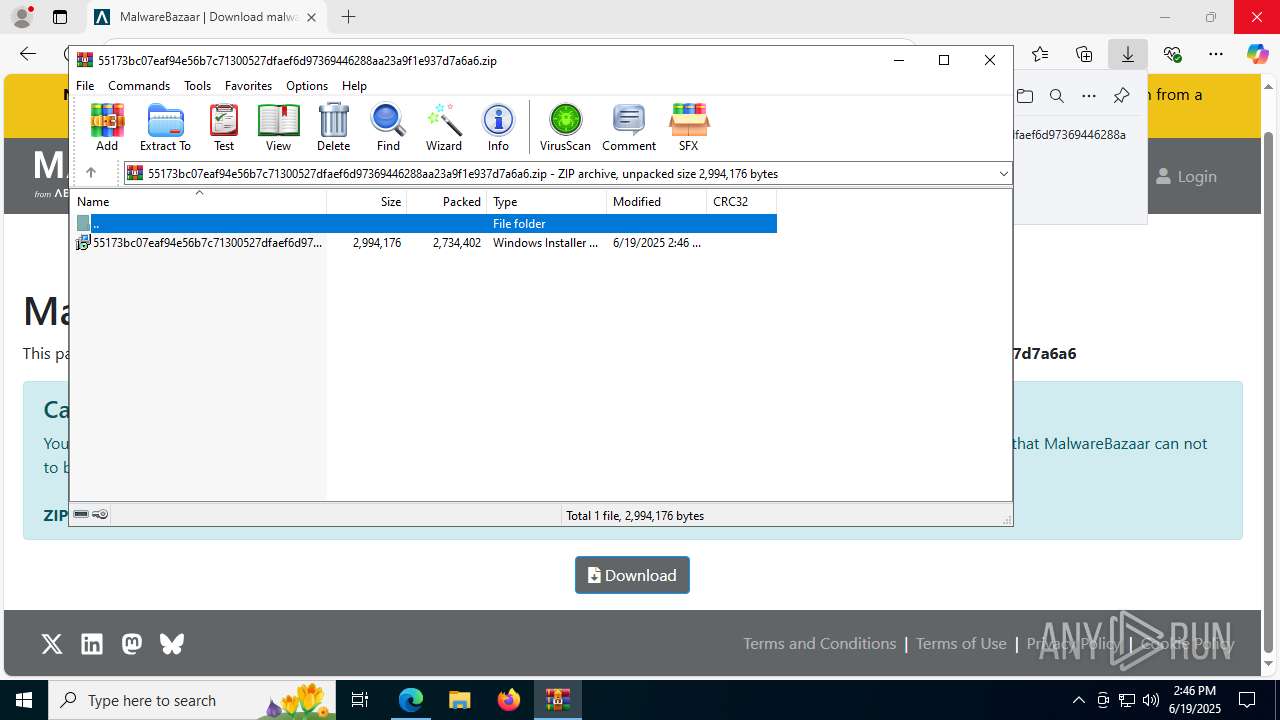
| URL: | https://bazaar.abuse.ch/download/55173bc07eaf94e56b7c71300527dfaef6d97369446288aa23a9f1e937d7a6a6/ |
| Full analysis: | https://app.any.run/tasks/024ff9cb-0d68-4454-84d6-d72a66a66c3b |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 14:46:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 220532021F7879C8A0B6C3D490121D21 |
| SHA1: | 05C5952B3135EFEE3D69CF68E40E9D1EB01DDD02 |
| SHA256: | DEEE4307711C6B5D1C4062D7A6BFF95E6F6B4EF39122454B1B27718F676DA889 |
| SSDEEP: | 3:N8N0uDWB4QkRTHIDp5jUcRRTPEpySEF:23GdkxYjrRYQS+ |
MALICIOUS
Starts NET.EXE for service management
- msiexec.exe (PID: 2324)
- net.exe (PID: 7812)
- msiexec.exe (PID: 8816)
- net.exe (PID: 8504)
- net.exe (PID: 8884)
Changes powershell execution policy (Bypass)
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageAgentInformation.exe (PID: 8292)
Bypass execution policy to execute commands
- powershell.exe (PID: 4864)
- powershell.exe (PID: 7184)
- powershell.exe (PID: 8636)
Executing a file with an untrusted certificate
- SRSelfSignCertUtil.exe (PID: 6268)
ATERA mutex has been found
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageMonitoring.exe (PID: 2632)
- AgentPackageInternalPoller.exe (PID: 8736)
- AgentPackageMonitoring.exe (PID: 4236)
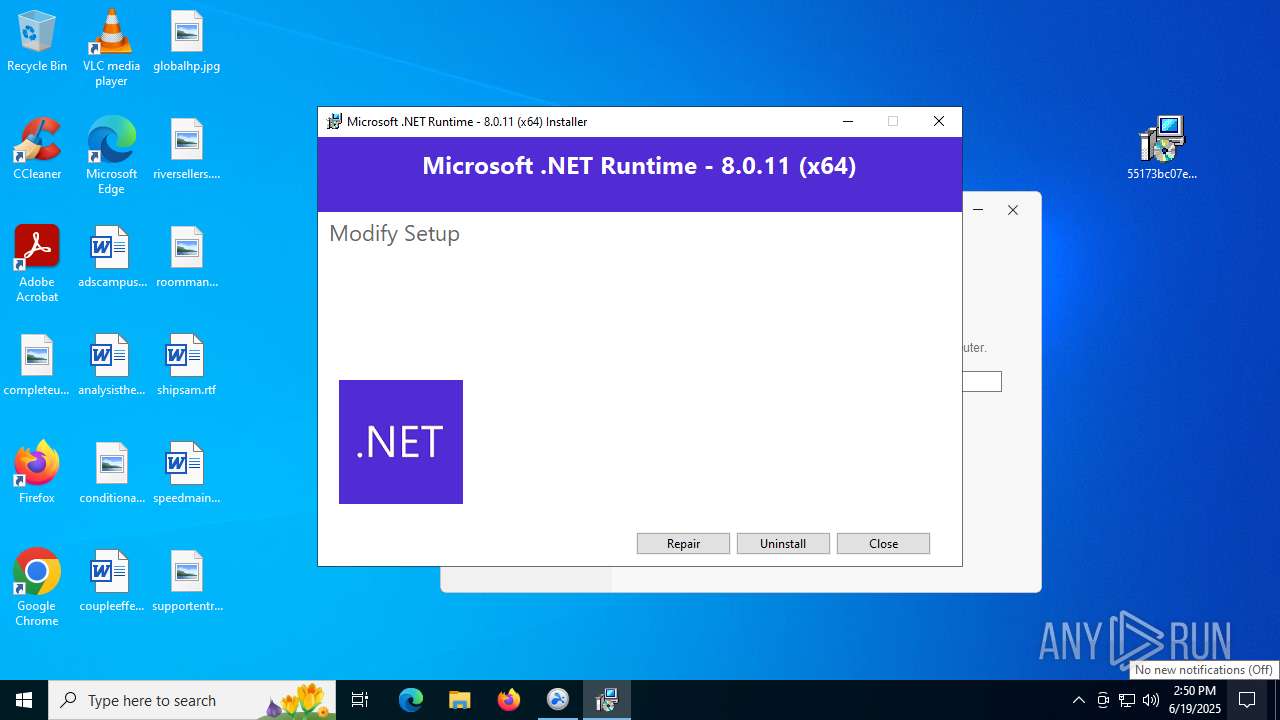
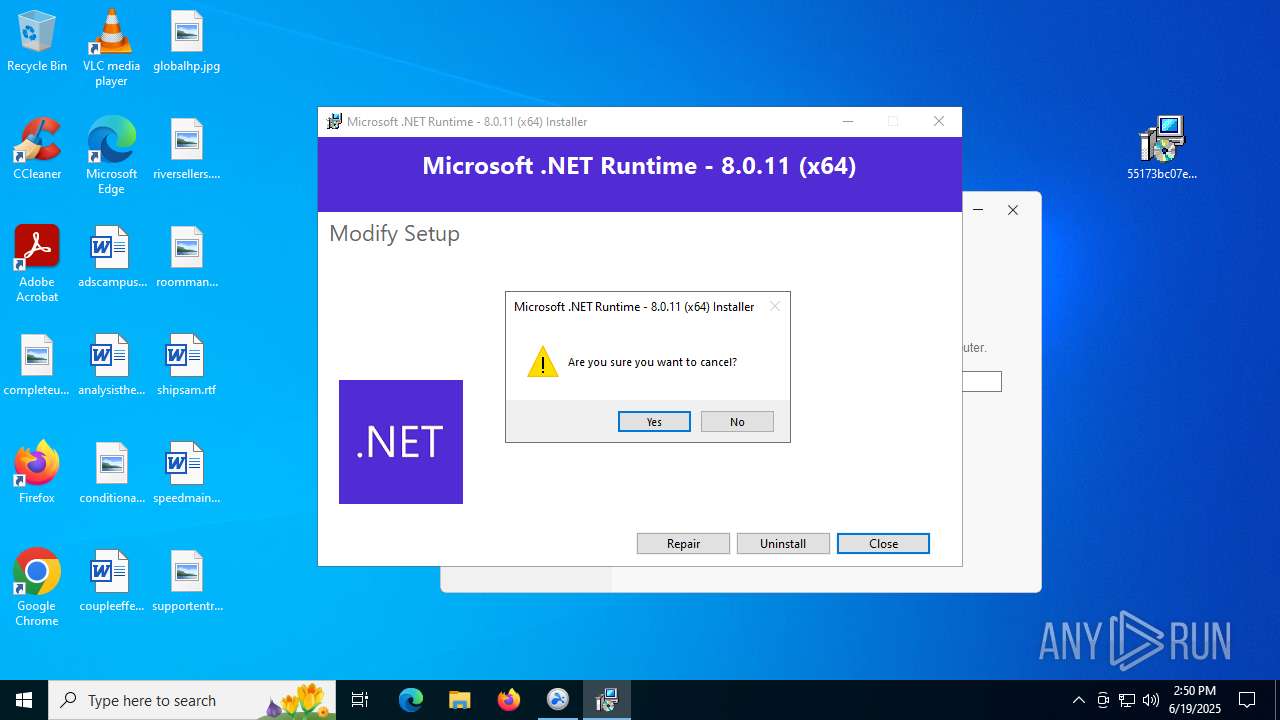
Changes the autorun value in the registry
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 1156)
- WinRAR.exe (PID: 5560)
- msiexec.exe (PID: 8176)
- AteraAgent.exe (PID: 7272)
- AteraAgent.exe (PID: 5808)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- 8-0-11.exe (PID: 8960)
- 8-0-11.exe (PID: 8996)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
- AteraAgent.exe (PID: 8588)
- Agent.Package.Availability.exe (PID: 6548)
- AgentPackageUpgradeAgent.exe (PID: 7156)
- AgentPackageUpgradeAgent.exe (PID: 8424)
Executes as Windows Service
- VSSVC.exe (PID: 416)
- AteraAgent.exe (PID: 7272)
- AteraAgent.exe (PID: 5808)
- SRService.exe (PID: 7120)
- AteraAgent.exe (PID: 8588)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8176)
Executable content was dropped or overwritten
- rundll32.exe (PID: 6868)
- rundll32.exe (PID: 6256)
- rundll32.exe (PID: 7664)
- AteraAgent.exe (PID: 7272)
- rundll32.exe (PID: 4836)
- SplashtopStreamer.exe (PID: 4824)
- csc.exe (PID: 7460)
- PreVerCheck.exe (PID: 7916)
- SetupUtil.exe (PID: 1028)
- AteraAgent.exe (PID: 5808)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- AgentPackageTicketing.exe (PID: 6172)
- rundll32.exe (PID: 8860)
- AgentPackageRuntimeInstaller.exe (PID: 6320)
- rundll32.exe (PID: 8928)
- 8-0-11.exe (PID: 8960)
- 8-0-11.exe (PID: 8996)
- rundll32.exe (PID: 9048)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
- csc.exe (PID: 9184)
- rundll32.exe (PID: 7700)
- AteraAgent.exe (PID: 8588)
- AgentPackageTicketing.exe (PID: 9028)
- Agent.Package.Availability.exe (PID: 6548)
- csc.exe (PID: 2972)
- Agent.Package.Availability.exe (PID: 1332)
- AgentPackageUpgradeAgent.exe (PID: 8424)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 7904)
- AgentPackageUpgradeAgent.exe (PID: 7156)
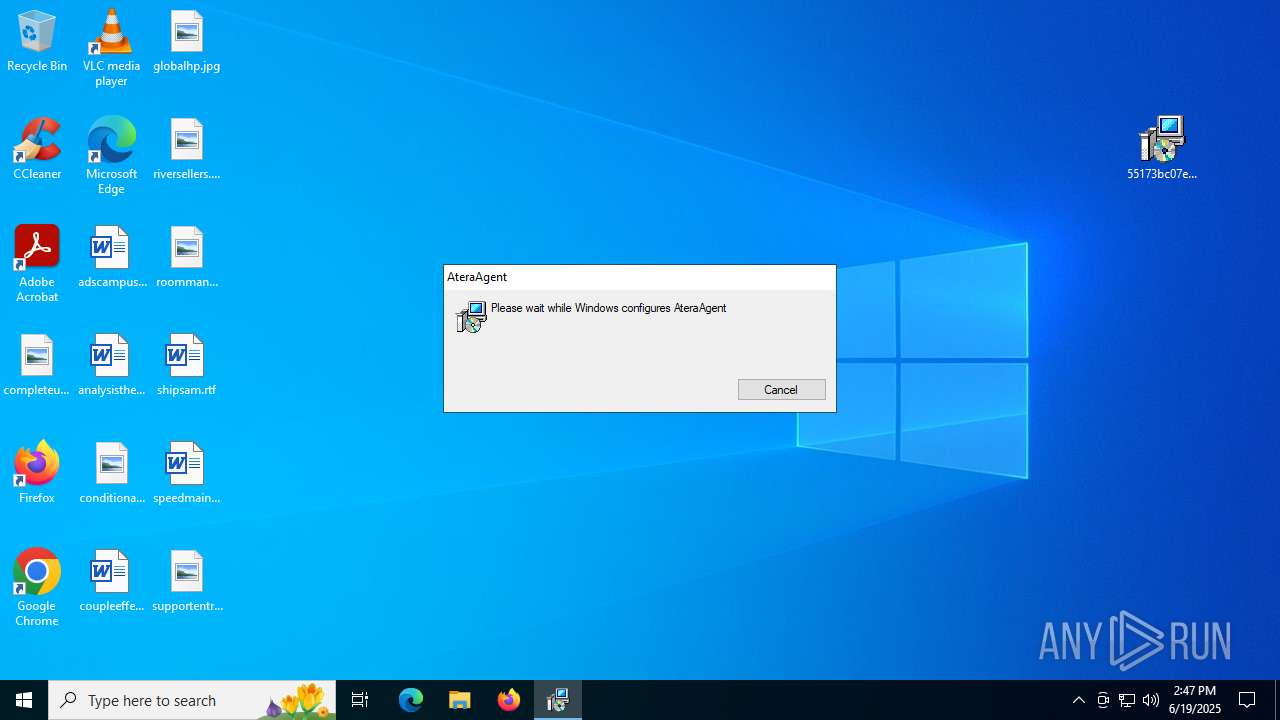
ATERAAGENT has been detected
- AteraAgent.exe (PID: 984)
- AteraAgent.exe (PID: 7272)
- AteraAgent.exe (PID: 5808)
- AteraAgent.exe (PID: 8908)
- AteraAgent.exe (PID: 9160)
- AteraAgent.exe (PID: 8588)
Potential Corporate Privacy Violation
- rundll32.exe (PID: 6868)
- AteraAgent.exe (PID: 7272)
- AgentPackageAgentInformation.exe (PID: 7864)
- AteraAgent.exe (PID: 5808)
- AgentPackageMonitoring.exe (PID: 7252)
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageSTRemote.exe (PID: 1128)
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageMarketplace.exe (PID: 5904)
- AgentPackageTicketing.exe (PID: 6172)
- rundll32.exe (PID: 8928)
- AgentPackageMonitoring.exe (PID: 2632)
- AgentPackageAgentInformation.exe (PID: 2324)
- rundll32.exe (PID: 7700)
- AteraAgent.exe (PID: 8588)
- AgentPackageInternalPoller.exe (PID: 8736)
- Agent.Package.Availability.exe (PID: 6548)
- AgentPackageMonitoring.exe (PID: 4236)
- AgentPackageAgentInformation.exe (PID: 8292)
- AgentPackageUpgradeAgent.exe (PID: 6808)
Reads security settings of Internet Explorer
- AteraAgent.exe (PID: 984)
