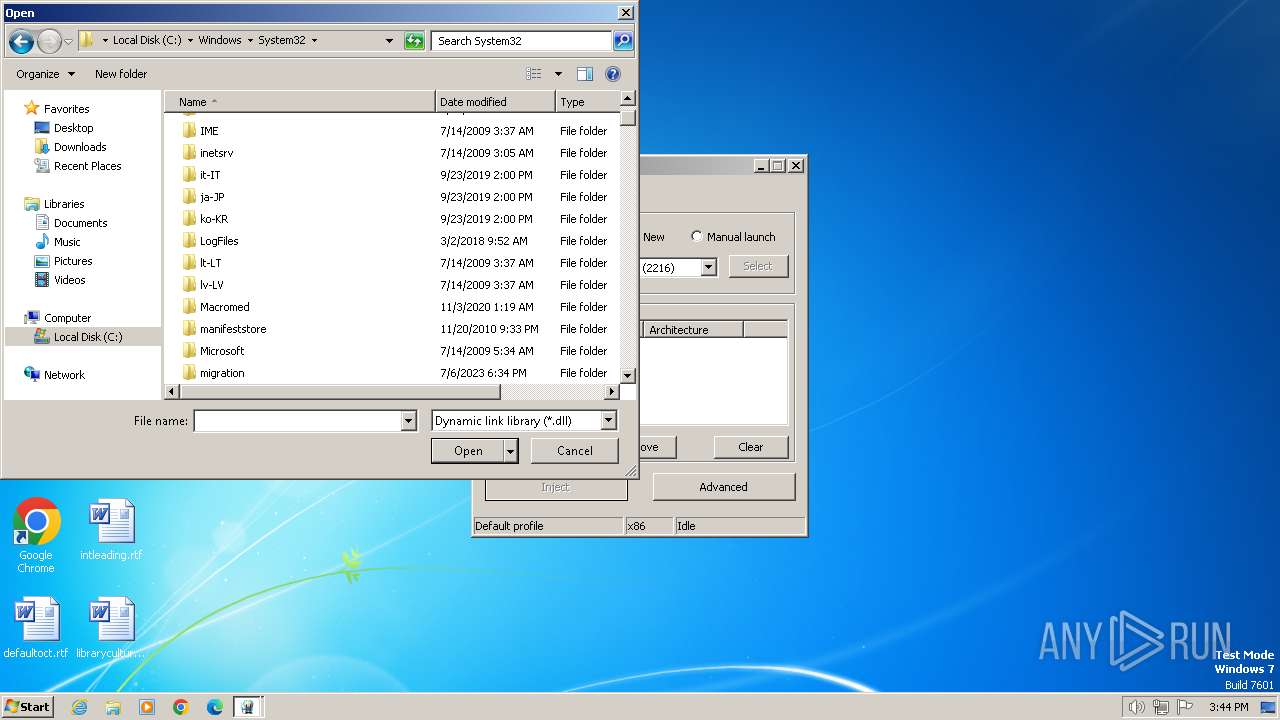
| FileDescription: | PE injector |
| FileVersion: | 2.3.2.0 |
| InternalName: | Xenos.exe |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFileName: | Xenos.exe |
| ProductName: | Xenos |
| ProductVersion: | 2.3.2.0 |
Total processes
40
Monitored processes
5
Malicious processes
3
Suspicious processes
0
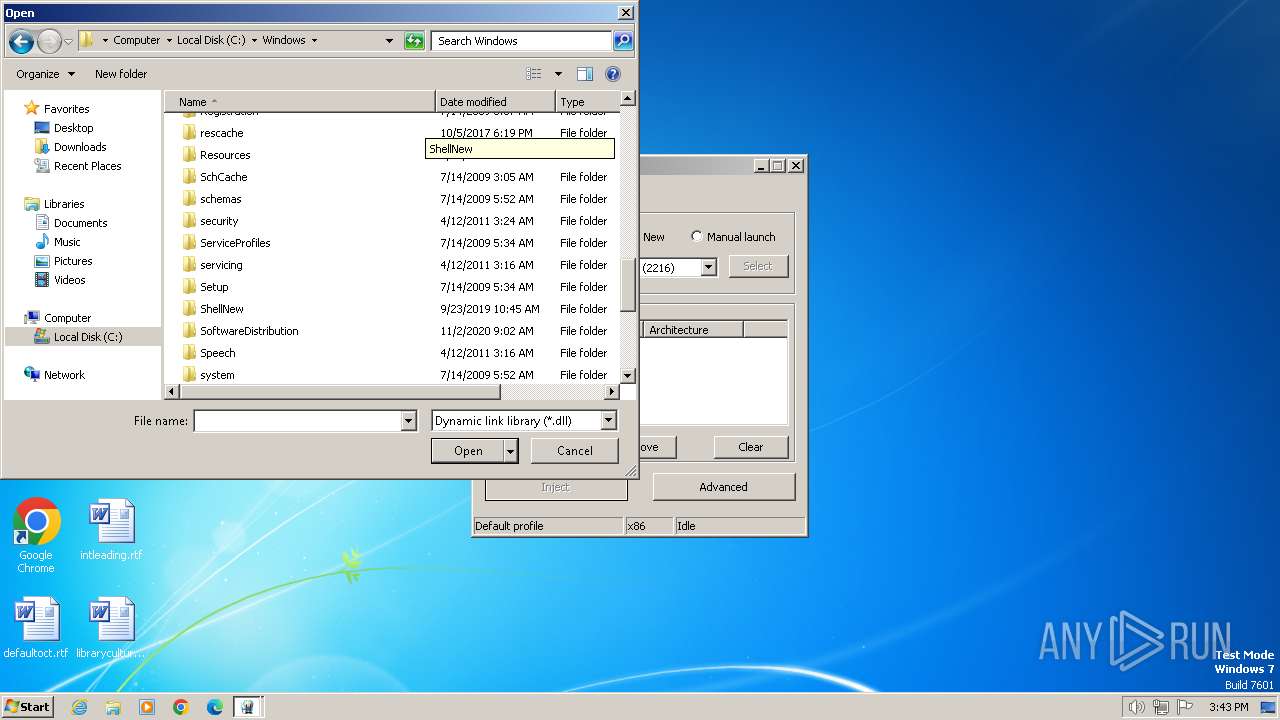
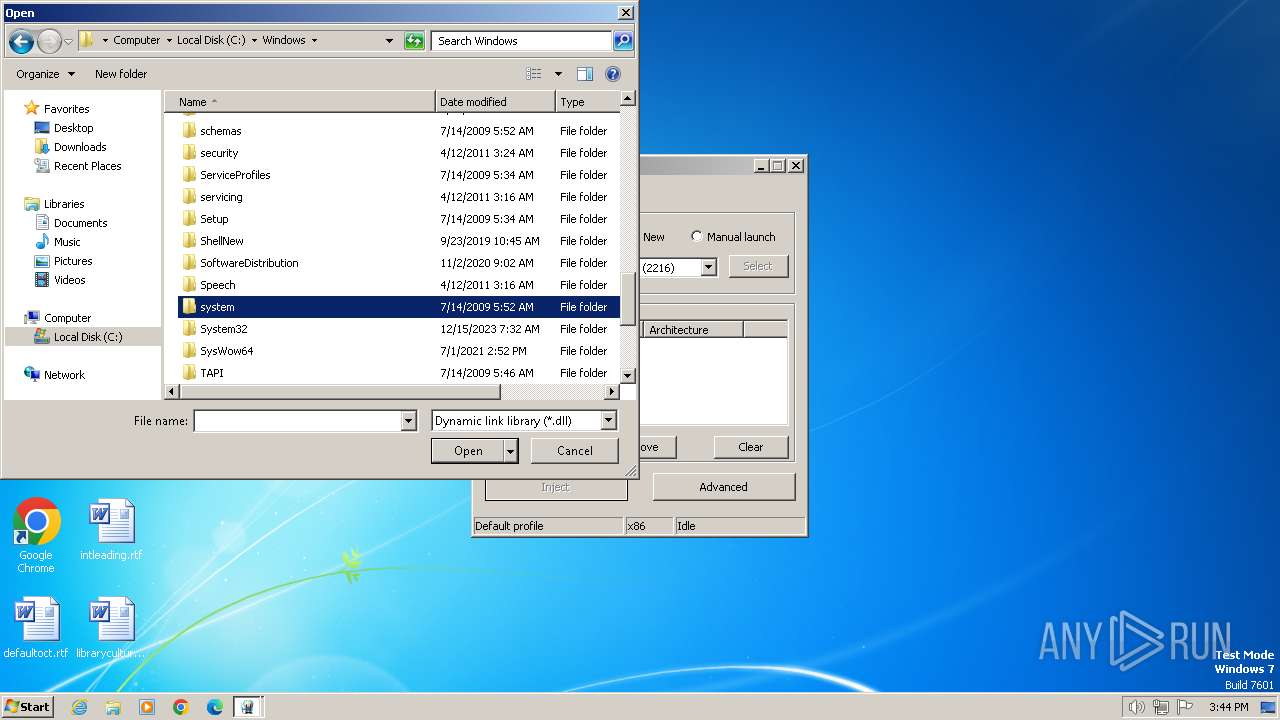
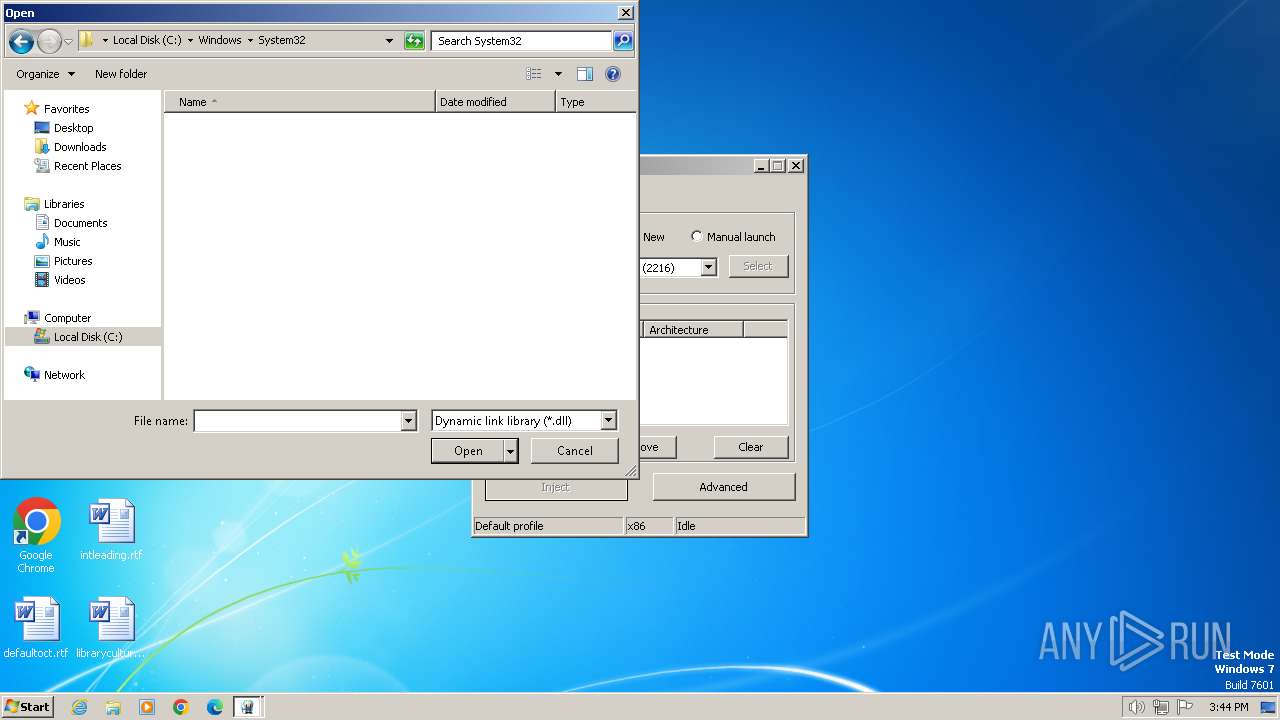
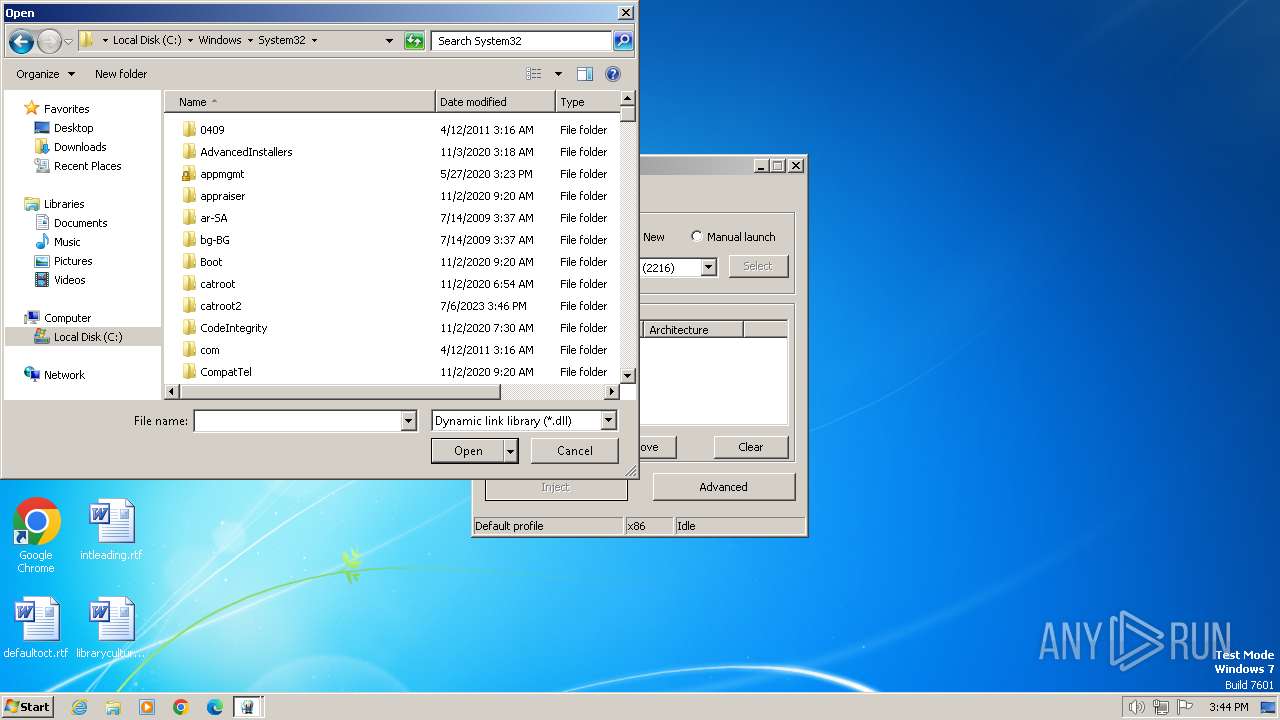
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2676 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | "C:\Users\admin\AppData\Local\Temp\Xenos.exe" | C:\Users\admin\AppData\Local\Temp\Xenos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PE injector Exit code: 0 Version: 2.3.2.0 Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\Xenos.exe" | C:\Users\admin\AppData\Local\Temp\Xenos.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PE injector Exit code: 3221226540 Version: 2.3.2.0 Modules
| |||||||||||||||
Total events
11 431
Read events
11 278
Write events
144
Delete events
9
Modification events
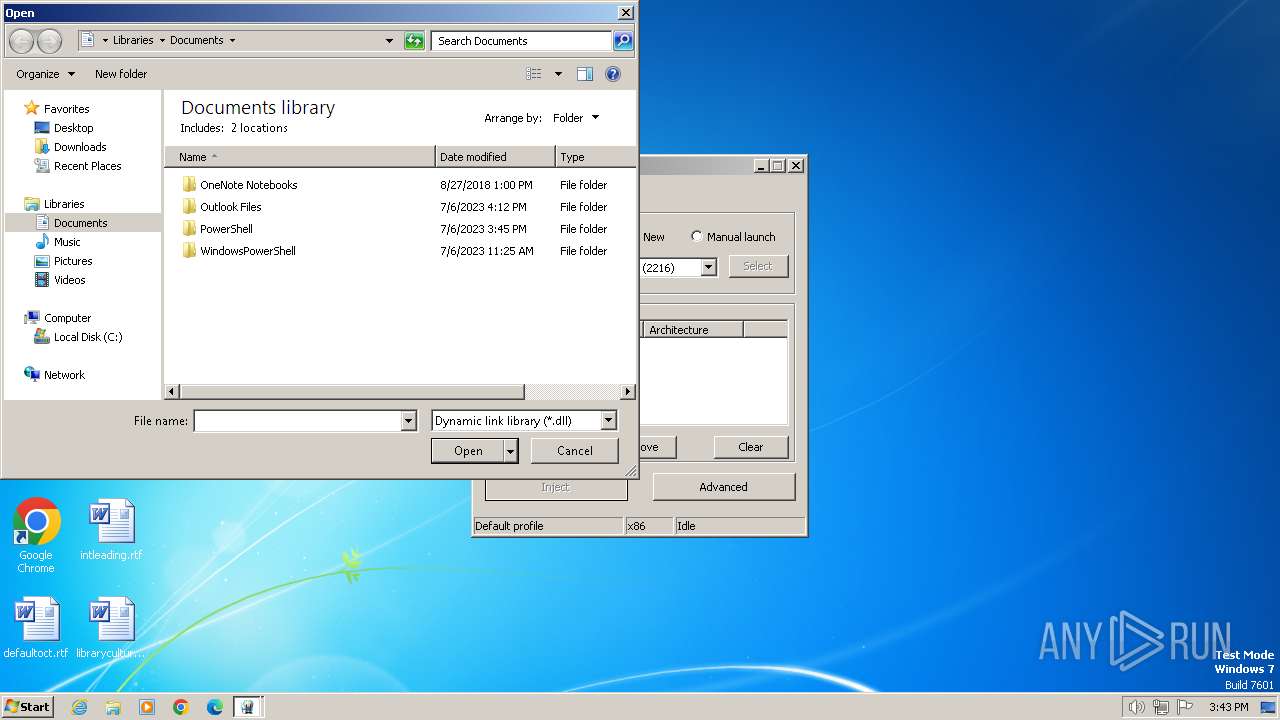
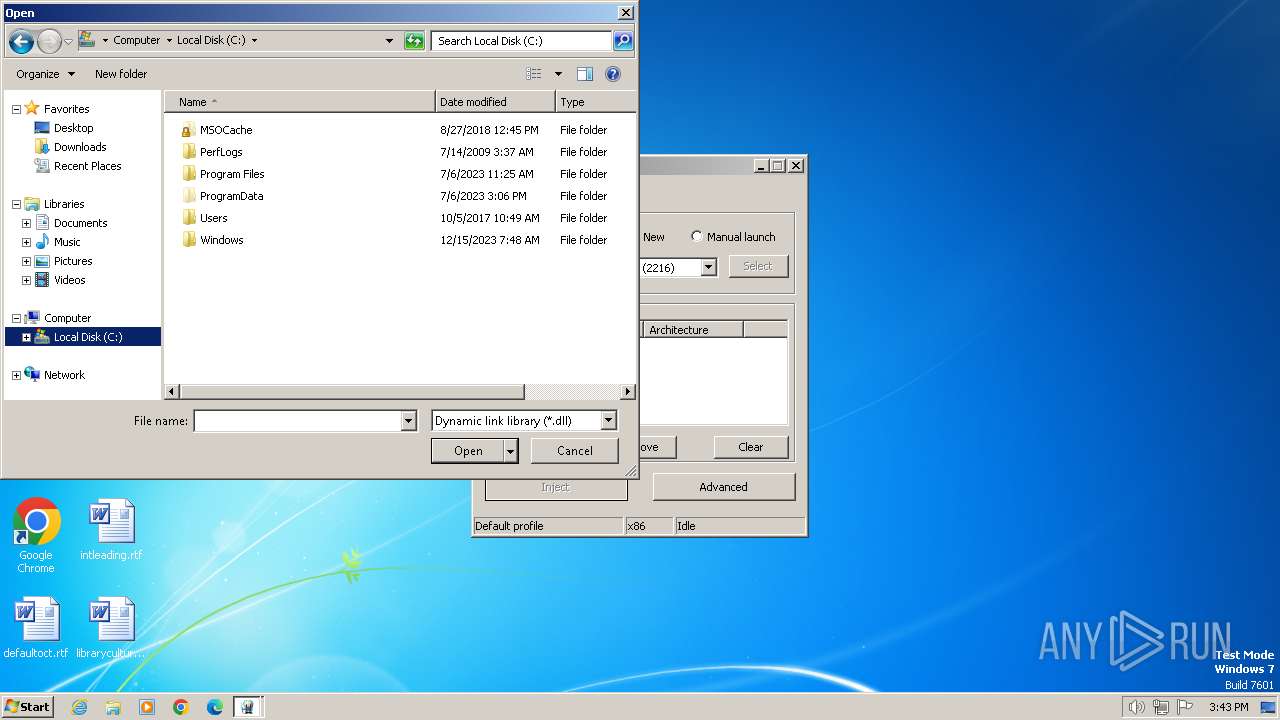
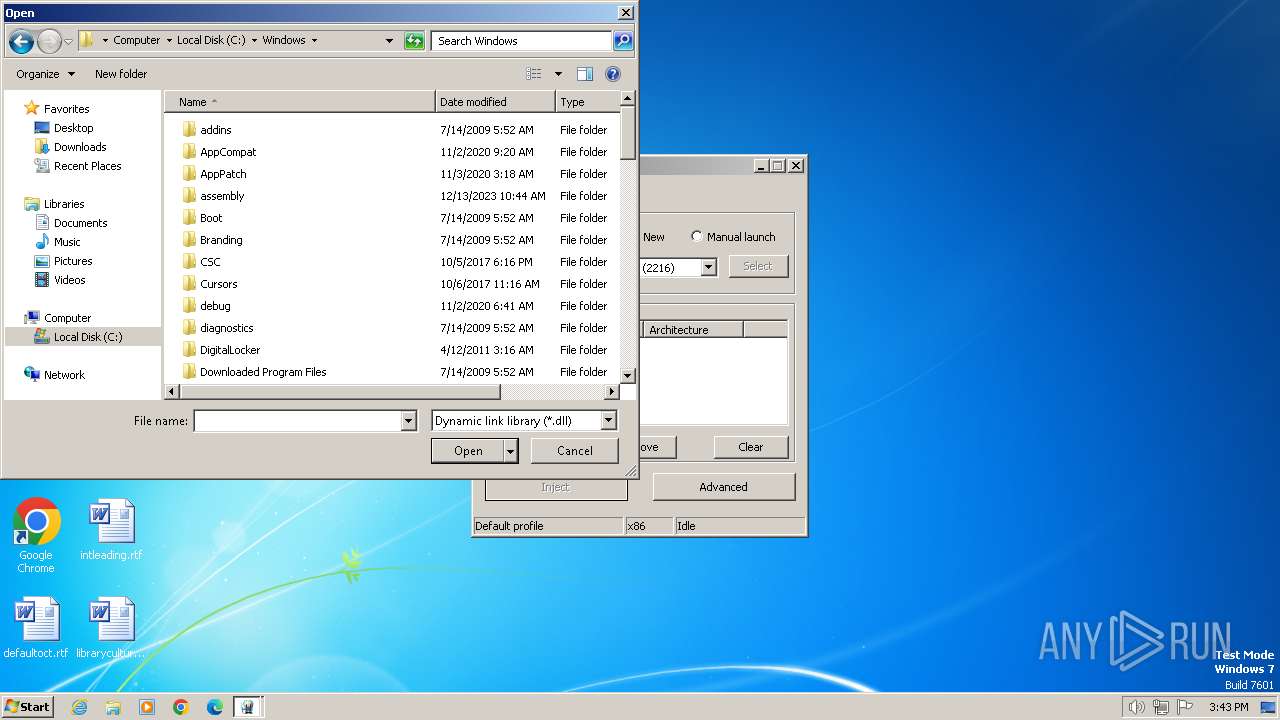
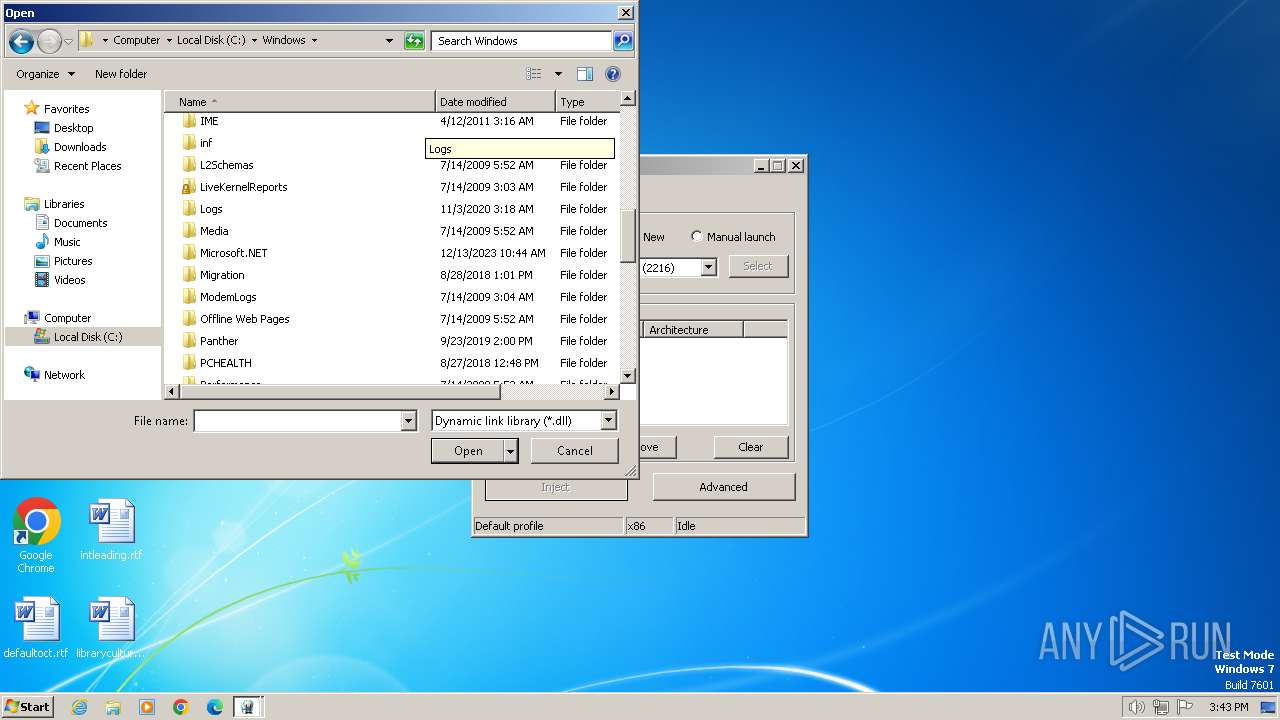
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.xpr |
| Operation: | write | Name: | Content Type |
Value: Application/xml | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000100000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000700000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3660) Xenos.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | unknown |