| File name: | dq.exe |
| Full analysis: | https://app.any.run/tasks/02b812fd-cad8-4725-9061-0d285cb8487e |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 22:19:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 1F2FD5B115B48F2A060E11F60CD3D7F1 |
| SHA1: | BDD4D645C491A34C6084543CB7F47B27B0A28611 |
| SHA256: | DE7148BDE8009AEC346D978E6836E6AEC1AE741E1AD58851EBFBCEAB7C1B5348 |
| SSDEEP: | 24576:mbaBr/DduQqmzhFfvRUKd/k6Ub1G8hzKP//7A3V3:VBrZkYZoRG8VKP//s3V3 |
MALICIOUS
Drops executable file immediately after starts
- msdt.exe (PID: 3816)
- csc.exe (PID: 3892)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 1564)
SUSPICIOUS
Drops a file with a compile date too recent
- msdt.exe (PID: 3816)
- csc.exe (PID: 3892)
Checks supported languages
- dq.exe (PID: 3596)
- cvtres.exe (PID: 3432)
- csc.exe (PID: 3892)
- dq.exe (PID: 2516)
Executable content was dropped or overwritten
- msdt.exe (PID: 3816)
- csc.exe (PID: 3892)
Executed via COM
- sdiagnhost.exe (PID: 1564)
INFO
Reads the computer name
- msdt.exe (PID: 3816)
- sdiagnhost.exe (PID: 1564)
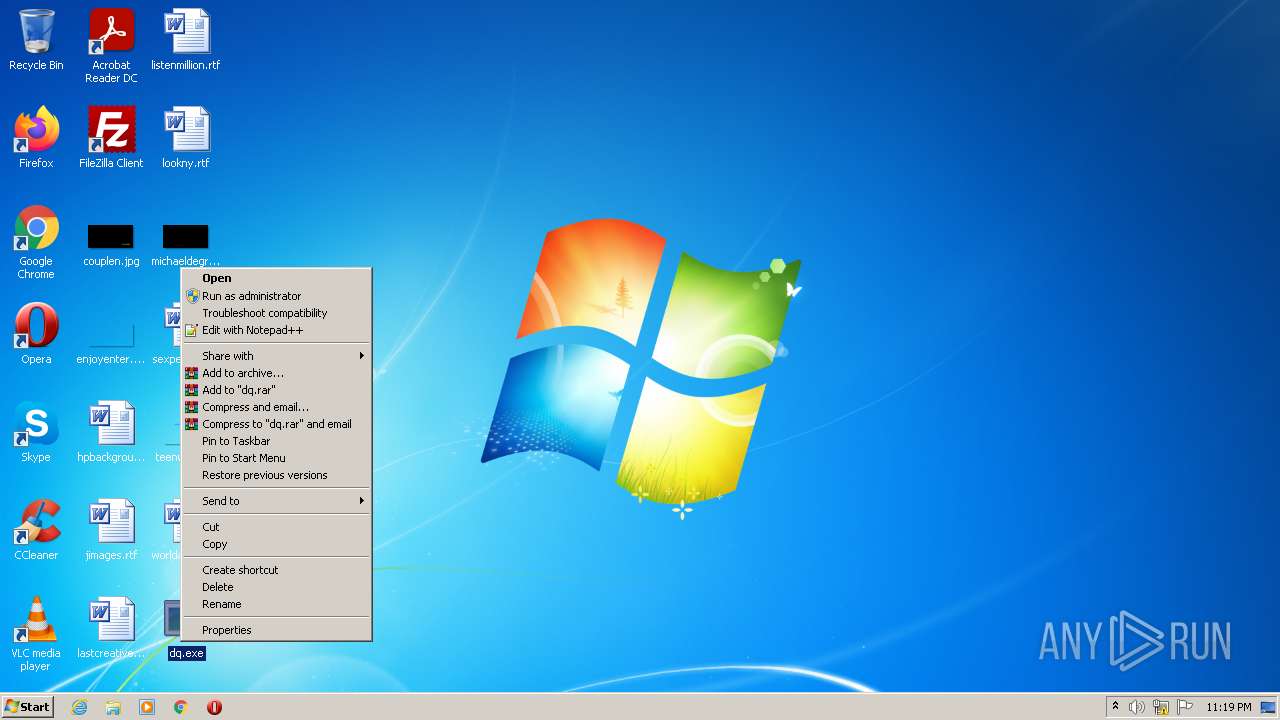
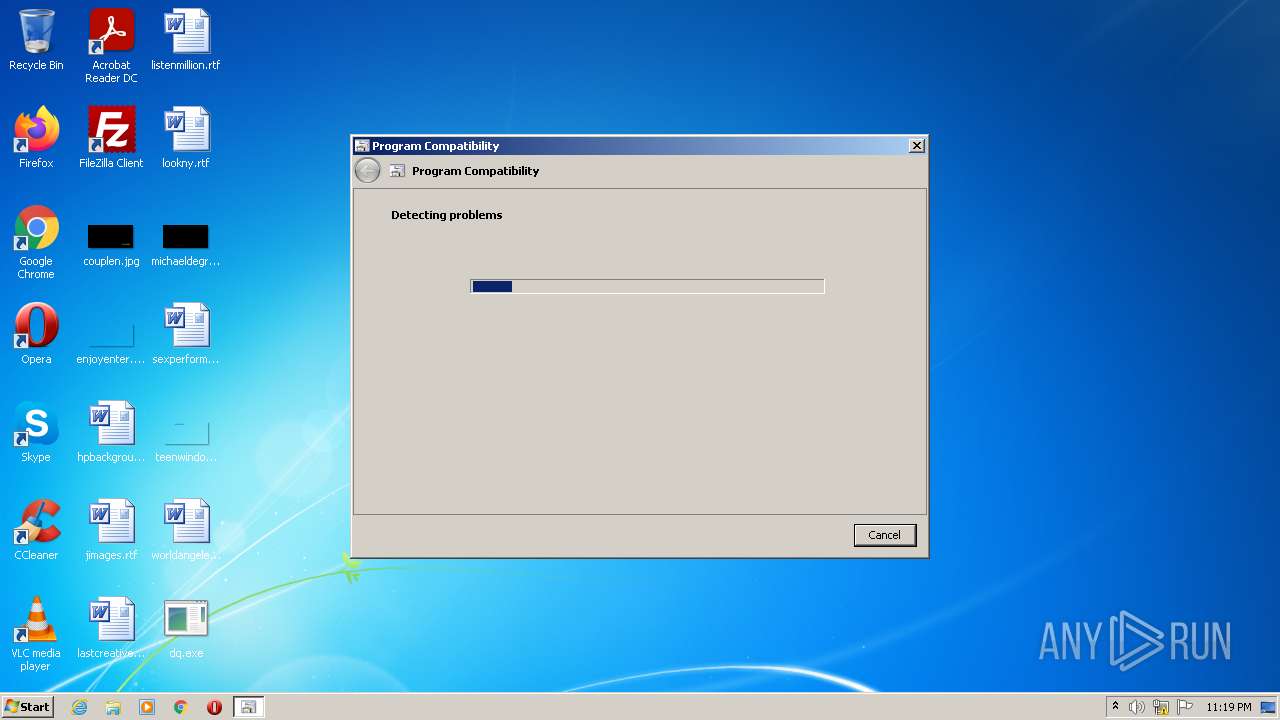
Manual execution by user
- pcwrun.exe (PID: 3360)
- dq.exe (PID: 2516)
Reads settings of System Certificates
- msdt.exe (PID: 3816)
Checks supported languages
- pcwrun.exe (PID: 3360)
- msdt.exe (PID: 3816)
- sdiagnhost.exe (PID: 1564)
Checks Windows Trust Settings
- msdt.exe (PID: 3816)
- sdiagnhost.exe (PID: 1564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x9679a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 380416 |
| CodeSize: | 724480 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2022:08:13 00:19:18+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 12-Aug-2022 22:19:18 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Aug-2022 22:19:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B0C04 | 0x000B0E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61429 |
.rdata | 0x000B2000 | 0x0004AD74 | 0x0004AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.20351 |
.data | 0x000FD000 | 0x00007E34 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88496 |
.rsrc | 0x00105000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7123 |
.reloc | 0x00106000 | 0x00009C6C | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59786 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
44
Monitored processes
7
