| File name: | Activator.exe |
| Full analysis: | https://app.any.run/tasks/d2ae4982-0d3a-4560-a6cc-9087269a507b |
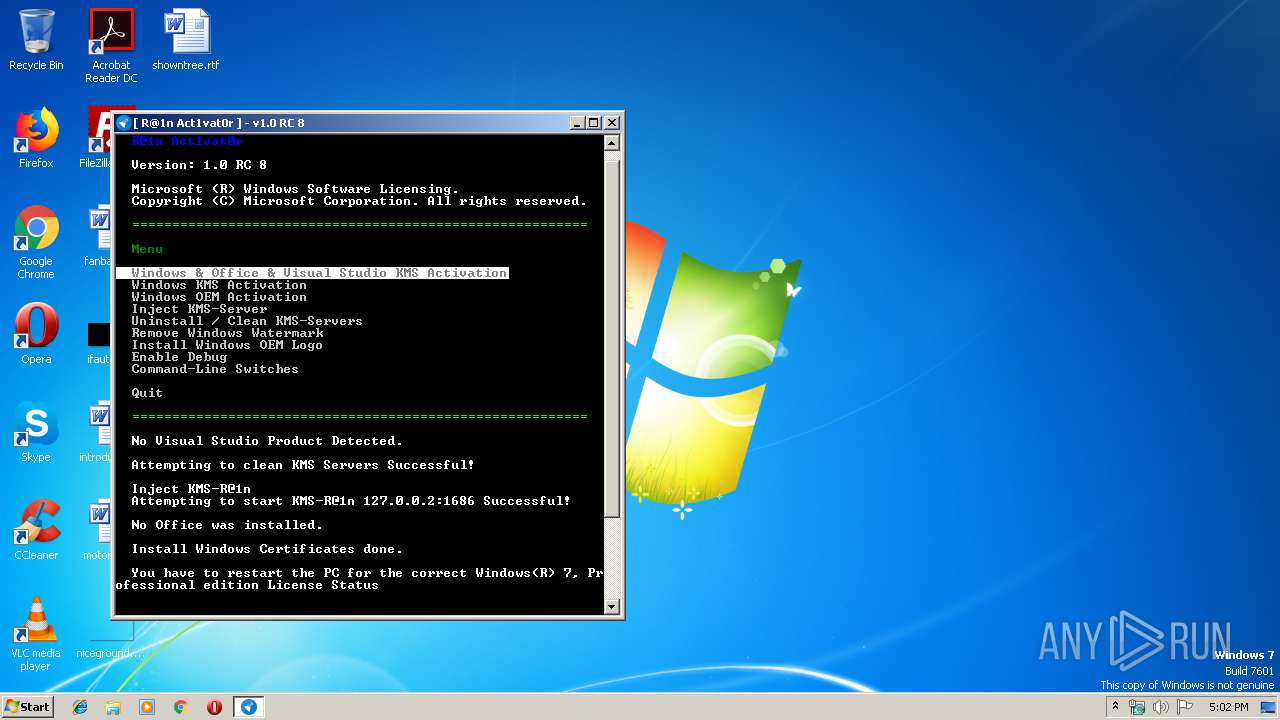
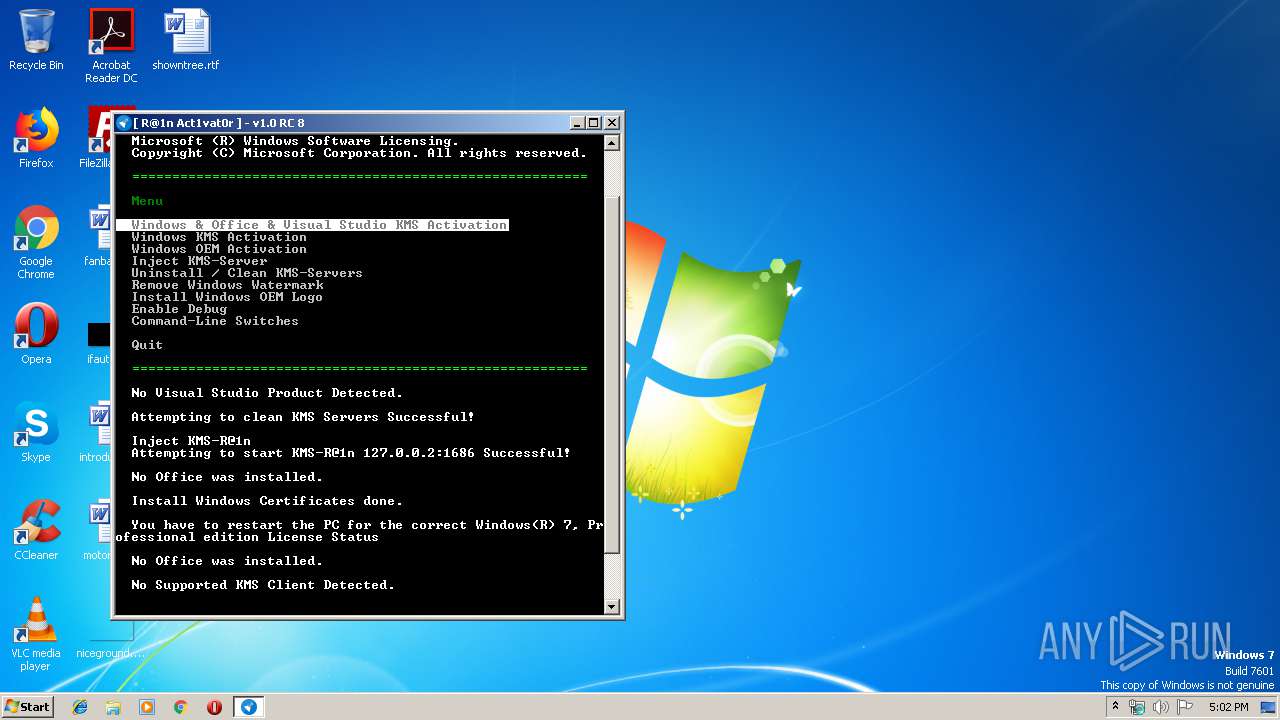
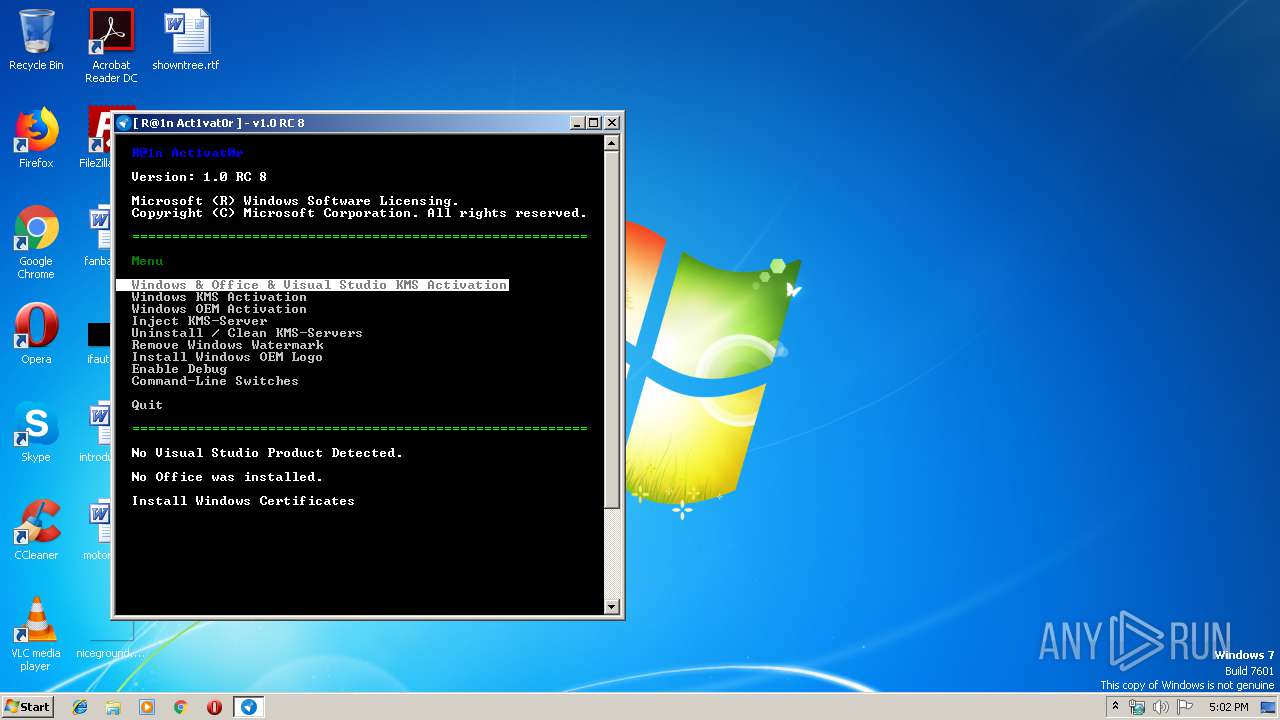
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2019, 16:01:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | CD1F98BF03EAE5C3A86BBAC863AC50F3 |
| SHA1: | EE7F39871486B04EB119C3290EC34DCF05EDED39 |
| SHA256: | DE49D6E07C706BA0BE11D1C1D17DB2A274142A03B8AE4B50663912F880249324 |
| SSDEEP: | 49152:IT2YvV1B707vhpkYVp5oeT7x5KSpSx/fyoECHzhkaXQvlg77h7lJNlgh:C2YNH07HVp5oevxJM75zhvQNiFl1gh |
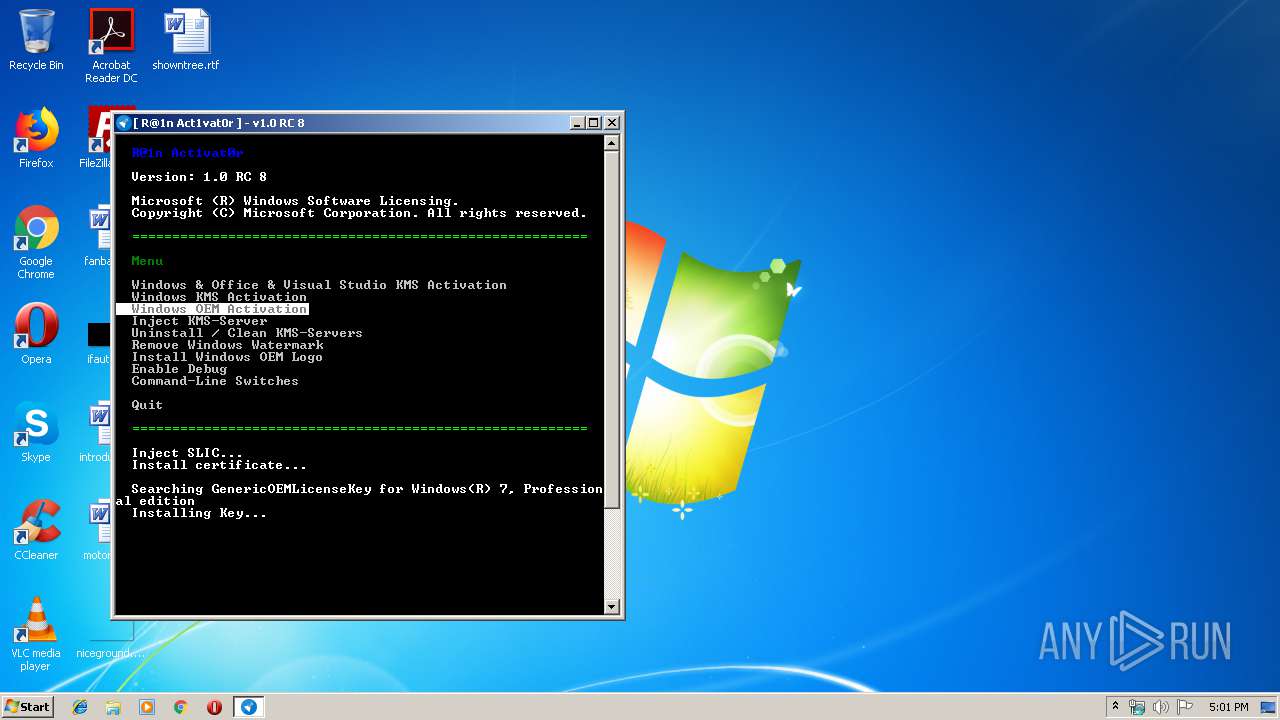
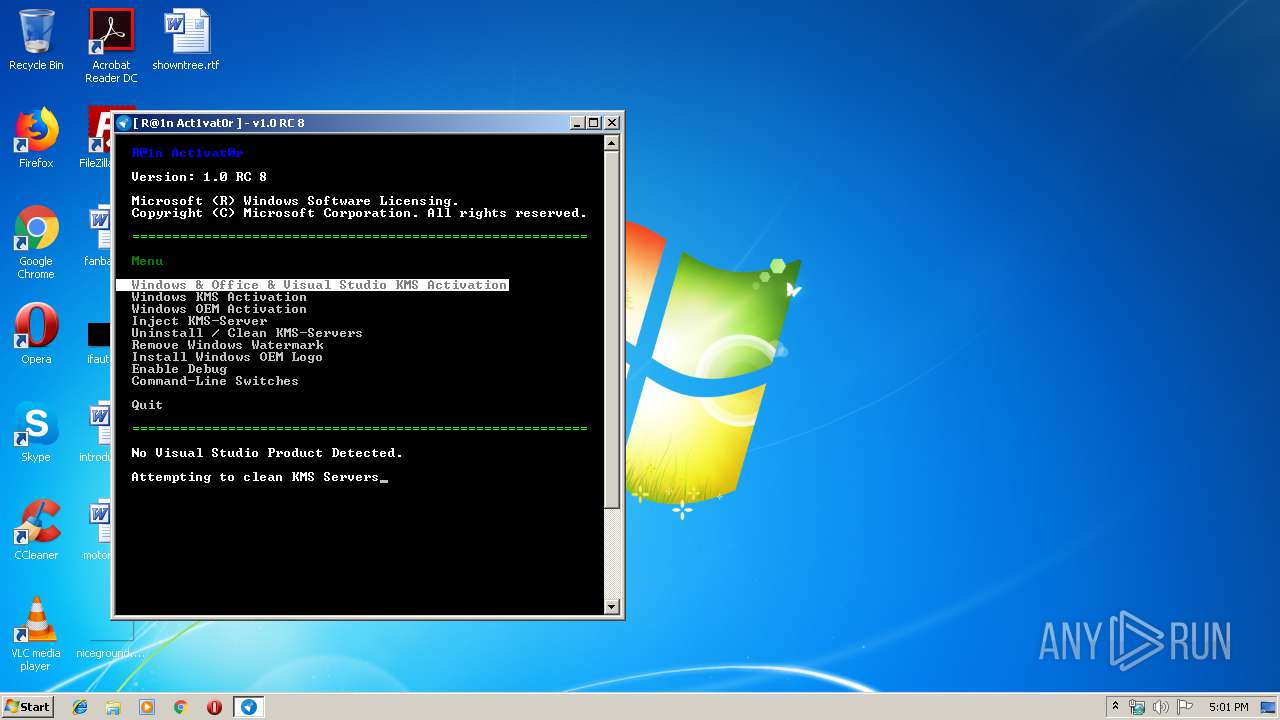
MALICIOUS
Application was dropped or rewritten from another process
- KMS-R@1n.exe (PID: 3392)
- KMS-R@1nHook.exe (PID: 2528)
- KMS-R@1nHook.exe (PID: 2432)
Loads dropped or rewritten executable
- sppsvc.exe (PID: 2620)
- OSPPSVC.EXE (PID: 2632)
Loads the Task Scheduler COM API
- sppsvc.exe (PID: 2620)
- Activator.exe (PID: 2420)
- OSPPSVC.EXE (PID: 2632)
Changes Image File Execution Options
- Activator.exe (PID: 2420)
SUSPICIOUS
Reads Environment values
- Activator.exe (PID: 2420)
Executable content was dropped or overwritten
- Activator.exe (PID: 2420)
Creates files in the Windows directory
- sppsvc.exe (PID: 2620)
- Activator.exe (PID: 2420)
Creates or modifies windows services
- Activator.exe (PID: 2420)
Executed as Windows Service
- KMS-R@1n.exe (PID: 3392)
- KMS-R@1nHook.exe (PID: 2432)
- KMS-R@1nHook.exe (PID: 2528)
Uses TASKKILL.EXE to kill process
- Activator.exe (PID: 2420)
Starts SC.EXE for service management
- Activator.exe (PID: 2420)
Uses NETSH.EXE for network configuration
- Activator.exe (PID: 2420)
Low-level read access rights to disk partition
- brset.exe (PID: 2272)
- bootsect.exe (PID: 3364)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:16 15:36:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 3237376 |
| InitializedDataSize: | 3274752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3184b2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.2.8 |
| ProductVersionNumber: | 1.0.2.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
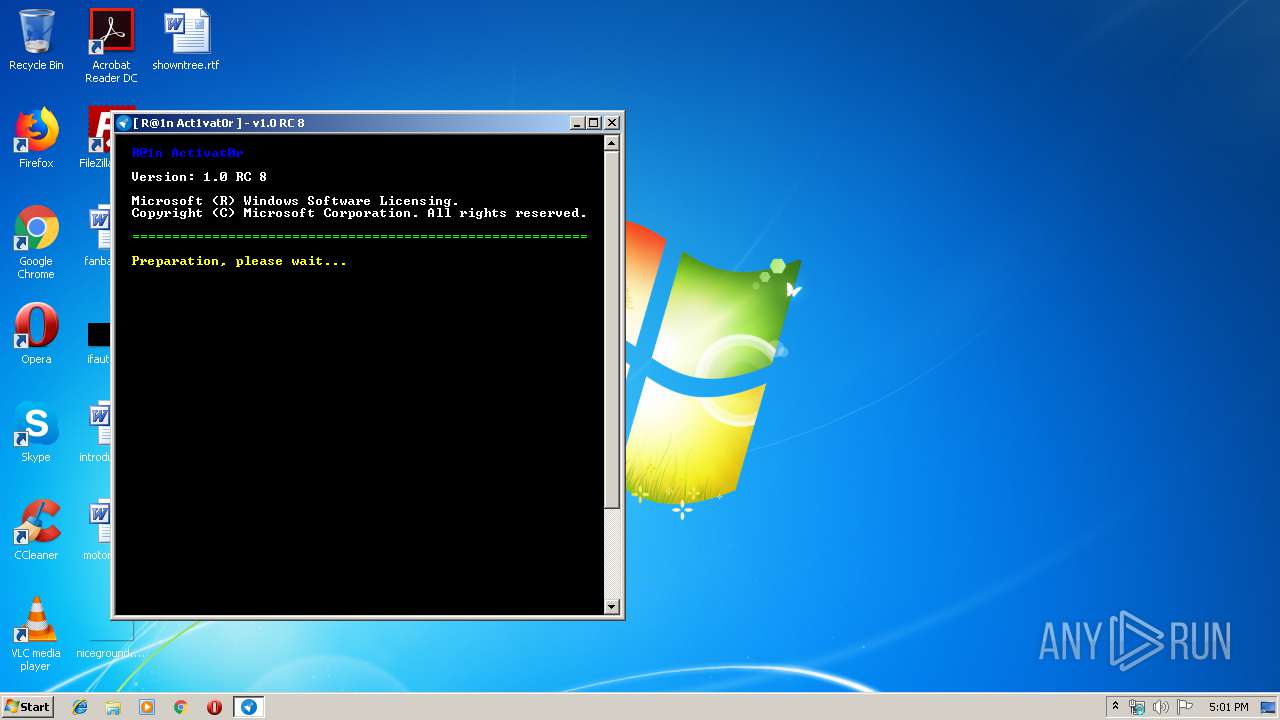
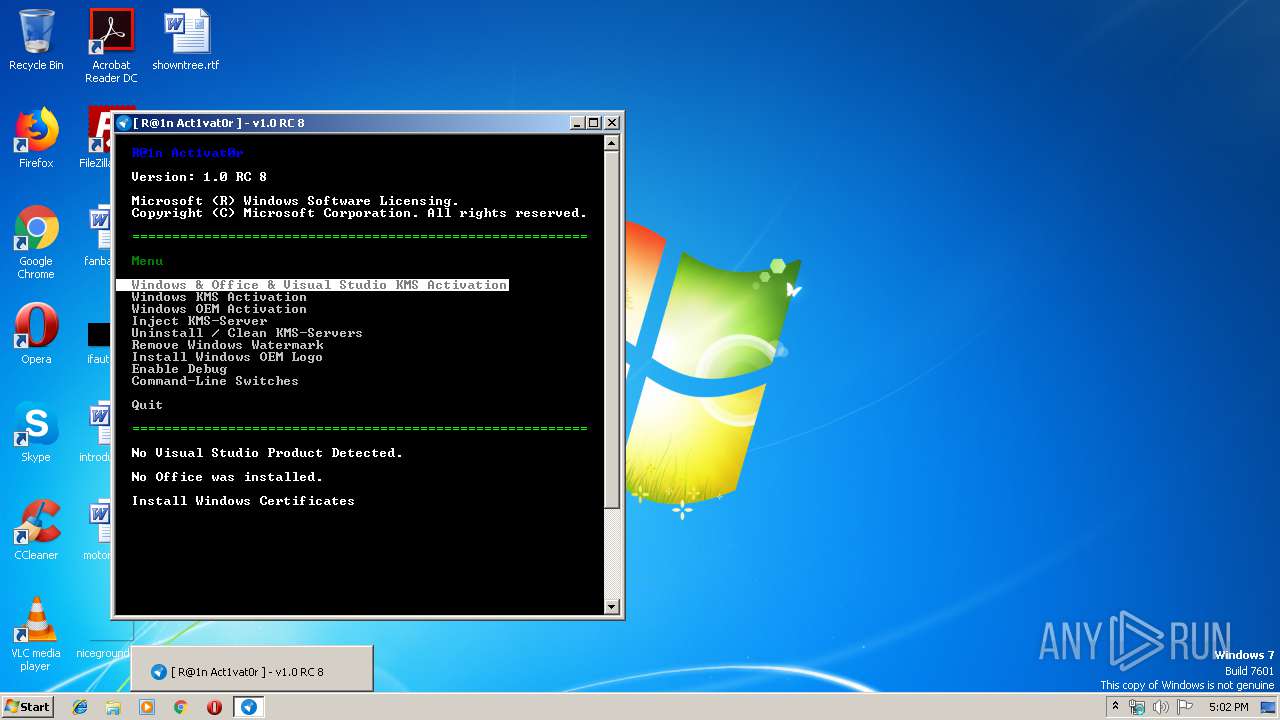
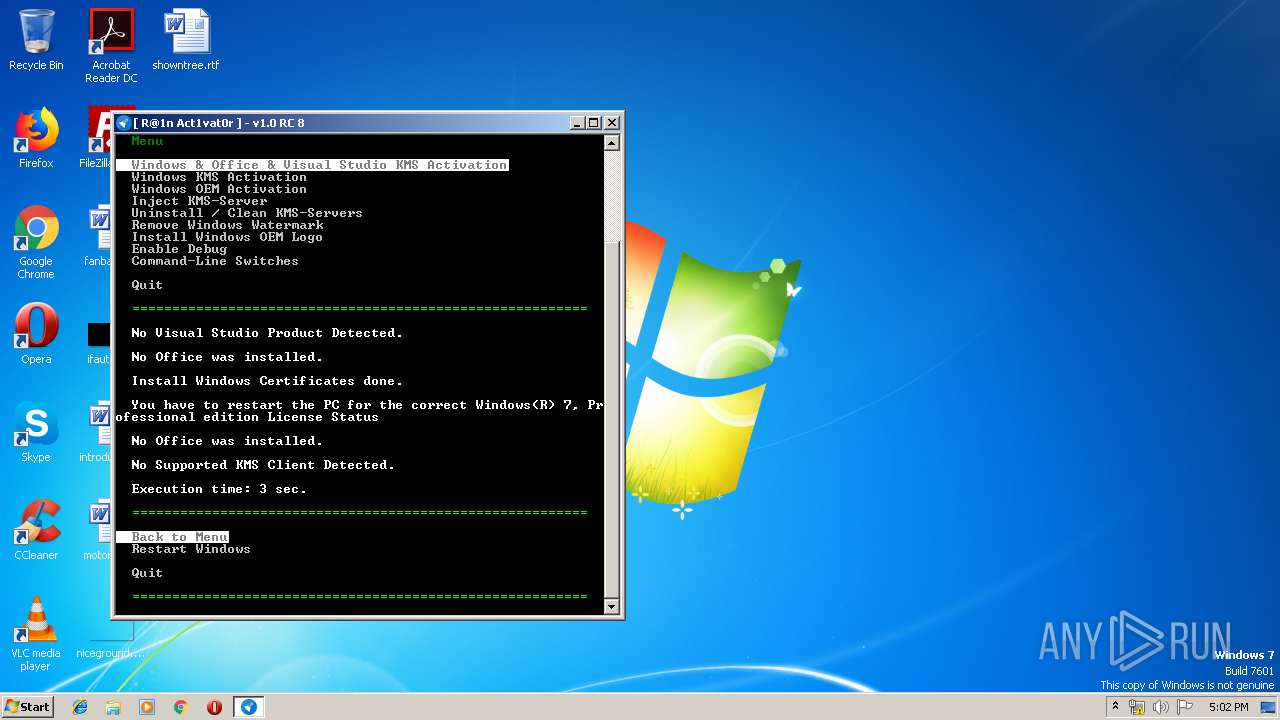
| FileDescription: | R@1n Activator |
| FileVersion: | 1.0.2.8 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | Activator.exe |
| ProductName: | R@1n Activator |
| ProductVersion: | 1.0.2.8 |
| AssemblyVersion: | 1.0.2.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jul-2017 13:36:23 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | R@1n Activator |
| FileVersion: | 1.0.2.8 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | Activator.exe |
| ProductName: | R@1n Activator |
| ProductVersion: | 1.0.2.8 |
| Assembly Version: | 1.0.2.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Jul-2017 13:36:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x003164B8 | 0x00316600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.87803 |
.reloc | 0x0031A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
.rsrc | 0x0031C000 | 0x00009080 | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65265 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.98093 | 3674 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.20217 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.25374 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.96972 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.62308 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
69
Monitored processes
18
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Windows\System32\taskkill.exe" /f /im OsppSvc | C:\Windows\System32\taskkill.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | "C:\Windows\System32\sc.exe" stop hkmsvc | C:\Windows\System32\sc.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1062 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Windows\System32\taskkill.exe" /f /im SppSvc | C:\Windows\System32\taskkill.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Local\Temp\Ra1n\OEM\brset.exe" /nt60 SYS /force | C:\Users\admin\AppData\Local\Temp\Ra1n\OEM\brset.exe | — | Activator.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Local\Temp\Activator.exe" | C:\Users\admin\AppData\Local\Temp\Activator.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: R@1n Activator Exit code: 0 Version: 1.0.2.8 Modules
| |||||||||||||||
| 2432 | KMS-R@1nHook.exe "C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE" | C:\Windows\KMS-R@1nHook.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2528 | KMS-R@1nHook.exe C:\Windows\system32\sppsvc.exe | C:\Windows\KMS-R@1nHook.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2620 | C:\Windows\system32\sppsvc.exe | C:\Windows\system32\sppsvc.exe | — | KMS-R@1nHook.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Software Protection Platform Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE" | C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE | — | KMS-R@1nHook.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Software Protection Platform Service Exit code: 0 Version: 14.0.0370.400 (longhorn(wmbla).090811-1833) Modules
| |||||||||||||||
| 2644 | "C:\Windows\System32\sc.exe" description "KMS-R@1n" "v0.2" | C:\Windows\System32\sc.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
477
Read events
394
Write events
81
Delete events
2
Modification events
| (PID) Process: | (2420) Activator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2420) Activator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2420) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | delete value | Name: | VLActivationInterval |
Value: 120 | |||
| (PID) Process: | (2420) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | delete value | Name: | VLRenewalInterval |
Value: 10080 | |||
| (PID) Process: | (2844) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2844) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2844) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2844) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2844) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2844) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | Activator.exe | C:\Users\admin\AppData\Local\Temp\Ra1n\OEM\brset.exe | — | |
MD5:— | SHA256:— | |||
| 2272 | brset.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 2420 | Activator.exe | C:\Users\admin\AppData\Local\Temp\Ra1n\OEM\SLIC\IC8MM | — | |
MD5:— | SHA256:— | |||
| 2420 | Activator.exe | C:\Users\admin\AppData\Local\Temp\Ra1n\OEM\bootsect.exe | — | |
MD5:— | SHA256:— | |||
| 3364 | bootsect.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 2620 | sppsvc.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Roaming\Microsoft\SoftwareProtectionPlatform\tokens.dat.bak | — | |
MD5:— | SHA256:— | |||
| 2620 | sppsvc.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Roaming\Microsoft\SoftwareProtectionPlatform\tokens.dat | — | |
MD5:— | SHA256:— | |||
| 2420 | Activator.exe | C:\Windows\KMS-R@1nHook.dll | executable | |
MD5:120A5D9A69FD6B2133F87FB61A5BCC69 | SHA256:E4651793B3C02E93A8D031DB4836C7F884E481F39D72BF831CA19B82D0D51340 | |||
| 2420 | Activator.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\IC8MM | binary | |
MD5:49864D91EDA705BB680AF048D74AD0A5 | SHA256:730DF9B3FFB7D69476D81EF8A20D4F845797B0344233F9C49EB962A378F7518C | |||
| 2420 | Activator.exe | C:\Windows\KMS-R@1n.exe | executable | |
MD5:45CC0A256BED89A997725A6B264CC3EC | SHA256:9D0BB3B3BC50B3CE8FEDEBFA98D9E16D0540AABCA2AA6B00B3C3A442B3C2B84D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report