| File name: | WRR.exe |
| Full analysis: | https://app.any.run/tasks/bf9d7ec2-4f50-4c17-8d3e-9dbc6eb4b056 |
| Verdict: | Malicious activity |
| Analysis date: | September 21, 2021, 13:06:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FBA410377A3291BA26F2DFD0690D969F |
| SHA1: | F757C399285CCFD7DB07D5FF984A3CF96EE393AE |
| SHA256: | DE88913C12C3C29C53E680C5E1C31CA90BDF4E94A0D98B778A19DA9FB900D6C0 |
| SSDEEP: | 49152:bT6nfP2JVHnXdNUP8w8ZLTFgN1PwWJXAwoPsqp:bWfeJhnNNxJZyN1PwWRAwoPxp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- WRR.exe (PID: 3572)
Checks supported languages
- WRR.exe (PID: 3572)
Reads the computer name
- WRR.exe (PID: 3572)
Reads Environment values
- WRR.exe (PID: 3572)
INFO
Reads settings of System Certificates
- WRR.exe (PID: 3572)
Checks Windows Trust Settings
- WRR.exe (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Generic (100) |
|---|
EXIF
EXE
| BuildTimestamp: | 2021-02-16 08:18:53 |
|---|---|
| ProductVersion: | 3.0.0.0 |
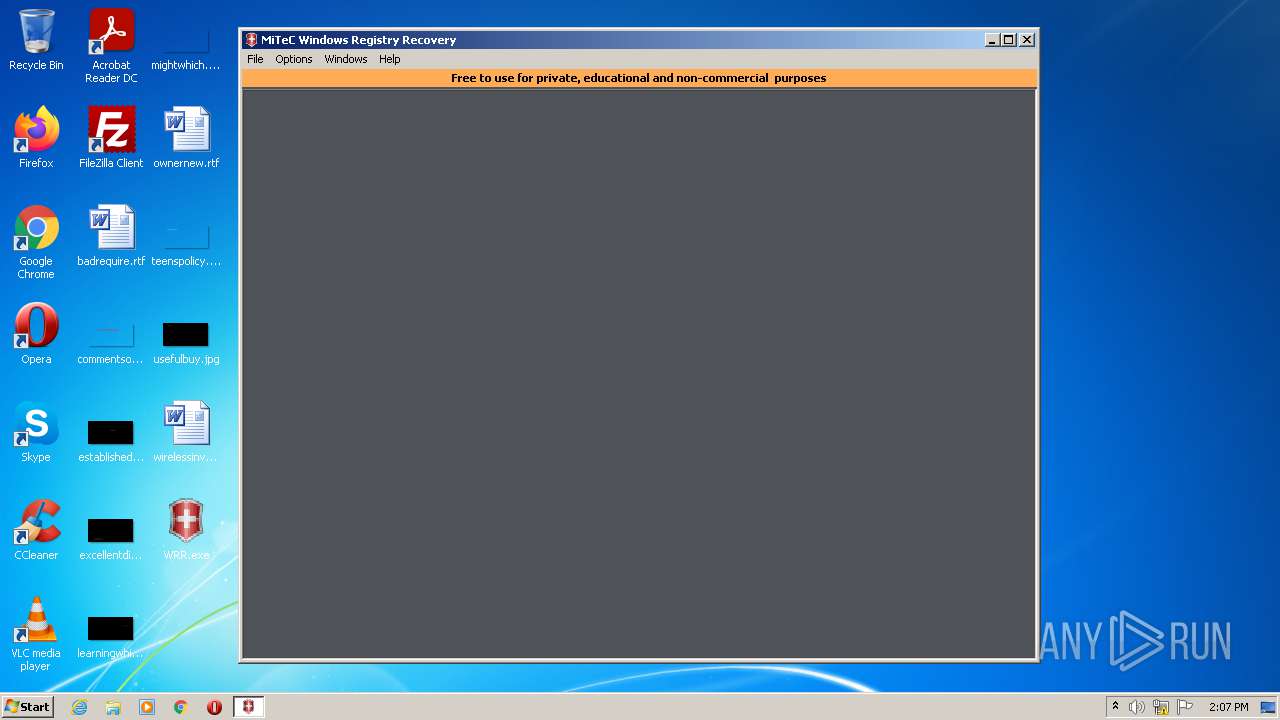
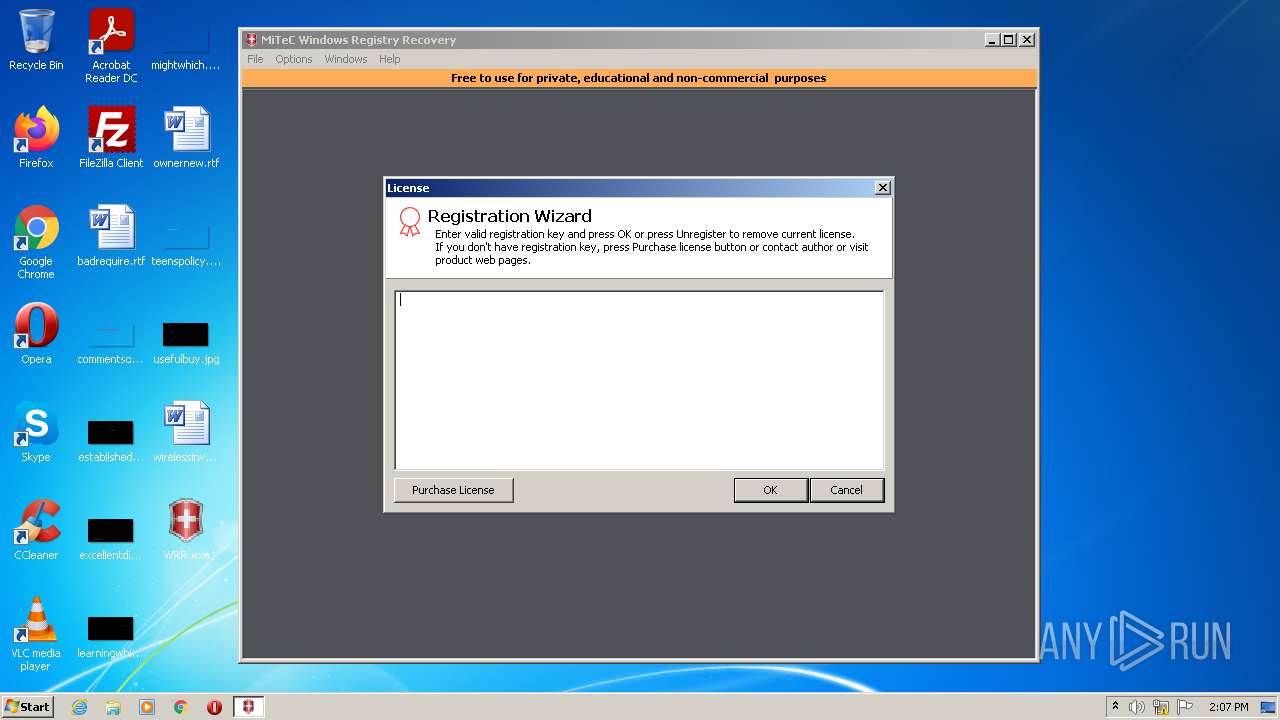
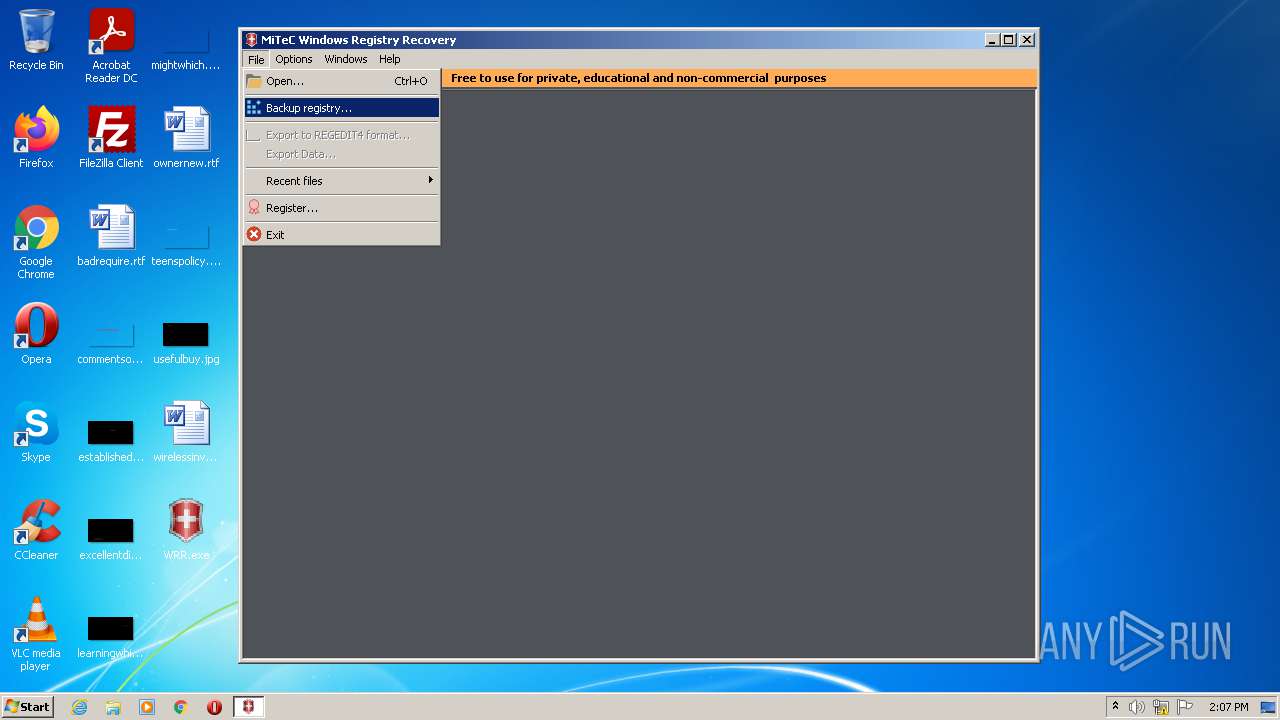
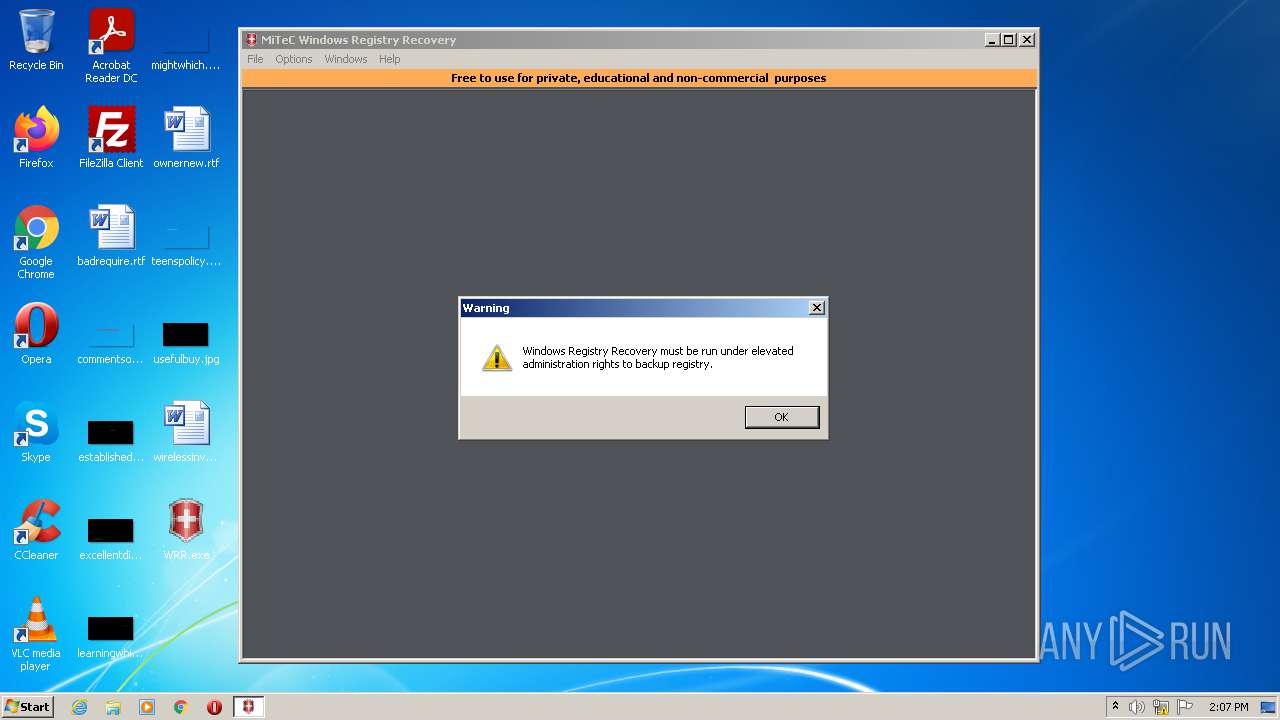
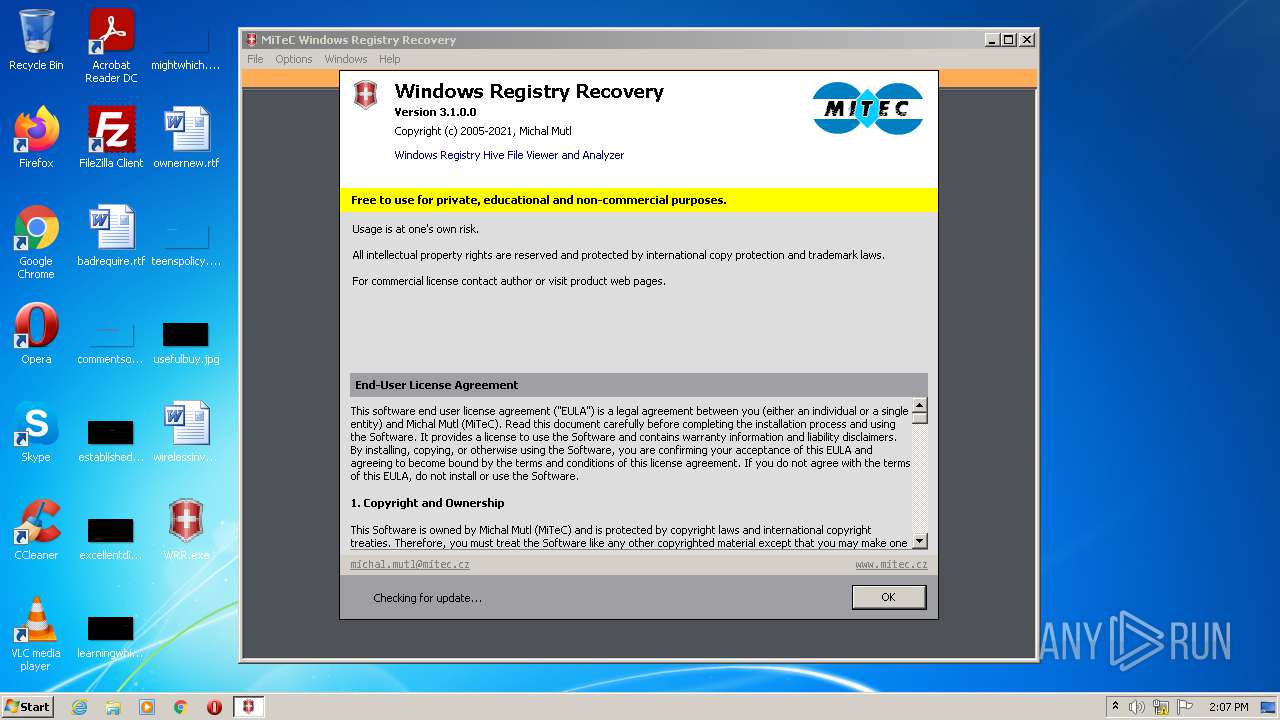
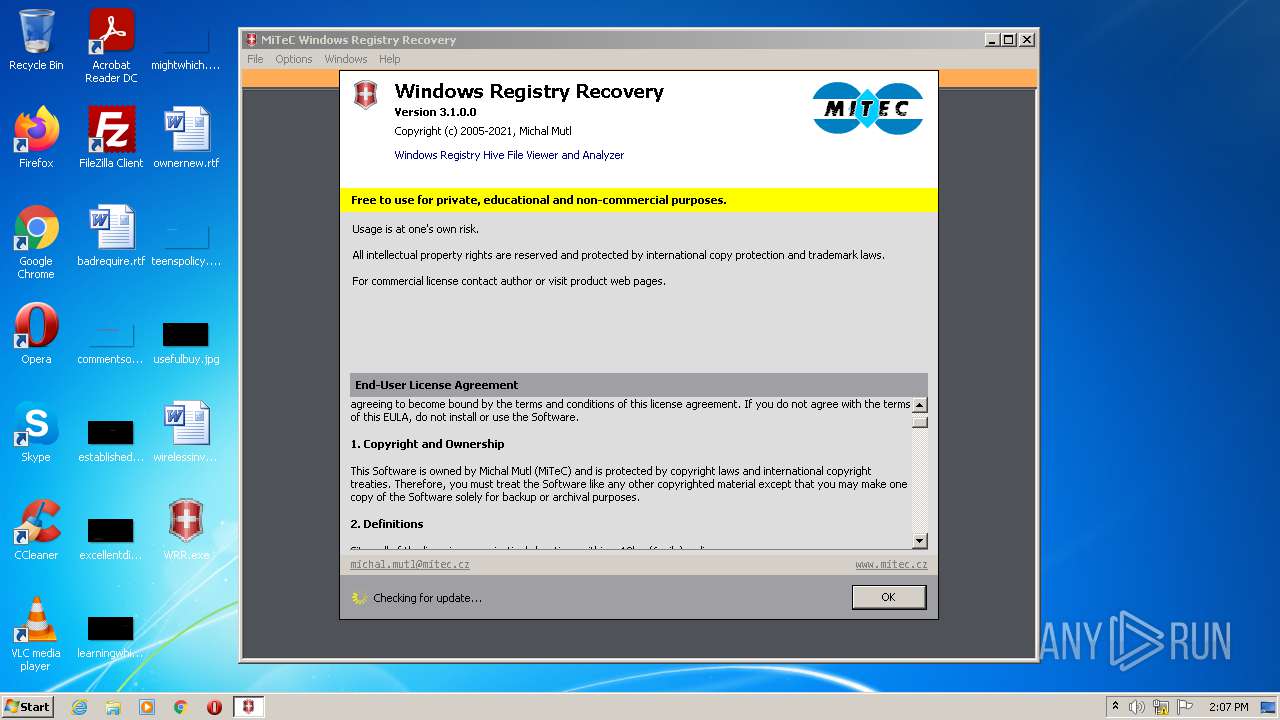
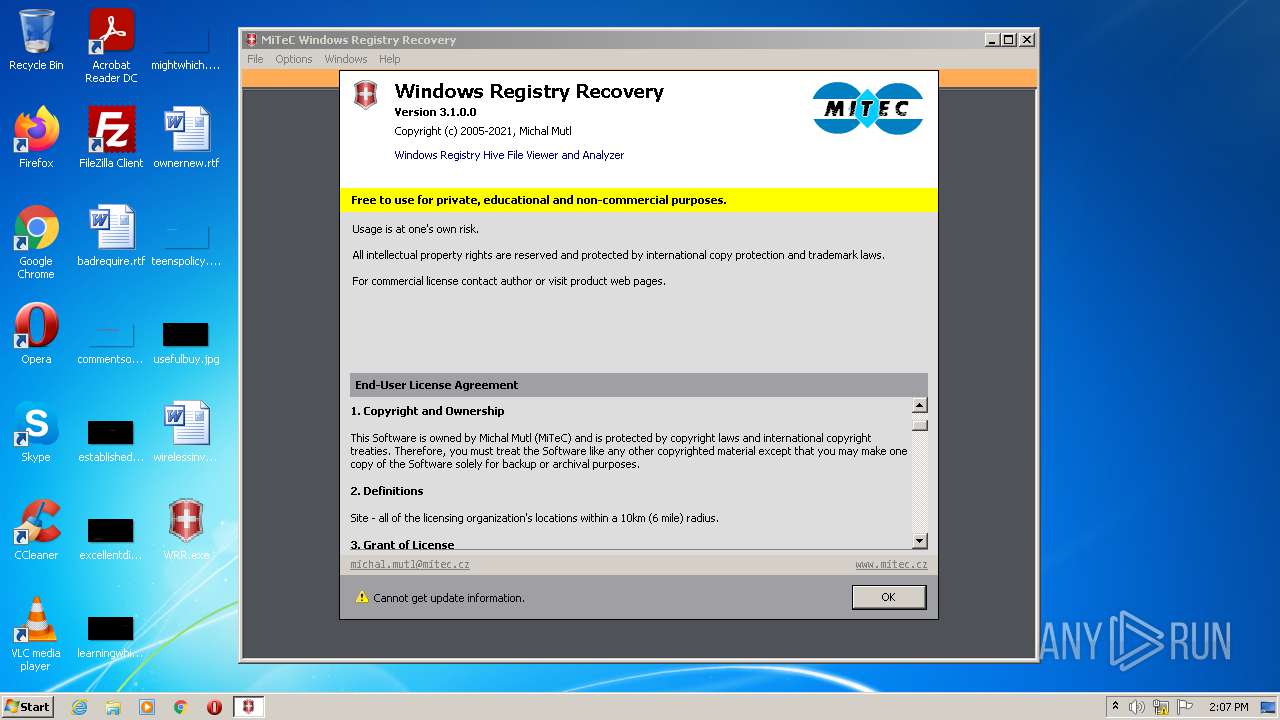
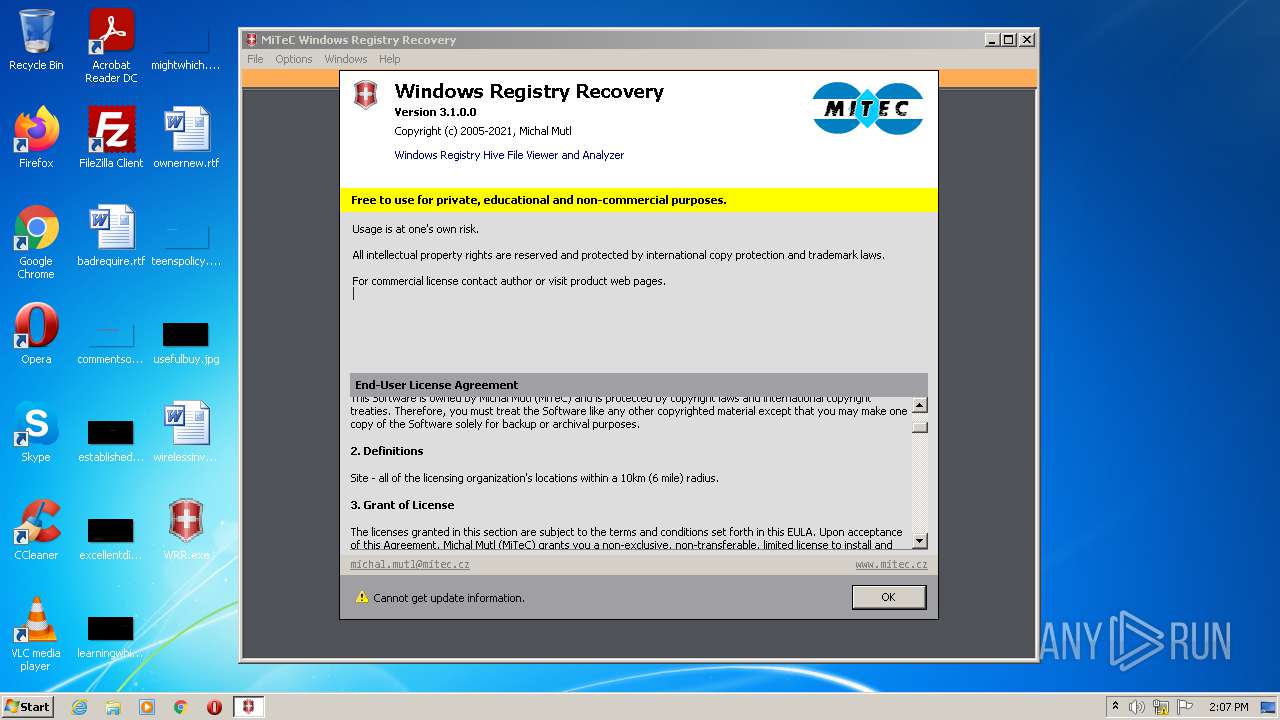
| ProductName: | Windows Registry Recovery |
| LegalTrademarks: | All rights reserved |
| LegalCopyright: | Copyright (c) 2005-2021, Michal Mutl |
| FileVersion: | 3.1.0.0 |
| FileDescription: | Windows Registry Hive File Viewer and Analyzer |
| CompanyName: | MiTeC |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.0.0.0 |
| FileVersionNumber: | 3.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x494000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 557056 |
| CodeSize: | 4173824 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2021:02:16 08:18:53+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Feb-2021 07:18:53 |
| Detected languages: |
|
| CompanyName: | MiTeC |
| FileDescription: | Windows Registry Hive File Viewer and Analyzer |
| FileVersion: | 3.1.0.0 |
| LegalCopyright: | Copyright (c) 2005-2021, Michal Mutl |
| LegalTrademarks: | All rights reserved |
| ProductName: | Windows Registry Recovery |
| ProductVersion: | 3.0.0.0 |
| BuildTimestamp: | 2021-02-16 08:18:53 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x8070 |
| Pages in file: | 0xE870 |
| Relocations: | 0x2176 |
| Size of header: | 0xD8D2 |
| Min extra paragraphs: | 0x6896 |
| Max extra paragraphs: | 0xEEC2 |
| Initial SS value: | 0x2398 |
| Initial SP value: | 0x621B |
| Checksum: | 0x0A8F |
| Initial IP value: | 0x908A |
| Initial CS value: | 0x479D |
| Overlay number: | 0x0F92 |
| OEM identifier: | 0xF8C0 |
| OEM information: | 0x5AB7 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 16-Feb-2021 07:18:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00494000 | 0x00018000 | 0x00017AA9 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99718 | |
.rsrc | 0x0041D000 | 0x00075990 | 0x000334C4 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.80745 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27093 | 1803 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.29737 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 7.3456 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 7.30513 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 7.32611 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 7.31685 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 7.32175 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
8 | 7.74791 | 748 | Latin 1 / Western European | German - Germany | RT_CURSOR |
9 | 7.74621 | 748 | Latin 1 / Western European | German - Germany | RT_CURSOR |
10 | 7.72489 | 748 | Latin 1 / Western European | German - Germany | RT_CURSOR |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
user32.dll |
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3572 | "C:\Users\admin\Desktop\WRR.exe" | C:\Users\admin\Desktop\WRR.exe | Explorer.EXE | ||||||||||||
User: admin Company: MiTeC Integrity Level: MEDIUM Description: Windows Registry Hive File Viewer and Analyzer Exit code: 0 Version: 3.1.0.0 Modules
| |||||||||||||||
Total events
3 595
Read events
3 563
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000042010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3572) WRR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{0FA59E78-A5D9-47A6-B762-5DBE7DEFFD64} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3572 | WRR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B43A6A2AB31D8F6B89DCFD4FD9686D5_A6D3E6111E119F3E0C64EEB33F6DCBD5 | der | |
MD5:— | SHA256:— | |||
| 3572 | WRR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\463A0CFFD55C1008D765CD90A5CA8812_CE005042706F522923C13C5726F0F589 | der | |
MD5:— | SHA256:— | |||
| 3572 | WRR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B43A6A2AB31D8F6B89DCFD4FD9686D5_A6D3E6111E119F3E0C64EEB33F6DCBD5 | binary | |
MD5:— | SHA256:— | |||
| 3572 | WRR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3572 | WRR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\463A0CFFD55C1008D765CD90A5CA8812_CE005042706F522923C13C5726F0F589 | binary | |
MD5:— | SHA256:— | |||
| 3572 | WRR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3572 | WRR.exe | GET | 200 | 109.70.240.130:80 | http://ocsp05.actalis.it/VA/AUTH-ROOT/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSw4x5v4bTlizjNRmTdkYSy7q0R9gQUUtiIOsifeGbtifN7OHCUyQICNtACEBJzd5ejFYht%2FrdsfmpaA1Q%3D | IT | der | 2.01 Kb | whitelisted |
1084 | svchost.exe | GET | 304 | 8.253.95.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f1a4a33104c3532a | US | — | — | whitelisted |
3572 | WRR.exe | GET | 200 | 109.70.240.114:80 | http://ocsp06.actalis.it/VA/AUTHDV-G3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBROJtlvaAzyepGCxfu9qEfsEKGHVgQUQoNtgHwJhGf9gFer8Sb1d8gignECEHk5KU3AwdmtX6VX%2BbFFM%2BA%3D | IT | der | 3.83 Kb | whitelisted |
3572 | WRR.exe | GET | 200 | 8.253.95.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?904b83b40813f559 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3572 | WRR.exe | 81.2.194.241:443 | www.mitec.cz | INTERNET CZ, a.s. | CZ | malicious |
3572 | WRR.exe | 109.70.240.114:80 | ocsp06.actalis.it | Aruba S.p.A. | IT | unknown |
3572 | WRR.exe | 109.70.240.130:80 | ocsp05.actalis.it | Aruba S.p.A. | IT | suspicious |
3572 | WRR.exe | 8.253.95.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
— | — | 8.253.95.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mitec.cz |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp05.actalis.it |
| whitelisted |
ocsp06.actalis.it |
| whitelisted |