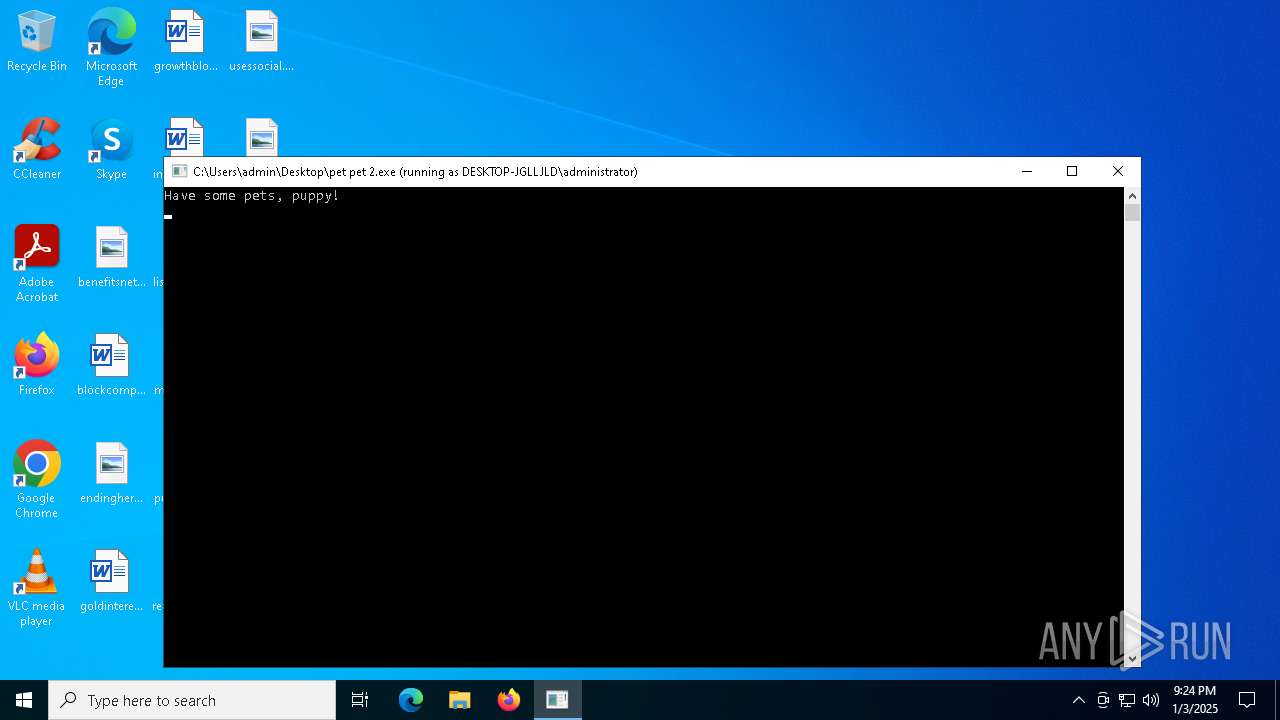
| File name: | pet pet 2.exe |
| Full analysis: | https://app.any.run/tasks/97ab17ed-6ebf-4980-8763-3a088bb778a5 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2025, 21:24:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | C267D57D1DBC5D7E85F9628262526DC1 |
| SHA1: | 235FD07BE5E6C78DAB2605889D54B681B6002582 |
| SHA256: | DDE720ADCC360541C1ED4437987EA050DEC335CBB12FCAD2D265A4A1B058396F |
| SSDEEP: | 3072:nCYa+0Nu6vQAkQ5S7JmyxCbBKhiTbMCvr:UQLi8NiTblvr |
MALICIOUS
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 6384)
SUSPICIOUS
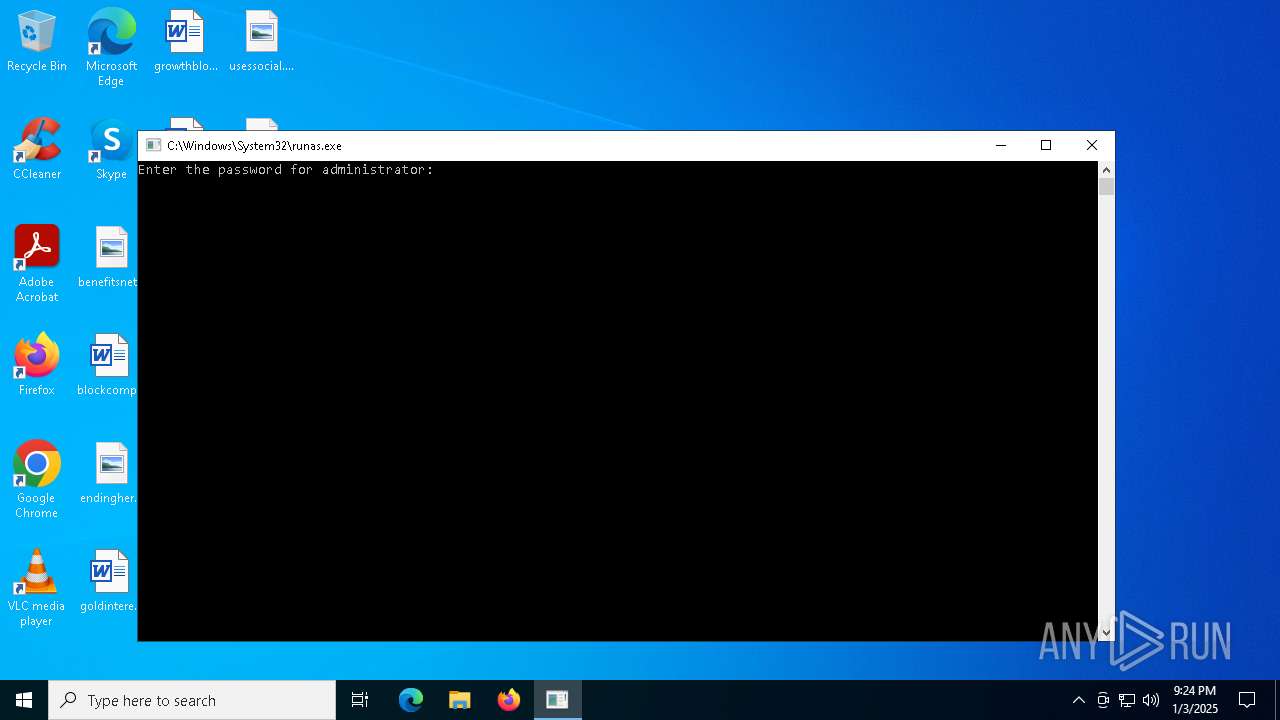
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 6328)
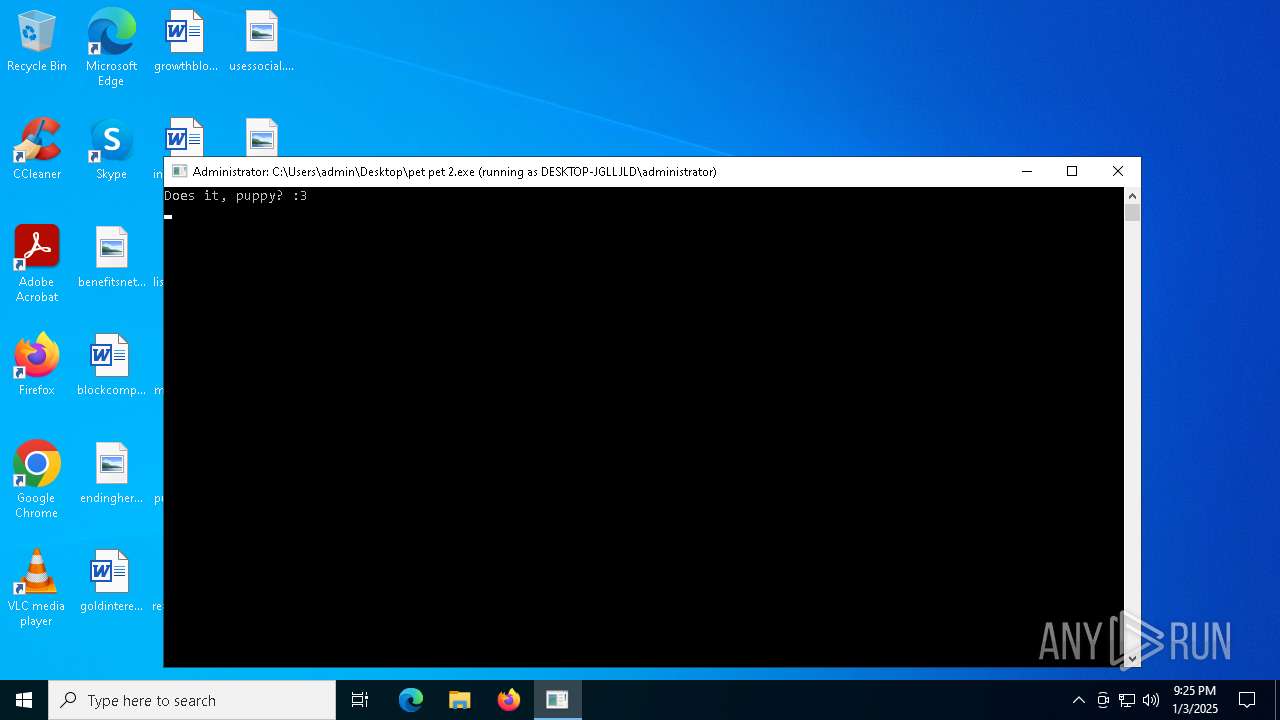
Executing commands from a ".bat" file
- pet pet 2.exe (PID: 6592)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6544)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6676)
- pet pet 2.exe (PID: 6592)
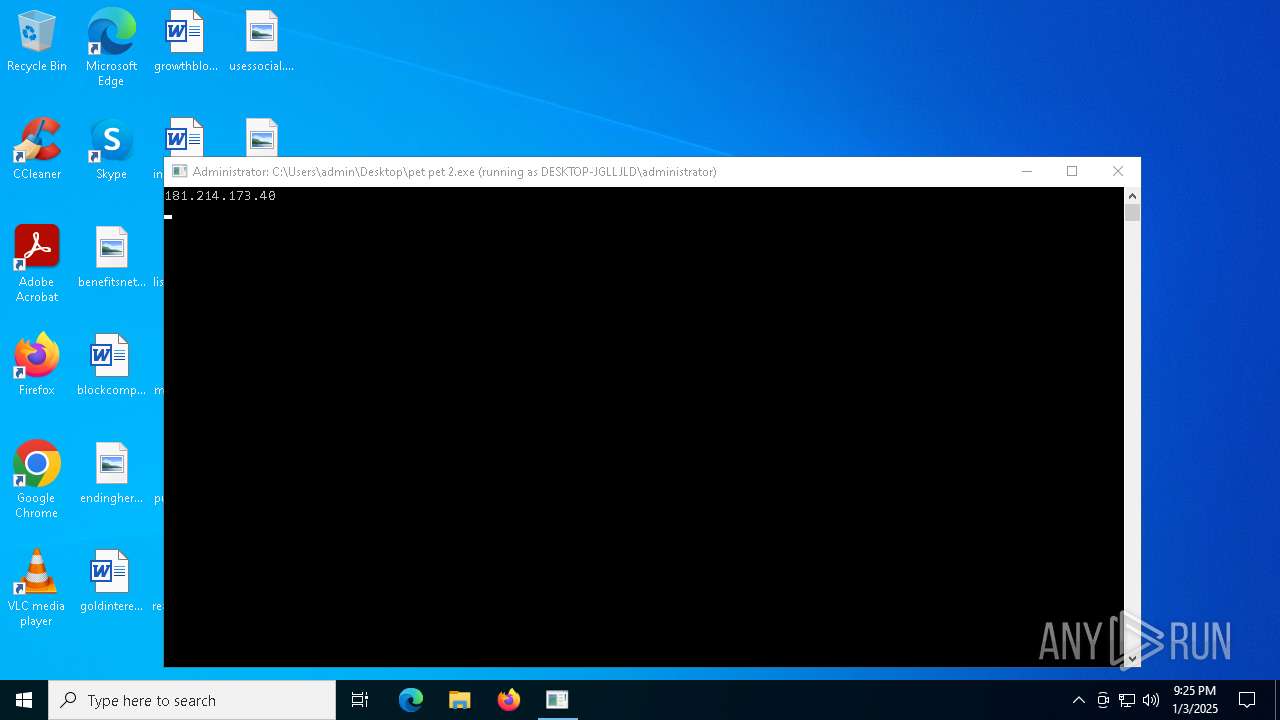
Checks for external IP
- powershell.exe (PID: 6384)
Application launched itself
- cmd.exe (PID: 6676)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6676)
INFO
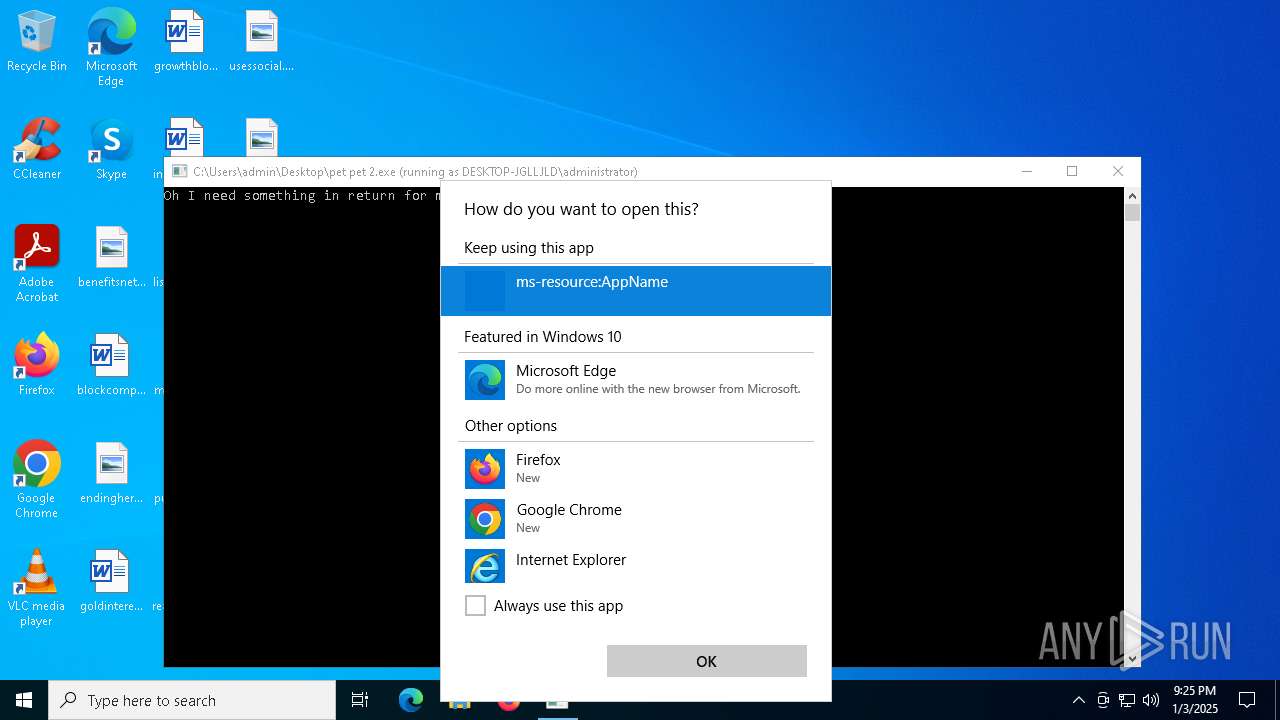
Reads security settings of Internet Explorer
- cmd.exe (PID: 6676)
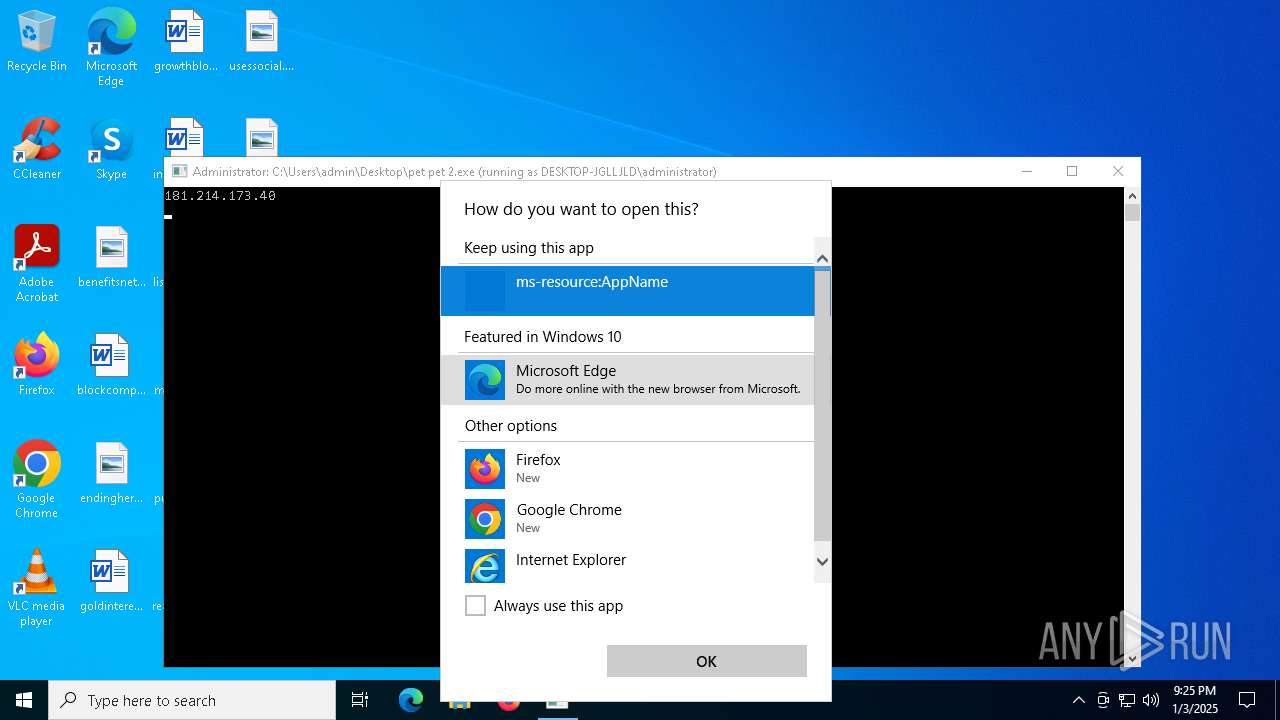
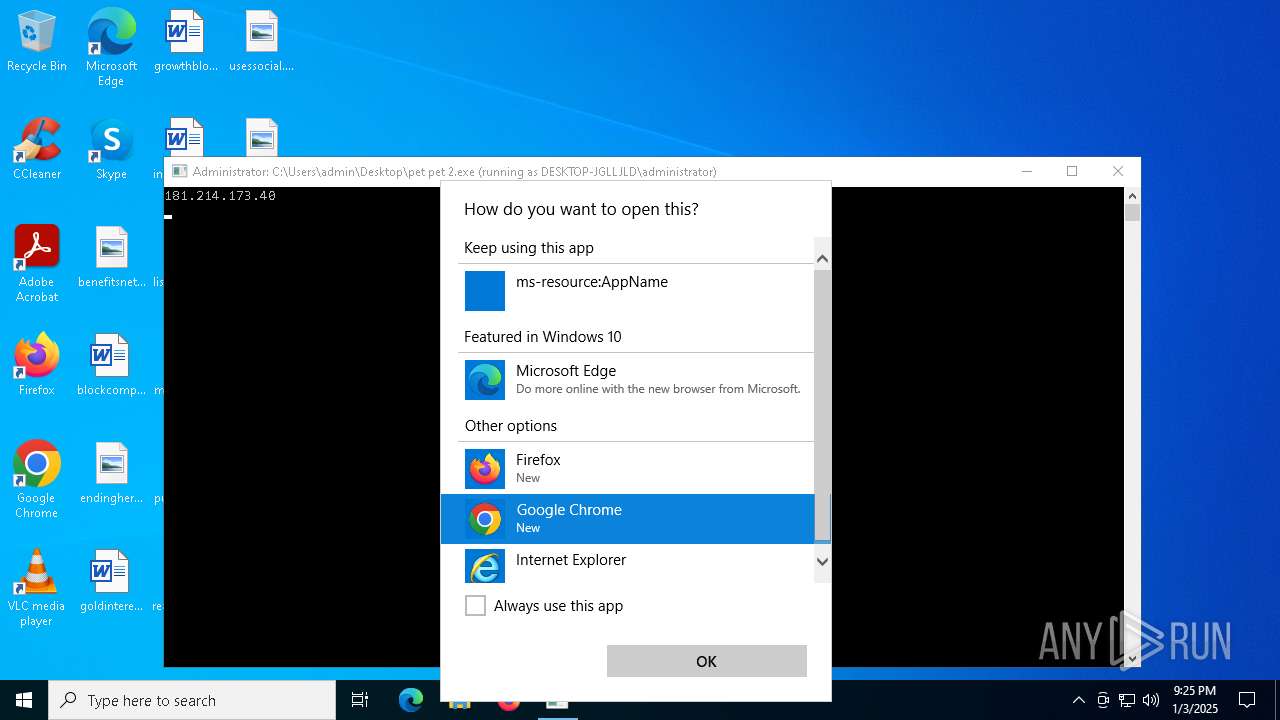
- OpenWith.exe (PID: 2672)
Checks proxy server information
- powershell.exe (PID: 6384)
Checks supported languages
- pet pet 2.exe (PID: 6592)
Creates files in the program directory
- chrome.exe (PID: 6212)
- chrmstp.exe (PID: 4548)
Sends debugging messages
- chrome.exe (PID: 6216)
Application launched itself
- chrome.exe (PID: 6212)
- chrmstp.exe (PID: 4548)
- chrmstp.exe (PID: 3652)
The process uses the downloaded file
- chrome.exe (PID: 6760)
- chrome.exe (PID: 7164)
- chrome.exe (PID: 5544)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 1512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:30 08:52:45+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 70656 |
| InitializedDataSize: | 25600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
200
Monitored processes
68
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3904 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6204 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2992 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\122.0.6261.70\Installer\chrmstp.exe" --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\WINDOWS\SystemTemp\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x29c,0x2a0,0x2a4,0x278,0x2a8,0x7ff7482717e8,0x7ff7482717f4,0x7ff748271800 | C:\Program Files\Google\Chrome\Application\122.0.6261.70\Installer\chrmstp.exe | — | chrmstp.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=5144 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2348 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=3048 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6636 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5612 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6568 --field-trial-handle=1924,i,17164979456807473124,2226850696288135103,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
19 653
Read events
19 616
Write events
37
Delete events
0
Modification events
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CacheVersion |
Value: 1 | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CacheLimit |
Value: 1 | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D7D0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CacheVersion |
Value: 1 | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CacheLimit |
Value: 337920 | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CacheVersion |
Value: 1 | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CacheLimit |
Value: 1 | |||
| (PID) Process: | (6676) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
423
Text files
106
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6592 | pet pet 2.exe | C:\Users\Administrator\AppData\Local\Temp\62E4.tmp\62E5.tmp\62E6.bat | text | |
MD5:383CBFBCD26F68296CB1C11A1B4AD60F | SHA256:63720E48119191877CDEC9396A3FC3C41C8339DFE79E18EC26D4979F82029162 | |||
| 6384 | powershell.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:2D0F6D7A03834156F1047B08C5D587A5 | SHA256:6CFCC673281EFD43FD576A3FBB9B9288760DAC7E63869B51E141B8E24385C0C9 | |||
| 2672 | OpenWith.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Explorer\thumbcache_16.db | binary | |
MD5:419A089E66B9E18ADA06C459B000CB4D | SHA256:C48E42E9AB4E25B92C43A7B0416D463B9FF7C69541E4623A39513BC98085F424 | |||
| 2672 | OpenWith.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Explorer\iconcache_idx.db | binary | |
MD5:3710BB5F5D2113999DCFB38073ABBF23 | SHA256:3F9EF843315549134459D439593D945A7936D31424351DBD32061449C3DB8EEA | |||
| 2672 | OpenWith.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Explorer\iconcache_16.db | binary | |
MD5:419A089E66B9E18ADA06C459B000CB4D | SHA256:C48E42E9AB4E25B92C43A7B0416D463B9FF7C69541E4623A39513BC98085F424 | |||
| 2672 | OpenWith.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Explorer\thumbcache_32.db | binary | |
MD5:60476A101249AEDFF09A43E047040191 | SHA256:35BC77A06BFDDE8C8F3A474C88520262B88C7B8992EE6B2D5CF41DDDC77A83FB | |||
| 2672 | OpenWith.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Explorer\iconcache_32.db | binary | |
MD5:54CD83F93EBFD2D11588E9CC9B1A7A51 | SHA256:96F4B3E7AA32697695B0E816EF0F676F020EF9E6DC5D74409209D15947AA52CE | |||
| 6384 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_fkh1rb1h.drr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2672 | OpenWith.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Explorer\thumbcache_idx.db | binary | |
MD5:7A00F6804FBEE4298EFC896075173882 | SHA256:3C0EB1FF4199D830398606076A12459EC0E3B516DEAA70A6AE0E5DDBB5079946 | |||
| 2672 | OpenWith.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Explorer\thumbcache_768.db | binary | |
MD5:D192F7C343602D02E3E020807707006E | SHA256:BB4D233C90BDBEE6EF83E40BFF1149EA884EFA790B3BEF496164DF6F90297C48 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
55
DNS requests
53
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6440 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6384 | powershell.exe | GET | 200 | 172.67.74.152:80 | http://api.ipify.org/ | unknown | — | — | malicious |
7124 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7124 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3092 | chrome.exe | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | unknown | — | — | whitelisted |
3092 | chrome.exe | GET | 200 | 74.125.162.198:80 | http://r1---sn-4g5ednds.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&met=1735939526,&mh=e_&mip=181.214.173.40&mm=28&mn=sn-4g5ednds&ms=nvh&mt=1735939216&mv=m&mvi=1&pl=24&rms=nvh,nvh&shardbypass=sd&smhost=r4---sn-4g5edndd.gvt1.com | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6072 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
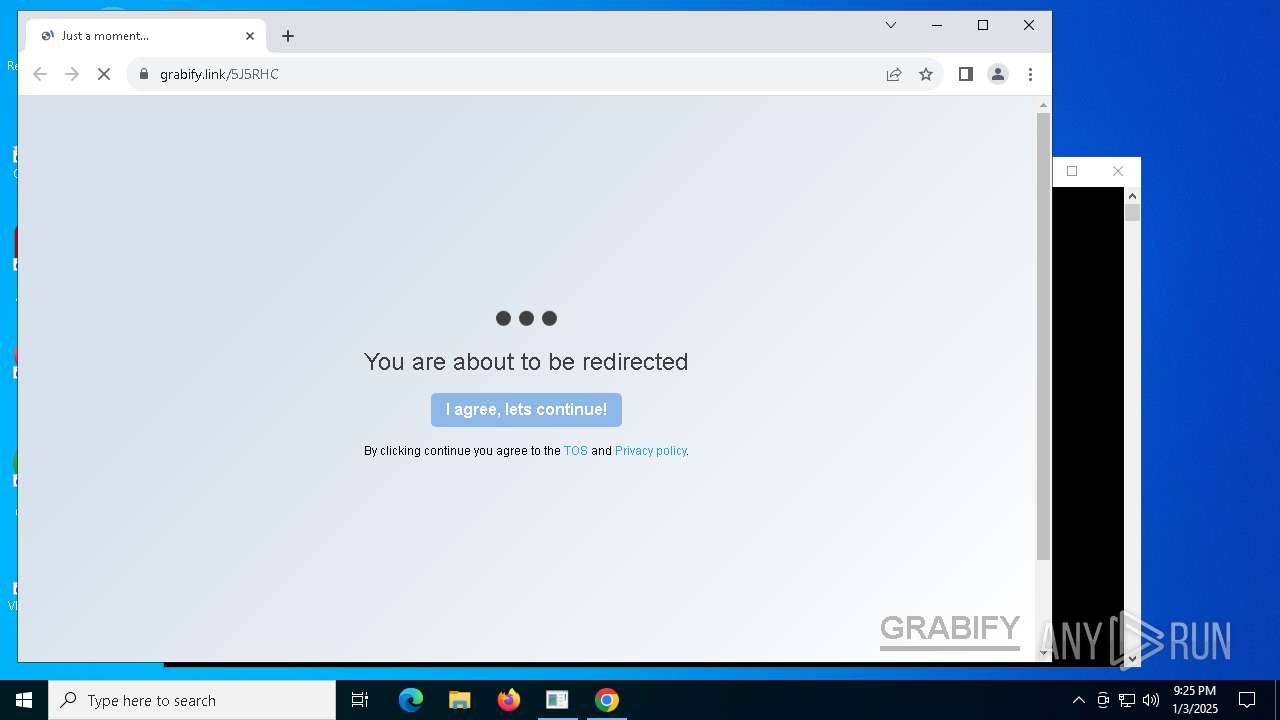
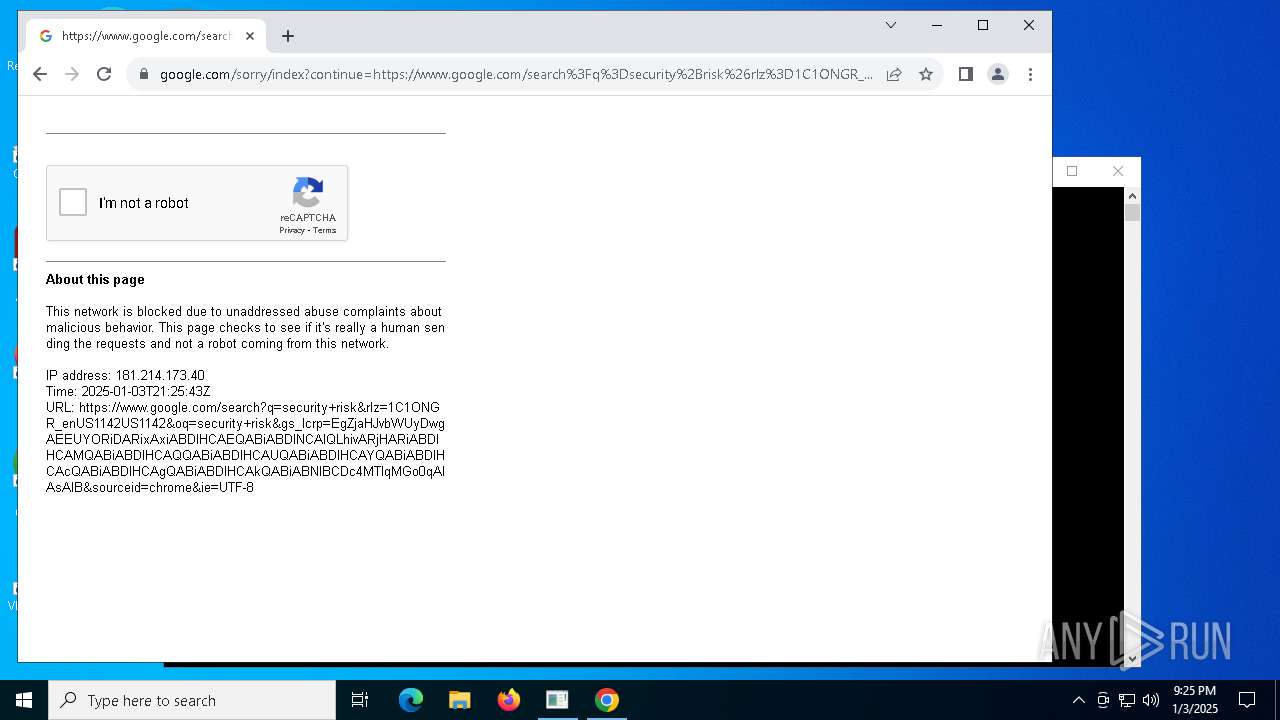
— | — | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
6384 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup api.ipify.org |
6384 | powershell.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
6384 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
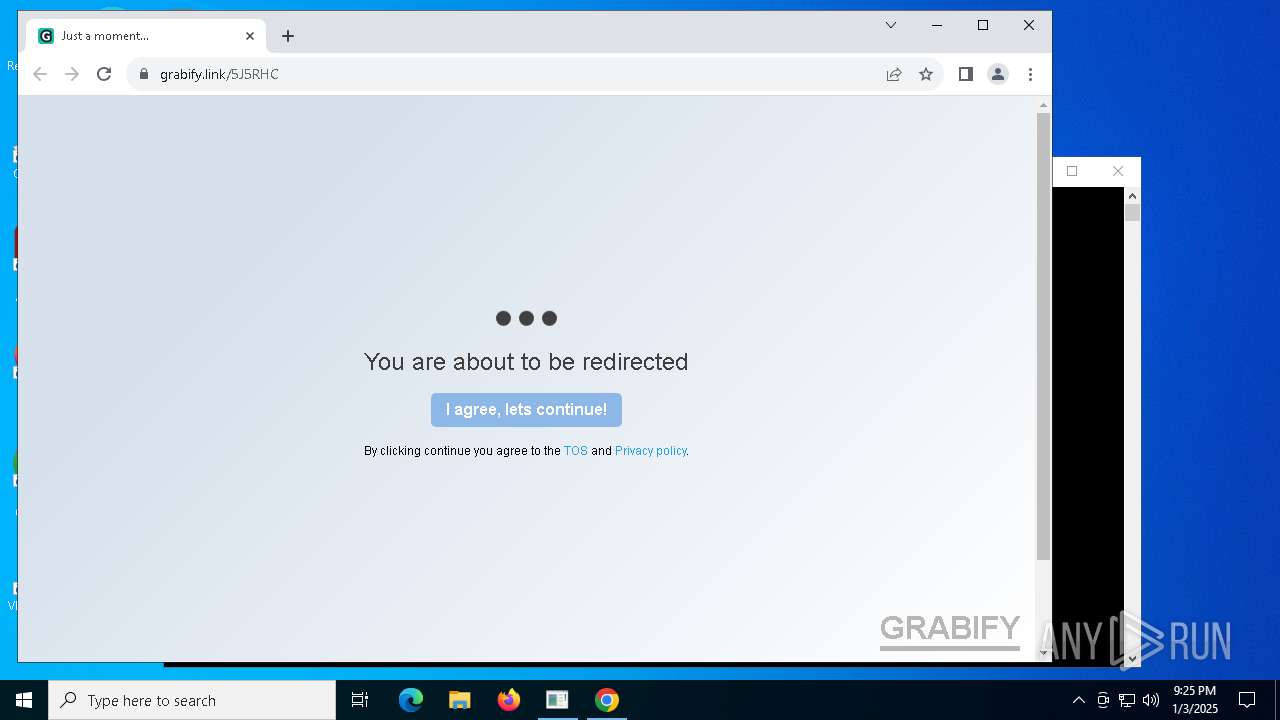
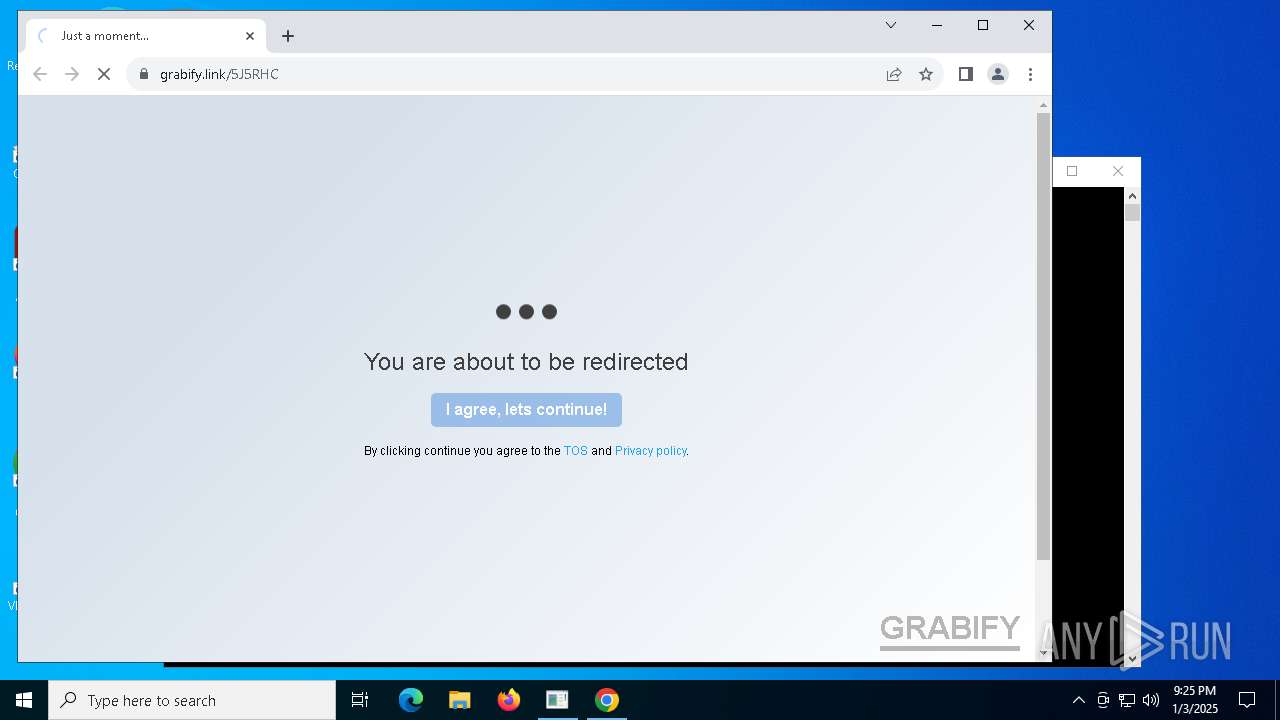
3092 | chrome.exe | Potentially Bad Traffic | ET INFO Observed IP Tracking Domain (grabify .link in TLS SNI) |
3092 | chrome.exe | Potentially Bad Traffic | ET INFO Observed IP Tracking Domain (grabify .link in TLS SNI) |
6384 | powershell.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
Process | Message |
|---|---|
chrome.exe | [0103/212524.673:ERROR:crash_report_database_win.cc(613)] CreateDirectory C:\Users\Administrator\AppData\Local\Google\Chrome\User Data\Crashpad: The system cannot find the path specified. (0x3)
|