- AteraAgent.exe (PID: 7272)
- AteraAgent.exe (PID: 5808)
- SplashtopStreamer.exe (PID: 4824)
- AgentPackageAgentInformation.exe (PID: 8140)
- SetupUtil.exe (PID: 1028)
- 8-0-11.exe (PID: 8996)
- AgentPackageAgentInformation.exe (PID: 2324)
- AteraAgent.exe (PID: 9160)
- AteraAgent.exe (PID: 8588)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 2324)
- cmd.exe (PID: 5372)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 1964)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 6180)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 4544)
- cmd.exe (PID: 7200)
- cmd.exe (PID: 4172)
- cmd.exe (PID: 7228)
- msiexec.exe (PID: 8816)
Reads the date of Windows installation
- AteraAgent.exe (PID: 7272)
- AteraAgent.exe (PID: 5808)
- AteraAgent.exe (PID: 8588)
Restarts service on failure
- sc.exe (PID: 5616)
- sc.exe (PID: 7920)
- sc.exe (PID: 6948)
Starts SC.EXE for service management
- AteraAgent.exe (PID: 7272)
- AteraAgent.exe (PID: 5808)
- AteraAgent.exe (PID: 8588)
Starts POWERSHELL.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageAgentInformation.exe (PID: 8292)
The process executes Powershell scripts
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageAgentInformation.exe (PID: 8292)
The process bypasses the loading of PowerShell profile settings
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageAgentInformation.exe (PID: 8292)
The process hides Powershell's copyright startup banner
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageAgentInformation.exe (PID: 8292)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7460)
- csc.exe (PID: 9184)
- csc.exe (PID: 2972)
Starts CMD.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 8140)
- msiexec.exe (PID: 1812)
- SetupUtil.exe (PID: 1028)
- AgentPackageRuntimeInstaller.exe (PID: 6320)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageRuntimeInstaller.exe (PID: 8792)
- AgentPackageAgentInformation.exe (PID: 8292)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Gets a collection of all available drive names (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Gets the drive type (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Accesses computer name via WMI (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
The process executes VB scripts
- cmd.exe (PID: 6320)
- cmd.exe (PID: 8400)
- cmd.exe (PID: 1128)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 6148)
- cscript.exe (PID: 4444)
- cscript.exe (PID: 8216)
Searches for installed software
- AgentPackageAgentInformation.exe (PID: 8140)
- 8-0-11.exe (PID: 8996)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
- AgentPackageAgentInformation.exe (PID: 2324)
- Agent.Package.Software.exe (PID: 1576)
- AgentPackageAgentInformation.exe (PID: 8292)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 7904)
The process creates files with name similar to system file names
- msiexec.exe (PID: 8176)
- AteraAgent.exe (PID: 5808)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 8176)
Creates/Modifies COM task schedule object
- SRService.exe (PID: 2668)
Starts a Microsoft application from unusual location
- 8-0-11.exe (PID: 8996)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
Starts itself from another location
- 8-0-11.exe (PID: 8996)
- Agent.Package.Availability.exe (PID: 6548)
- AgentPackageUpgradeAgent.exe (PID: 8424)
There is functionality for taking screenshot (YARA)
- SRService.exe (PID: 7120)
- SRManager.exe (PID: 3908)
- SRServer.exe (PID: 2792)
- SRAgent.exe (PID: 7256)
- SRFeature.exe (PID: 7860)
- SRAppPB.exe (PID: 1336)
Creates a software uninstall entry
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
Connects to unusual port
- Agent.Package.Availability.exe (PID: 6548)
- Agent.Package.Availability.exe (PID: 1332)
Application launched itself
- dotnet-runtime-8.0.11-win-x64.exe (PID: 8636)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 7228)
INFO
Checks supported languages
- SearchApp.exe (PID: 5328)
- identity_helper.exe (PID: 7776)
- identity_helper.exe (PID: 7920)
- msiexec.exe (PID: 8176)
- msiexec.exe (PID: 5348)
- msiexec.exe (PID: 2324)
- AteraAgent.exe (PID: 984)
- AgentPackageAgentInformation.exe (PID: 5476)
- AteraAgent.exe (PID: 7272)
- AgentPackageAgentInformation.exe (PID: 7864)
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 4688)
- AteraAgent.exe (PID: 5808)
- AgentPackageMonitoring.exe (PID: 7252)
- AgentPackageSTRemote.exe (PID: 4236)
- SplashtopStreamer.exe (PID: 4824)
- msiexec.exe (PID: 1812)
- cvtres.exe (PID: 2596)
- csc.exe (PID: 7460)
- PreVerCheck.exe (PID: 7916)
- _is3EC9.exe (PID: 1208)
- _is3EC9.exe (PID: 3844)
- _is3EC9.exe (PID: 3964)
- _is3EC9.exe (PID: 7100)
- _is3EC9.exe (PID: 5768)
- _is3EC9.exe (PID: 4172)
- _is3EC9.exe (PID: 7668)
- _is3EC9.exe (PID: 3780)
- _is485F.exe (PID: 7896)
- _is485F.exe (PID: 1056)
- _is485F.exe (PID: 5612)
- _is485F.exe (PID: 1488)
- _is485F.exe (PID: 4688)
- _is485F.exe (PID: 3844)
- _is485F.exe (PID: 2664)
- _is485F.exe (PID: 7416)
- _is5CE2.exe (PID: 2296)
- _is5CE2.exe (PID: 1204)
- _is5CE2.exe (PID: 5284)
- _is5CE2.exe (PID: 5172)
- _is5CE2.exe (PID: 7656)
- _is5CE2.exe (PID: 7128)
- _is5CE2.exe (PID: 1164)
- SetupUtil.exe (PID: 1520)
- SetupUtil.exe (PID: 1028)
- _is6F43.exe (PID: 7120)
- SetupUtil.exe (PID: 4752)
- _is6F43.exe (PID: 6868)
- _is6F43.exe (PID: 7028)
- _is6F43.exe (PID: 6896)
- _is6F43.exe (PID: 3732)
- SRService.exe (PID: 2668)
- _is733C.exe (PID: 7448)
- _is733C.exe (PID: 2468)
- _is6F43.exe (PID: 756)
- _is6F43.exe (PID: 516)
- _is733C.exe (PID: 7176)
- _is733C.exe (PID: 5172)
- _is733C.exe (PID: 7028)
- _is733C.exe (PID: 6524)
- _is733C.exe (PID: 3052)
- SRService.exe (PID: 7120)
- SRServer.exe (PID: 2792)
- SRAgent.exe (PID: 7256)
- SRFeature.exe (PID: 7860)
- SRAppPB.exe (PID: 1336)
- SRManager.exe (PID: 3908)
- BdEpSDK.exe (PID: 4320)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageSTRemote.exe (PID: 1128)
- AgentPackageMonitoring.exe (PID: 2632)
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageSystemTools.exe (PID: 2620)
- AgentPackageADRemote.exe (PID: 4476)
- AgentPackageRuntimeInstaller.exe (PID: 6320)
- Agent.Package.Watchdog.exe (PID: 8224)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- AgentPackageTicketing.exe (PID: 6172)
- msiexec.exe (PID: 8816)
- 8-0-11.exe (PID: 8960)
- 8-0-11.exe (PID: 8996)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
- cvtres.exe (PID: 9204)
- csc.exe (PID: 9184)
- AteraAgent.exe (PID: 8908)
- AteraAgent.exe (PID: 9160)
- msiexec.exe (PID: 8992)
- osqueryi.exe (PID: 8252)
- AteraAgent.exe (PID: 8588)
- SRVirtualDisplay.exe (PID: 4324)
- msiexec.exe (PID: 8384)
- msiexec.exe (PID: 632)
- dotnet.exe (PID: 7244)
- AgentPackageAgentInformation.exe (PID: 8292)
- AgentPackageHeartbeat.exe (PID: 5168)
- AgentPackageRuntimeInstaller.exe (PID: 8792)
- AgentPackageSTRemote.exe (PID: 6836)
- Agent.Package.Software.exe (PID: 1576)
- AgentPackageMonitoring.exe (PID: 4236)
- Agent.Package.Availability.exe (PID: 6548)
- AgentPackageMarketplace.exe (PID: 7688)
- Agent.Package.Watchdog.exe (PID: 6212)
- dotnet.exe (PID: 8196)
- AgentPackageTicketing.exe (PID: 9028)
- SRServer.exe (PID: 8884)
- Agent.Package.Availability.exe (PID: 1332)
- SRServer.exe (PID: 7476)
- csc.exe (PID: 2972)
- cvtres.exe (PID: 8332)
- AgentPackageHeartbeat.exe (PID: 8740)
- AgentPackageUpgradeAgent.exe (PID: 8424)
- AgentPackageTicketing.exe (PID: 7208)
- AgentPackageHeartbeat.exe (PID: 1560)
- AgentPackageUpgradeAgent.exe (PID: 7156)
- AgentPackageMonitoring.exe (PID: 8628)
- AgentPackageTicketing.exe (PID: 8356)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 7904)
- AgentPackageInternalPoller.exe (PID: 8380)
- AgentPackageHeartbeat.exe (PID: 6680)
- Agent.Package.Watchdog.exe (PID: 5400)
Launching a file from the Downloads directory
- msedge.exe (PID: 1156)
Application launched itself
- msedge.exe (PID: 1156)
- msedge.exe (PID: 7840)
Reads Environment values
- identity_helper.exe (PID: 7776)
- identity_helper.exe (PID: 7920)
- AteraAgent.exe (PID: 984)
- AteraAgent.exe (PID: 7272)
- AgentPackageAgentInformation.exe (PID: 5476)
- AgentPackageAgentInformation.exe (PID: 7864)
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 4688)
- AteraAgent.exe (PID: 5808)
- AgentPackageMonitoring.exe (PID: 7252)
- AgentPackageSTRemote.exe (PID: 4236)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageMonitoring.exe (PID: 2632)
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageHeartbeat.exe (PID: 4036)
- AgentPackageADRemote.exe (PID: 4476)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- AgentPackageTicketing.exe (PID: 6172)
- AgentPackageOsUpdates.exe (PID: 8464)
- AgentPackageMarketplace.exe (PID: 5904)
- SRManager.exe (PID: 3908)
- AteraAgent.exe (PID: 8908)
- AteraAgent.exe (PID: 9160)
- AgentPackageHeartbeat.exe (PID: 5168)
- AgentPackageAgentInformation.exe (PID: 8292)
- AgentPackageMarketplace.exe (PID: 7688)
- AgentPackageRuntimeInstaller.exe (PID: 8792)
- AgentPackageMonitoring.exe (PID: 4236)
- AgentPackageUpgradeAgent.exe (PID: 8424)
- AgentPackageUpgradeAgent.exe (PID: 7156)
- AgentPackageHeartbeat.exe (PID: 4920)
- AgentPackageHeartbeat.exe (PID: 6680)
- AgentPackageHeartbeat.exe (PID: 5876)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1156)
Reads the computer name
- identity_helper.exe (PID: 7776)
- identity_helper.exe (PID: 7920)
- msiexec.exe (PID: 8176)
- msiexec.exe (PID: 5348)
- msiexec.exe (PID: 2324)
- AteraAgent.exe (PID: 984)
- AteraAgent.exe (PID: 7272)
- AgentPackageAgentInformation.exe (PID: 5476)
- AgentPackageAgentInformation.exe (PID: 7864)
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 4688)
- AteraAgent.exe (PID: 5808)
- AgentPackageMonitoring.exe (PID: 7252)
- AgentPackageSTRemote.exe (PID: 4236)
- SplashtopStreamer.exe (PID: 4824)
- msiexec.exe (PID: 1812)
- _is3EC9.exe (PID: 3844)
- _is3EC9.exe (PID: 1208)
- _is3EC9.exe (PID: 3964)
- _is3EC9.exe (PID: 7100)
- _is3EC9.exe (PID: 5768)
- _is3EC9.exe (PID: 7668)
- _is3EC9.exe (PID: 3780)
- _is3EC9.exe (PID: 4172)
- _is485F.exe (PID: 7896)
- _is485F.exe (PID: 4688)
- _is485F.exe (PID: 5612)
- _is485F.exe (PID: 1488)
- _is485F.exe (PID: 1056)
- _is485F.exe (PID: 3844)
- _is485F.exe (PID: 2664)
- _is485F.exe (PID: 7416)
- _is5CE2.exe (PID: 5284)
- _is5CE2.exe (PID: 5172)
- _is5CE2.exe (PID: 7128)
- _is5CE2.exe (PID: 7656)
- _is5CE2.exe (PID: 1204)
- _is5CE2.exe (PID: 2296)
- _is5CE2.exe (PID: 1164)
- SetupUtil.exe (PID: 1028)
- _is6F43.exe (PID: 7120)
- _is6F43.exe (PID: 6868)
- _is6F43.exe (PID: 6896)
- _is6F43.exe (PID: 7028)
- _is6F43.exe (PID: 3732)
- _is6F43.exe (PID: 756)
- _is6F43.exe (PID: 516)
- SRService.exe (PID: 2668)
- _is733C.exe (PID: 2468)
- _is733C.exe (PID: 5172)
- _is733C.exe (PID: 7028)
- _is733C.exe (PID: 6524)
- _is733C.exe (PID: 7176)
- _is733C.exe (PID: 3052)
- SRService.exe (PID: 7120)
- _is733C.exe (PID: 7448)
- SRManager.exe (PID: 3908)
- SRAgent.exe (PID: 7256)
- SRFeature.exe (PID: 7860)
- AgentPackageSTRemote.exe (PID: 1128)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageMonitoring.exe (PID: 2632)
- AgentPackageHeartbeat.exe (PID: 4036)
- AgentPackageADRemote.exe (PID: 4476)
- AgentPackageRuntimeInstaller.exe (PID: 6320)
- Agent.Package.Watchdog.exe (PID: 8224)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- AgentPackageMarketplace.exe (PID: 5904)
- AgentPackageTicketing.exe (PID: 6172)
- msiexec.exe (PID: 8816)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
- 8-0-11.exe (PID: 8960)
- AteraAgent.exe (PID: 8908)
- AteraAgent.exe (PID: 9160)
- msiexec.exe (PID: 8992)
- osqueryi.exe (PID: 8252)
- AteraAgent.exe (PID: 8588)
- lockscreen.ext.exe (PID: 8792)
- wifiNetwork.ext.exe (PID: 8756)
- msiexec.exe (PID: 8384)
- msiexec.exe (PID: 632)
- AgentPackageHeartbeat.exe (PID: 5168)
- AgentPackageAgentInformation.exe (PID: 8292)
- AgentPackageMarketplace.exe (PID: 7688)
- AgentPackageRuntimeInstaller.exe (PID: 8792)
- AgentPackageSystemTools.exe (PID: 8252)
- AgentPackageTicketing.exe (PID: 9028)
- Agent.Package.Availability.exe (PID: 6548)
- SRServer.exe (PID: 7476)
- AgentPackageHeartbeat.exe (PID: 8740)
- AgentPackageUpgradeAgent.exe (PID: 8424)
- AgentPackageUpgradeAgent.exe (PID: 7156)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 7904)
- AgentPackageTicketing.exe (PID: 8356)
- Agent.Package.Watchdog.exe (PID: 5400)
- AgentPackageHeartbeat.exe (PID: 6680)
- AgentPackageHeartbeat.exe (PID: 5876)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2468)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5560)
- msiexec.exe (PID: 8176)
- msiexec.exe (PID: 1812)
Checks proxy server information
- msiexec.exe (PID: 2468)
- rundll32.exe (PID: 6868)
- rundll32.exe (PID: 4836)
- slui.exe (PID: 3980)
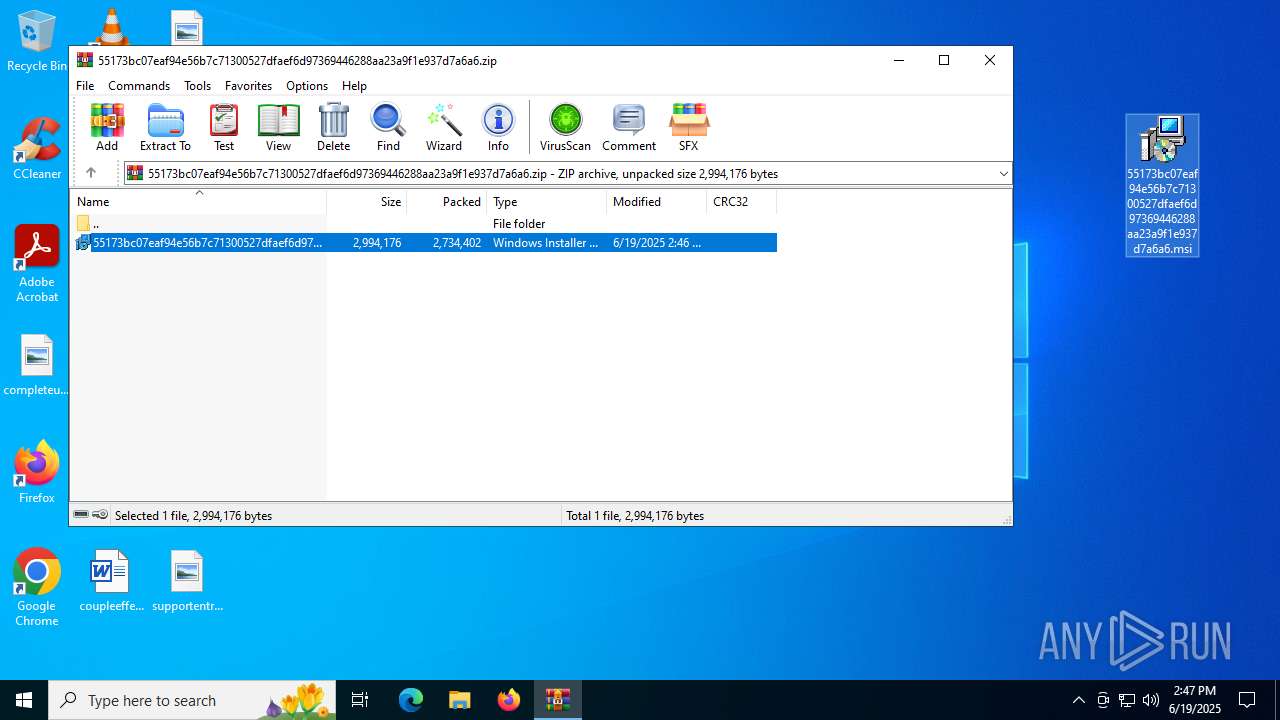
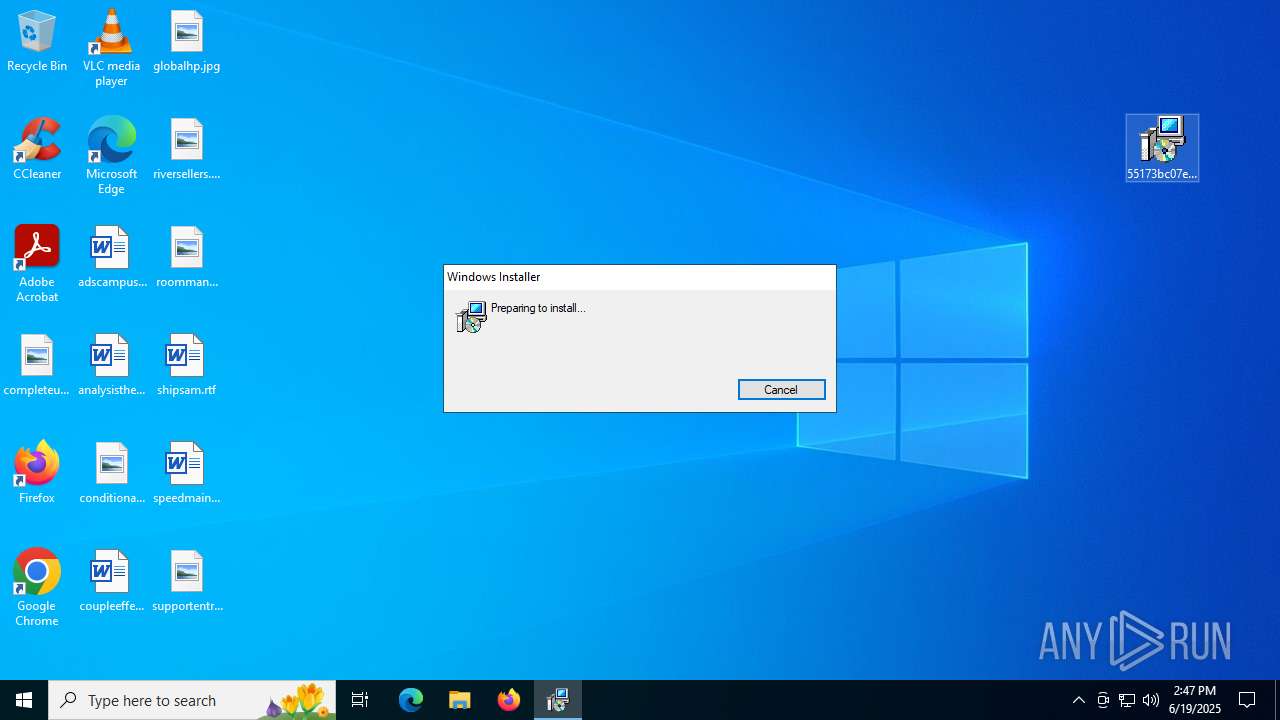
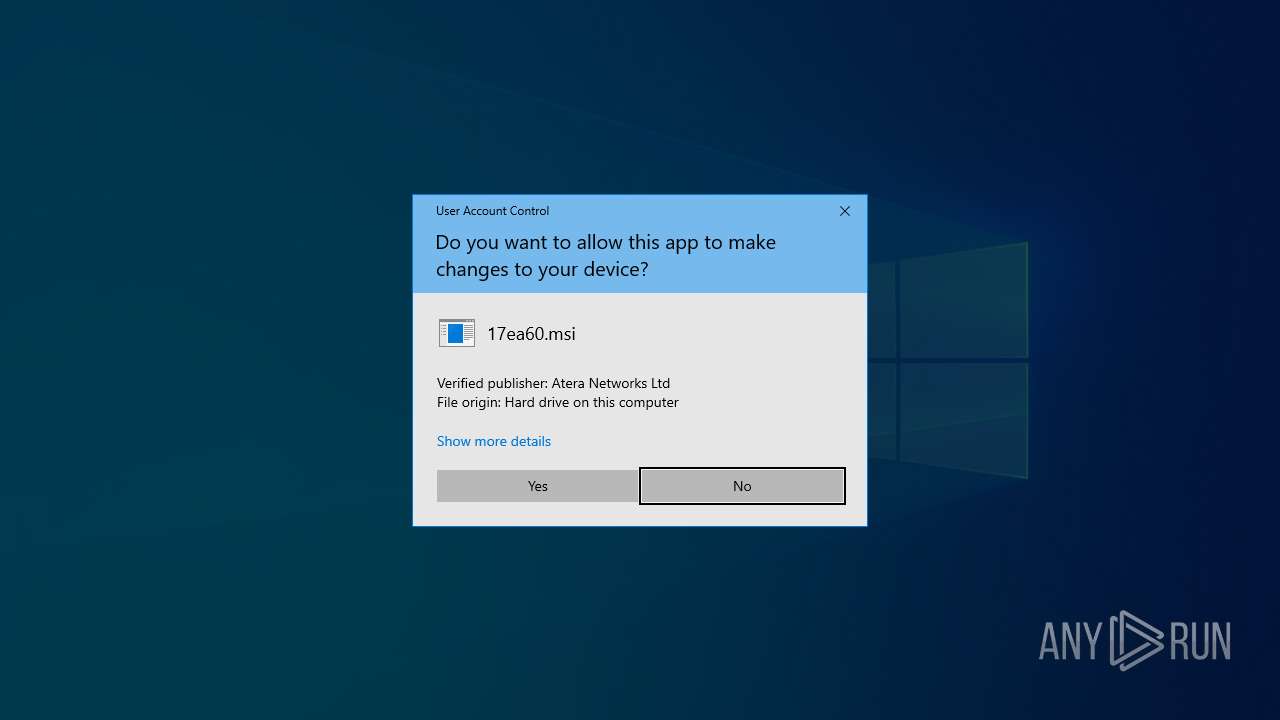
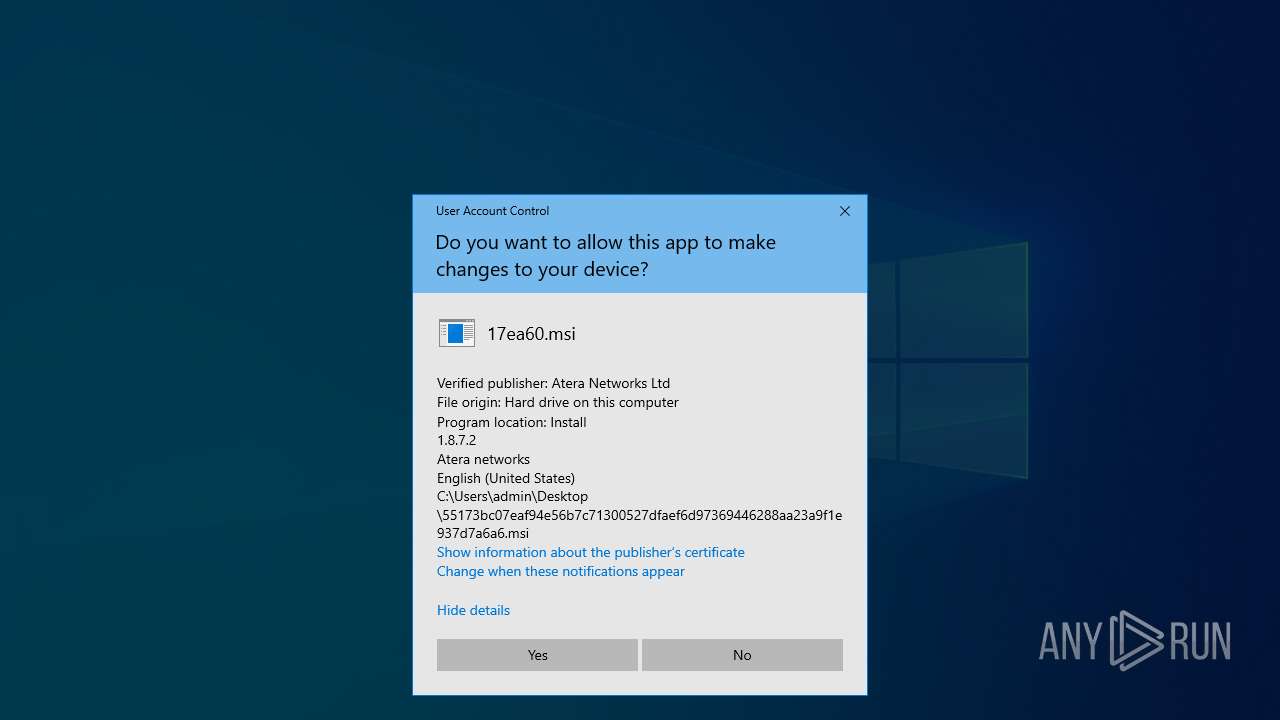
Manual execution by a user
- msiexec.exe (PID: 2468)
- SRServer.exe (PID: 8884)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 8636)
Reads the software policy settings
- msiexec.exe (PID: 2468)
- msiexec.exe (PID: 8176)
- rundll32.exe (PID: 6868)
- AteraAgent.exe (PID: 984)
- AteraAgent.exe (PID: 7272)
- rundll32.exe (PID: 4836)
- AgentPackageAgentInformation.exe (PID: 5476)
- AgentPackageAgentInformation.exe (PID: 7864)
- AteraAgent.exe (PID: 5808)
- AgentPackageSTRemote.exe (PID: 4236)
- msiexec.exe (PID: 1812)
- cscript.exe (PID: 6148)
- AgentPackageAgentInformation.exe (PID: 8140)
- SRManager.exe (PID: 3908)
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageHeartbeat.exe (PID: 4036)
- AgentPackageRuntimeInstaller.exe (PID: 6320)
- AgentPackageTicketing.exe (PID: 6172)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- rundll32.exe (PID: 8928)
- cscript.exe (PID: 4444)
- AgentPackageAgentInformation.exe (PID: 2324)
- AteraAgent.exe (PID: 9160)
- rundll32.exe (PID: 7700)
- AteraAgent.exe (PID: 8588)
- slui.exe (PID: 3980)
- SearchApp.exe (PID: 5328)
- AgentPackageInternalPoller.exe (PID: 8736)
- AgentPackageMarketplace.exe (PID: 7688)
- Agent.Package.Availability.exe (PID: 6548)
- Agent.Package.Availability.exe (PID: 1332)
- cscript.exe (PID: 8216)
- AgentPackageMonitoring.exe (PID: 4236)
- AgentPackageHeartbeat.exe (PID: 8740)
- AgentPackageHeartbeat.exe (PID: 4920)
Creates files or folders in the user directory
- msiexec.exe (PID: 2468)
Manages system restore points
- SrTasks.exe (PID: 4476)
Reads the machine GUID from the registry
- msiexec.exe (PID: 8176)
- AteraAgent.exe (PID: 984)
- AteraAgent.exe (PID: 7272)
- AgentPackageAgentInformation.exe (PID: 7864)
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageAgentInformation.exe (PID: 4688)
- AgentPackageAgentInformation.exe (PID: 5476)
- AgentPackageMonitoring.exe (PID: 7252)
- AgentPackageSTRemote.exe (PID: 4236)
- csc.exe (PID: 7460)
- msiexec.exe (PID: 1812)
- SRManager.exe (PID: 3908)
- AteraAgent.exe (PID: 5808)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageSTRemote.exe (PID: 1128)
- AgentPackageHeartbeat.exe (PID: 4036)
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageSystemTools.exe (PID: 2620)
- AgentPackageMonitoring.exe (PID: 2632)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- AgentPackageADRemote.exe (PID: 4476)
- AgentPackageTicketing.exe (PID: 6172)
- AgentPackageMarketplace.exe (PID: 5904)
- AgentPackageOsUpdates.exe (PID: 8464)
- AgentPackageRuntimeInstaller.exe (PID: 6320)
- csc.exe (PID: 9184)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
- AteraAgent.exe (PID: 9160)
- AteraAgent.exe (PID: 8908)
- AteraAgent.exe (PID: 8588)
- SearchApp.exe (PID: 5328)
- AgentPackageAgentInformation.exe (PID: 8292)
- AgentPackageMarketplace.exe (PID: 7688)
- AgentPackageRuntimeInstaller.exe (PID: 8792)
- AgentPackageSystemTools.exe (PID: 8252)
- Agent.Package.Availability.exe (PID: 6548)
- AgentPackageTicketing.exe (PID: 9028)
- csc.exe (PID: 2972)
- AgentPackageUpgradeAgent.exe (PID: 8424)
- AgentPackageHeartbeat.exe (PID: 1560)
- AgentPackageUpgradeAgent.exe (PID: 7156)
- AgentPackageHeartbeat.exe (PID: 4920)
- AgentPackageMonitoring.exe (PID: 8628)
- AgentPackageTicketing.exe (PID: 8356)
- AgentPackageHeartbeat.exe (PID: 6680)
- AgentPackageHeartbeat.exe (PID: 5876)
- AgentPackageInternalPoller.exe (PID: 8380)
Create files in a temporary directory
- rundll32.exe (PID: 6256)
- rundll32.exe (PID: 6868)
- rundll32.exe (PID: 7664)
- rundll32.exe (PID: 4836)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 7904)
The sample compiled with english language support
- rundll32.exe (PID: 6256)
- rundll32.exe (PID: 6868)
- rundll32.exe (PID: 7664)
- rundll32.exe (PID: 4836)
- AteraAgent.exe (PID: 7272)
- SplashtopStreamer.exe (PID: 4824)
- msiexec.exe (PID: 8176)
- msiexec.exe (PID: 1812)
- PreVerCheck.exe (PID: 7916)
- SetupUtil.exe (PID: 1028)
- AteraAgent.exe (PID: 5808)
- rundll32.exe (PID: 8860)
- rundll32.exe (PID: 8928)
- 8-0-11.exe (PID: 8960)
- 8-0-11.exe (PID: 8996)
- rundll32.exe (PID: 9048)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
- rundll32.exe (PID: 7700)
- AteraAgent.exe (PID: 8588)
- AgentPackageUpgradeAgent.exe (PID: 8424)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 7904)
Disables trace logs
- rundll32.exe (PID: 6868)
- AteraAgent.exe (PID: 7272)
- rundll32.exe (PID: 4836)
- AgentPackageAgentInformation.exe (PID: 5476)
- AgentPackageAgentInformation.exe (PID: 7864)
- AteraAgent.exe (PID: 5808)
- AgentPackageSTRemote.exe (PID: 4236)
- AgentPackageMonitoring.exe (PID: 7252)
- AgentPackageAgentInformation.exe (PID: 8140)
- AgentPackageHeartbeat.exe (PID: 4036)
- AgentPackageSTRemote.exe (PID: 1128)
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageMarketplace.exe (PID: 5904)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- AgentPackageTicketing.exe (PID: 6172)
- AgentPackageAgentInformation.exe (PID: 2324)
- AgentPackageMonitoring.exe (PID: 2632)
- AteraAgent.exe (PID: 8588)
- rundll32.exe (PID: 7700)
- AgentPackageInternalPoller.exe (PID: 8736)
- AgentPackageHeartbeat.exe (PID: 5168)
- AgentPackageMarketplace.exe (PID: 7688)
- AgentPackageRuntimeInstaller.exe (PID: 8792)
- AgentPackageTicketing.exe (PID: 9028)
- AgentPackageHeartbeat.exe (PID: 8740)
- AgentPackageHeartbeat.exe (PID: 1560)
- AgentPackageHeartbeat.exe (PID: 4920)
- AgentPackageHeartbeat.exe (PID: 6680)
Creates files in the program directory
- AteraAgent.exe (PID: 984)
- AteraAgent.exe (PID: 7272)
- AgentPackageSTRemote.exe (PID: 4236)
- AgentPackageMonitoring.exe (PID: 7252)
- AgentPackageAgentInformation.exe (PID: 8140)
- SetupUtil.exe (PID: 1028)
- SRSelfSignCertUtil.exe (PID: 6268)
- SRManager.exe (PID: 3908)
- AteraAgent.exe (PID: 5808)
- AgentPackageInternalPoller.exe (PID: 4708)
- AgentPackageSystemTools.exe (PID: 2620)
- AgentPackageUpgradeAgent.exe (PID: 6808)
- AgentPackageMonitoring.exe (PID: 2632)
- SRAgent.exe (PID: 7256)
- AteraAgent.exe (PID: 8588)
- AgentPackageInternalPoller.exe (PID: 8736)
- Agent.Package.Availability.exe (PID: 6548)
- AgentPackageMonitoring.exe (PID: 4236)
- AgentPackageAgentInformation.exe (PID: 8292)
- AgentPackageMonitoring.exe (PID: 8628)
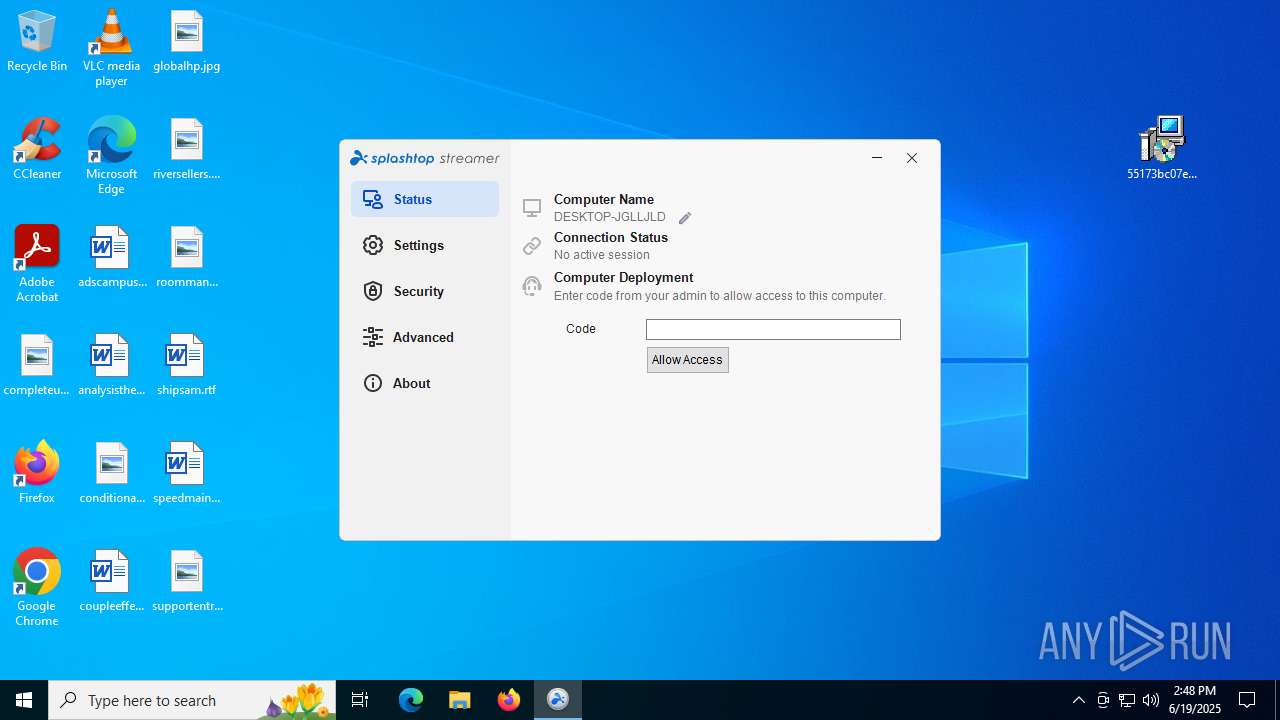
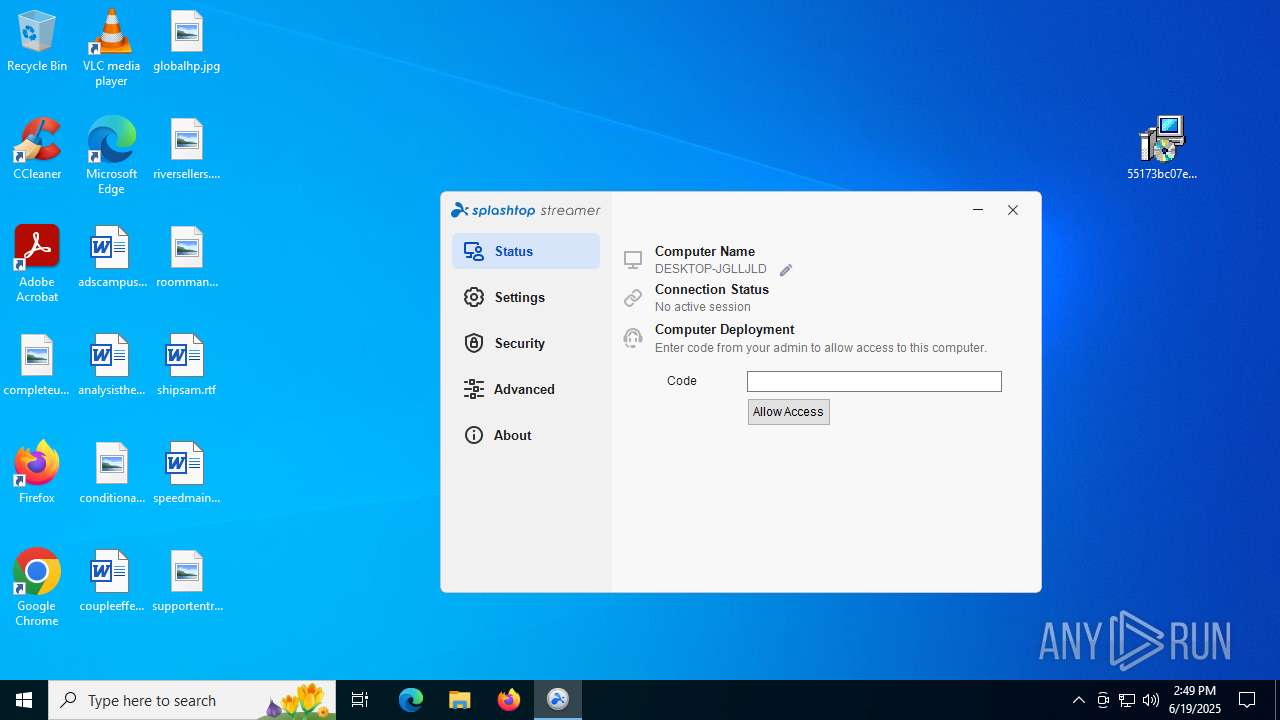
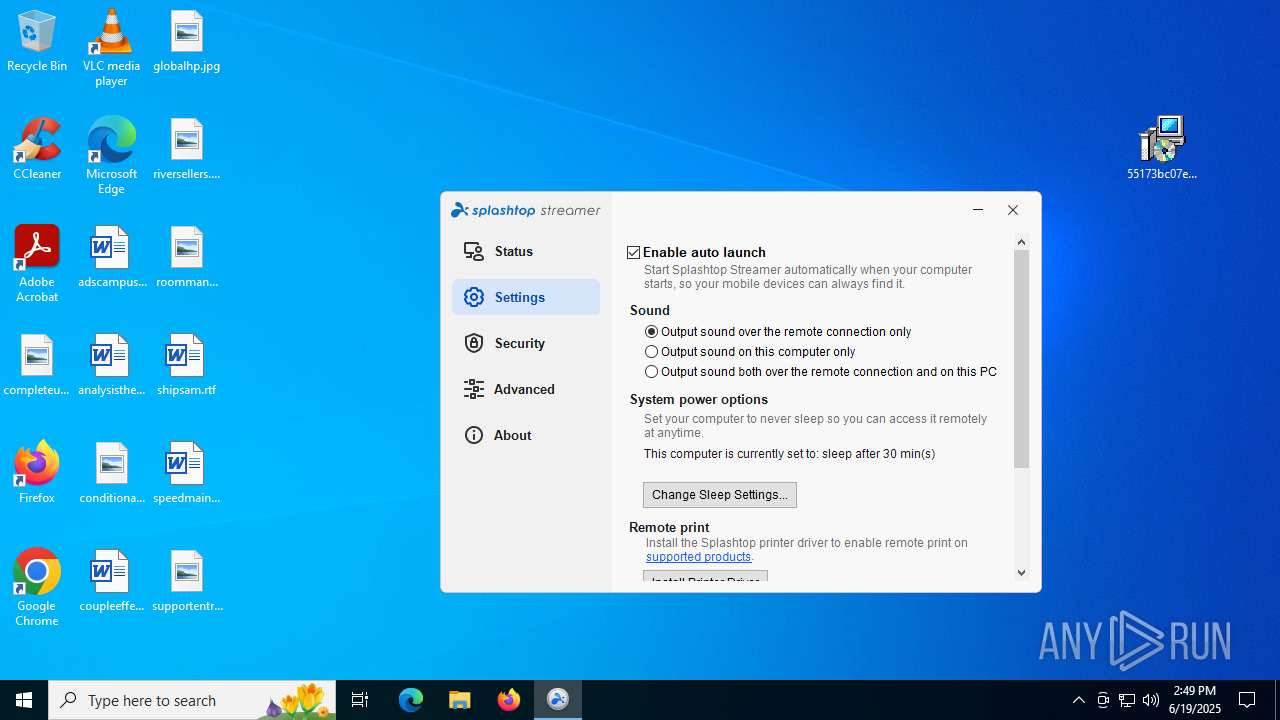
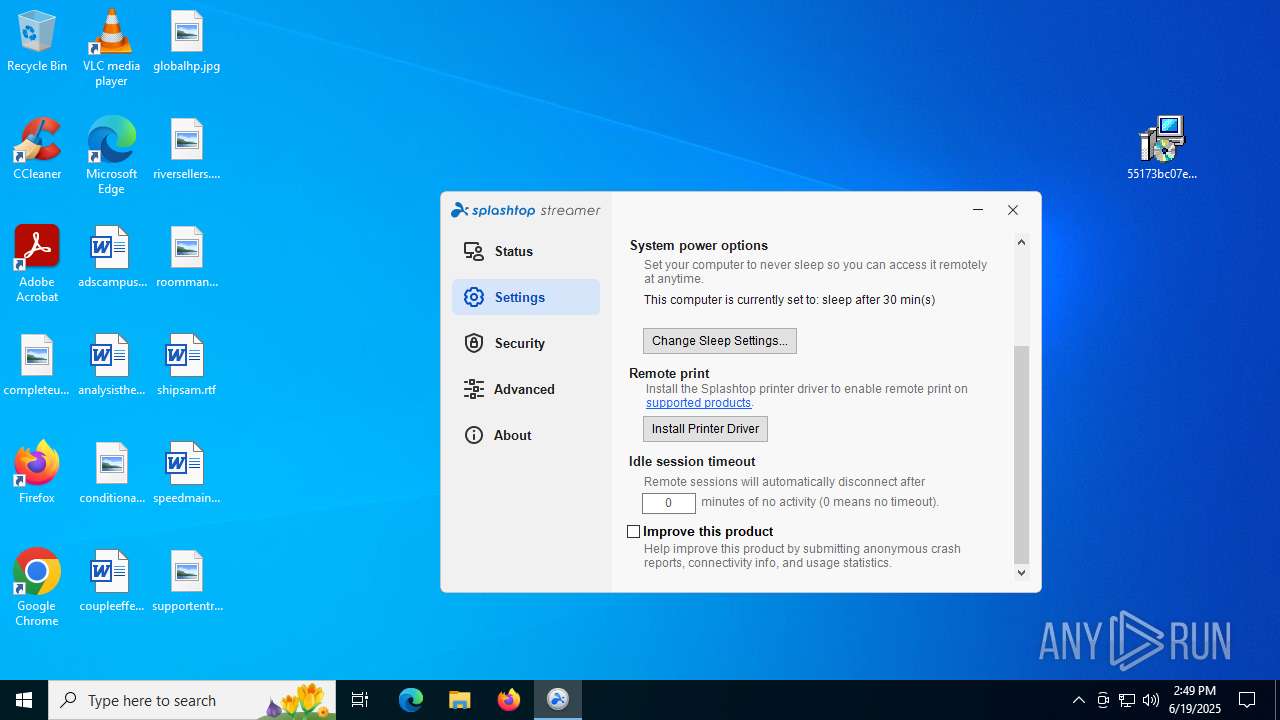
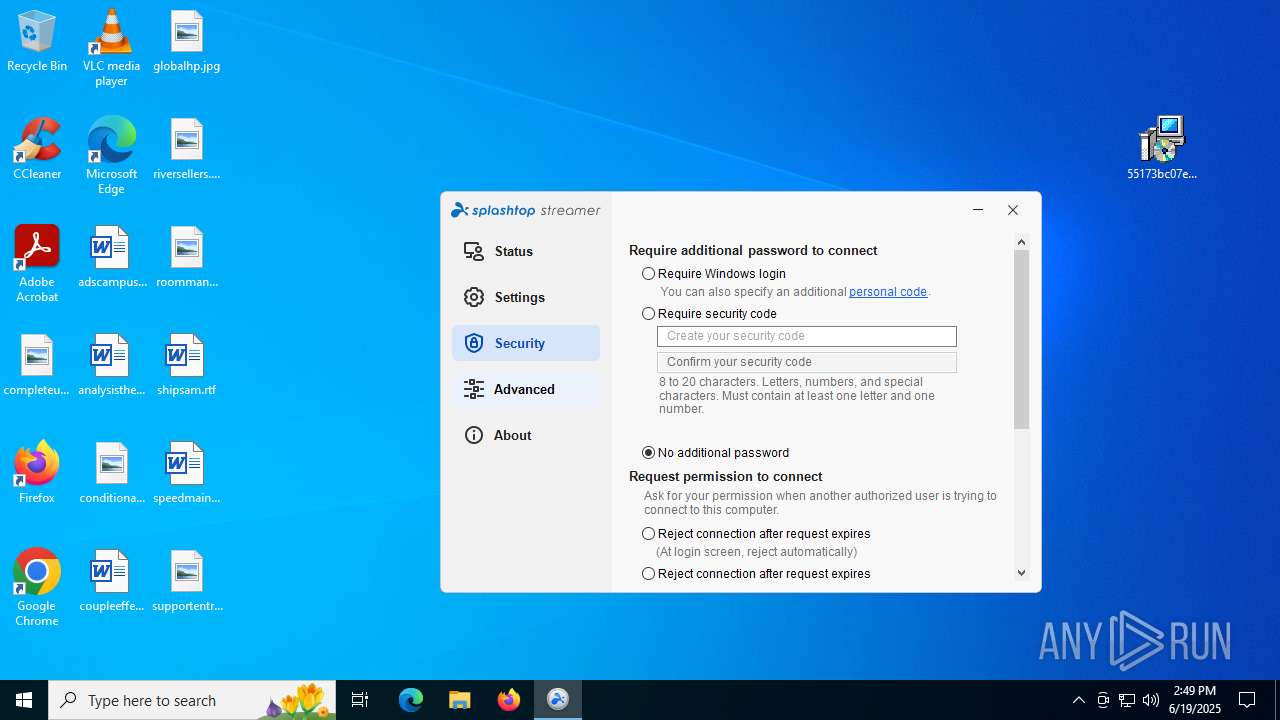
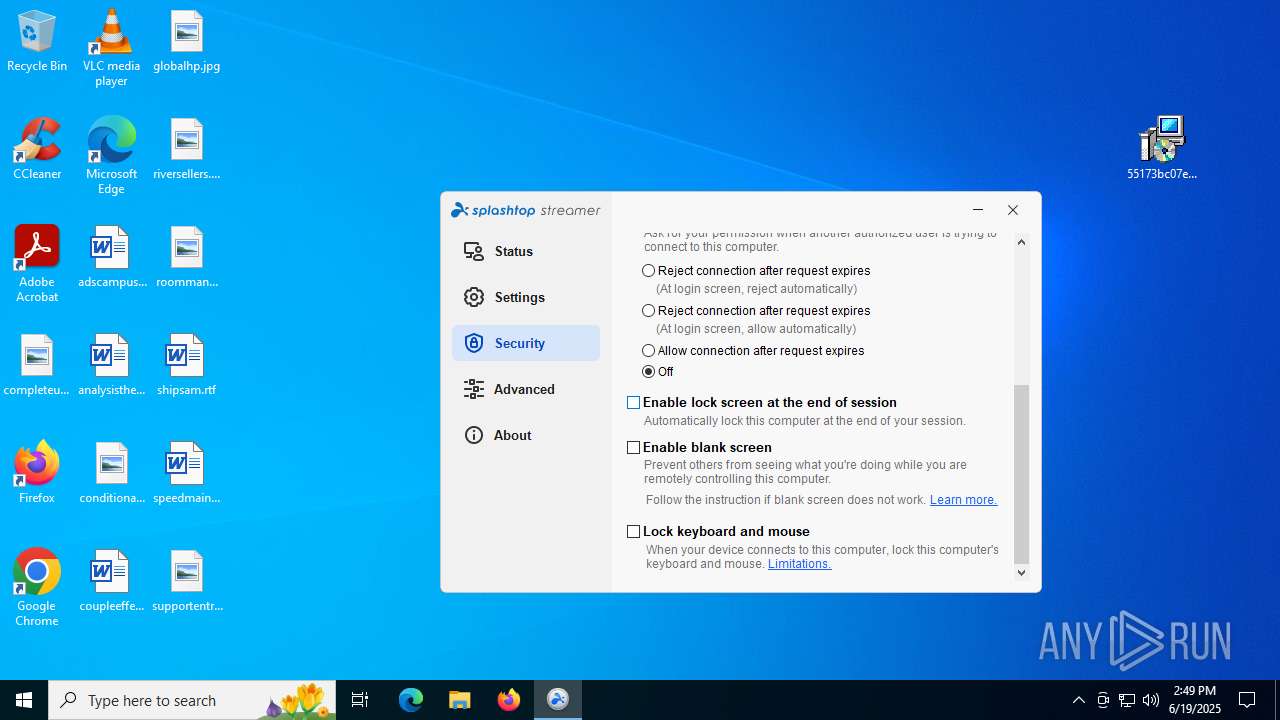
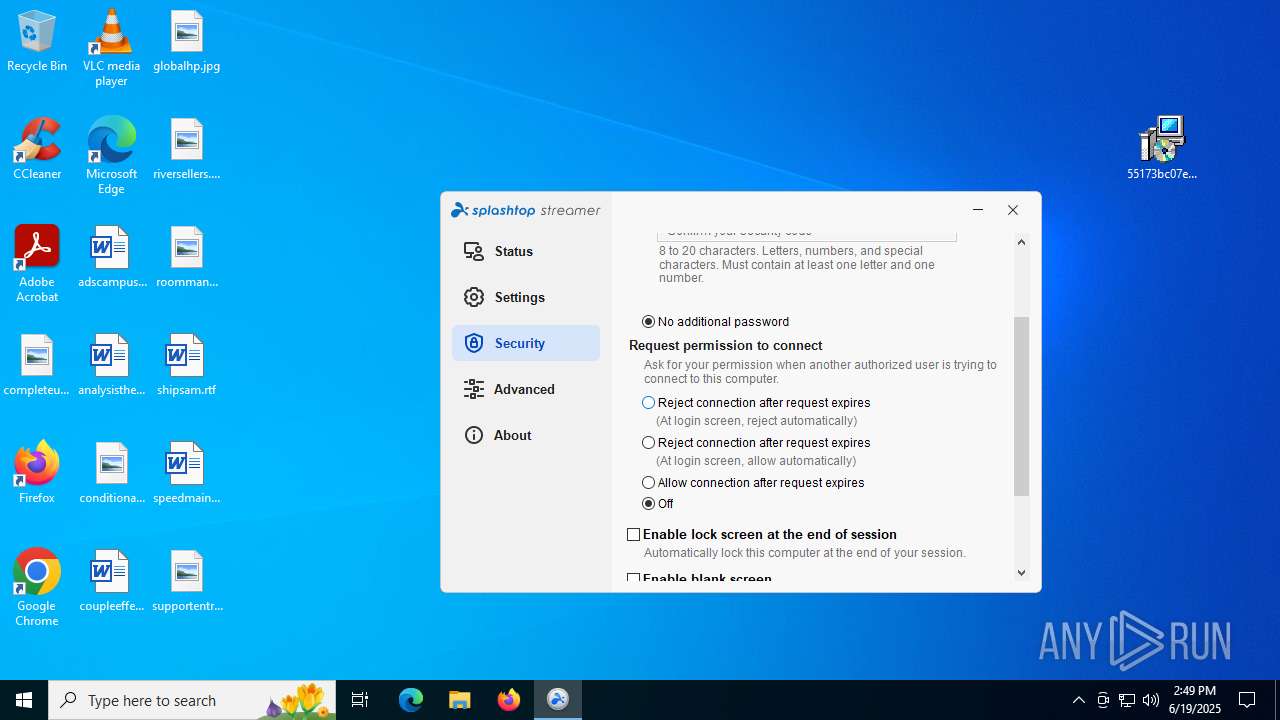
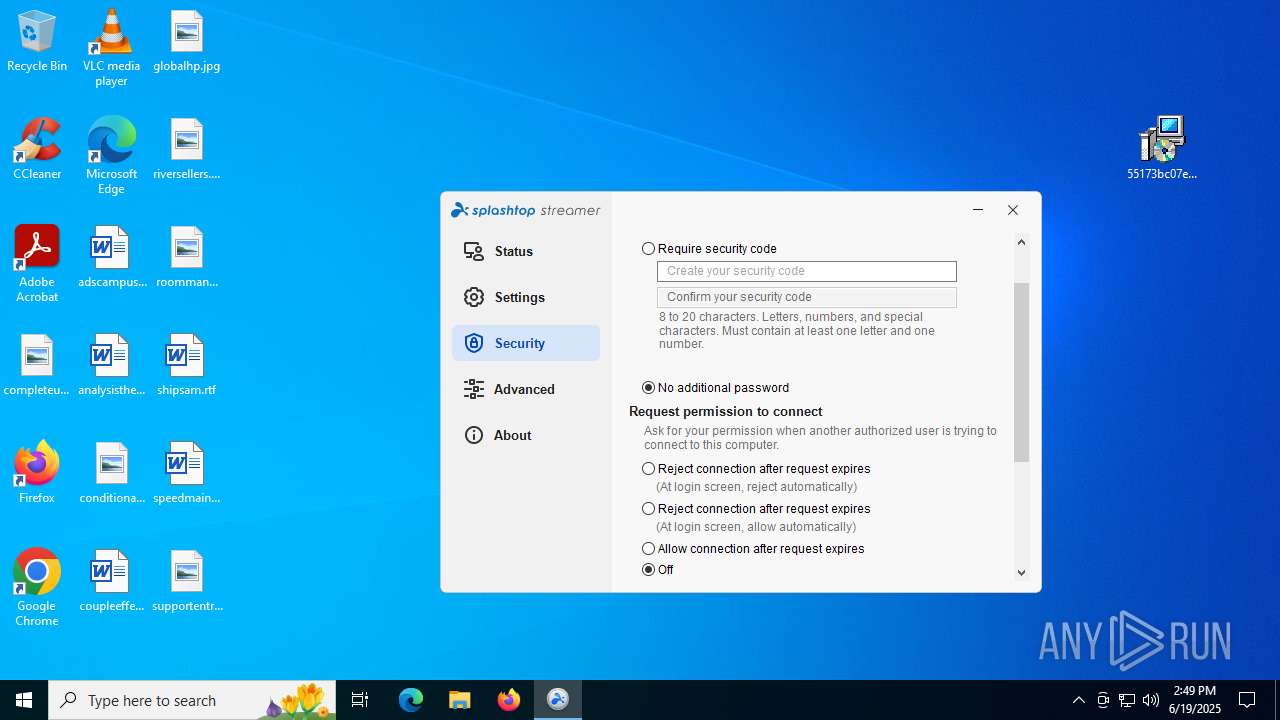
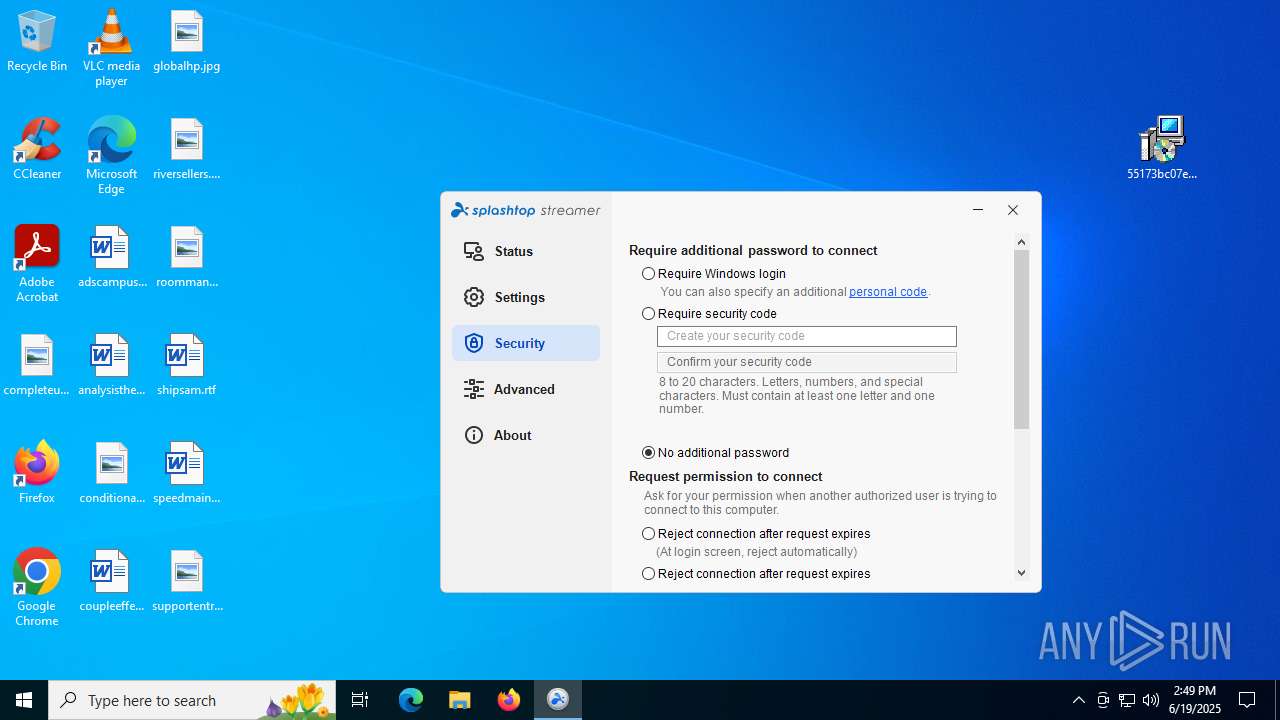
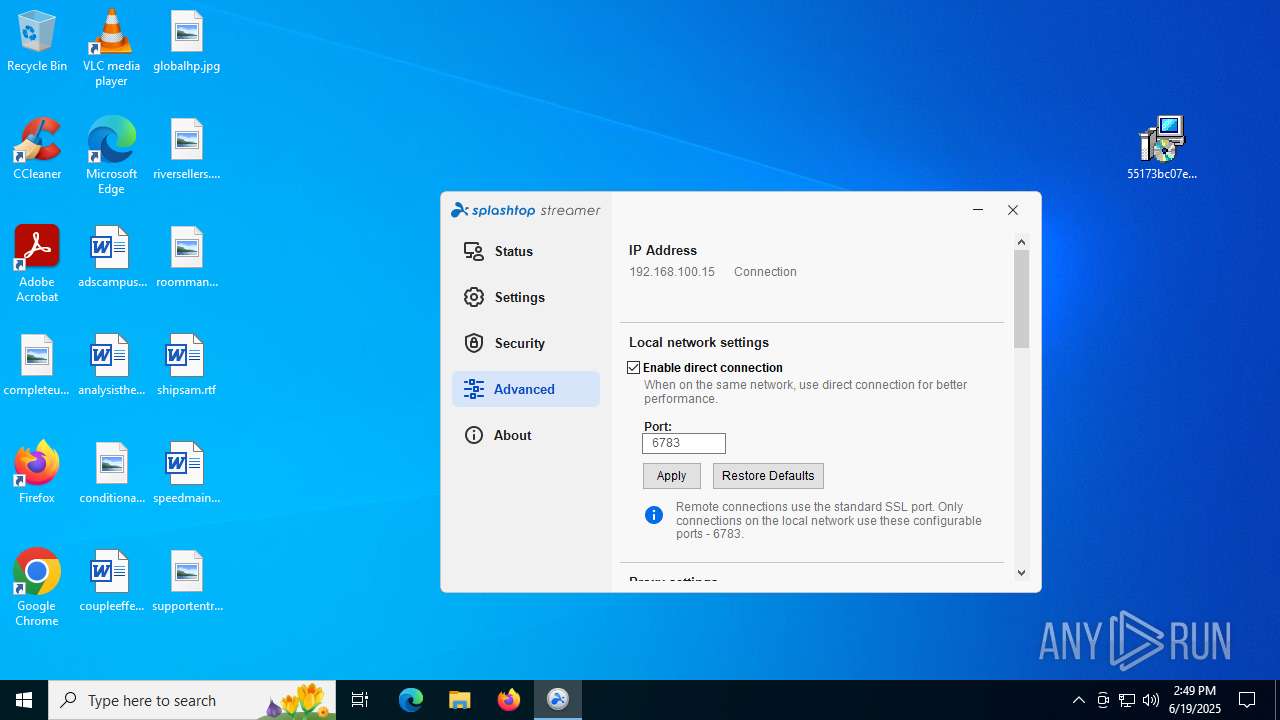
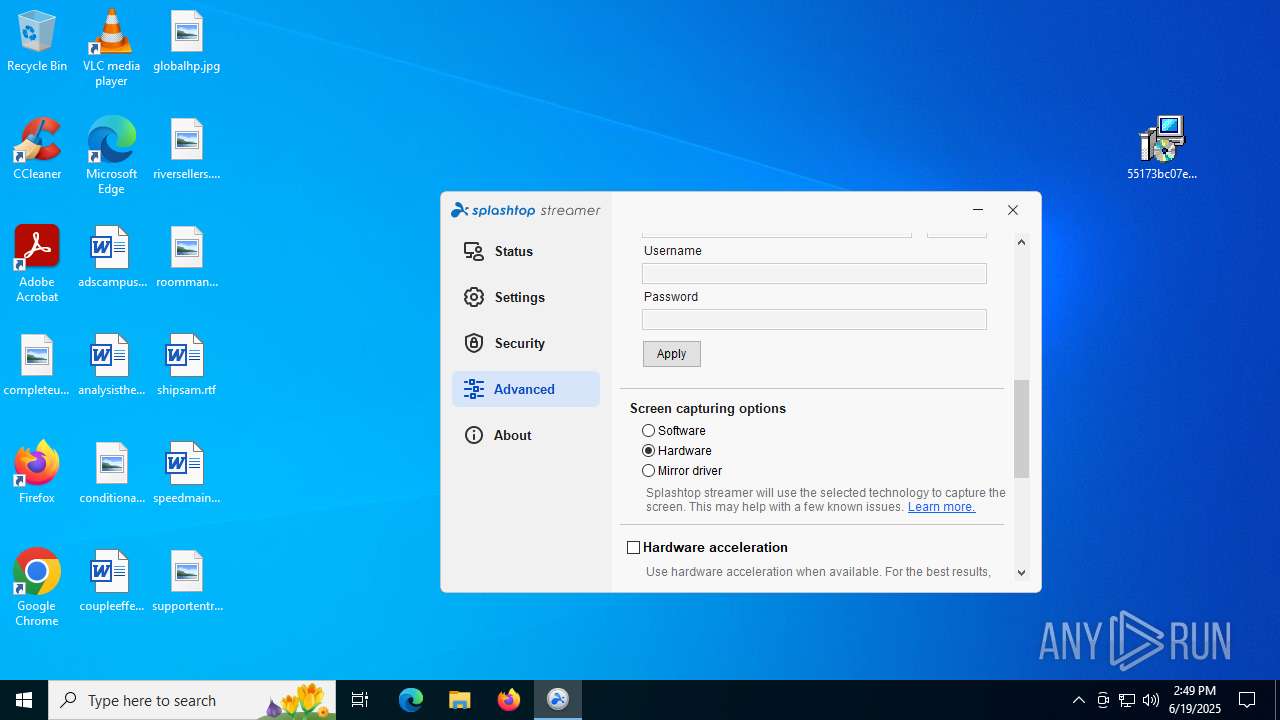
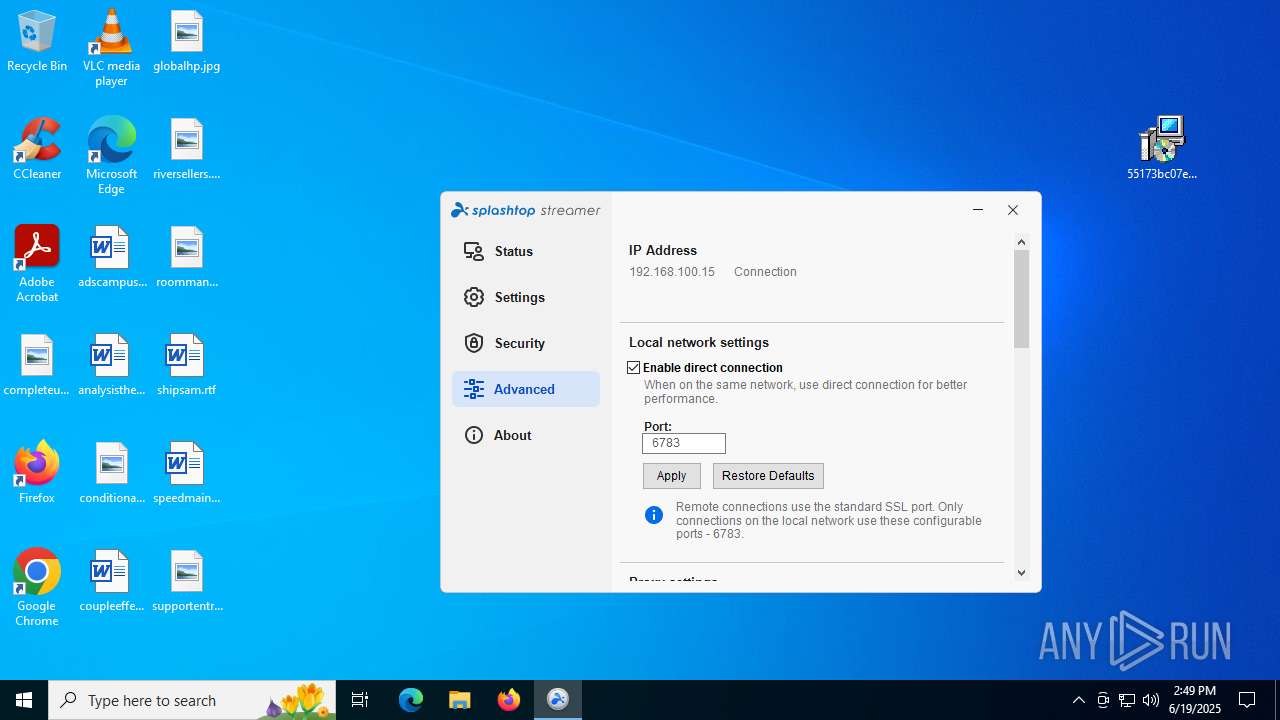
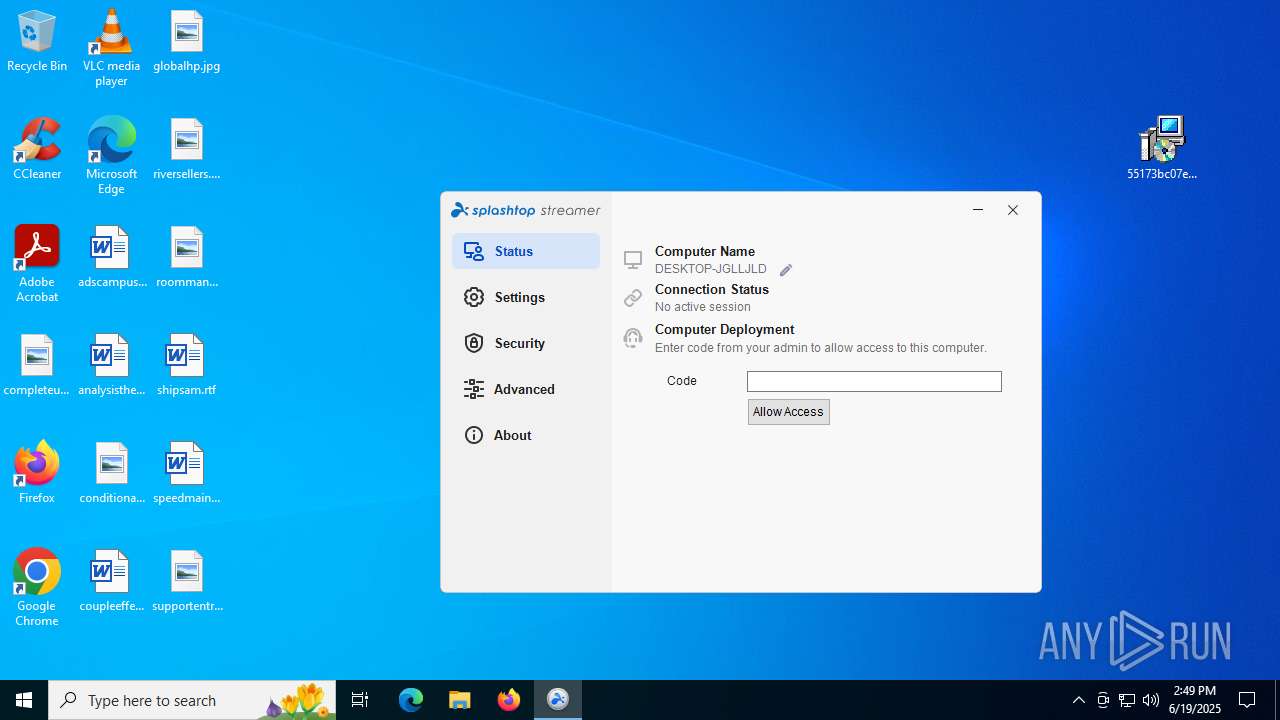
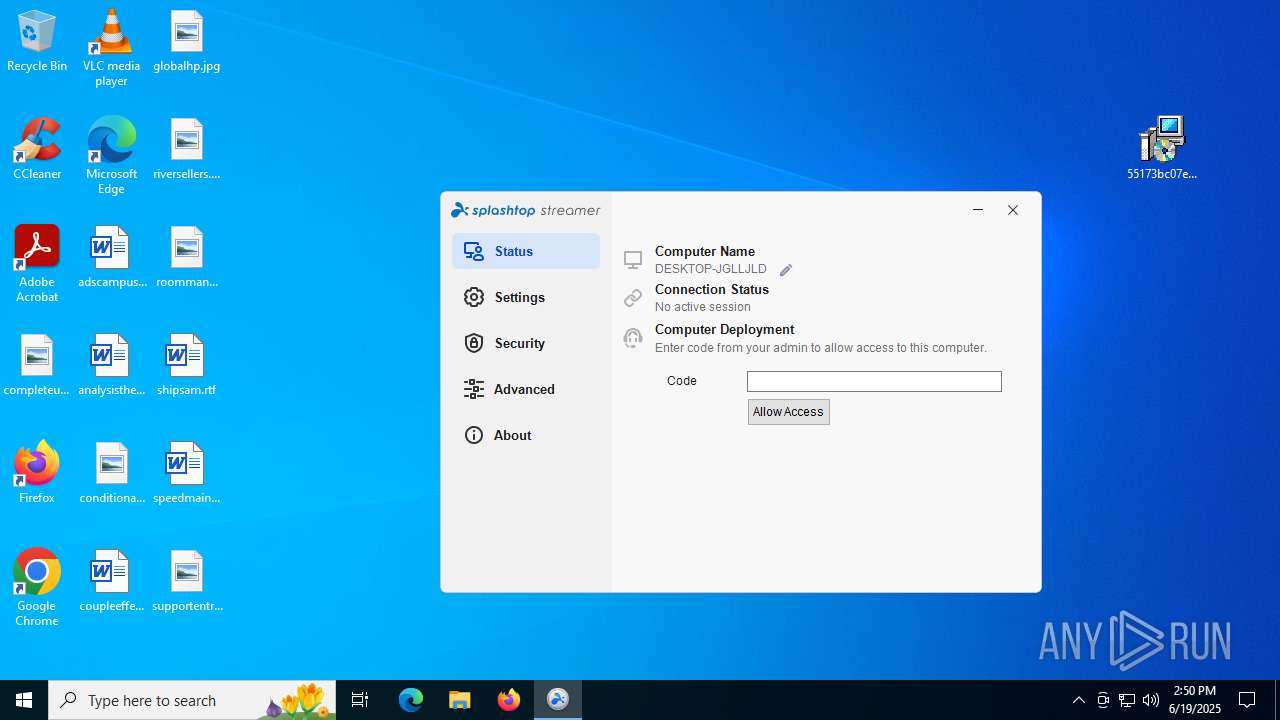
SPLASHTOP has been detected
- AgentPackageSTRemote.exe (PID: 4236)
- msiexec.exe (PID: 8176)
- msiexec.exe (PID: 1812)
- SetupUtil.exe (PID: 4752)
- SetupUtil.exe (PID: 1520)
- msiexec.exe (PID: 1812)
- cmd.exe (PID: 5744)
- SetupUtil.exe (PID: 1028)
- SRSelfSignCertUtil.exe (PID: 6268)
- cmd.exe (PID: 6160)
- SetupUtil.exe (PID: 4752)
- SRService.exe (PID: 2668)
- SRService.exe (PID: 7120)
- conhost.exe (PID: 4372)
- SRService.exe (PID: 3732)
- SRService.exe (PID: 7120)
- SRManager.exe (PID: 3908)
- SRAgent.exe (PID: 7256)
- SRAppPB.exe (PID: 1336)
- conhost.exe (PID: 6104)
- SRFeature.exe (PID: 7860)
- SRUtility.exe (PID: 756)
- SRServer.exe (PID: 2792)
- SRManager.exe (PID: 3908)
- SRFeature.exe (PID: 7860)
- SRAgent.exe (PID: 7256)
- SRServer.exe (PID: 2792)
- AgentPackageSTRemote.exe (PID: 4236)
- AgentPackageSTRemote.exe (PID: 1128)
- BdEpSDK.exe (PID: 4320)
- conhost.exe (PID: 6236)
- SRUtility.exe (PID: 7280)
- AgentPackageAgentInformation.exe (PID: 2324)
- lockscreen.ext.exe (PID: 8792)
- SRVirtualDisplay.exe (PID: 4324)
- osqueryi.exe (PID: 8252)
- AgentPackageSTRemote.exe (PID: 6836)
- conhost.exe (PID: 7184)
- SRServer.exe (PID: 8884)
- SRServer.exe (PID: 7280)
- AgentPackageAgentInformation.exe (PID: 8292)
- SRServer.exe (PID: 7476)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4864)
- powershell.exe (PID: 7184)
- powershell.exe (PID: 8636)
The sample compiled with chinese language support
- msiexec.exe (PID: 8176)
Launching a file from a Registry key
- dotnet-runtime-8.0.11-win-x64.exe (PID: 9096)
Reads product name
- SRManager.exe (PID: 3908)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
- Agent.Package.Watchdog.exe (PID: 6212)
UPX packer has been detected
- SRManager.exe (PID: 3908)
- SRAgent.exe (PID: 7256)
Creates a software uninstall entry
- msiexec.exe (PID: 8176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
498
Monitored processes
342
Malicious processes
22
Suspicious processes
15
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | C:\WINDOWS\TEMP\{67181E85-364B-42F2-ABC7-B9F6947E56BE}\_is6F43.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{9523E9FB-A6E9-4FB4-A2A8-CC96CA55526D} | C:\Windows\Temp\{67181E85-364B-42F2-ABC7-B9F6947E56BE}\_is6F43.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Flexera Integrity Level: SYSTEM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.122 Modules
| |||||||||||||||
| 632 | C:\Windows\syswow64\MsiExec.exe -Embedding BF0988F43AA9E0D93E29D62400C2133D E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | C:\WINDOWS\TEMP\{67181E85-364B-42F2-ABC7-B9F6947E56BE}\_is6F43.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{E9485E83-0339-429A-9E96-27E469704814} | C:\Windows\Temp\{67181E85-364B-42F2-ABC7-B9F6947E56BE}\_is6F43.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Flexera Integrity Level: SYSTEM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.122 Modules
| |||||||||||||||
| 756 | SRUtility.exe -r | C:\Program Files (x86)\Splashtop\Splashtop Remote\Server\SRUtility.exe | — | SRFeature.exe | |||||||||||
User: admin Company: Splashtop Inc. Integrity Level: MEDIUM Description: Splashtop® Streamer Utility Exit code: 0 Version: 3.74.3.26 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe" /i /IntegratorLogin="terra@onadrapery.com" /CompanyId="1" /IntegratorLoginUI="" /CompanyIdUI="" /FolderId="" /AccountId="001Q300000Tr1TZIAZ" /AgentId="4c72630a-1929-4233-ae1f-703ab903be54" | C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe | msiexec.exe | ||||||||||||
User: admin Company: ATERA Networks Ltd. Integrity Level: MEDIUM Description: AteraAgent Exit code: 0 Version: 1.8.7.2 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3380,i,3893160840401711343,15075858715258329505,262144 --variations-seed-version --mojo-platform-channel-handle=3392 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Splashtop\Splashtop Remote\Server\Support\SetupUtil.exe" /P ST_EVENT | C:\Program Files (x86)\Splashtop\Splashtop Remote\Server\Support\SetupUtil.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Splashtop Inc. Integrity Level: SYSTEM Description: Splashtop® Streamer Setup Utility Exit code: 0 Version: 1.0.4.1 Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\TEMP\{4E07AC12-E013-4F20-A3CE-3FC84A020779}\_is485F.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{F307D279-B1A6-466F-9F2D-AB00F198302C} | C:\Windows\Temp\{4E07AC12-E013-4F20-A3CE-3FC84A020779}\_is485F.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Flexera Integrity Level: SYSTEM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.122 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageSTRemote\AgentPackageSTRemote.exe" 4c72630a-1929-4233-ae1f-703ab903be54 "e2cca7ac-a4f2-411a-9747-d8a4ca2a45ca" agent-api.atera.com/Production 443 or8ixLi90Mf "downloadifneeded" 001Q300000Tr1TZIAZ | C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageSTRemote\AgentPackageSTRemote.exe | AteraAgent.exe | ||||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageSTRemote Exit code: 0 Version: 25.1.0.0 Modules
| |||||||||||||||
Total events
143 830
Read events
141 592
Write events
2 017
Delete events
221
Modification events
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\ConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0049006E007000750074005F007B00380033003200620036003800640032002D0037006600650032002D0034006500370031002D0061003300610064002D003200360031003600360062003600350036006500630036007D0000008EE37BF628E1DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0041007000700073005F007B00310032003000620036003500380033002D0061006300610062002D0034003900320034002D0062003300640066002D006400380065003900660066006200310031003800620034007D0000008EE37BF628E1DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LastConstraintIndexBuildCompleted |
Value: 46E17CF628E1DB018EE37BF628E1DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Input_{832b68d2-7fe2-4e71-a3ad-26166b656ec6} | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{120b6583-acab-4924-b3df-d8e9ffb118b4} | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | IndexedLanguage |
Value: en-US | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppIndexer |
| Operation: | write | Name: | LatestCacheFileName |
Value: 410070007000430061006300680065003100330033003900340038003100370039003900380031003700320030003100330036002E0074007800740000008EE37BF628E1DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppIndexer |
| Operation: | write | Name: | InstalledWin32AppsRevision |
Value: 7B00330036003100440036003700460038002D0046003800330035002D0034003300310045002D0041004600440031002D003100410042004600310033004100330035004500310030007D0000008EE37BF628E1DB01 | |||
| (PID) Process: | (1156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
1 260
Suspicious files
412
Text files
417
Unknown types
150
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176fe0.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176ff0.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176ff0.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176ff0.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17701f.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17701f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
190
DNS requests
135
Threats
85
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3572 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:x7ka8hIHtnLnKjKeEYaaeJgyCaf73VCkLjDrEGOBnuA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2468 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAnTy%2FhDMohv9omwS69%2Fdow%3D | unknown | — | — | whitelisted |
984 | AteraAgent.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7712 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6148 | cscript.exe | GET | 200 | 184.25.50.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7712 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
984 | AteraAgent.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
984 | AteraAgent.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAooSZl45YmN9AojjrilUug%3D | unknown | — | — | whitelisted |
1812 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAcc8pWv3eyMYM08IPZf5%2F0%3D | unknown | — | — | whitelisted |
6148 | cscript.exe | GET | 200 | 184.25.50.10:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6404 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3572 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 151.101.2.49:443 | bazaar.abuse.ch | FASTLY | US | whitelisted |
3572 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bazaar.abuse.ch |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
js.hcaptcha.com |
| whitelisted |
newassets.hcaptcha.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
6868 | rundll32.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7272 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7272 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7272 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
Process | Message |
|---|---|
AgentPackageMonitoring.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\x64\SQLite.Interop.dll"...
|
SplashtopStreamer.exe | [4824]2025-06-19 14:47:36 [CUnPack::UnPackFiles] (1/5)UnPack file name:C:\WINDOWS\TEMP\unpack\setup.msi (63211520) (Last=0) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:36 [CUnPack::UnPackFiles] FreeSpace:233048748032 FileSize:63211520 (Last=0) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:36 [CUtility::OSInfo] OS 10.0(19045) x64:1 (Last=0) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:36 [CUnPack::FindHeader] Name:C:\WINDOWS\TEMP\SplashtopStreamer.exe (Last=0) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:36 [CUnPack::FindHeader] Header offset:434176 (Last=183) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:36 [CUnPack::FindHeader] Sign Size:10440 (Last=0) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:37 [CUnPack::UnPackFiles] UnPack count:2 len:15 File:(null) (Last=0) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:37 [CUnPack::UnPackFiles] UnPack count:1 len:63211520 File:(null) (Last=0) |
SplashtopStreamer.exe | [4824]2025-06-19 14:47:37 [CUnPack::UnPackFiles] (2/5)UnPack file name:C:\WINDOWS\TEMP\unpack\run.bat (15) (Last=122) |