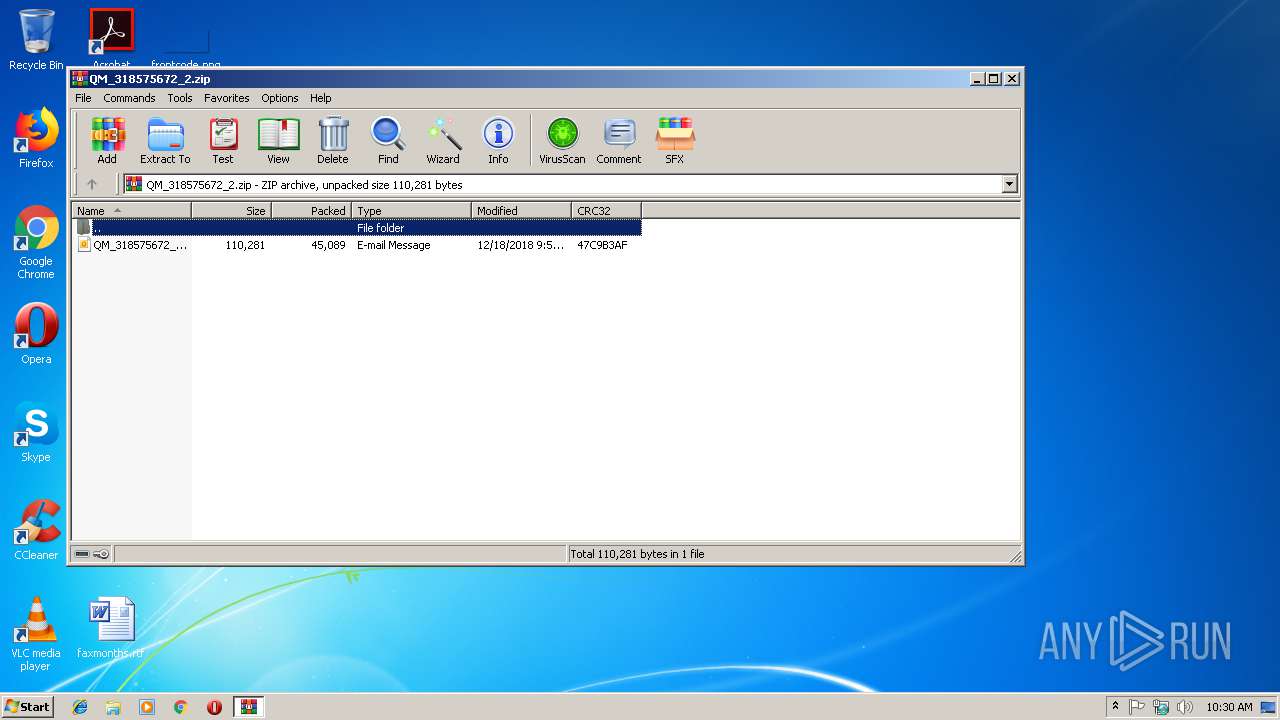
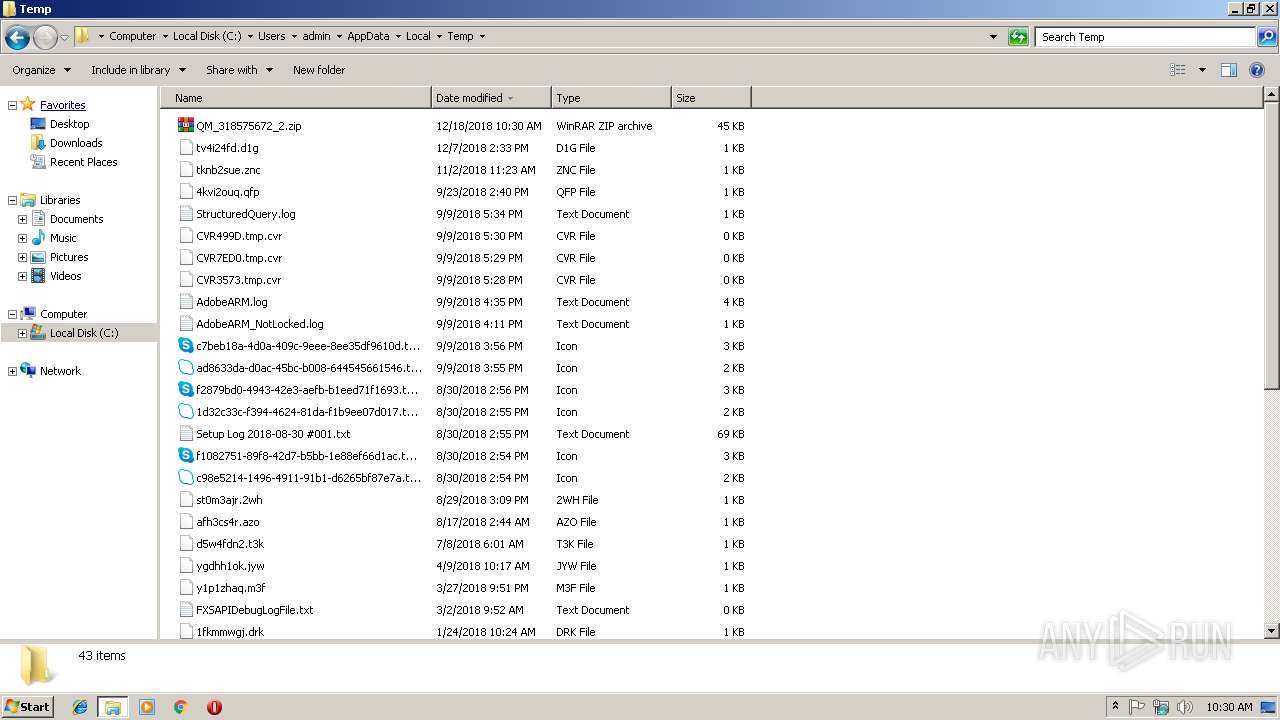
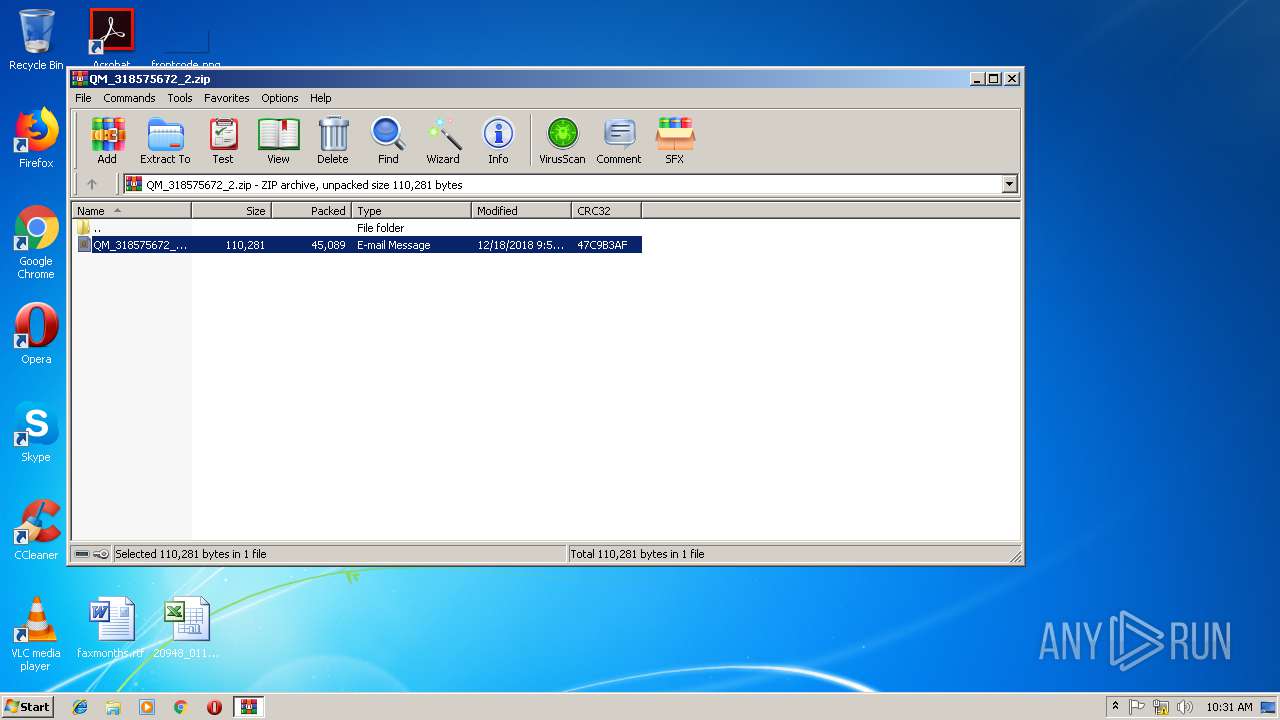
| File name: | QM_318575672_2.zip |
| Full analysis: | https://app.any.run/tasks/399f500e-da73-4f4f-9afe-7e0b03e7cd28 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 10:30:08 |
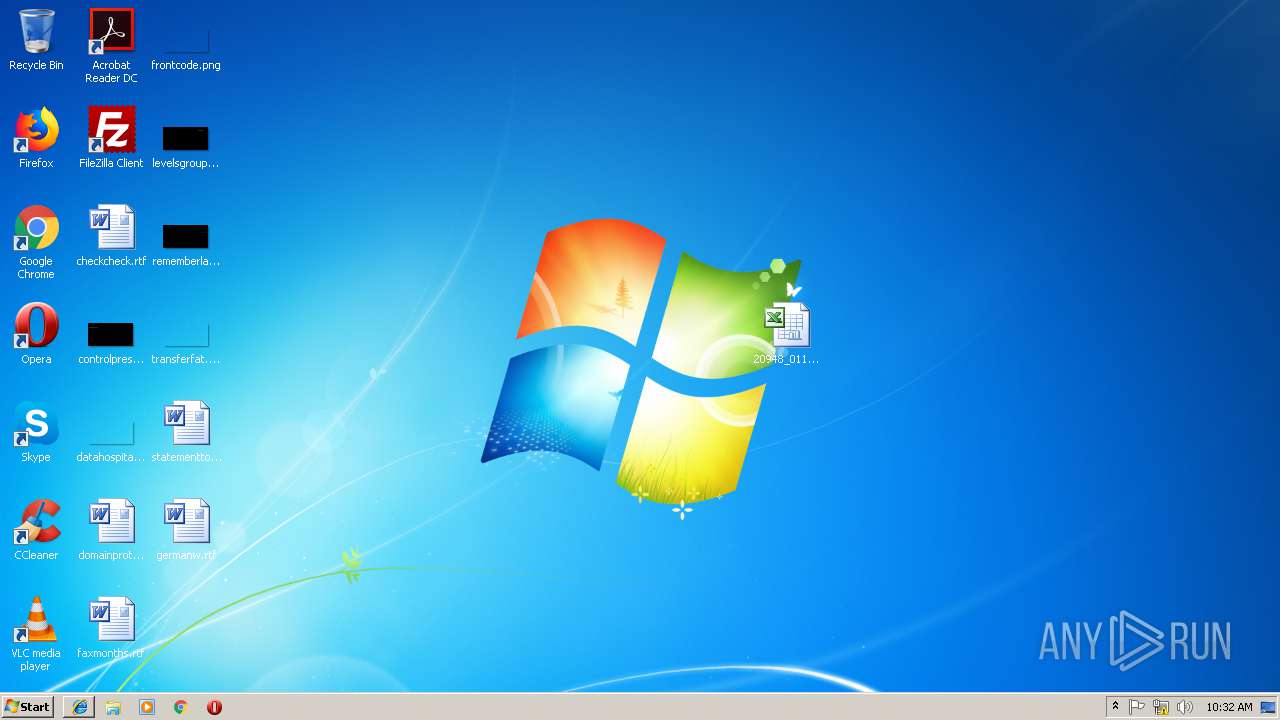
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
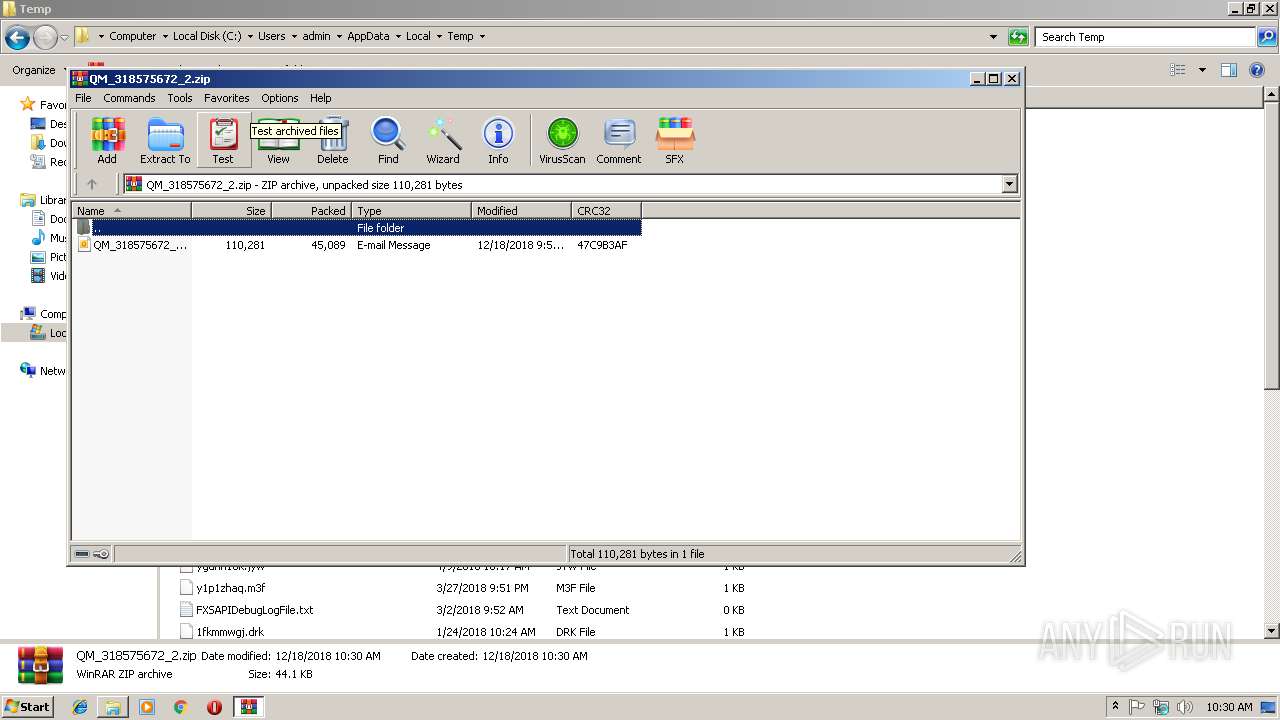
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
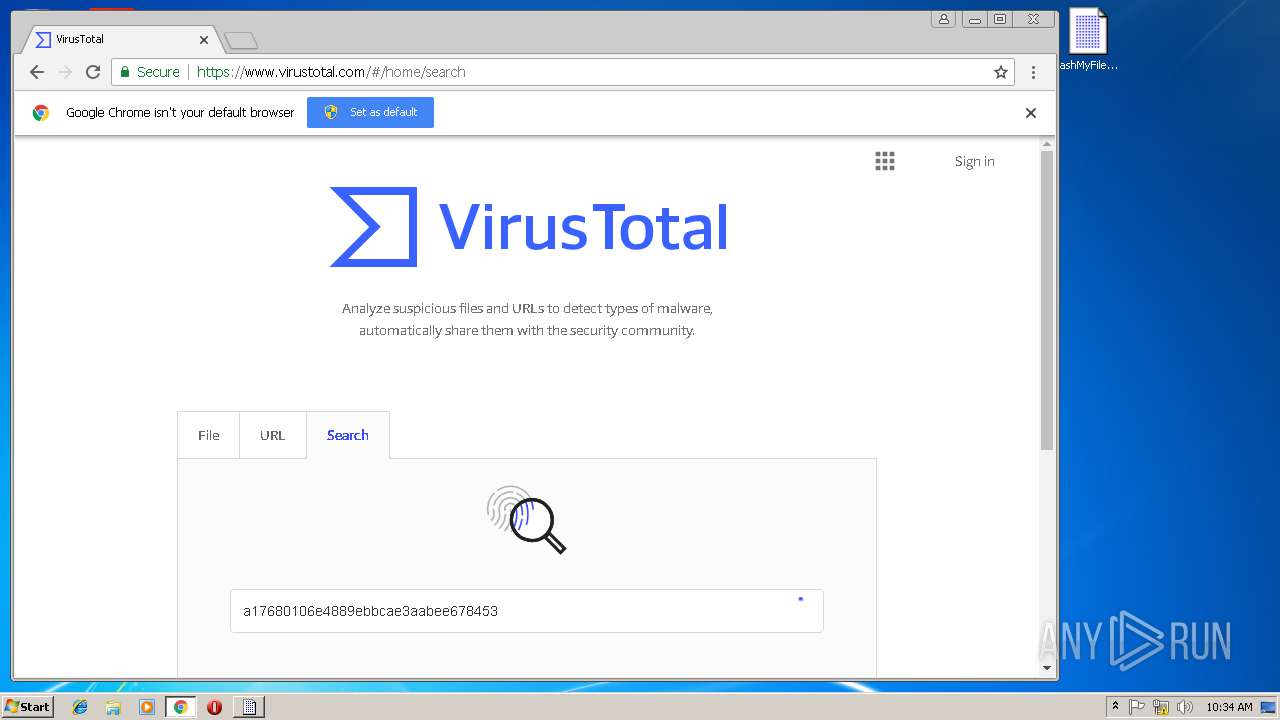
| MD5: | A02EB3C70D7DAD10B23679051E8D050F |
| SHA1: | AE6F49677D817CE7BA54C12AEE17172DBFD83308 |
| SHA256: | DEA5DC1FAD73CB526FD89E146EC22CFEF4855F7184E960D031B82CF26CD10306 |
| SSDEEP: | 768:vcXwfzc+vkHYlz0xswAqkH7pDvofBnEr4faUkdw1tY7nCwMNgKjrKbmigKX5tu6:vcXwgEkHYlz0Ow3esnErWa5KtJguogs |
MALICIOUS
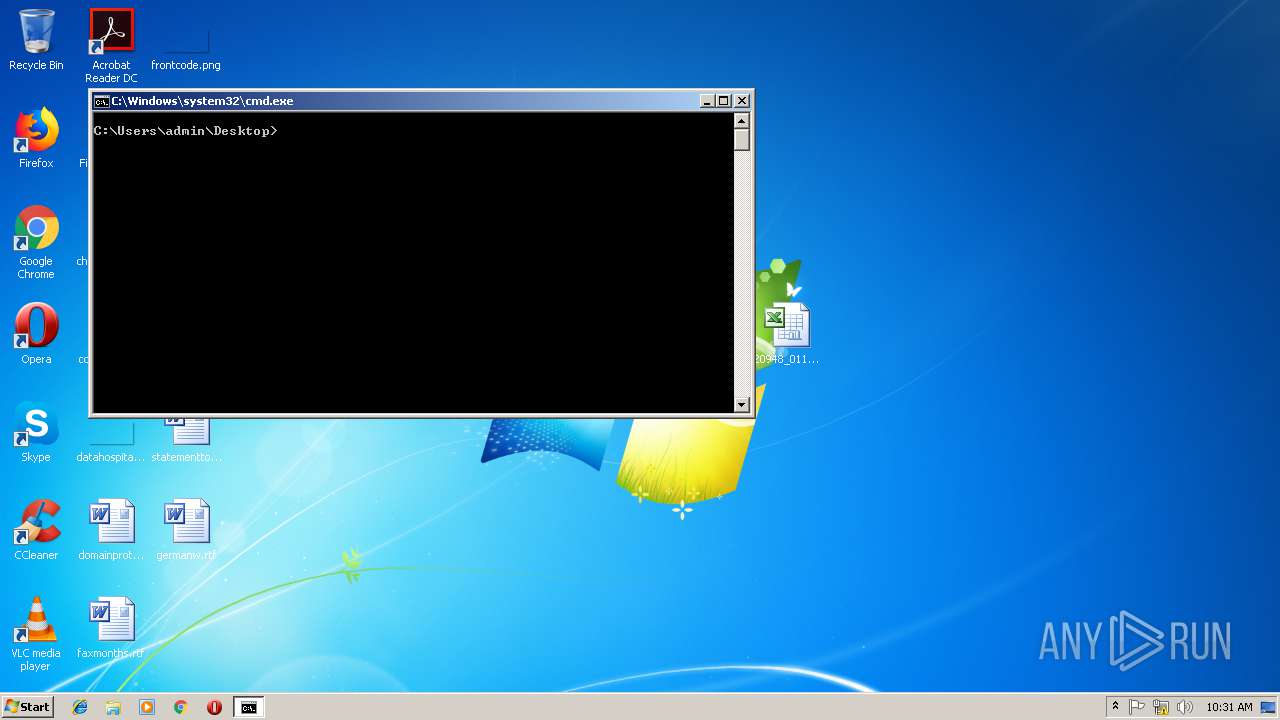
Executes PowerShell scripts
- cmd.exe (PID: 2296)
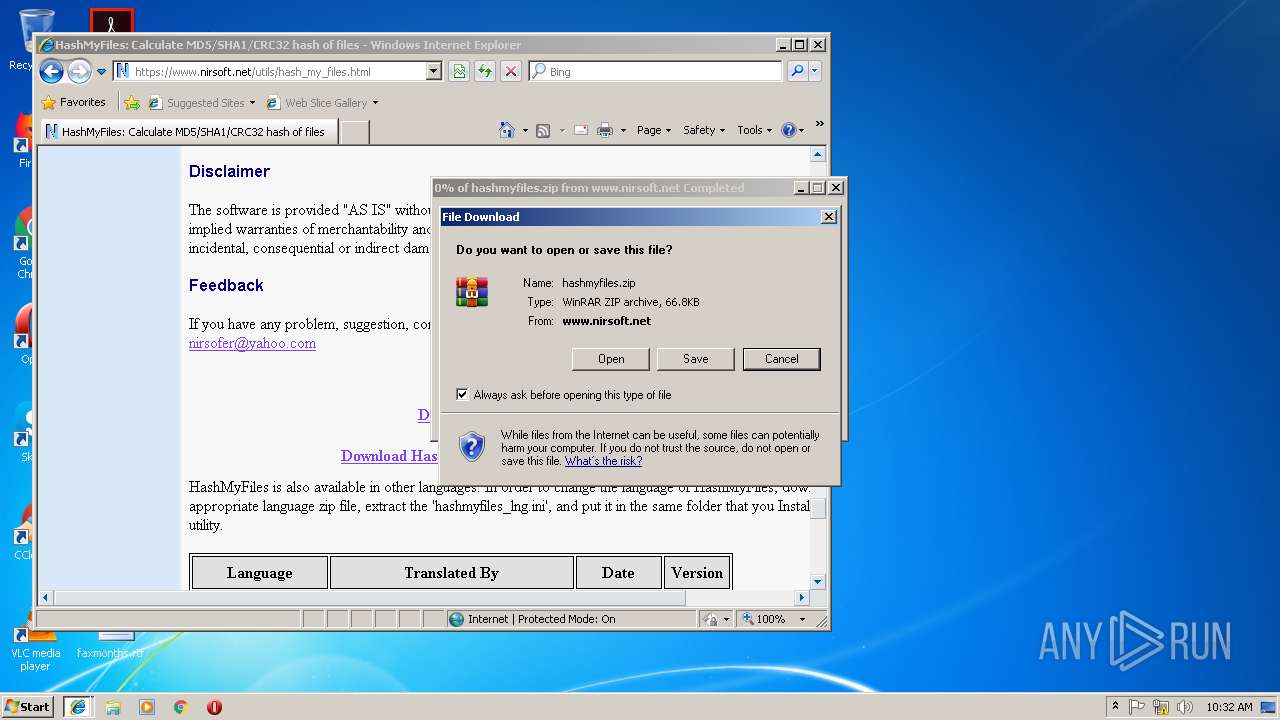
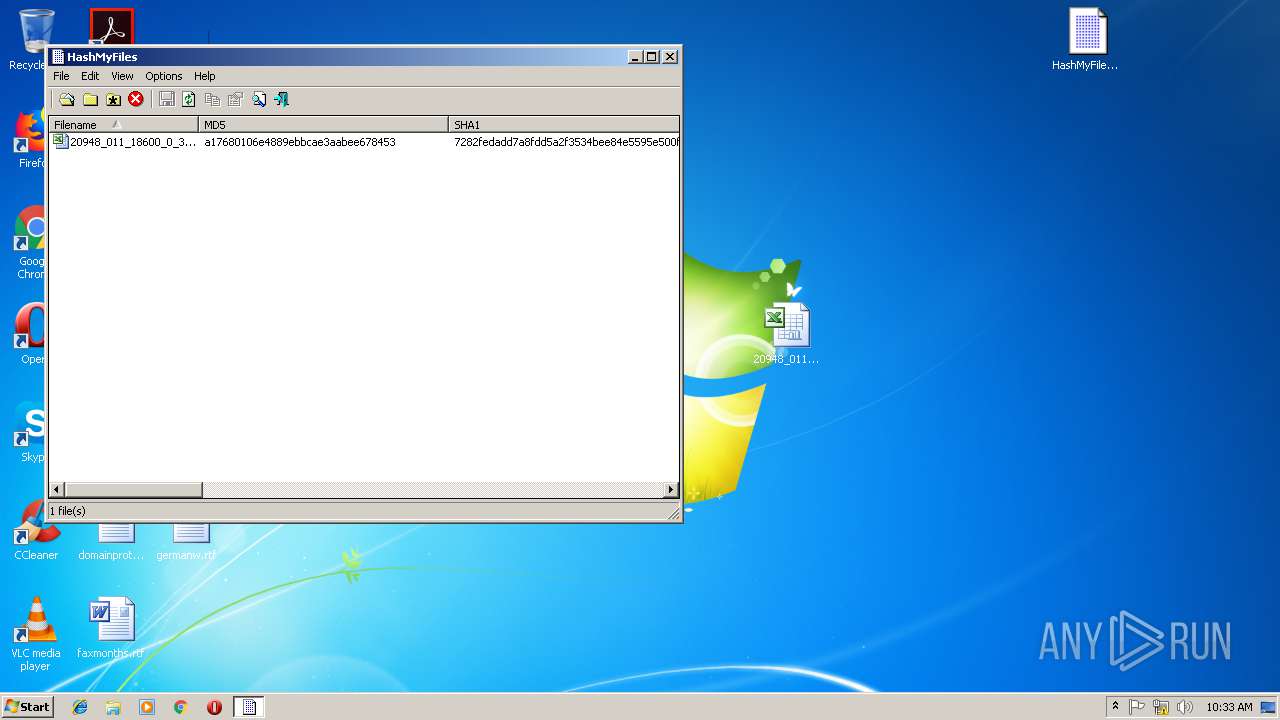
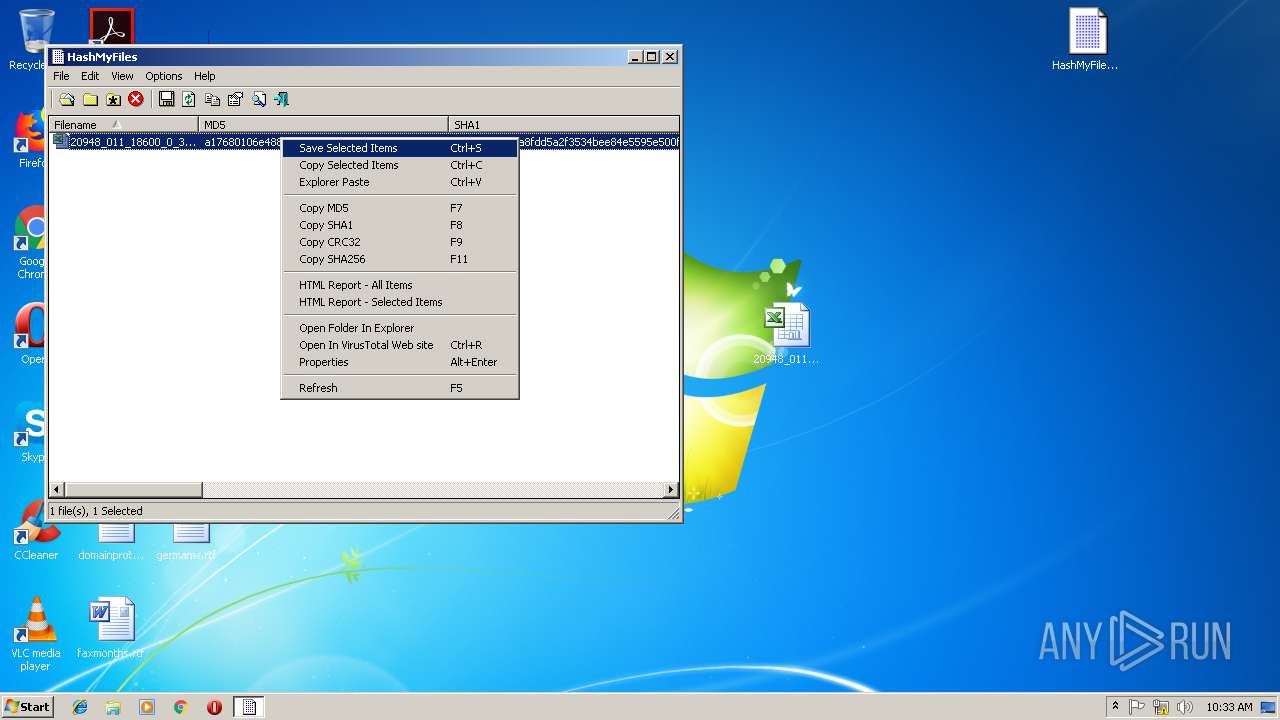
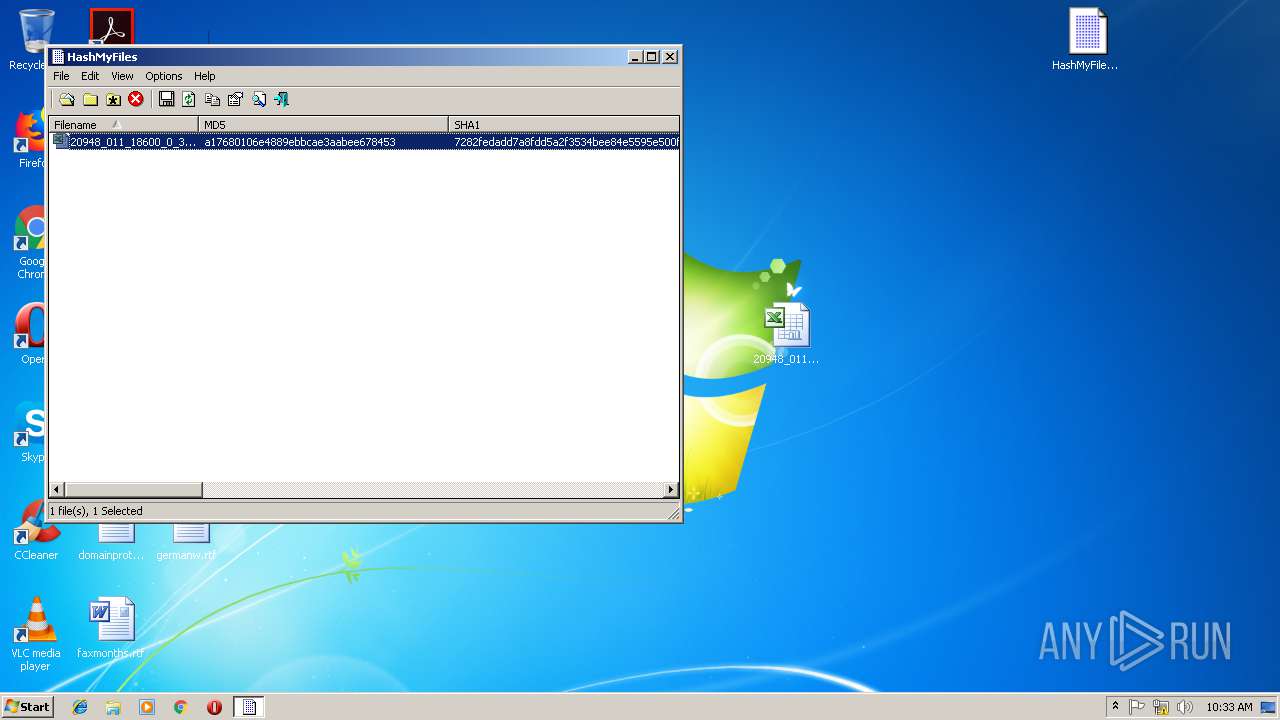
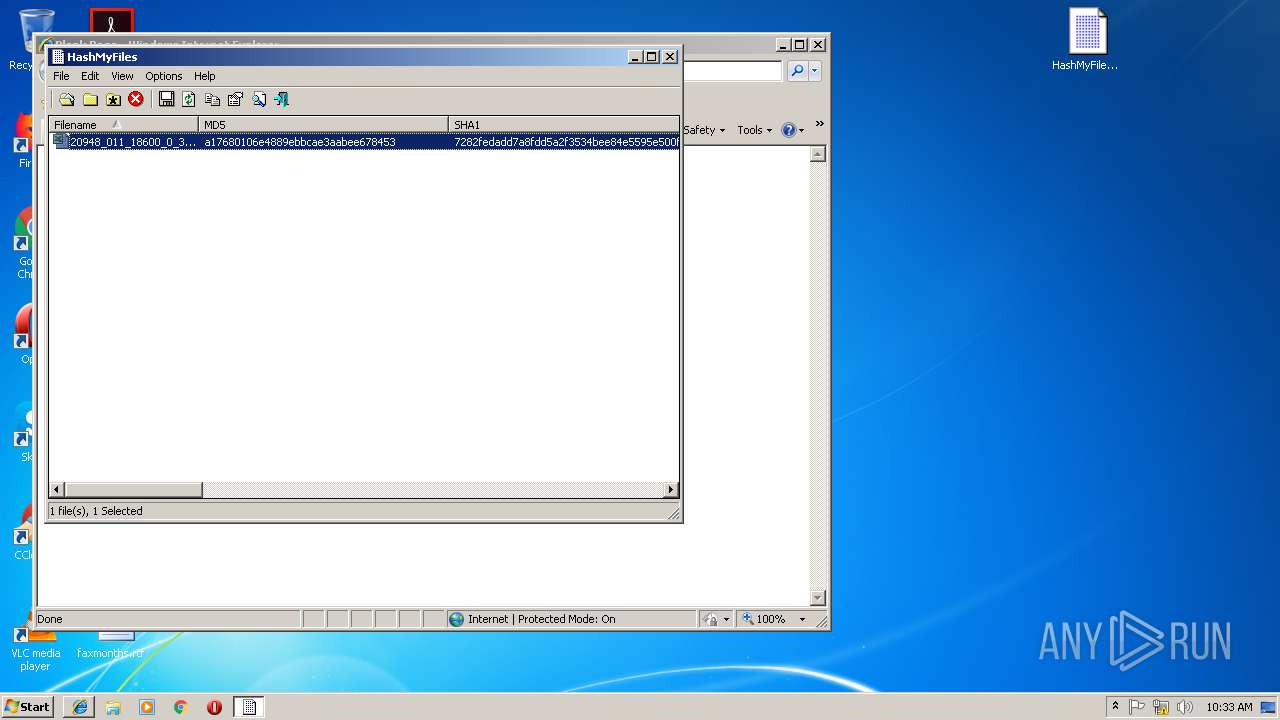
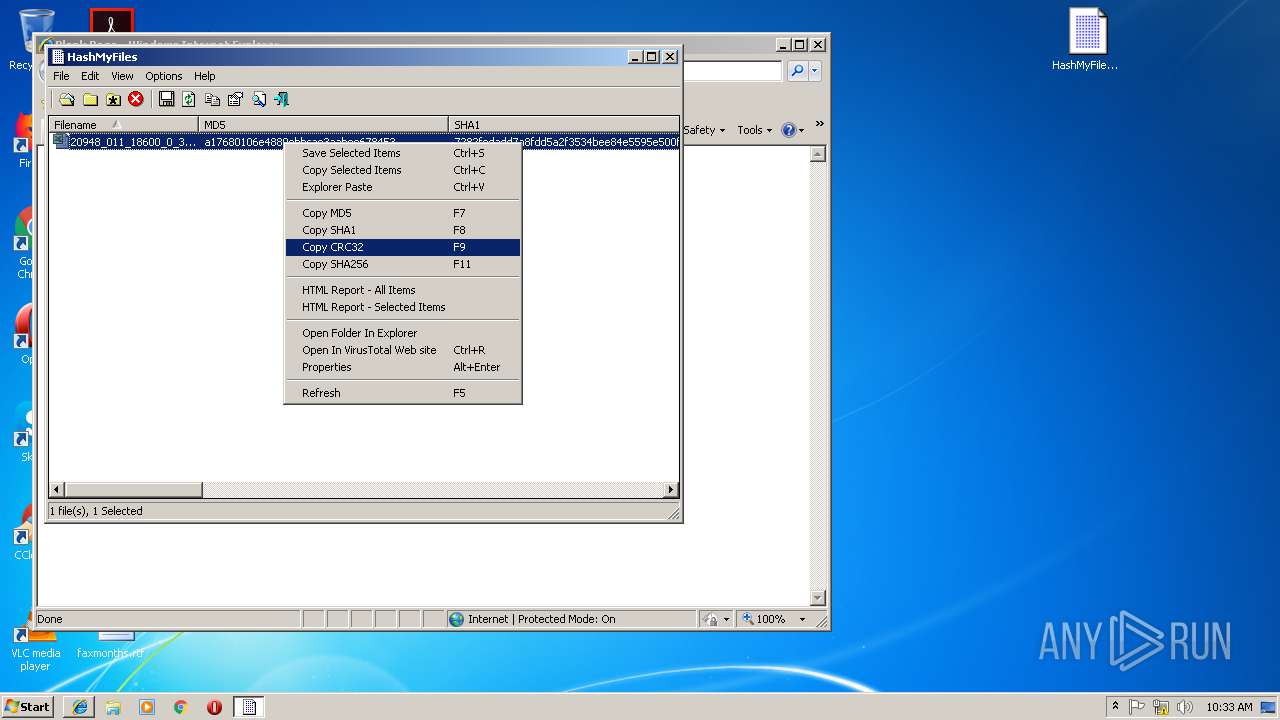
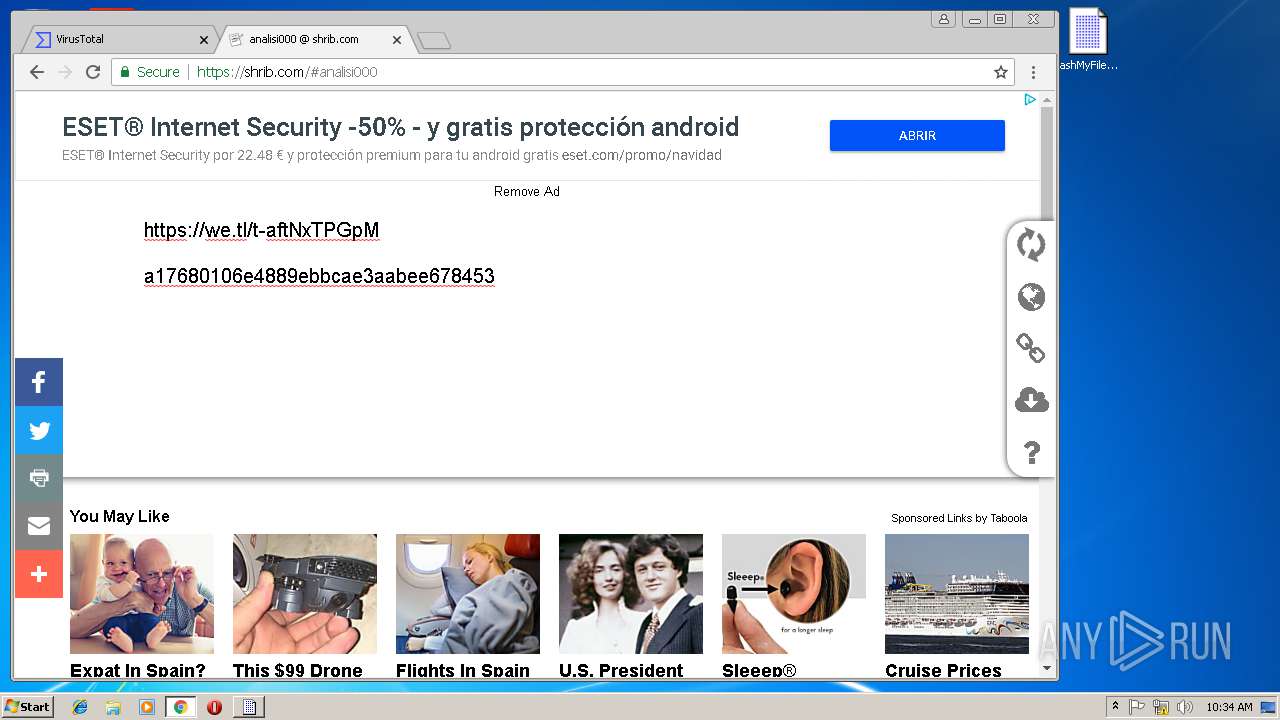
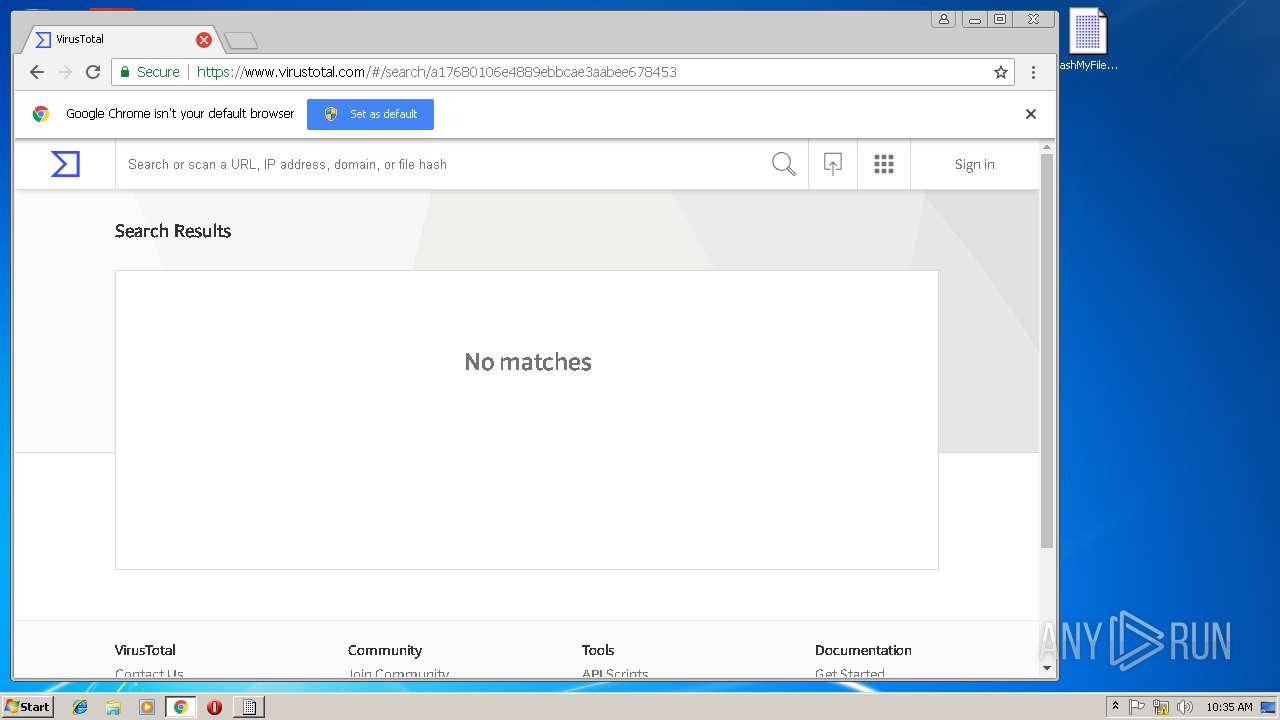
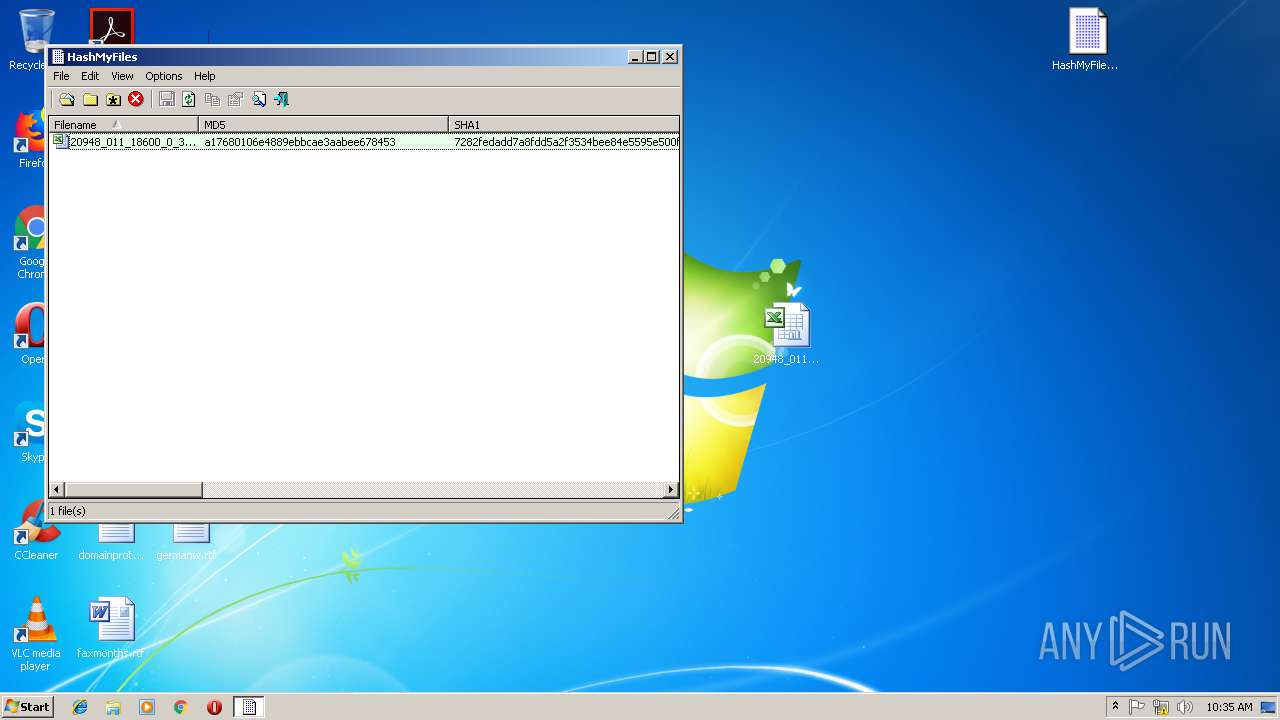
Application was dropped or rewritten from another process
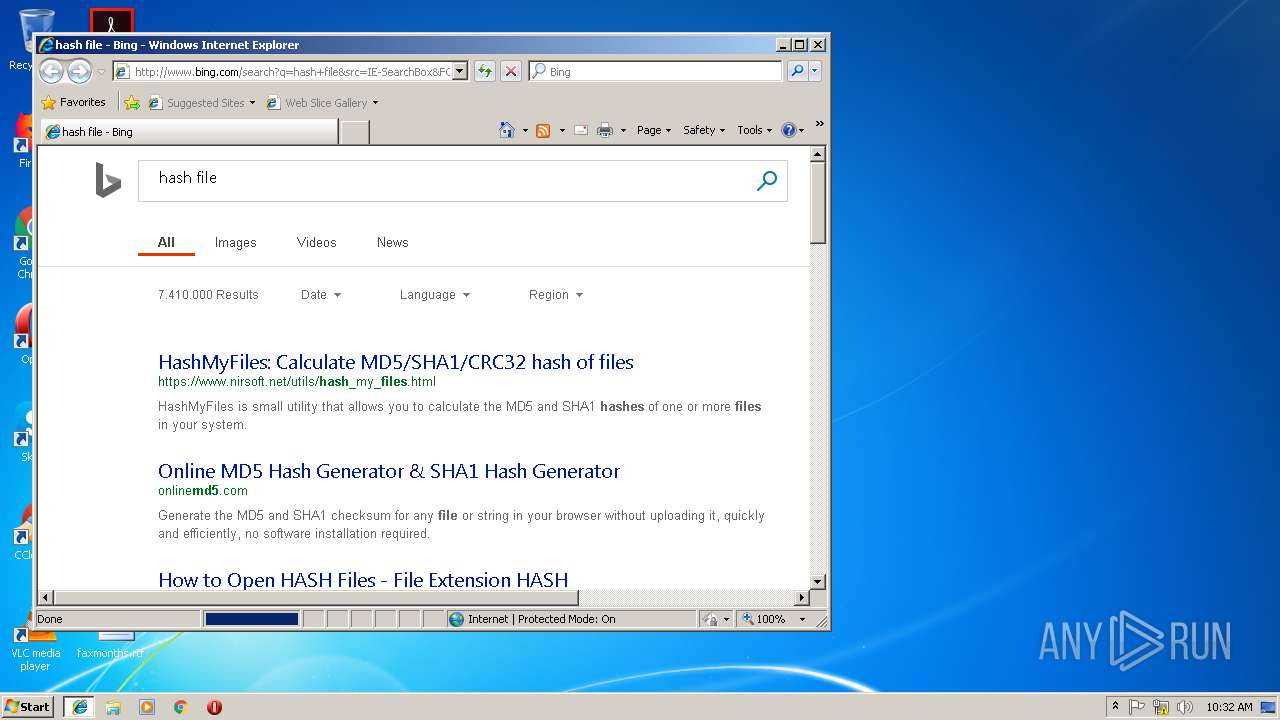
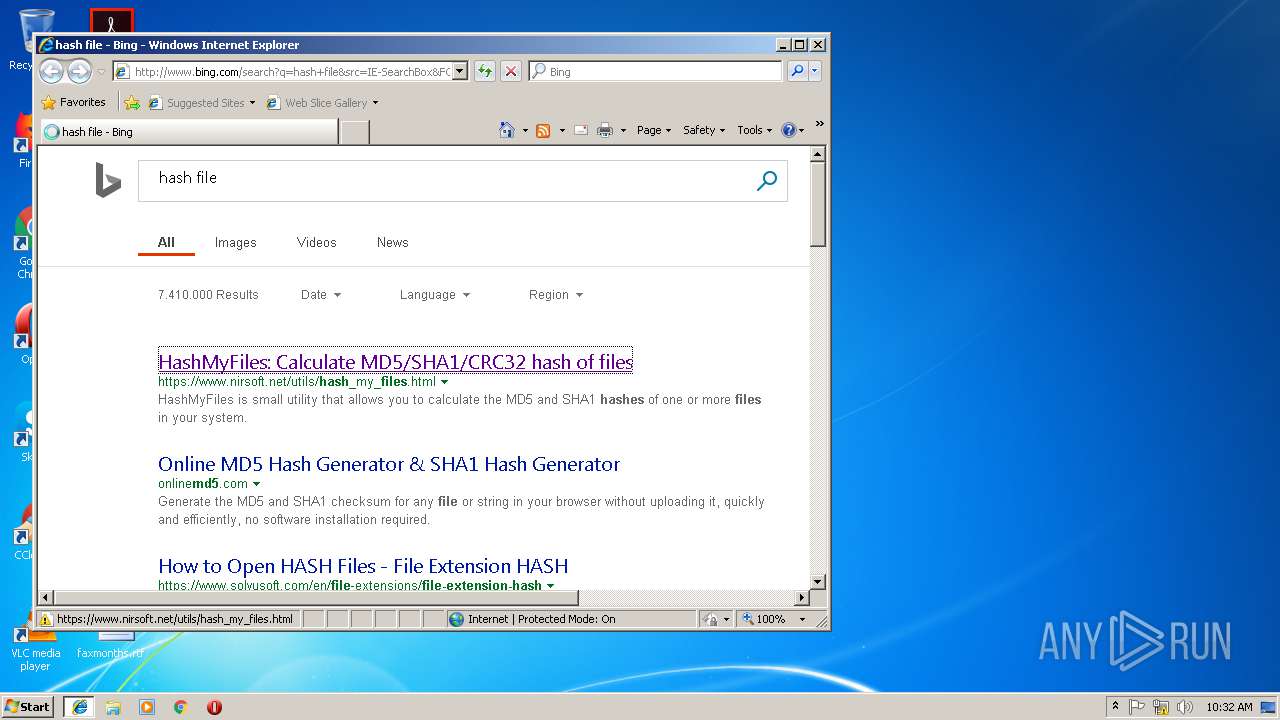
- HashMyFiles.exe (PID: 1320)
SUSPICIOUS
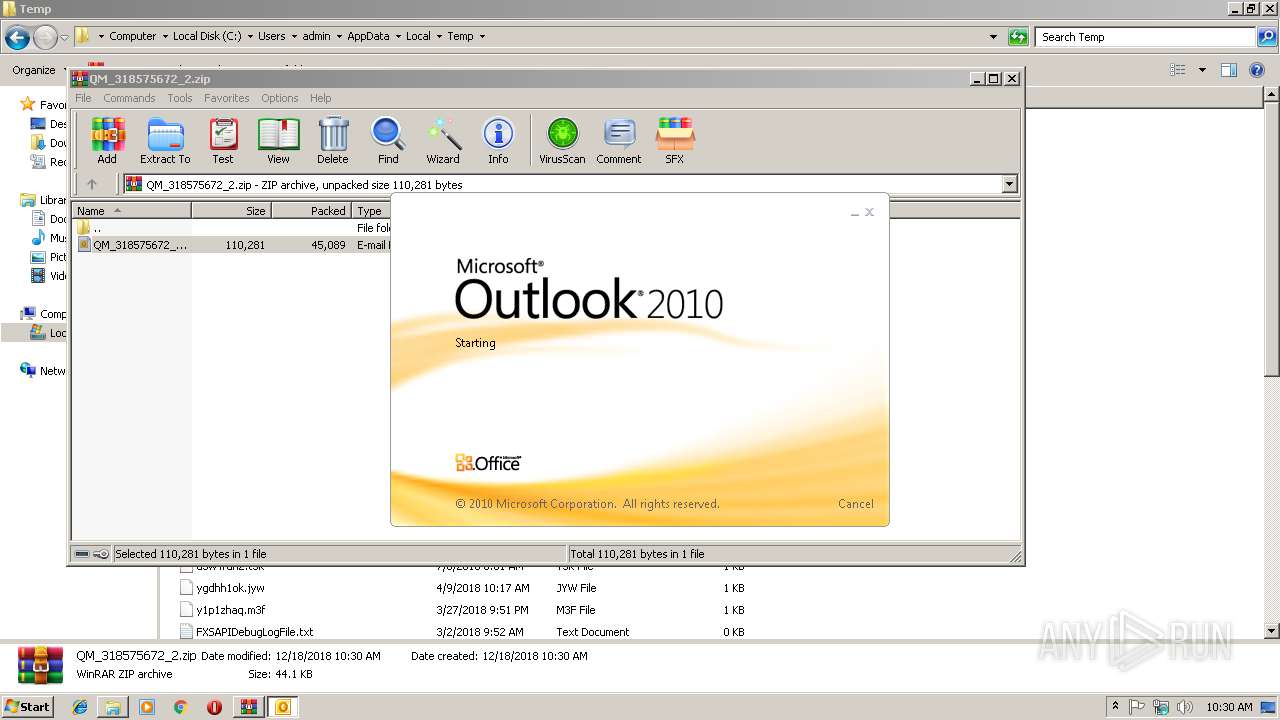
Reads Internet Cache Settings
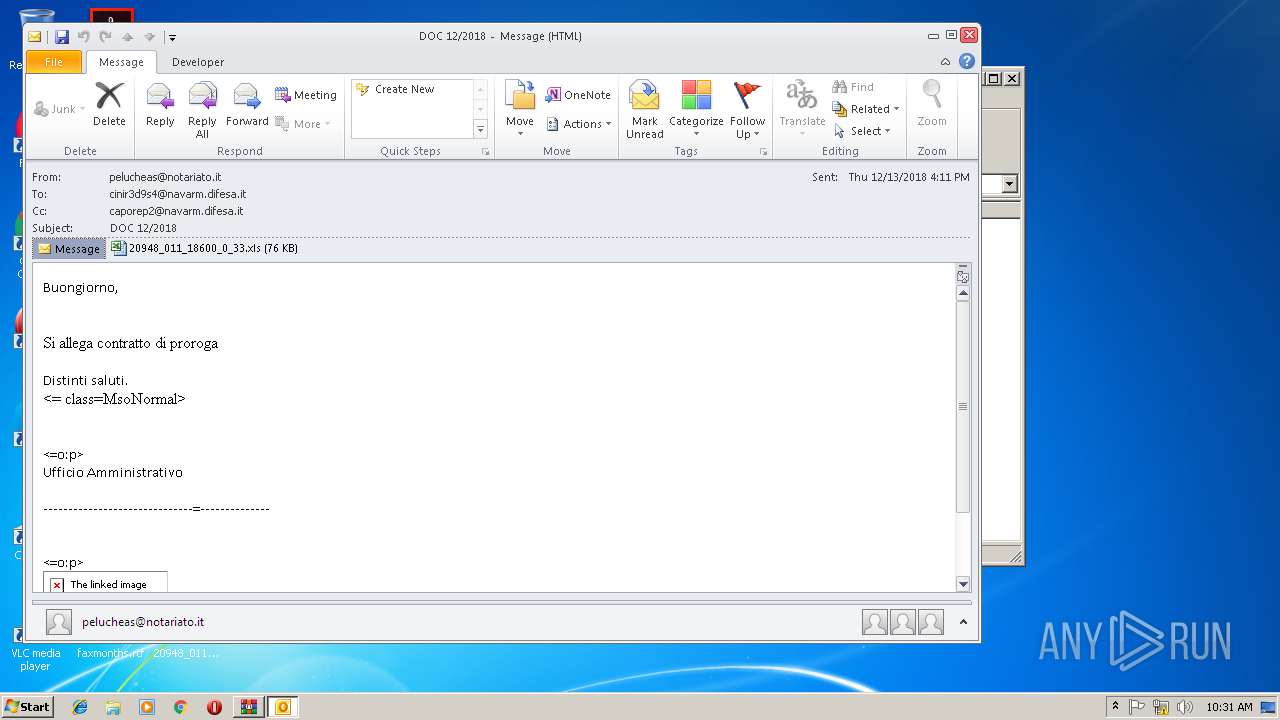
- OUTLOOK.EXE (PID: 2912)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2912)
- powershell.exe (PID: 3172)
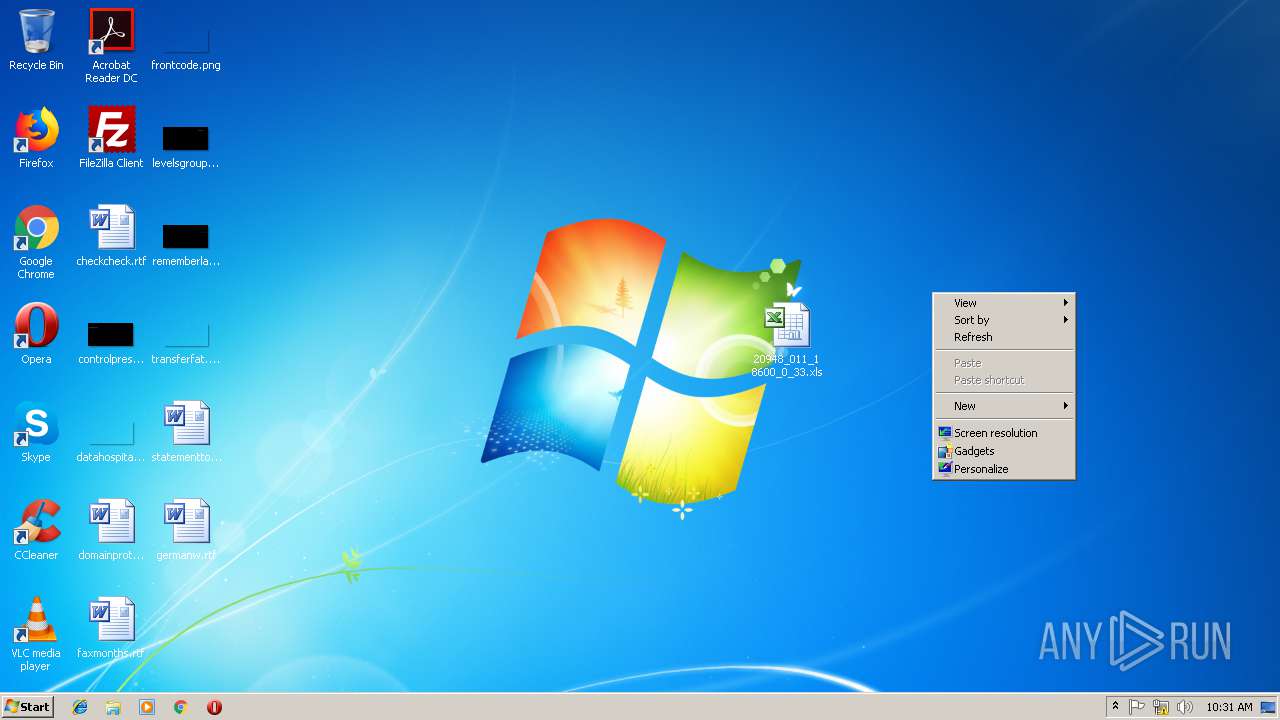
Executable content was dropped or overwritten
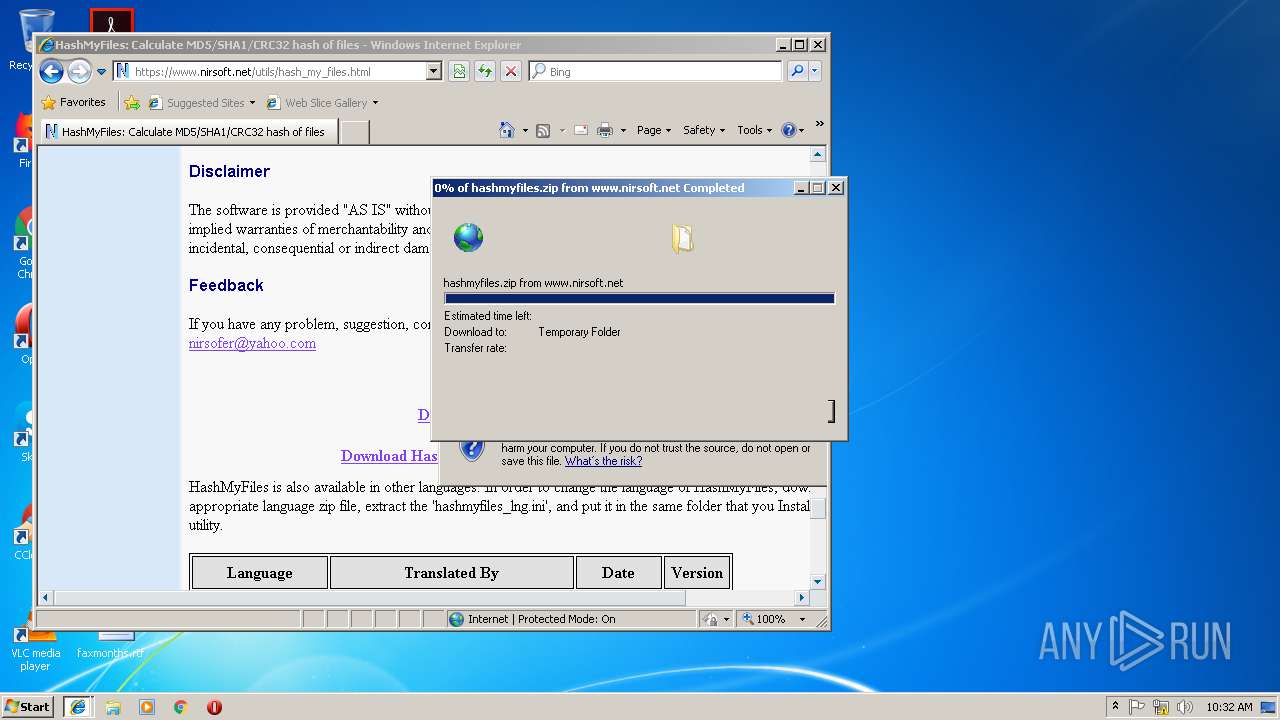
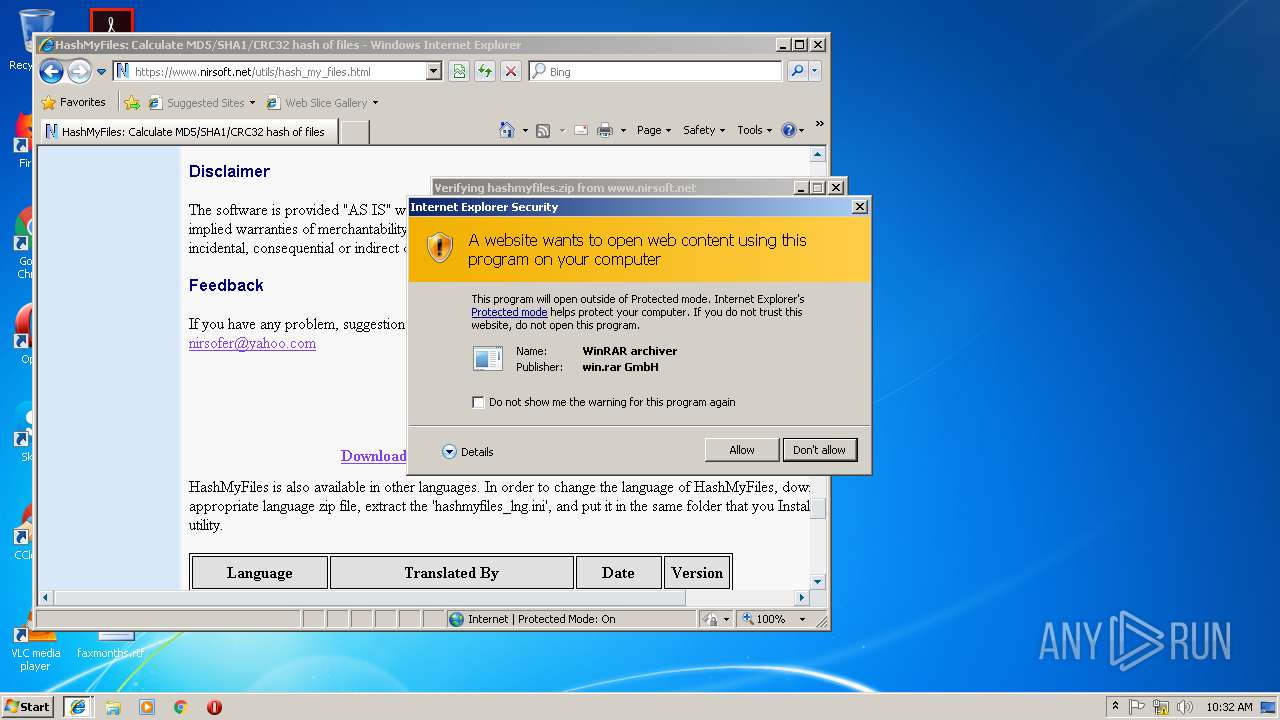
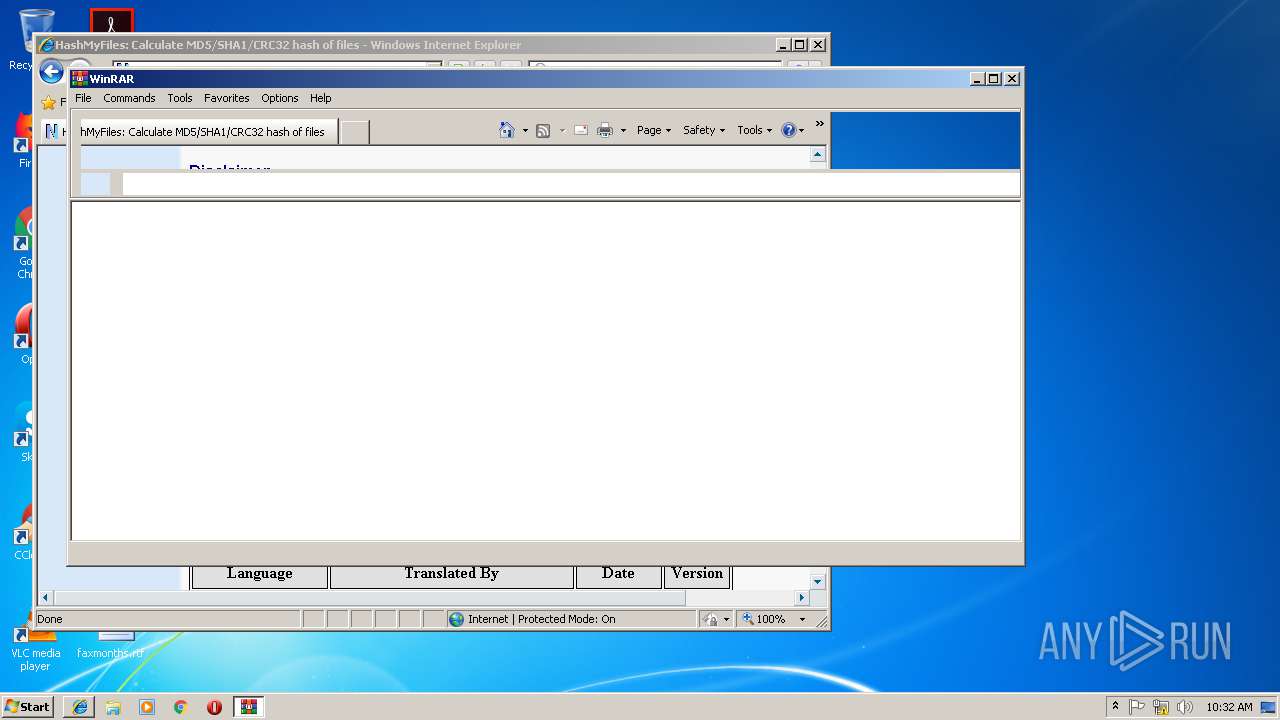
- WinRAR.exe (PID: 2068)
INFO
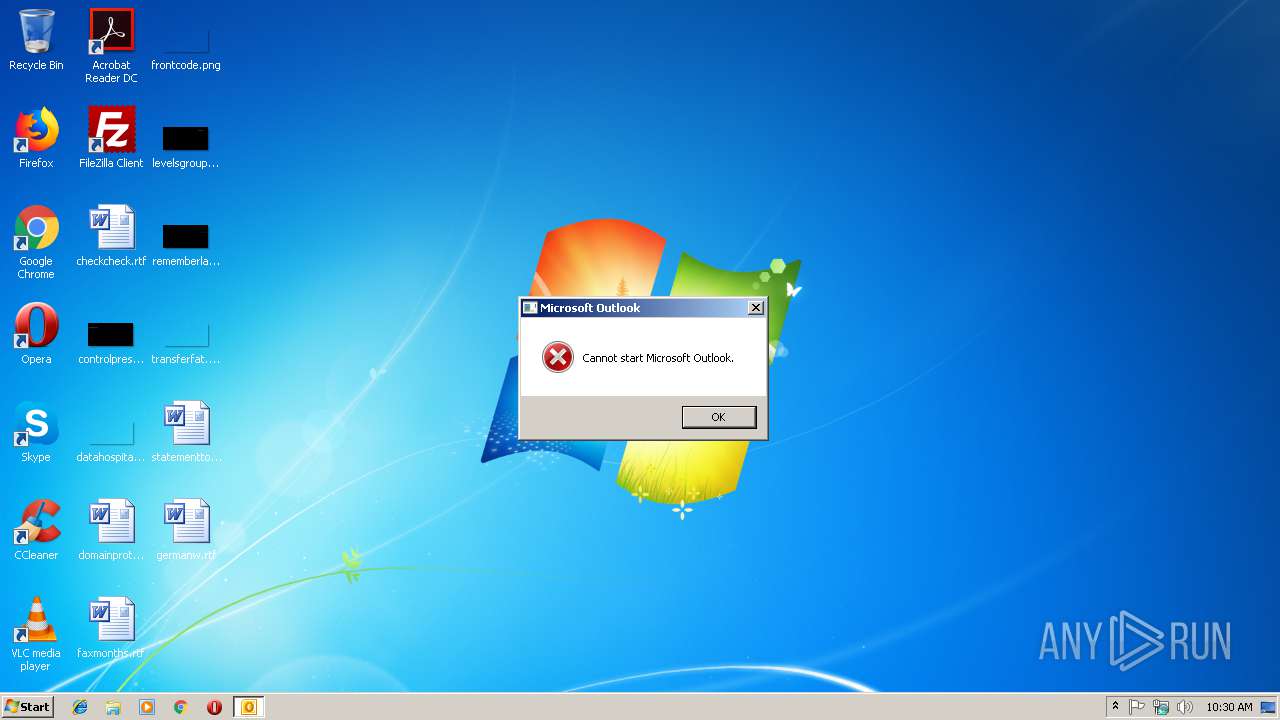
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2472)
- OUTLOOK.EXE (PID: 2912)
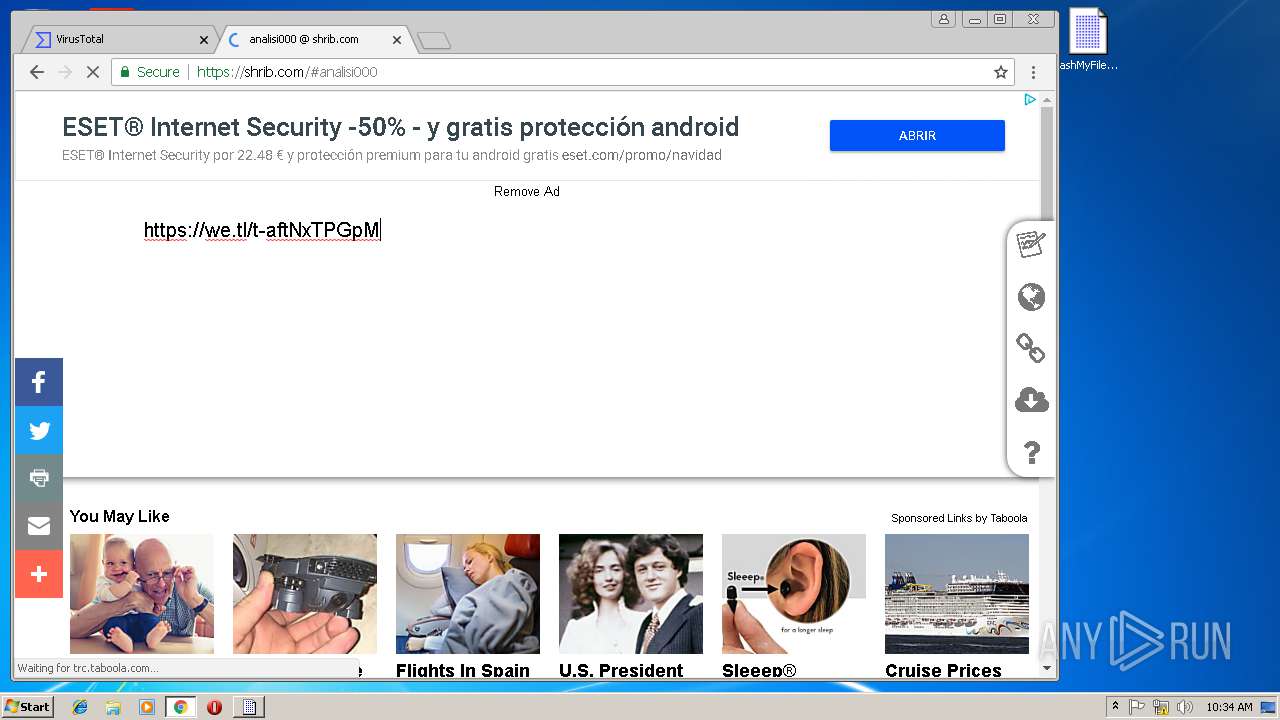
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2940)
- WinRAR.exe (PID: 3596)
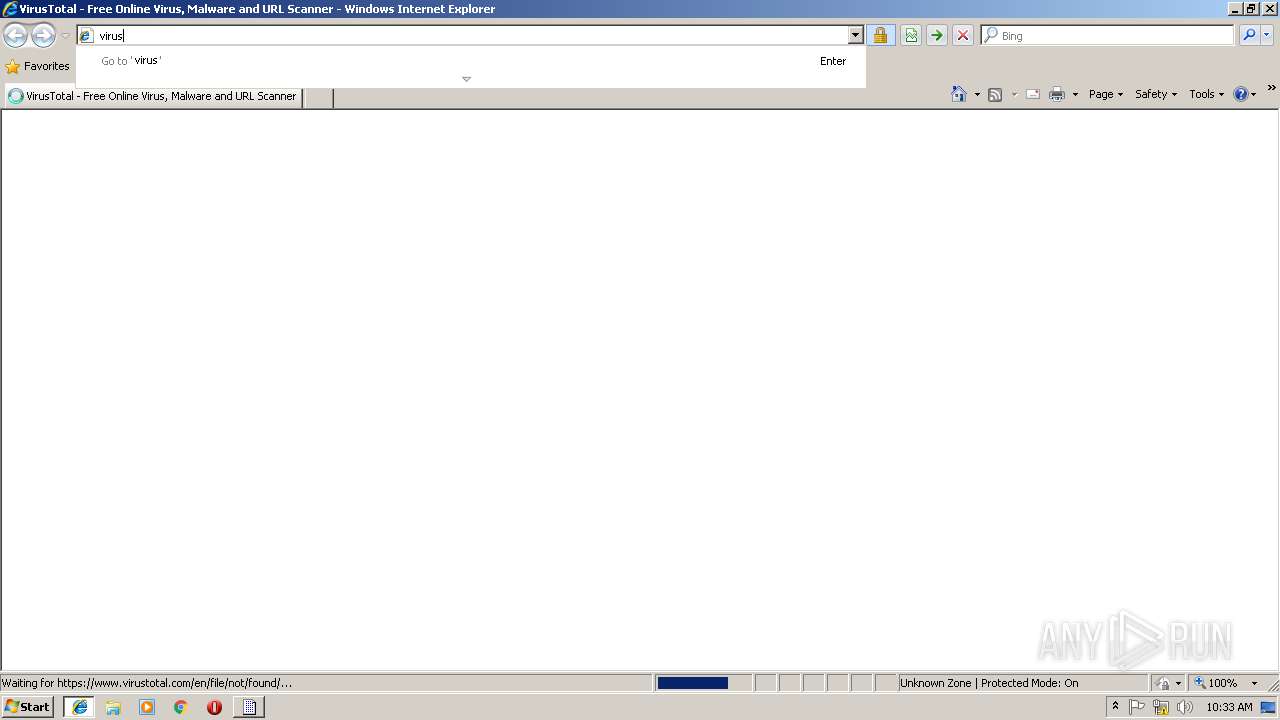
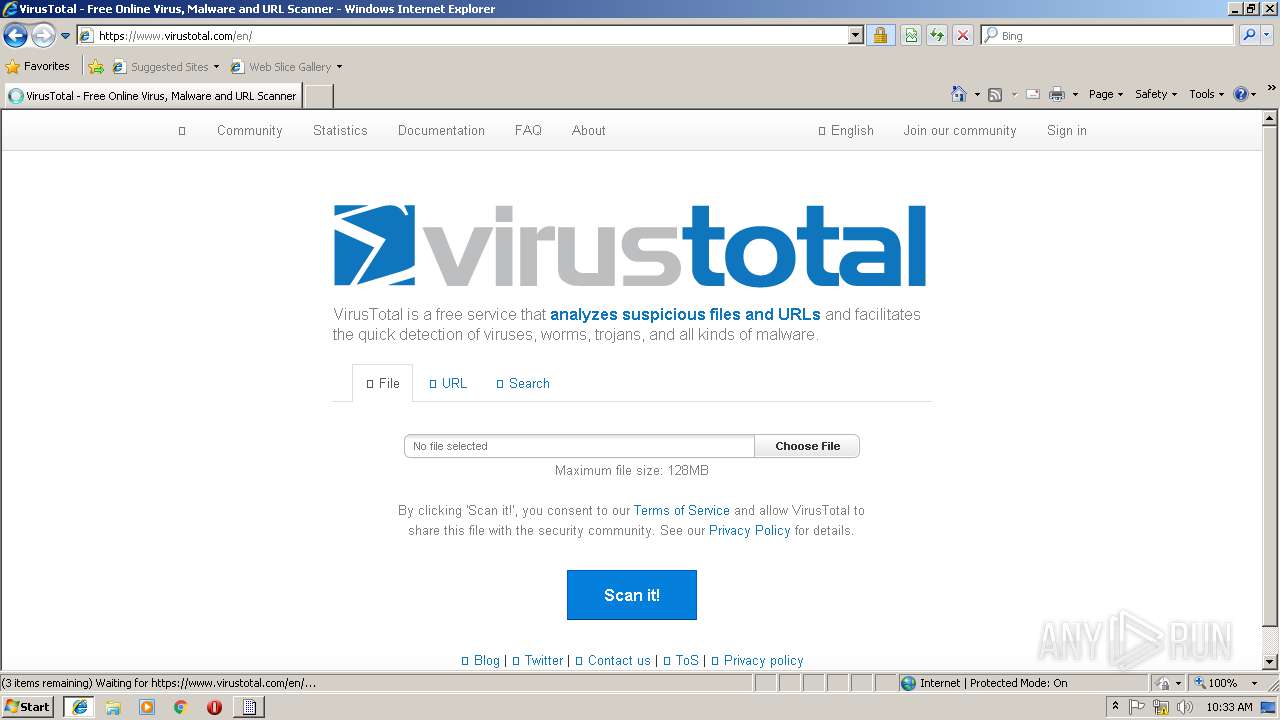
- iexplore.exe (PID: 3300)
Application launched itself
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 3176)
- chrome.exe (PID: 3956)
Creates files in the user directory
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 3004)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2212)
- iexplore.exe (PID: 3672)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2476)
- iexplore.exe (PID: 3176)
Reads Internet Cache Settings
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 4048)
- iexplore.exe (PID: 3672)
Reads internet explorer settings
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 4048)
- iexplore.exe (PID: 3672)
Reads settings of System Certificates
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 3176)
Changes internet zones settings
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 3004)
Changes settings of System certificates
- iexplore.exe (PID: 3176)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:18 10:57:07 |
| ZipCRC: | 0x47c9b3af |
| ZipCompressedSize: | 45089 |
| ZipUncompressedSize: | 110281 |
| ZipFileName: | QM_318575672_2.eml |
Total processes
67
Monitored processes
29
Malicious processes
1
Suspicious processes
1
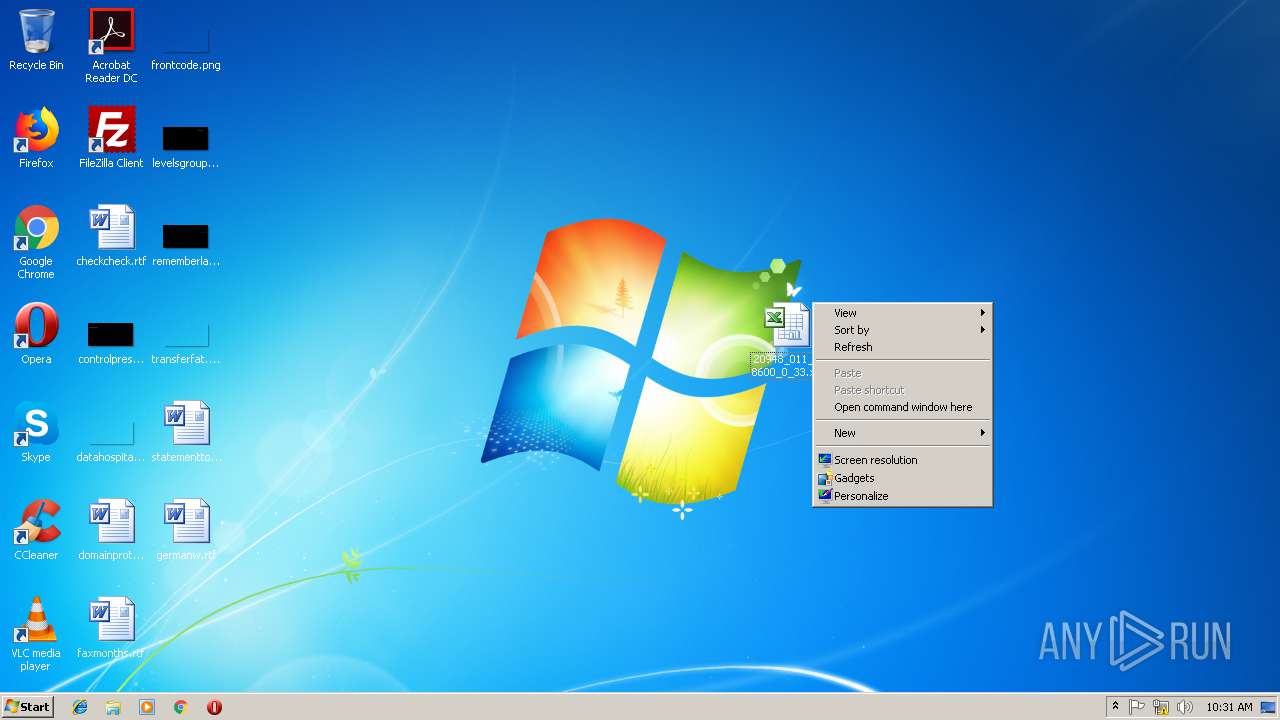
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18296270147029666929,17249125362124926726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=ED32AFE6755AB18E477D23BDF5119265 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=ED32AFE6755AB18E477D23BDF5119265 --renderer-client-id=6 --mojo-platform-channel-handle=3540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
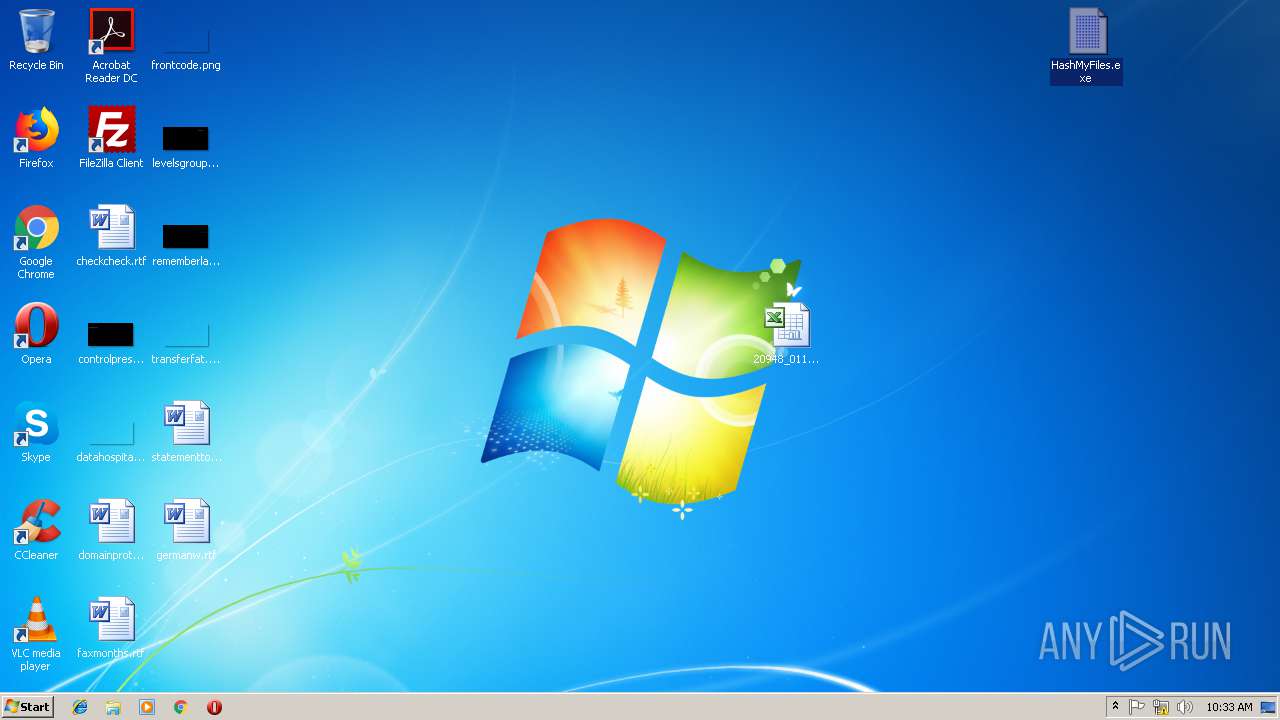
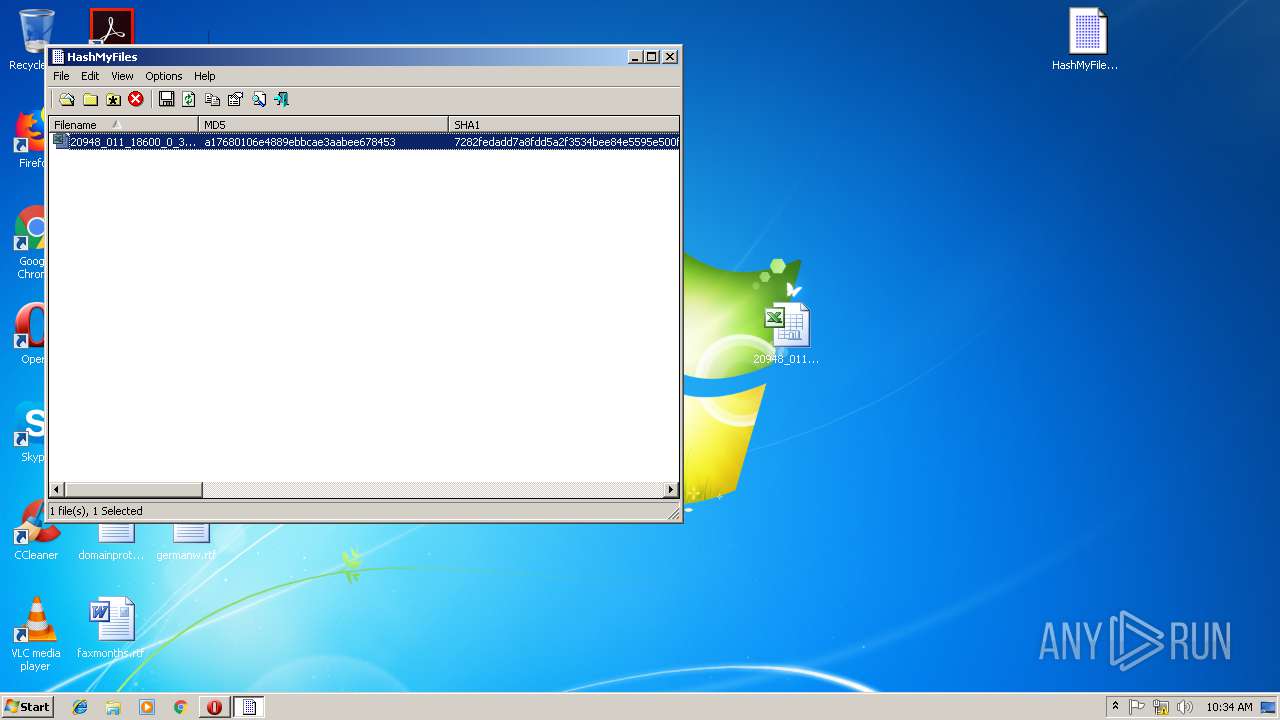
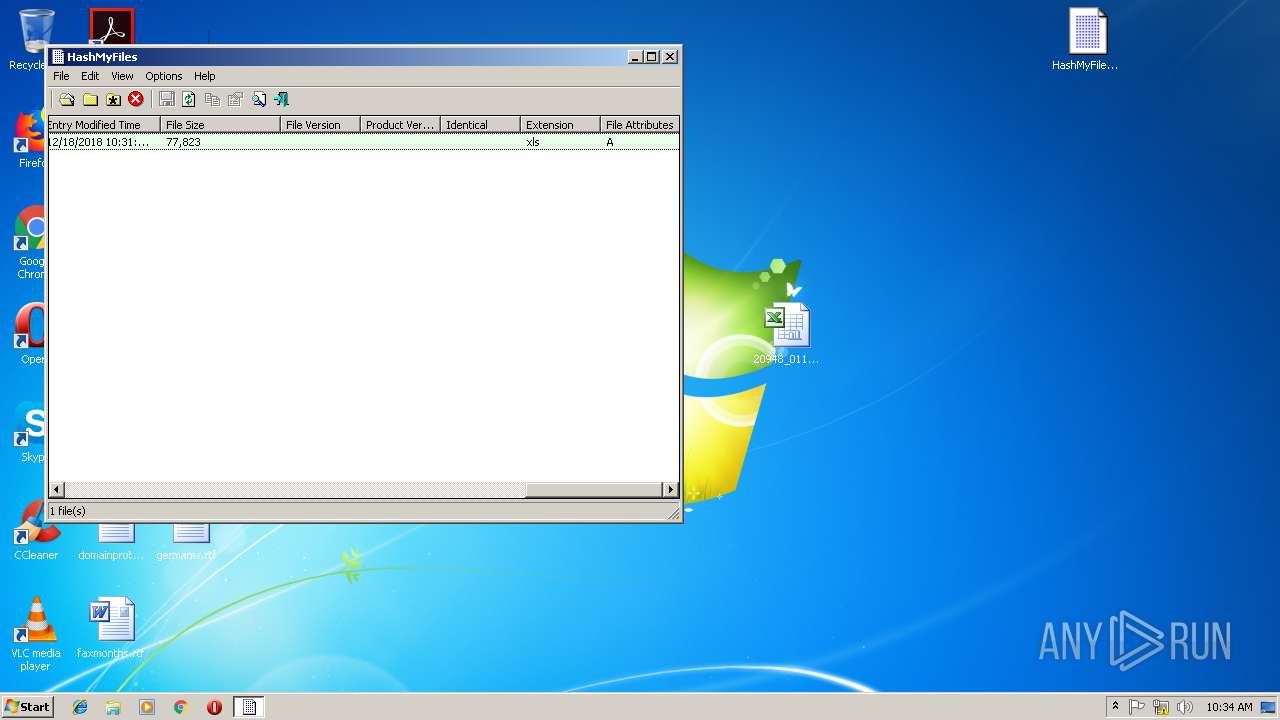
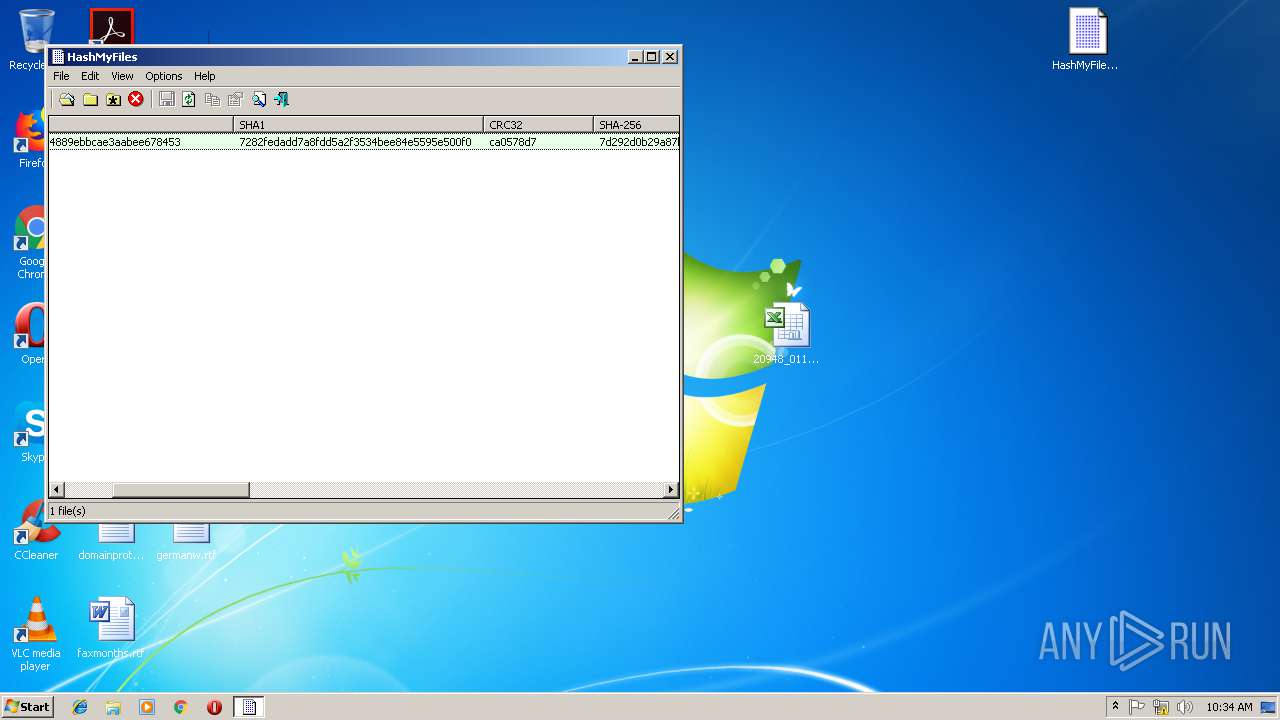
| 1320 | "C:\Users\admin\Desktop\HashMyFiles.exe" | C:\Users\admin\Desktop\HashMyFiles.exe | — | explorer.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: HashMyFiles Exit code: 0 Version: 2.31 Modules
| |||||||||||||||
| 1464 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18296270147029666929,17249125362124926726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8E2EF0C76B494BE836A7B3FA5863DE0F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8E2EF0C76B494BE836A7B3FA5863DE0F --renderer-client-id=12 --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
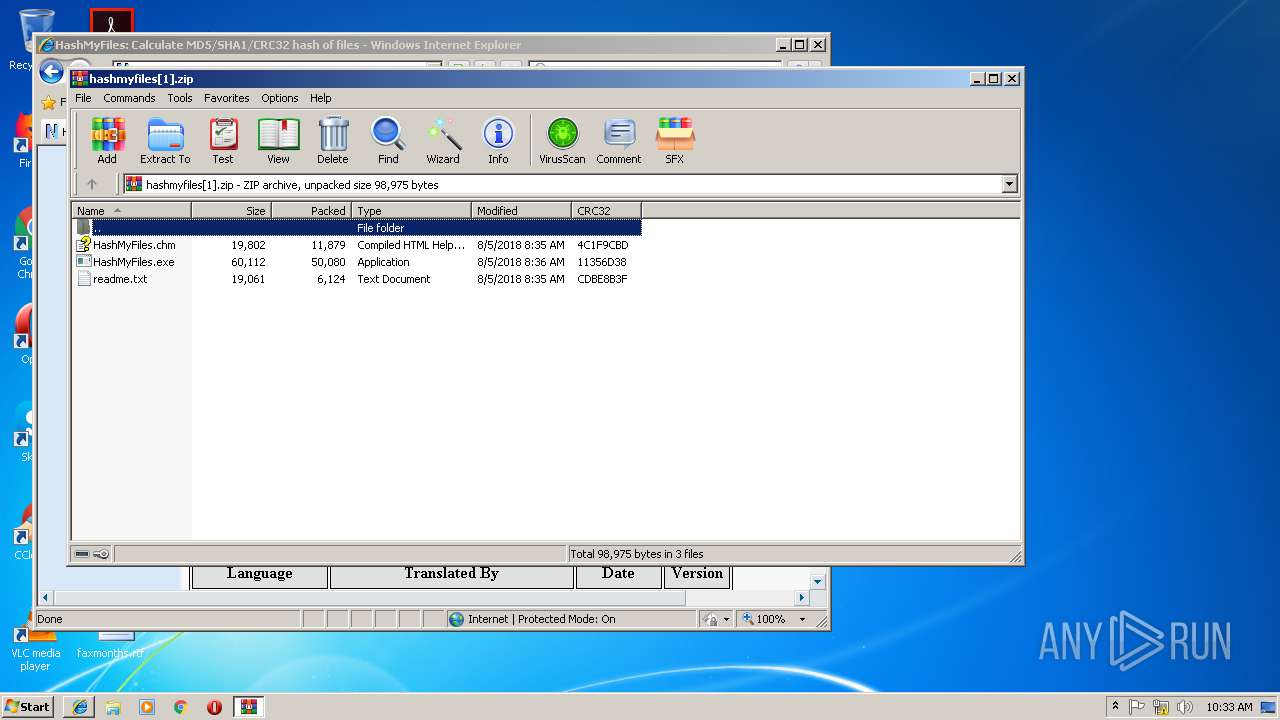
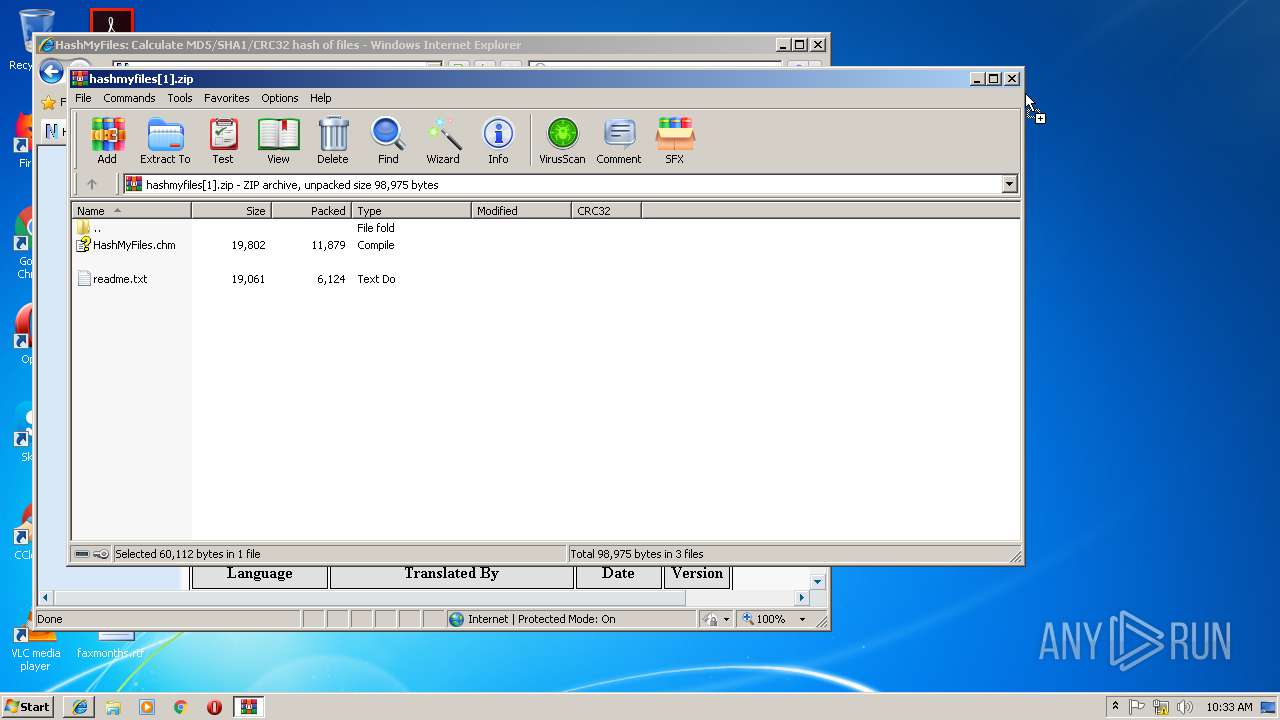
| 2068 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\hashmyfiles[1].zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18296270147029666929,17249125362124926726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=FB5BA4CB15F4F03D59763A0AF7D131EF --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FB5BA4CB15F4F03D59763A0AF7D131EF --renderer-client-id=11 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2212 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2296 | "cmd.exe" /s /k pushd "C:\Users\admin\Desktop" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18296270147029666929,17249125362124926726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1A74A92D6B06DC98021F6B50CC08138F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1A74A92D6B06DC98021F6B50CC08138F --renderer-client-id=13 --mojo-platform-channel-handle=4192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,18296270147029666929,17249125362124926726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=C0417972DC355A8F00A9311E875DDD70 --mojo-platform-channel-handle=3456 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
5 502
Read events
4 655
Write events
814
Delete events
33
Modification events
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\QM_318575672_2.zip | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
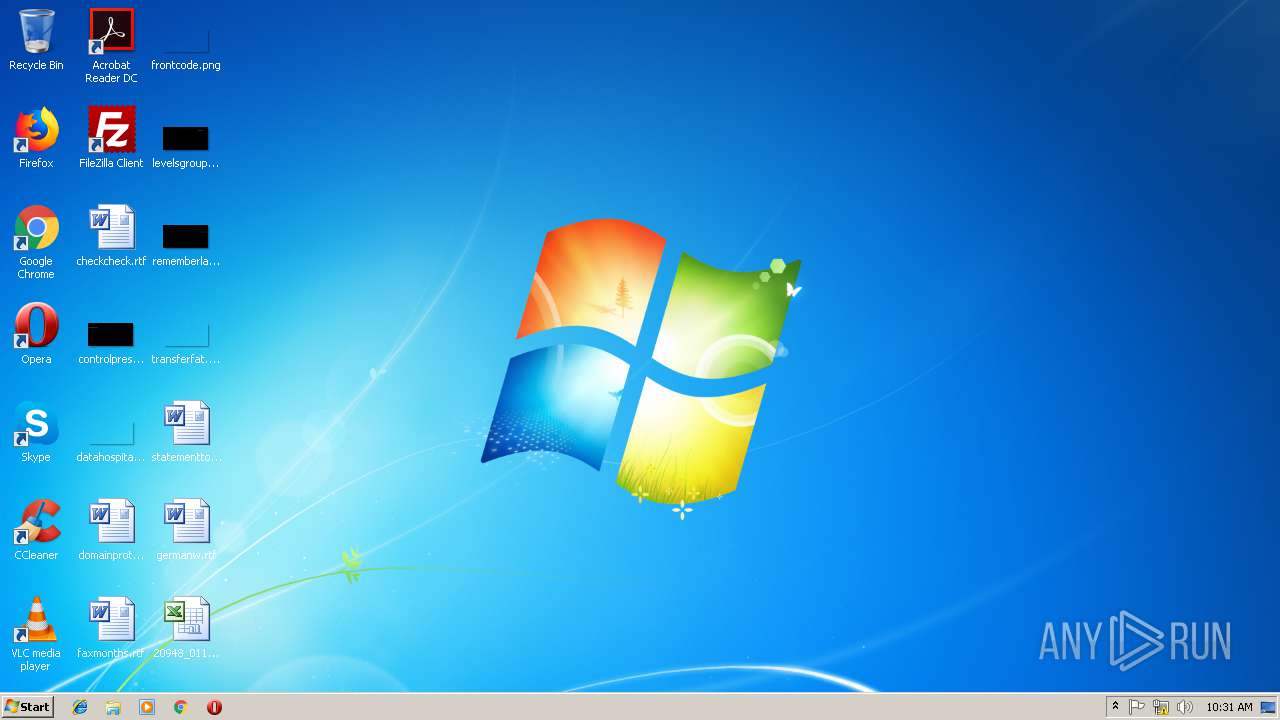
Executable files
1
Suspicious files
134
Text files
219
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR82DC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2472 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE4E2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2912 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF08BBC313D543CB3D.TMP | — | |
MD5:— | SHA256:— | |||
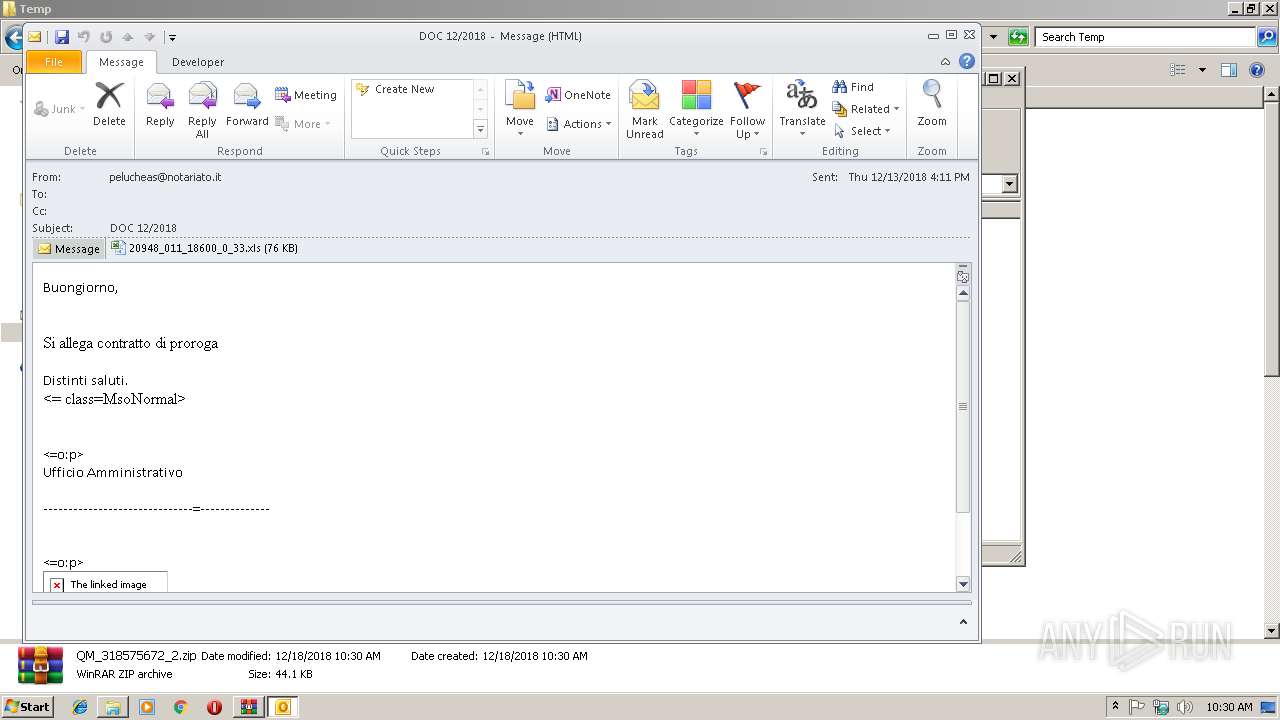
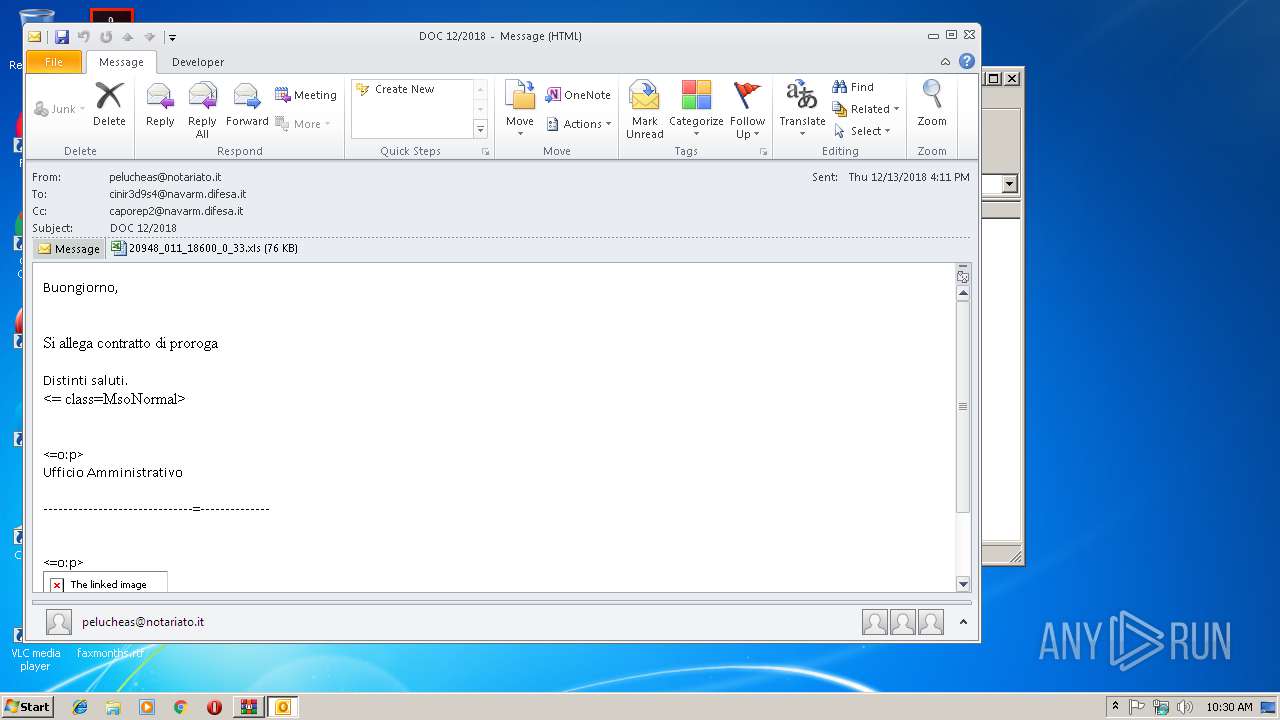
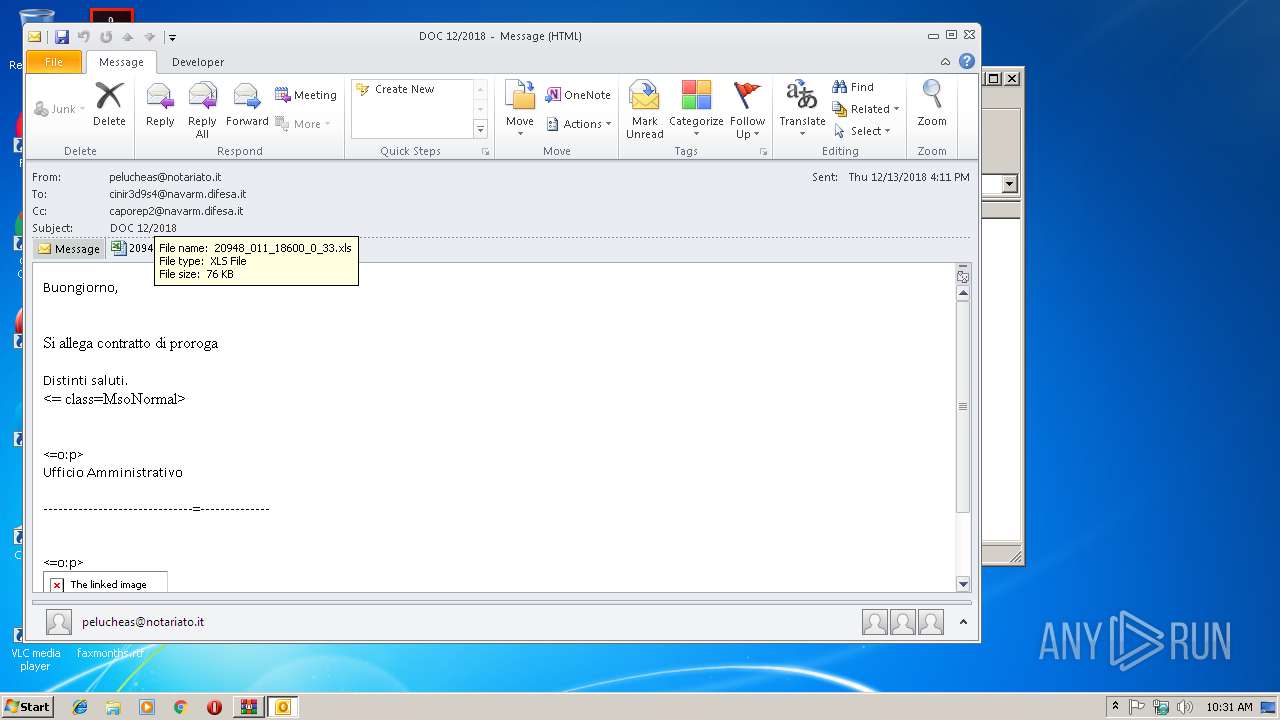
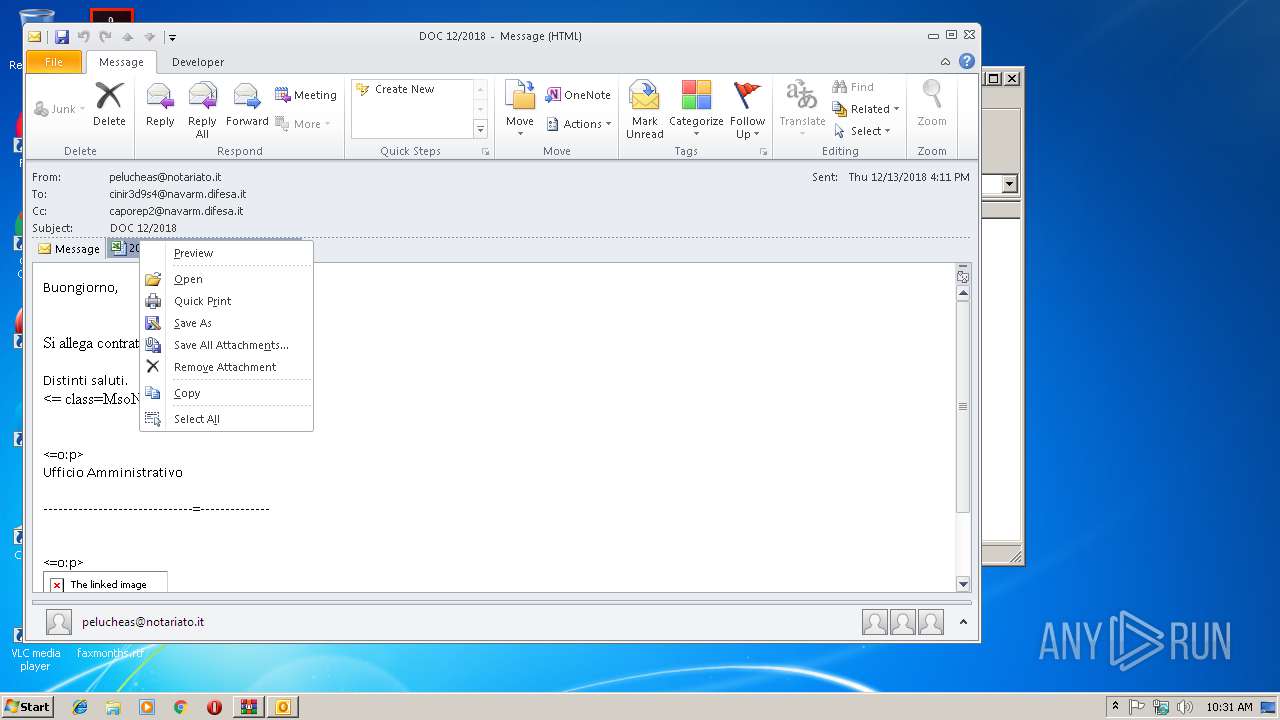
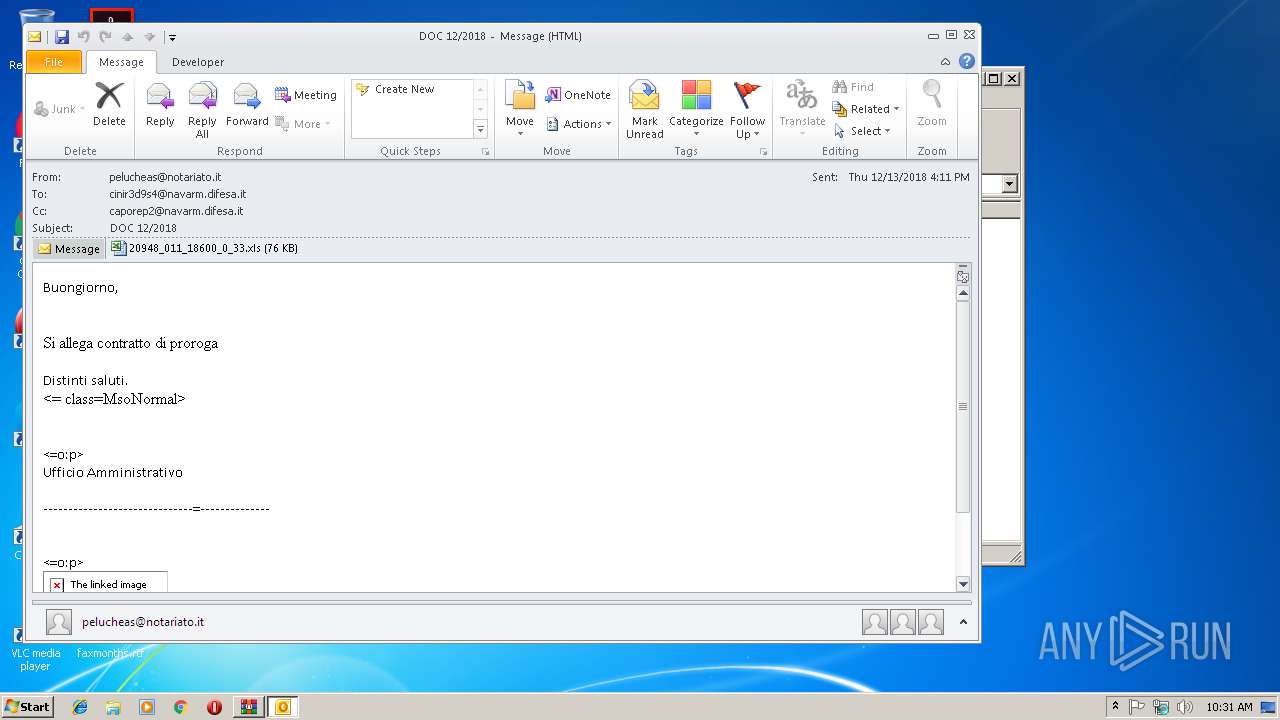
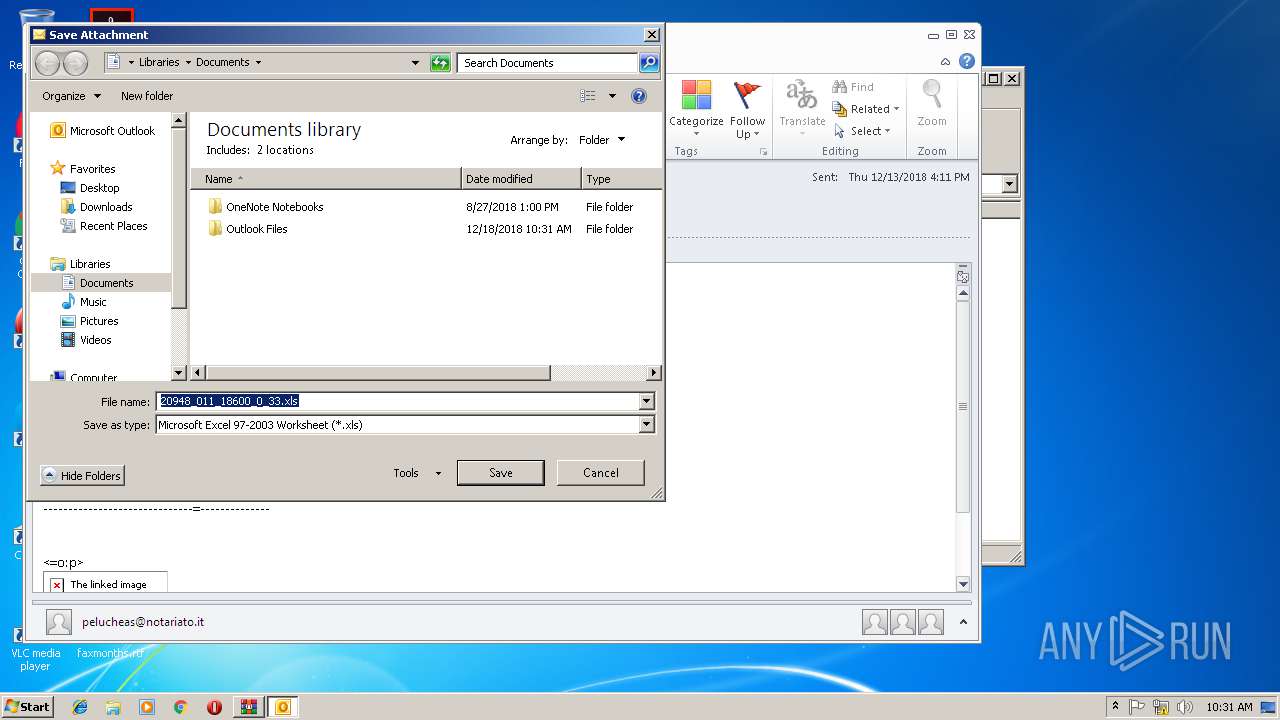
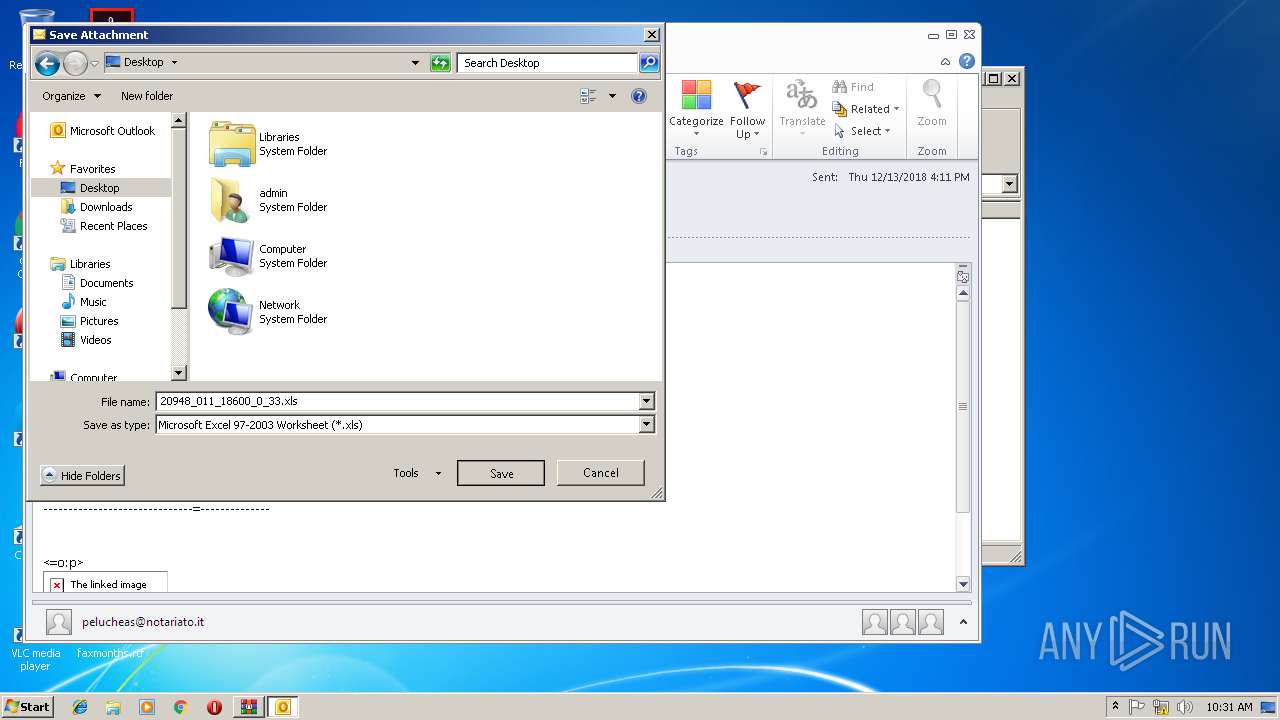
| 2912 | OUTLOOK.EXE | C:\Users\admin\Desktop\20948_011_18600_0_33.xls\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2912 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E2CABE06-A3BF-4EED-B683-9B8C478D440F}.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF65E7FA28A8E842D2.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFD2067350EABD2F3F.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{8611884E-D68F-442B-8CEE-F74CD9C7AC0D}.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OTGHLZE89UQFT33HF4CG.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
150
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=hash+file&src=IE-SearchBox&FORM=IE8SRC | US | html | 46.0 Kb | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=BEFFF0A157074BA1BB6AD96C5E89D715&CID=007CB39456DC6D700A21BF5D573A6C86&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"Object%20doesn%27t%20support%20this%20property%20or%20method","Meta":"http%3A//www.bing.com/search%3Fq%3Dhash+file%26src%3DIE-SearchBox%26FORM%3DIE8SRC","Line":23060862,"Char":%20undefined}] | US | compressed | 174 b | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6o/4R/cj,nj/57324345/ae00a169.js | US | text | 1.72 Kb | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=BEFFF0A157074BA1BB6AD96C5E89D715&CID=007CB39456DC6D700A21BF5D573A6C86&Type=Event.CPT&DATA={"pp":{"S":"L","FC":125,"BC":281,"SE":-1,"TC":-1,"H":343,"BP":453,"CT":468,"IL":7},"ad":[-1,-1,772,444,1089,498,0]}&P=SERP&DA=DUB02 | US | compressed | 46.0 Kb | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
3300 | iexplore.exe | POST | 204 | 204.79.197.200:80 | http://www.bing.com/fd/ls/lsp.aspx | US | compressed | 2.75 Kb | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5m/cj,nj/3e6a7d75/9a358300.js?bu=EpUesx7eHeEd7gTvHfEdvx7zHfodgh6rHqkenh6THbUcuByWHQ | US | text | 4.95 Kb | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/3Z/7a/cj,nj/ac1ded2c/e26c0b65.js | US | text | 303 b | whitelisted |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Y/1I/cj,nj/5983aa50/f8c6dd44.js | US | text | 773 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3004 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3300 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3300 | iexplore.exe | 157.55.135.134:443 | login.live.com | Microsoft Corporation | US | whitelisted |
3300 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3300 | iexplore.exe | 52.231.143.224:80 | c7672b08377855227b2e115574e11810.clo.footprintdns.com | Microsoft Corporation | KR | whitelisted |
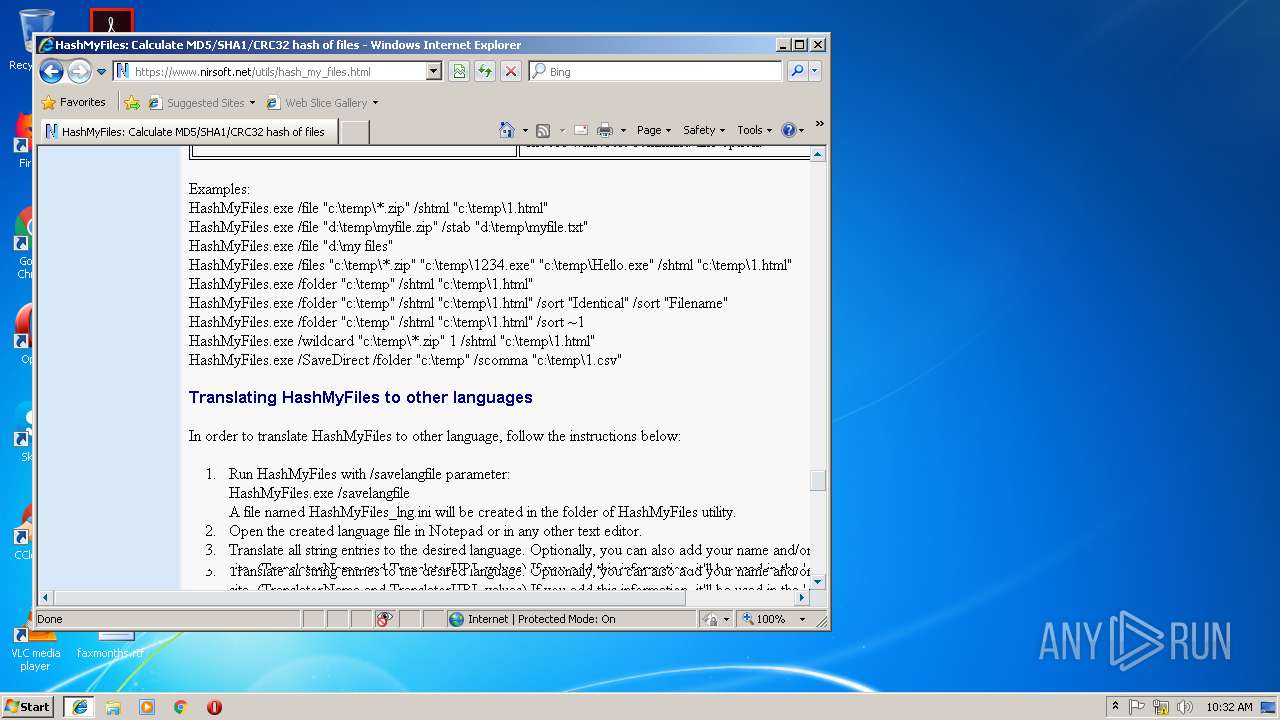
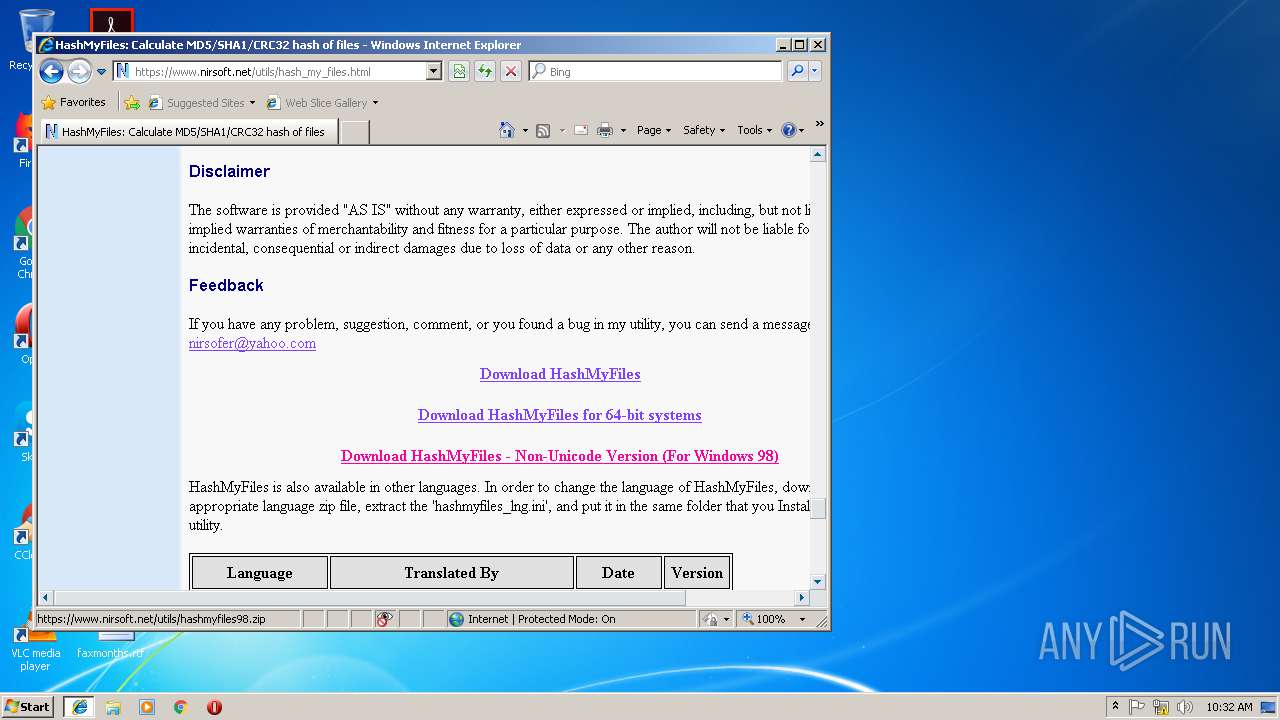
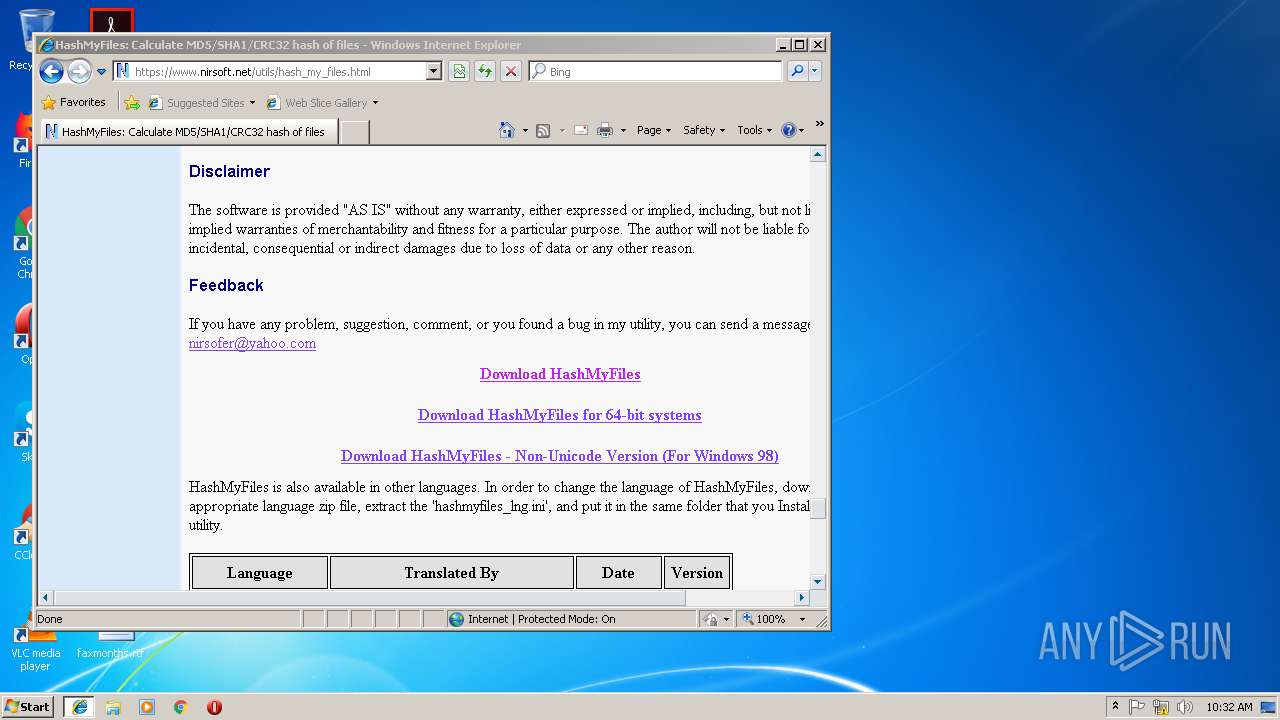
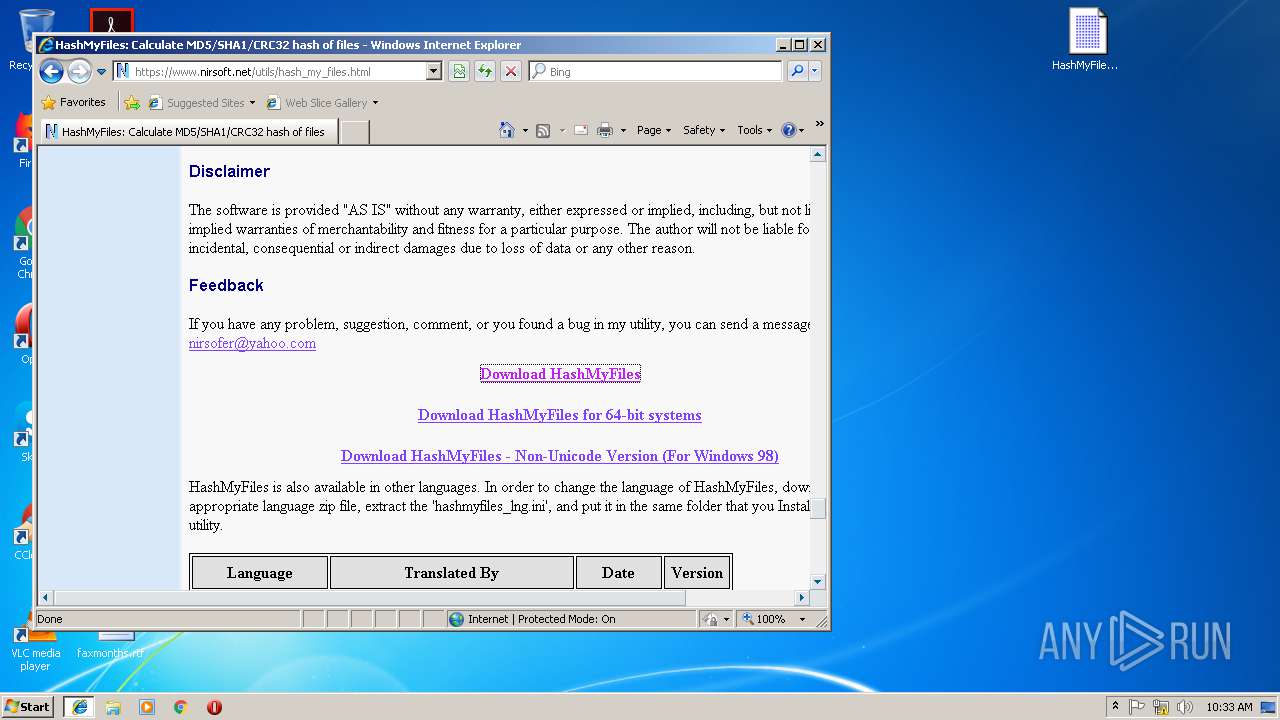
3300 | iexplore.exe | 138.128.181.26:443 | www.nirsoft.net | HostDime.com, Inc. | US | suspicious |
3300 | iexplore.exe | 52.231.32.10:80 | 352c24ae462d7c508b0cc3ebb0e5ebce.clo.footprintdns.com | Microsoft Corporation | KR | whitelisted |
3300 | iexplore.exe | 172.217.22.34:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3300 | iexplore.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
c7672b08377855227b2e115574e11810.clo.footprintdns.com |
| unknown |
www.nirsoft.net |
| whitelisted |
352c24ae462d7c508b0cc3ebb0e5ebce.clo.footprintdns.com |
| unknown |
pagead2.googlesyndication.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
adservice.google.es |
| whitelisted |
adservice.google.com |
| whitelisted |