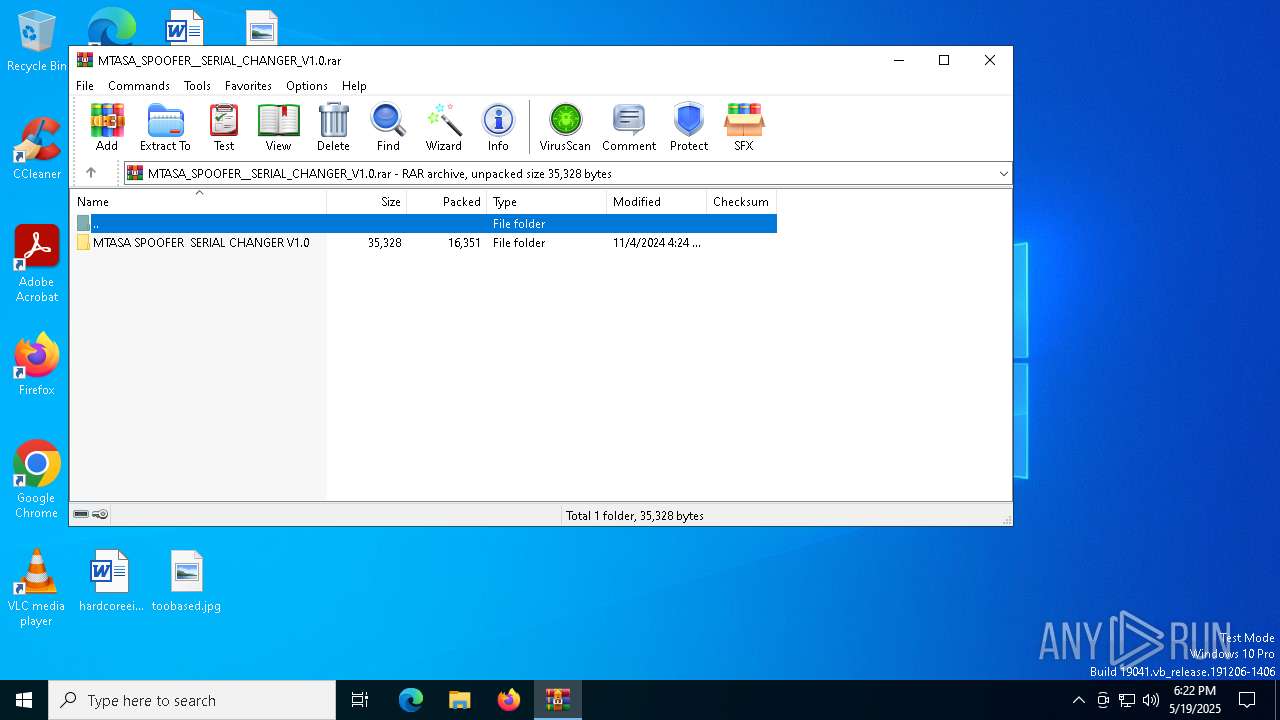
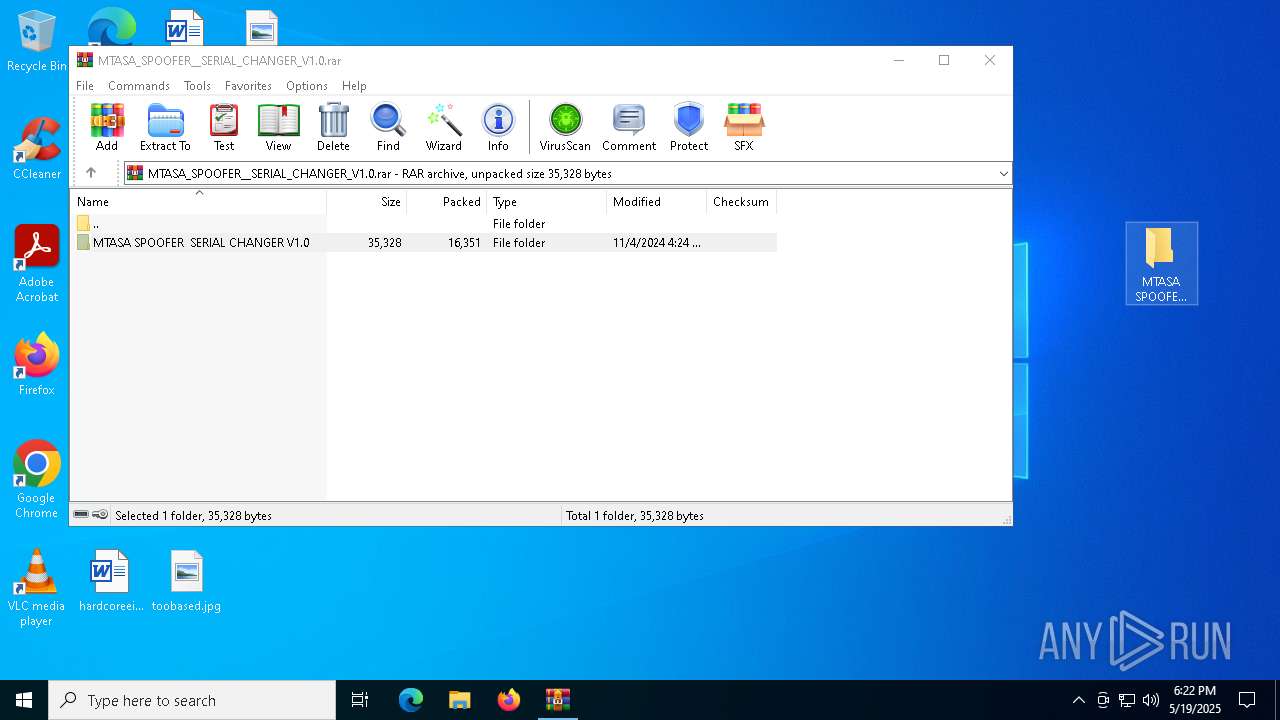
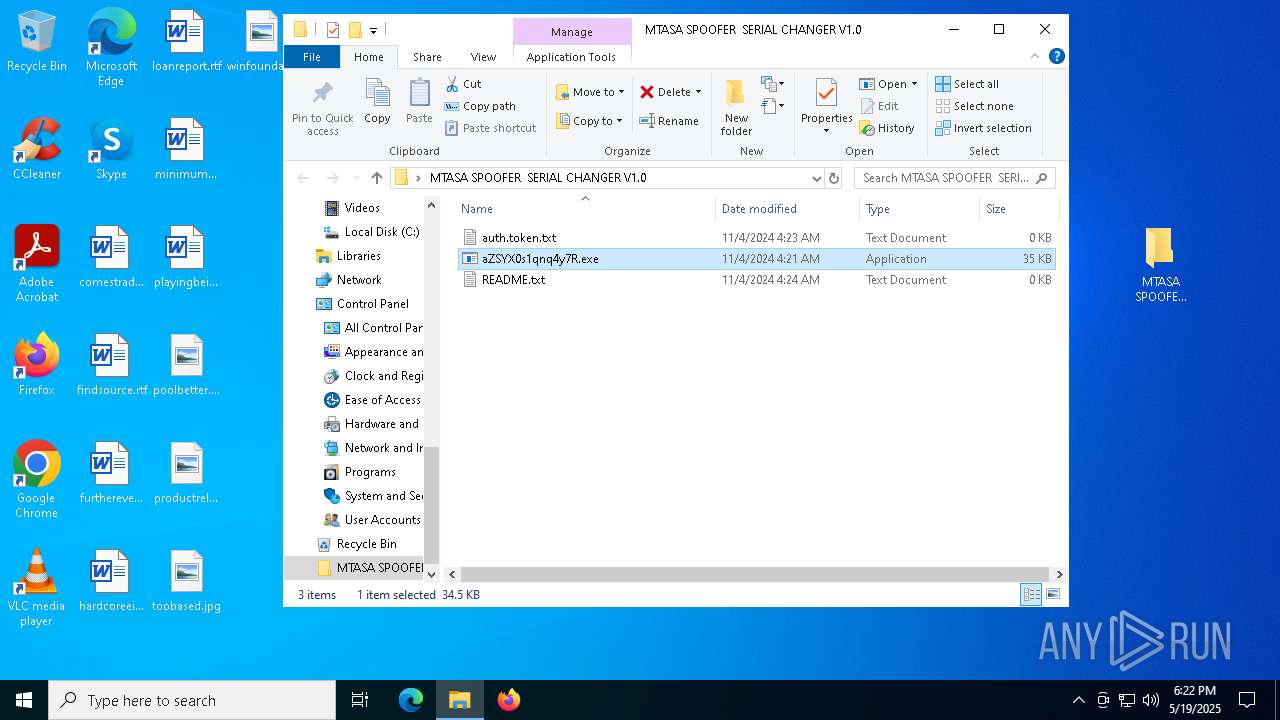
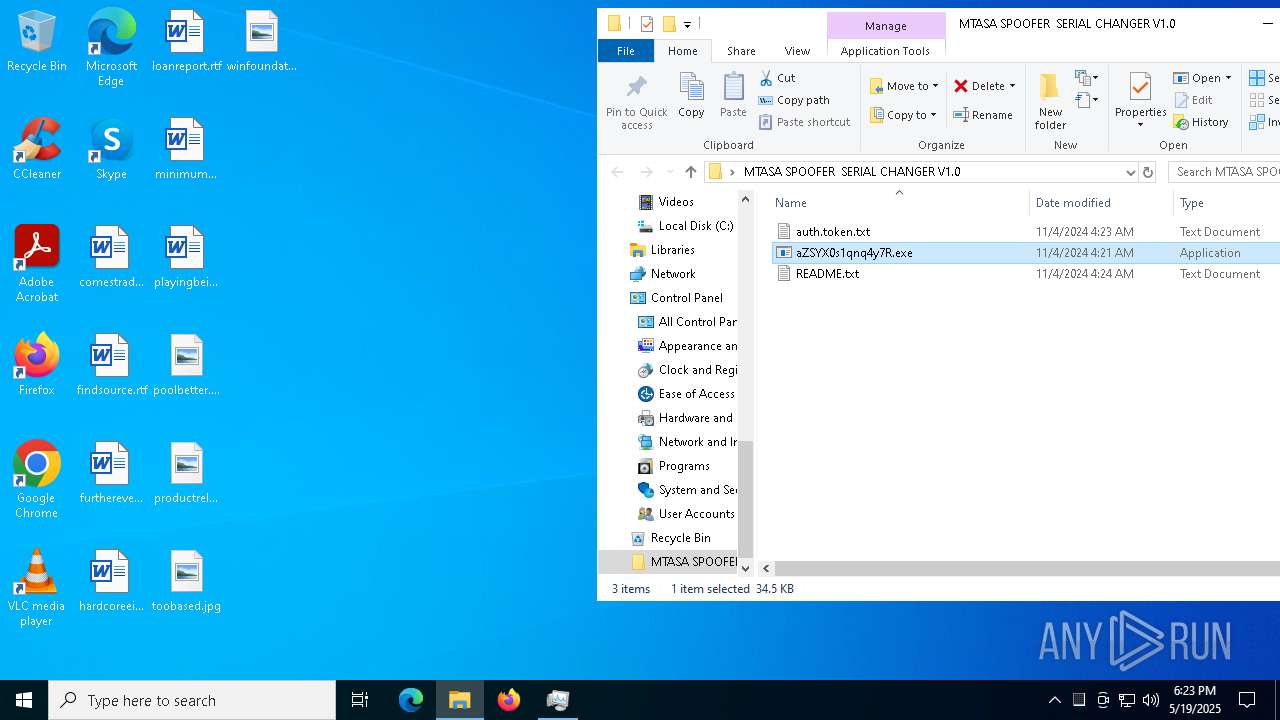
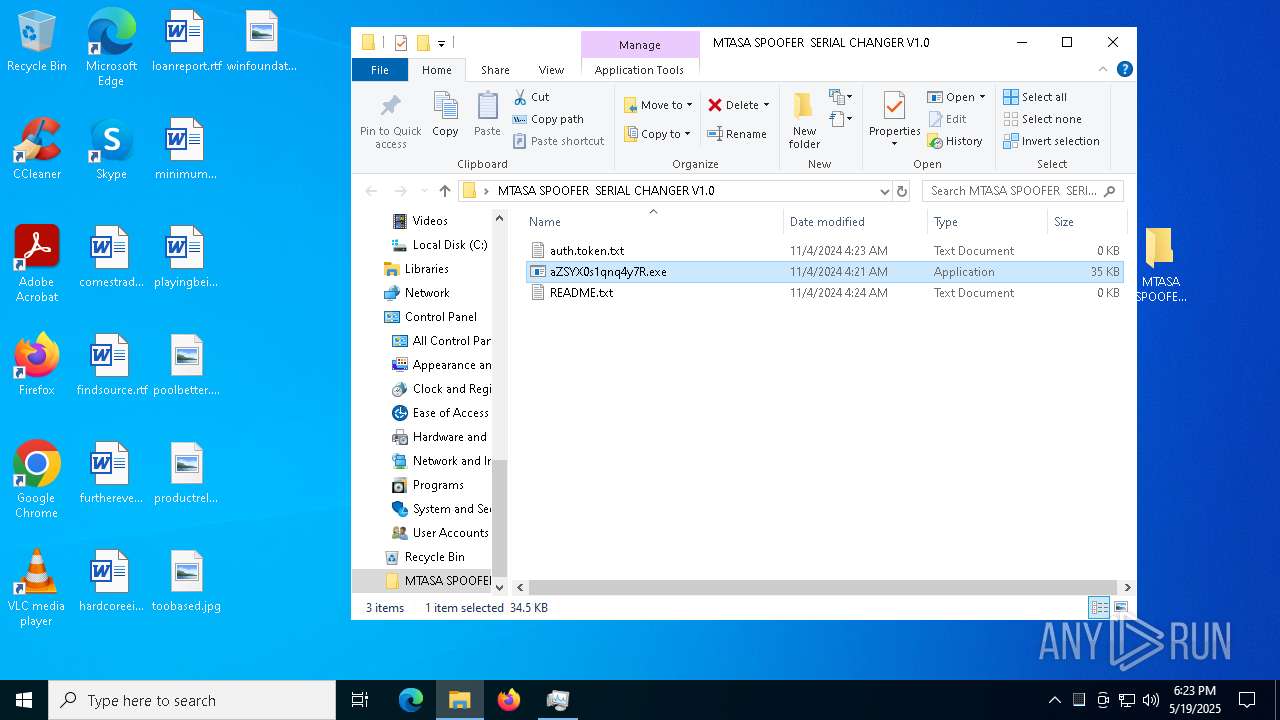
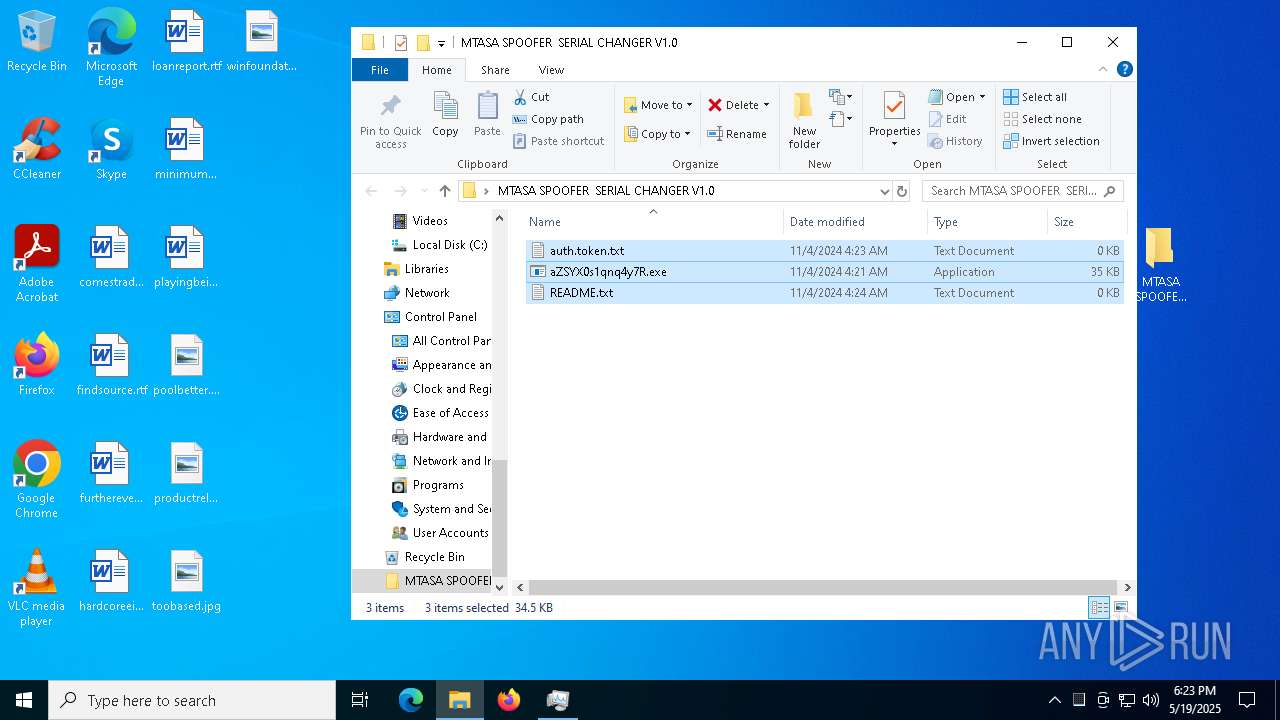
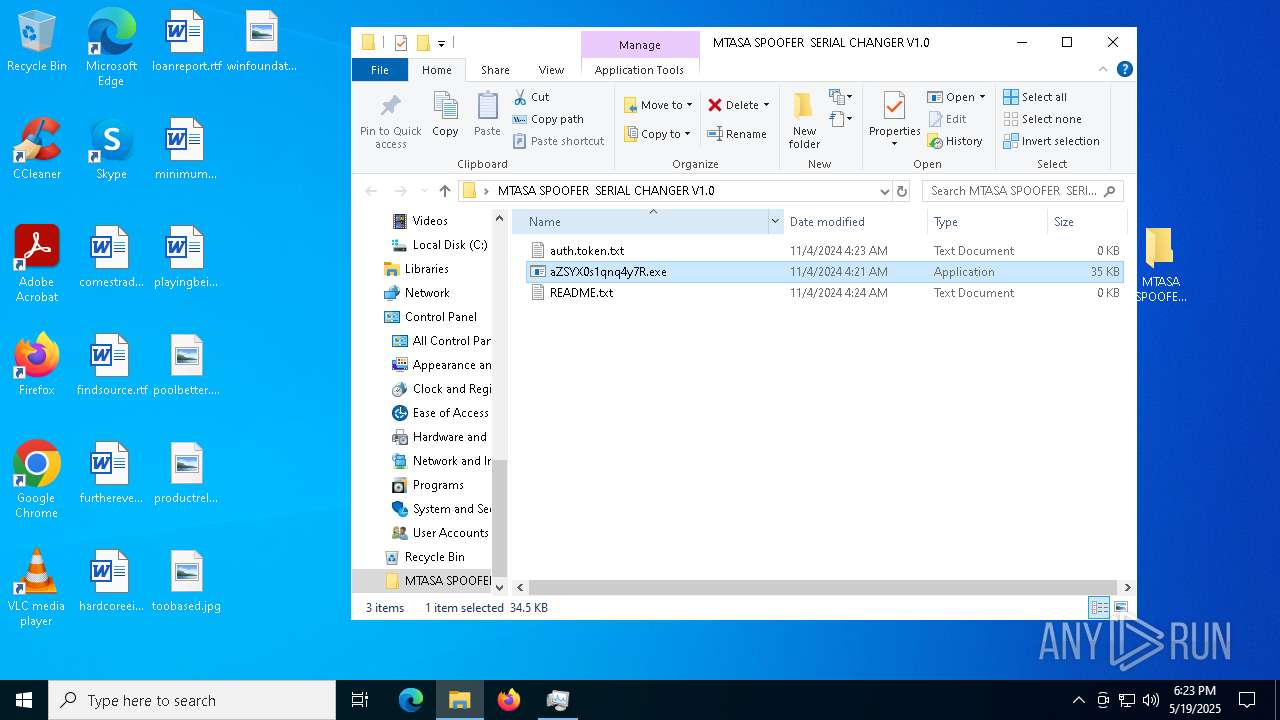
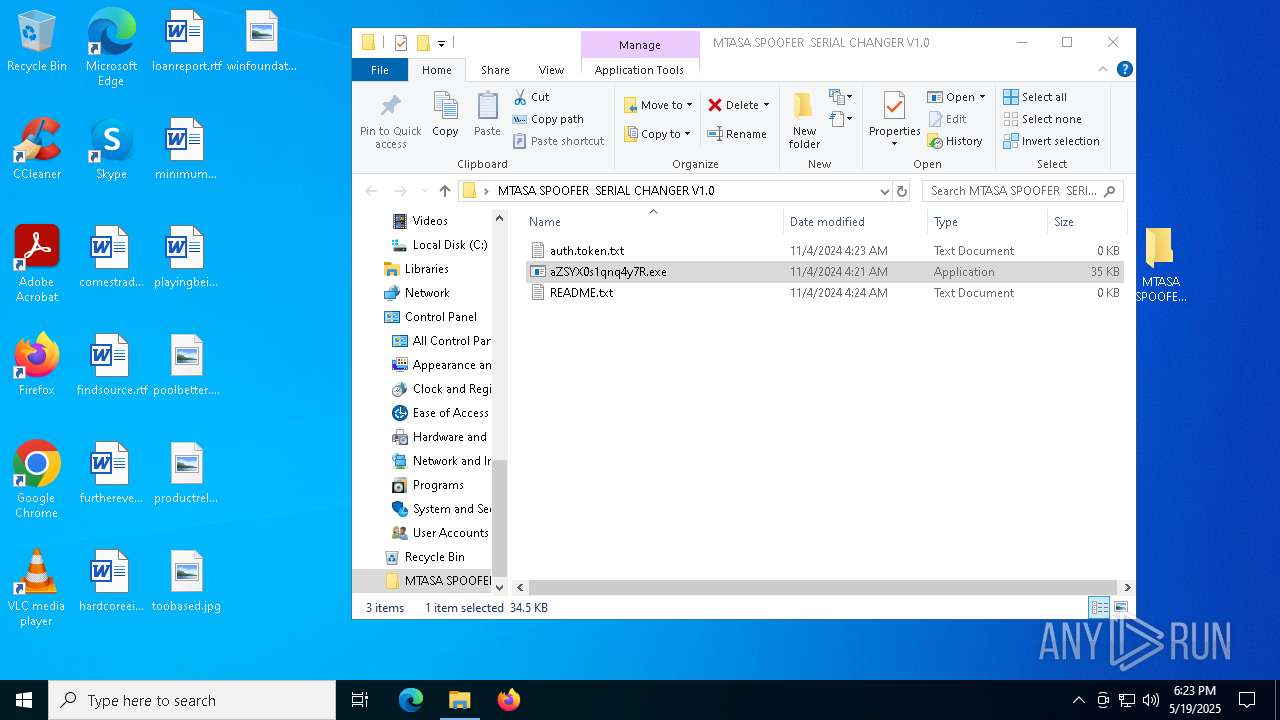
| File name: | MTASA_SPOOFER__SERIAL_CHANGER_V1.0.rar |
| Full analysis: | https://app.any.run/tasks/ed59f2ae-f8ea-4729-a2f1-663682f25513 |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | May 19, 2025, 18:21:59 |
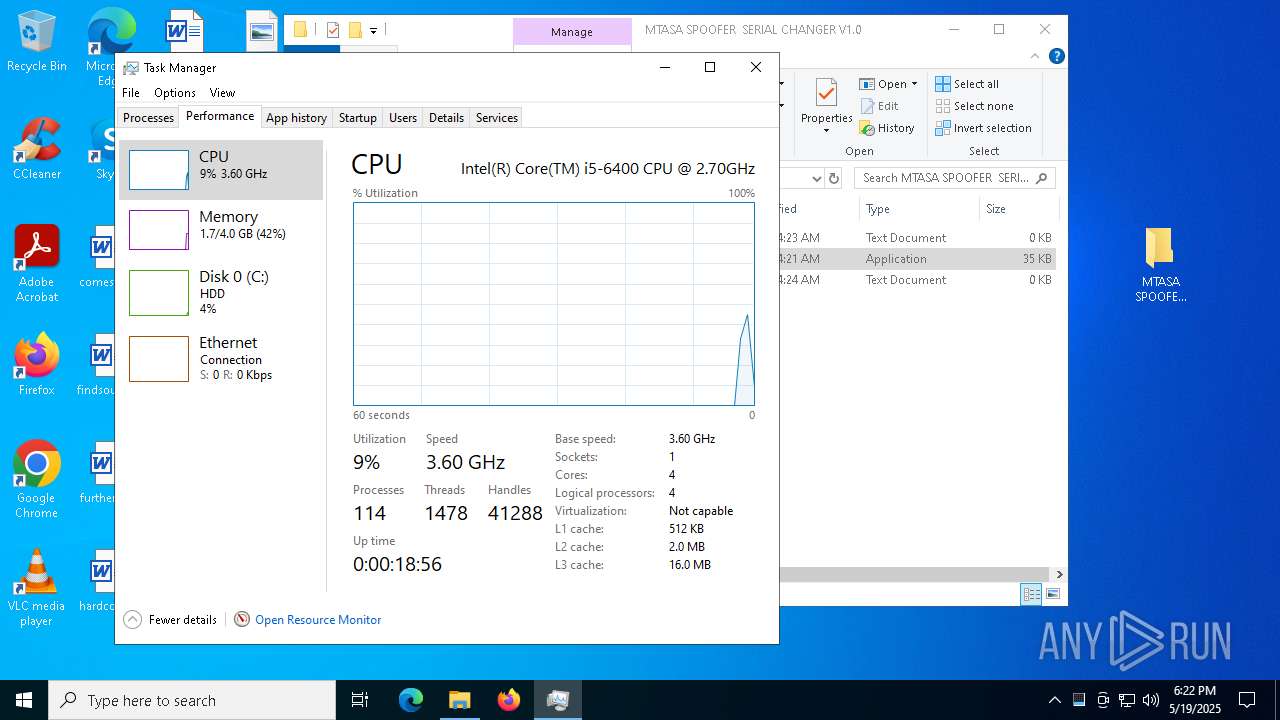
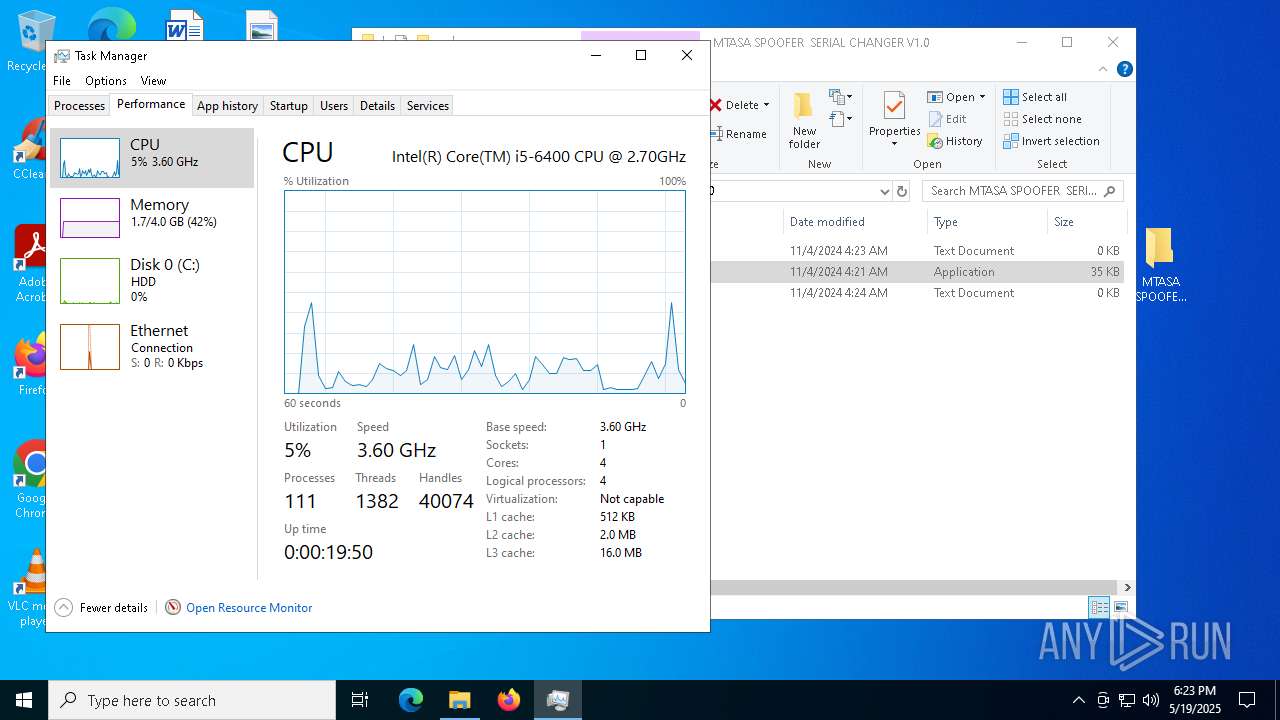
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