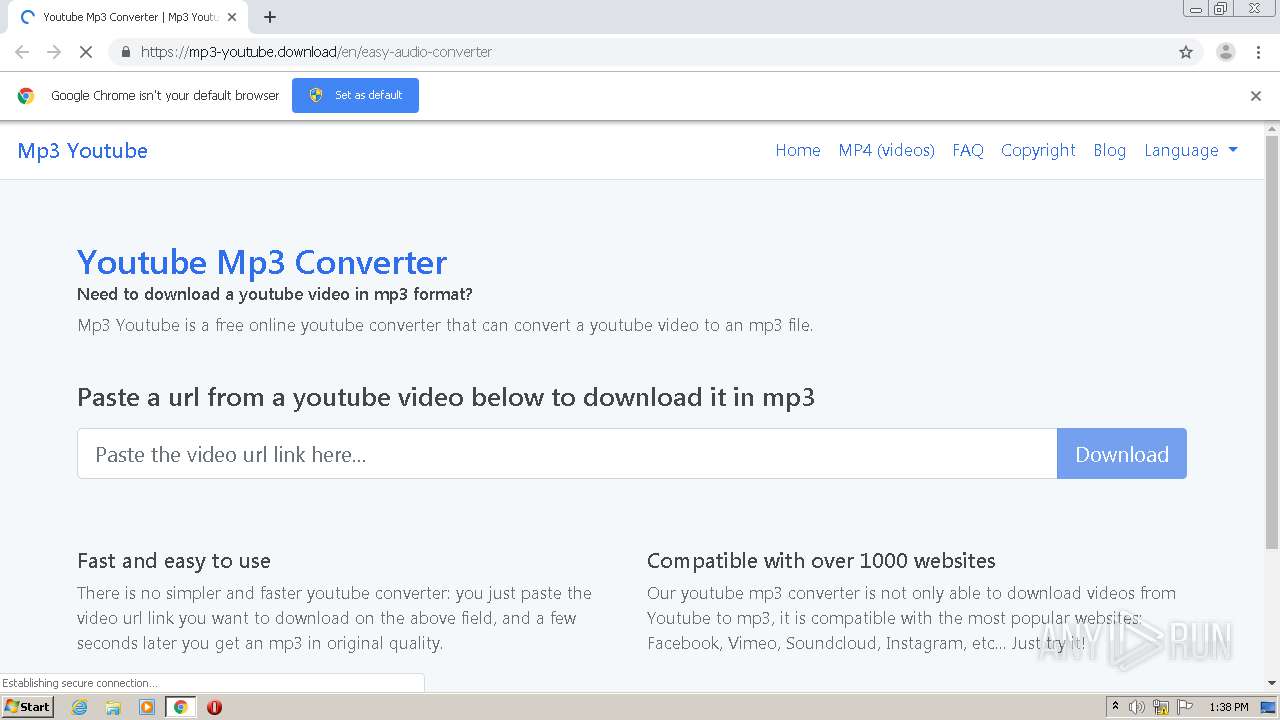
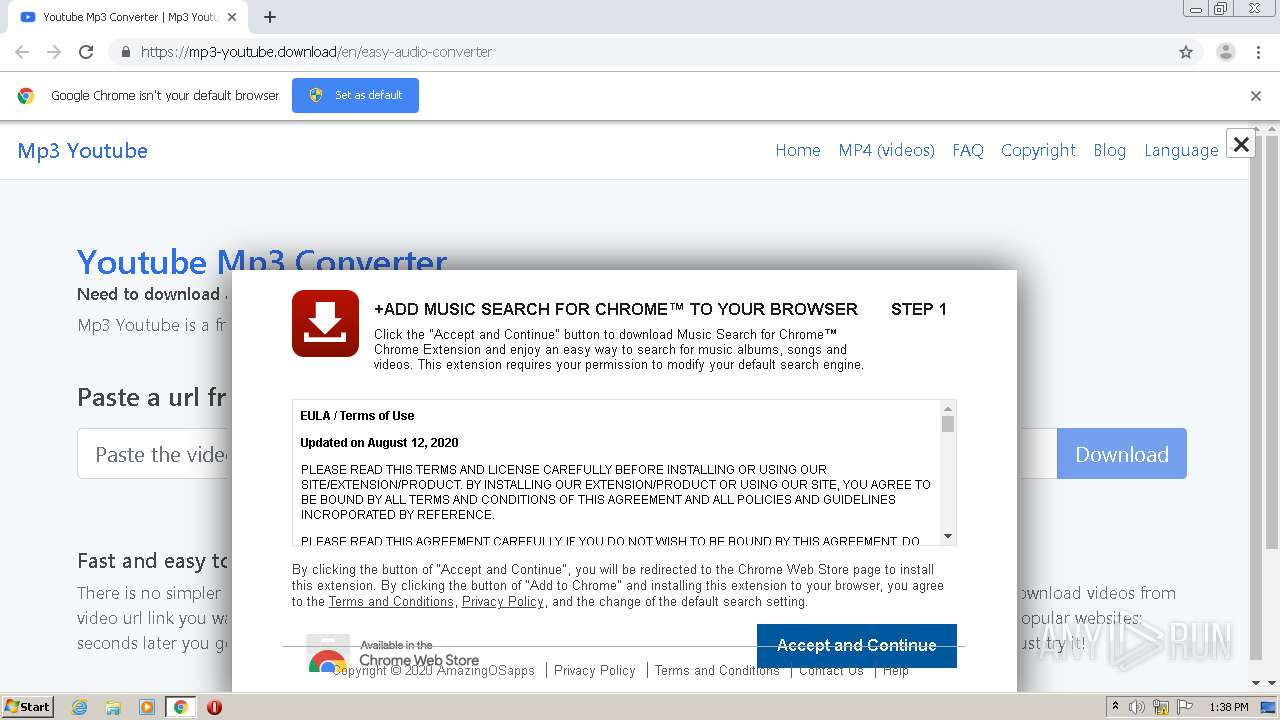
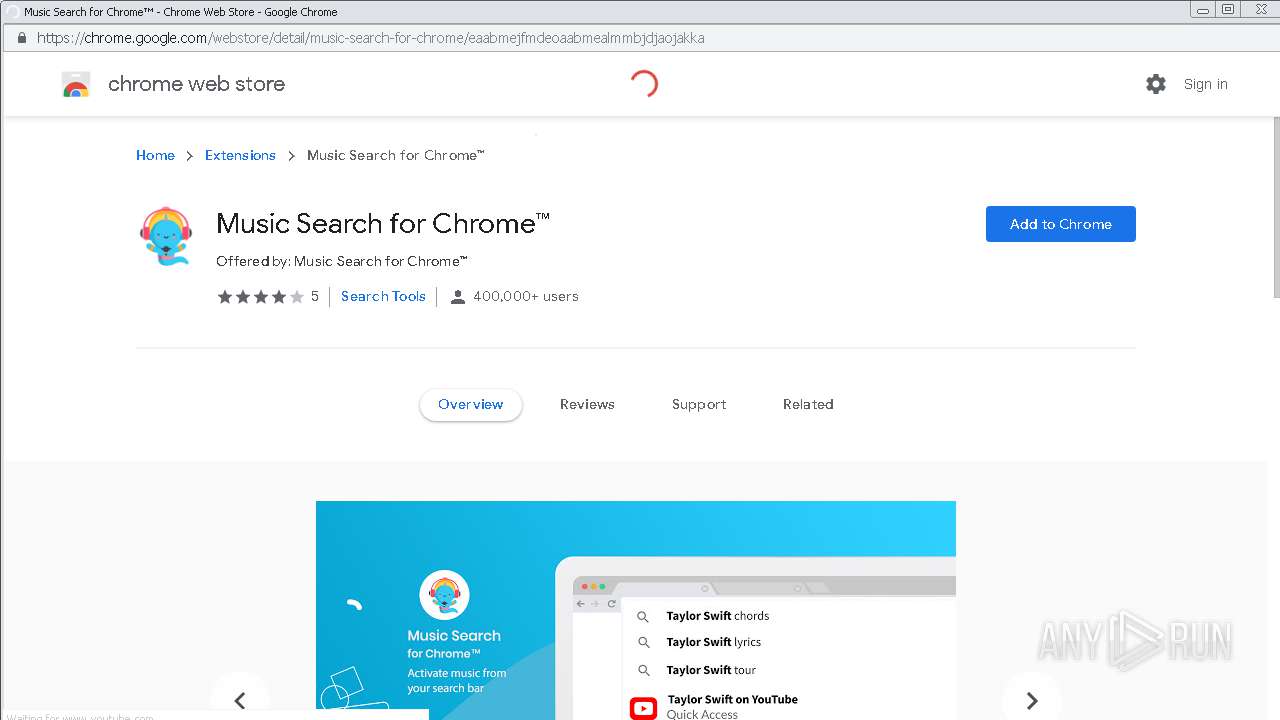
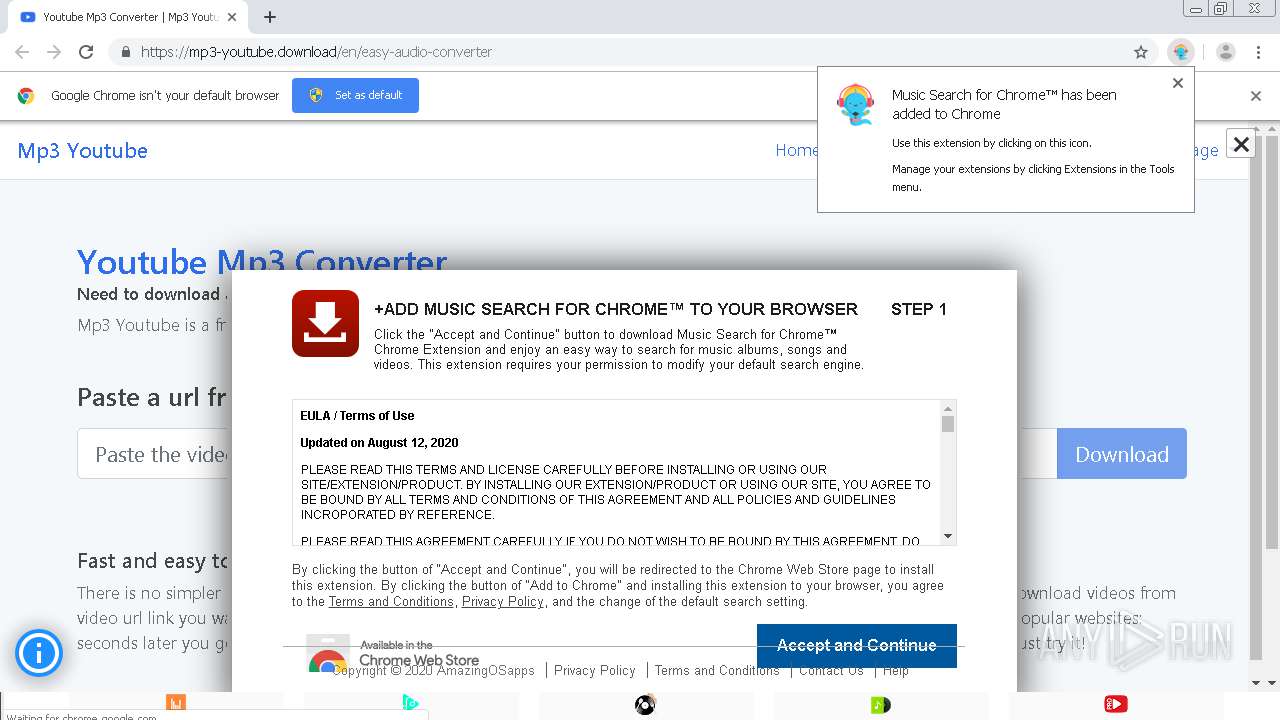
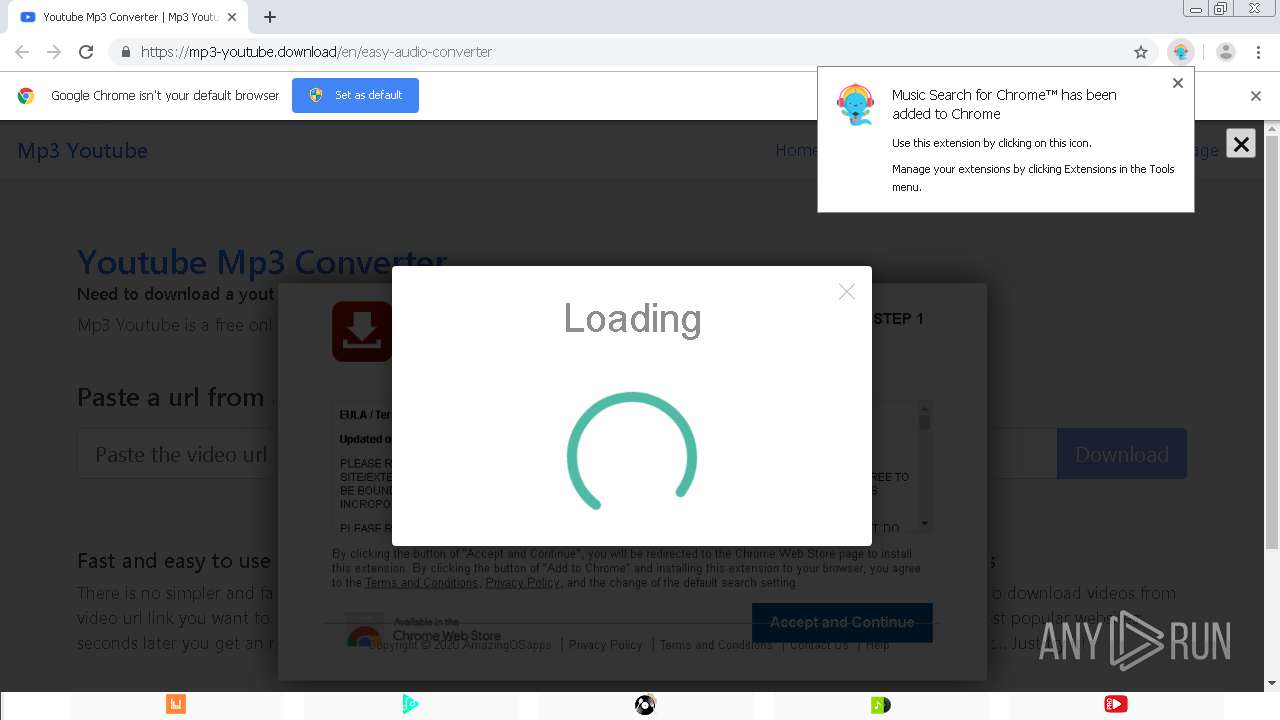
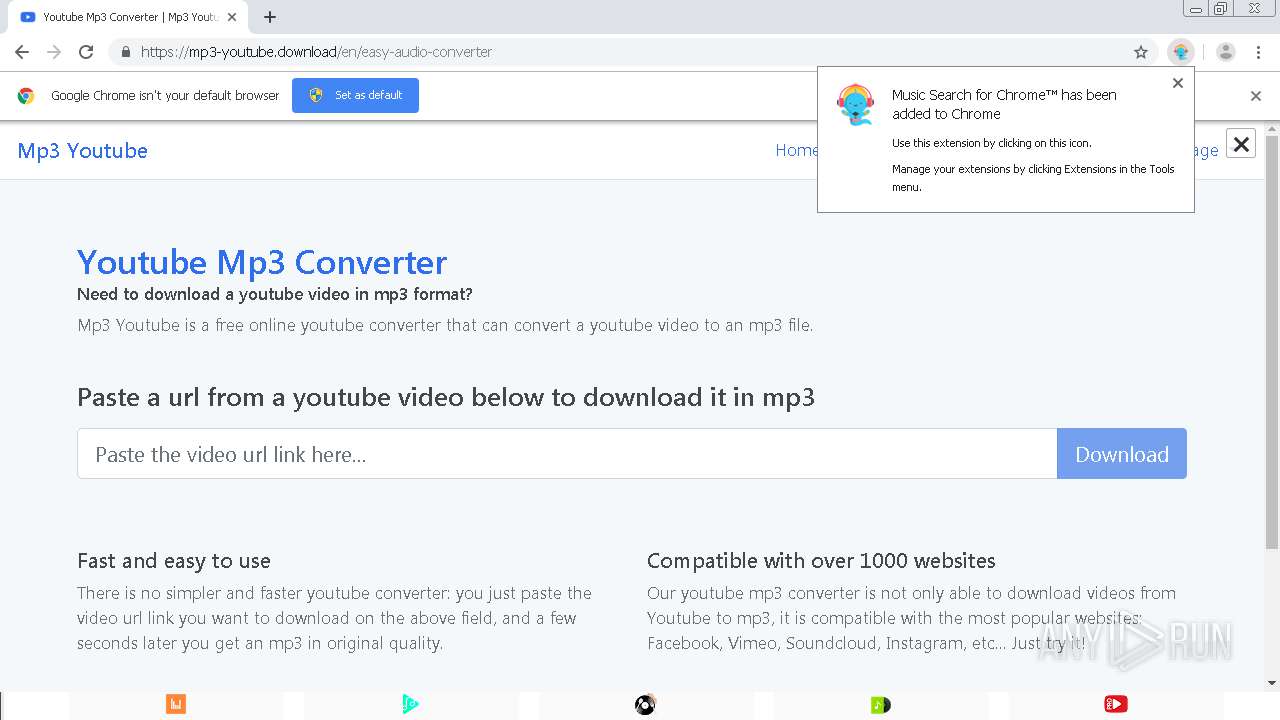
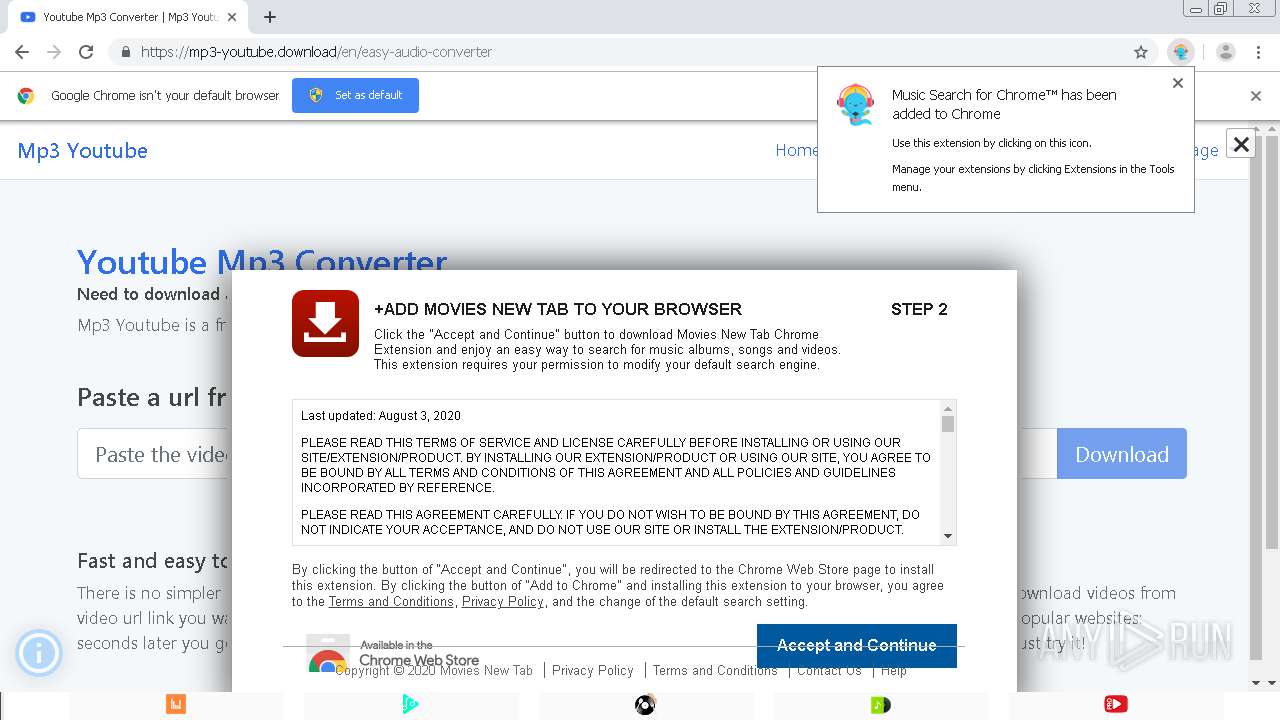
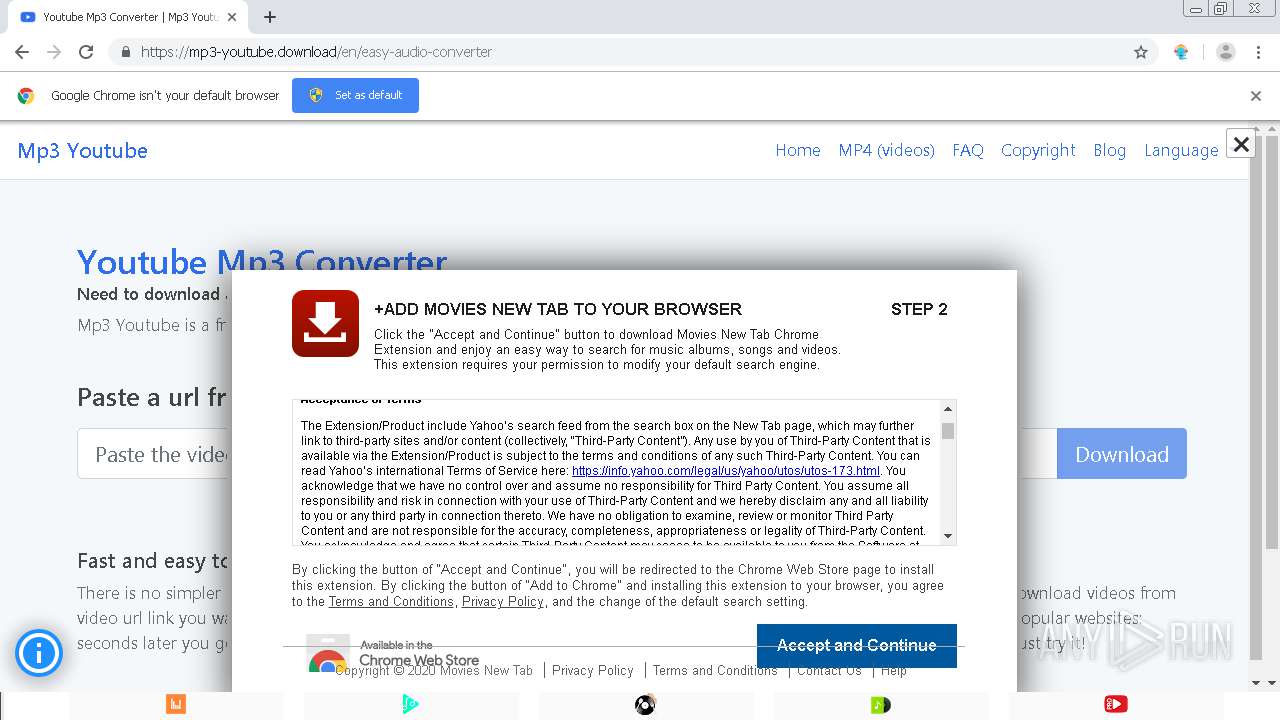
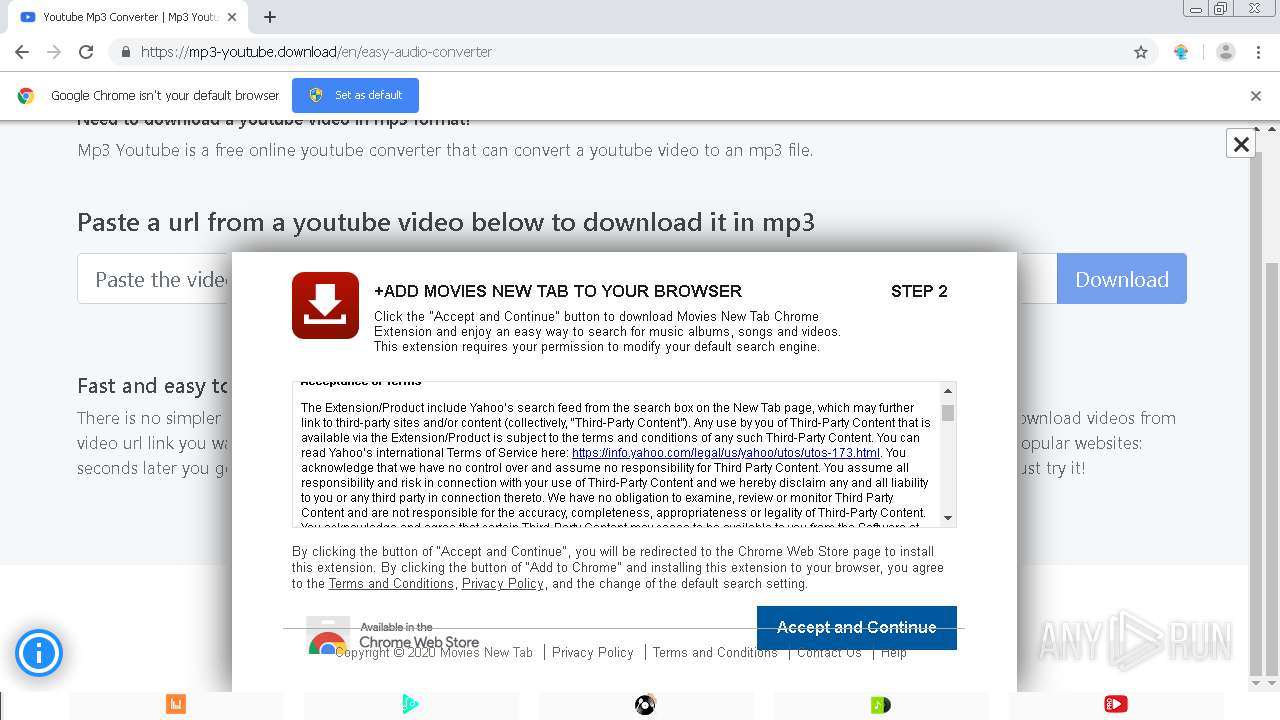
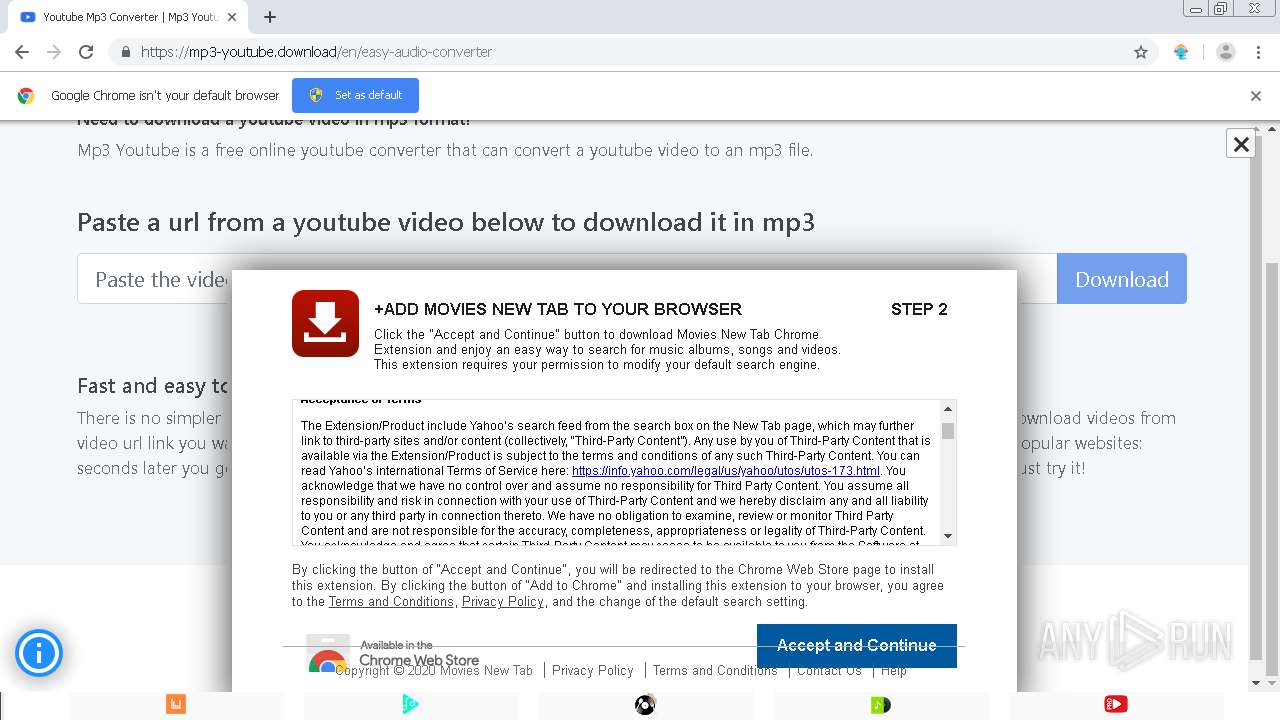
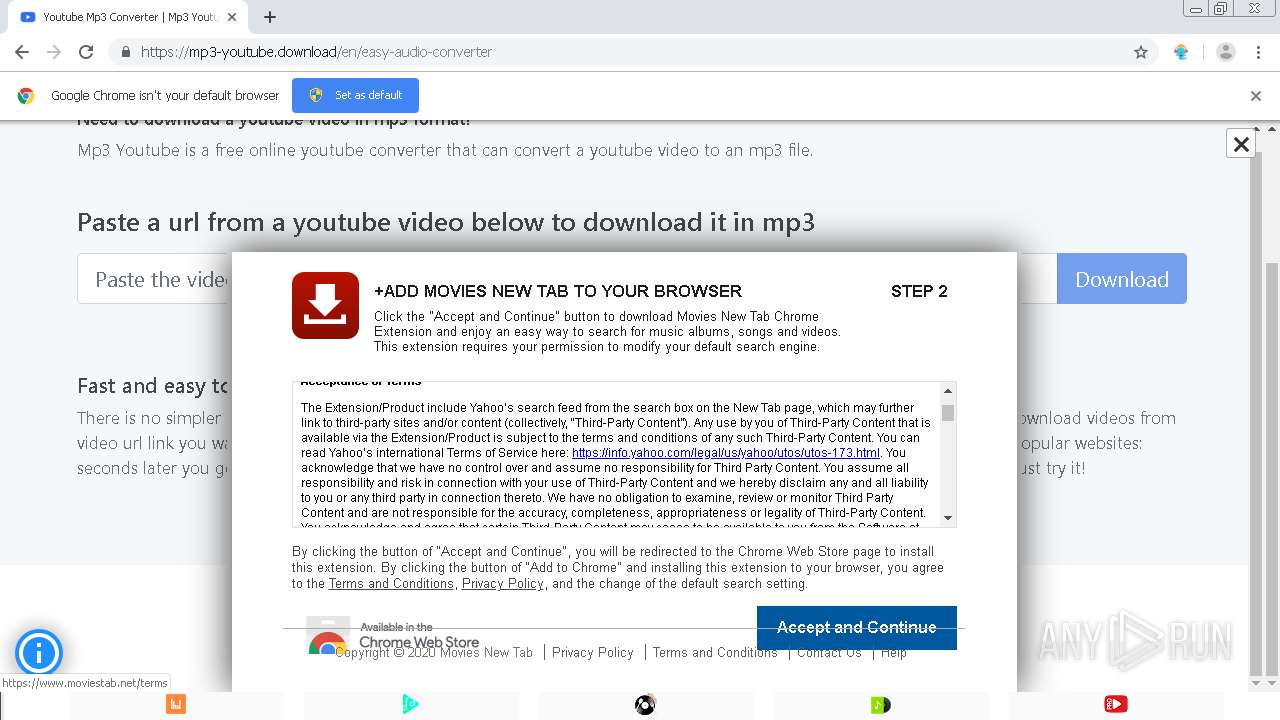
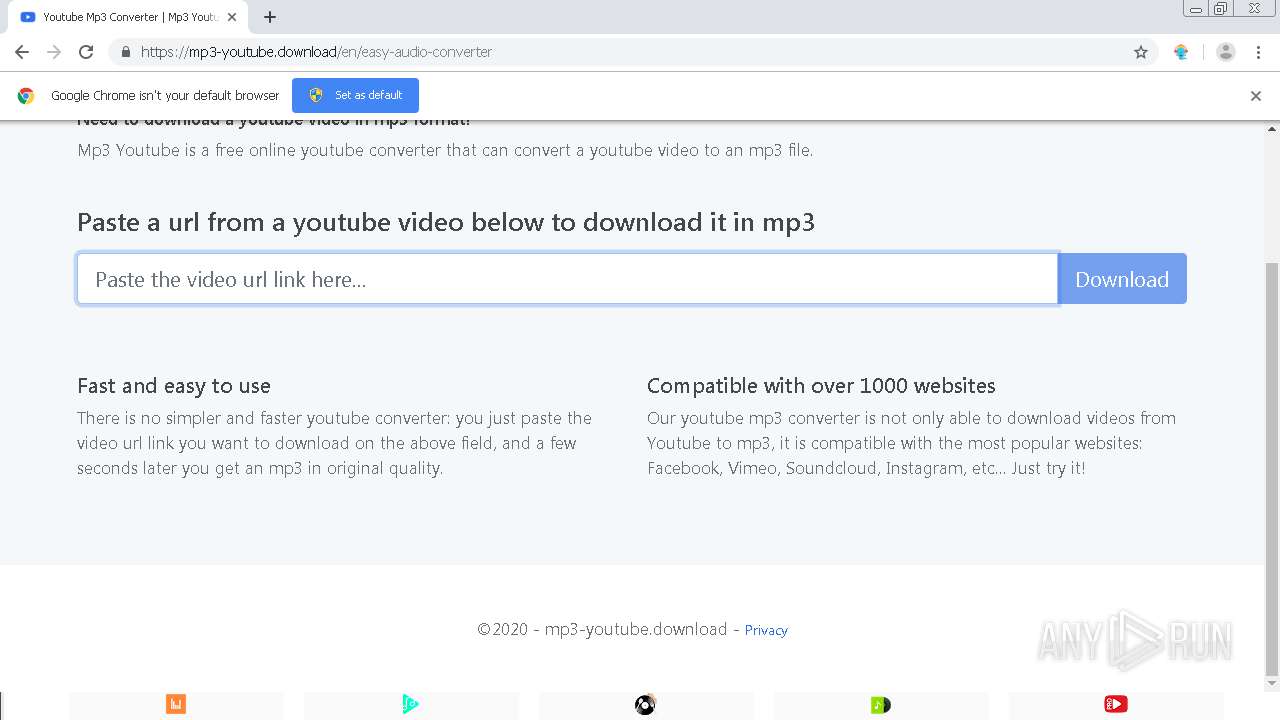
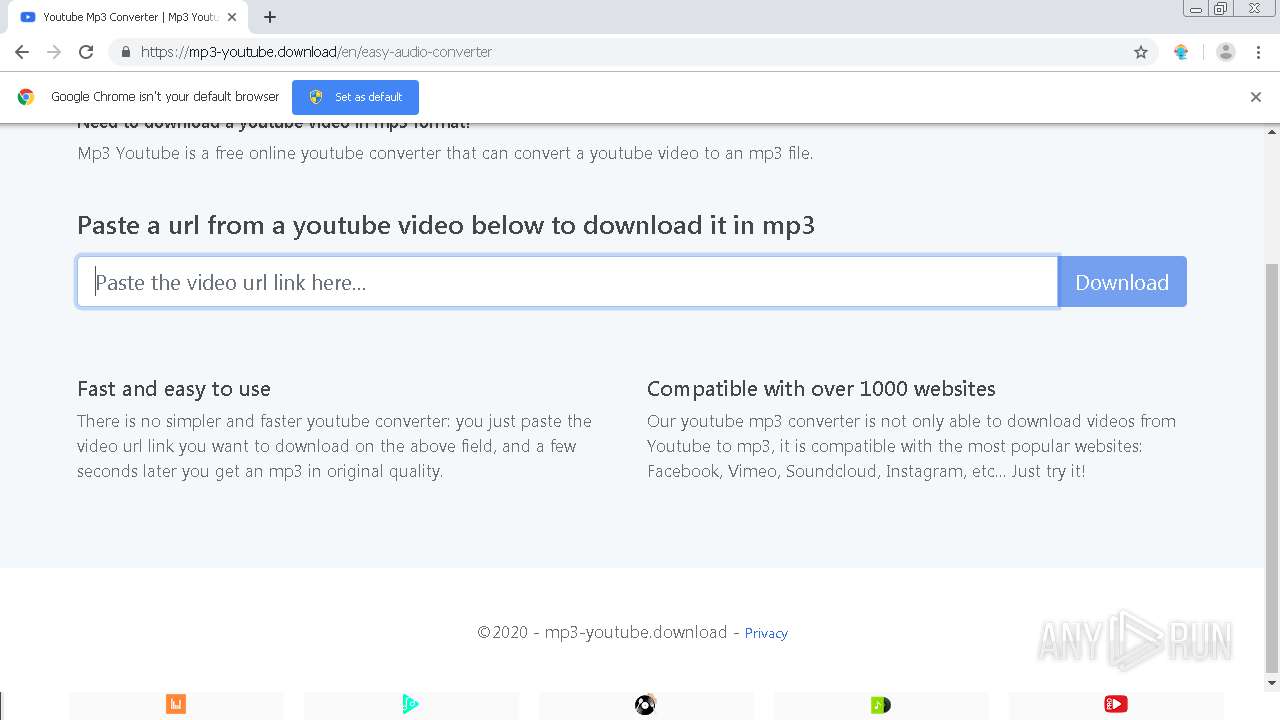
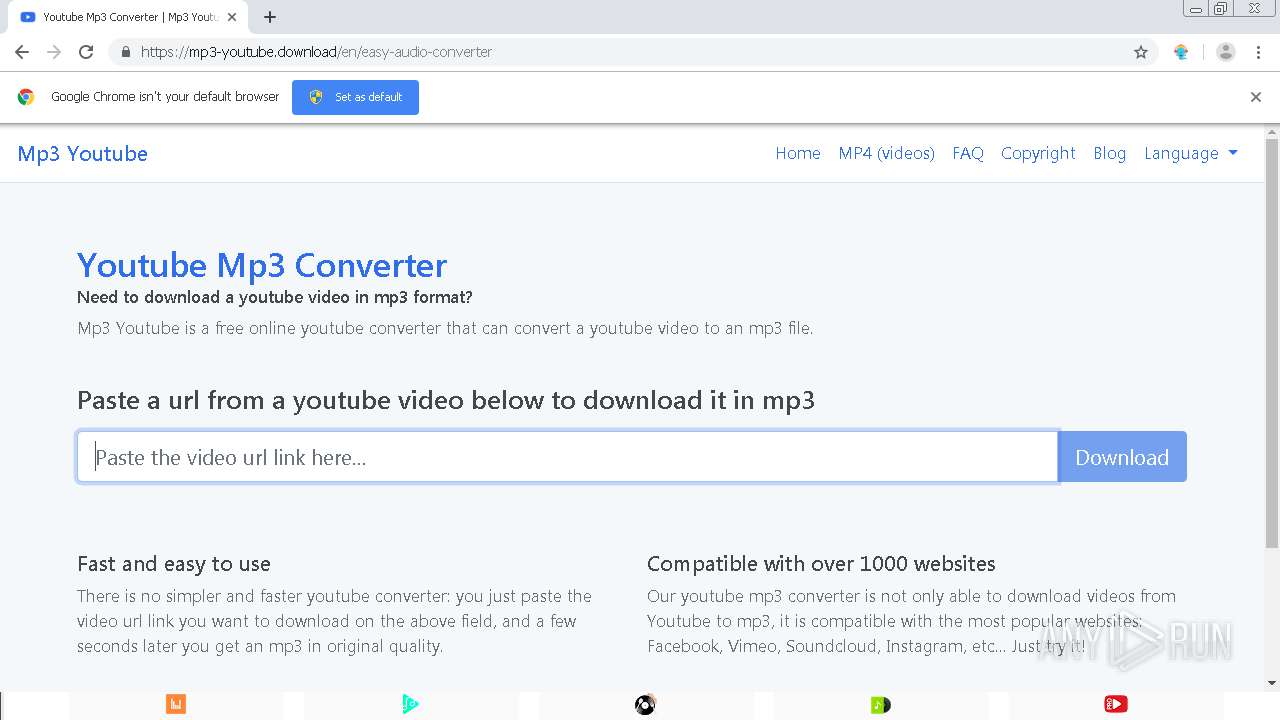
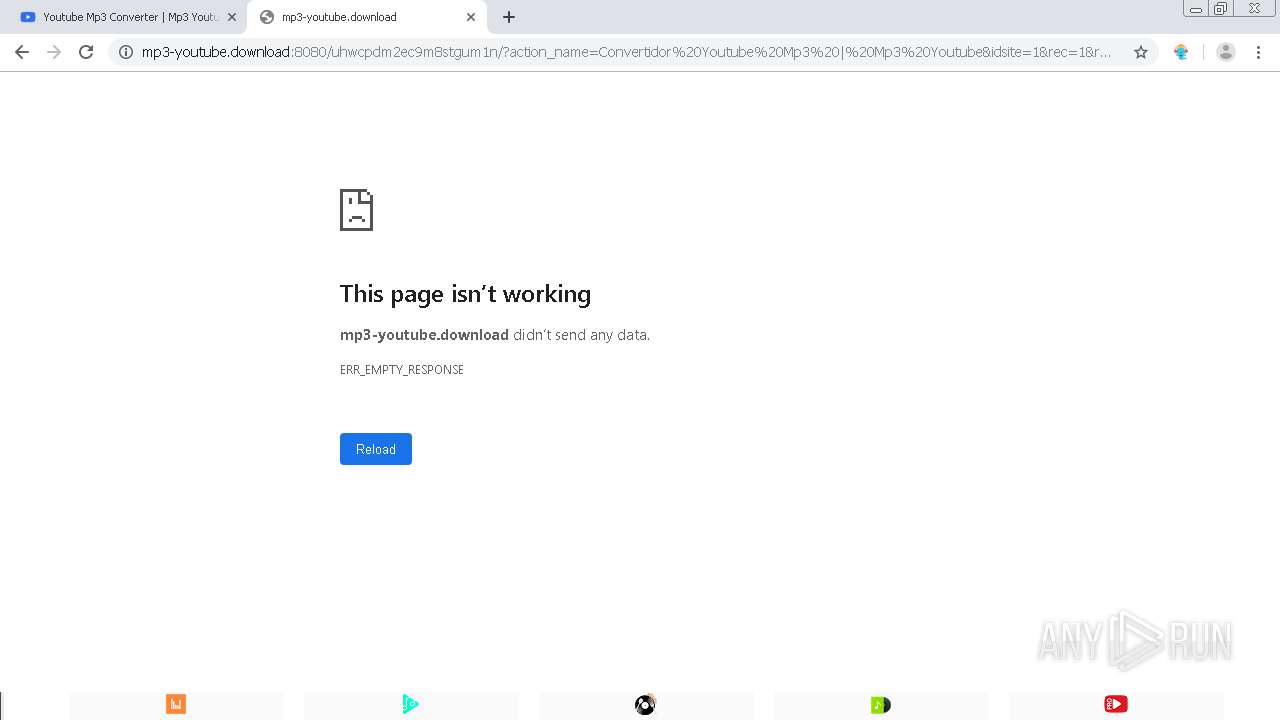
| URL: | http://mp3-youtube.download |
| Full analysis: | https://app.any.run/tasks/17e437fd-6b83-450f-b0f8-7b71f45b9cf7 |
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2020, 12:37:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B41CC541F4A6213F10A512D74E4FB221 |
| SHA1: | 6DC00541A7170179E50C131A38B9384259C72757 |
| SHA256: | DE88B680F2289474DA5DBC84CF85E1211DA6C4C8FF1AD912C3107AE9C415CC9E |
| SSDEEP: | 3:N1KTZUxBzKo:CixZp |
MALICIOUS
No malicious indicators.SUSPICIOUS
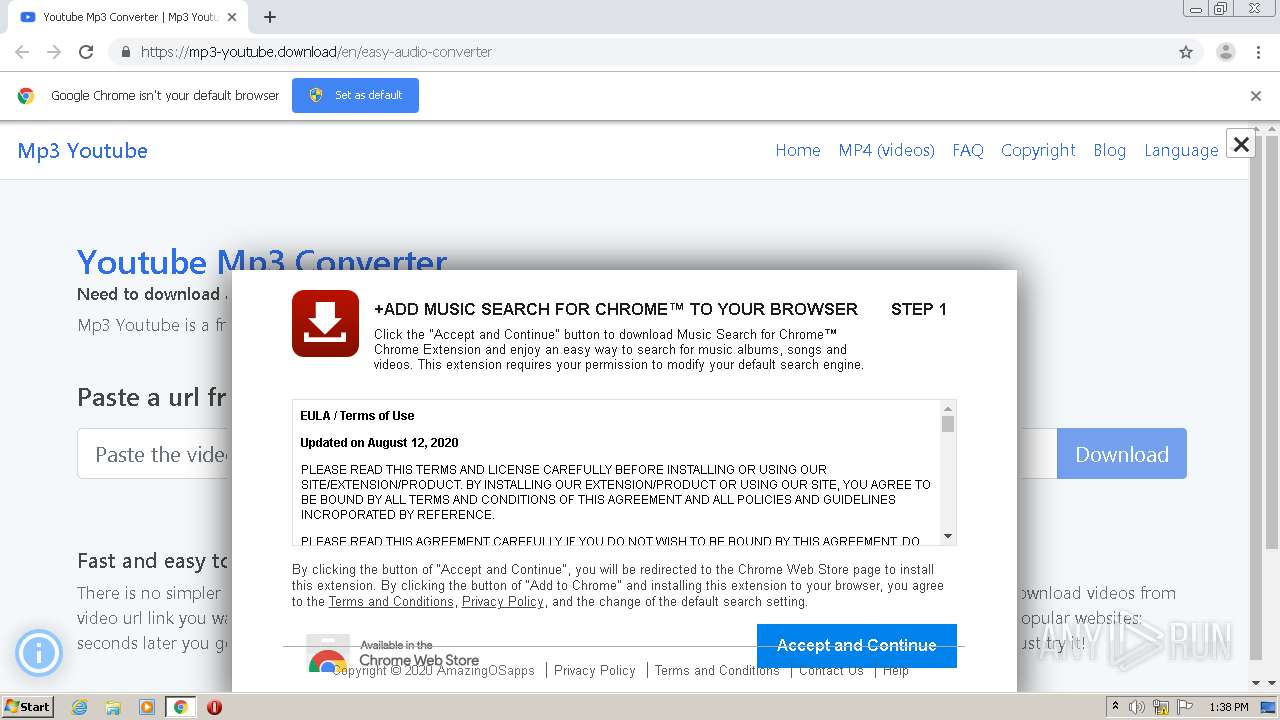
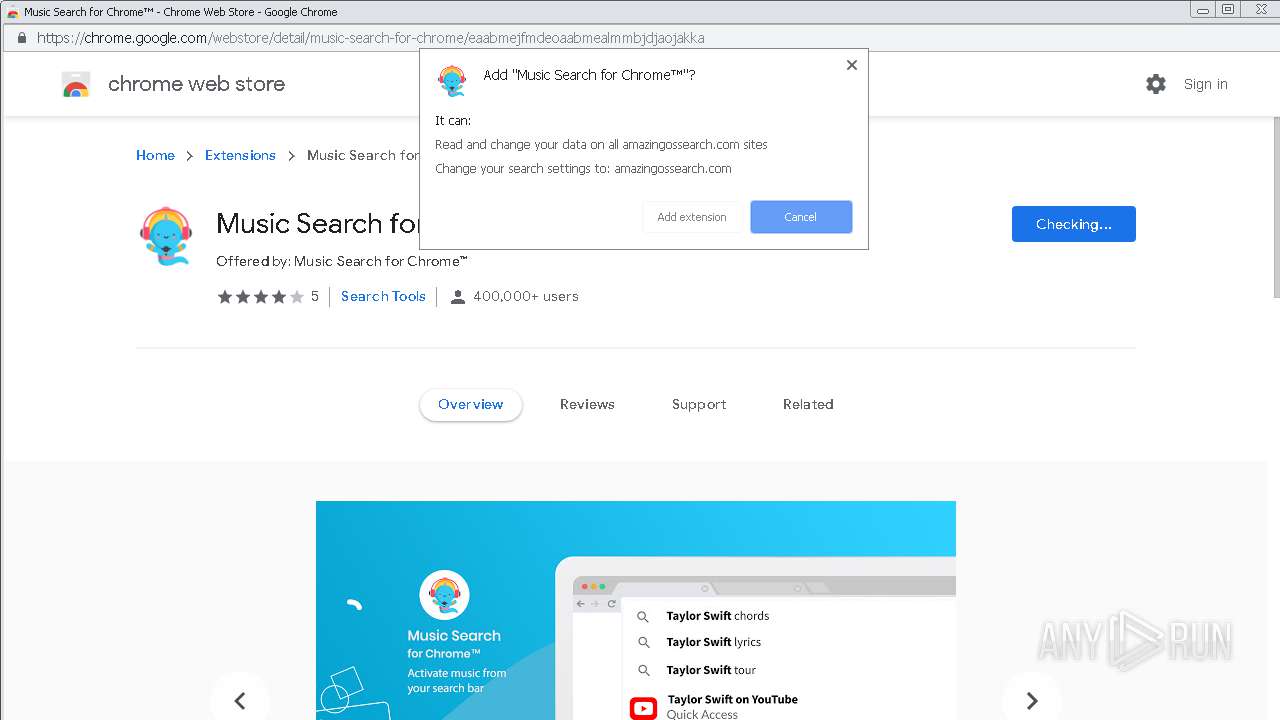
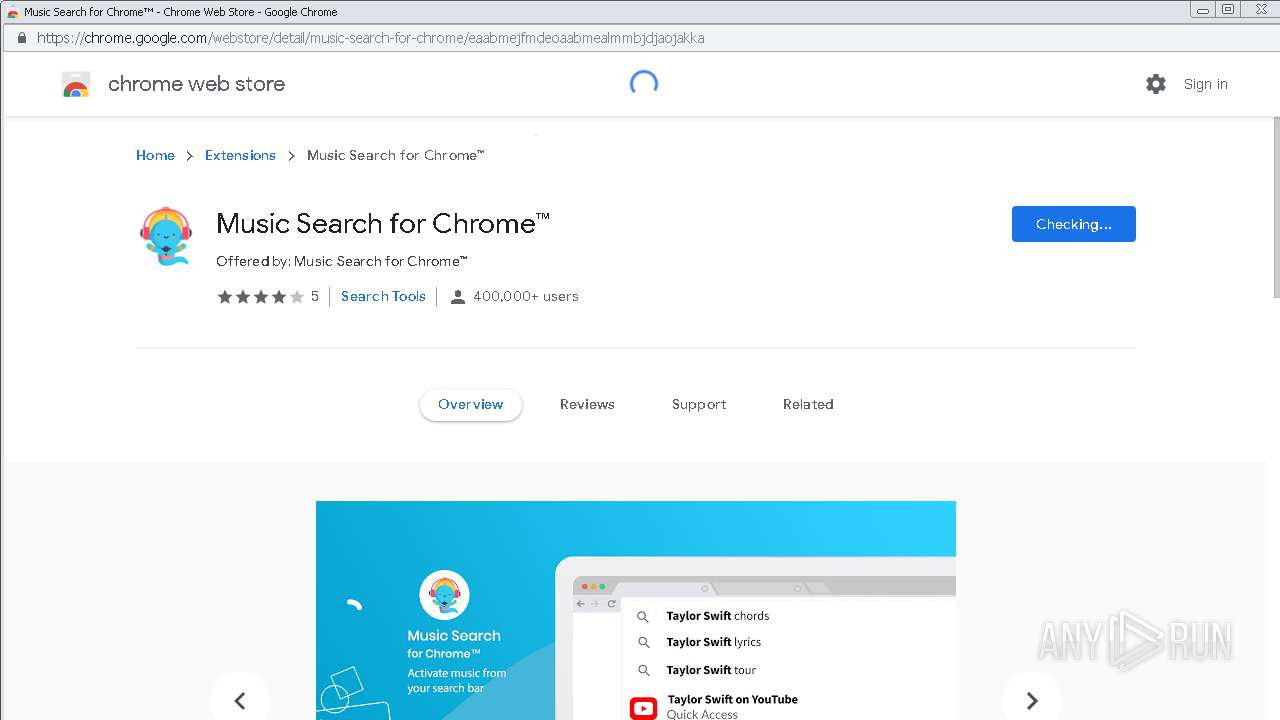
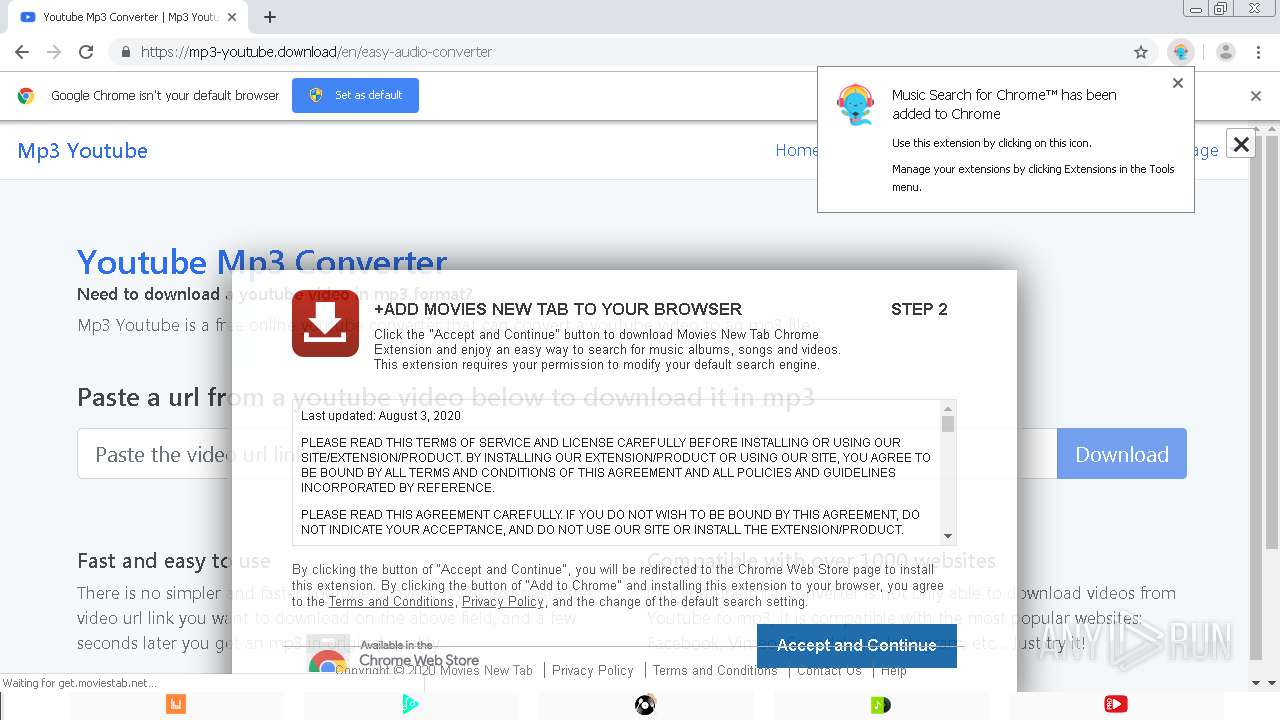
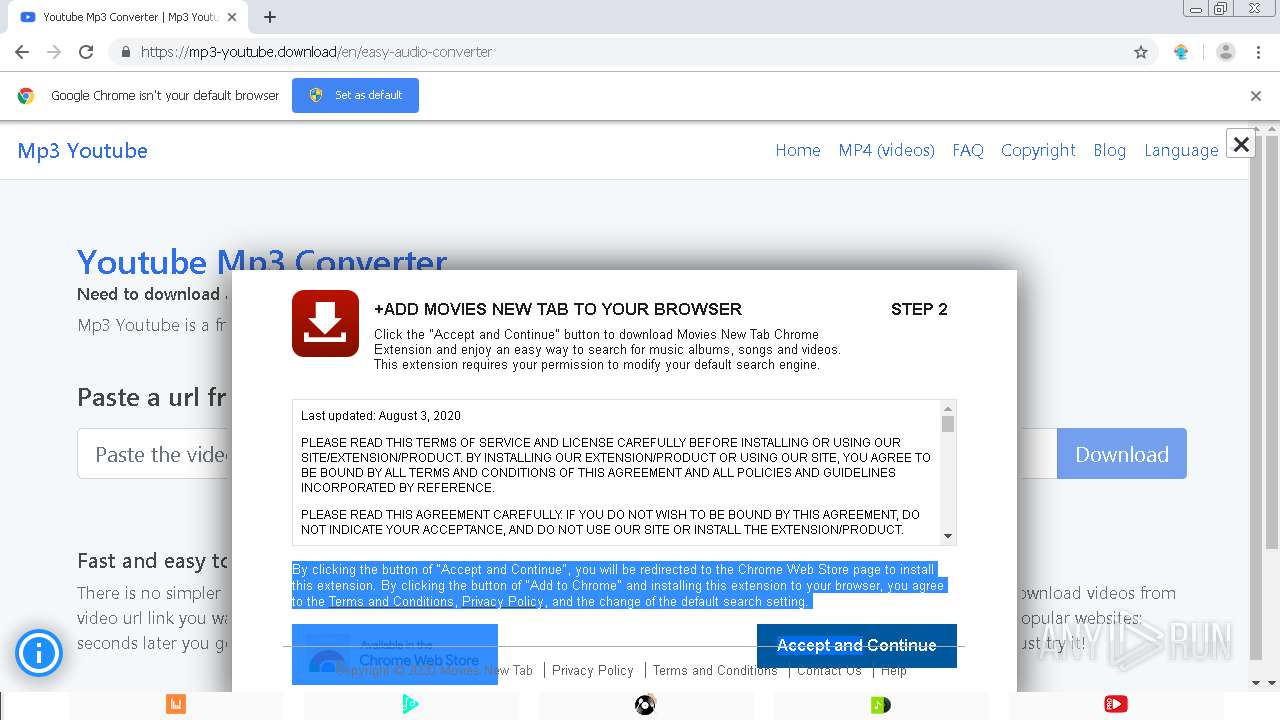
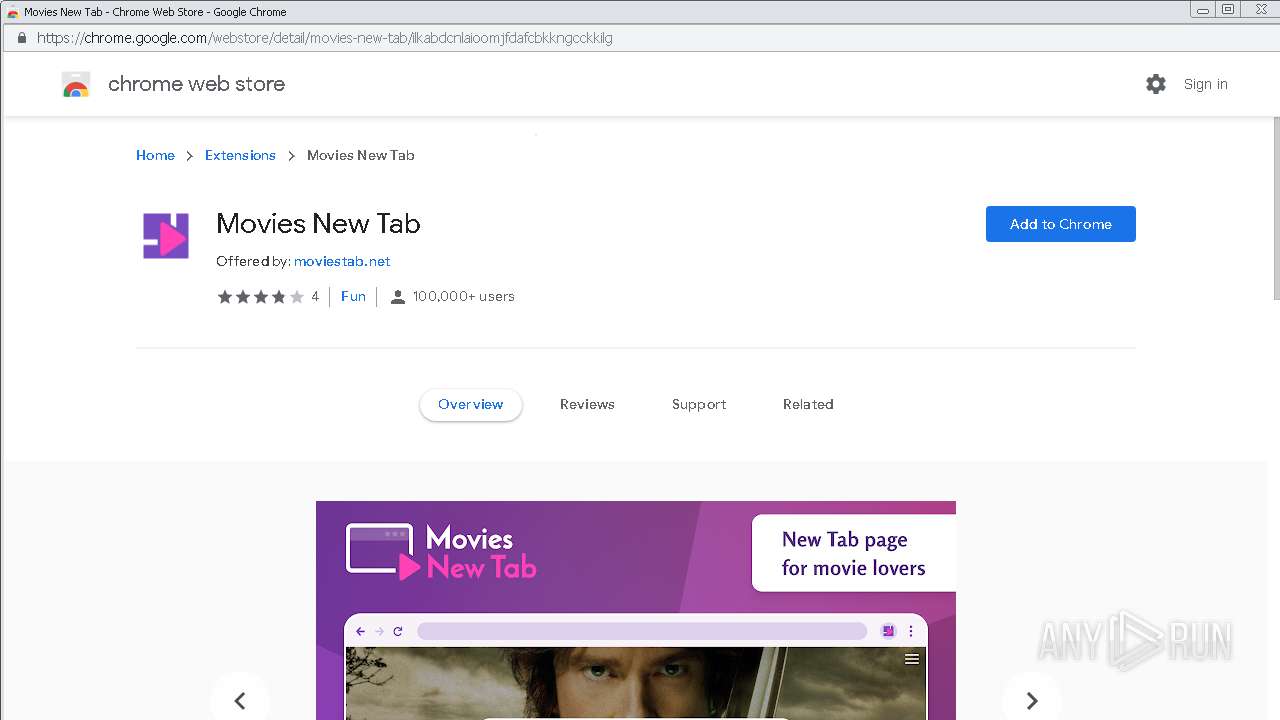
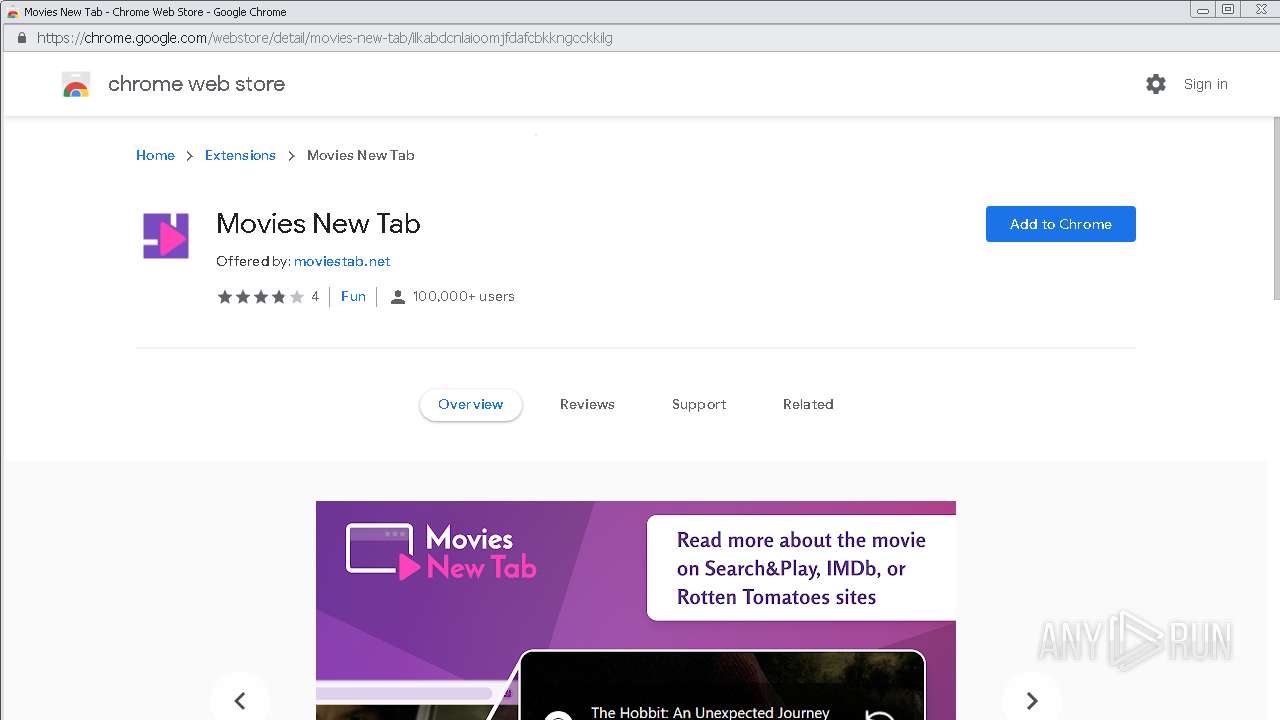
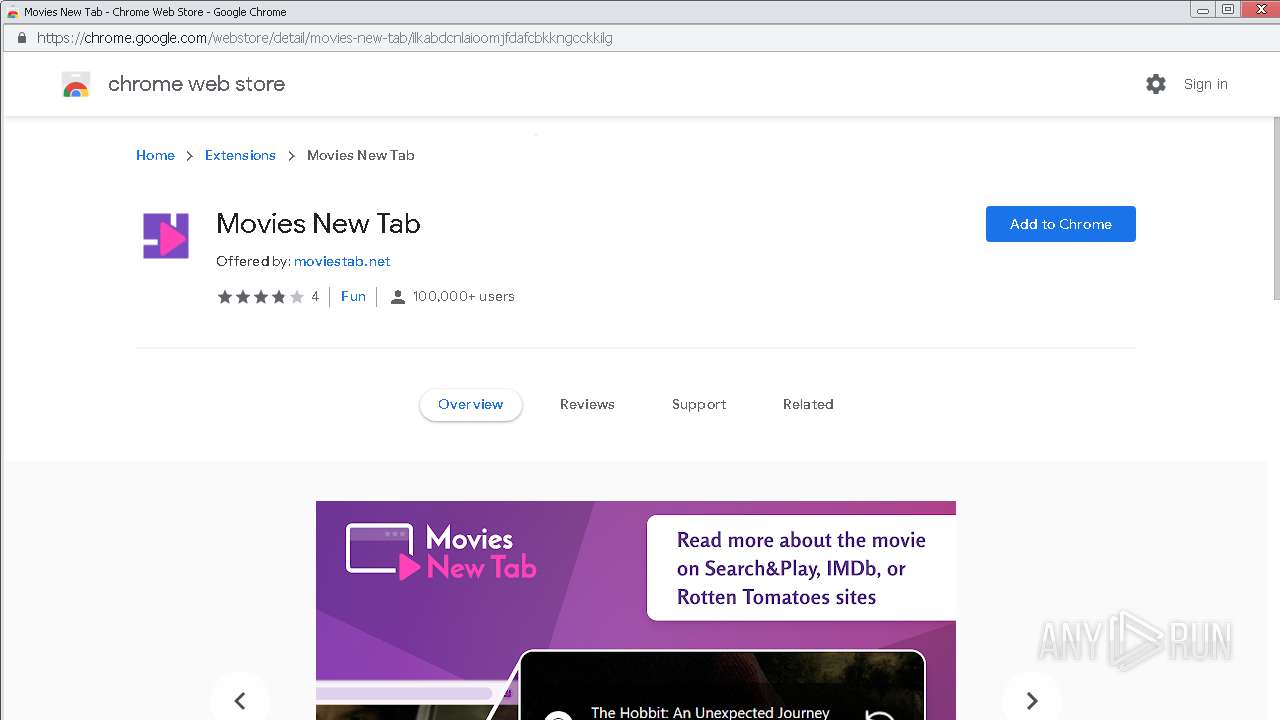
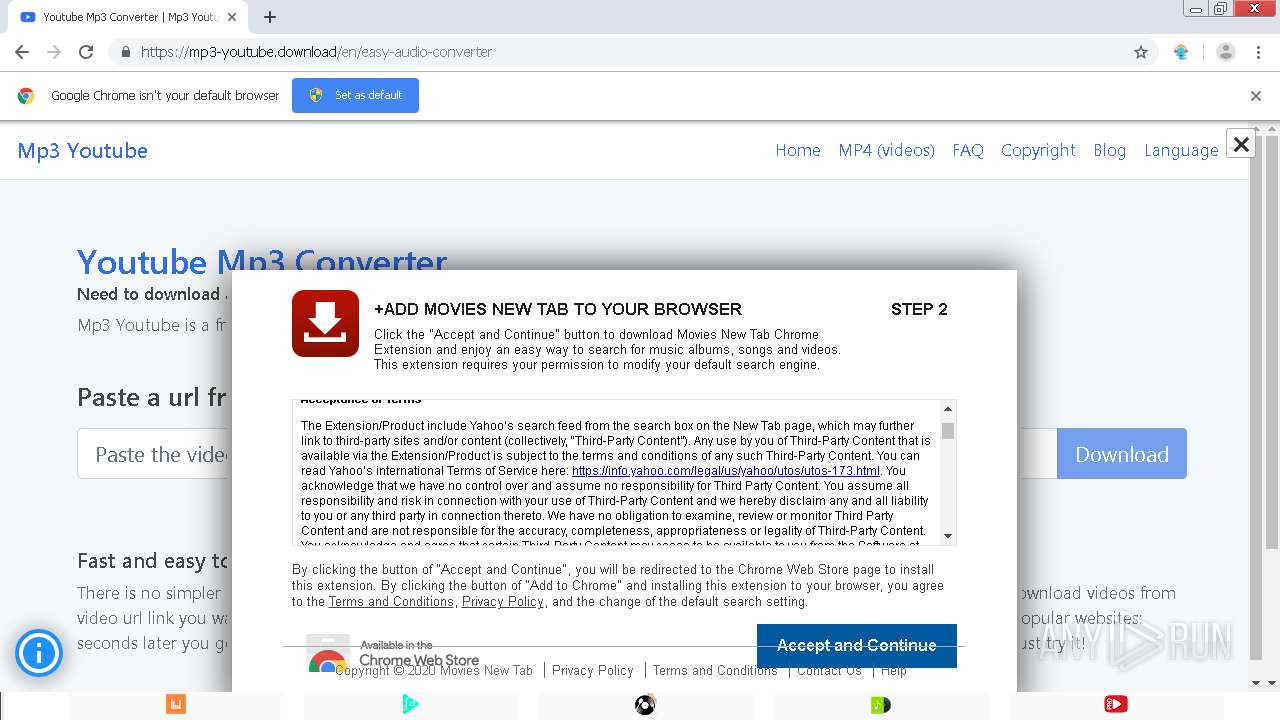
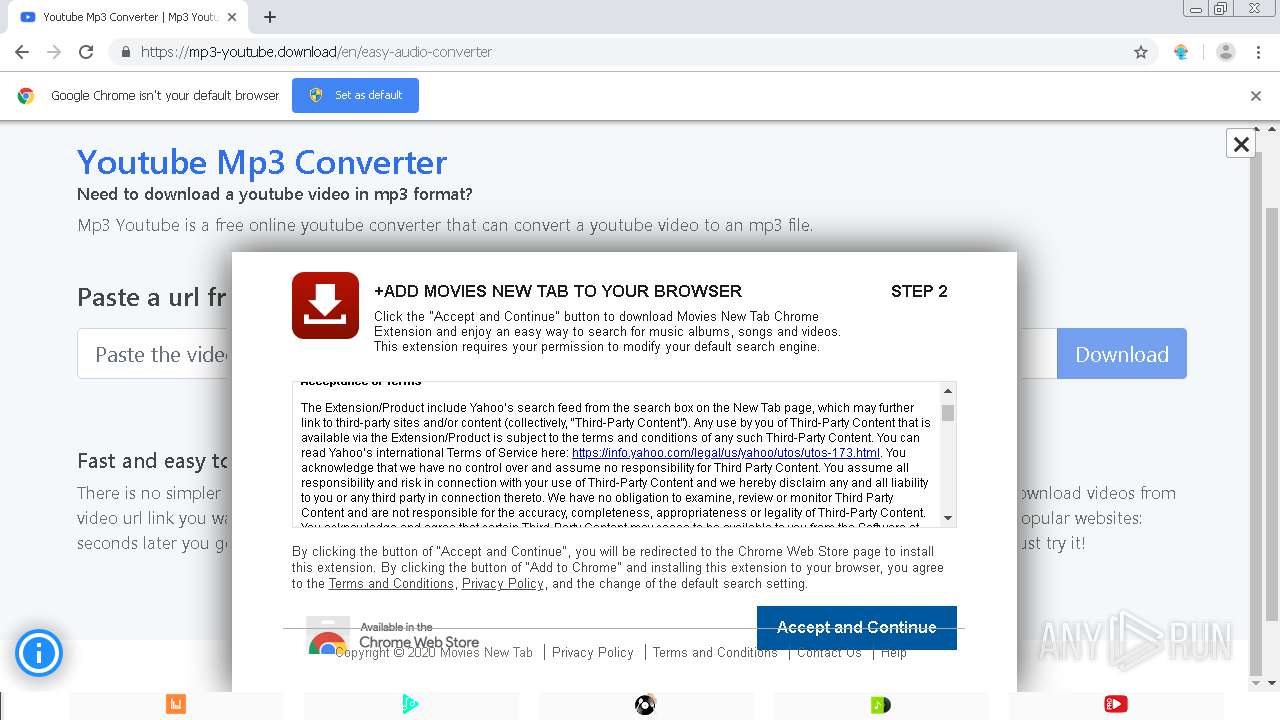
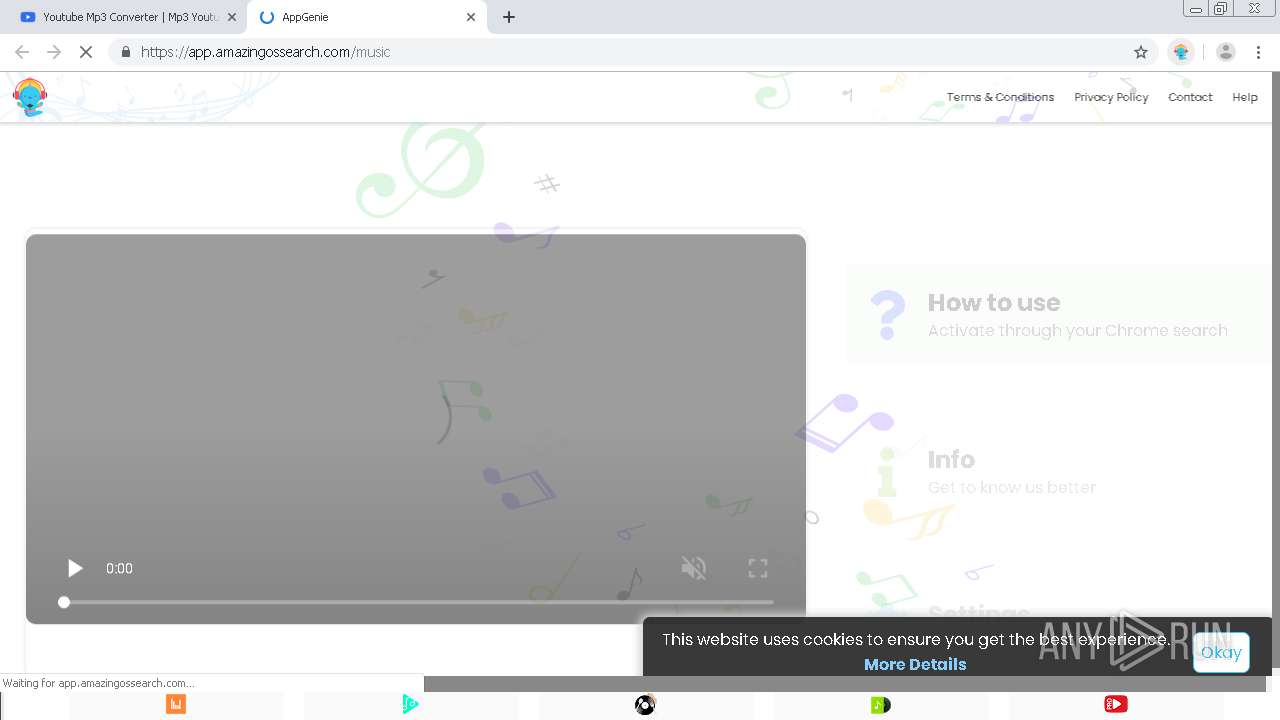
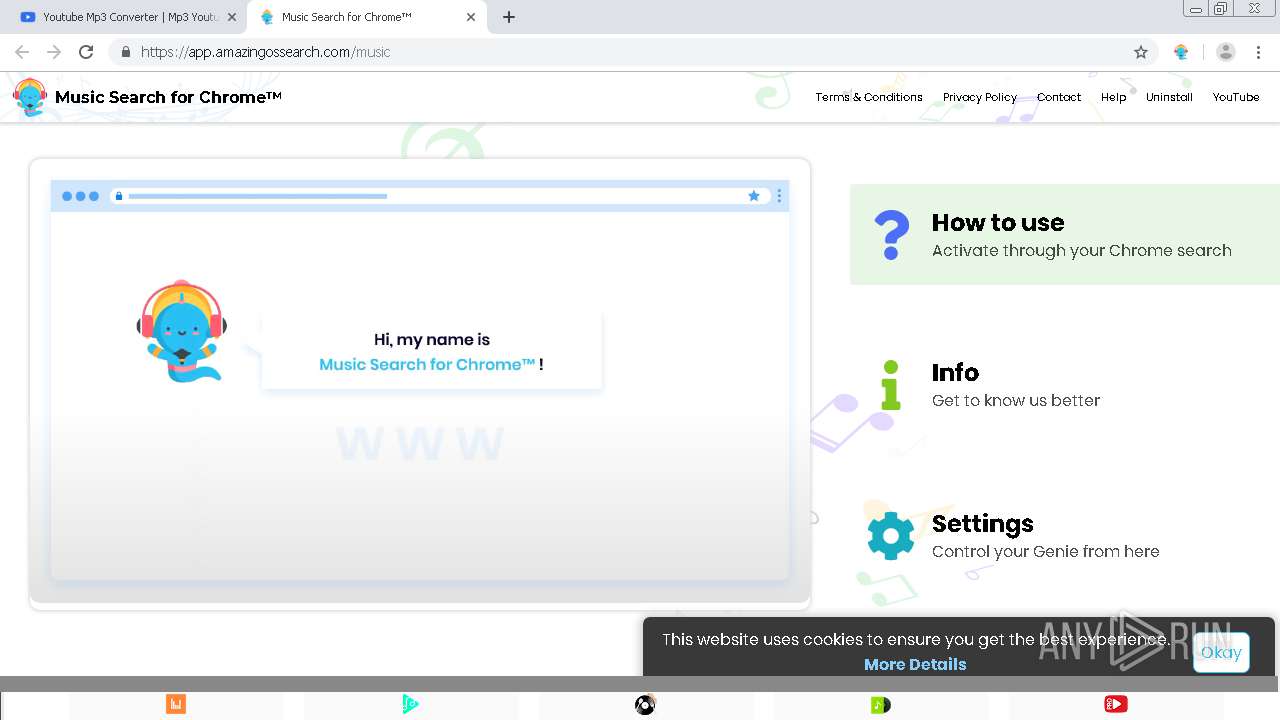
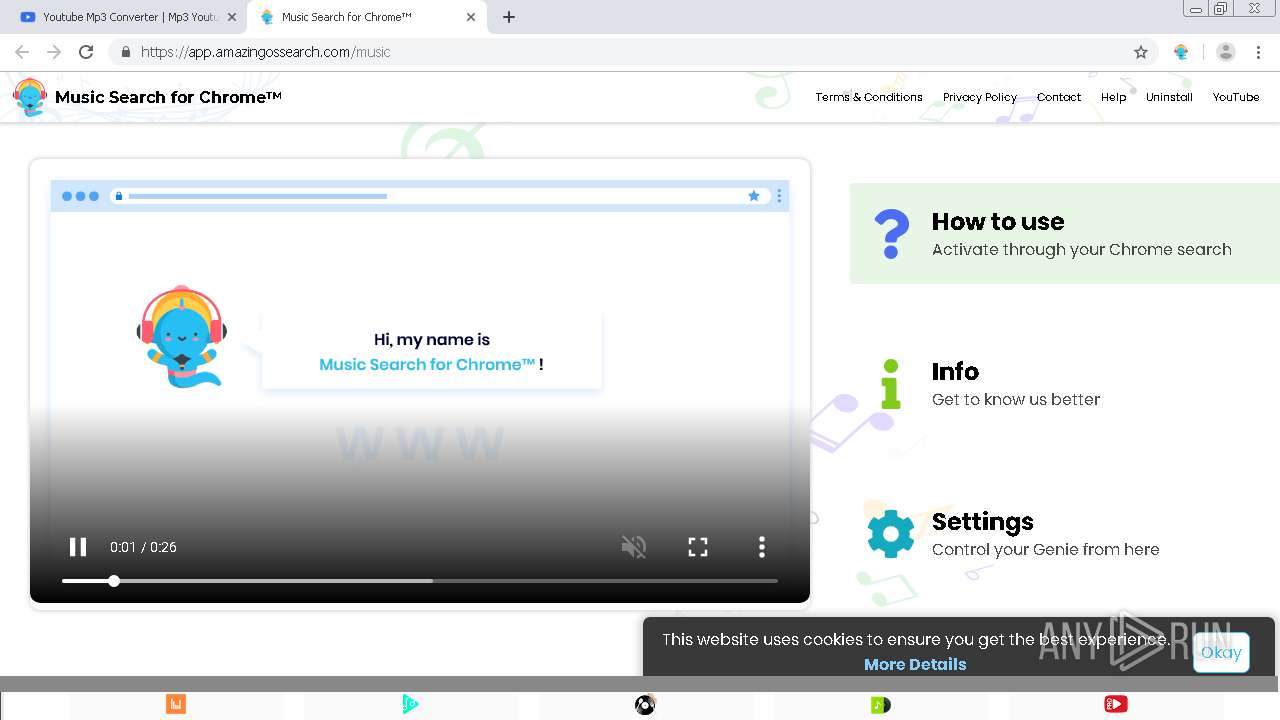
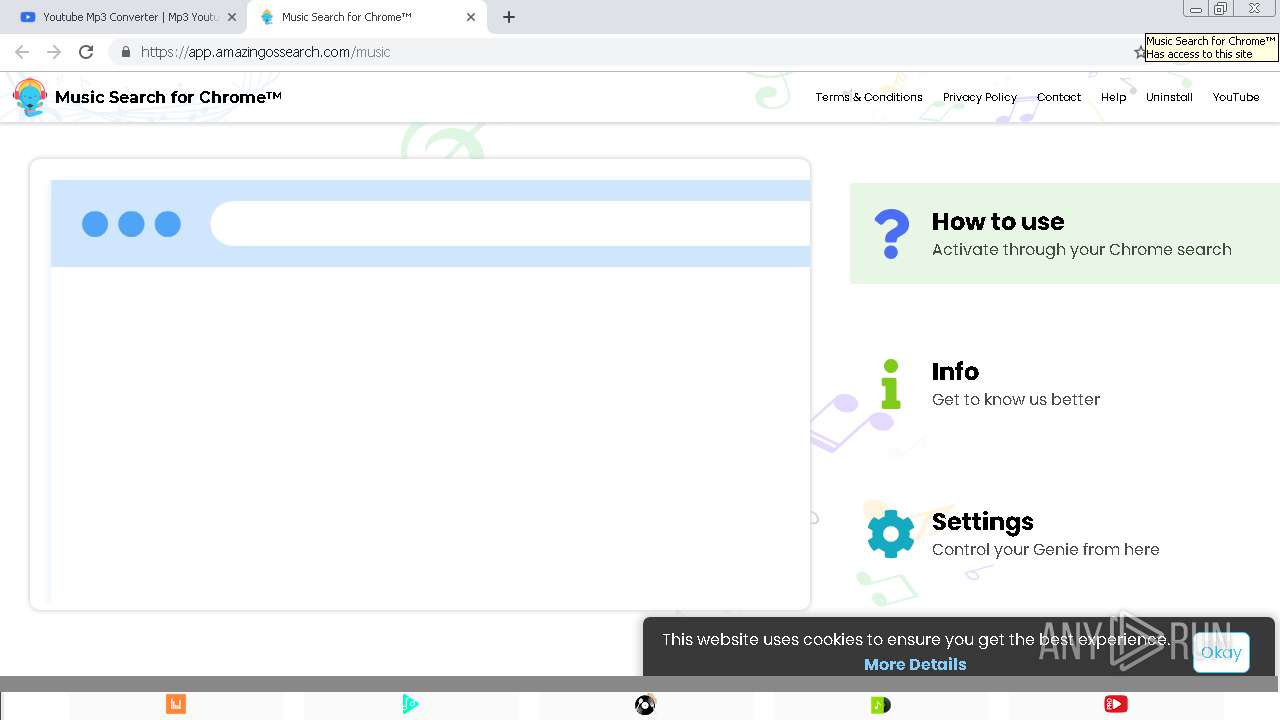
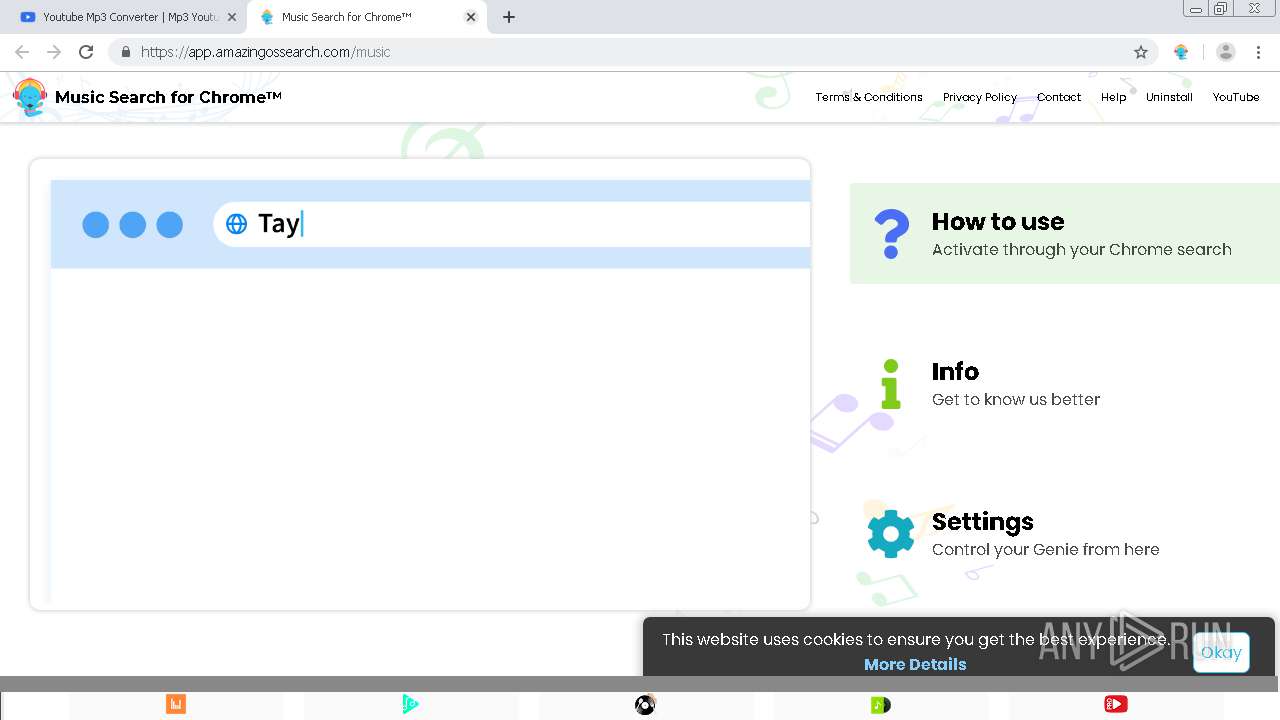
Modifies files in Chrome extension folder
- chrome.exe (PID: 2904)
INFO
Application launched itself
- chrome.exe (PID: 2904)
Reads settings of System Certificates
- chrome.exe (PID: 2544)
Reads Internet Cache Settings
- chrome.exe (PID: 2904)
Reads the hosts file
- chrome.exe (PID: 2904)
- chrome.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14482923927704232322 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2796 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4622916964917889520 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6958090302383495210 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4493389630159479837 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9916116081544679117 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3526364395220348860 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11974534981918175904 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15165945753208153334 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,1916147911066755973,12997642891295246505,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9658161361129963778 --mojo-platform-channel-handle=4032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
970
Read events
841
Write events
124
Delete events
5
Modification events
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2904-13242055086045000 |
Value: 259 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
84
Text files
158
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\128ebed6-fc38-4fdc-9826-8785fcd71ed1.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1911d8.TMP | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1911c9.TMP | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1913cc.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF191236.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
70
DNS requests
37
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
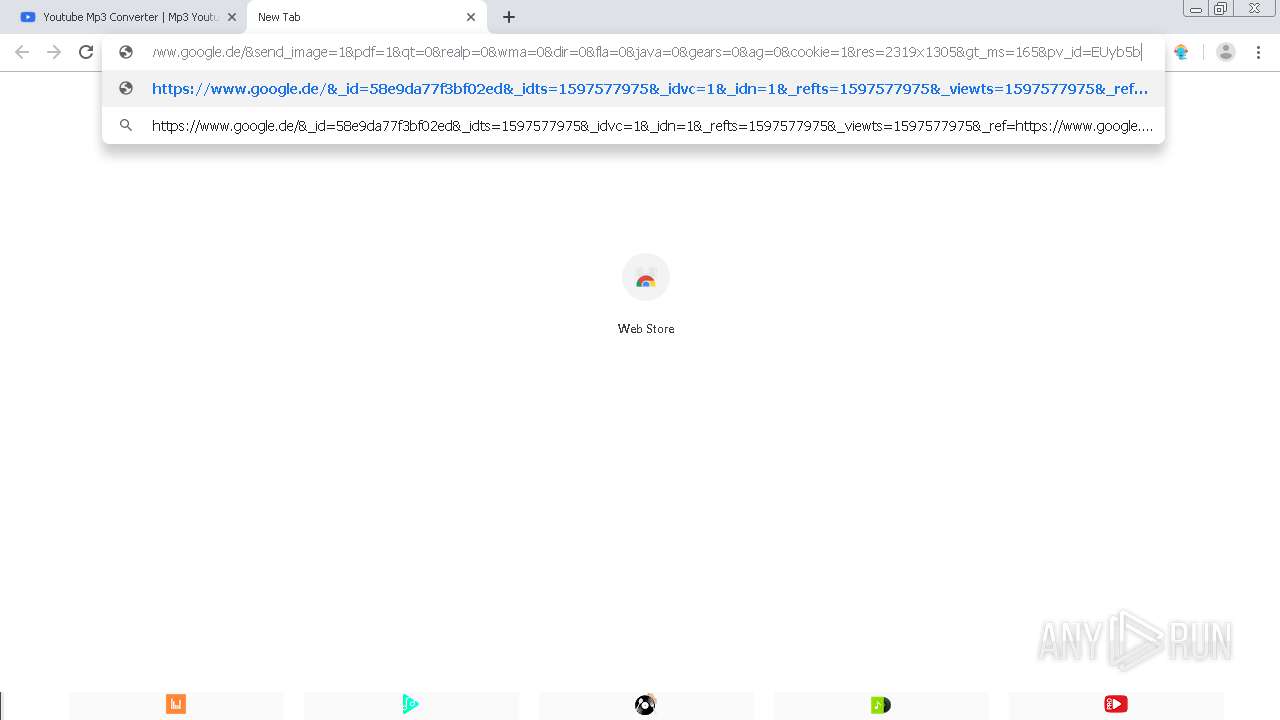
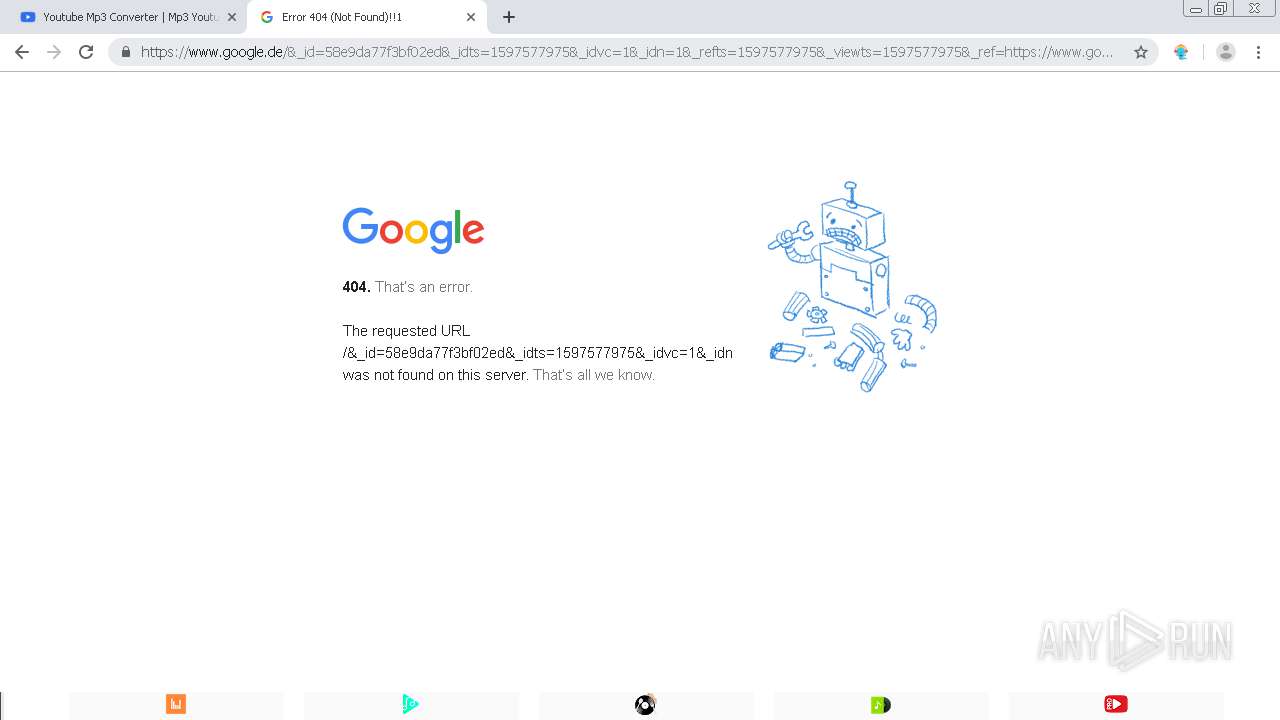
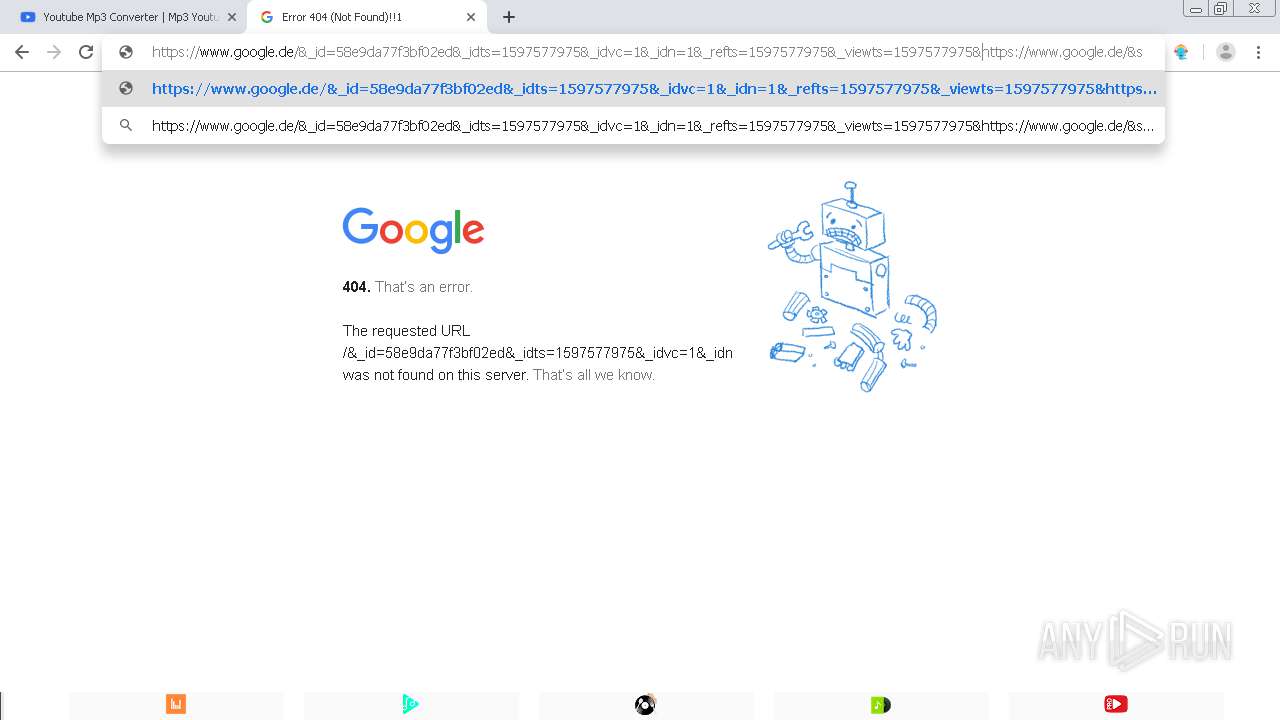
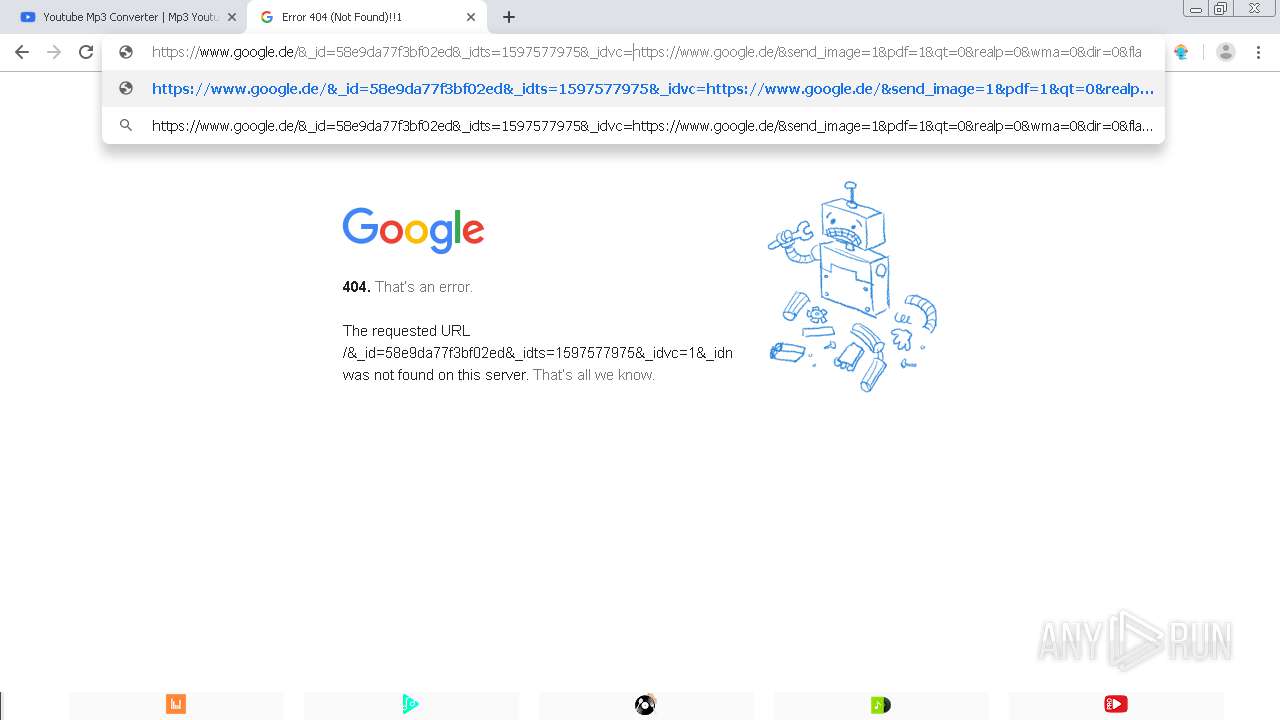
2544 | chrome.exe | GET | — | 51.68.117.181:8080 | http://mp3-youtube.download:8080/uhwcpdm2ec9m8stgum1n/?action_name=Convertidor%20Youtube%20Mp3%20|%20Mp3%20Youtube&idsite=1&rec=1&r=930386&h=13&m=39&s=34&url=https://mp3-youtube.download/es/easy-audio-converter&urlref=https://www.google.de/&_id=58e9da77f3bf02ed&_idts=1597577975&_idvc=1&_idn=1&_refts=1597577975&_viewts=1597577975&_ref=https://www.google.de/&send_image=1&pdf=1&qt=0&realp=0&wma=0&dir=0&fla=0&java=0&gears=0&ag=0&cookie=1&res=2319x1305>_ms=165&pv_id=EUyb5b | GB | — | — | suspicious |
2544 | chrome.exe | GET | 301 | 51.68.117.181:80 | http://mp3-youtube.download/ | GB | — | — | whitelisted |
2544 | chrome.exe | GET | — | 51.68.117.181:8080 | http://mp3-youtube.download:8080/uhwcpdm2ec9m8stgum1n/?action_name=Convertidor%20Youtube%20Mp3%20|%20Mp3%20Youtube&idsite=1&rec=1&r=930386&h=13&m=39&s=34&url=https://mp3-youtube.download/es/easy-audio-converter&urlref=https://www.google.de/&_id=58e9da77f3bf02ed&_idts=1597577975&_idvc=1&_idn=1&_refts=1597577975&_viewts=1597577975&_ref=https://www.google.de/&send_image=1&pdf=1&qt=0&realp=0&wma=0&dir=0&fla=0&java=0&gears=0&ag=0&cookie=1&res=2319x1305>_ms=165&pv_id=EUyb5b | GB | — | — | suspicious |
2544 | chrome.exe | GET | — | 51.68.117.181:8080 | http://mp3-youtube.download:8080/uhwcpdm2ec9m8stgum1n/?action_name=Convertidor%20Youtube%20Mp3%20|%20Mp3%20Youtube&idsite=1&rec=1&r=930386&h=13&m=39&s=34&url=https://mp3-youtube.download/es/easy-audio-converter&urlref=https://www.google.de/&_id=58e9da77f3bf02ed&_idts=1597577975&_idvc=1&_idn=1&_refts=1597577975&_viewts=1597577975&_ref=https://www.google.de/&send_image=1&pdf=1&qt=0&realp=0&wma=0&dir=0&fla=0&java=0&gears=0&ag=0&cookie=1&res=2319x1305>_ms=165&pv_id=EUyb5b | GB | — | — | suspicious |
2544 | chrome.exe | GET | — | 51.68.117.181:8080 | http://mp3-youtube.download:8080/uhwcpdm2ec9m8stgum1n/?action_name=Convertidor%20Youtube%20Mp3%20|%20Mp3%20Youtube&idsite=1&rec=1&r=930386&h=13&m=39&s=34&url=https://mp3-youtube.download/es/easy-audio-converter&urlref=https://www.google.de/&_id=58e9da77f3bf02ed&_idts=1597577975&_idvc=1&_idn=1&_refts=1597577975&_viewts=1597577975&_ref=https://www.google.de/&send_image=1&pdf=1&qt=0&realp=0&wma=0&dir=0&fla=0&java=0&gears=0&ag=0&cookie=1&res=2319x1305>_ms=165&pv_id=EUyb5b | GB | — | — | suspicious |
2544 | chrome.exe | GET | — | 51.68.117.181:8080 | http://mp3-youtube.download:8080/uhwcpdm2ec9m8stgum1n/?action_name=Convertidor%20Youtube%20Mp3%20|%20Mp3%20Youtube&idsite=1&rec=1&r=930386&h=13&m=39&s=34&url=https://mp3-youtube.download/es/easy-audio-converter&urlref=https://www.google.de/&_id=58e9da77f3bf02ed&_idts=1597577975&_idvc=1&_idn=1&_refts=1597577975&_viewts=1597577975&_ref=https://www.google.de/&send_image=1&pdf=1&qt=0&realp=0&wma=0&dir=0&fla=0&java=0&gears=0&ag=0&cookie=1&res=2319x1305>_ms=165&pv_id=EUyb5b | GB | — | — | suspicious |
2544 | chrome.exe | GET | — | 51.68.117.181:8080 | http://mp3-youtube.download:8080/uhwcpdm2ec9m8stgum1n/?action_name=Convertidor%20Youtube%20Mp3%20|%20Mp3%20Youtube&idsite=1&rec=1&r=930386&h=13&m=39&s=34&url=https://mp3-youtube.download/es/easy-audio-converter&urlref=https://www.google.de/&_id=58e9da77f3bf02ed&_idts=1597577975&_idvc=1&_idn=1&_refts=1597577975&_viewts=1597577975&_ref=https://www.google.de/&send_image=1&pdf=1&qt=0&realp=0&wma=0&dir=0&fla=0&java=0&gears=0&ag=0&cookie=1&res=2319x1305>_ms=165&pv_id=EUyb5b | GB | — | — | suspicious |
2544 | chrome.exe | GET | — | 51.68.117.181:8080 | http://mp3-youtube.download:8080/uhwcpdm2ec9m8stgum1n/ | GB | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | chrome.exe | 51.68.117.181:80 | mp3-youtube.download | — | GB | suspicious |
2544 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2544 | chrome.exe | 51.68.117.181:443 | mp3-youtube.download | — | GB | suspicious |
2544 | chrome.exe | 173.192.101.24:443 | p25433.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
2544 | chrome.exe | 94.31.29.128:443 | p25433.mycdn.co | netDNA | GB | malicious |
2544 | chrome.exe | 104.28.30.80:443 | www.getawesome10.com | Cloudflare Inc | US | shared |
2544 | chrome.exe | 104.24.110.188:443 | get.amazingosapps.com | Cloudflare Inc | US | unknown |
2544 | chrome.exe | 172.67.170.144:443 | app.amazingossearch.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mp3-youtube.download |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
p25433.clksite.com |
| suspicious |
infopicked.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2544 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |