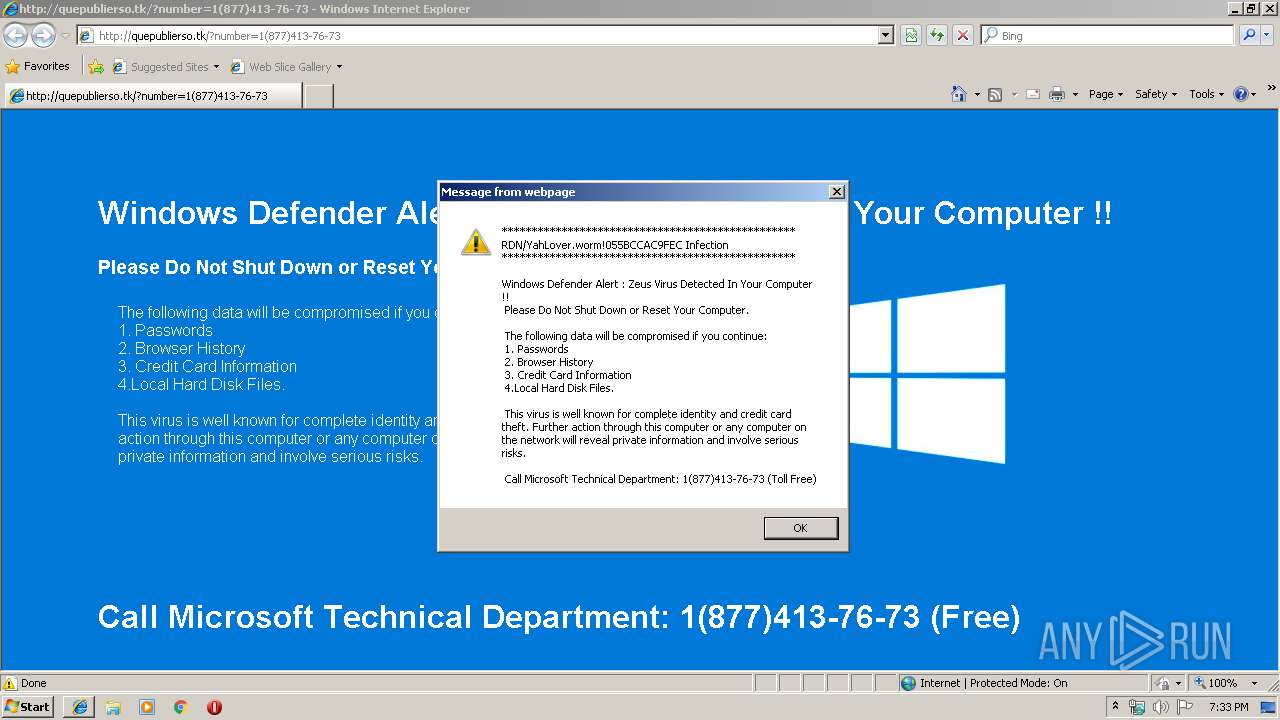
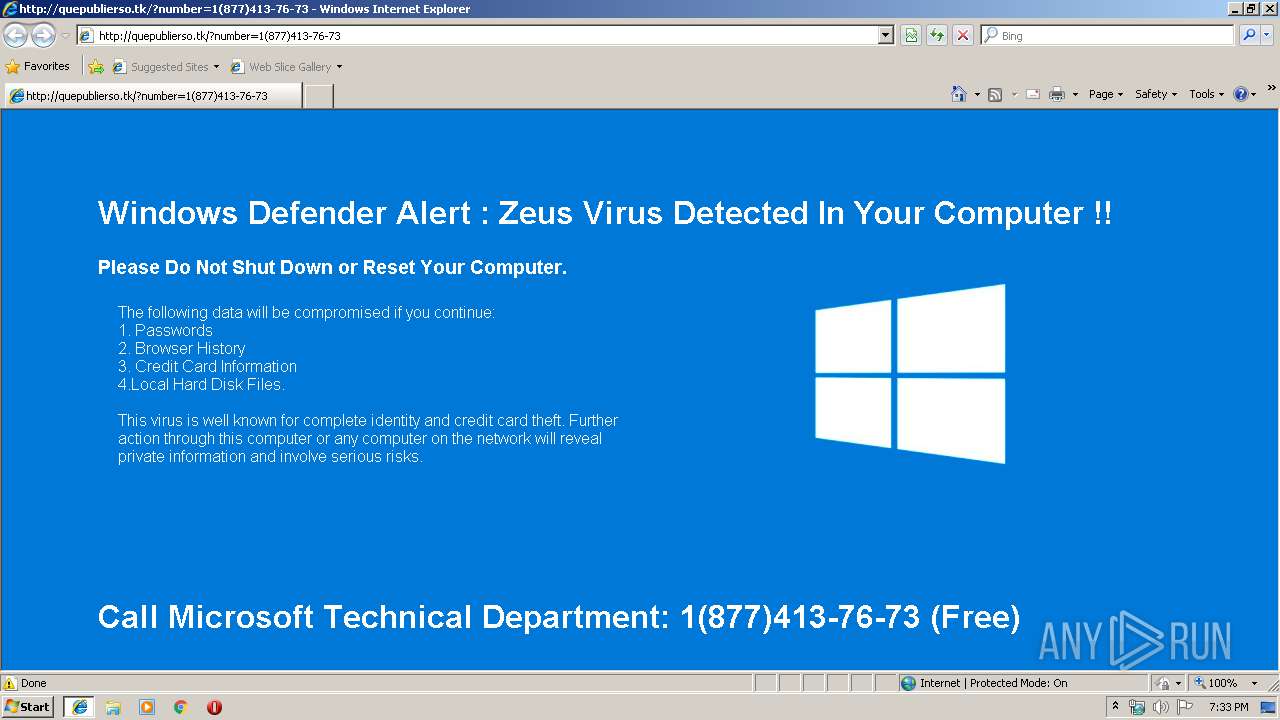
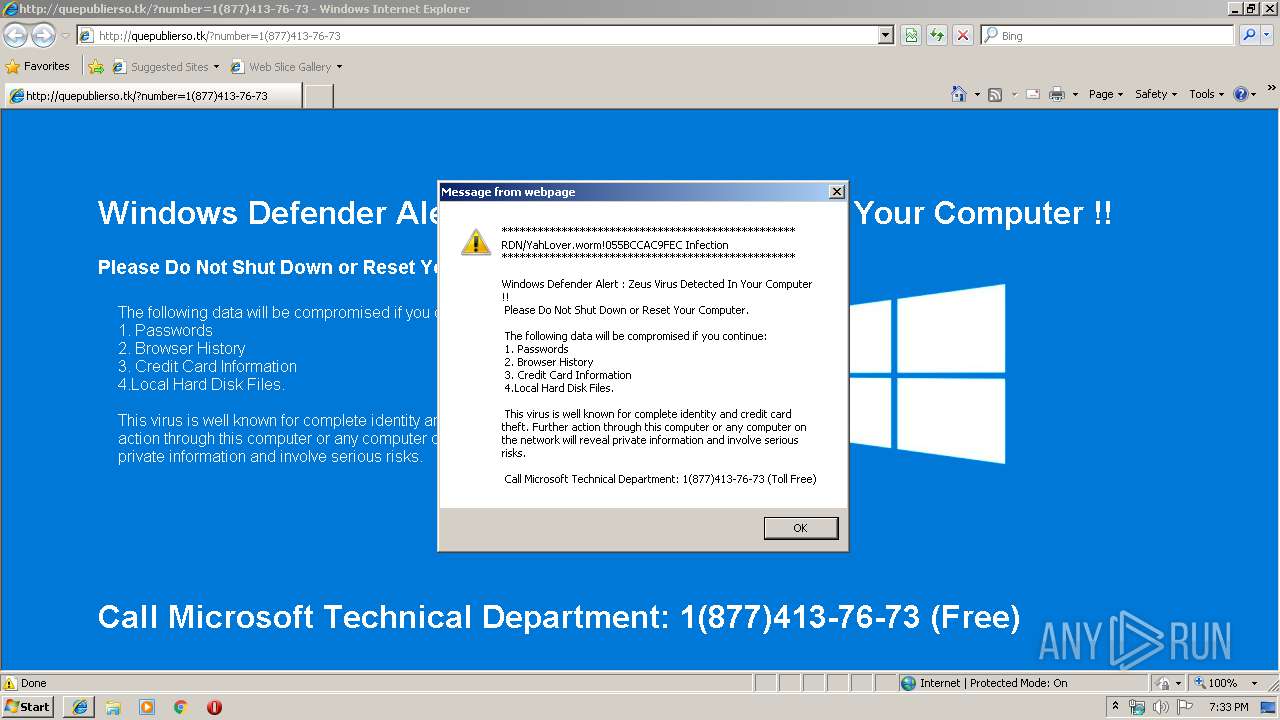
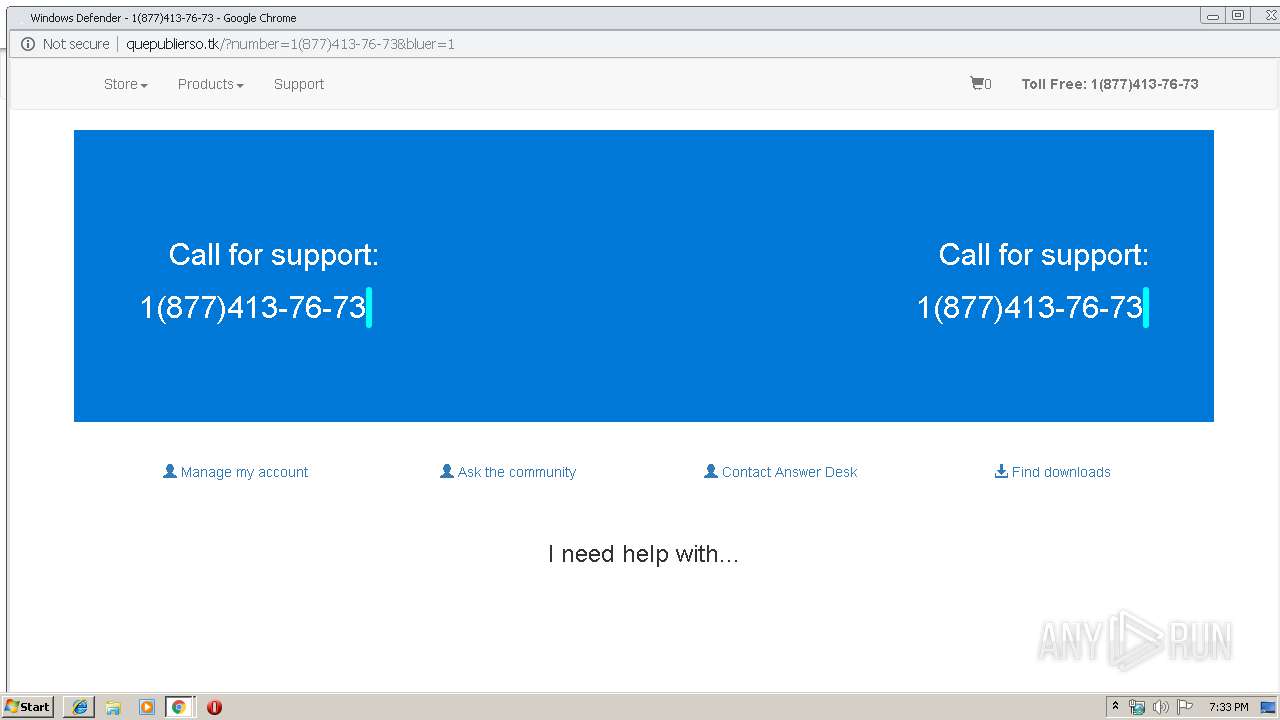
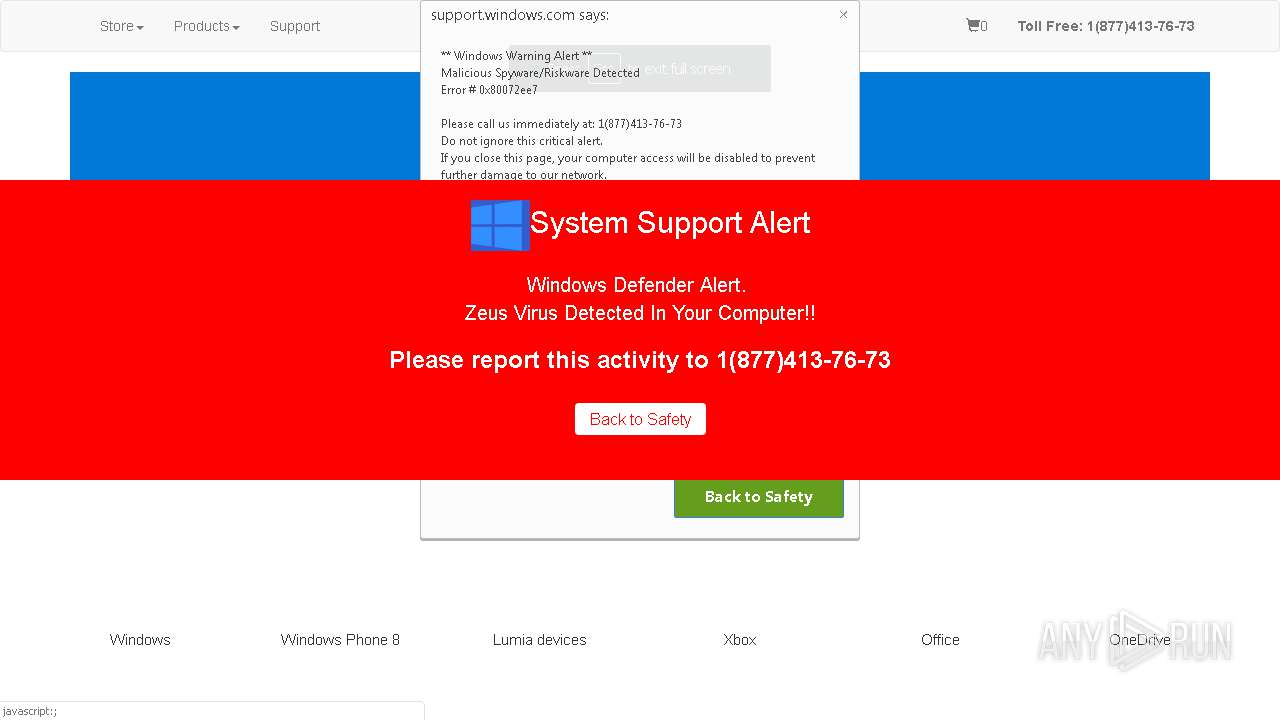
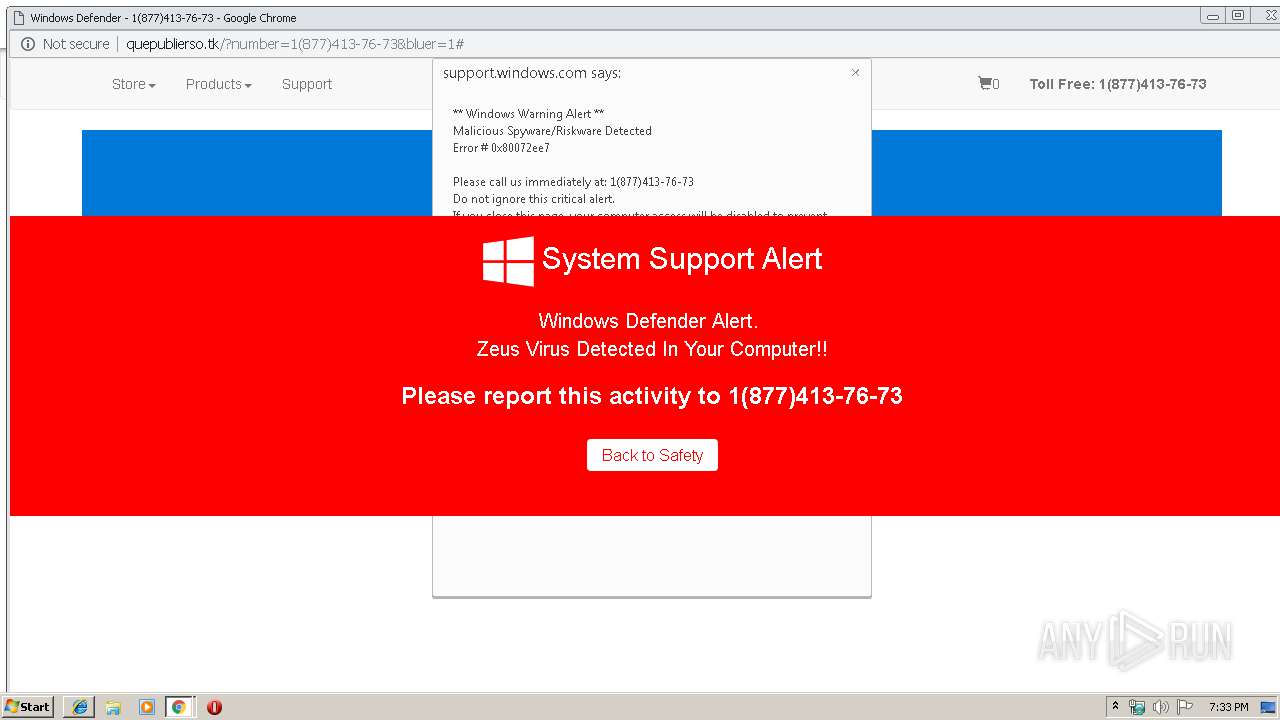
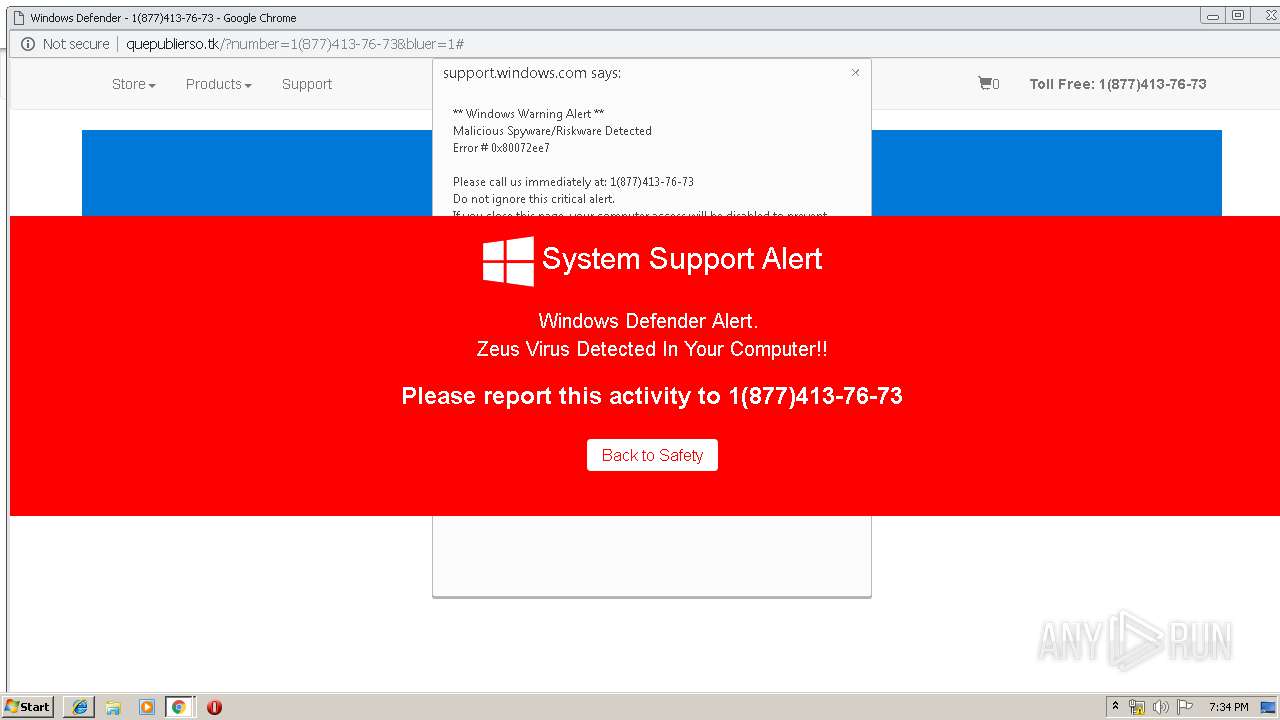
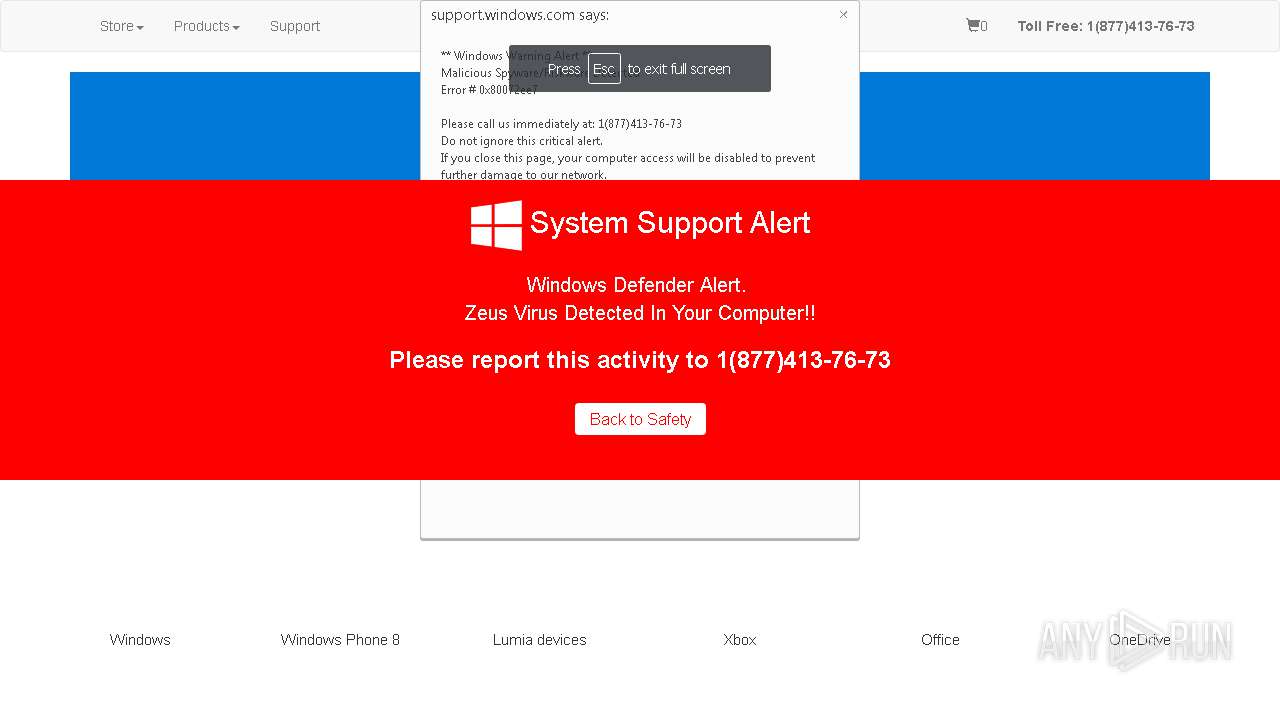
| URL: | http://quepublierso.tk/?number=1(877)413-76-73 |
| Full analysis: | https://app.any.run/tasks/69cc48a0-a7ca-4250-a55c-66c5238108d1 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 18:32:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3A341AA90688A2F9DDE47F4798AD4D62 |
| SHA1: | 941999AD1D705486589A44FA17F46F44D045E7EC |
| SHA256: | DE28697A16AB90E4541A71FB34A2D0683D981AF07CFDBDE49BDE89D85B44237E |
| SSDEEP: | 3:N1KPoJoy6CQwSEl:CUNNl |
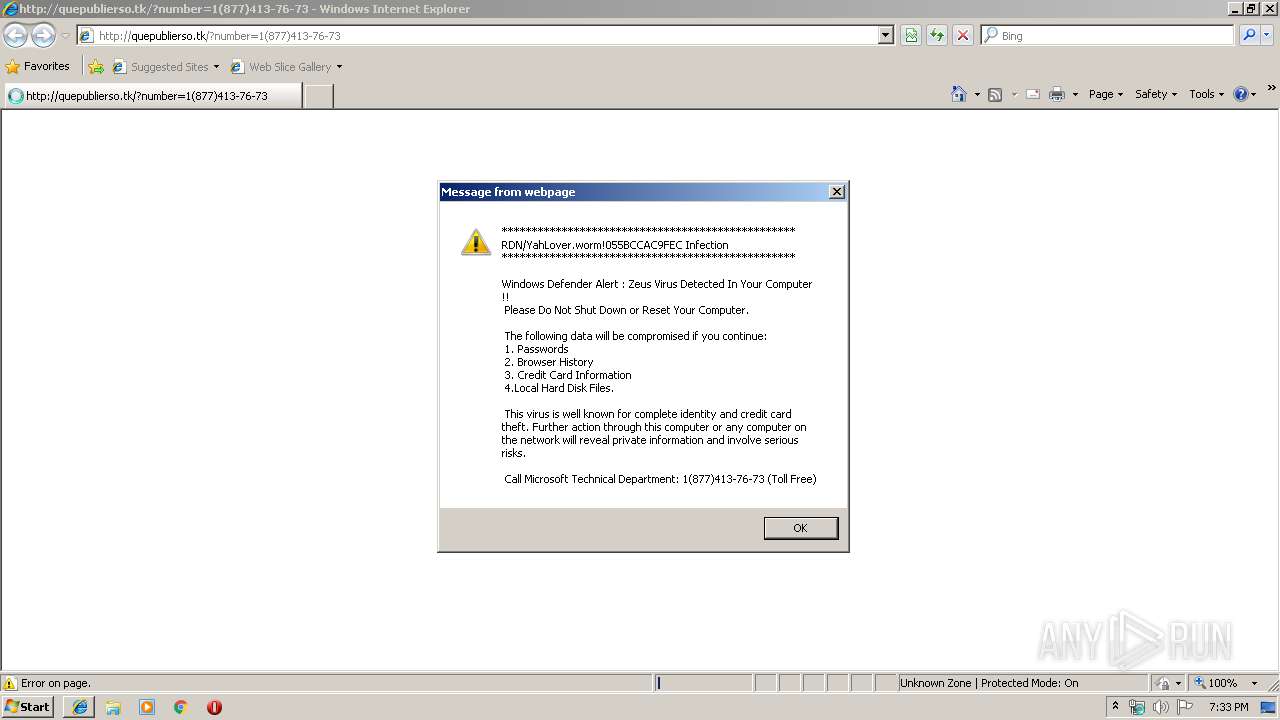
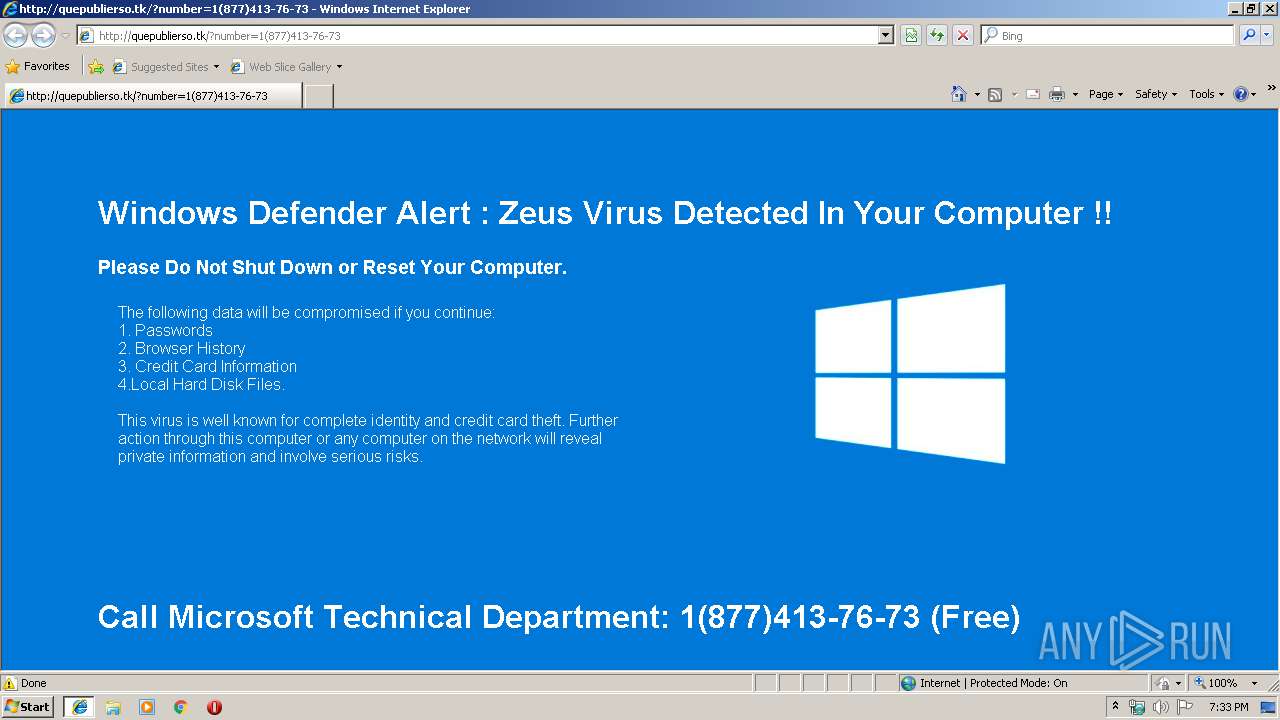
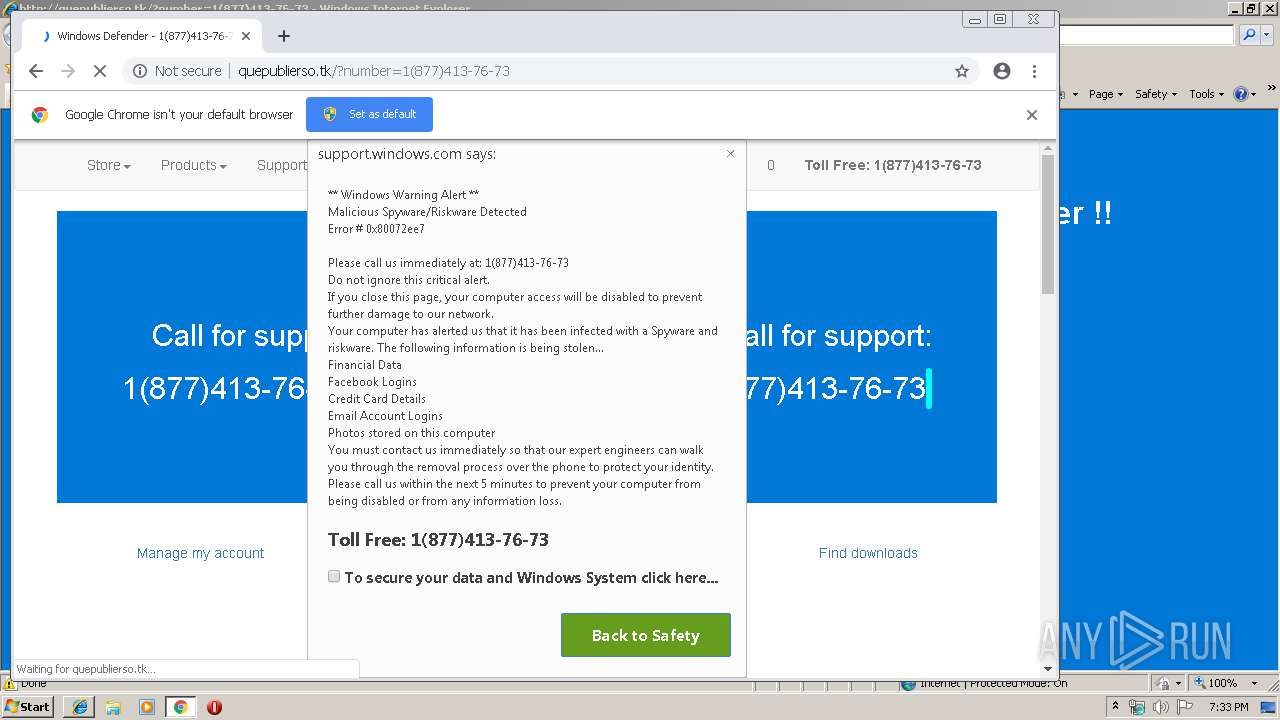
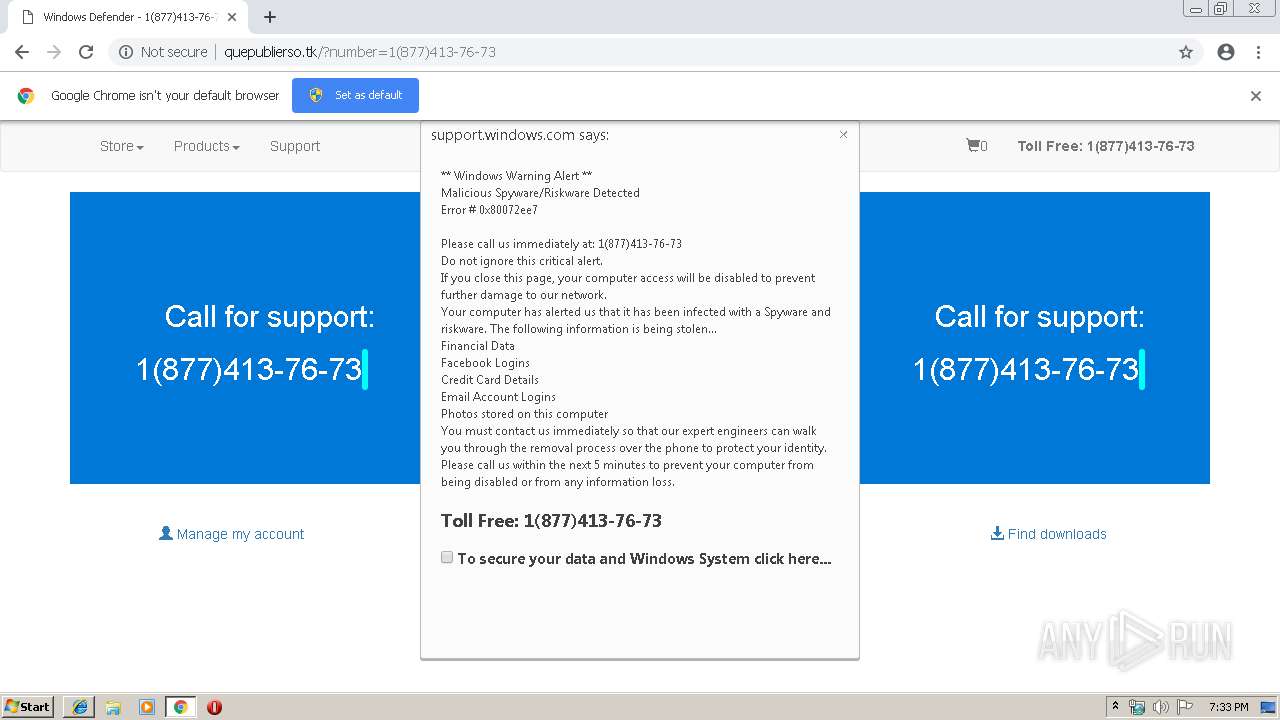
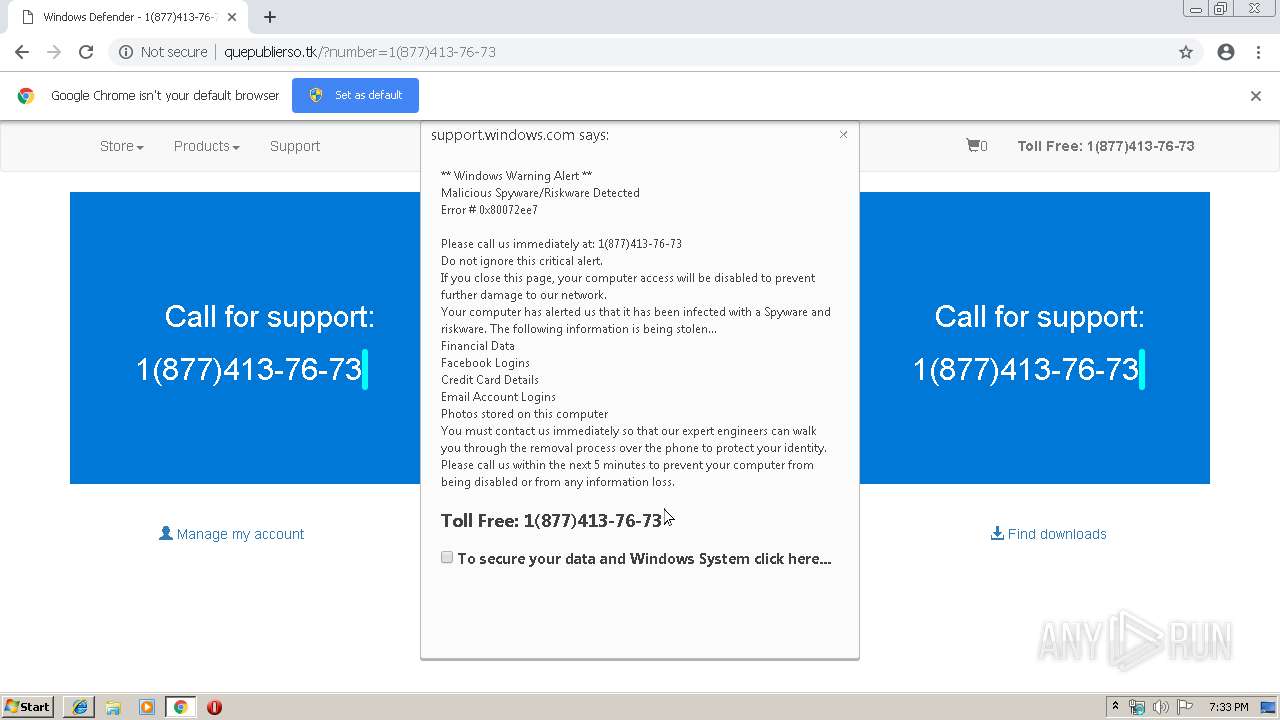
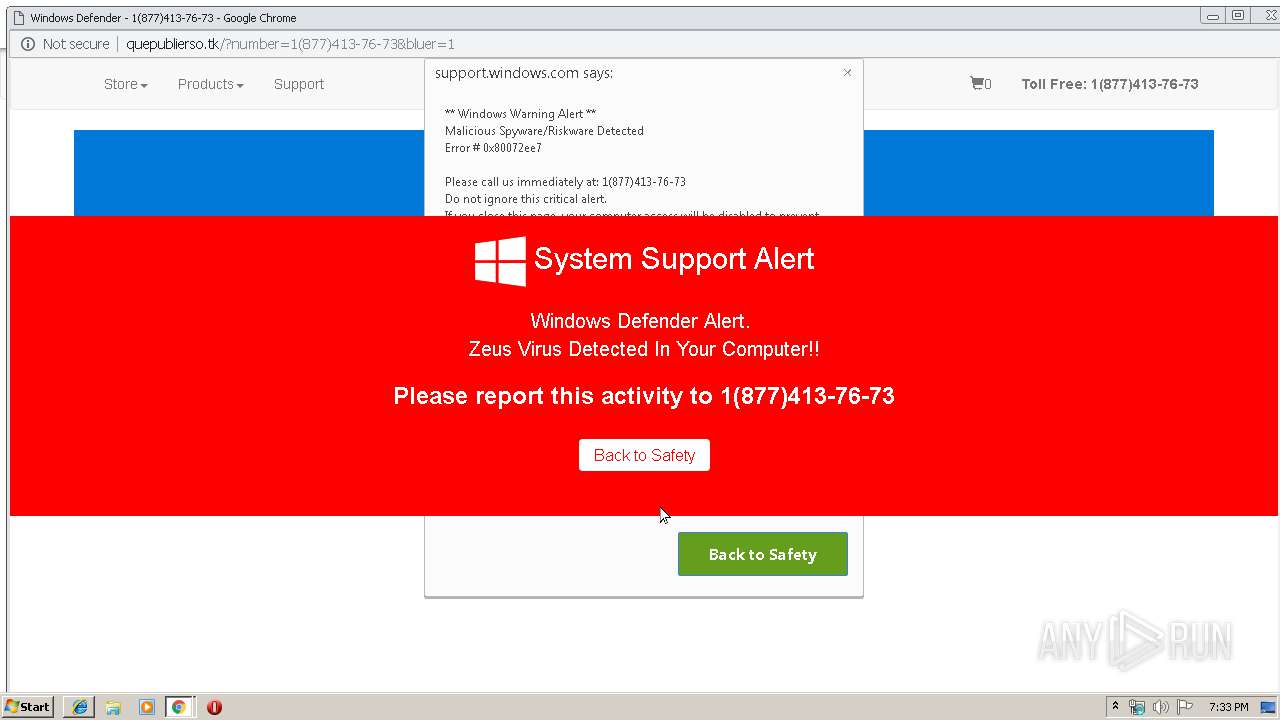
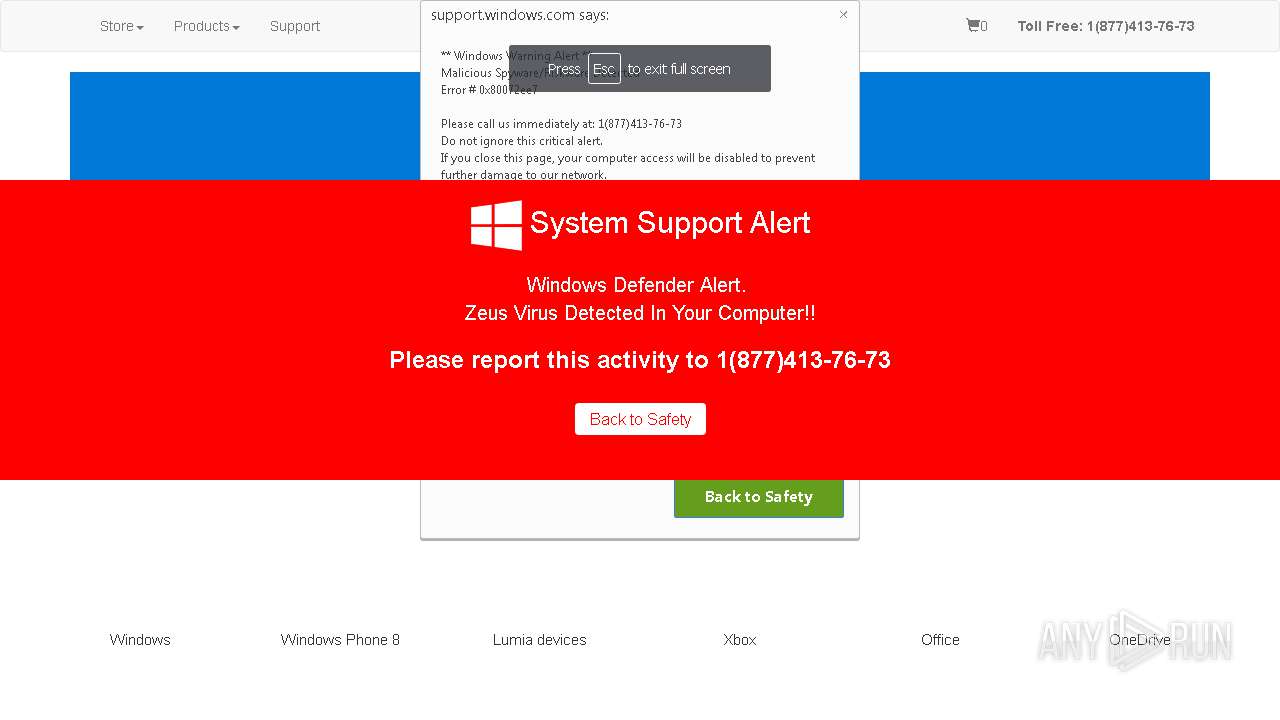
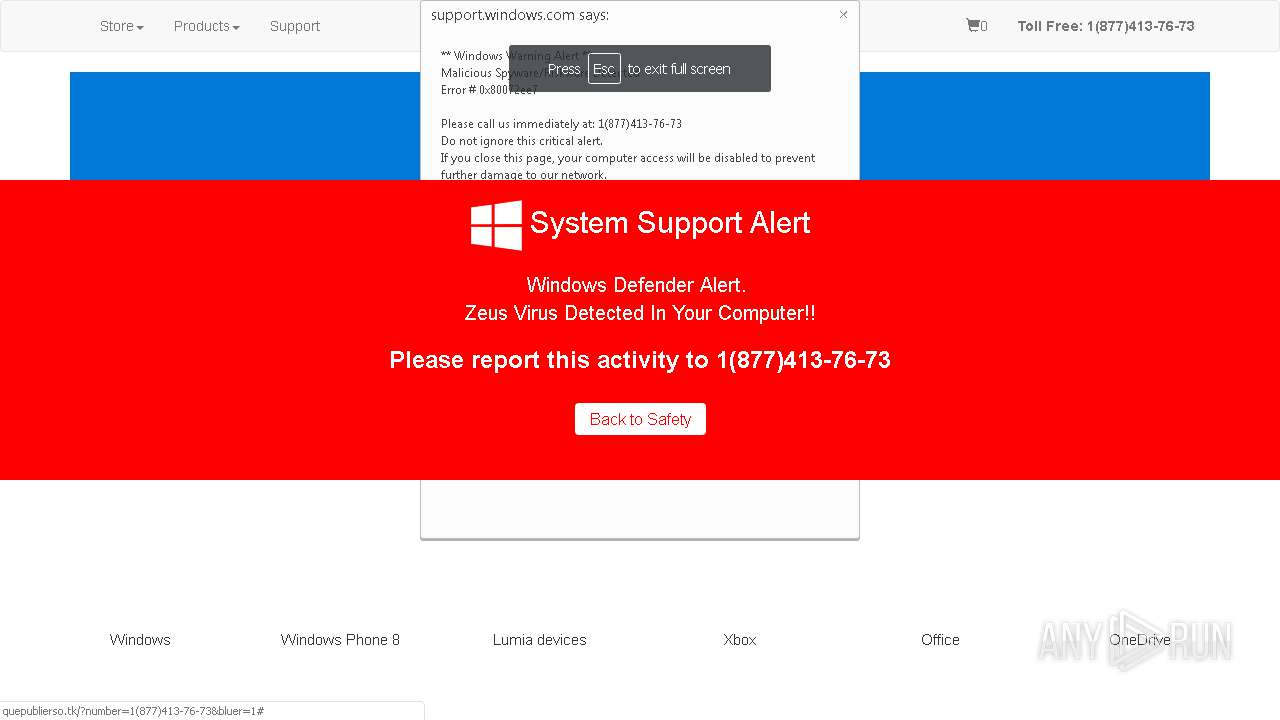
MALICIOUS
TECHSUPPORT was detected
- iexplore.exe (PID: 3384)
- chrome.exe (PID: 3352)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3352)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2836)
- iexplore.exe (PID: 3384)
Changes internet zones settings
- iexplore.exe (PID: 2836)
Application launched itself
- iexplore.exe (PID: 2836)
- chrome.exe (PID: 3352)
Reads internet explorer settings
- iexplore.exe (PID: 3384)
Reads Internet Cache Settings
- iexplore.exe (PID: 3384)
- iexplore.exe (PID: 2836)
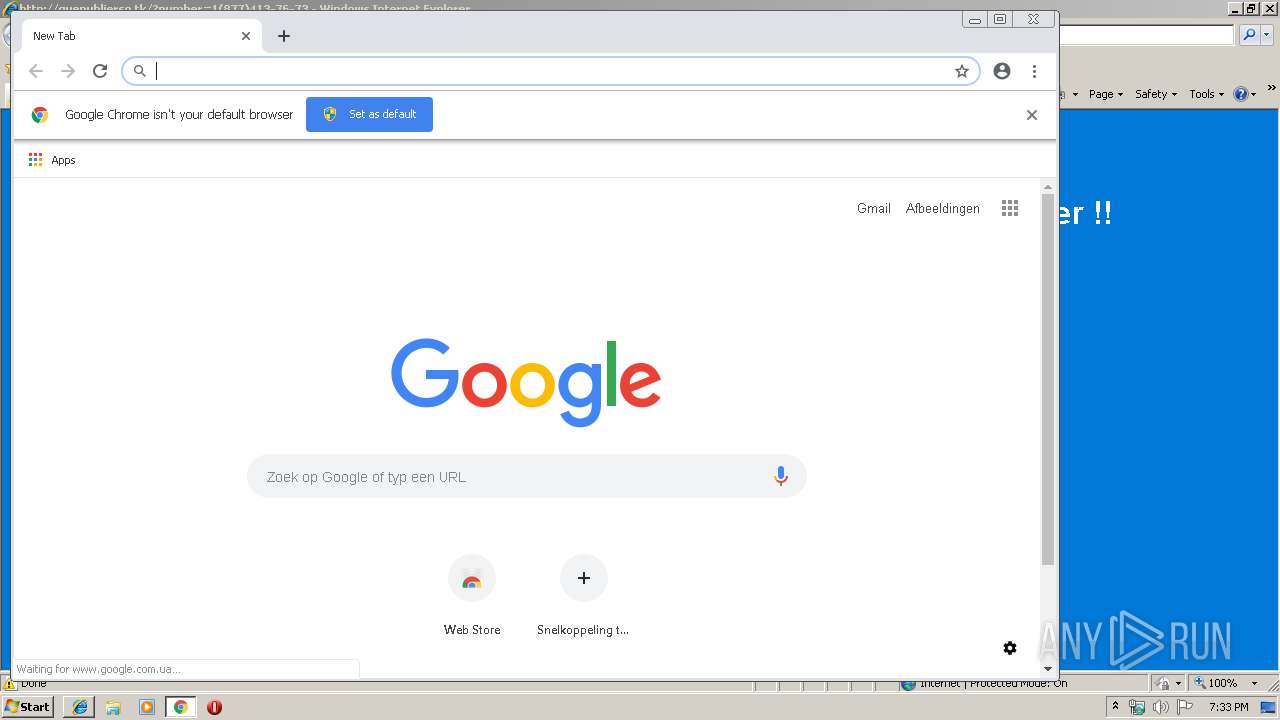
Manual execution by user
- chrome.exe (PID: 3352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
22
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6874154949985487223,4336153548195311001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1049572508763119462 --mojo-platform-channel-handle=4860 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6874154949985487223,4336153548195311001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7122321088250829442 --mojo-platform-channel-handle=4720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c470f18,0x6c470f28,0x6c470f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,6874154949985487223,4336153548195311001,131072 --enable-features=PasswordImport --service-pipe-token=2331362038261615534 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2331362038261615534 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6874154949985487223,4336153548195311001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6433390325537884808 --mojo-platform-channel-handle=4772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,6874154949985487223,4336153548195311001,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8055281183947743814 --mojo-platform-channel-handle=932 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Internet Explorer\iexplore.exe" http://quepublierso.tk/?number=1(877)413-76-73 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,6874154949985487223,4336153548195311001,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=834675601742976767 --mojo-platform-channel-handle=5008 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2836 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
658
Read events
536
Write events
116
Delete events
6
Modification events
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {5F3F4BB7-7E52-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050005001800120021000700E801 | |||
Executable files
0
Suspicious files
43
Text files
133
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\81QJN9XF\quepublierso_tk[1].txt | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
25
DNS requests
17
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/img/img-4.svg | UA | — | — | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/img/img-5.svg | UA | — | — | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/img/img-6.svg | UA | — | — | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/img/img-10.svg | UA | — | — | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/img/img-11.svg | UA | — | — | suspicious |
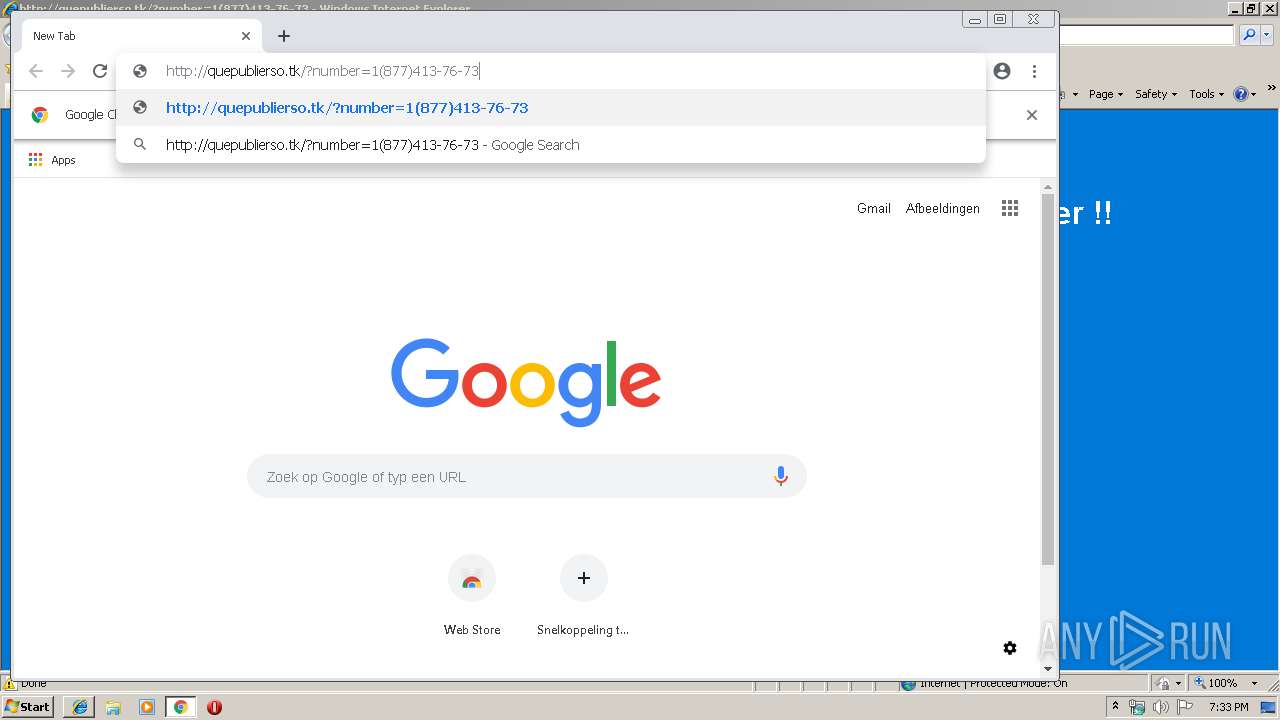
3384 | iexplore.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/?number=1(877)413-76-73 | UA | html | 3.75 Kb | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/?number=1(877)413-76-73 | UA | html | 23.9 Kb | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/img/img-2.svg | UA | text | 26.3 Kb | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/style/bootstrap.css | UA | text | 118 Kb | suspicious |
3352 | chrome.exe | GET | 200 | 185.86.77.9:80 | http://quepublierso.tk/include/chrome/style/main.css | UA | text | 26.3 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3352 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3384 | iexplore.exe | 185.86.77.9:80 | quepublierso.tk | Mulgin Alexander Sergeevich | UA | suspicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3384 | iexplore.exe | 216.58.207.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2836 | iexplore.exe | 185.86.77.9:80 | quepublierso.tk | Mulgin Alexander Sergeevich | UA | suspicious |
3352 | chrome.exe | 172.217.23.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3352 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3352 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
3352 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
quepublierso.tk |
| suspicious |
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3384 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3384 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS Fake AV Phone Scam Landing Feb 12 |
3384 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2836 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3352 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3352 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3352 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3352 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Tech Support Phone Scam Landing 2017-07-26 |
3352 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3352 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3 ETPRO signatures available at the full report