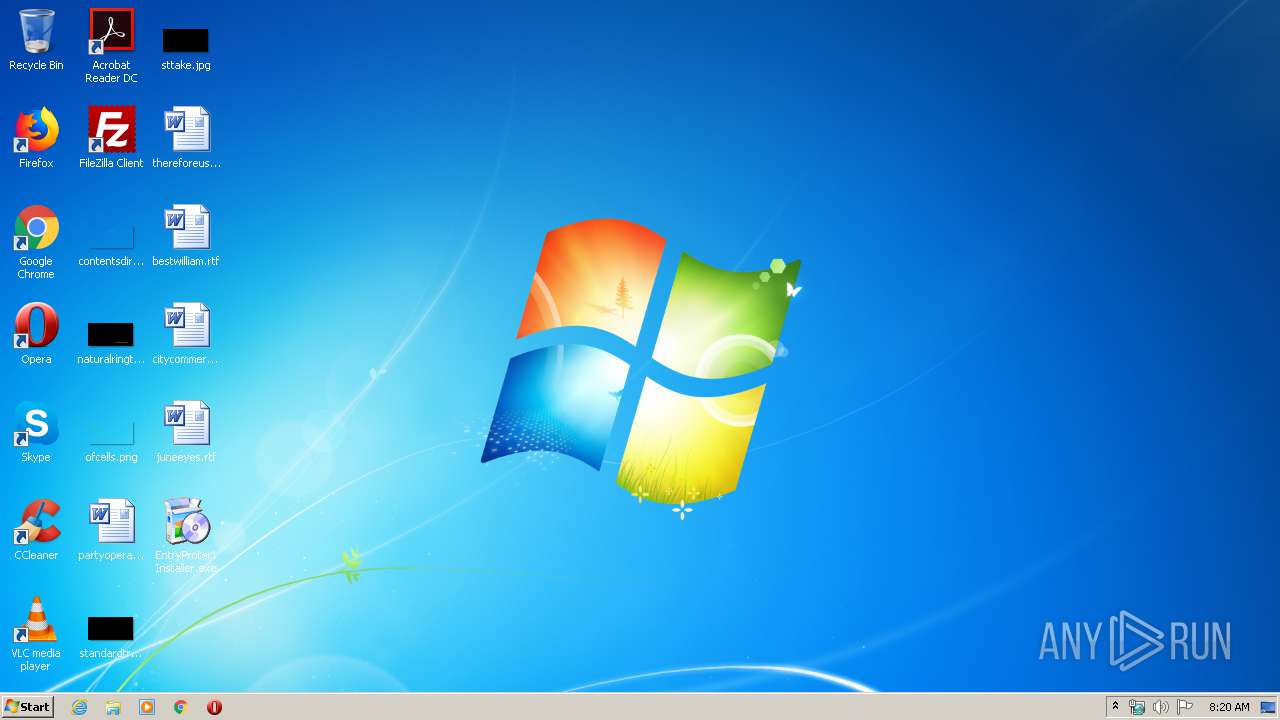
| File name: | EntryProtect Installer.exe |
| Full analysis: | https://app.any.run/tasks/c054f9f9-e74b-4ac6-a34a-570c3e2d2b61 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2020, 08:20:19 |
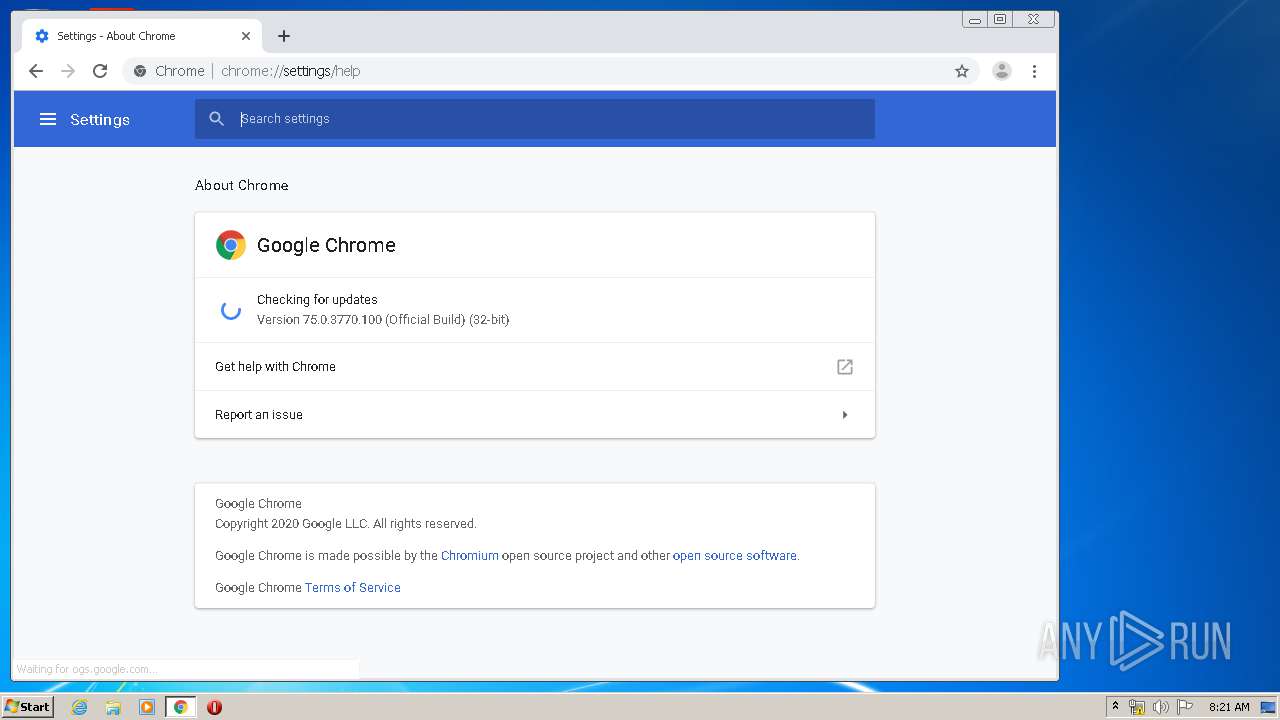
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 558DB933372B0D87DE161A5740DBFD8D |
| SHA1: | B662CC3370371B9239B1D2E859CDDF182B568005 |
| SHA256: | DDE7FFEF6927138B4E3572EEA4B2EEE19698A1014B0FBD3362CCA69BD1E59D22 |
| SSDEEP: | 24576:1VBvUmiMhl3wPkeW4o0DI0uPDMRe5HC5OS5bZfk4B6Ichik9:JniMX30DIhPDCeHqBzchik9 |
MALICIOUS
Loads dropped or rewritten executable
- tmp898B.exe (PID: 2780)
- EntryProtect Installer.exe (PID: 3324)
- inject.exe (PID: 3176)
- DllHost.exe (PID: 3808)
- DllHost.exe (PID: 628)
- taskeng.exe (PID: 1984)
- EntryProtect Installer.exe (PID: 2352)
- windanr.exe (PID: 3564)
- IMEDICTUPDATE.EXE (PID: 1364)
- ctfmon.exe (PID: 652)
- SearchFilterHost.exe (PID: 1860)
- explorer.exe (PID: 372)
- svchost.exe (PID: 1804)
- taskhost.exe (PID: 1968)
- SearchIndexer.exe (PID: 1120)
- svchost.exe (PID: 2196)
- svchost.exe (PID: 1216)
- SearchProtocolHost.exe (PID: 3548)
- winlogon.exe (PID: 428)
- spoolsv.exe (PID: 1188)
- svchost.exe (PID: 592)
- lsm.exe (PID: 492)
- svchost.exe (PID: 824)
- svchost.exe (PID: 796)
- svchost.exe (PID: 860)
- wininit.exe (PID: 380)
- dwm.exe (PID: 2044)
- svchost.exe (PID: 668)
- csrss.exe (PID: 388)
- svchost.exe (PID: 756)
- svchost.exe (PID: 1052)
- lsass.exe (PID: 484)
- services.exe (PID: 472)
- csrss.exe (PID: 344)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 660)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 676)
- chrome.exe (PID: 392)
- wmiprvse.exe (PID: 1232)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 1780)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 1500)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 872)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 1740)
- wmiprvse.exe (PID: 340)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 1928)
- chrome.exe (PID: 572)
- chrome.exe (PID: 744)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 3360)
- consent.exe (PID: 3760)
- chrome.exe (PID: 2948)
- GoogleUpdateBroker.exe (PID: 2932)
- GoogleUpdate.exe (PID: 3932)
- DllHost.exe (PID: 2572)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 1116)
- chrome.exe (PID: 348)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2744)
- GoogleUpdateOnDemand.exe (PID: 3056)
- GoogleUpdate.exe (PID: 2128)
- chrome.exe (PID: 3804)
Application was dropped or rewritten from another process
- tmp898B.exe (PID: 2780)
- inject.exe (PID: 4076)
- inject.exe (PID: 3176)
Application was injected by another process
- lsm.exe (PID: 492)
- services.exe (PID: 472)
- wininit.exe (PID: 380)
- svchost.exe (PID: 756)
- csrss.exe (PID: 344)
- qemu-ga.exe (PID: 1428)
- svchost.exe (PID: 592)
- SearchProtocolHost.exe (PID: 3548)
- explorer.exe (PID: 372)
- SearchIndexer.exe (PID: 1120)
- svchost.exe (PID: 860)
- DllHost.exe (PID: 3808)
- DllHost.exe (PID: 628)
- SearchFilterHost.exe (PID: 1860)
- lsass.exe (PID: 484)
- svchost.exe (PID: 1216)
- windanr.exe (PID: 3564)
- taskeng.exe (PID: 1984)
- svchost.exe (PID: 2196)
- ctfmon.exe (PID: 652)
- dwm.exe (PID: 2044)
- spoolsv.exe (PID: 1188)
- svchost.exe (PID: 1052)
- svchost.exe (PID: 1804)
- IMEDICTUPDATE.EXE (PID: 1364)
- svchost.exe (PID: 824)
- winlogon.exe (PID: 428)
- svchost.exe (PID: 668)
- csrss.exe (PID: 388)
- svchost.exe (PID: 796)
Runs injected code in another process
- inject.exe (PID: 3176)
Changes settings of System certificates
- GoogleUpdate.exe (PID: 2128)
SUSPICIOUS
Removes files from Windows directory
- svchost.exe (PID: 1052)
Application launched itself
- EntryProtect Installer.exe (PID: 3324)
Creates files in the program directory
- tmp898B.exe (PID: 2780)
- EntryProtect Installer.exe (PID: 2352)
Executable content was dropped or overwritten
- EntryProtect Installer.exe (PID: 2352)
- tmp898B.exe (PID: 2780)
Creates files in the Windows directory
- svchost.exe (PID: 1052)
Creates or modifies windows services
- services.exe (PID: 472)
- inject.exe (PID: 3176)
Searches for installed software
- svchost.exe (PID: 796)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 2128)
INFO
Application launched itself
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2944)
Reads the hosts file
- chrome.exe (PID: 392)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 872)
Reads settings of System Certificates
- chrome.exe (PID: 392)
- chrome.exe (PID: 872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:11 22:24:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 299520 |
| InitializedDataSize: | 1704960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3192a |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2019 21:24:04 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 11-Dec-2019 21:24:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004918A | 0x00049200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49904 |
.rdata | 0x0004B000 | 0x00018832 | 0x00018A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06116 |
.data | 0x00064000 | 0x00004264 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70084 |
.gfids | 0x00069000 | 0x000001C4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.4306 |
.tls | 0x0006A000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0006B000 | 0x0017E99C | 0x0017EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.5258 |
.reloc | 0x001EA000 | 0x0000565C | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.5399 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.84923 | 373 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.13669 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.91985 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.83772 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.68656 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.50268 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.86669 | 90 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
102 | 7.7944 | 1089040 | Latin 1 / Western European | UNKNOWN | BINRES |
103 | 6.46725 | 466984 | Latin 1 / Western European | UNKNOWN | BINRES |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
90
Monitored processes
83
Malicious processes
39
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | C:\Windows\system32\wbem\wmiprvse.exe -secured -Embedding | C:\Windows\system32\wbem\wmiprvse.exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Provider Host Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 344 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1152,9948927321608451533,14915475128369503710,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3294928707845383531 --mojo-platform-channel-handle=3924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 380 | wininit.exe | C:\Windows\System32\wininit.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | explorer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1200,7557334342452532223,7551773520862612363,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14818690704179793712 --mojo-platform-channel-handle=1732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 428 | winlogon.exe | C:\Windows\System32\winlogon.exe | explorer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 472 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 484 | C:\Windows\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 895
Read events
2 631
Write events
253
Delete events
11
Modification events
| (PID) Process: | (3324) EntryProtect Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3324) EntryProtect Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 6 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 5 | |||
| (PID) Process: | (1052) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (472) services.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\entryprotectdrv |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (472) services.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\entryprotectdrv |
| Operation: | write | Name: | Start |
Value: 2 | |||
| (PID) Process: | (472) services.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\entryprotectdrv |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (472) services.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\entryprotectdrv |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Program Files\SentryBay\EntryProtect\entryprotect.sys | |||
| (PID) Process: | (472) services.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\entryprotectdrv |
| Operation: | write | Name: | DisplayName |
Value: EntryProtect Driver | |||
Executable files
10
Suspicious files
53
Text files
318
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | tmp898B.exe | C:\Program Files\SentryBay\EntryProtect\epclient32.dll.6.4.0.11681.new | — | |
MD5:— | SHA256:— | |||
| 2780 | tmp898B.exe | C:\Program Files\SentryBay\EntryProtect\entryprotect.sys.6.4.0.11681.new | — | |
MD5:— | SHA256:— | |||
| 2780 | tmp898B.exe | C:\Program Files\SentryBay\EntryProtect\entryprotect.cat.6.4.0.11681.new | — | |
MD5:— | SHA256:— | |||
| 2780 | tmp898B.exe | C:\Program Files\SentryBay\EntryProtect\epinject.sys.6.4.0.11681.new | — | |
MD5:— | SHA256:— | |||
| 2780 | tmp898B.exe | C:\Program Files\SentryBay\EntryProtect\epinject.cat.6.4.0.11681.new | — | |
MD5:— | SHA256:— | |||
| 2780 | tmp898B.exe | C:\Users\admin\AppData\Local\Temp\nsg8A09.tmp | — | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E674DF0-C6C.pma | — | |
MD5:— | SHA256:— | |||
| 2352 | EntryProtect Installer.exe | C:\Users\admin\AppData\Local\Temp\tmp898B.exe | executable | |
MD5:— | SHA256:— | |||
| 2780 | tmp898B.exe | C:\Program Files\SentryBay\EntryProtect\epclient32.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
32
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
872 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
872 | chrome.exe | GET | 200 | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=159.148.186.185&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1583828415&mv=m&mvi=2&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
872 | chrome.exe | GET | 200 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=159.148.186.185&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1583828415&mv=m&mvi=1&pl=24&shardbypass=yes | LV | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | chrome.exe | 159.148.69.142:80 | r3---sn-a5uoxu-gpme.gvt1.com | LATNET SERVISS Ltd. | LV | whitelisted |
392 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
392 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
392 | chrome.exe | 216.58.208.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
392 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
392 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
392 | chrome.exe | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
392 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
392 | chrome.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
392 | chrome.exe | 172.217.16.195:443 | www.google.lv | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |