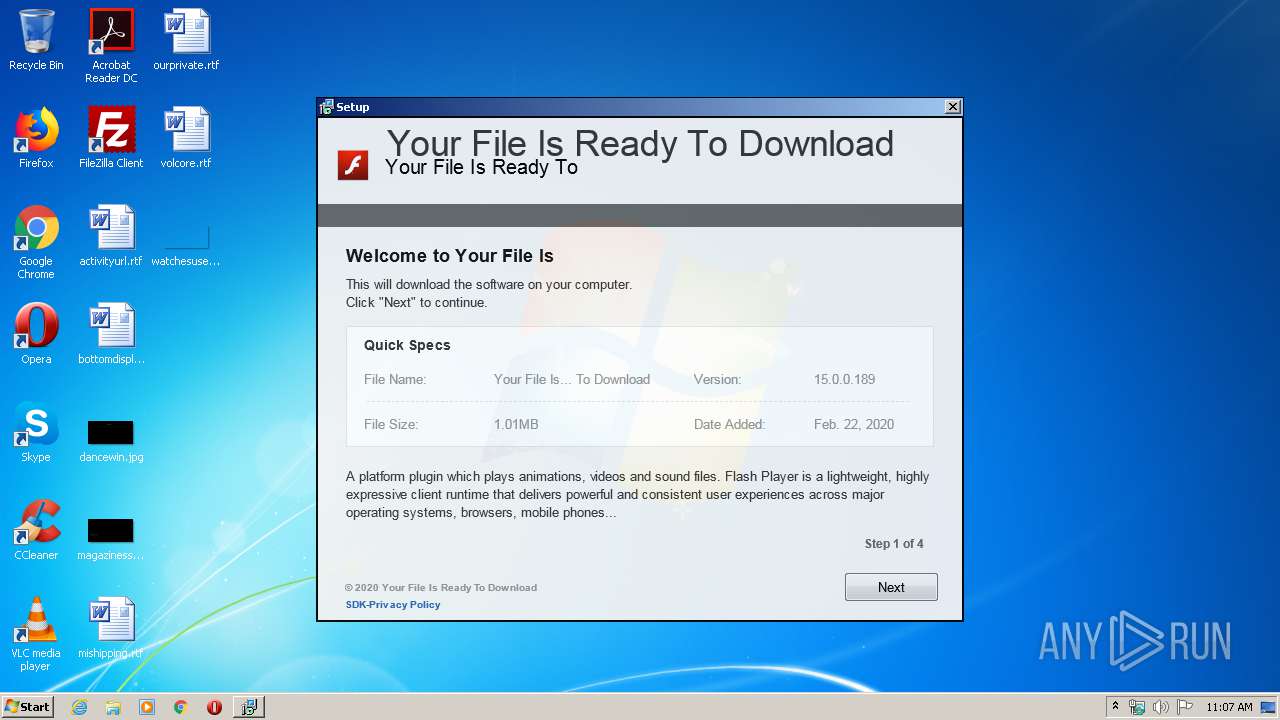
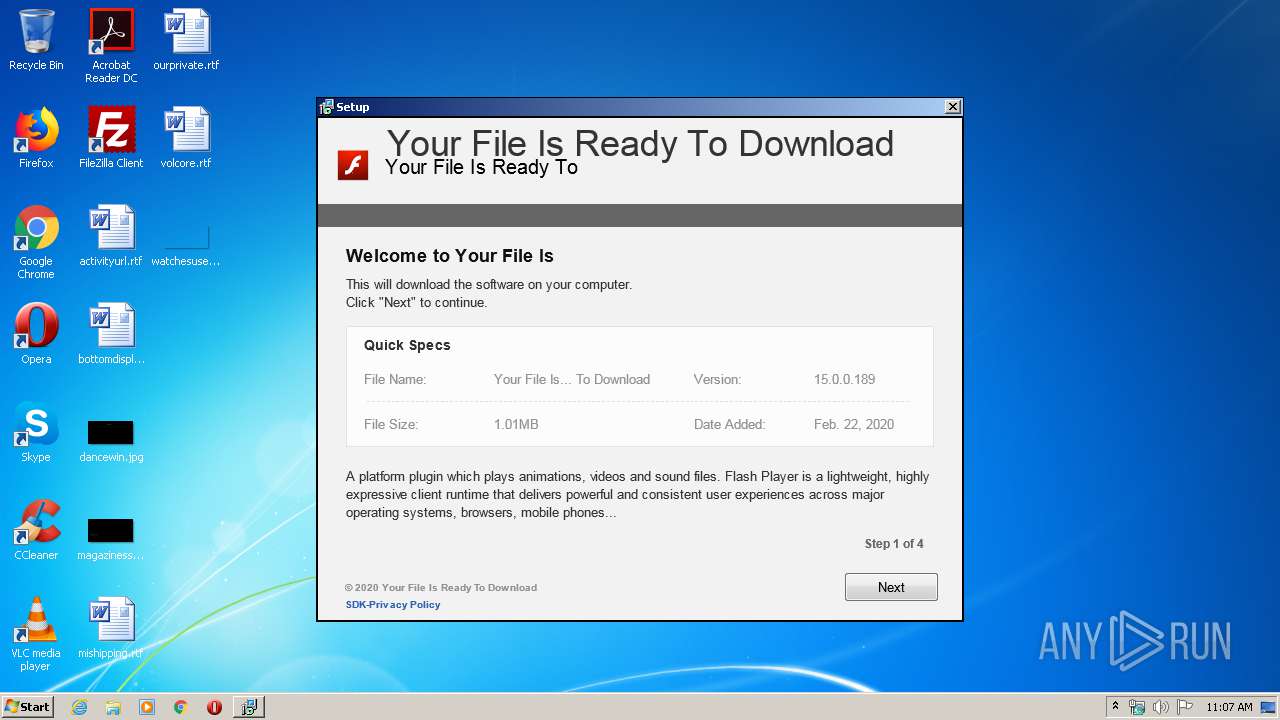
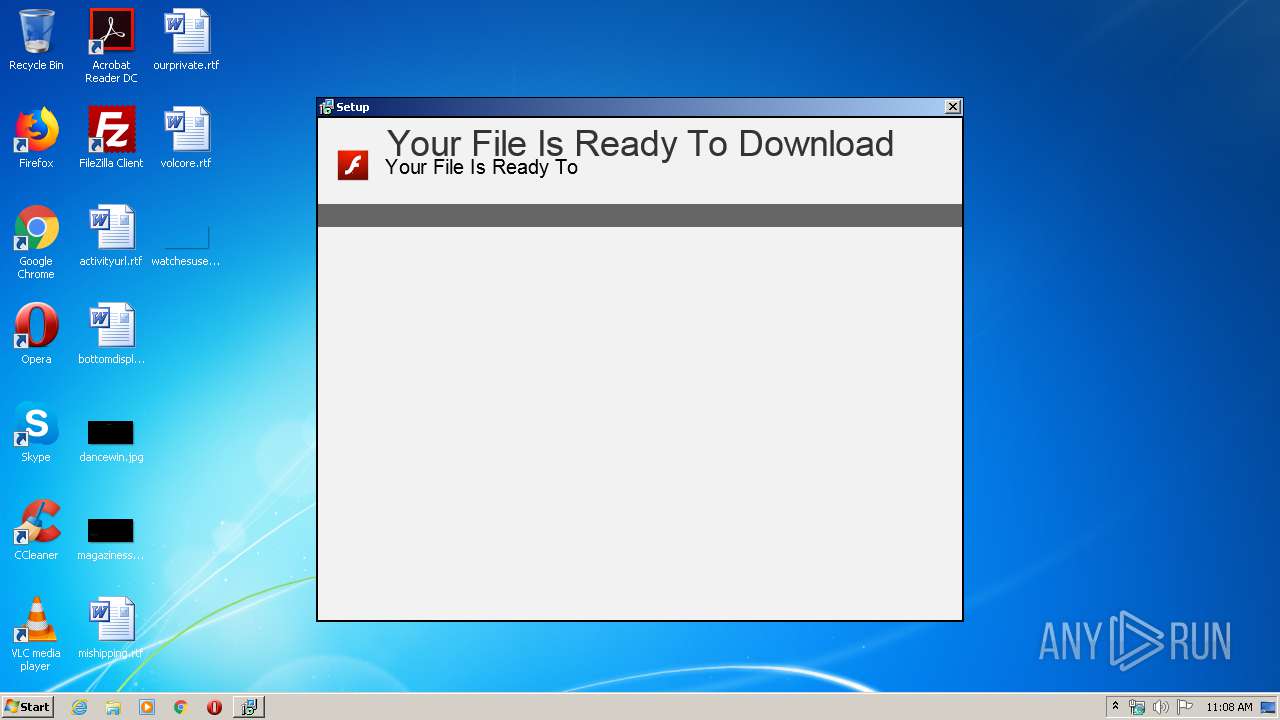
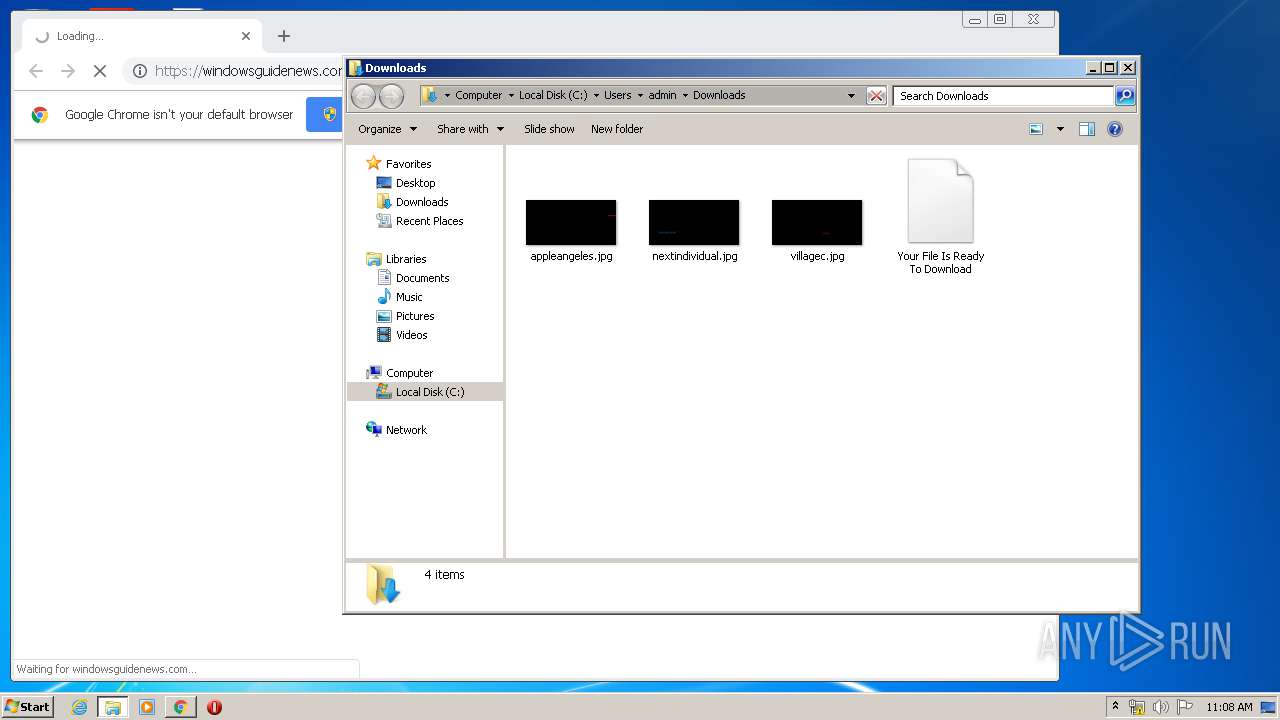
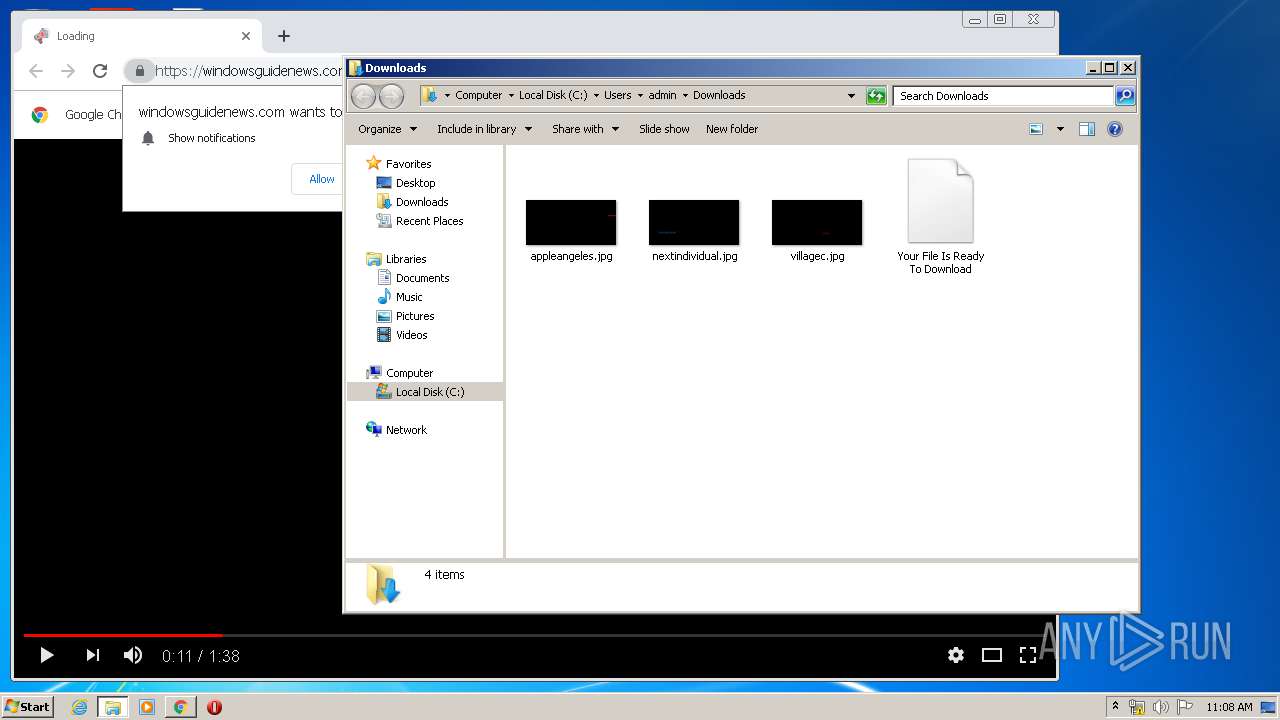
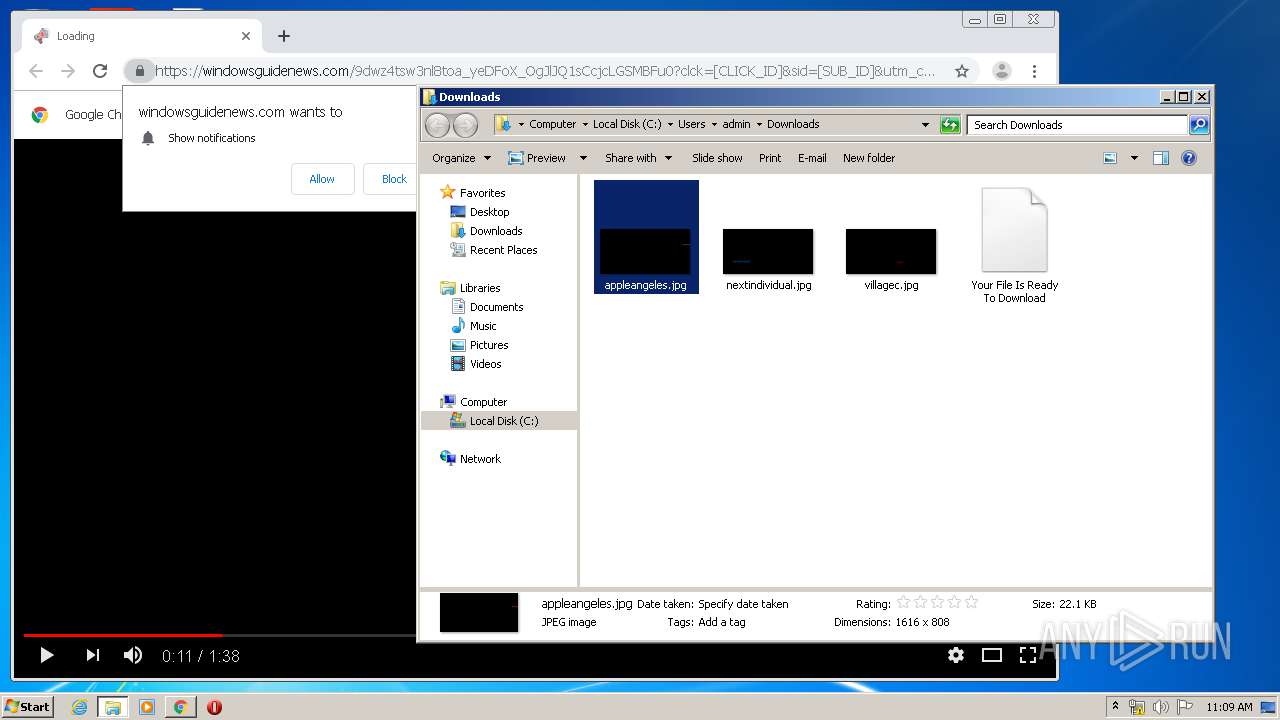
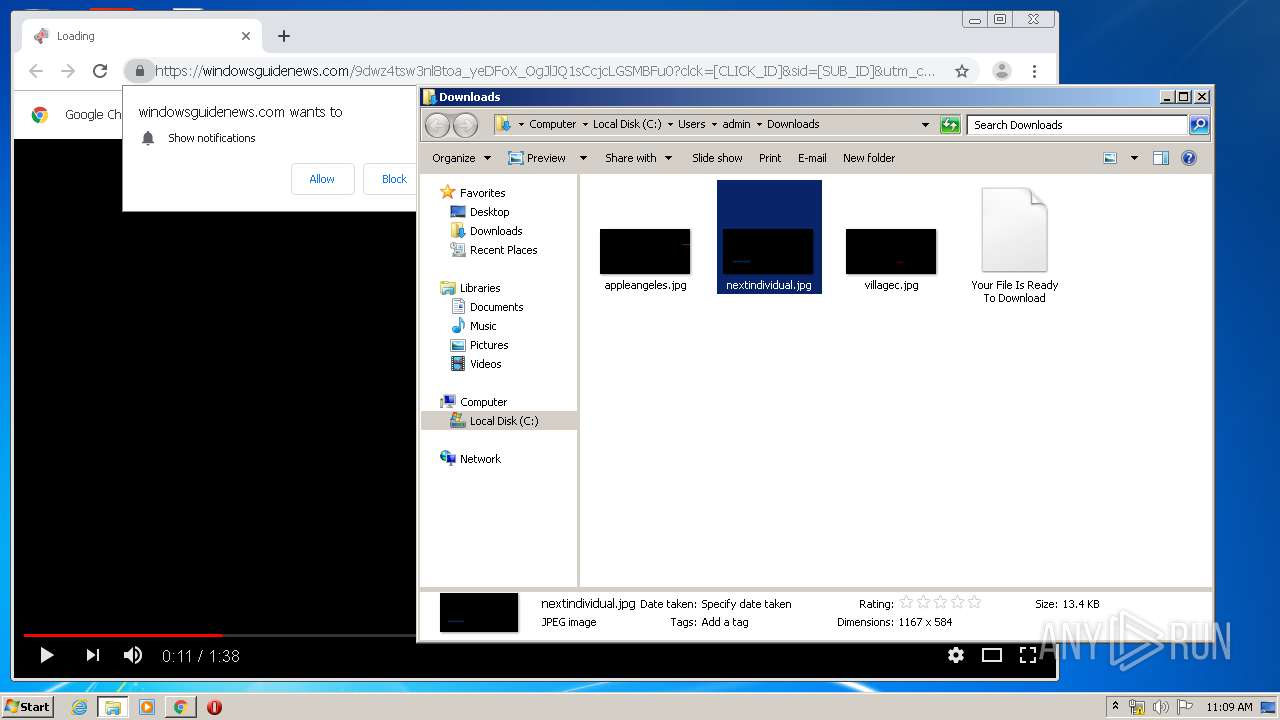
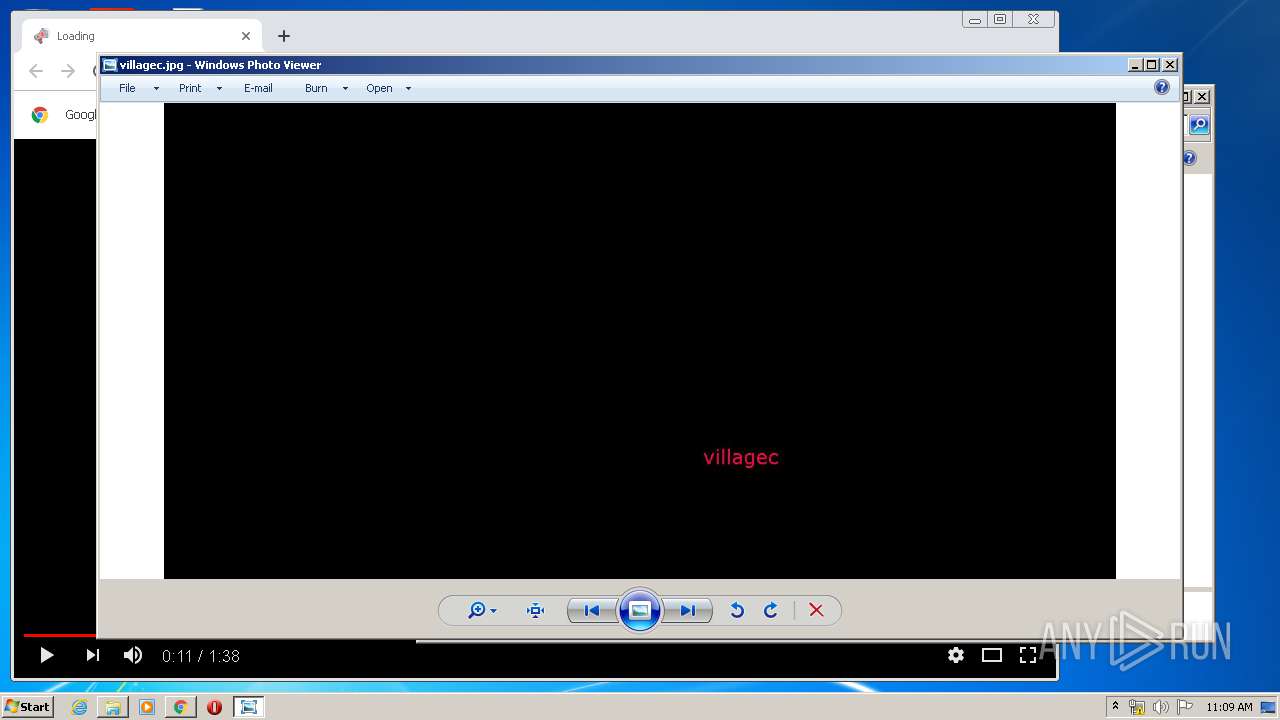
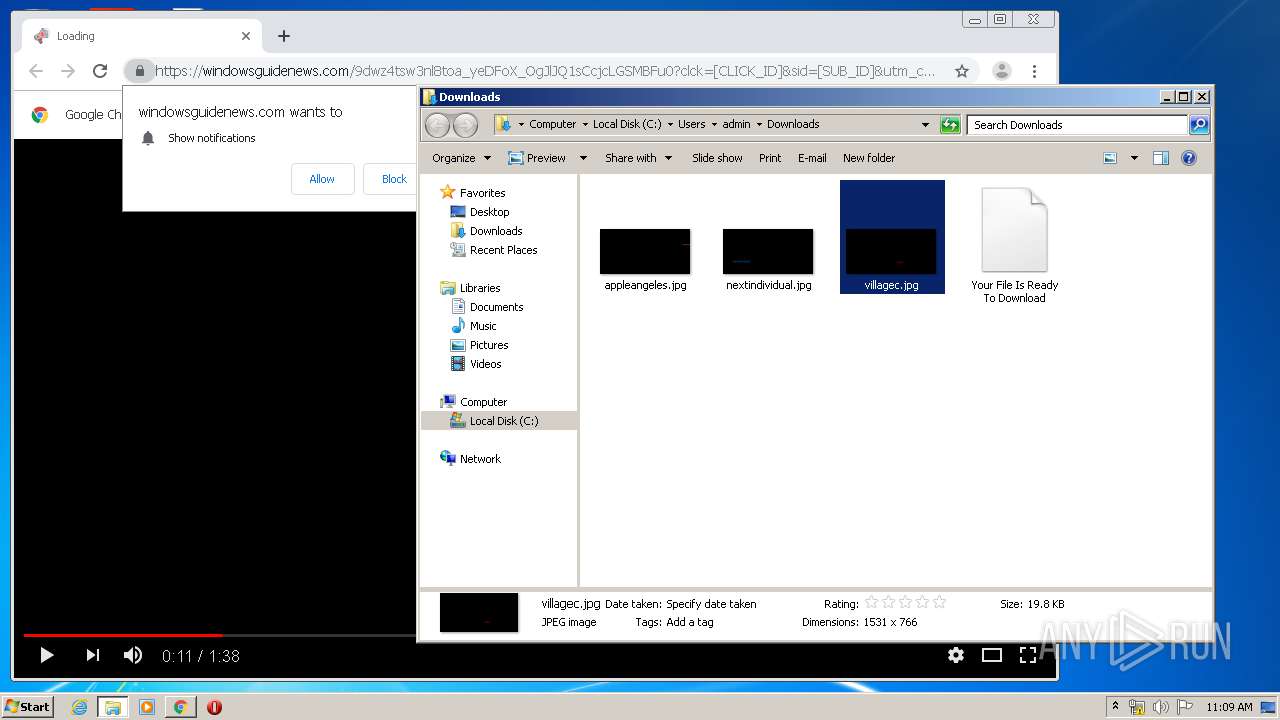
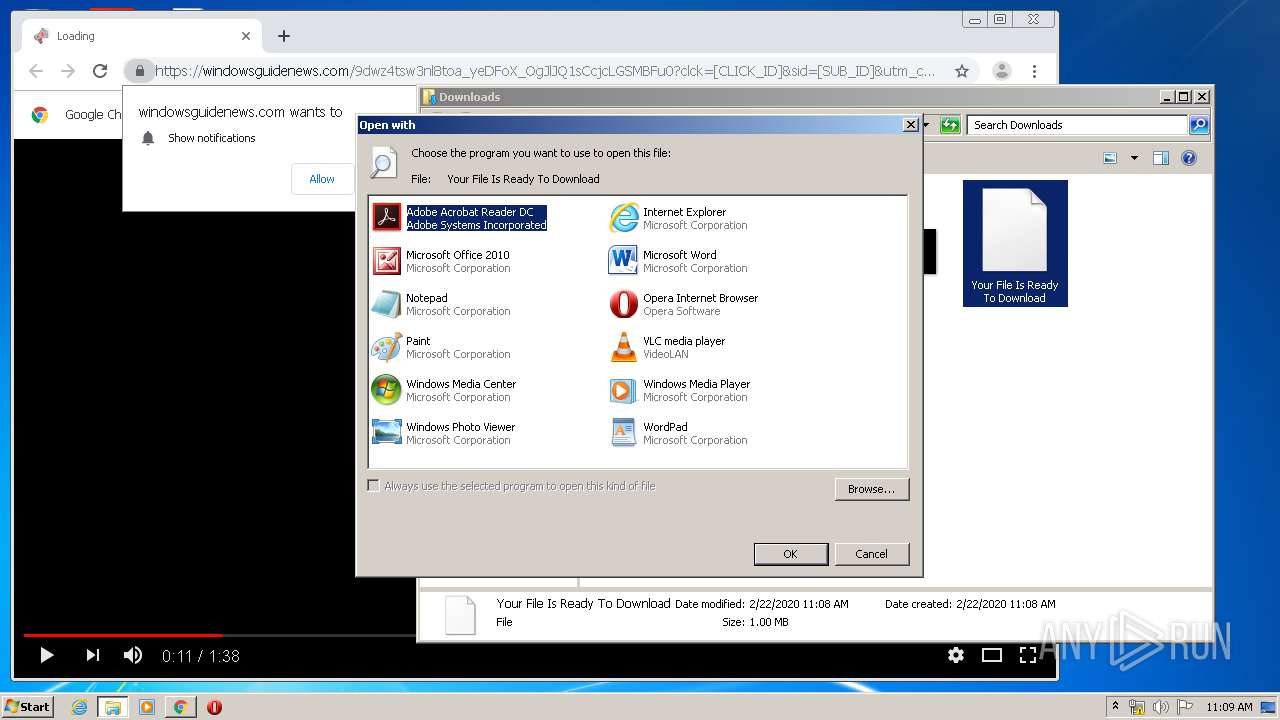
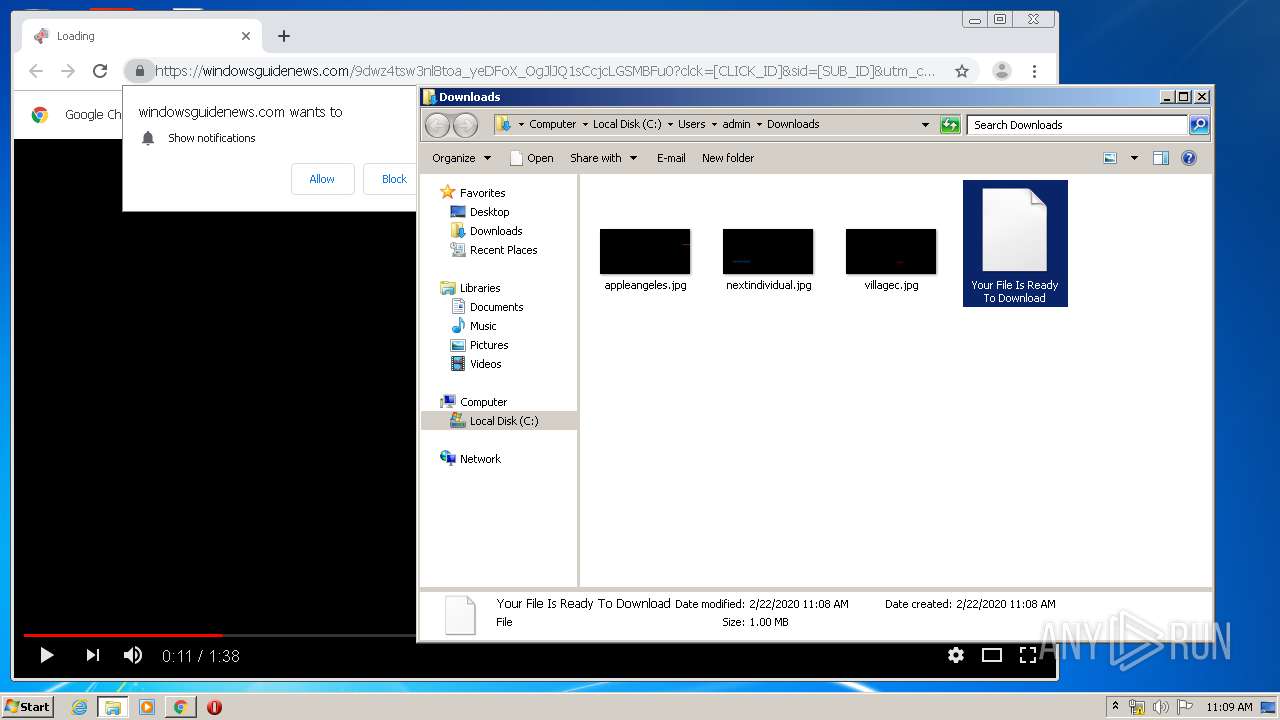
| File name: | Your File Is Ready To Download_3779881411.exe |
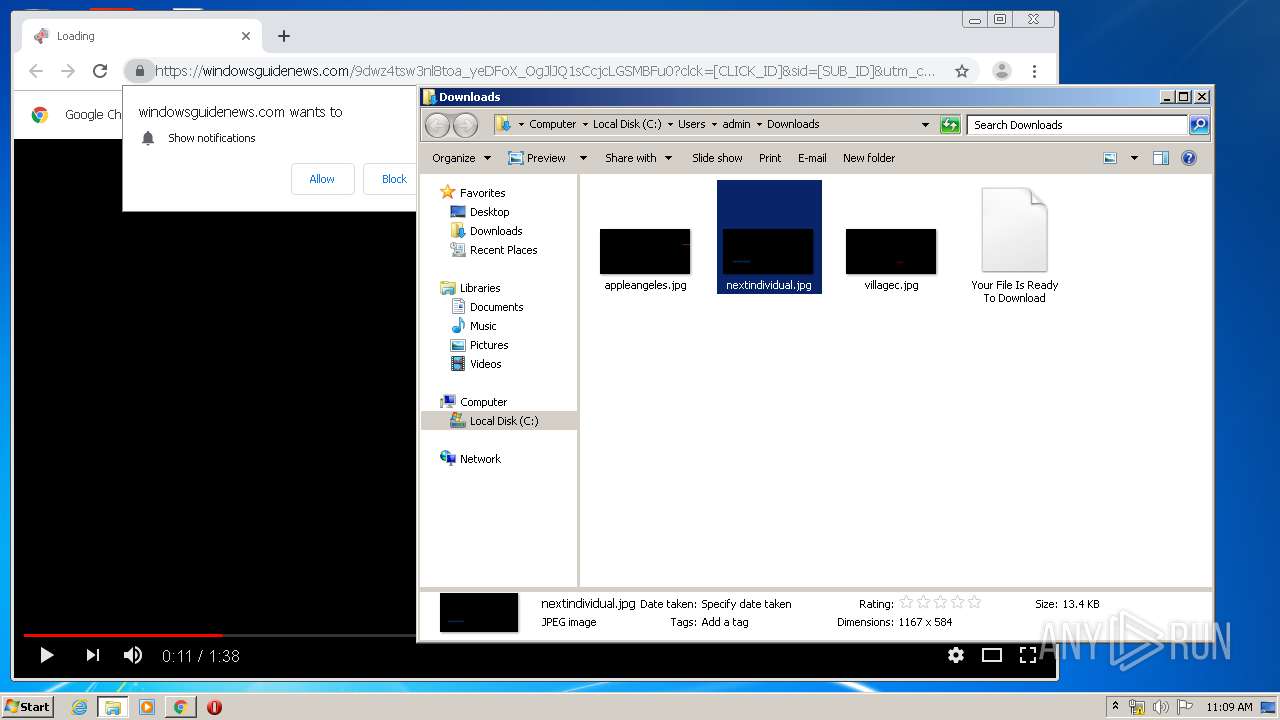
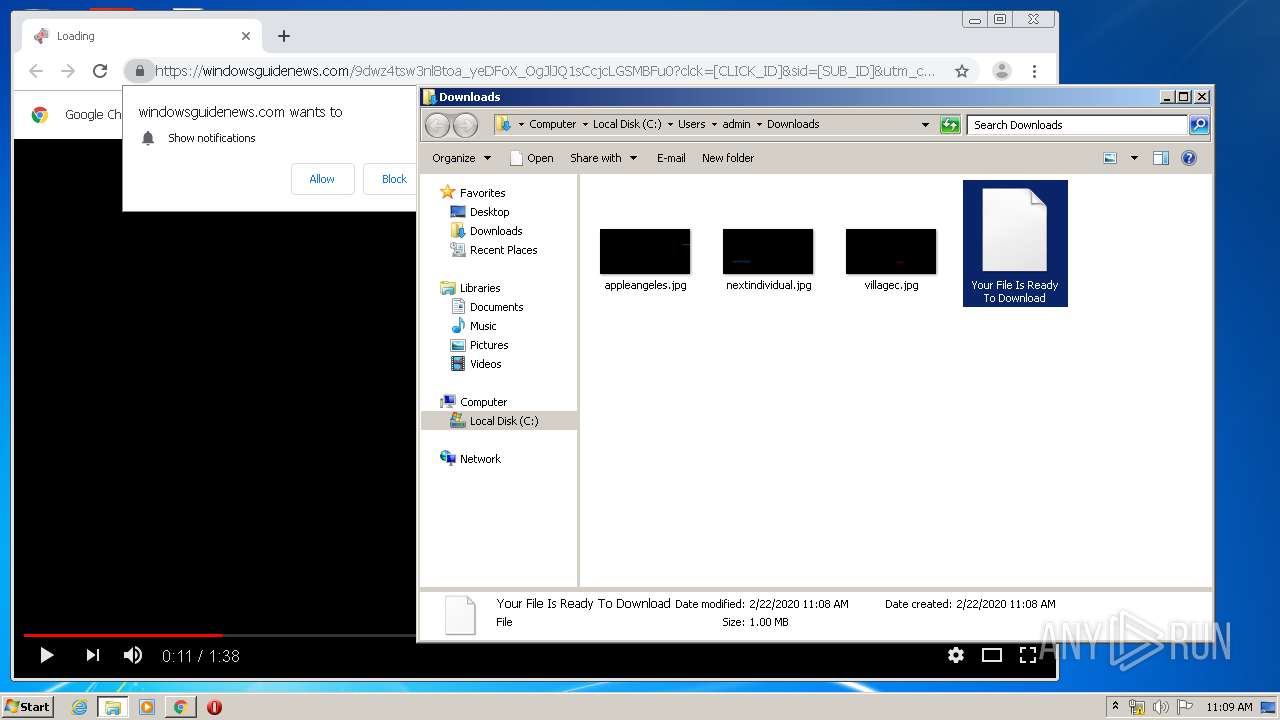
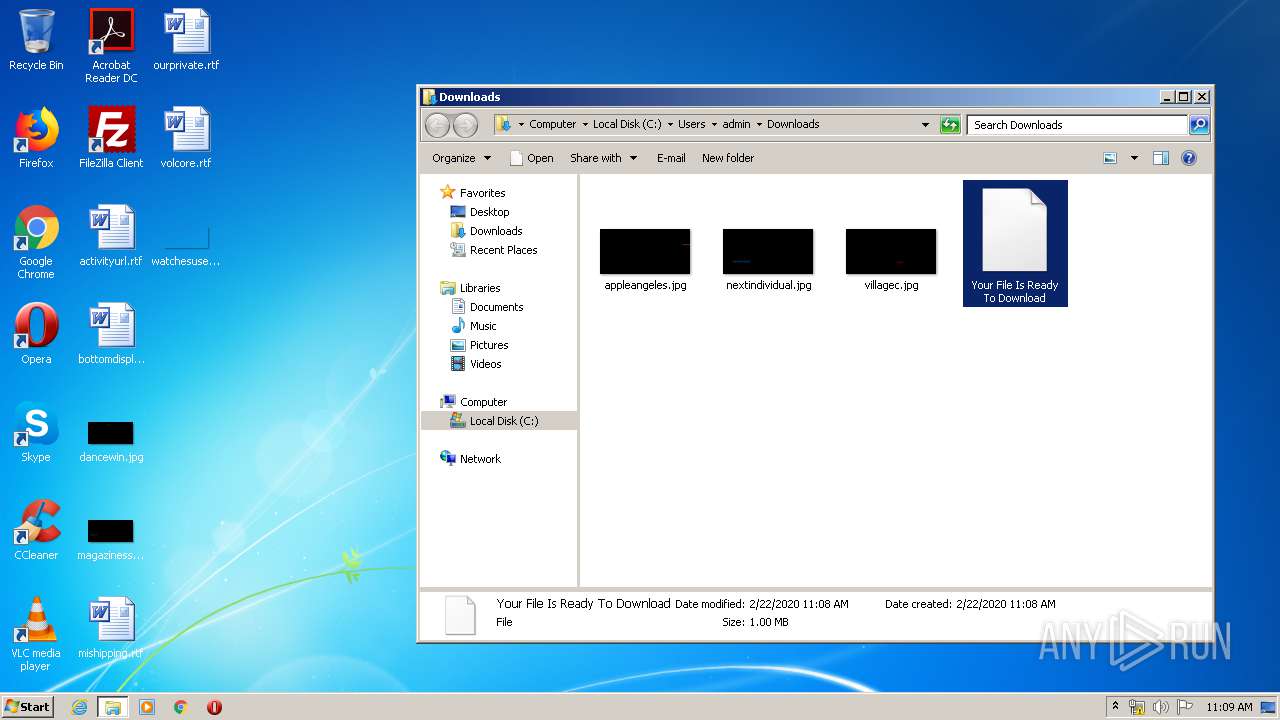
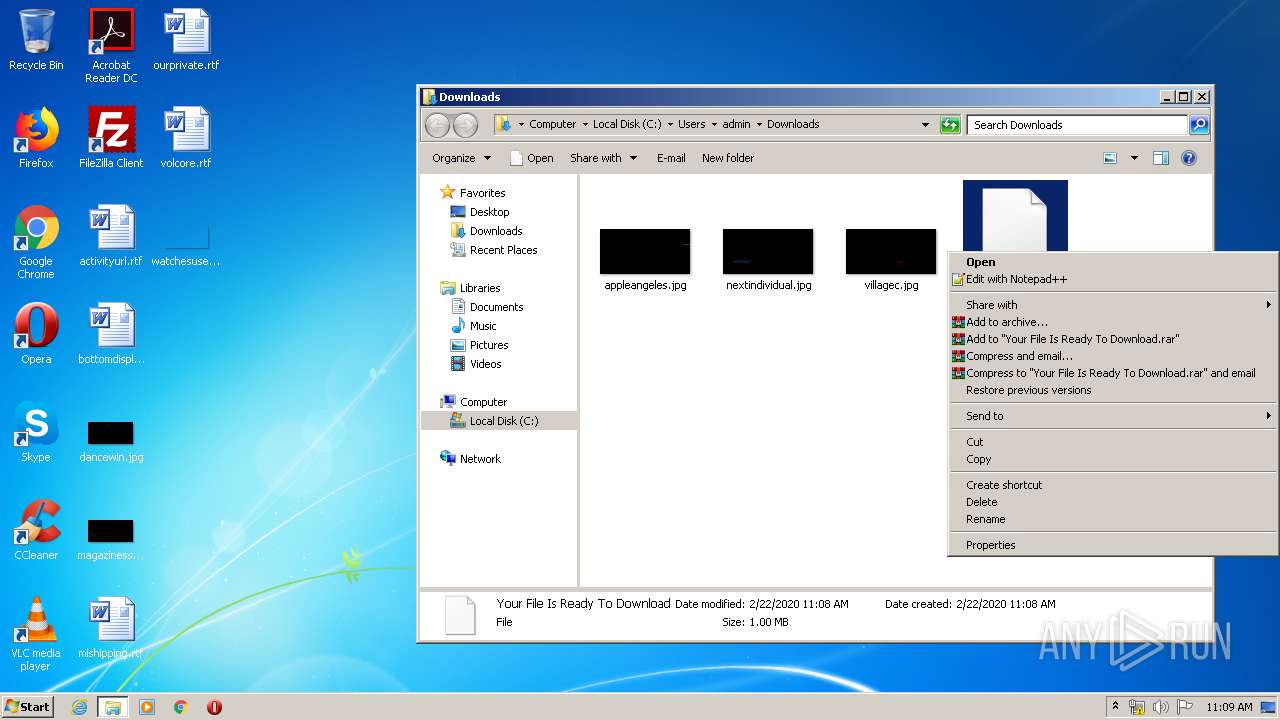
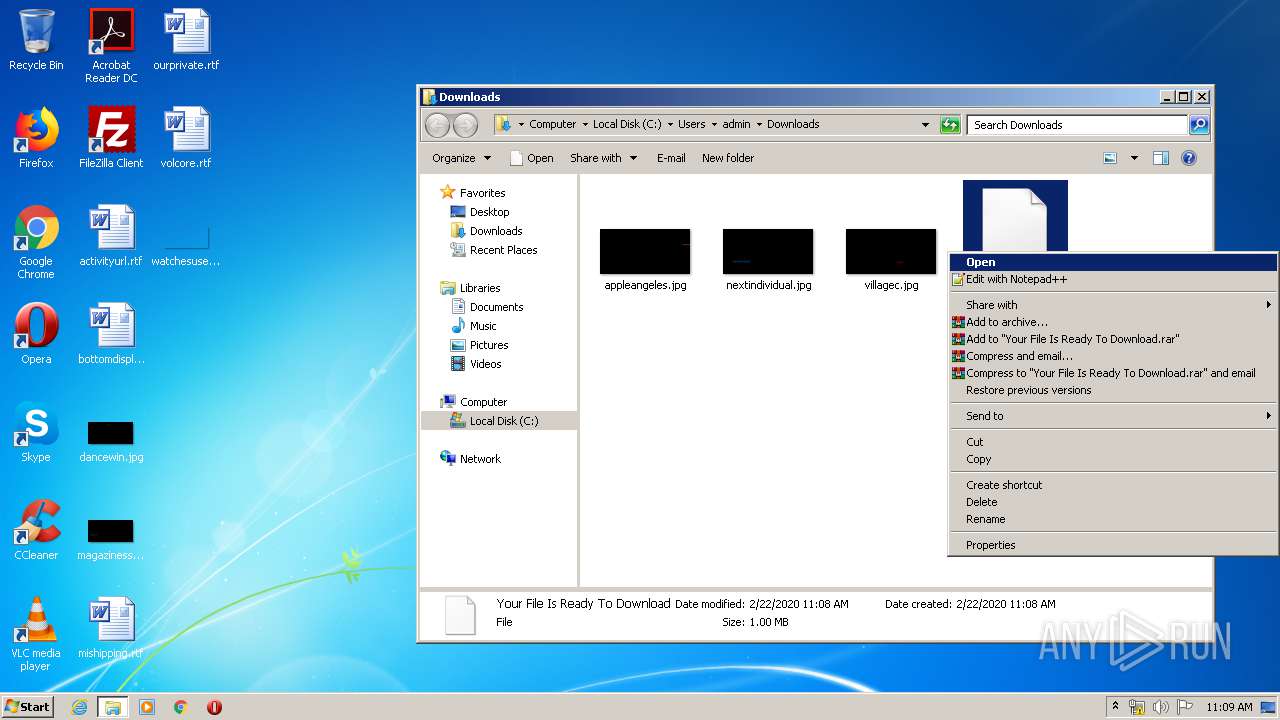
| Full analysis: | https://app.any.run/tasks/a7d512a0-f027-4a2d-b640-bb48fd48fb5f |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 11:07:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7FFE0E63D3FDA65A09BFBE453373A127 |
| SHA1: | 141DC2F30447209438ED15F09D2210AC177C0982 |
| SHA256: | DE7D8F518B9C1EE3D501FF239D641FF73939BF174167FBC3EAF4BB28764FD2DF |
| SSDEEP: | 49152:cxadEgwxYTBdsOwBV7qJuFkzHekL+TomBOAN3TCf8pgm3ccbkW/daE2+xEeAD:imwkgOwBV7Ne7ekSuANy8pHMc5daECr |
MALICIOUS
Loads dropped or rewritten executable
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
Changes settings of System certificates
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
SUSPICIOUS
Executable content was dropped or overwritten
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
Application launched itself
- Your File Is Ready To Download_3779881411.exe (PID: 4040)
- cmd.exe (PID: 2312)
Reads Environment values
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
Reads internet explorer settings
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
Executed via COM
- explorer.exe (PID: 2372)
- DllHost.exe (PID: 1688)
Starts CMD.EXE for self-deleting
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
Starts CMD.EXE for commands execution
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
- cmd.exe (PID: 2312)
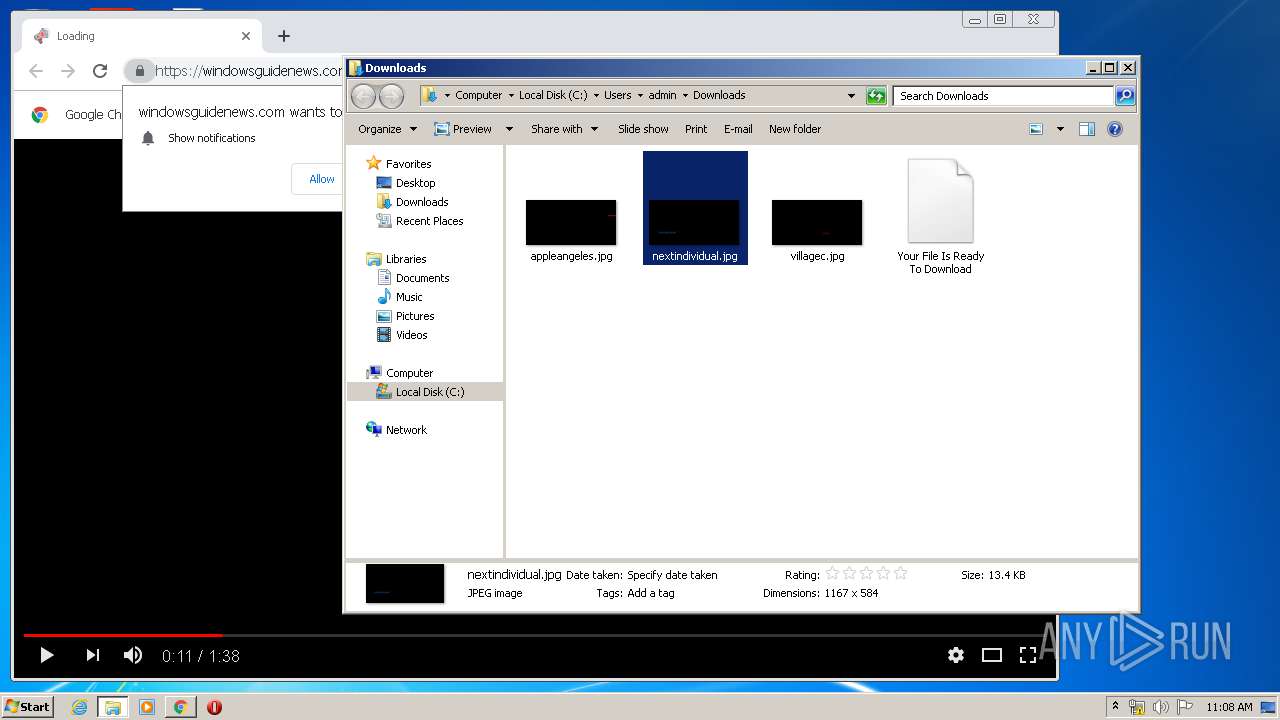
Modifies files in Chrome extension folder
- chrome.exe (PID: 2528)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 2372)
Adds / modifies Windows certificates
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
INFO
Reads the hosts file
- chrome.exe (PID: 1916)
- chrome.exe (PID: 2528)
Application launched itself
- chrome.exe (PID: 2528)
Changes settings of System certificates
- chrome.exe (PID: 1916)
Adds / modifies Windows certificates
- chrome.exe (PID: 1916)
Reads settings of System Certificates
- Your File Is Ready To Download_3779881411.exe (PID: 3312)
- chrome.exe (PID: 1916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.1.2 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Dahiteme Setup |
| FileVersion: | 2.3.1.2 |
| LegalCopyright: | Dop |
| ProductName: | Dahiteme |
| ProductVersion: | 1.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Dahiteme Setup |
| FileVersion: | 2.3.1.2 |
| LegalCopyright: | Dop |
| ProductName: | Dahiteme |
| ProductVersion: | 1.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64571 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75472 |
BSS | 0x0000C000 | 0x00000E90 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.58597 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
78
Monitored processes
34
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13299834994683147303 --mojo-platform-channel-handle=3560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8212951680397428123 --mojo-platform-channel-handle=4532 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2212897825849066095 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10920599921649696933 --mojo-platform-channel-handle=3640 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18155121565511363158 --mojo-platform-channel-handle=4140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6264321807809589990 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10341396775058717639 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16537523872040979316 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7080285128603719359,7496152257917027645,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10433823839292518249 --mojo-platform-channel-handle=3580 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 013
Read events
2 525
Write events
1 483
Delete events
5
Modification events
| (PID) Process: | (4040) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4040) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Your File Is Ready To Download_3779881411.exe | |||
| (PID) Process: | (3312) Your File Is Ready To Download_3779881411.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 708992537 | |||
Executable files
4
Suspicious files
46
Text files
331
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\00A679AD.log | — | |
MD5:— | SHA256:— | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\csshover3.htc | html | |
MD5:52FA0DA50BF4B27EE625C80D36C67941 | SHA256:E37E99DDFC73AC7BA774E23736B2EF429D9A0CB8C906453C75B14C029BDD5493 | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\form.bmp.Mask | binary | |
MD5:D2FC989F9C2043CD32332EC0FAD69C70 | SHA256:27DD029405CBFB0C3BF8BAC517BE5DB9AA83E981B1DC2BD5C5D6C549FA514101 | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\css\helpers\_align.scss | text | |
MD5:BBBBD243F9525ACC7DC6077010627409 | SHA256:1F11B5F53E0AA7DA1A1559A1A5CDD52BF03119EA74E5091462461C550E9288DB | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\css\_functions.scss | text | |
MD5:8F7259DE64F6DDF352BF461F44D34A81 | SHA256:80EDC9D67172BC830D68D33F4547735FB072CADF3EF25AAB37A10B50DB87A069 | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\css\main.css | text | |
MD5:B9FE0048E61ECC2ED850016AC6B52847 | SHA256:AEF6A01DA275B87AAE2A23E268DE53561D7728A9B152DE7D3F379D0E73E65A05 | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\css\main.scss | text | |
MD5:5FF4E5B6D700C7941F5C0A31E1690C09 | SHA256:D4745E8A6CB9451B6EA599DA869965643CBDD2AB267895DC2F3DADD1BFB612A8 | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\css\swAgent.css | text | |
MD5:2543E3AF757C7D7C8A26C7CF57795F60 | SHA256:C38892A06C8F50C6386ED794AF4F1EA3E1897AD5F0C7E19594D9EA7B20CFB3F1 | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\css\ie6_main.css | text | |
MD5:AD234E6A62580F62019C78B2A718DE00 | SHA256:C4F2684F16C8E4553CC29C604A2F505399039638A34E652A7A1ACDEB157A0861 | |||
| 3312 | Your File Is Ready To Download_3779881411.exe | C:\Users\admin\AppData\Local\Temp\inH109101255833\css\helpers\_border-radius.scss | text | |
MD5:6BDF3FD89410E39D33F8137E04AD4A16 | SHA256:2C6B98CB19C3E3A0E37472767C53DF213243AE92BC80EF9A7F5BAA17F7B6FA31 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3312 | Your File Is Ready To Download_3779881411.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
3312 | Your File Is Ready To Download_3779881411.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
1916 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
1916 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
1916 | chrome.exe | GET | 200 | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1582369316&mv=u&mvi=2&pl=24&shardbypass=yes | LV | crx | 862 Kb | whitelisted |
1916 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1582369316&mv=u&mvi=3&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3312 | Your File Is Ready To Download_3779881411.exe | 13.227.198.95:443 | stats.cawoshevu.com | — | US | unknown |
3312 | Your File Is Ready To Download_3779881411.exe | 13.227.209.184:443 | d3rgy9jxa1r1e2.cloudfront.net | — | US | unknown |
3312 | Your File Is Ready To Download_3779881411.exe | 13.227.198.15:443 | www1.cawoshevu.com | — | US | unknown |
3312 | Your File Is Ready To Download_3779881411.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
3312 | Your File Is Ready To Download_3779881411.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3312 | Your File Is Ready To Download_3779881411.exe | 13.227.198.34:443 | demo.cawoshevu.com | — | US | unknown |
— | — | 13.227.209.87:443 | d3rgy9jxa1r1e2.cloudfront.net | — | US | unknown |
3312 | Your File Is Ready To Download_3779881411.exe | 13.227.209.87:443 | d3rgy9jxa1r1e2.cloudfront.net | — | US | unknown |
1916 | chrome.exe | 3.225.159.248:443 | windowsguidenews.com | — | US | unknown |
1916 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stats.cawoshevu.com |
| shared |
www1.cawoshevu.com |
| whitelisted |
d3rgy9jxa1r1e2.cloudfront.net |
| whitelisted |
s.symcd.com |
| shared |
ocsp.digicert.com |
| whitelisted |
demo.cawoshevu.com |
| whitelisted |
windowsguidenews.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
feed.r-tb.com |
| suspicious |