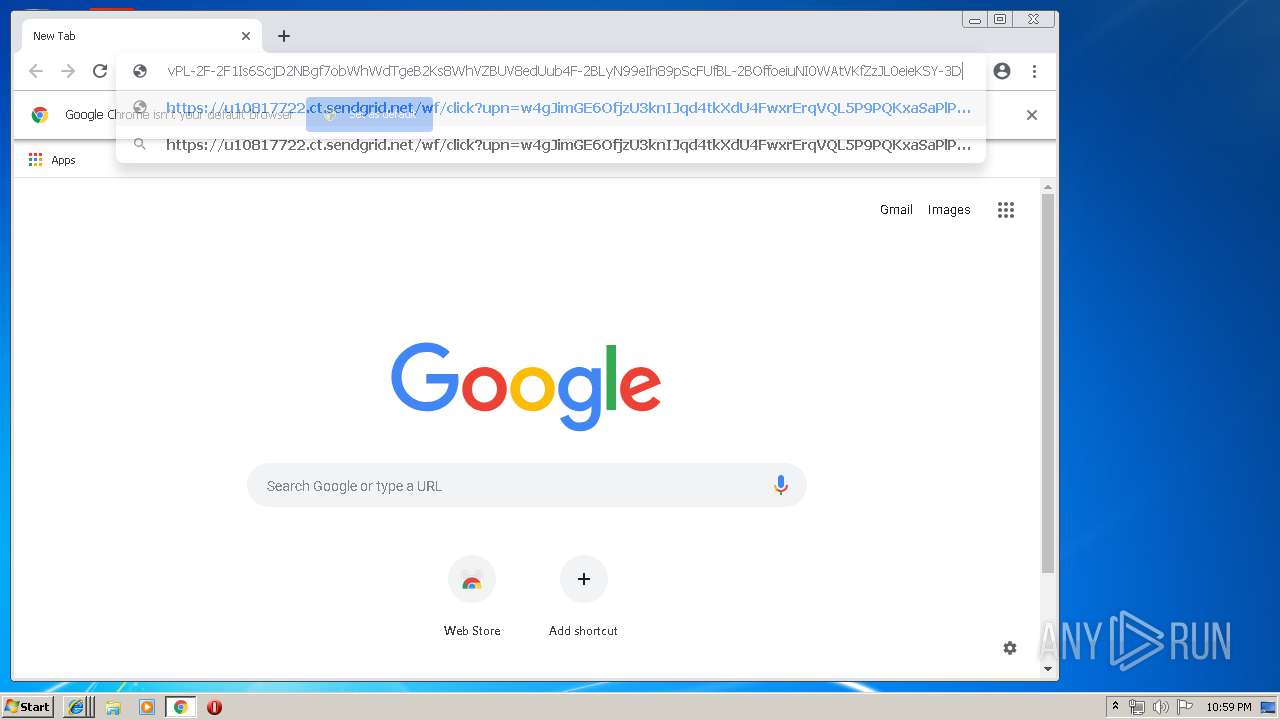
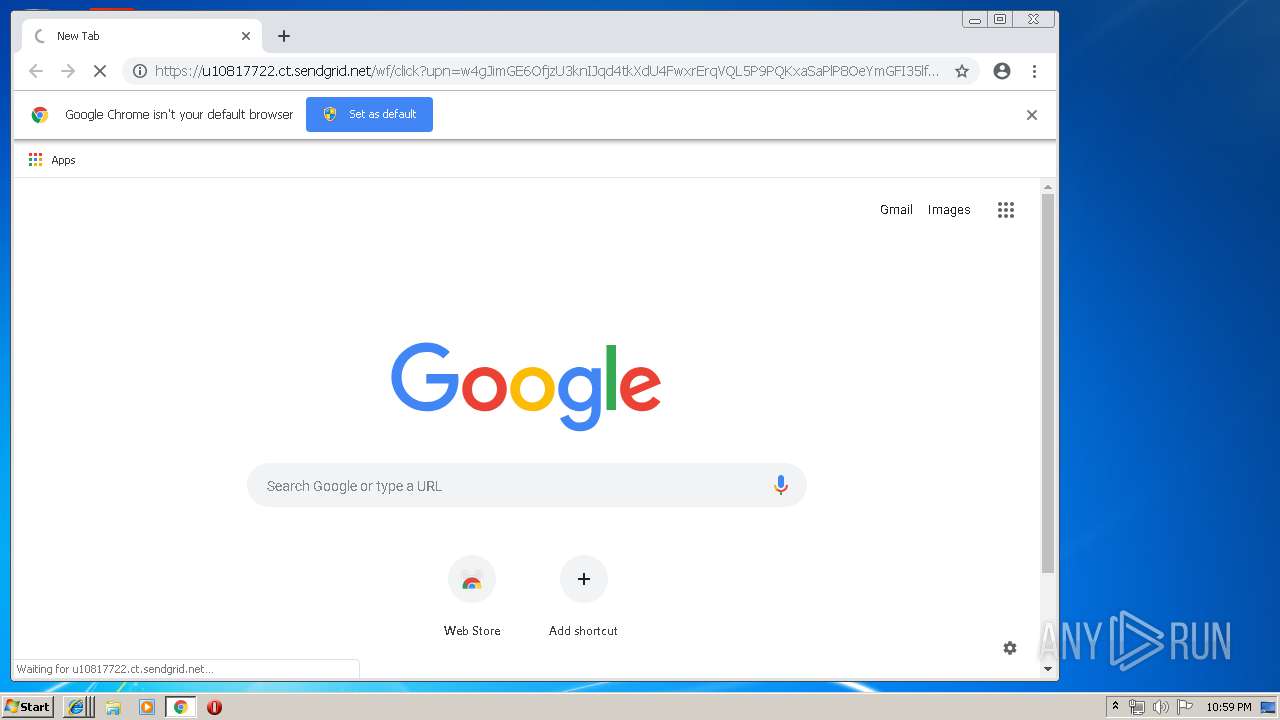
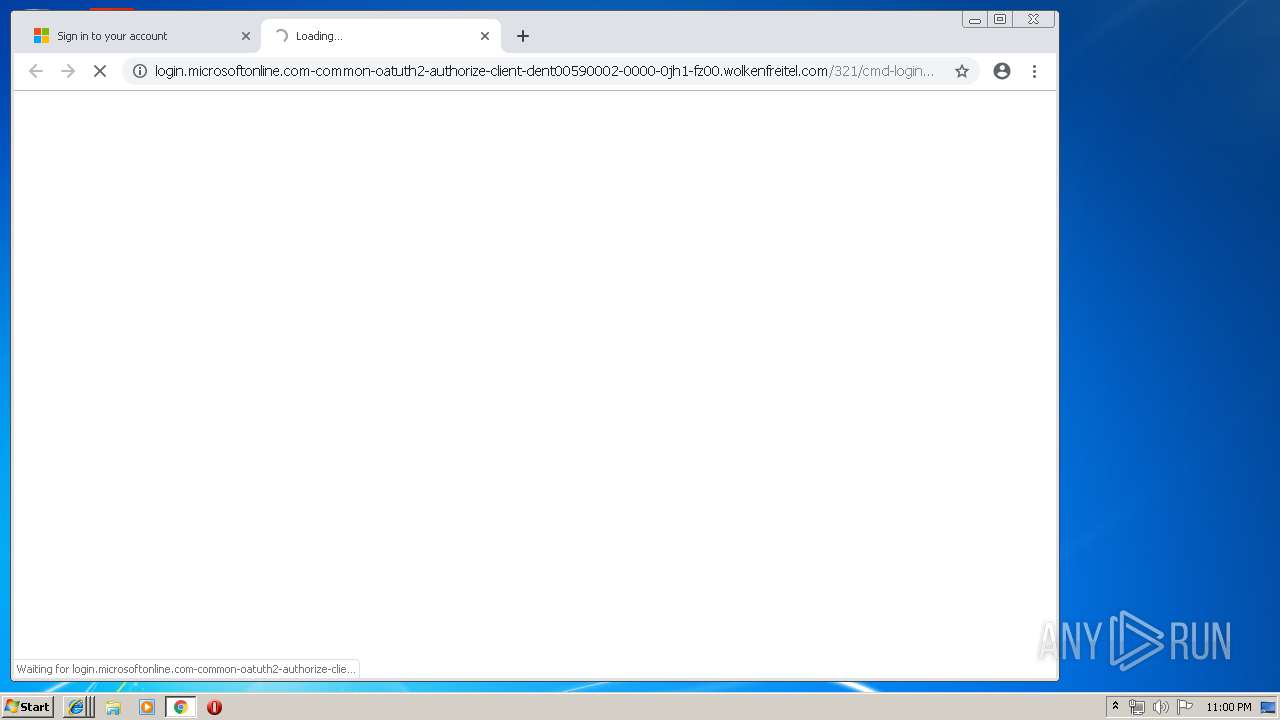
| URL: | https://u10817722.ct.sendgrid.net/wf/click?upn=w4gJimGE6OfjzU3knIJqd4tkXdU4FwxrErqVQL5P9PQKxaSaPlP8OeYmGFI35lfbd1B-2BhEBP5n9kWnk0NK5KdkLakpJl3DOpTYaBUZi7iFAVu0BiAQbWoYEtHNzyIuh-2FItM3QSUG8Bx0NxmvbGcTNQgrY690OJmYc9mTyDexi-2B5gYvw6o2GuPKemhk8Ttf0uvnqt5IZSizMcGFXMNSGaMj-2BsdLfRx1G9Ma-2BGim9BQYM-3D_RponfwD6SWCG-2FiVEIcoB4HjTrvP54Omdf-2BKfk78FDiHM-2FU5qTL5U-2Bj-2BVKVrZkbf97zT4H8YorIdHL92FTBuuMdqmMLMnGCwT-2FhoZGAhJdFKu-2FeBfw3Jrv3OInZiAU2SB5MIpmZtIY2KVvPL-2F-2F1Is6ScjD2NBgf7obWhWdTgeB2Ks8WhVZBUV8edUub4F-2BLyN99eIh89pScFUfBL-2BOffoeiuNI0WAtVKfZzJL0eieKSY-3D |
| Full analysis: | https://app.any.run/tasks/10c0af06-cb55-47f3-8384-8cb325160e91 |
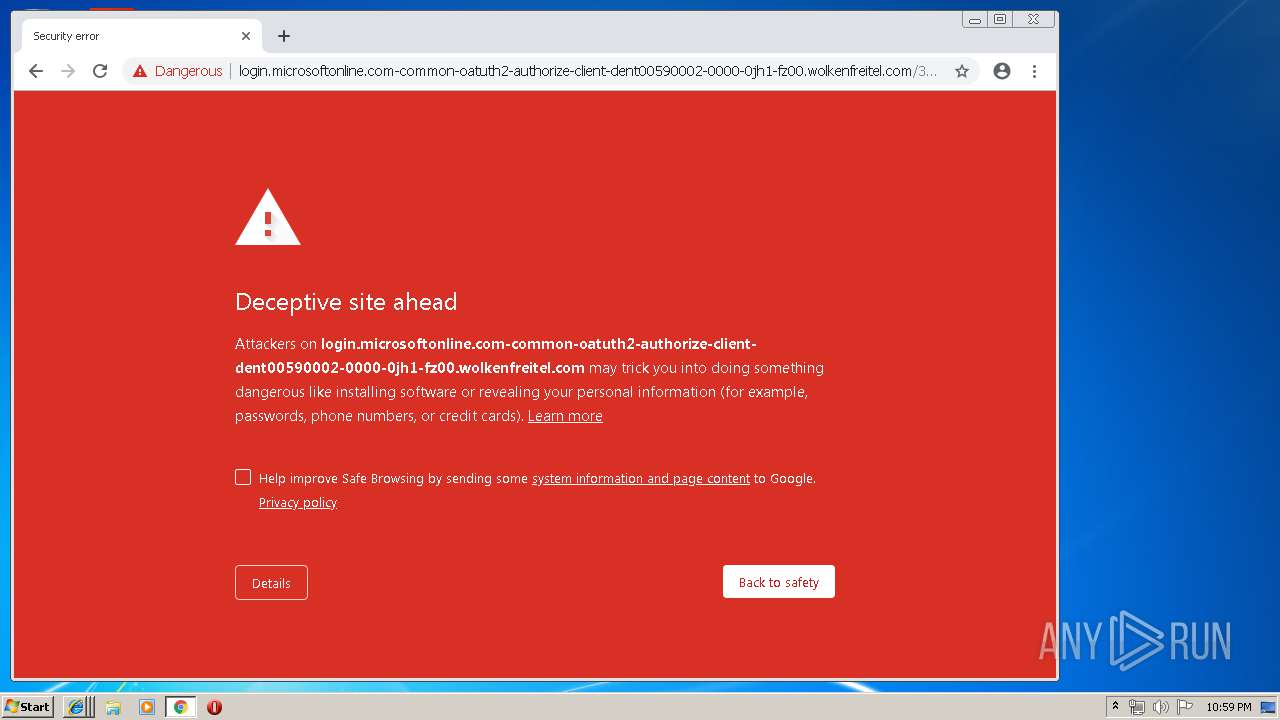
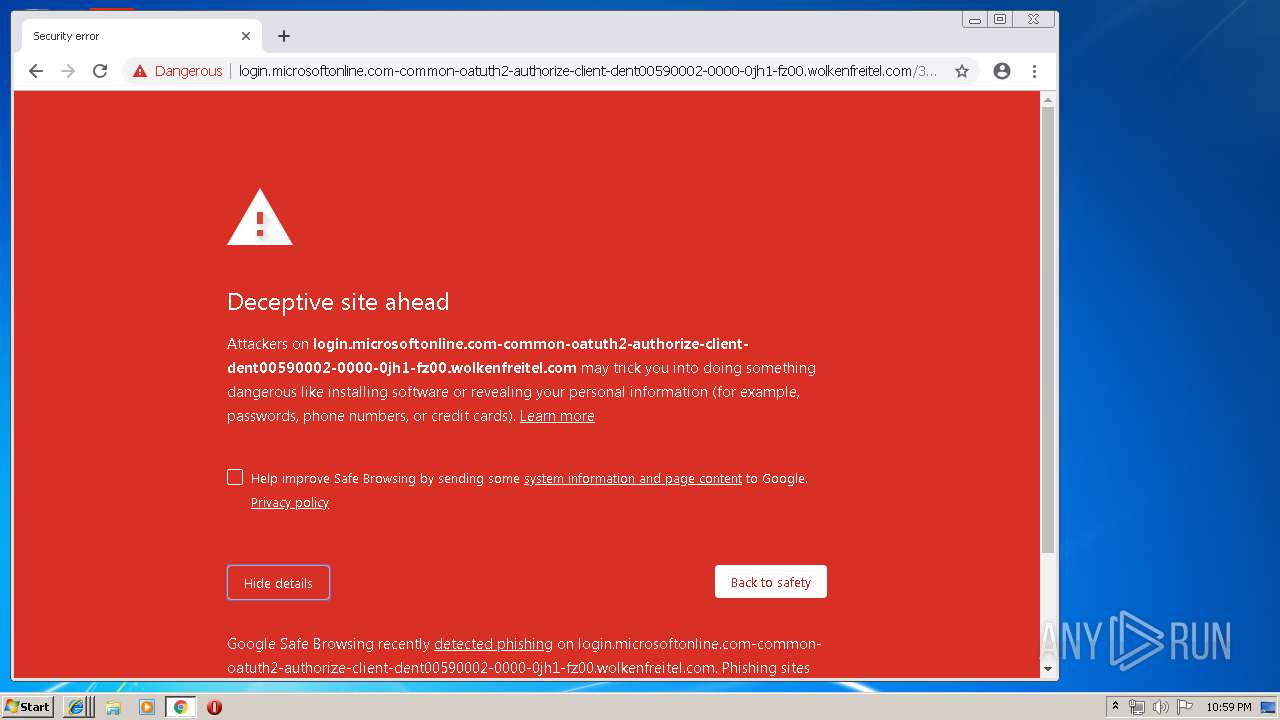
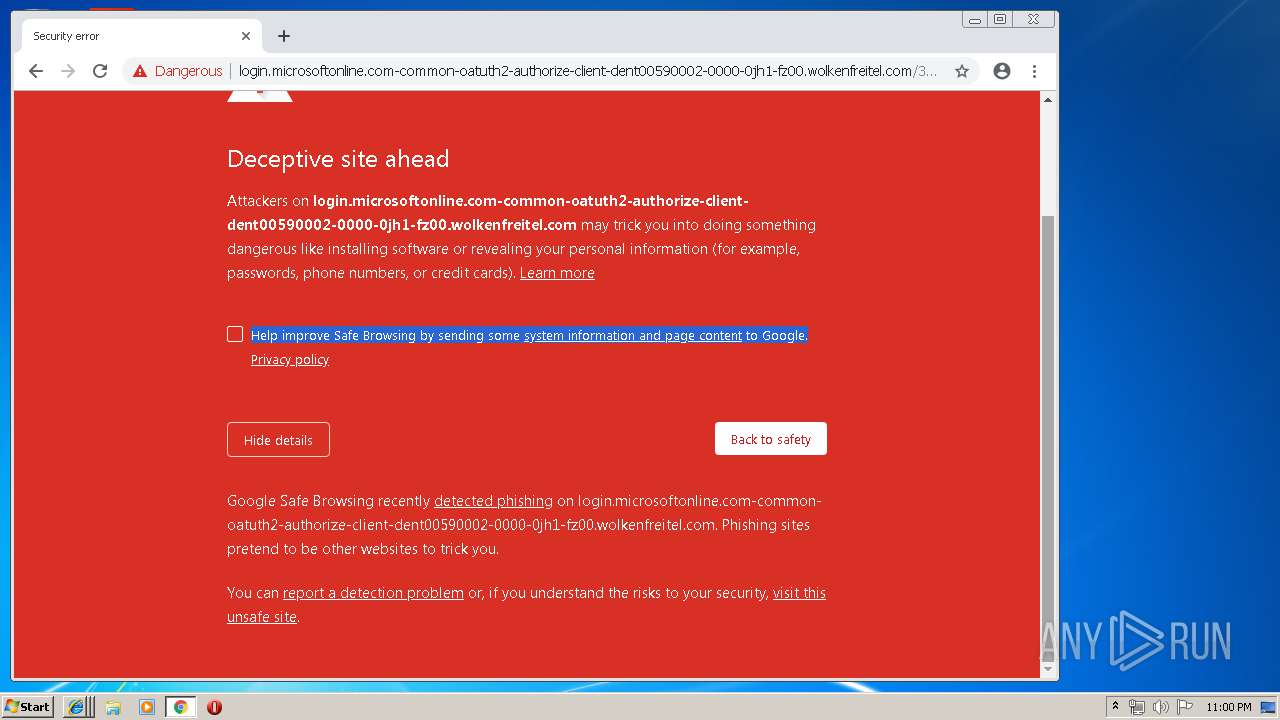
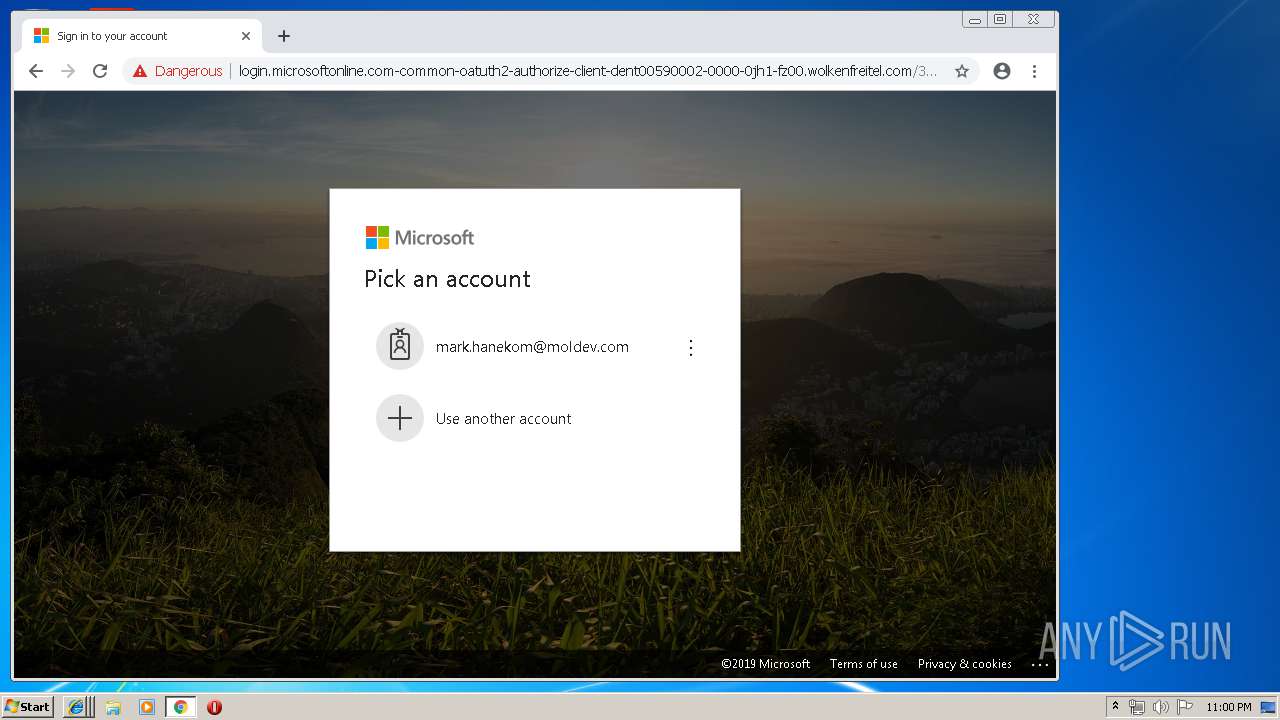
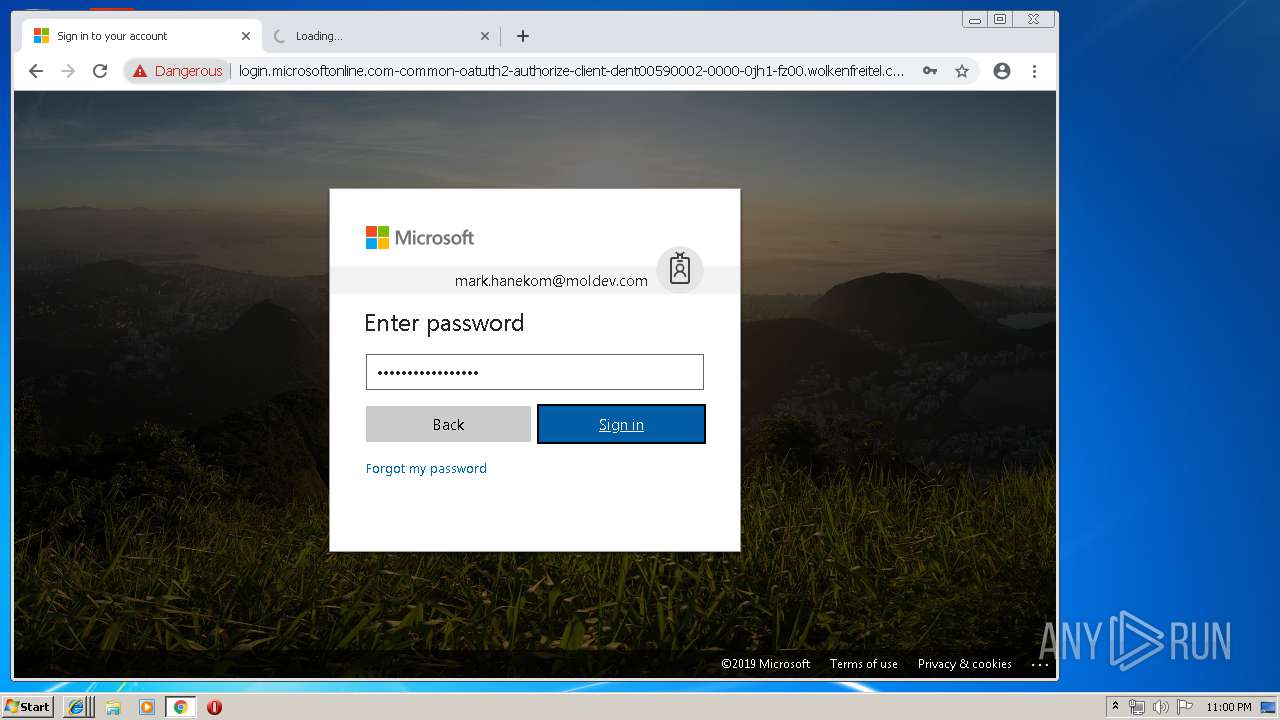
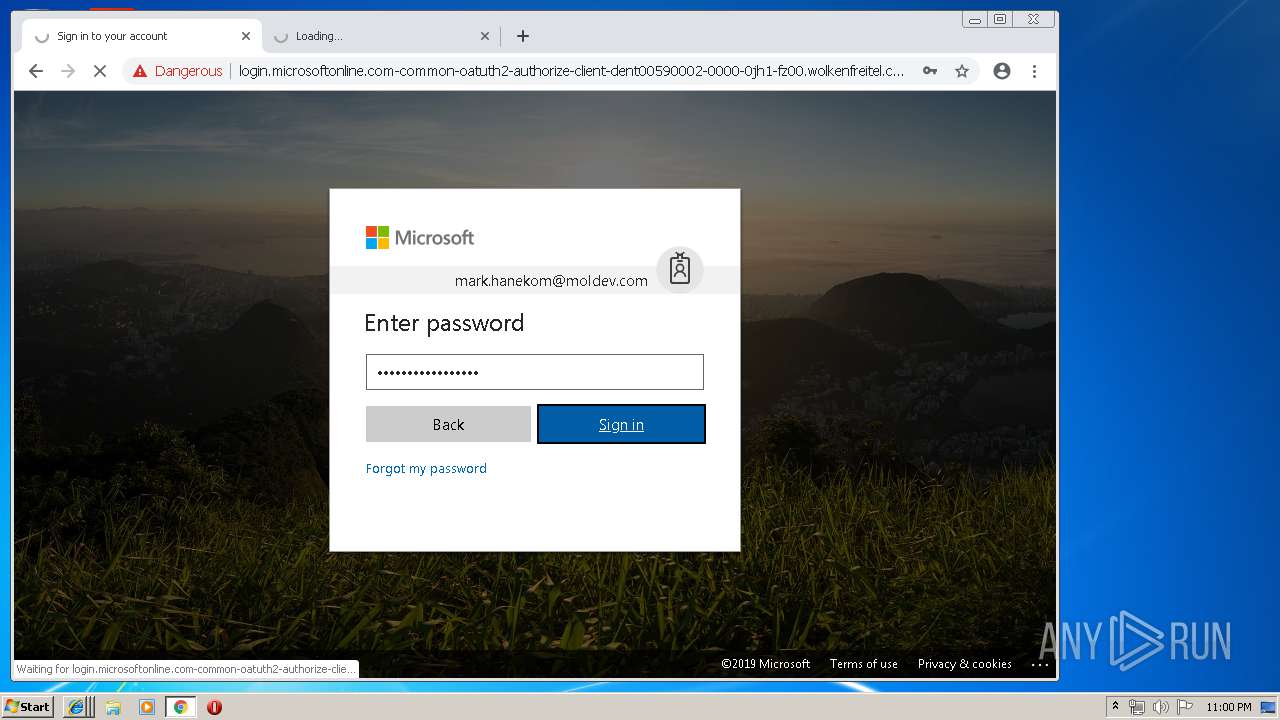
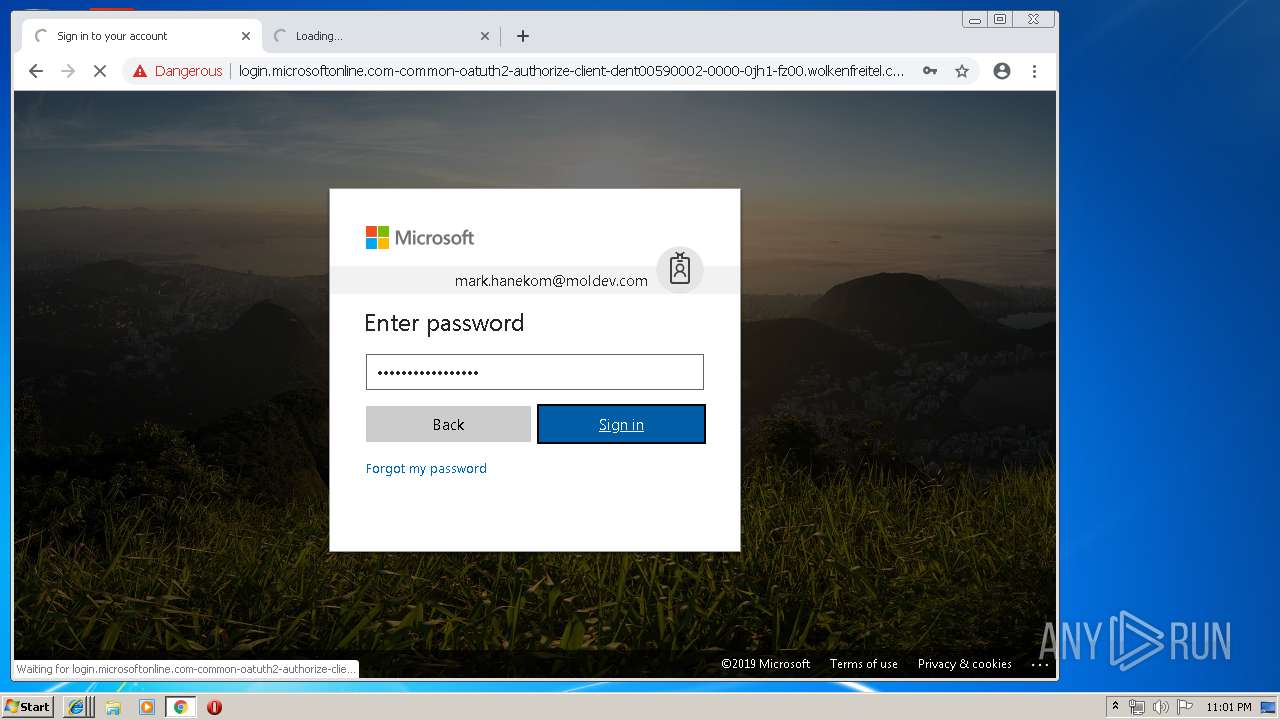
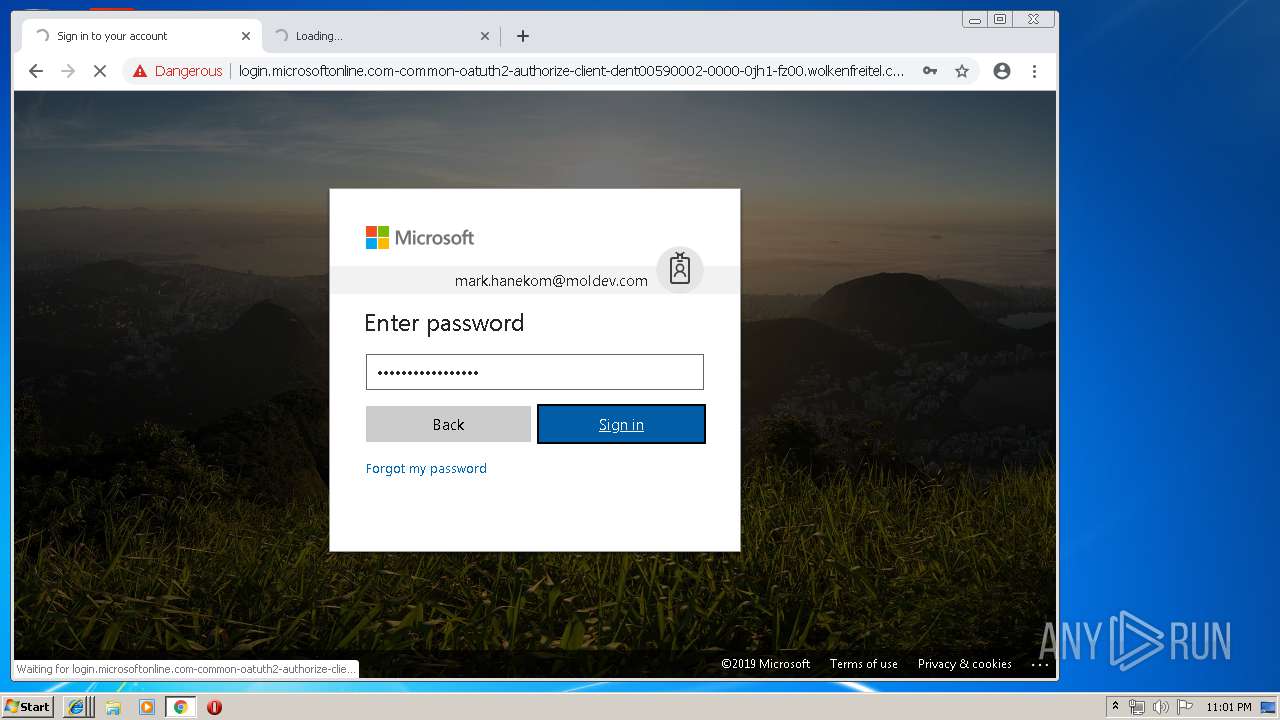
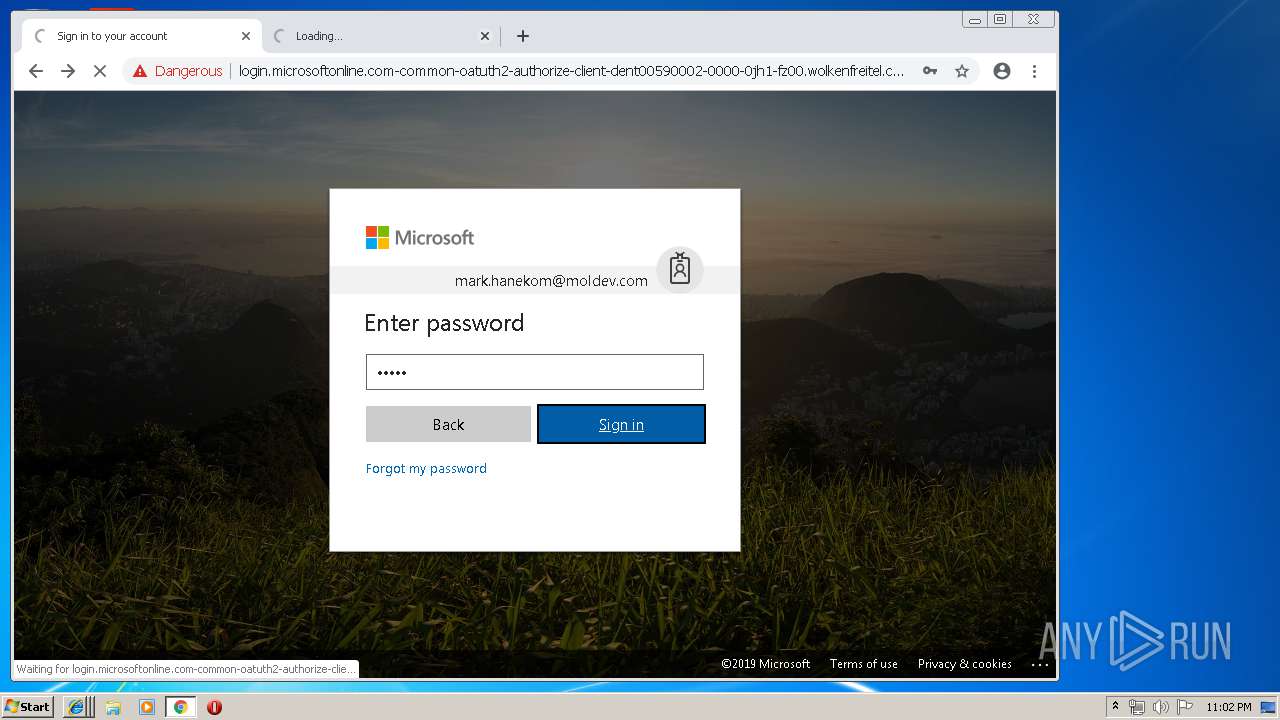
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2019, 21:57:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FC365A8BA05195EBDC54094A0A140D33 |
| SHA1: | A00EEB0FBB66139EE3E9E70D59D91D3B8EFD659D |
| SHA256: | DED556305E243182C79FFDF3D22B45297C82B8C03957F87317C1D33A38F38C43 |
| SSDEEP: | 12:2mDSspLW2EDXDXNXp62hMsql8JoZ2pliV6dpMy2j1phvhCMoGMyA:20hLxQD9p62hBGs4OliQdKyc1/8GdA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2760)
INFO
Application launched itself
- iexplore.exe (PID: 2888)
- RdrCEF.exe (PID: 1076)
- chrome.exe (PID: 2760)
- AcroRd32.exe (PID: 2376)
Changes internet zones settings
- iexplore.exe (PID: 2888)
Manual execution by user
- chrome.exe (PID: 2760)
Reads settings of System Certificates
- chrome.exe (PID: 2760)
- iexplore.exe (PID: 2888)
Creates files in the user directory
- iexplore.exe (PID: 3652)
- iexplore.exe (PID: 3884)
- iexplore.exe (PID: 2224)
Reads internet explorer settings
- iexplore.exe (PID: 3652)
- iexplore.exe (PID: 2224)
- iexplore.exe (PID: 3884)
Reads Internet Cache Settings
- iexplore.exe (PID: 3652)
- iexplore.exe (PID: 3884)
- iexplore.exe (PID: 2224)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2888)
Changes settings of System certificates
- iexplore.exe (PID: 2888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
40
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,2401568916709382391,13182061299520279265,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=587104504523857428 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=587104504523857428 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,2401568916709382391,13182061299520279265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14845478252667974322 --mojo-platform-channel-handle=4196 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,2401568916709382391,13182061299520279265,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1929199584147898783 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1929199584147898783 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,2401568916709382391,13182061299520279265,131072 --enable-features=PasswordImport --service-pipe-token=8623460266936936742 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8623460266936936742 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /o /eo /l /b /id 3652 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,2401568916709382391,13182061299520279265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1981162813299333824 --mojo-platform-channel-handle=4616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,2401568916709382391,13182061299520279265,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10928181647112091032 --mojo-platform-channel-handle=2620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="1076.2.1666119087\1271606699" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,2401568916709382391,13182061299520279265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1117488447457353370 --mojo-platform-channel-handle=2104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 588
Read events
1 359
Write events
221
Delete events
8
Modification events
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {11E8D0E7-9214-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307060002001200150039002000D200 | |||
Executable files
0
Suspicious files
95
Text files
288
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\4USXVLNX\ja0tdw0pjzg7b7x6t7imtcbn[1].php | — | |
MD5:— | SHA256:— | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\4USXVLNX\ja0tdw0pjzg7b7x6t7imtcbn[1].htm | html | |
MD5:— | SHA256:— | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\9K6URZS3\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZCFTFX24\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
111
TCP/UDP connections
120
DNS requests
51
Threats
76
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
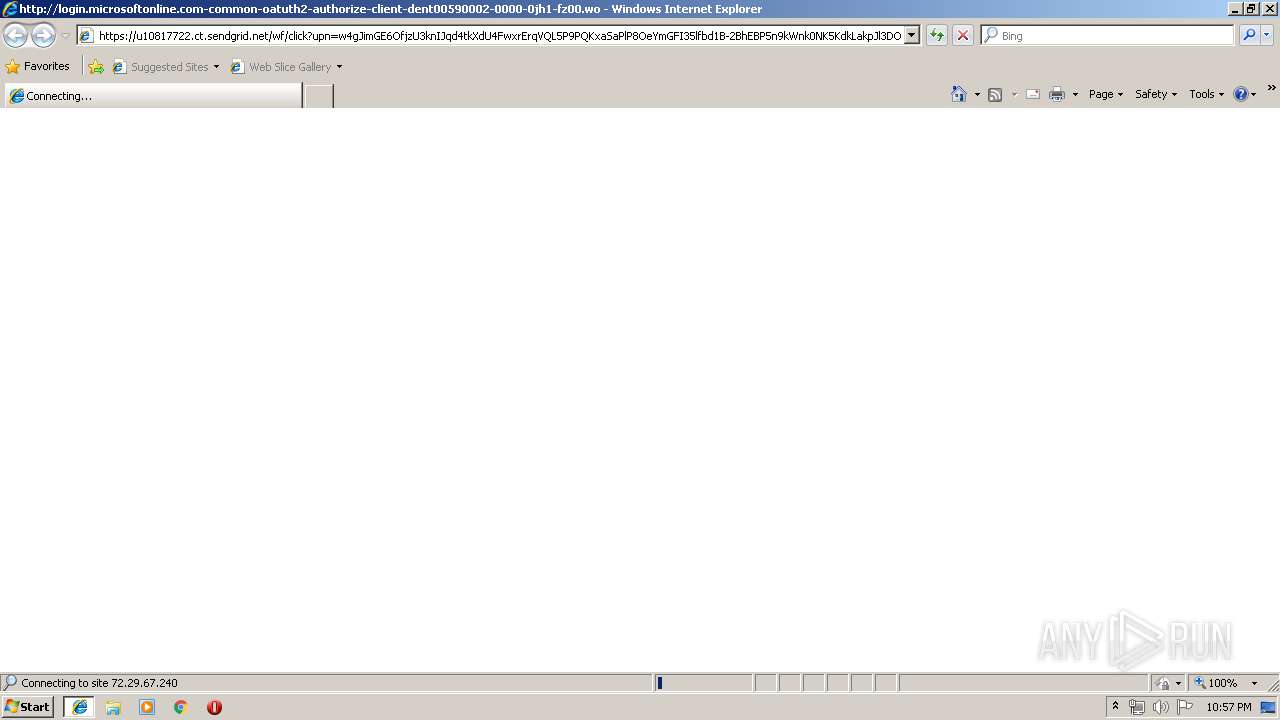
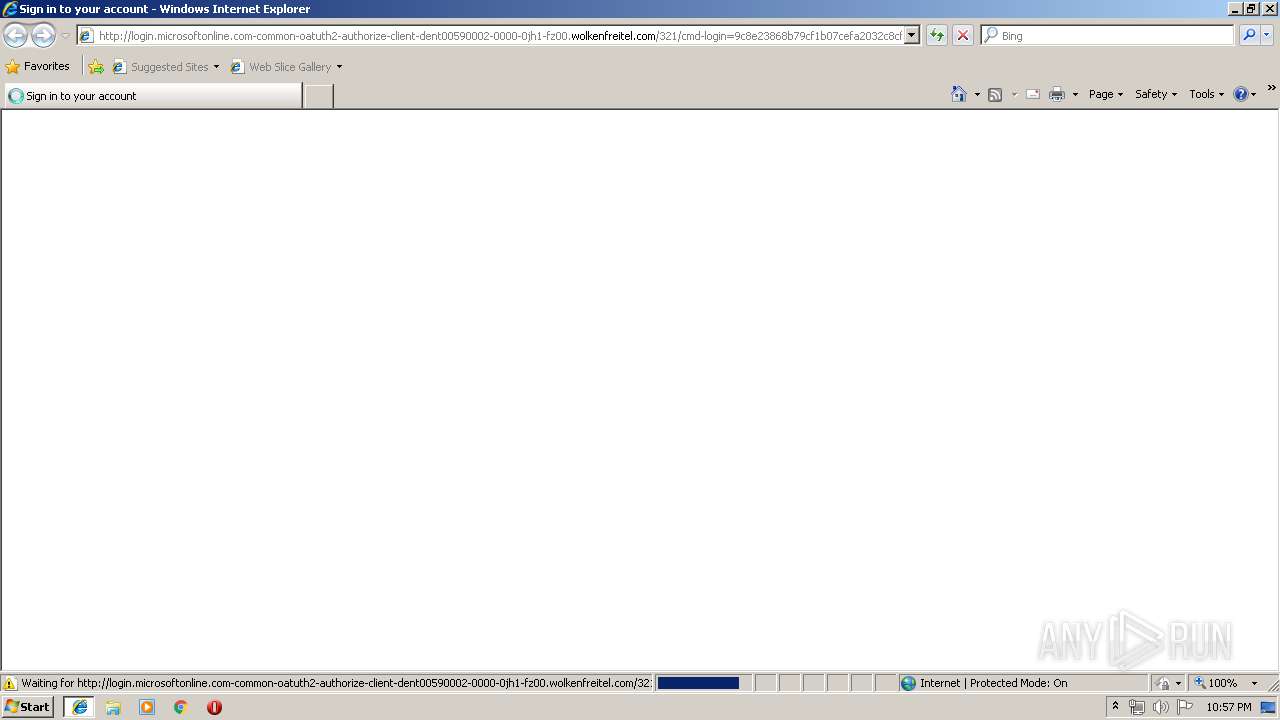
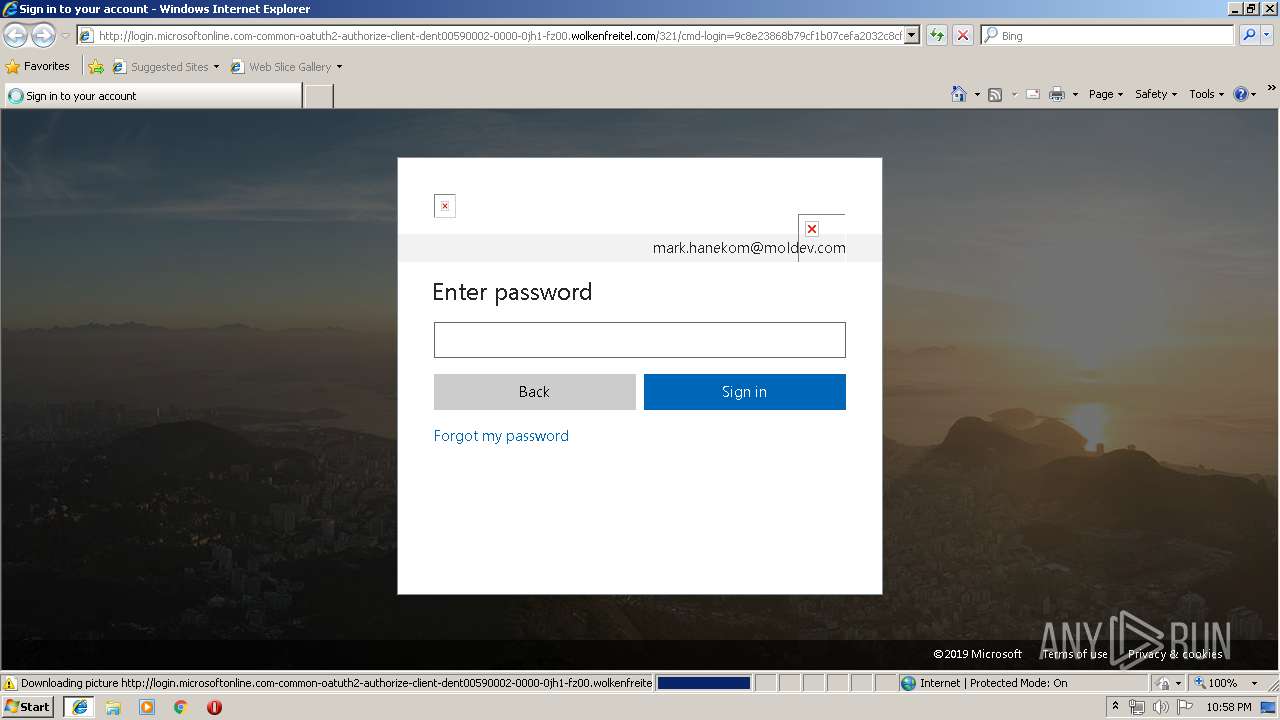
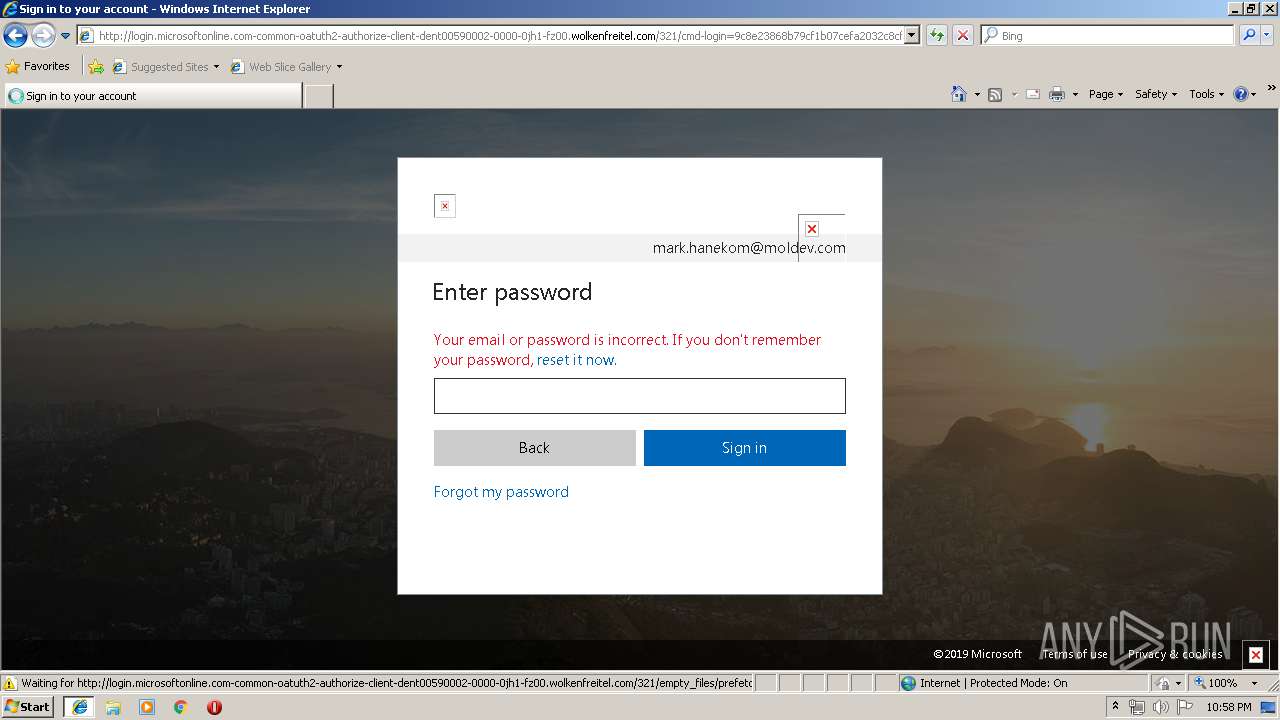
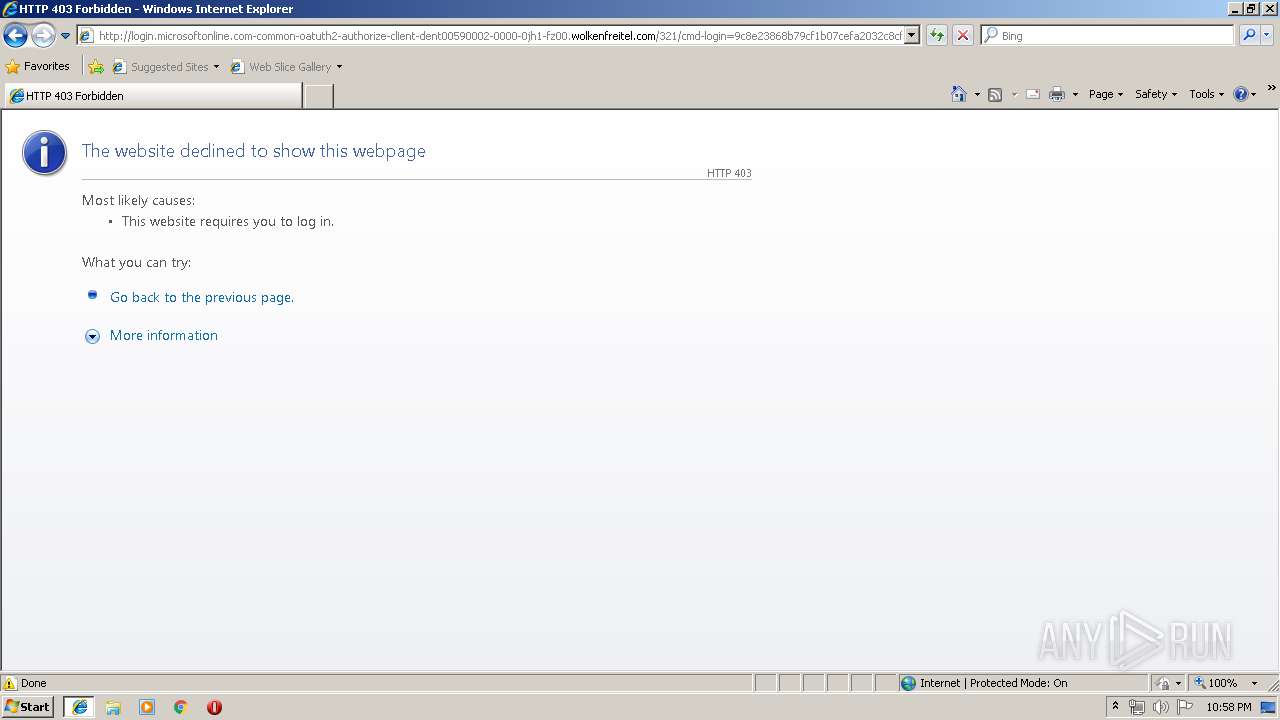
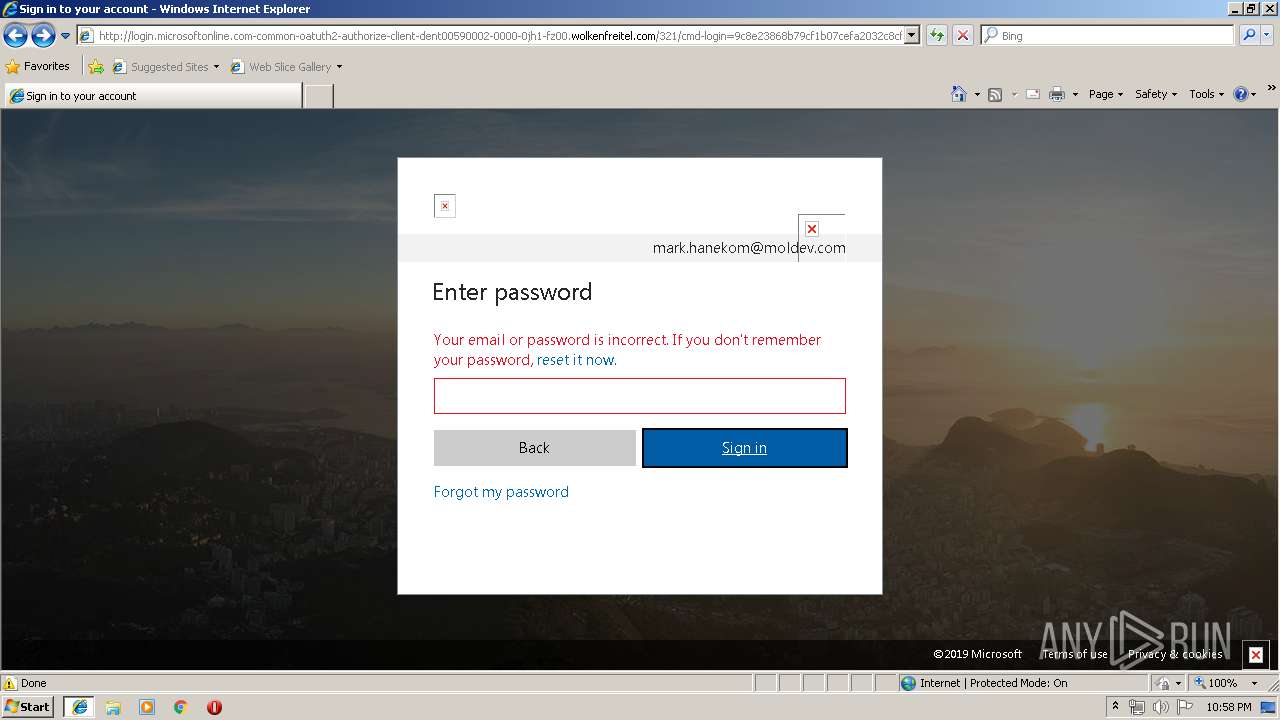
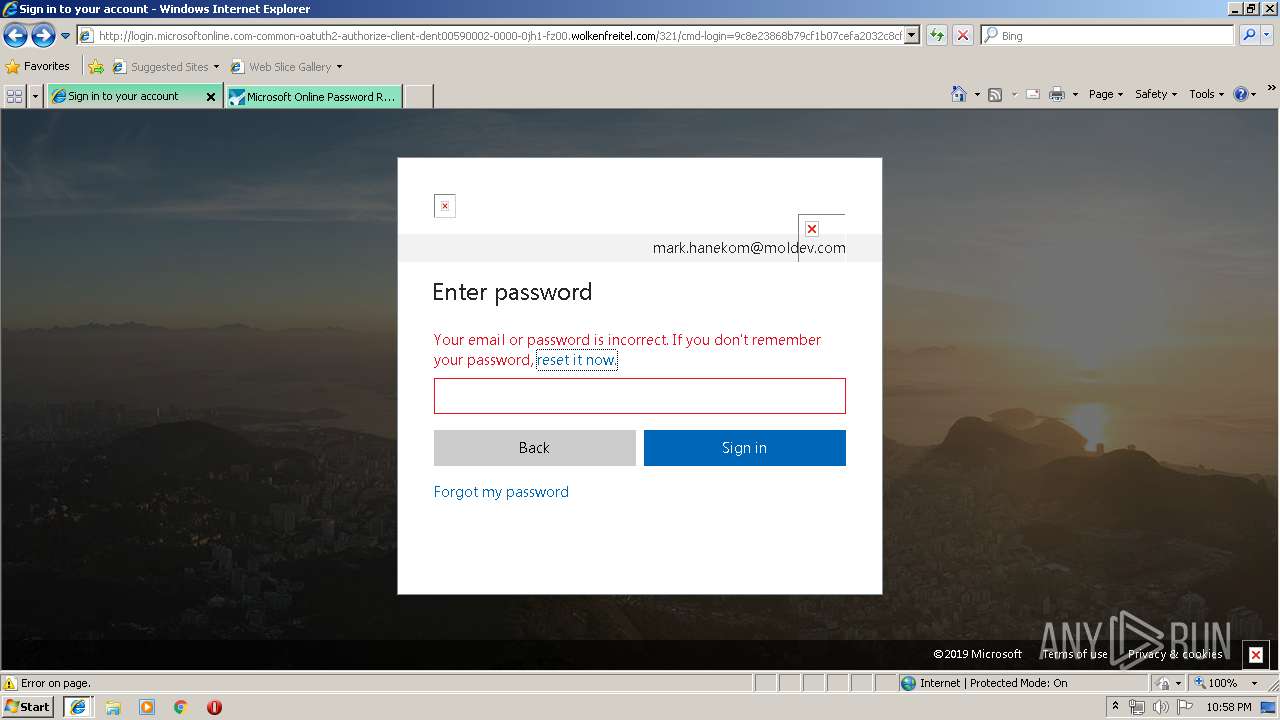
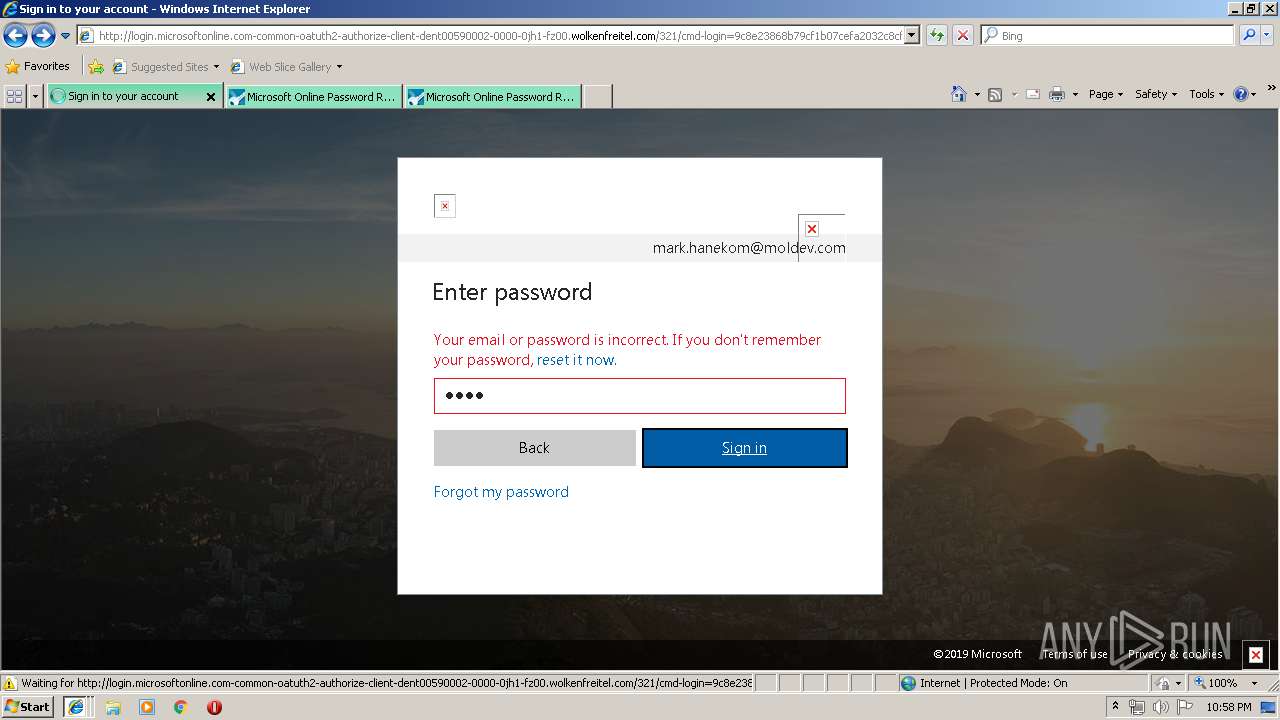
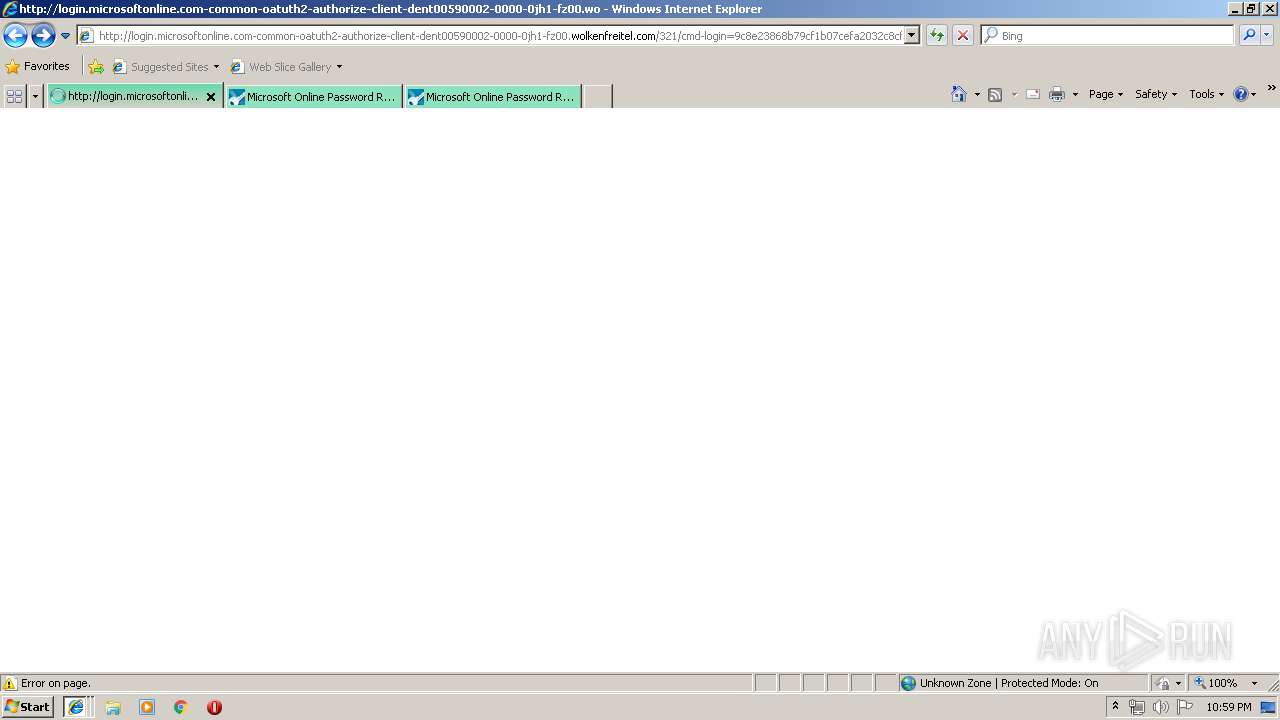
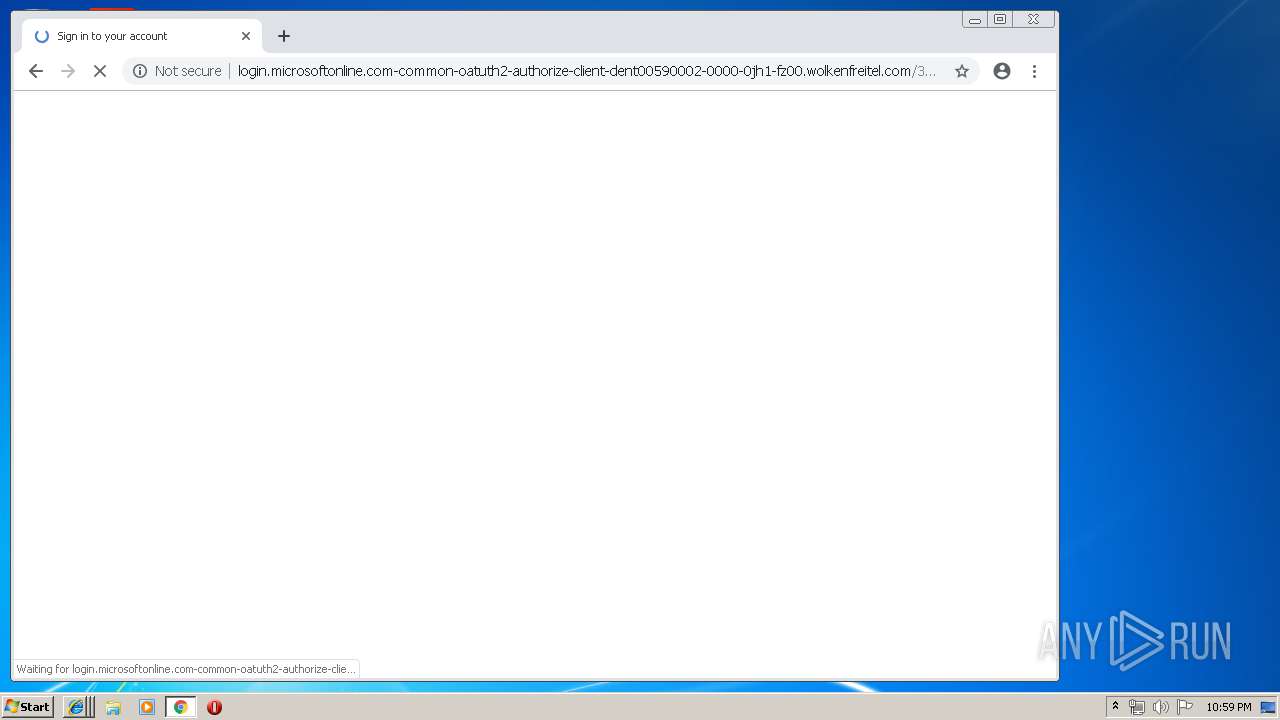
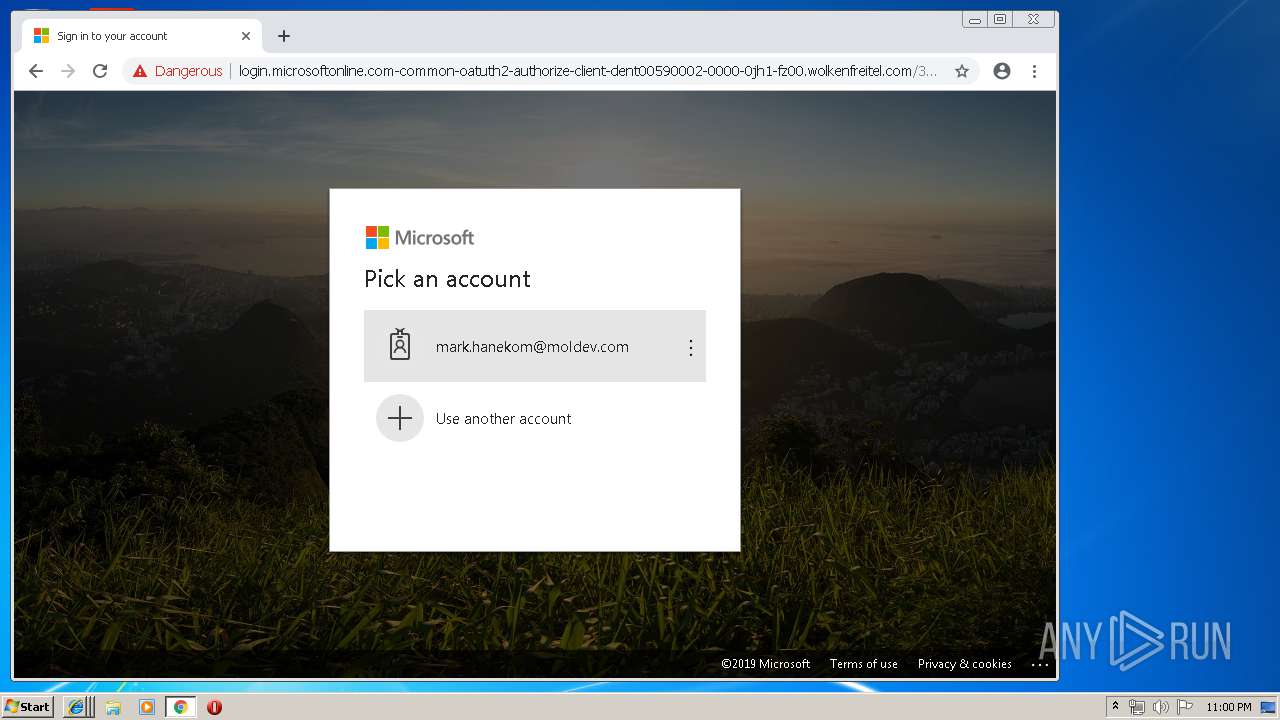
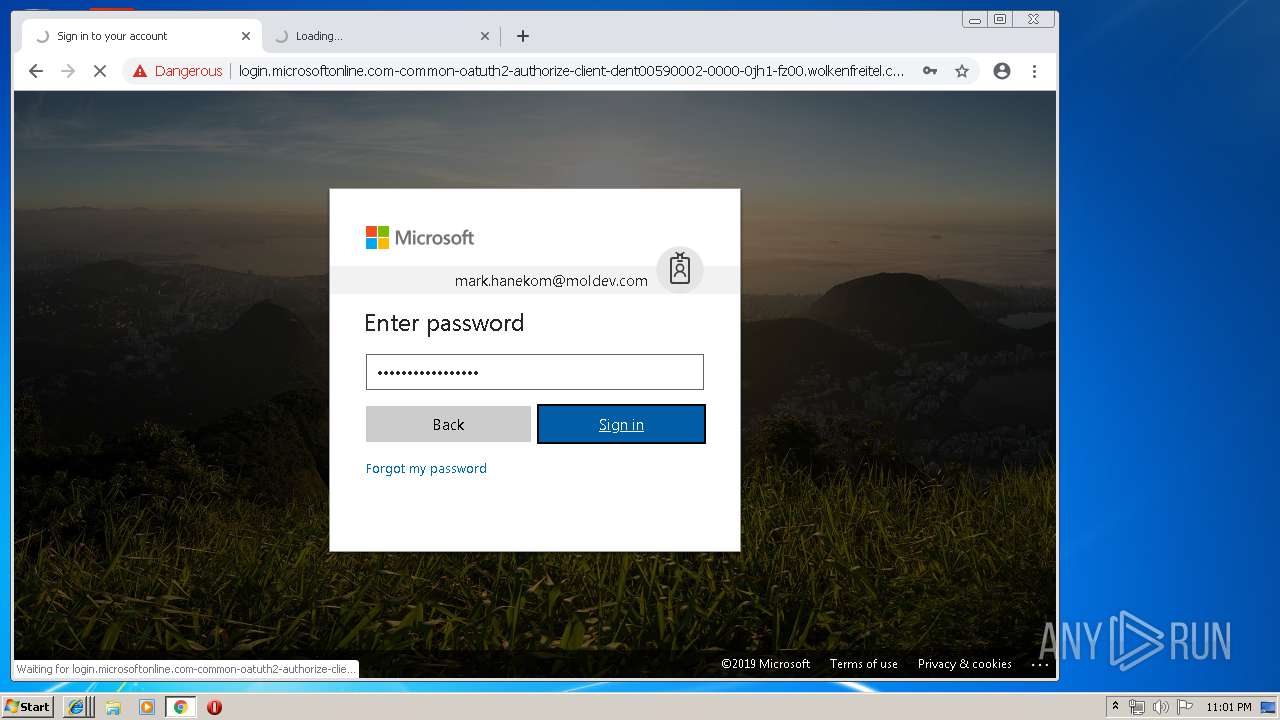
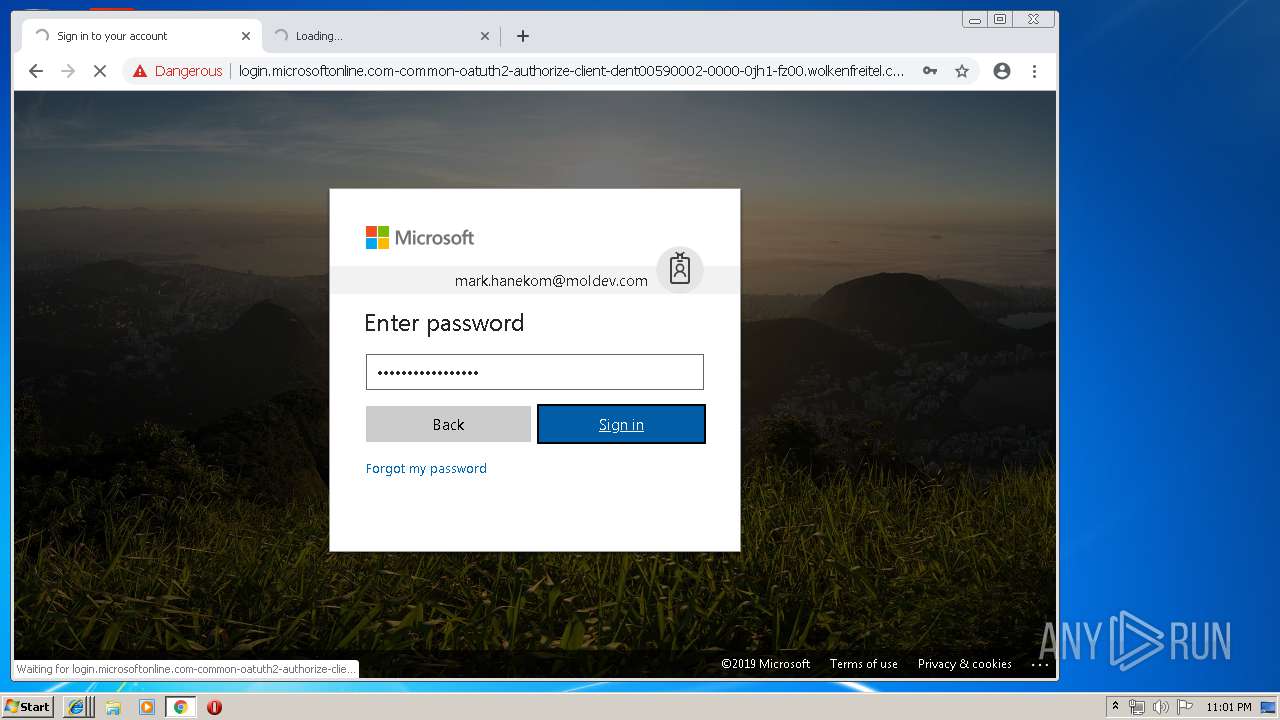
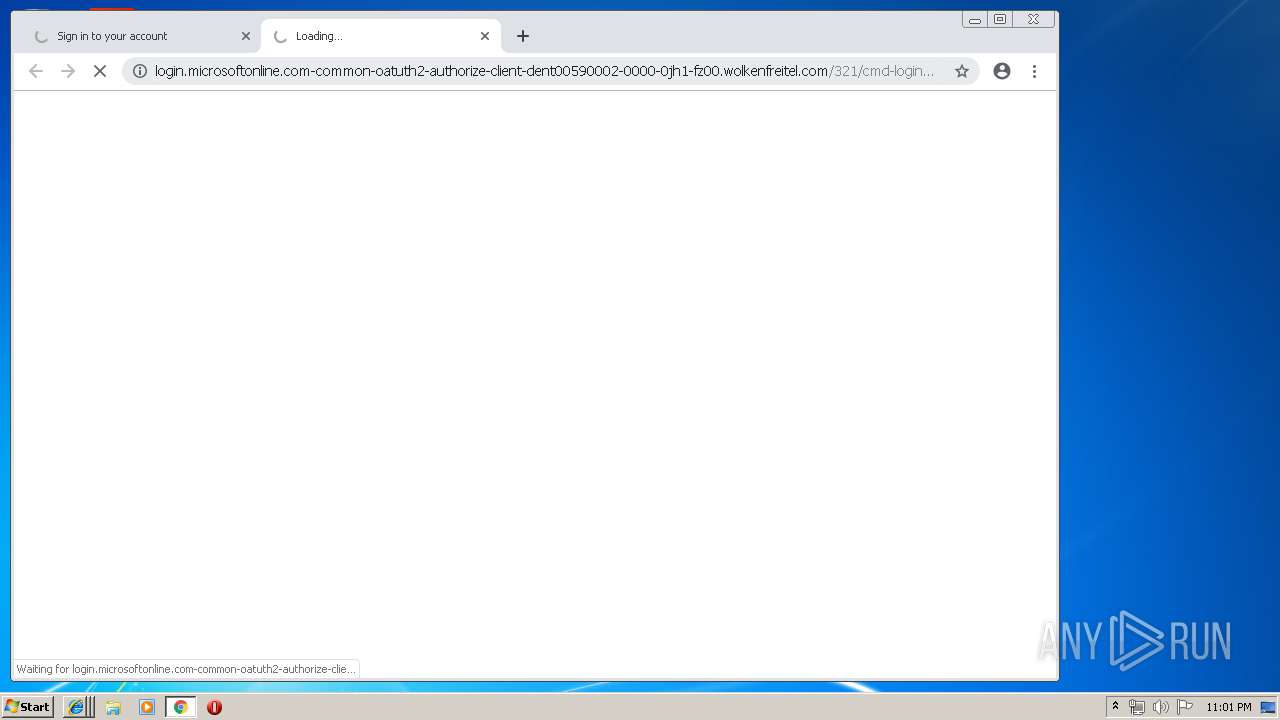
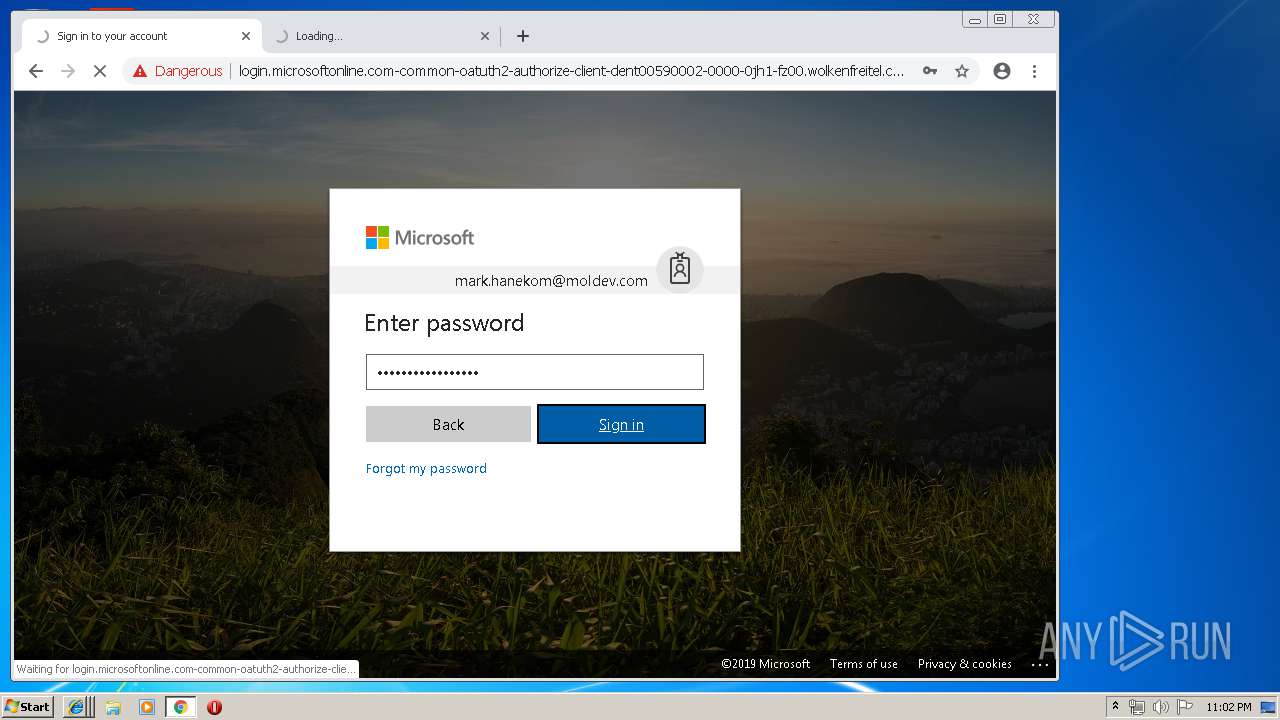
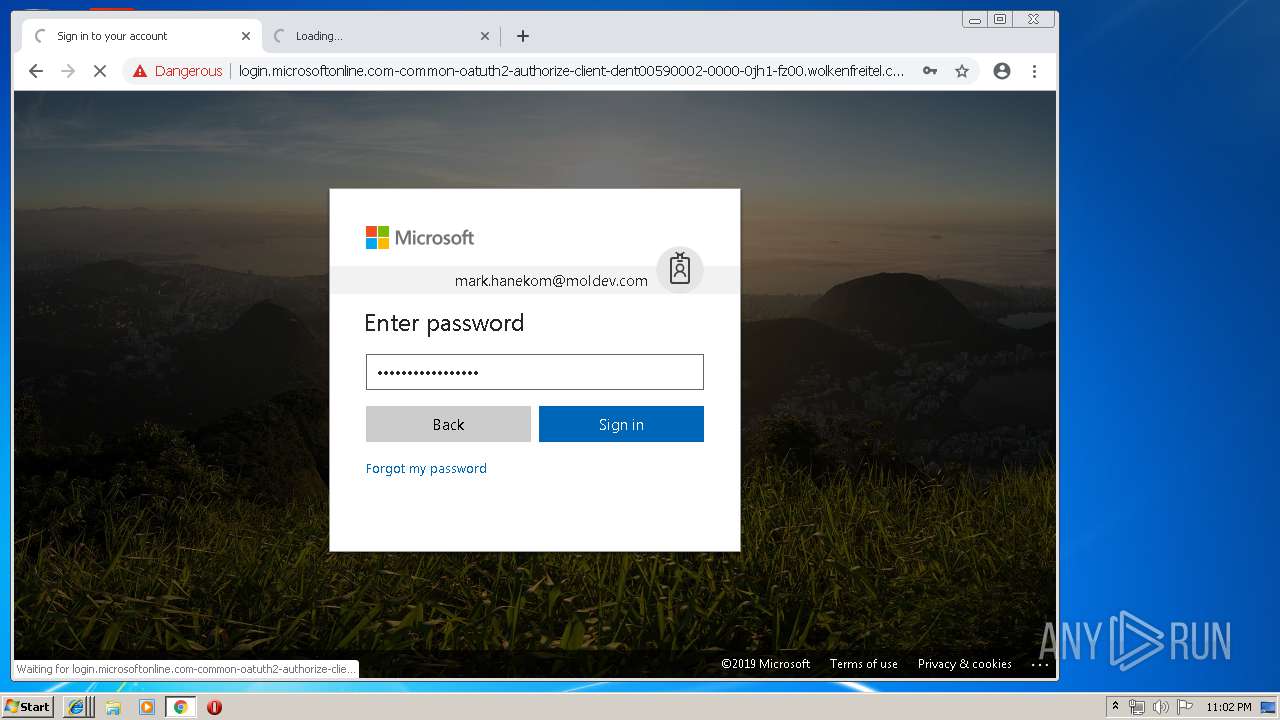
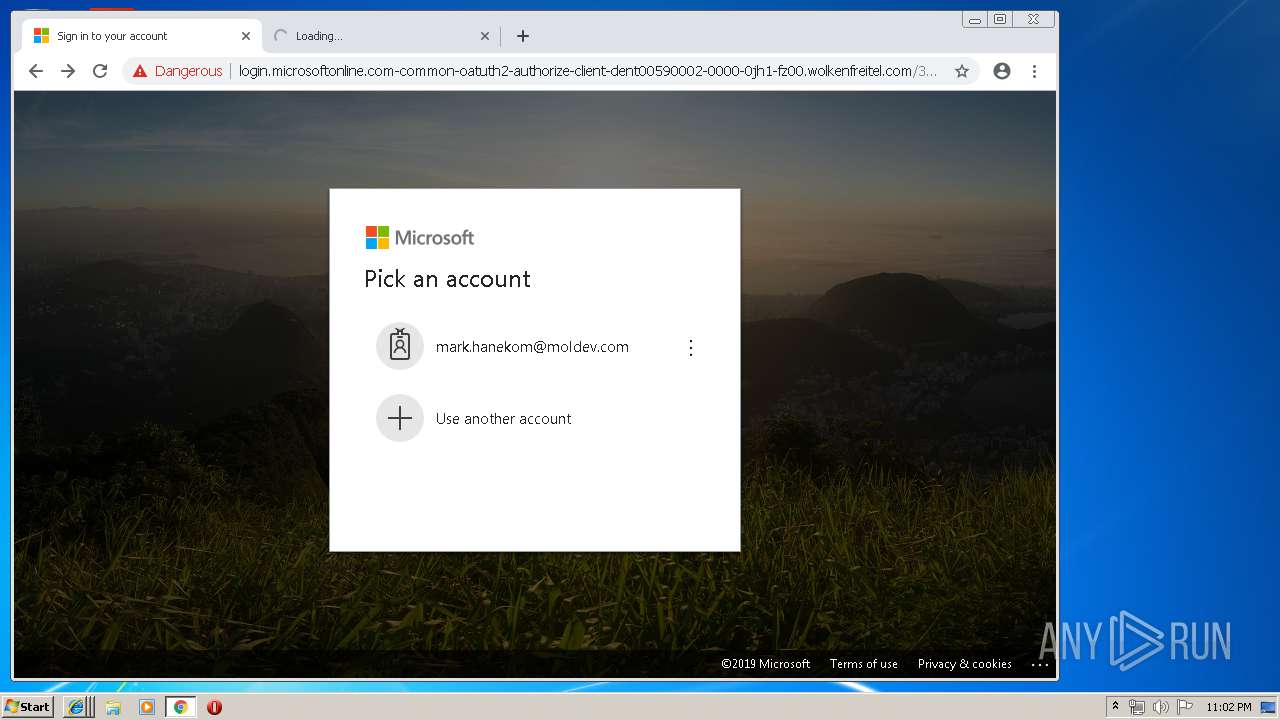
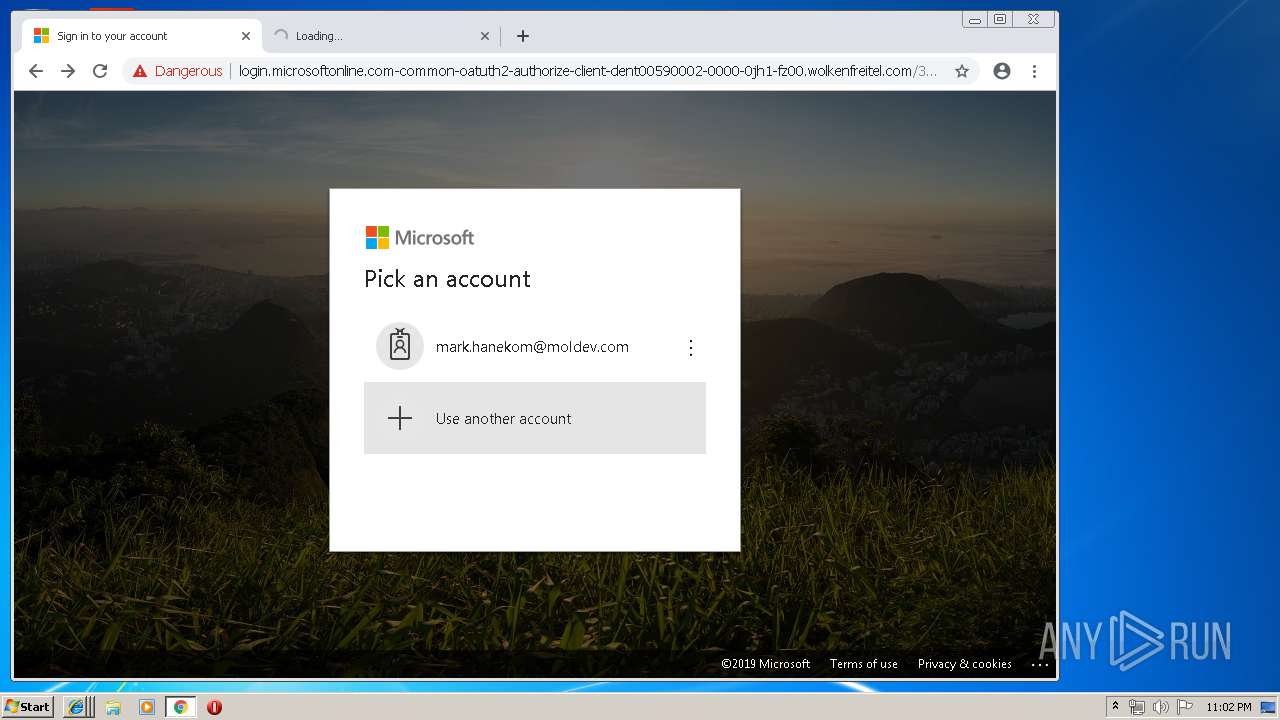
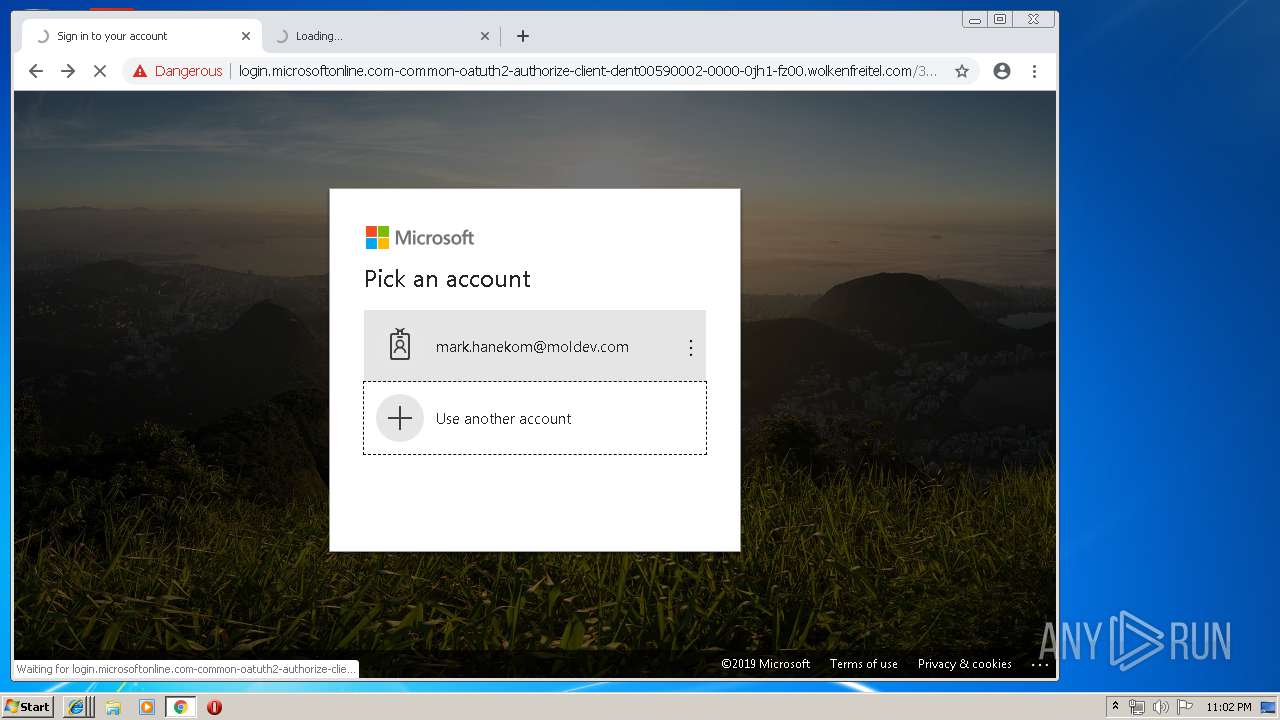
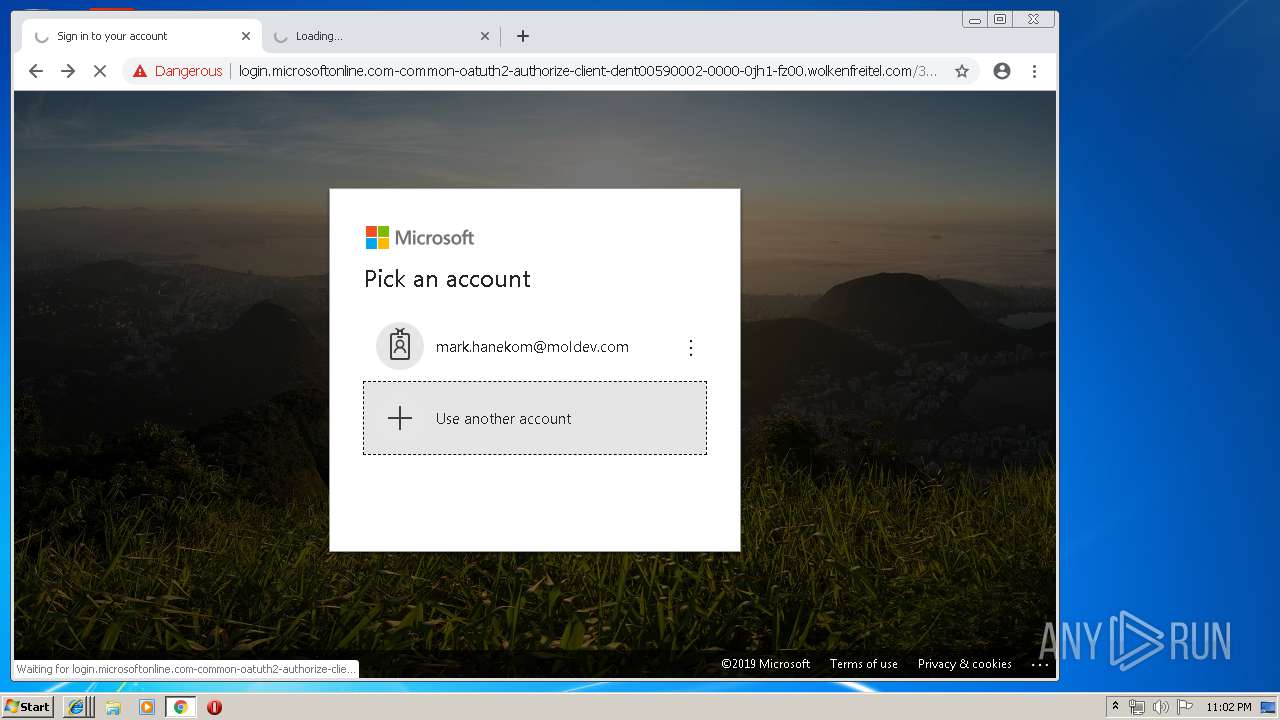
3652 | iexplore.exe | GET | — | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/prefetch.htm | US | — | — | malicious |
3652 | iexplore.exe | GET | — | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/picker_account_add.svg | US | — | — | malicious |
3652 | iexplore.exe | GET | — | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/ellipsis_white.svg | US | — | — | malicious |
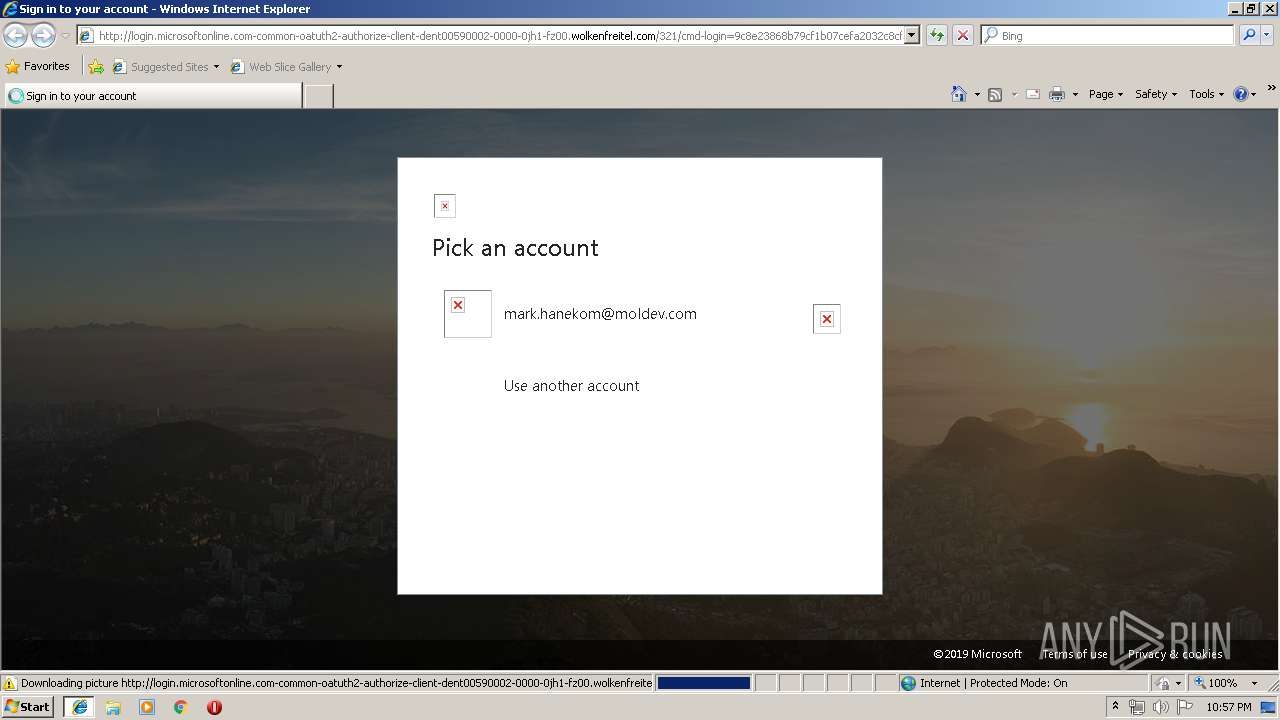
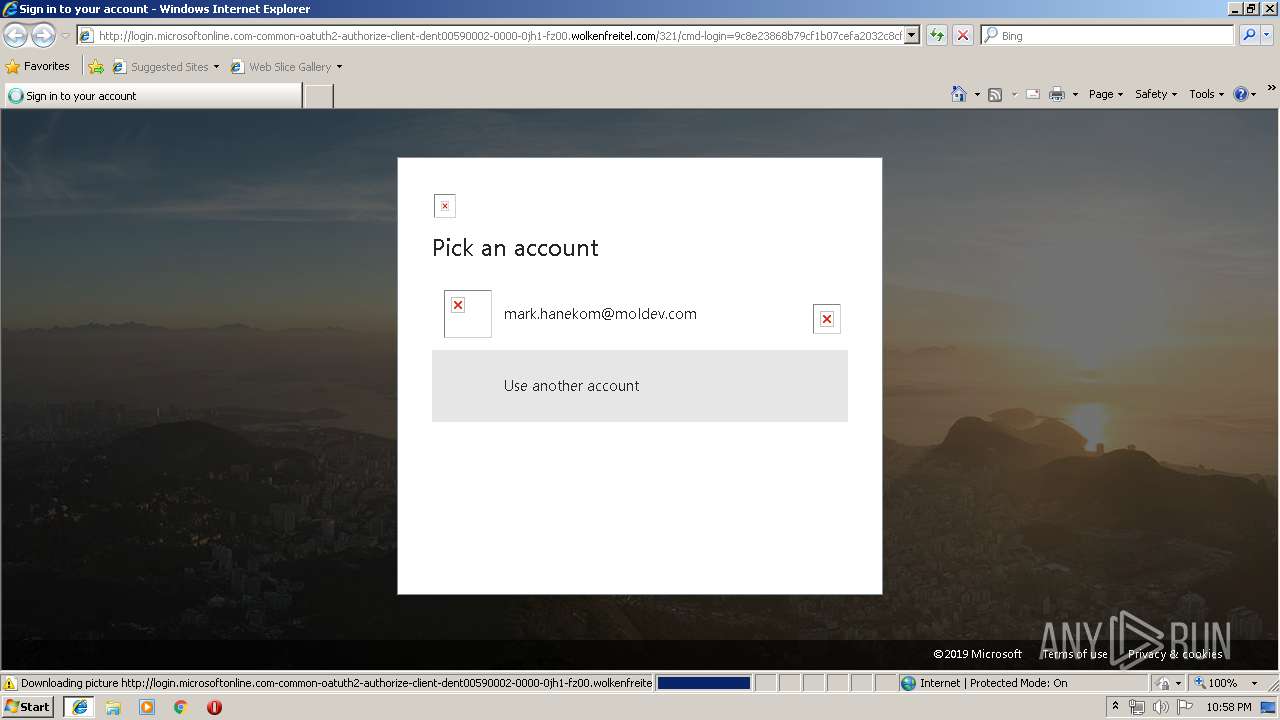
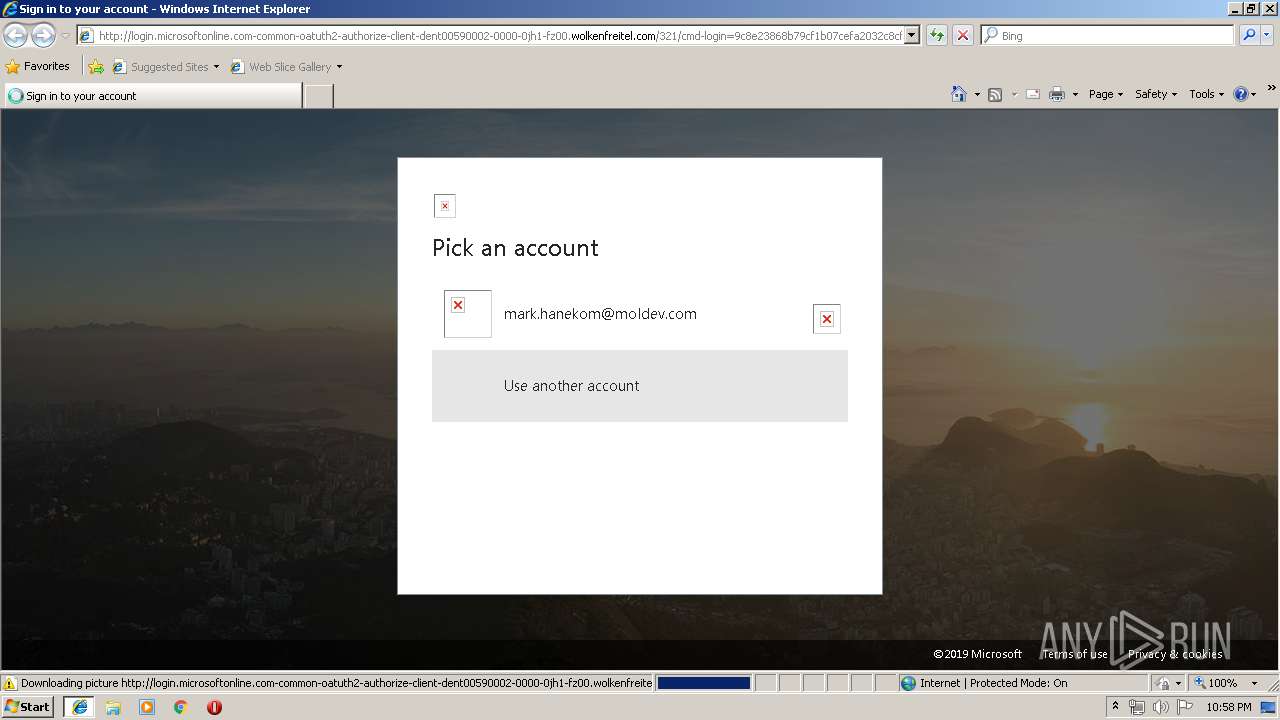
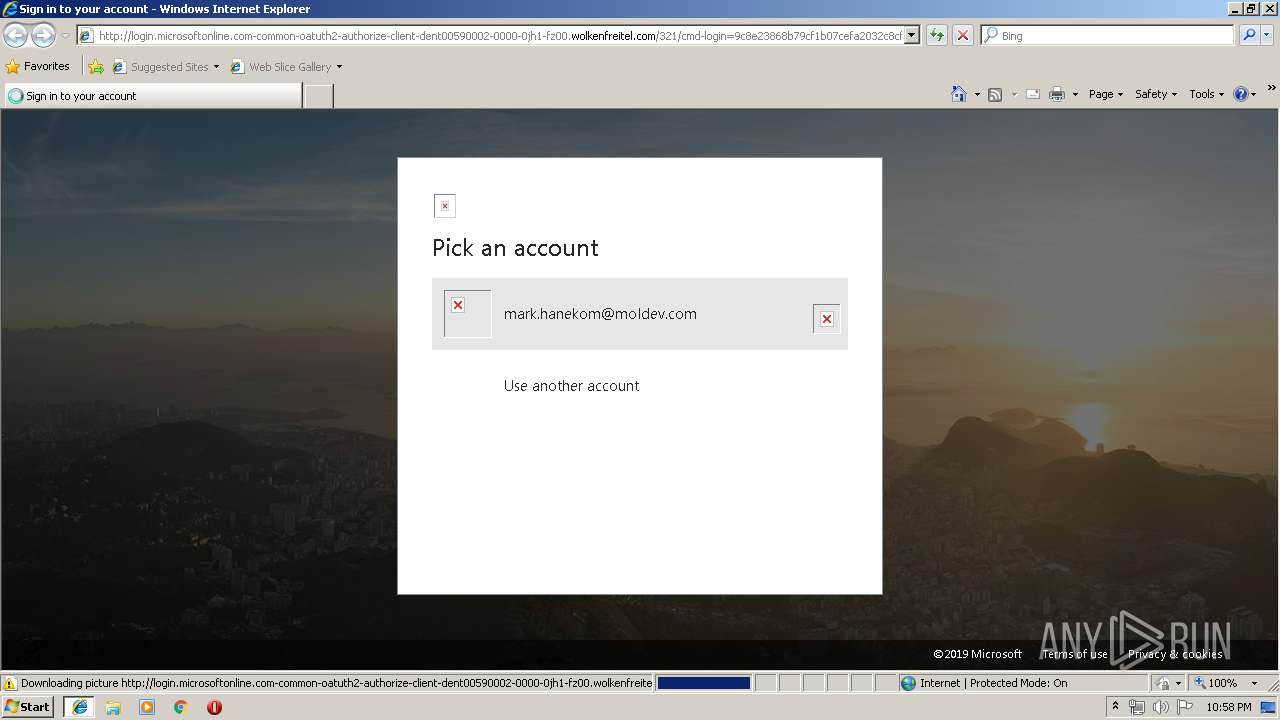
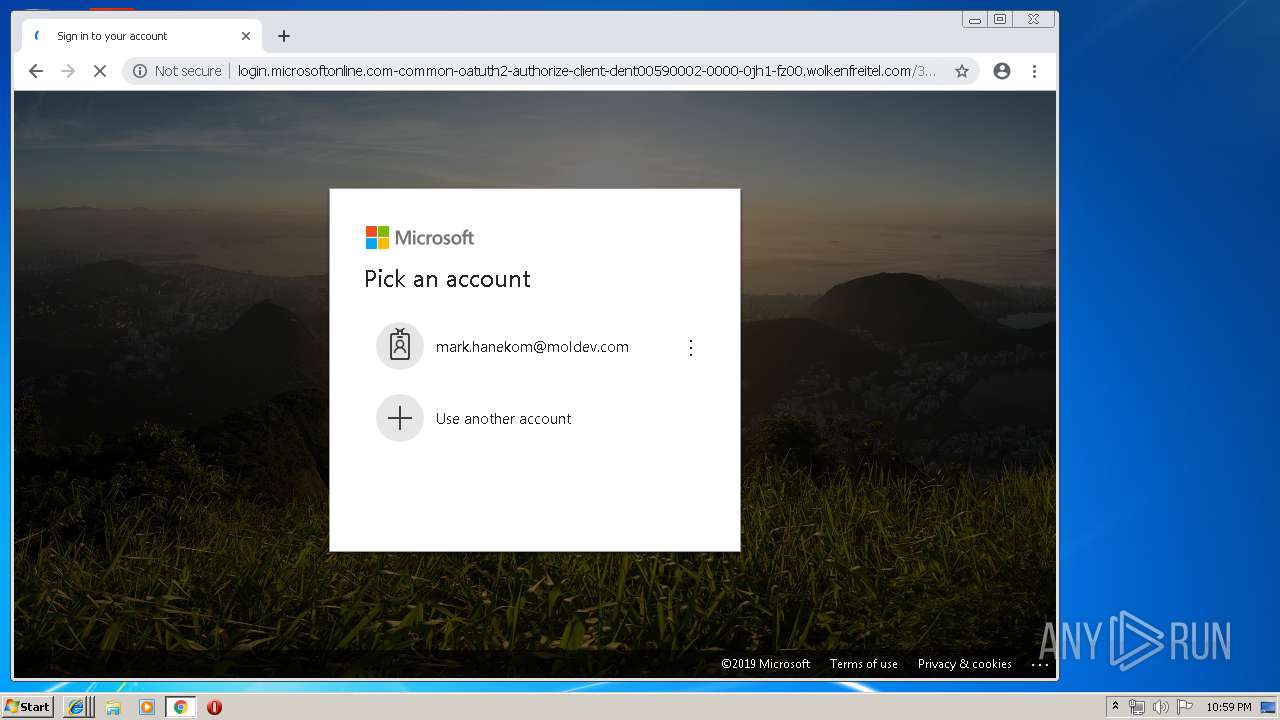
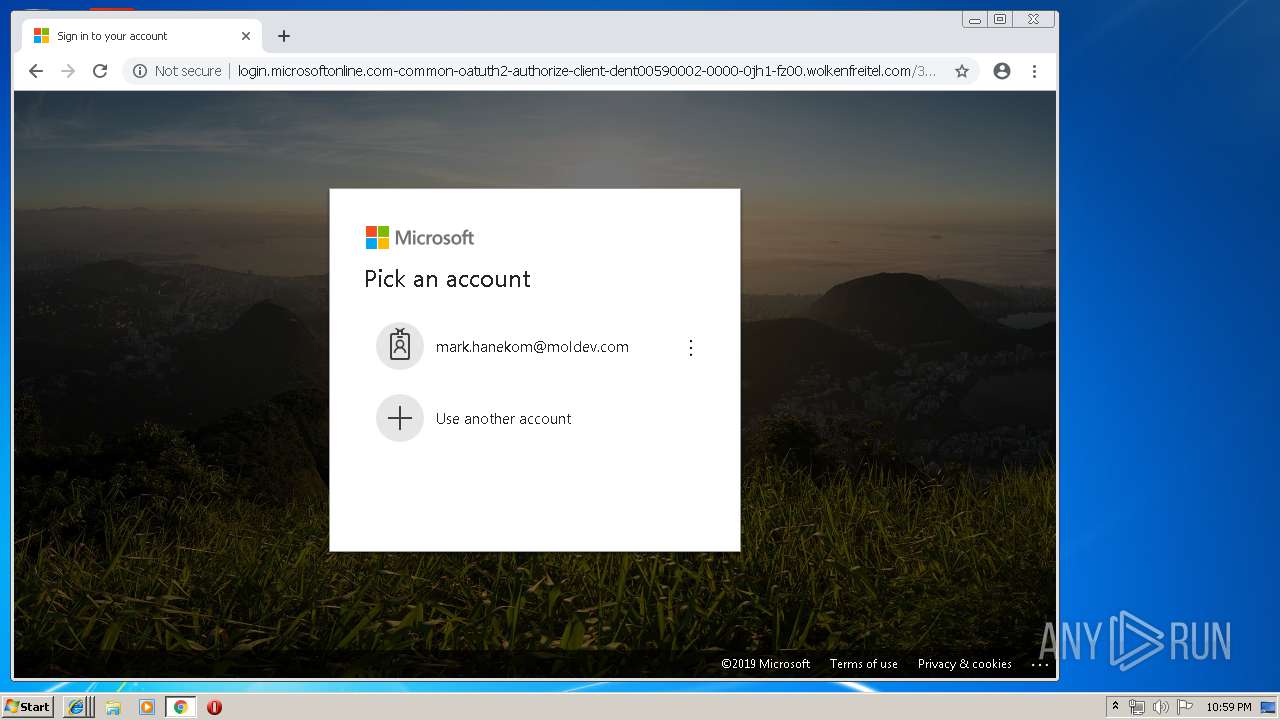
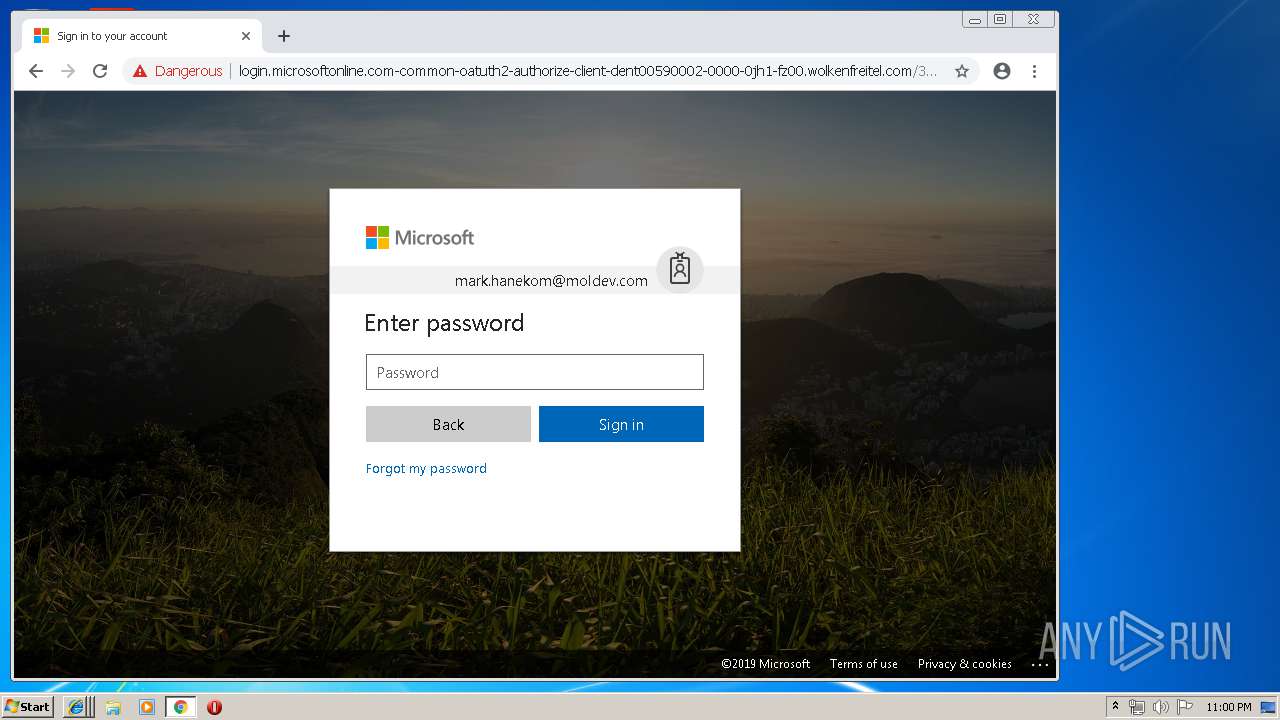
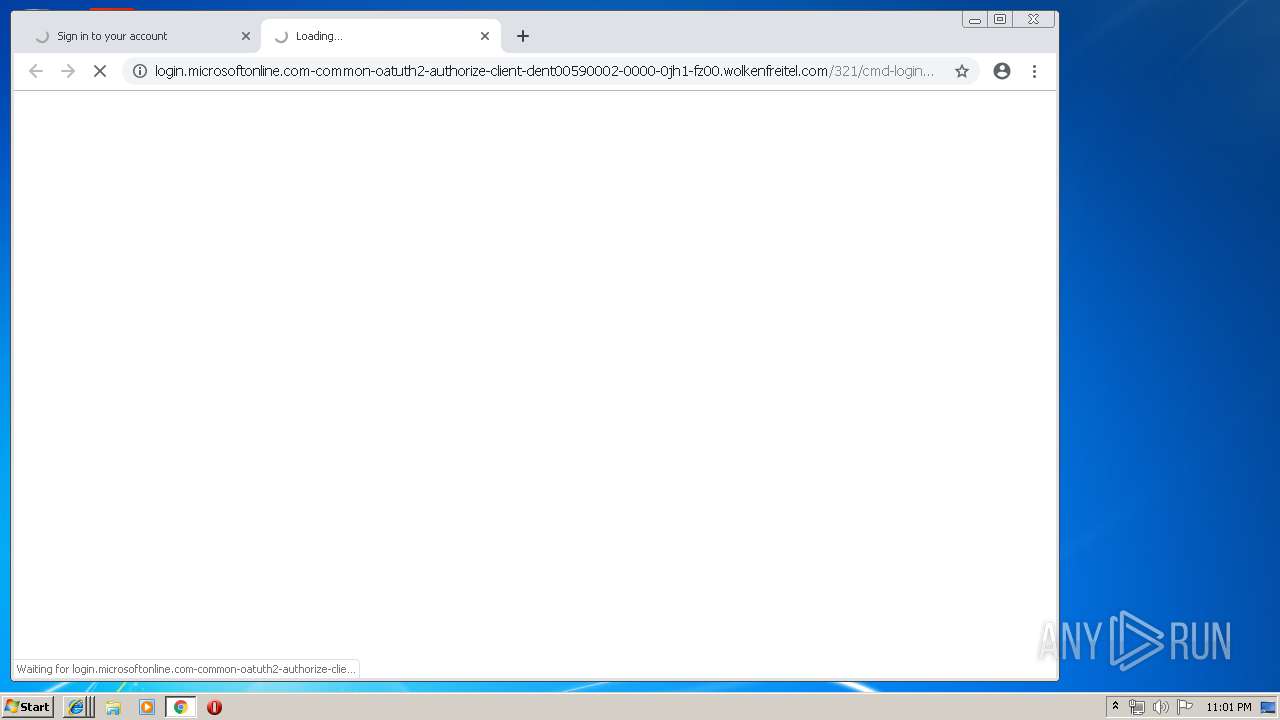
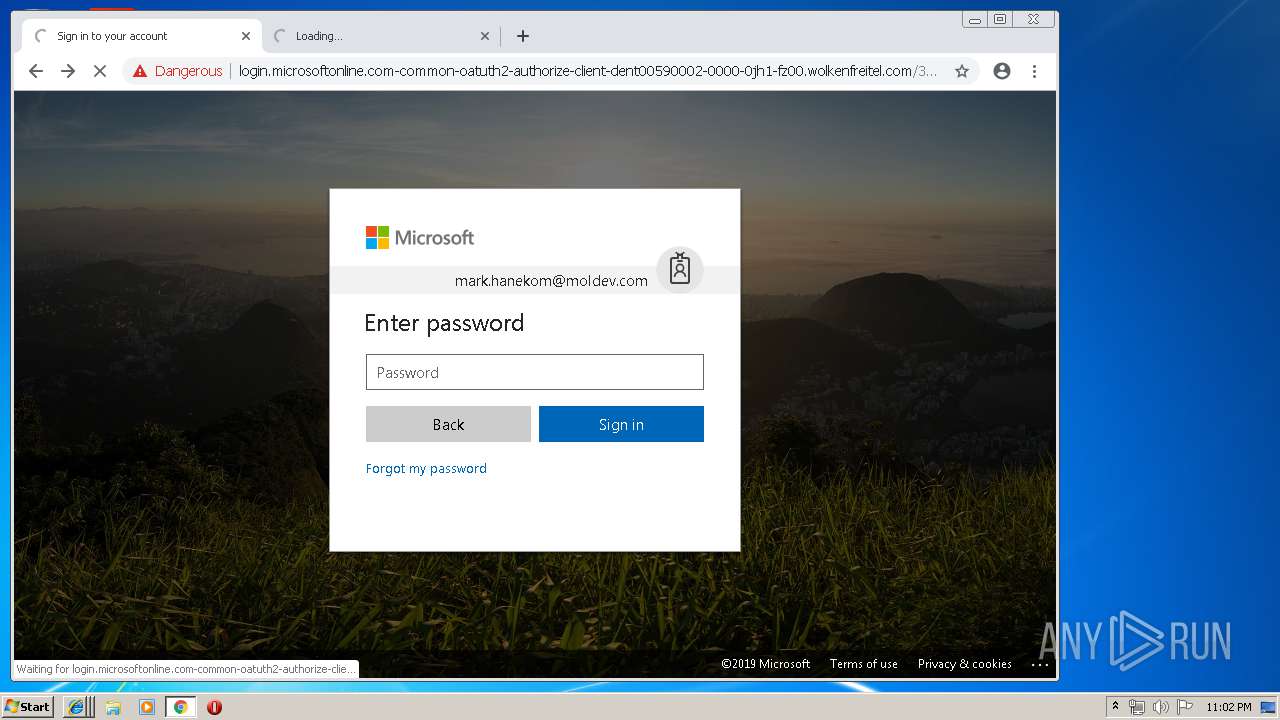
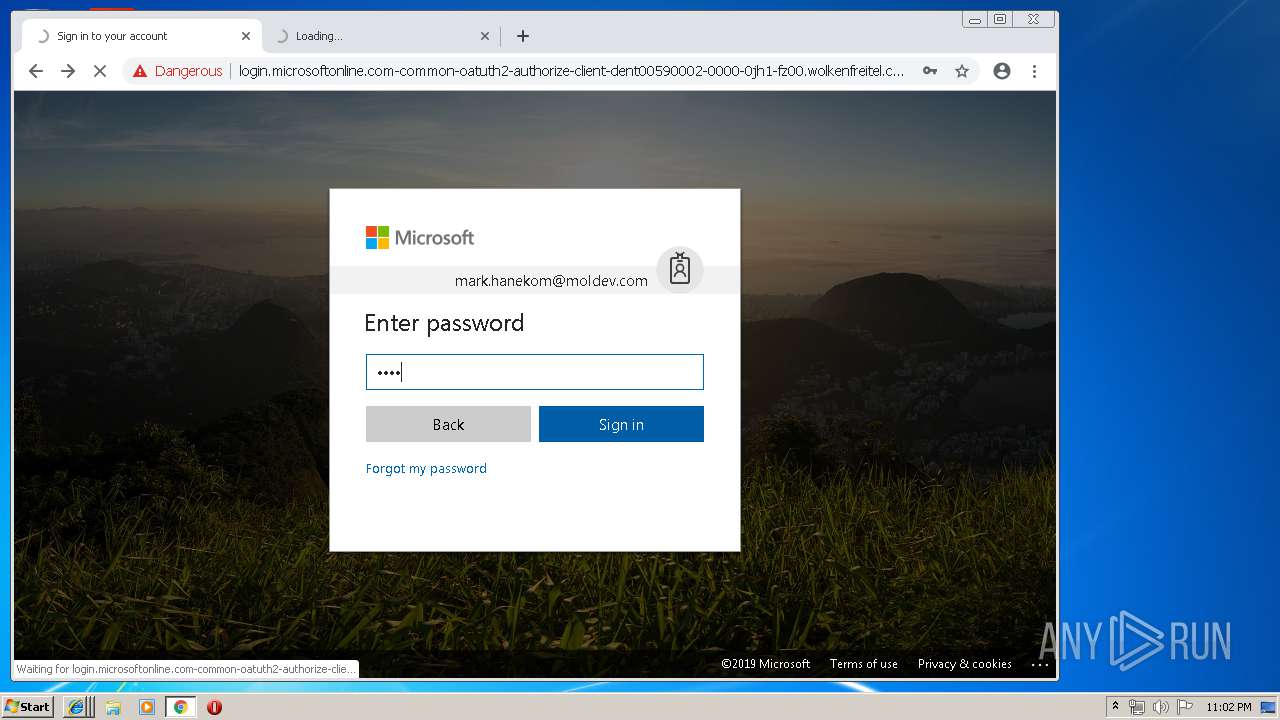
3652 | iexplore.exe | GET | 200 | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/cmd-login=9c8e23868b79cf1b07cefa2032c8cf7f/ja0tdw0pjzg7b7x6t7imtcbn.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=mark.hanekom@moldev.com&loginpage=&.rand=13InboxLight.aspx?n=1774256418&fid=4 | US | html | 37.0 Kb | malicious |
3652 | iexplore.exe | GET | 200 | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/convergedloginpaginatedstrings-en.js | US | text | 11.1 Kb | malicious |
3652 | iexplore.exe | GET | 200 | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/converged.css | US | text | 85.3 Kb | malicious |
3652 | iexplore.exe | GET | 200 | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/convergedlogin_pcore.js | US | text | 422 Kb | malicious |
3652 | iexplore.exe | GET | 200 | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/prefetch.htm | US | html | 3.93 Kb | malicious |
3652 | iexplore.exe | GET | 200 | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/prefetch_data/boot_002_002.js | US | text | 639 Kb | malicious |
3652 | iexplore.exe | GET | 200 | 72.29.67.240:80 | http://login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com/321/empty_files/prefetch_data/boot_004.js | US | txt | 643 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2888 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
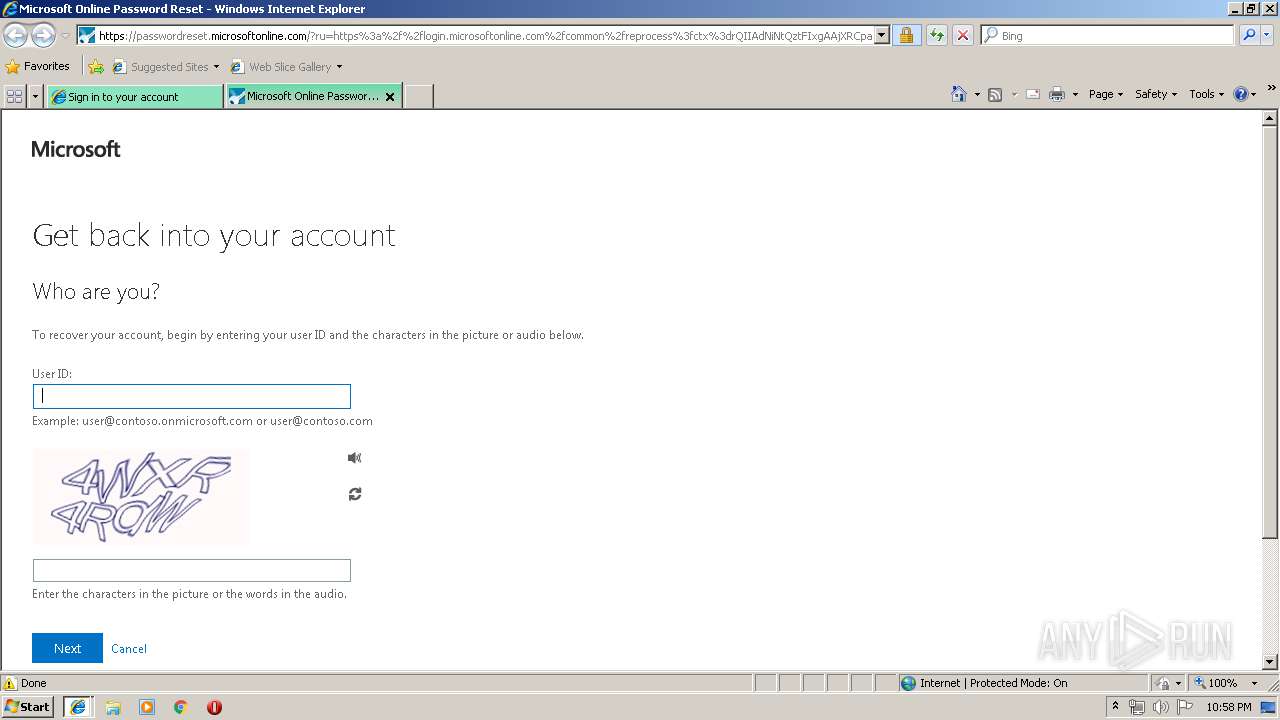
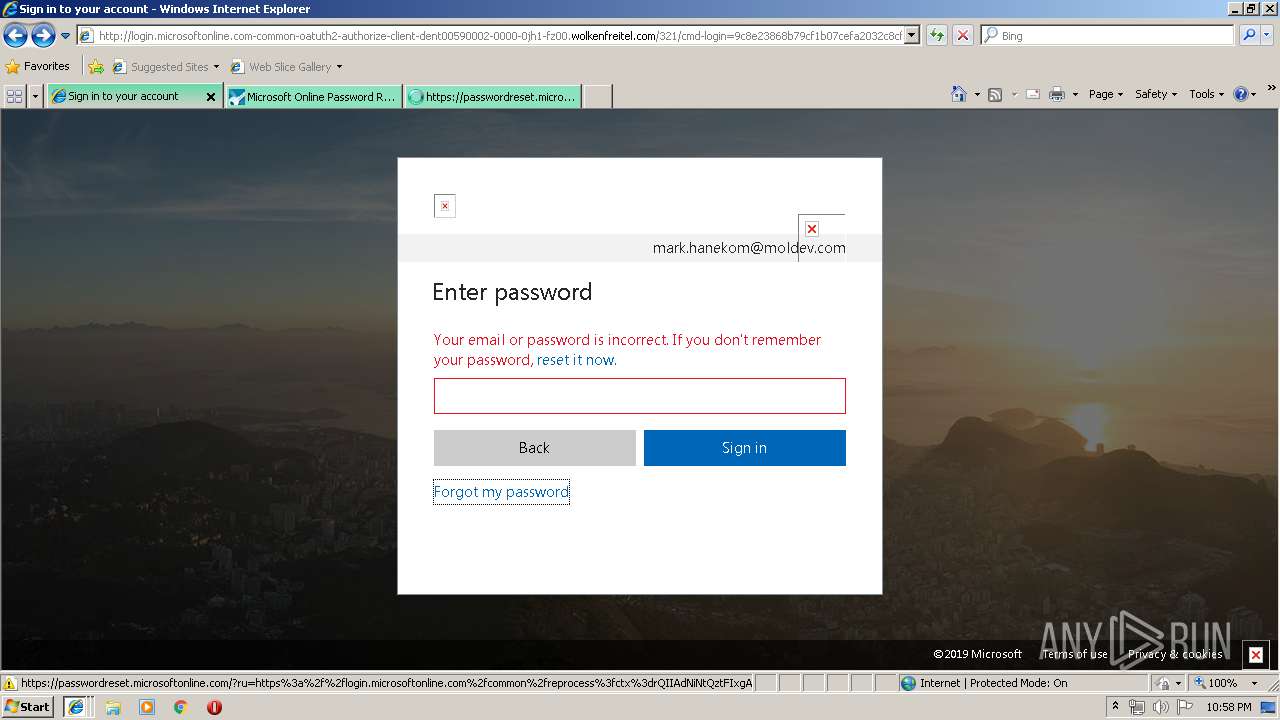
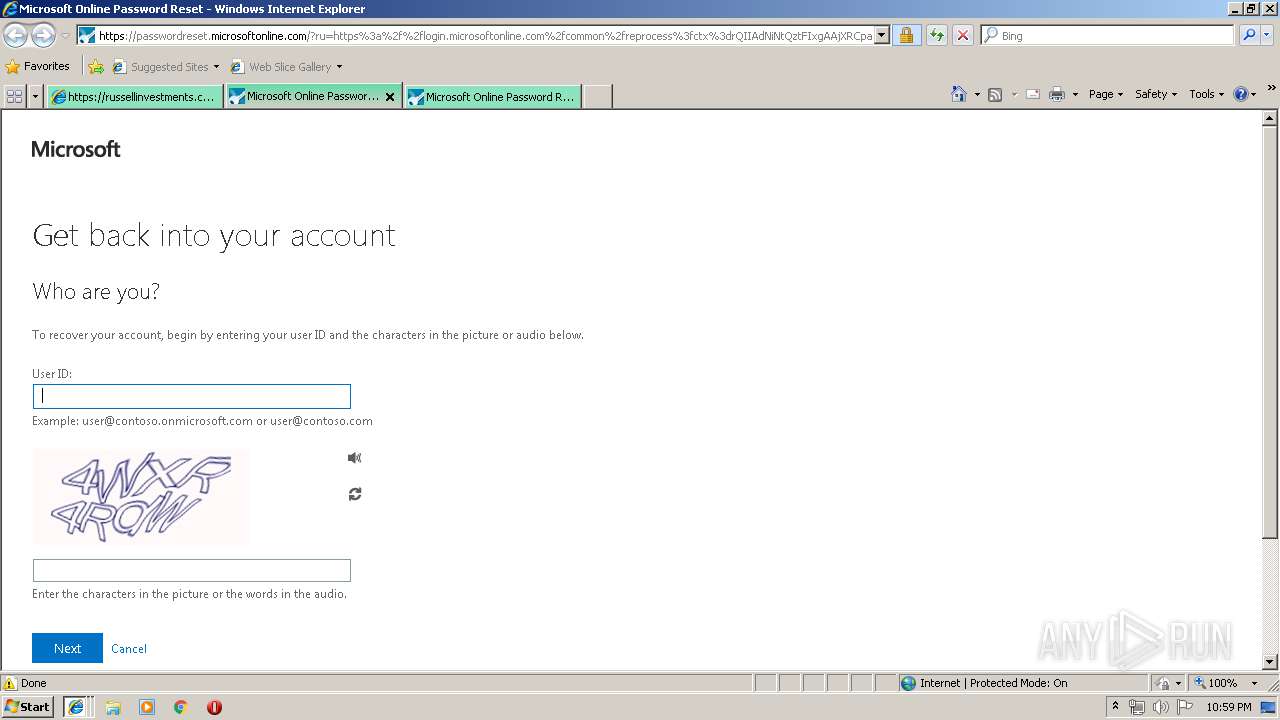
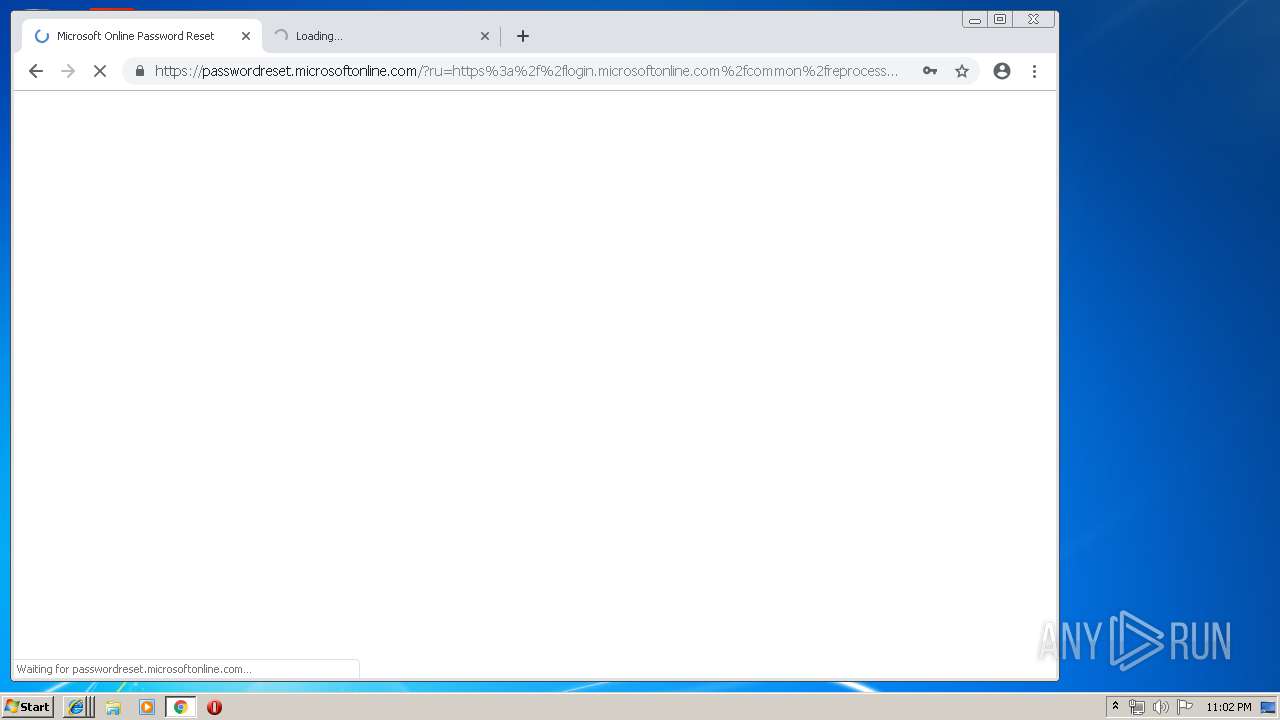
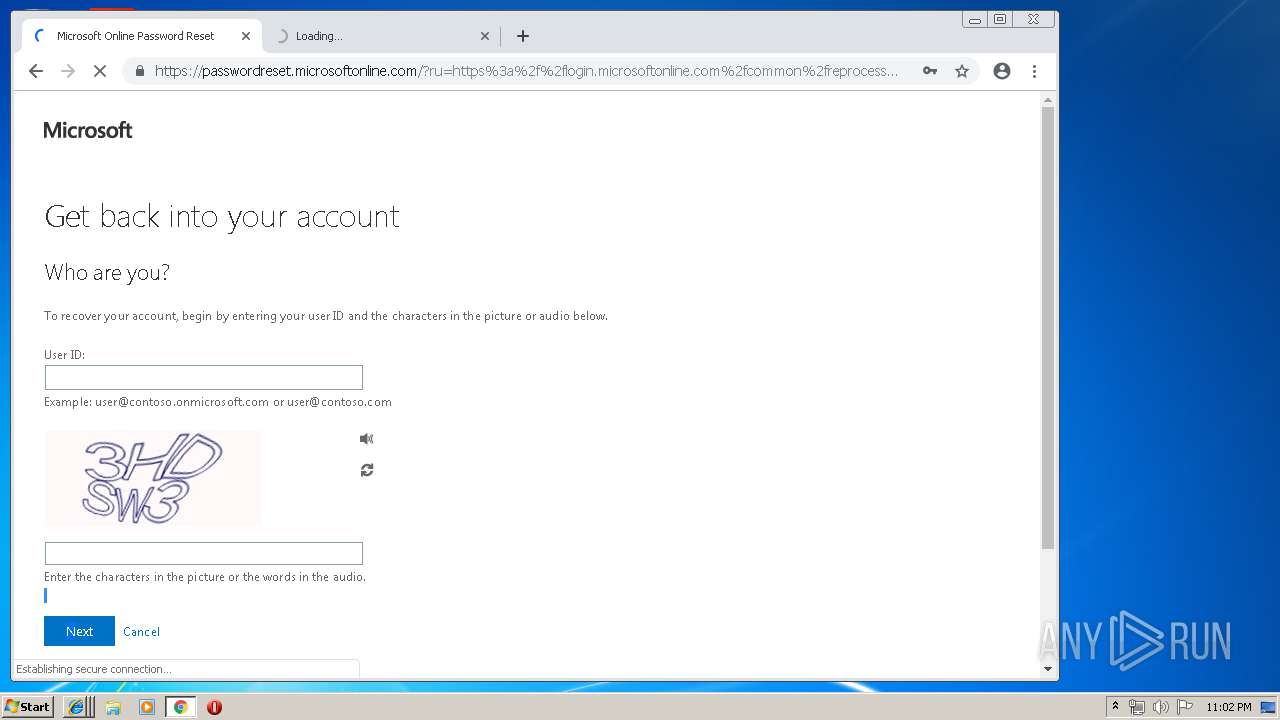
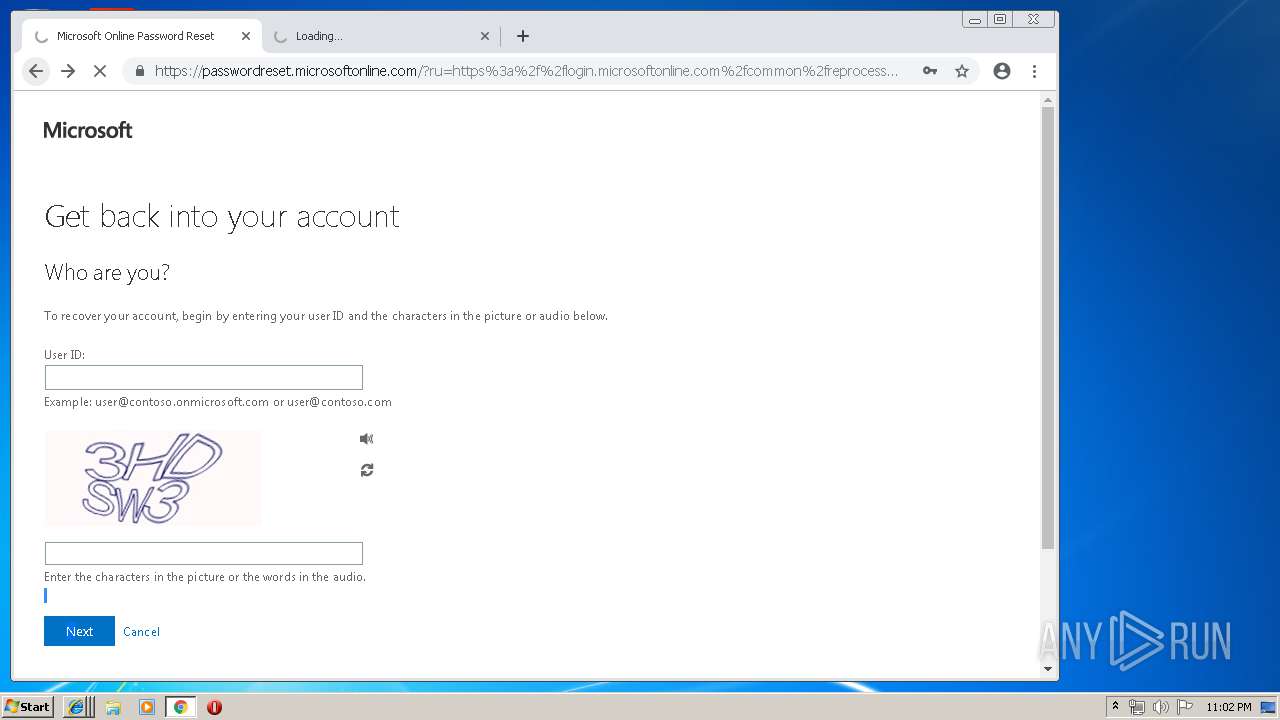
3884 | iexplore.exe | 20.190.137.0:443 | passwordreset.microsoftonline.com | Microsoft Corporation | US | unknown |
3884 | iexplore.exe | 152.199.19.160:443 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3884 | iexplore.exe | 104.215.74.84:443 | client.hip.live.com | Microsoft Corporation | US | unknown |
3884 | iexplore.exe | 23.96.111.19:443 | client.hip.live.com | Microsoft Corporation | US | whitelisted |
2224 | iexplore.exe | 20.190.137.0:443 | passwordreset.microsoftonline.com | Microsoft Corporation | US | unknown |
2888 | iexplore.exe | 20.190.137.0:443 | passwordreset.microsoftonline.com | Microsoft Corporation | US | unknown |
2224 | iexplore.exe | 23.96.111.19:443 | client.hip.live.com | Microsoft Corporation | US | whitelisted |
3884 | iexplore.exe | 104.210.51.228:443 | wut.smartscreen.microsoft.com | Microsoft Corporation | US | unknown |
2224 | iexplore.exe | 152.199.19.160:443 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u10817722.ct.sendgrid.net |
| malicious |
www.bing.com |
| whitelisted |
login.microsoftonline.com-common-oatuth2-authorize-client-dent00590002-0000-0jh1-fz00.wolkenfreitel.com |
| malicious |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
r4.res.office365.com |
| whitelisted |
passwordreset.microsoftonline.com |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
client.hip.live.com |
| whitelisted |
eus.client.hip.live.com |
| whitelisted |
wut.smartscreen.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3652 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
3652 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Phishing Landing 2018-08-07 |
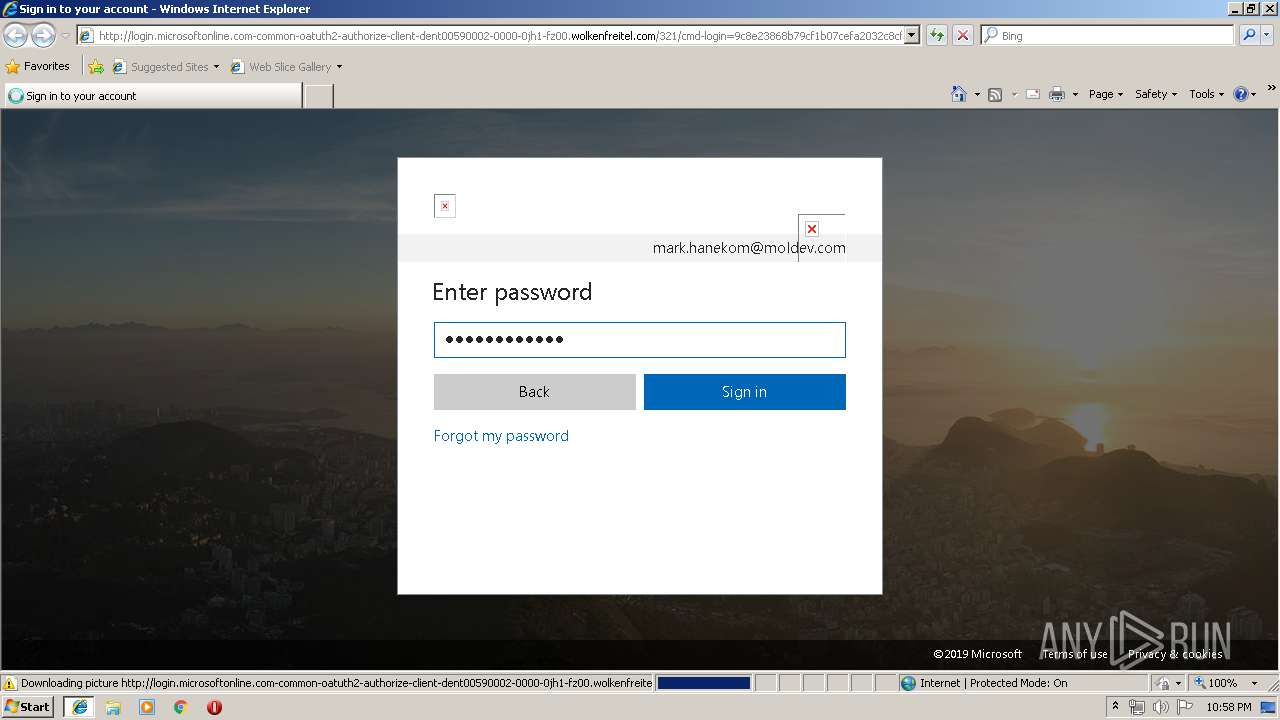
3652 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
3652 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Phishing Landing 2018-08-07 |
3652 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
3652 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
3652 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
2760 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
2760 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Phishing Landing 2018-08-07 |
2760 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
57 ETPRO signatures available at the full report