| File name: | 7ZipSetup.exe |
| Full analysis: | https://app.any.run/tasks/bb5ef91d-952c-486a-98ab-ebc761036f15 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 03:23:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive, 7 sections |
| MD5: | 02E0B78E2876087F678F070ED60E4C30 |
| SHA1: | 28AB8945612608716CA3959061CE79B92B9C5F41 |
| SHA256: | DDF2542DC5AC74A98D5EE9E55497572104D6C880AAD9137CAF884D10CA5953CE |
| SSDEEP: | 3072:NRwJJwMuPCVVgSDENXkaD0ie4cikNKEaFQqFklrOsfy+b4h:I/0CVVgMENXkaIFTikNKET8w/y24 |
MALICIOUS
Executing a file with an untrusted certificate
- 7ZipSetup.exe (PID: 7424)
- 7ZipSetup.exe (PID: 7504)
SUSPICIOUS
Executable content was dropped or overwritten
- 7ZipSetup.exe (PID: 7504)
Reads Microsoft Outlook installation path
- biclient.exe (PID: 7540)
Reads security settings of Internet Explorer
- biclient.exe (PID: 7540)
Reads Internet Explorer settings
- biclient.exe (PID: 7540)
INFO
The sample compiled with english language support
- 7ZipSetup.exe (PID: 7504)
Reads the computer name
- biclient.exe (PID: 7540)
Checks supported languages
- 7ZipSetup.exe (PID: 7504)
- biclient.exe (PID: 7540)
Create files in a temporary directory
- 7ZipSetup.exe (PID: 7504)
Reads the software policy settings
- biclient.exe (PID: 7540)
Creates files or folders in the user directory
- biclient.exe (PID: 7540)
Checks proxy server information
- biclient.exe (PID: 7540)
Reads the machine GUID from the registry
- biclient.exe (PID: 7540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:17 09:14:12+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 29184 |
| InitializedDataSize: | 14848 |
| UninitializedDataSize: | 110592 |
| EntryPoint: | 0x39ac |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
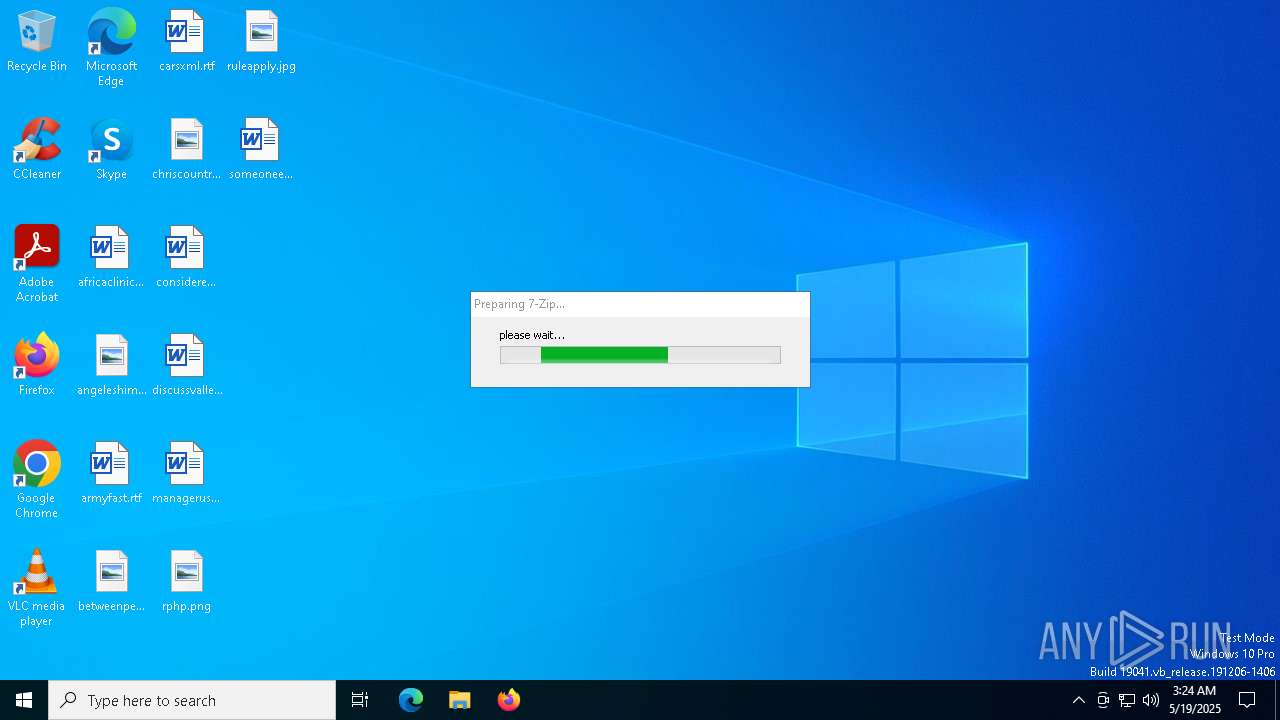
| FileDescription: | Powered by BetterInstaller |
| FileVersion: | 2.0.0.0 |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | - |
Total processes
133
Monitored processes
5
Malicious processes
1
Suspicious processes
2
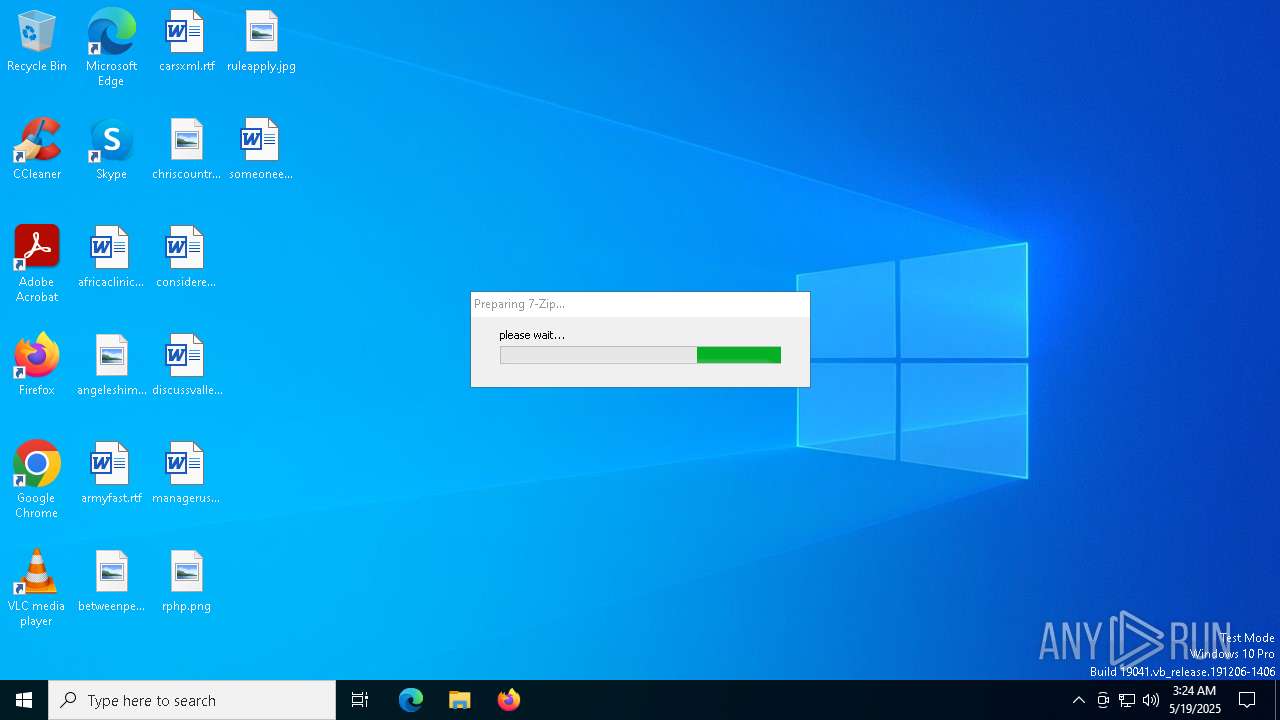
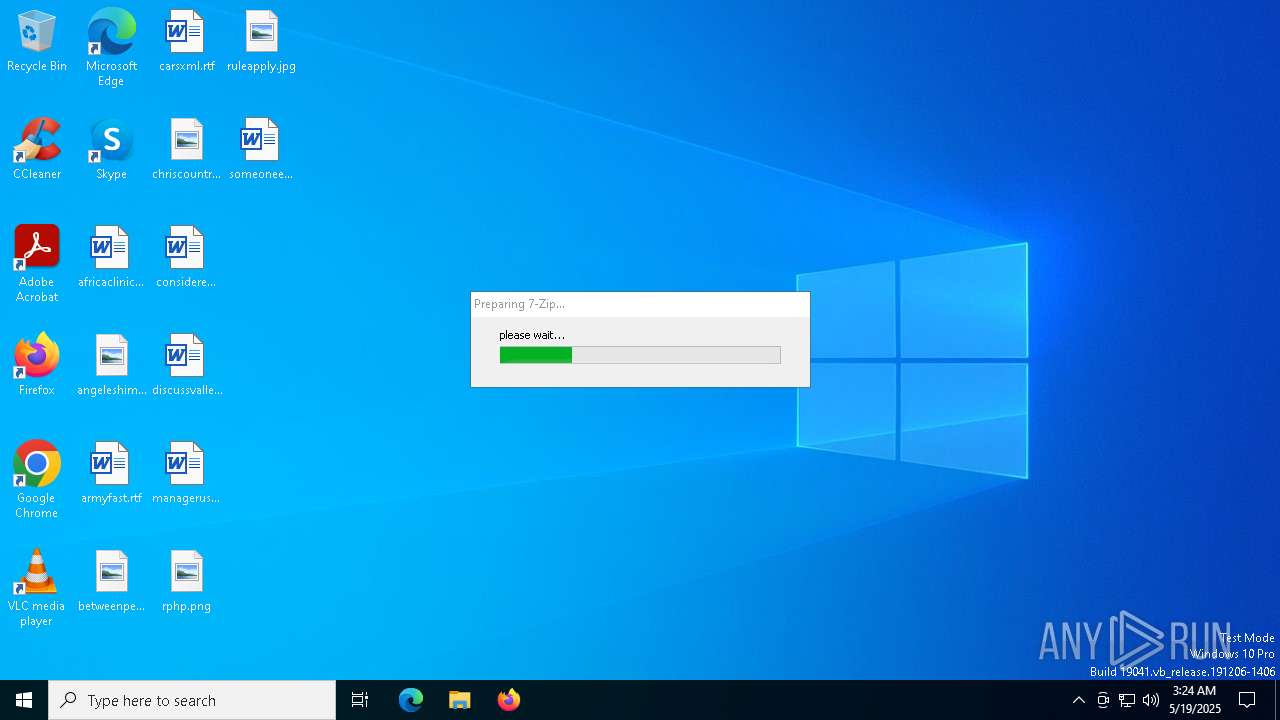
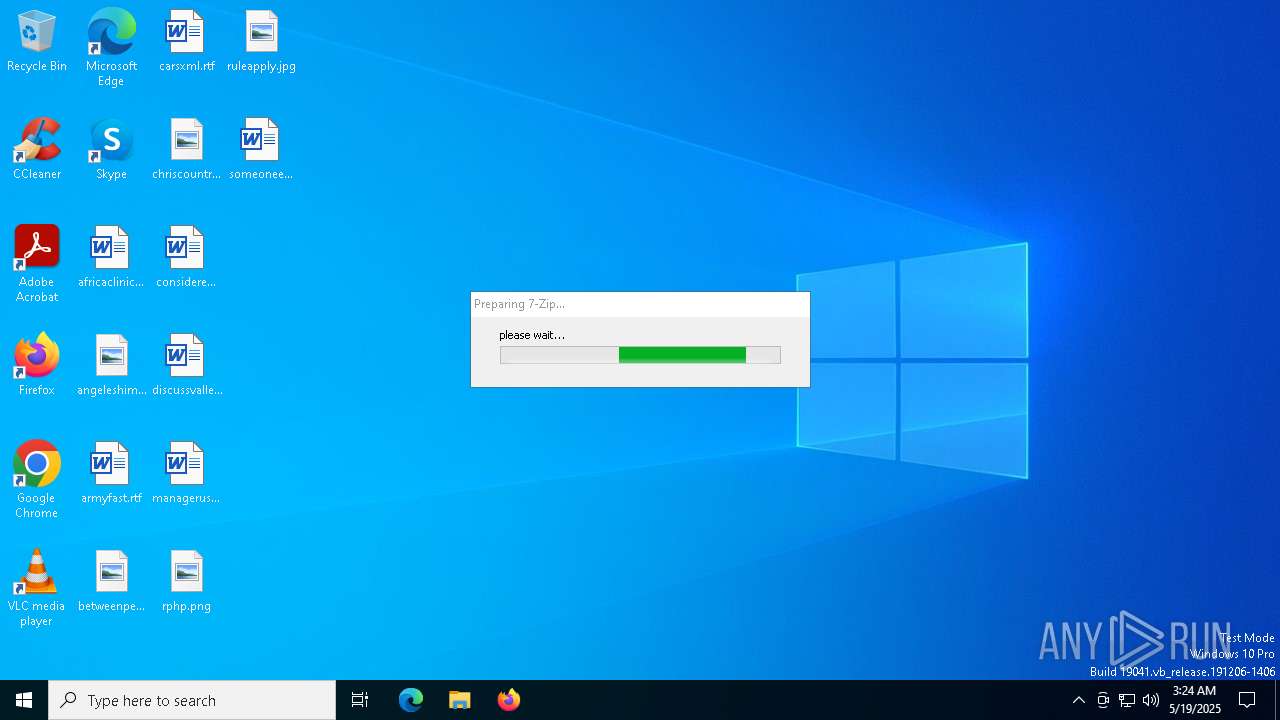
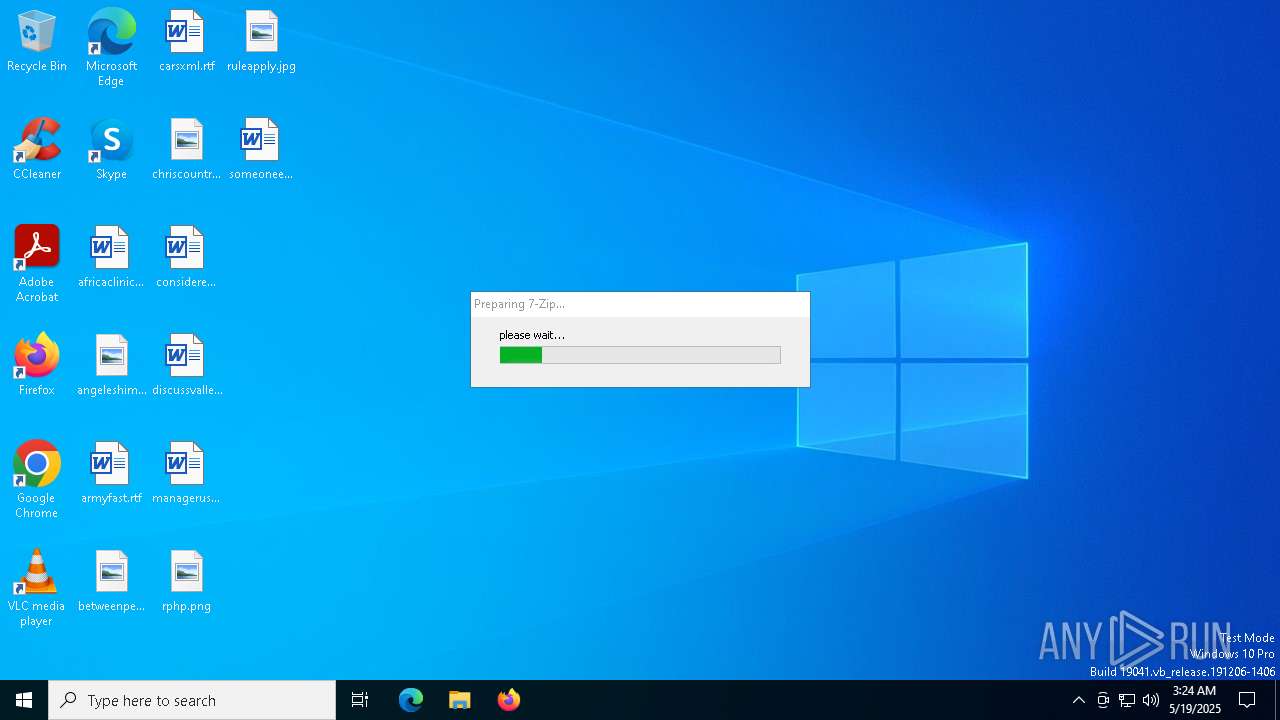
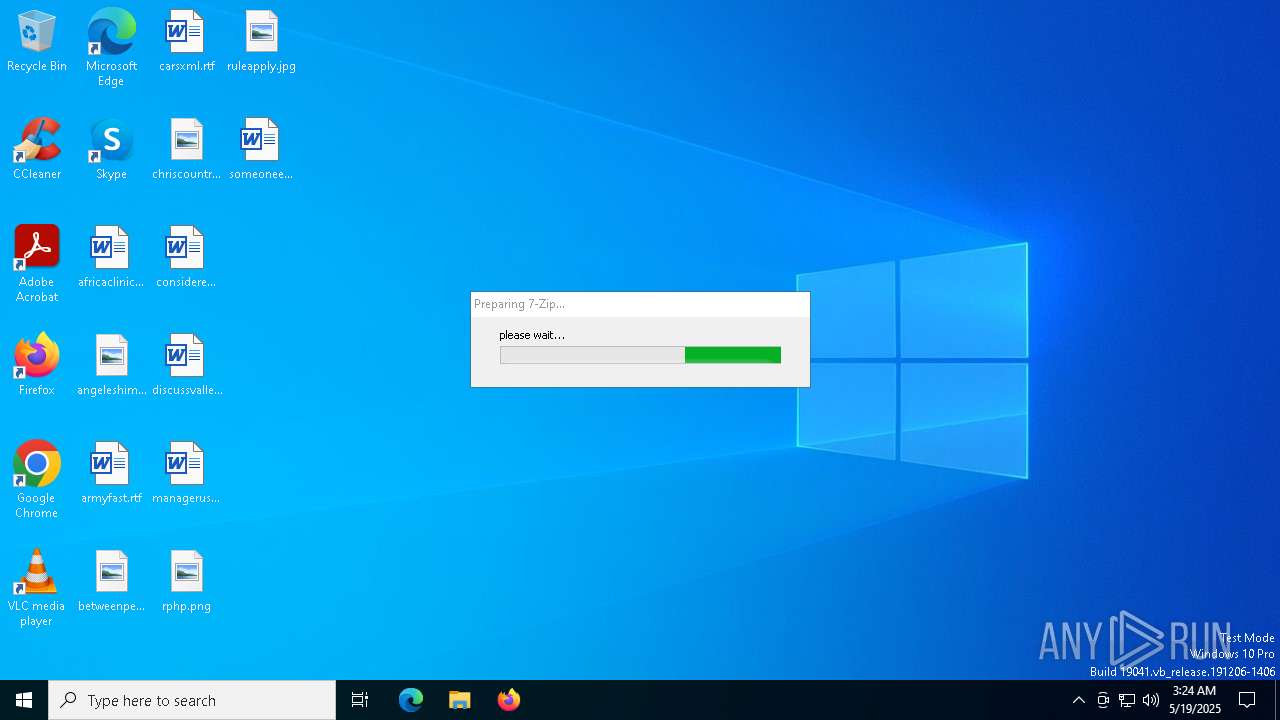
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7424 | "C:\Users\admin\AppData\Local\Temp\7ZipSetup.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Powered by BetterInstaller Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
| 7504 | "C:\Users\admin\AppData\Local\Temp\7ZipSetup.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Powered by BetterInstaller Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 7540 | "C:\Users\admin\AppData\Local\Temp\biclient.exe" /url bi.bisrv.com /affid "awde7zip19538" /id "7zip" /name "7-Zip" /browser ie | C:\Users\admin\AppData\Local\Temp\biclient.exe | 7ZipSetup.exe | ||||||||||||
User: admin Company: Somoto Ltd. Integrity Level: HIGH Description: Better Installer Host Version: 2.0.0.0 Modules
| |||||||||||||||
| 7724 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7756 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 982
Read events
4 979
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7540) biclient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7540) biclient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7540) biclient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
32
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7504 | 7ZipSetup.exe | C:\Users\admin\AppData\Local\Temp\biclient.exe | executable | |
MD5:1BDF5E5015EFCAA68B05CEC0A79BE484 | SHA256:F613D98031EFC7359C708B9D8A11573526C49E4B60D2614E56747927FA6C2D7B | |||
| 7540 | biclient.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:D1F783D4B48EDFEC9E4099E14B726111 | SHA256:A134AF3A0EF67A78A0DC4B1C8860797EFFD37D70C7CF71FB057D678C8D2CDCDC | |||
| 7540 | biclient.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:4A90329071AE30B759D279CCA342B0A6 | SHA256:4F544379EDA8E2653F71472AB968AEFD6B5D1F4B3CE28A5EDB14196184ED3B60 | |||
| 7504 | 7ZipSetup.exe | C:\Users\admin\AppData\Local\Temp\config.ini | text | |
MD5:02C10DC34553FB5FA9D912E75427BB82 | SHA256:BC30A32CC8AFD9322B26BF19587785DFF65CF47204CA5C53CB3C314947E895F3 | |||
| 7504 | 7ZipSetup.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp | binary | |
MD5:DAB2F5FECCCE27C8D38E9A4A04071752 | SHA256:75412A816D5142F87C55FF1CE8FCBC5C6D19BD0E86E6DB8856766F041B989AC2 | |||
| 7540 | biclient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\domain_profile[1].htm | html | |
MD5:5FA7A50E39BF2CAA19D5B2DEF1B3BE67 | SHA256:AAECAD3B1B576F9A12F0332BDE5F6246076EB694F1786652C0FDB2FDCE9368F5 | |||
| 7540 | biclient.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:1FBB37F79B317A9A248E7C4CE4F5BAC5 | SHA256:9BF639C595FE335B6F694EE35990BEFD2123F5E07FD1973FF619E3FC88F5F49F | |||
| 7540 | biclient.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D6AA22DA63AEAA61826C0D7C76455F33_B87D4DA580A9C07F59962FFCFA48D53B | binary | |
MD5:B17B71422B60A88850A492B120F782D1 | SHA256:F57399A6E296EEF3B269C3D1272E721D983475CB72606CB424A92902DFF8167F | |||
| 7540 | biclient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\hd-style-print[1].css | text | |
MD5:1428E811A5676705CB34BE576370E5F9 | SHA256:2A207BE4D6AA734C55E88A0DD2E035449DFC080AA24E5C39DE0B2E269CF3D9A0 | |||
| 7540 | biclient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\reboot.min[1].css | text | |
MD5:51B8B71098EEED2C55A4534E48579A16 | SHA256:BD78E3BCC569D029E7C709144E4038DEDE4D92A143E77BC46E4F15913769758B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
40
DNS requests
29
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 302 | 3.130.253.23:80 | http://bi.bisrv.com/awde7zip19538/7zip/45fc7f6113ad604f86f59033bb29bb4b?v=2.0&muid=A50D937D517FD085822E9A5128E35287 | unknown | — | — | malicious |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 200 | 216.58.212.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 200 | 216.58.212.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 200 | 151.101.130.133:80 | http://ocsp2.globalsign.com/rootr3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEQCA5WrF4j1Lr8MOJXyXArf%2F | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEA5sXoYl5VpVCVfRvCVK8Mg%3D | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEFYLKxOzl6hEEuPKhM%2BnvHQ%3D | unknown | — | — | whitelisted |
7540 | biclient.exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEEALuY4zRY58EDp%2FMW%2B6MIw%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7540 | biclient.exe | 3.130.253.23:80 | bi.bisrv.com | AMAZON-02 | US | malicious |
7540 | biclient.exe | 104.26.7.37:443 | www.hugedomains.com | CLOUDFLARENET | US | whitelisted |
7540 | biclient.exe | 216.58.212.131:80 | c.pki.goog | GOOGLE | US | whitelisted |
7540 | biclient.exe | 151.101.1.229:443 | cdn.jsdelivr.net | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
bi.bisrv.com |
| malicious |
www.hugedomains.com |
| whitelisted |
c.pki.goog |
| whitelisted |
cdn-cookieyes.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
static.hugedomains.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |