| File name: | PDFConverty.exe |
| Full analysis: | https://app.any.run/tasks/a8ce585a-174f-48cf-8b90-7680e2a34620 |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2023, 00:13:56 |
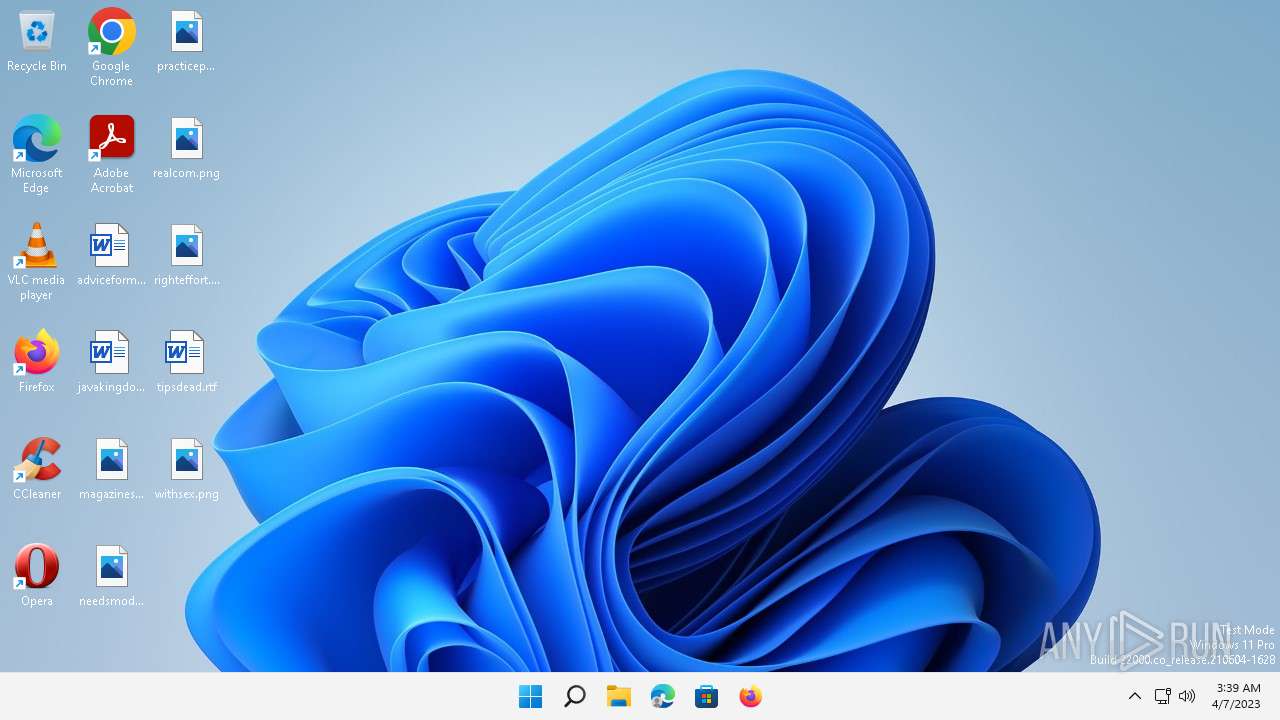
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 176E59D04D8B3E5F3BB05F3FD4B154A6 |
| SHA1: | 5784A6021DE8ABA5893B86AABD8726F8FE2D1639 |
| SHA256: | DE877BD0FE61BE5627D1B906EAAF59D56E8F0F985EBB8A7812EBA039B19EEB19 |
| SSDEEP: | 24576:QFGQ7I2W0sdMKPAOhJPAOhXnebe+/Apd2BEbFn++4dYH:/29sdMtZSnebe+/AXbFn++f |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
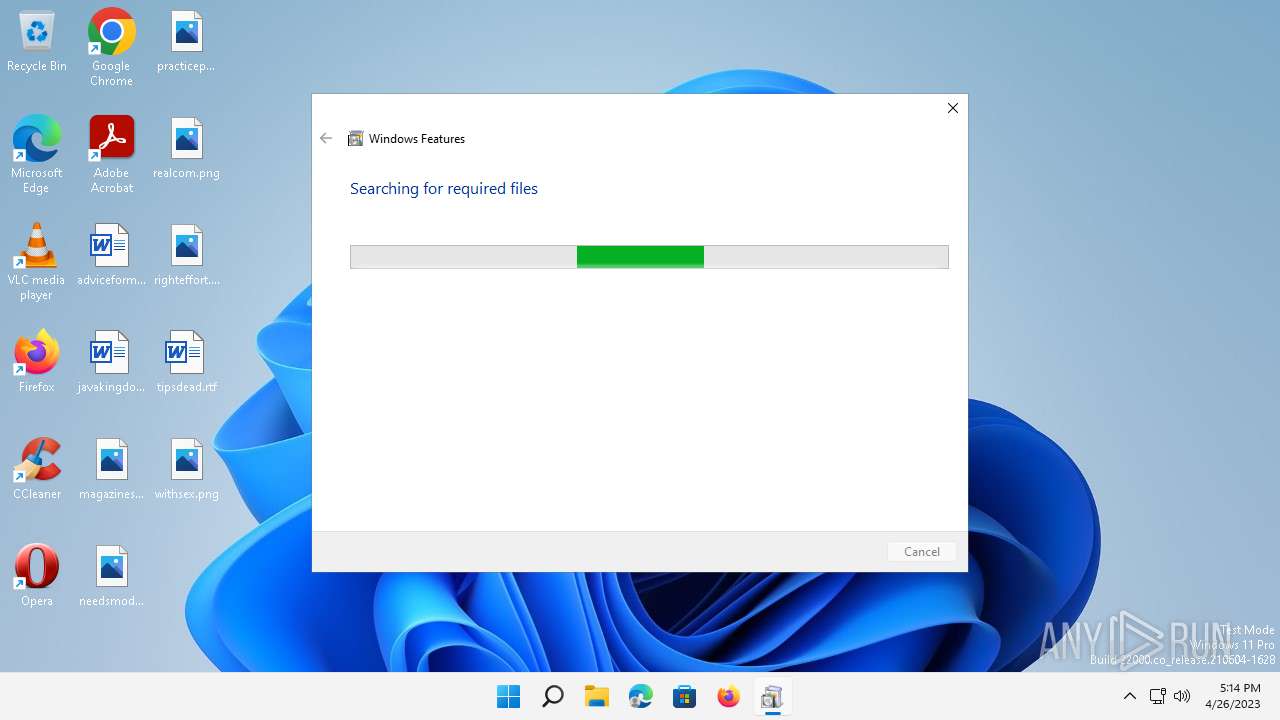
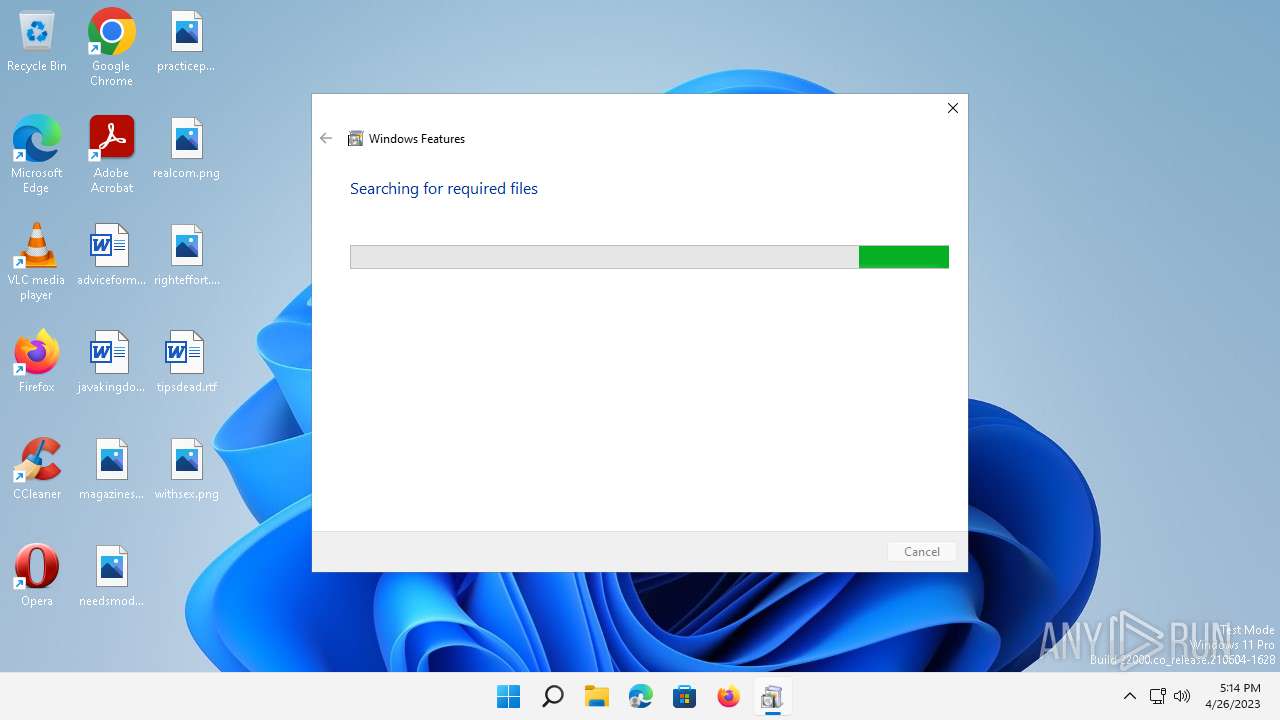
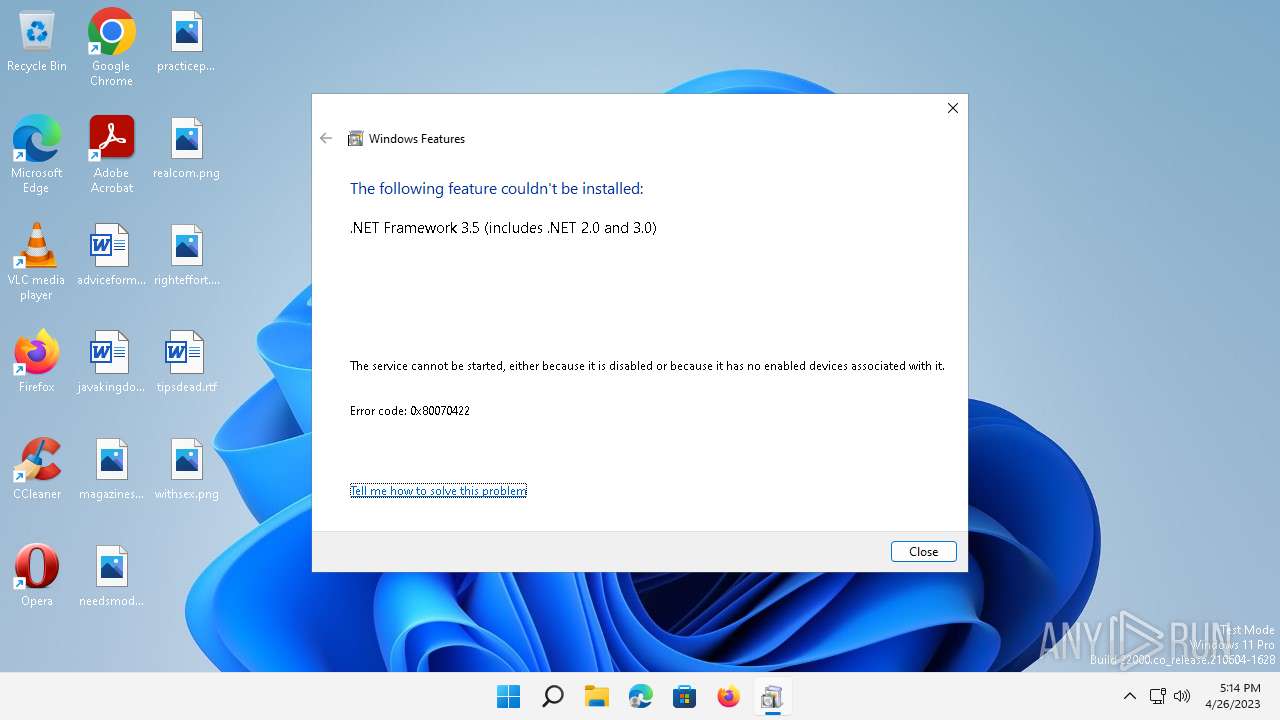
- Fondue.exe (PID: 5880)
- Fondue.exe (PID: 3064)
Searches for installed software
- TiWorker.exe (PID: 5548)
Executes as Windows Service
- VSSVC.exe (PID: 2164)
Reads settings of System Certificates
- wermgr.exe (PID: 272)
- TiWorker.exe (PID: 5548)
INFO
The process checks LSA protection
- Fondue.exe (PID: 5880)
- Fondue.exe (PID: 3064)
- OptionalFeatures.exe (PID: 3848)
- VSSVC.exe (PID: 2164)
- SrTasks.exe (PID: 3280)
Checks supported languages
- PDFConverty.exe (PID: 6092)
Creates files in the program directory
- TiWorker.exe (PID: 5548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| AssemblyVersion: | 1.0.6.0 |
|---|---|
| ProductVersion: | 1.0.6 |
| ProductName: | PDFConverty |
| OriginalFileName: | PDFConvertyexe.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2022 |
| InternalName: | PDFConvertyexe.exe |
| FileVersion: | 1.0.6 |
| FileDescription: | PDFConverty |
| CompanyName: | - |
| Comments: | PDFConverty |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.6.0 |
| FileVersionNumber: | 1.0.6.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xfc452 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 22528 |
| CodeSize: | 1025536 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:02:27 06:17:39+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Feb-2023 06:17:39 |
| Debug artifacts: |
|
| Comments: | PDFConverty |
| CompanyName: | - |
| FileDescription: | PDFConverty |
| FileVersion: | 1.0.6 |
| InternalName: | PDFConvertyexe.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFilename: | PDFConvertyexe.exe |
| ProductName: | PDFConverty |
| ProductVersion: | 1.0.6 |
| Assembly Version: | 1.0.6.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 27-Feb-2023 06:17:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000FA4E7 | 0x000FA600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47626 |
.rsrc | 0x000FE000 | 0x0000544F | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81739 |
.reloc | 0x00104000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99932 | 3483 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
138
Monitored processes
10
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Windows\system32\wermgr.exe" "-outproc" "0" "5548" "1540" "1508" "1544" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | — | TiWorker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2164 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
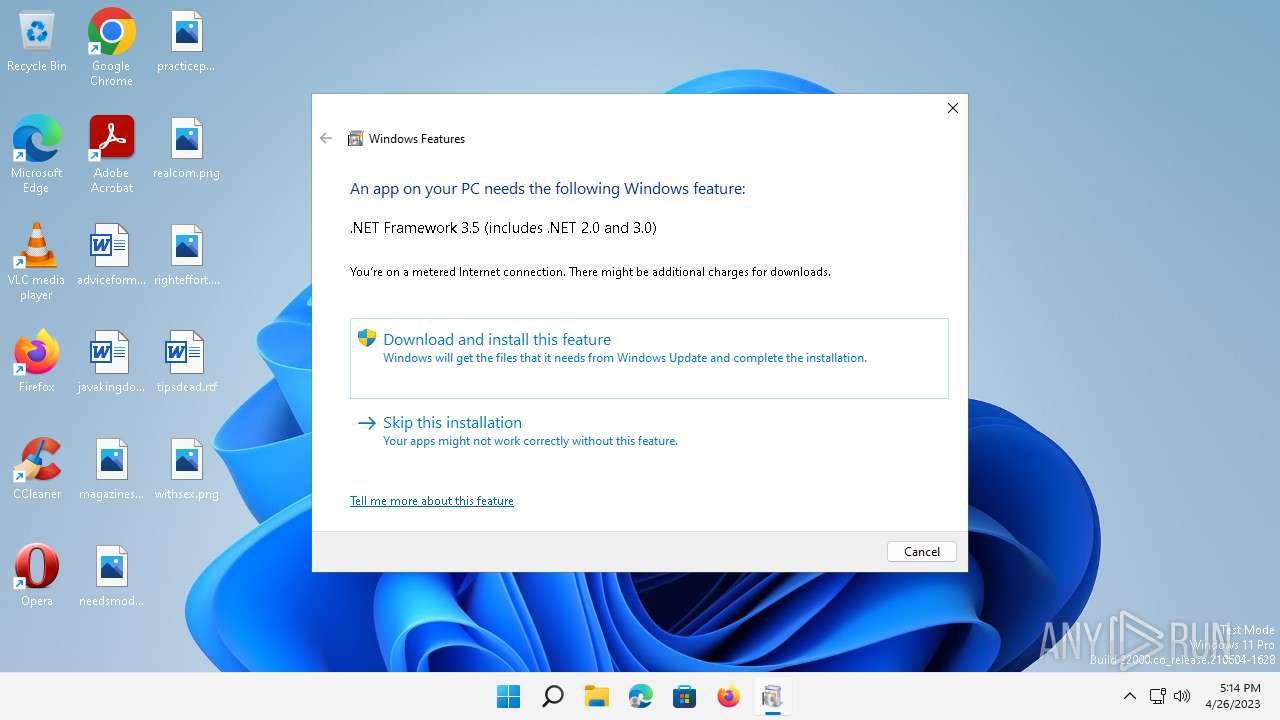
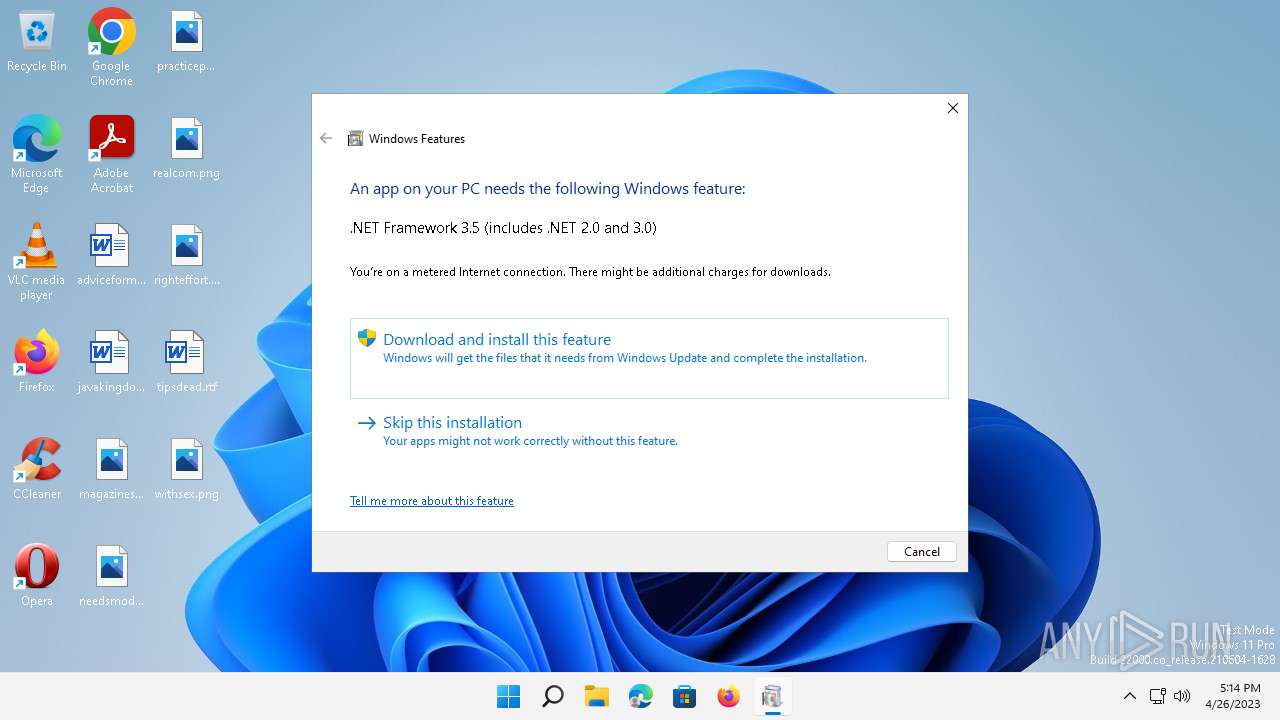
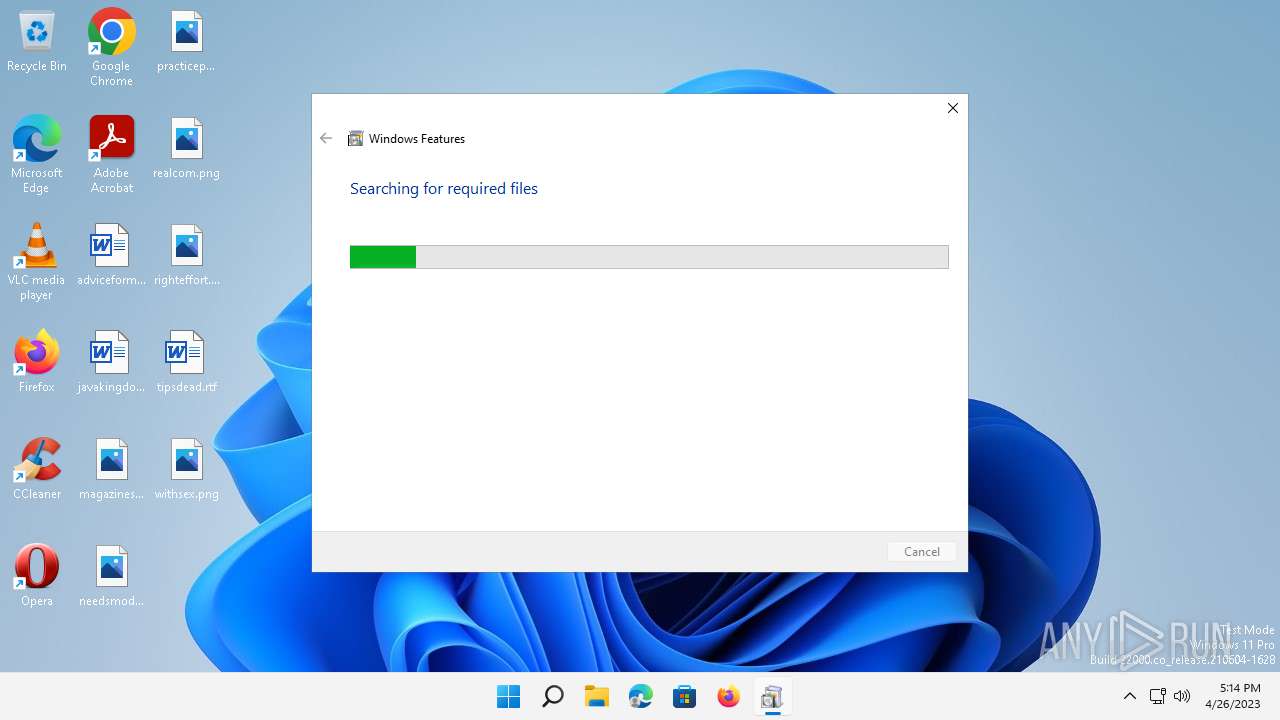
| 2516 | "C:\Windows\system32\OptionalFeatures.EXE" /enable-feature:NetFx3 /caller-name:mscoreei.dll | C:\Windows\System32\OptionalFeatures.exe | — | Fondue.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Features Exit code: 3221226540 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3064 | "C:\Windows\sysnative\FonDUE.EXE" /enable-feature:NetFx3 /caller-name:mscoreei.dll | C:\Windows\System32\Fondue.exe | — | Fondue.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Features on Demand UX Exit code: 1058 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3280 | C:\Windows\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:6 | C:\Windows\System32\SrTasks.exe | — | TiWorker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | "C:\Windows\system32\OptionalFeatures.EXE" /enable-feature:NetFx3 /caller-name:mscoreei.dll | C:\Windows\System32\OptionalFeatures.exe | Fondue.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Features Exit code: 1058 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | C:\Windows\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.22000.795_none_047def894cac2b60\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.22000.795_none_047def894cac2b60\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.22000.795 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5880 | "C:\Windows\system32\fondue.exe" /enable-feature:NetFx3 /caller-name:mscoreei.dll | C:\Windows\SysWOW64\Fondue.exe | — | PDFConverty.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Features on Demand UX Exit code: 1058 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6092 | "C:\Users\admin\AppData\Local\Temp\PDFConverty.exe" | C:\Users\admin\AppData\Local\Temp\PDFConverty.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PDFConverty Exit code: 2148734720 Version: 1.0.6 Modules
| |||||||||||||||
Total events
8 994
Read events
8 628
Write events
362
Delete events
4
Modification events
| (PID) Process: | (5880) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5880) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5880) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5880) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5548) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide |
| Operation: | write | Name: | LastScavengingStarvationReport |
Value: F07F9ADD1AD4D801 | |||
| (PID) Process: | (5548) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 30991330 | |||
| (PID) Process: | (3064) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3064) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3064) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3064) Fondue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5548 | TiWorker.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 272 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\Critical_10.0.22000.795_17bc7d3aa660e6f994699253e8f2601fb4697e_00000000_b61660fc-557a-4c65-a56a-c2928deb3bd3\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5548 | TiWorker.exe | C:\Windows\servicing\Sessions\Sessions.xml | — | |
MD5:— | SHA256:— | |||
| 5548 | TiWorker.exe | C:\Windows\Servicing\Sessions\Sessions.back.xml | — | |
MD5:— | SHA256:— | |||
| 5548 | TiWorker.exe | C:\Windows\servicing\Sessions\31029405_834328401.back.xml | xml | |
MD5:8B9DEEDBA099B6905F43510C995A2F29 | SHA256:E711B3686E9F84912CD3636985F9B3076C50B250740B6ED46EFBCE4AB5EA45F9 | |||
| 5548 | TiWorker.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:ADCE2045B4CED74E37A27BF73066FA08 | SHA256:9177F25D2249B40426C63C5D7E89137951DDC382BBA43CB4E37A0B188DD900CD | |||
| 5548 | TiWorker.exe | C:\Windows\Servicing\Sessions\FODRetry.xml | xml | |
MD5:5A3B0ECE6D57EB4F132D104B6B57E84B | SHA256:9F0F46F3E3D82C59CBD3F3F40135852C2BCD0FE20C861D22B96F85902FFC81DF | |||
| 272 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER.a800703c-7d03-44d5-aa22-5a8daeb5364c.tmp.xml | xml | |
MD5:5135D29D28D67DA67BF72D36207E2EAA | SHA256:43A074117A6F1D5255598D46C0E757C1B4C8CD13F96C0F15D9776B8719E62485 | |||
| 5548 | TiWorker.exe | C:\Windows\Servicing\Sessions\FODRetry.back.xml | xml | |
MD5:5A3B0ECE6D57EB4F132D104B6B57E84B | SHA256:9F0F46F3E3D82C59CBD3F3F40135852C2BCD0FE20C861D22B96F85902FFC81DF | |||
| 272 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER.40c9ae0b-22d7-4451-9509-fa09d142194f.tmp.WERInternalMetadata.xml | xml | |
MD5:AC7E2C93C117E083CB7926233398203F | SHA256:28C9E30BC5312C1219BBB5DB4339A836340B47508B13B26168D5AC3B5D30A819 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
9
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6492 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
6492 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53d377990962ce98 | US | — | — | whitelisted |
1480 | svchost.exe | GET | 200 | 13.107.4.52:80 | http://www.msftconnecttest.com/connecttest.txt | US | text | 22 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6492 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | suspicious |
6492 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1480 | svchost.exe | 13.107.4.52:80 | www.msftconnecttest.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 2.19.229.151:443 | fs.microsoft.com | AKAMAI-AS | FR | suspicious |
6492 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.msftconnecttest.com |
| whitelisted |
time.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1480 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
Process | Message |
|---|---|
TiWorker.exe | Populating UpdatePolicy AllowList |
TiWorker.exe | SKU MDM licensing allow list string from SLAPI:
|
TiWorker.exe | AboveLock|Accounts|ActiveXControls|ADMXIngest|AllowMessageSync|AppHVSI|ApplicationDefaults|AllowAllTrustedApps|AllowAppStoreAutoUpdate|AllowAutomaticAppArchiving|AllowDeveloperUnlock|AllowGameDVR|AllowSharedUserAppData|ApplicationRestrictions|Audit|ConfigureChatIcon|LaunchAppAfterLogOn|MSIAllowUserControlOverInstall|MSIAlwaysInstallWithElevatedPrivileges|RestrictAppDataToSystemVolume|RestrictAppToSystemVolume|AppRuntime|AttachmentManager|Authentication|Autoplay|BitLocker|BITS|Bluetooth|Browser|Camera|Cellular|Connectivity|ControlPolicyConflict|CredentialProviders|CredentialsDelegation|CredentialsUI|Cryptography|DataProtection|DataUsage|Defender|DeliveryOptimization|Desktop|ConfigureSystemGuardLaunch|EnableVirtualizationBasedSecurity|DeviceHealthMonitoring|DeviceInstallation|DeviceLock|Display|DmaGuard|ErrorReporting|Eap|Education|EnterpriseCloudPrint|EventLogService|AllowClipboardHistory|AllowCopyPaste|AllowCortana|AllowDeviceDiscovery|AllowManualMDMUnenrollment|AllowSaveAsOfOfficeFiles|AllowScreenCapture|AllowSharingOfOfficeFiles|AllowSIMErrorDialogPromptWhenNoSIM|AllowSyncMySettings|AllowTailoredExperiencesWithDiagnosticData|AllowTaskSwitcher|AllowThirdPartySuggestionsInWindowsSpotlight|AllowVoiceRecording|DoNotShowFeedbackNotifications|DoNotSyncBrowserSettings|AllowFindMyDevice|ExploitGuard|Feeds|FileExplorer|Games|Handwriting|HumanPresence|InternetExplorer|Kerberos|KioskBrowser|Knobs|LanmanWorkstation|Licensing|LocalPoliciesSecurityOptions|LocalUsersAndGroups|Lockdown|Maps|MemoryDump|MSSecurityGuide|MSSLegacy|Multitasking|NetworkIsolation|NetworkListManager|NewsAndInterests|Notifications|OneDrive|Power|Printers|Privacy|RemoteAssistance|RemoteDesktopServices|RemoteDesktop|RemoteManagement|RemoteProcedureCall|RemoteShell|RestrictedGroups|Search|Security|Settings|SmartScreen|Speech|Start|Storage|System|SystemServices|TaskManager|TaskScheduler|TenantRestrictions|TextInput|TimeLanguageSettings|Troubleshooting|Update|UserRights|VirtualizationBasedTechnology|WiFi|WindowsLogon|WirelessDisplay|Location|WindowsAutopilot|WindowsConnectionManager|WindowsDefenderSecurityCenter|WindowsInkWorkspace|WindowsPowerShell|WindowsSandbox|WiredNetwork|ADMX_ |
TiWorker.exe | |
TiWorker.exe | All policies are allowed
|
TiWorker.exe | Populating UpdatePolicy AllowList |
TiWorker.exe | SKU MDM licensing allow list string from SLAPI:
|
TiWorker.exe | AboveLock|Accounts|ActiveXControls|ADMXIngest|AllowMessageSync|AppHVSI|ApplicationDefaults|AllowAllTrustedApps|AllowAppStoreAutoUpdate|AllowAutomaticAppArchiving|AllowDeveloperUnlock|AllowGameDVR|AllowSharedUserAppData|ApplicationRestrictions|Audit|ConfigureChatIcon|LaunchAppAfterLogOn|MSIAllowUserControlOverInstall|MSIAlwaysInstallWithElevatedPrivileges|RestrictAppDataToSystemVolume|RestrictAppToSystemVolume|AppRuntime|AttachmentManager|Authentication|Autoplay|BitLocker|BITS|Bluetooth|Browser|Camera|Cellular|Connectivity|ControlPolicyConflict|CredentialProviders|CredentialsDelegation|CredentialsUI|Cryptography|DataProtection|DataUsage|Defender|DeliveryOptimization|Desktop|ConfigureSystemGuardLaunch|EnableVirtualizationBasedSecurity|DeviceHealthMonitoring|DeviceInstallation|DeviceLock|Display|DmaGuard|ErrorReporting|Eap|Education|EnterpriseCloudPrint|EventLogService|AllowClipboardHistory|AllowCopyPaste|AllowCortana|AllowDeviceDiscovery|AllowManualMDMUnenrollment|AllowSaveAsOfOfficeFiles|AllowScreenCapture|AllowSharingOfOfficeFiles|AllowSIMErrorDialogPromptWhenNoSIM|AllowSyncMySettings|AllowTailoredExperiencesWithDiagnosticData|AllowTaskSwitcher|AllowThirdPartySuggestionsInWindowsSpotlight|AllowVoiceRecording|DoNotShowFeedbackNotifications|DoNotSyncBrowserSettings|AllowFindMyDevice|ExploitGuard|Feeds|FileExplorer|Games|Handwriting|HumanPresence|InternetExplorer|Kerberos|KioskBrowser|Knobs|LanmanWorkstation|Licensing|LocalPoliciesSecurityOptions|LocalUsersAndGroups|Lockdown|Maps|MemoryDump|MSSecurityGuide|MSSLegacy|Multitasking|NetworkIsolation|NetworkListManager|NewsAndInterests|Notifications|OneDrive|Power|Printers|Privacy|RemoteAssistance|RemoteDesktopServices|RemoteDesktop|RemoteManagement|RemoteProcedureCall|RemoteShell|RestrictedGroups|Search|Security|Settings|SmartScreen|Speech|Start|Storage|System|SystemServices|TaskManager|TaskScheduler|TenantRestrictions|TextInput|TimeLanguageSettings|Troubleshooting|Update|UserRights|VirtualizationBasedTechnology|WiFi|WindowsLogon|WirelessDisplay|Location|WindowsAutopilot|WindowsConnectionManager|WindowsDefenderSecurityCenter|WindowsInkWorkspace|WindowsPowerShell|WindowsSandbox|WiredNetwork|ADMX_ |
TiWorker.exe | |
TiWorker.exe | All policies are allowed
|