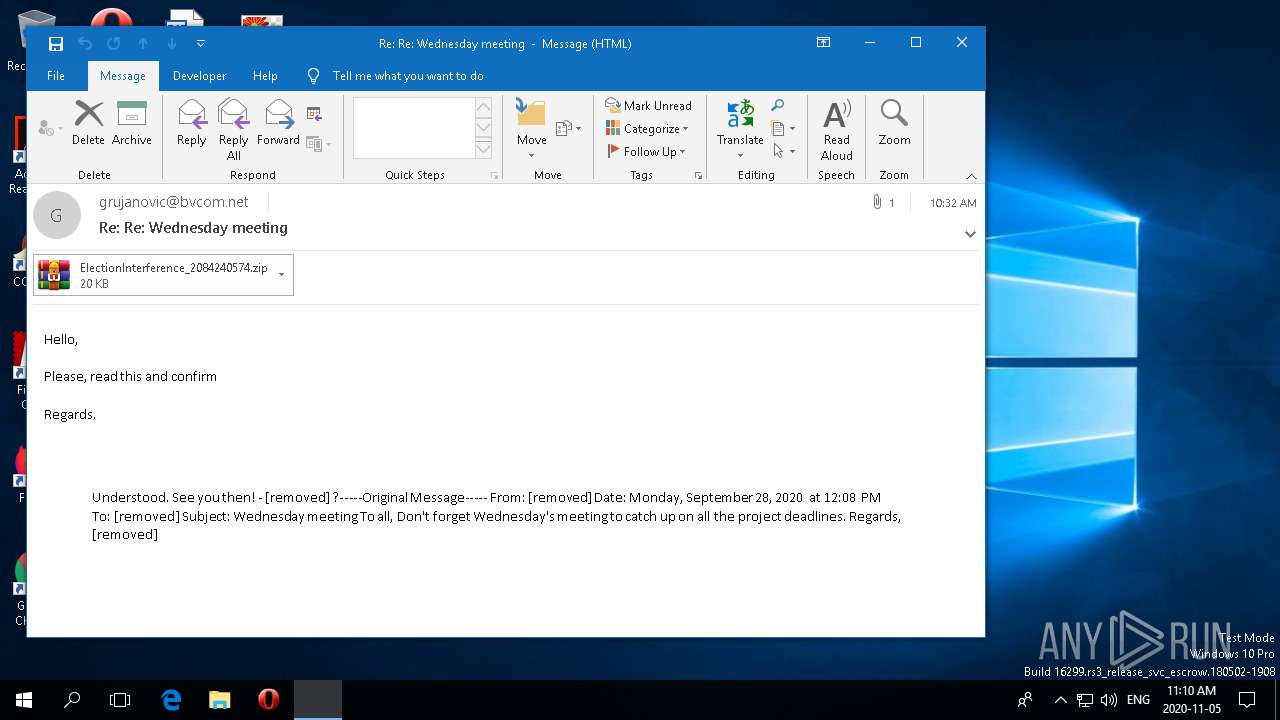
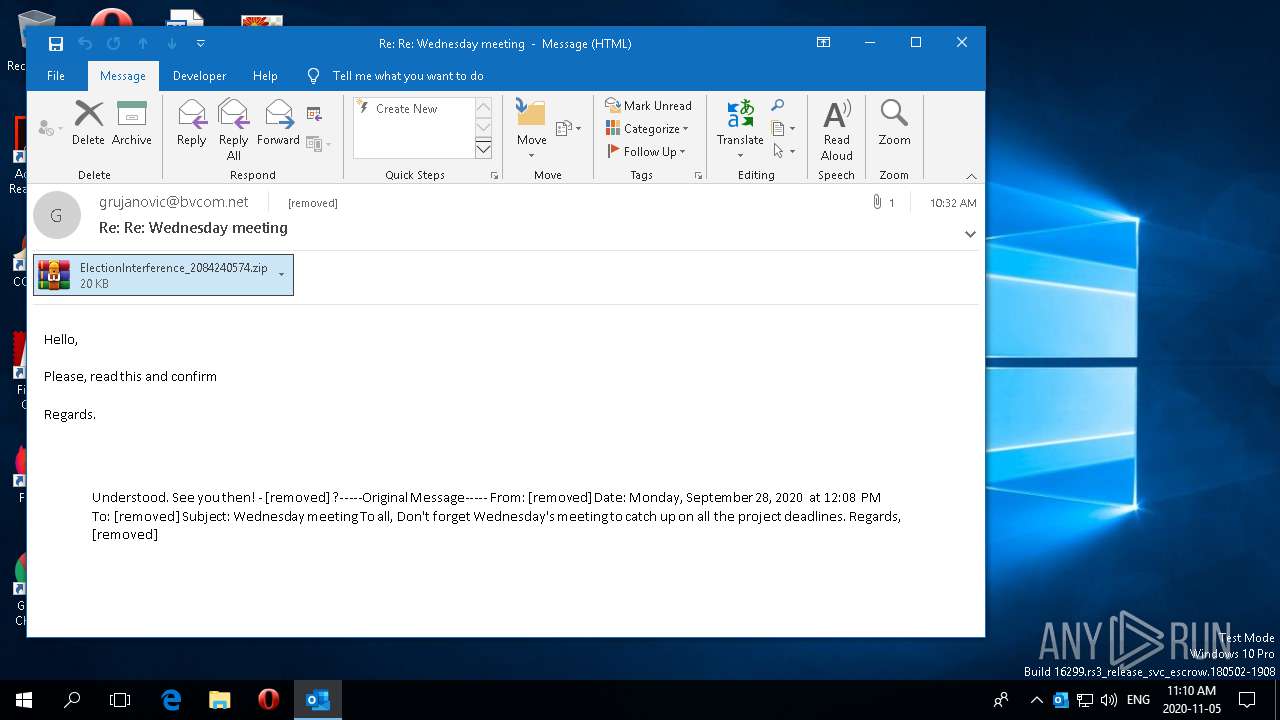
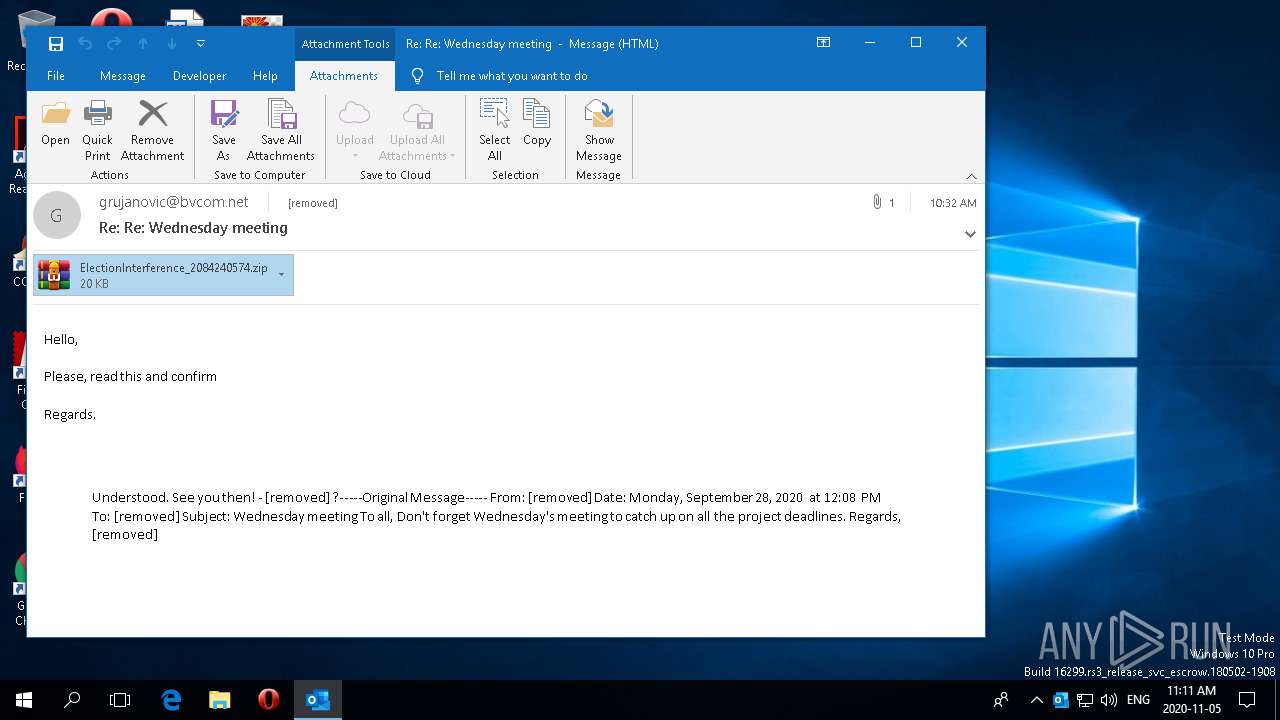
| File name: | 2020-11-05-Qakbot-malspam.eml |
| Full analysis: | https://app.any.run/tasks/03119661-5abb-4ca9-926f-e0b10d8af19e |
| Verdict: | Malicious activity |
| Analysis date: | November 05, 2020, 16:09:55 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | AD2D2B99B91009359763CBCF2B24C527 |
| SHA1: | D6D0B1660ED42D142201B1426A3EEBC595E5A7B5 |
| SHA256: | DE1117731FCB2E3B322F3C2950386A109A65E99621674513B2D1450F625B44CC |
| SSDEEP: | 768:ggMBxsiySaTliWg6gkhusqrJ0yQeQZ6PE0nfGdhT:PM7sBxTcWg6xgAe/PXnfGdF |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- rundll32.exe (PID: 4908)
- BackgroundTaskHost.exe (PID: 2288)
- RuntimeBroker.exe (PID: 2064)
INFO
Reads Environment values
- OUTLOOK.EXE (PID: 2172)
- EXCEL.EXE (PID: 4480)
- EXCEL.EXE (PID: 1340)
Reads the software policy settings
- OUTLOOK.EXE (PID: 2172)
- EXCEL.EXE (PID: 4480)
- EXCEL.EXE (PID: 1340)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 2172)
- EXCEL.EXE (PID: 4480)
- EXCEL.EXE (PID: 1340)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2172)
- EXCEL.EXE (PID: 4480)
- EXCEL.EXE (PID: 1340)
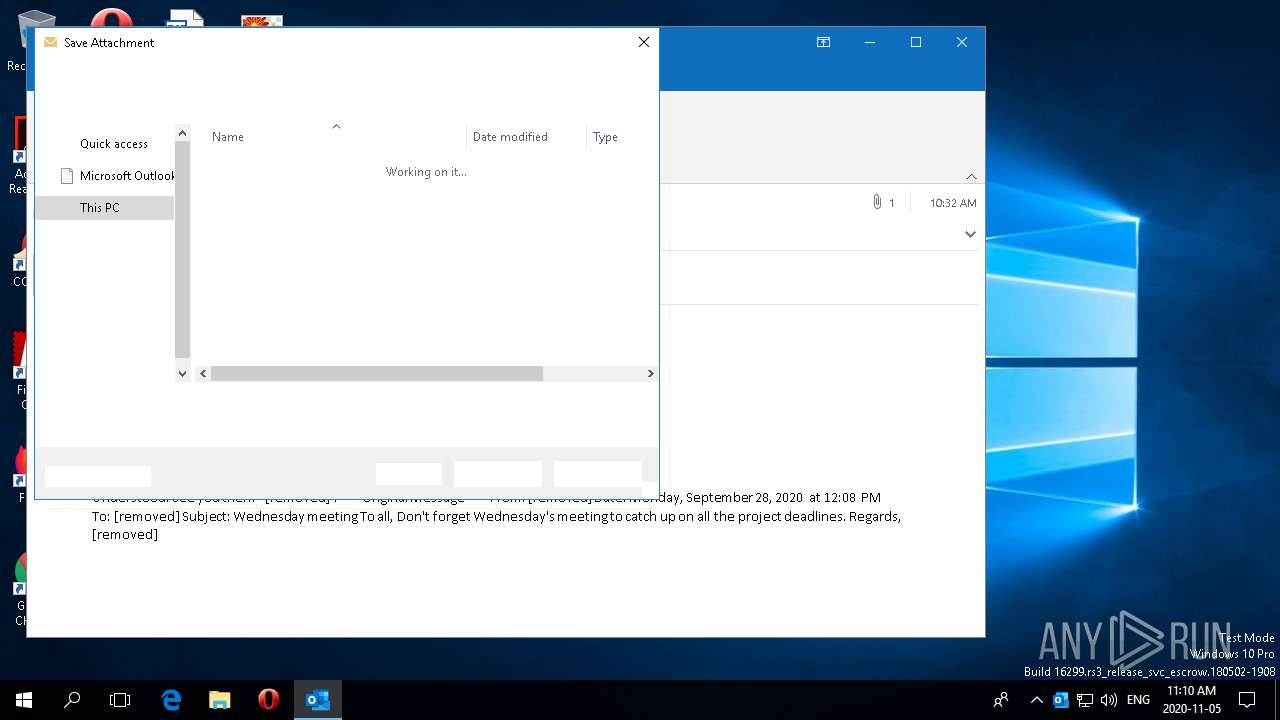
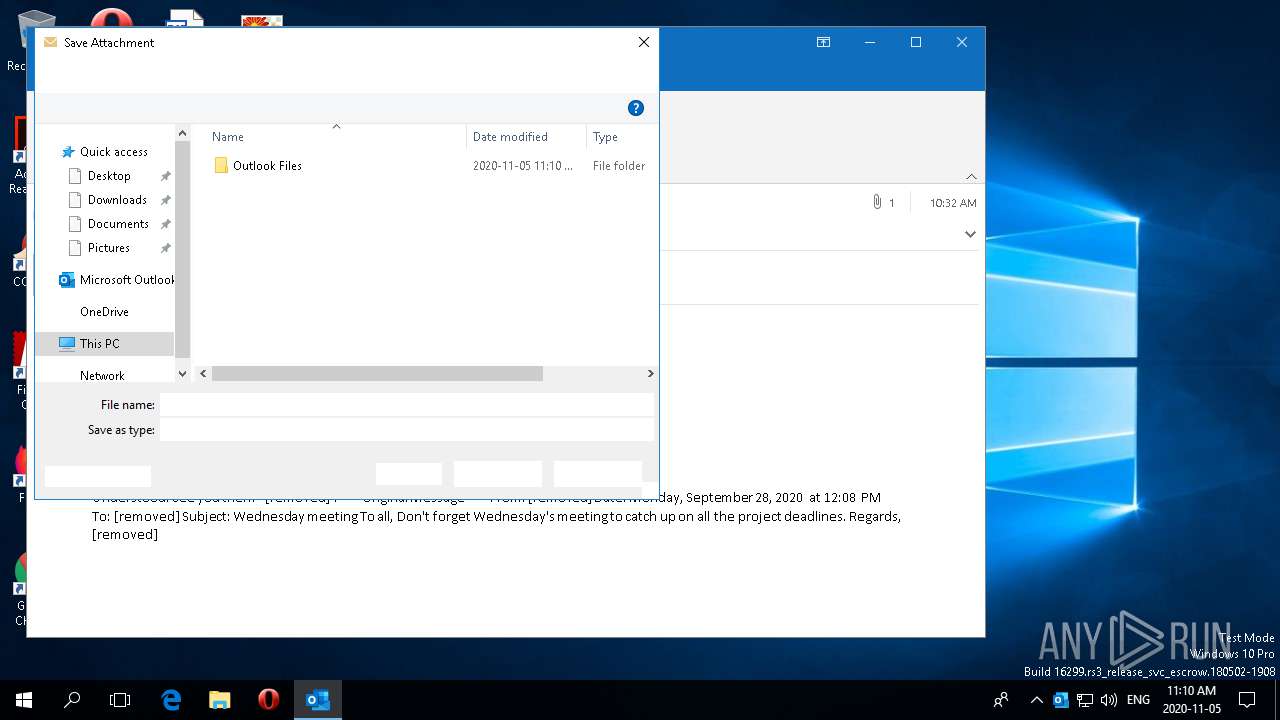
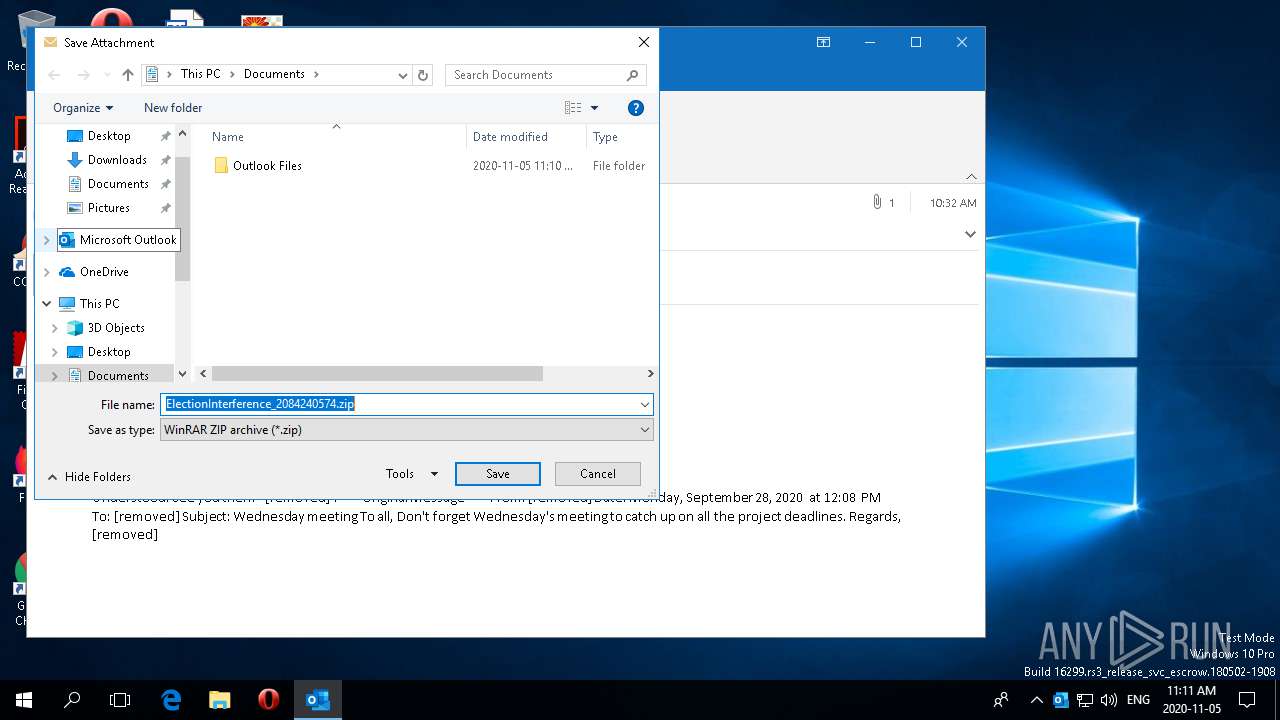
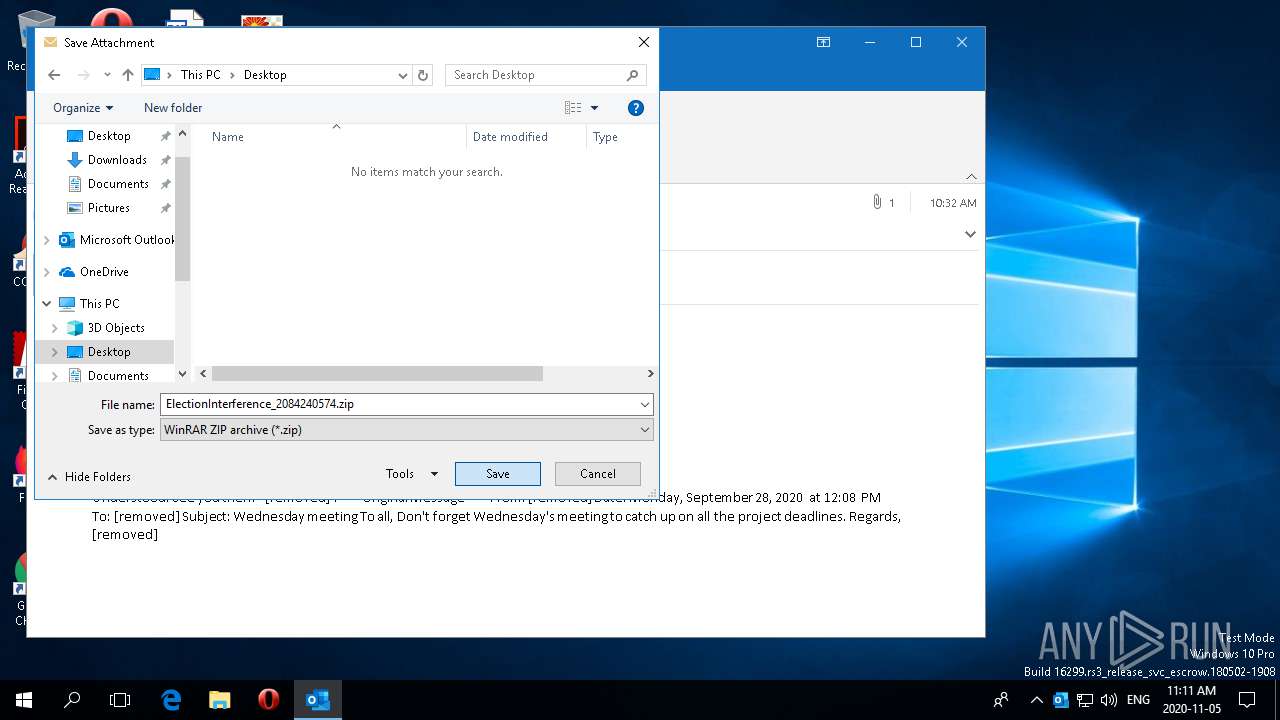
Creates files in the user directory
- OUTLOOK.EXE (PID: 2172)
- EXCEL.EXE (PID: 4480)
- EXCEL.EXE (PID: 1340)
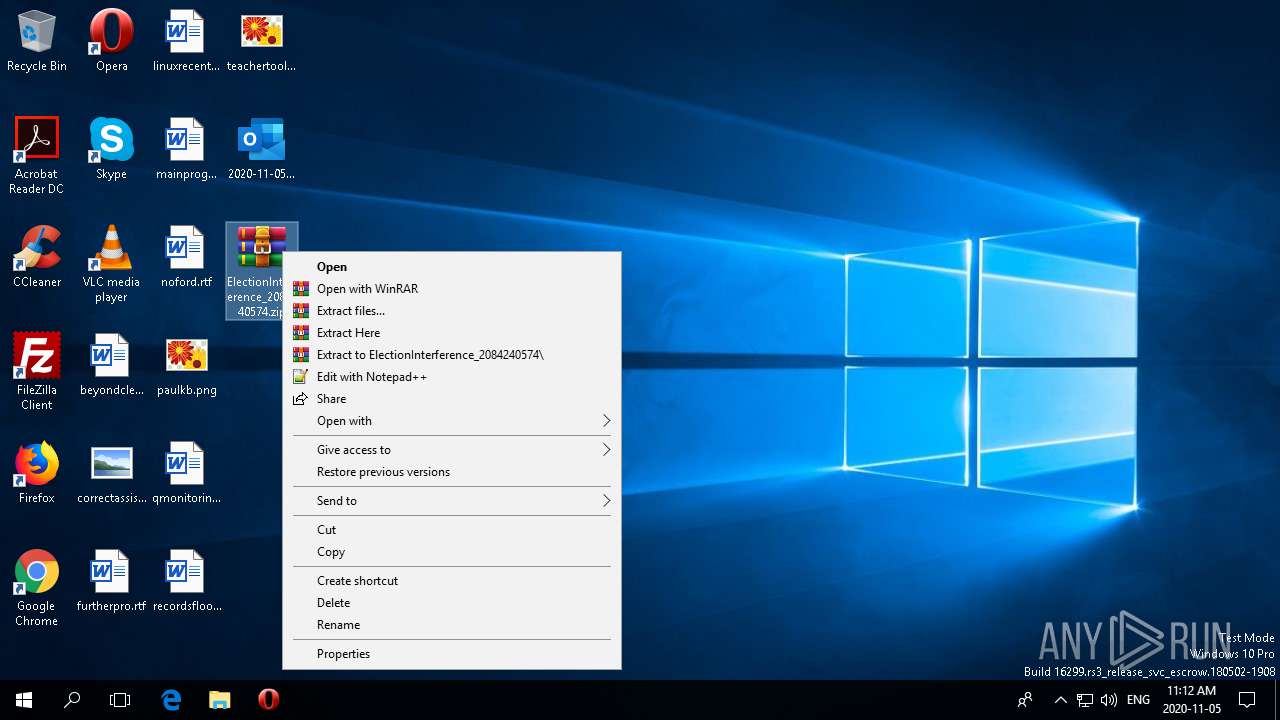
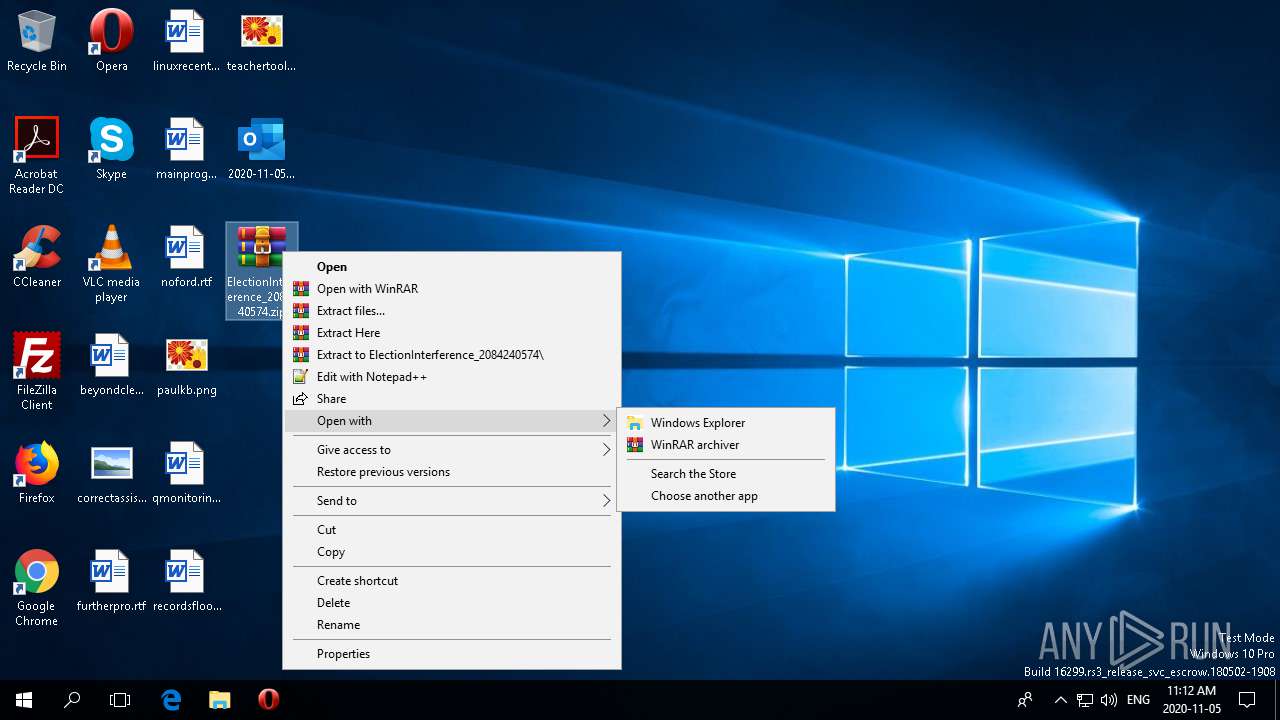
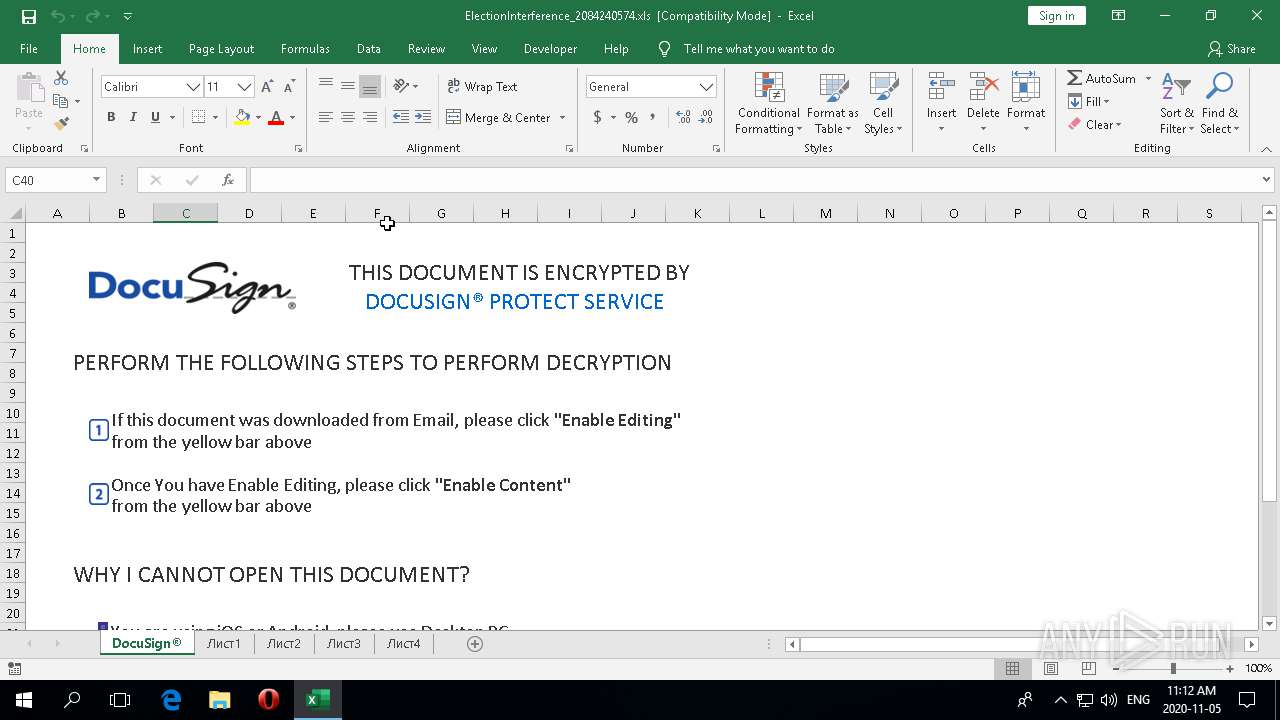
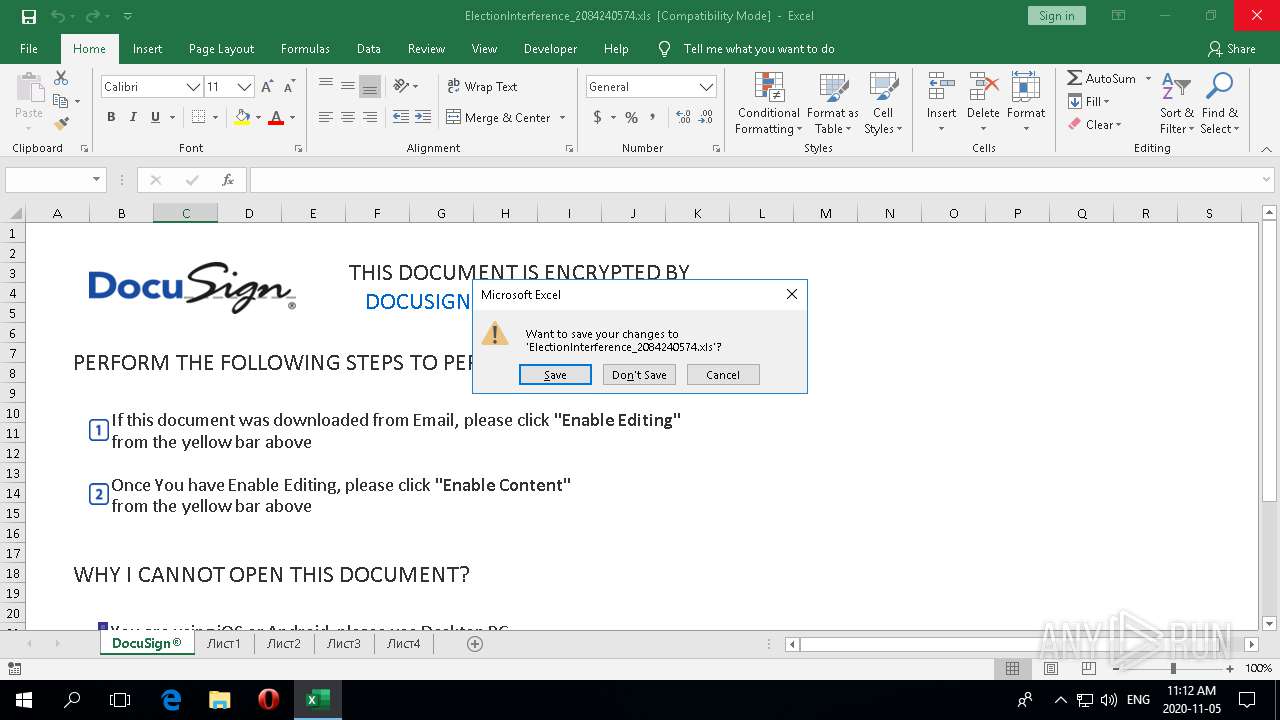
Manual execution by user
- EXCEL.EXE (PID: 4480)
- EXCEL.EXE (PID: 1340)
Scans artifacts that could help determine the target
- EXCEL.EXE (PID: 4480)
- OUTLOOK.EXE (PID: 2172)
- EXCEL.EXE (PID: 1340)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 4480)
- EXCEL.EXE (PID: 1340)
- OUTLOOK.EXE (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
96
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
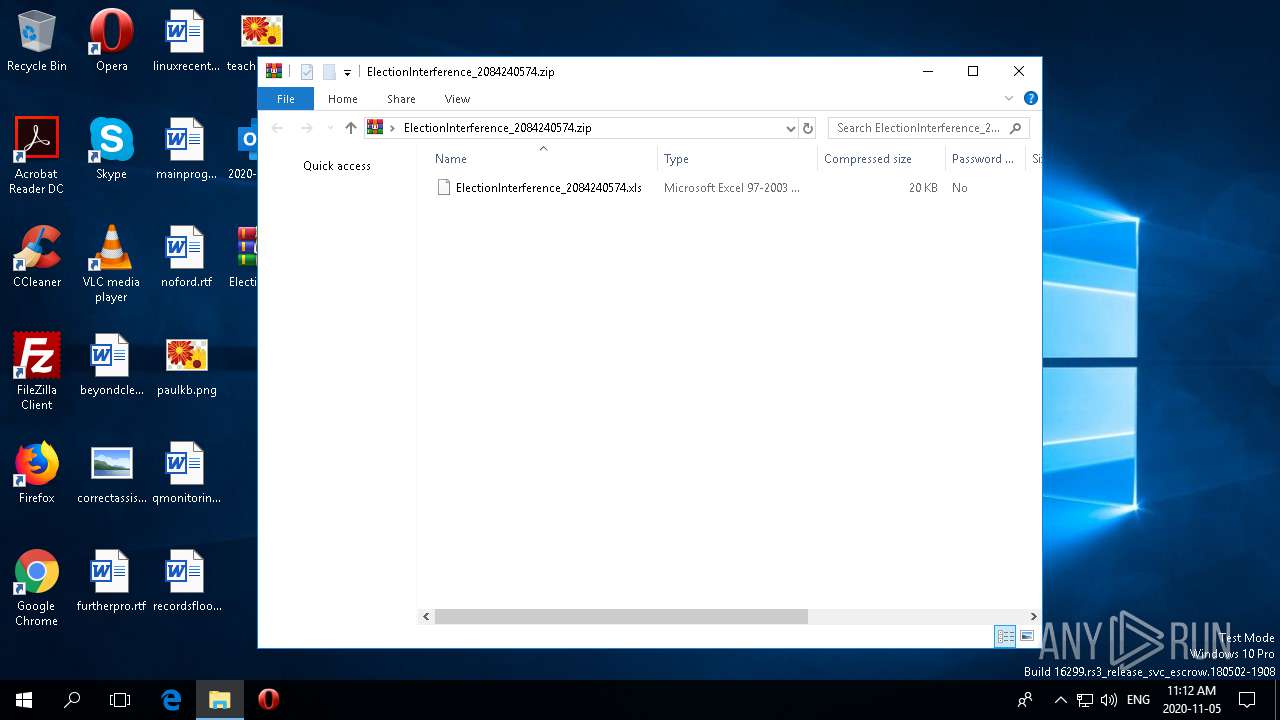
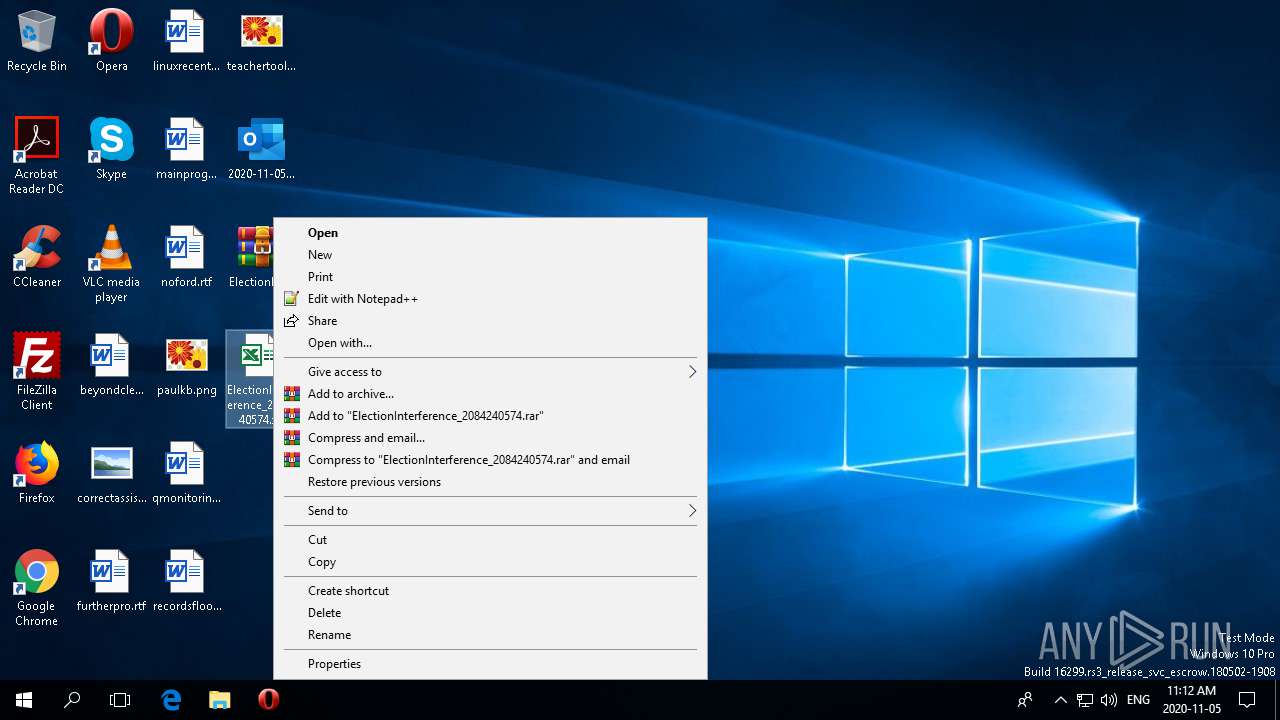
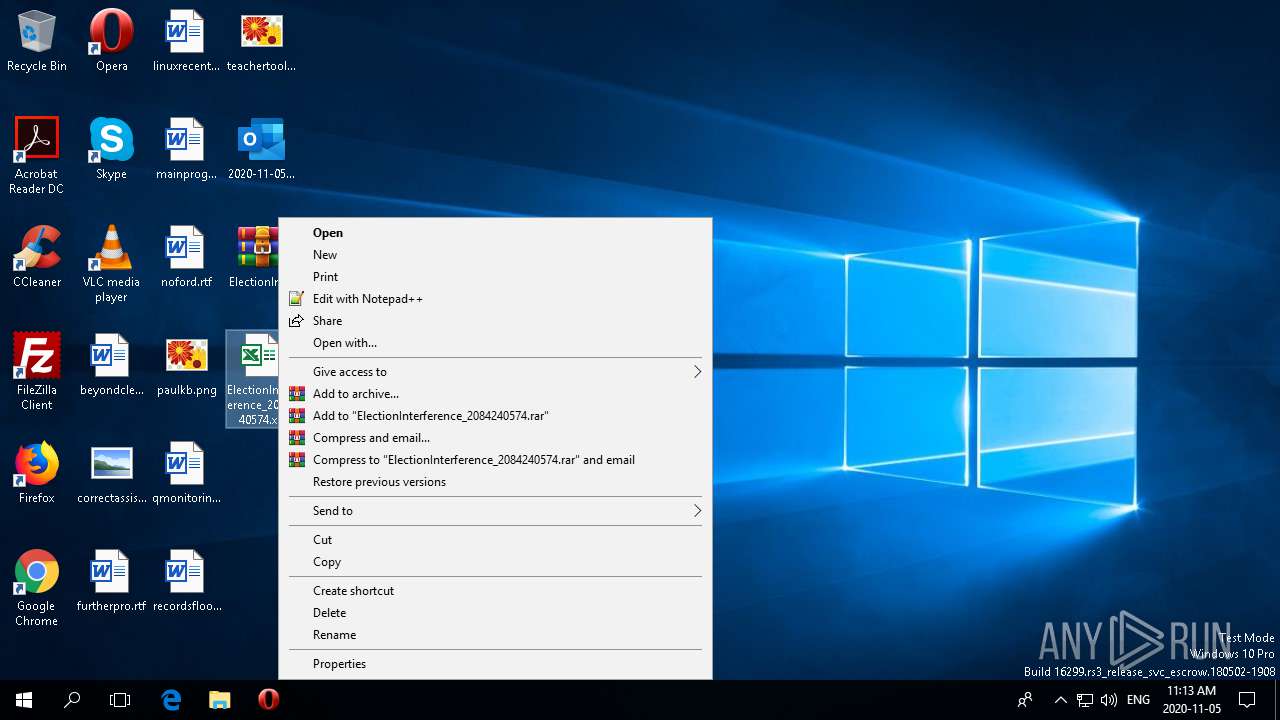
| 1340 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\Desktop\ElectionInterference_2084240574.xls" | C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 2064 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\Desktop\2020-11-05-Qakbot-malspam.eml" | C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 2288 | "C:\WINDOWS\system32\BackgroundTaskHost.exe" -ServerName:BackgroundTaskHost.WebAccountProvider | C:\WINDOWS\system32\BackgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4480 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\Desktop\ElectionInterference_2084240574.xls" | C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 4908 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\WINDOWS\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 348
Read events
4 928
Write events
1 212
Delete events
208
Modification events
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 017C11000000001000284FFA2E01000000000000000300000000000000 | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\OUTLOOK\2172 |
| Operation: | write | Name: | 0 |
Value: 0B0E10D60EC7F6EFE22443B883FC57C3C09CB8230046F3B082C6E2F1ACEB016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E22504F38414E6B6373746B636172474A6766584B757268766239486548717741554A6E78536E416A3275354D3D2200 | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\Logging |
| Operation: | write | Name: | (default) |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK-20201105T1110200444-v2.etl | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: A8D02E06-7F60-429E-AE14-BF99173D2779 | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsData |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | write | Name: | OutlookBootFlag |
Value: 1 | |||
| (PID) Process: | (2172) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
Executable files
0
Suspicious files
7
Text files
38
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
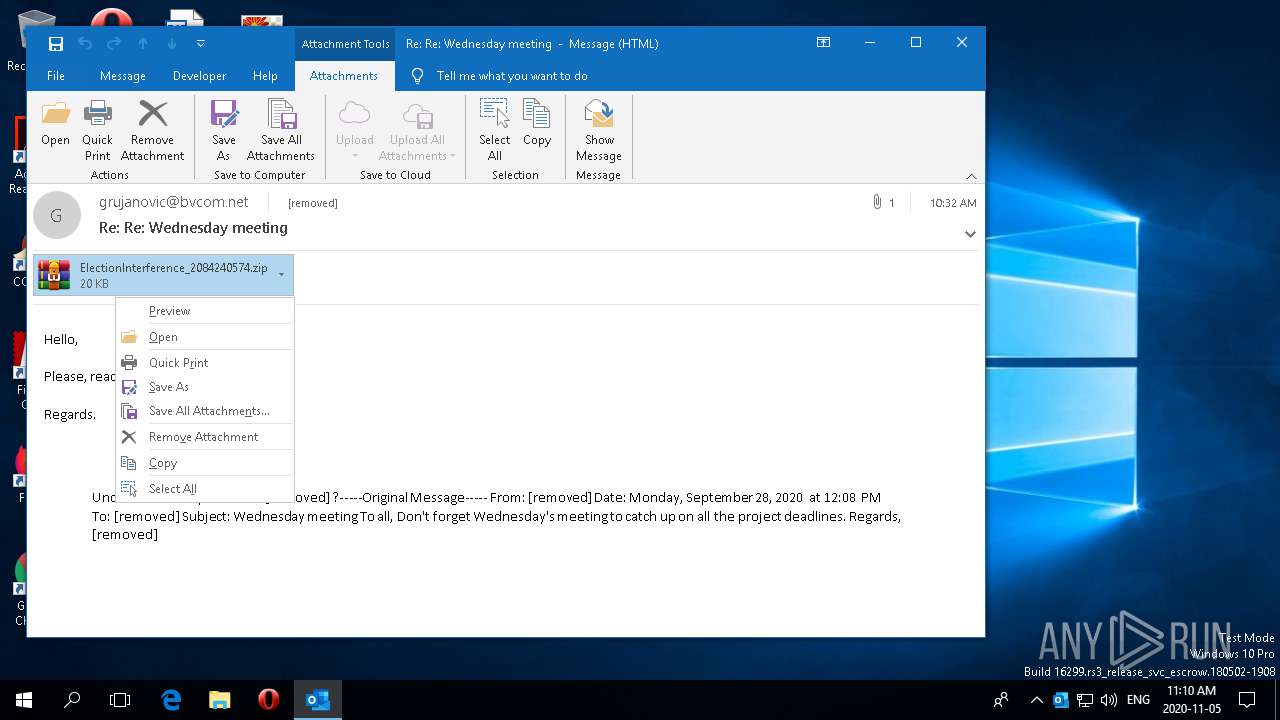
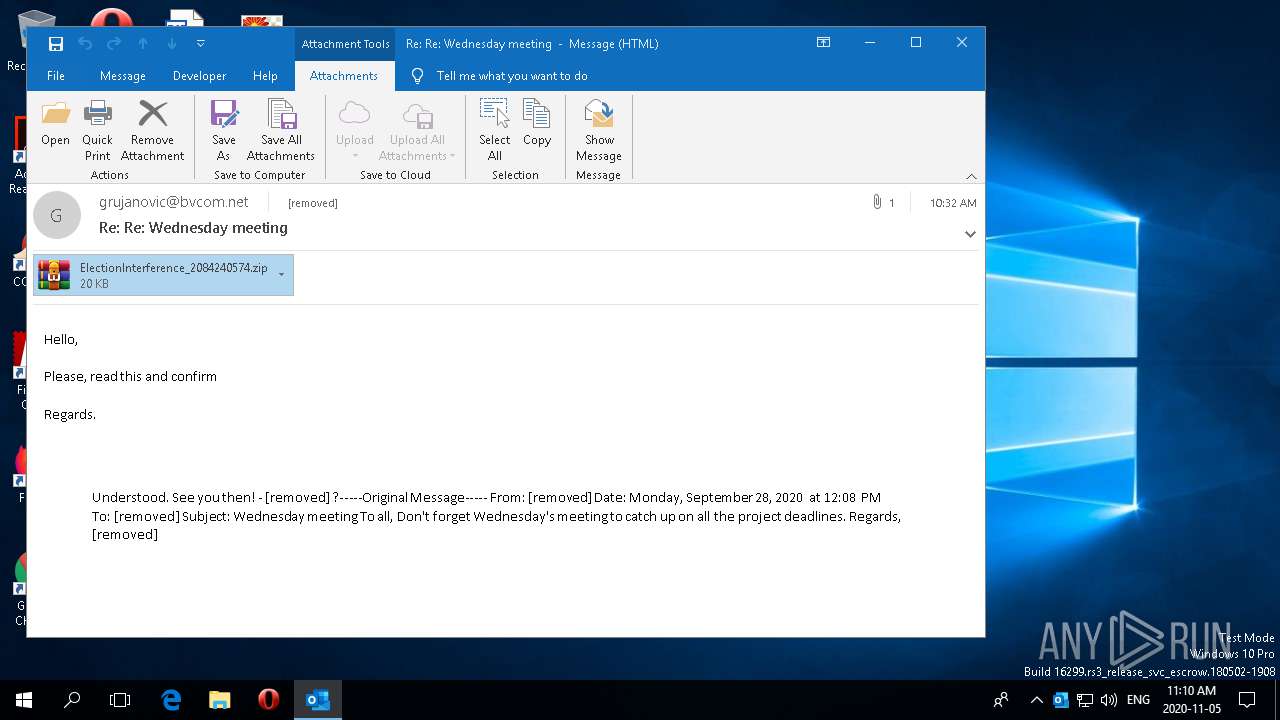
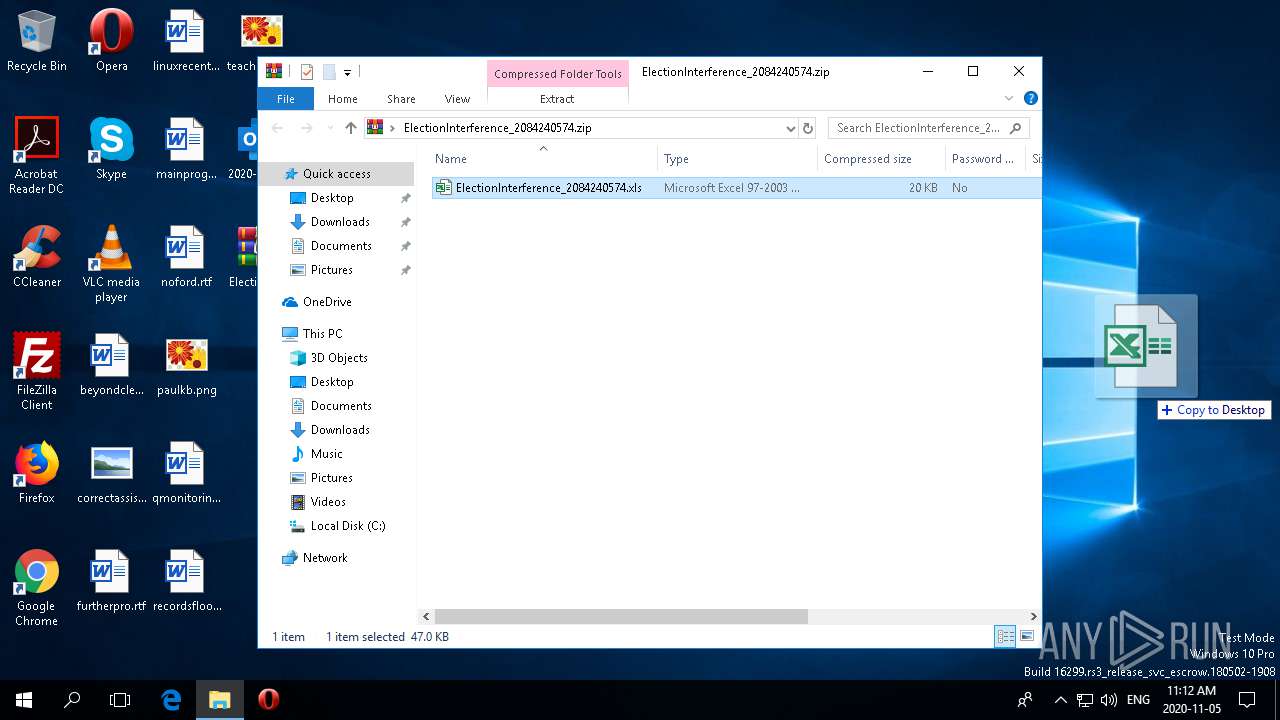
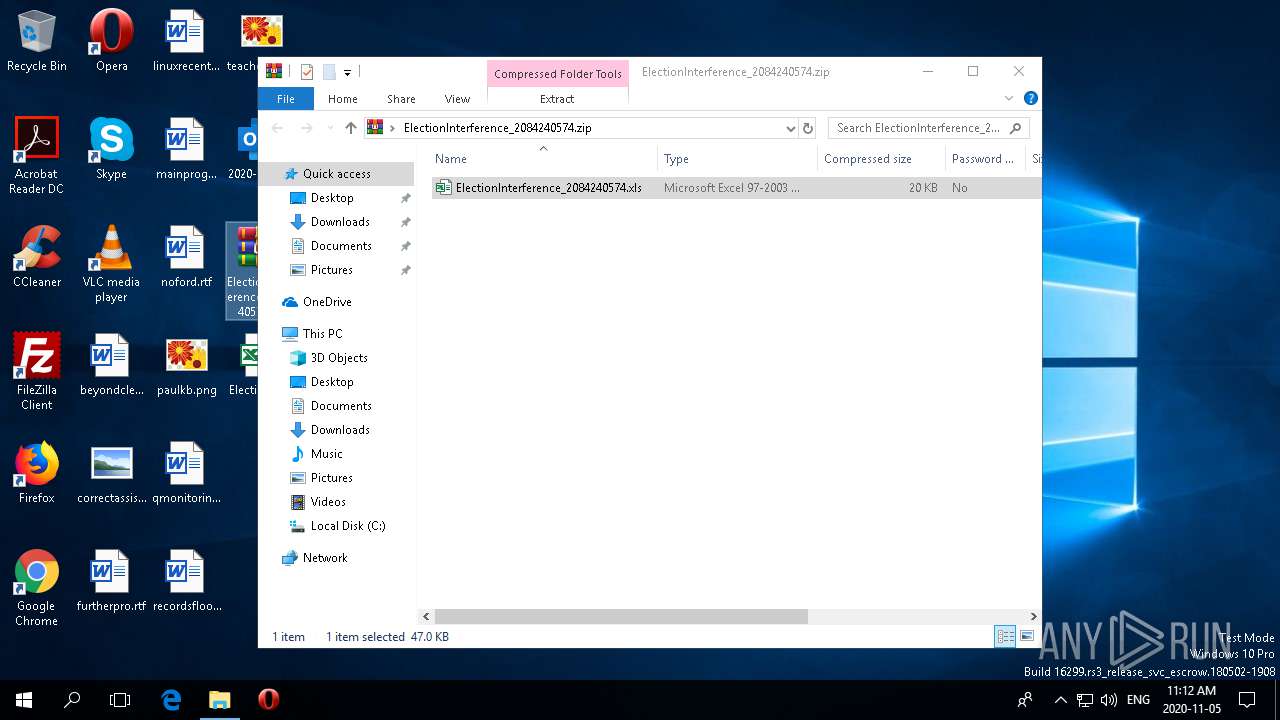
| 2172 | OUTLOOK.EXE | C:\Users\admin\Desktop\ElectionInterference_2084240574.zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\~Outlook1.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{3B77C9BA-2B63-45E6-B9CB-D8A9BA17F147}.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\AA630352-1C21-473B-BCFA-C5E3A556D42A | xml | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Outlook\Outlook.srs | srs | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\.ses | text | |
MD5:— | SHA256:— | |||
| 2172 | OUTLOOK.EXE | C:\Users\admin\Desktop\ElectionInterference_2084240574.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
34
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1928 | svchost.exe | GET | 200 | 52.109.52.36:443 | https://messaging.office.com/lifecycle/legacygetcustommessage16?app=6&ui=en-US&src=Office_CanvasBoot_Win32&messagetype=Canvas&hwid=04111-083-043729&ver=16.0.12026&lc=en-CA&platform=10%3A0%3A16299%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA044%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7BF6C70ED6-E2EF-4324-B883-FC57C3C09CB8%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofgg6vdq3anjh131%2Cofrntm2bbmxkw431%22%7D | JP | xml | 495 b | whitelisted |
1928 | svchost.exe | GET | 200 | 52.109.76.6:443 | https://officeclient.microsoft.com/config16/?syslcid=4105&build=16.0.12026&crev=3 | IE | xml | 127 Kb | whitelisted |
1928 | svchost.exe | GET | 200 | 52.109.52.36:443 | https://messaging.office.com/lifecycle/legacygetcustommessage16?app=6&ui=en-US&src=Office_CanvasLocalSaveDocument_Win32&messagetype=Canvas&hwid=04111-083-043729&ver=16.0.12026&lc=en-CA&platform=10%3A0%3A16299%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA044%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7BF6C70ED6-E2EF-4324-B883-FC57C3C09CB8%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofgg6vdq3anjh131%2Cofrntm2bbmxkw431%22%7D | JP | xml | 495 b | whitelisted |
1928 | svchost.exe | POST | 400 | 40.90.137.124:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 210 b | whitelisted |
1928 | svchost.exe | POST | 200 | 40.90.137.124:443 | https://login.live.com/RST2.srf | US | xml | 1.29 Kb | whitelisted |
1928 | svchost.exe | POST | 200 | 40.90.137.124:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
1928 | svchost.exe | GET | 200 | 52.109.88.5:443 | https://odc.officeapps.live.com/odc/servicemanager/catalog?lcid=1033&syslcid=4105&uilcid=1033&app=5&ver=16&schema=8 | NL | xml | 28.3 Kb | whitelisted |
1928 | svchost.exe | POST | 200 | 40.90.137.124:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 16.7 Kb | whitelisted |
1928 | svchost.exe | POST | 200 | 40.90.137.124:443 | https://login.live.com/RST2.srf | US | xml | 1.98 Kb | whitelisted |
1928 | svchost.exe | POST | 200 | 40.90.137.124:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4480 | EXCEL.EXE | 74.221.216.140:80 | sglr2.revpdev.com | Level 3 Communications, Inc. | US | malicious |
2172 | OUTLOOK.EXE | 52.109.52.36:443 | messaging.office.com | Microsoft Corporation | JP | unknown |
1076 | svchost.exe | 40.90.137.124:443 | login.live.com | Microsoft Corporation | US | unknown |
2172 | OUTLOOK.EXE | 52.109.76.6:443 | officeclient.microsoft.com | Microsoft Corporation | IE | whitelisted |
2172 | OUTLOOK.EXE | 52.109.76.124:443 | roaming.officeapps.live.com | Microsoft Corporation | IE | whitelisted |
2172 | OUTLOOK.EXE | 52.225.255.33:443 | config.edge.skype.com | Microsoft Corporation | US | unknown |
2172 | OUTLOOK.EXE | 52.114.133.60:443 | self.events.data.microsoft.com | Microsoft Corporation | US | suspicious |
2172 | OUTLOOK.EXE | 52.109.88.5:443 | odc.officeapps.live.com | Microsoft Corporation | NL | whitelisted |
2172 | OUTLOOK.EXE | 52.109.8.21:443 | nexusrules.officeapps.live.com | Microsoft Corporation | US | whitelisted |
4480 | EXCEL.EXE | 52.109.76.6:443 | officeclient.microsoft.com | Microsoft Corporation | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
roaming.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |
messaging.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
odc.officeapps.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
sglr2.revpdev.com |
| malicious |
Threats
Process | Message |
|---|---|
OUTLOOK.EXE | ReminderQueueBase:InitializeTable hr=0
|
OUTLOOK.EXE | ReminderQueue: ProcessNotification: End<-----
|
OUTLOOK.EXE | ReminderQueue: Hrinitialize hr = 0
|
OUTLOOK.EXE | Reminder Queue Starts ===========================:
|