| File name: | 14383-02_02.exe |
| Full analysis: | https://app.any.run/tasks/85401d13-553d-498a-878a-9491d26d1678 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 15:51:04 |
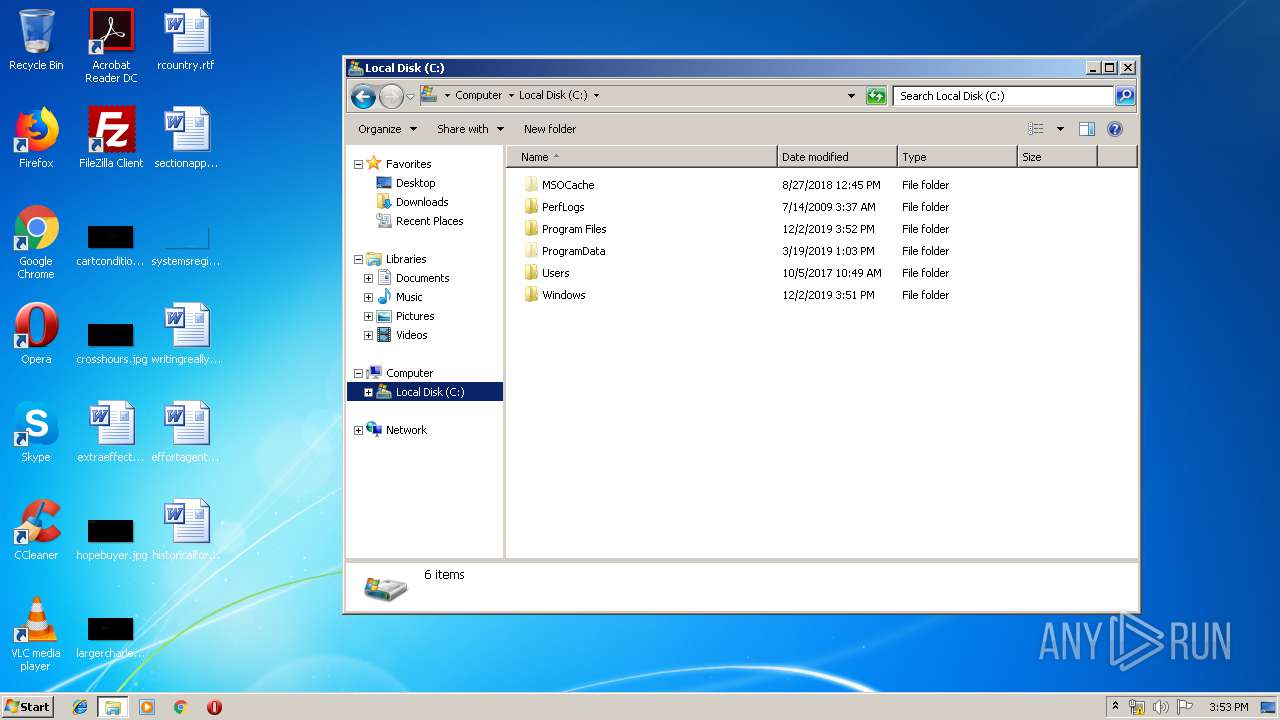
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BE5FE079187C540C2FE8B0CBB76363EB |
| SHA1: | 4134CCE58176754B9FDB9AA1DB7B3E50D5EBFCBE |
| SHA256: | DE66B7E4D353B39174A28E3497C8756BD25F0B8FF7D80E6E38EFDCC92C408A24 |
| SSDEEP: | 393216:9uMkqE5TUpCf2ivKH1Bgofj+G9ZlqHFBDiJ0n:cMkPW9xH1B1b+GUlBDi+n |
MALICIOUS
Application was dropped or rewritten from another process
- IDriver.exe (PID: 1448)
- IDriver.exe (PID: 3760)
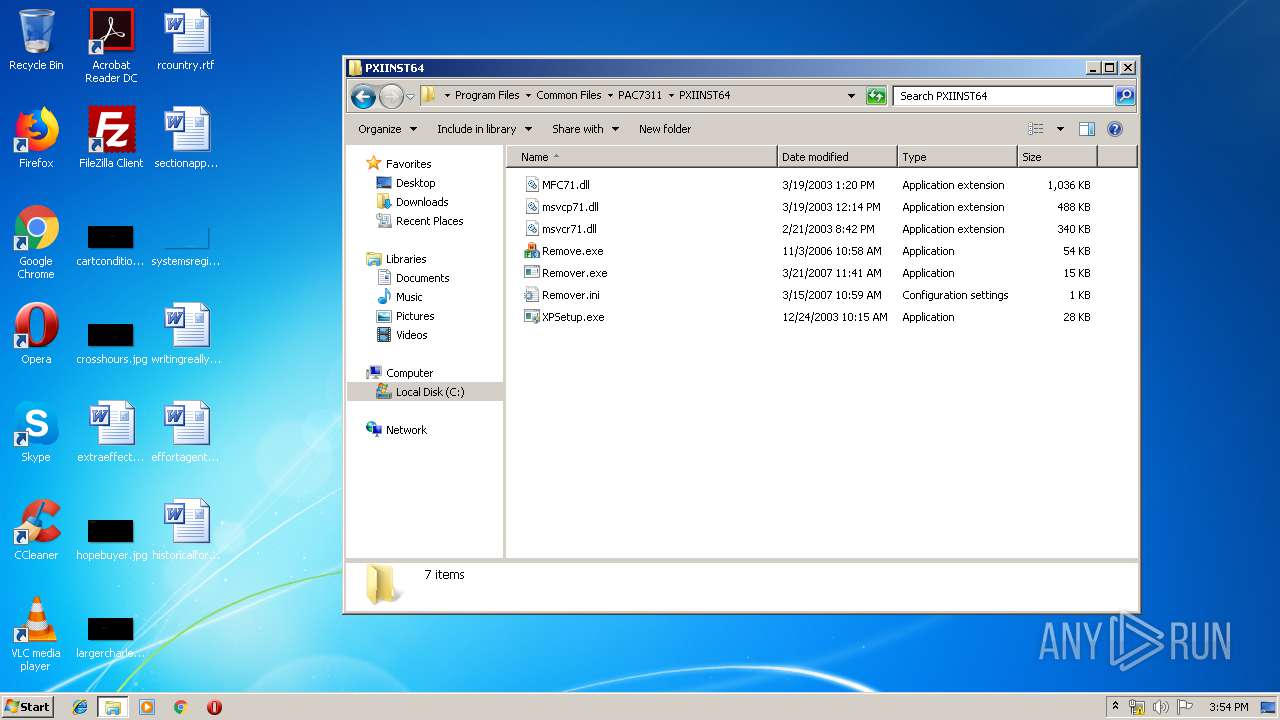
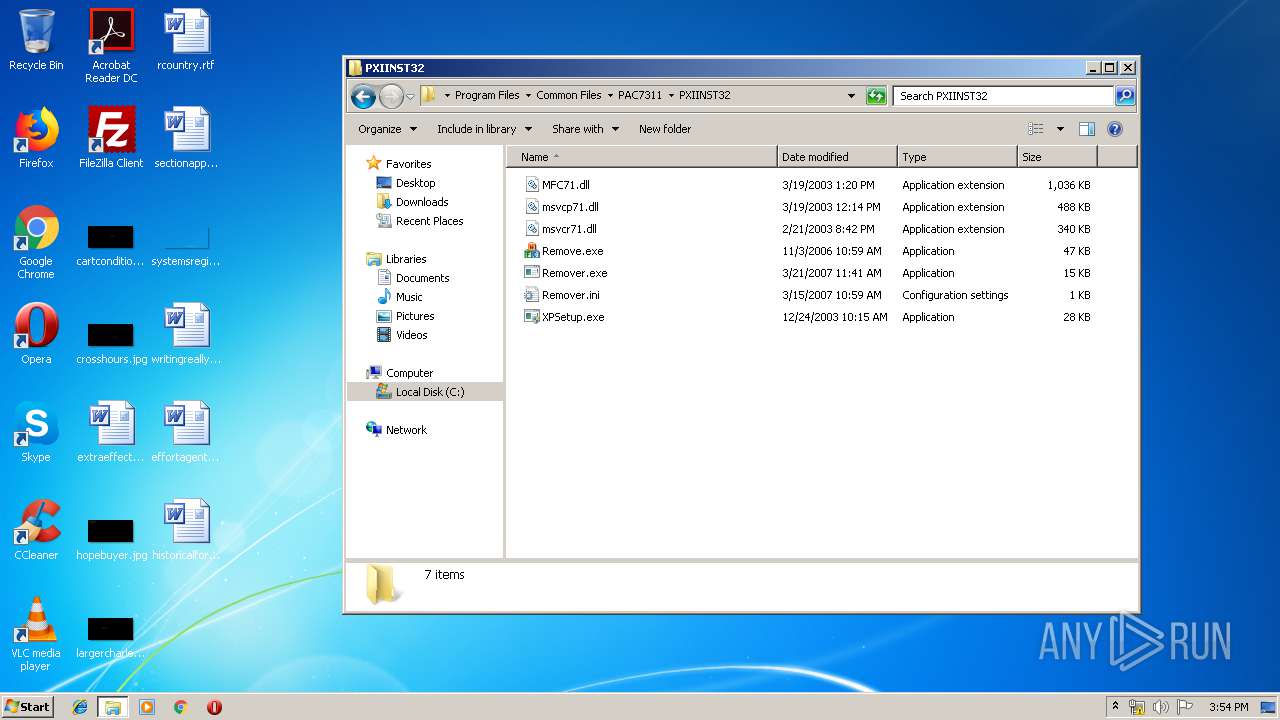
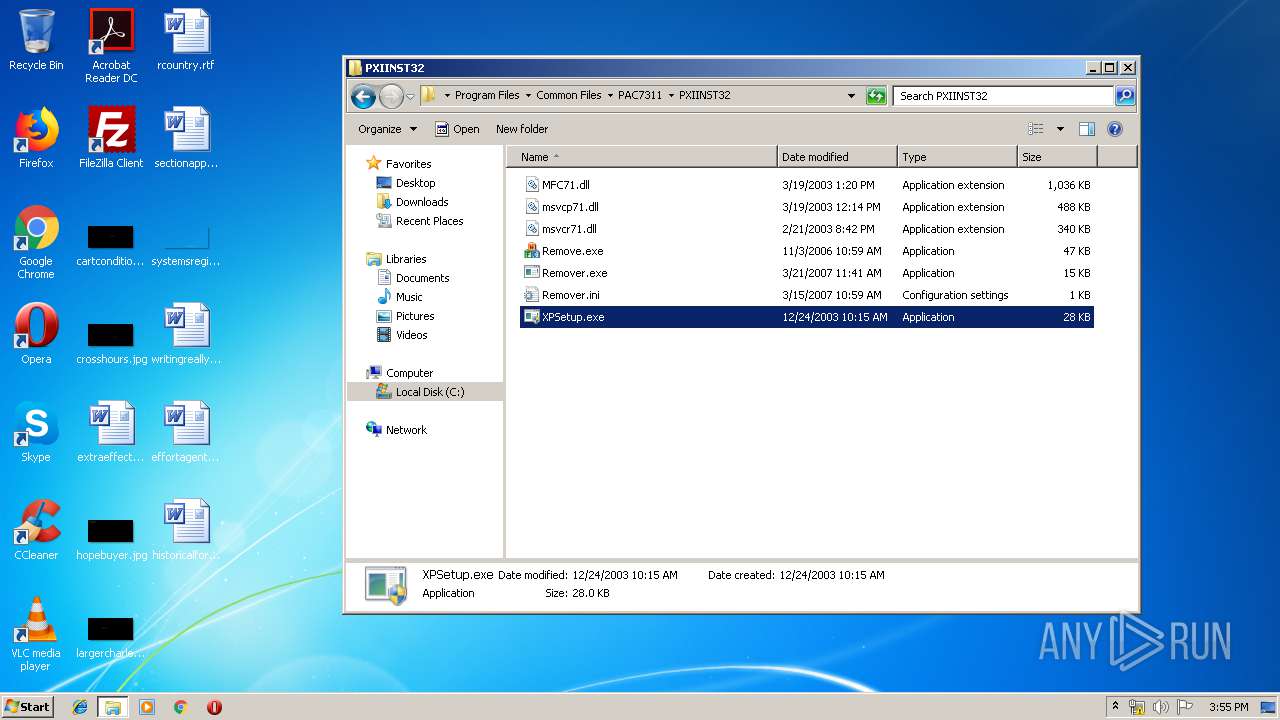
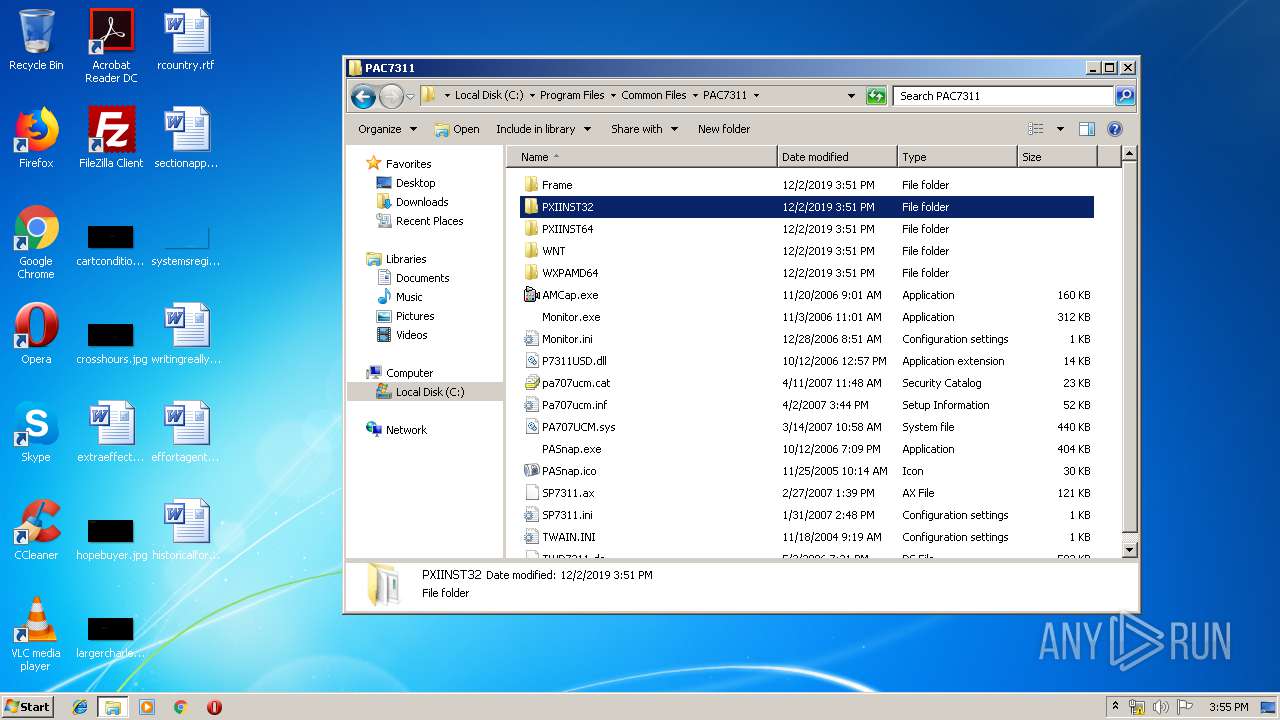
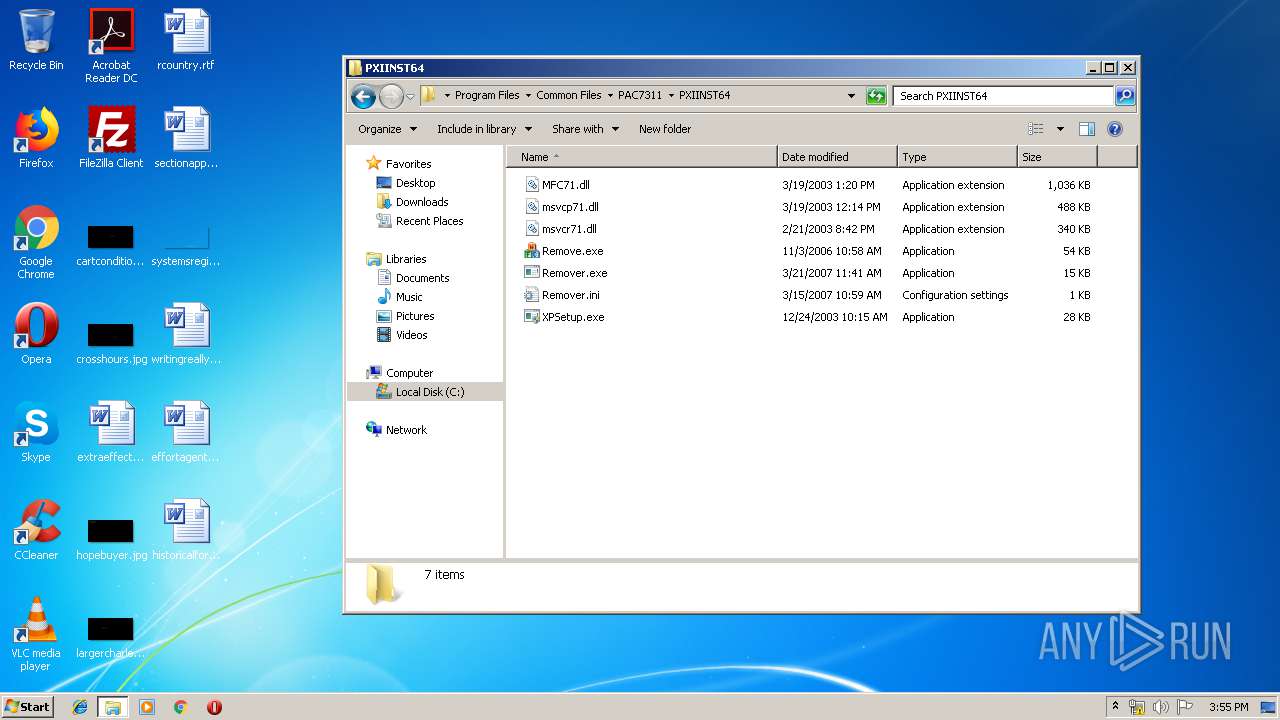
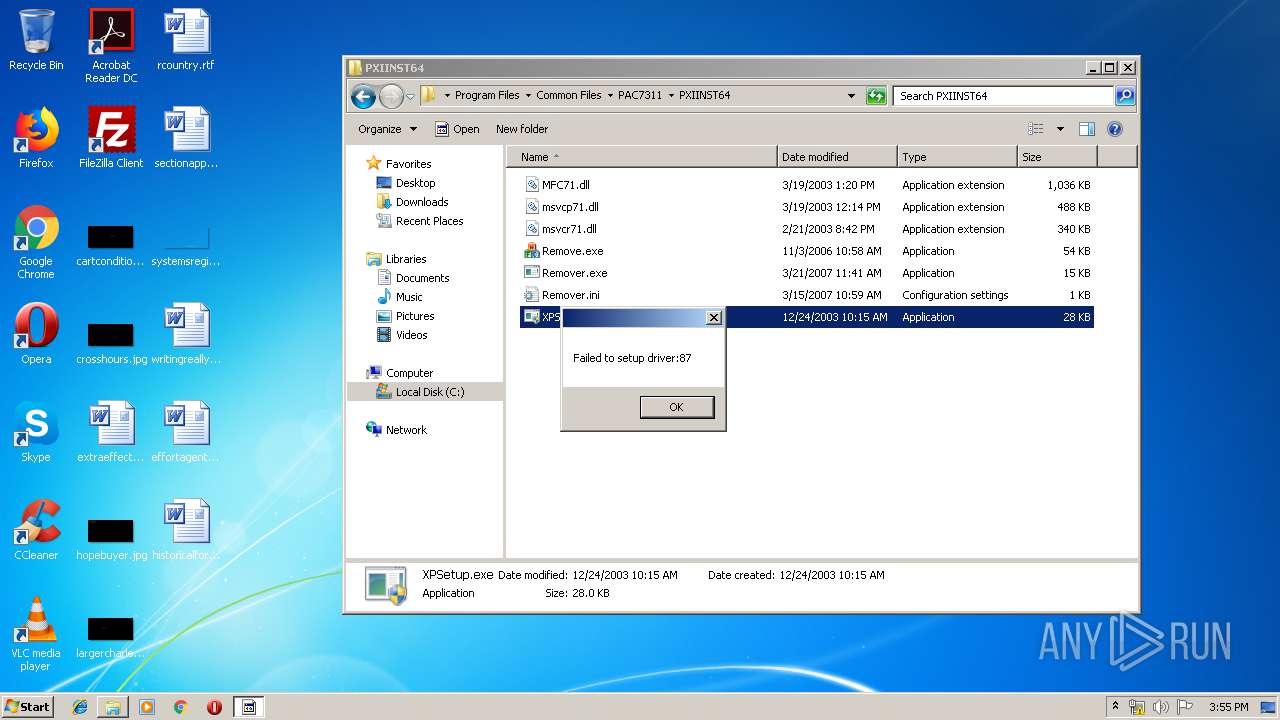
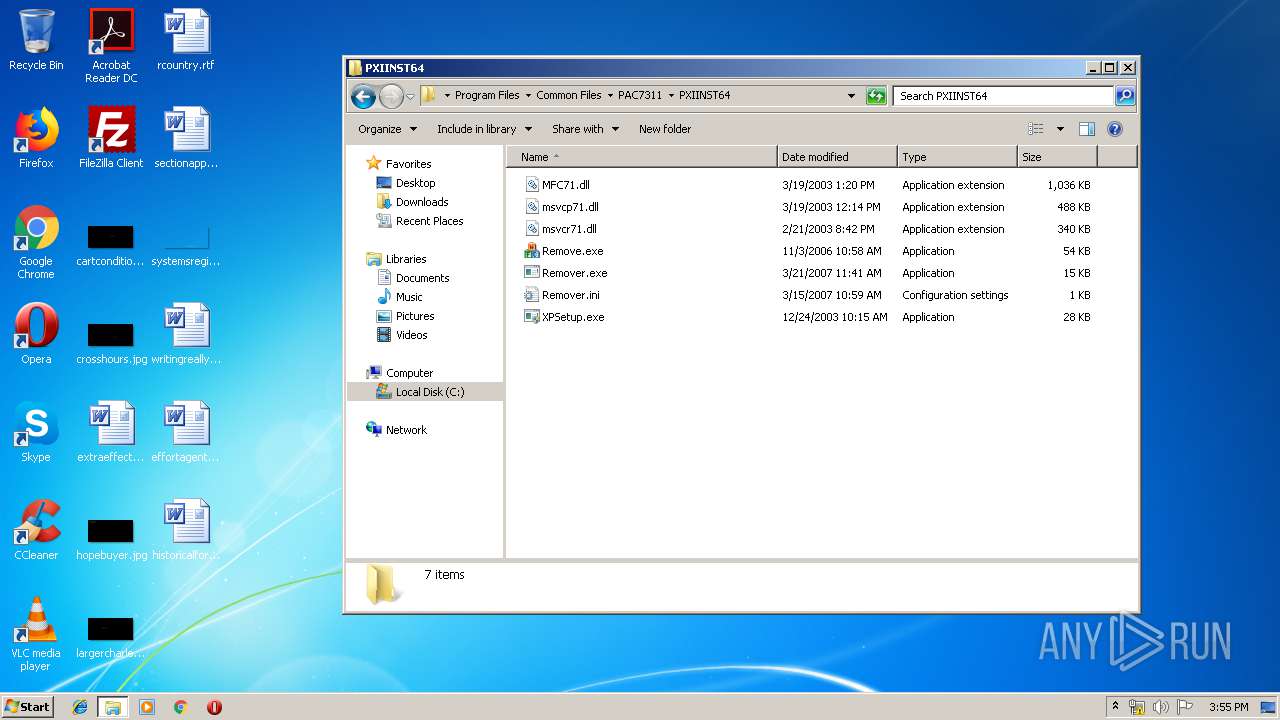
- XPSetup.exe (PID: 388)
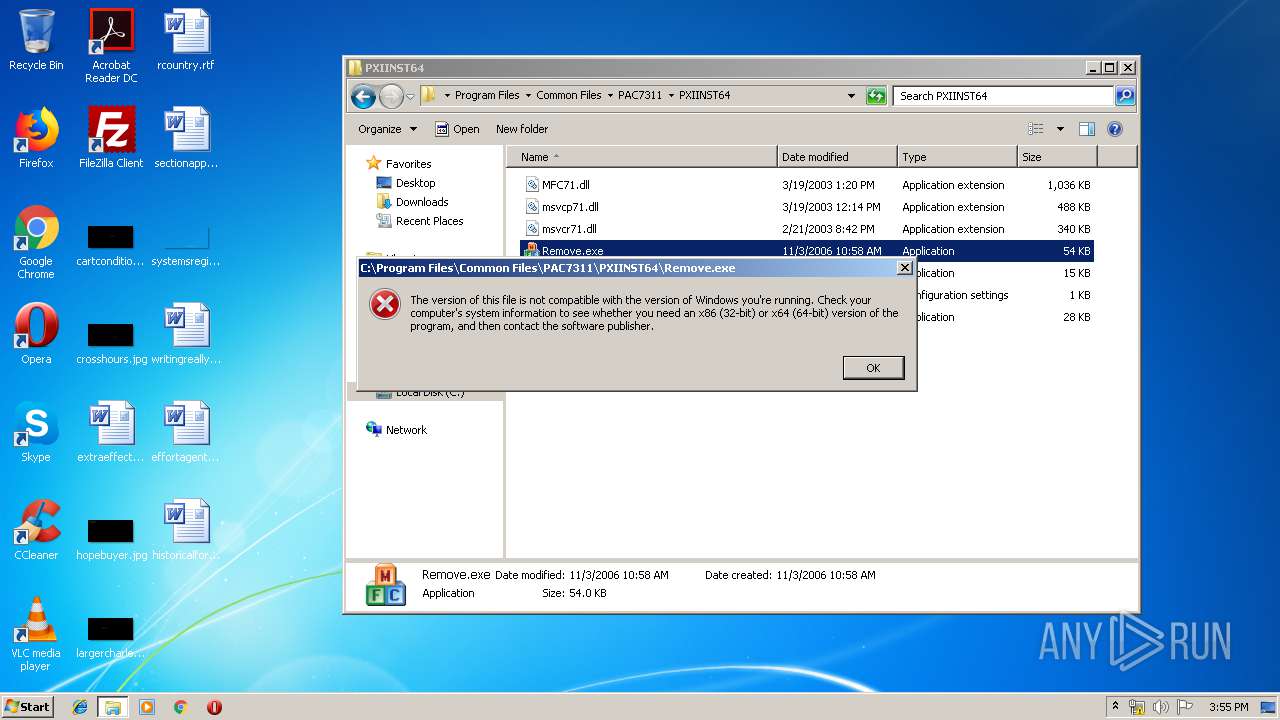
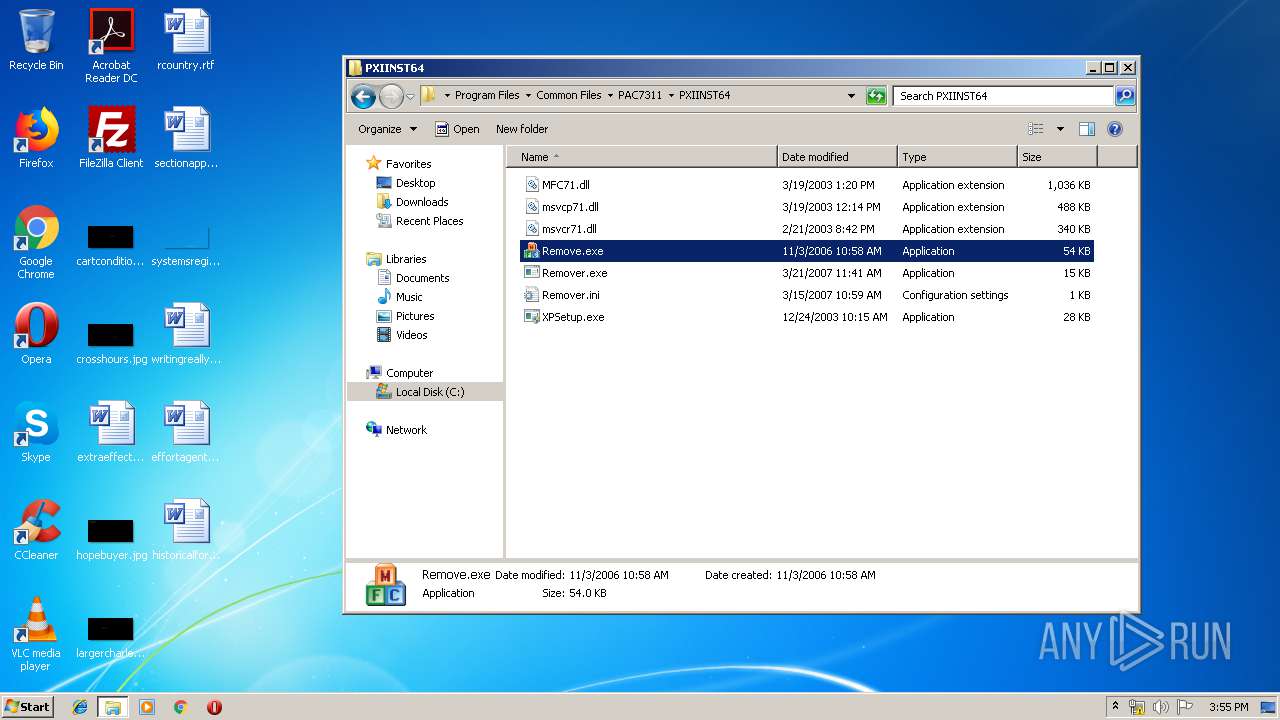
- Remove.exe (PID: 2364)
- XPSetup.exe (PID: 776)
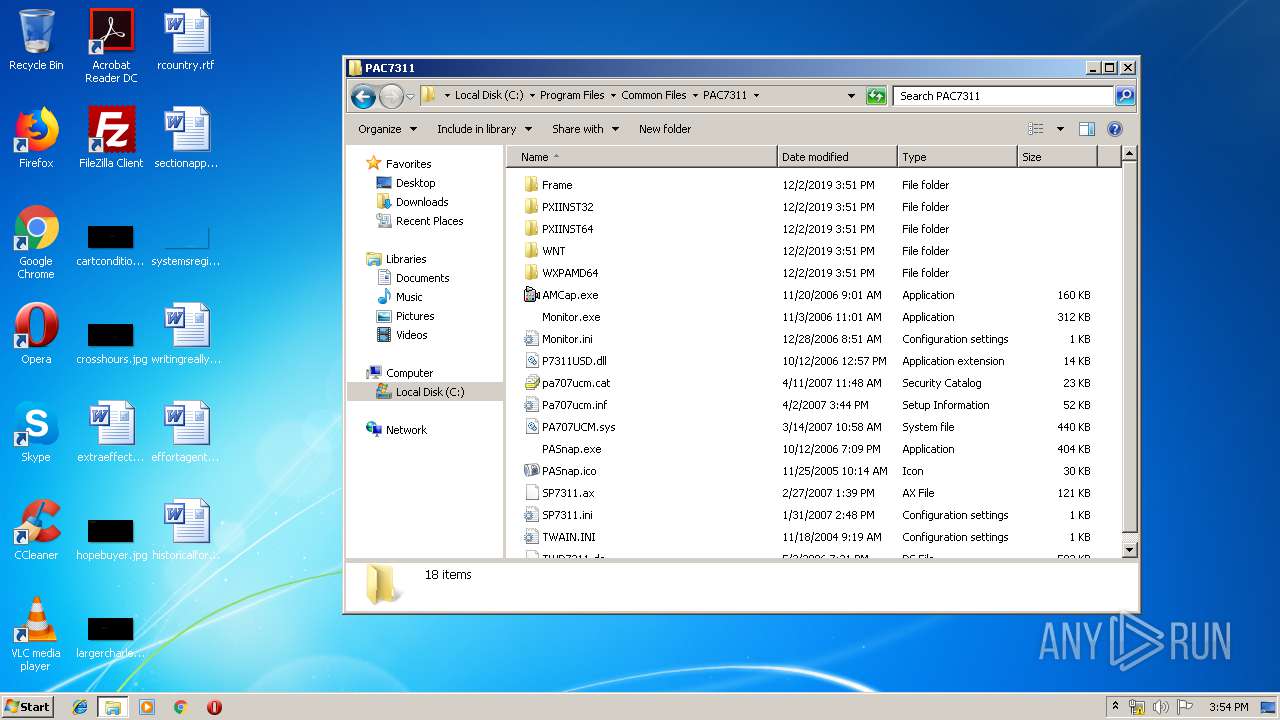
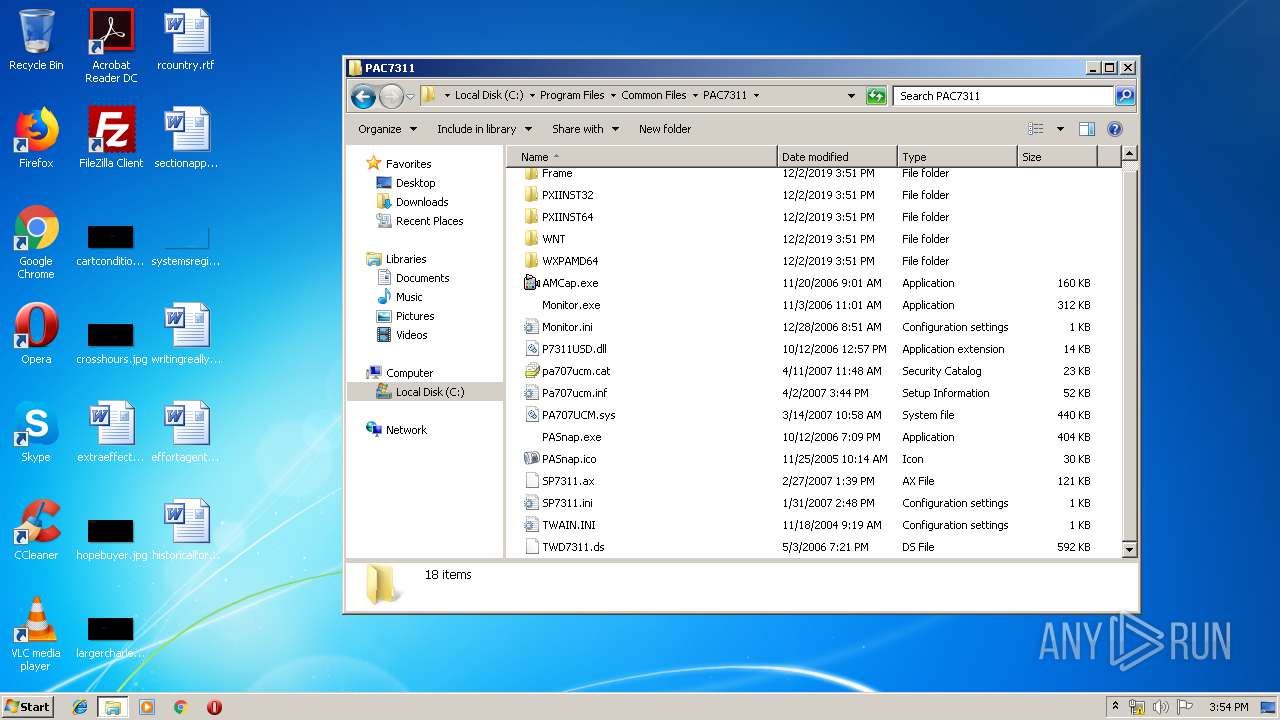
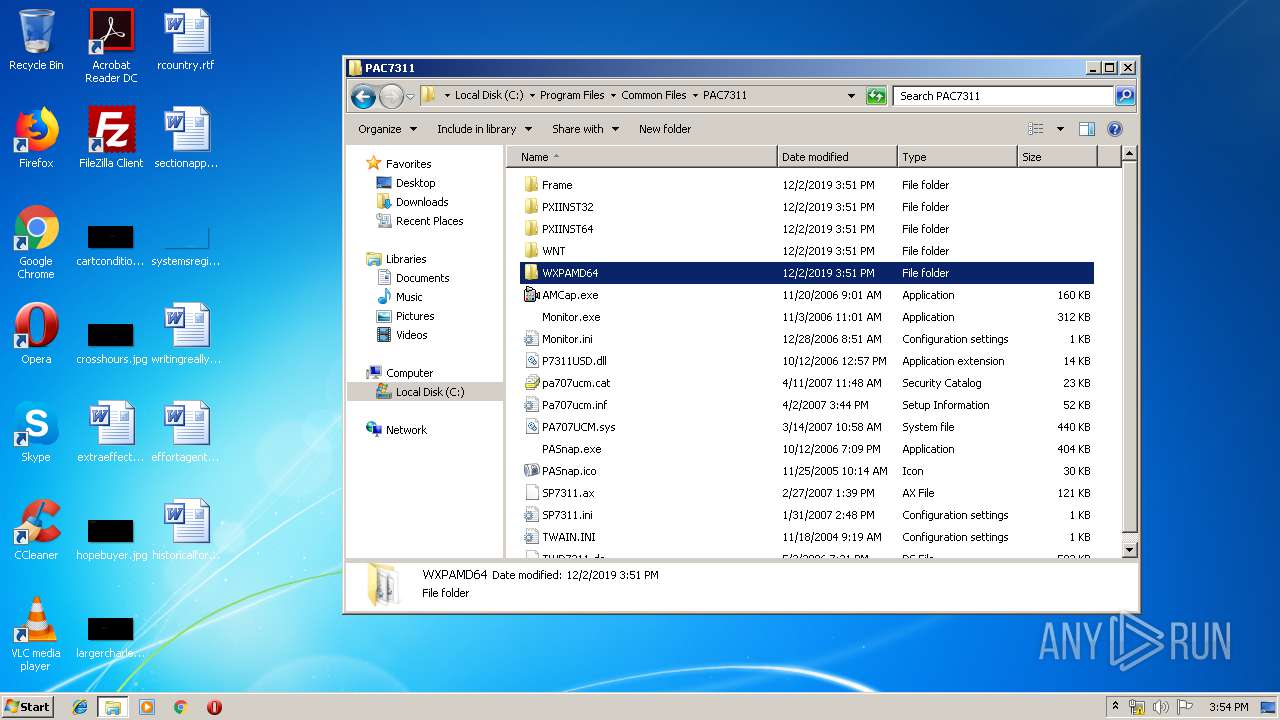
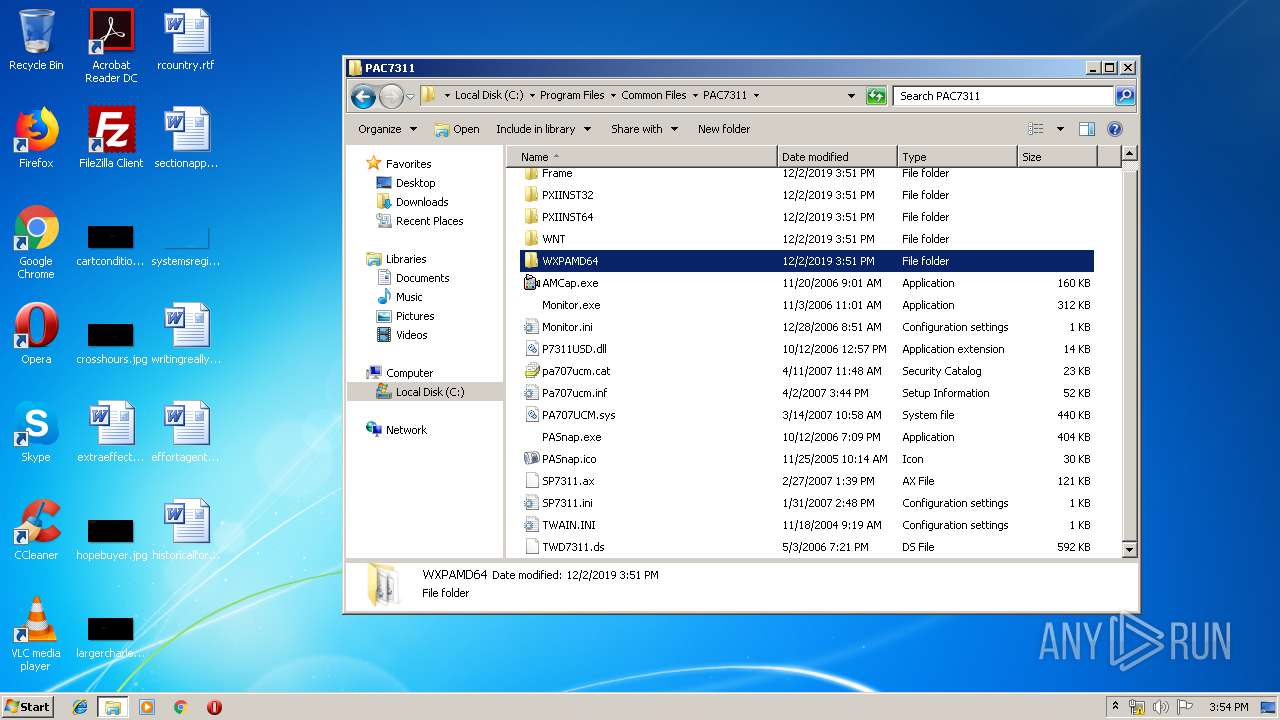
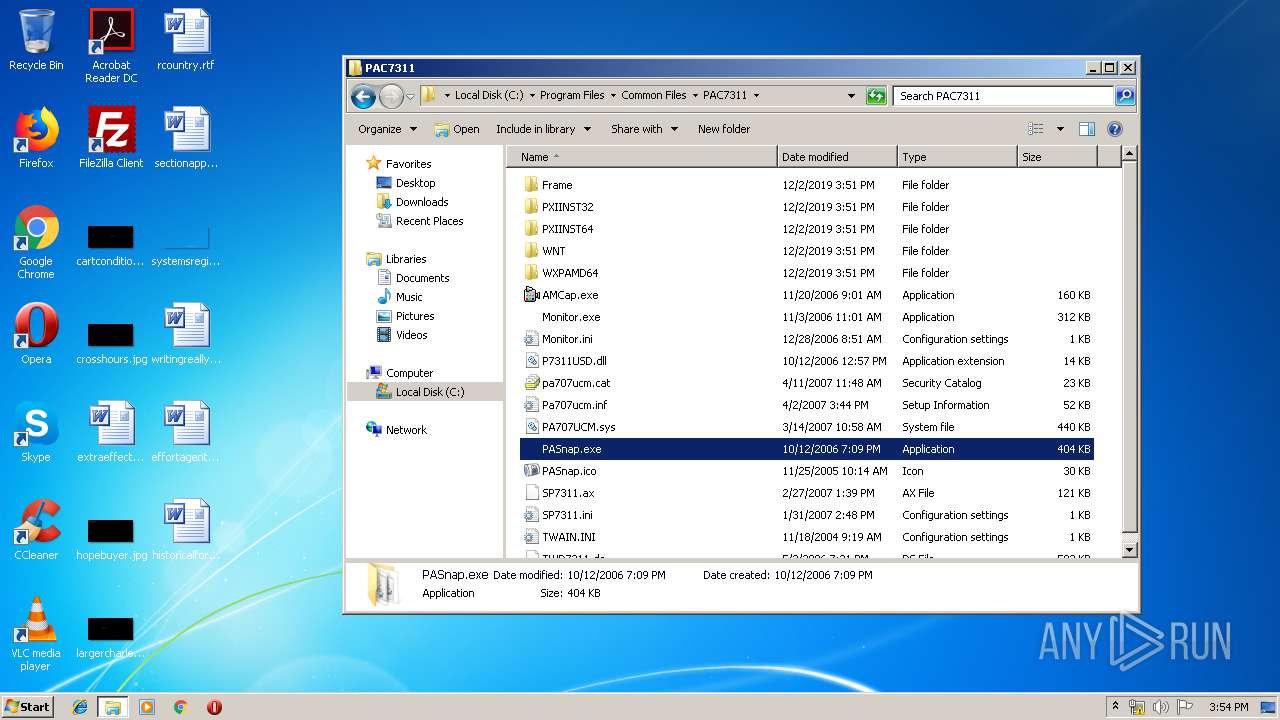
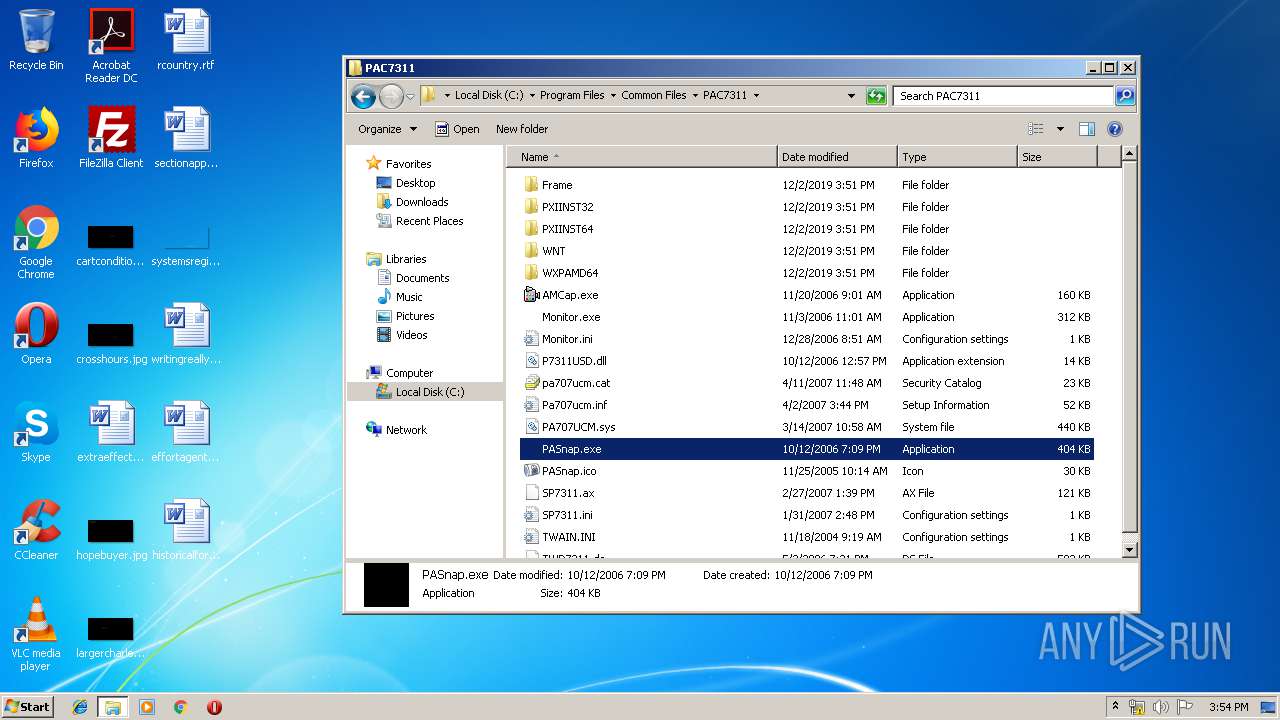
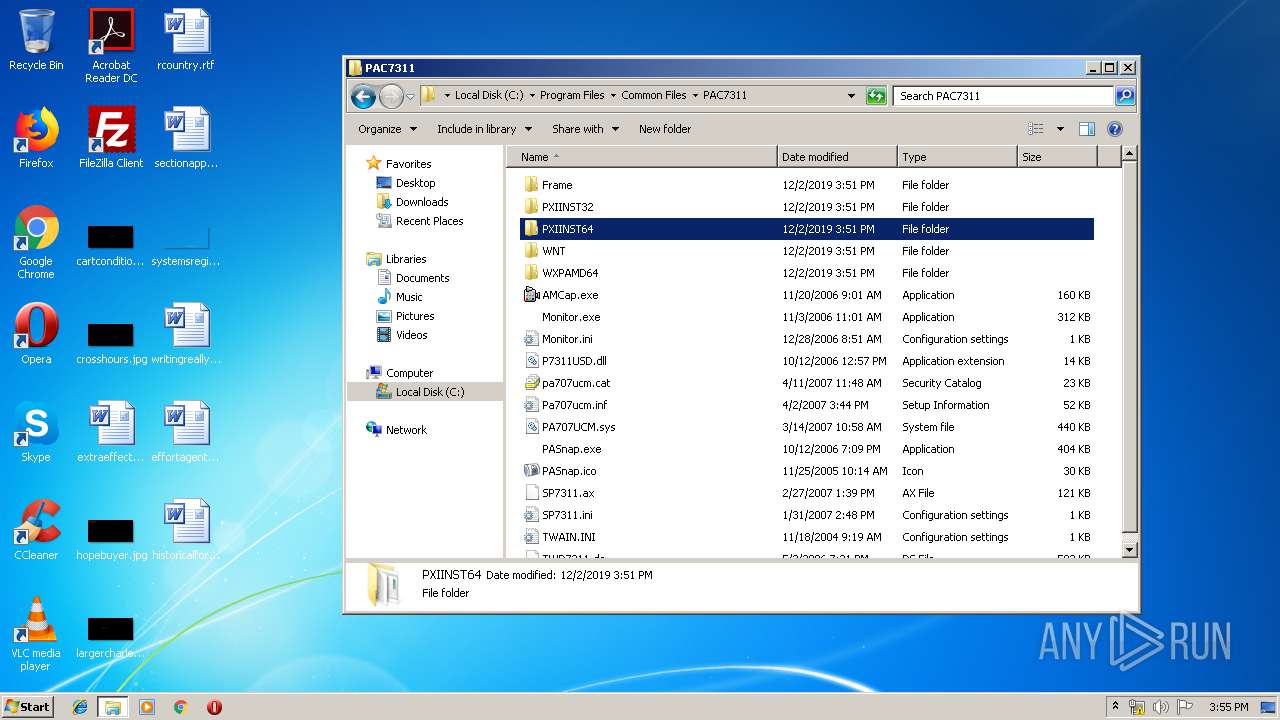
- PASnap.exe (PID: 3184)
- XPSetup.exe (PID: 1316)
- XPSetup.exe (PID: 2760)
- XPSetup.exe (PID: 2308)
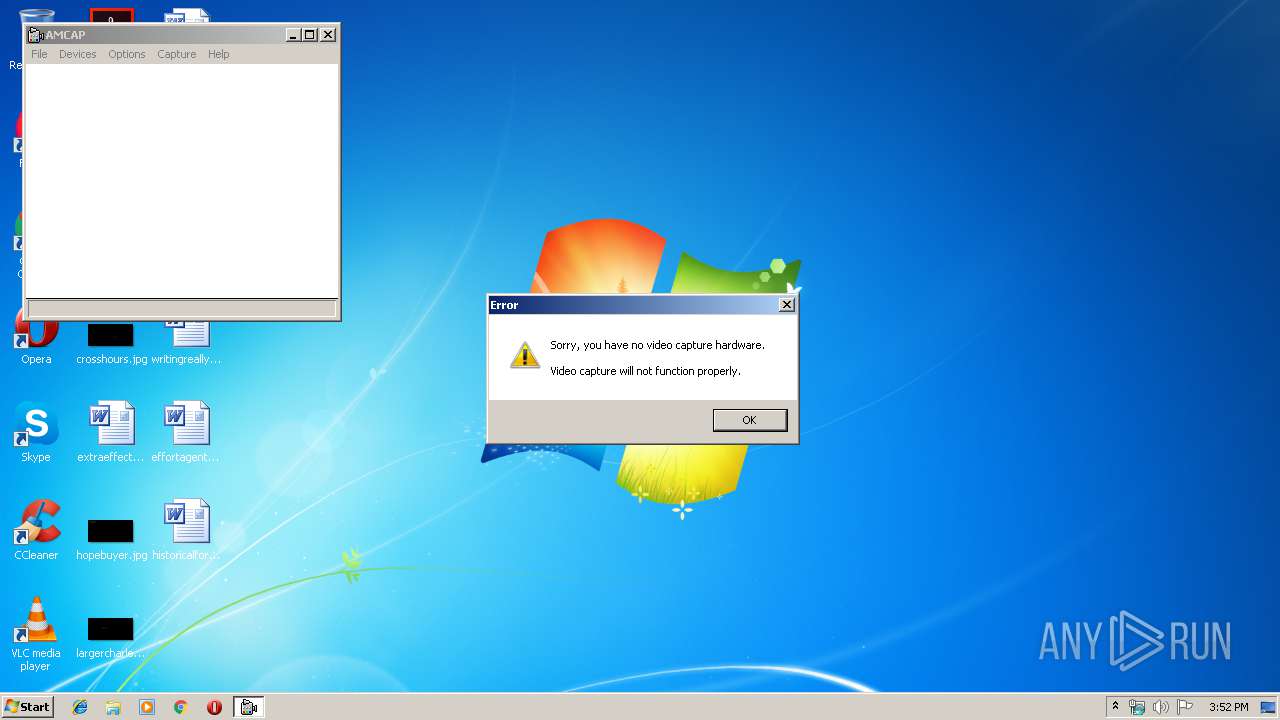
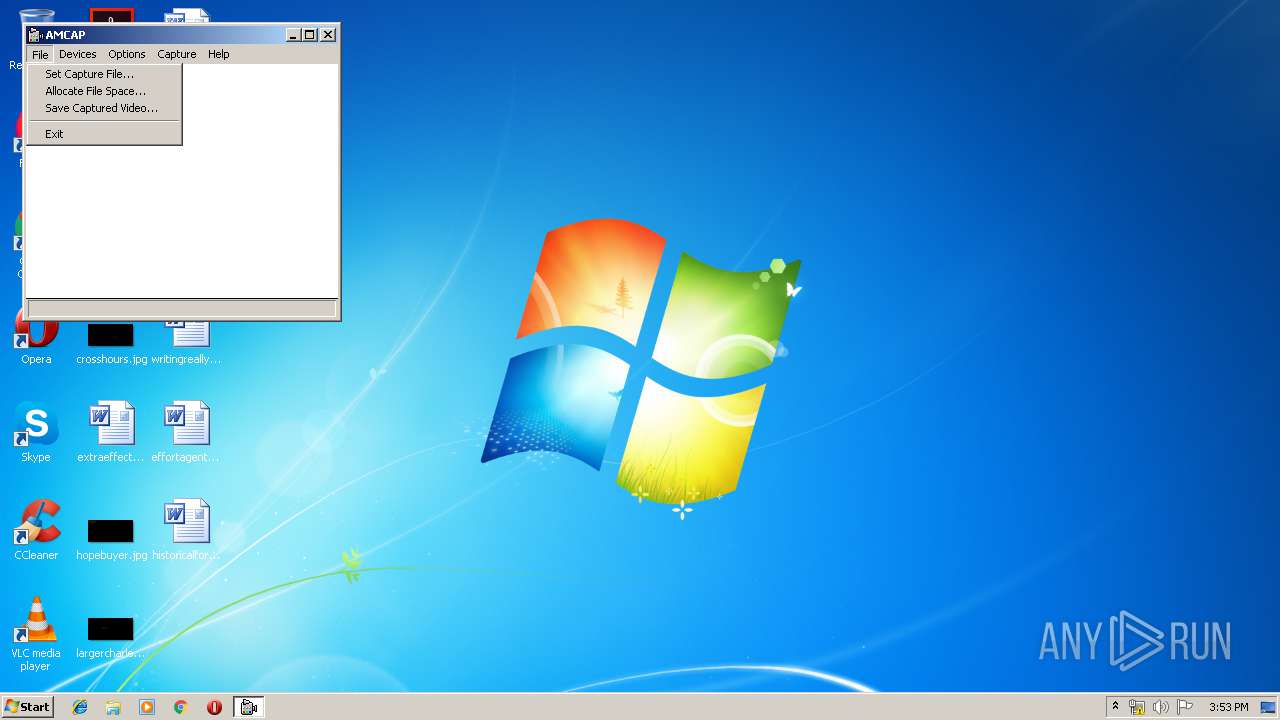
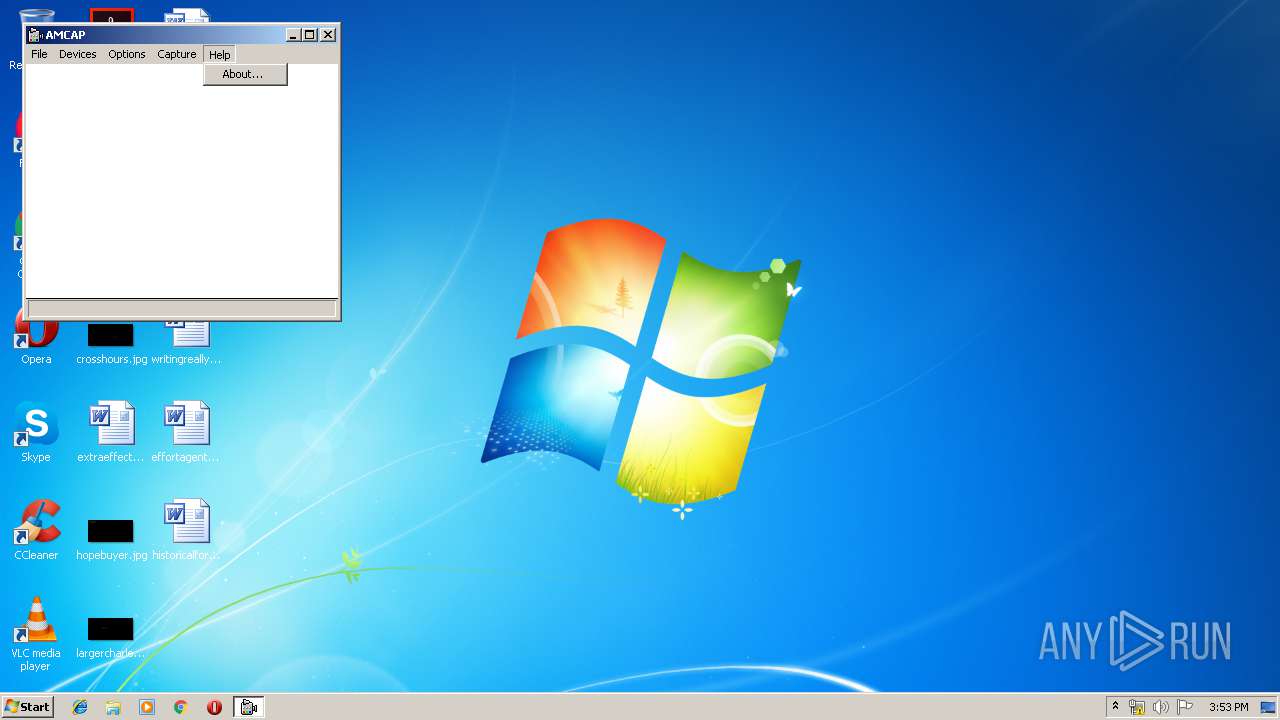
- AMCap.exe (PID: 2496)
Changes settings of System certificates
- msiexec.exe (PID: 2612)
Loads dropped or rewritten executable
- IDriver.exe (PID: 3760)
Starts NET.EXE for service management
- IDriver.exe (PID: 3760)
SUSPICIOUS
Executable content was dropped or overwritten
- 14383-02_02.exe (PID: 3188)
- msiexec.exe (PID: 2612)
- IDriver.exe (PID: 3760)
- XPSetup.exe (PID: 388)
- DrvInst.exe (PID: 184)
Adds / modifies Windows certificates
- msiexec.exe (PID: 2612)
Creates COM task schedule object
- msiexec.exe (PID: 2612)
Creates files in the Windows directory
- 14383-02_02.exe (PID: 3188)
- msiexec.exe (PID: 2612)
- DrvInst.exe (PID: 184)
Executed via COM
- IDriver.exe (PID: 1448)
- DllHost.exe (PID: 444)
- DrvInst.exe (PID: 184)
Executed as Windows Service
- vssvc.exe (PID: 2656)
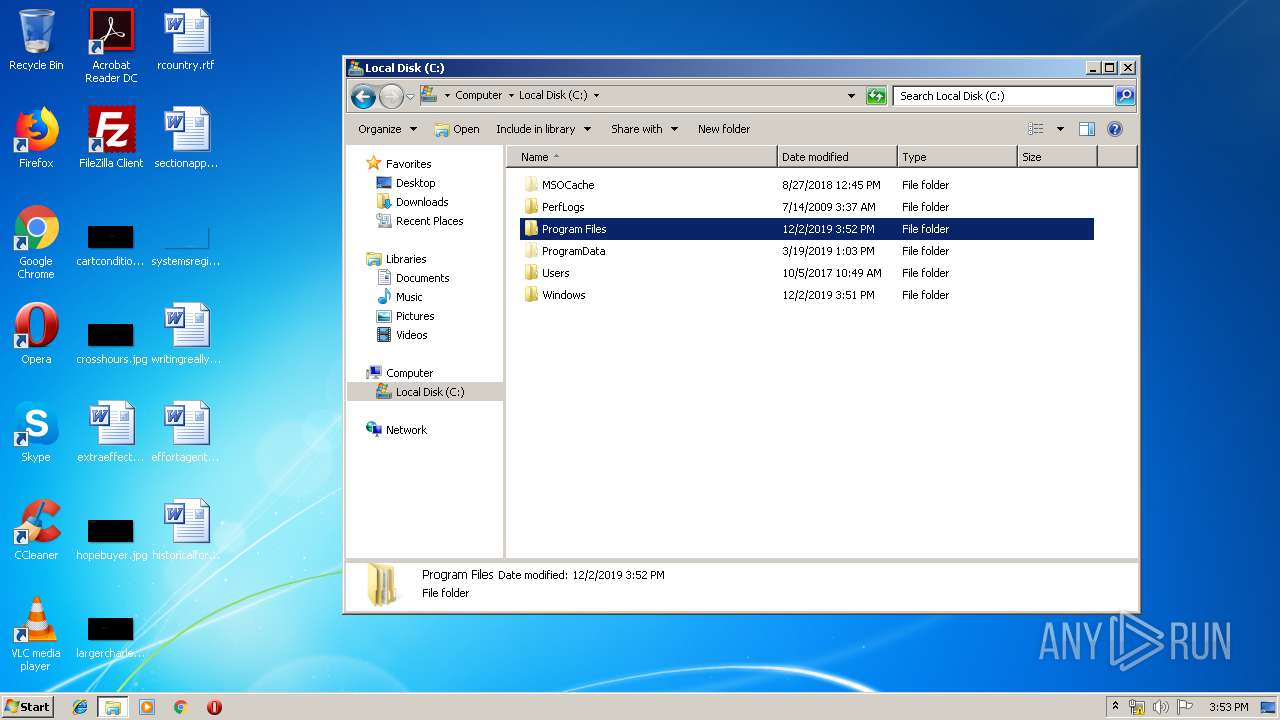
Searches for installed software
- IDriver.exe (PID: 3760)
Removes files from Windows directory
- DrvInst.exe (PID: 184)
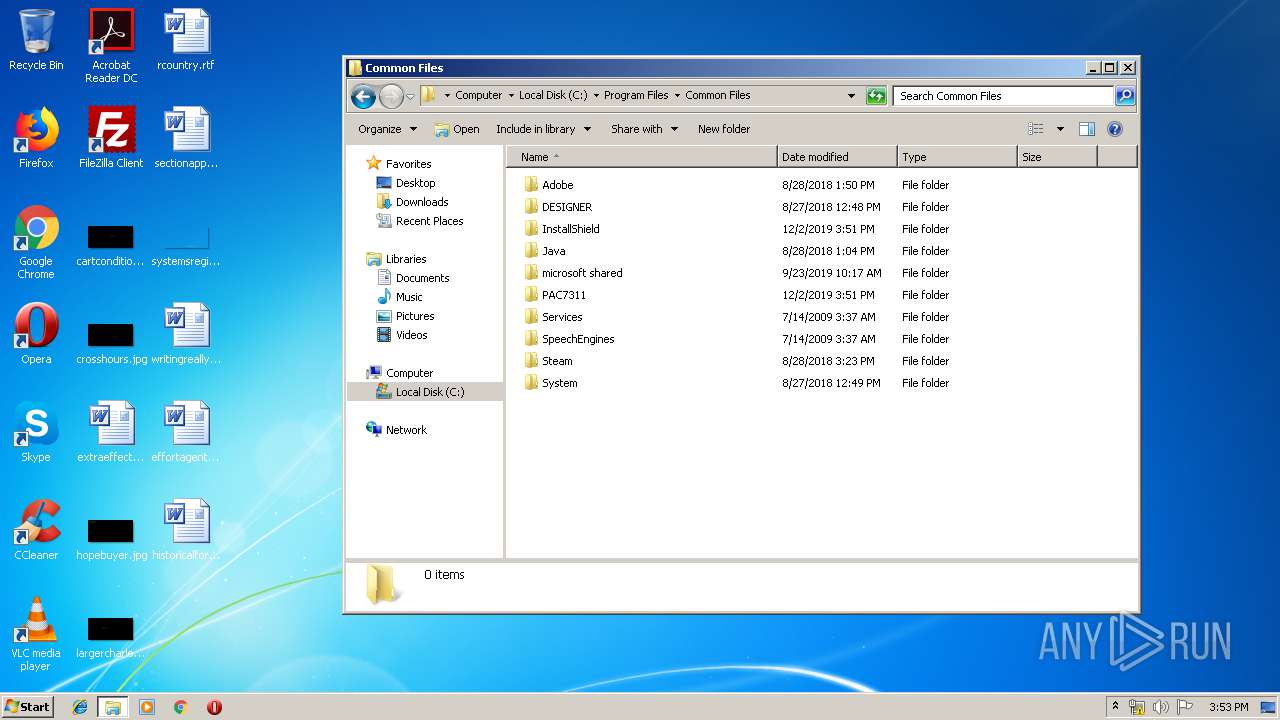
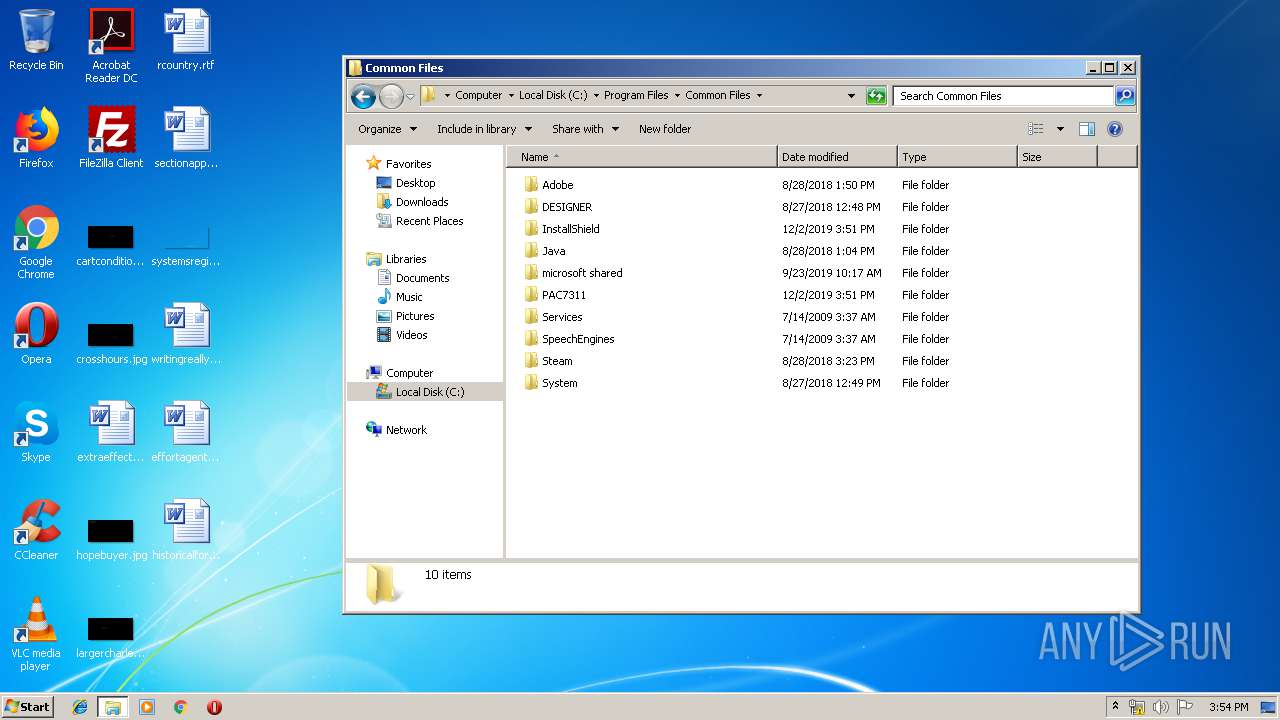
Creates files in the driver directory
- DrvInst.exe (PID: 184)
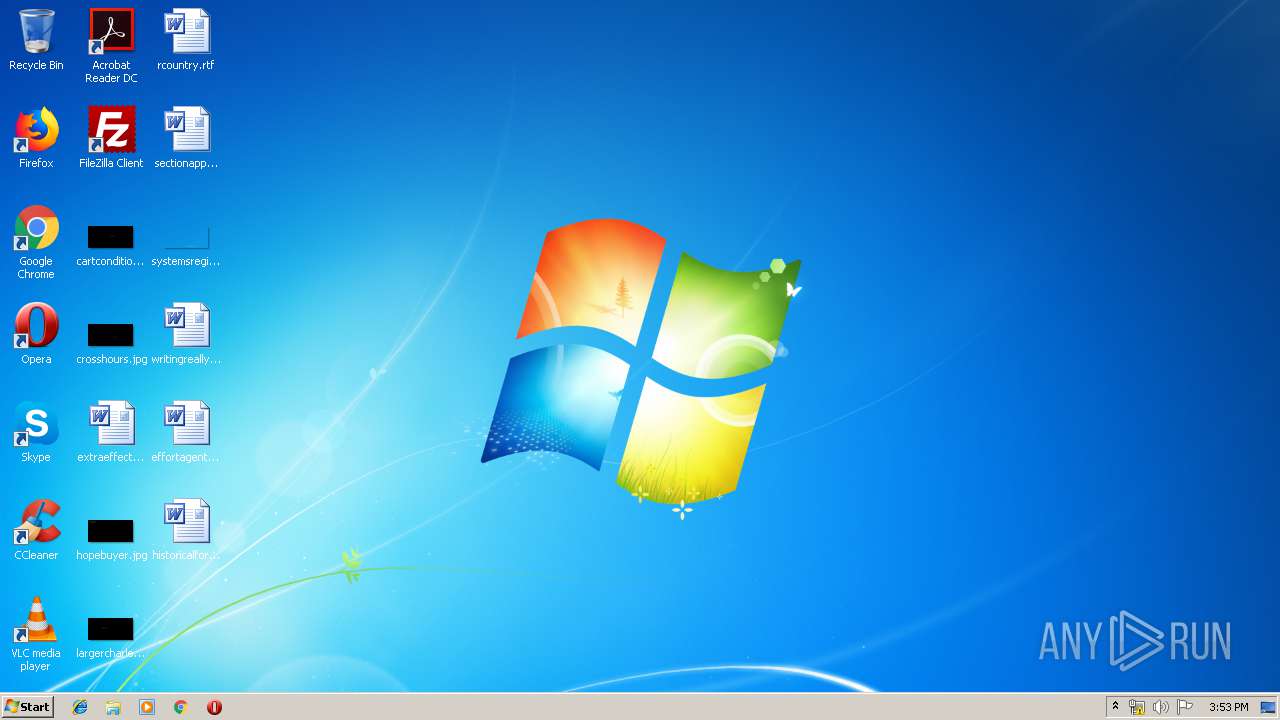
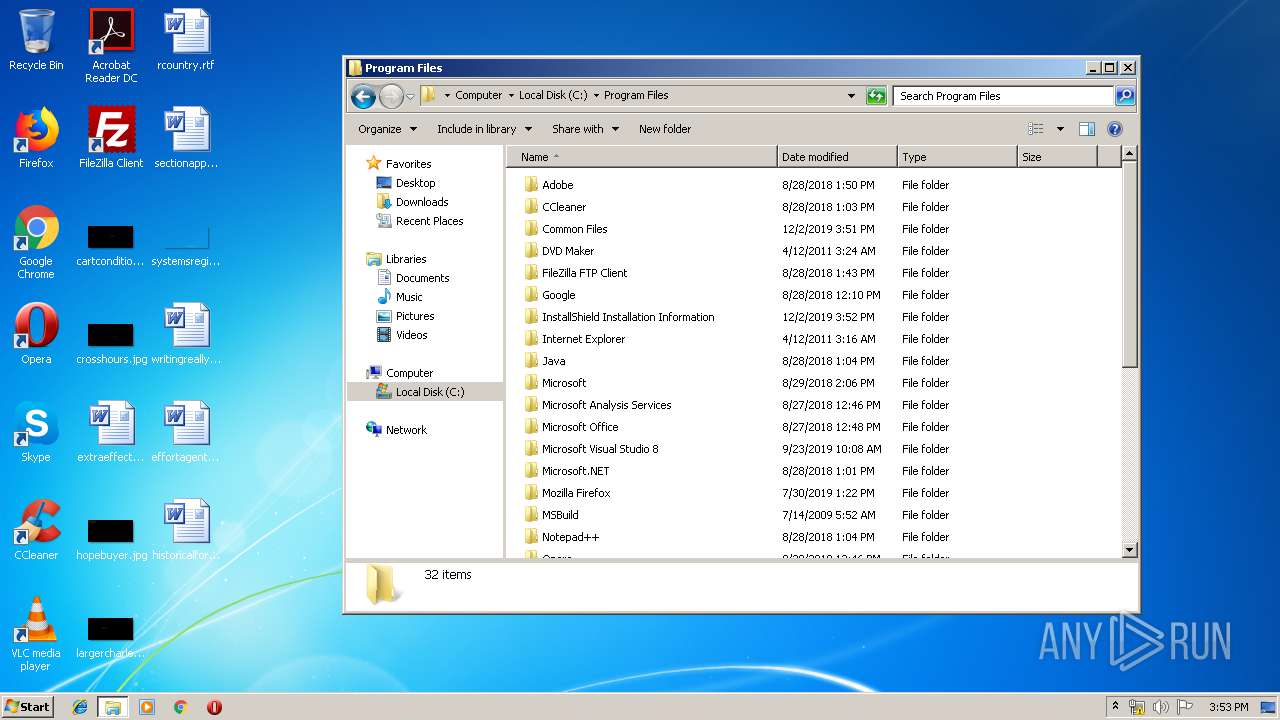
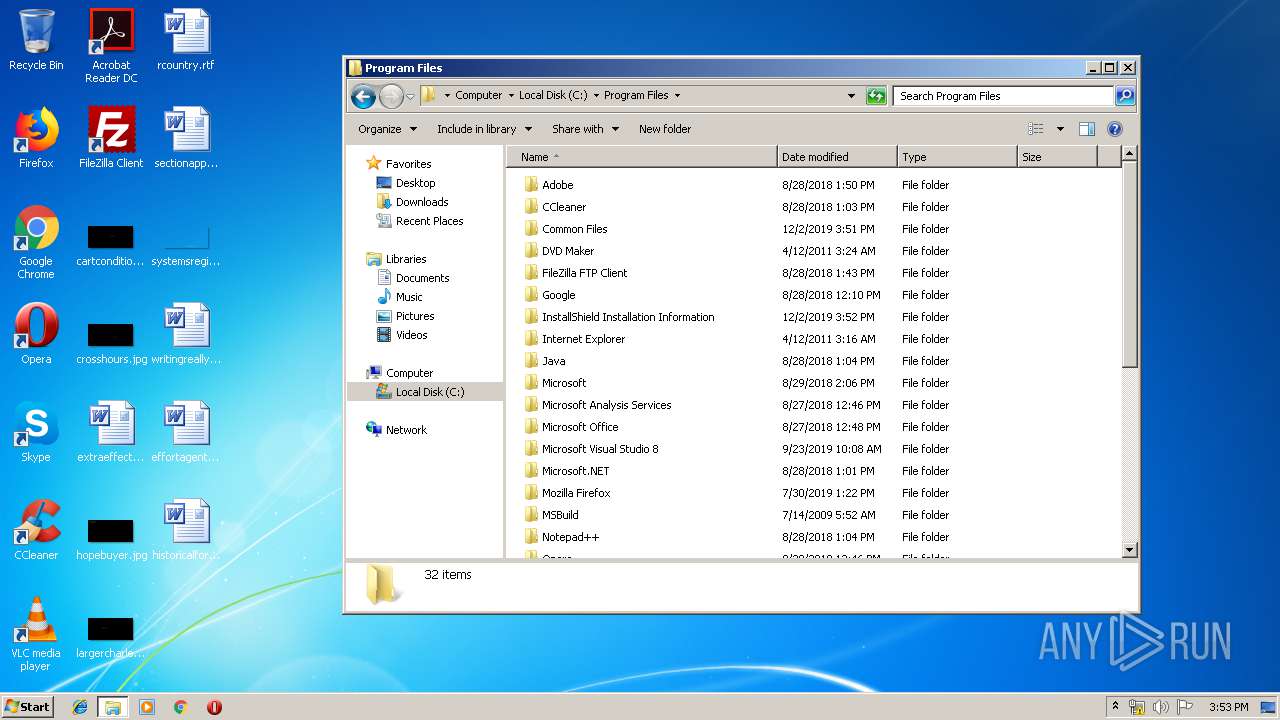
Creates files in the program directory
- IDriver.exe (PID: 3760)
Creates a software uninstall entry
- IDriver.exe (PID: 3760)
INFO
Creates files in the program directory
- msiexec.exe (PID: 2612)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2656)
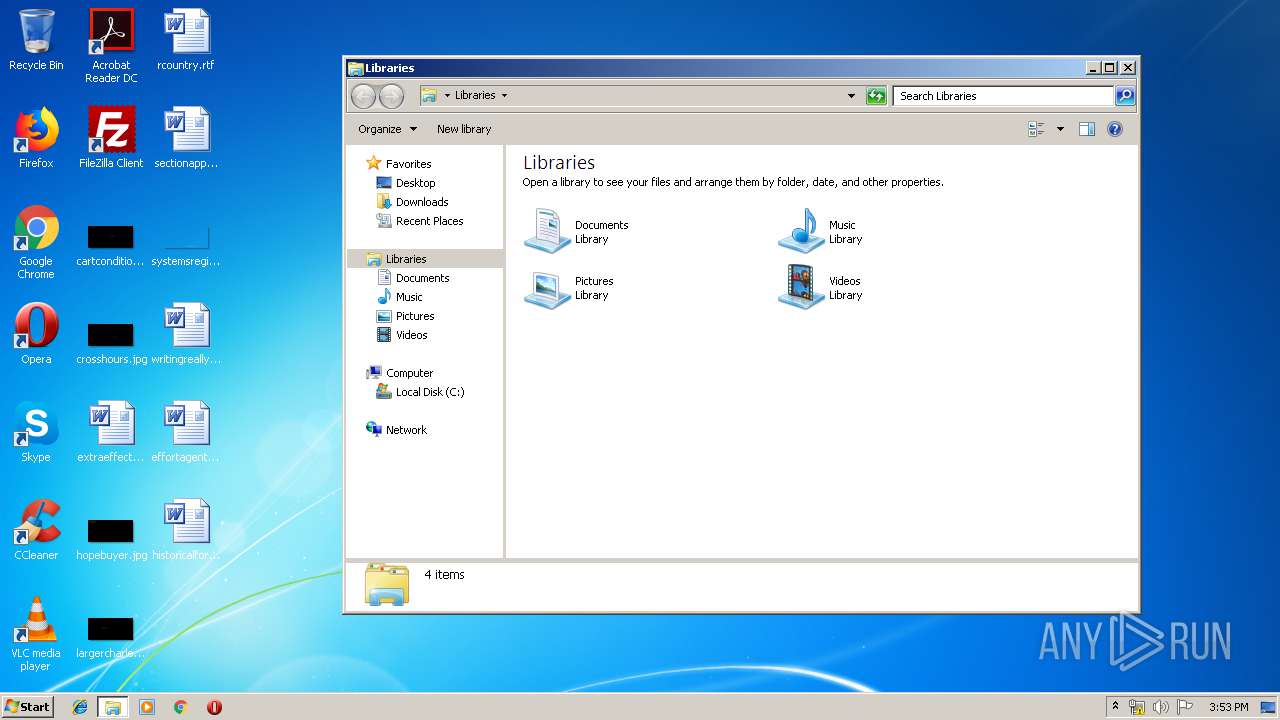
Application launched itself
- msiexec.exe (PID: 2612)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2896)
- MsiExec.exe (PID: 3452)
- MsiExec.exe (PID: 4072)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2612)
- DrvInst.exe (PID: 184)
- XPSetup.exe (PID: 388)
Creates a software uninstall entry
- msiexec.exe (PID: 2612)
Manual execution by user
- PASnap.exe (PID: 3184)
- XPSetup.exe (PID: 2760)
- AMCap.exe (PID: 2496)
- Remove.exe (PID: 2364)
- XPSetup.exe (PID: 776)
- explorer.exe (PID: 3992)
- XPSetup.exe (PID: 2308)
- XPSetup.exe (PID: 1316)
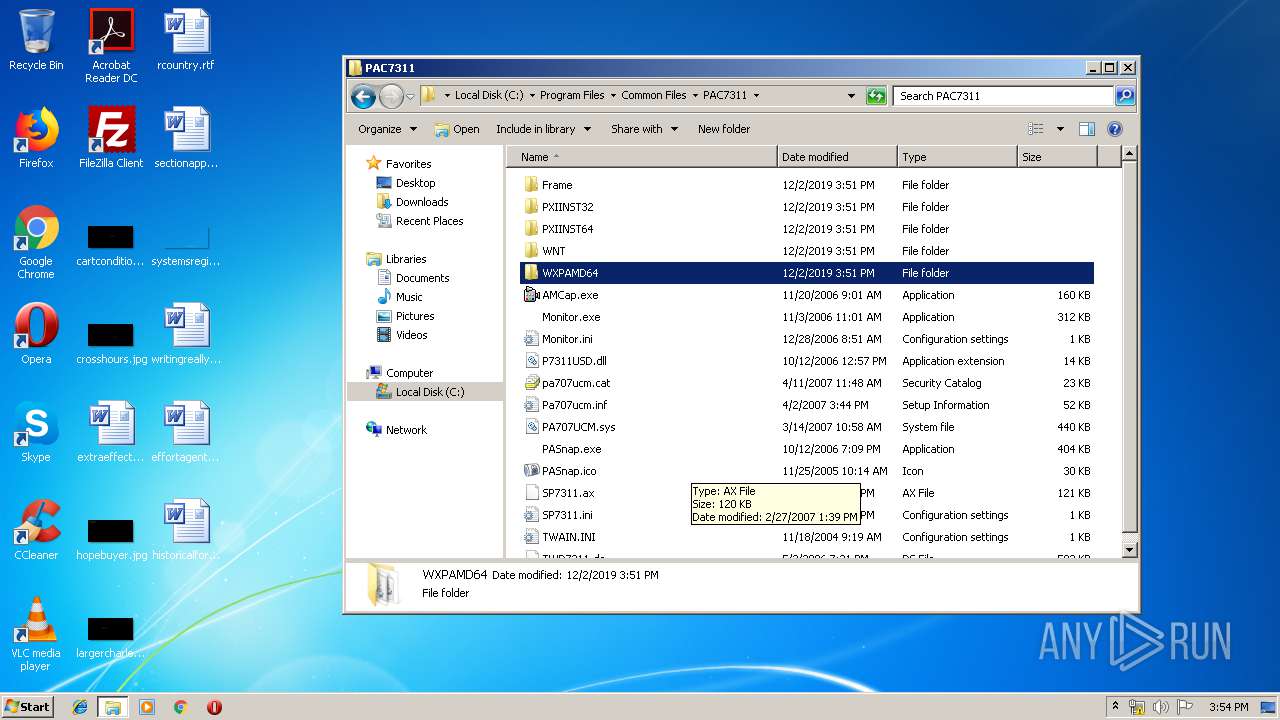
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
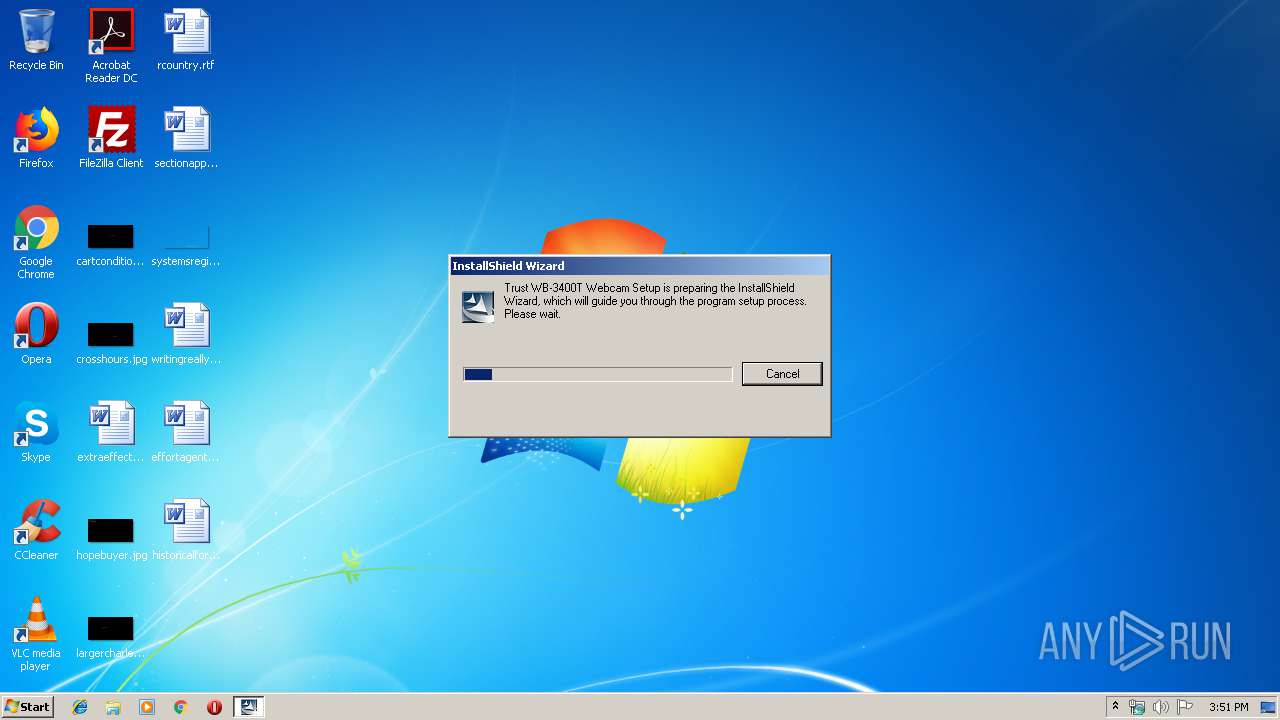
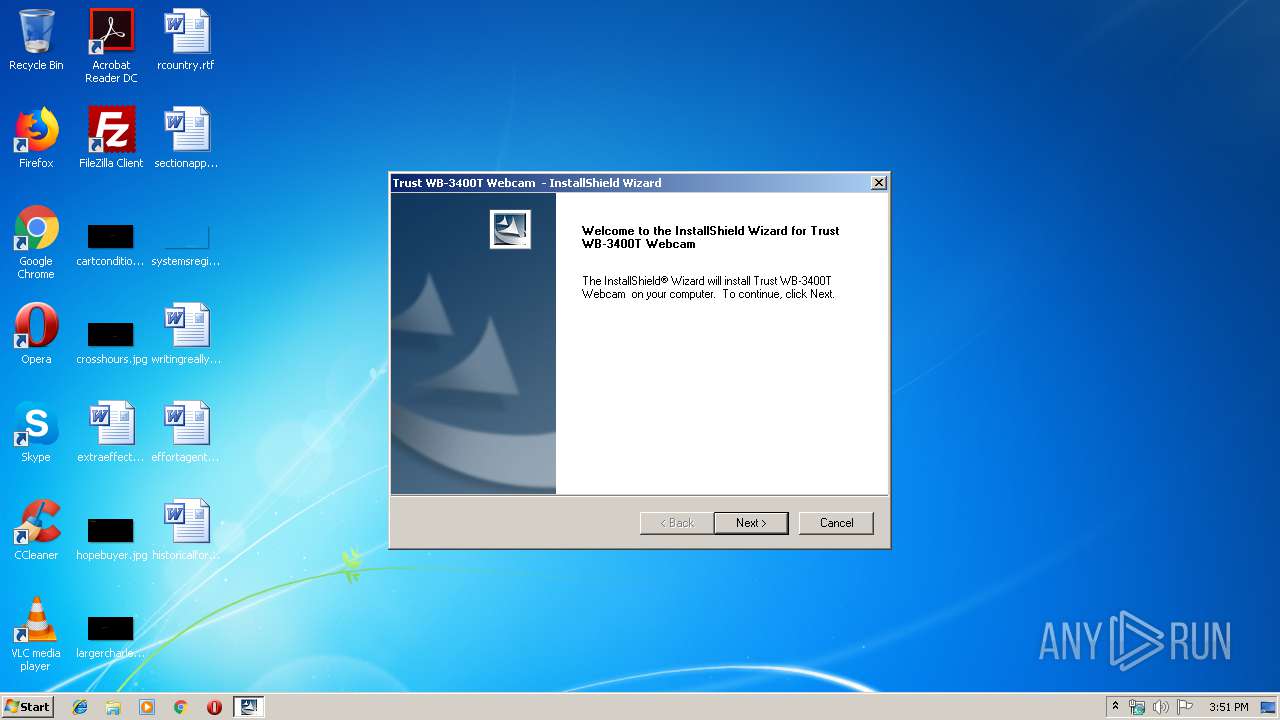
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:09:03 11:09:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 139264 |
| InitializedDataSize: | 106496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x194ec |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.333.0 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x0002 |
| FileFlags: | Pre-release |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | |
| CompanyName: | PC Camera |
| FileDescription: | Setup Launcher |
| FileVersion: | 1.0.2.13 |
| InternalName: | setup.exe |
| OriginalFileName: | setup.exe |
| LegalCopyright: | Copyright (C) 2004 InstallShield Software Corp. |
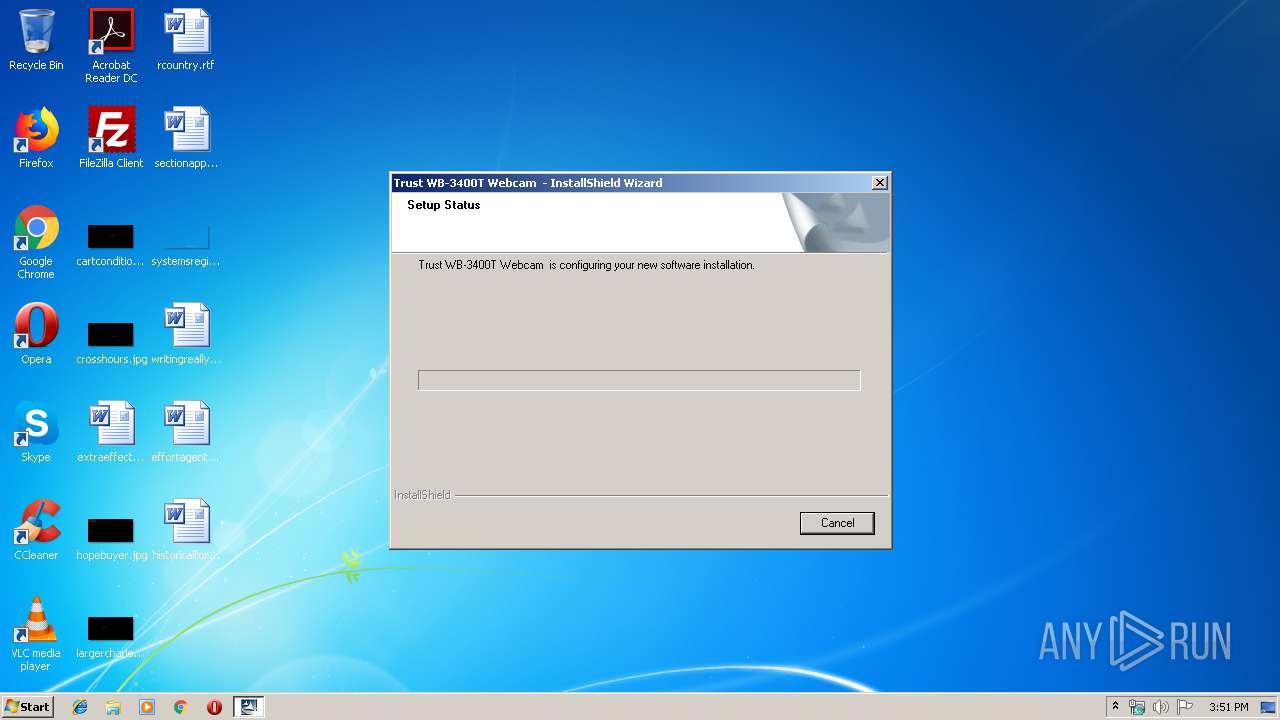
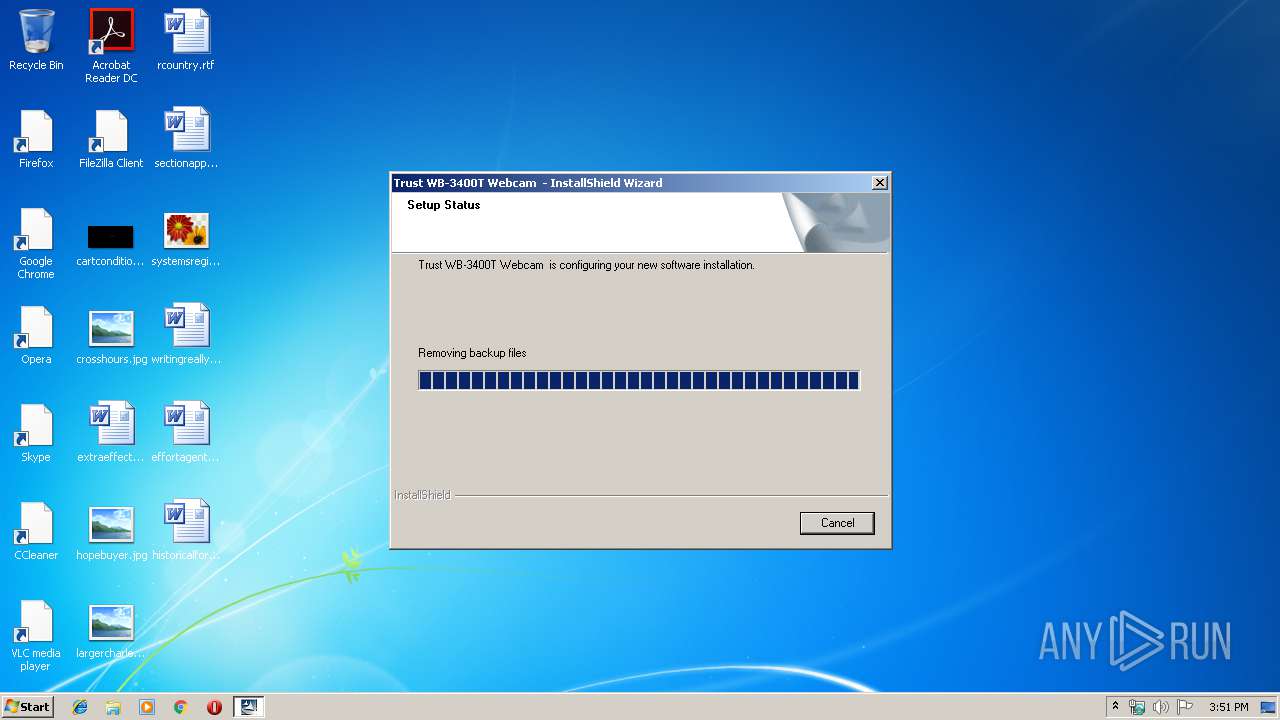
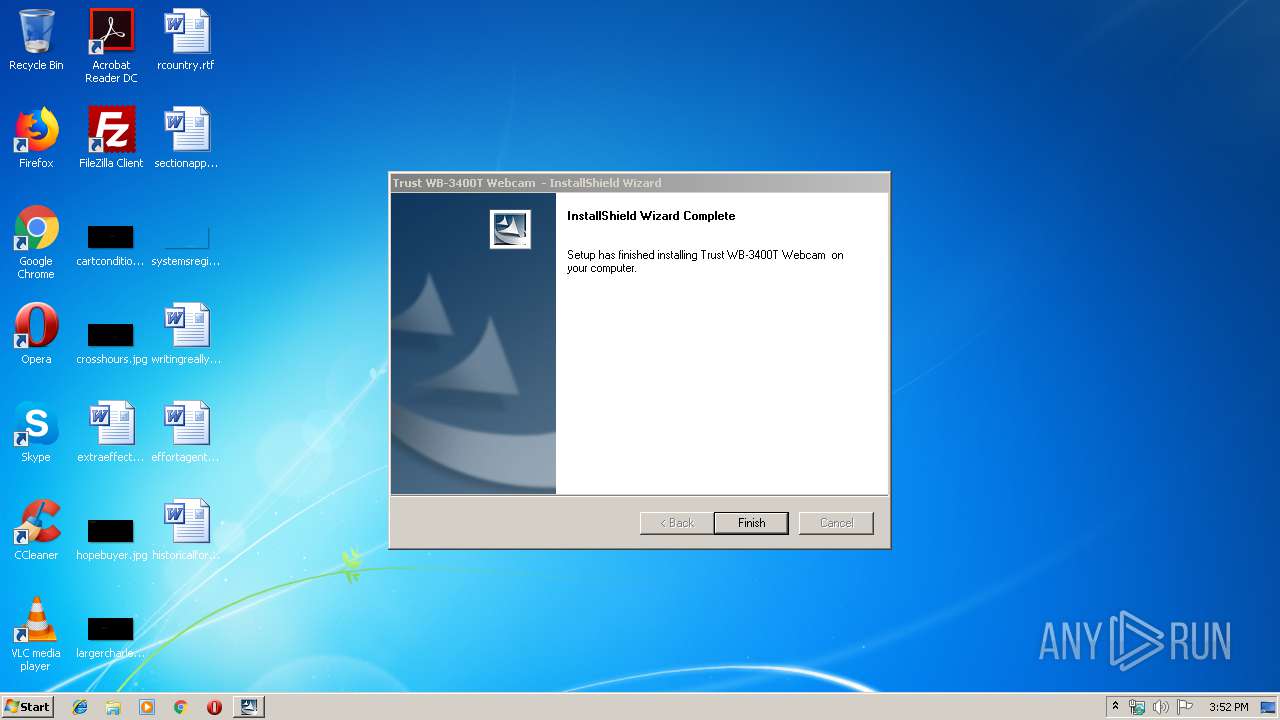
| ProductName: | Trust WB-3400T Webcam |
| ProductVersion: | 1.0.2.13 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Sep-2003 09:09:31 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | PC Camera |
| FileDescription: | Setup Launcher |
| FileVersion: | 1.0.2.13 |
| InternalName: | setup.exe |
| OriginalFilename: | setup.exe |
| LegalCopyright: | Copyright (C) 2004 InstallShield Software Corp. |
| ProductName: | Trust WB-3400T Webcam |
| ProductVersion: | 1.0.2.13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Sep-2003 09:09:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00021E5E | 0x00022000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54983 |
.rdata | 0x00023000 | 0x00004170 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.77312 |
.data | 0x00028000 | 0x00009298 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.1623 |
.rsrc | 0x00032000 | 0x0000A2E0 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.23947 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87924 | 666 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.39652 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.9625 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 6.7616 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.48972 | 308 | UNKNOWN | English - United States | RT_CURSOR |
69 | 2.47806 | 110 | UNKNOWN | English - United States | RT_STRING |
72 | 2.32551 | 110 | UNKNOWN | English - United States | RT_STRING |
73 | 2.76648 | 204 | UNKNOWN | English - United States | RT_STRING |
100 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.01924 | 20 | UNKNOWN | English - United States | RT_GROUP_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
80
Monitored processes
24
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
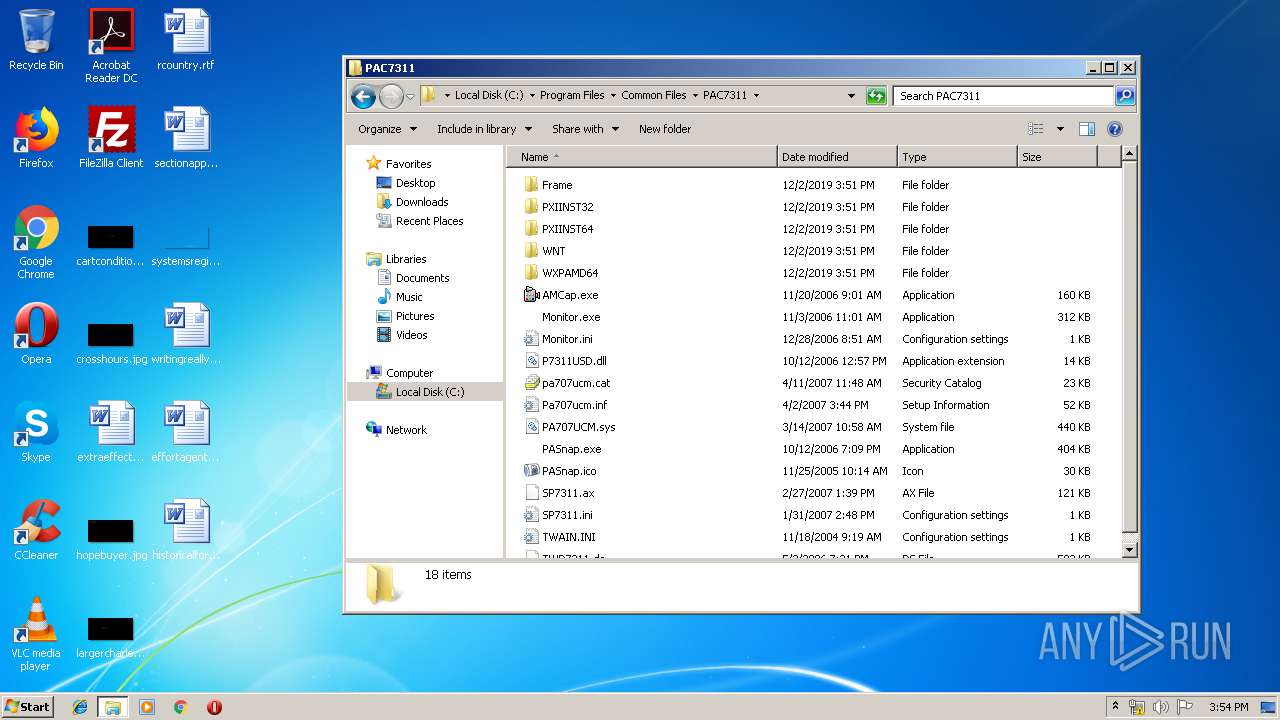
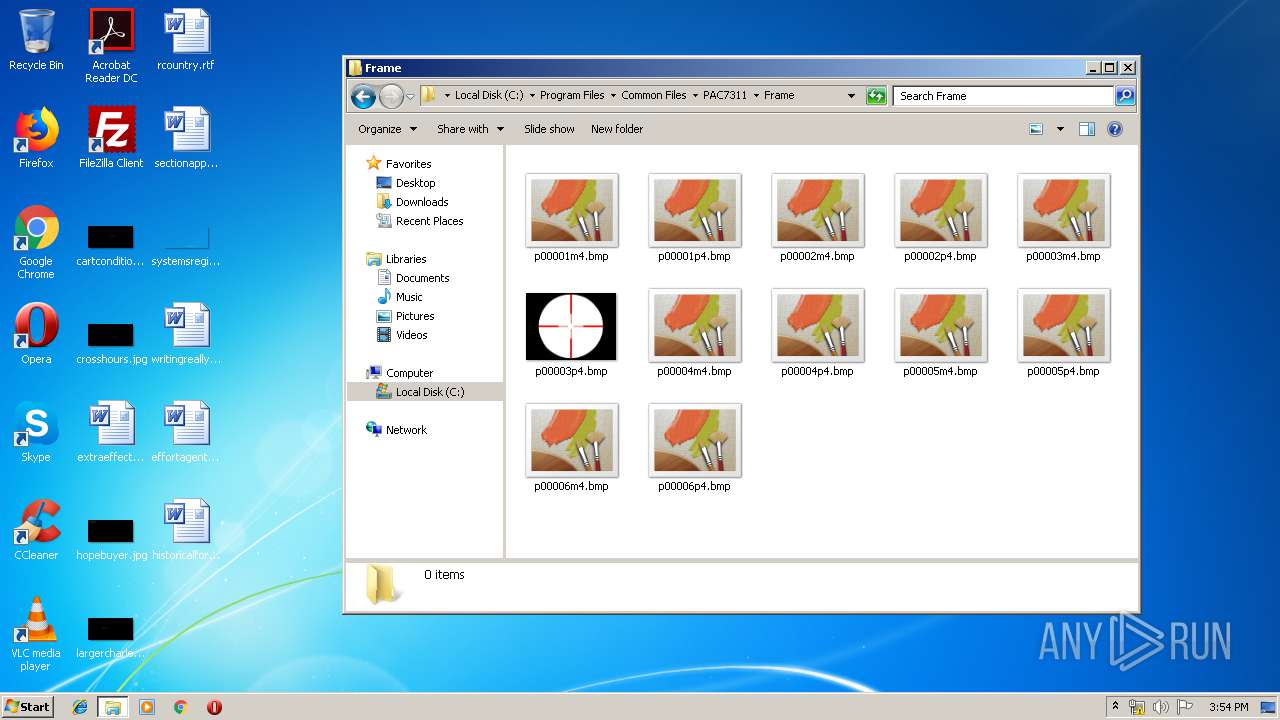
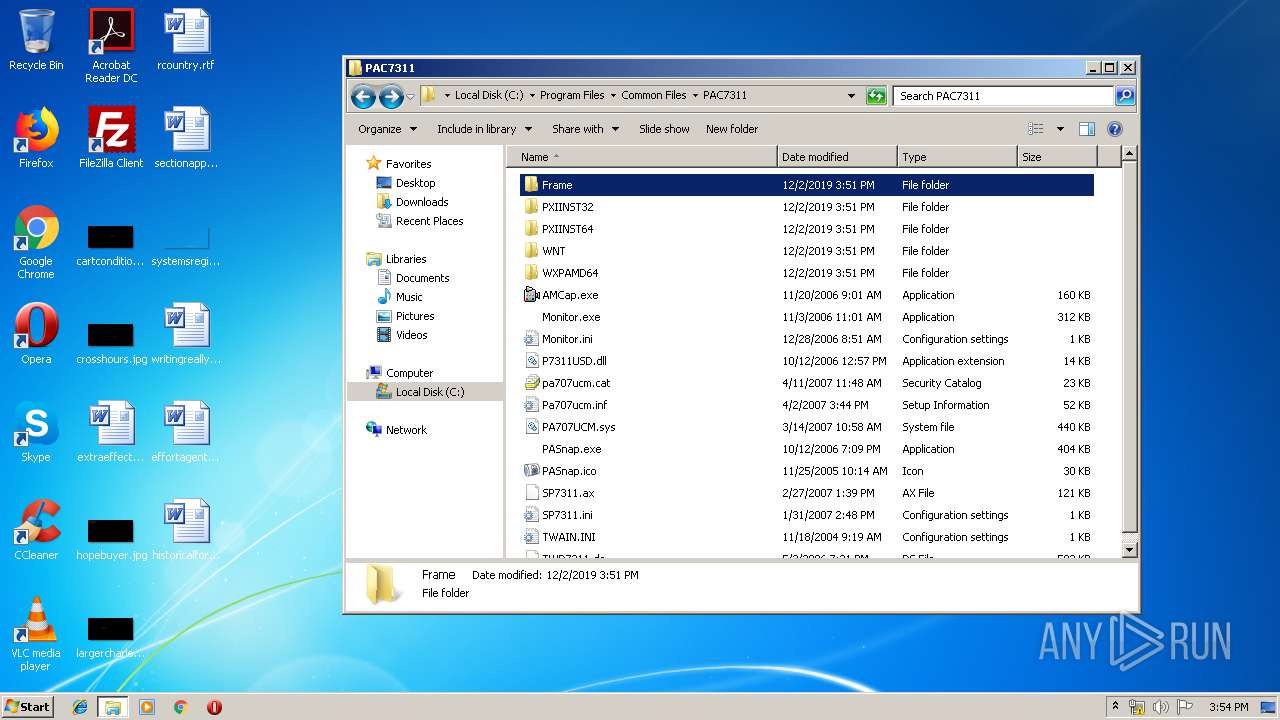
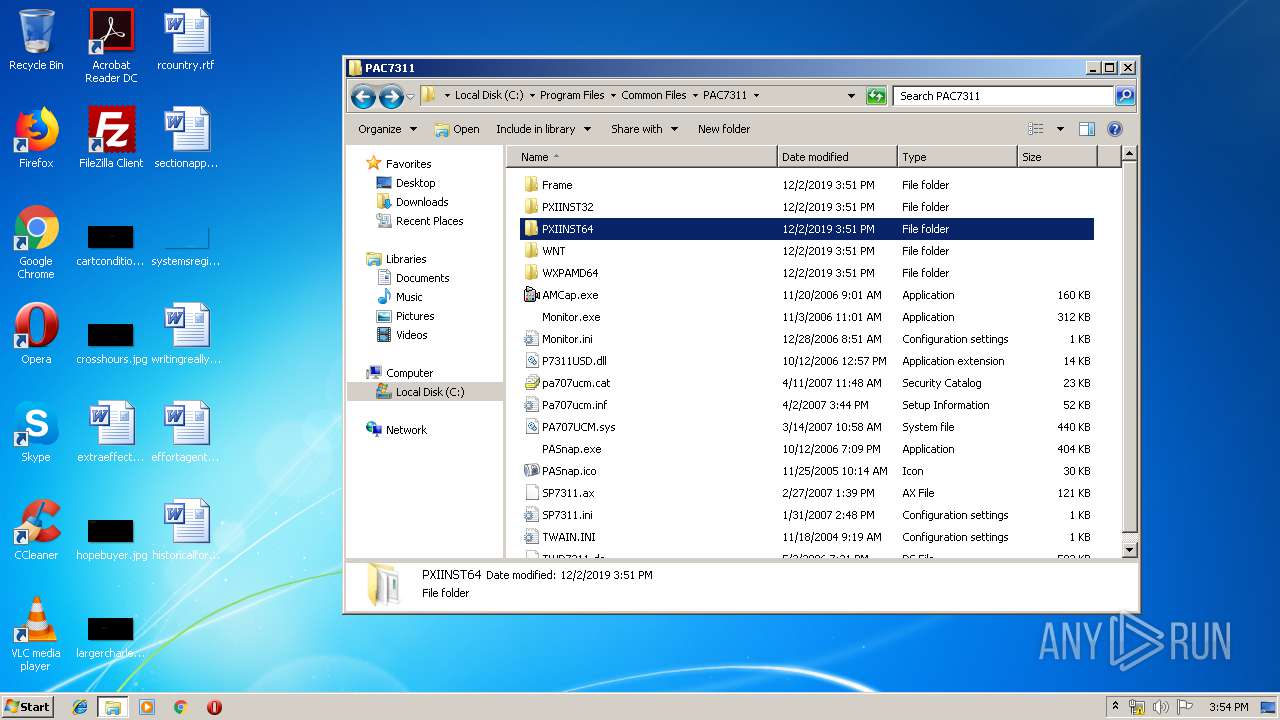
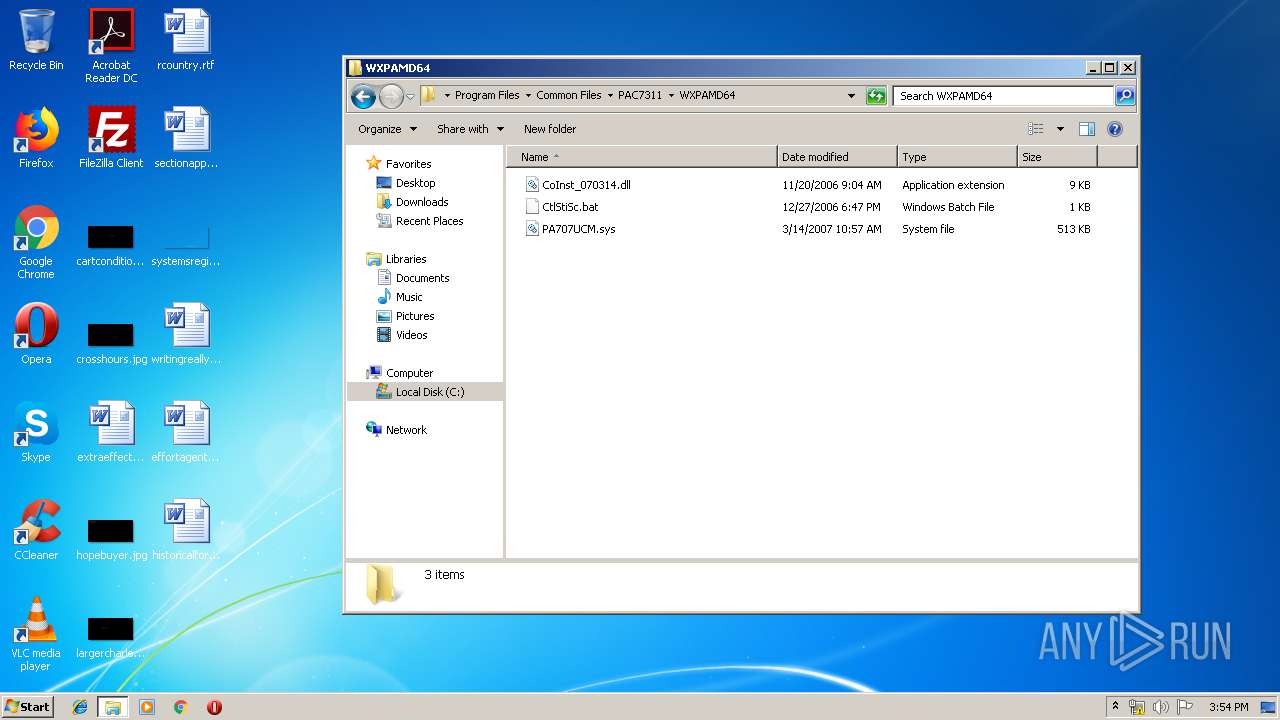
| 184 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{34f2b236-179f-3879-d9be-ac4fac7dd22b}\Pa707ucm.inf" "0" "69d4997e7" "000003E4" "WinSta0\Default" "000005A4" "208" "C:\Program Files\Common Files\PAC7311" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
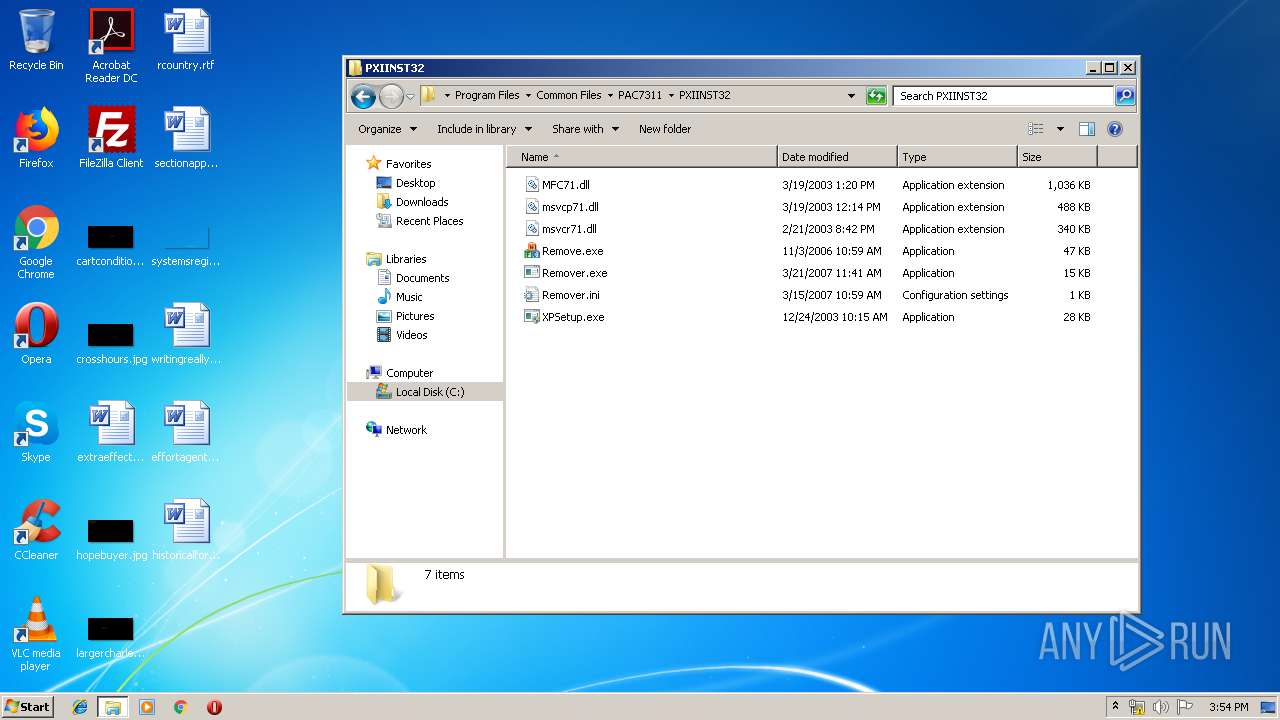
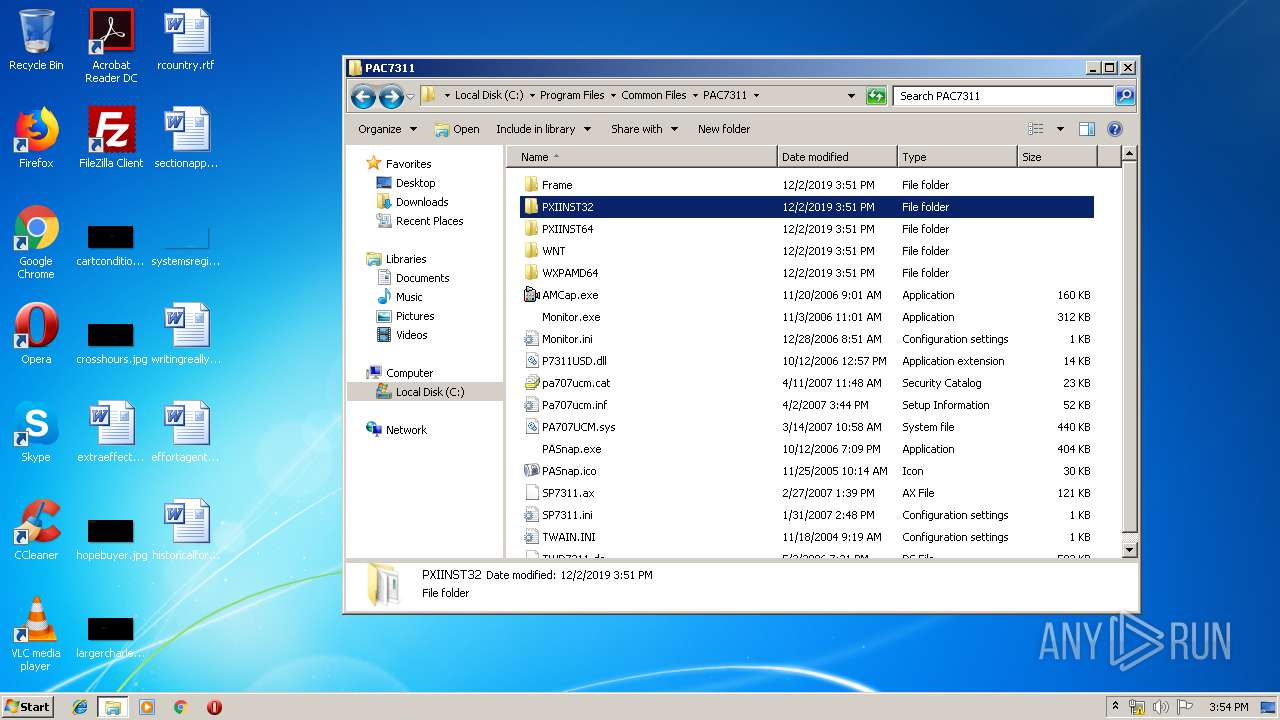
| 388 | "C:\Program Files\Common Files\PAC7311\PXIINST32\XPSetup.exe" C:\Program Files\Common Files\PAC7311\Pa707ucm.inf | C:\Program Files\Common Files\PAC7311\PXIINST32\XPSetup.exe | IDriver.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 444 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | "C:\Program Files\Common Files\PAC7311\PXIINST32\XPSetup.exe" | C:\Program Files\Common Files\PAC7311\PXIINST32\XPSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1316 | C:\Windows\system32\net1 stop stisvc | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Common Files\PAC7311\PXIINST64\XPSetup.exe" | C:\Program Files\Common Files\PAC7311\PXIINST64\XPSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1448 | C:\PROGRA~1\COMMON~1\INSTAL~1\Driver\9\INTEL3~1\IDriver.exe -Embedding | C:\PROGRA~1\COMMON~1\INSTAL~1\Driver\9\INTEL3~1\IDriver.exe | — | svchost.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: MEDIUM Description: InstallDriver Module Exit code: 3221226540 Version: 9.01.429 Modules
| |||||||||||||||
| 1952 | C:\Windows\System32\net.exe start stisvc | C:\Windows\System32\net.exe | — | IDriver.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Common Files\PAC7311\PXIINST64\XPSetup.exe" | C:\Program Files\Common Files\PAC7311\PXIINST64\XPSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Common Files\PAC7311\PXIINST32\Remove.exe" | C:\Program Files\Common Files\PAC7311\PXIINST32\Remove.exe | — | explorer.exe | |||||||||||
User: admin Company: PixArt Imaging Incorporation Integrity Level: MEDIUM Description: Driver Remover Exit code: 1006 Version: 0003.0002.2006.1103 Modules
| |||||||||||||||
Total events
1 849
Read events
936
Write events
887
Delete events
26
Modification events
| (PID) Process: | (3188) 14383-02_02.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{31EE4FE8-7F9C-11D5-ABB8-00B0D02332EB} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\23E594945195F2414803B4D564D2A3A3F5D88B8C |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000100000001015676C3B5DEDEC330183A43E1FCCA2620000000100000020000000B4410B73E2E6EACA47FBC42F8FA4018AF4381DC54CFAA84450461EED09454DE9090000000100000016000000301406082B0601050507030106082B060105050703031400000001000000140000000715286D7073AAB28A7C0F86CE38930038058AB11D0000000100000010000000FF28C3DDD914074F50198F568DBE43A60B000000010000000E00000074006800610077007400650000006800000001000000080000000000876ACE99D10103000000010000001400000023E594945195F2414803B4D564D2A3A3F5D88B8C200000000100000017030000308203133082027CA003020102020101300D06092A864886F70D01010405003081C4310B3009060355040613025A41311530130603550408130C5765737465726E204361706531123010060355040713094361706520546F776E311D301B060355040A131454686177746520436F6E73756C74696E6720636331283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E3119301706035504031310546861777465205365727665722043413126302406092A864886F70D01090116177365727665722D6365727473407468617774652E636F6D301E170D3936303830313030303030305A170D3230313233313233353935395A3081C4310B3009060355040613025A41311530130603550408130C5765737465726E204361706531123010060355040713094361706520546F776E311D301B060355040A131454686177746520436F6E73756C74696E6720636331283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E3119301706035504031310546861777465205365727665722043413126302406092A864886F70D01090116177365727665722D6365727473407468617774652E636F6D30819F300D06092A864886F70D010101050003818D0030818902818100D3A4506EC8FF566BE6CF5DB6EA0C687547A2AAC2DA8425FCA8F44751DA85B5207494861E0F75C9E90861F5066D306E151902E952C062DB4D999EE26A0C4438CDFEBEE3640970C5FEB16B29B62F49C83BD427042510972FE7906DC0284299D74C43DEC3F5216D549F5DC358E1C0E4D95BB0B8DCB47BDF363AC2B5662212D6870D0203010001A3133011300F0603551D130101FF040530030101FF300D06092A864886F70D01010405000381810007FA4C695CFB95CC46EE85834D21308ECAD9A86F491AE6DA51E360706C846111A11AC8483E59437D4F953DA18BB70B62987A758ADD884E4E9E40DBA8CC3274B96F0DC6E3B3440BD98A6F9A299B9918283BD1E340289A5A3CD5B5E7201B8BCAA4AB8DE951D9E24C2C59A9DAB9B2751BF642F2EFC7F218F989BCA3FF8A232E7047 | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\18F7C1FCC3090203FD5BAA2F861A754976C8DD25 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000EBB04F1D3A2E372F1DDA6E27D6B680FA1400000001000000140000003EDF290CC1F5CC732CEB3D24E17E52DABD27E2F00B000000010000003400000056006500720069005300690067006E002000540069006D00650020005300740061006D00700069006E006700200043004100000009000000010000000C000000300A06082B0601050507030803000000010000001400000018F7C1FCC3090203FD5BAA2F861A754976C8DD250F000000010000001000000065FC47520F66383962EC0B7B88A0821D190000000100000010000000E53D34CECB05C17EE332C749D78C02562000000001000000C0020000308202BC3082022502104A19D2388C82591CA55D735F155DDCA3300D06092A864886F70D010104050030819E311F301D060355040A1316566572695369676E205472757374204E6574776F726B31173015060355040B130E566572695369676E2C20496E632E312C302A060355040B1323566572695369676E2054696D65205374616D70696E67205365727669636520526F6F7431343032060355040B132B4E4F204C494142494C4954592041434345505445442C20286329393720566572695369676E2C20496E632E301E170D3937303531323030303030305A170D3034303130373233353935395A30819E311F301D060355040A1316566572695369676E205472757374204E6574776F726B31173015060355040B130E566572695369676E2C20496E632E312C302A060355040B1323566572695369676E2054696D65205374616D70696E67205365727669636520526F6F7431343032060355040B132B4E4F204C494142494C4954592041434345505445442C20286329393720566572695369676E2C20496E632E30819F300D06092A864886F70D010101050003818D0030818902818100D32E20F0687C2C2D2E811CB106B2A70BB7110D57DA53D875E3C9332AB2D4F6095B34F3E990FE090CD0DB1B5AB9CDE7F688B19DC08725EB7D5810736A78CB7115FDC658F629AB585E9604FD2D621158811CCA7194D522582FD5CC14058436BA94AAB44D4AE9EE3B22AD56997E219C6C86C04A47976AB4A636D5FC092DD3B4399B0203010001300D06092A864886F70D01010405000381810061550E3E7BC792127E11108E22CCD4B3132B5BE844E40B789EA47EF3A707721EE259EFCC84E389944CDB4E61EFB3A4FB463D50340B9F7056F68E2A7F17CEE563BF796907732EB095288AF5EDAAA9D25DCD0ACA10098FCEB3AF2896C479298492DCFFBA674248A69010E4BF61F89C53E593D1733FF8FD9D4F84AC55D1FD116363 | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\23E594945195F2414803B4D564D2A3A3F5D88B8C |
| Operation: | write | Name: | Blob |
Value: 1900000001000000100000004187D1F7D569D7CAB129111DF899918103000000010000001400000023E594945195F2414803B4D564D2A3A3F5D88B8C6800000001000000080000000000876ACE99D1010B000000010000000E00000074006800610077007400650000001D0000000100000010000000FF28C3DDD914074F50198F568DBE43A61400000001000000140000000715286D7073AAB28A7C0F86CE38930038058AB1090000000100000016000000301406082B0601050507030106082B06010505070303620000000100000020000000B4410B73E2E6EACA47FBC42F8FA4018AF4381DC54CFAA84450461EED09454DE90F00000001000000100000001015676C3B5DEDEC330183A43E1FCCA2200000000100000017030000308203133082027CA003020102020101300D06092A864886F70D01010405003081C4310B3009060355040613025A41311530130603550408130C5765737465726E204361706531123010060355040713094361706520546F776E311D301B060355040A131454686177746520436F6E73756C74696E6720636331283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E3119301706035504031310546861777465205365727665722043413126302406092A864886F70D01090116177365727665722D6365727473407468617774652E636F6D301E170D3936303830313030303030305A170D3230313233313233353935395A3081C4310B3009060355040613025A41311530130603550408130C5765737465726E204361706531123010060355040713094361706520546F776E311D301B060355040A131454686177746520436F6E73756C74696E6720636331283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E3119301706035504031310546861777465205365727665722043413126302406092A864886F70D01090116177365727665722D6365727473407468617774652E636F6D30819F300D06092A864886F70D010101050003818D0030818902818100D3A4506EC8FF566BE6CF5DB6EA0C687547A2AAC2DA8425FCA8F44751DA85B5207494861E0F75C9E90861F5066D306E151902E952C062DB4D999EE26A0C4438CDFEBEE3640970C5FEB16B29B62F49C83BD427042510972FE7906DC0284299D74C43DEC3F5216D549F5DC358E1C0E4D95BB0B8DCB47BDF363AC2B5662212D6870D0203010001A3133011300F0603551D130101FF040530030101FF300D06092A864886F70D01010405000381810007FA4C695CFB95CC46EE85834D21308ECAD9A86F491AE6DA51E360706C846111A11AC8483E59437D4F953DA18BB70B62987A758ADD884E4E9E40DBA8CC3274B96F0DC6E3B3440BD98A6F9A299B9918283BD1E340289A5A3CD5B5E7201B8BCAA4AB8DE951D9E24C2C59A9DAB9B2751BF642F2EFC7F218F989BCA3FF8A232E7047 | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 340A000064C1925D28A9D501 | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 3CFB2F6D2B4FB7ABD4257F757C0DD10ABF7AE9FA24AC30CFE4595F7F50643E9C | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | |
Value: C:\Windows\Installer\39050e.ipi | |||
| (PID) Process: | (2612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
Executable files
53
Suspicious files
21
Text files
138
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3188 | 14383-02_02.exe | C:\Users\admin\AppData\Local\Temp\~F646.tmp | — | |
MD5:— | SHA256:— | |||
| 3188 | 14383-02_02.exe | C:\Users\admin\AppData\Local\Temp\_isF657\Trust WB-3400T Webcam .msi | — | |
MD5:— | SHA256:— | |||
| 2612 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab569.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar56A.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab57B.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar57C.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab638.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar639.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF5BB6B2CC61E7063D.TMP | — | |
MD5:— | SHA256:— | |||
| 3188 | 14383-02_02.exe | C:\Users\admin\AppData\Local\Temp\_isF657\_ISMSIDEL.INI | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2612 | msiexec.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2612 | msiexec.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
PASnap.exe | The system cannot find the file specified.
|