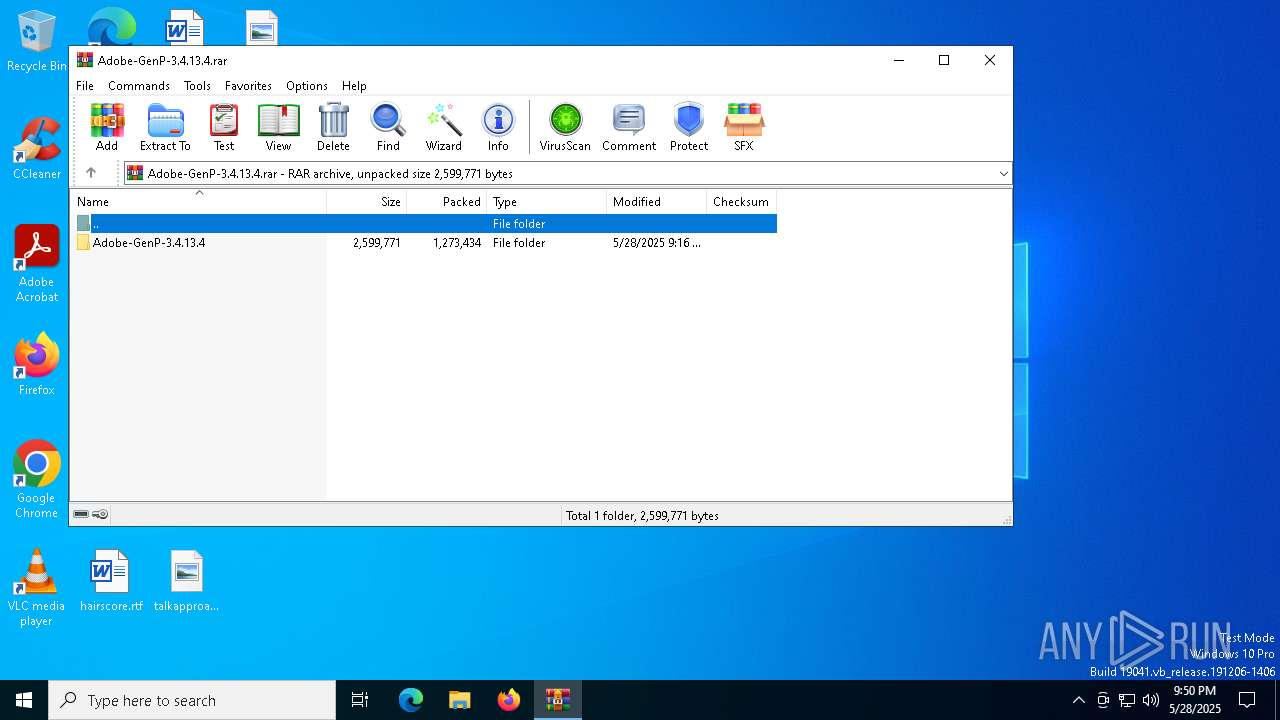
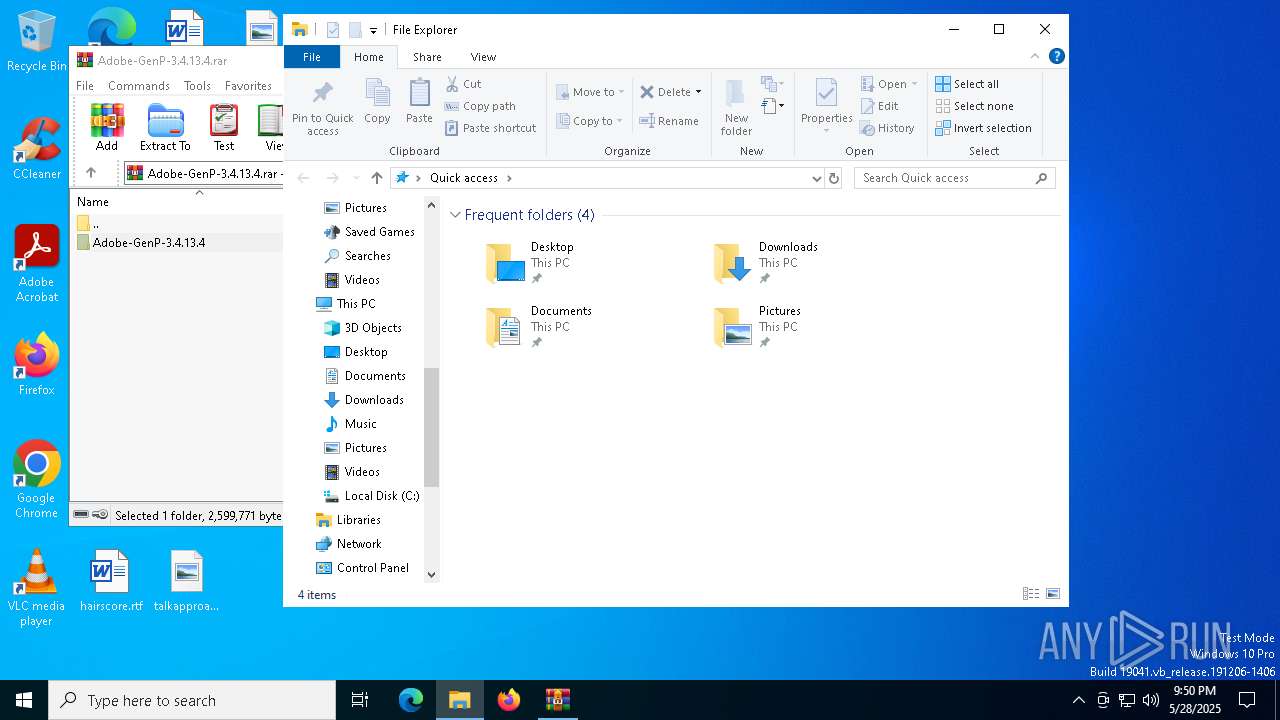
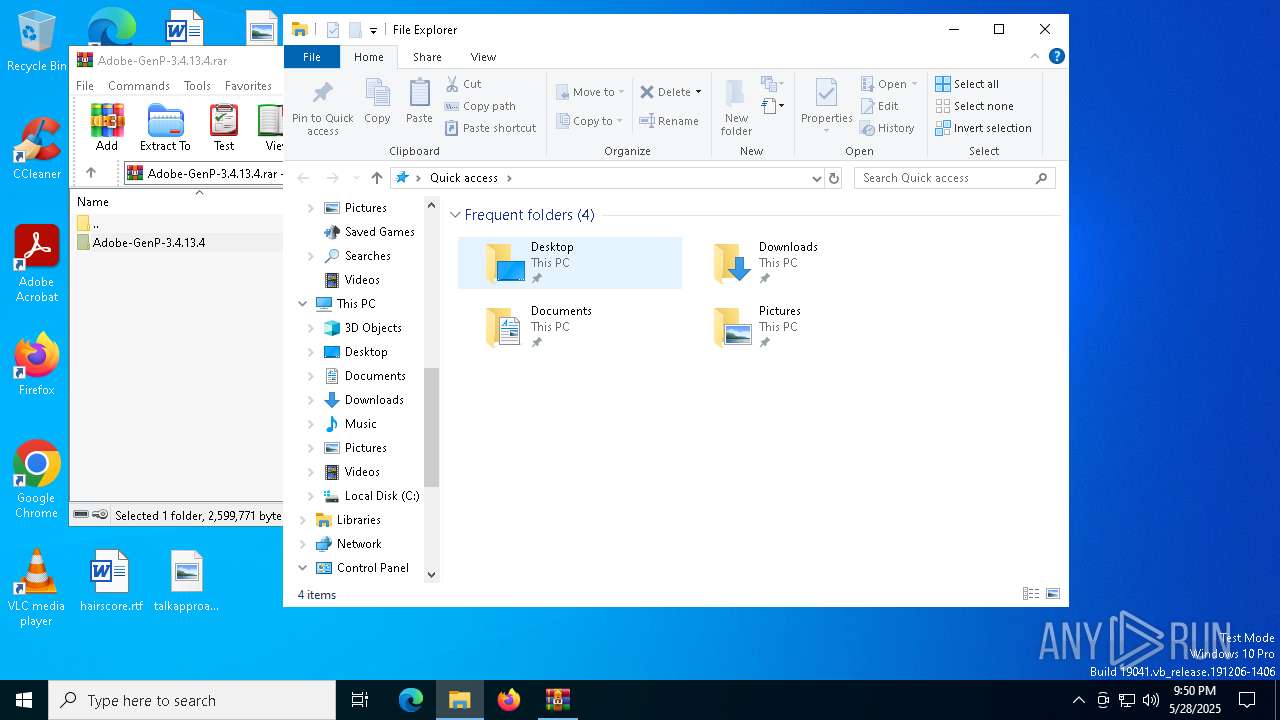
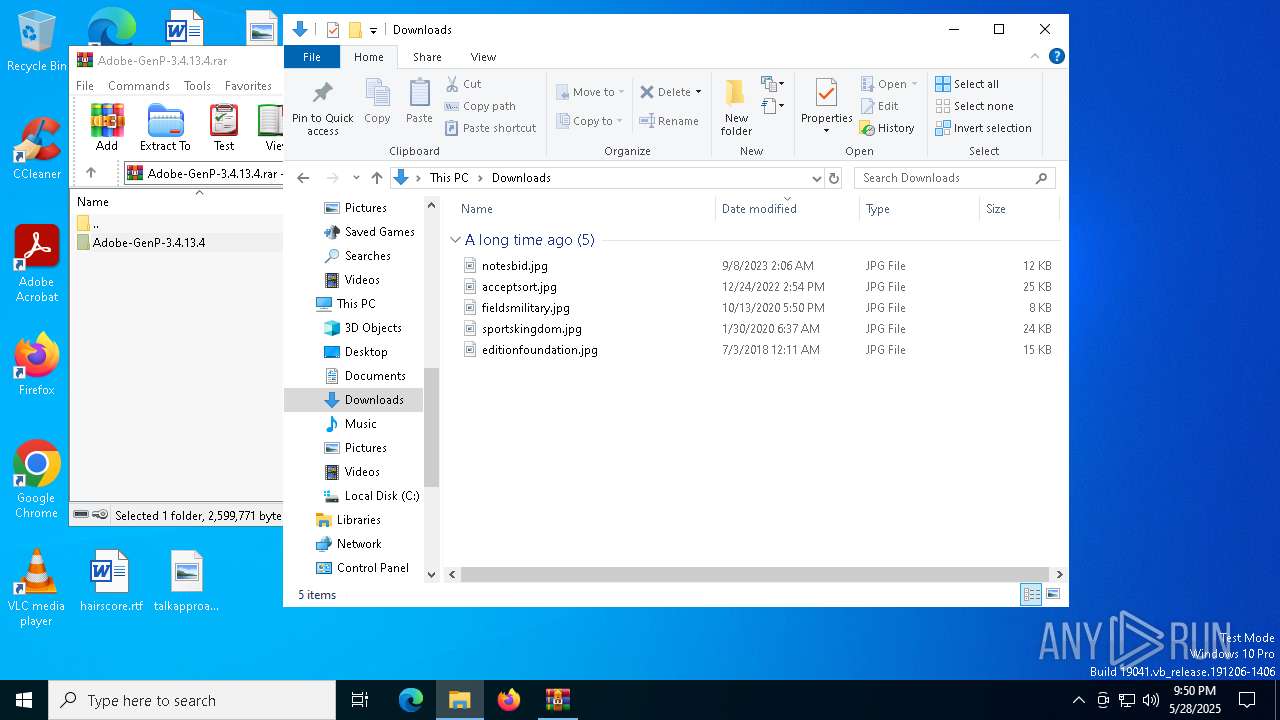
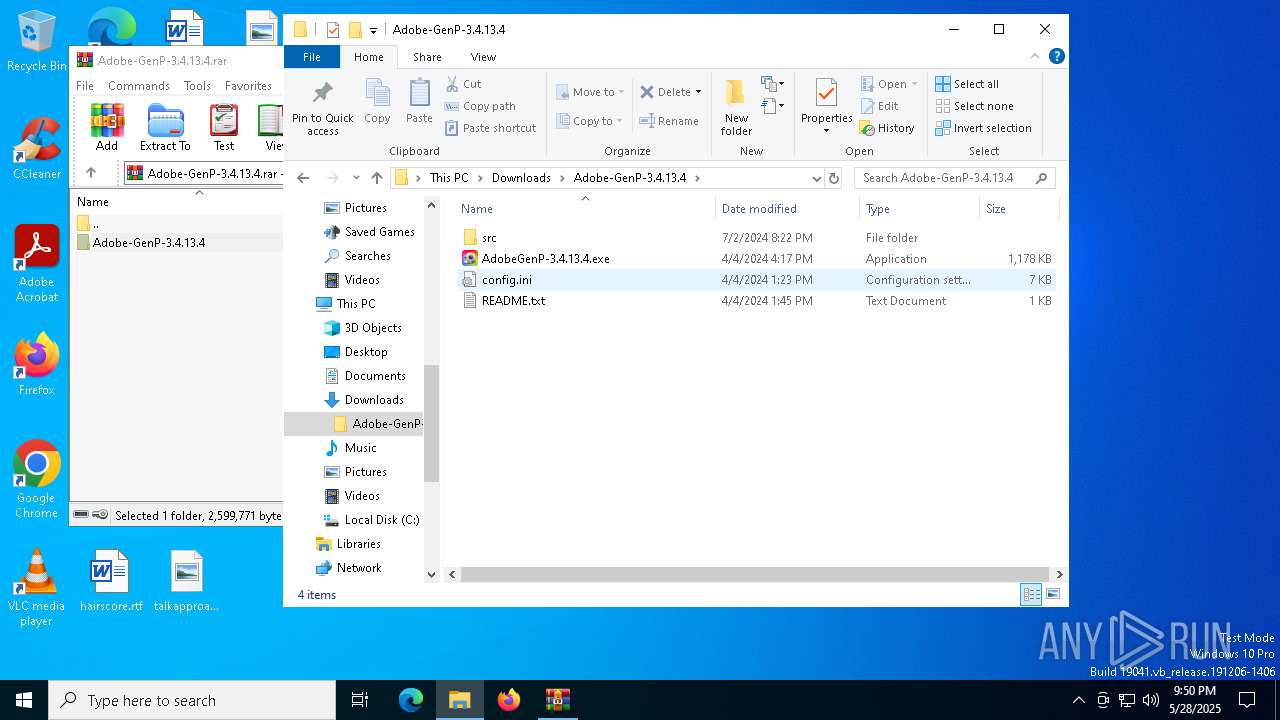
| File name: | Adobe-GenP-3.4.13.4.rar |
| Full analysis: | https://app.any.run/tasks/3dd75fc4-c65e-4c69-b580-b4dc795affa2 |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 21:50:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 1319004CEE9E19E1AF79F06F749F9664 |
| SHA1: | C0CE8E84C010C88203A2AEC4344ABE6F7DC2E52F |
| SHA256: | DDD21A6D7167D846C49F1E86F544505C35E67F611830BFF90237E514D273726A |
| SSDEEP: | 49152:FzDR4qBpsb0SLJ2L1E4NjSKFP5mGTvzj3If/Or6BJ/WcJqgY+zWdo6Opx+RPvQBu:hD2K20SOOZKfm4v33Ifmr6fucJS+zeoy |
MALICIOUS
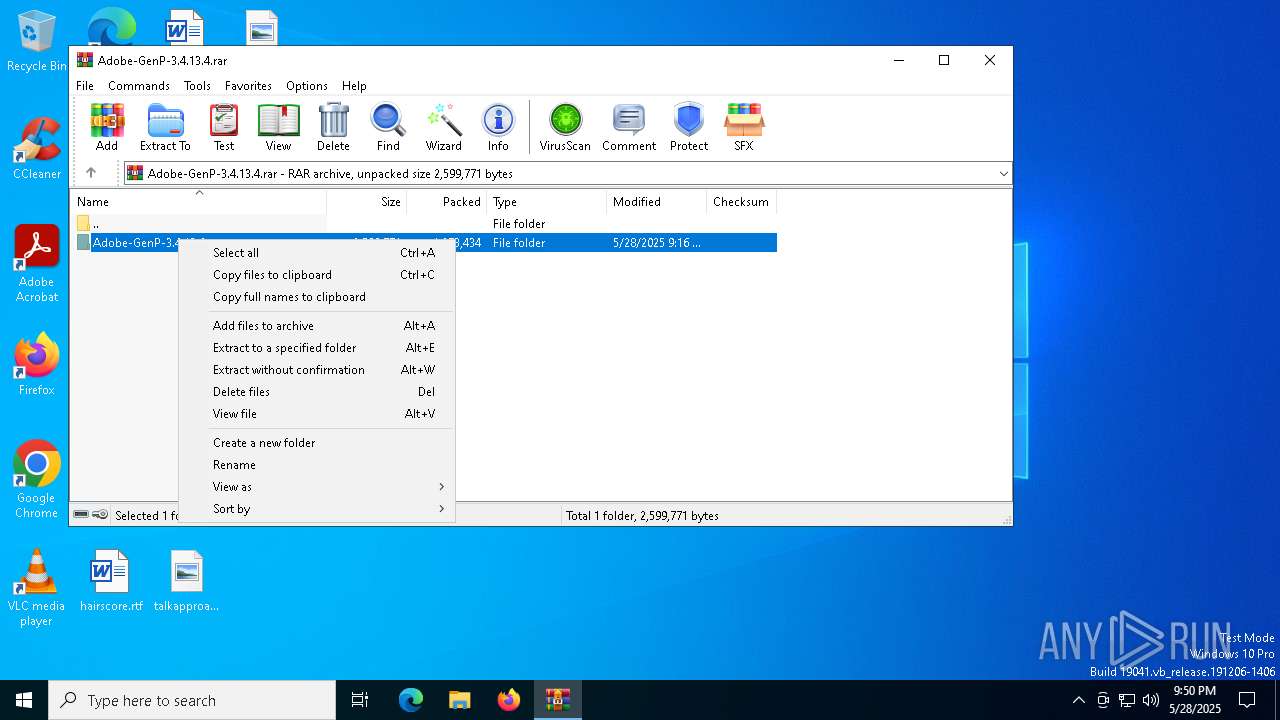
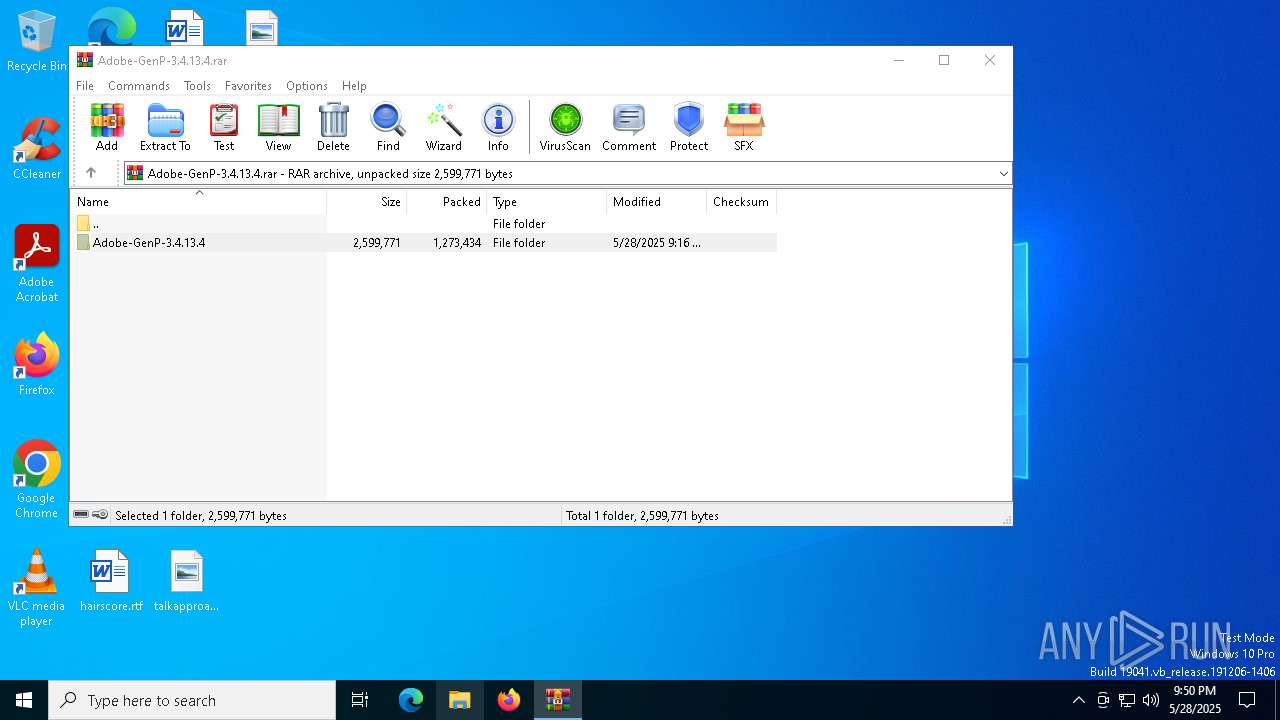
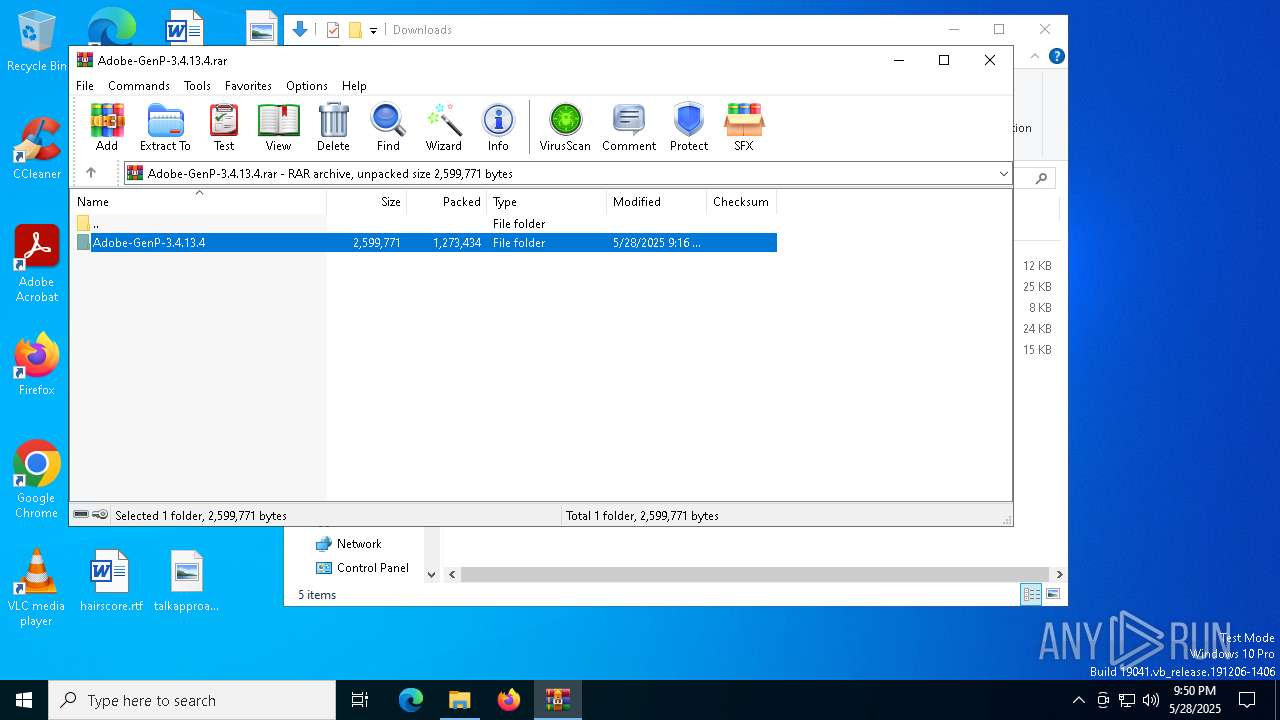
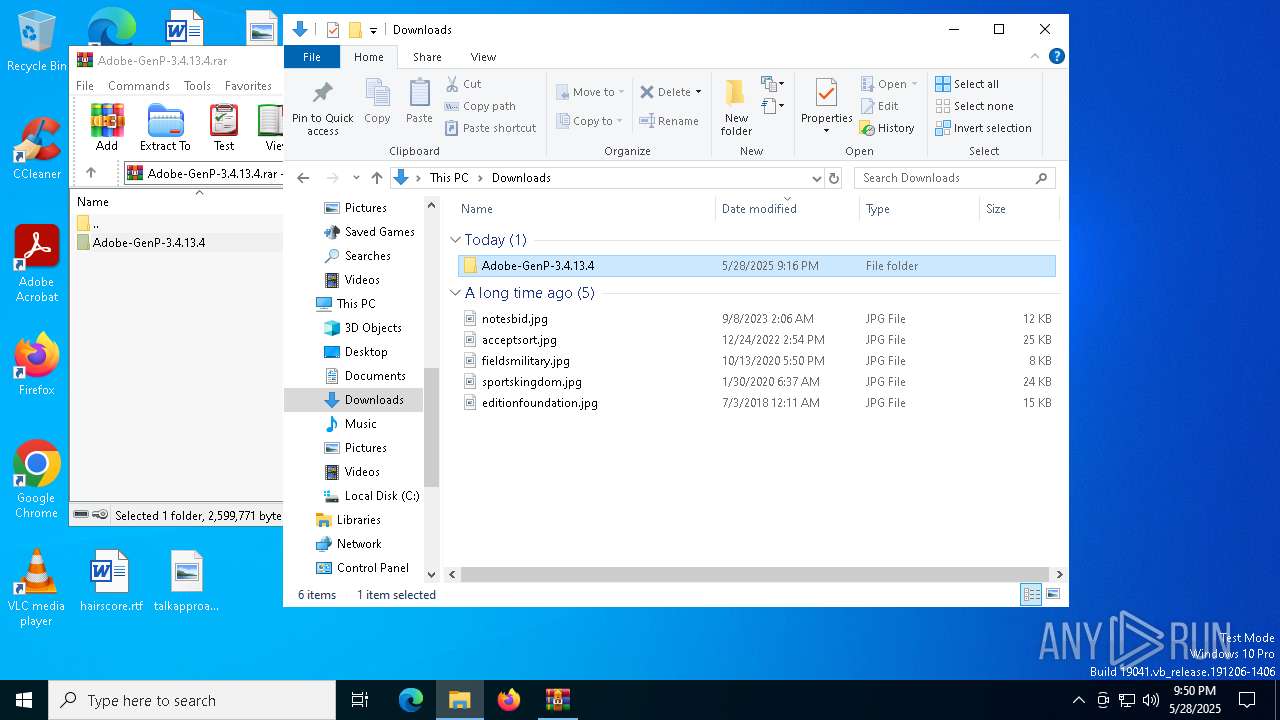
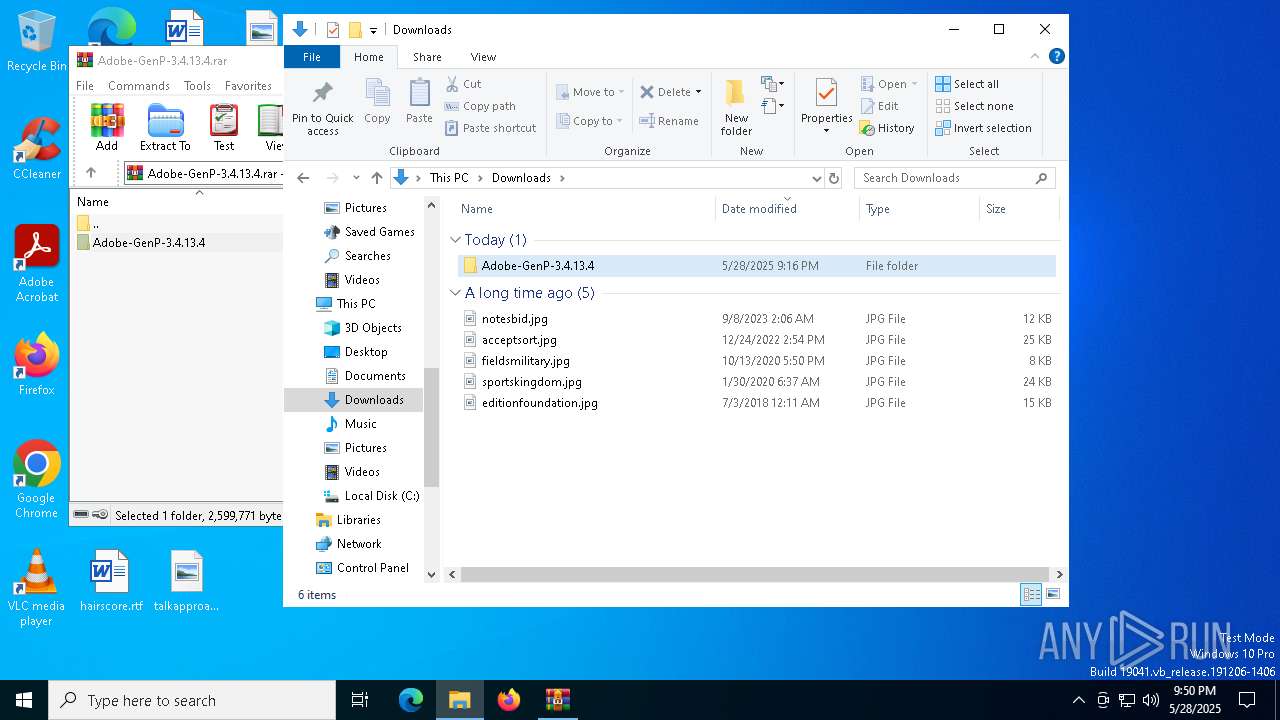
Generic archive extractor
- WinRAR.exe (PID: 7428)
SUSPICIOUS
Reads the date of Windows installation
- AdobeGenP-3.4.13.4.exe (PID: 8000)
Reads security settings of Internet Explorer
- AdobeGenP-3.4.13.4.exe (PID: 8000)
Found IP address in command line
- powershell.exe (PID: 2516)
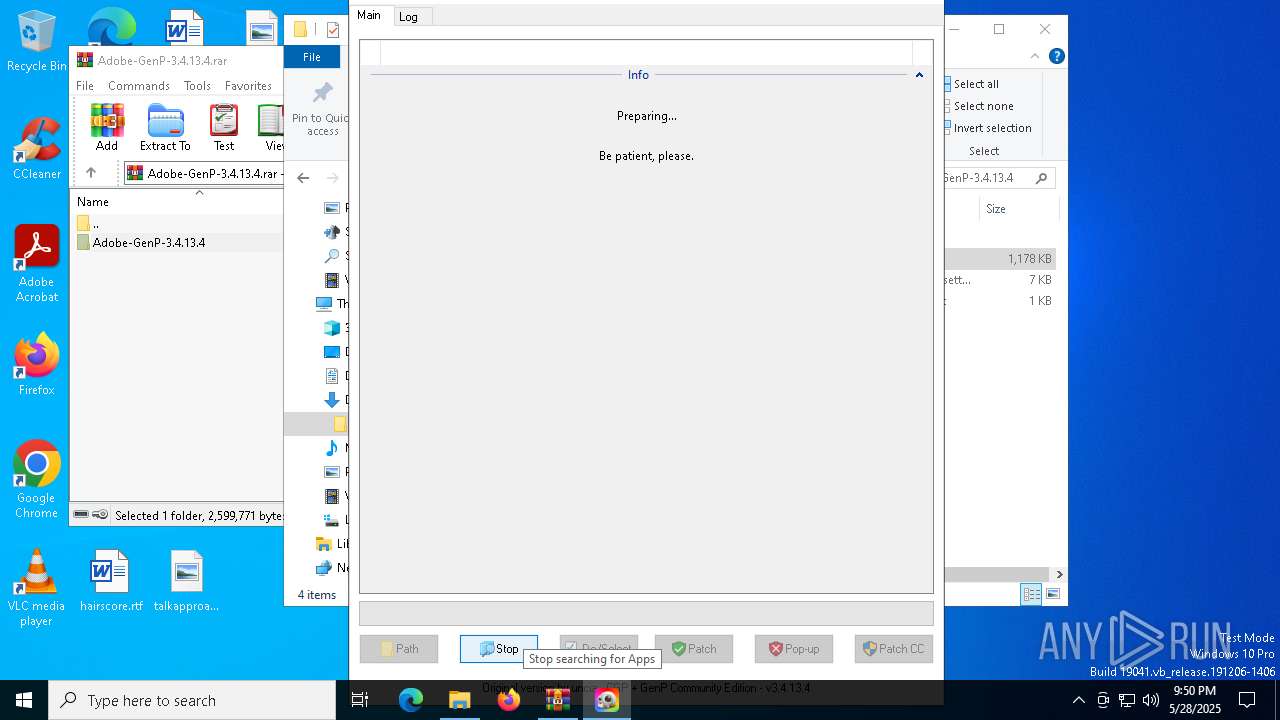
Application launched itself
- AdobeGenP-3.4.13.4.exe (PID: 8000)
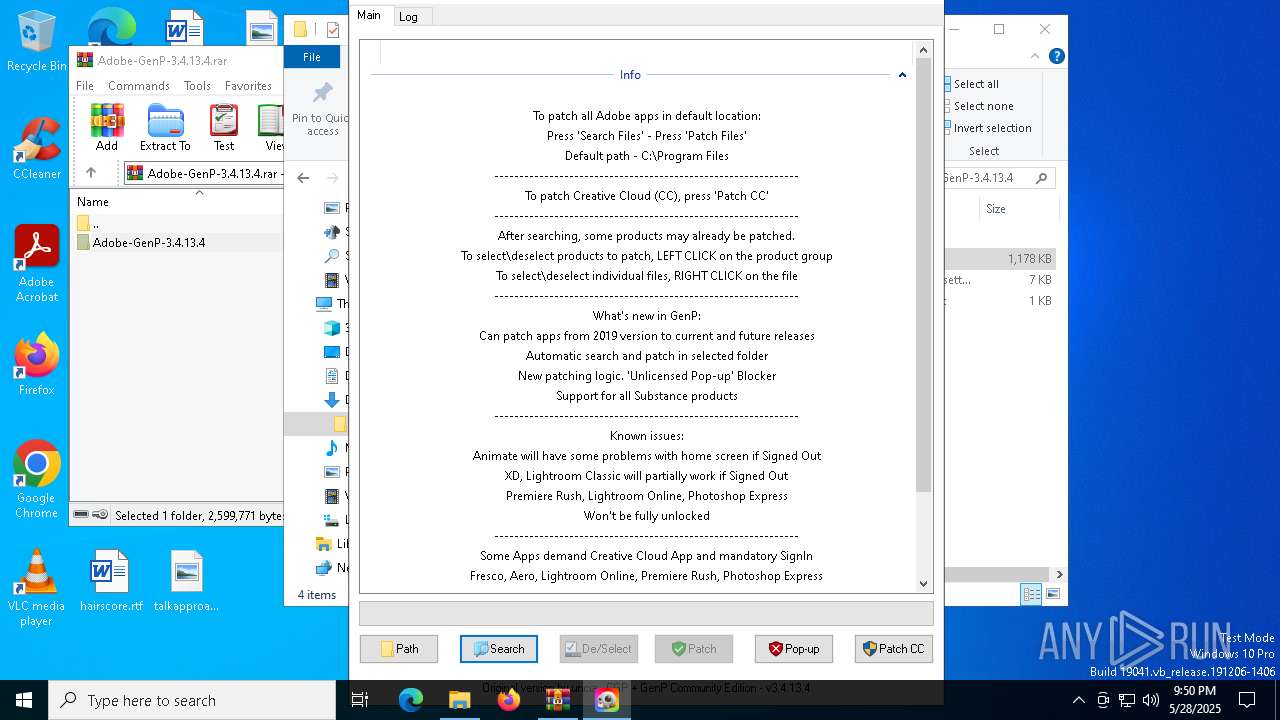
There is functionality for taking screenshot (YARA)
- AdobeGenP-3.4.13.4.exe (PID: 8072)
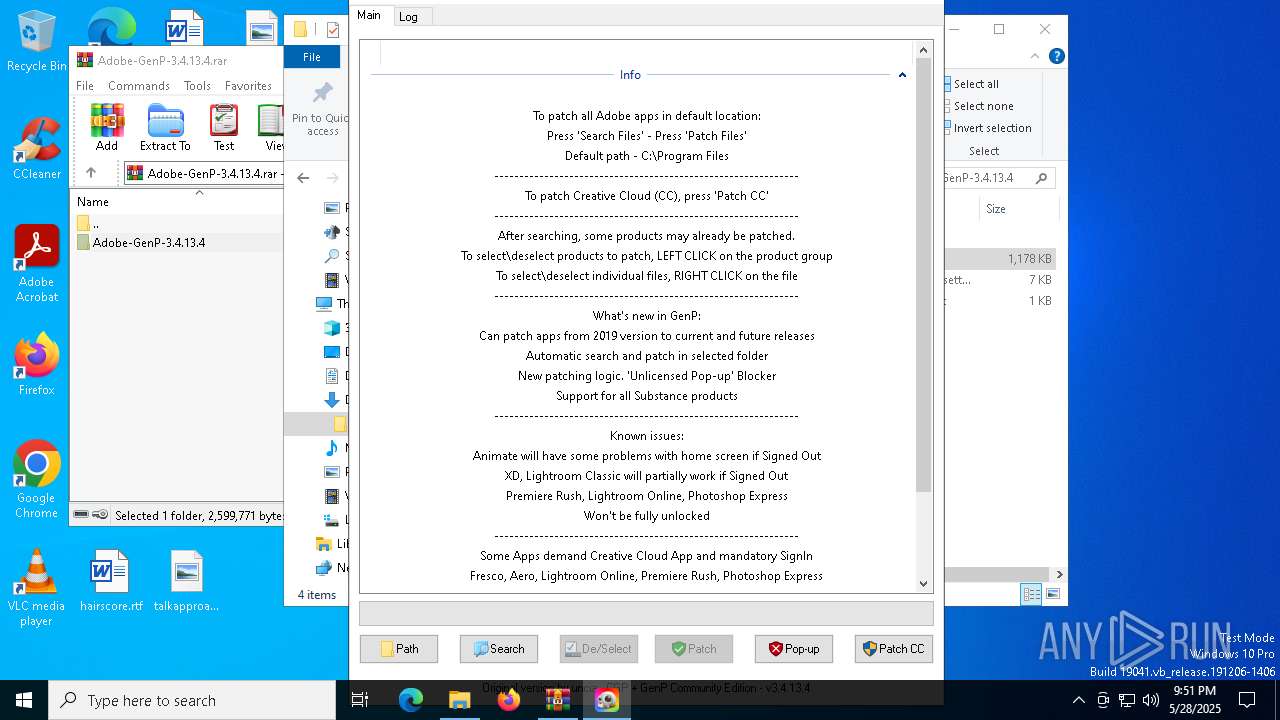
Starts POWERSHELL.EXE for commands execution
- AdobeGenP-3.4.13.4.exe (PID: 8072)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- AdobeGenP-3.4.13.4.exe (PID: 8072)
Probably obfuscated PowerShell command line is found
- AdobeGenP-3.4.13.4.exe (PID: 8072)
The process bypasses the loading of PowerShell profile settings
- AdobeGenP-3.4.13.4.exe (PID: 8072)
Uses NETSH.EXE to add a firewall rule or allowed programs
- AdobeGenP-3.4.13.4.exe (PID: 8072)
The process checks if current user has admin rights
- AdobeGenP-3.4.13.4.exe (PID: 8072)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7428)
Reads mouse settings
- AdobeGenP-3.4.13.4.exe (PID: 8072)
- AdobeGenP-3.4.13.4.exe (PID: 8000)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7428)
Reads the computer name
- AdobeGenP-3.4.13.4.exe (PID: 8072)
- AdobeGenP-3.4.13.4.exe (PID: 8000)
Process checks computer location settings
- AdobeGenP-3.4.13.4.exe (PID: 8000)
Checks supported languages
- AdobeGenP-3.4.13.4.exe (PID: 8072)
- AdobeGenP-3.4.13.4.exe (PID: 8000)
Manual execution by a user
- AdobeGenP-3.4.13.4.exe (PID: 8000)
The process uses AutoIt
- AdobeGenP-3.4.13.4.exe (PID: 8072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 553952 |
| UncompressedSize: | 1205760 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Adobe-GenP-3.4.13.4/AdobeGenP-3.4.13.4.exe |
Total processes
145
Monitored processes
16
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | "C:\Windows\System32\WindowsPowerShell\v1.0\PowerShell.exe" -Command "$currentDate=Get-Date;$ipAddresses=@();try{$SOA=(Resolve-DnsName -Name adobe.io -Type SOA -ErrorAction Stop).PrimaryServer}catch{$SOA=$null};if($SOA){Do{if((New-TimeSpan -Start $currentDate -End (Get-Date)).TotalSeconds -gt 5){if($ipAddresses.Count -eq 0){$ipAddresses+='False'};break};try{$ipAddress=(Resolve-DnsName -Name adobe.io -Server $SOA -ErrorAction Stop).IPAddress}catch{$ipAddress=$null};if($ipAddress){$ipAddresses+=$ipAddress};$ipAddresses=$ipAddresses|Select -Unique|Sort-Object}While($ipAddresses.Count -lt 8)}else{$ipAddresses+='False'};Do{if((New-TimeSpan -Start $currentDate -End (Get-Date)).TotalSeconds -gt 5 -or $ipAddresses[0] -eq 'False'){break};try{$ipAddress=(Resolve-DnsName -Name 3u6k9as4bj.adobestats.io -ErrorAction Stop).IPAddress}catch{$ipAddress=$null};if($ipAddress){$ipAddresses+=$ipAddress};$ipAddresses=$ipAddresses|Select -Unique|Sort-Object}While($ipAddresses.Count -lt 12 -and $ipAddresses[0] -ne 'False');$ipAddresses=$ipAddresses -ne 'False'|Select -Unique|Sort-Object;$ipAddressList=if($ipAddresses.Count -eq 0){'False'}else{$ipAddresses -join ','};$ipAddressList" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | AdobeGenP-3.4.13.4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | "C:\Windows\System32\WindowsPowerShell\v1.0\PowerShell.exe" -Command "Test-Connection 8.8.8.8 -Count 1 -Quiet" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AdobeGenP-3.4.13.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5776 | netsh advfirewall firewall add rule name="Adobe Unlicensed Pop-up" dir=out action=block remoteip="107.22.247.231,18.207.85.246,34.193.227.236,54.144.73.197" | C:\Windows\System32\netsh.exe | — | AdobeGenP-3.4.13.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5780 | netsh advfirewall firewall delete rule name="Adobe Unlicensed Pop-up" | C:\Windows\System32\netsh.exe | — | AdobeGenP-3.4.13.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7428 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Adobe-GenP-3.4.13.4.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
18 793
Read events
18 785
Write events
8
Delete events
0
Modification events
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Adobe-GenP-3.4.13.4.rar | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
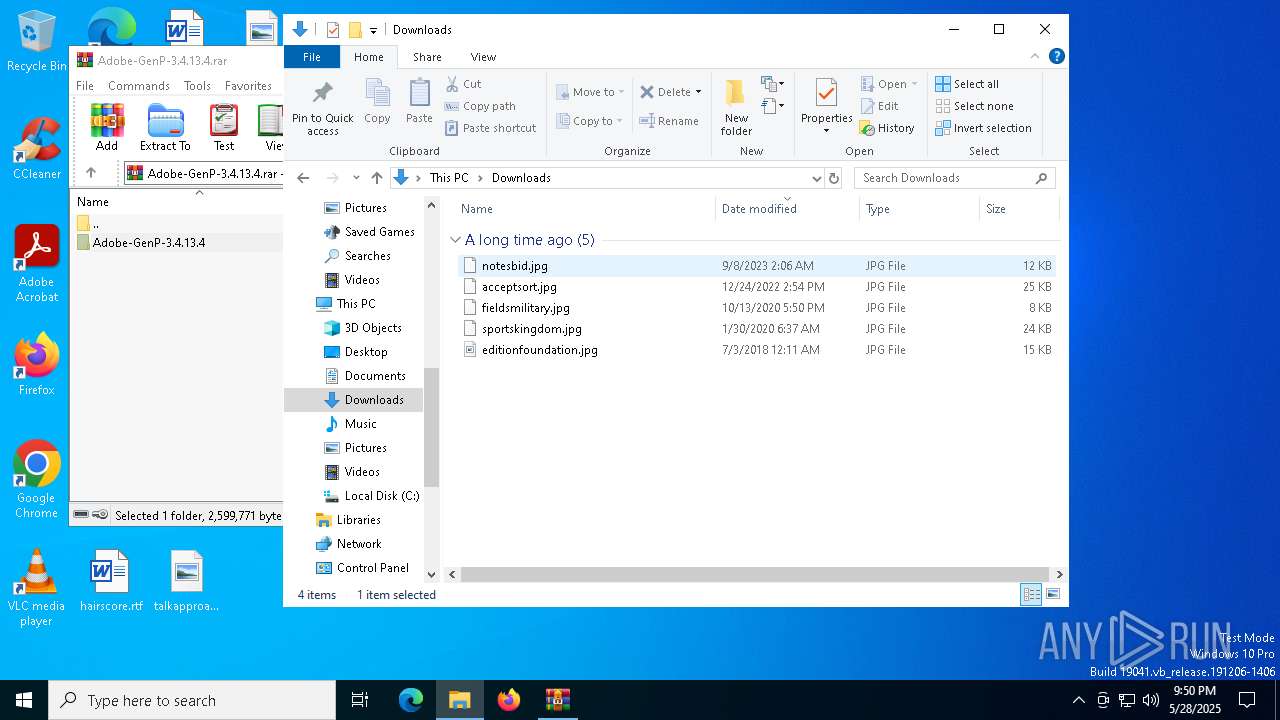
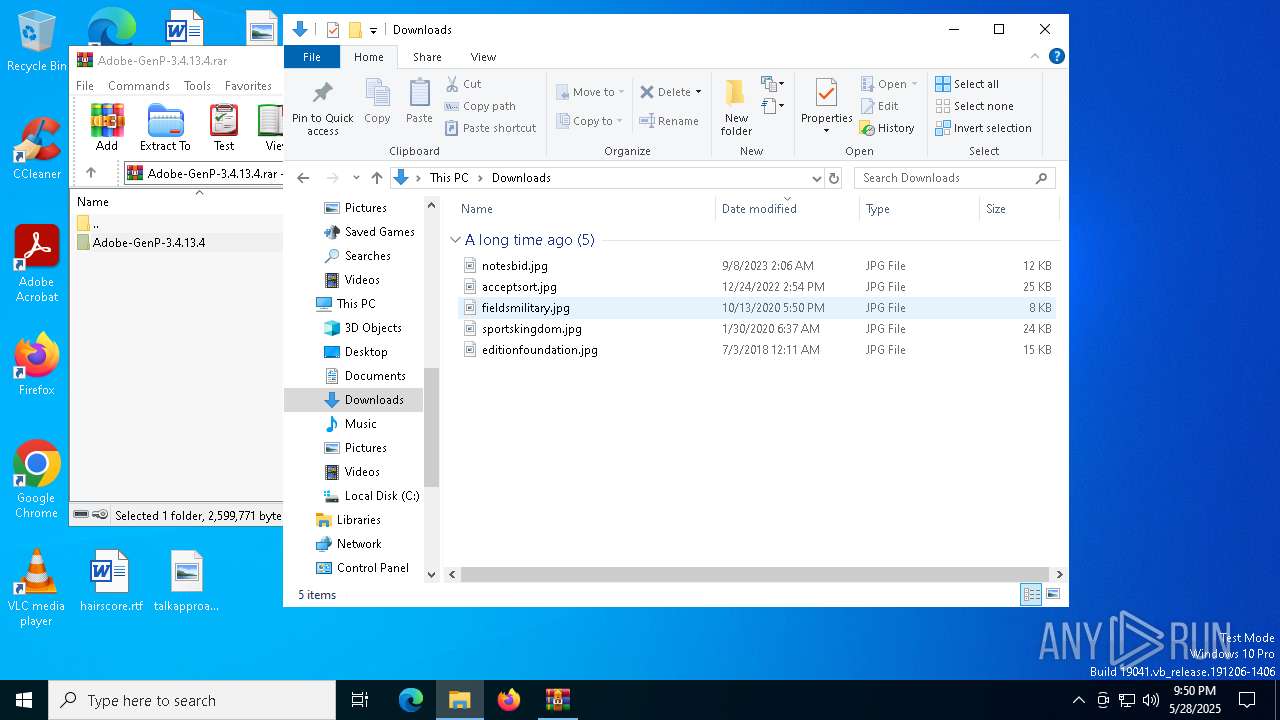
Executable files
4
Suspicious files
1
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
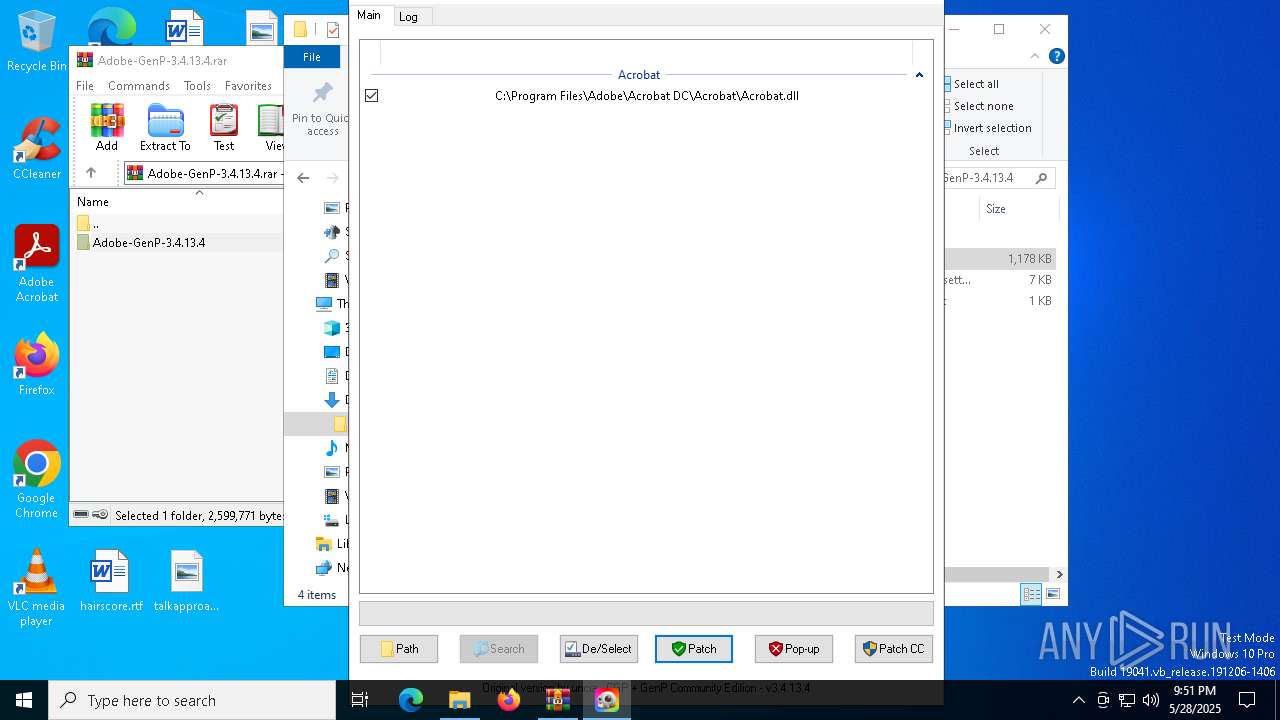
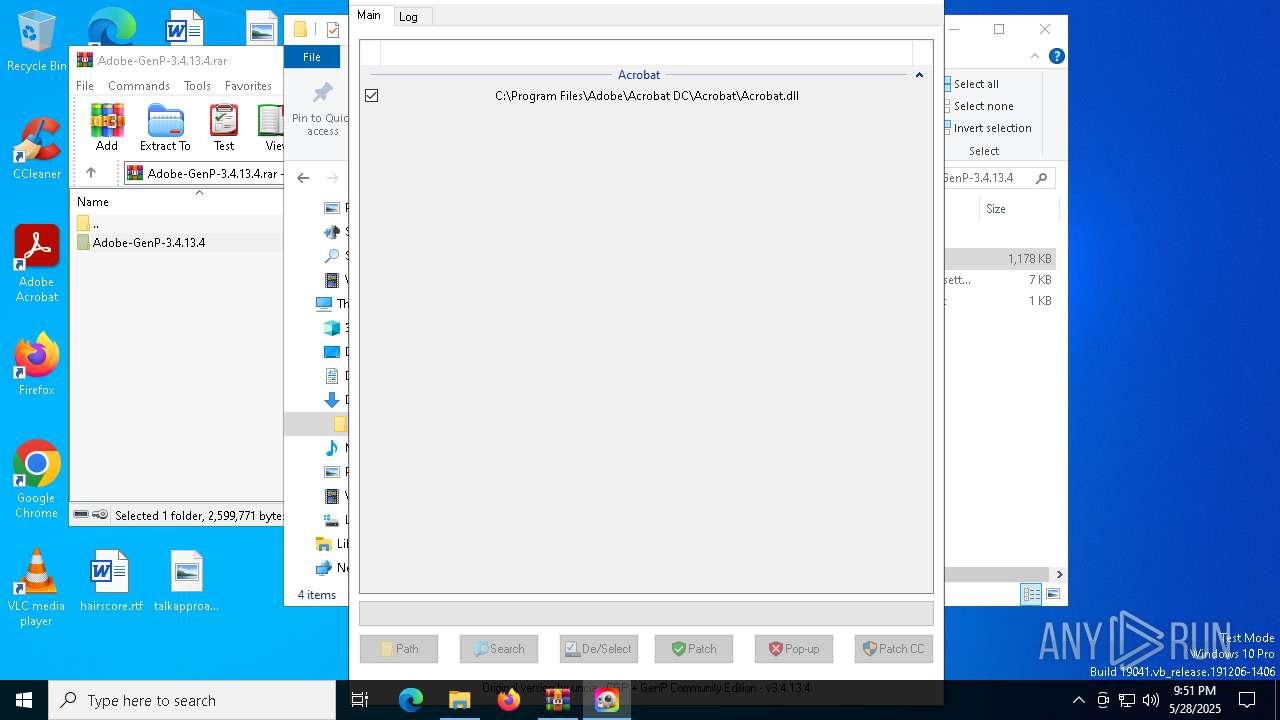
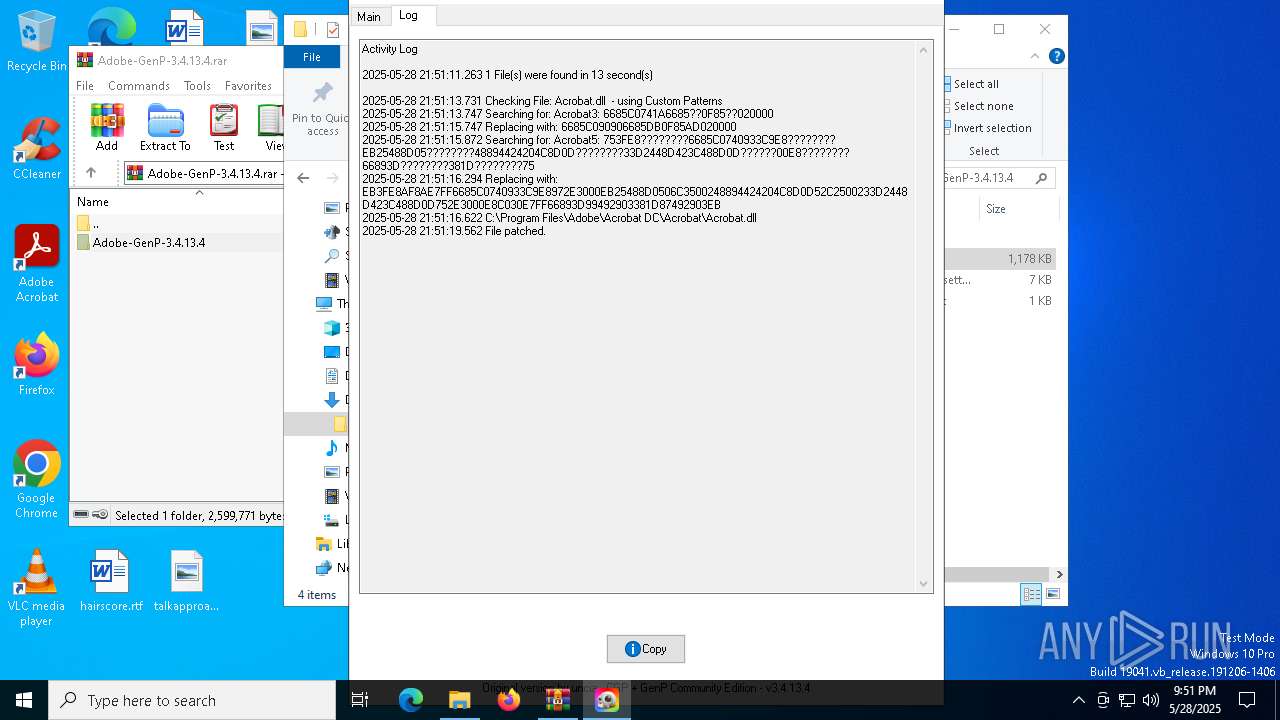
| 8072 | AdobeGenP-3.4.13.4.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 8072 | AdobeGenP-3.4.13.4.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 7428 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7428.36068\Adobe-GenP-3.4.13.4\src\AdobeGenP.au3 | text | |
MD5:FAFC7453A8AE5B2E9FAE0671642EF3B9 | SHA256:F28F2CB13EBA2667C1AD3F14A7D82CAE7A98833982C9AE604AF84BAEDECB7966 | |||
| 2504 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sfxccyru.wxy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7600 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cjiqw42s.gi1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7600 | powershell.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:2370C90B972BDEFA28A7B7F5332607BD | SHA256:6E85EFC4EABEA74546F970F5AABA4910FD4B23179E77B5BFDB89890E137E428F | |||
| 2516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5n0fvobk.klg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7428 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7428.36068\Adobe-GenP-3.4.13.4\README.txt | text | |
MD5:9BACEB44FEA06BC4B7AD82B1D6780ADB | SHA256:1DC14896653DC0B0A88D7A04631712C3934C3625825F7E1CF02D3725DF48F885 | |||
| 2516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uqyjjz5p.lik.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7428 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7428.36068\Adobe-GenP-3.4.13.4\src\AdobeGenP.exe | executable | |
MD5:8115E2B092B1C678099A4A28C5842FDB | SHA256:7DA588B70BFB209FAFFB91C558BFF4915F0C00104BFAE49B4CC87FAC8B87AE67 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
435
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4784 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
adobe.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |