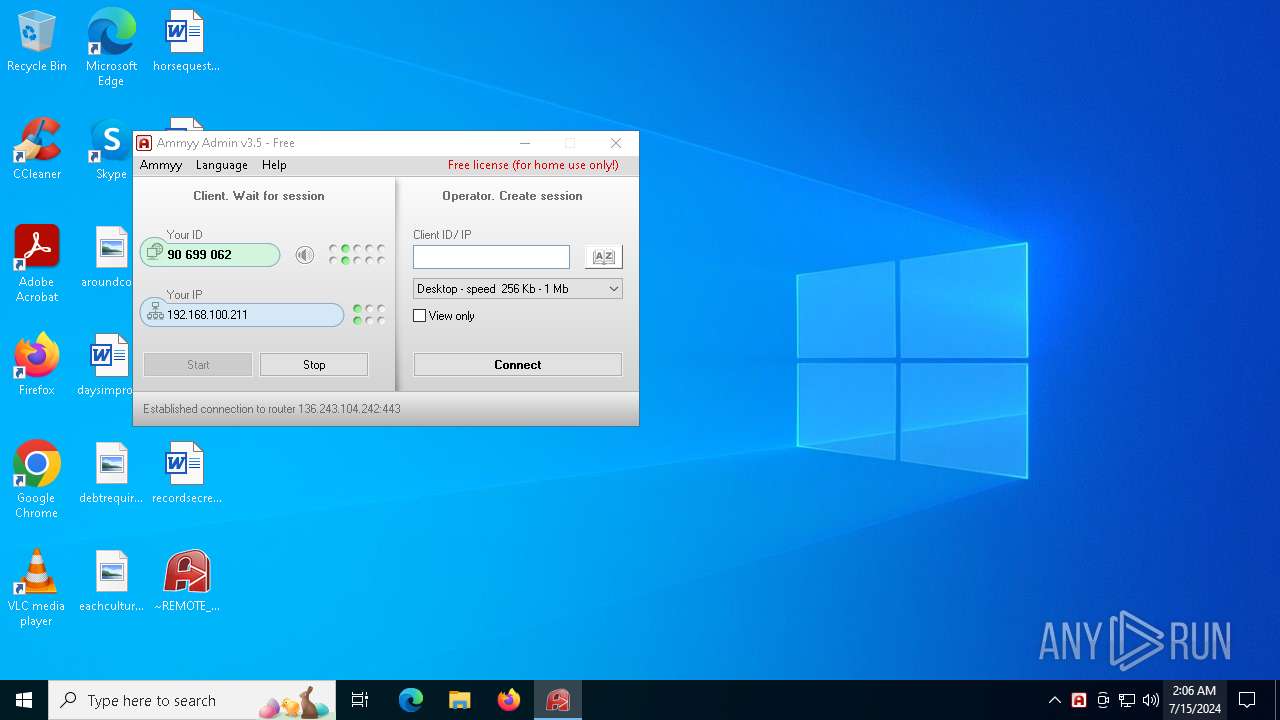
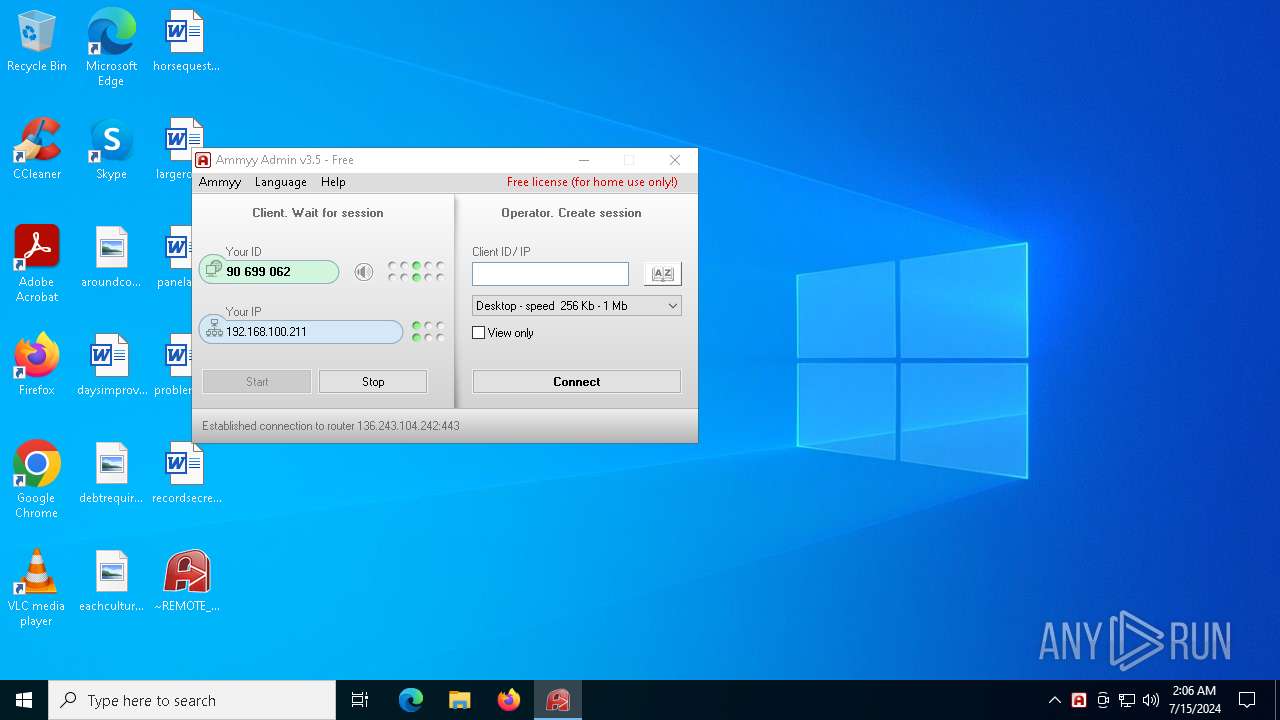
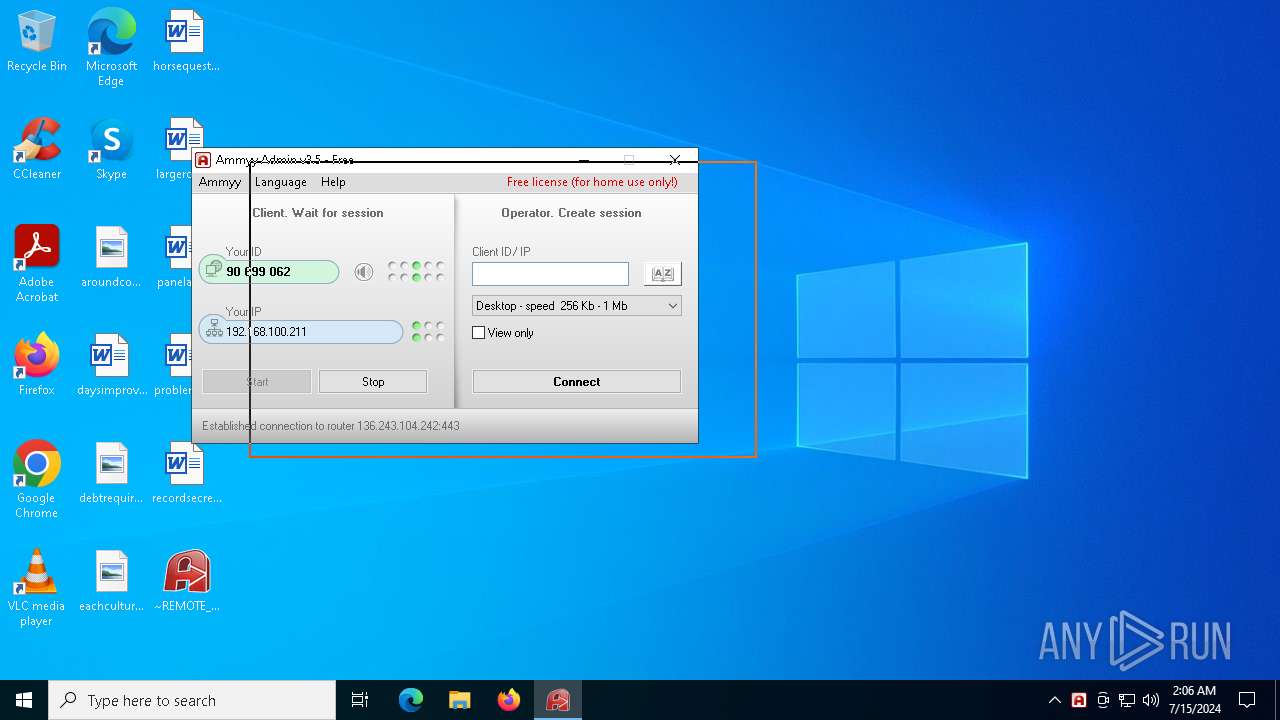
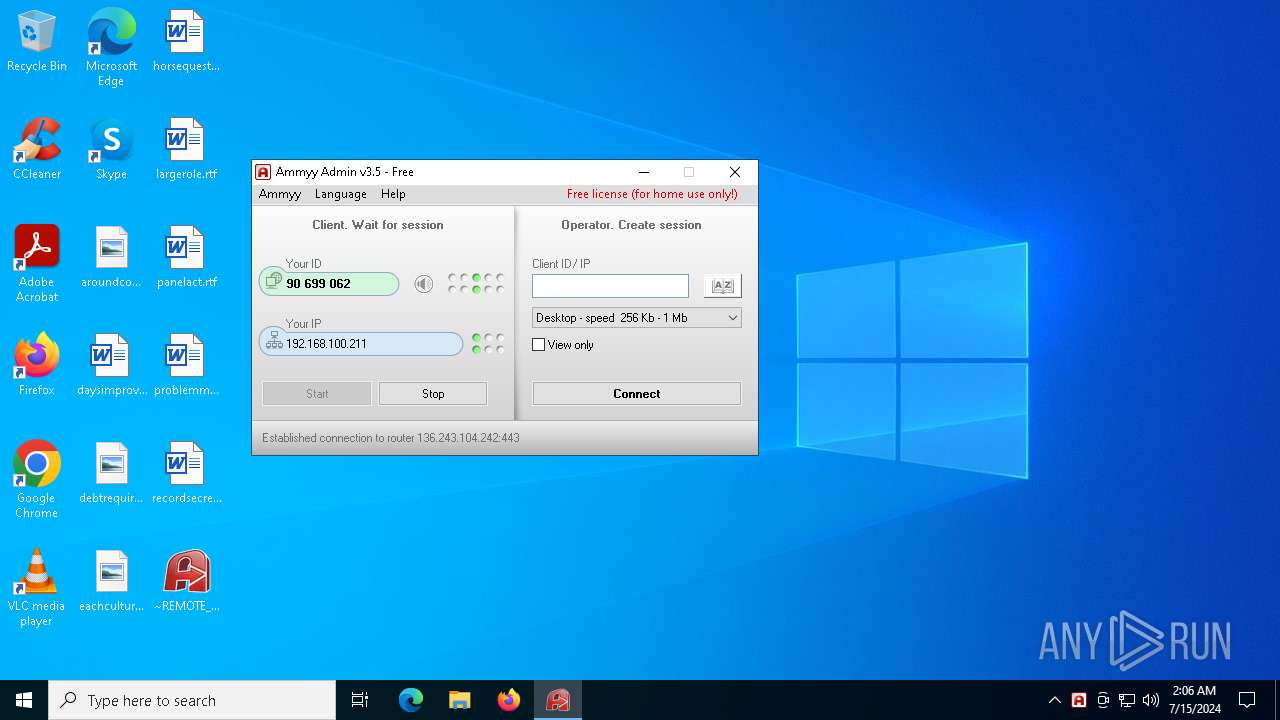
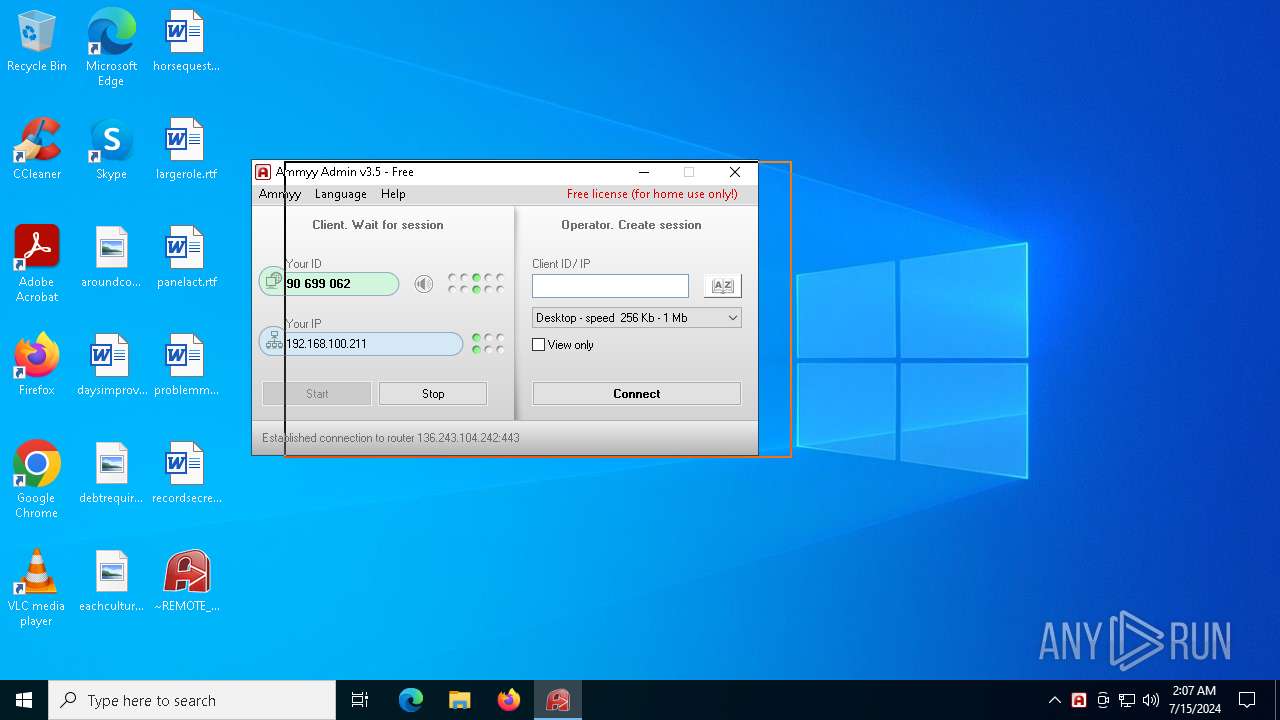
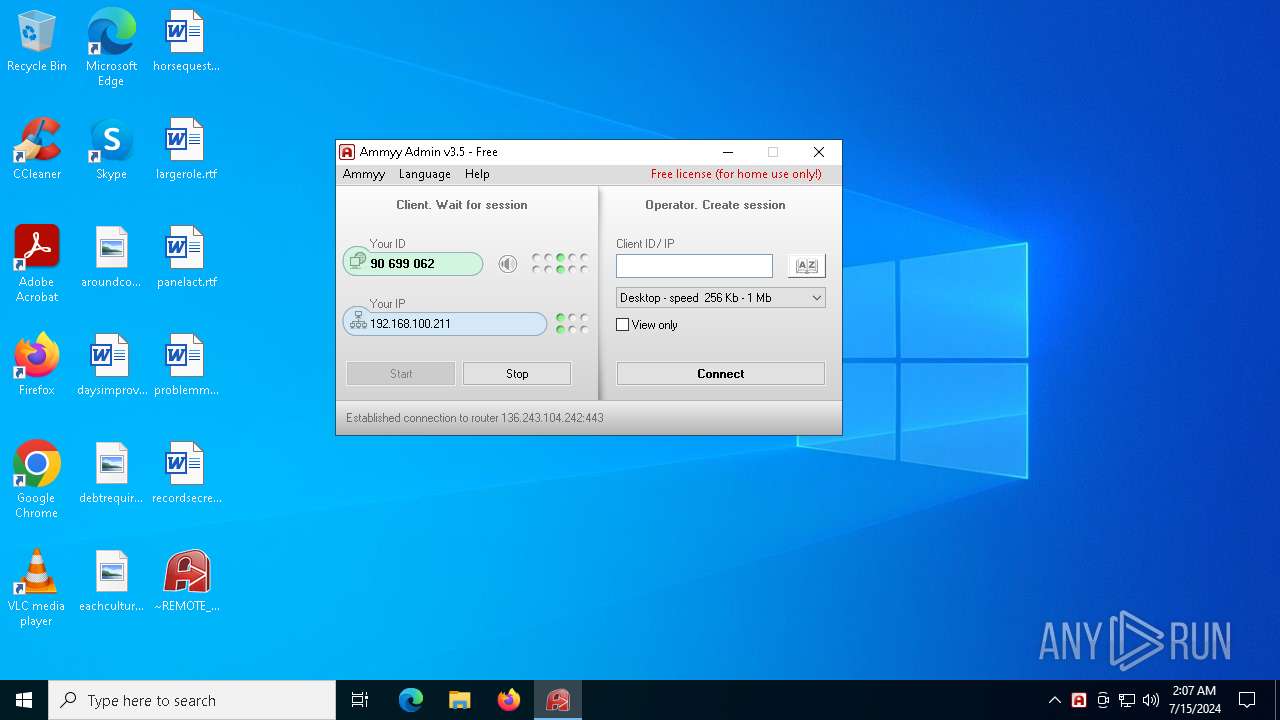
| File name: | ~REMOTE_3.5.exe |
| Full analysis: | https://app.any.run/tasks/3ff208ca-55cf-4478-b93d-46cc2bf6f8b1 |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2024, 02:06:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B10E8F0195D9B5023BBE1675851DFFBD |
| SHA1: | 50AE142BD045C55C12770BCD961556071B83FAE0 |
| SHA256: | DE807D6035C423B3C63A52504D644C07F6C30DA93FC14288A34D21DBEAFB5600 |
| SSDEEP: | 12288:2tsmP0QCzDXA8Mbw4UwhRg0RdxYgKYUF9IQlJJodqM:22q0lzTD4UwhRg0jxY5YeeQlJJodqM |
MALICIOUS
Drops the executable file immediately after the start
- ~REMOTE_3.5.exe (PID: 1660)
SUSPICIOUS
Reads security settings of Internet Explorer
- ~REMOTE_3.5.exe (PID: 1660)
Reads the date of Windows installation
- ~REMOTE_3.5.exe (PID: 1660)
INFO
Creates files in the program directory
- ~REMOTE_3.5.exe (PID: 1660)
Checks supported languages
- ~REMOTE_3.5.exe (PID: 1660)
Checks proxy server information
- ~REMOTE_3.5.exe (PID: 1660)
Reads the computer name
- ~REMOTE_3.5.exe (PID: 1660)
Process checks computer location settings
- ~REMOTE_3.5.exe (PID: 1660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:01:22 22:06:25+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 532480 |
| InitializedDataSize: | 253952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7c41e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.0 |
| ProductVersionNumber: | 3.5.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Ammyy LLC |
| FileDescription: | Ammyy Admin |
| FileVersion: | 3.5 |
| InternalName: | Ammyy Admin |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
| ProductName: | Ammyy Admin |
| ProductVersion: | 3.5 |
| SpecialBuild: | - |
Total processes
130
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1660 | "C:\Users\admin\Desktop\~REMOTE_3.5.exe" | C:\Users\admin\Desktop\~REMOTE_3.5.exe | — | explorer.exe | |||||||||||
User: admin Company: Ammyy LLC Integrity Level: MEDIUM Description: Ammyy Admin Version: 3.5 Modules
| |||||||||||||||
Total events
707
Read events
695
Write events
12
Delete events
0
Modification events
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Ammyy\Admin |
| Operation: | write | Name: | hr |
Value: 537D5673663152A063F122F7BB52 | |||
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ammyy\Admin |
| Operation: | write | Name: | hr |
Value: 537D5673663152A063F122F7BB52 | |||
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 7920E56F17972CC780C2D7EA03A04D3D66B20F148C74D7B96A7D6EFBA83FBBF9FAA12B2E443376378A7F76822E358DCE7B9D8F4137A9C9DA6A1F19 | |||
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 7920E56F17972CC780C2D7EA03A04D3D66B20F148C74D7B96A7D6EFBA83FBBF9FAA12B2E443376378A7F76822E358DCE7B9D8F4137A9C9DA6A1F19 | |||
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1660) ~REMOTE_3.5.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1660 | ~REMOTE_3.5.exe | C:\ProgramData\AMMYY\settings3.bin | binary | |
MD5:714F2508D4227F74B6ADACFEF73815D8 | SHA256:A5579945F23747541C0E80B79E79375D4CA44FEAFCD425EE9BD9302E35312480 | |||
| 1660 | ~REMOTE_3.5.exe | C:\ProgramData\AMMYY\hr | text | |
MD5:3C9CBFDEB0E9B250A679A6F738125BCA | SHA256:D8680086A9016C6F74E290A53D12ECFF9FD88CB33BFB76419C92185D0CB9CFC3 | |||
| 1660 | ~REMOTE_3.5.exe | C:\ProgramData\AMMYY\hr3 | binary | |
MD5:B9EA7592E6C1A3F0966CA83C38AECAEF | SHA256:6D45870AFAE5D6B25B98552FE1E5E3EFE89B950300D1E68E56D9A3195CD08430 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
65
DNS requests
17
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
444 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
444 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 188.42.129.148:80 | http://rl.ammyy.com/ | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6740 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6740 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4840 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
448 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3580 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
444 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
444 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 188.42.129.148:80 | rl.ammyy.com | SERVERS-COM | LU | unknown |
— | — | 136.243.104.242:443 | — | Hetzner Online GmbH | DE | unknown |
4656 | SearchApp.exe | 92.123.104.34:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
rl.ammyy.com |
| malicious |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
2 ETPRO signatures available at the full report