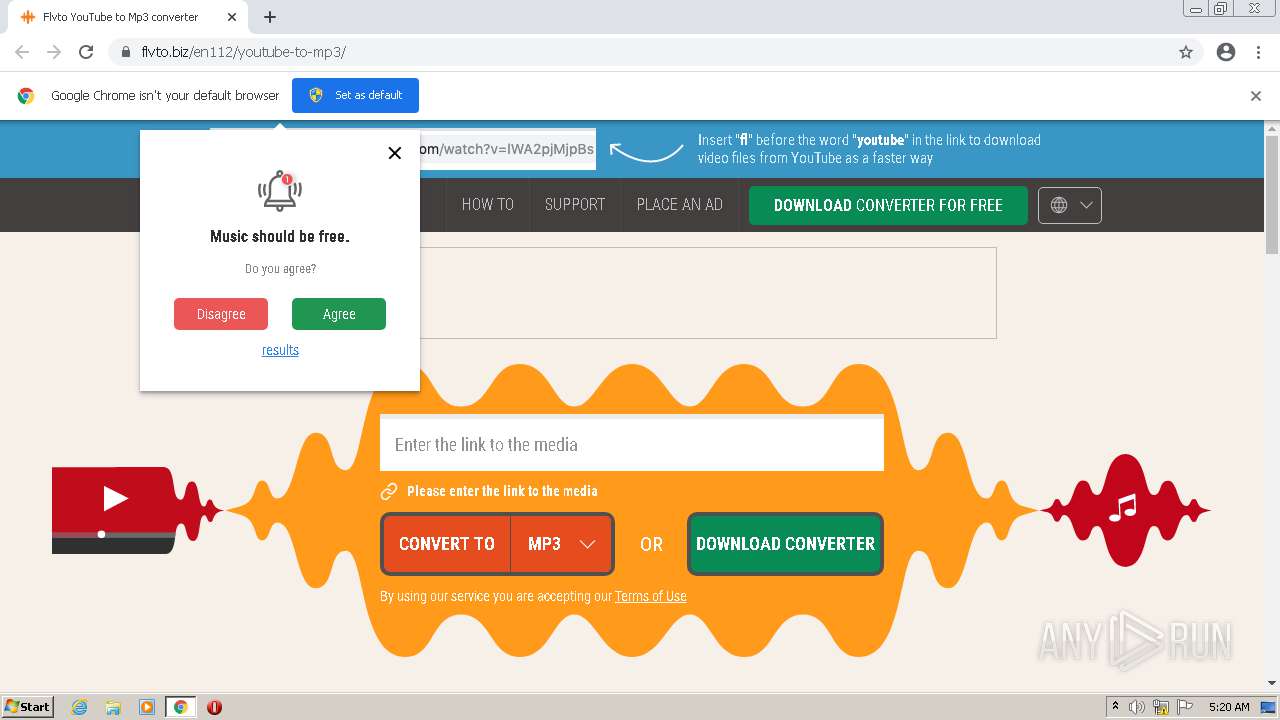
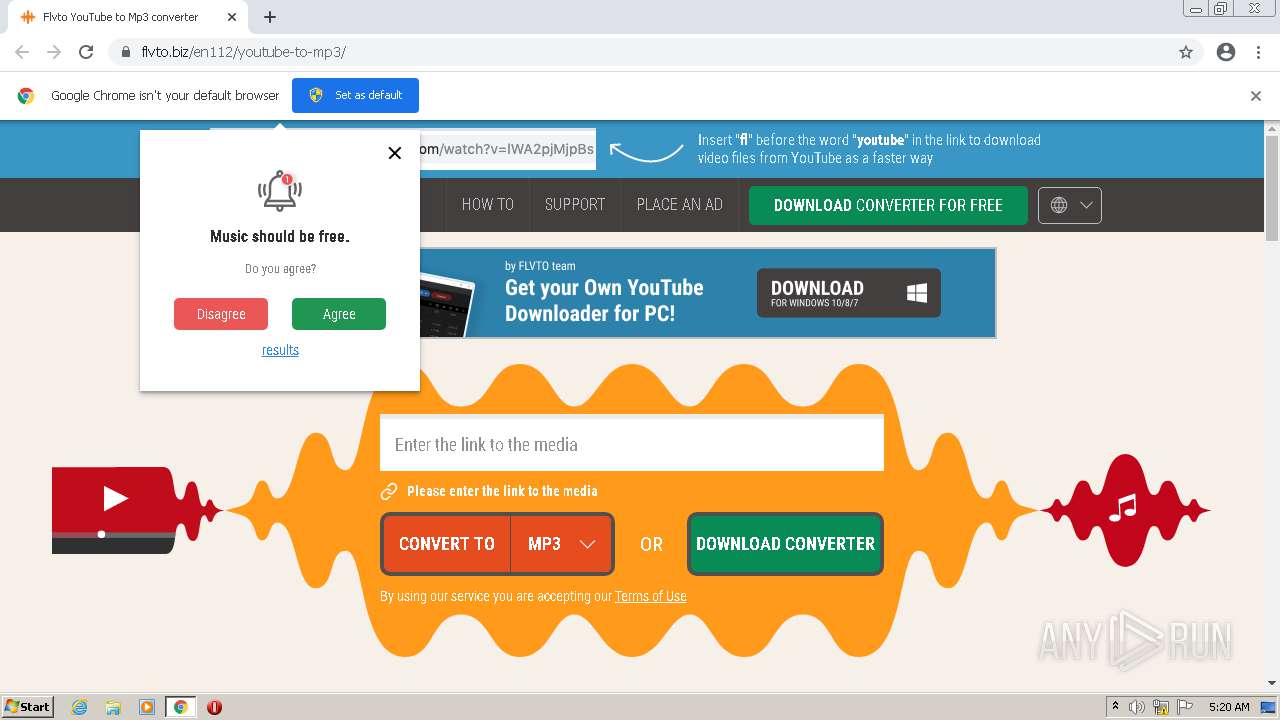
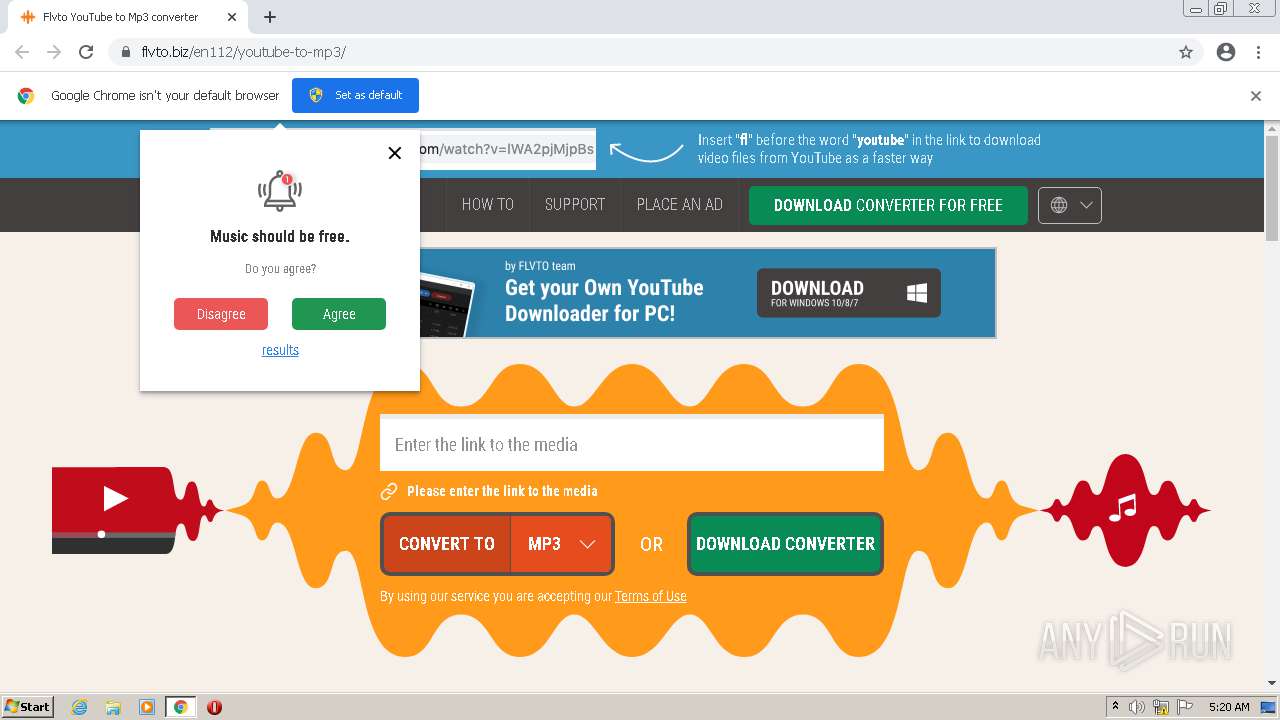
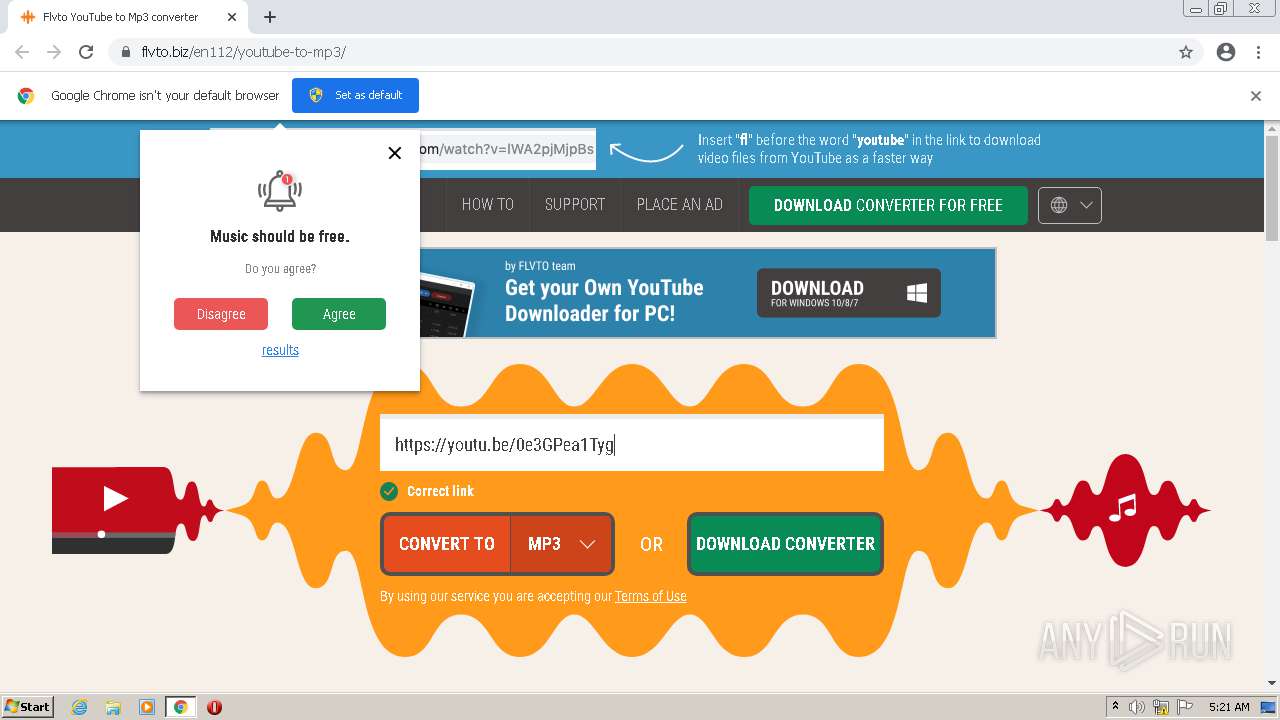
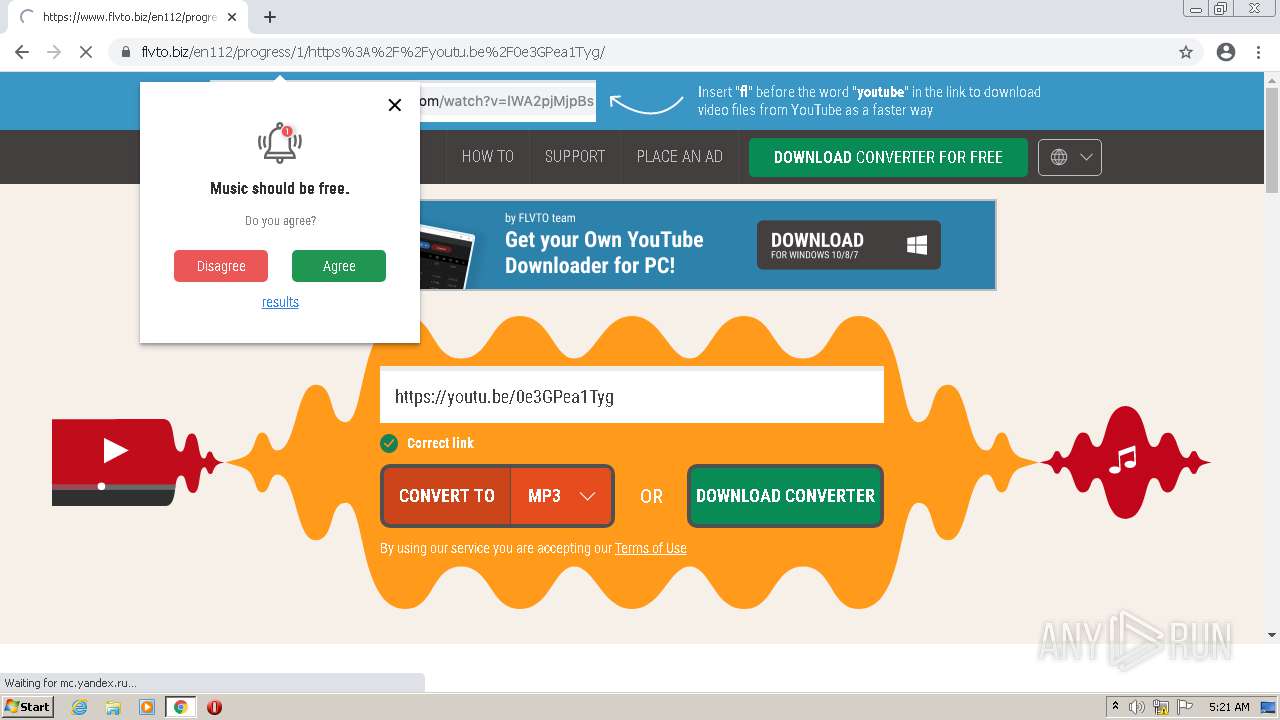
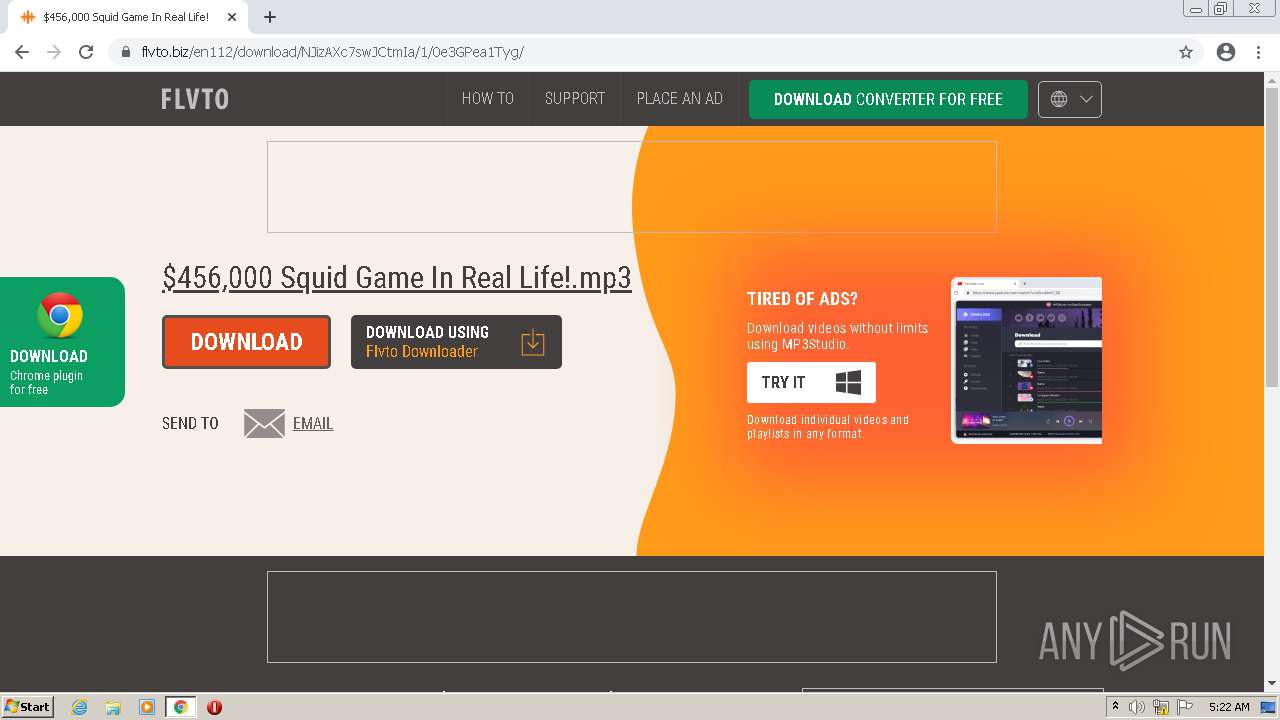
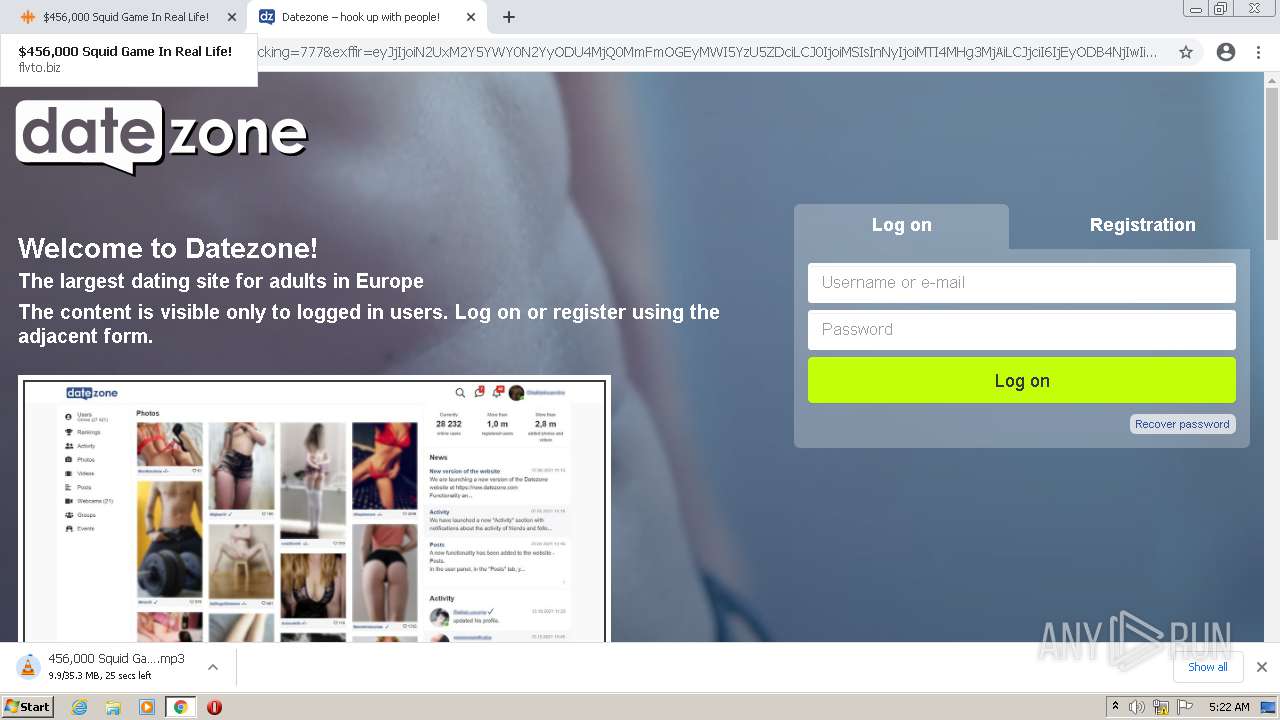
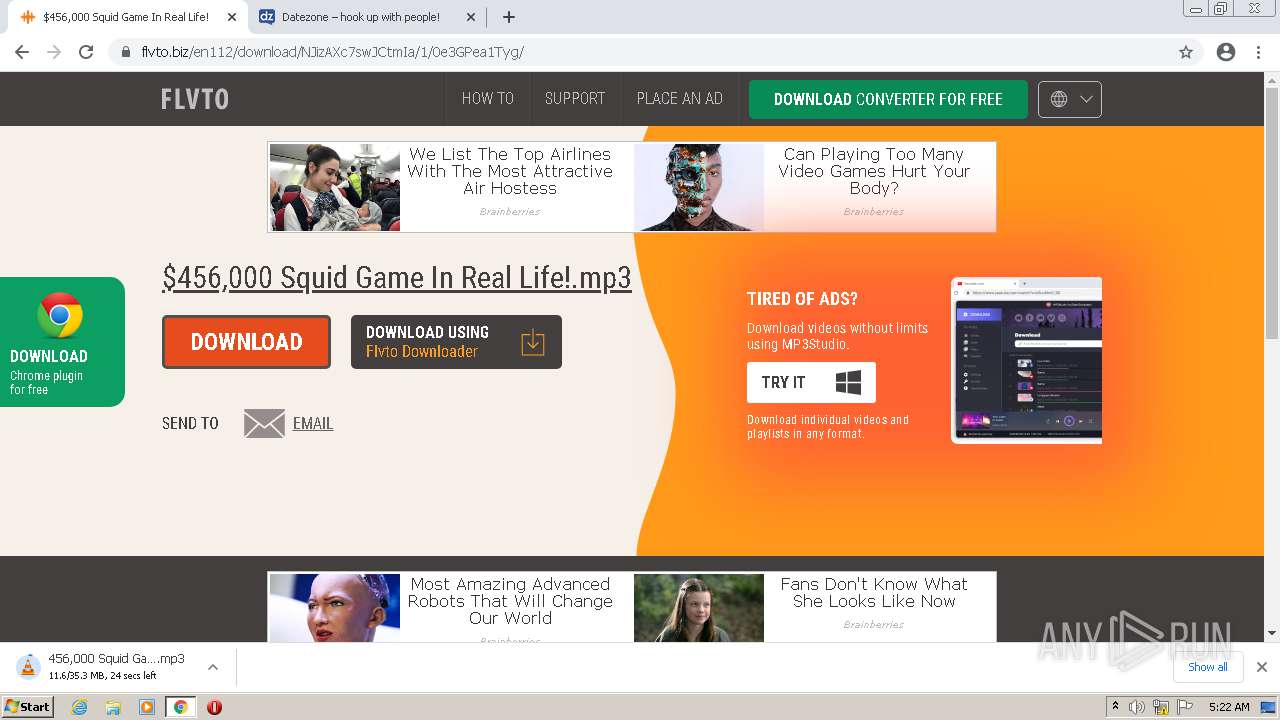
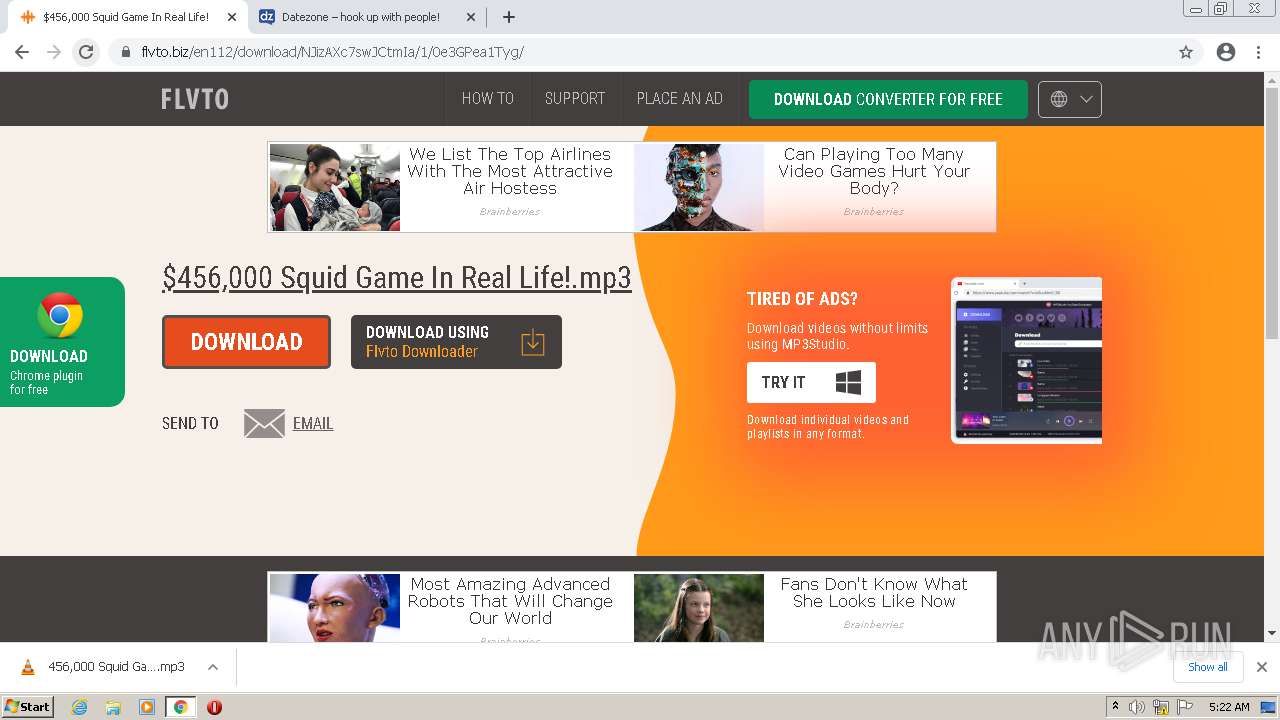
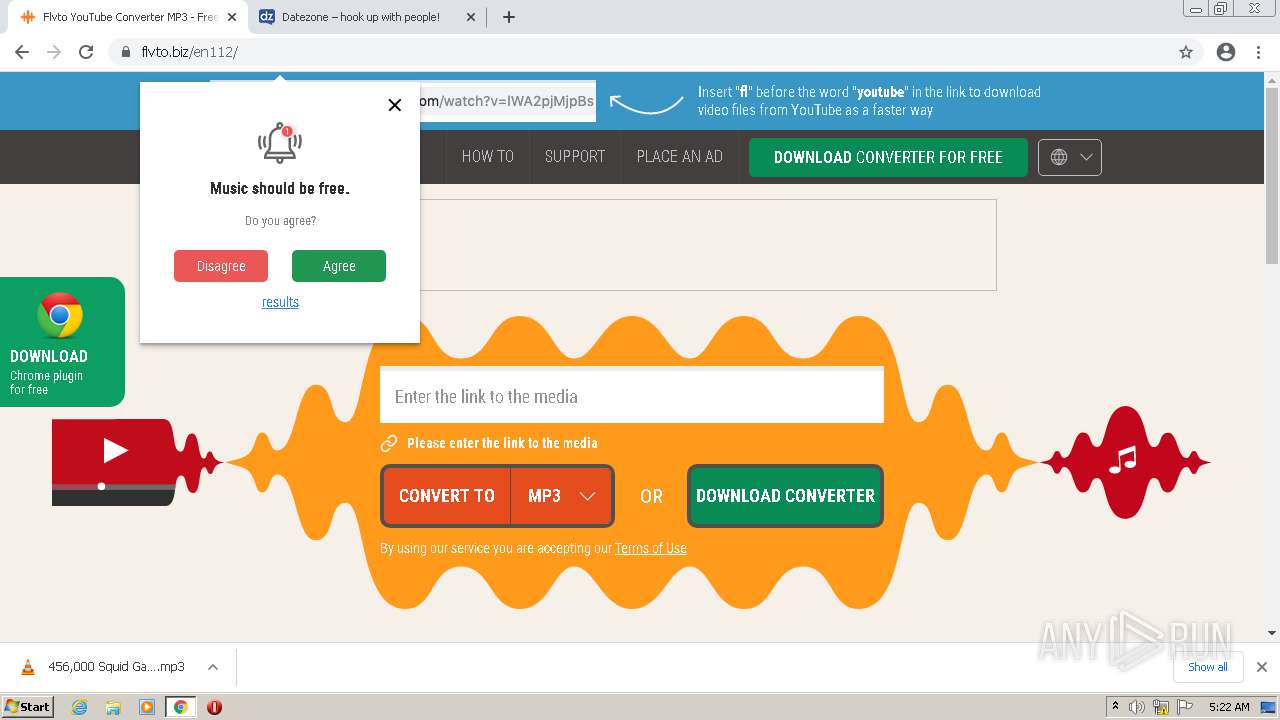
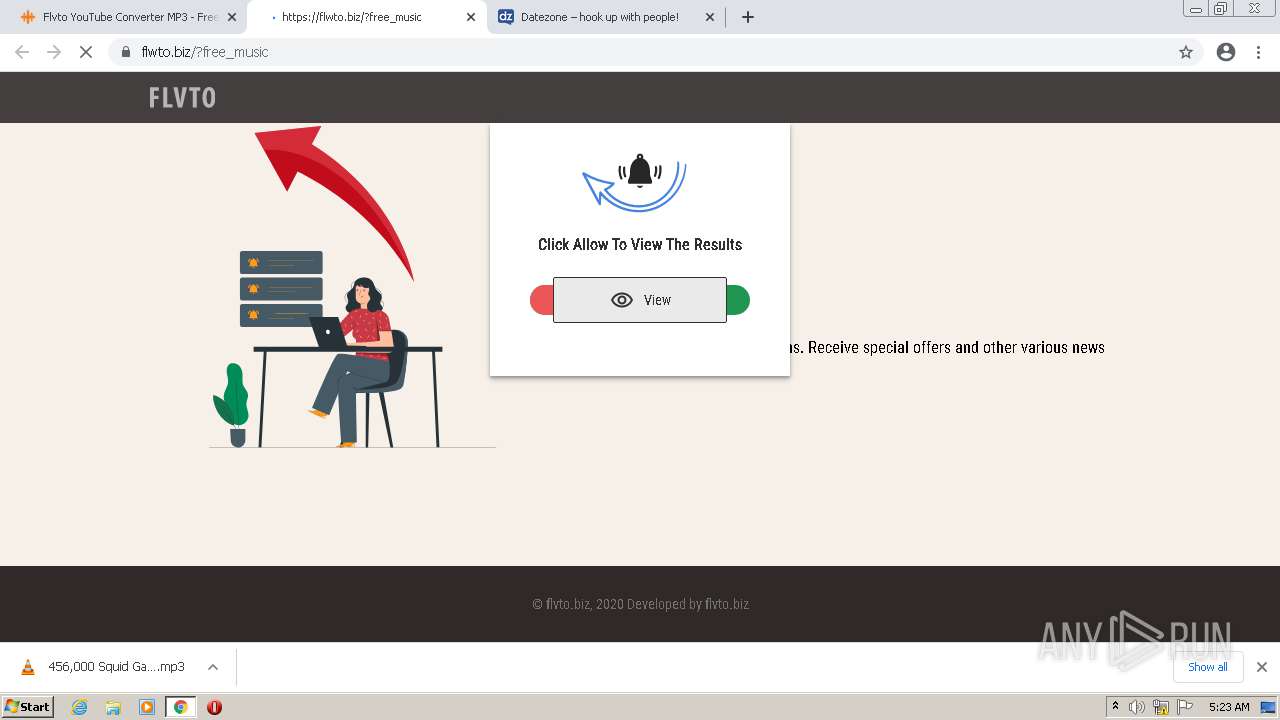
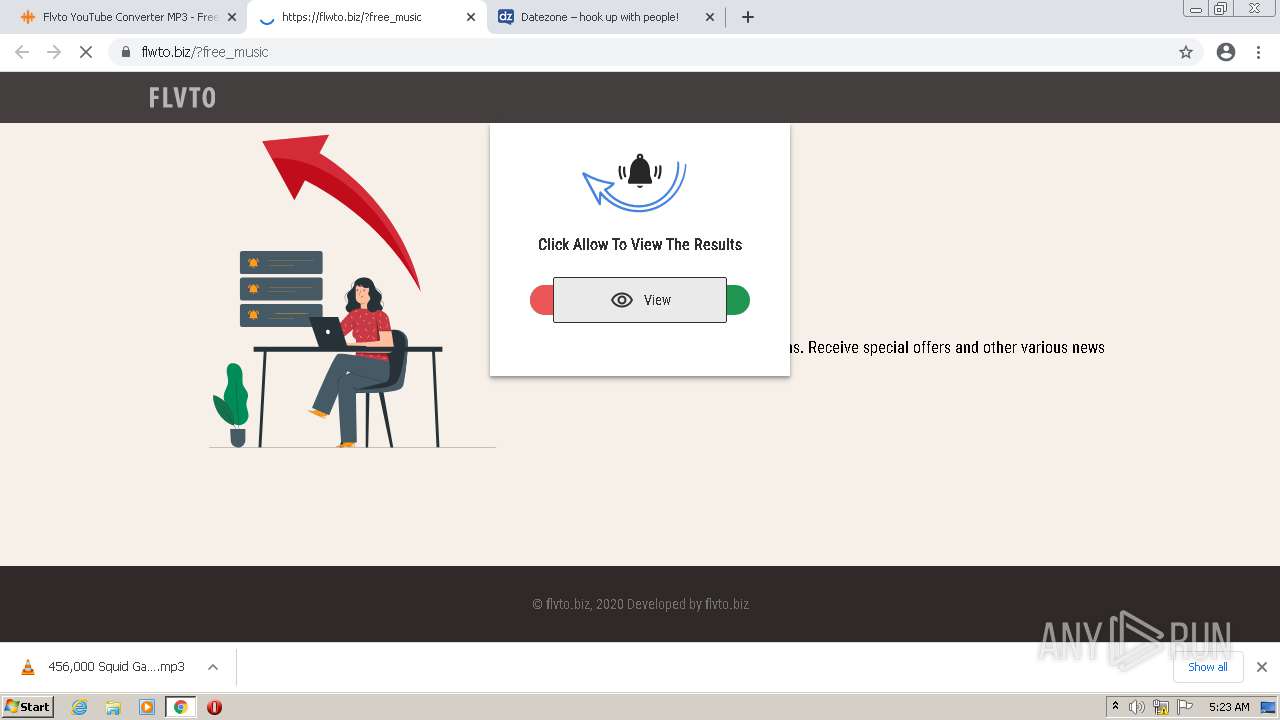
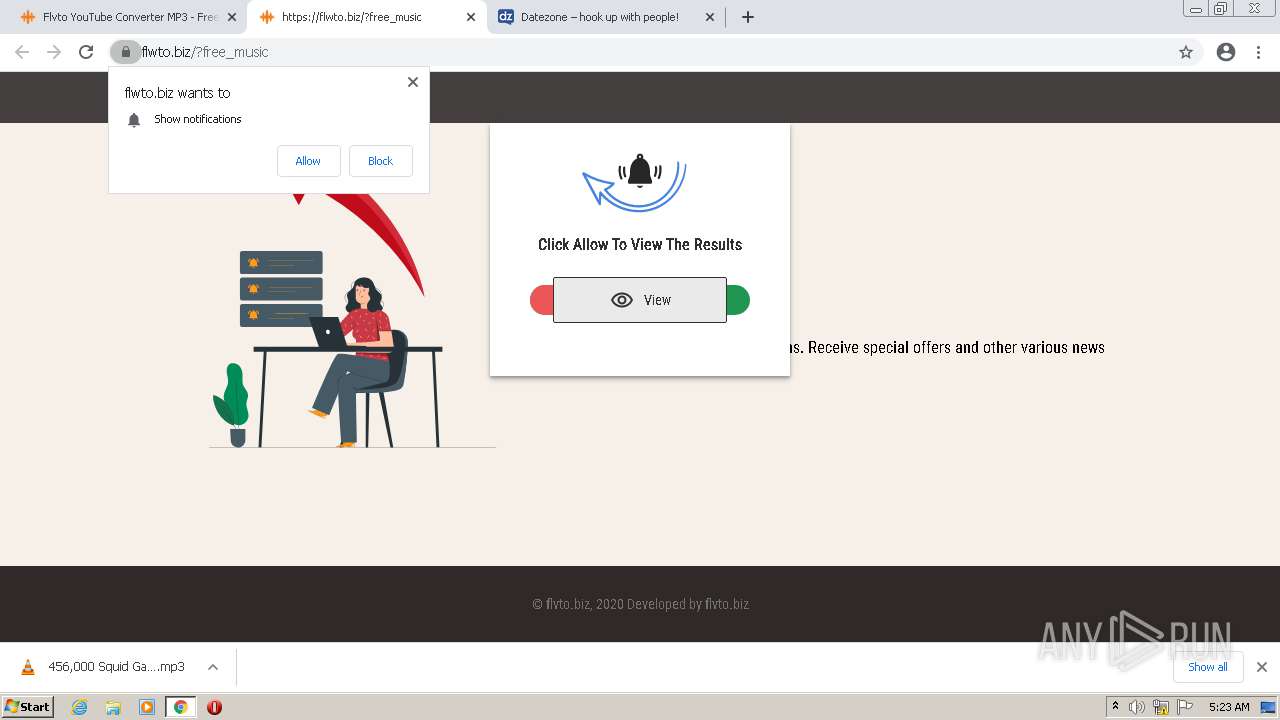
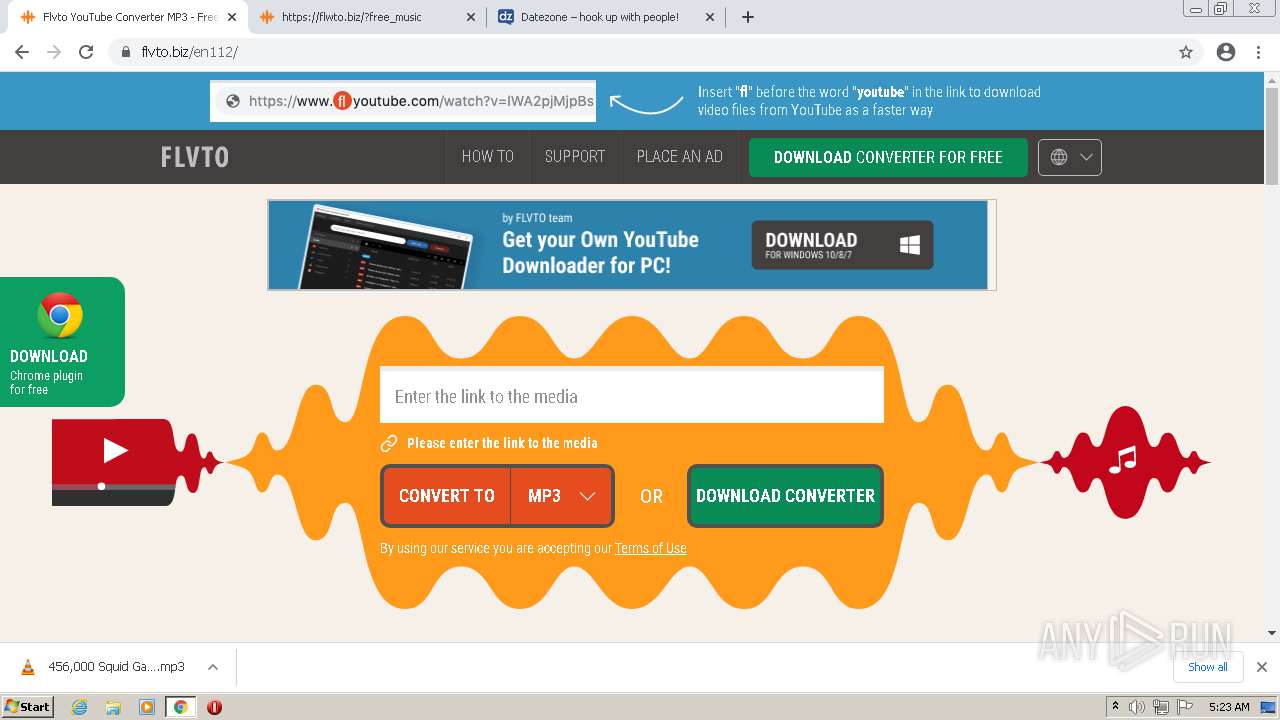
| URL: | https://www.flvto.biz/en112/youtube-to-mp3/ |
| Full analysis: | https://app.any.run/tasks/68643a38-b9eb-44bf-91a5-25f6af52f32a |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2021, 05:20:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6EB1AC3B05104DF22FF1E988593836AD |
| SHA1: | F931703FC2882C9E914828CAD6376D558B118372 |
| SHA256: | DDDBB2DD1D1B3B774D975D1FF9935F7B0D9E5E8EF90D6F4FC5CBE93AA700F6E9 |
| SSDEEP: | 3:N8DSLVTIAjQHts1VWK:2OL59sH21VN |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2376)
SUSPICIOUS
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2376)
Executable content was dropped or overwritten
- chrome.exe (PID: 2376)
INFO
Application launched itself
- chrome.exe (PID: 3696)
Reads the computer name
- chrome.exe (PID: 3696)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 560)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 736)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 2704)
Reads the hosts file
- chrome.exe (PID: 3696)
- chrome.exe (PID: 3788)
Checks supported languages
- chrome.exe (PID: 2360)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 560)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 736)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 636)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 1284)
Reads settings of System Certificates
- chrome.exe (PID: 3788)
Reads the date of Windows installation
- chrome.exe (PID: 2704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
31
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3792 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
14 540
Read events
14 390
Write events
145
Delete events
5
Modification events
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1
Suspicious files
68
Text files
183
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61A06E8F-E70.pma | — | |
MD5:— | SHA256:— | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dac7e860-2731-4594-b60a-38ae1b7d4d12.tmp | text | |
MD5:— | SHA256:— | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF11584e.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF115a62.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF11585e.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF115c36.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7eda0cb4-6391-482f-aba5-5a6a37f57a70.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
119
DNS requests
65
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | HEAD | 200 | 194.9.24.78:80 | http://r3---sn-5uh5o-f5f6.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=188.212.135.7&mm=28&mn=sn-5uh5o-f5f6&ms=nvh&mt=1637903785&mv=m&mvi=3&pl=24&shardbypass=yes | PL | — | — | whitelisted |
876 | svchost.exe | HEAD | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
876 | svchost.exe | GET | 206 | 194.9.24.78:80 | http://r3---sn-5uh5o-f5f6.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=188.212.135.7&mm=28&mn=sn-5uh5o-f5f6&ms=nvh&mt=1637903785&mv=m&mvi=3&pcm2cms=yes&pl=24&shardbypass=yes | PL | binary | 9.51 Kb | whitelisted |
876 | svchost.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 544 b | whitelisted |
876 | svchost.exe | GET | 206 | 194.9.24.78:80 | http://r3---sn-5uh5o-f5f6.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=188.212.135.7&mm=28&mn=sn-5uh5o-f5f6&ms=nvh&mt=1637903785&mv=m&mvi=3&pl=24&shardbypass=yes | PL | binary | 5.63 Kb | whitelisted |
876 | svchost.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 560 b | whitelisted |
876 | svchost.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 560 b | whitelisted |
876 | svchost.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 544 b | whitelisted |
876 | svchost.exe | GET | 206 | 194.9.24.78:80 | http://r3---sn-5uh5o-f5f6.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=188.212.135.7&mm=28&mn=sn-5uh5o-f5f6&ms=nvh&mt=1637903785&mv=m&mvi=3&pl=24&shardbypass=yes | PL | binary | 9.52 Kb | whitelisted |
876 | svchost.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 544 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3788 | chrome.exe | 142.251.39.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3788 | chrome.exe | 94.237.57.11:443 | www.flvto.biz | — | FI | unknown |
3788 | chrome.exe | 172.217.19.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3788 | chrome.exe | 195.181.175.49:443 | cdn.flvto.biz | Datacamp Limited | DE | suspicious |
— | — | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3788 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3788 | chrome.exe | 104.18.16.65:443 | jsc.adskeeper.com | Cloudflare Inc | US | suspicious |
— | — | 104.18.16.65:443 | jsc.adskeeper.com | Cloudflare Inc | US | suspicious |
876 | svchost.exe | 194.9.24.78:80 | r3---sn-5uh5o-f5f6.gvt1.com | ATM S.A. | PL | whitelisted |
3788 | chrome.exe | 185.59.220.17:443 | cdn.flvto.biz | Datacamp Limited | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.flvto.biz |
| malicious |
fonts.googleapis.com |
| whitelisted |
cdn.flvto.biz |
| malicious |
mc.yandex.ru |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
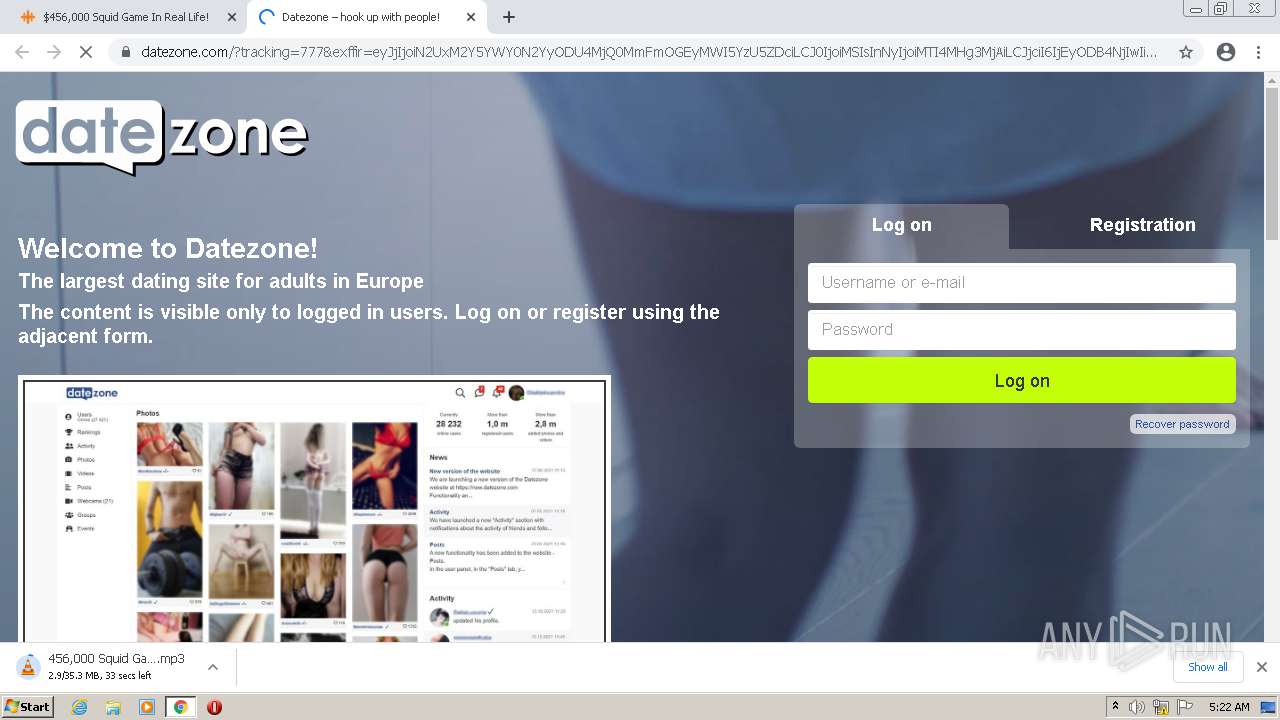
dl.zabanit.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |