| File name: | 61.brr |
| Full analysis: | https://app.any.run/tasks/5b7e868b-160d-4599-b7ee-78f722a6fc46 |
| Verdict: | Malicious activity |
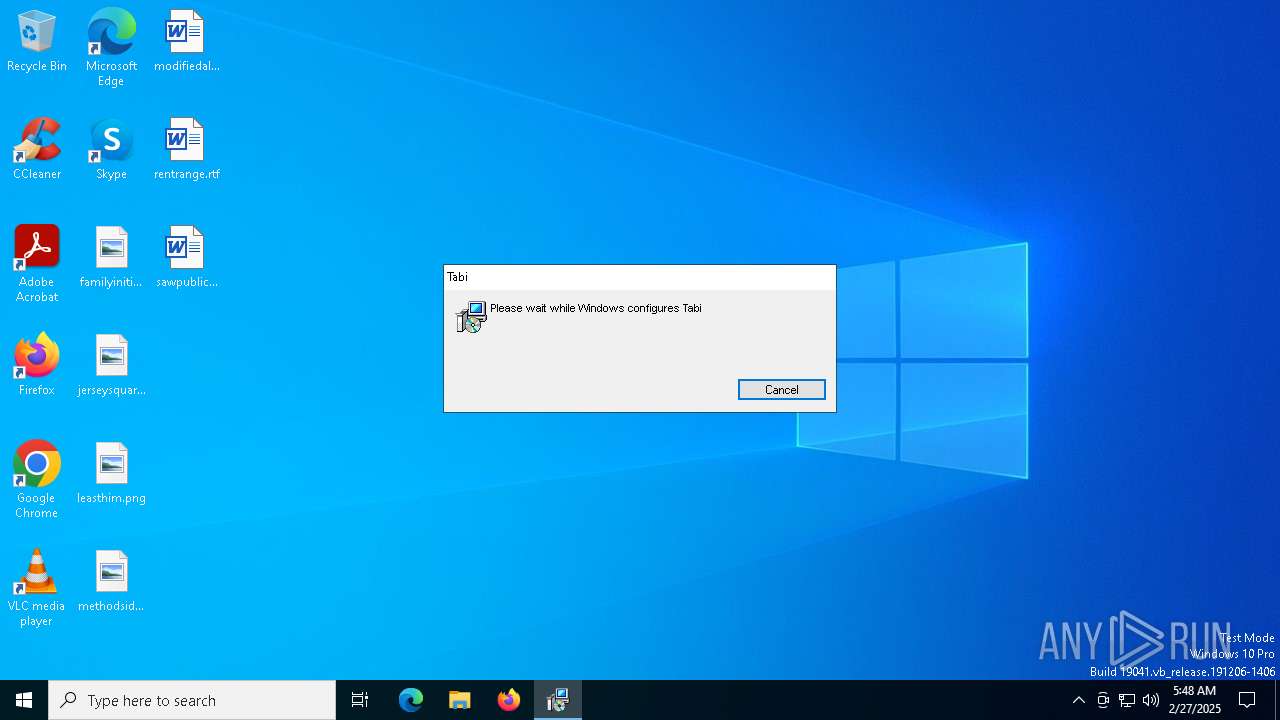
| Analysis date: | February 27, 2025, 05:48:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Tabi, Author: Aeciospore Protanopia, Keywords: Installer, Comments: This installer database contains the logic and data required to install Tabi., Template: Intel;1033, Revision Number: {5D9E2A4F-4DBD-4815-B218-E3F5EEF5932F}, Create Time/Date: Mon Feb 24 03:55:28 2025, Last Saved Time/Date: Mon Feb 24 03:55:28 2025, Number of Pages: 500, Number of Words: 10, Name of Creating Application: WiX Toolset (4.0.0.0), Security: 2 |
| MD5: | EDFA951162F885729864766075266751 |
| SHA1: | 1A351354321B69B4B970D61B906D196C36C1B730 |
| SHA256: | DE7734BAC9FCBE4355DD56B089487CFECEA762FA35E9C5B44E5047F6BAE96D3A |
| SSDEEP: | 98304:e7Pwr2DAqdmysudq1t8bWJ4r8V4dbCLG7GR6TaZnnkQYGtx2MGTIjcyHKtq2ByXN:enKkn0ijLanHOX224PEXoSO |
MALICIOUS
GENERIC has been found (auto)
- Ahnenblatt4.exe (PID: 7188)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1628)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5352)
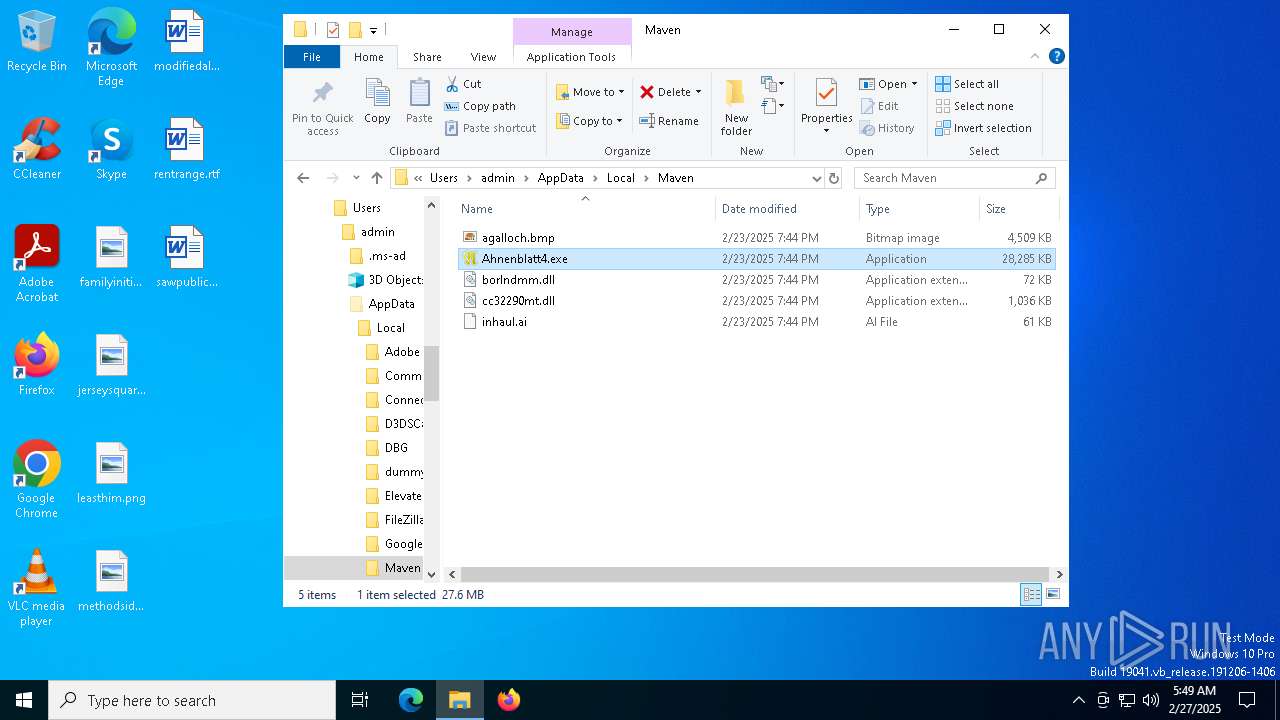
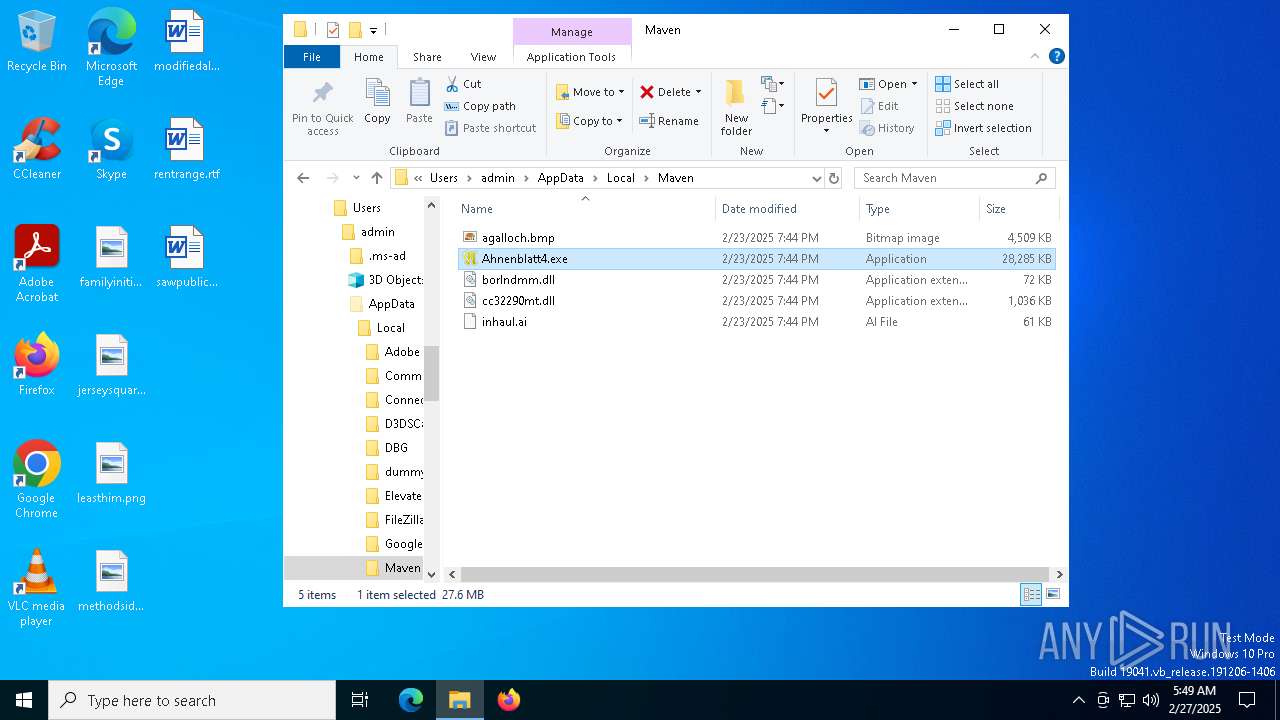
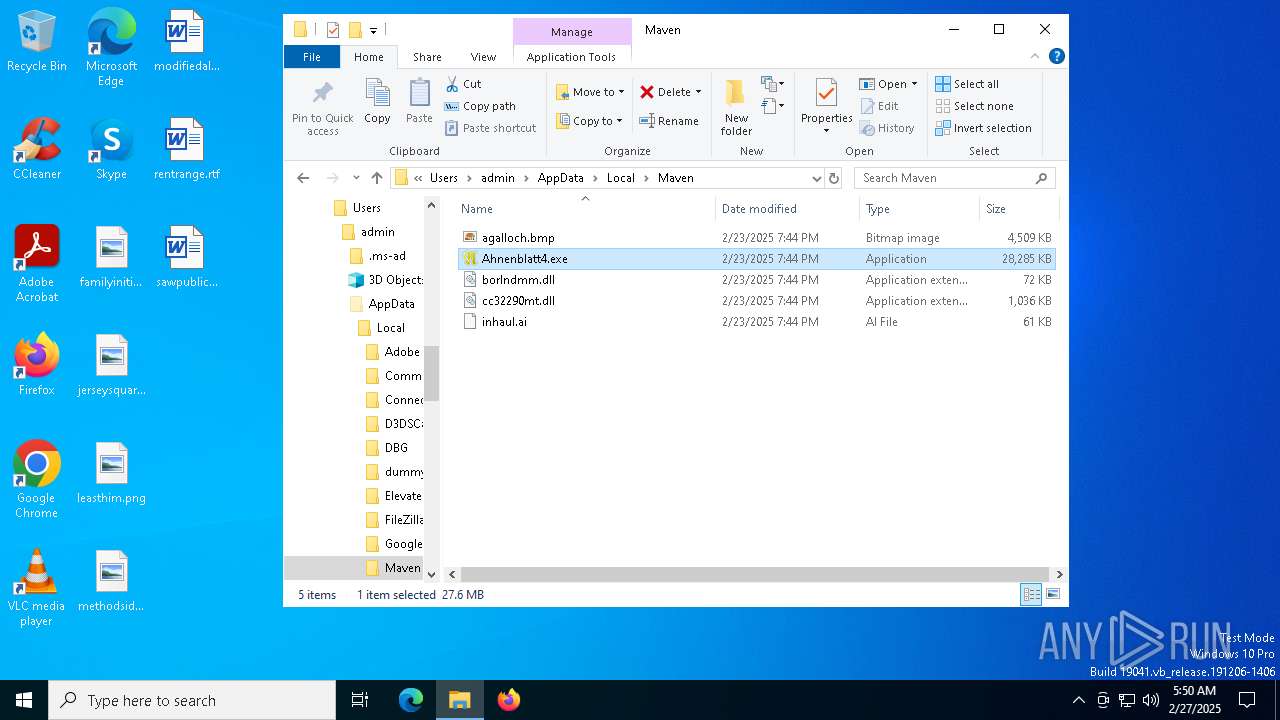
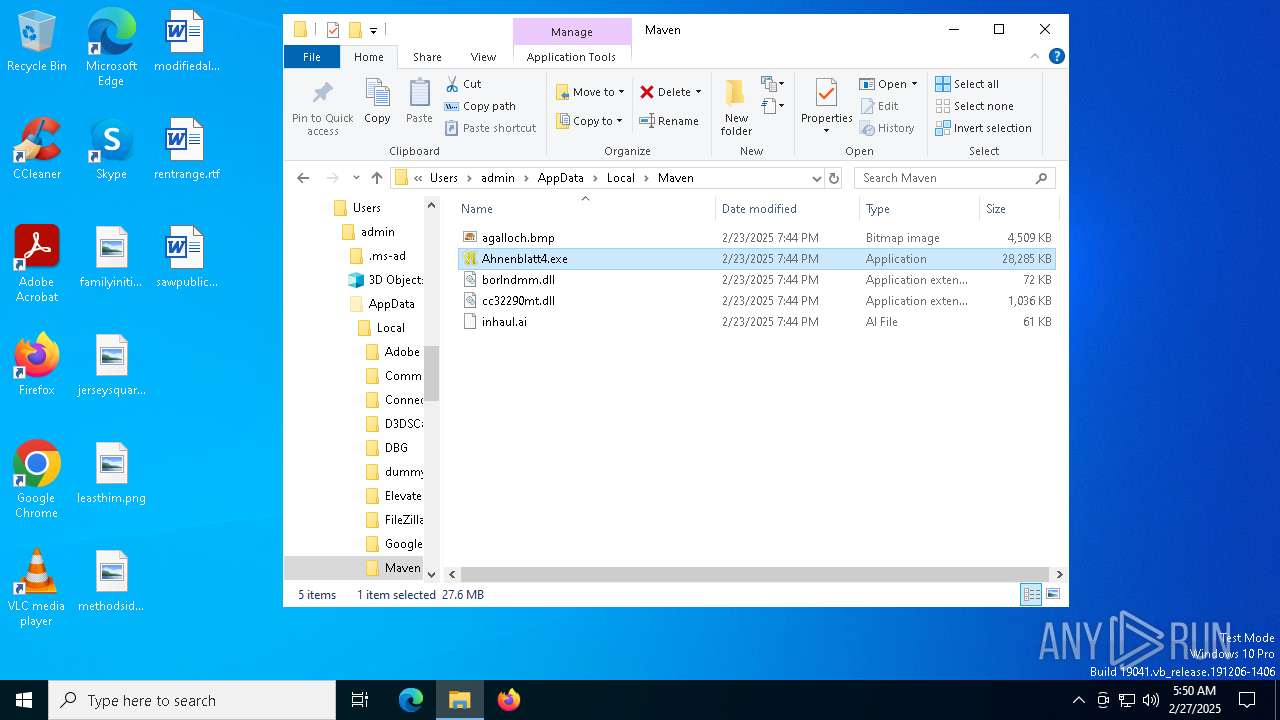
Executable content was dropped or overwritten
- Ahnenblatt4.exe (PID: 7188)
- cmd.exe (PID: 7288)
Starts itself from another location
- Ahnenblatt4.exe (PID: 7188)
- Ahnenblatt4.exe (PID: 7900)
- Ahnenblatt4.exe (PID: 7220)
- Ahnenblatt4.exe (PID: 8052)
Starts CMD.EXE for commands execution
- Ahnenblatt4.exe (PID: 7260)
- Ahnenblatt4.exe (PID: 7924)
- Ahnenblatt4.exe (PID: 4776)
- Ahnenblatt4.exe (PID: 8072)
The executable file from the user directory is run by the CMD process
- ToolBeacon_3.exe (PID: 7664)
- ToolBeacon_3.exe (PID: 8156)
- ToolBeacon_3.exe (PID: 4728)
- ToolBeacon_3.exe (PID: 7224)
Reads the date of Windows installation
- ToolBeacon_3.exe (PID: 7664)
- ToolBeacon_3.exe (PID: 8156)
- ToolBeacon_3.exe (PID: 7224)
- ToolBeacon_3.exe (PID: 4728)
INFO
Executable content was dropped or overwritten
- msiexec.exe (PID: 5352)
Checks supported languages
- msiexec.exe (PID: 5352)
- Ahnenblatt4.exe (PID: 7188)
- Ahnenblatt4.exe (PID: 7260)
- ToolBeacon_3.exe (PID: 7664)
- Ahnenblatt4.exe (PID: 7900)
- Ahnenblatt4.exe (PID: 7924)
- Ahnenblatt4.exe (PID: 4776)
- Ahnenblatt4.exe (PID: 7220)
- Ahnenblatt4.exe (PID: 8052)
- Ahnenblatt4.exe (PID: 8072)
- ToolBeacon_3.exe (PID: 8156)
- ToolBeacon_3.exe (PID: 7224)
- ToolBeacon_3.exe (PID: 4728)
Manages system restore points
- SrTasks.exe (PID: 3676)
The sample compiled with english language support
- msiexec.exe (PID: 4428)
- msiexec.exe (PID: 5352)
- Ahnenblatt4.exe (PID: 7188)
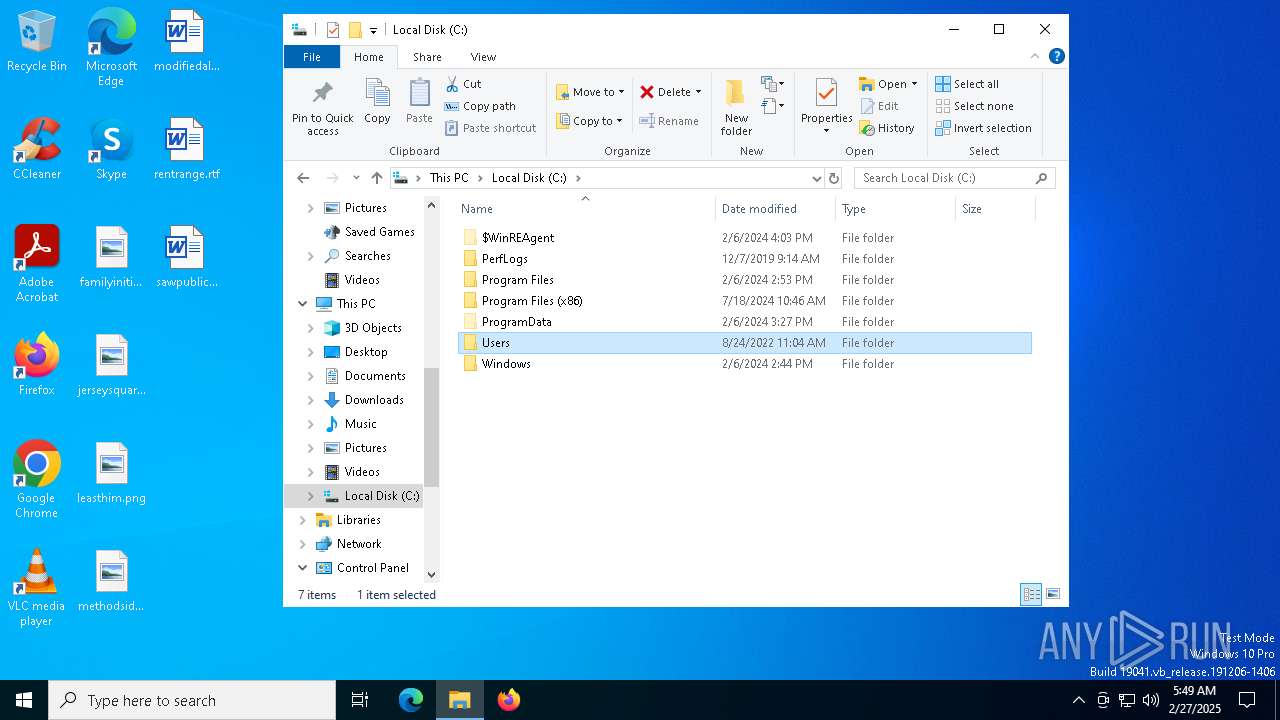
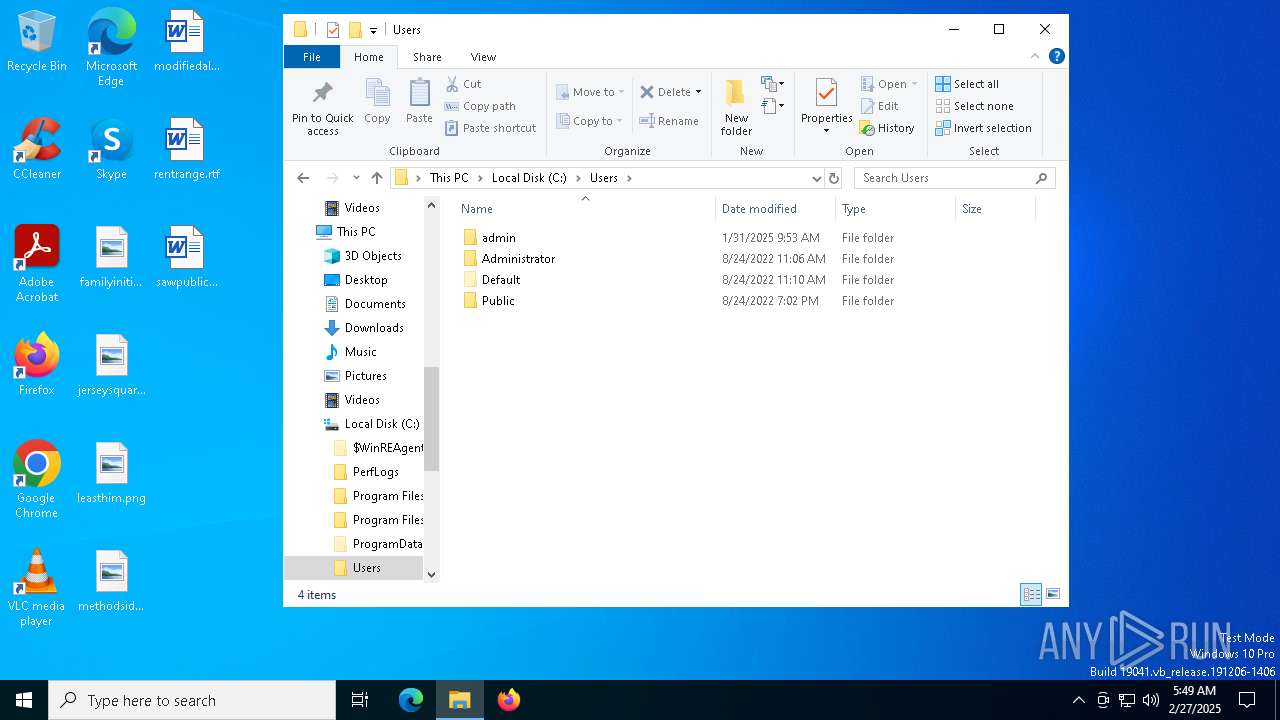
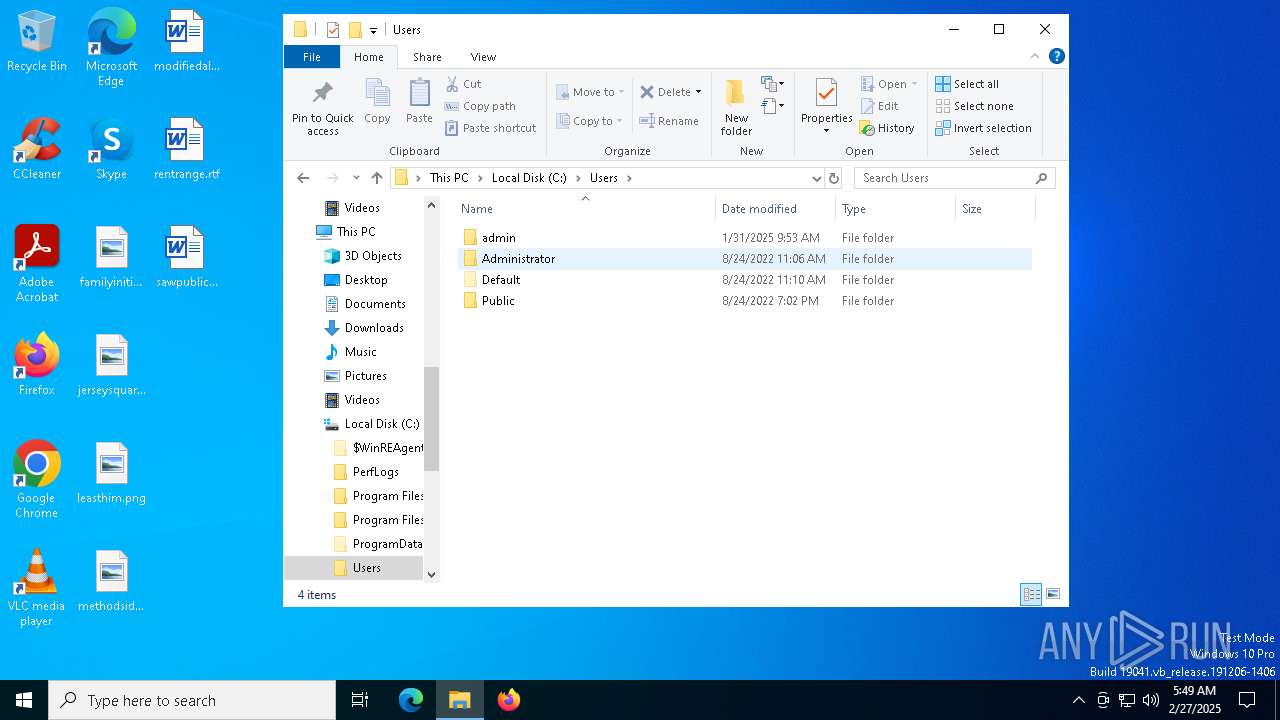
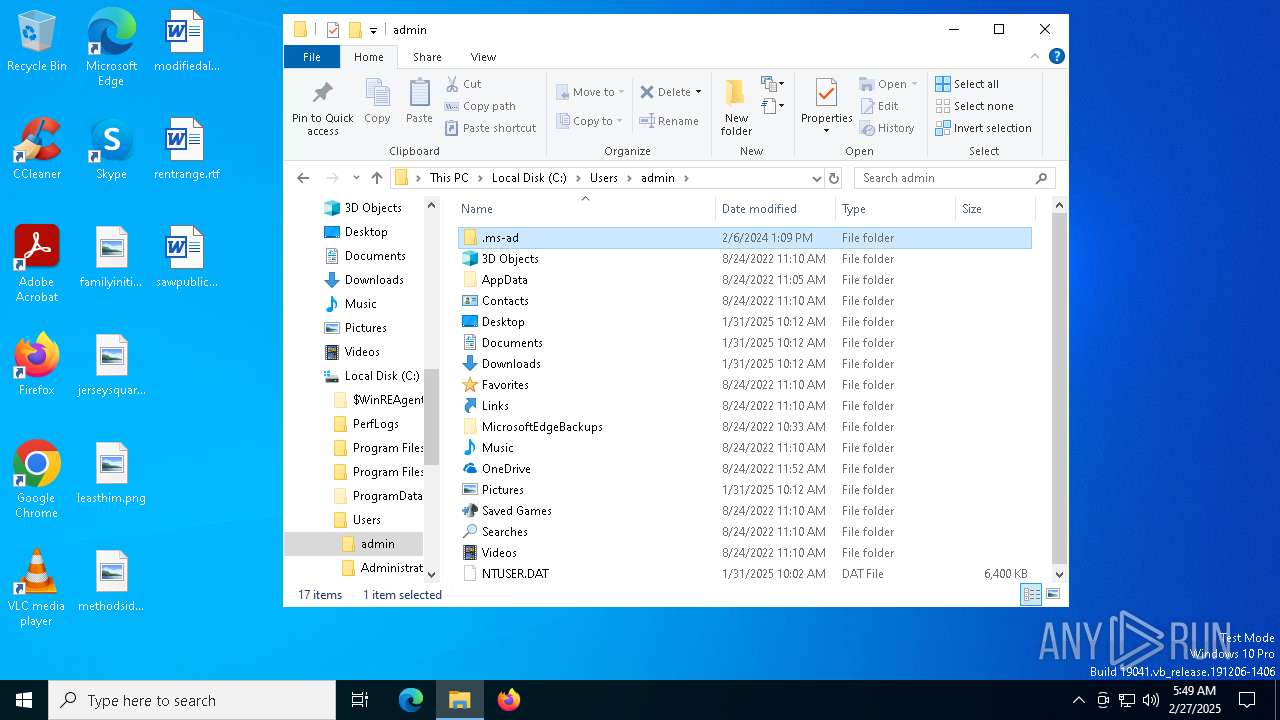
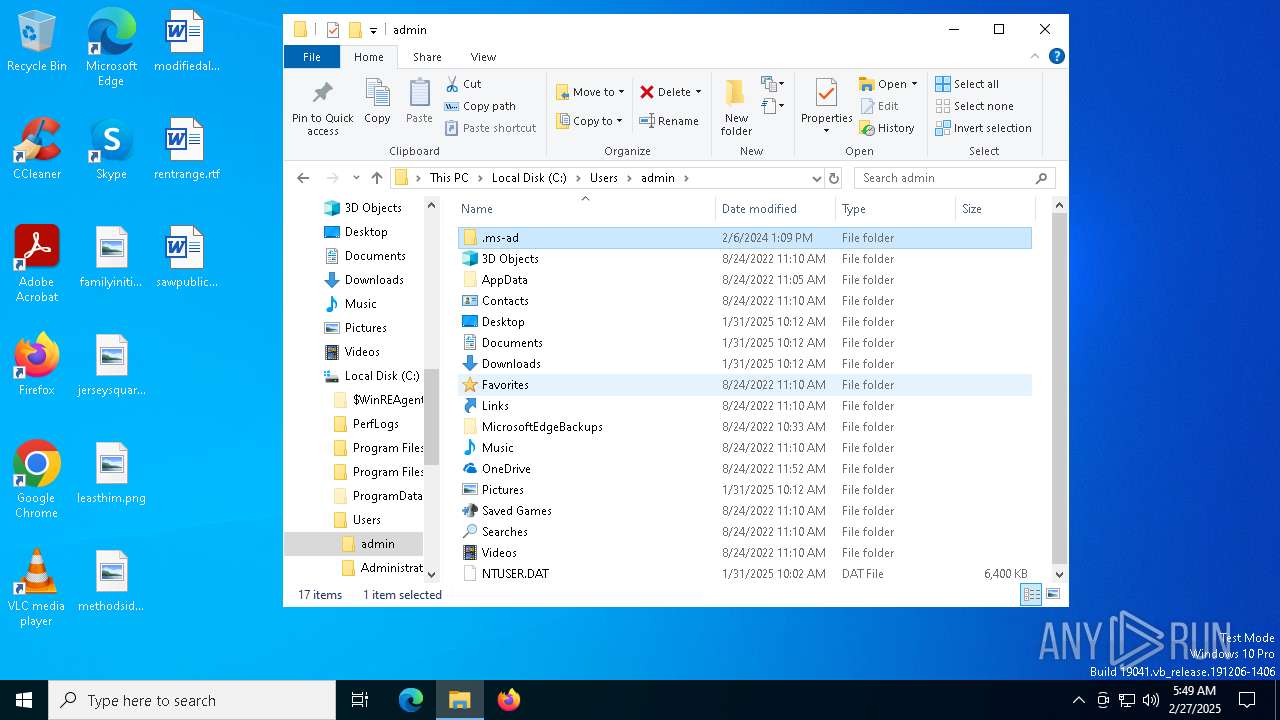
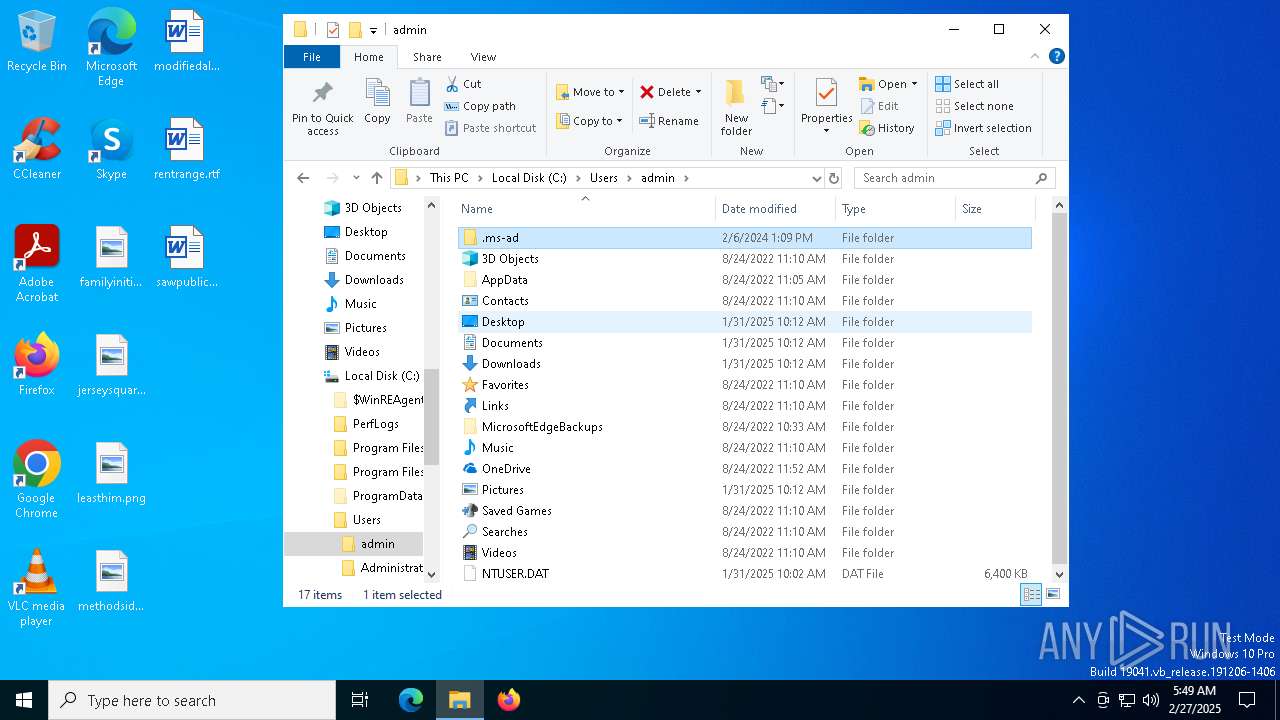
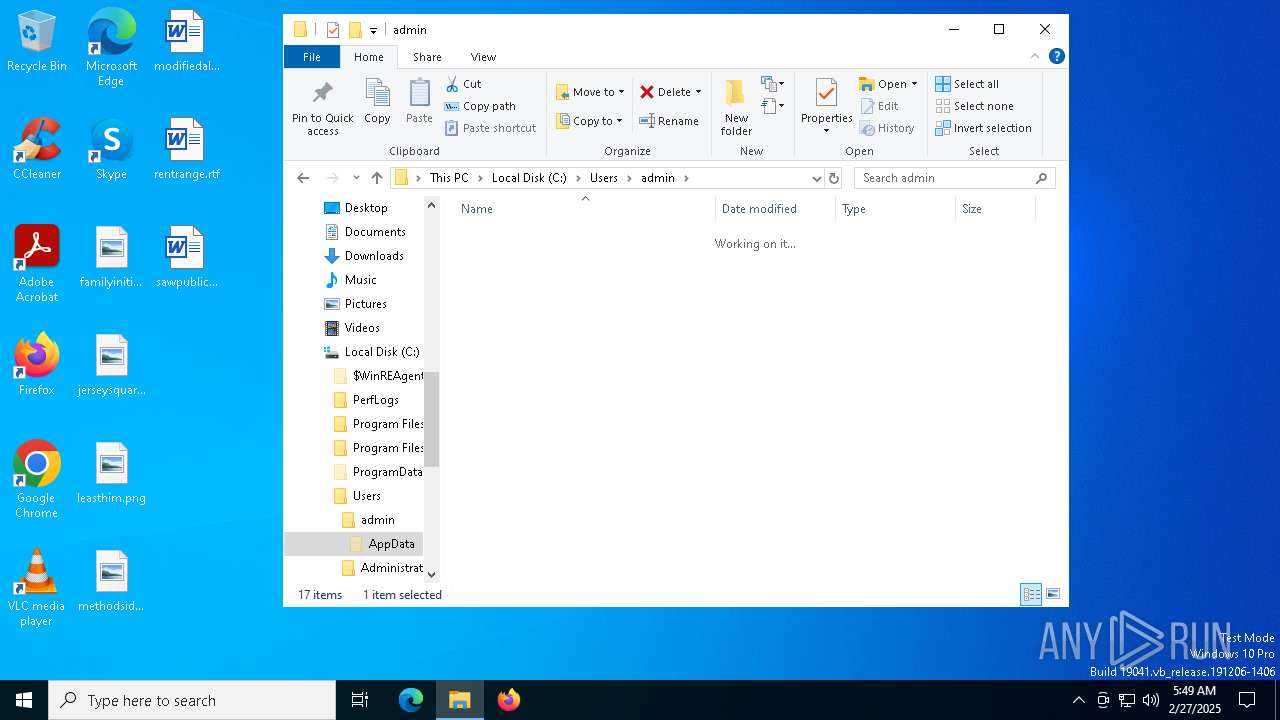
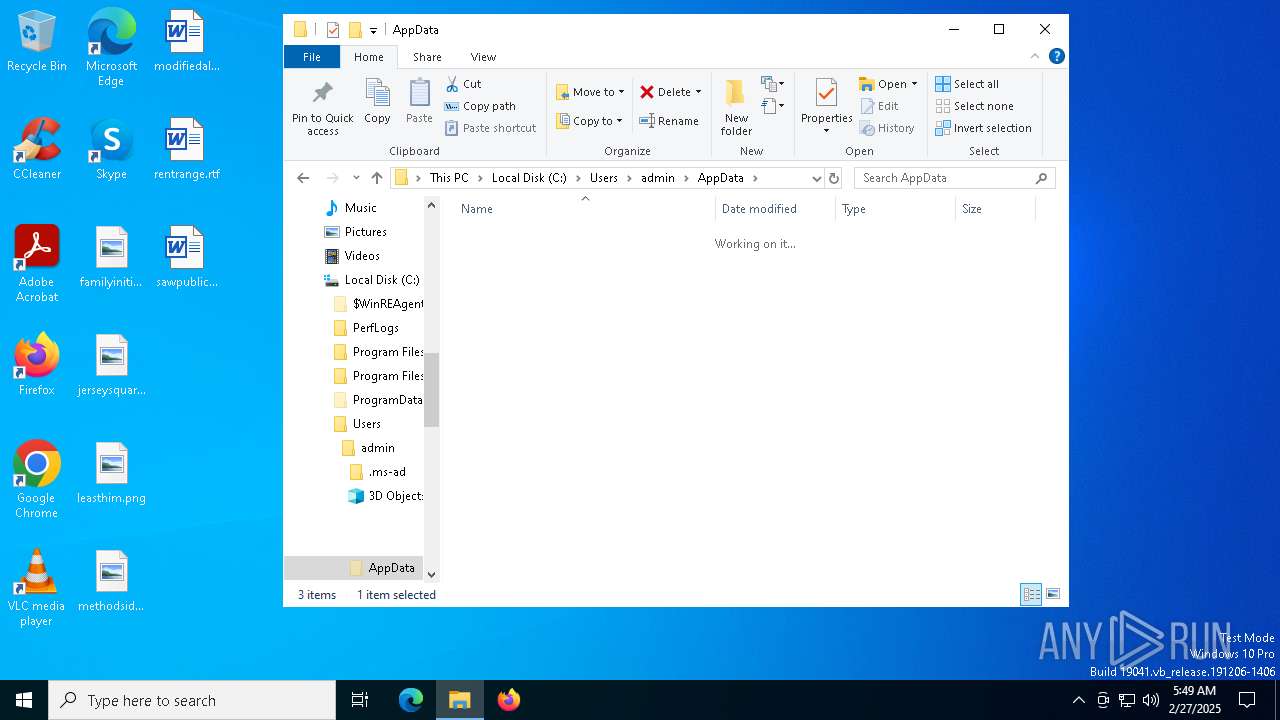
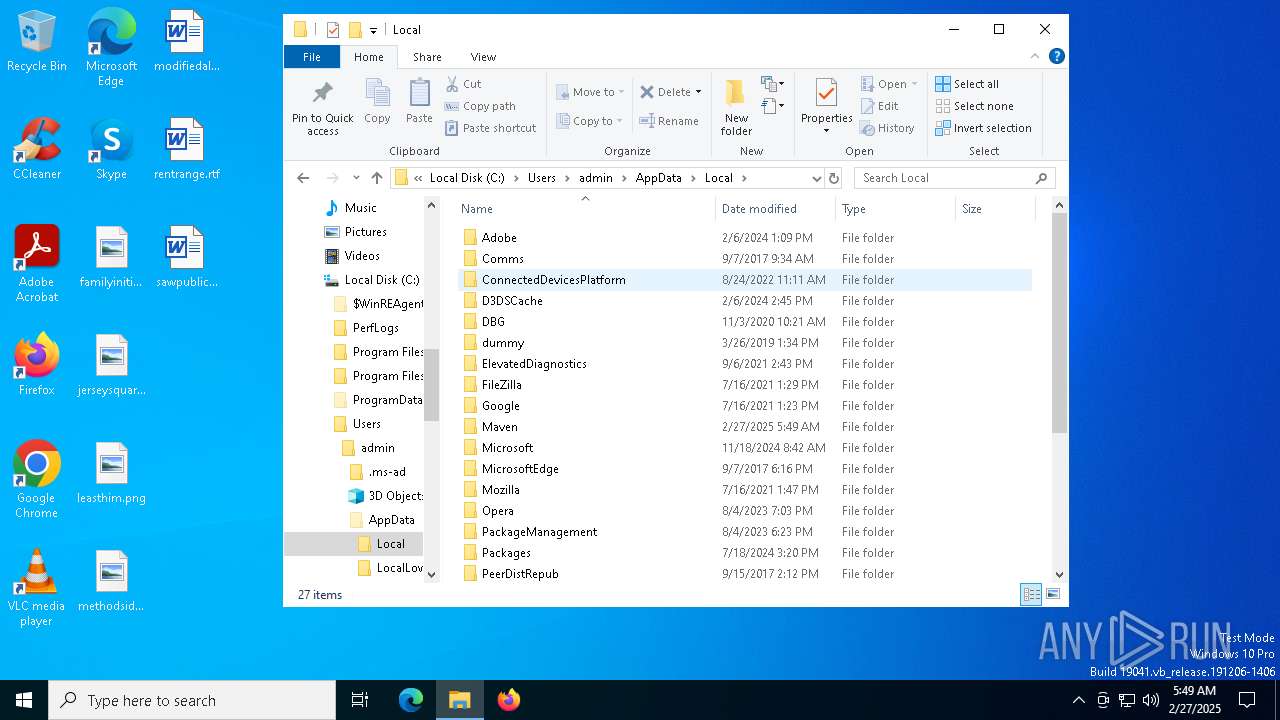
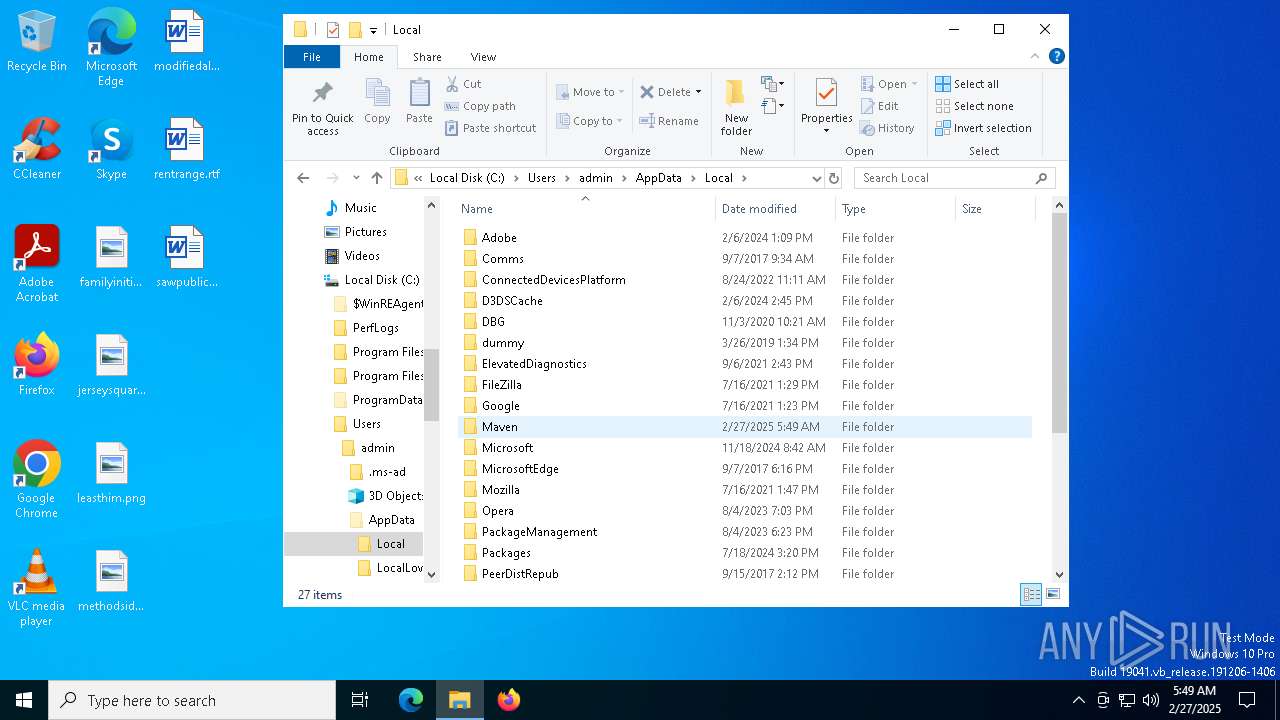
Creates files or folders in the user directory
- msiexec.exe (PID: 5352)
- Ahnenblatt4.exe (PID: 7188)
Reads the computer name
- Ahnenblatt4.exe (PID: 7188)
- Ahnenblatt4.exe (PID: 7260)
- ToolBeacon_3.exe (PID: 7664)
- Ahnenblatt4.exe (PID: 7924)
- Ahnenblatt4.exe (PID: 7900)
- Ahnenblatt4.exe (PID: 7220)
- Ahnenblatt4.exe (PID: 4776)
- Ahnenblatt4.exe (PID: 8052)
- Ahnenblatt4.exe (PID: 8072)
- ToolBeacon_3.exe (PID: 8156)
- ToolBeacon_3.exe (PID: 7224)
- ToolBeacon_3.exe (PID: 4728)
Creates a software uninstall entry
- msiexec.exe (PID: 5352)
Create files in a temporary directory
- Ahnenblatt4.exe (PID: 7260)
- Ahnenblatt4.exe (PID: 7924)
- Ahnenblatt4.exe (PID: 8072)
- Ahnenblatt4.exe (PID: 4776)
Manual execution by a user
- Ahnenblatt4.exe (PID: 7900)
- Ahnenblatt4.exe (PID: 7220)
- Ahnenblatt4.exe (PID: 8052)
Reads the machine GUID from the registry
- ToolBeacon_3.exe (PID: 7664)
- ToolBeacon_3.exe (PID: 8156)
- ToolBeacon_3.exe (PID: 4728)
- ToolBeacon_3.exe (PID: 7224)
Reads the software policy settings
- ToolBeacon_3.exe (PID: 7664)
- slui.exe (PID: 7848)
- ToolBeacon_3.exe (PID: 8156)
- ToolBeacon_3.exe (PID: 7224)
- ToolBeacon_3.exe (PID: 4728)
Checks proxy server information
- ToolBeacon_3.exe (PID: 7664)
- slui.exe (PID: 7848)
- ToolBeacon_3.exe (PID: 8156)
- ToolBeacon_3.exe (PID: 7224)
- ToolBeacon_3.exe (PID: 4728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Tabi |
| Author: | Aeciospore Protanopia |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Tabi. |
| Template: | Intel;1033 |
| RevisionNumber: | {5D9E2A4F-4DBD-4815-B218-E3F5EEF5932F} |
| CreateDate: | 2025:02:24 03:55:28 |
| ModifyDate: | 2025:02:24 03:55:28 |
| Pages: | 500 |
| Words: | 10 |
| Software: | WiX Toolset (4.0.0.0) |
| Security: | Read-only recommended |
Total processes
163
Monitored processes
27
Malicious processes
1
Suspicious processes
1
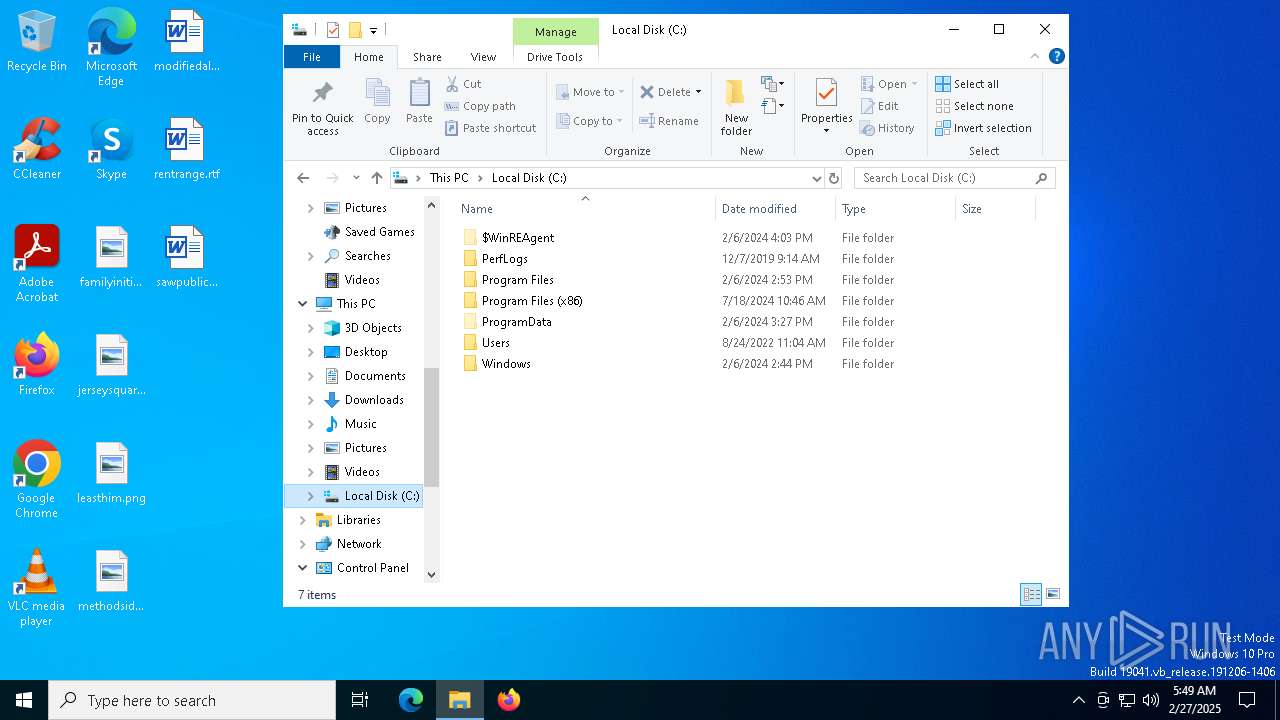
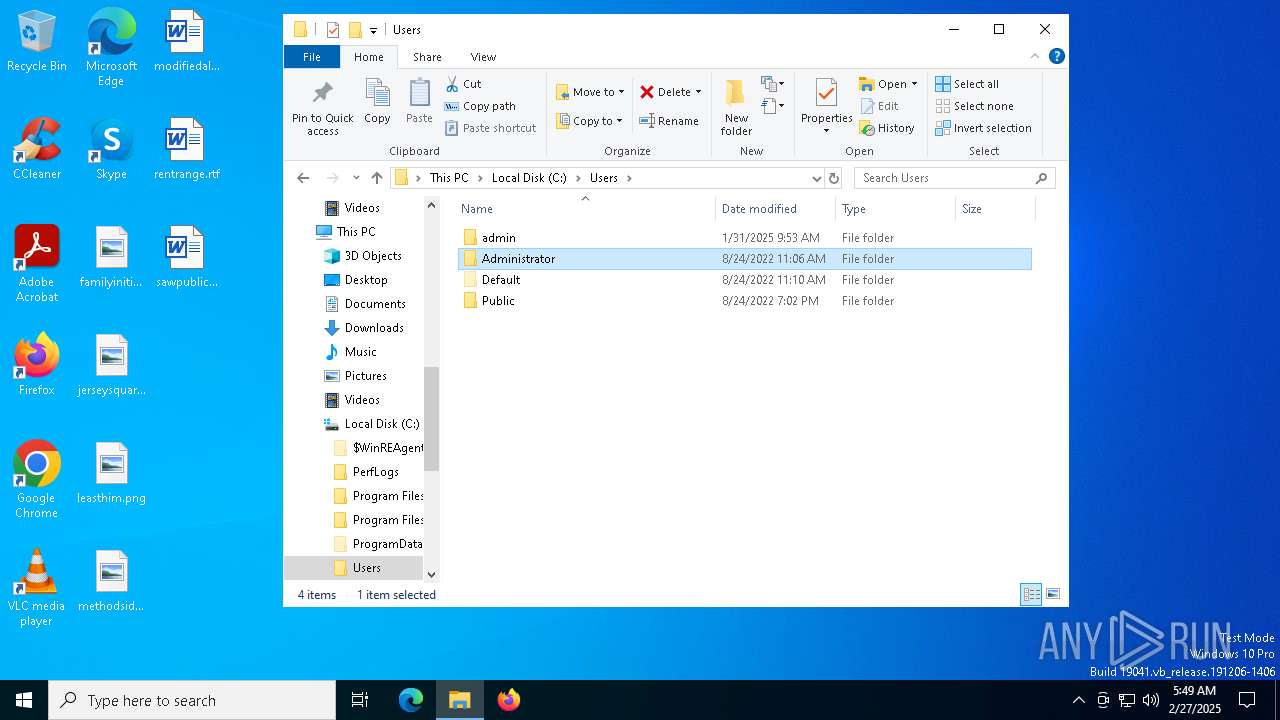
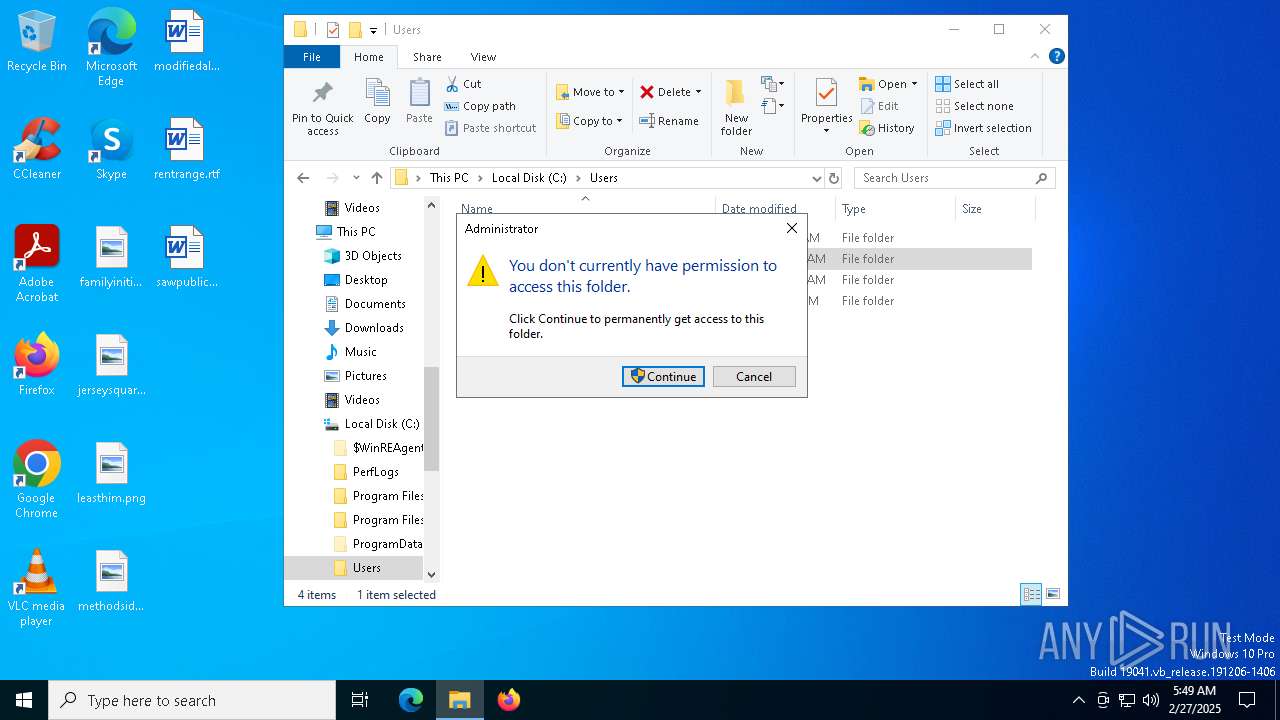
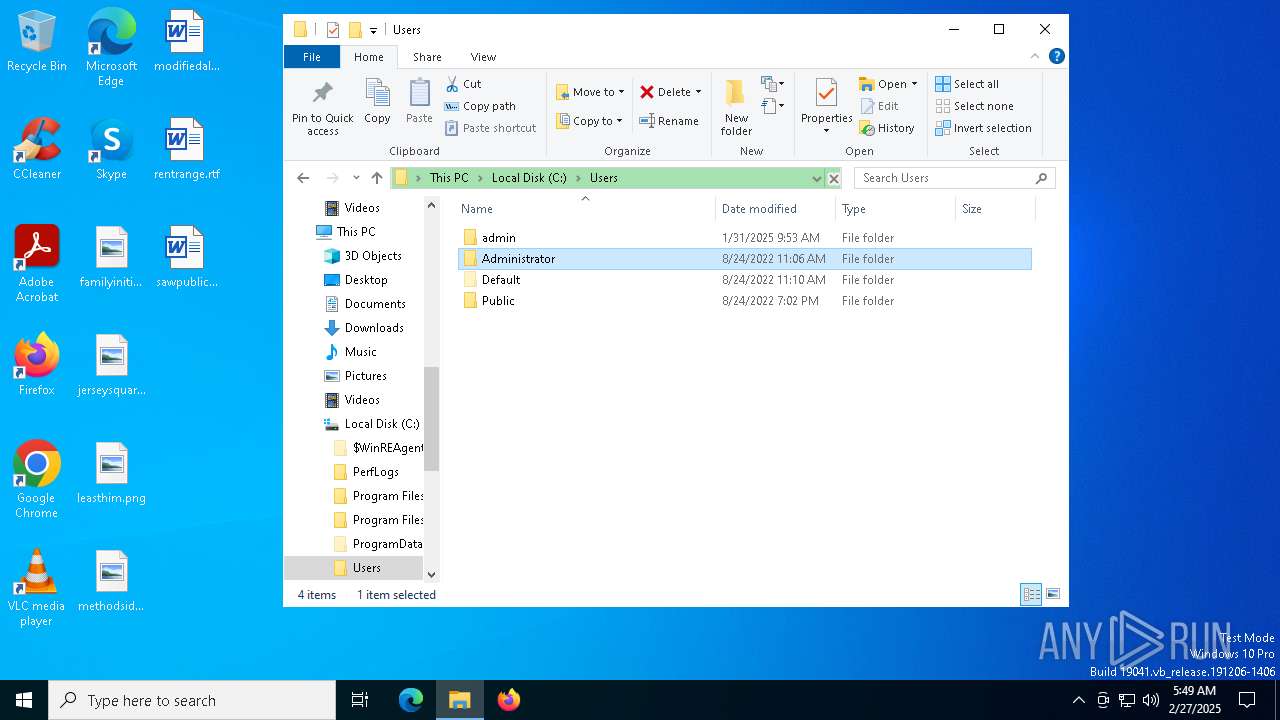
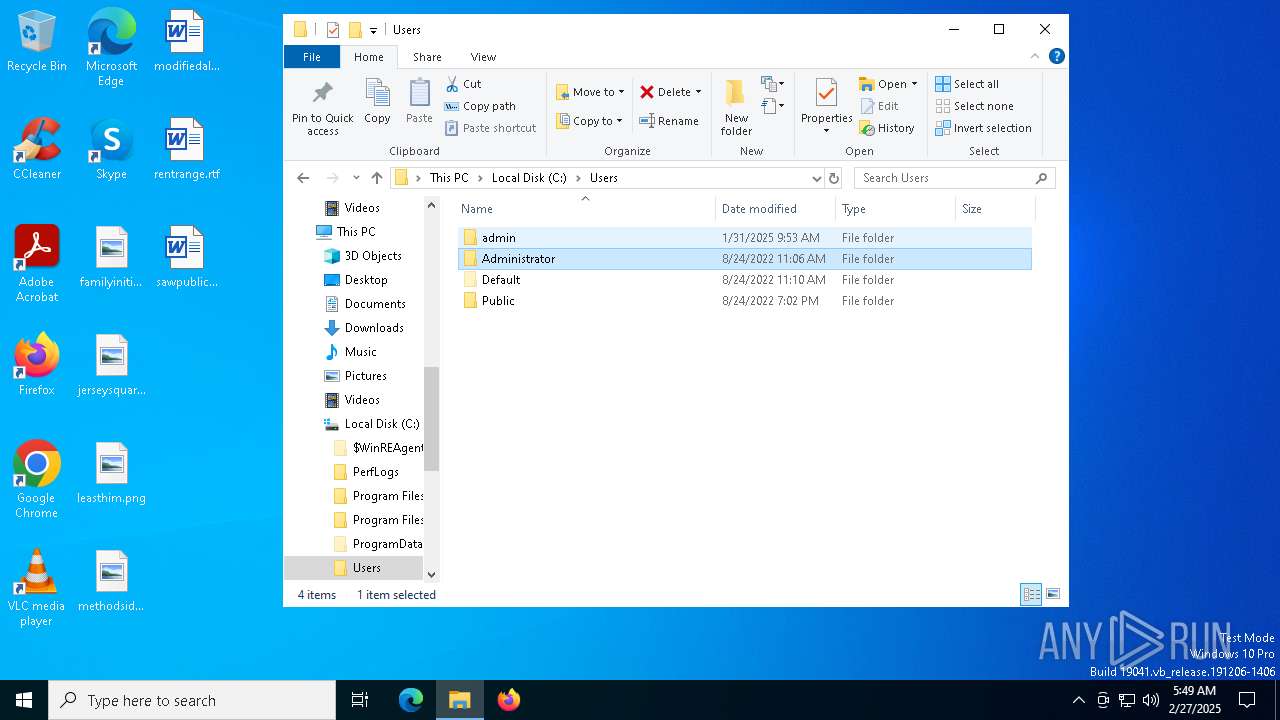
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1628 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2340 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | Ahnenblatt4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\61.brr.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4728 | C:\Users\admin\AppData\Local\Temp\ToolBeacon_3.exe | C:\Users\admin\AppData\Local\Temp\ToolBeacon_3.exe | cmd.exe | ||||||||||||
User: admin Company: Nenad Hrg (SoftwareOK.com) Integrity Level: MEDIUM Description: Q-Dir Version: 11,4,4,0 Modules
| |||||||||||||||
| 4776 | C:\Users\admin\AppData\Roaming\tu_Advanced_alpha\Ahnenblatt4.exe | C:\Users\admin\AppData\Roaming\tu_Advanced_alpha\Ahnenblatt4.exe | — | Ahnenblatt4.exe | |||||||||||
User: admin Company: Dirk Böttcher Integrity Level: MEDIUM Description: Ahnenblatt Exit code: 1 Version: 4.20.0.4 Modules
| |||||||||||||||
| 5352 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
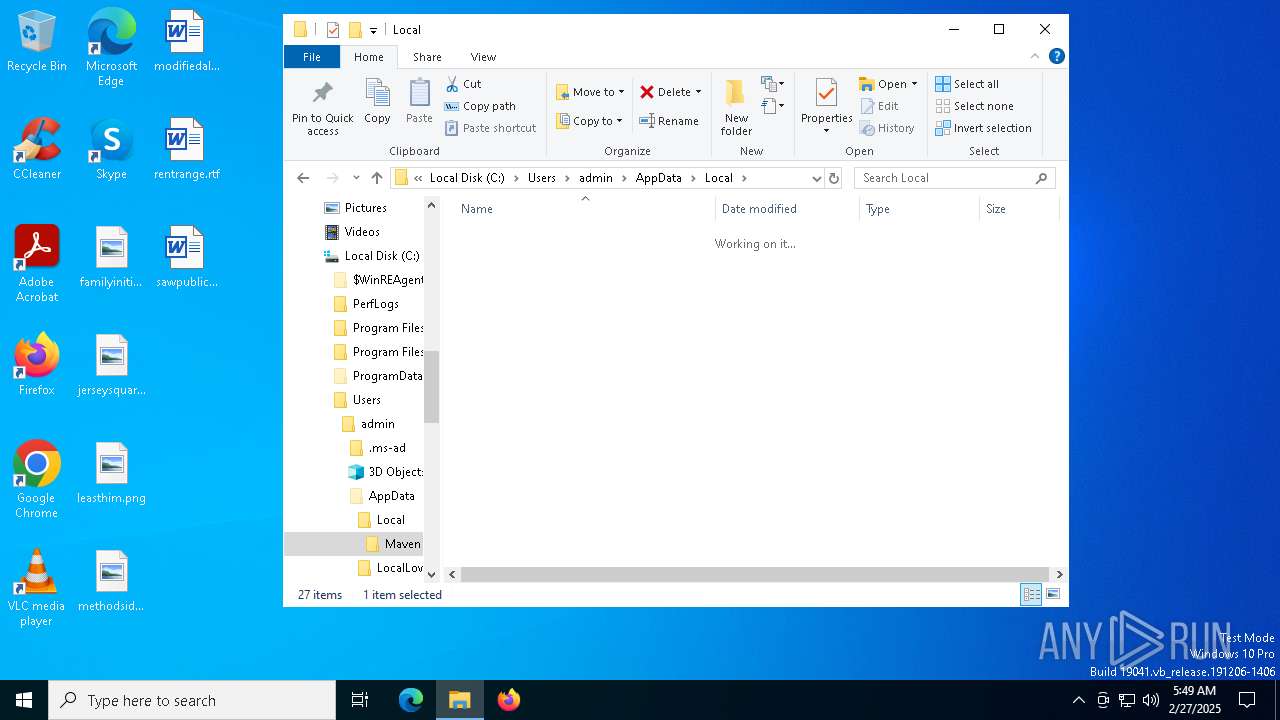
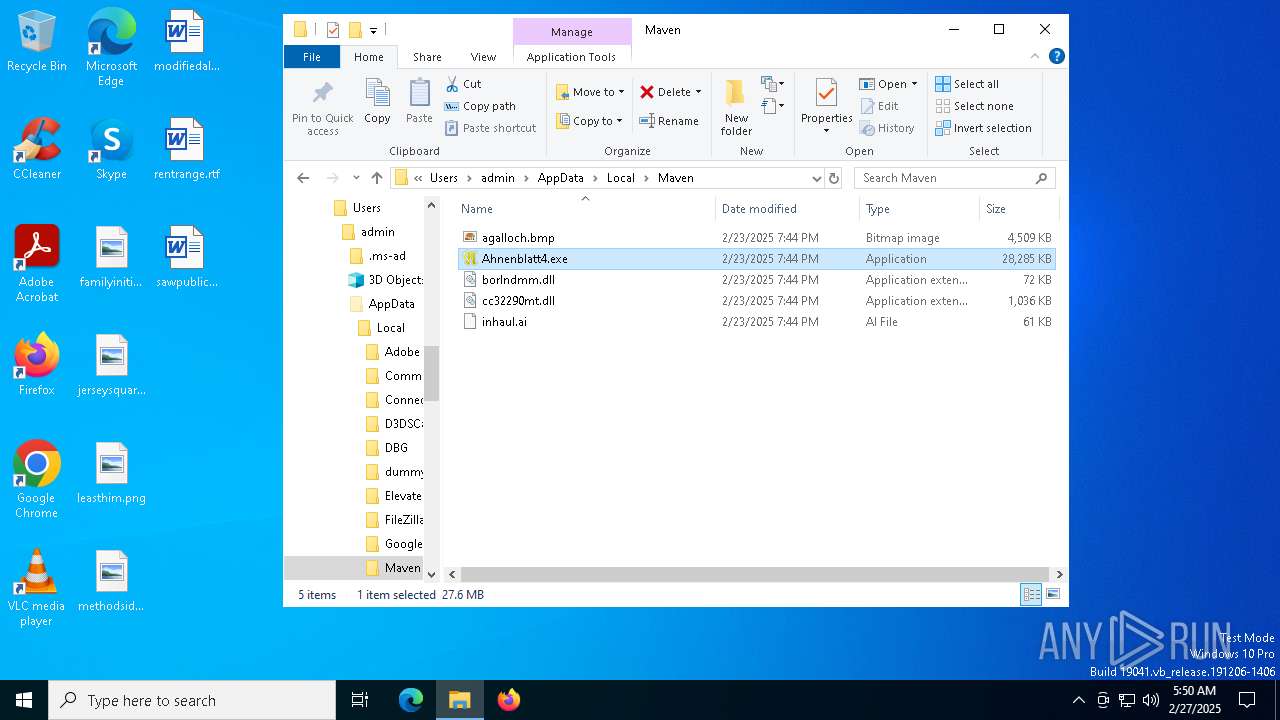
| 7188 | "C:\Users\admin\AppData\Local\Maven\Ahnenblatt4.exe" | C:\Users\admin\AppData\Local\Maven\Ahnenblatt4.exe | msiexec.exe | ||||||||||||
User: admin Company: Dirk Böttcher Integrity Level: MEDIUM Description: Ahnenblatt Exit code: 0 Version: 4.20.0.4 Modules
| |||||||||||||||
Total events
4 123
Read events
3 892
Write events
222
Delete events
9
Modification events
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000004EC6B345DB88DB01E8140000F4190000E803000000000000000000000000000077F7AB8F17F8EB49B3311B8299685F8200000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | GETSTATE (Enter) |
Value: 480000000000000021AF9C49DB88DB01E8140000341A0000F903000001000000000000000000000077F7AB8F17F8EB49B3311B8299685F8200000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | GETSTATE (Leave) |
Value: 48000000000000000D019F49DB88DB01E8140000341A0000F903000000000000000000000000000077F7AB8F17F8EB49B3311B8299685F8200000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | DOSNAPSHOT (Enter) |
Value: 4800000000000000CEFCBD49DB88DB01E8140000341B00000A04000001000000000000000000000077F7AB8F17F8EB49B3311B8299685F8200000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 48000000000000003E0A4249DB88DB01E8140000341B0000D30700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 48000000000000003E0A4249DB88DB01E8140000341B0000D40700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 4800000000000000108A5749DB88DB01E8140000341B0000D40700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1628) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Enter) |
Value: 480000000000000026A17D49DB88DB015C060000641700000104000001000000000000000000000077F7AB8F17F8EB49B3311B8299685F8200000000000000000000000000000000 | |||
| (PID) Process: | (1628) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Leave) |
Value: 480000000000000026A17D49DB88DB015C060000641700000104000000000000000000000000000077F7AB8F17F8EB49B3311B8299685F8200000000000000000000000000000000 | |||
| (PID) Process: | (1628) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | PREPAREBACKUP (Enter) |
Value: 480000000000000050038049DB88DB015C060000AC050000E903000001000000010000000000000077F7AB8F17F8EB49B3311B8299685F8200000000000000000000000000000000 | |||
Executable files
7
Suspicious files
18
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5352 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5352 | msiexec.exe | C:\Windows\Installer\1119ee.msi | — | |
MD5:— | SHA256:— | |||
| 5352 | msiexec.exe | C:\Users\admin\AppData\Local\Maven\agalloch.bmp | — | |
MD5:— | SHA256:— | |||
| 5352 | msiexec.exe | C:\Windows\Installer\1119f0.msi | — | |
MD5:— | SHA256:— | |||
| 5352 | msiexec.exe | C:\Windows\Installer\MSI1C8D.tmp | binary | |
MD5:6E8A954B9F0C65548ED29678206029C9 | SHA256:4A1DF61ABA495F2A740112BBA62690C4DAF2DE8B8C3EC73C24B579885E57100F | |||
| 5352 | msiexec.exe | C:\Windows\Temp\~DF292947033C61F65B.TMP | binary | |
MD5:4985B0EDF4ED030EC9E2C3F4B071998F | SHA256:30778B6787517E30862F7DBEA06BD9EF188A6ED771088443098BC200E1D2B539 | |||
| 5352 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:5B3A061D216E11769C54D3D1BDC8A7AB | SHA256:EF0269BD883B13E34F40DE0E193CF498B3D2C97B1BD0746242A79BEBE99DE246 | |||
| 5352 | msiexec.exe | C:\Windows\Temp\~DF75F7CA80F654D3EA.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 5352 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{8fabf777-f817-49eb-b331-1b8299685f82}_OnDiskSnapshotProp | binary | |
MD5:5B3A061D216E11769C54D3D1BDC8A7AB | SHA256:EF0269BD883B13E34F40DE0E193CF498B3D2C97B1BD0746242A79BEBE99DE246 | |||
| 5352 | msiexec.exe | C:\Users\admin\AppData\Local\Maven\cc32290mt.dll | executable | |
MD5:D04F9D0B75D122046ADC8EE7B895638D | SHA256:DAB744A533BCBC4A2D3F19A54694CEB00587A0CE68D046CA9085D5013321EA5A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
36
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4724 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.96.128:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2040 | backgroundTaskHost.exe | 20.103.156.88:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6028 | svchost.exe | 2.19.106.8:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |