| File name: | CAI.v17.4.0.0.Architect.exe |
| Full analysis: | https://app.any.run/tasks/74a6ce04-9d2a-4847-b142-8d9ac7459c3d |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2021, 02:24:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 60B0446EE38CE6E4502CF6A0EDFD8409 |
| SHA1: | 4F6110A7B08BDD49F081BC9A58B29A549D7819B4 |
| SHA256: | DE47868C6D0773FA40AF826984629BD7002F5245C6F9A97898268DFA3C88D7F1 |
| SSDEEP: | 6144:tcYxvb8og4mTrzF9lTBtNzEnleKGCD9ckSRFvwvvobmIpIdP:t1xvgXFT7Ntm9ckQAUHC |
MALICIOUS
Loads dropped or rewritten executable
- CAI.v17.4.0.0.Architect.exe (PID: 2732)
SUSPICIOUS
Drops a file with too old compile date
- CAI.v17.4.0.0.Architect.exe (PID: 2732)
Executable content was dropped or overwritten
- CAI.v17.4.0.0.Architect.exe (PID: 2732)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
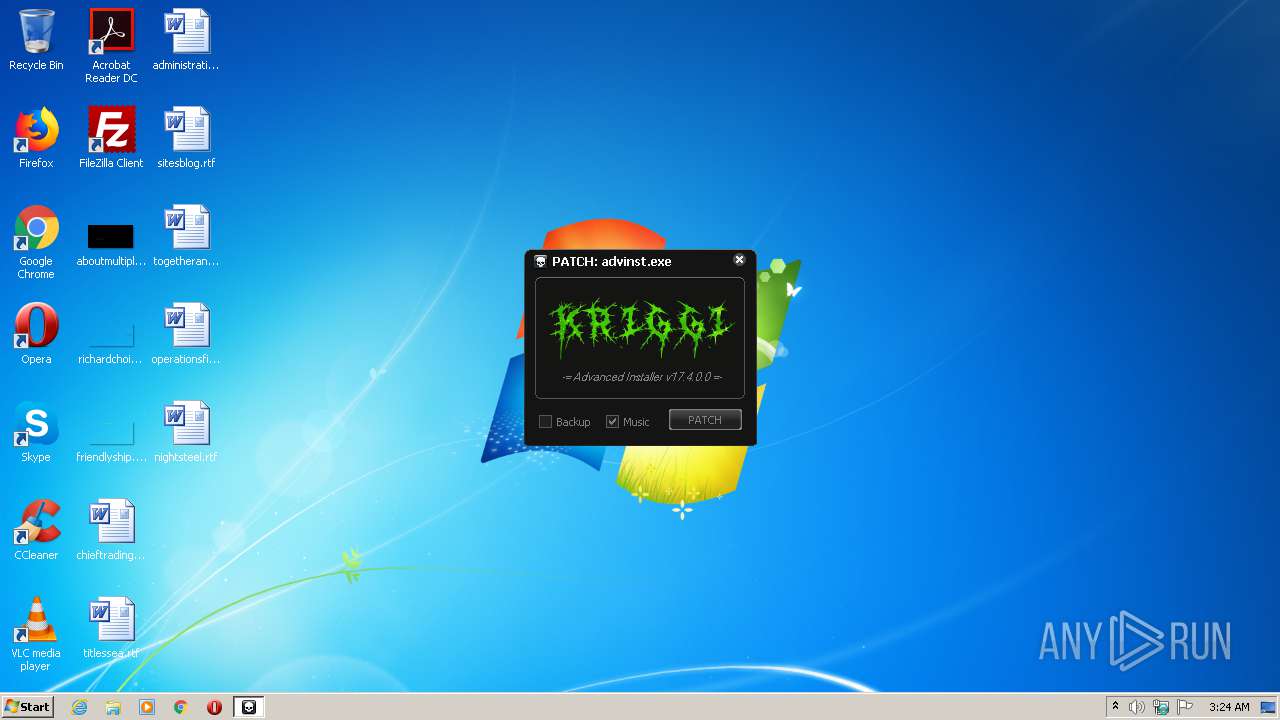
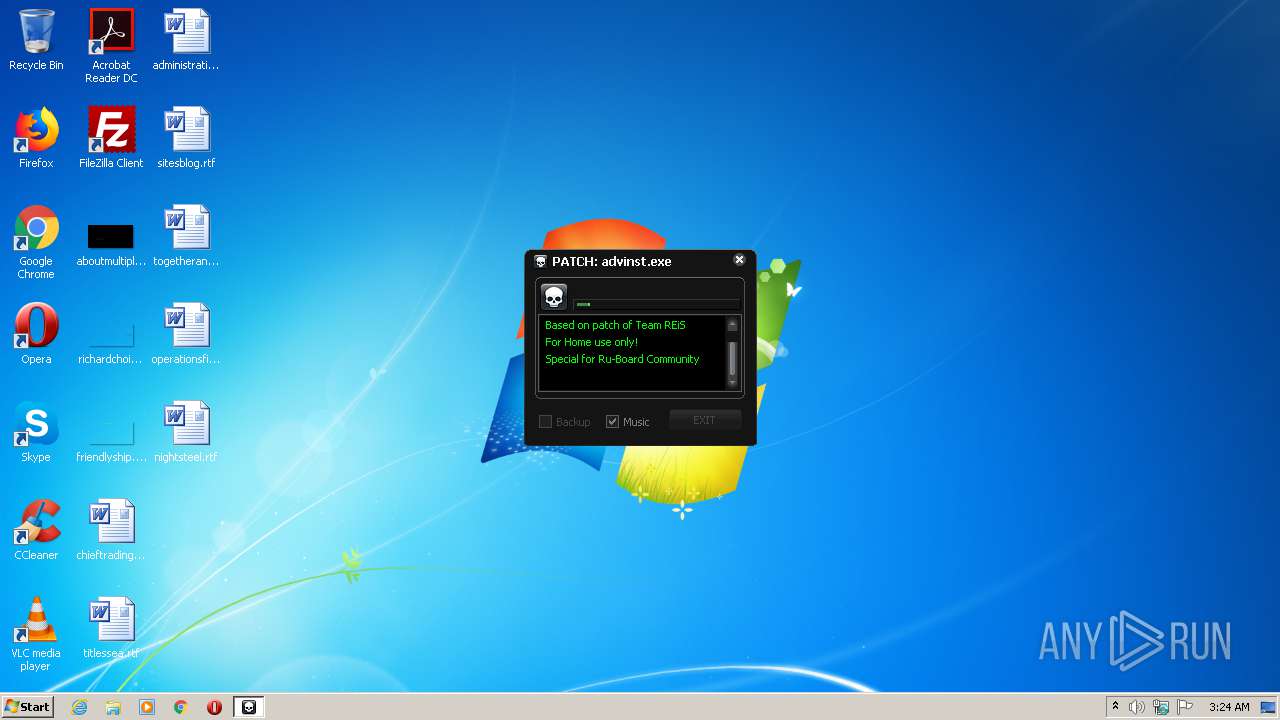
| ProductName: | Patch Advanced Installer |
|---|---|
| LegalTrademarks: | REiS |
| LegalCopyright: | 2020©Kriggi |
| FileVersion: | 1.1.5.0 |
| FileDescription: | Update for Advanced Installer |
| CompanyName: | 2020, Kriggi/REiS |
| Comments: | Created by Kriggi. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.1.4.0 |
| FileVersionNumber: | 1.1.4.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0xb4960 |
| UninitializedDataSize: | 716800 |
| InitializedDataSize: | 20480 |
| CodeSize: | 20480 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2020:02:12 23:11:13+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Feb-2020 22:11:13 |
| Detected languages: |
|
| Comments: | Created by Kriggi. |
| CompanyName: | 2020, Kriggi/REiS |
| FileDescription: | Update for Advanced Installer |
| FileVersion: | 1.1.5.0 |
| LegalCopyright: | 2020©Kriggi |
| LegalTrademarks: | REiS |
| ProductName: | Patch Advanced Installer |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Feb-2020 22:11:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000AF000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000B0000 | 0x00005000 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.83156 |
.rsrc | 0x000B5000 | 0x00005000 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.24924 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.32715 | 1112 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.08554 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.15366 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 7.19738 | 320 | UNKNOWN | English - United States | RT_DIALOG |
106 | 7.10474 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 6.2646 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
36
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
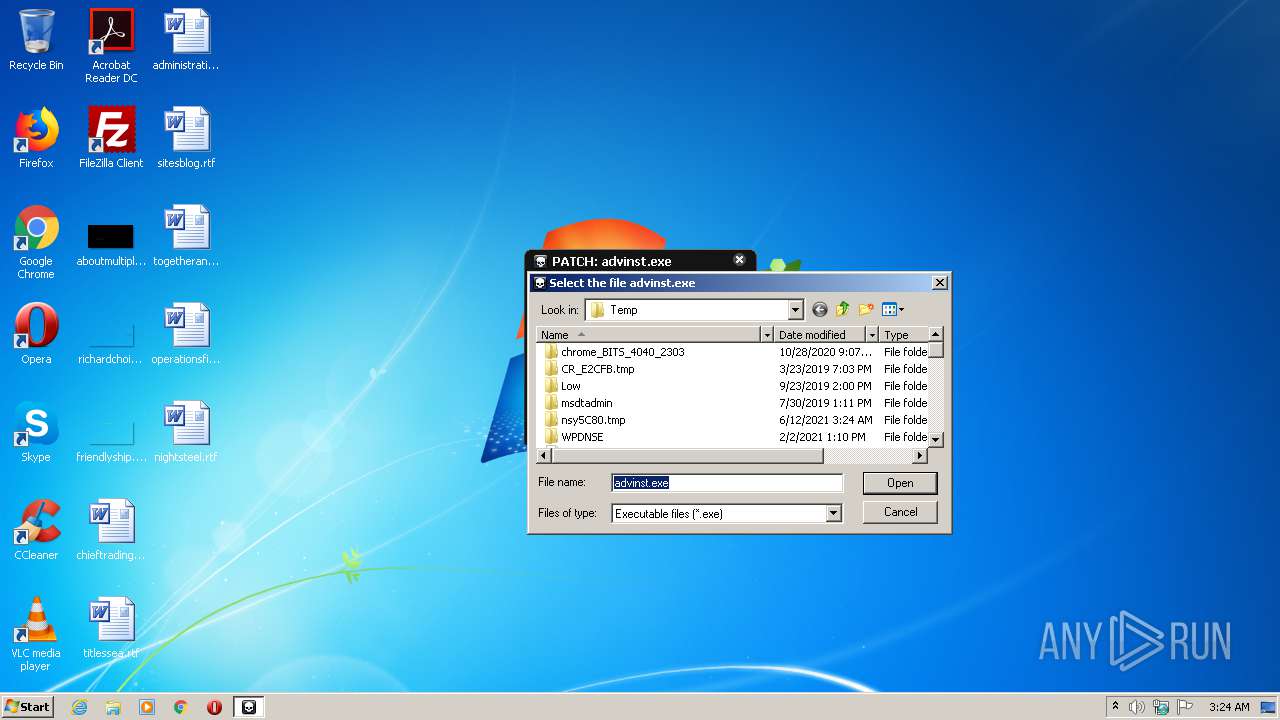
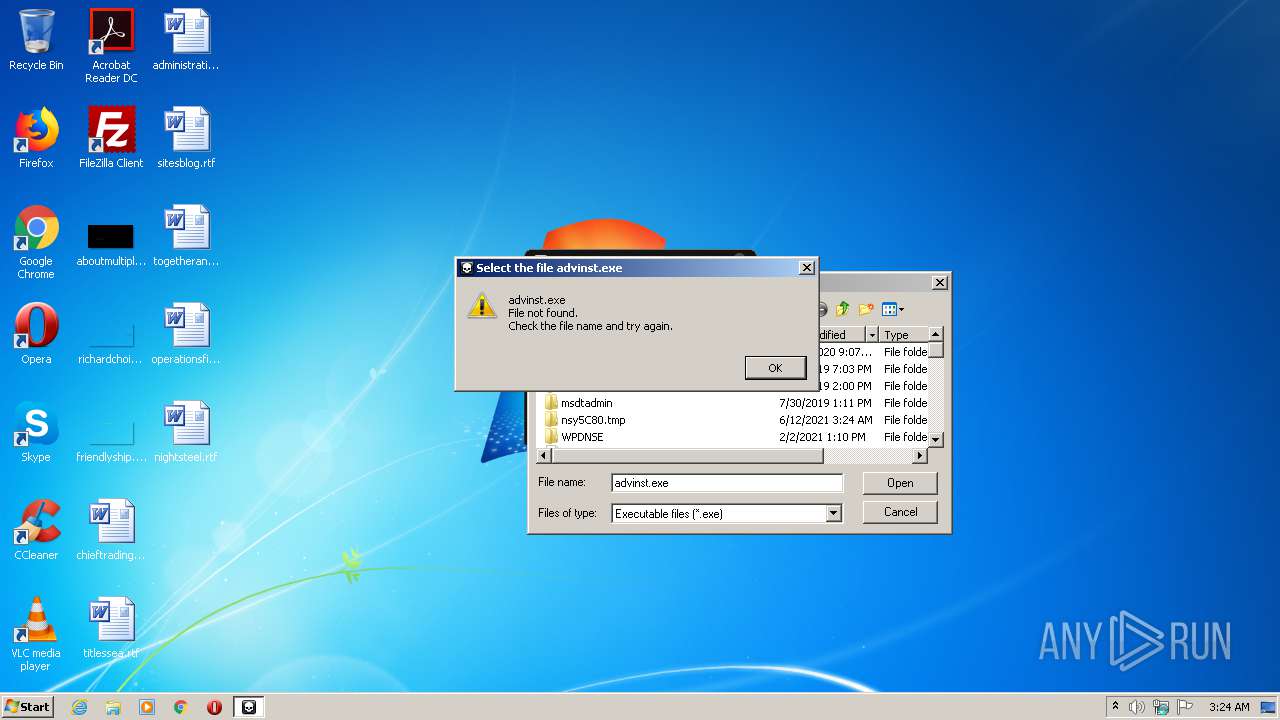
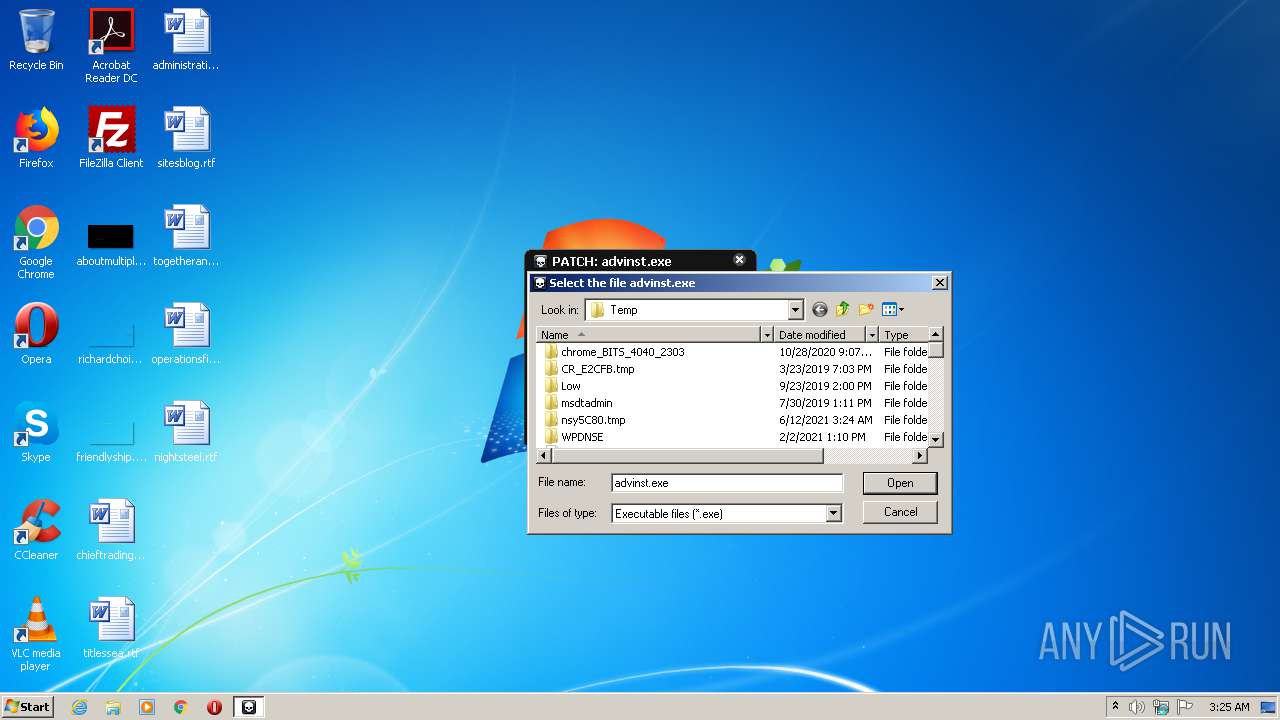
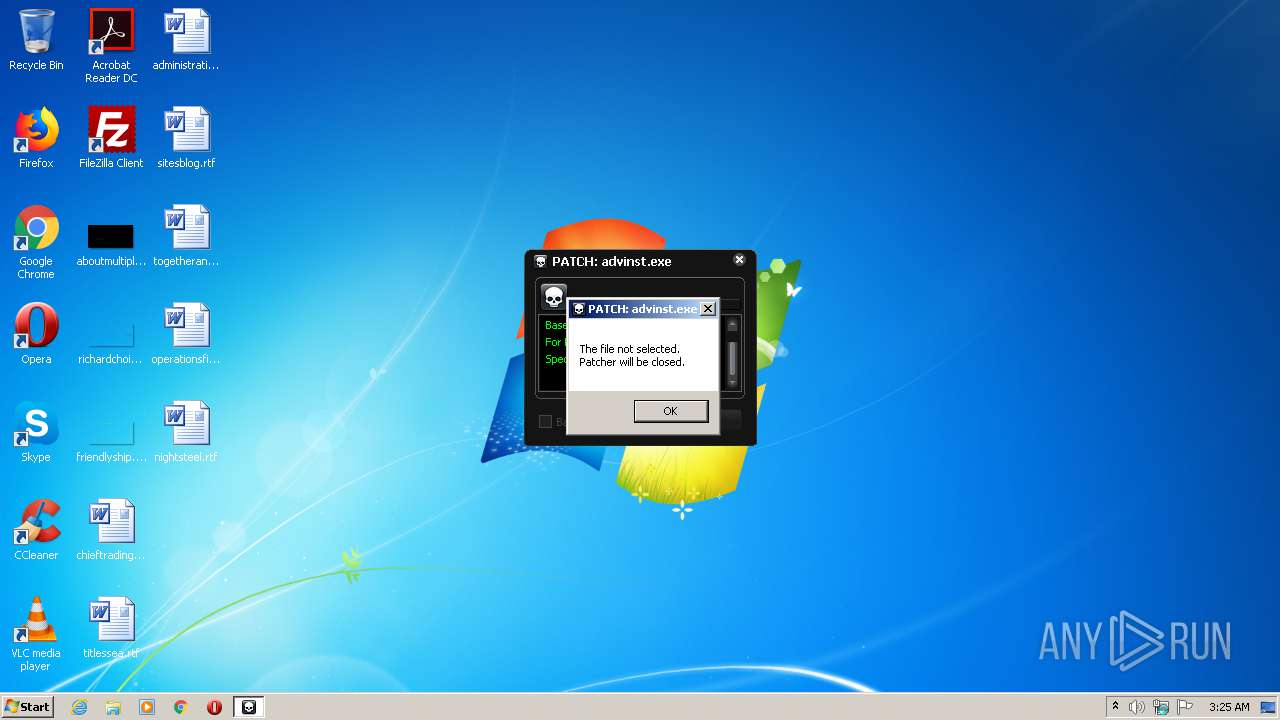
| 2732 | "C:\Users\admin\AppData\Local\Temp\CAI.v17.4.0.0.Architect.exe" | C:\Users\admin\AppData\Local\Temp\CAI.v17.4.0.0.Architect.exe | explorer.exe | ||||||||||||
User: admin Company: 2020, Kriggi/REiS Integrity Level: MEDIUM Description: Update for Advanced Installer Exit code: 0 Version: 1.1.5.0 Modules
| |||||||||||||||
Total events
507
Read events
475
Write events
31
Delete events
1
Modification events
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C004300410049002E007600310037002E0034002E0030002E0030002E004100720063006800690074006500630074002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 070000000100000000000000020000000B0000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 3 |
Value: 4300410049002E007600310037002E0034002E0030002E0030002E004100720063006800690074006500630074002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000F0200000F010000B90300001702000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 3 |
Value: 4300410049002E007600310037002E0034002E0030002E0030002E004100720063006800690074006500630074002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000F0200000F010000B90300001702000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 3 |
Value: 4300410049002E007600310037002E0034002E0030002E0030002E004100720063006800690074006500630074002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000B020000F8000000F6020000BE0100000F0200000F010000B90300001702000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2732) CAI.v17.4.0.0.Architect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000020000000100000000000000FFFFFFFF | |||
Executable files
6
Suspicious files
1
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\patch.bmp | image | |
MD5:— | SHA256:— | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\strangetris.xm | xm | |
MD5:— | SHA256:— | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\SkinH.dll | executable | |
MD5:205E3693CB24B95018EAEE62AF86AE03 | SHA256:4954323E4532552E5B3691986D579FDCE8EBE60B6EC1EB049658103E05C9D52D | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\bassmod.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\ButtonEvent.dll | executable | |
MD5:55788069D3FA4E1DAF80F3339FA86FE2 | SHA256:D6E429A063ADF637F4D19D4E2EB094D9FF27382B21A1F6DCCF9284AFB5FF8C7F | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\crc.exe | executable | |
MD5:F3086C21B96EC02DF3BB8B147C0A707C | SHA256:F4D02C51EB6C1A2BE918898CE9AEAEDEC23851647362EA307BA9242D80F4E4D5 | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\skinh.she | binary | |
MD5:05ADAC05496F567275819EA16AA406E4 | SHA256:93DEAB5004A59AFD1419AEA862D67BE375D880EC5C62990A585D8648BE9C27C7 | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\nsDialogs.dll | executable | |
MD5:E7411F8CC064A675709E32CFBDE95201 | SHA256:961788AAA469E9B55981AE07DE02AB132354CC3D64BEF6915589653B8D08CEBA | |||
| 2732 | CAI.v17.4.0.0.Architect.exe | C:\Users\admin\AppData\Local\Temp\nsy5C80.tmp\System.dll | executable | |
MD5:C72727780796203CF4514C867304908D | SHA256:8AC8FFC8059EC1F27398081D44B18D0B5734124767DF80EFEF654AE2633461BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report