| download: | gmer.zip |
| Full analysis: | https://app.any.run/tasks/c69de14a-b50e-492f-9768-89ac8a5b56ad |
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2020, 00:55:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
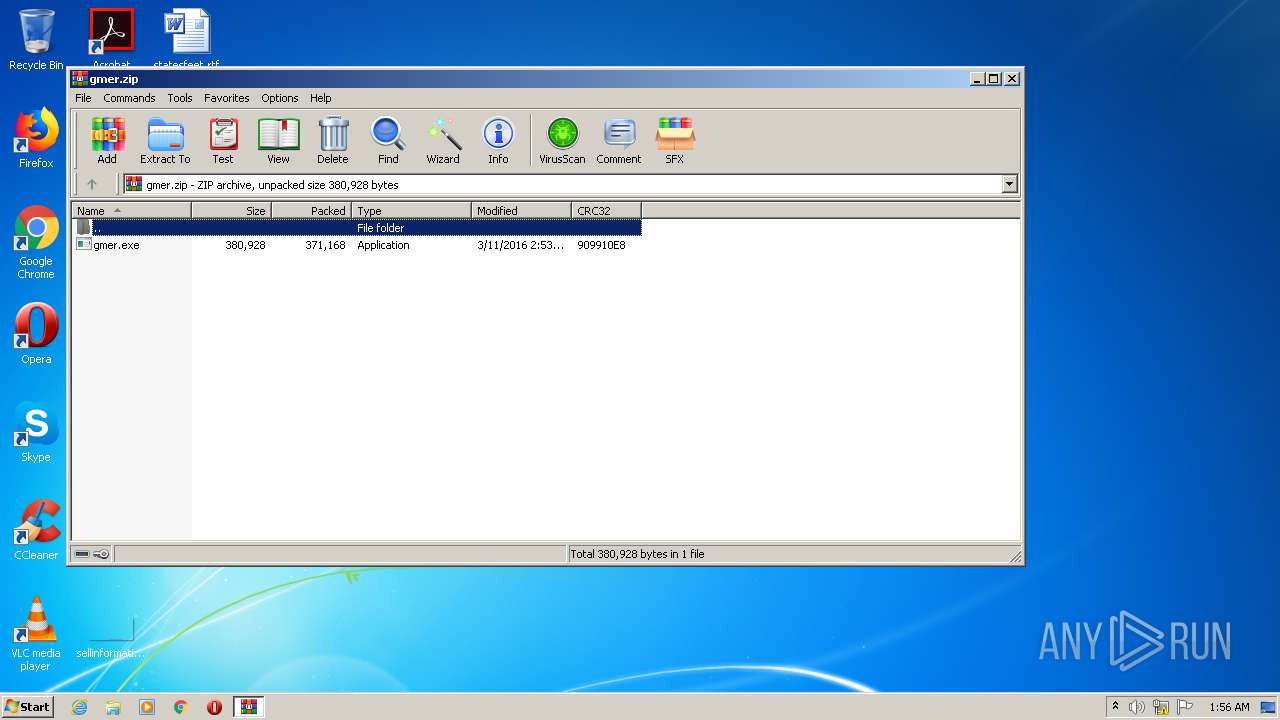
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | FC98D351CA1A64897503036E665E14C6 |
| SHA1: | 3FB1EA6EADF5551E5B81C22B0A45CE892C5A87B2 |
| SHA256: | DE3ABDE117D7EACBB638BC7D0151F929CF80A4BB5E5BEB1E390839E96FC6722A |
| SSDEEP: | 6144:uBzWZvuPzYt+4gpqK6w+cdLMXzl3udtSToGLjwaurCDG2h46ArZLtQ2AA:Wz4k2+nzANXz5u3HX6AdLAA |
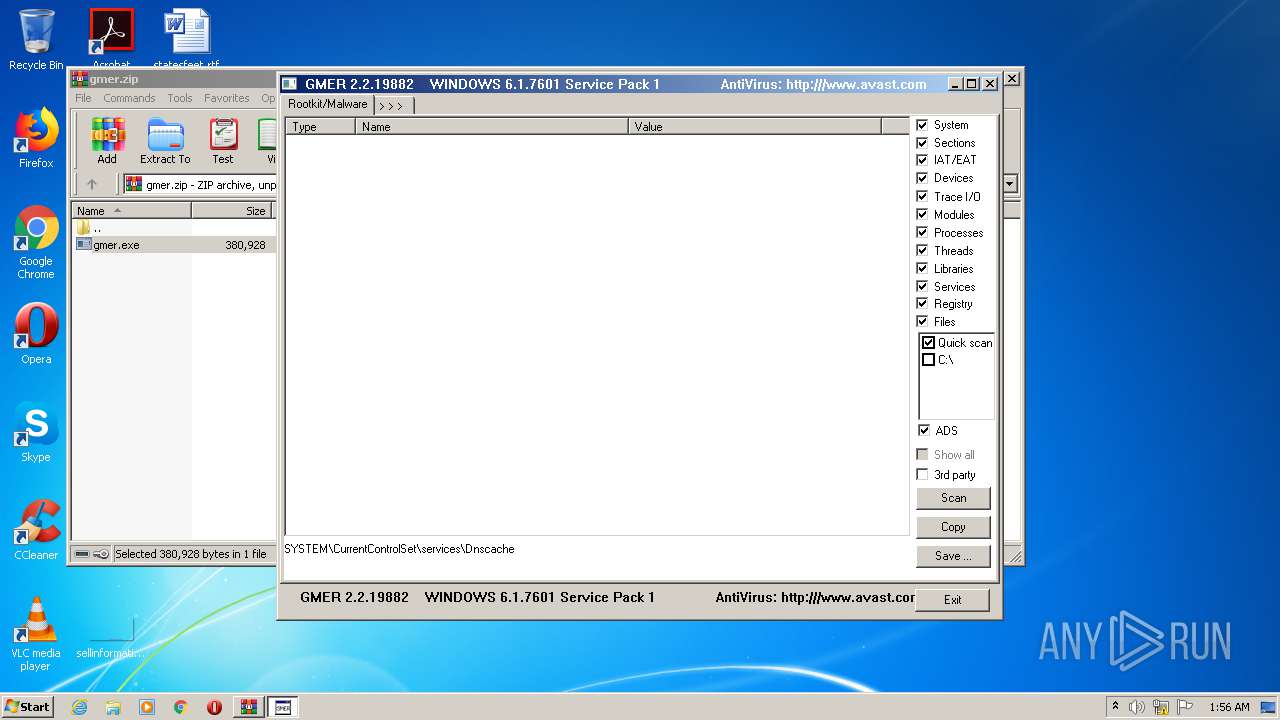
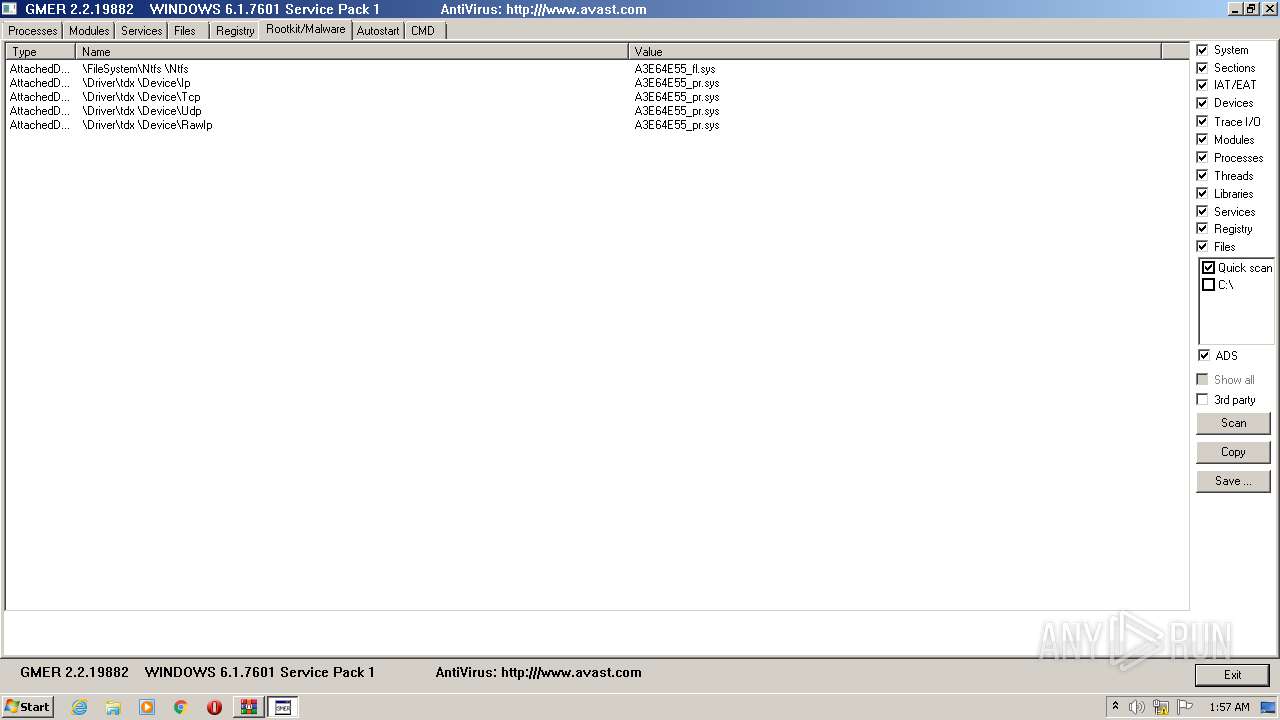
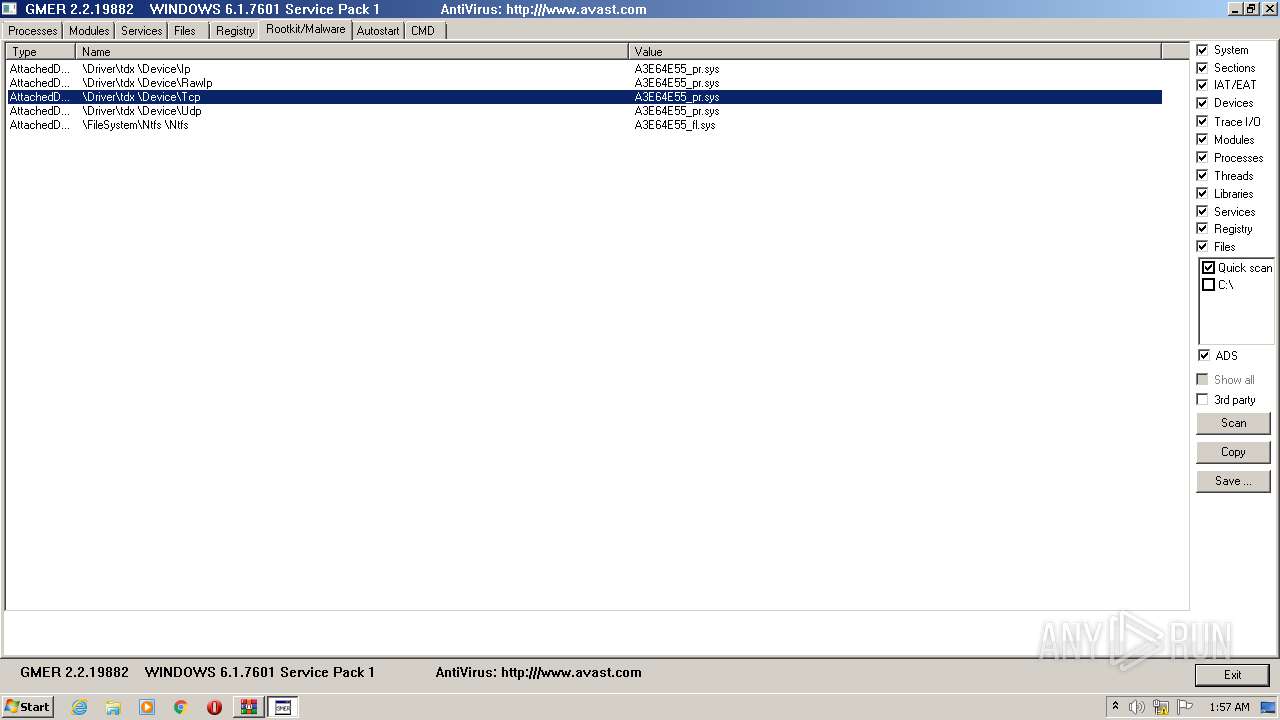
MALICIOUS
Application was dropped or rewritten from another process
- gmer.exe (PID: 3196)
- gmer.exe (PID: 2276)
SUSPICIOUS
Executable content was dropped or overwritten
- gmer.exe (PID: 2276)
- WinRAR.exe (PID: 2300)
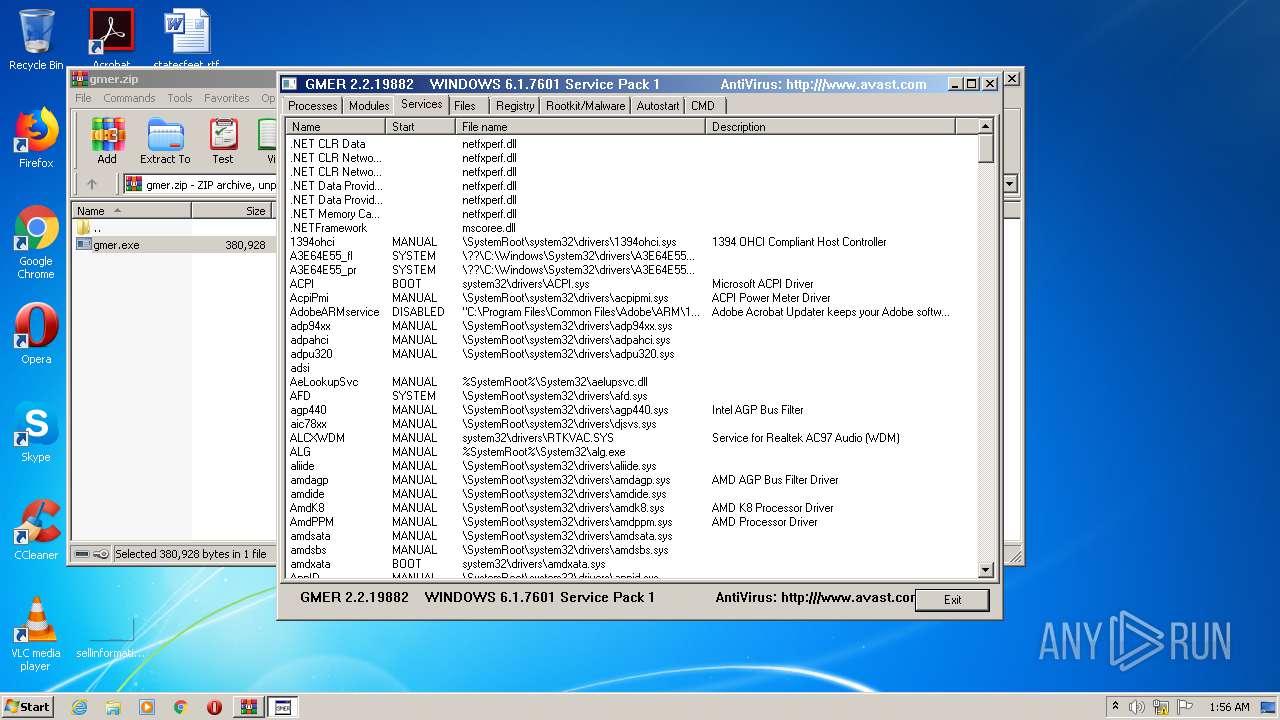
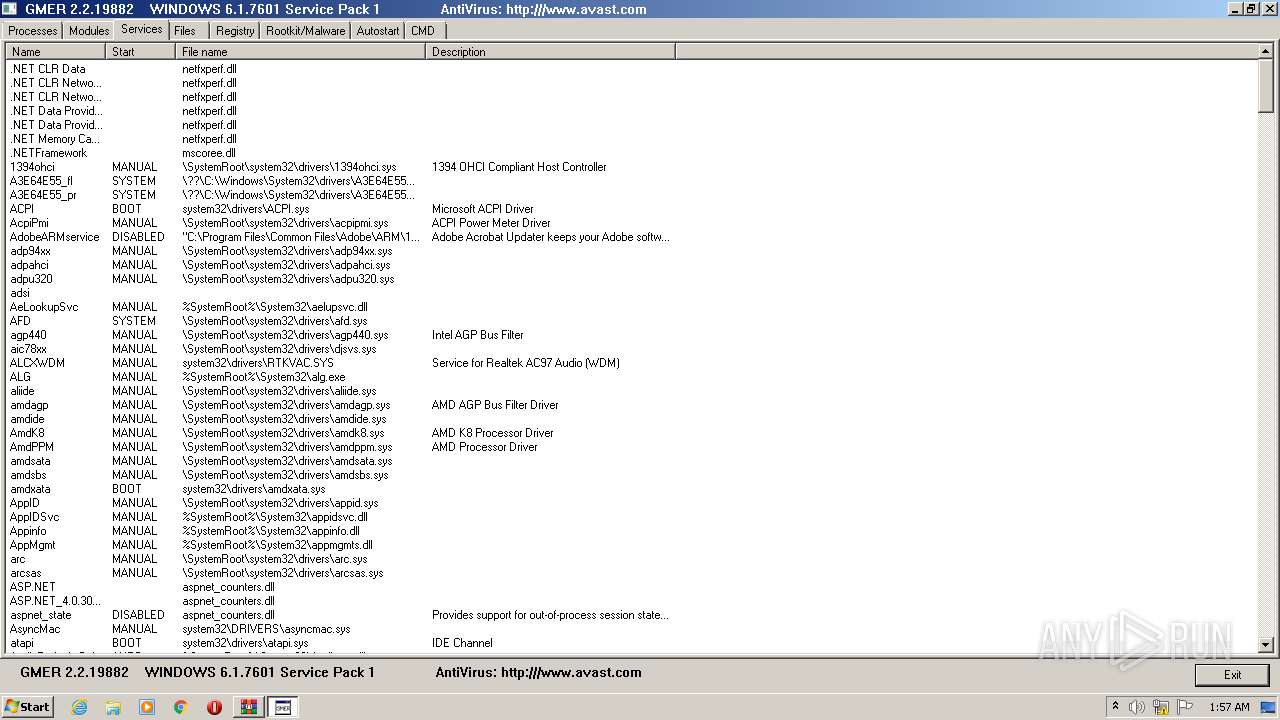
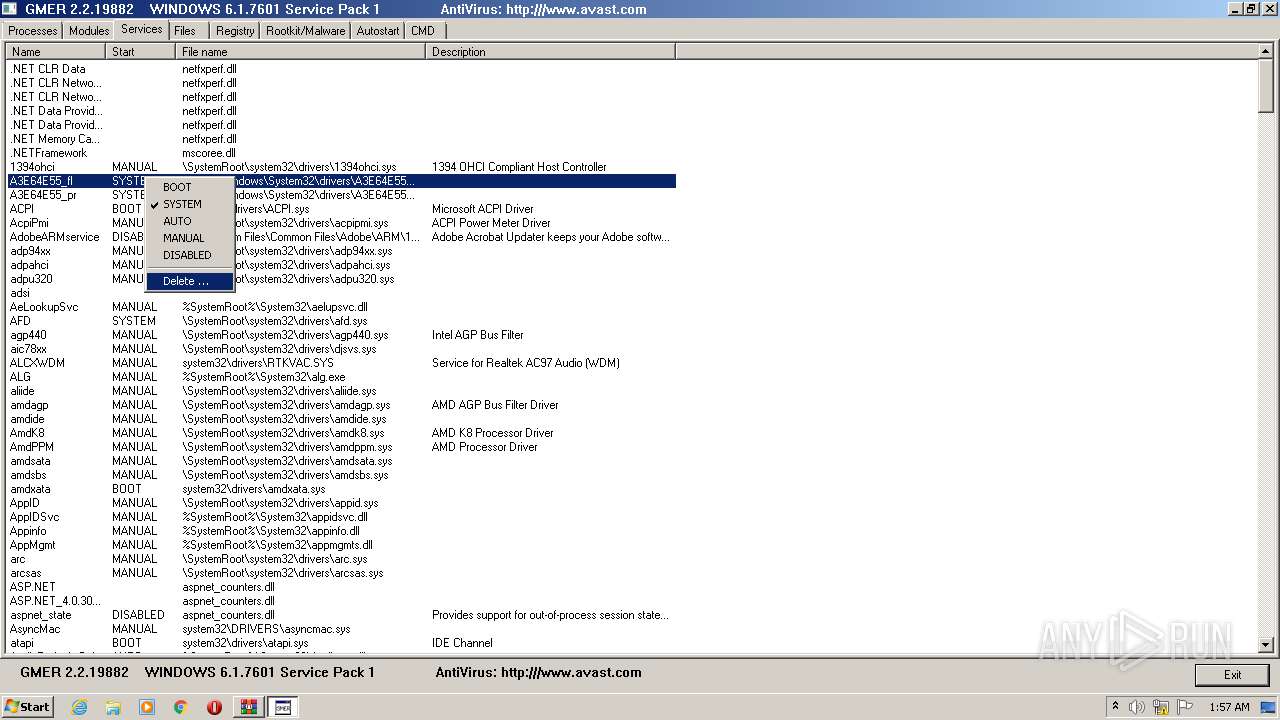
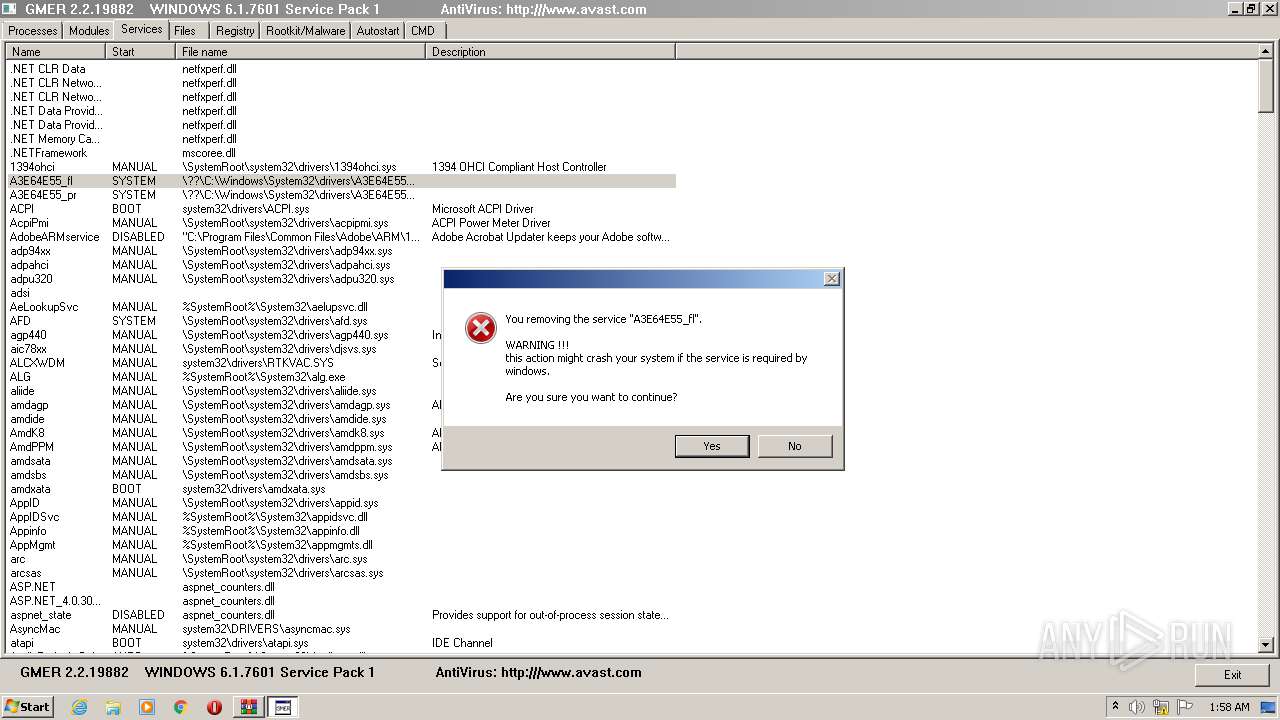
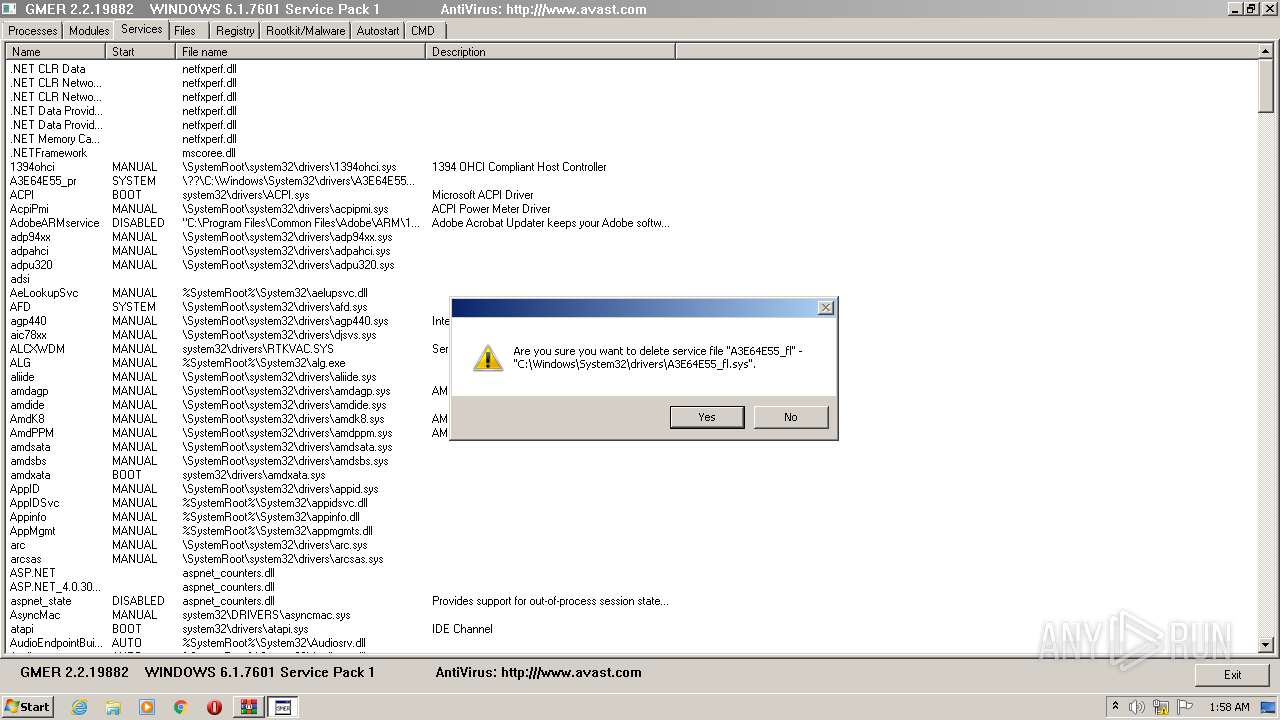
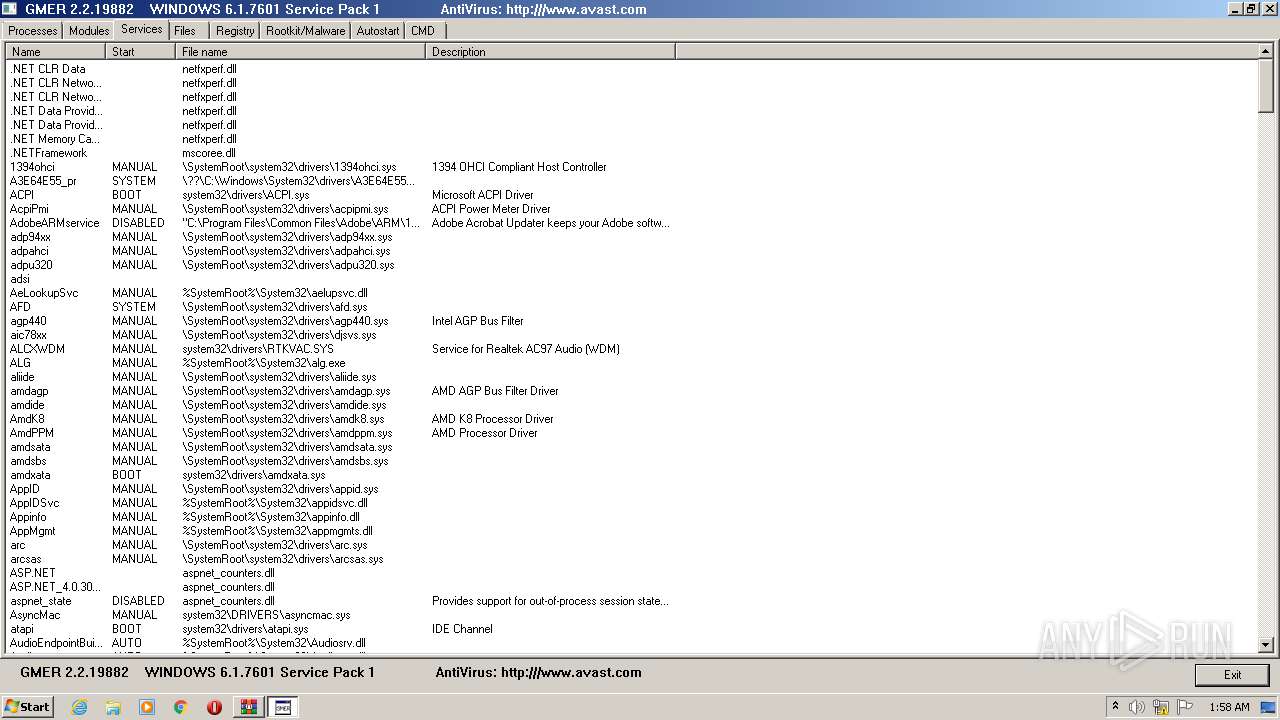
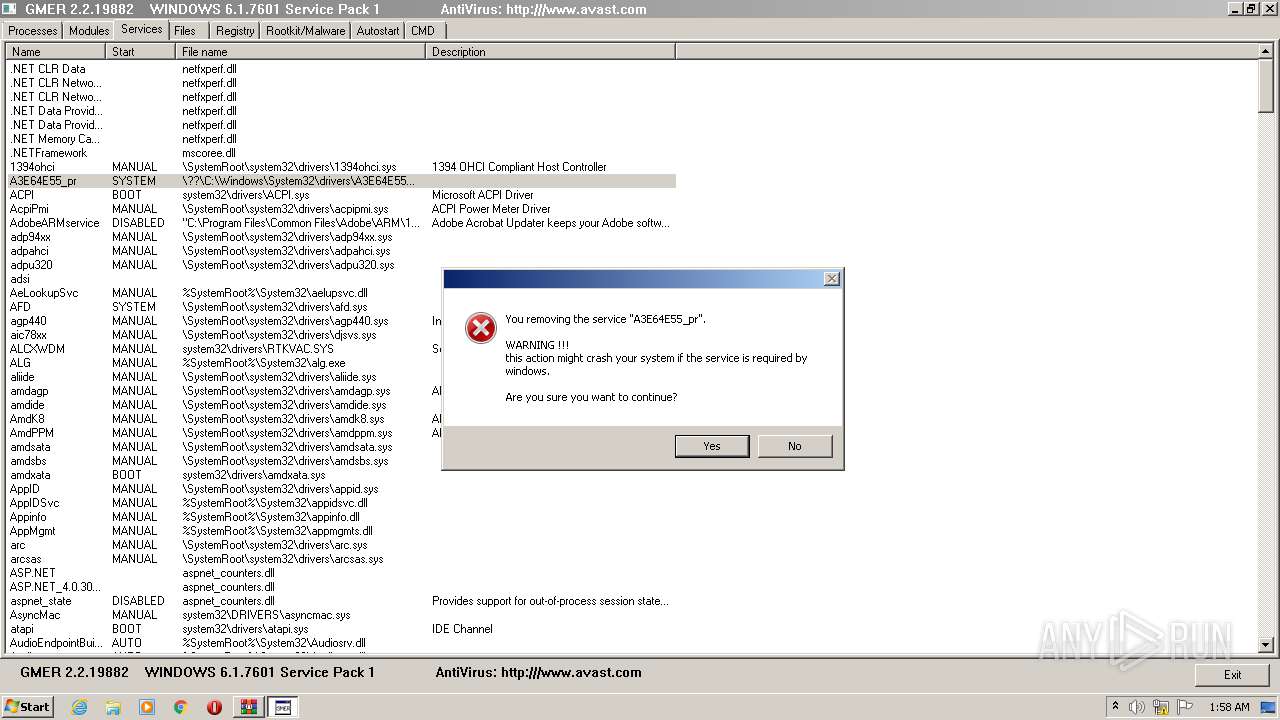
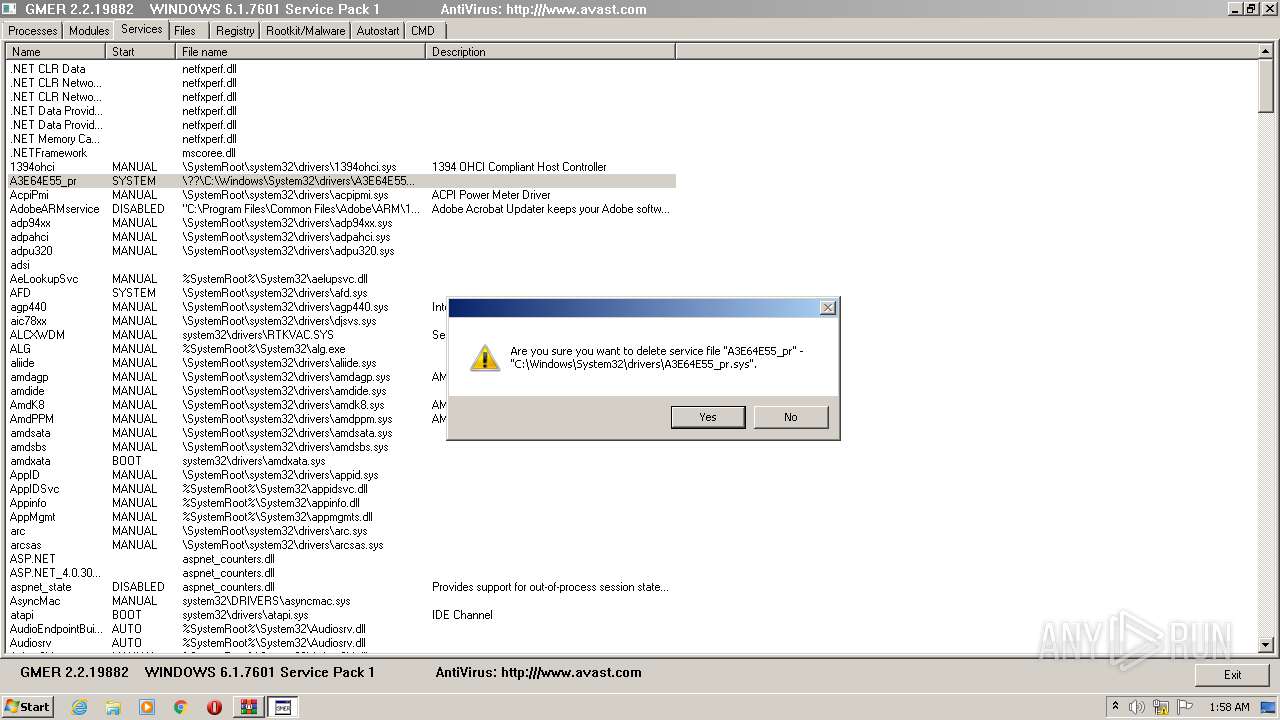
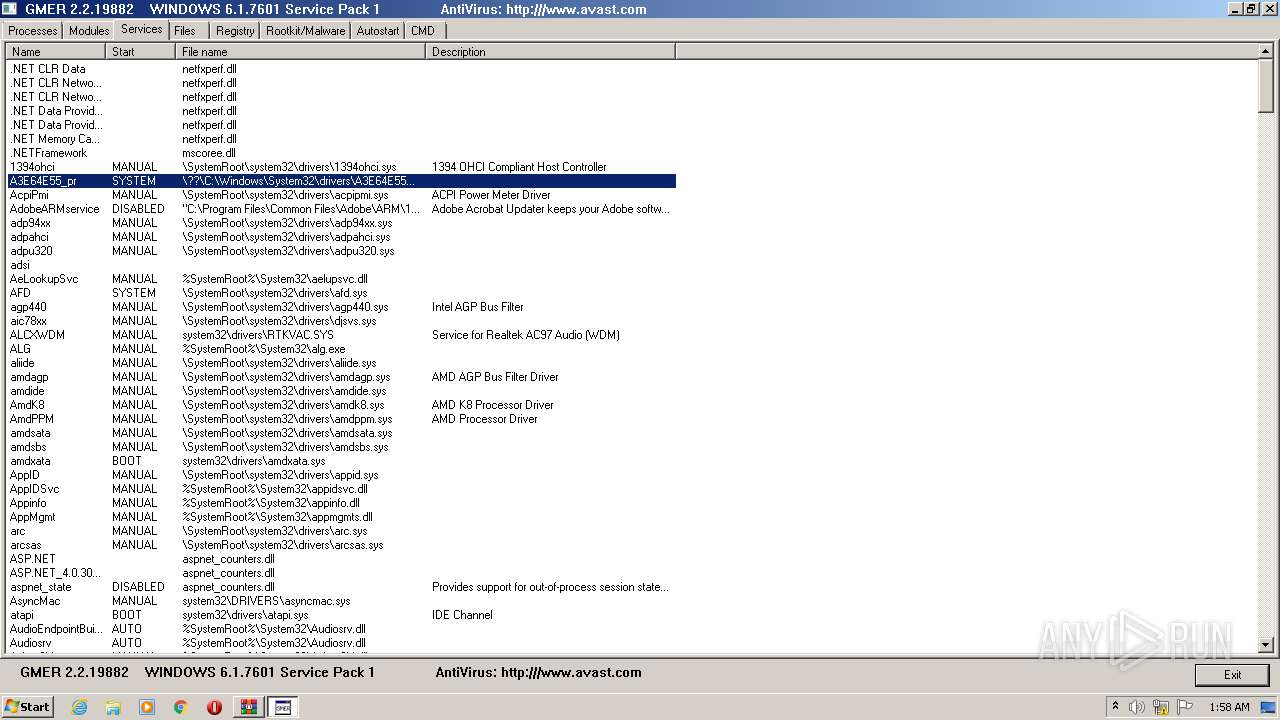
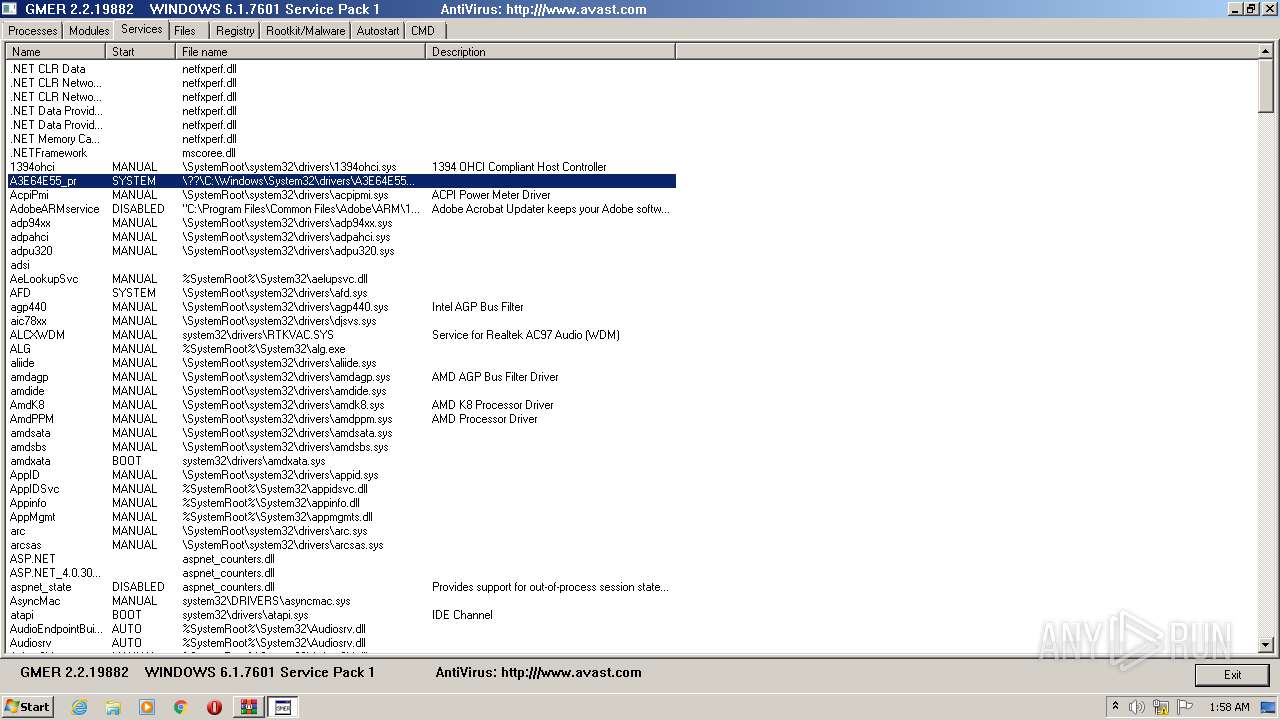
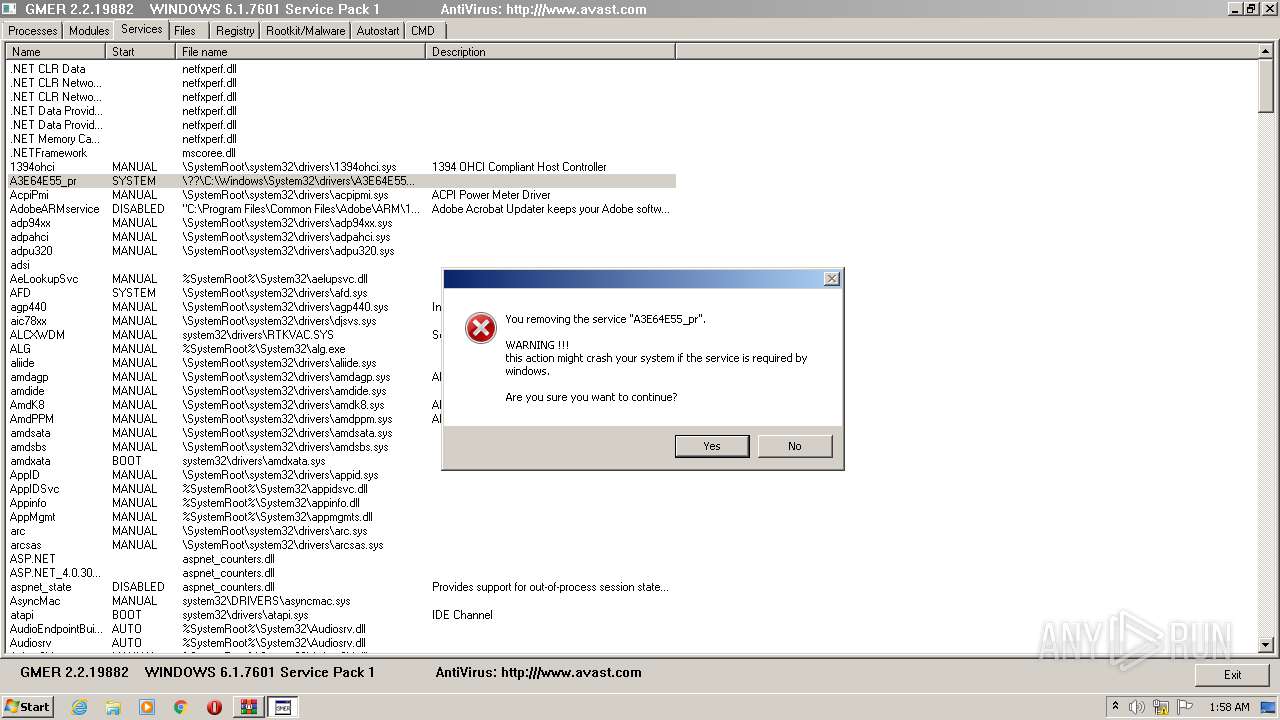
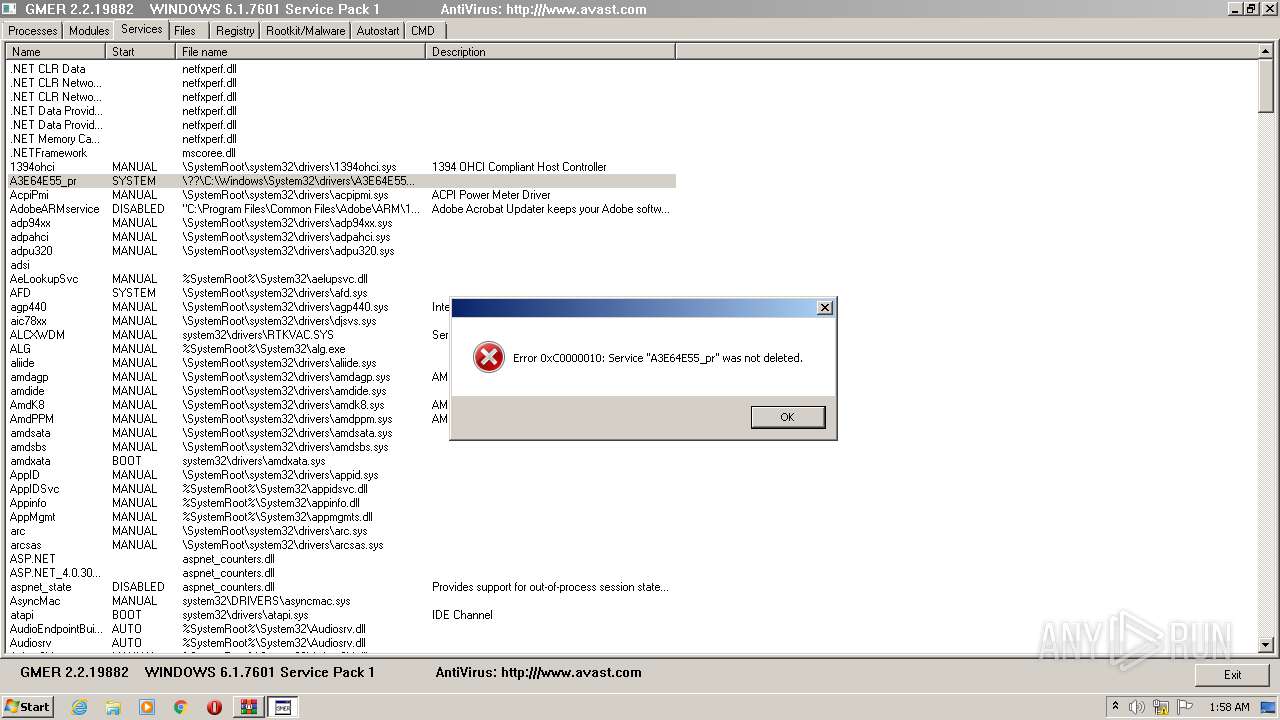
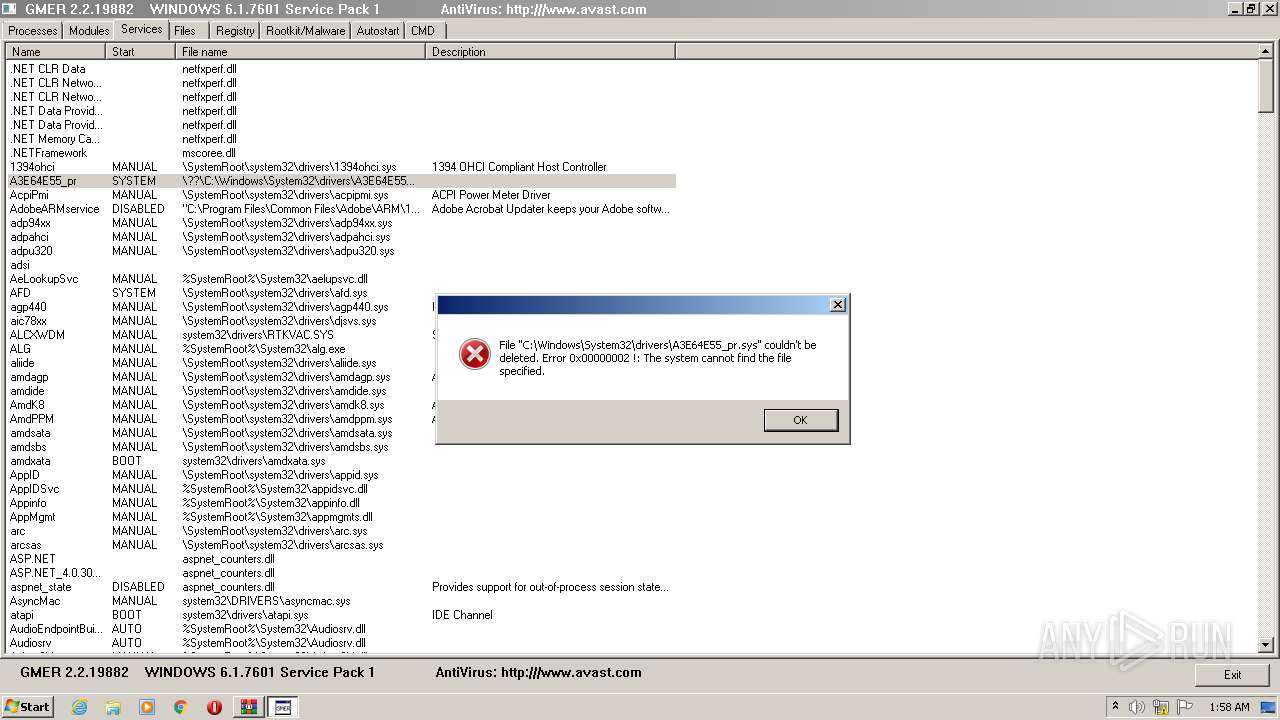
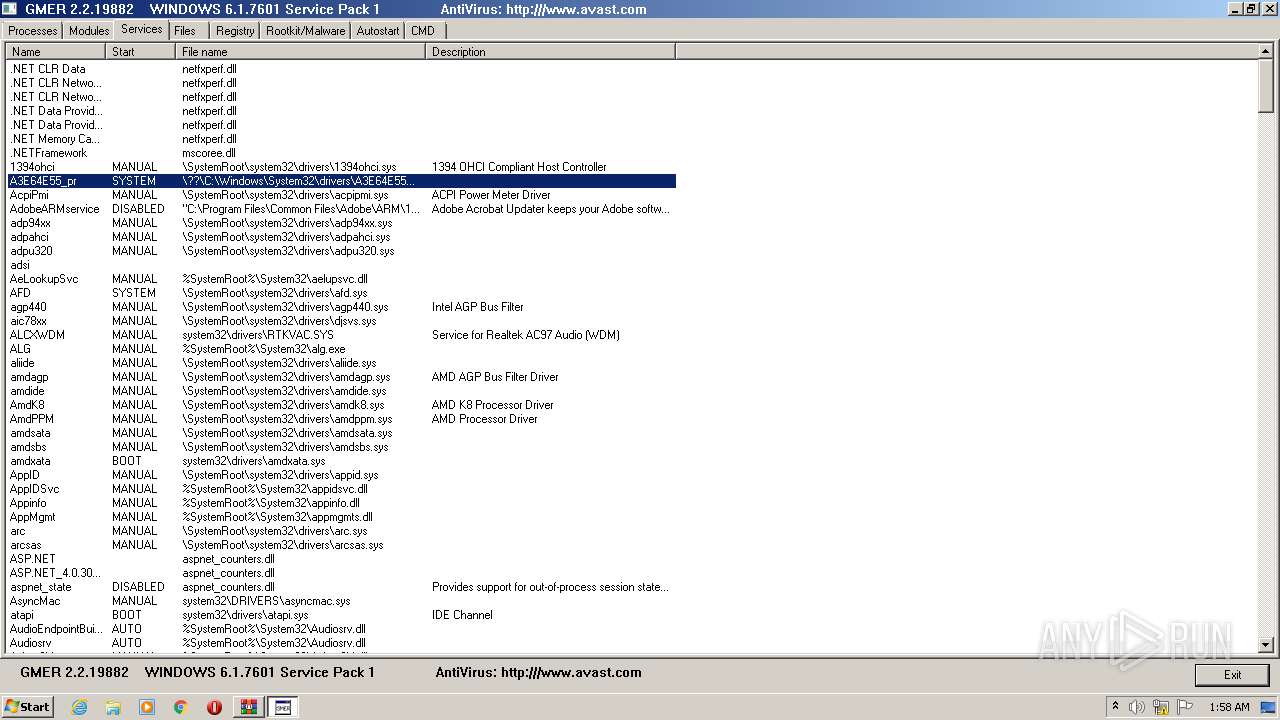
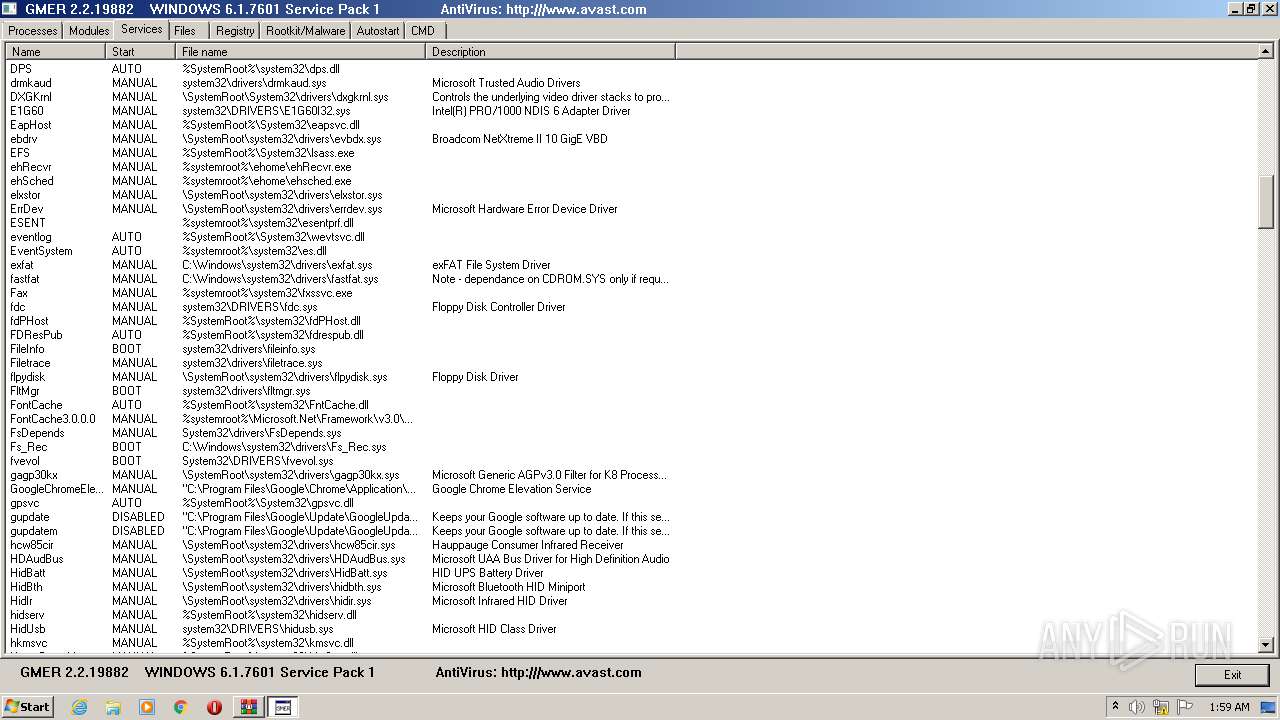
Creates or modifies windows services
- gmer.exe (PID: 2276)
Low-level read access rights to disk partition
- gmer.exe (PID: 2276)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:03:11 14:53:07 |
| ZipCRC: | 0x909910e8 |
| ZipCompressedSize: | 371168 |
| ZipUncompressedSize: | 380928 |
| ZipFileName: | gmer.exe |
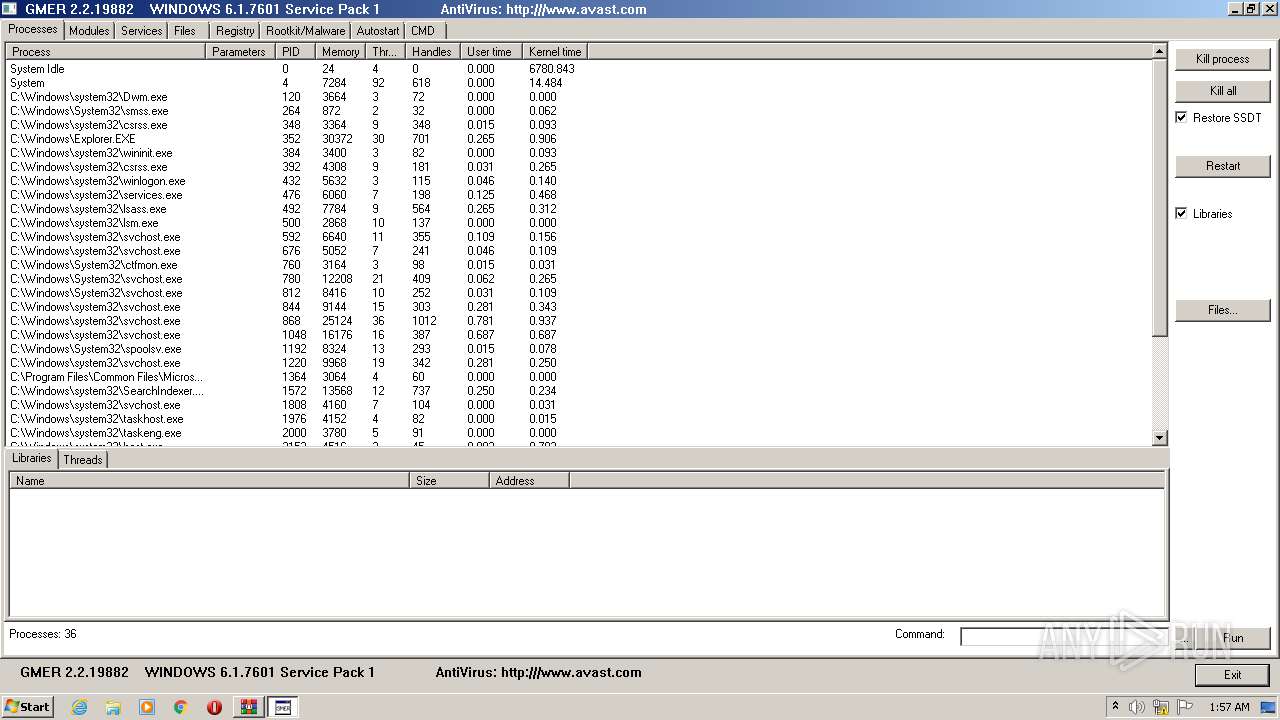
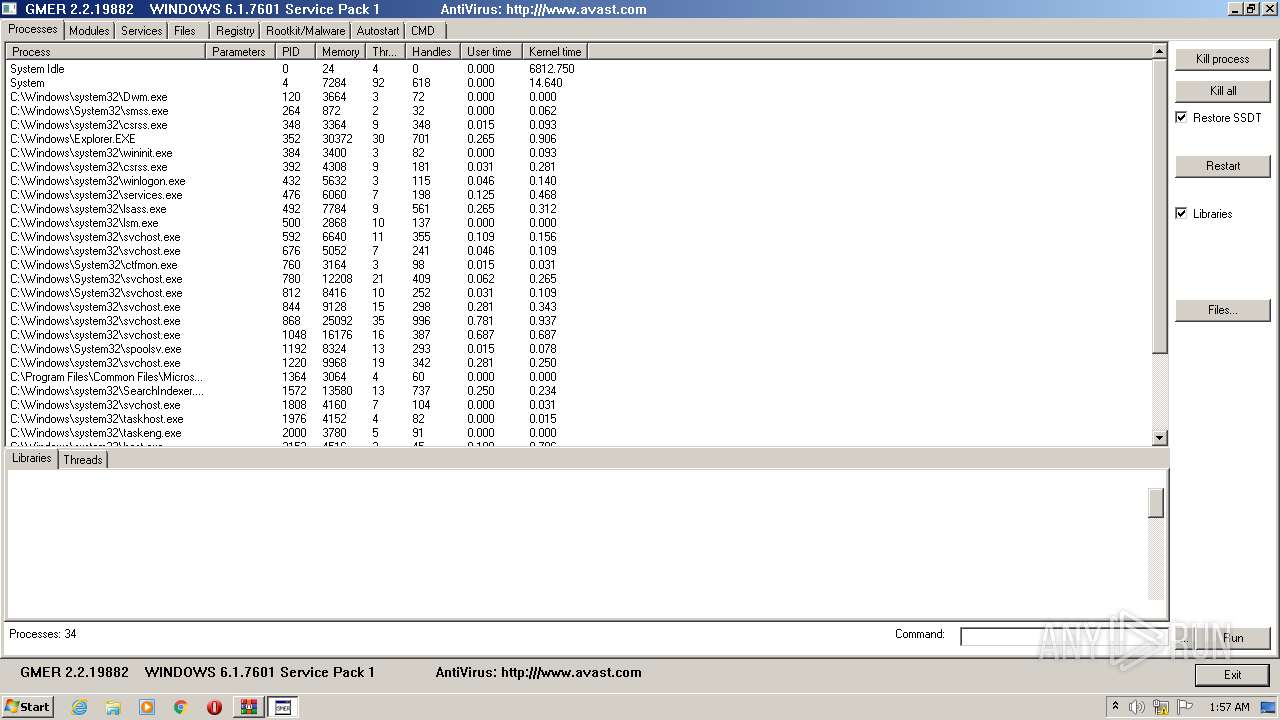
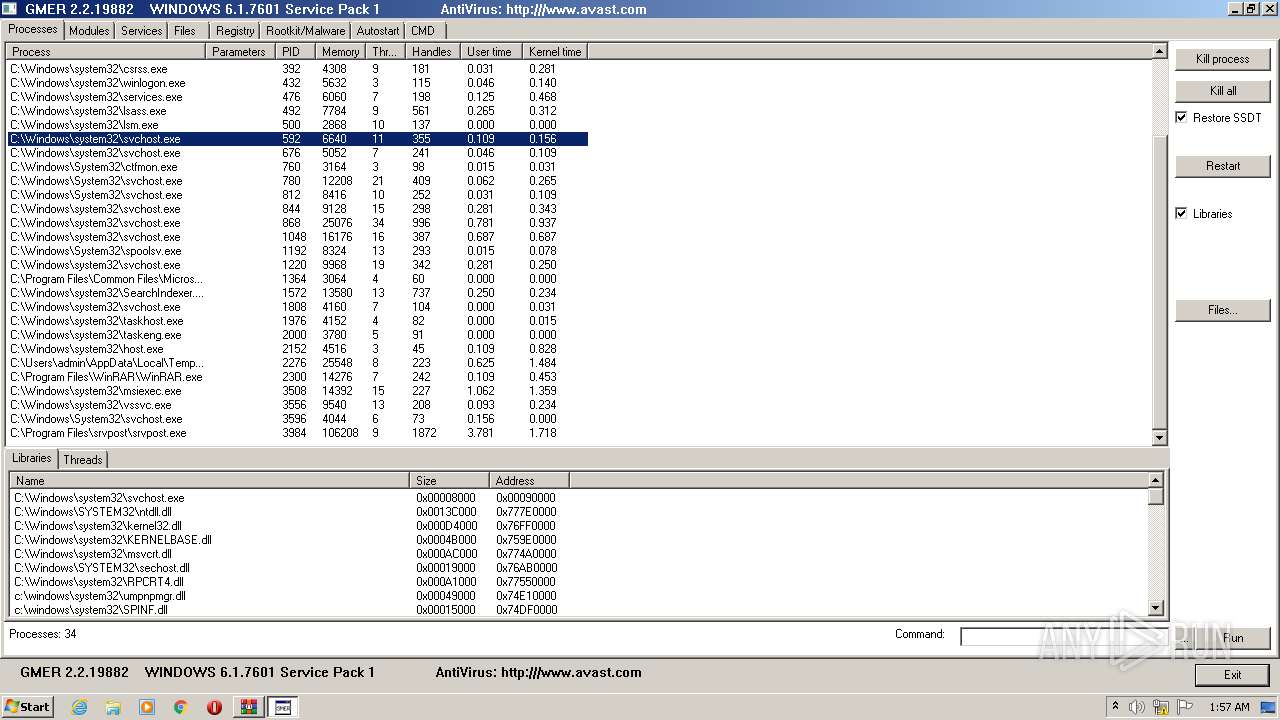
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
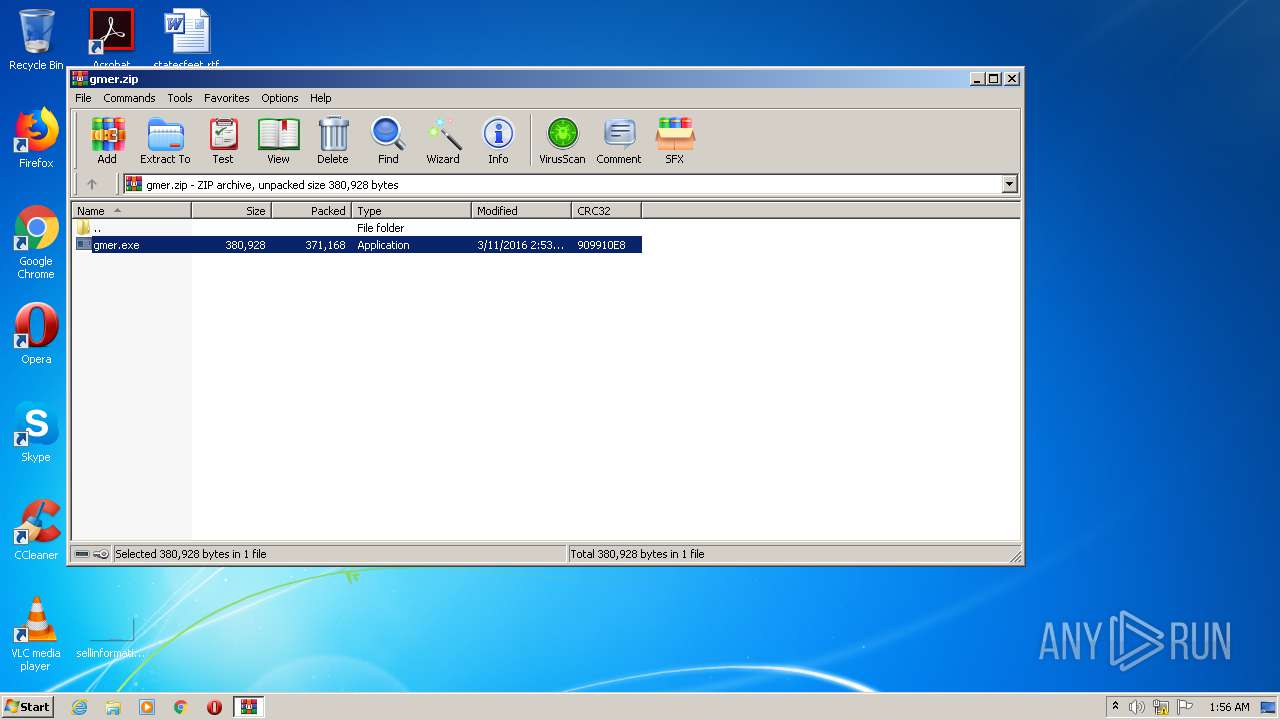
| 2276 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2300.30944\gmer.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2300.30944\gmer.exe | WinRAR.exe | ||||||||||||
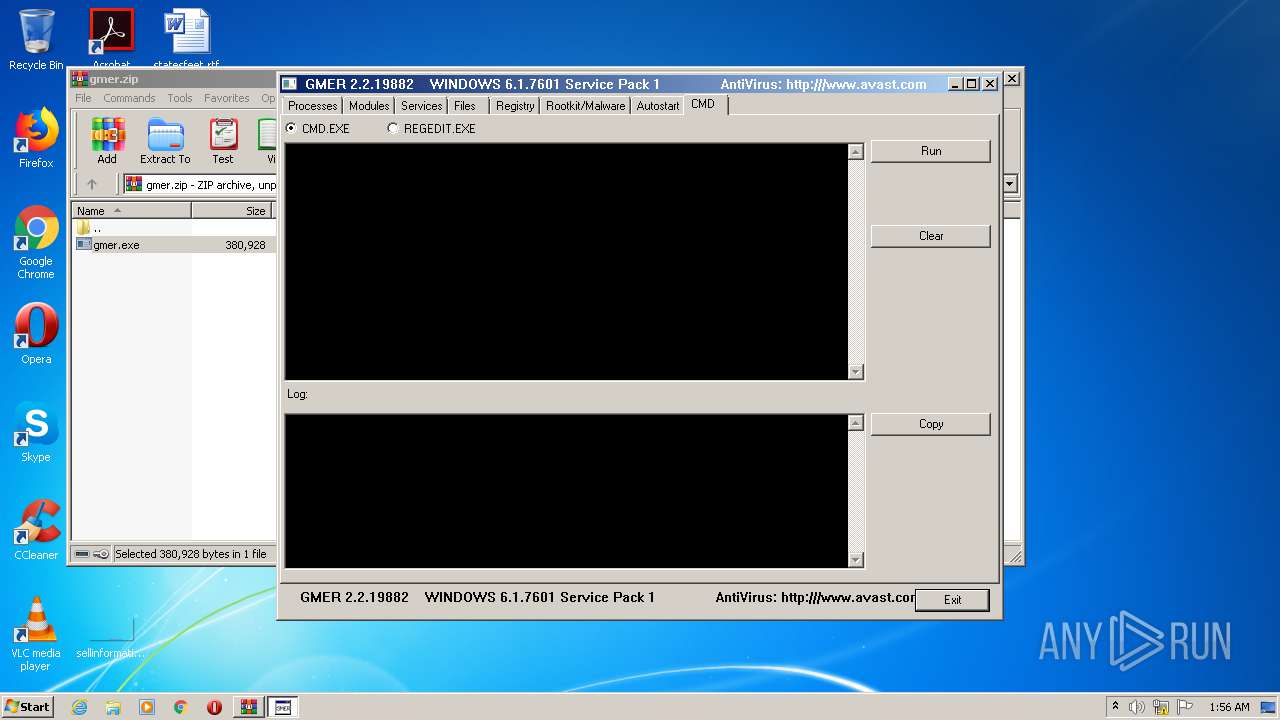
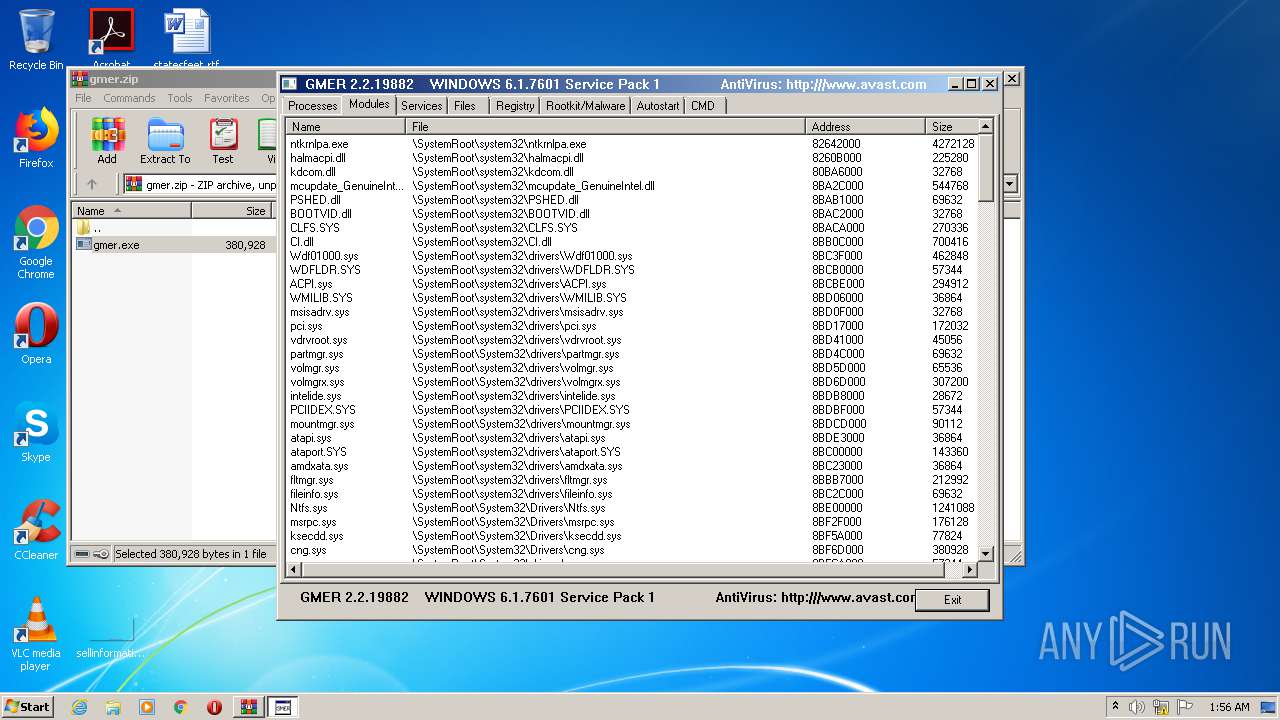
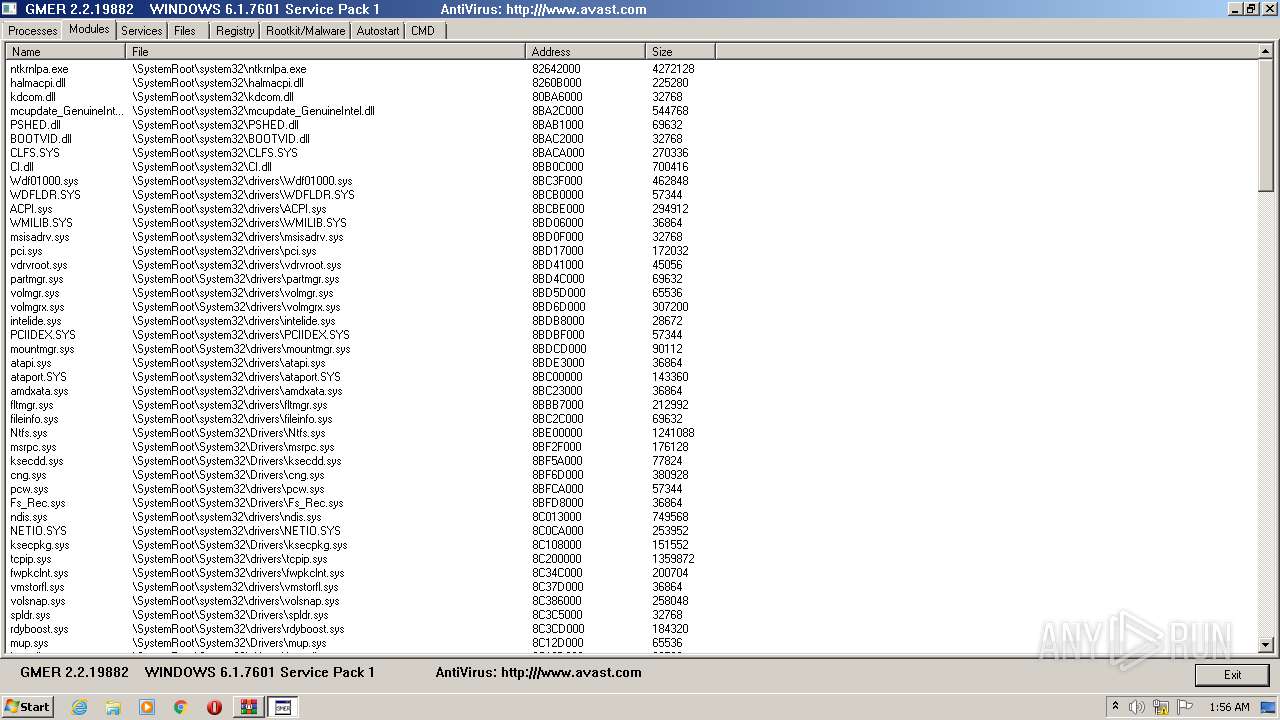
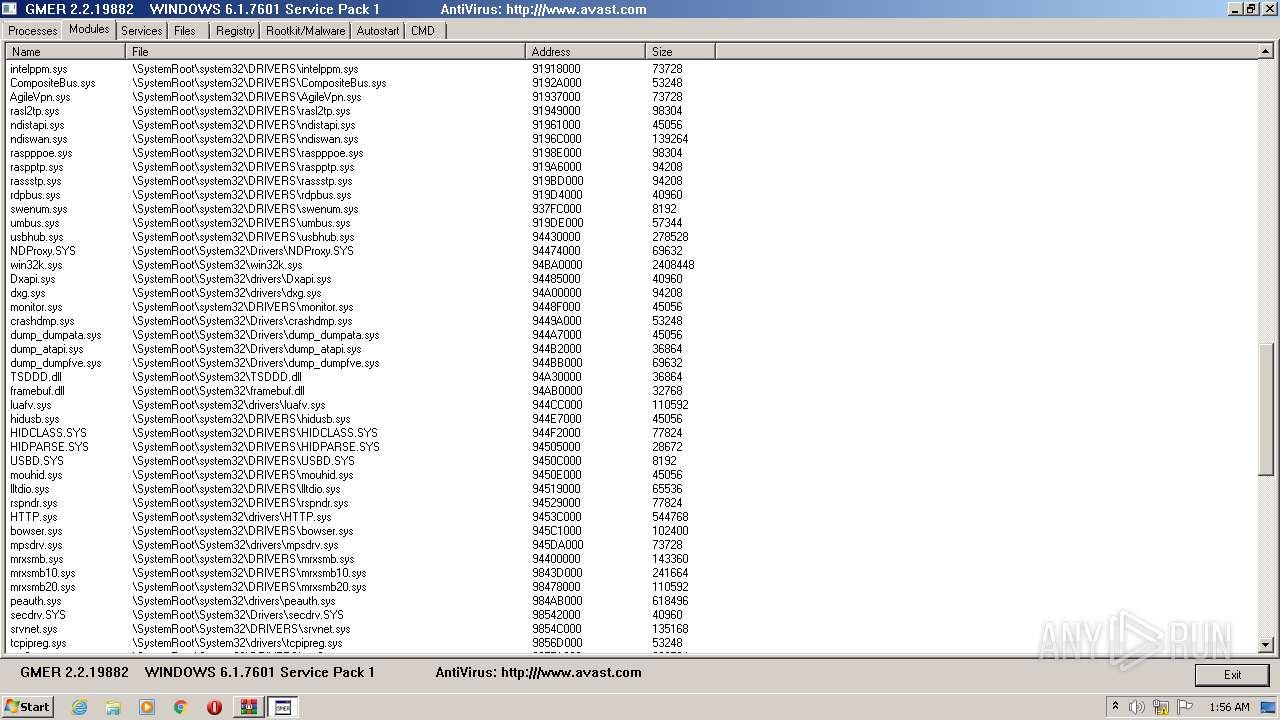
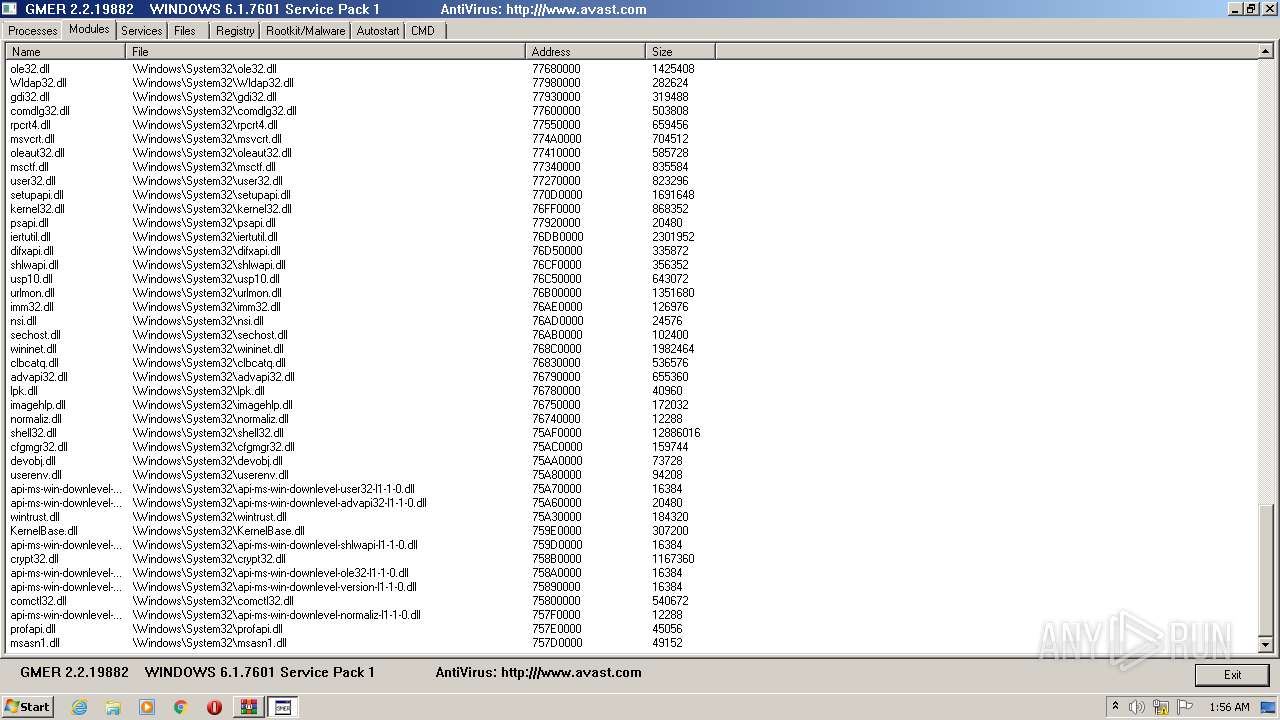
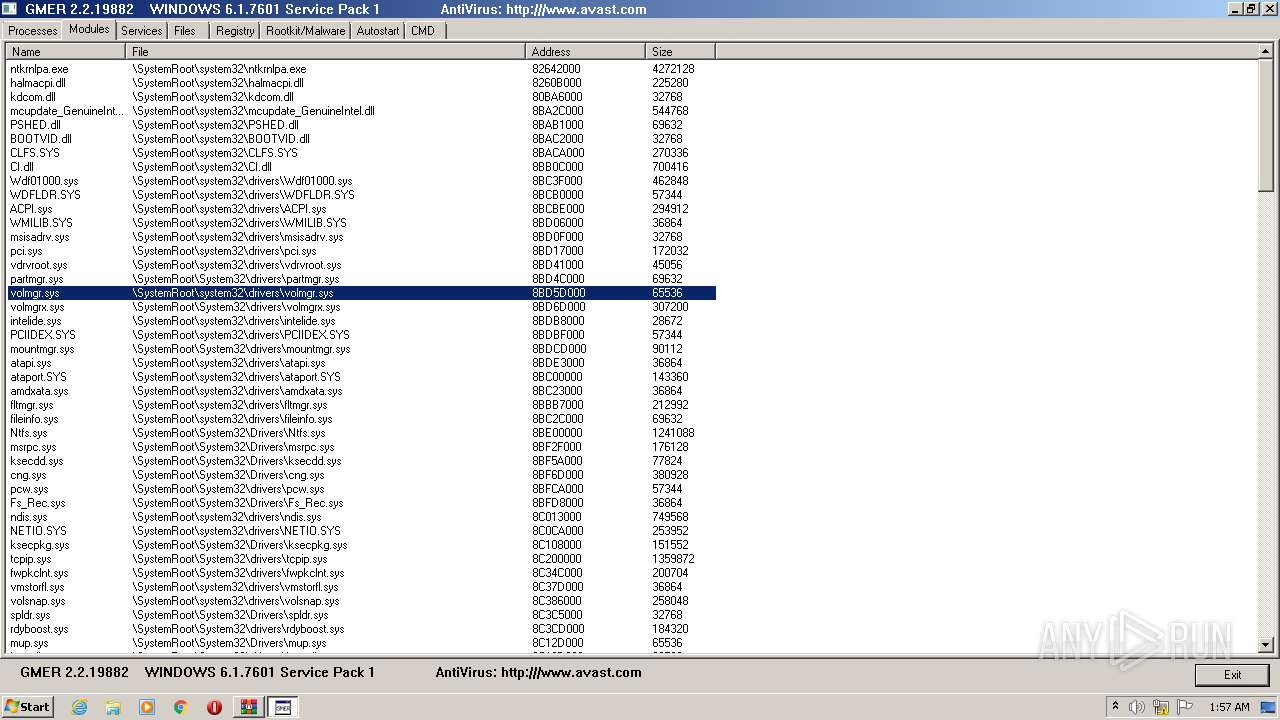
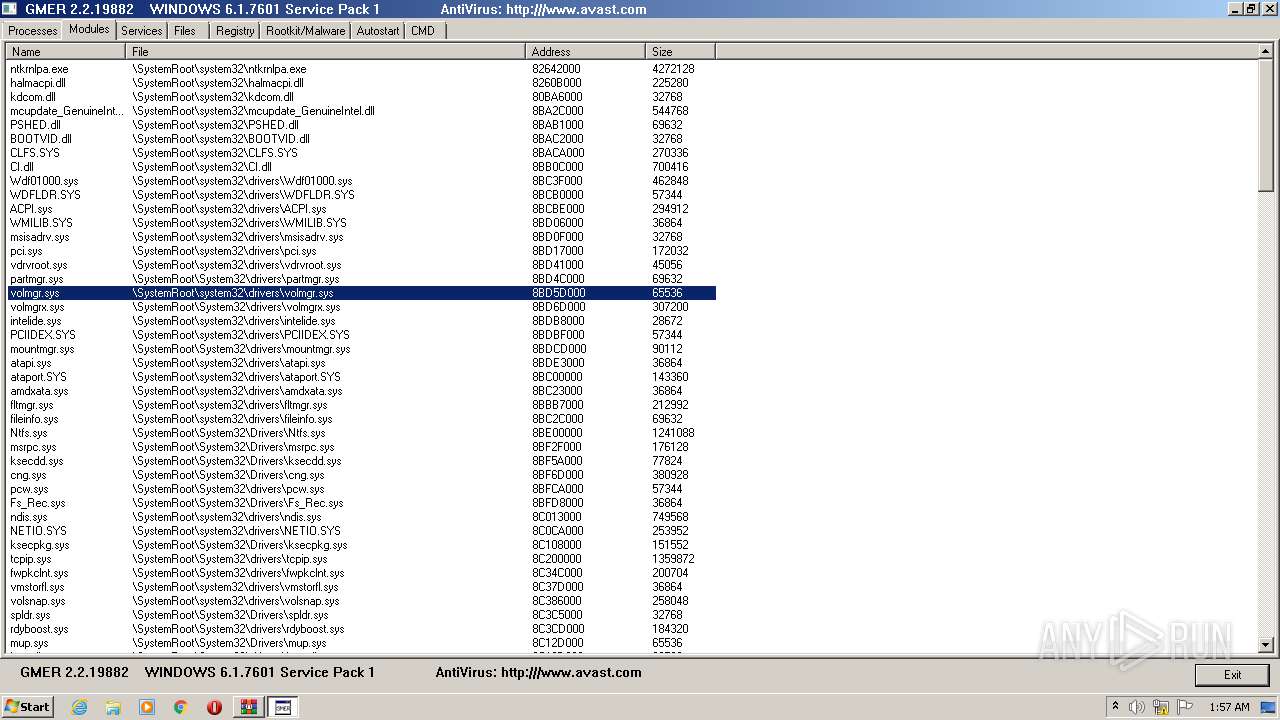
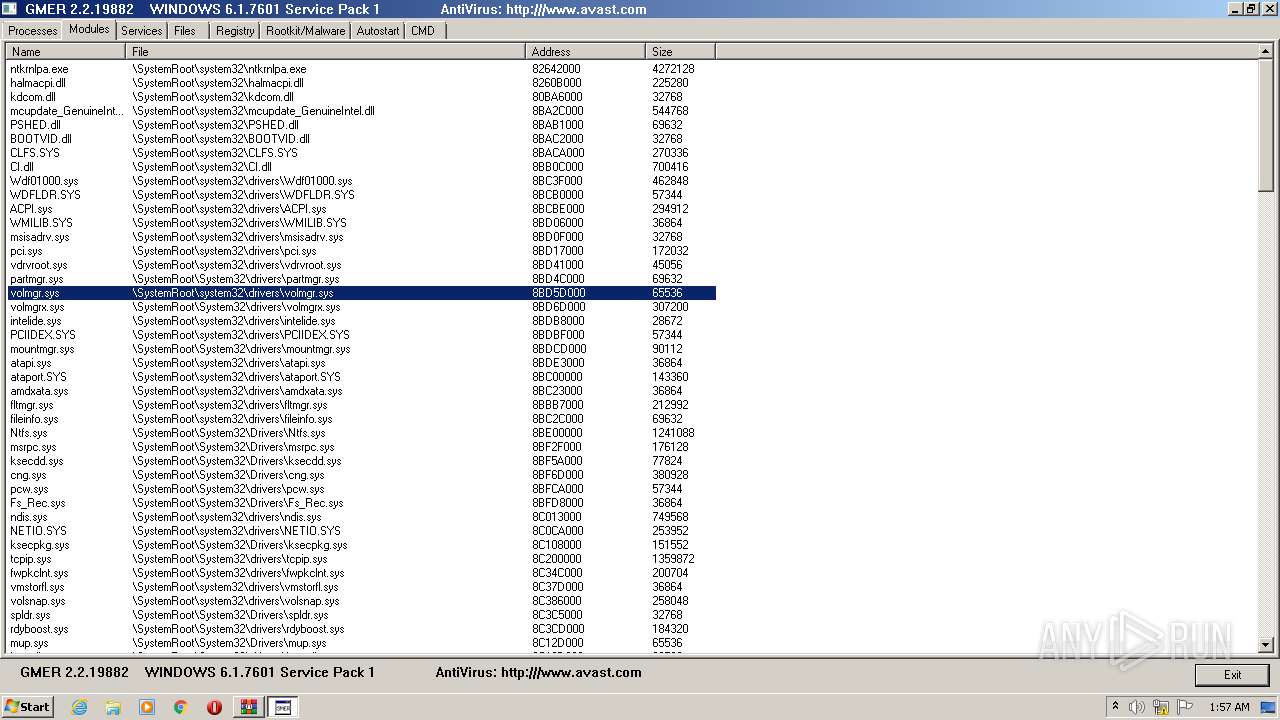
User: admin Integrity Level: HIGH Exit code: 0 Version: 2, 2, 19882 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\gmer.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2300.30944\gmer.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2300.30944\gmer.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2, 2, 19882 Modules
| |||||||||||||||
Total events
541
Read events
513
Write events
28
Delete events
0
Modification events
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\gmer.zip | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
6
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2276 | gmer.exe | C:\Users\admin\AppData\Local\Temp\Cab5D88.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\Local\Temp\Tar5D89.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmp5E07.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmp5E28.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmp5EA7.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmp5EF6.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmp5F26.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F90F18257CBB4D84216AC1E1F3BB2C76 | der | |
MD5:— | SHA256:— | |||
| 2276 | gmer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B8CC409ACDBF2A2FE04C56F2875B1FD6 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2276 | gmer.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
2276 | gmer.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | der | 530 b | whitelisted |
2276 | gmer.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2276 | gmer.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |