| File name: | VMenuGTAG.bat |
| Full analysis: | https://app.any.run/tasks/15f51db0-7ac7-4830-ba51-4cc1577b0516 |
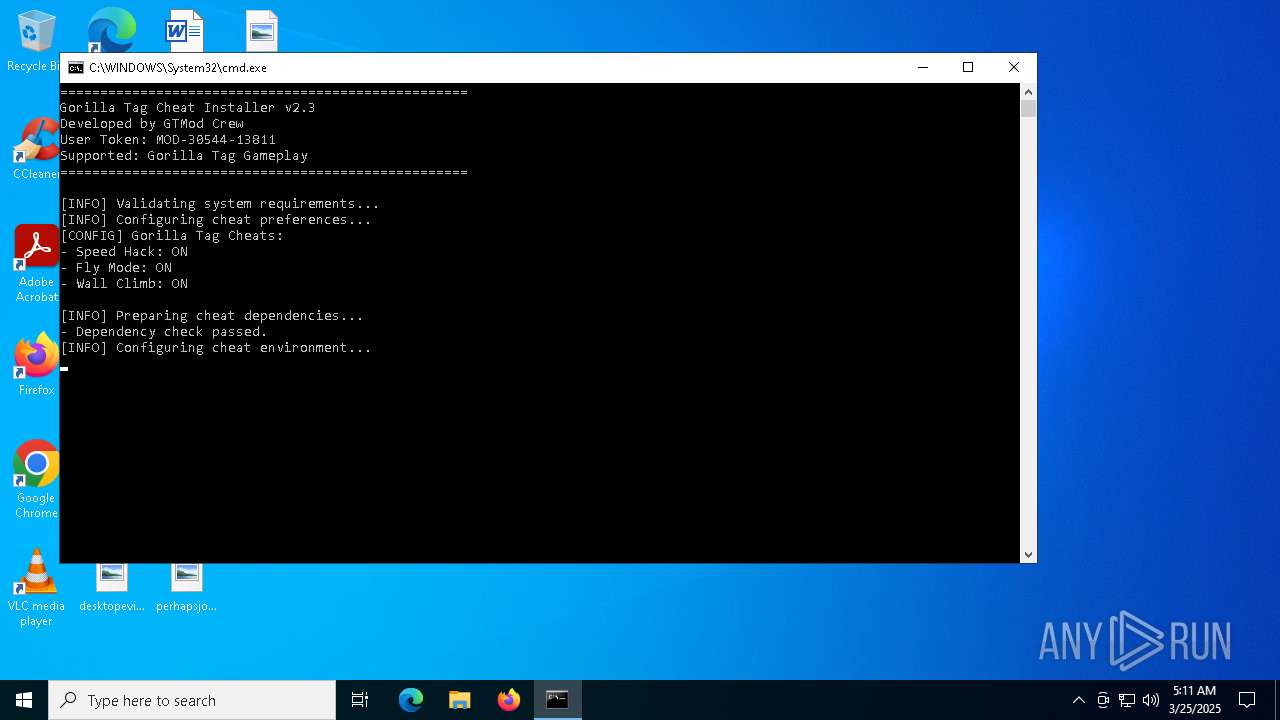
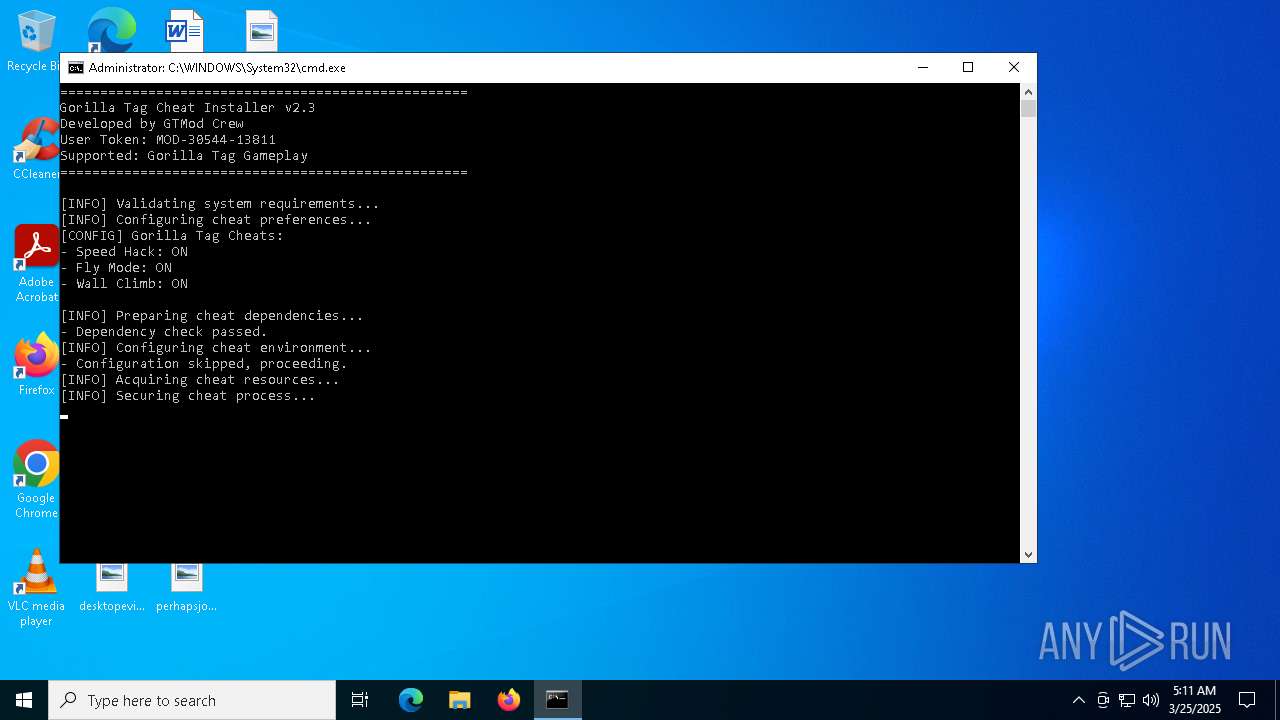
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | March 25, 2025, 05:10:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with very long lines (596), with CRLF line terminators |
| MD5: | 8DDF53335E0BD2ADA5BF016E4B362910 |
| SHA1: | 92EB6F8E4A4E353841F61F9734C112294C3C50F5 |
| SHA256: | DED64750FC41A5FEAD5987C8CBDA129268EB174F874CFAFB781B6831DBA82DA3 |
| SSDEEP: | 96:dkmtOVUIdM9WSPkCP9LAhY+0h2v9RjQrc1RzdT+0pd44UEjzH9VeqPLZ+XUCgkJP:dkmMKJgCP9LAhY+0Qv9RU4/h+0v44UEU |
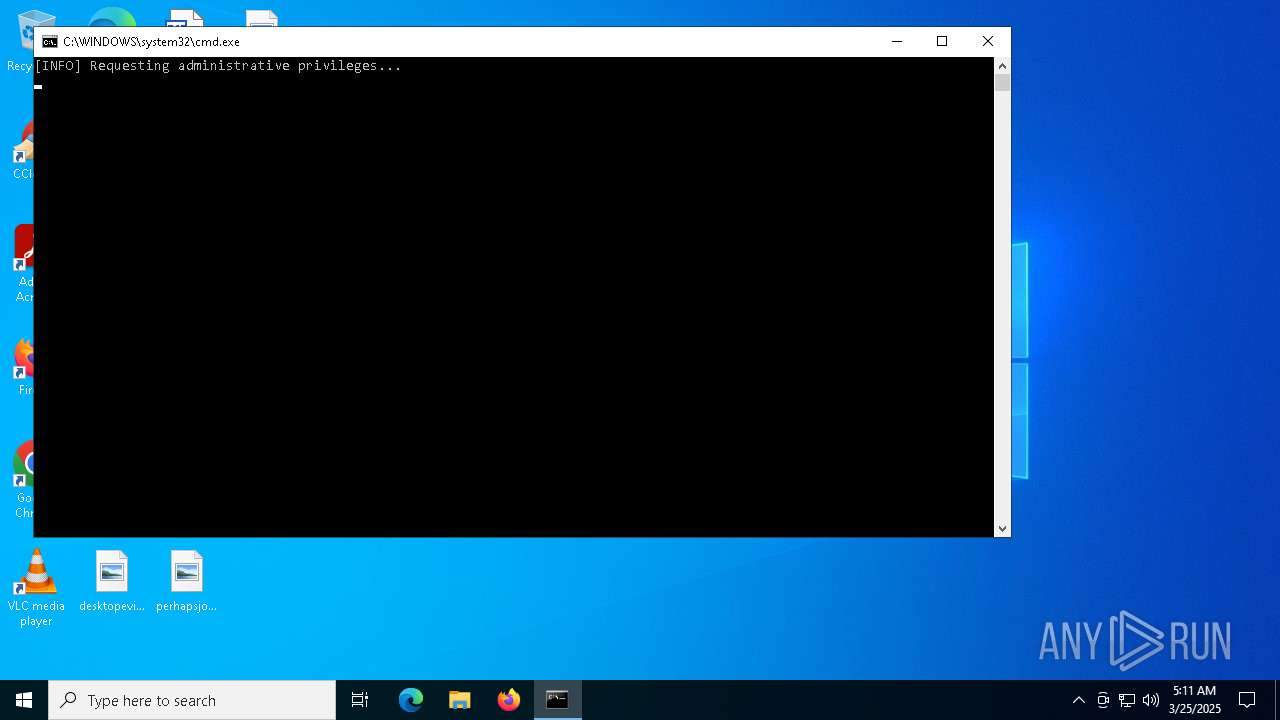
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7676)
- RuntimeBroker_4340.exe (PID: 7252)
Bypass execution policy to execute commands
- powershell.exe (PID: 7792)
- powershell.exe (PID: 5936)
- powershell.exe (PID: 8128)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 2096)
- powershell.exe (PID: 5964)
- powershell.exe (PID: 7520)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7676)
- RuntimeBroker_4340.exe (PID: 7252)
Changes Windows Defender settings
- cmd.exe (PID: 7676)
- RuntimeBroker_4340.exe (PID: 7252)
Adds process to the Windows Defender exclusion list
- cmd.exe (PID: 7676)
- RuntimeBroker_4340.exe (PID: 7252)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 7676)
XWORM has been detected (YARA)
- RuntimeBroker_4340.exe (PID: 7252)
Uses Task Scheduler to run other applications
- RuntimeBroker_4340.exe (PID: 7252)
Changes the autorun value in the registry
- RuntimeBroker_4340.exe (PID: 7252)
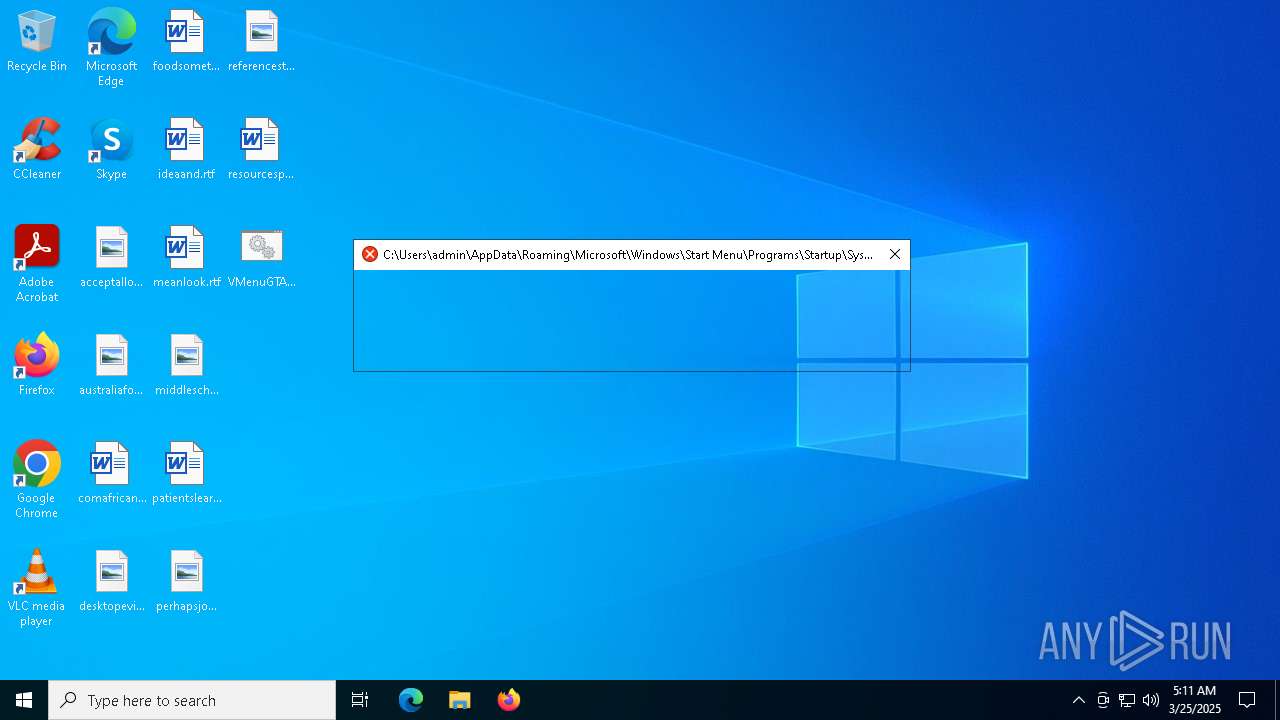
Create files in the Startup directory
- RuntimeBroker_4340.exe (PID: 7252)
XWORM has been detected (SURICATA)
- RuntimeBroker_4340.exe (PID: 7252)
SUSPICIOUS
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7404)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7676)
- RuntimeBroker_4340.exe (PID: 7252)
Starts process via Powershell
- powershell.exe (PID: 7404)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 7356)
- cmd.exe (PID: 7292)
- net.exe (PID: 7744)
- cmd.exe (PID: 7676)
Executing commands from a ".bat" file
- powershell.exe (PID: 7404)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7792)
- powershell.exe (PID: 8128)
- powershell.exe (PID: 5936)
Manipulates environment variables
- powershell.exe (PID: 7792)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8128)
- powershell.exe (PID: 5936)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7676)
- RuntimeBroker_4340.exe (PID: 7252)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7676)
Downloads file from URI via Powershell
- powershell.exe (PID: 7988)
Script adds exclusion process to Windows Defender
- cmd.exe (PID: 7676)
- RuntimeBroker_4340.exe (PID: 7252)
The executable file from the user directory is run by the CMD process
- RuntimeBroker_4340.exe (PID: 7252)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7988)
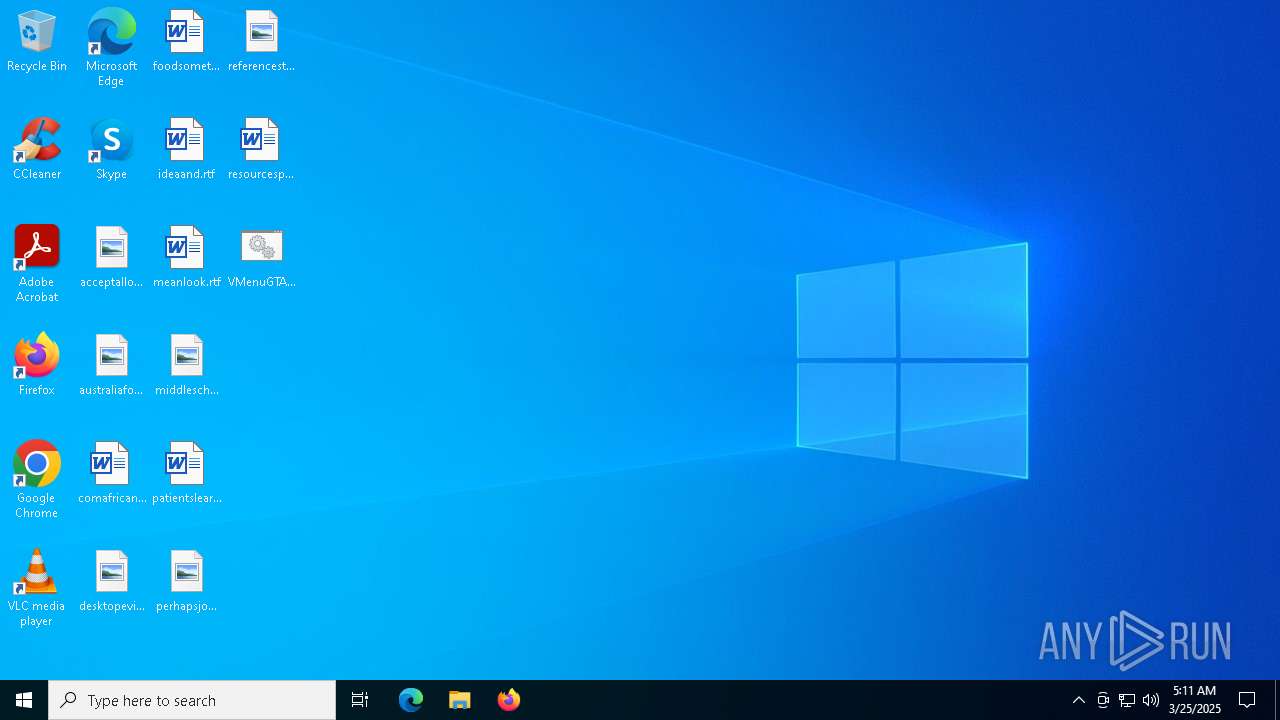
Executable content was dropped or overwritten
- powershell.exe (PID: 7988)
- RuntimeBroker_4340.exe (PID: 7252)
Reads security settings of Internet Explorer
- RuntimeBroker_4340.exe (PID: 7252)
Reads the date of Windows installation
- RuntimeBroker_4340.exe (PID: 7252)
Checks for external IP
- svchost.exe (PID: 2196)
- RuntimeBroker_4340.exe (PID: 7252)
Connects to unusual port
- RuntimeBroker_4340.exe (PID: 7252)
Contacting a server suspected of hosting an CnC
- RuntimeBroker_4340.exe (PID: 7252)
The process executes via Task Scheduler
- Sys32.exe (PID: 7824)
- Sys32.exe (PID: 5544)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7792)
- powershell.exe (PID: 8128)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 5936)
- powershell.exe (PID: 2096)
- powershell.exe (PID: 5964)
- powershell.exe (PID: 7520)
Disables trace logs
- powershell.exe (PID: 7988)
- RuntimeBroker_4340.exe (PID: 7252)
Checks proxy server information
- powershell.exe (PID: 7988)
- RuntimeBroker_4340.exe (PID: 7252)
- slui.exe (PID: 8008)
Checks supported languages
- RuntimeBroker_4340.exe (PID: 7252)
- Sys32.exe (PID: 5544)
- Sys32.exe (PID: 7824)
Reads the computer name
- RuntimeBroker_4340.exe (PID: 7252)
- Sys32.exe (PID: 7824)
- Sys32.exe (PID: 5544)
Reads Environment values
- RuntimeBroker_4340.exe (PID: 7252)
Process checks computer location settings
- RuntimeBroker_4340.exe (PID: 7252)
Manual execution by a user
- OpenWith.exe (PID: 4008)
Reads the machine GUID from the registry
- RuntimeBroker_4340.exe (PID: 7252)
- Sys32.exe (PID: 7824)
- Sys32.exe (PID: 5544)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2096)
- powershell.exe (PID: 5964)
- powershell.exe (PID: 7520)
- powershell.exe (PID: 3888)
Creates files or folders in the user directory
- RuntimeBroker_4340.exe (PID: 7252)
Create files in a temporary directory
- RuntimeBroker_4340.exe (PID: 7252)
Autorun file from Startup directory
- RuntimeBroker_4340.exe (PID: 7252)
Reads the software policy settings
- slui.exe (PID: 8008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(7252) RuntimeBroker_4340.exe
C2necessary-homepage.gl.at.ply.gg:2772
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.6
MutexGqZksLtnS1SHeSU0
Total processes
153
Monitored processes
30
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionProcess 'RuntimeBroker_4340.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | RuntimeBroker_4340.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\RuntimeBroker_4340.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | RuntimeBroker_4340.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | "C:\WINDOWS\System32\OpenWith.exe" \"C:\Users\admin\AppData\Local\Temp\RuntimeBroker_4340.exe\" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147942487 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | "C:\Users\admin\AppData\Local\Temp\Sys32.exe" | C:\Users\admin\AppData\Local\Temp\Sys32.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5936 | powershell -NoProfile -ExecutionPolicy Bypass -Command "Remove-MpPreference -ExclusionPath \"$env:TEMP\" -ErrorAction SilentlyContinue" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5964 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\Sys32.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | RuntimeBroker_4340.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6392 | schtasks /create /tn "SystemUtil_9443" /tr "\"C:\Users\admin\AppData\Local\Temp\RuntimeBroker_4340.exe\"" /sc ONLOGON /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7252 | "C:\Users\admin\AppData\Local\Temp\RuntimeBroker_4340.exe" | C:\Users\admin\AppData\Local\Temp\RuntimeBroker_4340.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 1.0.0.0 Modules
XWorm(PID) Process(7252) RuntimeBroker_4340.exe C2necessary-homepage.gl.at.ply.gg:2772 Keys AES<123456789> Options Splitter<Xwormmm> Sleep time3 USB drop nameXWorm V5.6 MutexGqZksLtnS1SHeSU0 | |||||||||||||||
Total events
52 201
Read events
52 183
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7404) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (7404) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7252) RuntimeBroker_4340.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuntimeBroker_4340_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7792 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ti4t1jux.jcy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\RuntimeBroker_4340.exe | executable | |
MD5:74FFB700CA794D4AA47FAAD0B4A4B6BD | SHA256:15C81819F702C88D6D722BAF1EC71CDC1CF1F329EC0ECC0DC92567663CFDB2CC | |||
| 8128 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vwb3p2xw.p4t.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7792 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_alha54ns.bht.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vz5kx4y2.mkj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7404 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:78BC3B4F3866F82AA1C6D1C2D144F87C | SHA256:E741A1EDD9E8E699CBC3FBC108F7E9D83BC440E670E3761266085C33E391179C | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lkkyyjhx.gbp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vqv3dh5p.a3x.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2096 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xennzgjv.rxt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8128 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_102gtq1t.kvh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
9
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 302 | 140.82.121.4:443 | https://github.com/venisz/Roblox-Coding-Tutorial/raw/refs/heads/gang/System32.exe | unknown | — | — | unknown |
2104 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7252 | RuntimeBroker_4340.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/venisz/Roblox-Coding-Tutorial/refs/heads/gang/System32.exe | unknown | executable | 73.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7988 | powershell.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7988 | powershell.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7252 | RuntimeBroker_4340.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
7252 | RuntimeBroker_4340.exe | 147.185.221.27:2772 | necessary-homepage.gl.at.ply.gg | PLAYIT-GG | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
ip-api.com |
| whitelisted |
necessary-homepage.gl.at.ply.gg |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET HUNTING EXE Downloaded from Github |
— | — | Misc activity | ET INFO EXE CheckRemoteDebuggerPresent (Used in Malware Anti-Debugging) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |