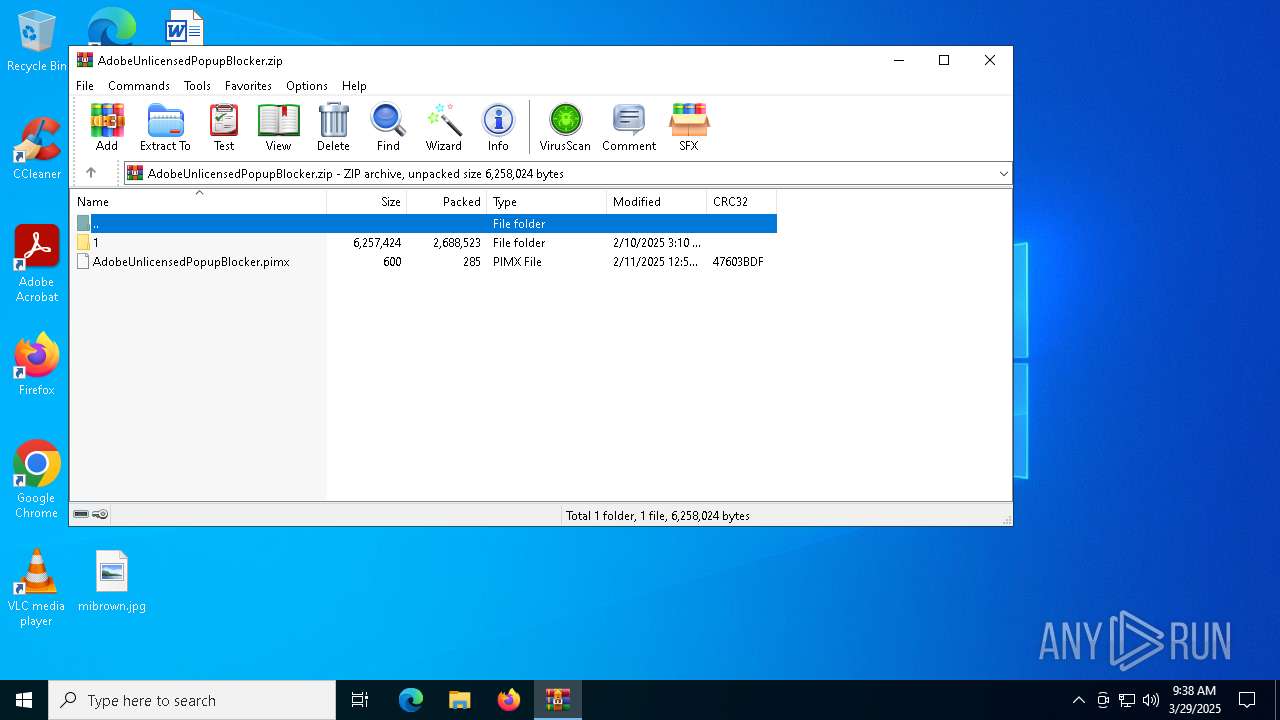
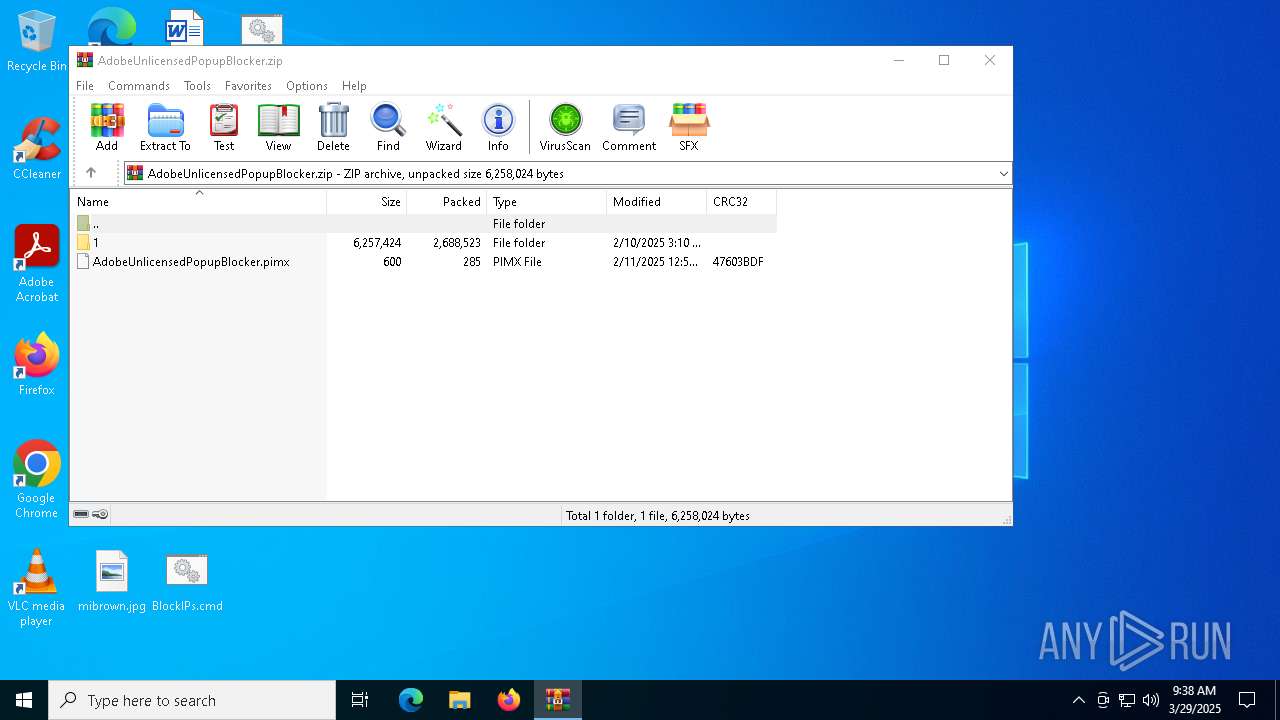
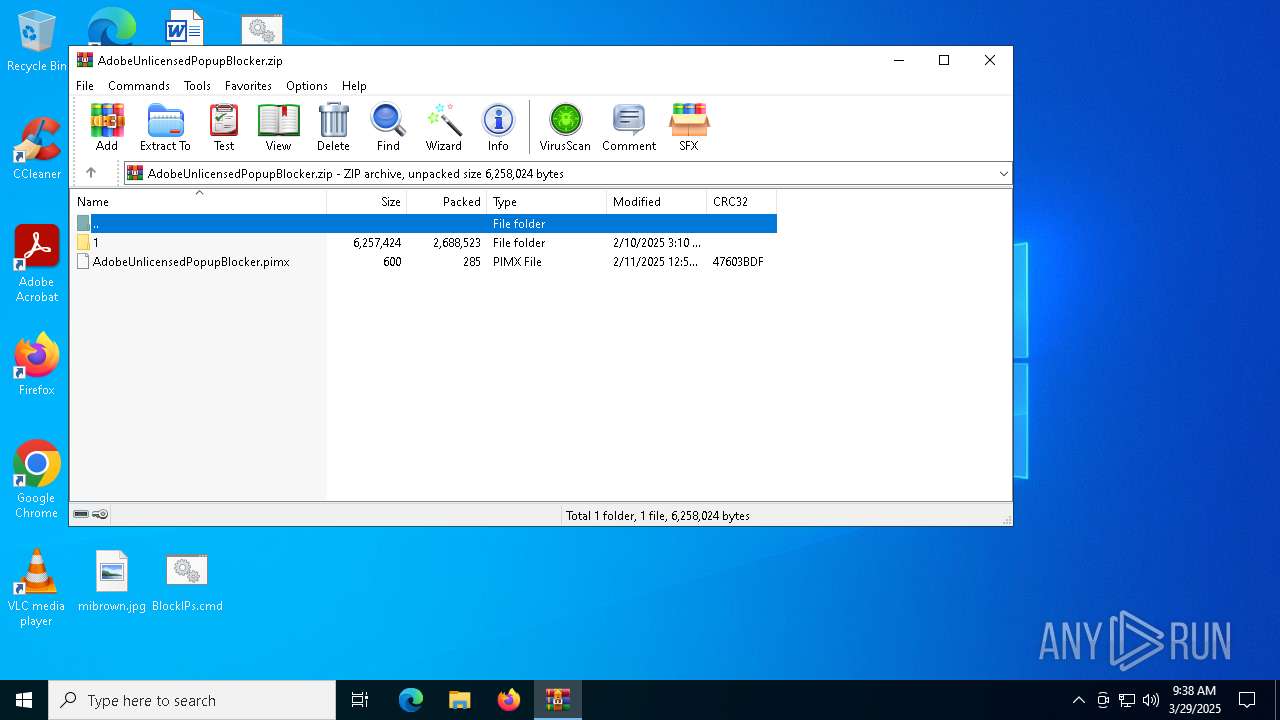
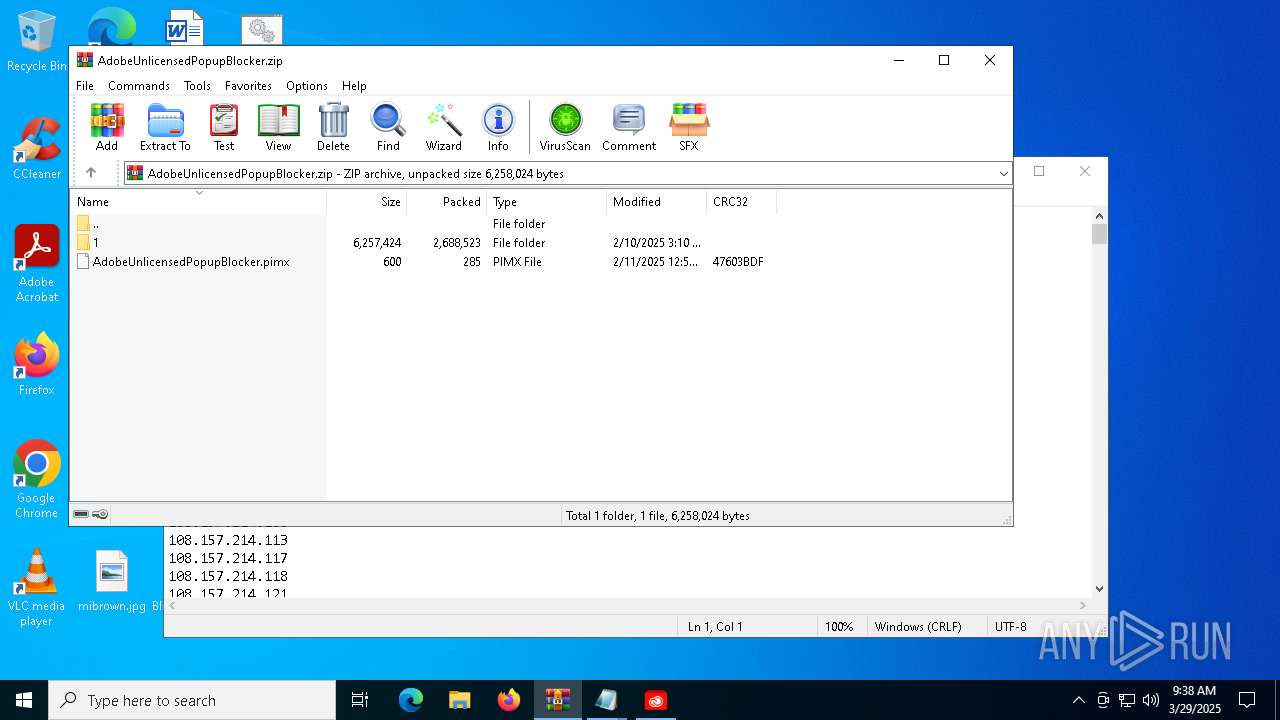
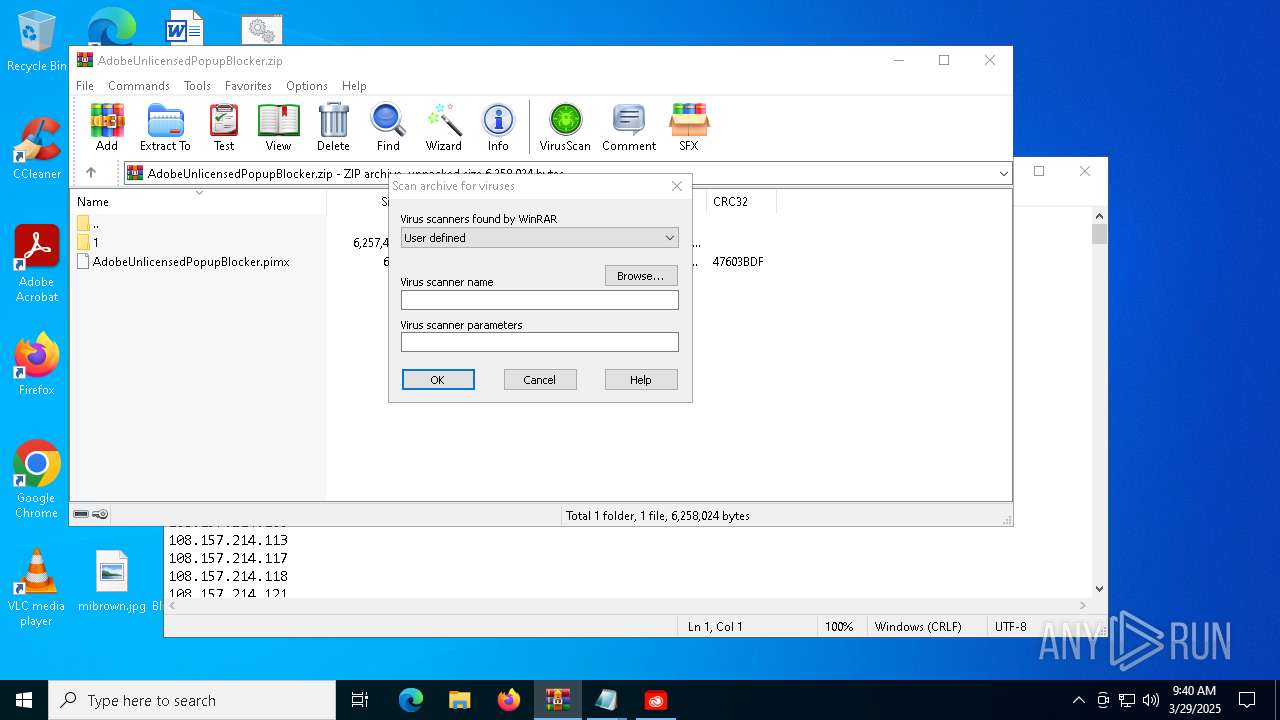
| File name: | AdobeUnlicensedPopupBlocker.zip |
| Full analysis: | https://app.any.run/tasks/5aa907f6-bdb1-4d6f-80ed-11c0f6f71660 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2025, 09:37:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | C2C3A0E857AC236306711D51CC8CE2B4 |
| SHA1: | EF43EBE18AF3FB49CB0296ECEE89A2098A0C5C1A |
| SHA256: | DE1814E4C419A647155F1746F69B7E5CEBED8224B38FD3BD1207E057BCDBB369 |
| SSDEEP: | 98304:PH9m9/A21oIum56cbwlpzazqzWWc+m89g/DfvnaKaY9W9IyXznyD5ZUUwa4Iq5GW:2gURbY8O |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7152)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5056)
SUSPICIOUS
Runs PING.EXE to delay simulation
- cmd.exe (PID: 1628)
- cmd.exe (PID: 5352)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1628)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 6800)
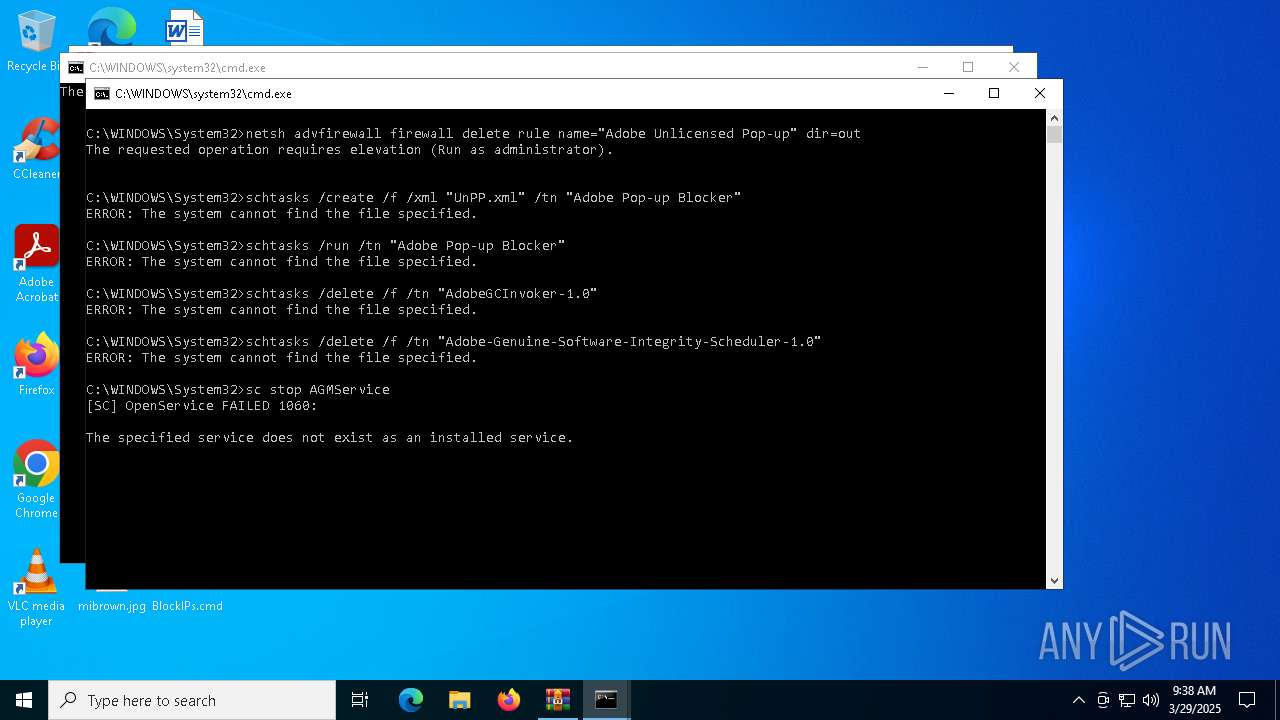
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 1628)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 5352)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5344)
- schtasks.exe (PID: 7020)
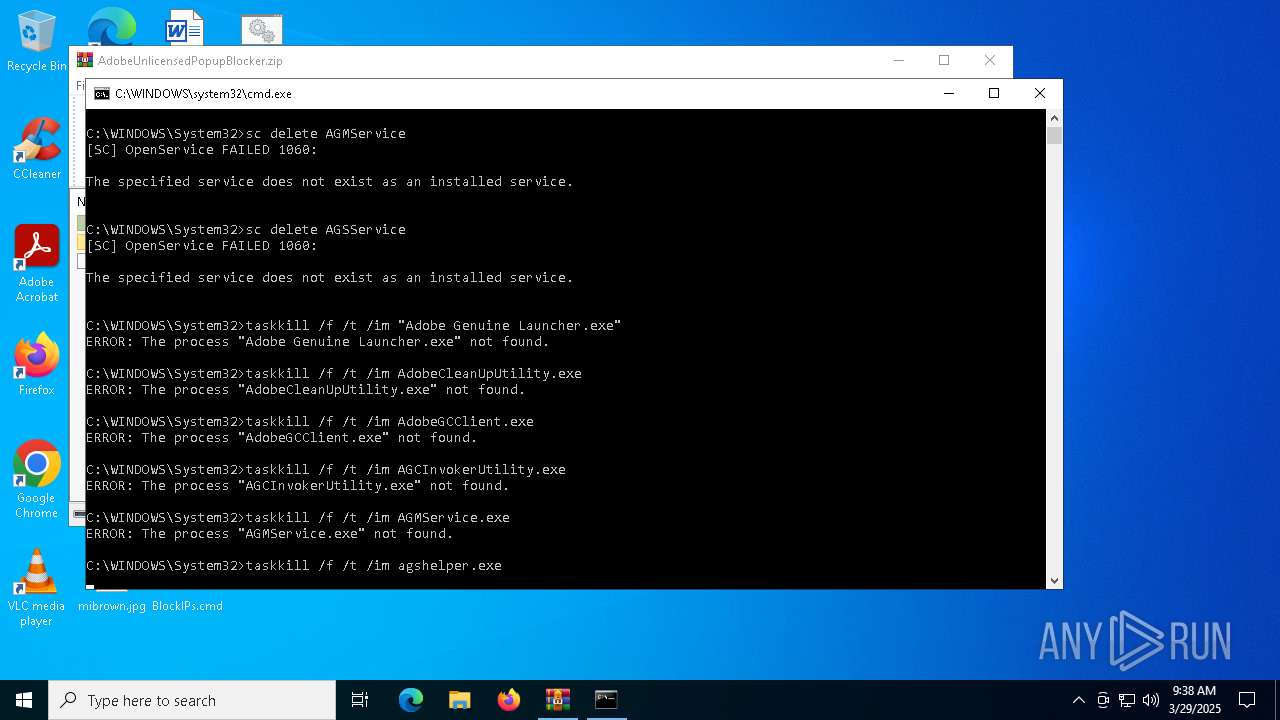
Stops a currently running service
- sc.exe (PID: 4120)
- sc.exe (PID: 6132)
Starts SC.EXE for service management
- cmd.exe (PID: 5056)
Application launched itself
- cmd.exe (PID: 1628)
- Start.exe (PID: 1276)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 7020)
Hides command output
- cmd.exe (PID: 1532)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6800)
Windows service management via SC.EXE
- sc.exe (PID: 2656)
- sc.exe (PID: 4608)
Uses NSLOOKUP.EXE to check DNS info
- cmd.exe (PID: 1532)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6800)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1628)
- Start.exe (PID: 4208)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 7020)
Reads security settings of Internet Explorer
- Start.exe (PID: 4208)
Executing commands from ".cmd" file
- Start.exe (PID: 4208)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5056)
There is functionality for taking screenshot (YARA)
- Start.exe (PID: 1276)
INFO
Manual execution by a user
- cmd.exe (PID: 5056)
- cmd.exe (PID: 1628)
- Start.exe (PID: 1276)
- notepad.exe (PID: 1324)
- wget.exe (PID: 7000)
- notepad.exe (PID: 2108)
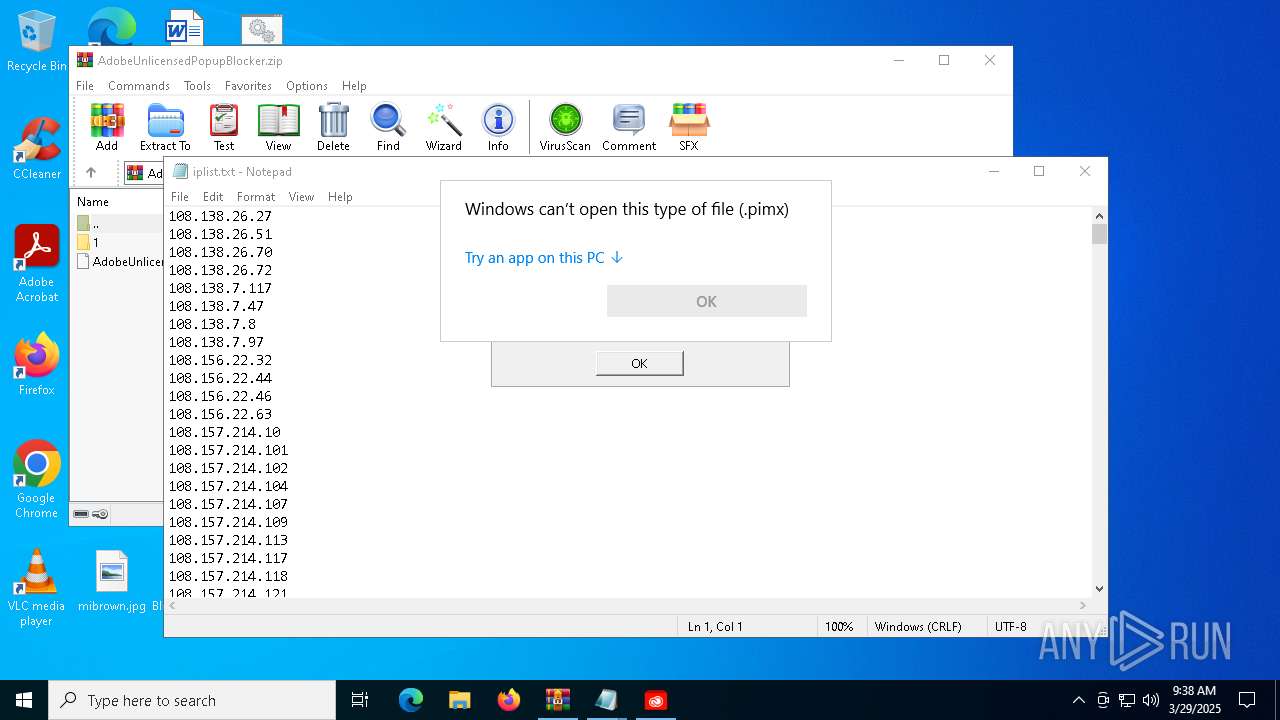
- OpenWith.exe (PID: 5936)
Checks supported languages
- Start.exe (PID: 1276)
- Start.exe (PID: 4208)
- wget.exe (PID: 7000)
- wget.exe (PID: 6268)
Reads the computer name
- Start.exe (PID: 1276)
- Start.exe (PID: 4208)
- wget.exe (PID: 6268)
Process checks computer location settings
- Start.exe (PID: 4208)
Create files in a temporary directory
- Start.exe (PID: 1276)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1324)
- notepad.exe (PID: 2108)
Checks proxy server information
- slui.exe (PID: 2096)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5936)
Reads the software policy settings
- slui.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:10 15:10:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | 1/ |
Total processes
185
Monitored processes
62
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
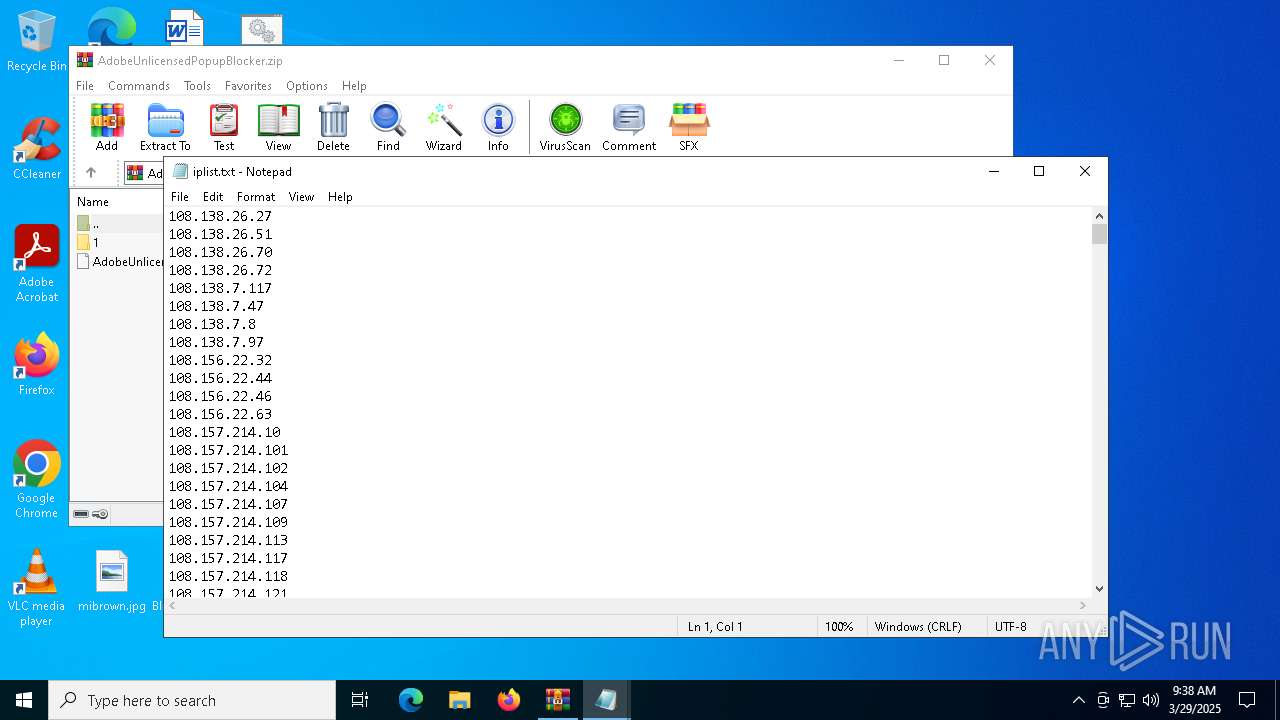
| 896 | nslookup -type=ns ic.adobe.io | C:\Windows\SysWOW64\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | netsh advfirewall firewall delete rule name="Adobe Unlicensed Pop-up" dir=out | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | netsh advfirewall firewall delete rule name="Adobe Unlicensed Pop-up Blocker" dir=out | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\Users\admin\Desktop\Start.exe" | C:\Users\admin\Desktop\Start.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Adobe Unlicensed Pop-up Block Starter Version: 1.0.0.0000 Modules
| |||||||||||||||
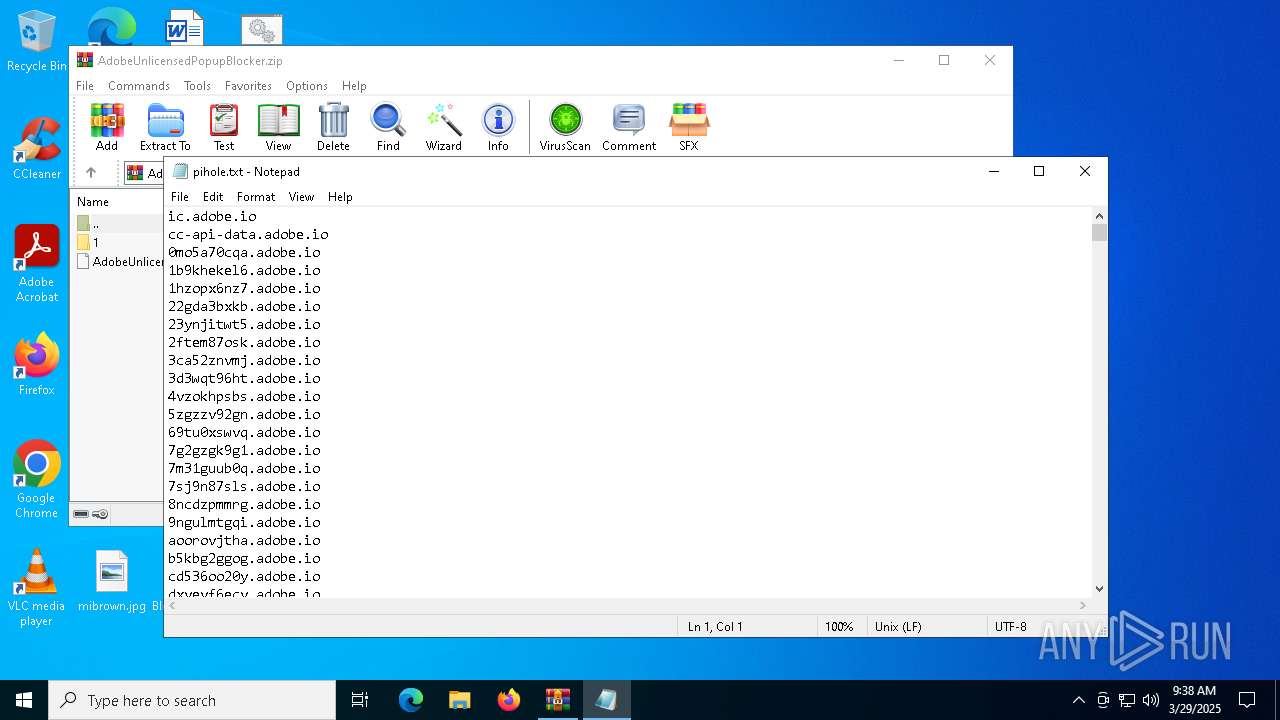
| 1324 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\pihole.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | C:\WINDOWS\system32\cmd.exe /c 2>nul nslookup -type=ns ic.adobe.io|findstr /i /l /c:"nameserver = " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wget.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\BlockIPs.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | nslookup -type=ns ic.adobe.io | C:\Windows\System32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 075
Read events
11 066
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\AdobeUnlicensedPopupBlocker.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6040 | findstr.exe | C:\Users\admin\Desktop\pihole_new.txt | text | |
MD5:4940F66A06224D7532C364824ABAAFF4 | SHA256:5B0CC6A16937571C205A0704DD5AA0B13F4CA29A7E286F51EC551E80257E2EAF | |||
| 5352 | cmd.exe | C:\Users\admin\Desktop\pihole.txt | text | |
MD5:4940F66A06224D7532C364824ABAAFF4 | SHA256:5B0CC6A16937571C205A0704DD5AA0B13F4CA29A7E286F51EC551E80257E2EAF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7000 | RUXIMICS.exe | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 200 | 104.21.80.1:443 | https://a.dove.isdumb.one/pihole.txt | unknown | text | 36.9 Kb | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7000 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7000 | RUXIMICS.exe | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6268 | wget.exe | 104.21.80.1:443 | a.dove.isdumb.one | CLOUDFLARENET | — | unknown |
2320 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2096 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
2.100.168.192.in-addr.arpa |
| whitelisted |
ic.adobe.io |
| whitelisted |
a.dove.isdumb.one |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |