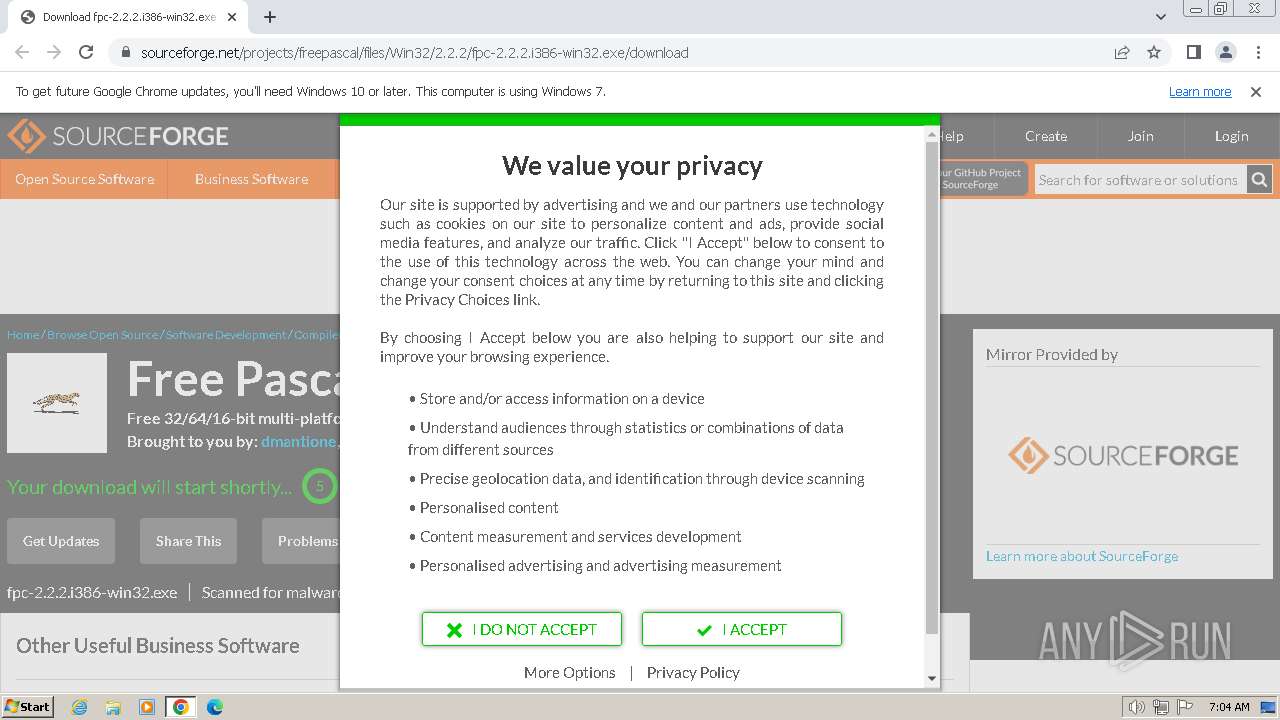
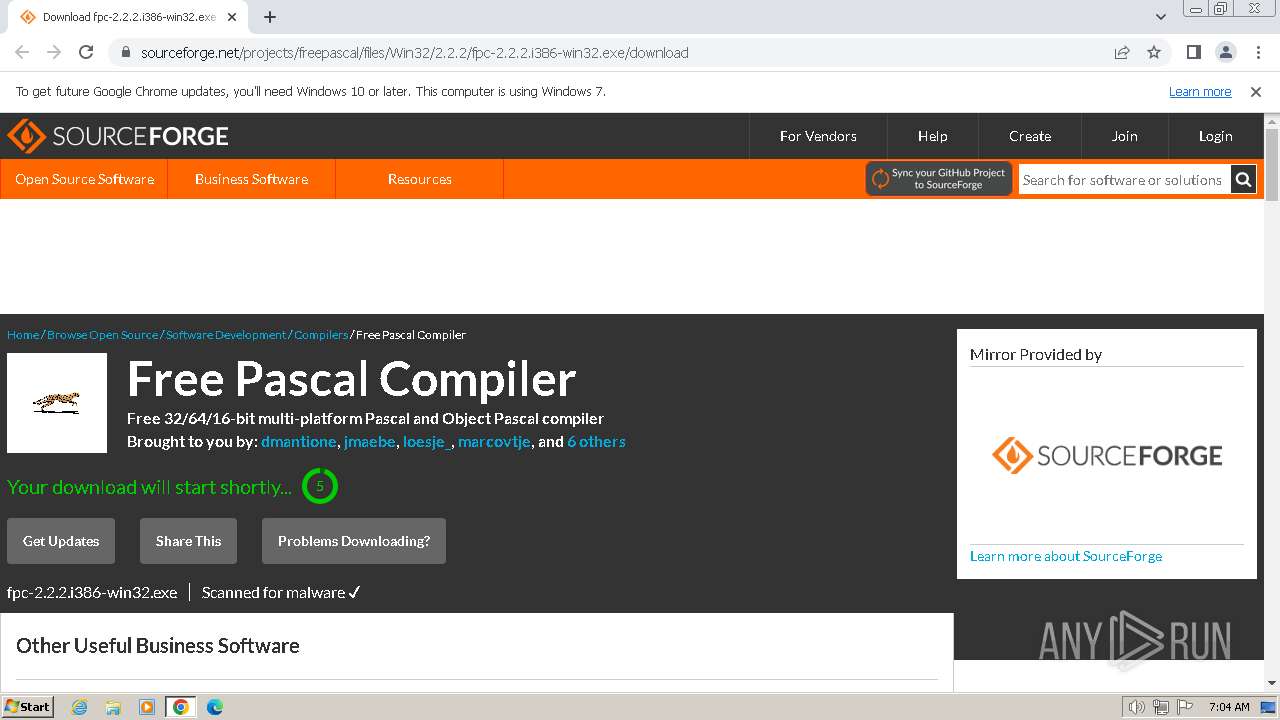
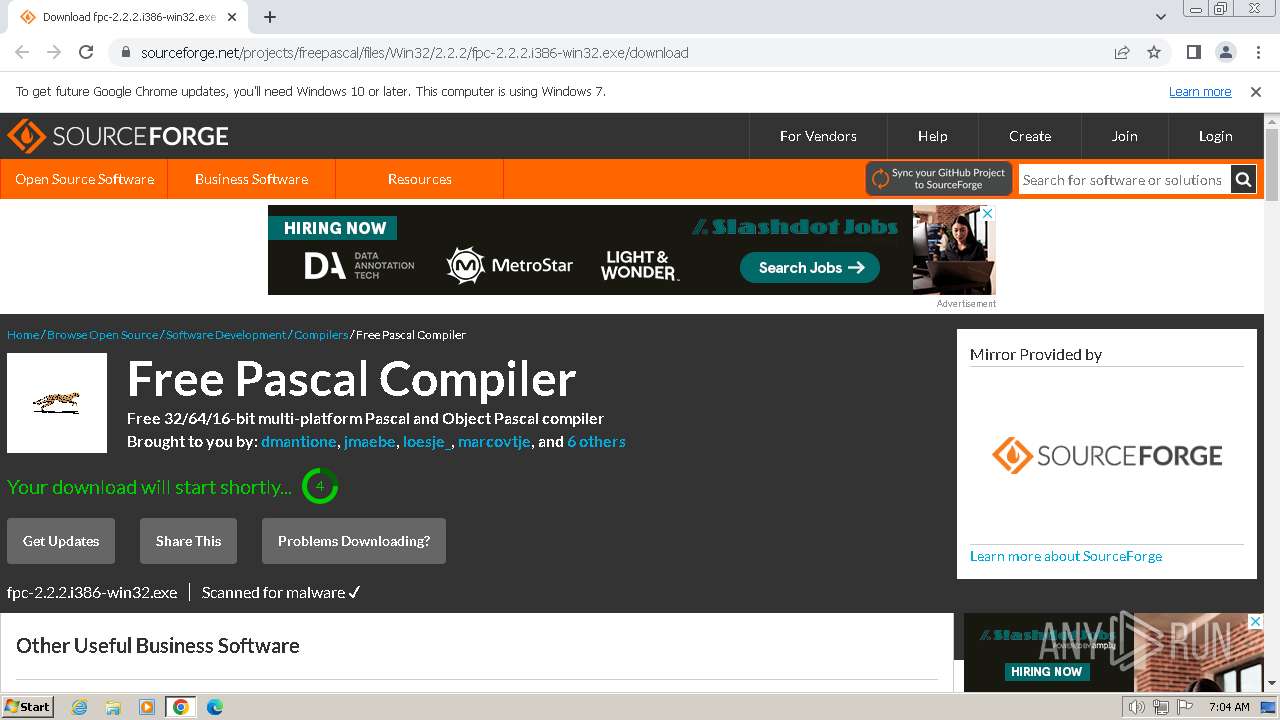
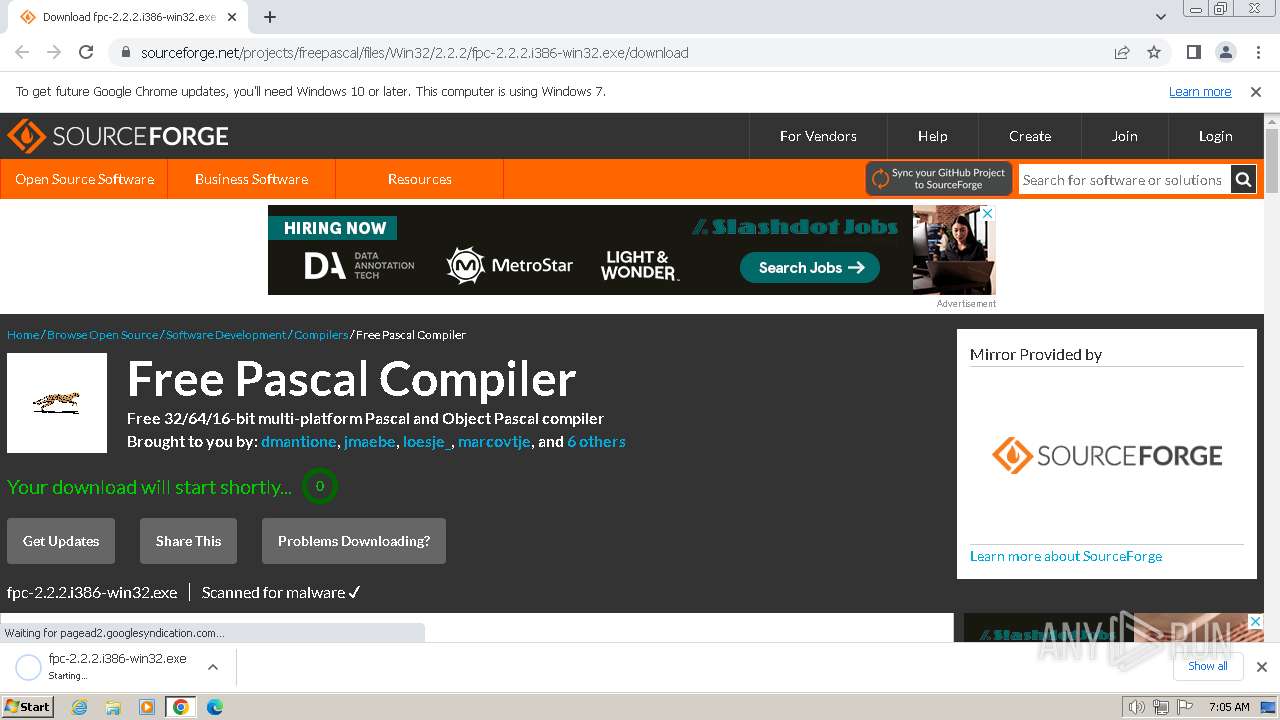
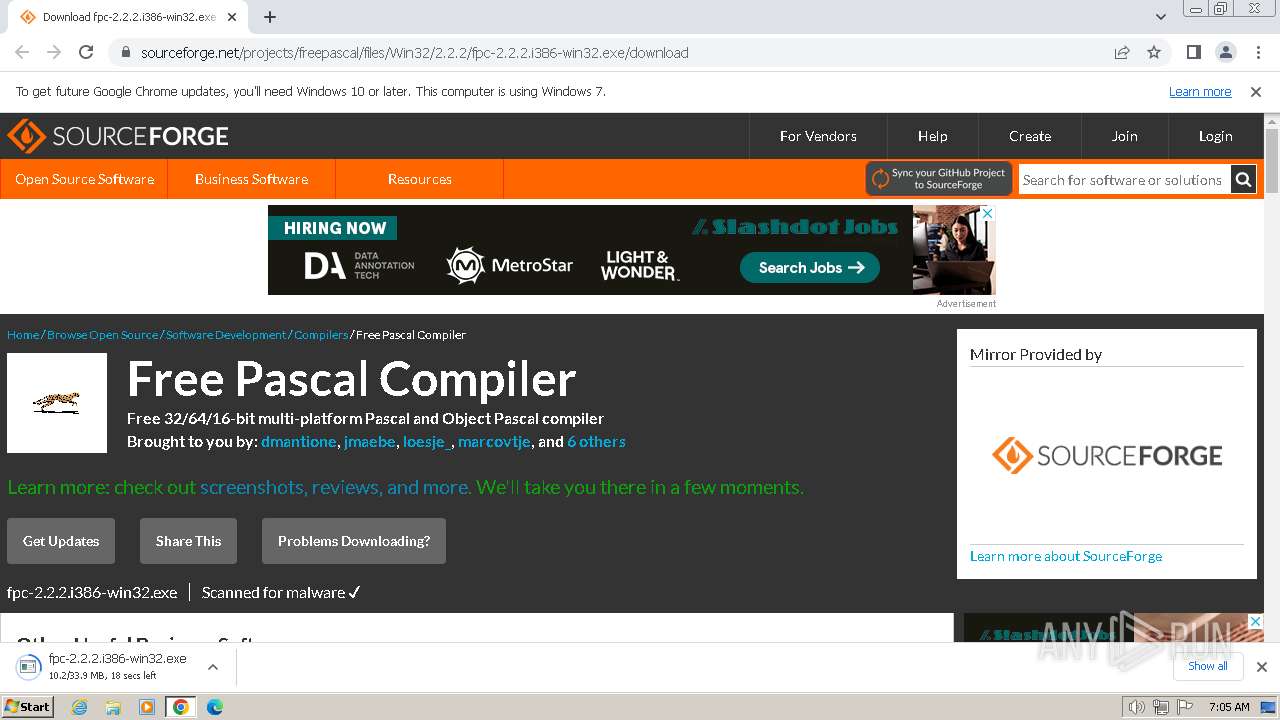
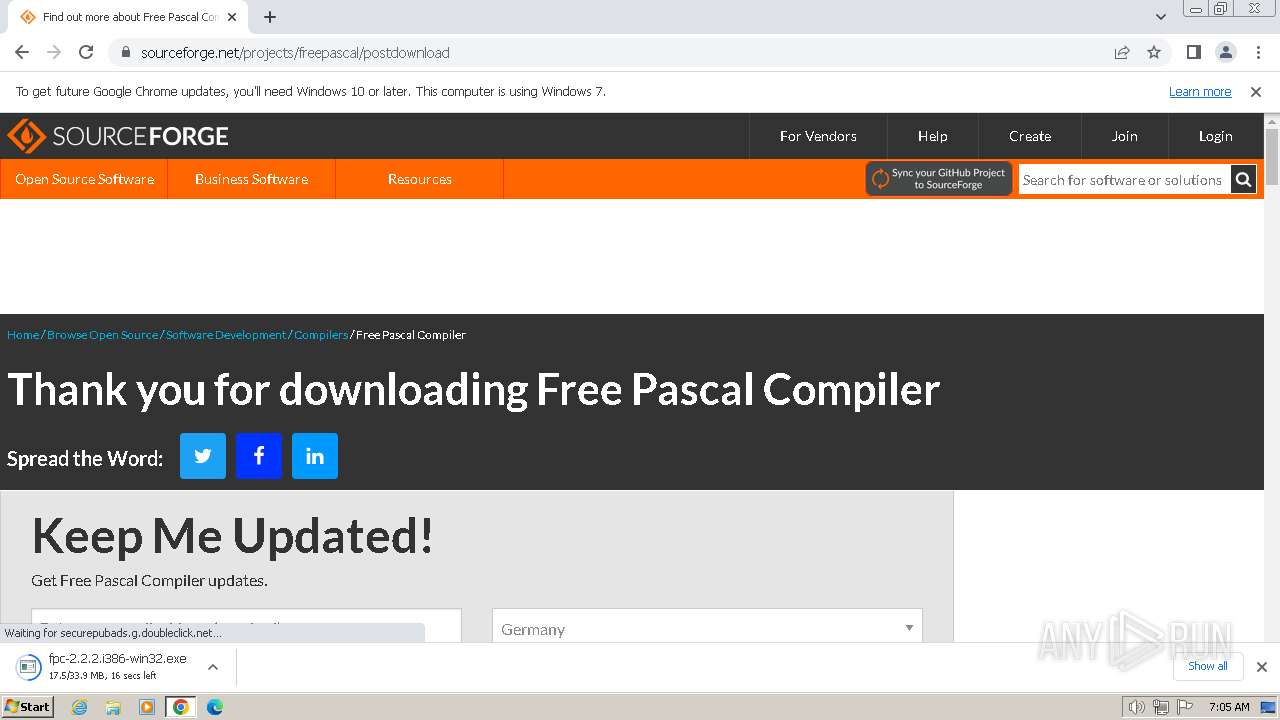
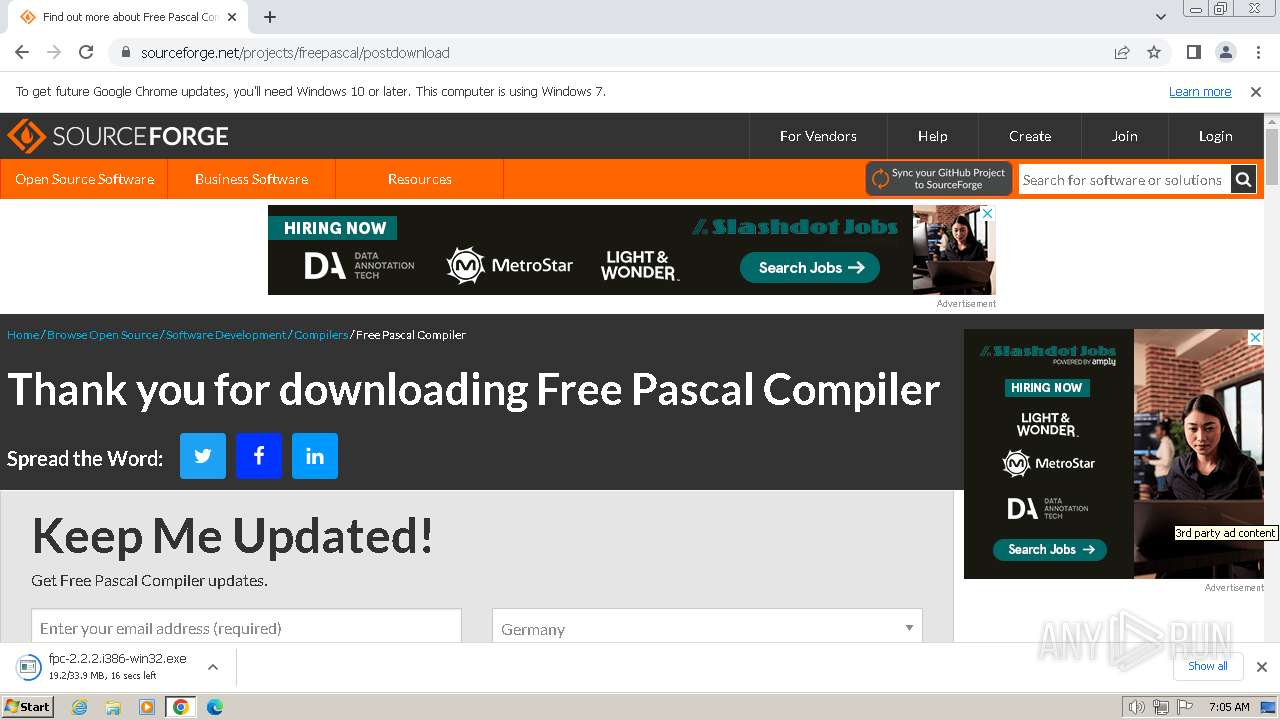
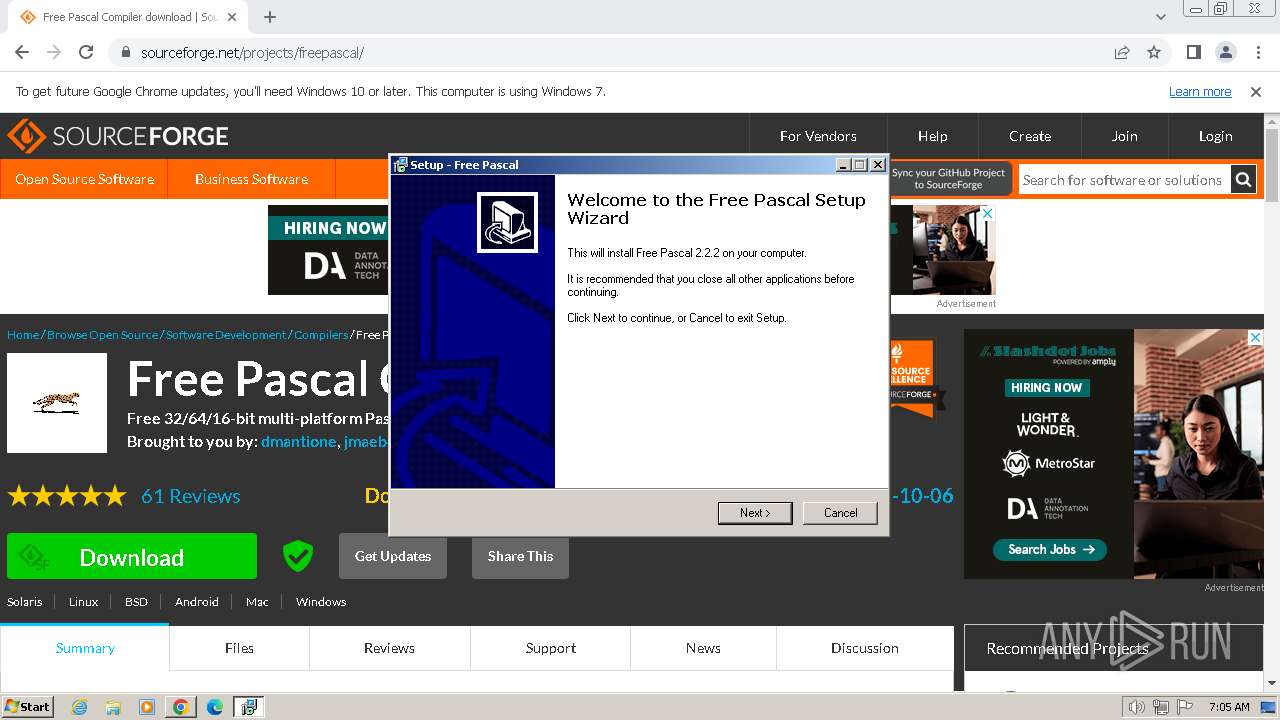
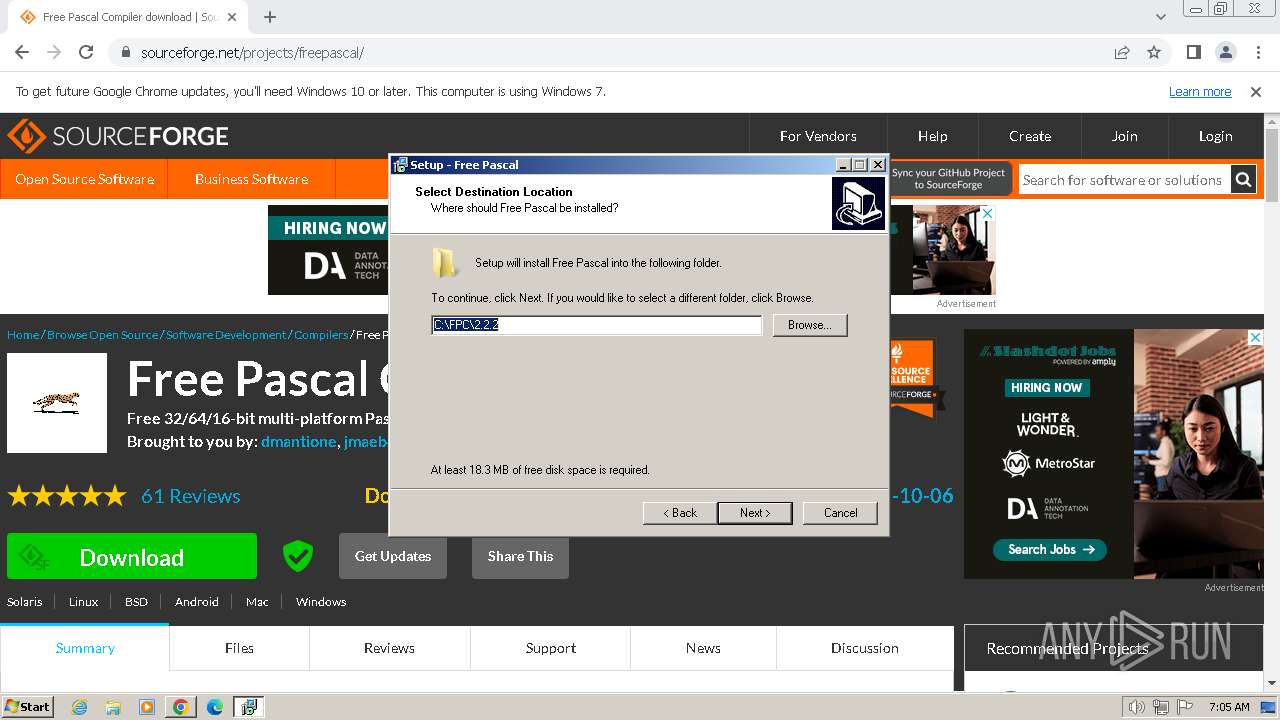
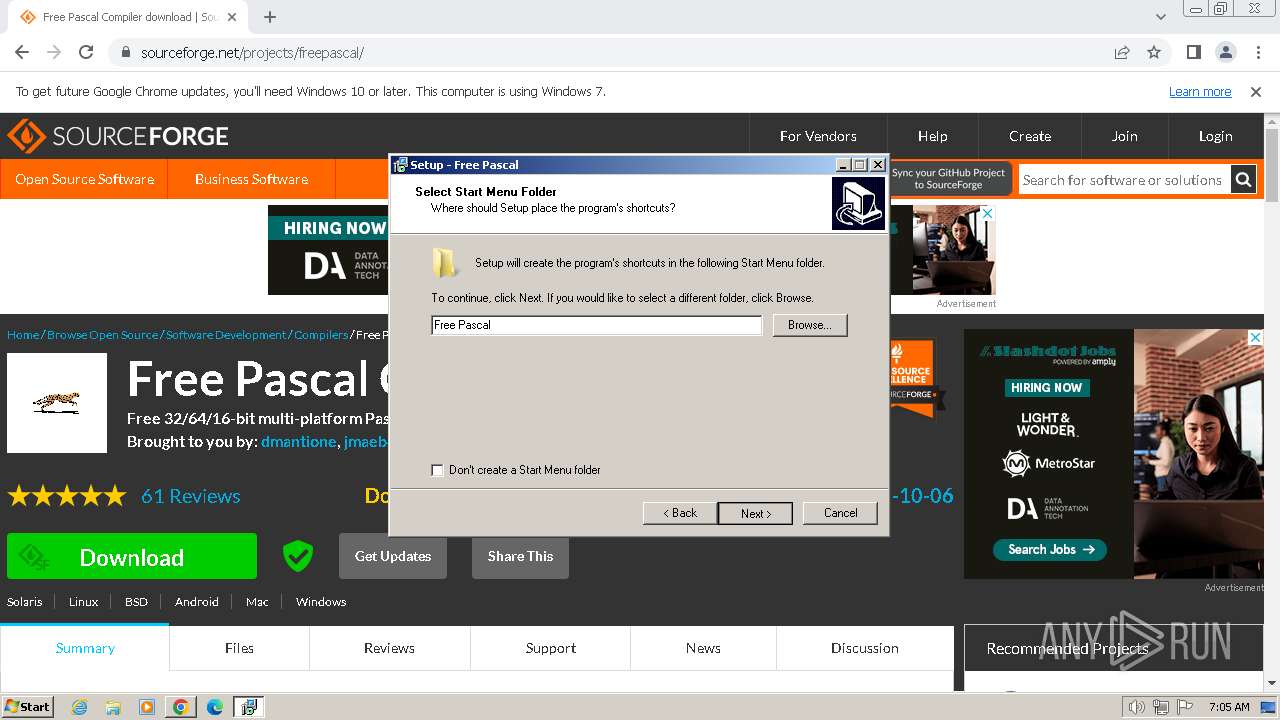
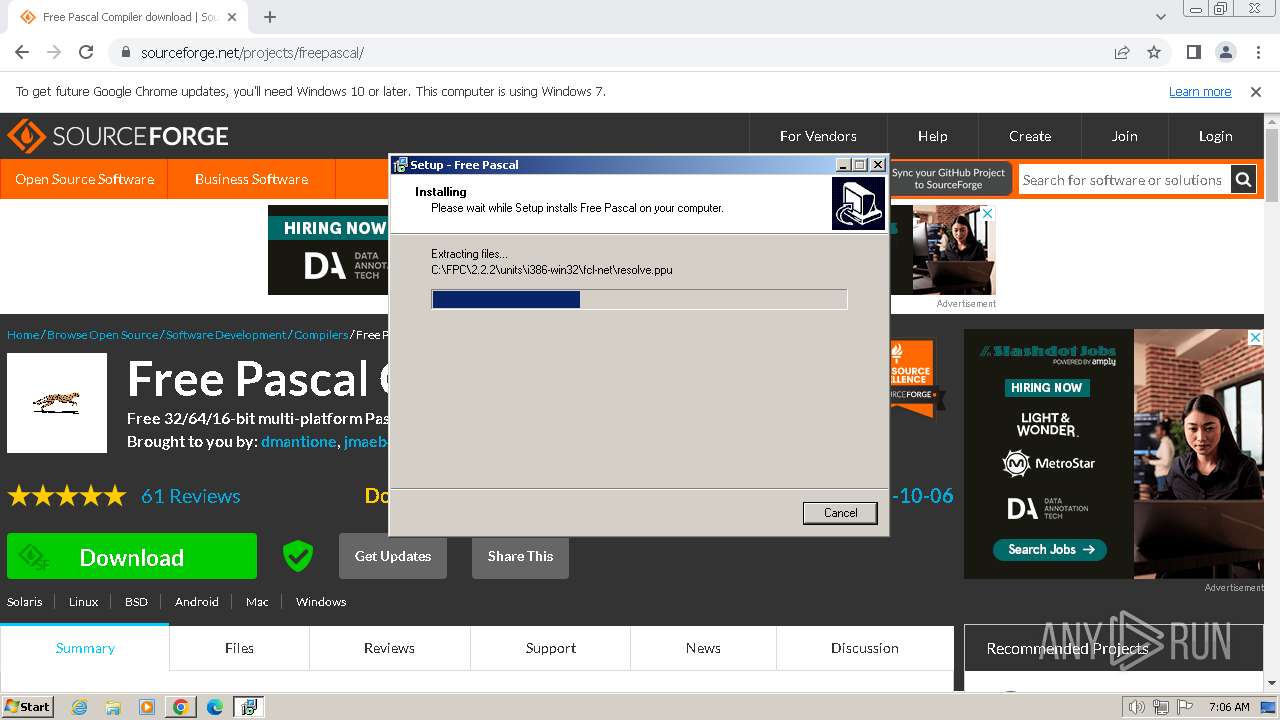
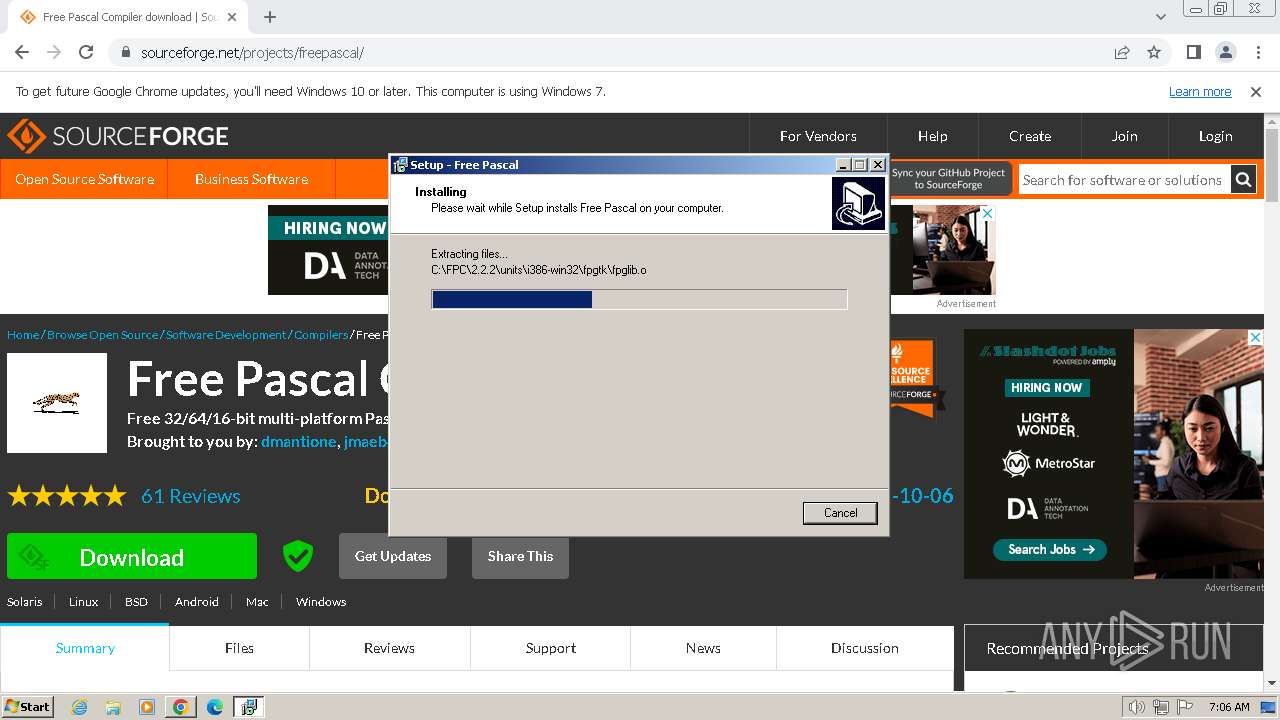
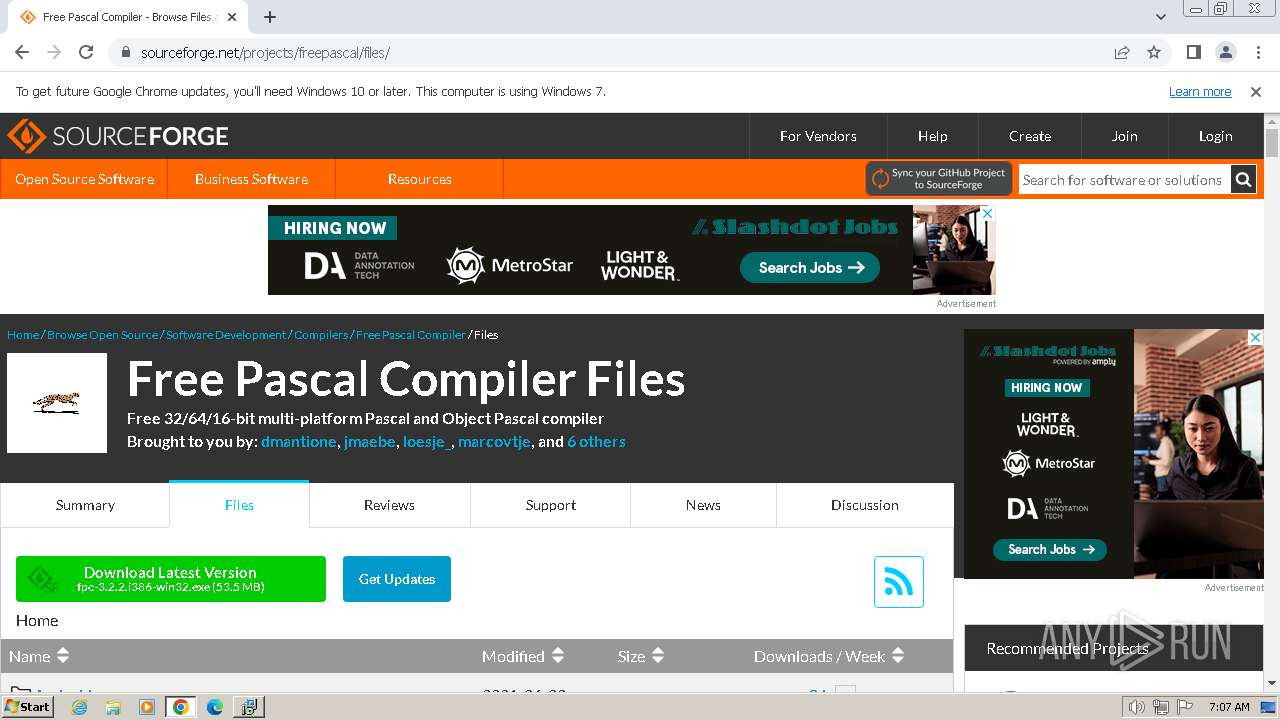
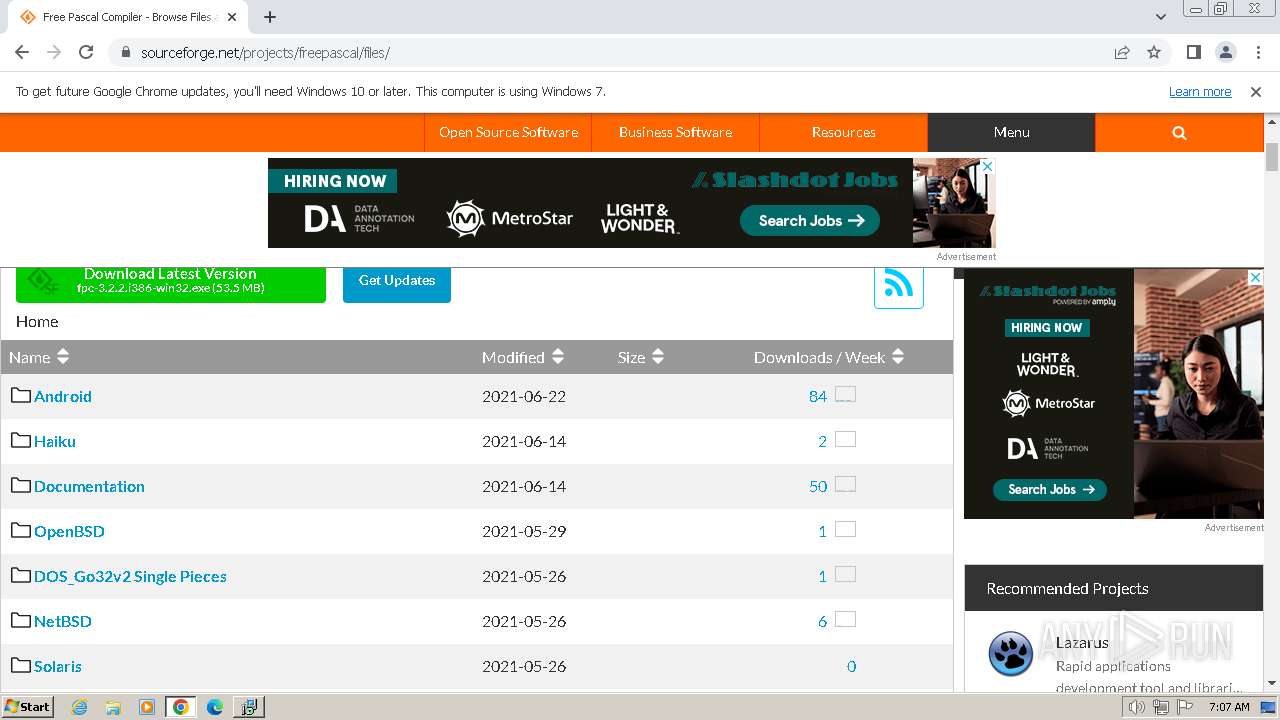
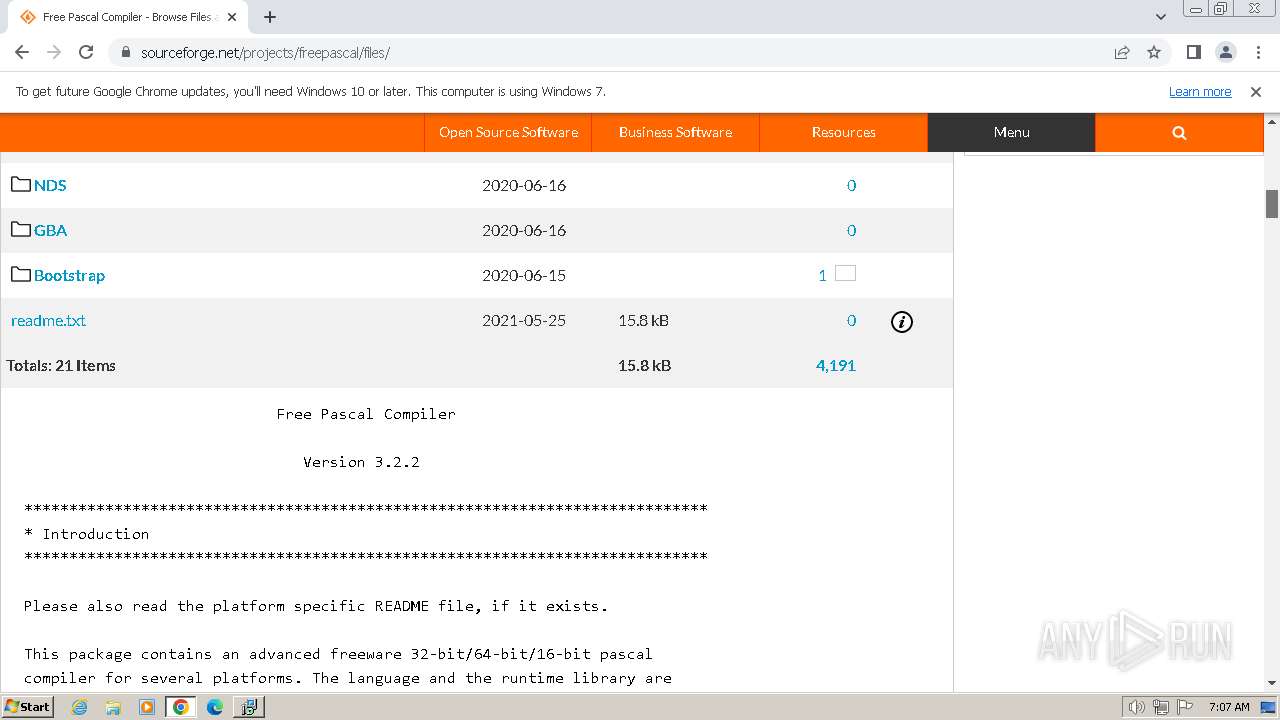
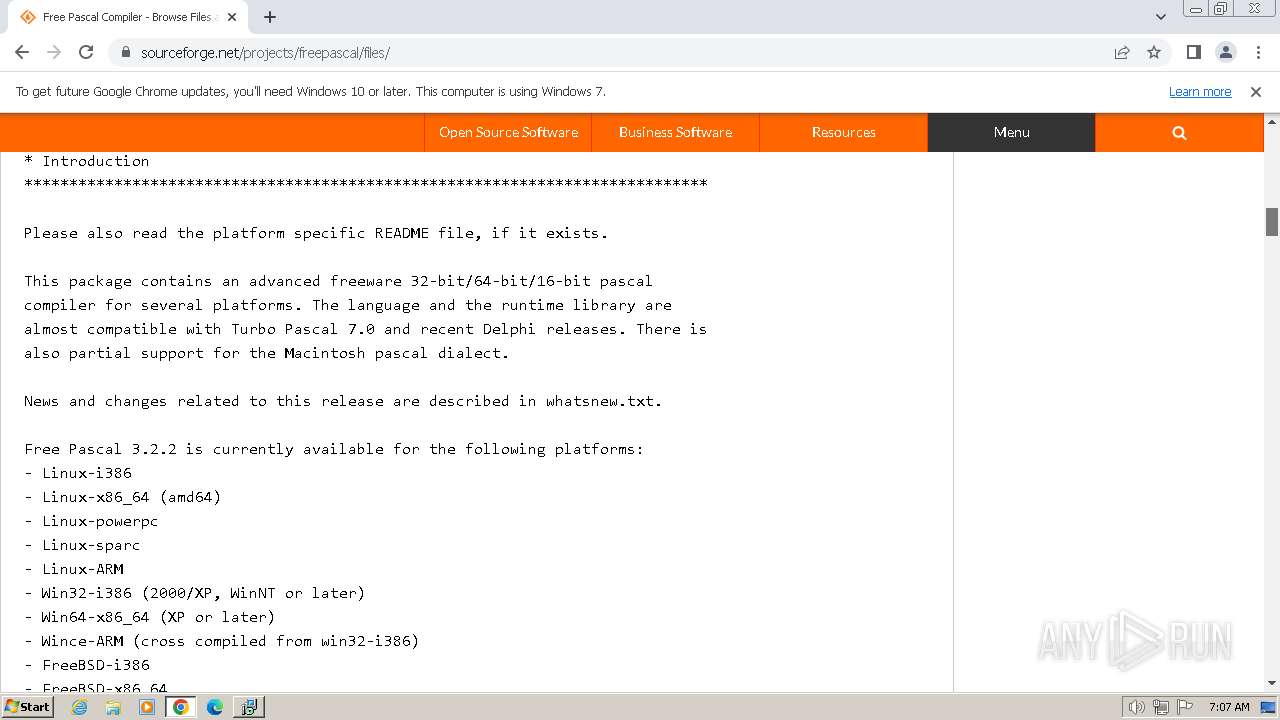
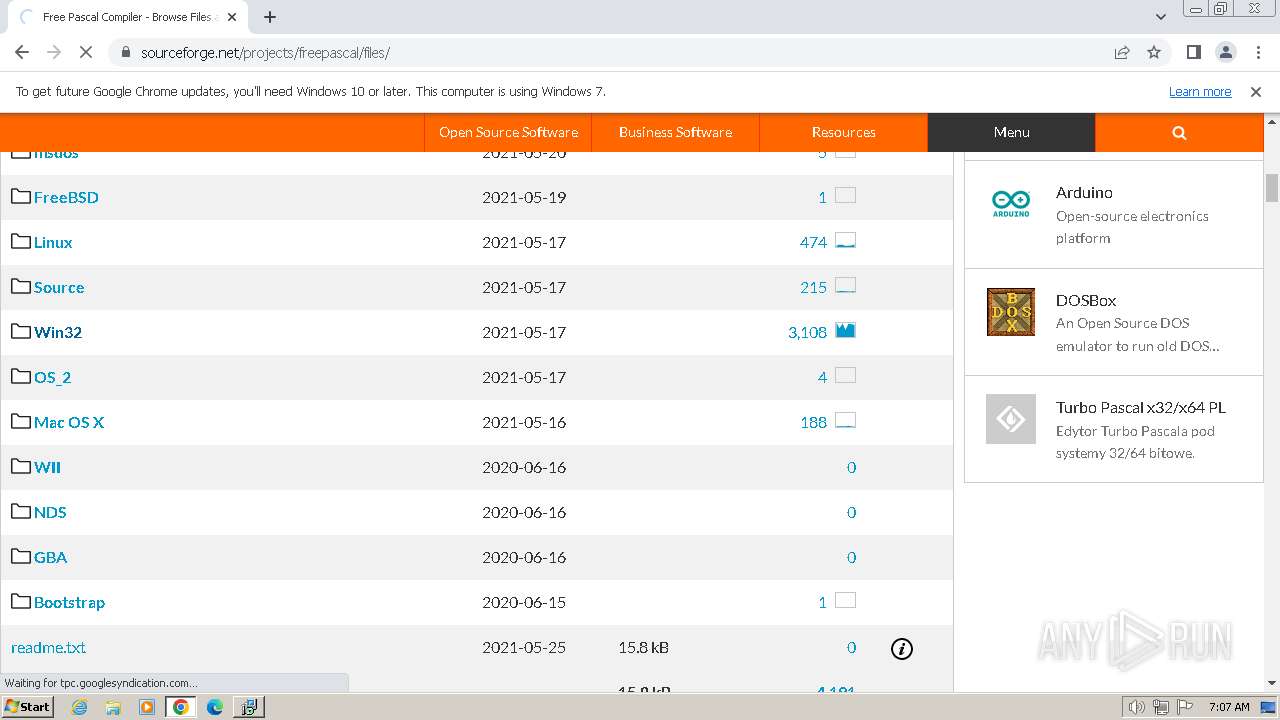
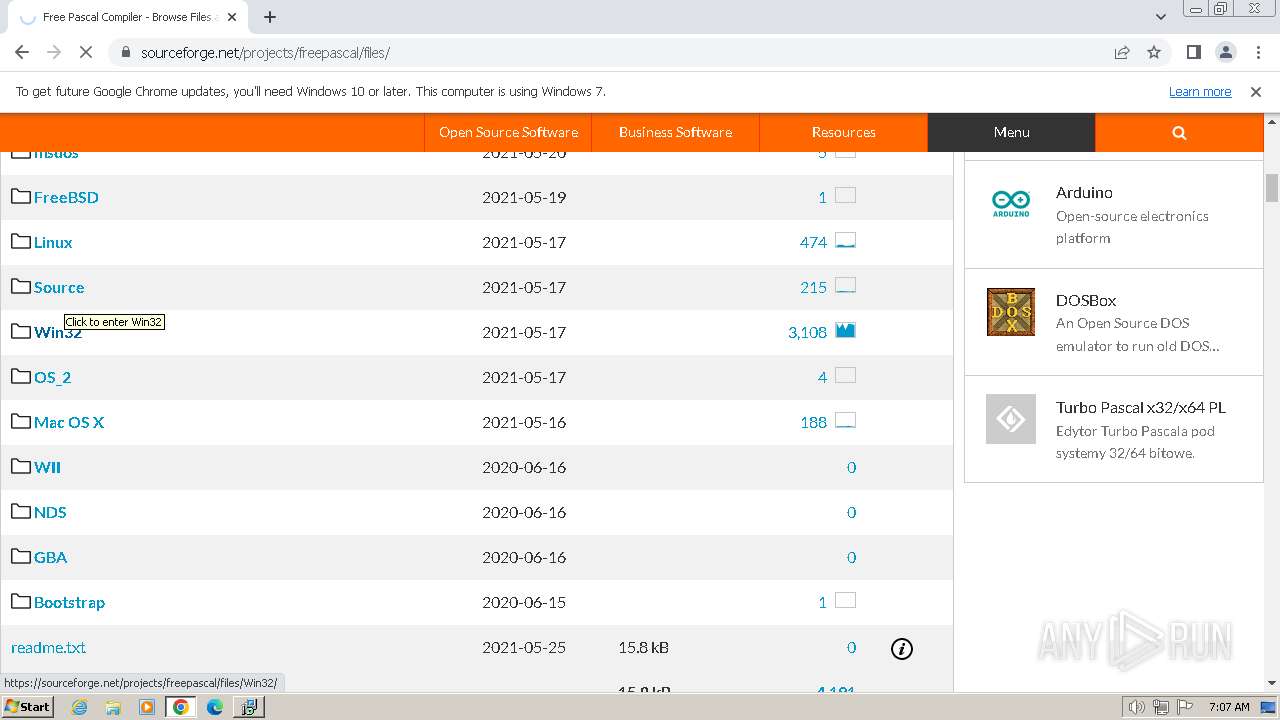
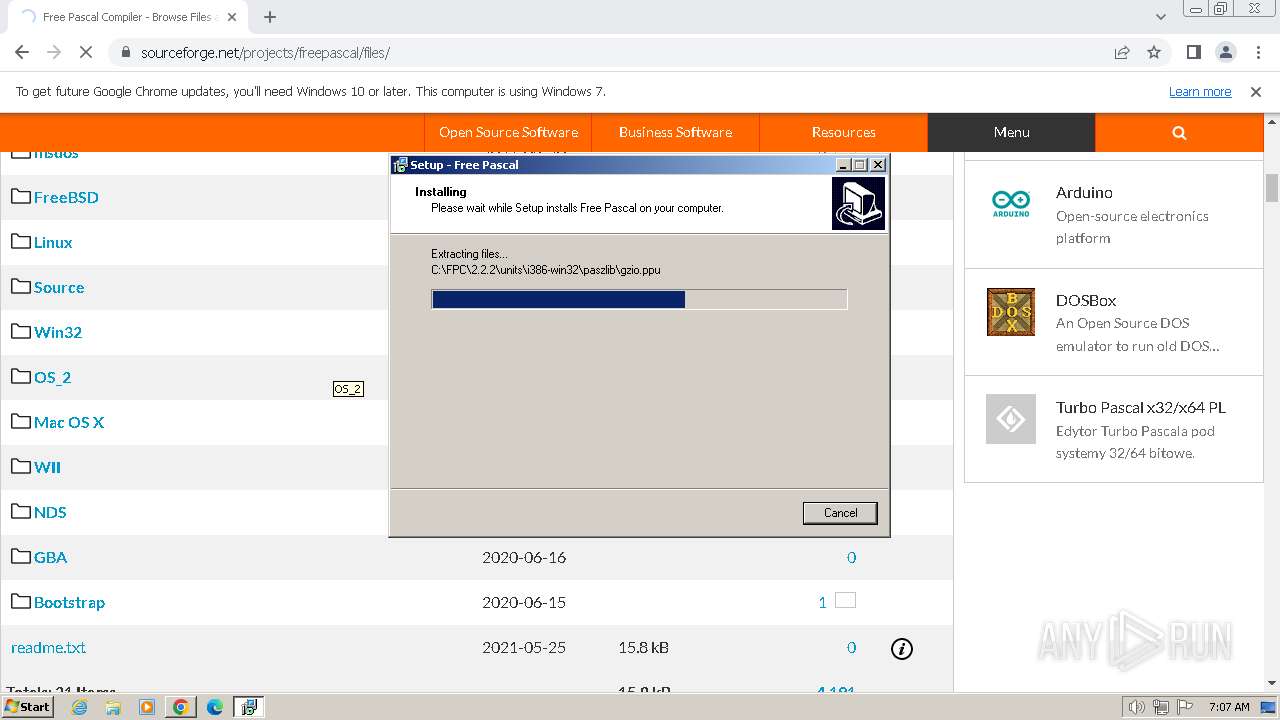
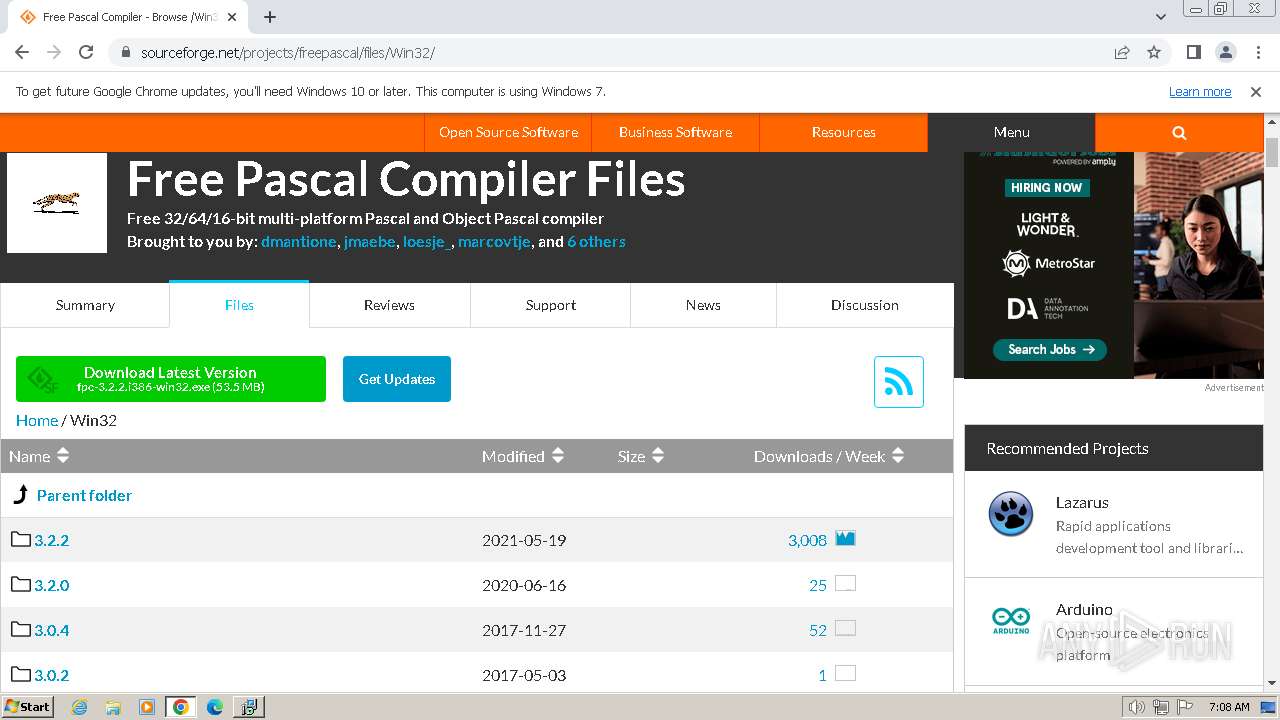
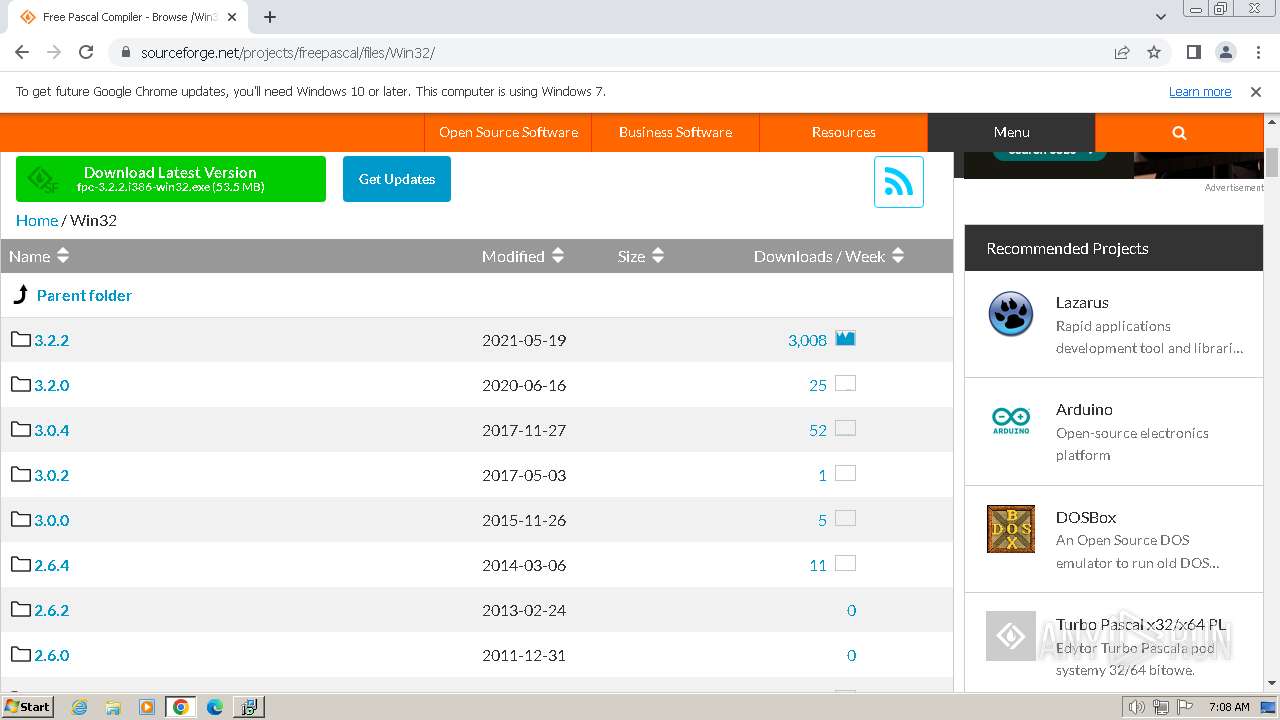
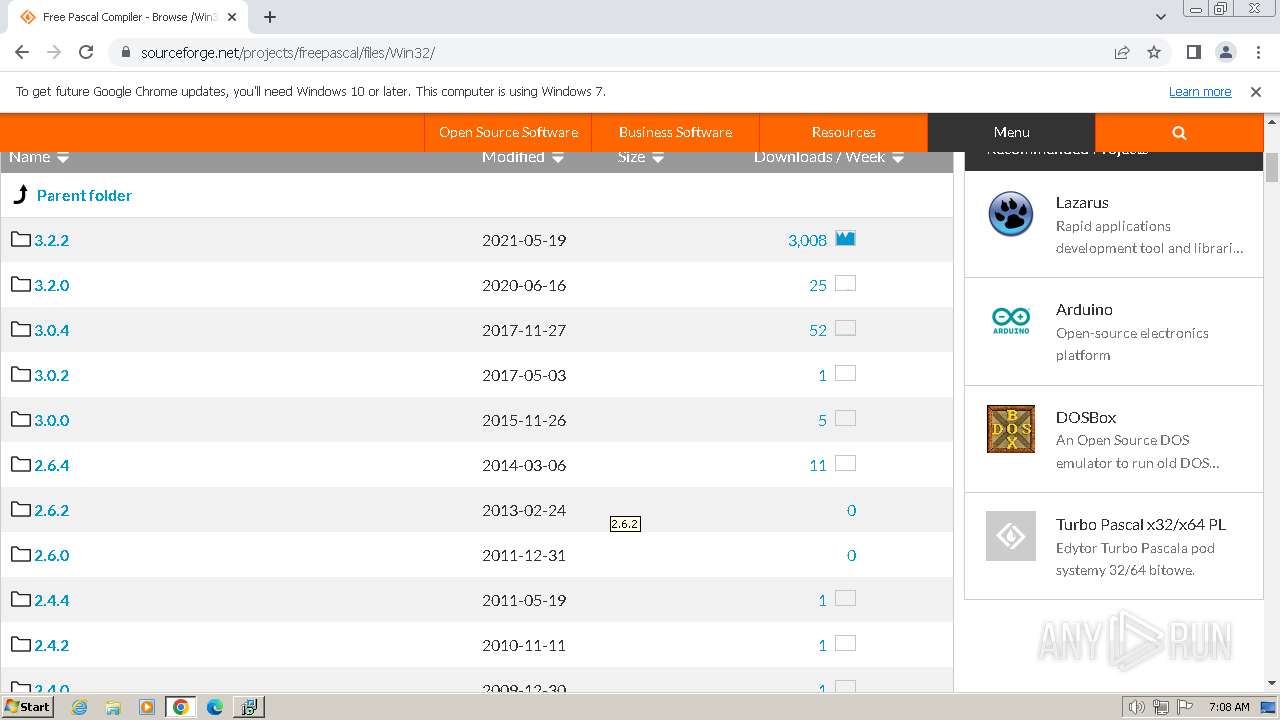
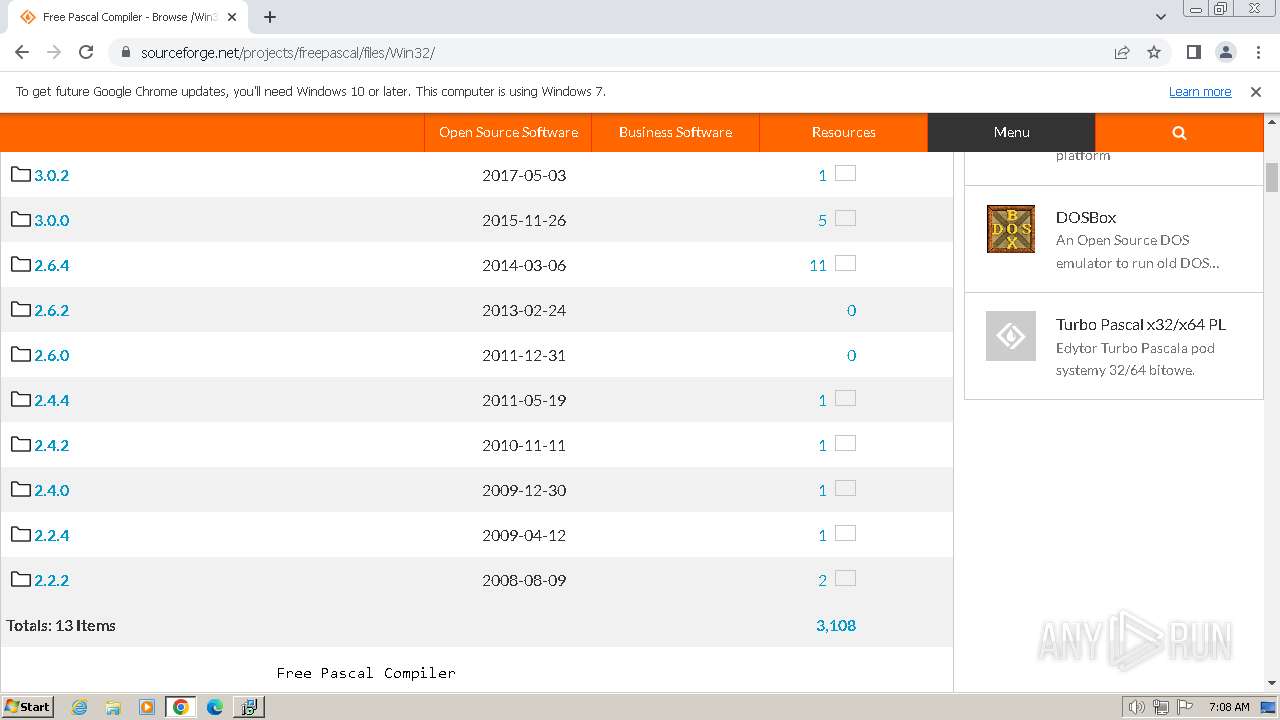
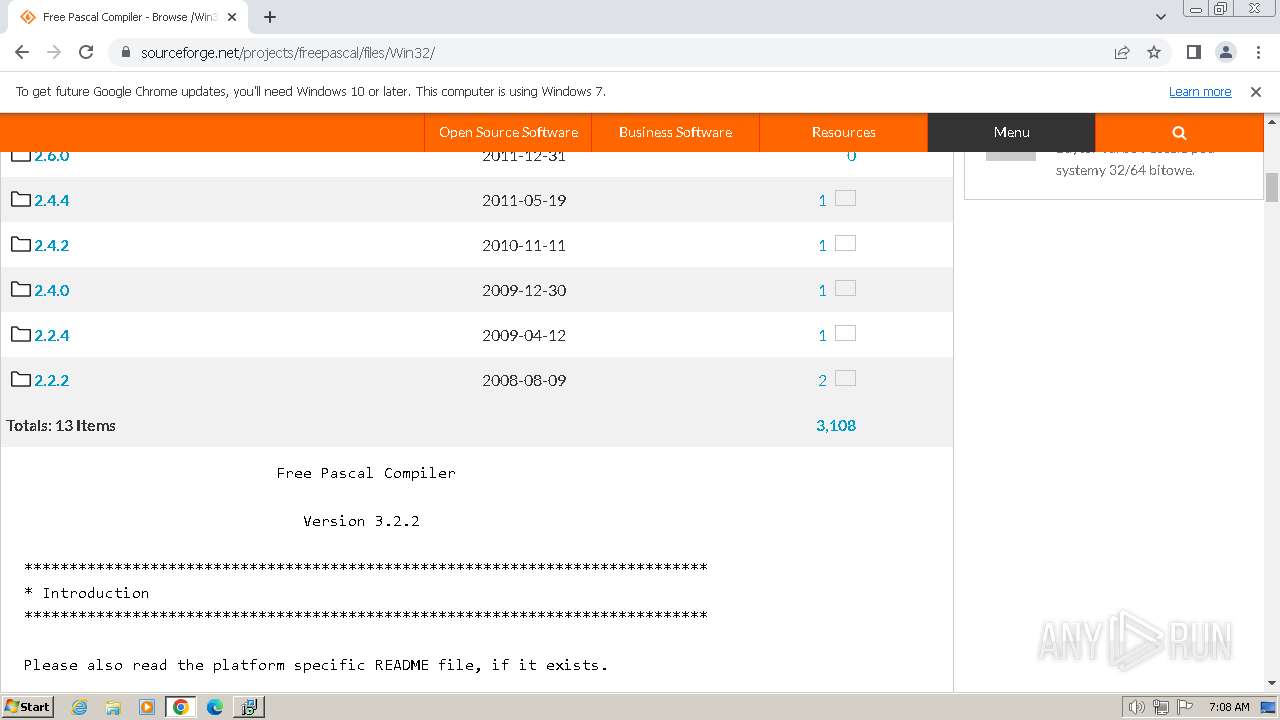
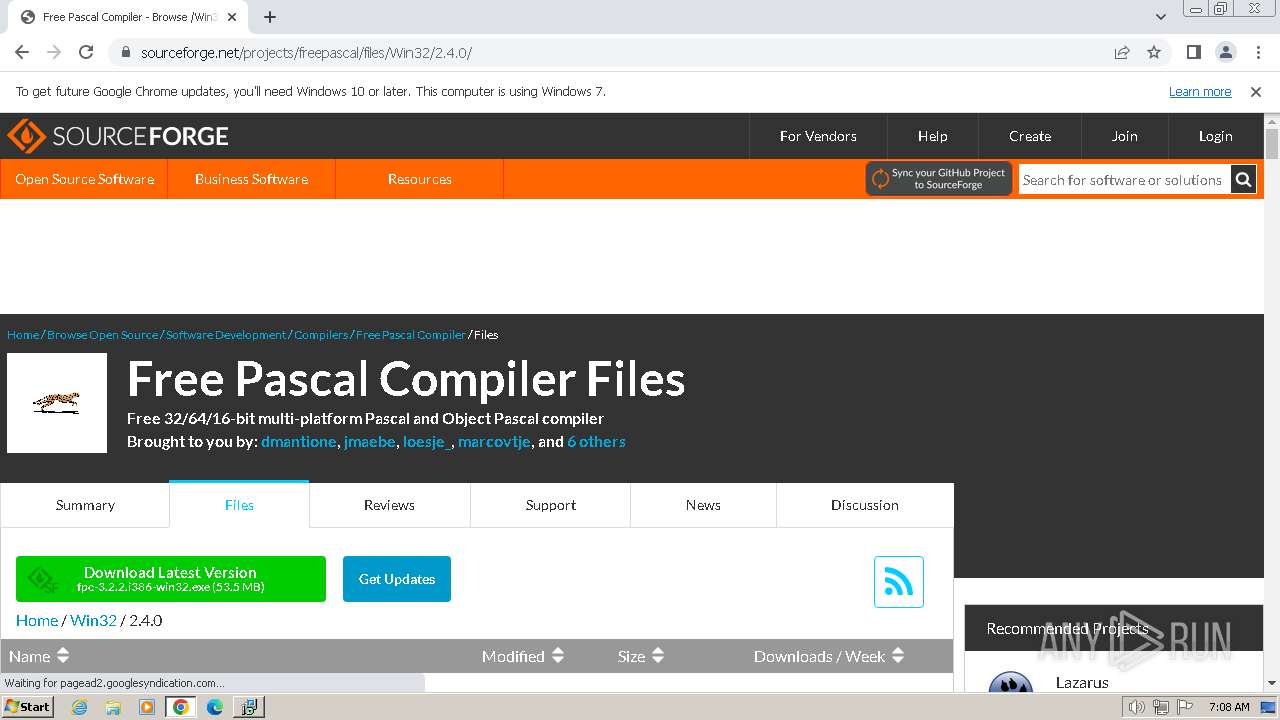
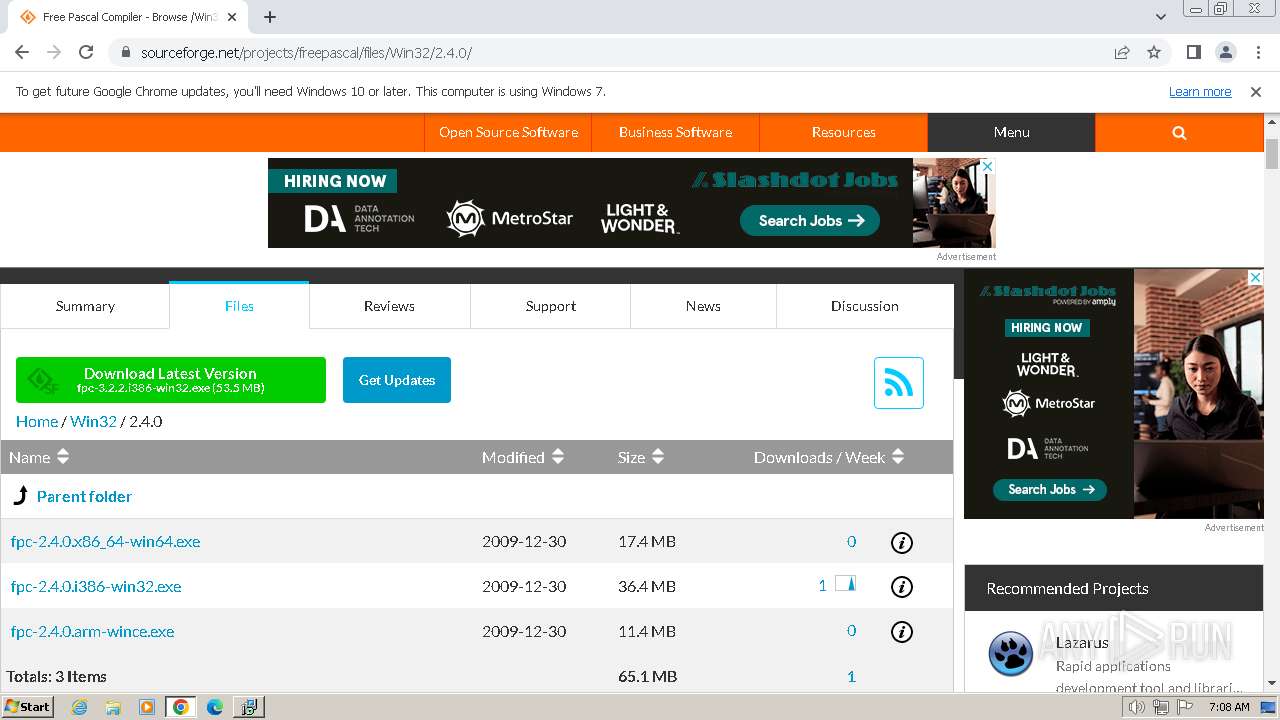
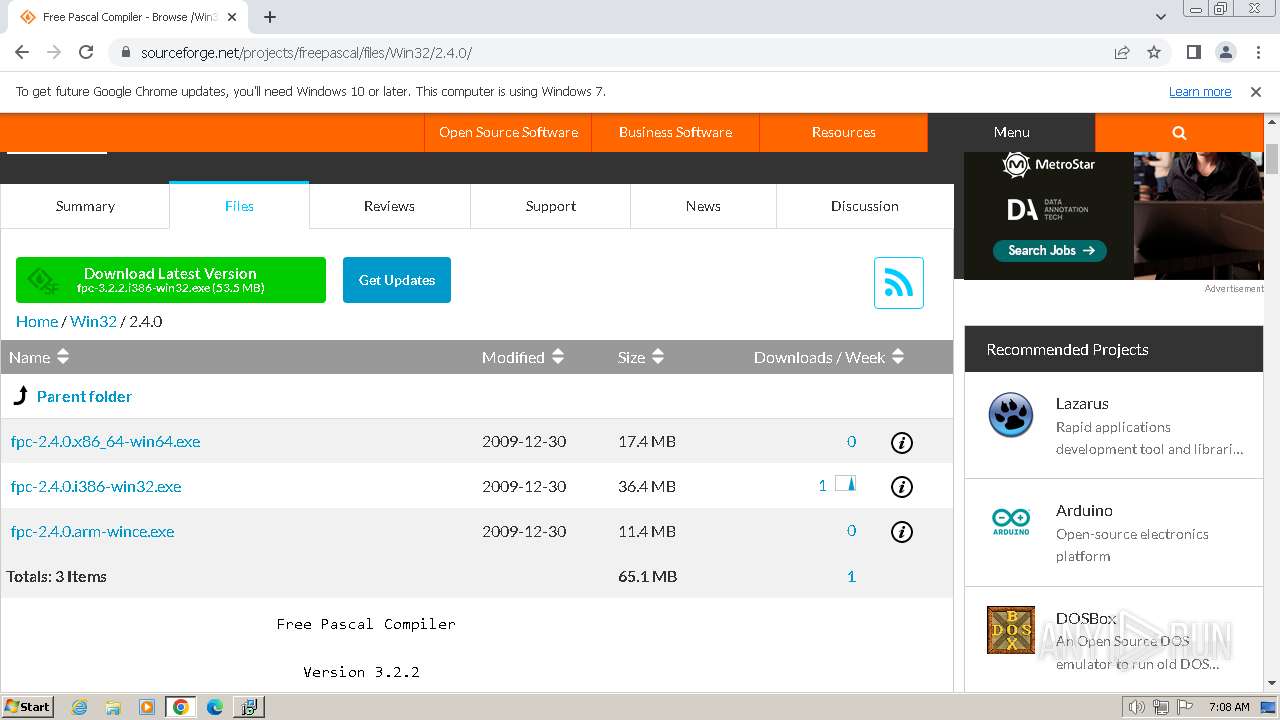
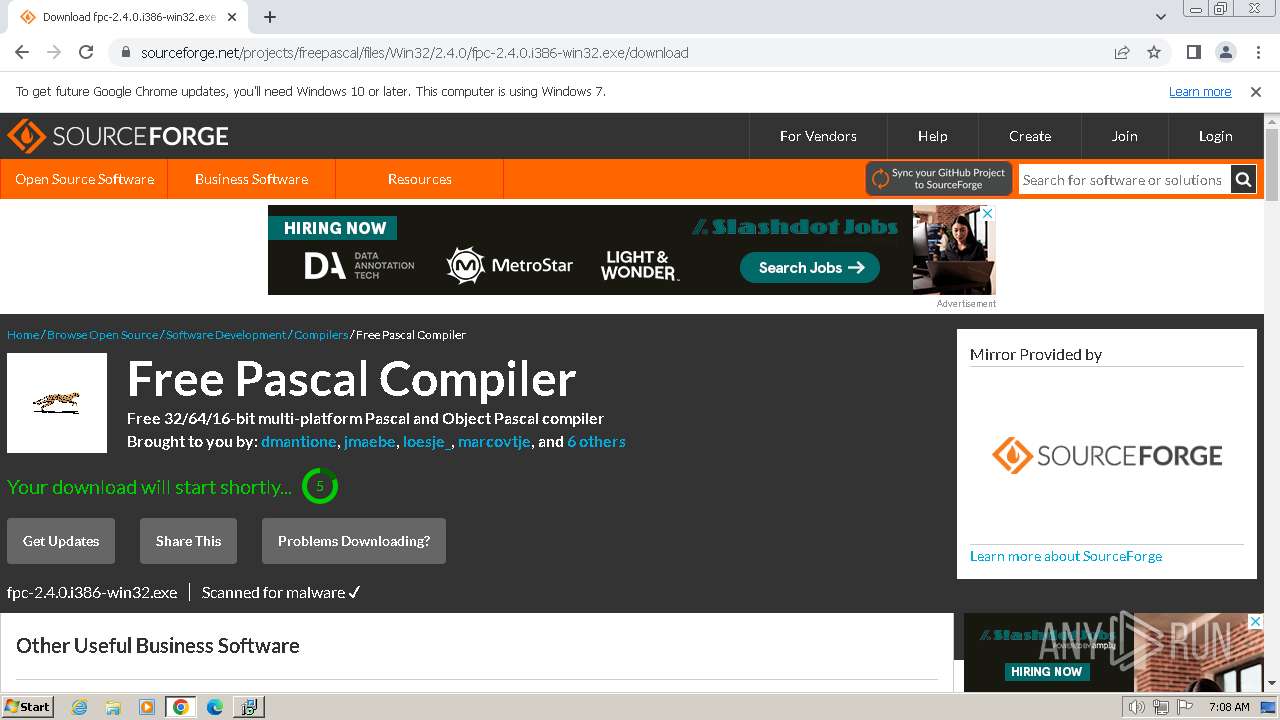
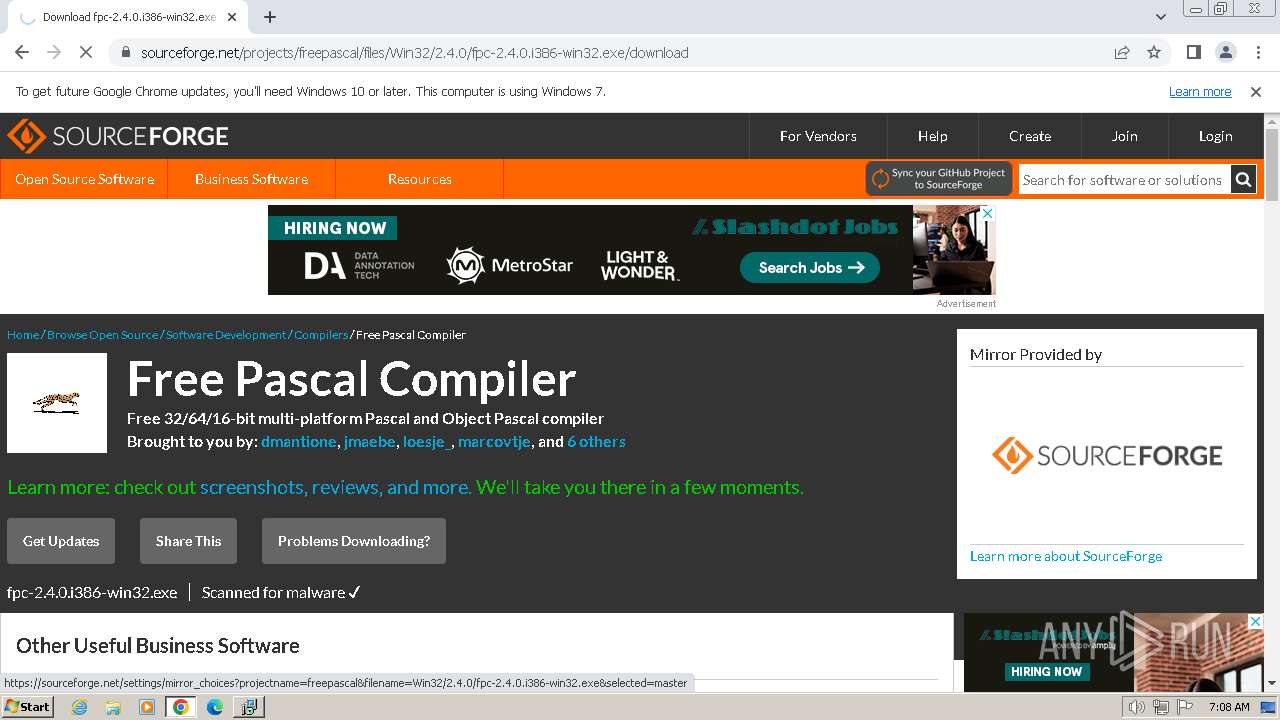
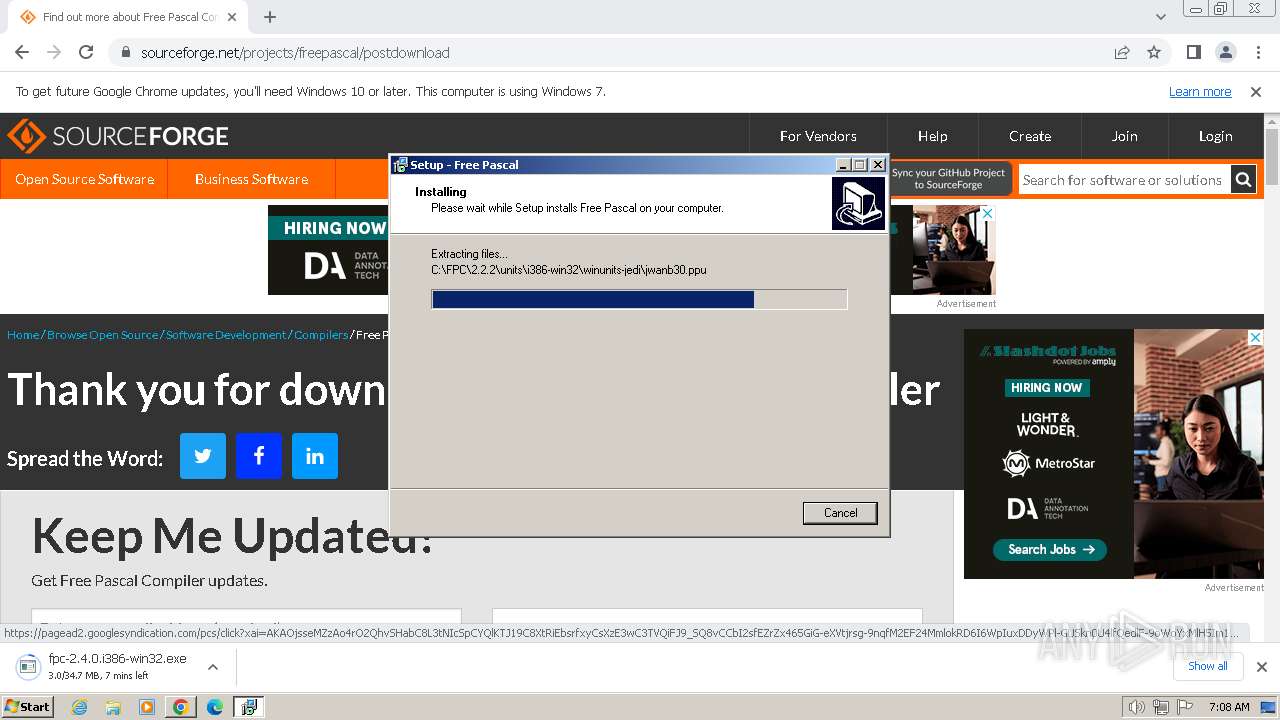
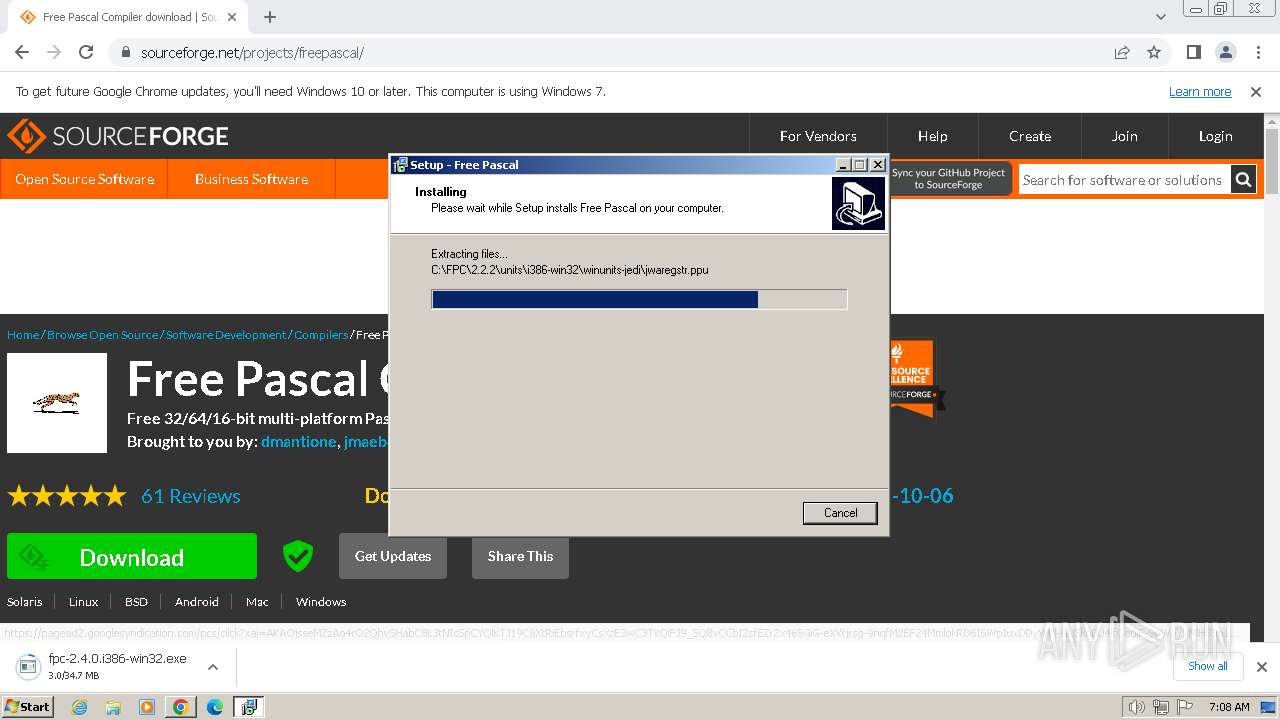
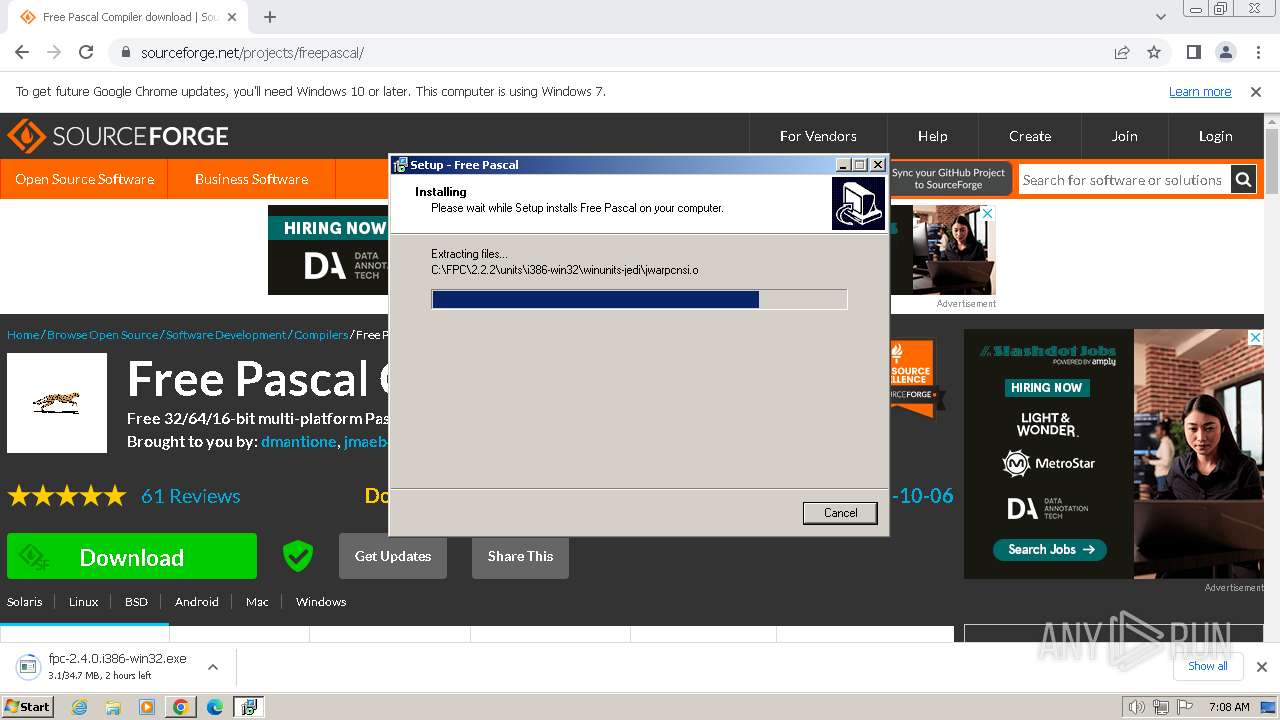
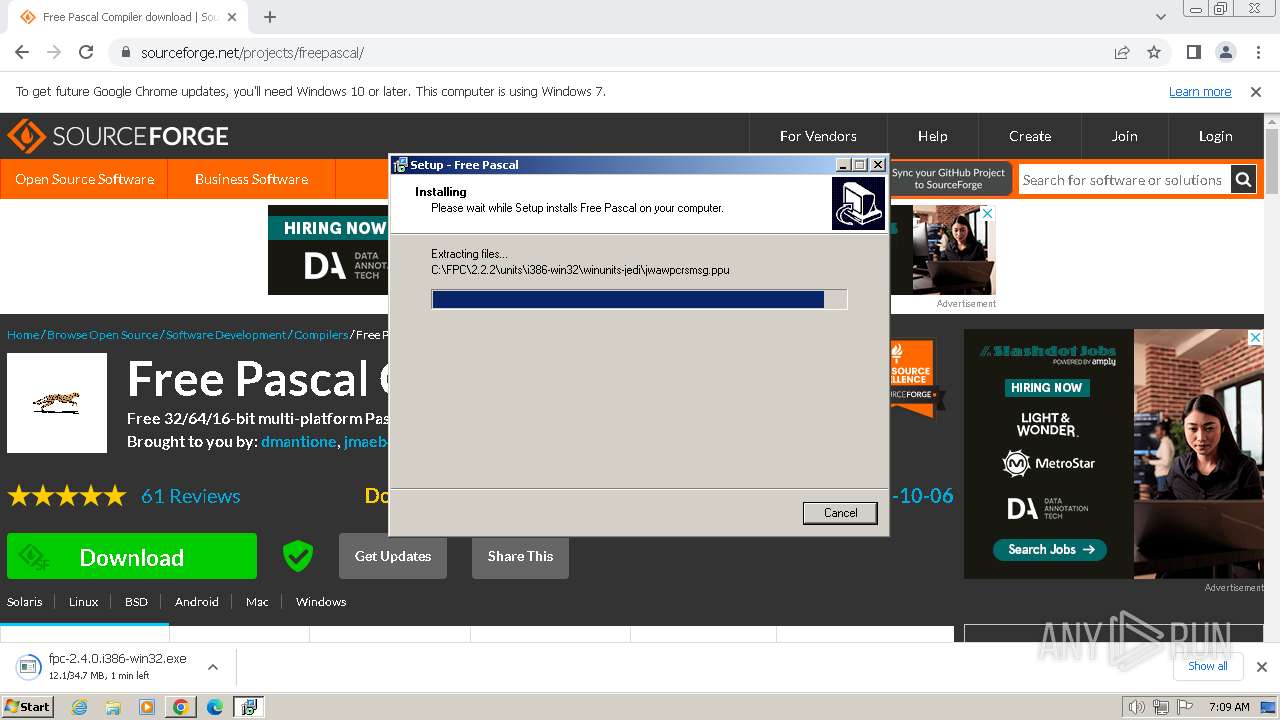
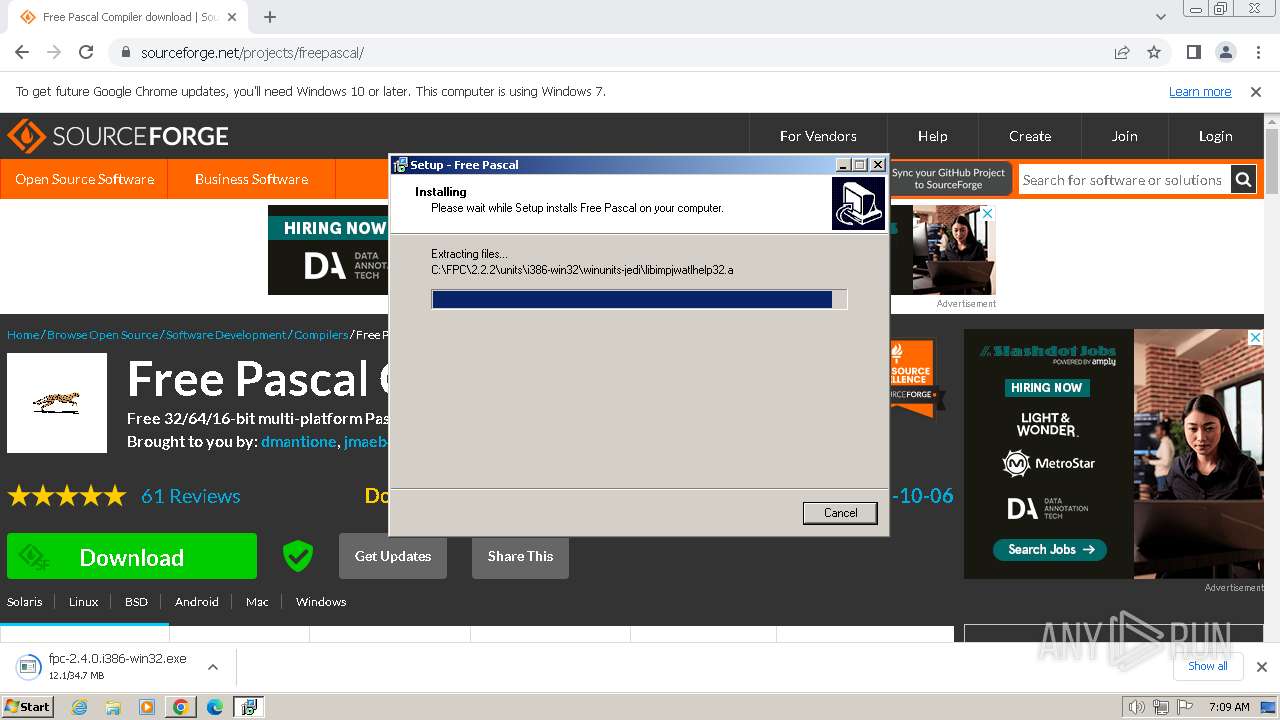
| URL: | https://sourceforge.net/projects/freepascal/files/Win32/2.2.2/fpc-2.2.2.i386-win32.exe/download |
| Full analysis: | https://app.any.run/tasks/e3d10b71-a21a-446c-b91b-7666320d4eb1 |
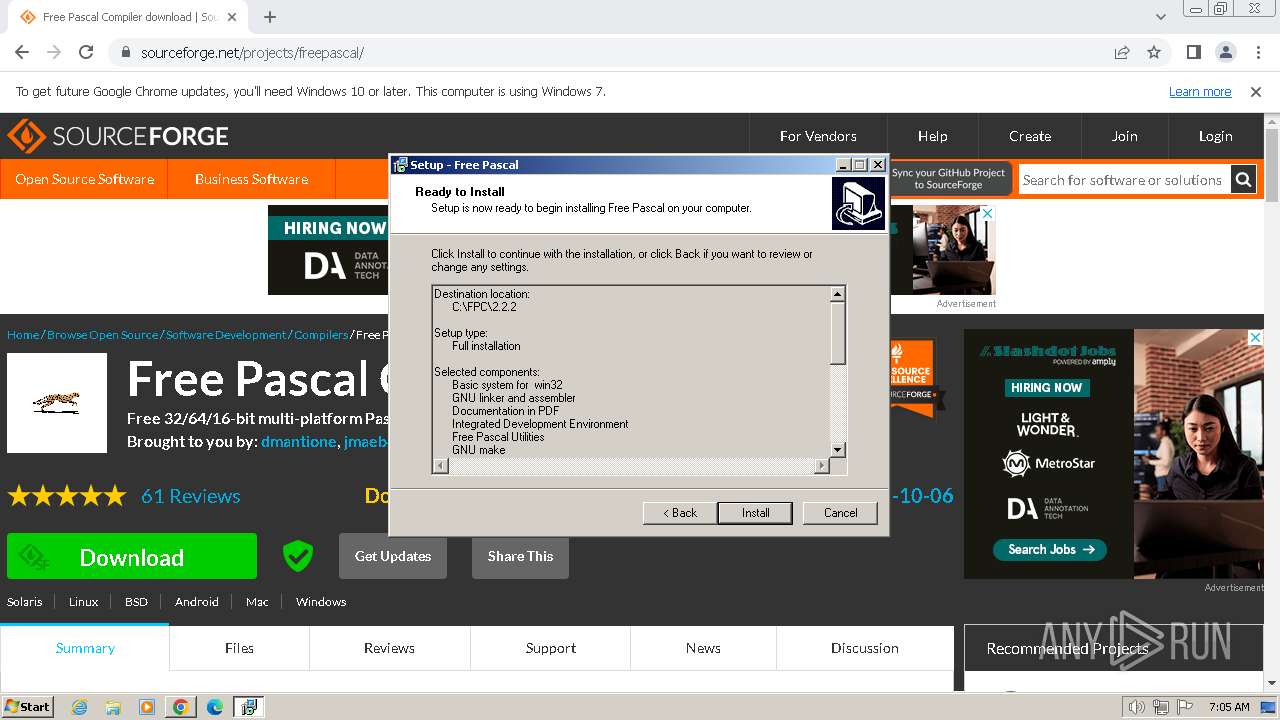
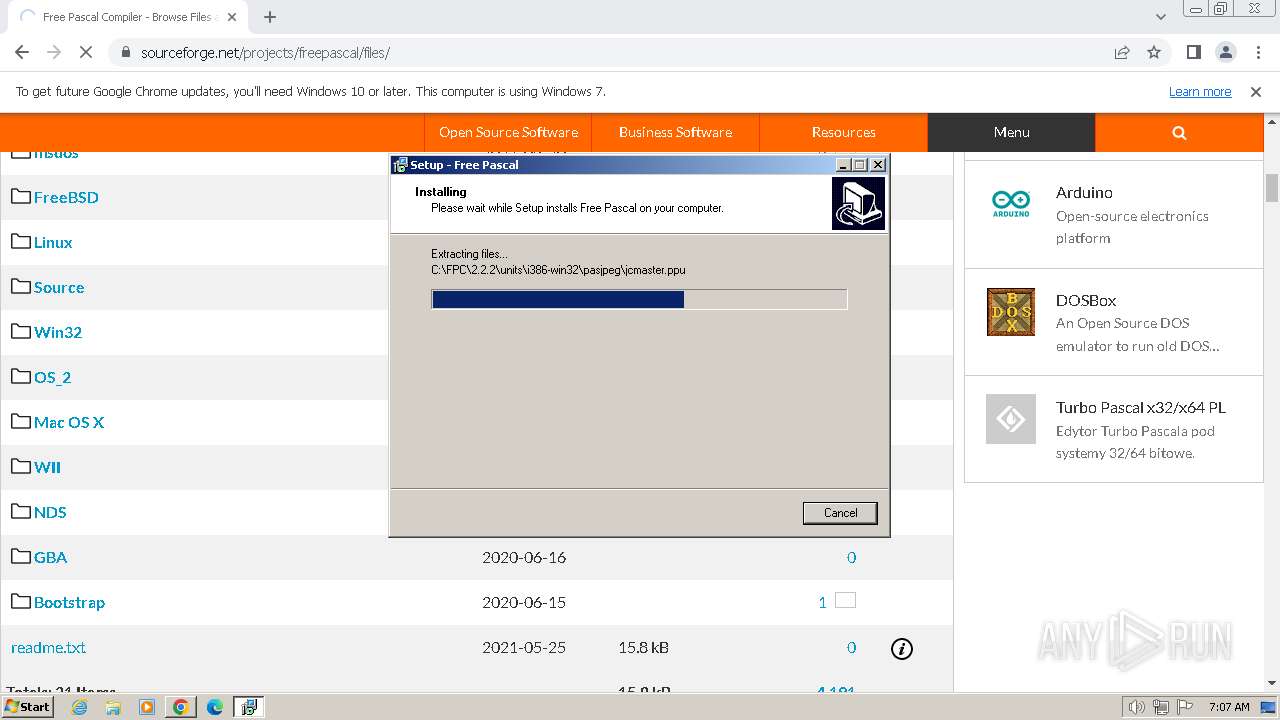
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2024, 07:04:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2D36EA2937223C1594AA101F9E1D2C1B |
| SHA1: | 13DB63CBB2876B7CFA6CE154968B51DB482E1DEB |
| SHA256: | DEA8B3D3A692E7AC8AE6EB61A6C42280C3B5C800CA5EEDFD431697D3D27117FD |
| SSDEEP: | 3:N8HCGSuLAuUtXuWFhUfLWXLZLbXdEDWXkAaJLz:2iGnCtXZ8LWXLZLpRkZJ/ |
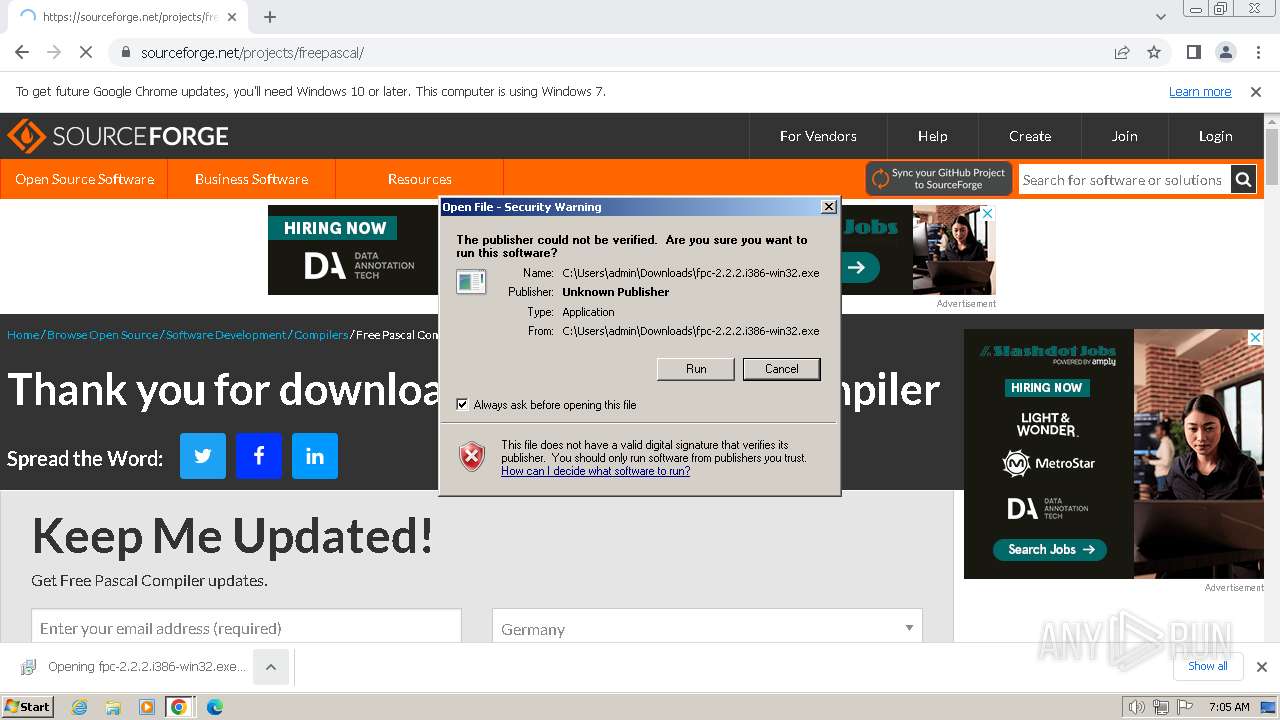
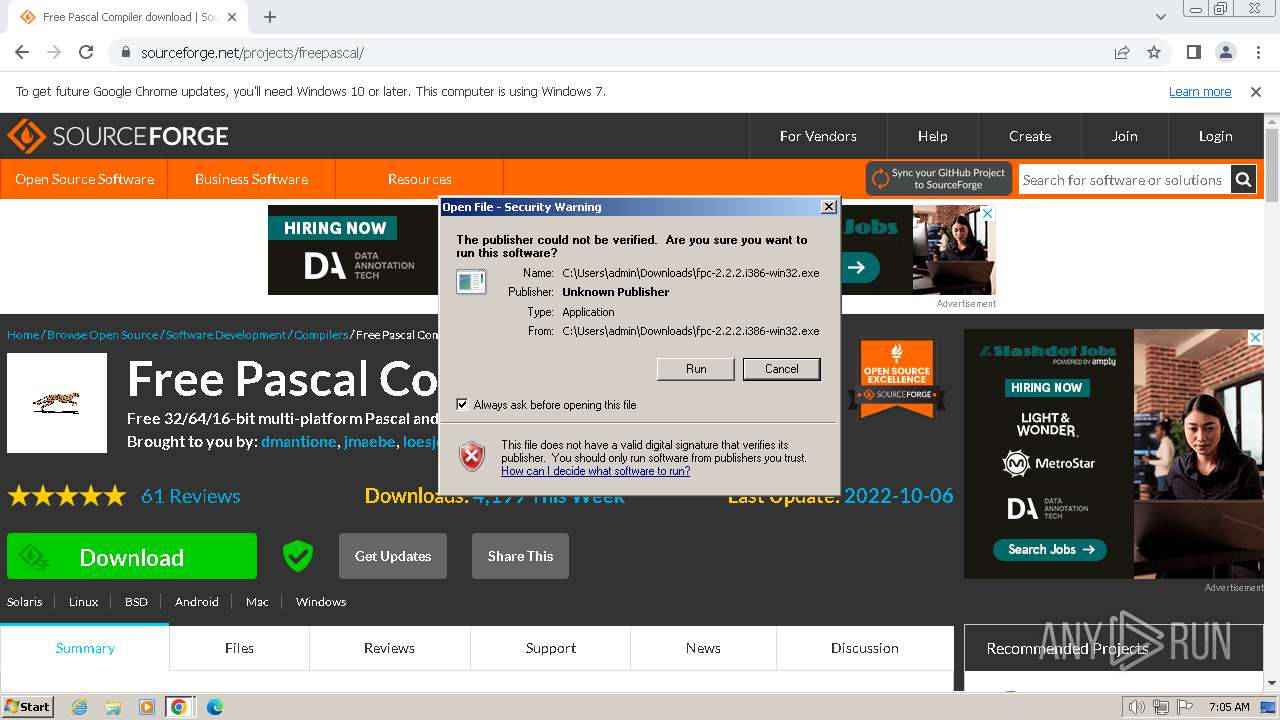
MALICIOUS
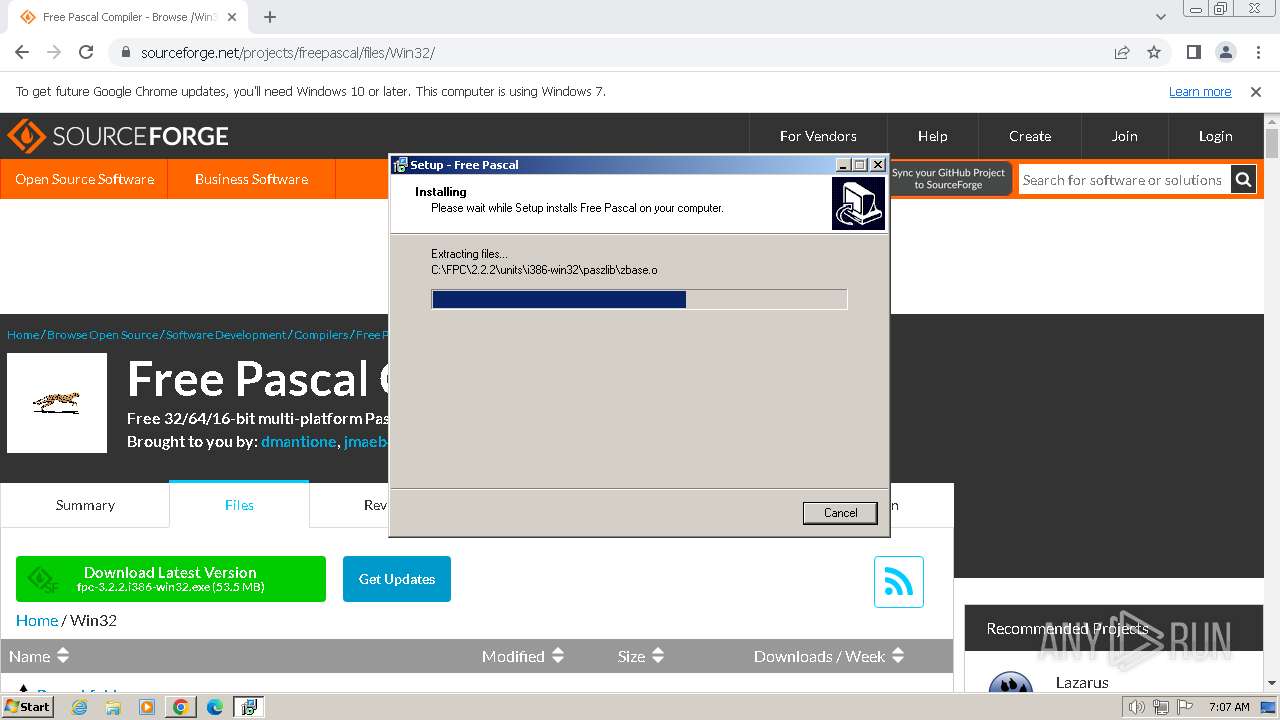
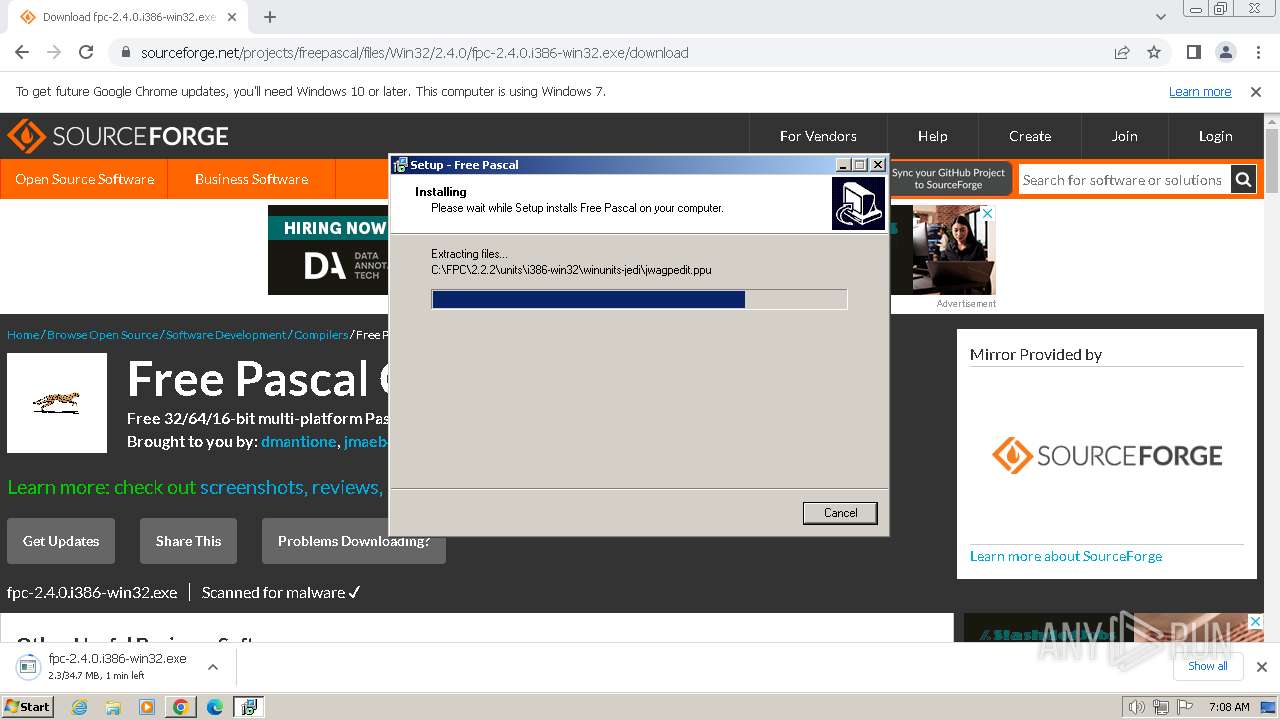
Drops the executable file immediately after the start
- fpc-2.2.2.i386-win32.exe (PID: 748)
- fpc-2.2.2.i386-win32.exe (PID: 980)
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
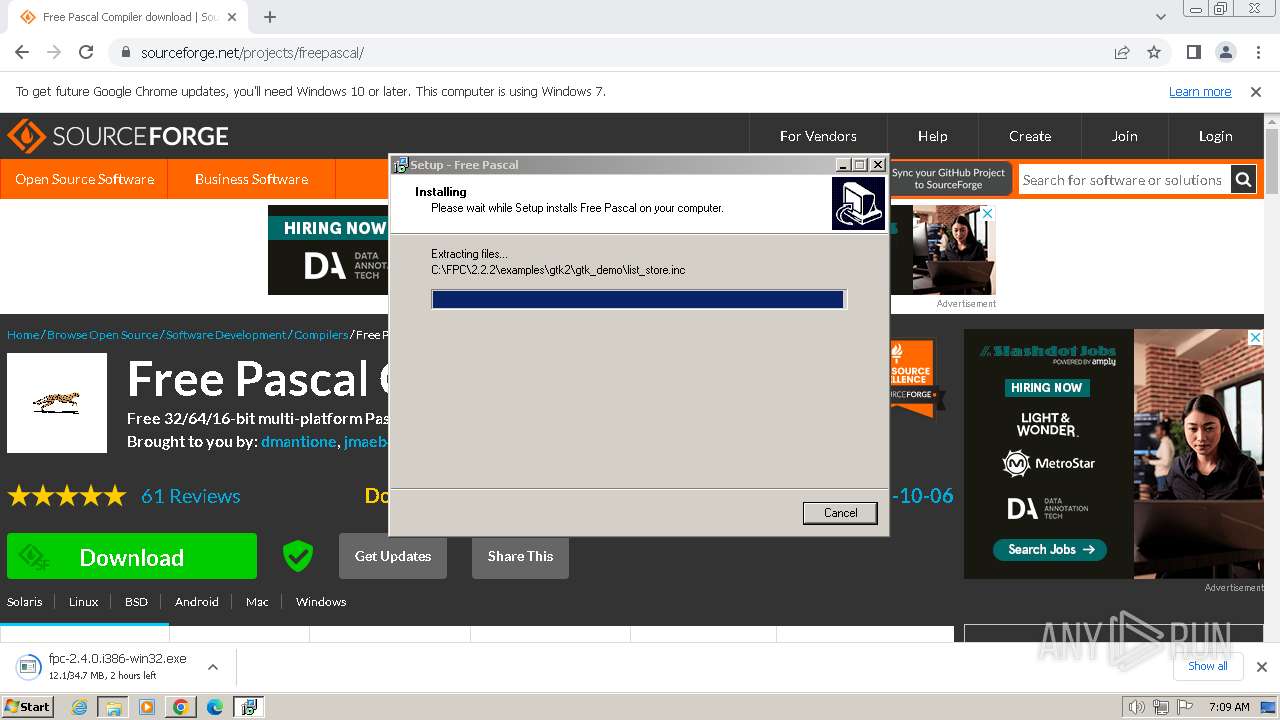
SUSPICIOUS
Executable content was dropped or overwritten
- fpc-2.2.2.i386-win32.exe (PID: 748)
- fpc-2.2.2.i386-win32.exe (PID: 980)
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
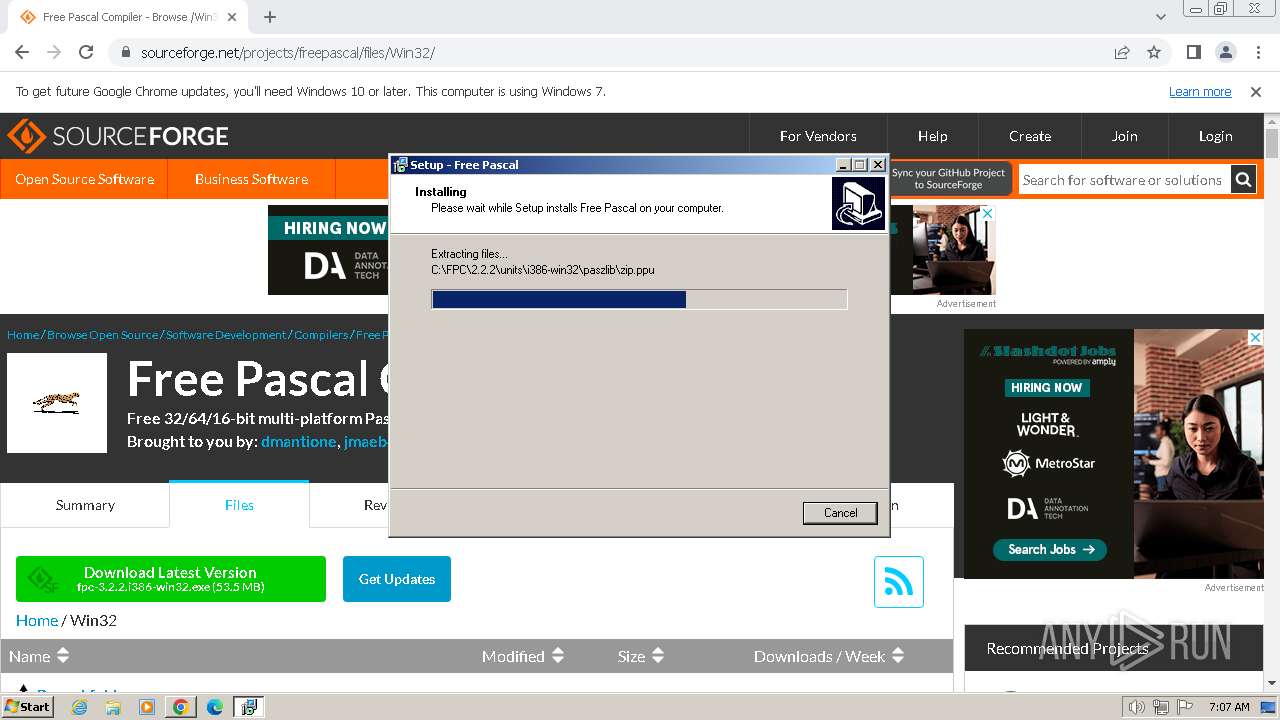
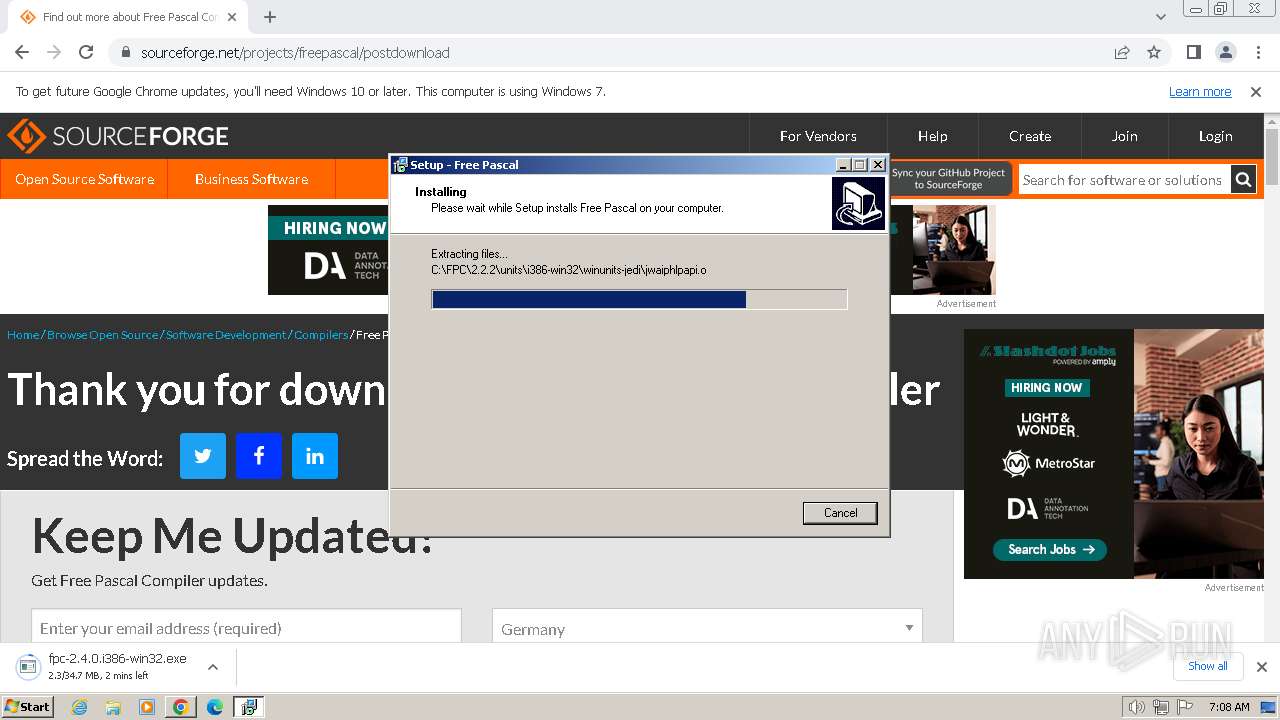
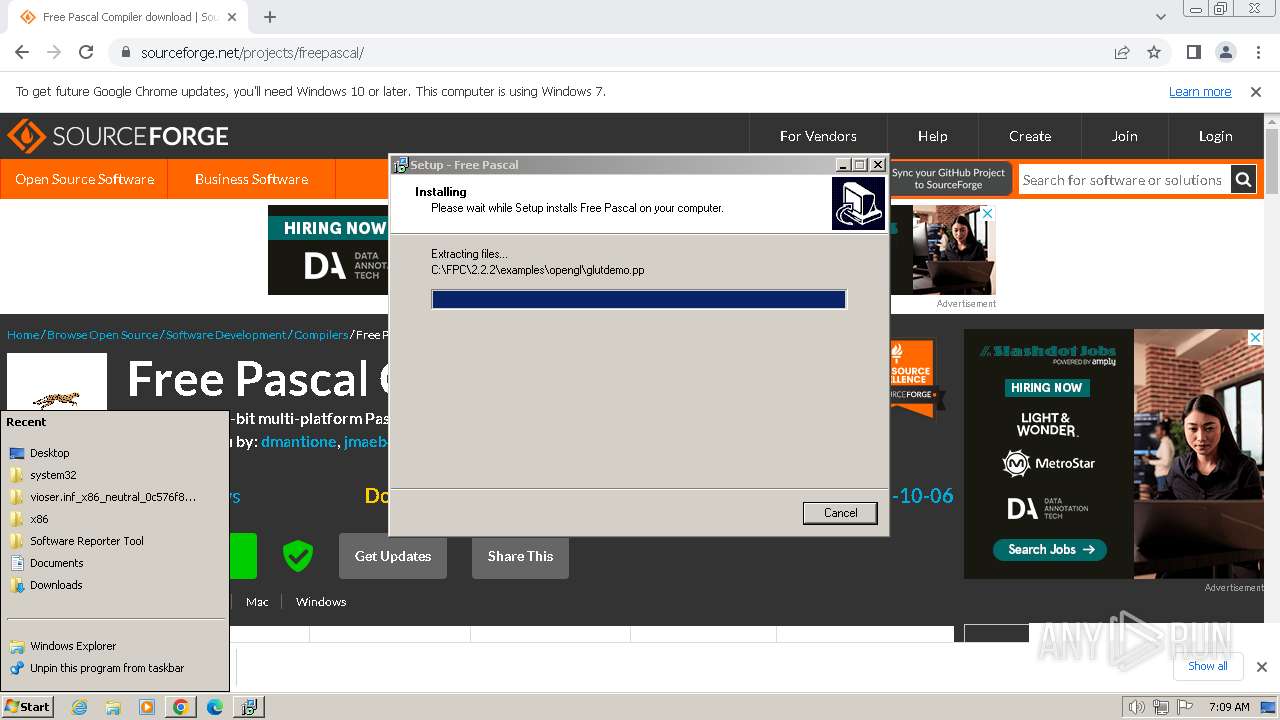
Reads the Windows owner or organization settings
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
Process drops legitimate windows executable
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
INFO
Application launched itself
- chrome.exe (PID: 3456)
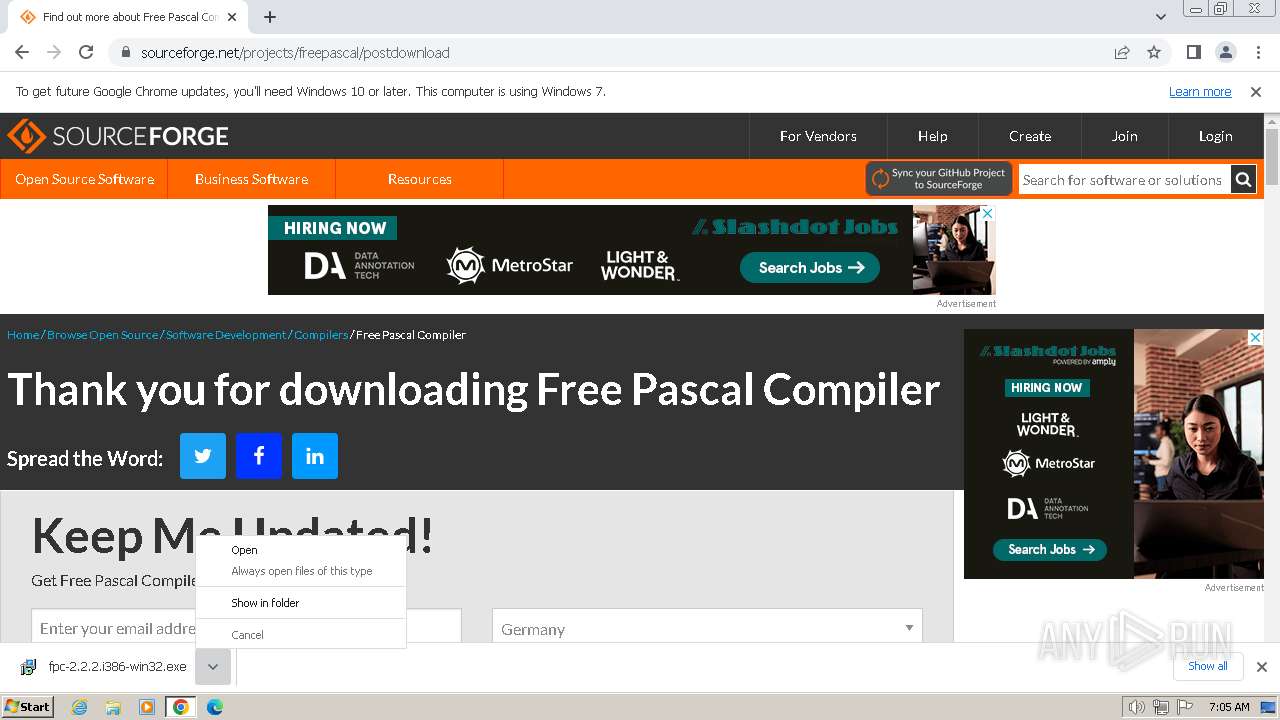
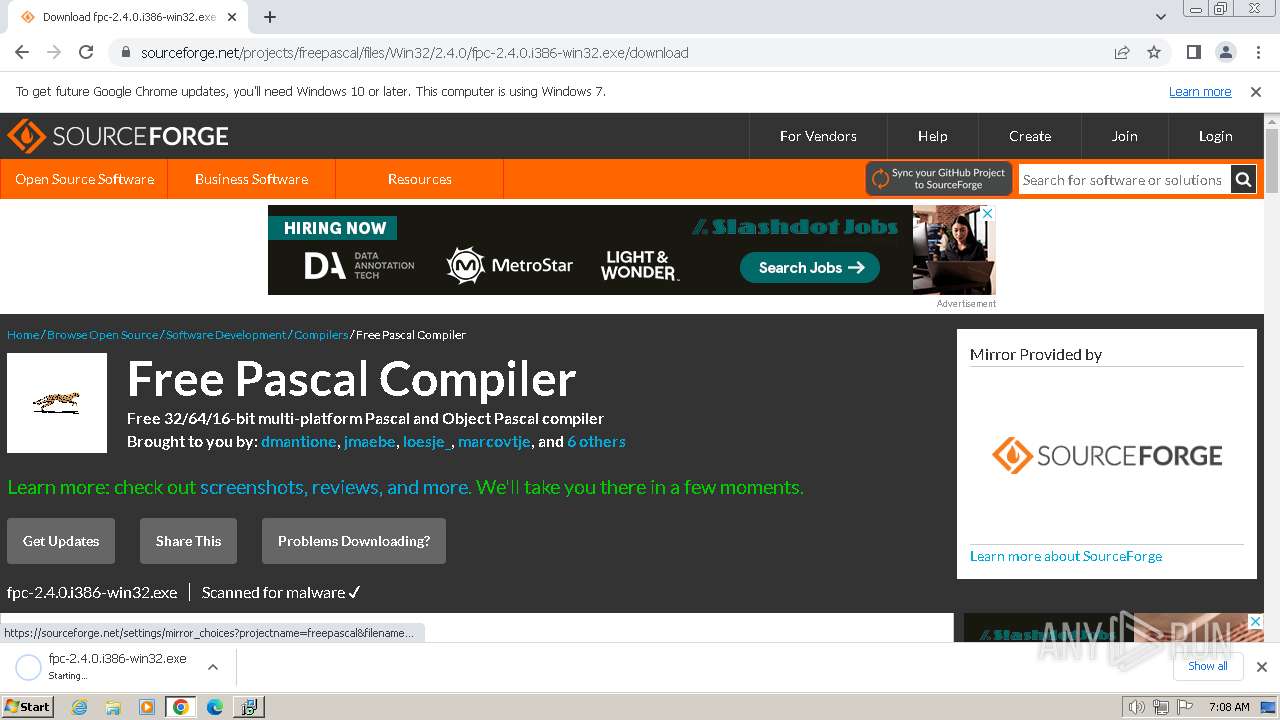
The process uses the downloaded file
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3456)
Executable content was dropped or overwritten
- chrome.exe (PID: 3456)
Drops the executable file immediately after the start
- chrome.exe (PID: 3456)
Create files in a temporary directory
- fpc-2.2.2.i386-win32.exe (PID: 748)
- fpc-2.2.2.i386-win32.exe (PID: 980)
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
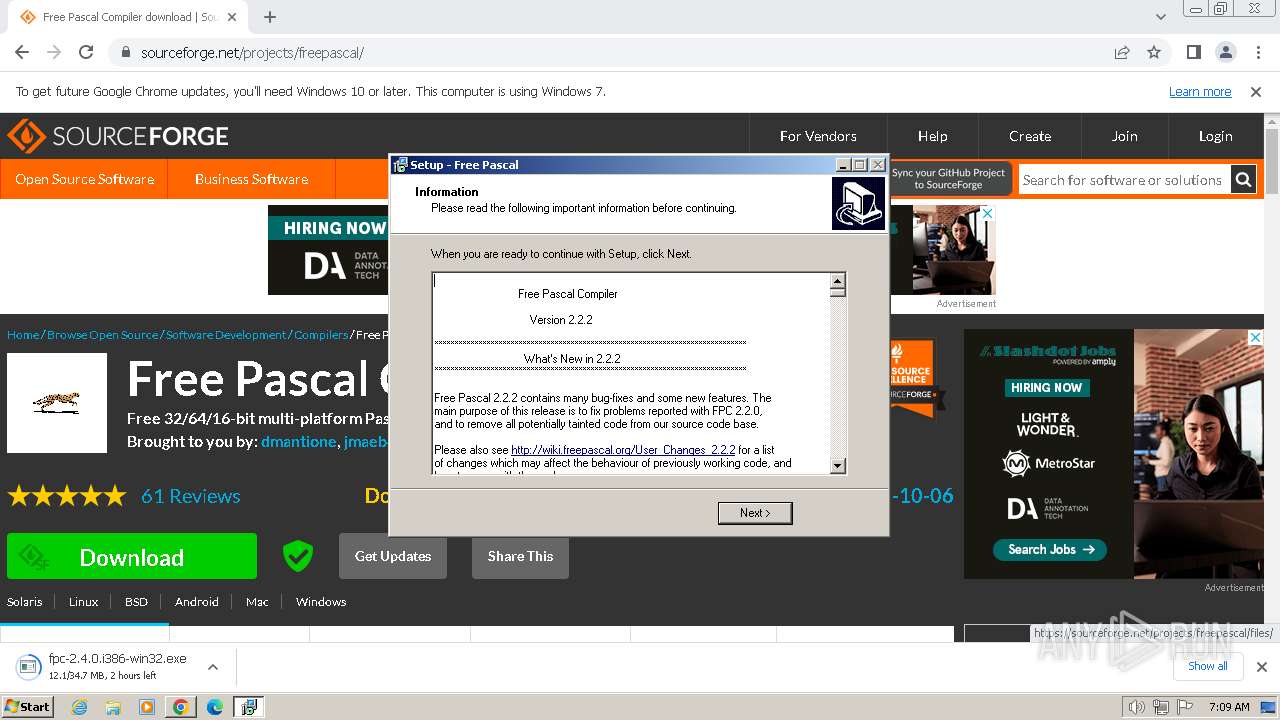
Checks supported languages
- fpc-2.2.2.i386-win32.exe (PID: 748)
- fpc-2.2.2.i386-win32.exe (PID: 980)
- fpc-2.2.2.i386-win32.tmp (PID: 2148)
- fpcmkcfg.exe (PID: 2616)
- fpcmkcfg.exe (PID: 3016)
- fpcmkcfg.exe (PID: 3260)
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
Reads the computer name
- fpc-2.2.2.i386-win32.tmp (PID: 2148)
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
Creates files in the program directory
- fpc-2.2.2.i386-win32.tmp (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
30
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3372 --field-trial-handle=892,i,8193624597876908942,13328106718418091537,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 748 | "C:\Users\admin\Downloads\fpc-2.2.2.i386-win32.exe" | C:\Users\admin\Downloads\fpc-2.2.2.i386-win32.exe | chrome.exe | ||||||||||||
User: admin Company: Free Pascal Team Integrity Level: MEDIUM Description: Free Pascal Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 980 | "C:\Users\admin\Downloads\fpc-2.2.2.i386-win32.exe" /SPAWNWND=$1F01AC /NOTIFYWND=$C0162 | C:\Users\admin\Downloads\fpc-2.2.2.i386-win32.exe | fpc-2.2.2.i386-win32.tmp | ||||||||||||
User: admin Company: Free Pascal Team Integrity Level: HIGH Description: Free Pascal Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4124 --field-trial-handle=892,i,8193624597876908942,13328106718418091537,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3924 --field-trial-handle=892,i,8193624597876908942,13328106718418091537,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1764 --field-trial-handle=892,i,8193624597876908942,13328106718418091537,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1884 --field-trial-handle=892,i,8193624597876908942,13328106718418091537,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1792 --field-trial-handle=892,i,8193624597876908942,13328106718418091537,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\AppData\Local\Temp\is-MCJ8M.tmp\fpc-2.2.2.i386-win32.tmp" /SL5="$C0162,35209052,53248,C:\Users\admin\Downloads\fpc-2.2.2.i386-win32.exe" | C:\Users\admin\AppData\Local\Temp\is-MCJ8M.tmp\fpc-2.2.2.i386-win32.tmp | — | fpc-2.2.2.i386-win32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1508 --field-trial-handle=892,i,8193624597876908942,13328106718418091537,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
5 486
Read events
5 375
Write events
110
Delete events
1
Modification events
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
250
Suspicious files
3 603
Text files
580
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1635ab.TMP | — | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF163c33.TMP | — | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1635ba.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF164839.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
72
DNS requests
75
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3456 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3136 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
3136 | chrome.exe | 172.64.150.145:443 | sourceforge.net | CLOUDFLARENET | US | unknown |
3136 | chrome.exe | 104.18.40.209:443 | a.fsdn.com | CLOUDFLARENET | — | shared |
3136 | chrome.exe | 104.16.57.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
3136 | chrome.exe | 87.230.98.76:443 | d.delivery.consentmanager.net | PlusServer GmbH | DE | unknown |
3136 | chrome.exe | 195.181.175.16:443 | cdn.consentmanager.net | Datacamp Limited | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
sourceforge.net |
| whitelisted |
a.fsdn.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
d.delivery.consentmanager.net |
| unknown |
cdn.consentmanager.net |
| malicious |
c.sf-syn.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |