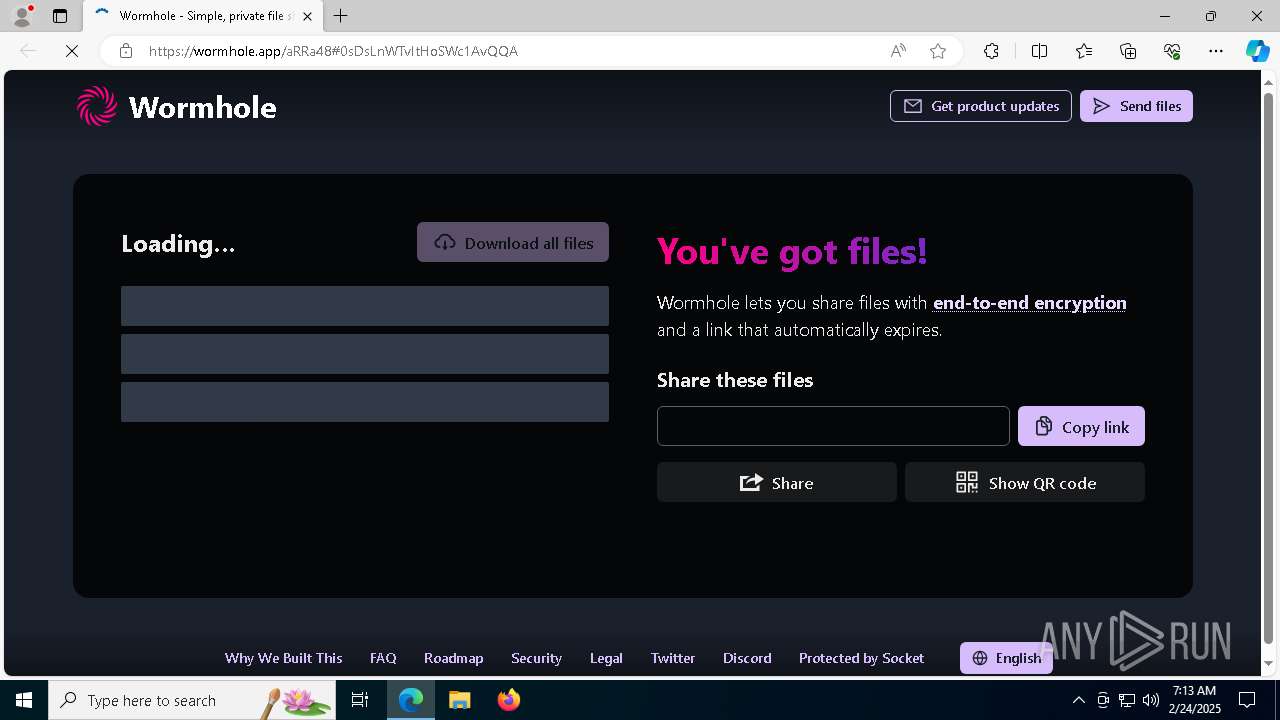
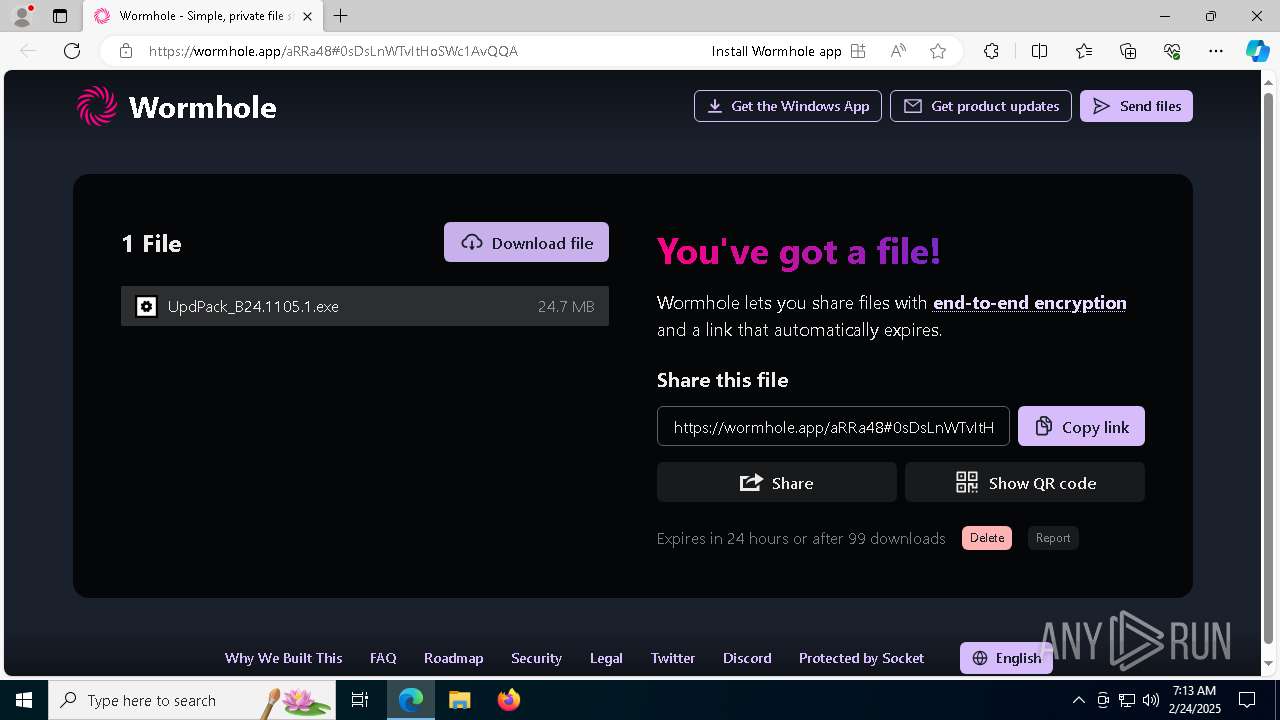
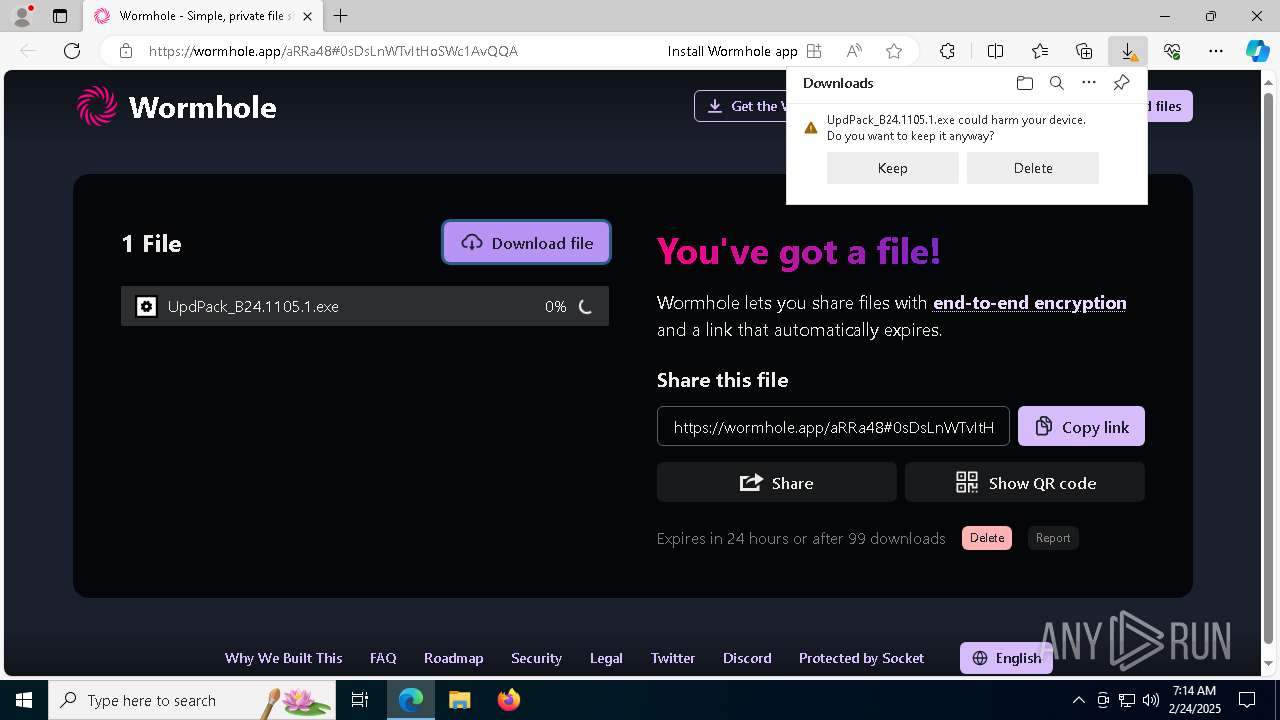
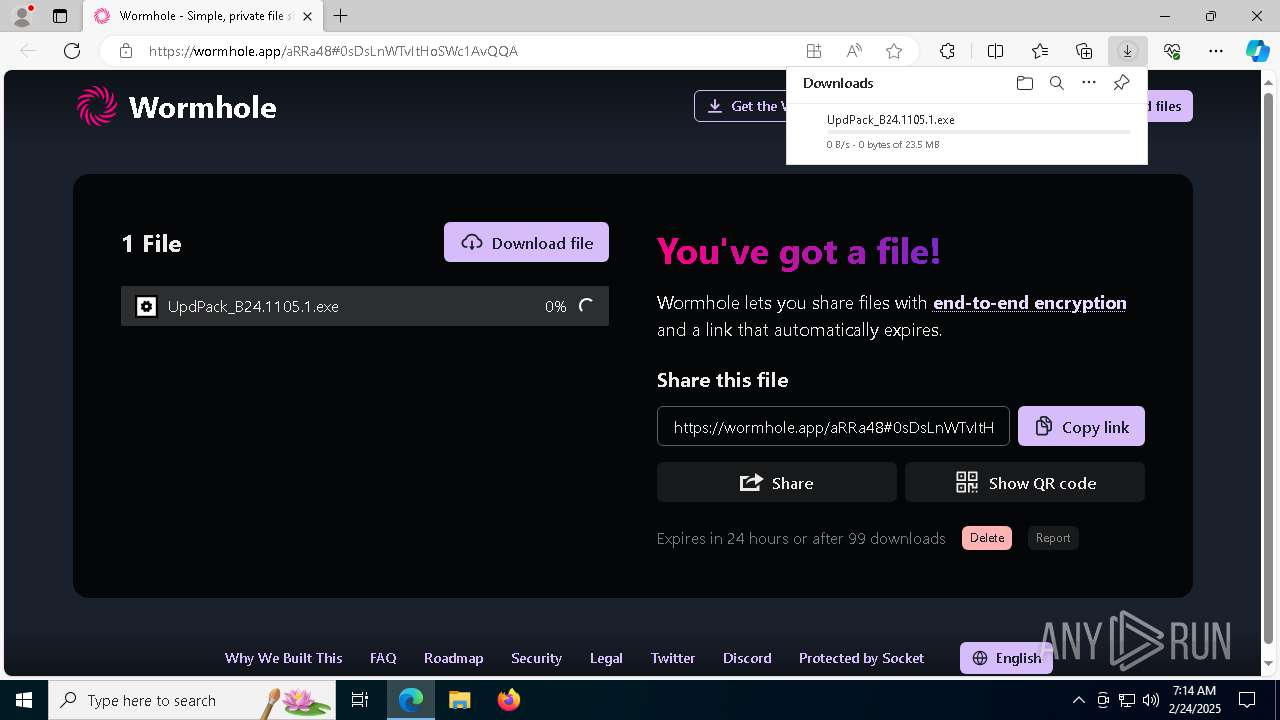
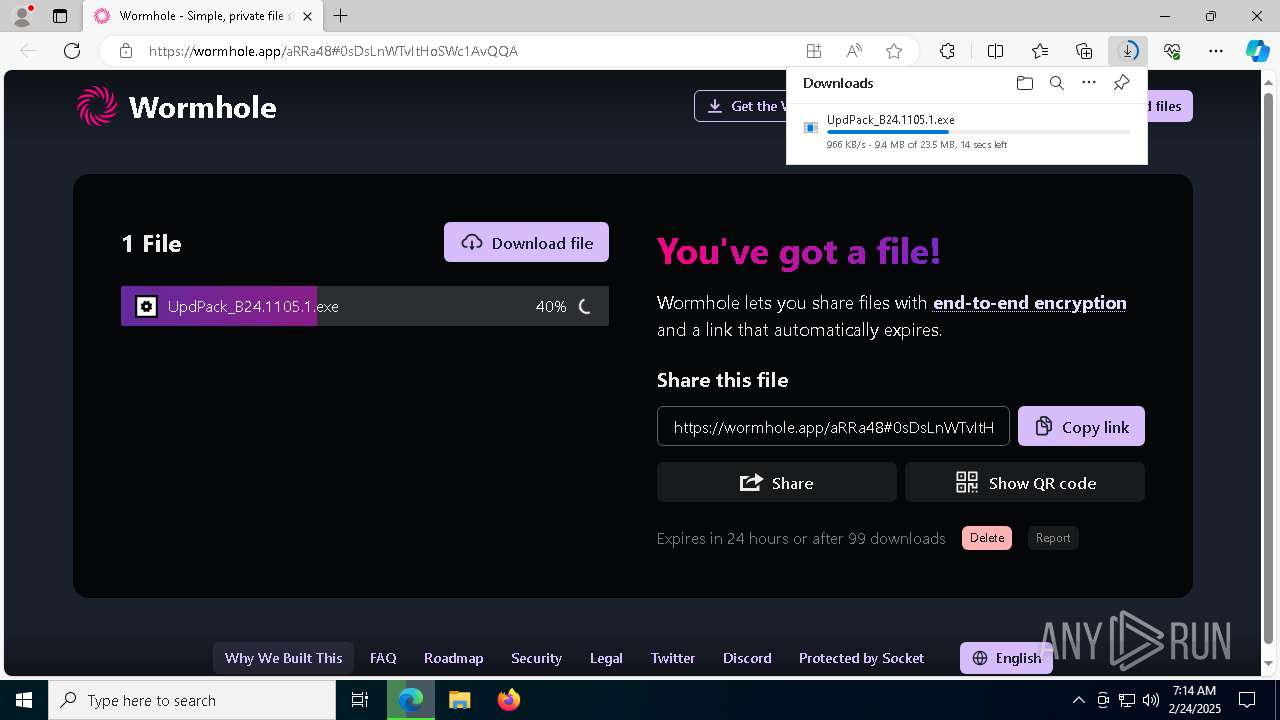
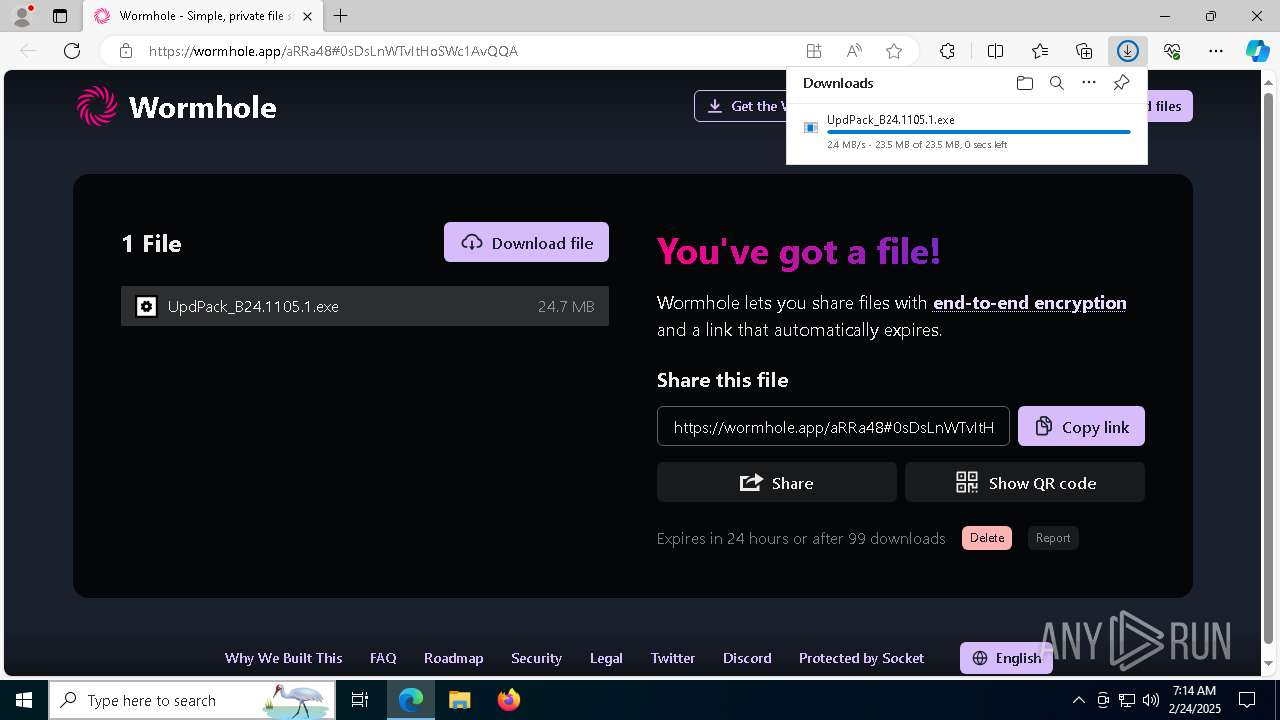
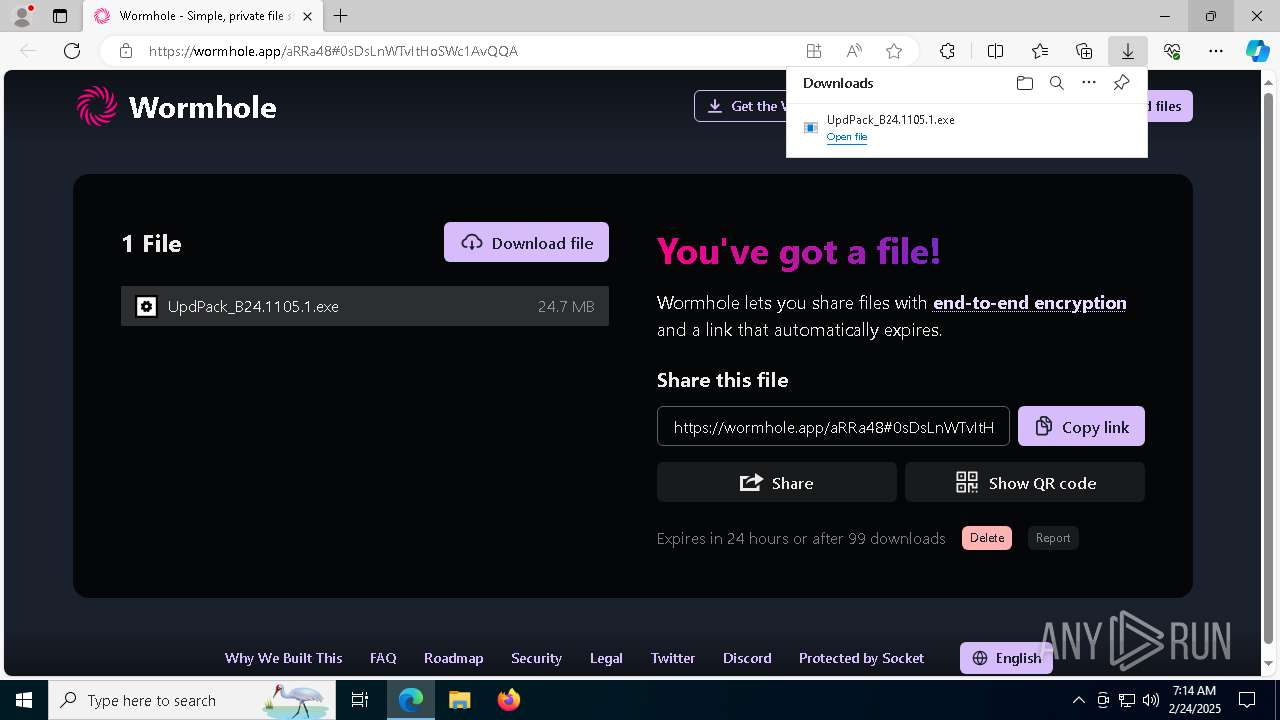
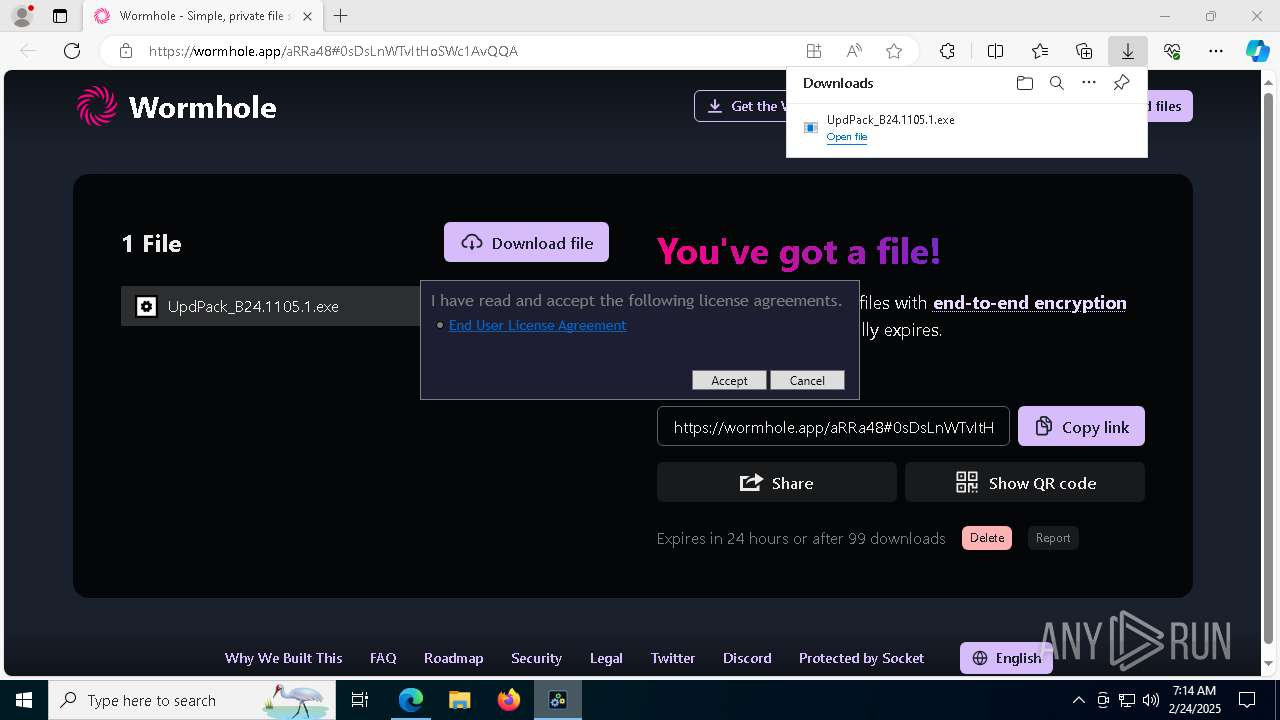
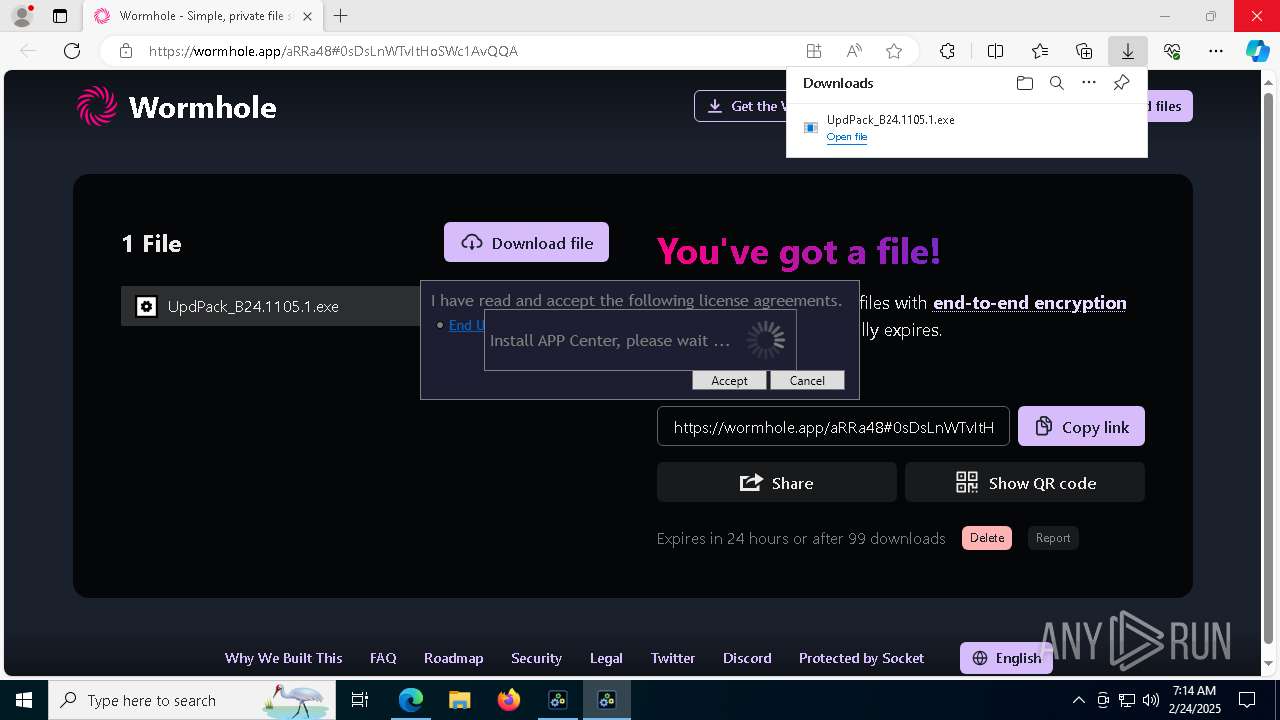
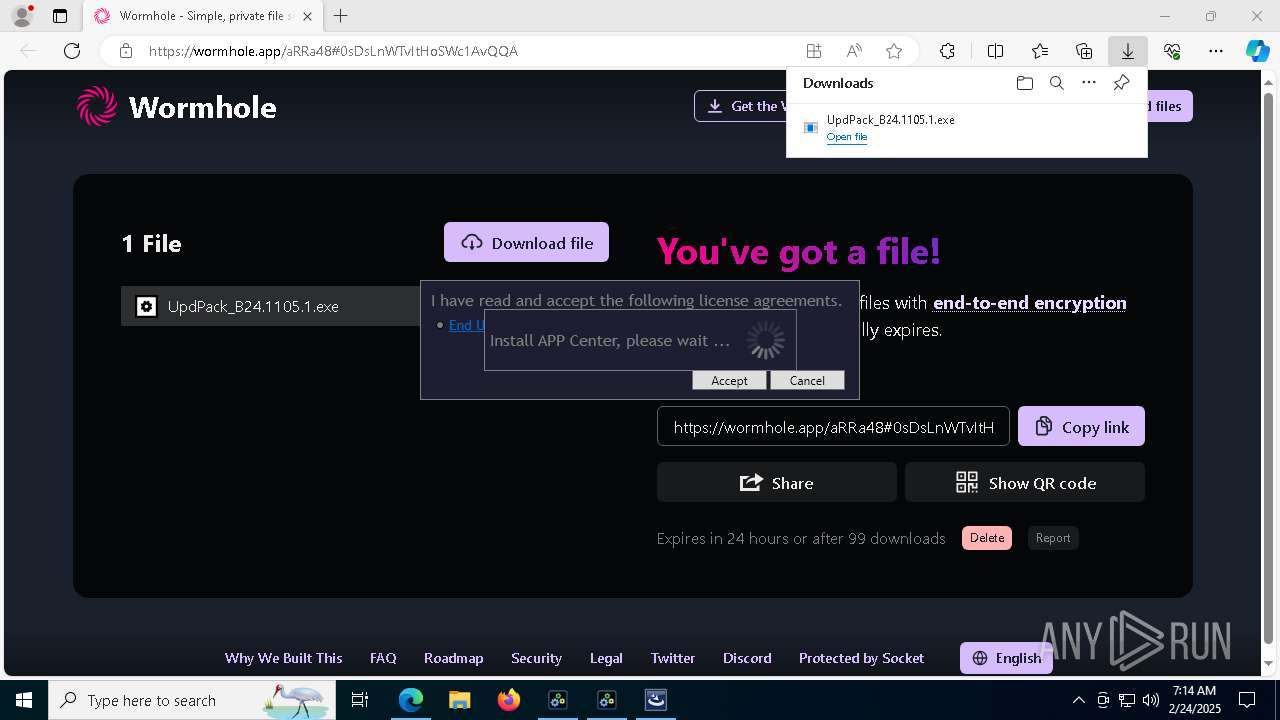
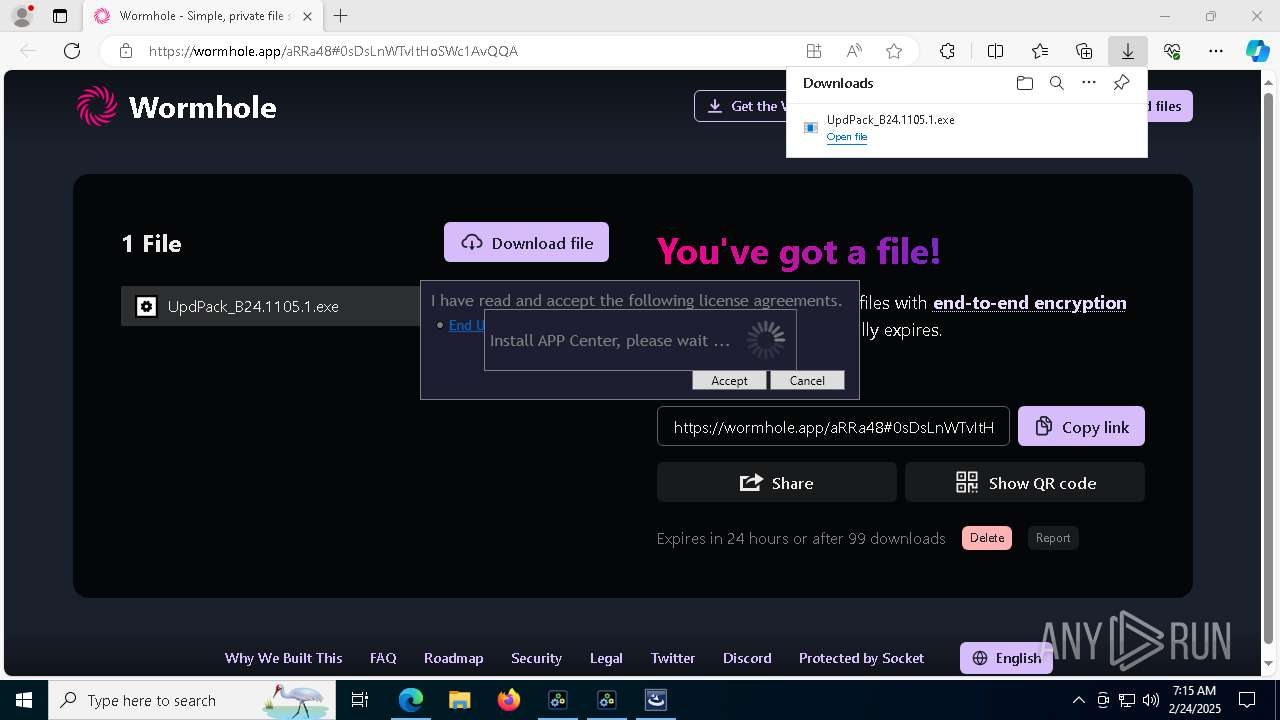
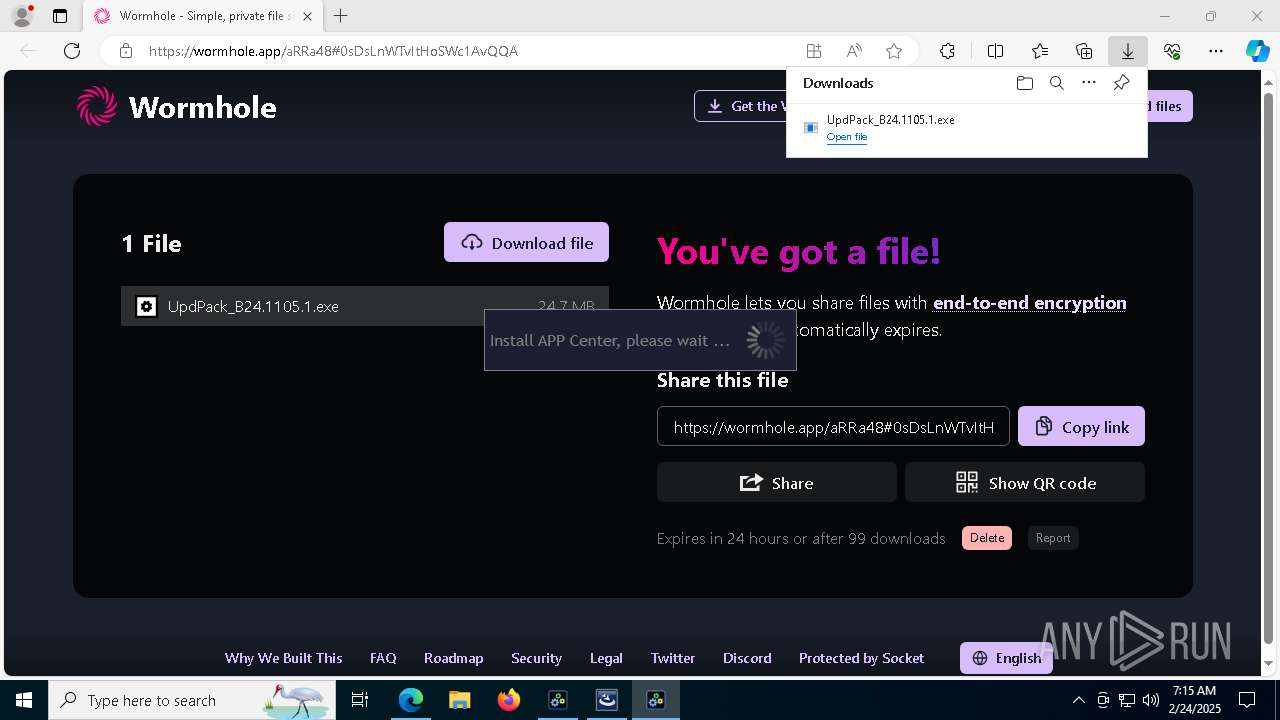
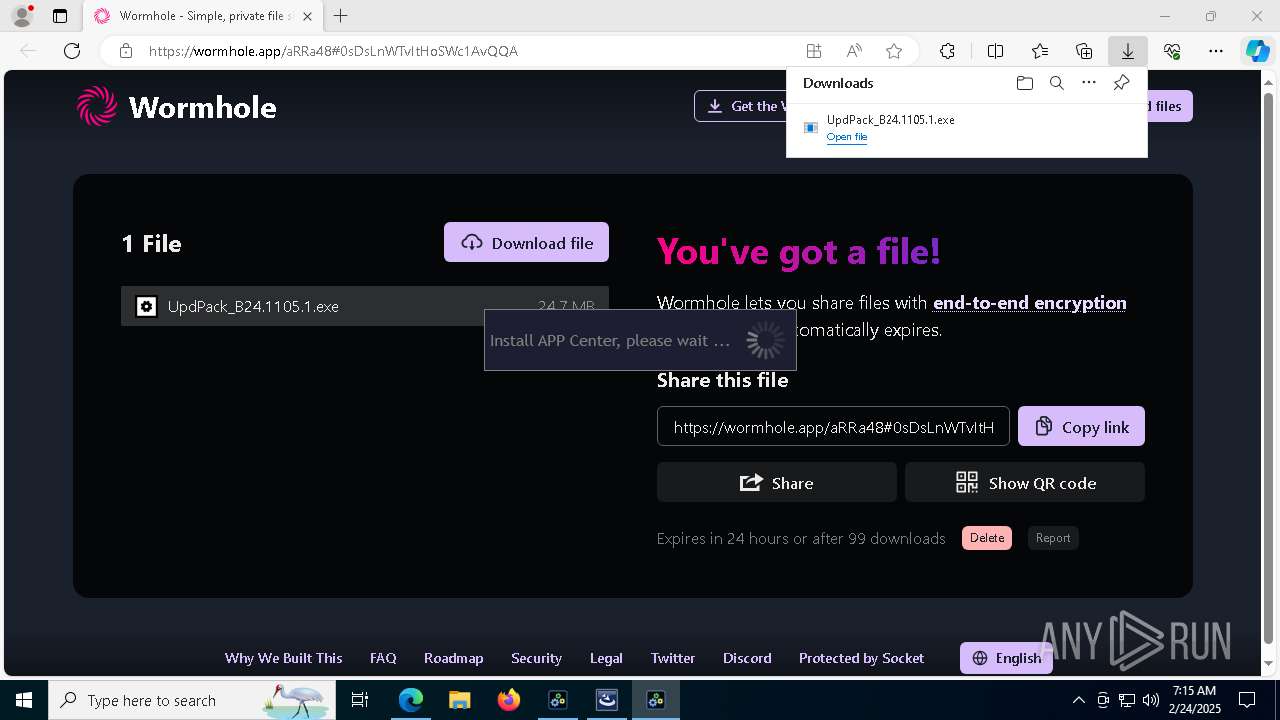
| URL: | https://wormhole.app/aRRa48#0sDsLnWTvItHoSWc1AvQQA |
| Full analysis: | https://app.any.run/tasks/b8682dc5-71e0-4ad7-8a3e-fae831eecb31 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2025, 07:13:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | C913E060F5A4C8F26AD3A7B8676D481F |
| SHA1: | CB4E35B696DDF45590607D6E80EEB6E0A60037C5 |
| SHA256: | DE51943AC3A14CE5A0D4A9EBEDFBD3C5EE694F8B64617437AAD2196F5B0773AD |
| SSDEEP: | 3:N8bXINKJujEwGVWAlyVsR4VDk5k:2kNSujFChoVw2D1 |
MALICIOUS
Executing a file with an untrusted certificate
- setup.exe (PID: 1328)
- ISBEW64.exe (PID: 6208)
- vcredist_x86.exe (PID: 4724)
- vcredist_x86.exe (PID: 5236)
- vcredist_x64.exe (PID: 5092)
- vcredist_x64.exe (PID: 7064)
- setup.exe (PID: 2432)
- ISBEW64.exe (PID: 4428)
- PreRun.exe (PID: 5004)
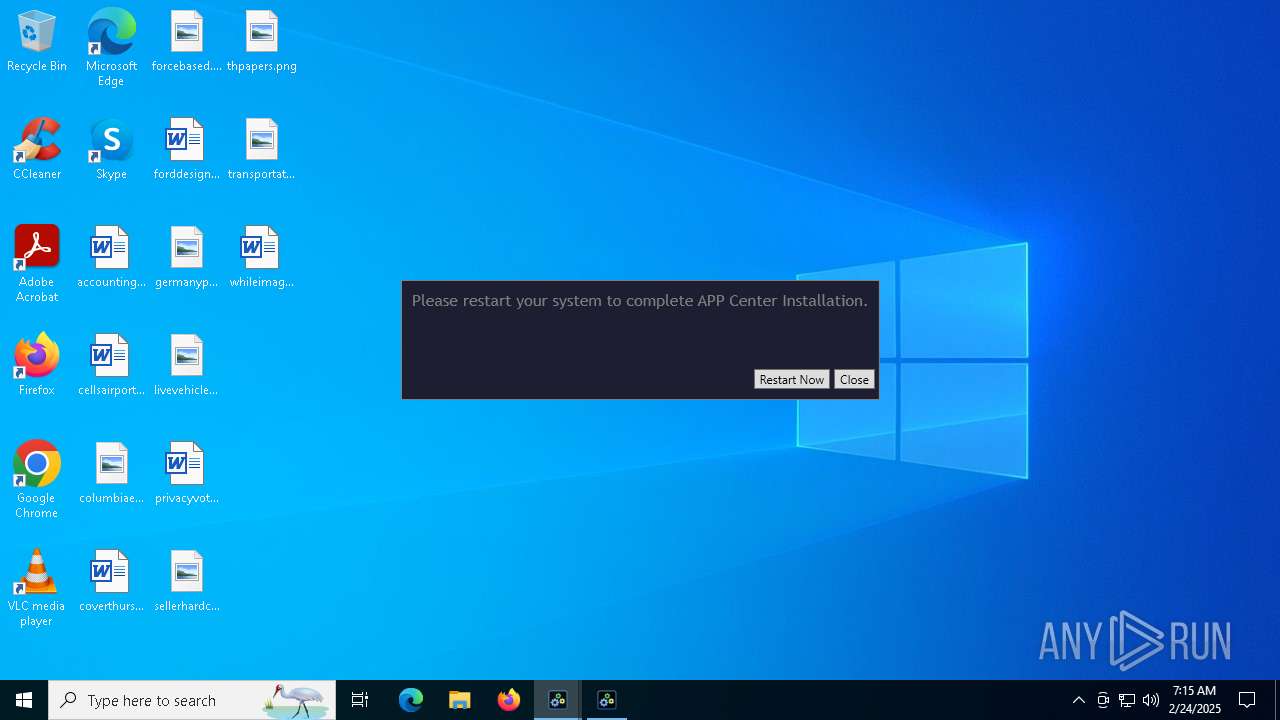
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 7064)
- setup.exe (PID: 1328)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- msedge.exe (PID: 6340)
Executable content was dropped or overwritten
- UpdPack_B24.1105.1.exe (PID: 7400)
- UpdPack_B24.1105.1.exe (PID: 3736)
- setup.exe (PID: 1328)
- vcredist_x86.exe (PID: 5236)
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 5092)
- vcredist_x64.exe (PID: 7064)
- setup.exe (PID: 2432)
- ApCent.exe (PID: 6000)
Reads security settings of Internet Explorer
- InstUpd.exe (PID: 7176)
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 7064)
- addfwrule.exe (PID: 7224)
- InstUpd.exe (PID: 7416)
- PreRun.exe (PID: 5004)
- RunUpd.exe (PID: 2436)
- ApCent.exe (PID: 6000)
Reads the Windows owner or organization settings
- setup.exe (PID: 1328)
- msiexec.exe (PID: 6184)
- setup.exe (PID: 2432)
Process drops legitimate windows executable
- msiexec.exe (PID: 7876)
- vcredist_x86.exe (PID: 5236)
- vcredist_x86.exe (PID: 4724)
- msiexec.exe (PID: 6184)
- vcredist_x64.exe (PID: 5092)
- vcredist_x64.exe (PID: 7064)
- msiexec.exe (PID: 7816)
Application launched itself
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 7064)
Starts a Microsoft application from unusual location
- vcredist_x86.exe (PID: 5236)
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 7064)
- vcredist_x64.exe (PID: 5092)
Executes as Windows Service
- VSSVC.exe (PID: 5432)
- AdjustService.exe (PID: 1076)
Searches for installed software
- dllhost.exe (PID: 7656)
- vcredist_x86.exe (PID: 5236)
- vcredist_x64.exe (PID: 5092)
- vcredist_x64.exe (PID: 7064)
- setup.exe (PID: 1328)
- setup.exe (PID: 2432)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 7064)
- setup.exe (PID: 1328)
Checks Windows Trust Settings
- vcredist_x86.exe (PID: 4724)
- msiexec.exe (PID: 6184)
- vcredist_x64.exe (PID: 7064)
The process drops C-runtime libraries
- msiexec.exe (PID: 6184)
Uses NETSH.EXE to add a firewall rule or allowed programs
- addfwrule.exe (PID: 7224)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 1328)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 2308)
Creates files in the driver directory
- ApCent.exe (PID: 6000)
Drops a system driver (possible attempt to evade defenses)
- ApCent.exe (PID: 6000)
The process verifies whether the antivirus software is installed
- ApCent.exe (PID: 6000)
INFO
Checks supported languages
- identity_helper.exe (PID: 7180)
- InstUpd.exe (PID: 7416)
- UpdPack_B24.1105.1.exe (PID: 3736)
- UpdPack_B24.1105.1.exe (PID: 7400)
- setup.exe (PID: 1328)
- msiexec.exe (PID: 6184)
- msiexec.exe (PID: 7876)
- ISBEW64.exe (PID: 6208)
- vcredist_x86.exe (PID: 5236)
- InstUpd.exe (PID: 7176)
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 5092)
- msiexec.exe (PID: 1192)
- AdjustService.exe (PID: 1076)
- addfwrule.exe (PID: 7224)
- setup.exe (PID: 2432)
- msiexec.exe (PID: 7816)
- identity_helper.exe (PID: 7748)
- vcredist_x64.exe (PID: 7064)
- ISBEW64.exe (PID: 4428)
- PLUGScheduler.exe (PID: 2308)
- PreRun.exe (PID: 5004)
- RunUpd.exe (PID: 2436)
- ApCent.exe (PID: 6000)
Reads the computer name
- identity_helper.exe (PID: 7180)
- InstUpd.exe (PID: 7176)
- InstUpd.exe (PID: 7416)
- msiexec.exe (PID: 6184)
- msiexec.exe (PID: 7876)
- ISBEW64.exe (PID: 6208)
- setup.exe (PID: 1328)
- vcredist_x86.exe (PID: 5236)
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 5092)
- vcredist_x64.exe (PID: 7064)
- msiexec.exe (PID: 1192)
- AdjustService.exe (PID: 1076)
- addfwrule.exe (PID: 7224)
- setup.exe (PID: 2432)
- msiexec.exe (PID: 7816)
- identity_helper.exe (PID: 7748)
- ISBEW64.exe (PID: 4428)
- PreRun.exe (PID: 5004)
- RunUpd.exe (PID: 2436)
- PLUGScheduler.exe (PID: 2308)
- ApCent.exe (PID: 6000)
Reads Environment values
- identity_helper.exe (PID: 7180)
- identity_helper.exe (PID: 7748)
Create files in a temporary directory
- UpdPack_B24.1105.1.exe (PID: 7400)
- setup.exe (PID: 1328)
- msiexec.exe (PID: 7876)
- UpdPack_B24.1105.1.exe (PID: 3736)
- vcredist_x86.exe (PID: 5236)
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 5092)
- vcredist_x64.exe (PID: 7064)
- setup.exe (PID: 2432)
- msiexec.exe (PID: 7816)
- ApCent.exe (PID: 6000)
Executable content was dropped or overwritten
- msedge.exe (PID: 6340)
- msiexec.exe (PID: 7876)
- msiexec.exe (PID: 6184)
- msiexec.exe (PID: 7816)
Application launched itself
- msedge.exe (PID: 6340)
- msedge.exe (PID: 6764)
Reads the machine GUID from the registry
- InstUpd.exe (PID: 7416)
- InstUpd.exe (PID: 7176)
- vcredist_x86.exe (PID: 4724)
- msiexec.exe (PID: 6184)
- vcredist_x64.exe (PID: 7064)
- RunUpd.exe (PID: 2436)
- ApCent.exe (PID: 6000)
The sample compiled with english language support
- UpdPack_B24.1105.1.exe (PID: 7400)
- UpdPack_B24.1105.1.exe (PID: 3736)
- setup.exe (PID: 1328)
- msiexec.exe (PID: 7876)
- msedge.exe (PID: 6340)
- vcredist_x86.exe (PID: 5236)
- vcredist_x86.exe (PID: 4724)
- msiexec.exe (PID: 6184)
- vcredist_x64.exe (PID: 5092)
- vcredist_x64.exe (PID: 7064)
- setup.exe (PID: 2432)
- msiexec.exe (PID: 7816)
Process checks computer location settings
- InstUpd.exe (PID: 7176)
- addfwrule.exe (PID: 7224)
- InstUpd.exe (PID: 7416)
- PreRun.exe (PID: 5004)
- RunUpd.exe (PID: 2436)
Creates files in the program directory
- vcredist_x86.exe (PID: 4724)
- setup.exe (PID: 1328)
- PLUGScheduler.exe (PID: 2308)
- ApCent.exe (PID: 6000)
- vcredist_x64.exe (PID: 7064)
Creates files or folders in the user directory
- vcredist_x86.exe (PID: 4724)
Reads the software policy settings
- vcredist_x86.exe (PID: 4724)
- vcredist_x64.exe (PID: 7064)
- msiexec.exe (PID: 6184)
- ApCent.exe (PID: 6000)
Manages system restore points
- SrTasks.exe (PID: 1828)
Checks proxy server information
- vcredist_x86.exe (PID: 4724)
- ApCent.exe (PID: 6000)
The sample compiled with chinese language support
- msiexec.exe (PID: 6184)
The sample compiled with german language support
- msiexec.exe (PID: 6184)
The sample compiled with spanish language support
- msiexec.exe (PID: 6184)
The sample compiled with korean language support
- msiexec.exe (PID: 6184)
The sample compiled with japanese language support
- msiexec.exe (PID: 6184)
The sample compiled with russian language support
- msiexec.exe (PID: 6184)
The sample compiled with Italian language support
- msiexec.exe (PID: 6184)
The sample compiled with french language support
- msiexec.exe (PID: 6184)
Creates a software uninstall entry
- msiexec.exe (PID: 6184)
Reads security settings of Internet Explorer
- runonce.exe (PID: 4452)
Reads the time zone
- runonce.exe (PID: 4404)
Manual execution by a user
- runonce.exe (PID: 4404)
Disables trace logs
- ApCent.exe (PID: 6000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
360
Monitored processes
83
Malicious processes
14
Suspicious processes
5
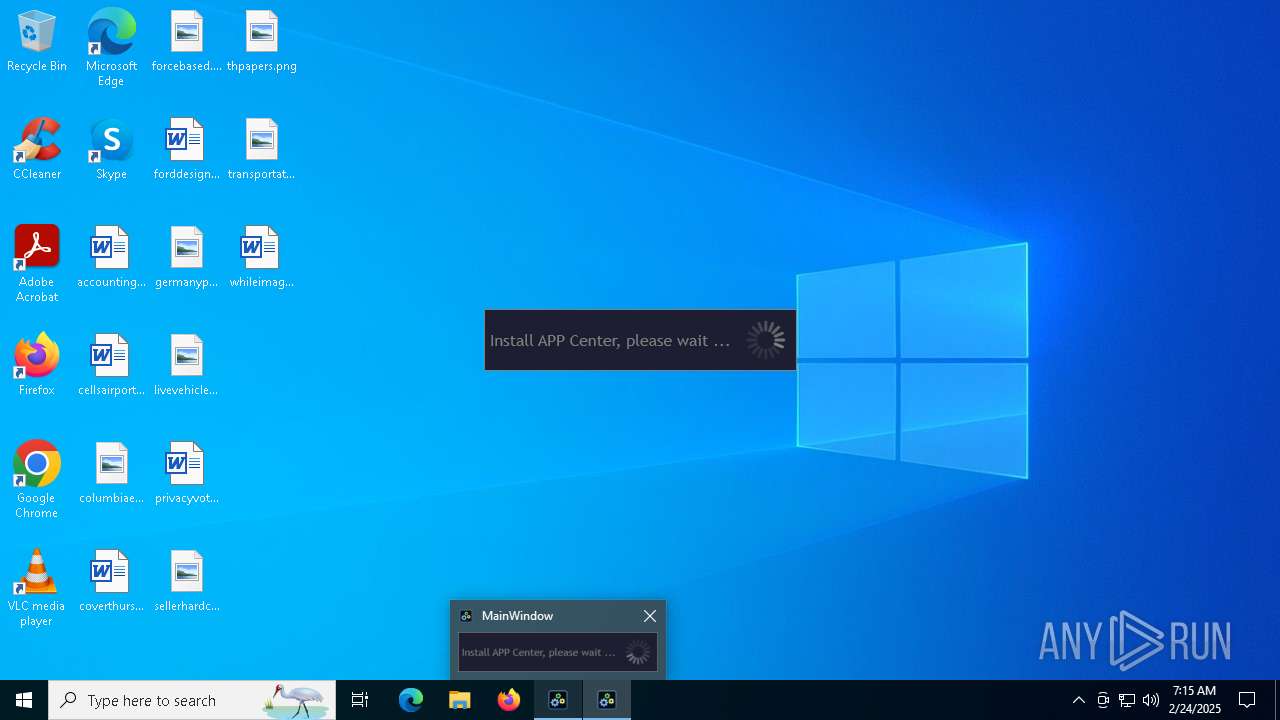
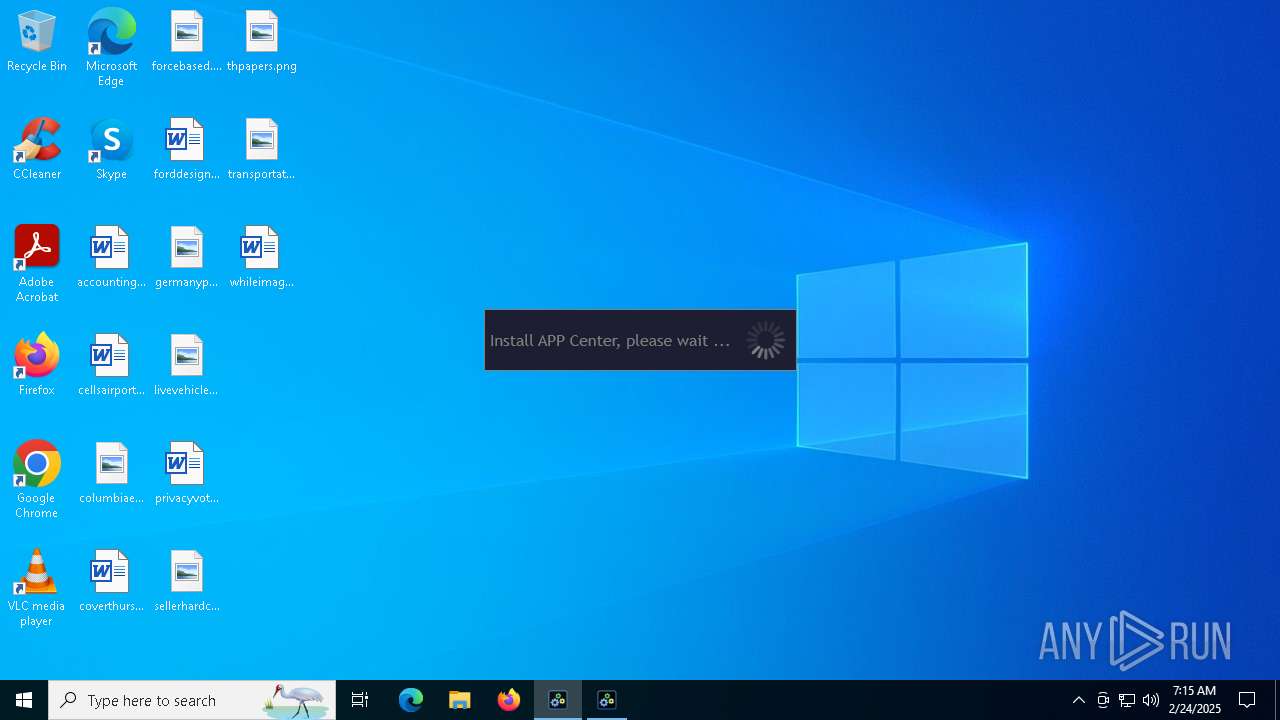
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x28c,0x20c,0x7ff818485fd8,0x7ff818485fe4,0x7ff818485ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1073807364 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 880 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4028 --field-trial-handle=2280,i,8727739504990865877,3114694487761572138,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1076 | "C:\Program Files (x86)\Gigabyte\AppCenter\AdjustService.exe" | C:\Program Files (x86)\Gigabyte\AppCenter\AdjustService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: AdjustService Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1192 | C:\Windows\syswow64\MsiExec.exe -Embedding 0FB0C96B0DEC3B5EF37D18BF646CB047 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7476 --field-trial-handle=2388,i,2879324781436963372,490928450552389950,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\AppData\Local\Temp\7zSED22.tmp\AppCenter\setup.exe" /s | C:\Users\admin\AppData\Local\Temp\7zSED22.tmp\AppCenter\setup.exe | InstUpd.exe | ||||||||||||
User: admin Company: Gigabyte Integrity Level: HIGH Description: Setup Launcher Unicode Exit code: 0 Version: 3.24.1105.1 Modules
| |||||||||||||||
| 1412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=41 --mojo-platform-channel-handle=5072 --field-trial-handle=2388,i,2879324781436963372,490928450552389950,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1580 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1828 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3128 --field-trial-handle=2280,i,8727739504990865877,3114694487761572138,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
33 473
Read events
32 291
Write events
1 104
Delete events
78
Modification events
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EEE2DE5D748D2F00 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D58F95D748D2F00 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 61EE445E748D2F00 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
138
Suspicious files
526
Text files
138
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136545.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136555.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136555.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136555.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136574.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
165
DNS requests
104
Threats
74
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1620 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1620 | svchost.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2100 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1740404276&P2=404&P3=2&P4=nhcUif9dPwnooyGx32jHTceZSuubKjXpVeaeAsvBPSLUu4WiCsCJtoaKcOauUxsHzsNQwgXG5lTc5s8HO4Bjdw%3d%3d | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6316 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2100 | svchost.exe | HEAD | 200 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1740404276&P2=404&P3=2&P4=nhcUif9dPwnooyGx32jHTceZSuubKjXpVeaeAsvBPSLUu4WiCsCJtoaKcOauUxsHzsNQwgXG5lTc5s8HO4Bjdw%3d%3d | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4724 | vcredist_x86.exe | GET | 200 | 2.16.164.51:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
2100 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1740404275&P2=404&P3=2&P4=YYydD7JtOMydQsPVLy2qRnN8UztRm4QFbMJhzIzEuz5gpipHjN%2ft%2bcHDHYSv0qnhREt2PdcHJM0K8evBCNAmaA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1620 | svchost.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1620 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 184.86.251.28:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6692 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6692 | msedge.exe | 104.26.6.129:443 | wormhole.app | — | — | suspicious |
6340 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
wormhole.app |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6692 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
6692 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
6692 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
6692 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |
6692 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
6692 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |
6692 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard Low Port) |
6692 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard Low Port) |
6692 | msedge.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard Low Port) |
6692 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |