| File name: | mscorsvw_v3.0.0.6.1.exe |
| Full analysis: | https://app.any.run/tasks/f115130c-6e03-44a0-8f46-745cb4c20a41 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 13:43:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CD0955E656A3B7D57A9B745D4289750F |
| SHA1: | ED5CFF3732F0F15CBFDDD7A1A5A797EEED6C4043 |
| SHA256: | DEE2CBED1F1C71BDE1594D254A8CCF2099641CEE7100748359CD4AAC309DEBD2 |
| SSDEEP: | 1536:swBevcd2mOEC+XquYzDcmZDnsWjcdUyszI06tA5dPikgE:9ekdbj9Uts0fikgE |
MALICIOUS
Changes the autorun value in the registry
- msFB37.exe (PID: 3100)
Uses SVCHOST.EXE for hidden code execution
- mscorsvw_v3.0.0.6.1.exe (PID: 3076)
Application was dropped or rewritten from another process
- msFB37.exe (PID: 3100)
SUSPICIOUS
Executable content was dropped or overwritten
- svchost.exe (PID: 3536)
Creates files in the Windows directory
- msFB37.exe (PID: 3100)
INFO
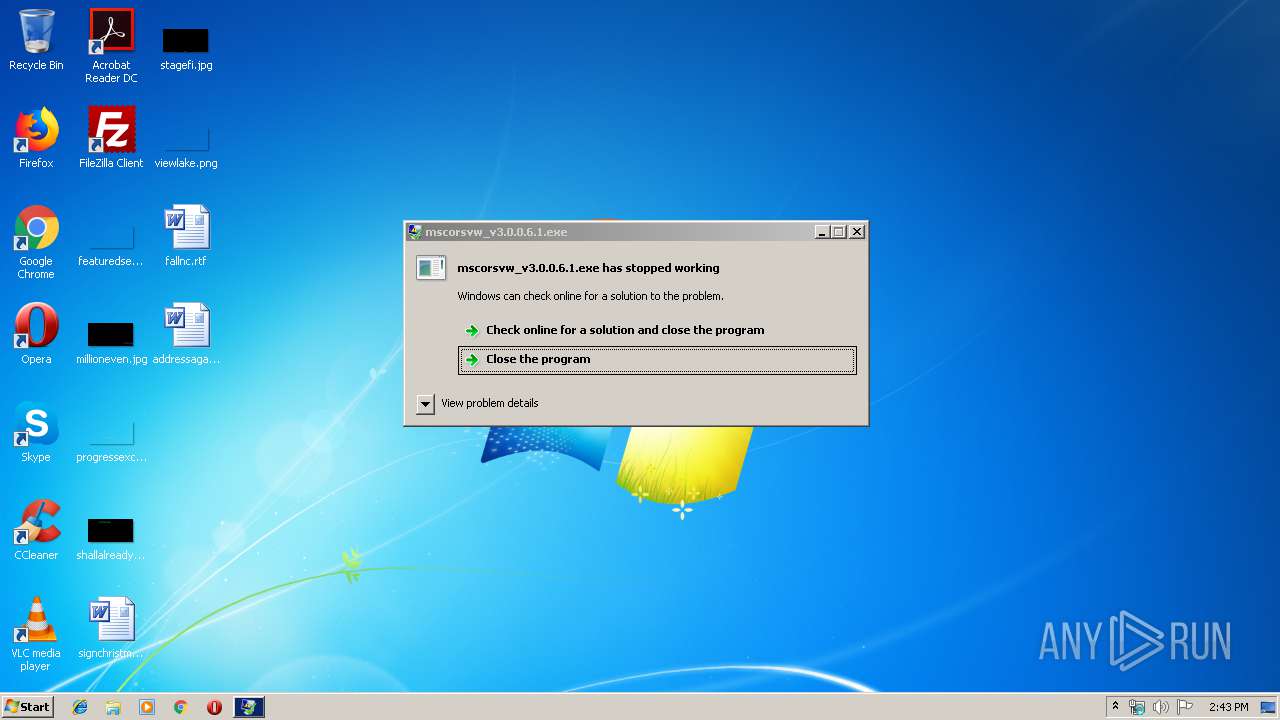
Application was crashed
- mscorsvw_v3.0.0.6.1.exe (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:04:20 16:00:21+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 42496 |
| InitializedDataSize: | 50176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16f1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Apr-2017 14:00:21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 20-Apr-2017 14:00:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000A5C4 | 0x0000A600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6975 |
.rdata | 0x0000C000 | 0x000050F2 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.68355 |
.data | 0x00012000 | 0x000060FC | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.16309 |
.reloc | 0x00019000 | 0x00000E14 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.18777 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3076 | "C:\Users\admin\AppData\Local\Temp\mscorsvw_v3.0.0.6.1.exe" -k | C:\Users\admin\AppData\Local\Temp\mscorsvw_v3.0.0.6.1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\msFB37.exe" | C:\Users\admin\AppData\Local\Temp\msFB37.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3536 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | mscorsvw_v3.0.0.6.1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
72
Read events
35
Write events
37
Delete events
0
Modification events
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3536) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | msFB37.exe | C:\Windows\Temp\xmr_dlr_test.txt | text | |
MD5:— | SHA256:— | |||
| 3536 | svchost.exe | C:\Users\admin\AppData\Local\Temp\msFB37.exe | executable | |
MD5:— | SHA256:— | |||
| 3100 | msFB37.exe | C:\Users\admin\AppData\Local\Temp\NVIDIA\config.json | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3100 | msFB37.exe | GET | — | 27.102.101.96:80 | http://27.102.101.96/nvxmrsync.exe | KR | — | — | suspicious |
3536 | svchost.exe | GET | — | 42.121.252.58:80 | http://www.cnblogs.com/wakawaka2006/p/6141629.html | CN | — | — | whitelisted |
3100 | msFB37.exe | GET | 404 | 27.102.101.96:80 | http://27.102.101.96/config.json | KR | html | 288 b | suspicious |
3536 | svchost.exe | GET | 200 | 42.121.252.58:80 | http://www.cnblogs.com/wakawaka2006/p/6141629.html | CN | html | 39.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3100 | msFB37.exe | 27.102.101.96:80 | — | DAOU TECHNOLOGY | KR | suspicious |
3536 | svchost.exe | 42.121.252.58:80 | www.cnblogs.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cnblogs.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3100 | msFB37.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3100 | msFB37.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3100 | msFB37.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3100 | msFB37.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |