| File name: | Dell-Bios-inventory.exe |
| Full analysis: | https://app.any.run/tasks/8a405fe3-2882-448e-a863-cf499cc899e4 |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2020, 06:32:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4FA07AFAD729182301E65A45838B5C8E |
| SHA1: | BC1444345BB38E842AB68ADB33388DC113535F53 |
| SHA256: | DECE93CC89CDDB3AAA8DD081DACDBC8BC486FAF5803FF222297F338D1F82EAF1 |
| SSDEEP: | 24576:/8R0nYRa++h7RfDtCAoGN0r2QIByVedWlzG8xQiak/2sl4MX2YN1n7:/8t2xRf5eGN0rduEedQS8QtMNX/7 |
MALICIOUS
Application was dropped or rewritten from another process
- DrvSetup.exe (PID: 1456)
- Setup.exe (PID: 3500)
- OmcaClientModule32.exe (PID: 2752)
Loads dropped or rewritten executable
- OmcaClientModule32.exe (PID: 2752)
Changes settings of System certificates
- DrvSetup.exe (PID: 1456)
SUSPICIOUS
Executable content was dropped or overwritten
- Dell-Bios-inventory.exe (PID: 1812)
- Setup.exe (PID: 3500)
- DrvSetup.exe (PID: 1456)
- DrvInst.exe (PID: 2704)
- DrvInst.exe (PID: 2748)
Executed via COM
- DrvInst.exe (PID: 2748)
- DrvInst.exe (PID: 2704)
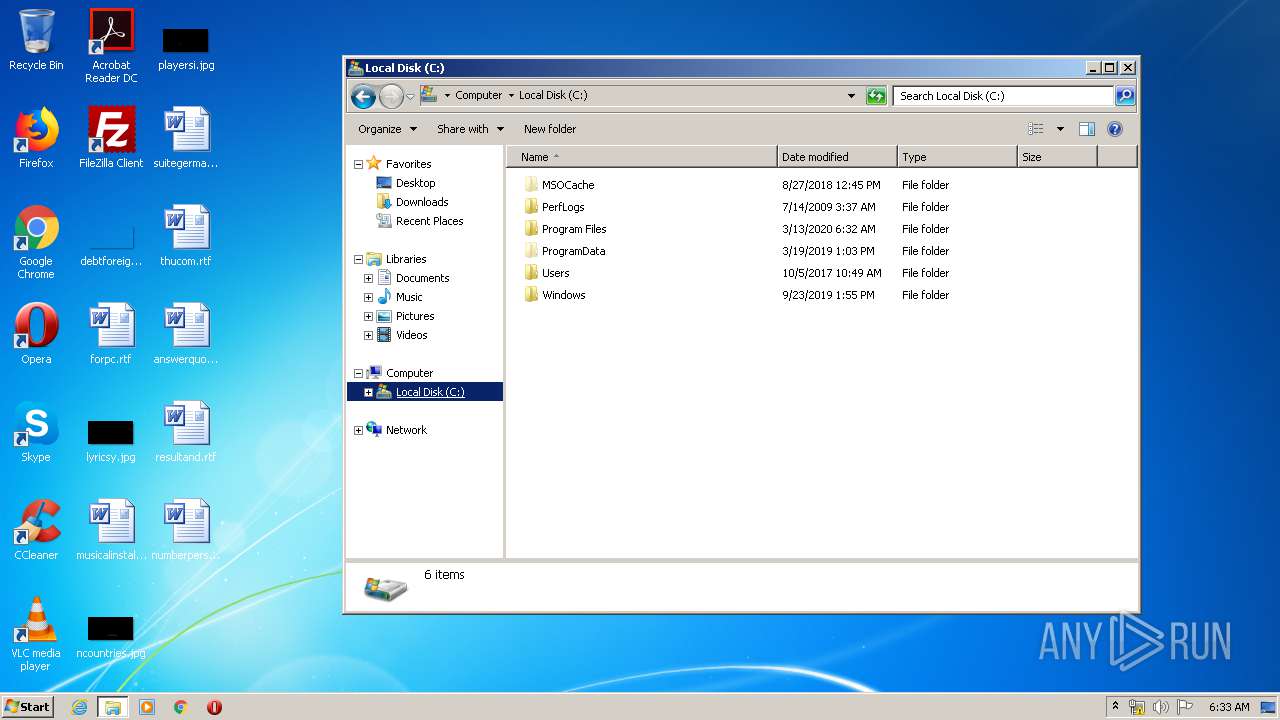
Creates files in the program directory
- Setup.exe (PID: 3500)
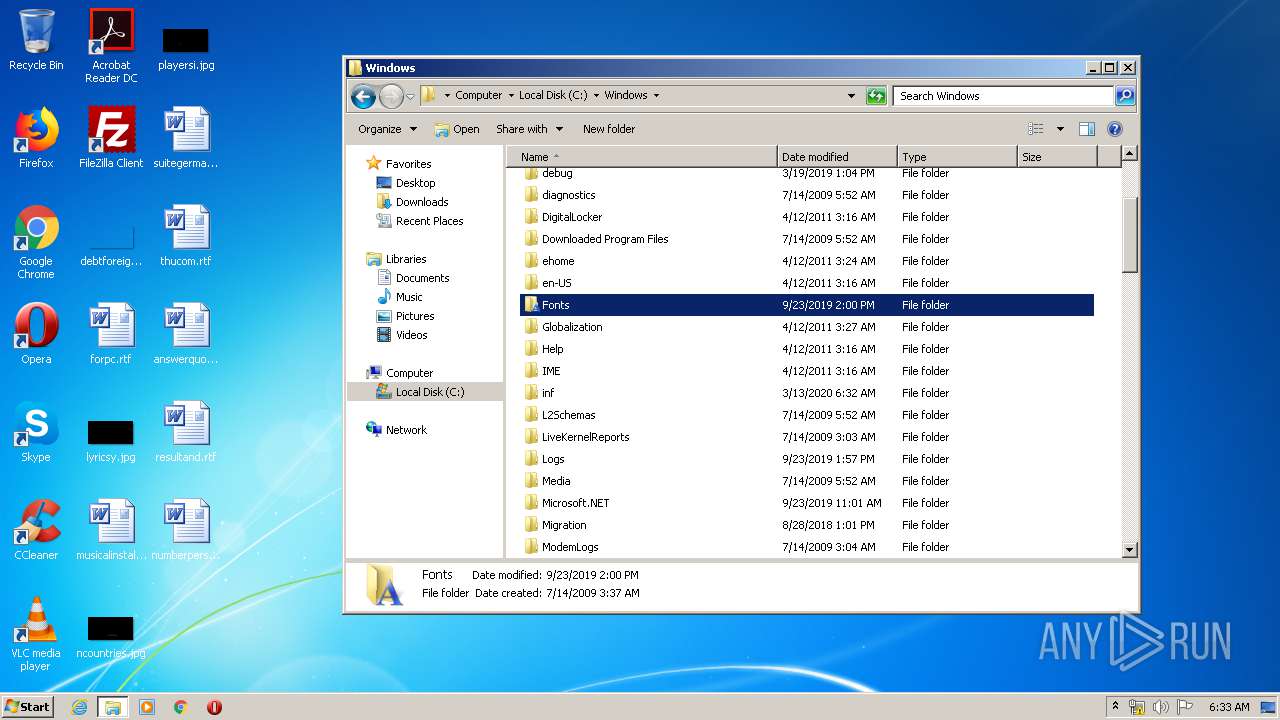
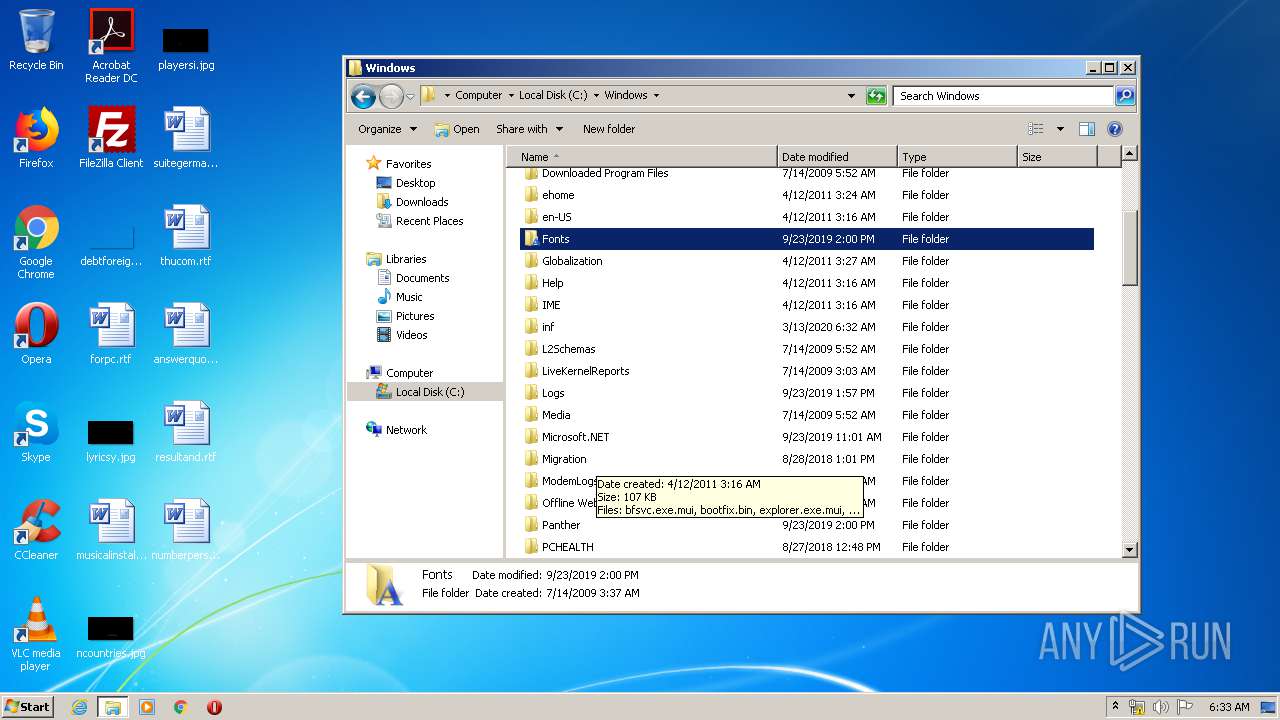
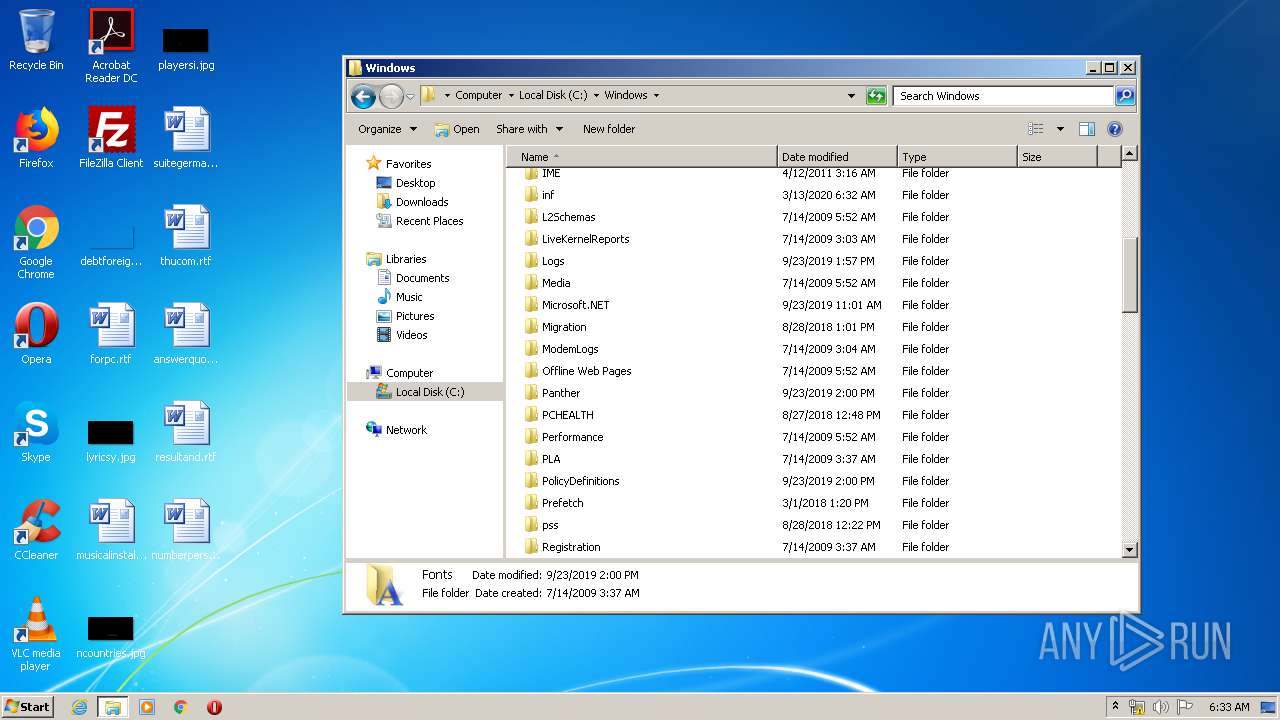
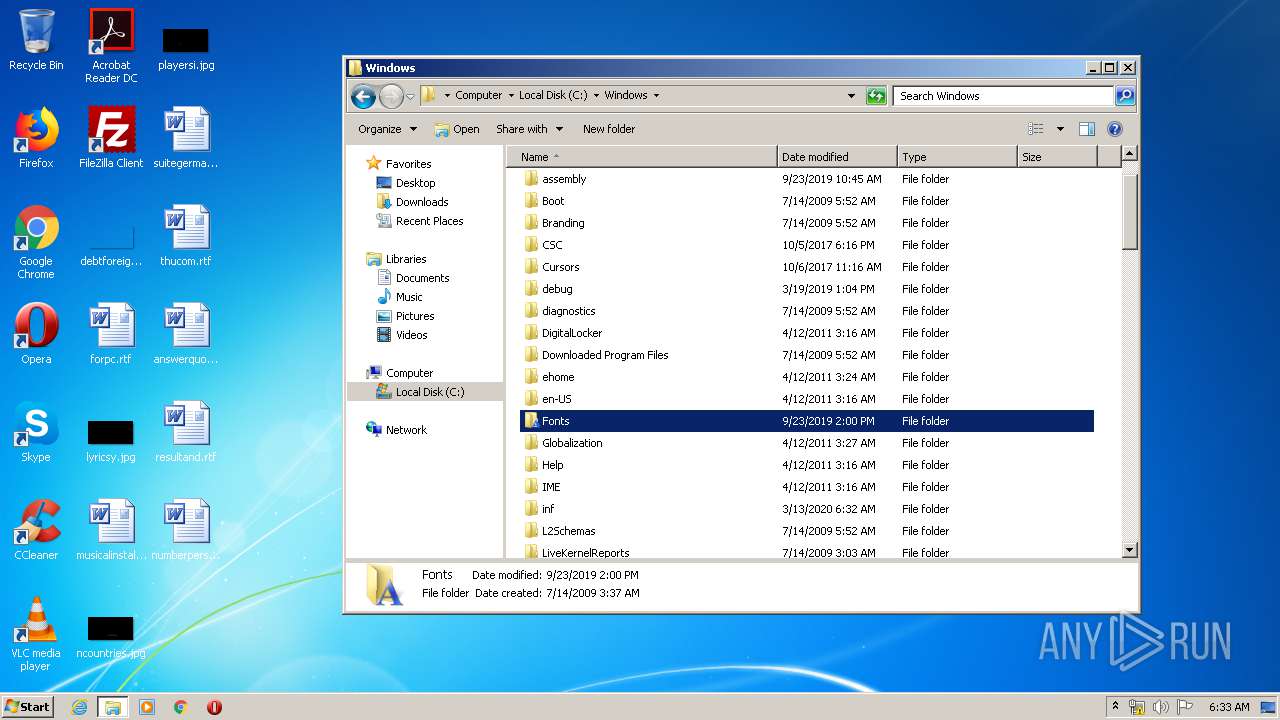
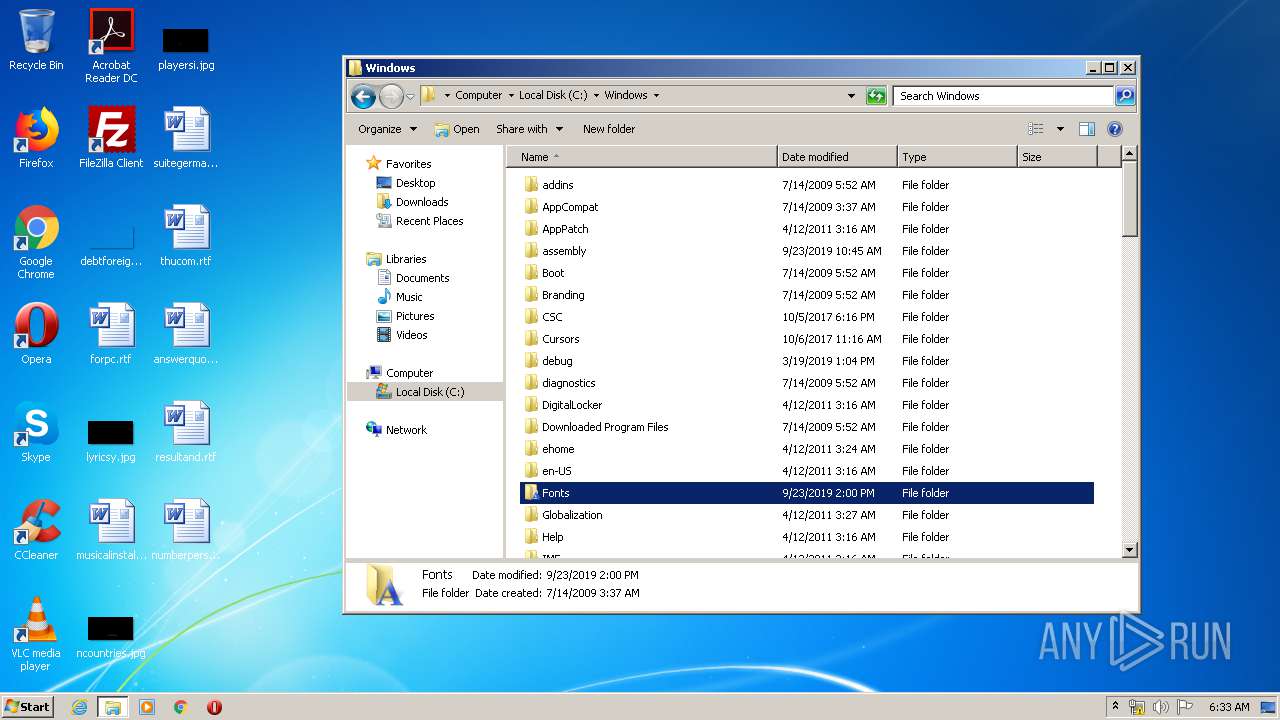
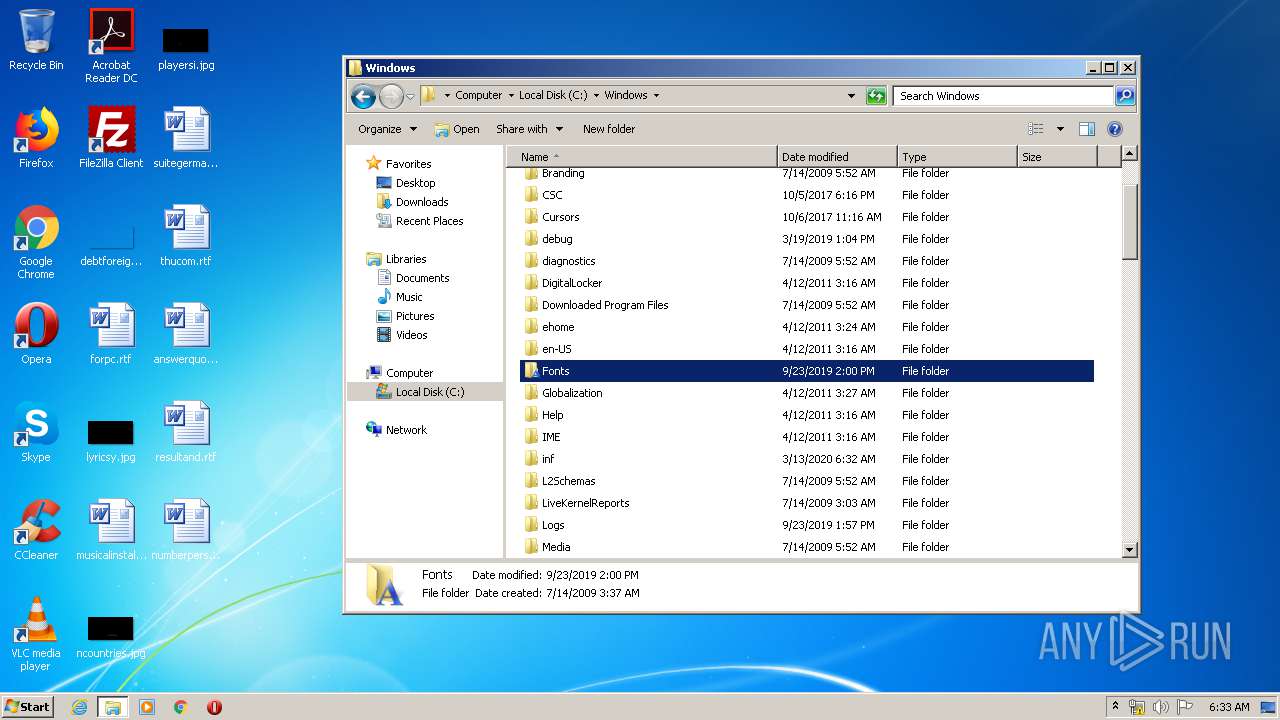
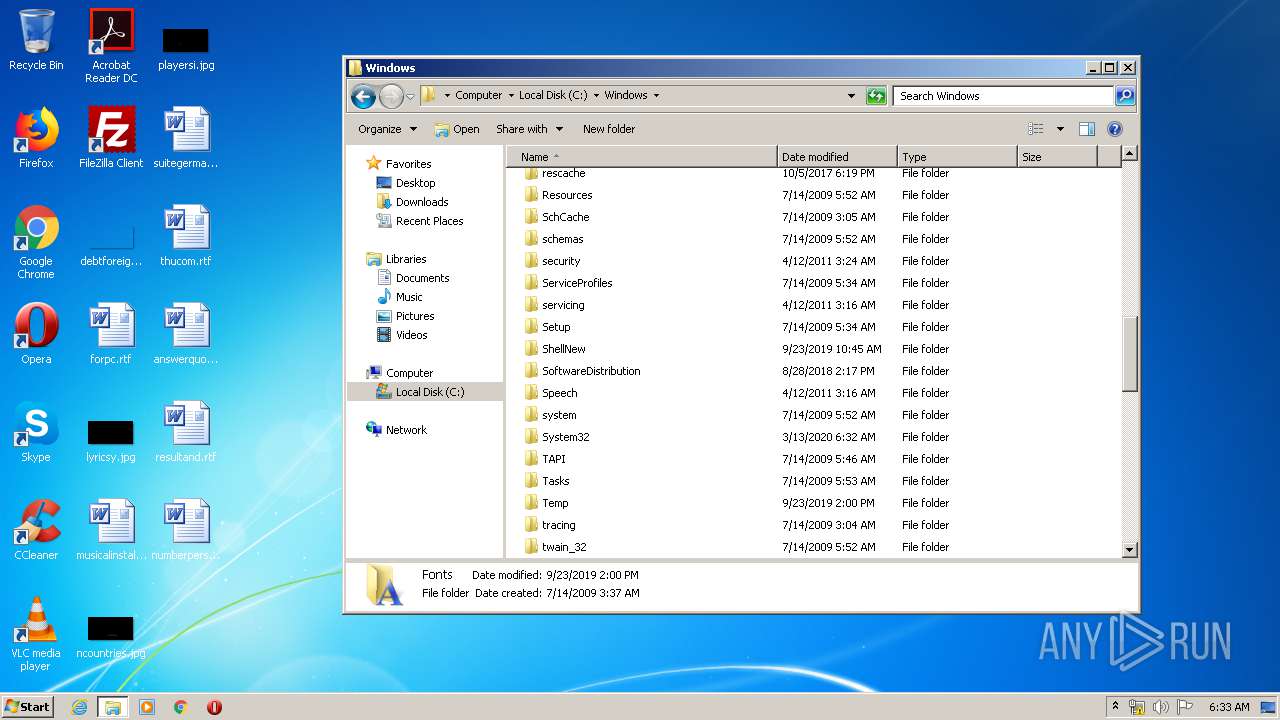
Removes files from Windows directory
- DrvInst.exe (PID: 2748)
- DrvInst.exe (PID: 2704)
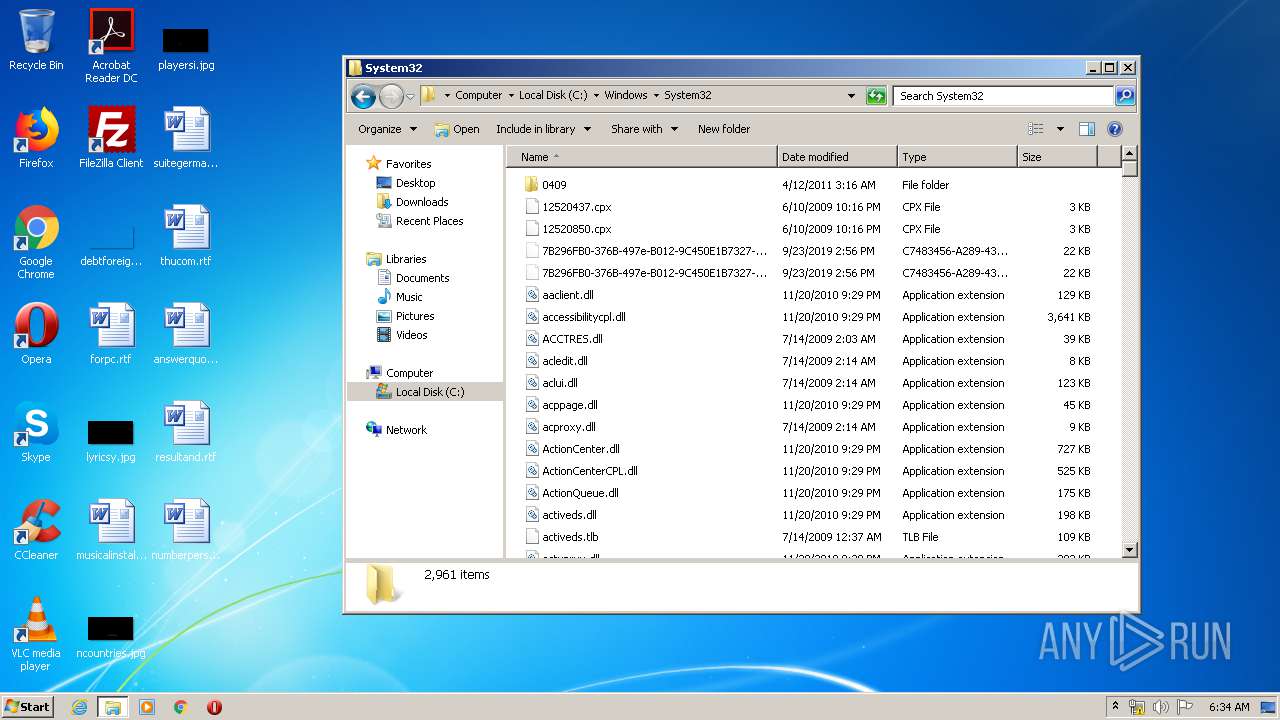
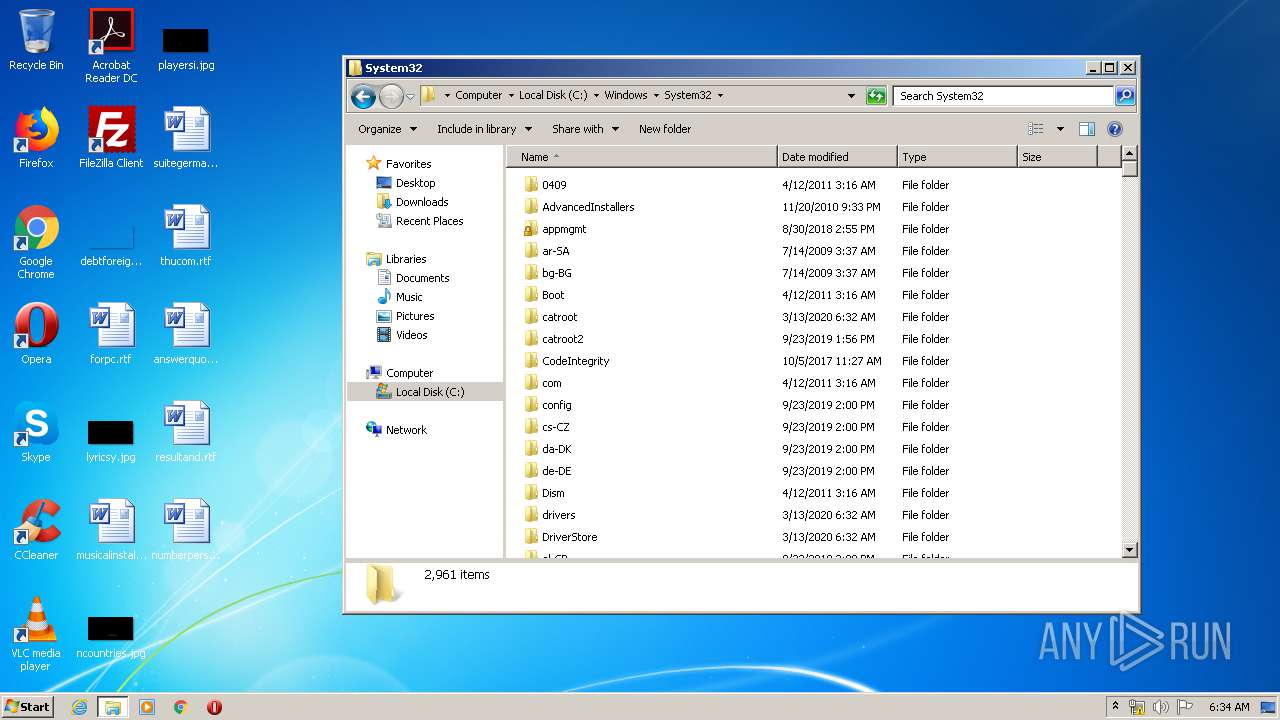
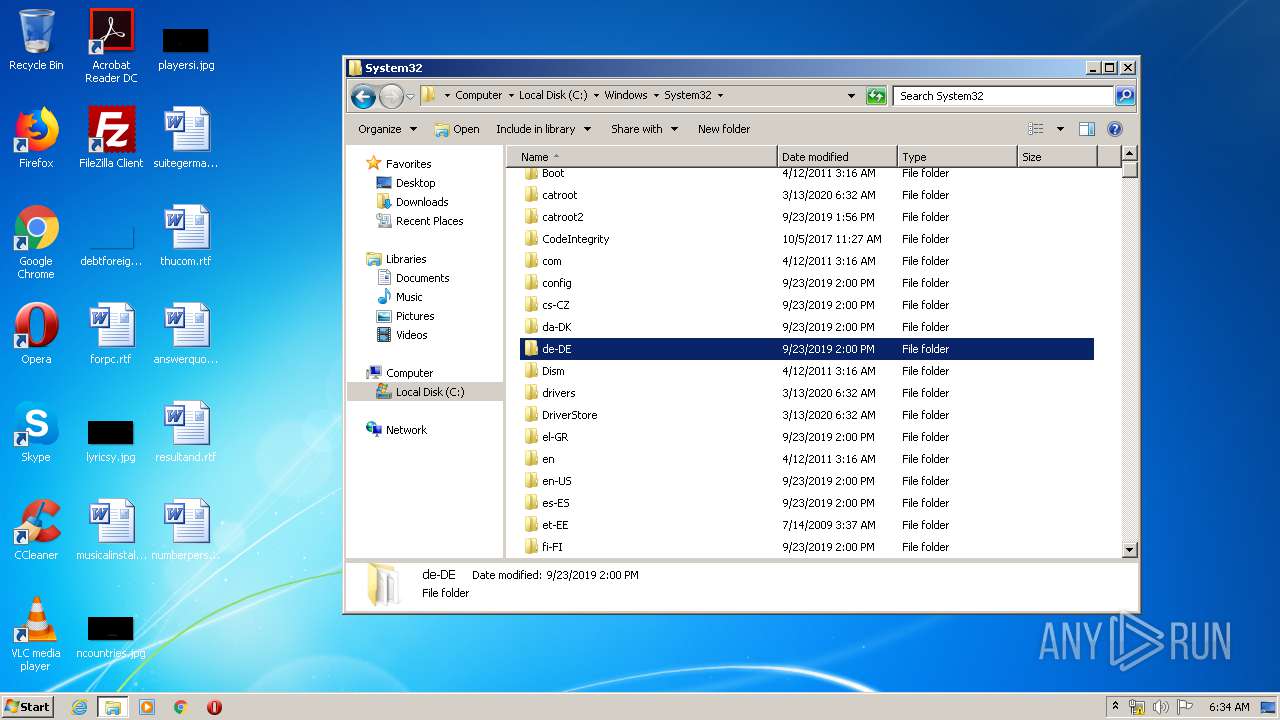
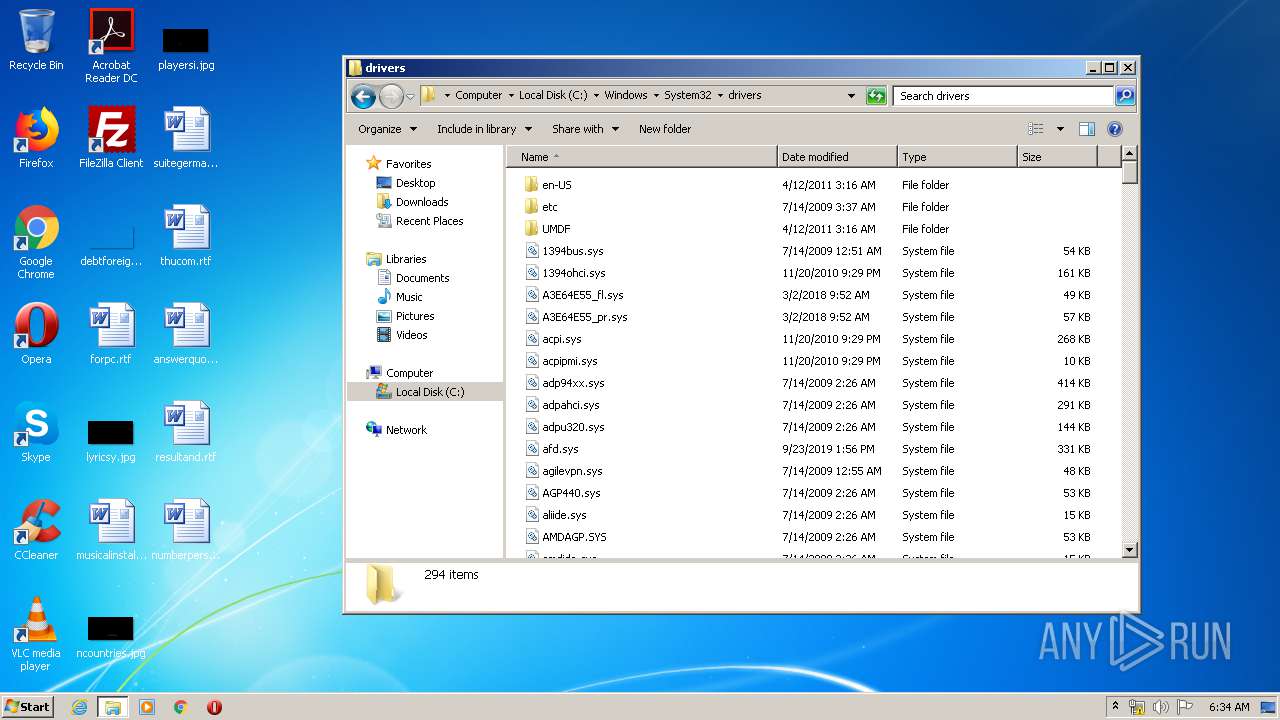
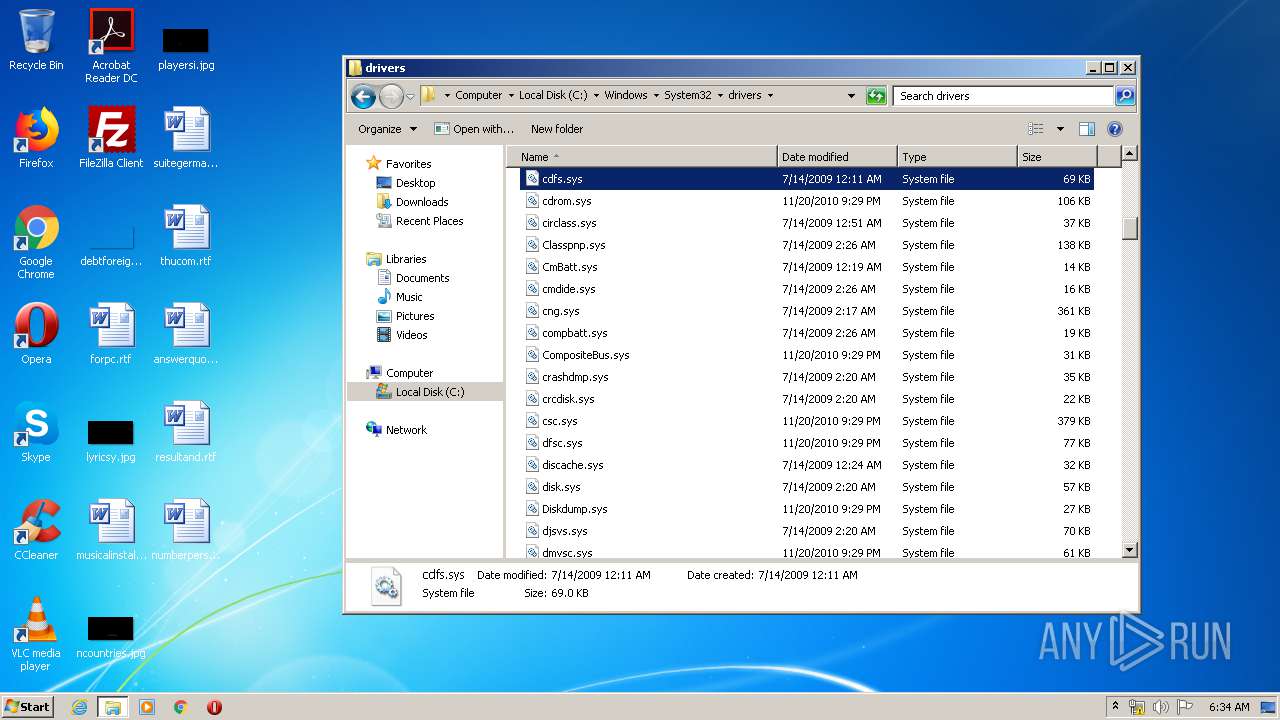
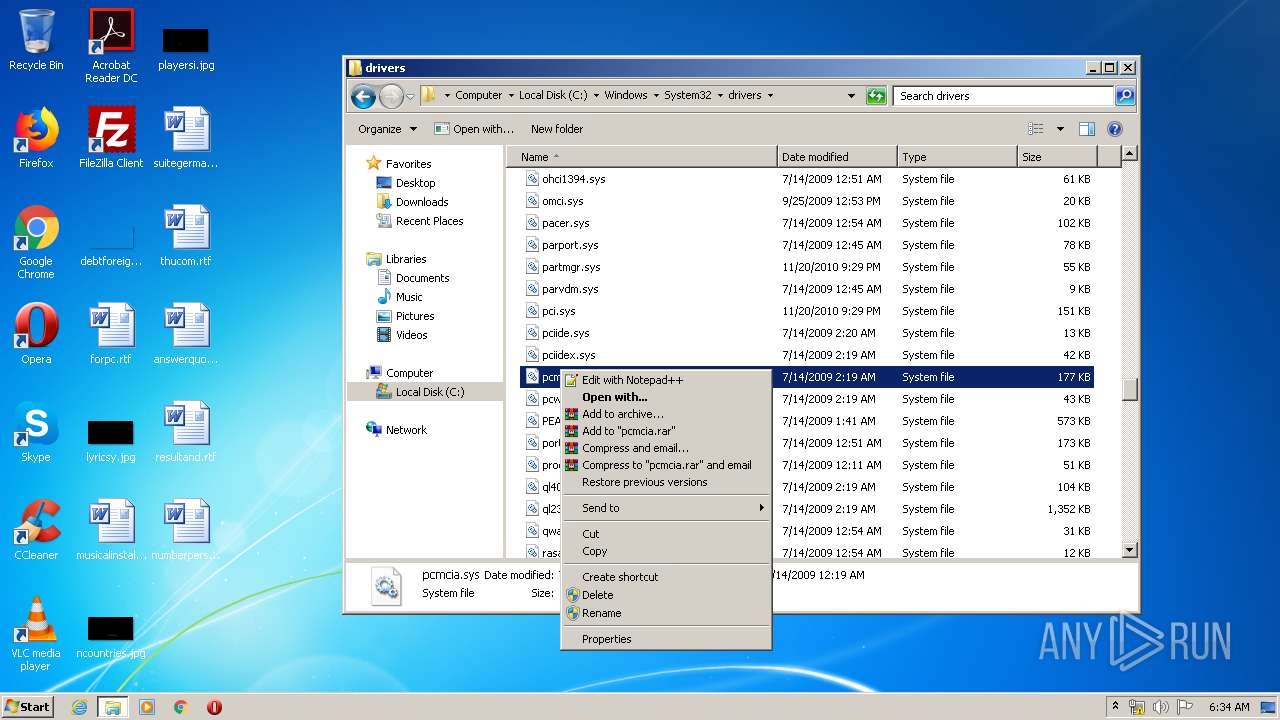
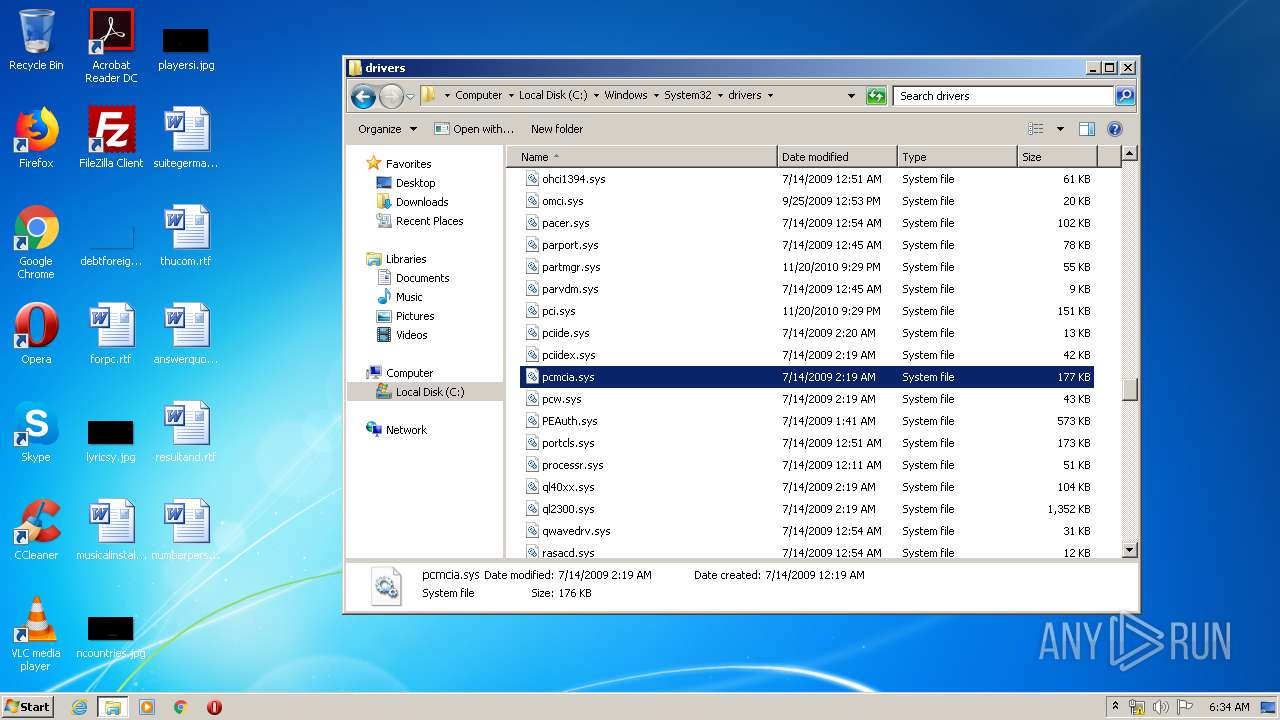
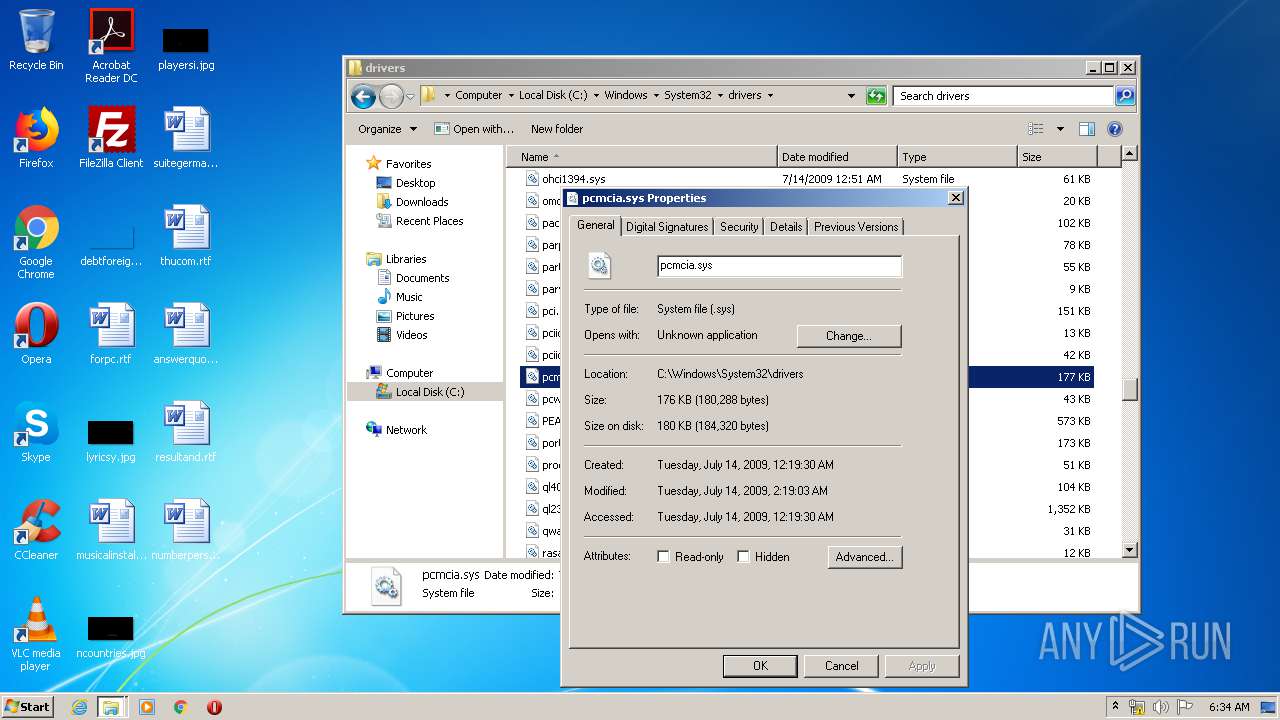
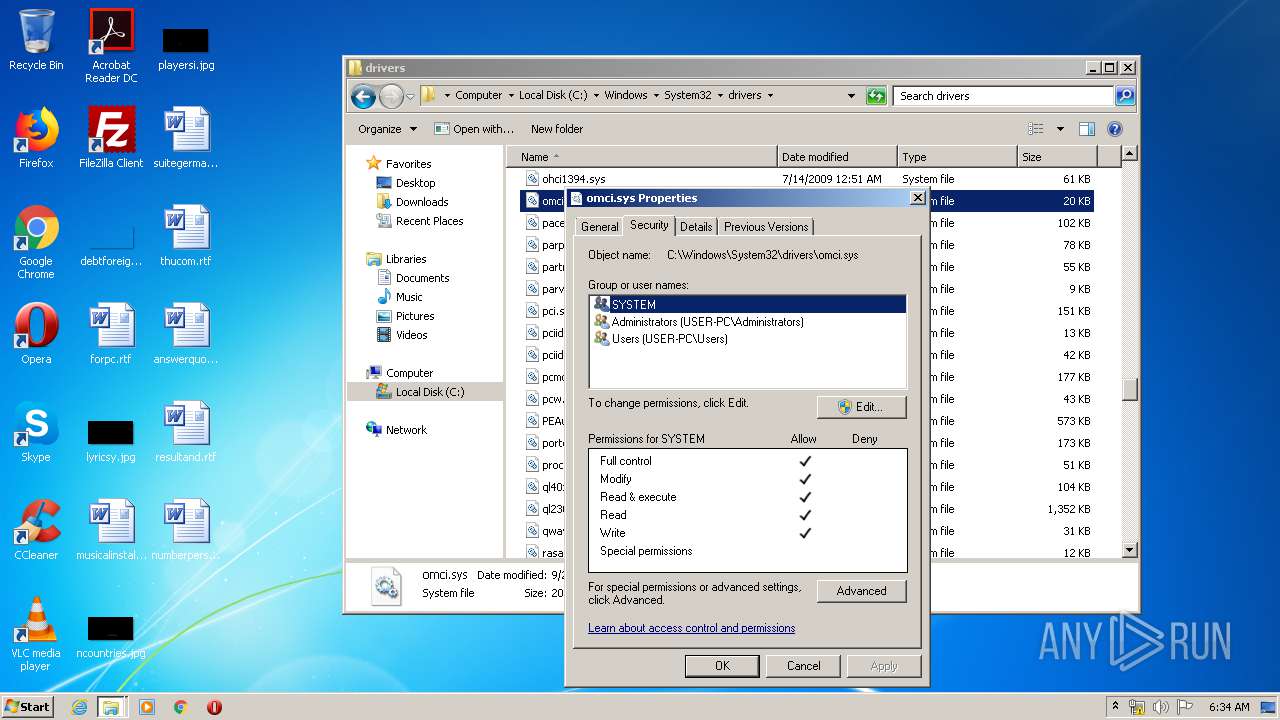
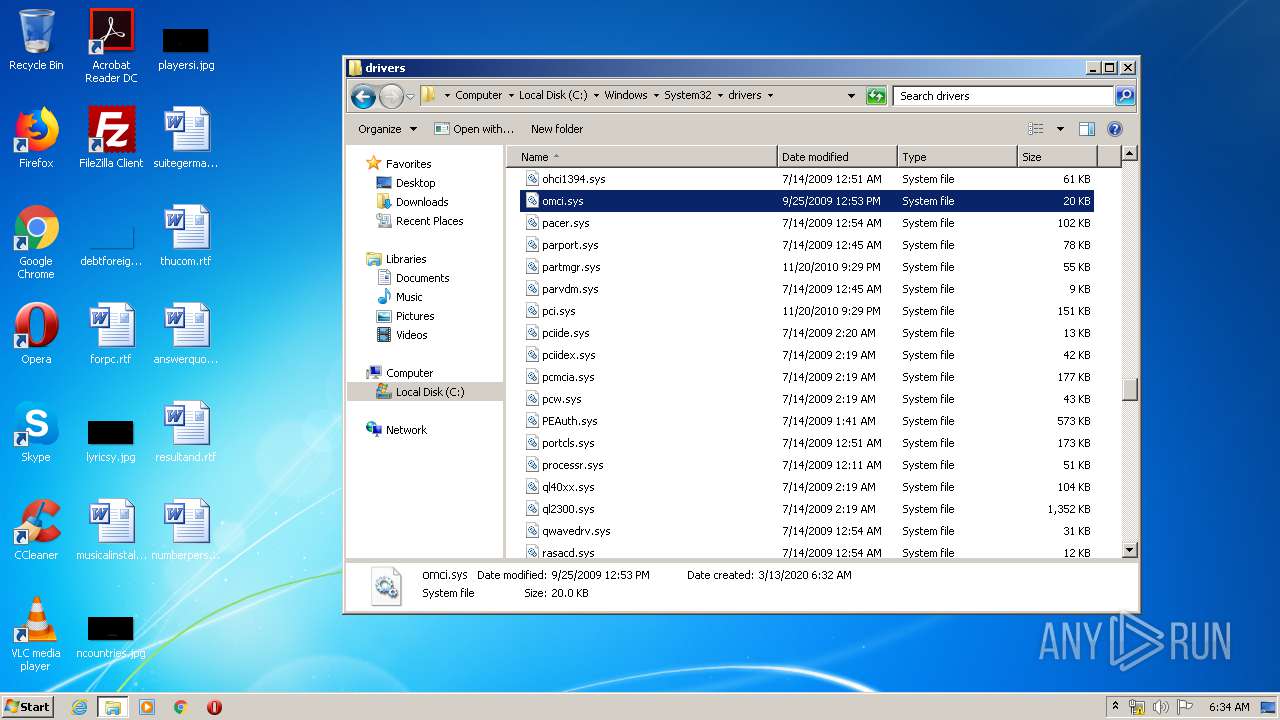
Creates files in the driver directory
- DrvInst.exe (PID: 2748)
- DrvInst.exe (PID: 2704)
Creates files in the Windows directory
- DrvInst.exe (PID: 2704)
- DrvInst.exe (PID: 2748)
- Setup.exe (PID: 3500)
Starts CMD.EXE for commands execution
- Dell-Bios-inventory.exe (PID: 1812)
Adds / modifies Windows certificates
- DrvSetup.exe (PID: 1456)
INFO
Reads settings of System Certificates
- DrvSetup.exe (PID: 1456)
- iexplore.exe (PID: 576)
- iexplore.exe (PID: 2436)
Reads Internet Cache Settings
- iexplore.exe (PID: 576)
- iexplore.exe (PID: 2436)
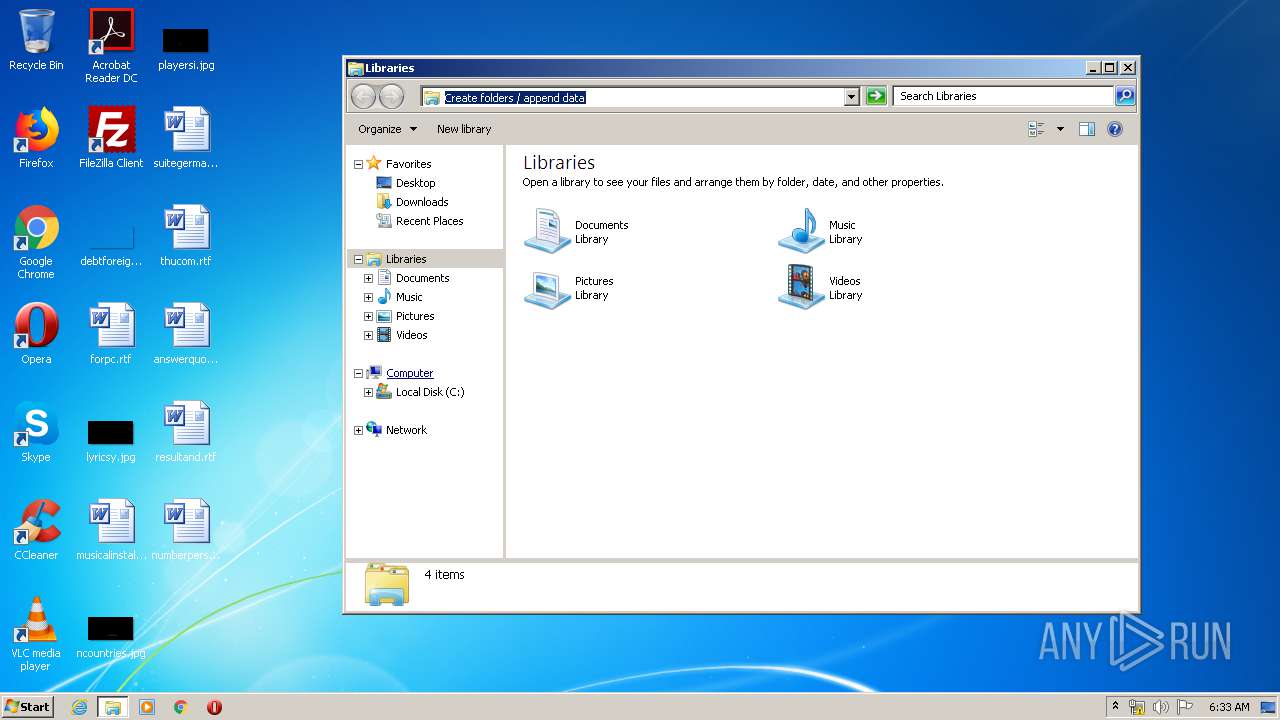
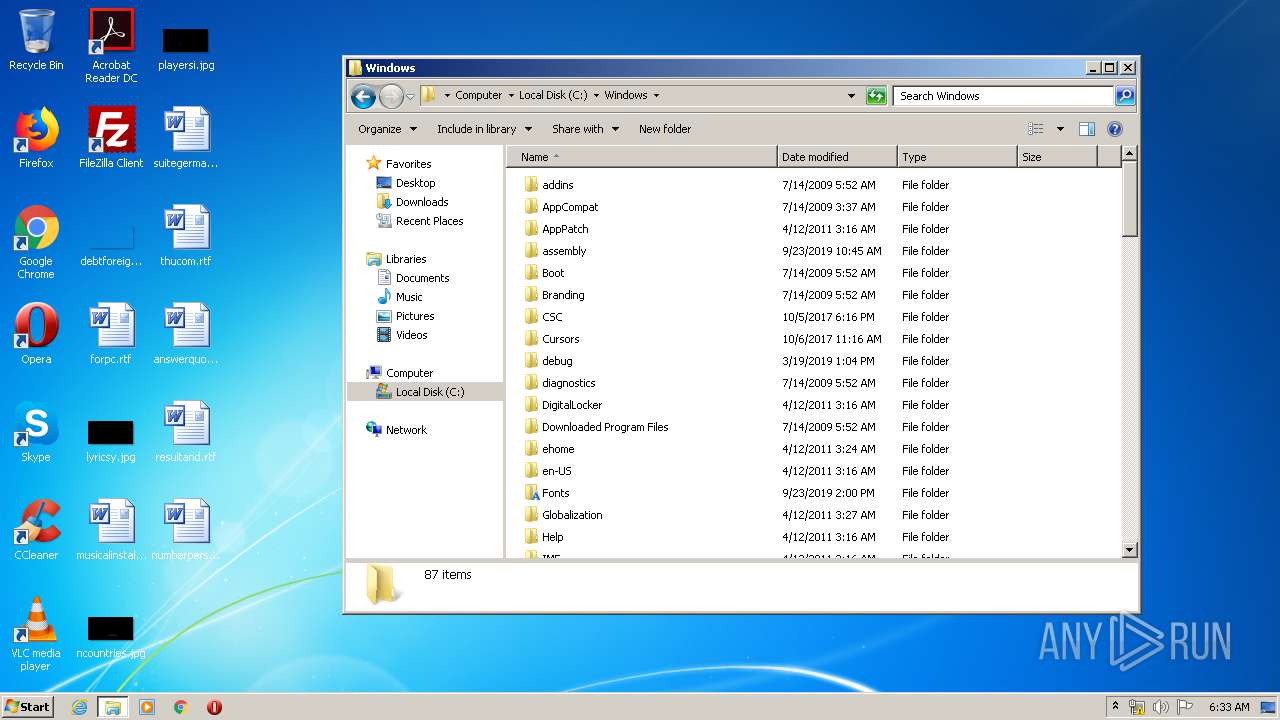
Manual execution by user
- explorer.exe (PID: 1520)
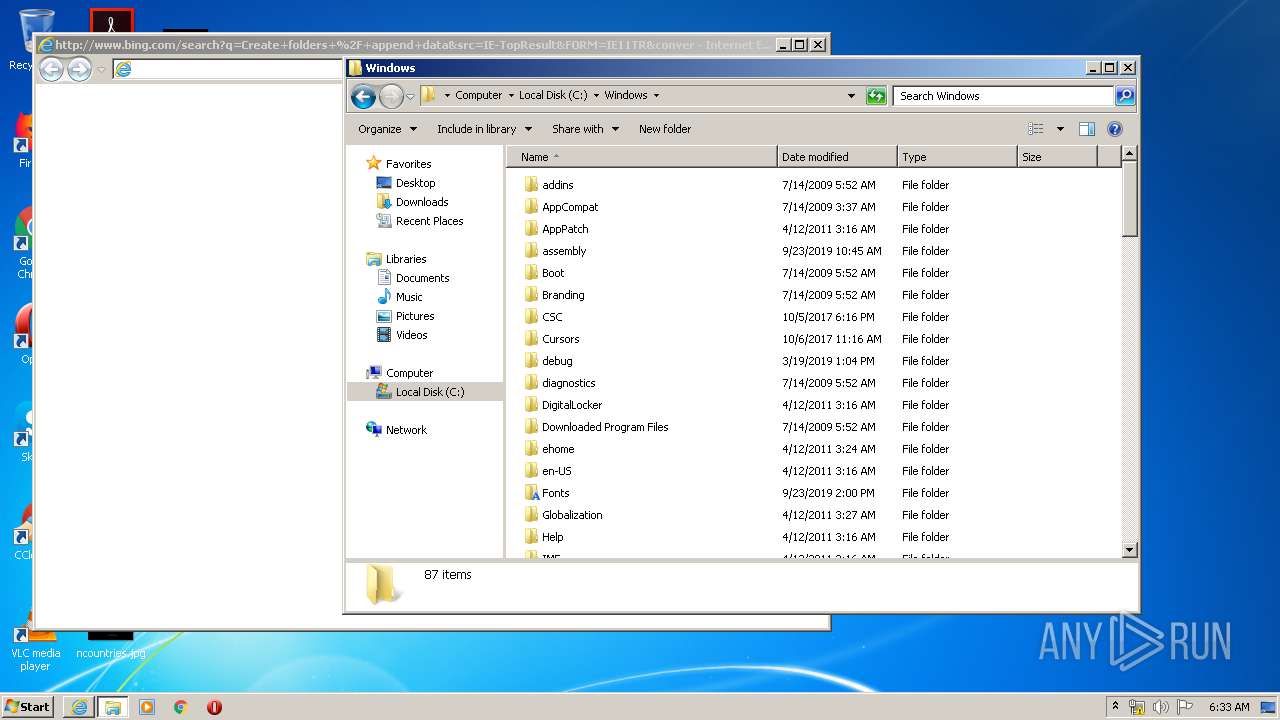
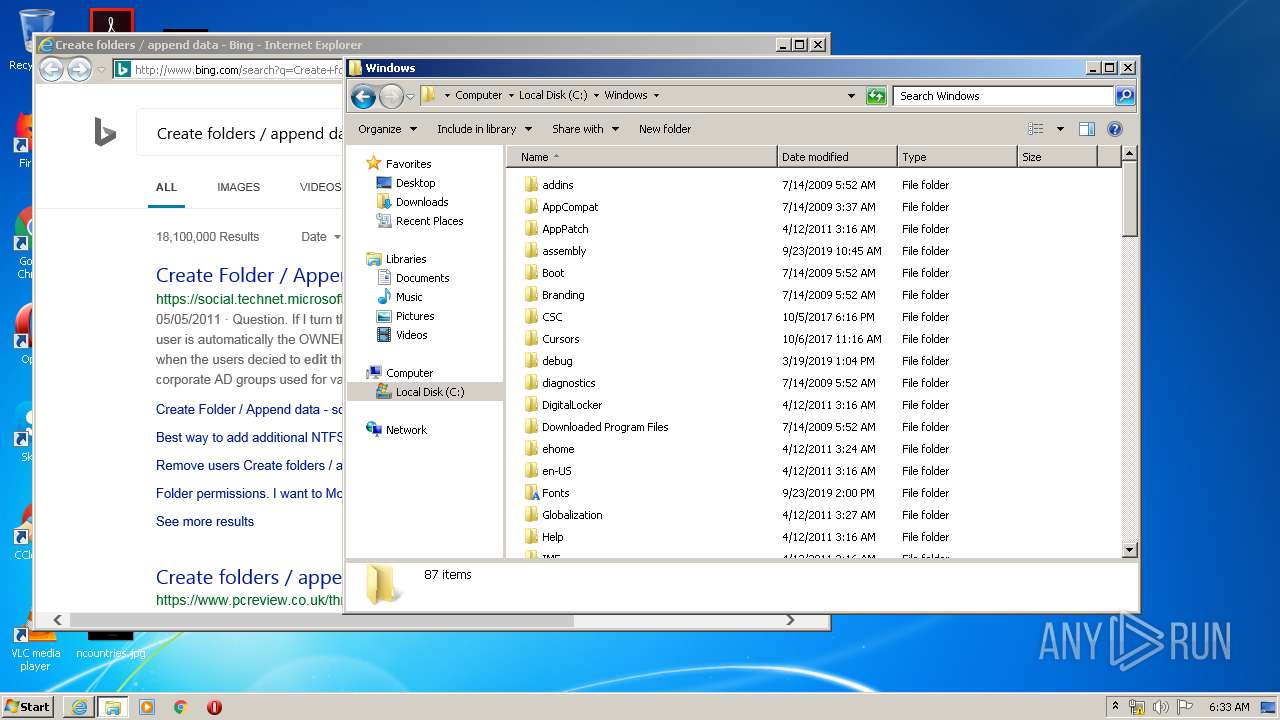
- iexplore.exe (PID: 2436)
Reads internet explorer settings
- iexplore.exe (PID: 576)
Changes internet zones settings
- iexplore.exe (PID: 2436)
Changes settings of System certificates
- iexplore.exe (PID: 2436)
Creates files in the user directory
- iexplore.exe (PID: 576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:01:14 13:33:07+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 90112 |
| InitializedDataSize: | 1363968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8385 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jan-2010 12:33:07 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 14-Jan-2010 12:33:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000151BC | 0x00016000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54266 |
.rdata | 0x00017000 | 0x00004450 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.84964 |
.data | 0x0001C000 | 0x00003234 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.36969 |
.rsrc | 0x00020000 | 0x00145730 | 0x00146000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.83578 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91527 | 520 | Latin 1 / Western European | English - United States | RT_MANIFEST |
103 | 7.99397 | 339191 | Latin 1 / Western European | English - United States | BINARY |
104 | 7.99642 | 199519 | Latin 1 / Western European | English - United States | BINARY |
105 | 7.99728 | 136716 | Latin 1 / Western European | English - United States | BINARY |
106 | 7.99758 | 235711 | Latin 1 / Western European | English - United States | BINARY |
107 | 2.84022 | 15 | Latin 1 / Western European | English - United States | BINARY |
110 | 3.12193 | 10 | Latin 1 / Western European | English - United States | BINARY |
112 | 4.84917 | 24576 | Latin 1 / Western European | English - United States | BINARY |
113 | 4.54376 | 24576 | Latin 1 / Western European | English - United States | BINARY |
114 | 3.39275 | 13 | Latin 1 / Western European | English - United States | BINARY |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
ole32.dll |
Total processes
57
Monitored processes
11
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2436 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1456 | C:\Users\admin\AppData\Local\Temp\omcixlt\DrvSetup.exe | C:\Users\admin\AppData\Local\Temp\omcixlt\DrvSetup.exe | Setup.exe | ||||||||||||
User: admin Company: Dell Inc Integrity Level: HIGH Description: DrvSetup Module Exit code: 0 Version: 7, 3, 450, 0 Modules
| |||||||||||||||
| 1520 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\AppData\Local\Temp\Dell-Bios-inventory.exe" | C:\Users\admin\AppData\Local\Temp\Dell-Bios-inventory.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2340 | cmd /c C:\Users\admin\AppData\Local\Temp\deldccu.bat | C:\Windows\system32\cmd.exe | — | Dell-Bios-inventory.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
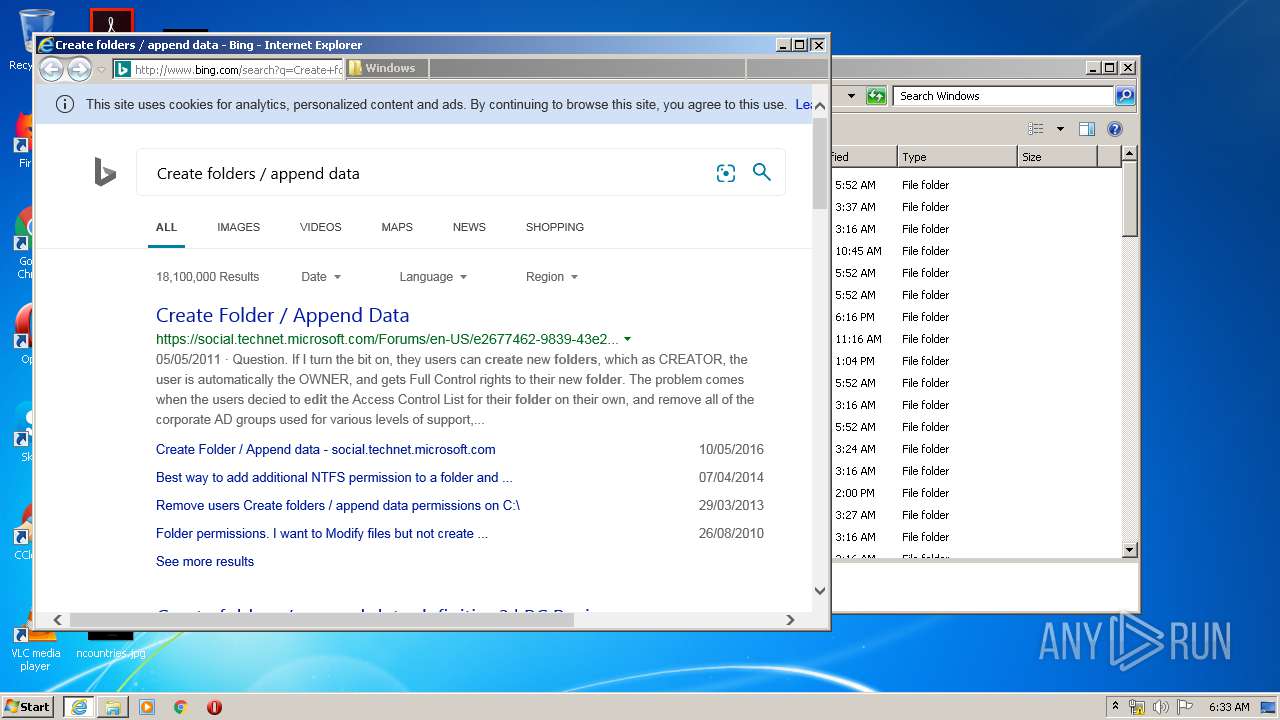
| 2436 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.bing.com/search?q=Create+folders+%2F+append+data&src=IE-TopResult&FORM=IE11TR&conversationid= | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2704 | DrvInst.exe "2" "211" "ROOT\SYSTEM\0001" "C:\Windows\INF\oem4.inf" "dellomci.inf:MfgDeviceSection:OmciDriverInstall:7.7.0.841:root\omci" "6019da953" "000003FC" "000005D0" "000005D4" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{516eaf0a-6903-506d-635d-7f4396ca6868}\dellomci.inf" "0" "6019da953" "000003FC" "WinSta0\Default" "00000558" "208" "c:\program files\dell\dellsys" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2752 | C:\Users\admin\AppData\Local\Temp\OmcaClientModule32.exe -file:profile.xml | C:\Users\admin\AppData\Local\Temp\OmcaClientModule32.exe | Dell-Bios-inventory.exe | ||||||||||||
User: admin Company: Altiris, Inc Integrity Level: HIGH Description: OMCA Client Module Exit code: 0 Version: 3.1.1128 Modules
| |||||||||||||||
| 3500 | -l -s | C:\Users\admin\AppData\Local\Temp\omcixlt\Setup.exe | Dell-Bios-inventory.exe | ||||||||||||
User: admin Company: Dell Inc Integrity Level: HIGH Description: Setup Module Exit code: 0 Version: 7, 3, 450, 0 Modules
| |||||||||||||||
Total events
2 303
Read events
1 011
Write events
1 283
Delete events
9
Modification events
| (PID) Process: | (1812) Dell-Bios-inventory.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1812) Dell-Bios-inventory.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3500) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Dell\DellSys |
| Operation: | write | Name: | InfPath |
Value: C:\Program Files\Dell\DellSys | |||
| (PID) Process: | (1456) DrvSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (1456) DrvSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1456) DrvSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\CDD4EEAE6000AC7F40C3802C171E30148030C072 |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000014000000391BE92883D52509155BFEAE27B9BD340170B76B030000000100000014000000CDD4EEAE6000AC7F40C3802C171E30148030C0720B000000010000004A0000004D006900630072006F0073006F0066007400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F007200690074007900000069000000010000000E000000300C060A2B0601040182373C030220000000010000009D0500003082059930820381A003020102021079AD16A14AA0A5AD4C7358F407132E65300D06092A864886F70D0101050500305F31133011060A0992268993F22C6401191603636F6D31193017060A0992268993F22C64011916096D6963726F736F6674312D302B060355040313244D6963726F736F667420526F6F7420436572746966696361746520417574686F72697479301E170D3031303530393233313932325A170D3231303530393233323831335A305F31133011060A0992268993F22C6401191603636F6D31193017060A0992268993F22C64011916096D6963726F736F6674312D302B060355040313244D6963726F736F667420526F6F7420436572746966696361746520417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A0282020100F35DFA8067D45AA7A90C2C9020D035083C7584CDB707899C89DADECEC360FA91685A9E94712918767CC2E0C82576940E58FA043436E6DFAFF780BAE9580B2B93E59D05E3772291F734643C22911D5EE10990BC14FEFC755819E179B70792A3AE885908D89F07CA0358FC68296D32D7D2A8CB4BFCE10B48324FE6EBB8AD4FE45C6F139499DB95D575DBA81AB79491B4775BF5480C8F6A797D1470047D6DAF90F5DA70D847B7BF9B2F6CE705B7E11160AC7991147CC5D6A6E4E17ED5C37EE592D23C00B53682DE79E16DF3B56EF89F33C9CB527D739836DB8BA16BA295979BA3DEC24D26FF0696672506C8E7ACE4EE1233953199C835084E34CA7953D5B5BE6332594036C0A54E044D3DDB5B0733E458BFEF3F5364D842593557FD0F457C24044D9ED6387411972290CE684474926FD54B6FB086E3C73642A0D0FCC1C05AF9A361B9304771960A16B091C04295EF107F286AE32A1FB1E4CD033F777104C720FC490F1D4588A4D7CB7E88AD8E2DEC45DBC45104C92AFCEC869E9A11975BDECE5388E6E2B7FDAC95C22840DBEF0490DF813339D9B245A5238706A5558931BB062D600E41187D1F2EB597CB11EB15D524A594EF151489FD4B73FA325BFCD13300F95962700732EA2EAB402D7BCADD21671B30998F16AA23A841D1B06E119B36C4DE40749CE15865C1601E7A5B38C88FBB04267CD41640E5B66B6CAA86FD00BFCEC1350203010001A351304F300B0603551D0F0404030201C6300F0603551D130101FF040530030101FF301D0603551D0E041604140EAC826040562797E52513FC2AE10A539559E4A4301006092B06010401823715010403020100300D06092A864886F70D01010505000382020100C5114D033A60DD5D5211778FB2BB36C8B205BFB4B7A8D8209D5C1303B61C22FA061335B6C863D49A476F2657D255F104B1265FD6A95068A0BCD2B86ECCC3E9ACDF19CD78AC5974AC663436C41B3E6C384C330E30120DA326FE515300FFAF5A4E840D0F1FE46D052E4E854B8D6C336F54D264ABBF50AF7D7A39A037ED63030FFC1306CE1636D4543B951B51623AE54D17D40539929A27A85BAABDECBBBEE3208960716C56B3A513D06D0E237E9503ED683DF2D863B86B4DB6E830B5E1CA944BF7A2AA5D9930B23DA7C2516C28200124272B4B00B79D116B70BEB21082BC0C9B68D08D3B2487AA9928729D335F5990BDF5DE939E3A625A3439E288551DB906B0C1896B2DD769C319123684D0C9A0DAFF2F6978B2E57ADAEBD70CC0F7BD6317B8391338A2365B7BF285566A1D6462C138E2AABF5166A294F5129C6622106BF2B730922DF229F03D3B144368A2F19C2937CBCE3820256D7C67F37E24122403088147ECA59E97F518D7CFBBD5EF7696EFFDCEDB569D95A042F99758E1D73122D35F59E63E6E2200EA4384B625DBD9F3085668C0646B1D7CECB693A262576E2ED8E7588FC4314926DDDE293587F53071705B143C69BD89127DEB2EA3FED87F9E825A520A2BC1432BD930889FC810FB898DE6A18575337E6C9EDB7313646269A52F7DCA966D9FF8044D30923D6E211421C93DE0C3FD8A6B9D4AFDD1A19D9943773FB0DA | |||
| (PID) Process: | (1456) DrvSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\A43489159A520F0D93D032CCAF37E7FE20A8B419 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000100000008B3C3087B7056F5EC5DDBA91A1B901F069000000010000000E000000300C060A2B0601040182373C03020B00000001000000320000004D006900630072006F0073006F0066007400200052006F006F007400200041007500740068006F0072006900740079000000030000000100000014000000A43489159A520F0D93D032CCAF37E7FE20A8B41920000000010000001604000030820412308202FAA003020102020F00C1008B3C3C8811D13EF663ECDF40300D06092A864886F70D01010405003070312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E3121301F060355040313184D6963726F736F667420526F6F7420417574686F72697479301E170D3937303131303037303030305A170D3230313233313037303030305A3070312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E3121301F060355040313184D6963726F736F667420526F6F7420417574686F7269747930820122300D06092A864886F70D01010105000382010F003082010A0282010100A902BDC170E63BF24E1B289F97785E30EAA2A98D255FF8FE954CA3B7FE9DA2203E7C51A29BA28F60326BD1426479EEAC76C954DAF2EB9C861C8F9F8466B3C56B7A6223D61D3CDE0F0192E896C4BF2D669A9A682699D03A2CBF0CB55826C146E70A3E38962CA92839A8EC498342E3840FBB9A6C5561AC827CA1602D774CE999B4643B9A501C310824149FA9E7912B18E63D986314605805659F1D375287F7A7EF9402C61BD3BF5545B38980BF3AEC54944EAEFDA77A6D744EAF18CC96092821005790606937BB4B12073C56FF5BFBA4660A08A6D2815657EFB63B5E16817704DAF6BEAE8095FEB0CD7FD6A71A725C3CCABCF008A32230B30685C9B320771385DF0203010001A381A83081A53081A20603551D0104819A30819780105BD070EF69729E23517E14B24D8EFFCBA1723070312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E3121301F060355040313184D6963726F736F667420526F6F7420417574686F72697479820F00C1008B3C3C8811D13EF663ECDF40300D06092A864886F70D0101040500038201010095E80BC08DF3971835EDB80124D87711F35C60329F9E0BCB3E0591888FC93AE621F2F057932CB5A047C862EFFCD7CC3B3B5AA9365469FE246D3FC9CCAADE057CDD318D3D9F10706ABBFE124F1869C0FCD043E3115A204FEA627BAFAA19C82B37252DBE65A1128A250F63A3F7541CF921C9D615F352AC6E433207FD8217F8E5676C0D51F6BDF152C7BDE7C430FC203109881D95291A4DD51D02A5F180E003B45BF4B1DDC857EE6549C75254B6B4032812FF90D6F0088F7EB897C5AB372CE47AE4A877E376A000D06A3FC1D2368AE04112A8356A1B6ADB35E1D41C04E4A84504C85A33386E4D1C0D62B70AA28CD3D5543F46CD1C55A670DB123A8793759FA7D2A0 | |||
| (PID) Process: | (1456) DrvSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\7F88CD7223F3C813818C994614A89C99FA3B5247 |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000010000000D67576F5521D1CCAB52E9215E0F9F7430B00000001000000400000004D006900630072006F0073006F00660074002000410075007400680065006E007400690063006F0064006500280074006D002900200052006F006F0074000000090000000100000016000000301406082B0601050507030406082B060105050703030300000001000000140000007F88CD7223F3C813818C994614A89C99FA3B52472000000001000000DA030000308203D6308202BEA003020102020101300D06092A864886F70D01010405003050310B3009060355040613025553310D300B060355040A13044D53465431323030060355040313294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F72697479301E170D3935303130313038303030315A170D3939313233313233353935395A3050310B3009060355040613025553310D300B060355040A13044D53465431323030060355040313294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F7269747930820122300D06092A864886F70D01010105000382010F003082010A0282010100DF08BAE33F6E649BF589AF28964A078F1B2E8B3E1DFCB88069A3A1CEDBDFB08E6C8976294FCA603539AD7232E00BAE293D4C16D94B3C9DDAC5D3D109C92C6FA6C2605345DD4BD155CD031CD2595624F3E578D807CCD8B31F903FC01A71501D2DA712086D7CB0866CC7BA853207E1616FAF03C56DE5D6A18F36F6C10BD13E69974872C97FA4C8C24A4C7EA1D194A6D7DCEB05462EB818B4571D8649DB694A2C21F55E0F542D5A43A97A7E6A8E504D2557A1BF1B1505437B2C058DBD3D038C93227D63EA0A5705060ADB6198652D4749A8E7E656755CB8640863A9304066B2F9B6E334E86730E1430B87FFC9BE72105E23F09BA74865BF09887BCD72BC2E799B7B0203010001A381BA3081B7300D0603551D0A040630040302078030320603550403042B13294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F7269747930720603551D01046B306980101A1BE75B9FFD8C2AC339AE0C622E5332A1523050310B3009060355040613025553310D300B060355040A13044D53465431323030060355040313294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F72697479820101300D06092A864886F70D010104050003820101002DC9E2F6129E5D5667FAFA4B9A7EDC29565C80140228856E26F3CD58DA5080C5F819B3A67CE29D6B5F3B8F2274E61804FC4740D87A3F3066F012A4D1EB1DE7B6F498AB5322865158EE230976E41D455C4BFF4CE302500113CC41A45297D486D5C4FE8383657DEABEA2683BC1B12998BFA2A5FC9DD384EE701750F30BFA3CEFA9278B91B448C845A0E101424B4476041CC219A28E6B2098C4DD02ACB4D2A20E8D5DB9368E4A1B5D6C1AE2CB007F10F4B295EFE3E8FFA17358A9752CA2499585FECCDA448AC21244D244C8A5A21FA95A8E56C2C37BCF4260DC821FFBCE74067ED6F1AC196A4F745CC51566316CC16271910F595B7D2A821ADFB1B4D81D37DE0D0F | |||
| (PID) Process: | (1456) DrvSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\3B1EFD3A66EA28B16697394703A72CA340A05BD5 |
| Operation: | write | Name: | Blob |
Value: 0F000000010000002000000008FBA831C08544208F5208686B991CA1B2CFC510E7301784DDF1EB5BF039323969000000010000000E000000300C060A2B0601040182373C03020B00000001000000540000004D006900630072006F0073006F0066007400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F0072006900740079002000320030003100300000000300000001000000140000003B1EFD3A66EA28B16697394703A72CA340A05BD52000000001000000F1050000308205ED308203D5A003020102021028CC3A25BFBA44AC449A9B586B4339AA300D06092A864886F70D01010B0500308188310B3009060355040613025553311330110603550408130A57617368696E67746F6E3110300E060355040713075265646D6F6E64311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E31323030060355040313294D6963726F736F667420526F6F7420436572746966696361746520417574686F726974792032303130301E170D3130303632333231353732345A170D3335303632333232303430315A308188310B3009060355040613025553311330110603550408130A57617368696E67746F6E3110300E060355040713075265646D6F6E64311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E31323030060355040313294D6963726F736F667420526F6F7420436572746966696361746520417574686F72697479203230313030820222300D06092A864886F70D01010105000382020F003082020A0282020100B9089E28E4E4EC064E5068B341C57BEBAEB68EAF81BA22441F6534694CBE704017F2167BE279FD86ED0D39F41BA8AD92901ECB3D768F5AD9B591102E3C058D8A6D2454E71FED56AD83B4509C15A51774885920FC08C58476D368D46F2878CE5CB8F3509044FFE3635FBEA19A2C961504D607FE1E8421E0423111C4283694CF50A4629EC9D6AB7100B25B0CE696D40A2496F5FFC6D5B71BD7CBB72162AF12DCA15D37E31AFB1A4698C09BC0E7631F2A0893027E1E6A8EF29F1889E42285A2B1845740FFF50ED86F9CEDE2453101CD17E97FB08145E3AA214026A172AAA74F3C01057EEE8358B15E06639962917882B70D930C246AB41BDB27EC5F95043F934A30F59718B3A7F919A793331D01C8DB22525CD725C946F9A2FB875943BE9B62B18D2D86441A46AC78617E3009FAAE89C4412A2266039139459CC78B0CA8CA0D2FFB52EA0CF76333239DFEB01FAD67D6A75003C6047063B52CB1865A43B7FBAEF96E296E21214126068CC9C3EEB0C28593A1B985D9E6326C4B4C3FD65DA3E5B59D77C39CC055B77400E3B838AB839750E19A42241DC6C0A330D11A5AC85234F773F1C7181F33AD7AECCB4160F3239420C24845AC5C51C62E80C2E27715BD8587ED369D9691EE00B5A370EC9FE38D80688376BAAF5D70522216E266FBBAB3C5C2F73E2F77A6CADEC1A6C6484CC3375123D327D7B84E7096F0A14476AF78CF9AE166130203010001A351304F300B0603551D0F040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414D5F656CB8FE8A25C6268D13D94905BD7CE9A18C4301006092B06010401823715010403020100300D06092A864886F70D01010B05000382020100ACA5968CBFBBAEA6F6D7718743315688FD1C32715B35B7D4F091F2AF37E214F1F30226053E16147F14BAB84FFB89B2B2E7D409CC6DB95B3B64657066B7F2B15ADF1A02F3F551B8676D79F3BF567BE484B92B1E9B409C2634F947189869D81CD7B6D1BF8F61C267C4B5EF60438E101B3649E420CAADA7C1B1276509F8CDF55B2AD08433F3EF1FF2F59C0B589337A075A0DE72DE6C752A6622F58C0630569F40B930AA40771582D78BECC0D3B2BD83C5770C1EAEAF1953A04D79719F0FAF30CE67F9D62CCC22417A07F2974218CE59791055DE6F10E4B8DA836640160968235B972E269A02BB578CC5B8BA69623280899EA1FDC0927C7B2B3319842A63C5006862FA9F478D997A453AA7E9EDEE6942B5F3819B4756107BFC7036841873EAEFF9974D9E3323DD260BBA2AB73F44DC8327FFBD61592B11B7CA4FDBC58B0C1C31AE32F8F8B942F77FDC619A76B15A04E1113D6645B71871BEC92485D6F3D4BA41345D122D25B98DA613486D4BB0077D99930961817457268AAB69E3E4D9C788CC24D8EC52245C1EBC9114E296DEEB0ADA9EDD5FB35BDBD482ECC620508725403AFBC7EECDFE33E56EC3840955032539C0E9355D6531A8F6BFA009CD29C7B336322EDC95F383C15ACF8B8DF6EAB321F8A4ED1E310EB64C11AB600BA412232217A3366482910412E0AB6F1ECB500561B440FF598671D1D533697CA9738A38D7640CF169 | |||
| (PID) Process: | (1456) DrvSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\245C97DF7514E7CF2DF8BE72AE957B9E04741E85 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000100000009DF0D13100123AECA770130F4AD8D209030000000100000014000000245C97DF7514E7CF2DF8BE72AE957B9E04741E8509000000010000000C000000300A06082B060105050703080B00000001000000320000004D006900630072006F0073006F00660074002000540069006D0065007300740061006D007000200052006F006F00740000002000000001000000B1020000308202AD30820216020101300D06092A864886F70D010104050030819E3120301E060355040A13174D6963726F736F6674205472757374204E6574776F726B311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E312D302B060355040B13244D6963726F736F66742054696D65205374616D70696E67205365727669636520526F6F74312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E301E170D3937303531333136313235395A170D3939313233303233353935395A30819E3120301E060355040A13174D6963726F736F6674205472757374204E6574776F726B311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E312D302B060355040B13244D6963726F736F66742054696D65205374616D70696E67205365727669636520526F6F74312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E30819F300D06092A864886F70D010101050003818D0030818902818100B75A38F51F37CCA943C4DC2418BEF28552B41D5B5F18B90B8F4B6DA8FFCD40506CD3A0D35C47C2B9F786E4CD7D350569371FAF3DDD1FFD8F1534C2C479CC59748A6F8C0EC3E811EB8438479853E1F10C0DE4010CF01B1E20DA2A7A3DC215528E8AFF7B32BF581E25988326CB8AC9C4071424BC499ED77AB3871A2533BC6D08470203010001300D06092A864886F70D010104050003818100505BC56B6F8D525B0DC9BDAC347398CA0A87CAAE4C4ABA14A4EB52709521E0B5A1604EF743025101AF1E3A70CEBF18B686289967EB08E897405C1682FDB825FB366F6F763EC54C8EE2A751FACAC163BA5E8324470B9372F6449ACEA7953A8F50109E1DB15916ABCF3EDF838BC7FAC36BDC649F402B1F452404AE492FF6DF0C91 | |||
Executable files
13
Suspicious files
32
Text files
136
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\XLT.cab | — | |
MD5:— | SHA256:— | |||
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\ClientExec.cab | — | |
MD5:— | SHA256:— | |||
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\DCMStandaloneSvc.cab | — | |
MD5:— | SHA256:— | |||
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\omcixlt\DellSys.dll | executable | |
MD5:— | SHA256:— | |||
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\omcixlt\omci.cat | cat | |
MD5:— | SHA256:— | |||
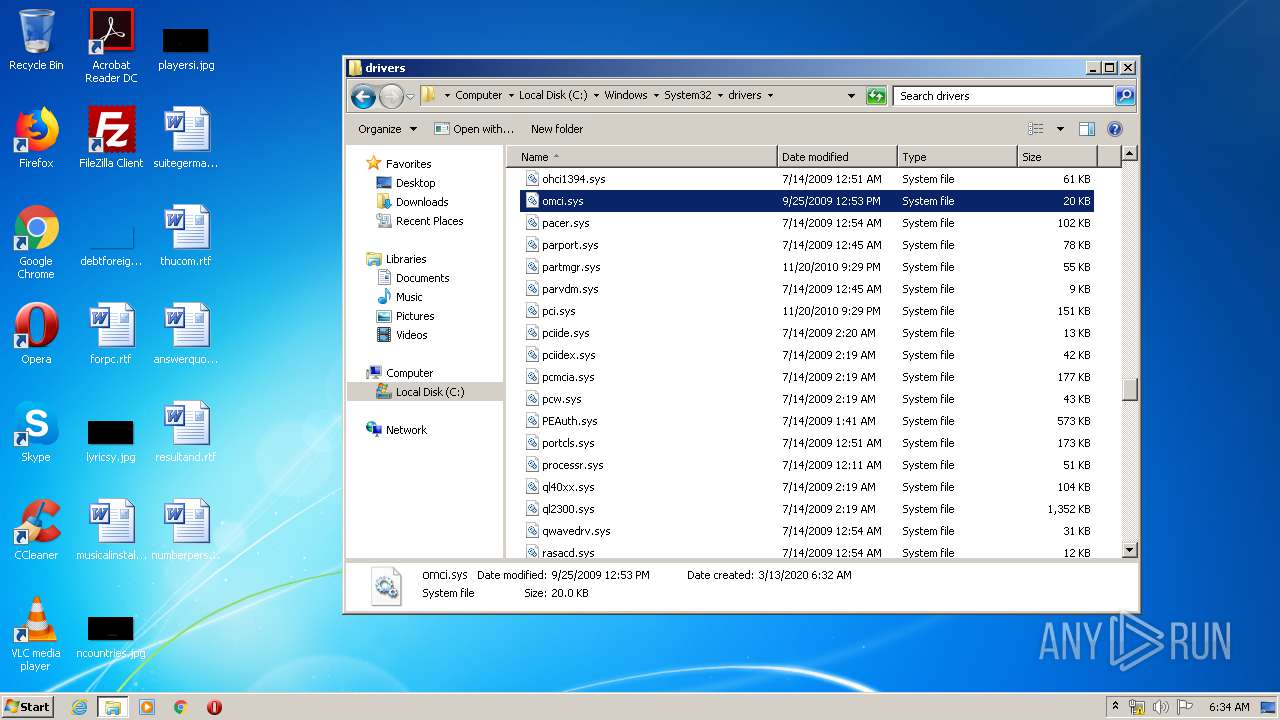
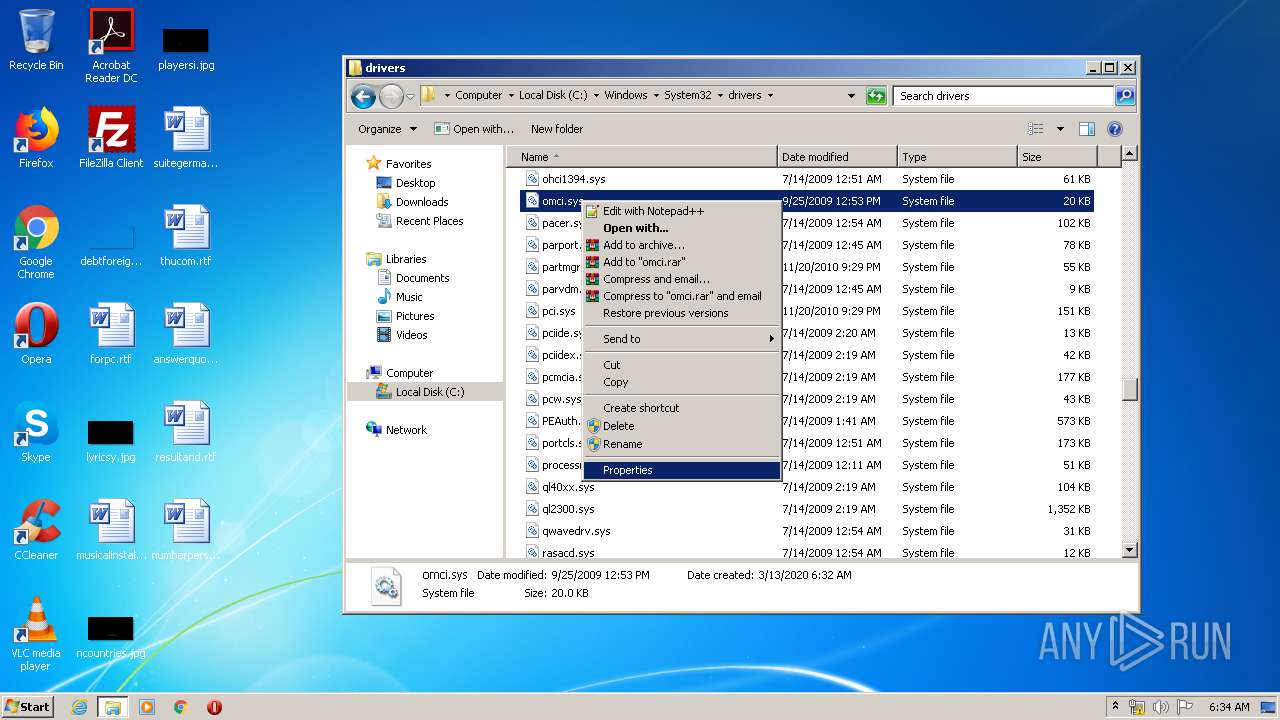
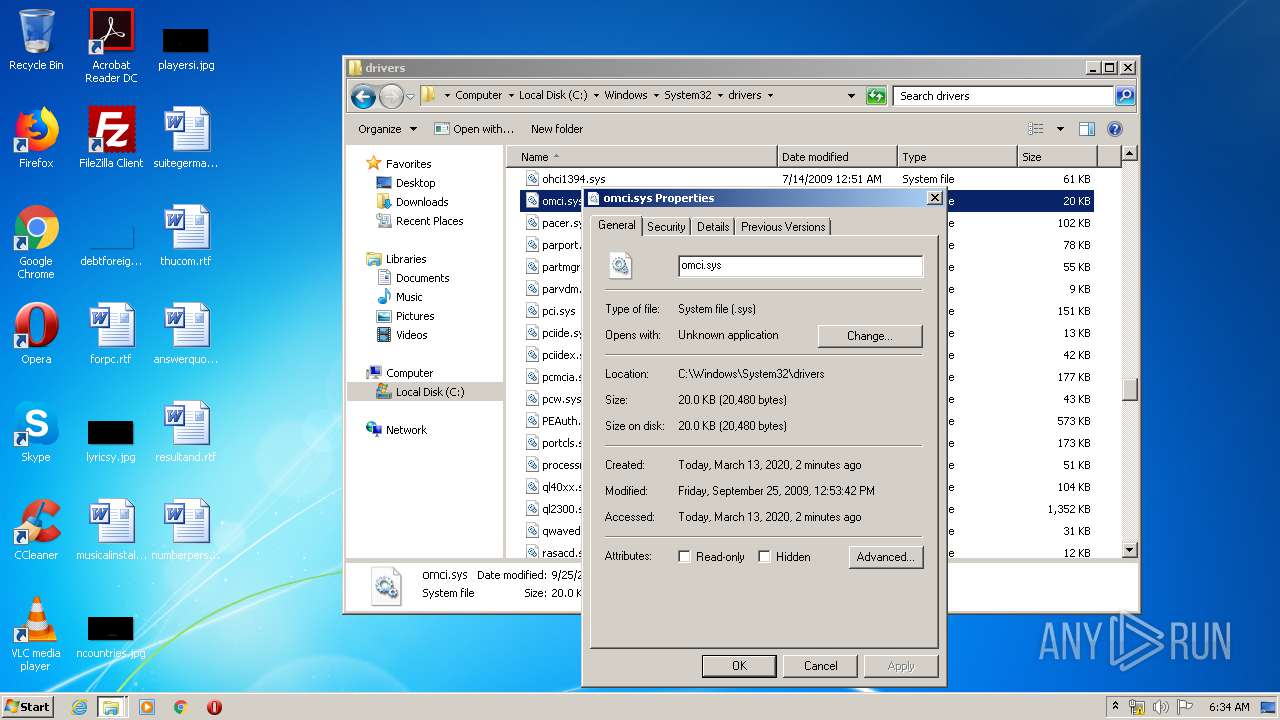
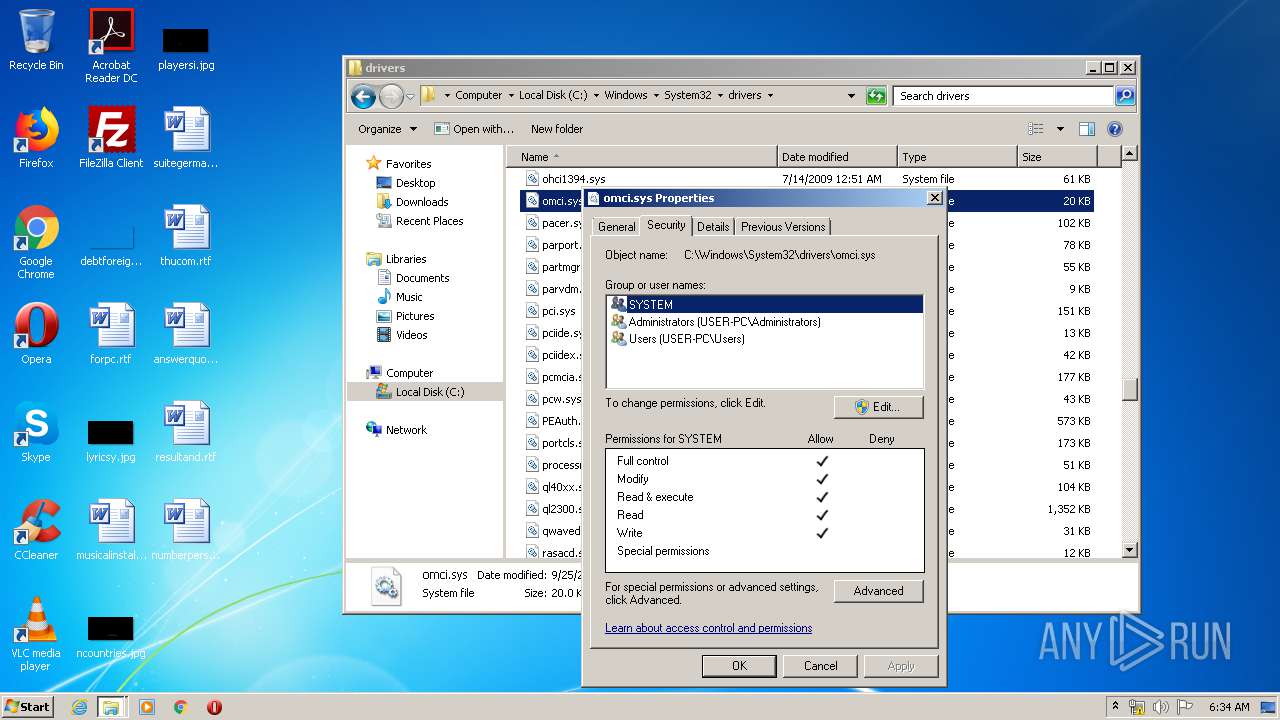
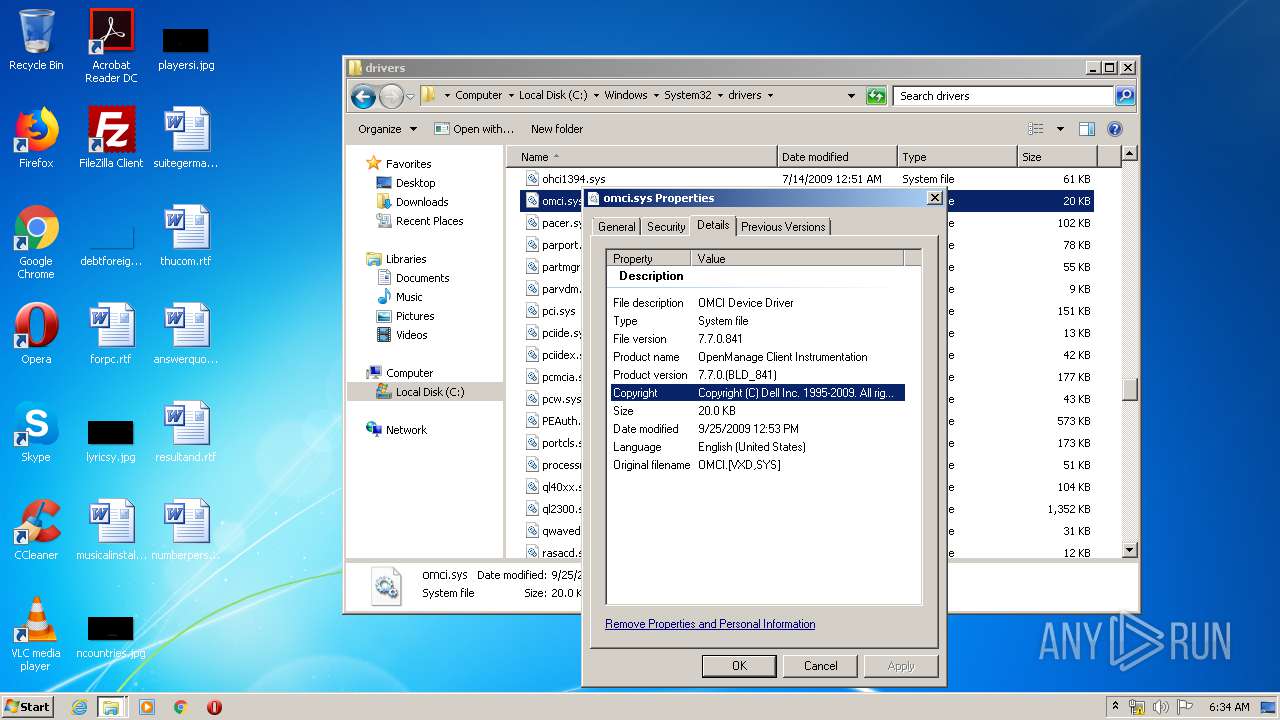
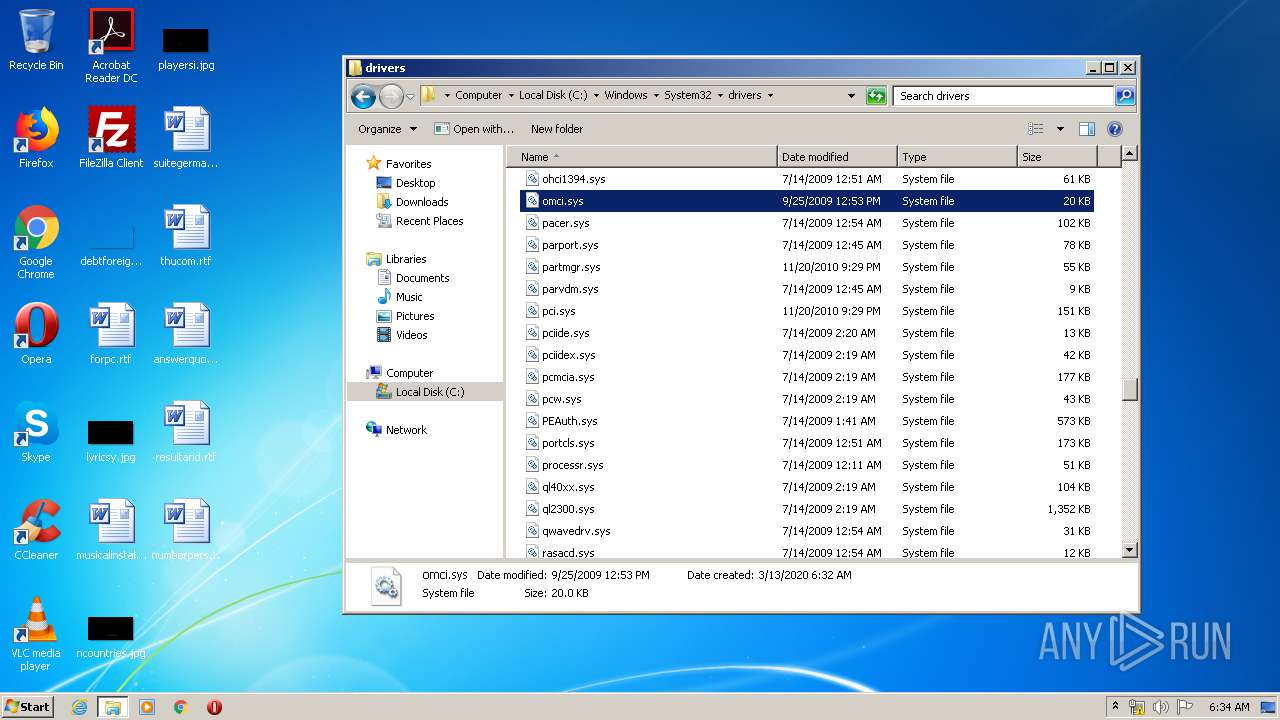
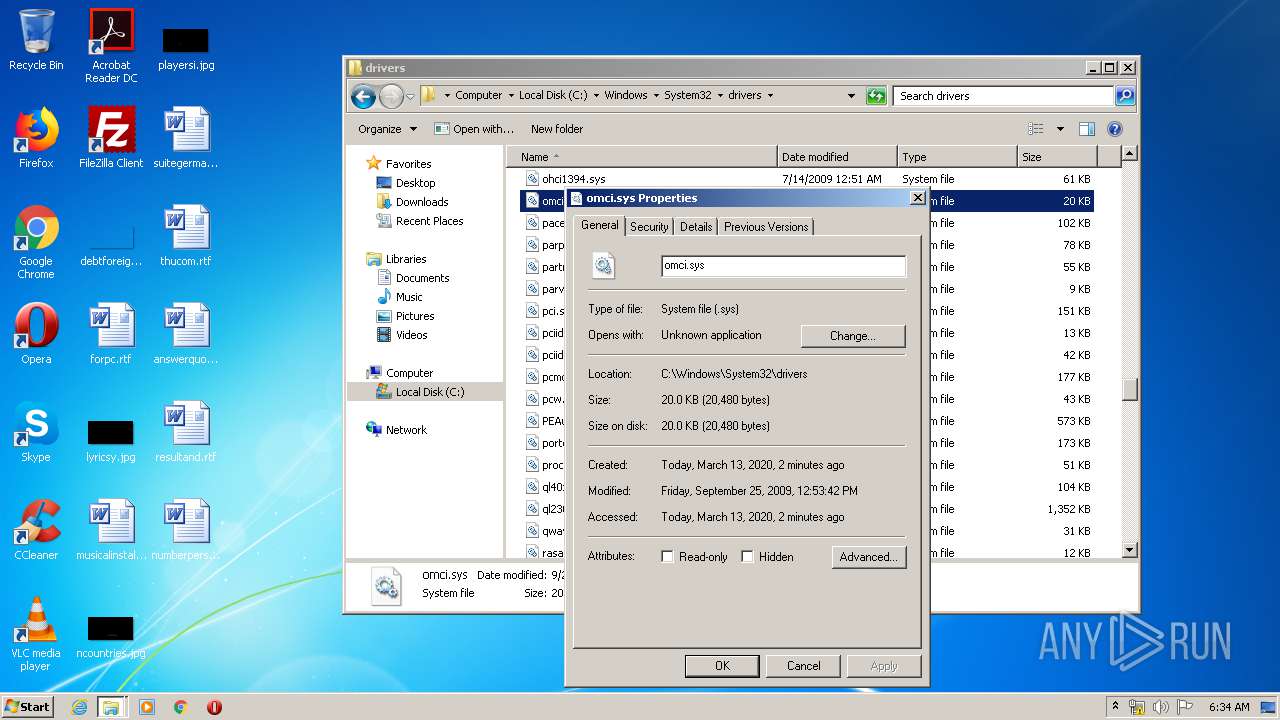
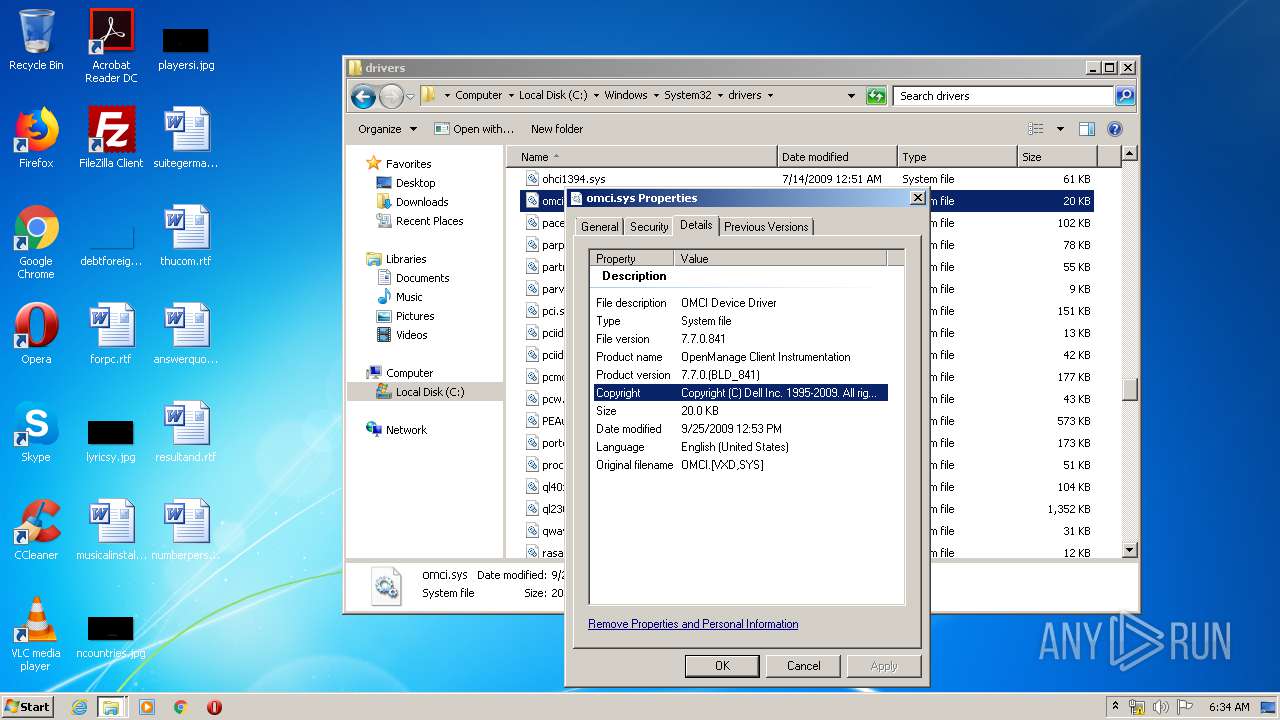
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\omcixlt\omci.sys | executable | |
MD5:— | SHA256:— | |||
| 1456 | DrvSetup.exe | C:\Users\admin\AppData\Local\Temp\{516eaf0a-6903-506d-635d-7f4396ca6868}\SET7DB4.tmp | — | |
MD5:— | SHA256:— | |||
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\OmcaClientModule32.exe | executable | |
MD5:— | SHA256:— | |||
| 1456 | DrvSetup.exe | C:\Users\admin\AppData\Local\Temp\{516eaf0a-6903-506d-635d-7f4396ca6868}\SET7DB5.tmp | — | |
MD5:— | SHA256:— | |||
| 1812 | Dell-Bios-inventory.exe | C:\Users\admin\AppData\Local\Temp\omcixlt\DrvSetup.exe | executable | |
MD5:9652BAF3E8A0BFA260DFFF0169197255 | SHA256:C4F13B39F3B501350E6C8350A94E86094A11BCC3C9D11568350D4A3691957B3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
27
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktop_TealSpyglassUpdate_2x_021820.png | US | image | 11.2 Kb | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6D/wg/nj/d695a46a/a9b12688.js | US | text | 353 b | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=Create+folders+%2F+append+data&src=IE-TopResult&FORM=IE11TR&conversationid= | US | html | 45.4 Kb | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/4V/3p/cj,nj/8e81c8c7/37f3511b.js | US | text | 529 b | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/4V/bw/cj,nj/be2cb8dd/68177b13.js | US | text | 759 b | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/58/30/cj,nj/4df0cf24/0120f753.js | US | text | 2.92 Kb | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6k/5v/cj,nj/a9e57fe1/1f2a14b8.js | US | text | 1.83 Kb | whitelisted |
576 | iexplore.exe | POST | 204 | 204.79.197.200:80 | http://www.bing.com/fd/ls/lsp.aspx? | US | compressed | 45.4 Kb | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/48/9/cj,nj/64cc4a49/e70a8ff8.js | US | text | 354 b | whitelisted |
576 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/2z/cj,nj/bf587ad6/f1d86b5a.js | US | text | 181 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
576 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
576 | iexplore.exe | 20.190.129.2:443 | login.microsoftonline.com | Microsoft Corporation | US | unknown |
2436 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
576 | iexplore.exe | 40.90.22.191:443 | login.live.com | Microsoft Corporation | US | malicious |
576 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
576 | iexplore.exe | 13.107.3.254:80 | 582d46a1c1c6080ac107ff244c280232.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
576 | iexplore.exe | 104.18.24.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
576 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
576 | iexplore.exe | 13.66.167.250:80 | 16cc56df71cae9d42b3bf14ff444086b.clo.footprintdns.com | Microsoft Corporation | US | unknown |
2436 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
582d46a1c1c6080ac107ff244c280232.clo.footprintdns.com |
| suspicious |
16cc56df71cae9d42b3bf14ff444086b.clo.footprintdns.com |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Dell-Bios-inventory.exe | fn_CheckOS: Operating System supported |
Dell-Bios-inventory.exe | Information on cabinet file '.\XLT.cab'
Total length of cabinet file : 136716
Number of folders in cabinet : 1
Number of files in cabinet : 6
Cabinet set ID : 0
Cabinet number in set : 0
RESERVE area in cabinet? : no
Chained to prev cabinet? : no
Chained to next cabinet? : no
|
Dell-Bios-inventory.exe | Information on cabinet file '.\XLT.cab'
Total length of cabinet file : 136716
Number of folders in cabinet : 1
Number of files in cabinet : 6
Cabinet set ID : 0
Cabinet number in set : 0
RESERVE area in cabinet? : no
Chained to prev cabinet? : no
Chained to next cabinet? : no
|
Dell-Bios-inventory.exe | Information on cabinet file '.\ClientExec.cab'
Total length of cabinet file : 235711
Number of folders in cabinet : 1
Number of files in cabinet : 1
Cabinet set ID : 0
Cabinet number in set : 0
RESERVE area in cabinet? : no
Chained to prev cabinet? : no
Chained to next cabinet? : no
|
Dell-Bios-inventory.exe | Information on cabinet file '.\DCMStandaloneSvc.cab'
Total length of cabinet file : 103047
Number of folders in cabinet : 1
Number of files in cabinet : 1
Cabinet set ID : 0
Cabinet number in set : 0
RESERVE area in cabinet? : no
Chained to prev cabinet? : no
Chained to next cabinet? : no
|
Dell-Bios-inventory.exe | Information on cabinet file '.\DCMStandaloneSvc.cab'
Total length of cabinet file : 103047
Number of folders in cabinet : 1
Number of files in cabinet : 1
Cabinet set ID : 0
Cabinet number in set : 0
RESERVE area in cabinet? : no
Chained to prev cabinet? : no
Chained to next cabinet? : no
|
Dell-Bios-inventory.exe | Information on cabinet file '.\ClientExec.cab'
Total length of cabinet file : 235711
Number of folders in cabinet : 1
Number of files in cabinet : 1
Cabinet set ID : 0
Cabinet number in set : 0
RESERVE area in cabinet? : no
Chained to prev cabinet? : no
Chained to next cabinet? : no
|
Dell-Bios-inventory.exe | fn_CreateInstallationFiles: All files created successfully. |
Dell-Bios-inventory.exe | BIOS image name is: Flash.hdr |
Dell-Bios-inventory.exe | OMCI XLT not already installed |