| URL: | http://evgeni7e.beget.tech |
| Full analysis: | https://app.any.run/tasks/b174e196-c3c8-4e9e-a659-f1c4d854c02a |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 08:10:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AE8E040F4C1742F222B0C53C009DEC16 |
| SHA1: | F061DCB0E550C5BA100C08DA98563B13D6D80530 |
| SHA256: | DEB98A7EB071AD0003CFBF223A130966FBCD65DFB167CCC7C716A04E909B7EEA |
| SSDEEP: | 3:N1KbwzACyRx:CszACyL |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 636)
INFO
Application launched itself
- chrome.exe (PID: 636)
Reads settings of System Certificates
- chrome.exe (PID: 636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://evgeni7e.beget.tech | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7006863420207857532 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7006863420207857532 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11466844003335221649 --mojo-platform-channel-handle=3756 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14432492168284791461 --mojo-platform-channel-handle=4032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10093091208031160921 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10093091208031160921 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --service-pipe-token=8076518067853529745 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8076518067853529745 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4653882520501665880 --mojo-platform-channel-handle=4116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --service-pipe-token=2363462892910469281 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2363462892910469281 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --service-pipe-token=16547718943242765485 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16547718943242765485 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,11341847121421366635,6546104172052626430,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17136307837116538275 --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
531
Read events
461
Write events
66
Delete events
4
Modification events
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 636-13200653468956125 |
Value: 259 | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (636) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
37
Text files
510
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0fec472a-4fb6-4dd4-a3b6-2d18094d7c0d.tmp | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
476
TCP/UDP connections
37
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
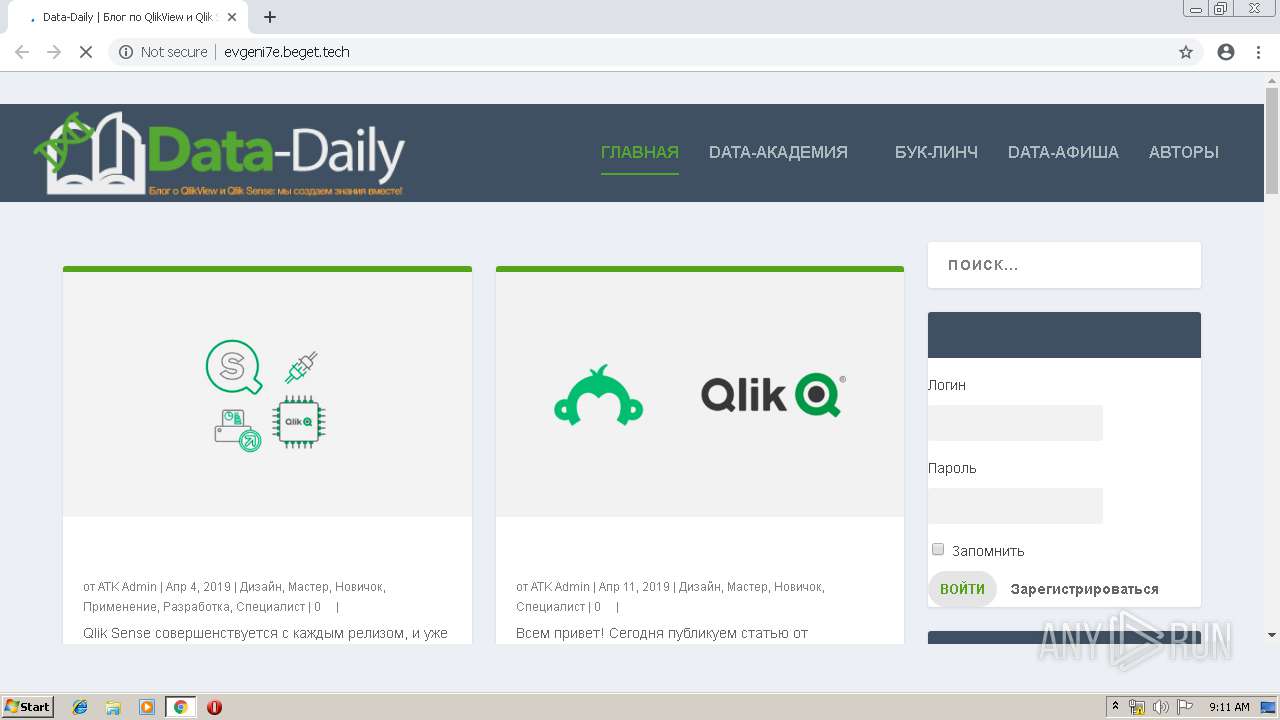
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://evgeni7e.beget.tech/wp-content/uploads/2017/04/DataDaily_logo_2017-new-design_white-reverse.png | RU | image | 6.75 Kb | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/themes/Extra/style.css?ver=2.0.33 | RU | text | 79.0 Kb | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/plugins/author-avatars/css/widget.css?ver=1.12 | RU | text | 297 b | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/plugins/author-avatars/css/shortcode.css?ver=1.12 | RU | text | 403 b | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/themes/Extra/epanel/shortcodes/css/shortcodes.css?ver=2.0.33 | RU | text | 5.65 Kb | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-includes/css/admin-bar.min.css?ver=4.8.3 | RU | text | 3.84 Kb | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/plugins/buddypress/bp-core/css/admin-bar.min.css?ver=2.9.1 | RU | text | 450 b | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/plugins/crayon-syntax-highlighter/css/min/crayon.min.css?ver=_2.7.2_beta | RU | text | 3.87 Kb | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/plugins/crayon-syntax-highlighter/fonts/monaco.css?ver=_2.7.2_beta | RU | text | 240 b | malicious |
636 | chrome.exe | GET | 200 | 87.236.19.193:80 | http://blog.atkcg.ru/wp-content/plugins/buddypress/bp-templates/bp-legacy/css/buddypress.min.css?ver=2.9.1 | RU | text | 6.74 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
636 | chrome.exe | 87.236.19.193:80 | evgeni7e.beget.tech | Beget Ltd | RU | malicious |
636 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 172.217.18.106:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 74.125.140.84:443 | accounts.google.com | Google Inc. | US | unknown |
636 | chrome.exe | 216.58.206.3:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 216.58.208.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 192.0.73.2:80 | www.gravatar.com | Automattic, Inc | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
evgeni7e.beget.tech |
| unknown |
blog.atkcg.ru |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
s.w.org |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.gravatar.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report