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1564 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\Desktop\dq.exe" | C:\Users\admin\Desktop\dq.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3360 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\Desktop\dq.exe" | C:\Windows\system32\pcwrun.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3432 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESEC3B.tmp" "c:\Users\admin\AppData\Local\Temp\CSCEC2A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 3596 | "C:\Users\admin\Desktop\dq.exe" | C:\Users\admin\Desktop\dq.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3816 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCWE67D.xml /skip TRUE | C:\Windows\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\zbo8pcza.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
Total events
4 166
Read events
4 144
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3816) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1564) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1564) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1564) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1564) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
7
Text files
17
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3596 | dq.exe | C:\Users\admin\ntuser.ini.protected | binary | |
MD5:— | SHA256:— | |||
| 3892 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCEC2A.tmp | res | |
MD5:— | SHA256:— | |||
| 1564 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\zbo8pcza.cmdline | text | |
MD5:— | SHA256:— | |||
| 3892 | csc.exe | C:\Users\admin\AppData\Local\Temp\zbo8pcza.pdb | pdb | |
MD5:— | SHA256:— | |||
| 3816 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_1221cd44-8ca7-40da-a3e8-2714e910365d\RS_ProgramCompatibilityWizard.ps1 | text | |
MD5:367FE5F4C6DB87E1600F46687E5AAC54 | SHA256:177625AC9B07BBFFCBBB47101C2D1121F47B03B42226861BFD7974B9CEBC0C98 | |||
| 3816 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_1221cd44-8ca7-40da-a3e8-2714e910365d\en-US\DiagPackage.dll.mui | executable | |
MD5:C31BD28AB34E75BC65A5458AC8D37539 | SHA256:5FB9E280013D58043C5689478F9DCFAD3212F4681534627EB33998DDD6F63308 | |||
| 3816 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_1221cd44-8ca7-40da-a3e8-2714e910365d\DiagPackage.diagpkg | html | |
MD5:18A906A43C1C3E27064DB30C81505234 | SHA256:041430D1F0AE14300C46BDCD917C882F4850DA3D6010E3FBF692023655BC406E | |||
| 1564 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\zbo8pcza.0.cs | text | |
MD5:B0DC59B099CA7C12FB8AD72D3C50C82C | SHA256:E75EAAA3D7908FB05000C0A957048D20091A0D2575E87D091D11CDB3A5B562E5 | |||
| 3360 | pcwrun.exe | C:\Users\admin\AppData\Local\Temp\PCWE67D.xml | xml | |
MD5:80681B26E76818EC8BB3F99F3C1B1D97 | SHA256:B32857E34DD8099890EC37E3D642C8738D942DEBA5FB85C0EDCB09FADCB7F0C2 | |||
| 3816 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_1221cd44-8ca7-40da-a3e8-2714e910365d\result\results.xsl | xml | |
MD5:310E1DA2344BA6CA96666FB639840EA9 | SHA256:67401342192BABC27E62D4C1E0940409CC3F2BD28F77399E71D245EAE8D3F63C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|