0784128738A4B47CB6A10F99414A1C48 |
| SHA1: | 783A56AA1D69B0E457709178A8EF576FDCCA6E72 |
| SHA256: | DDC8492F4D044B6D7FBBBDB3C705B2847503ED47A7BF2665DEC46AB6ED508152 |
| SSDEEP: | 384:ljbG4T1OvkTTmWTYAMhB9BLquBMHmWmbG1mKJROTNw99:E7vU6hBbtImWmbG1mNU9 |
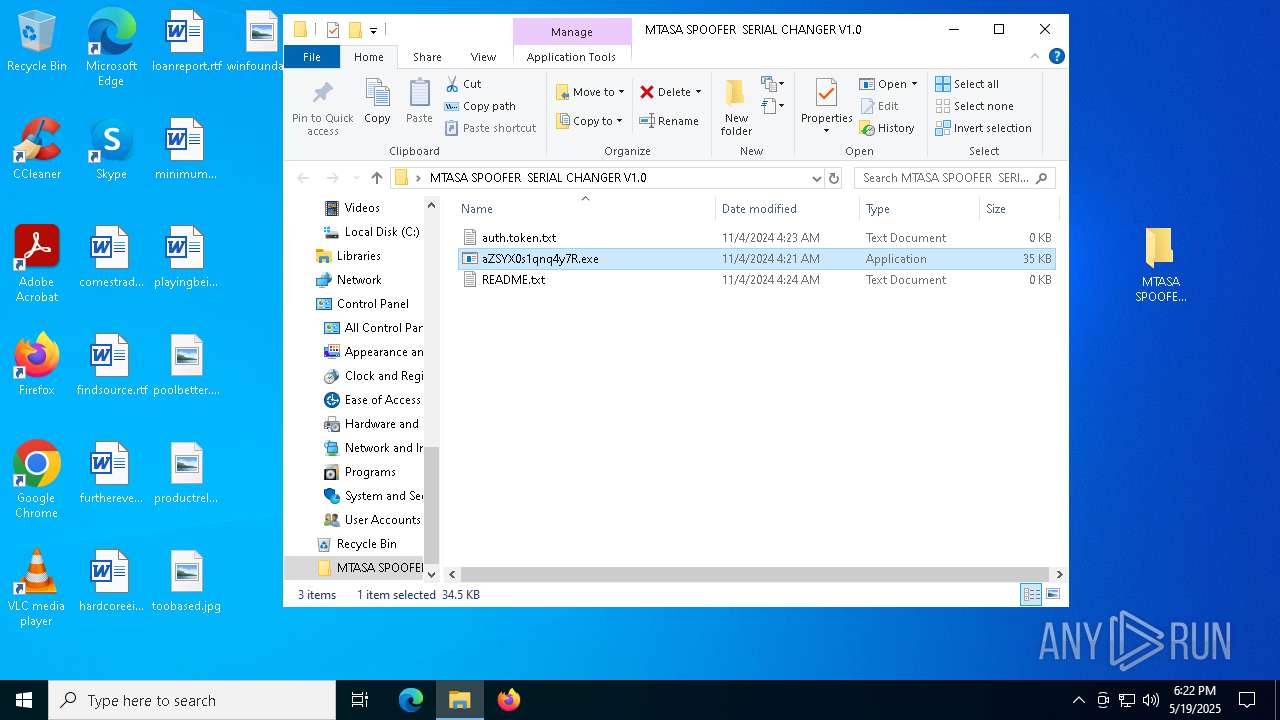
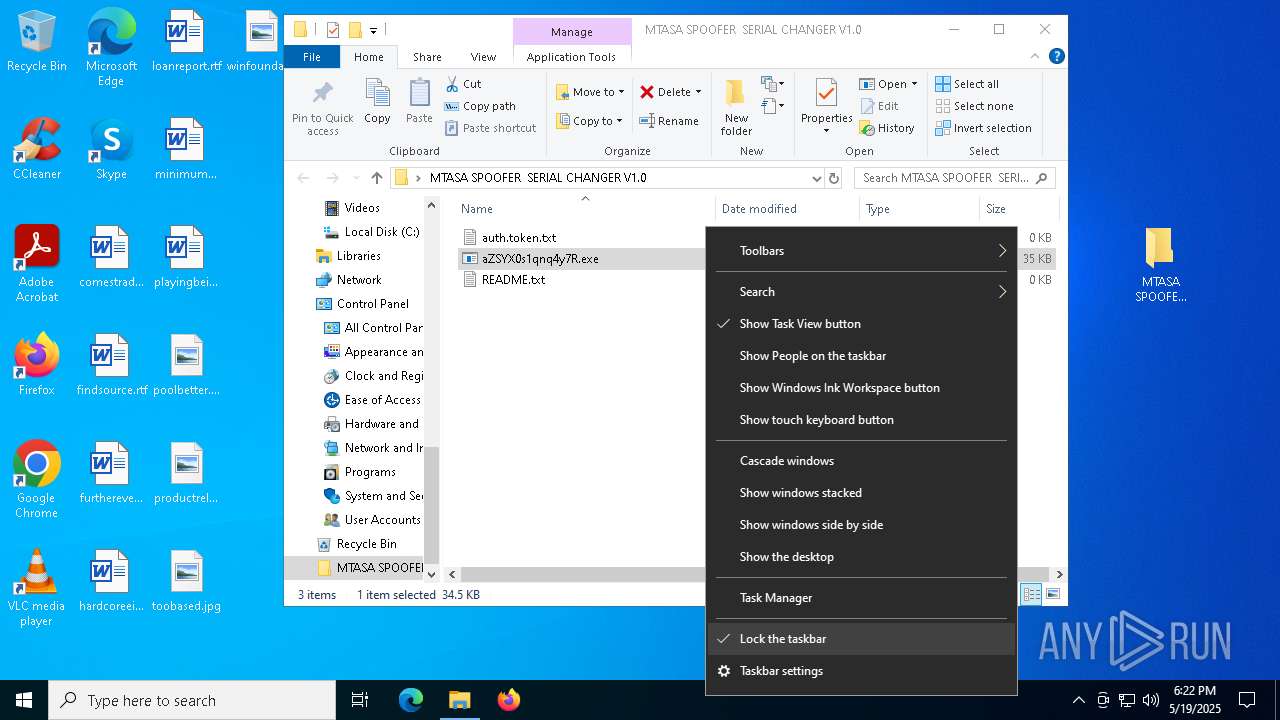
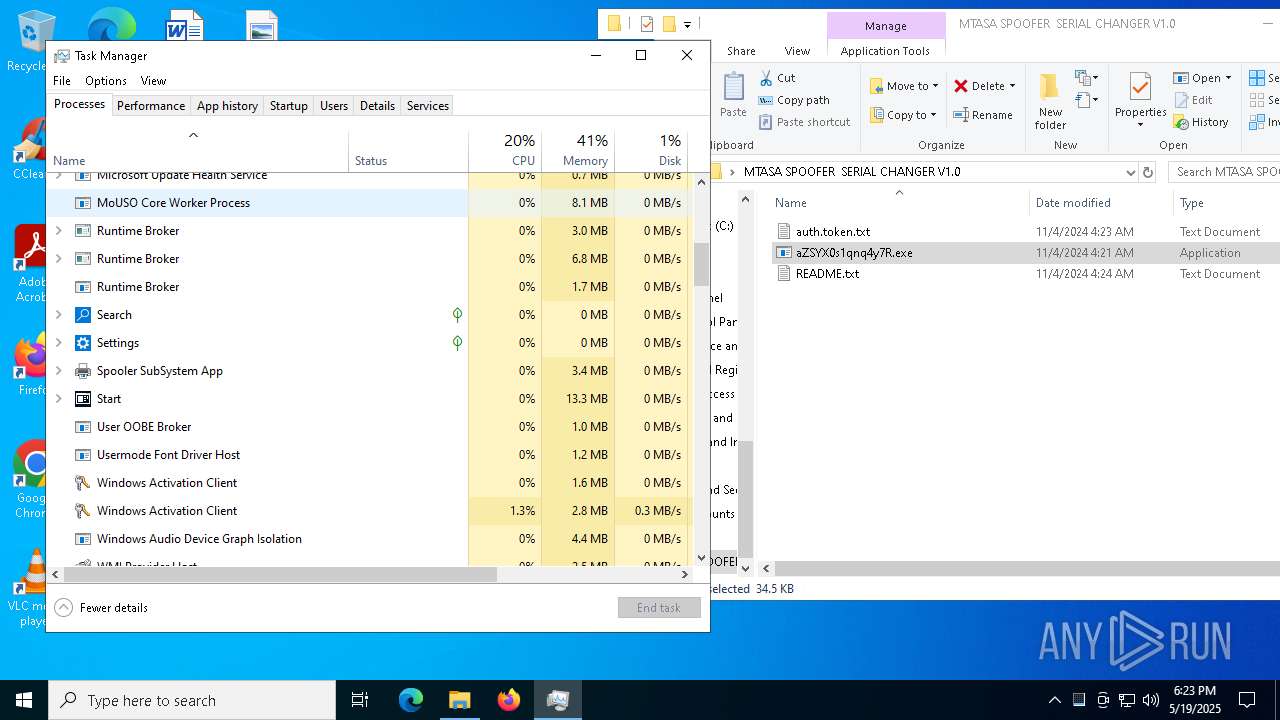
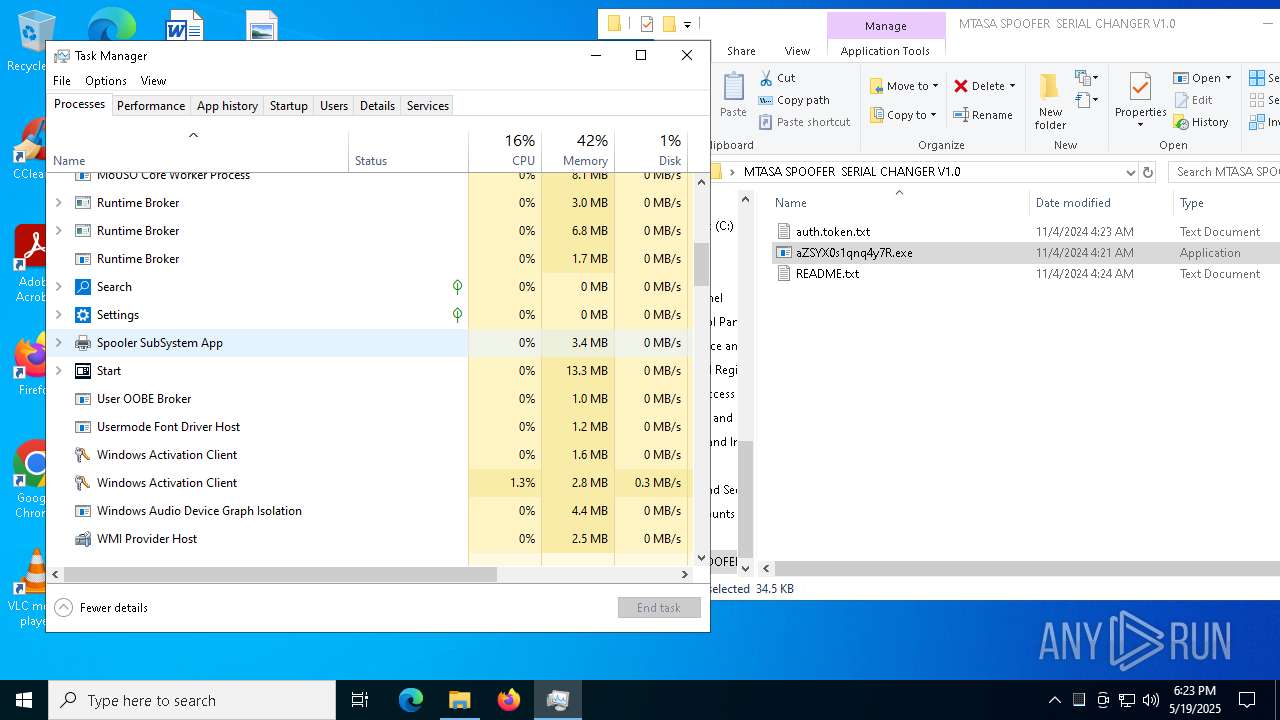
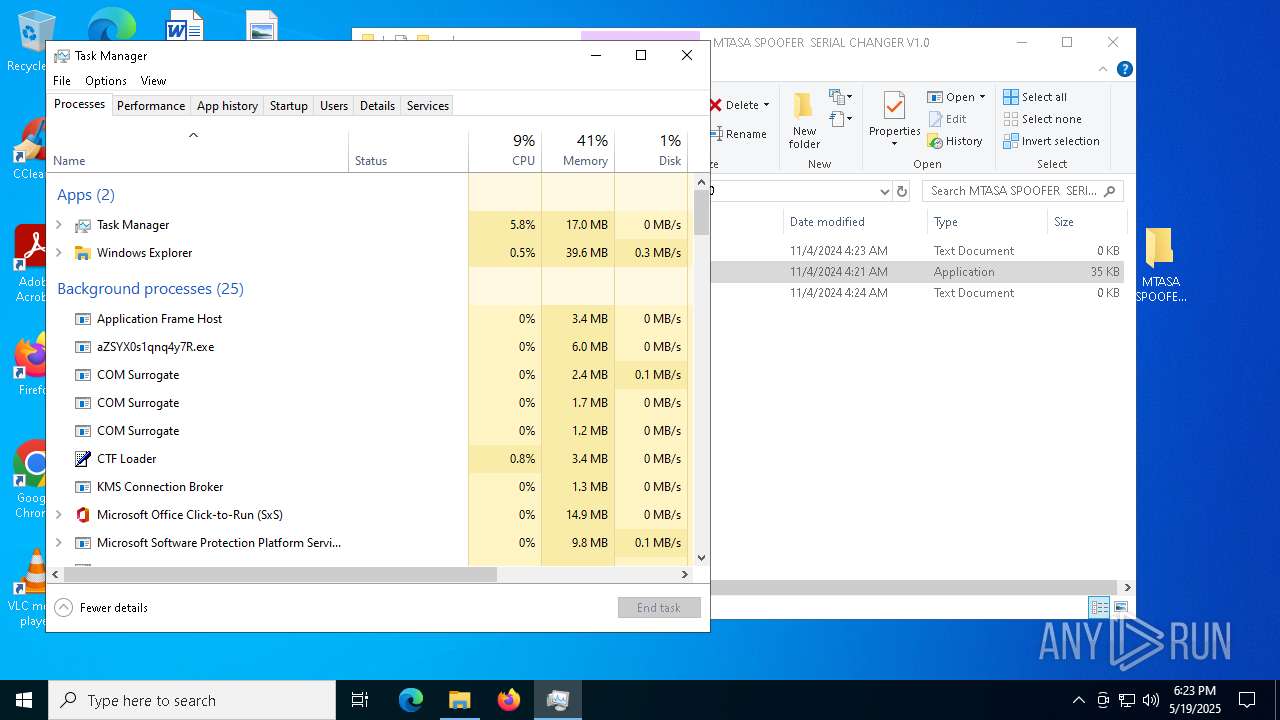
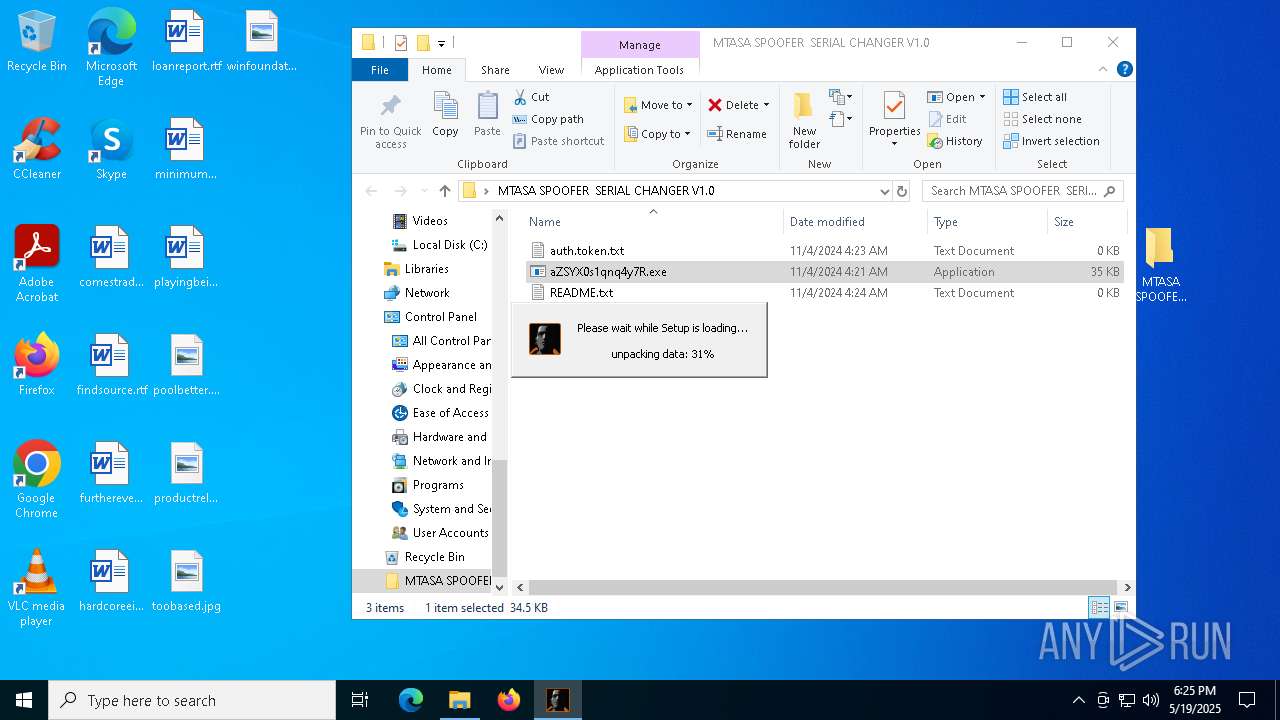
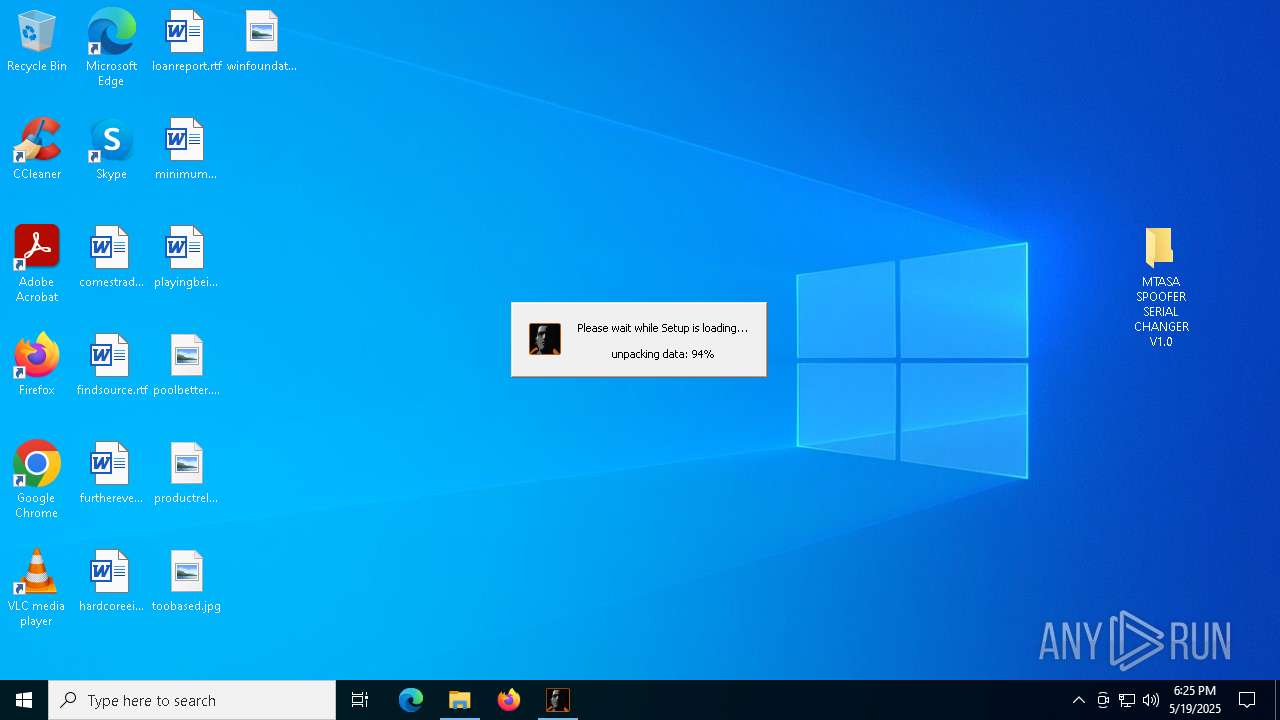
MALICIOUS
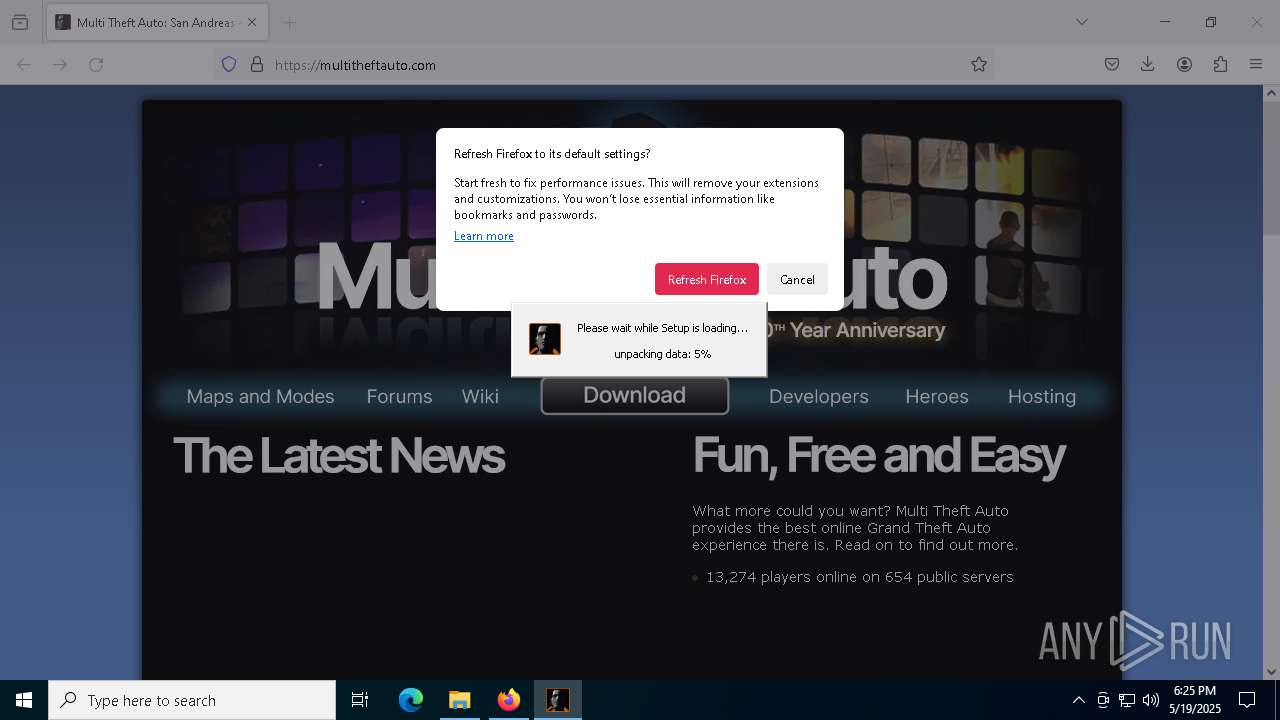
Generic archive extractor
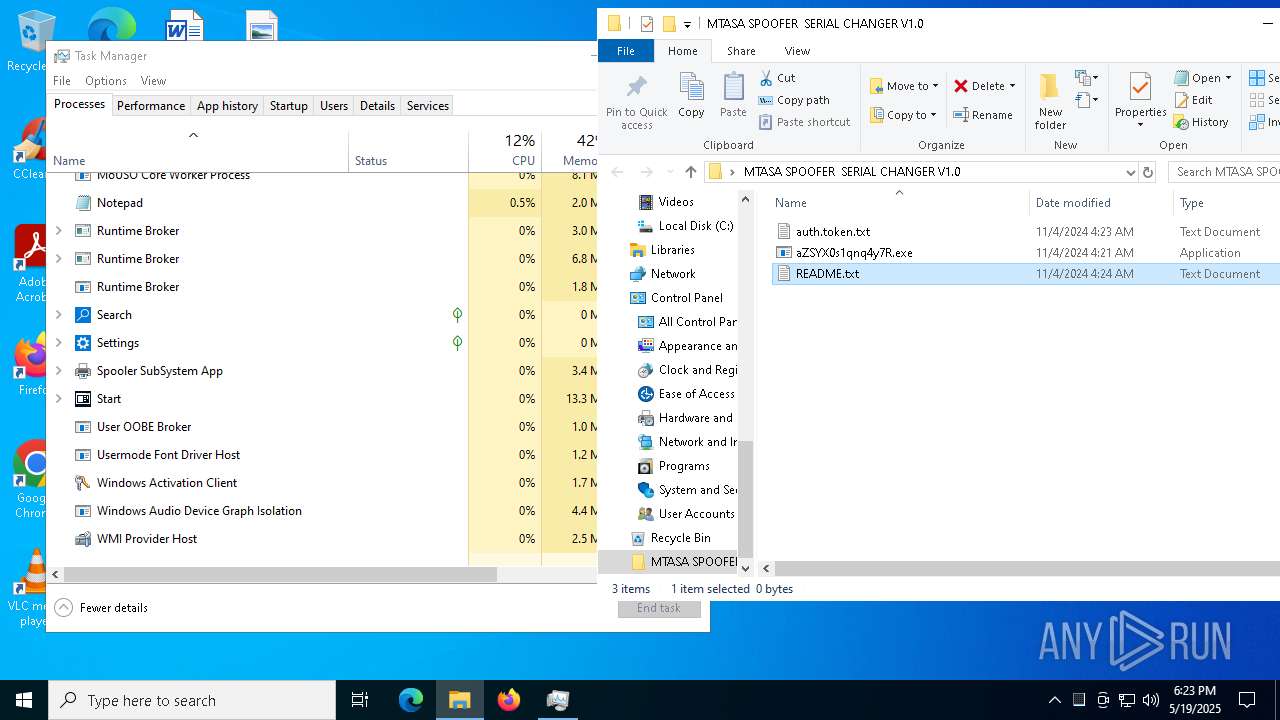
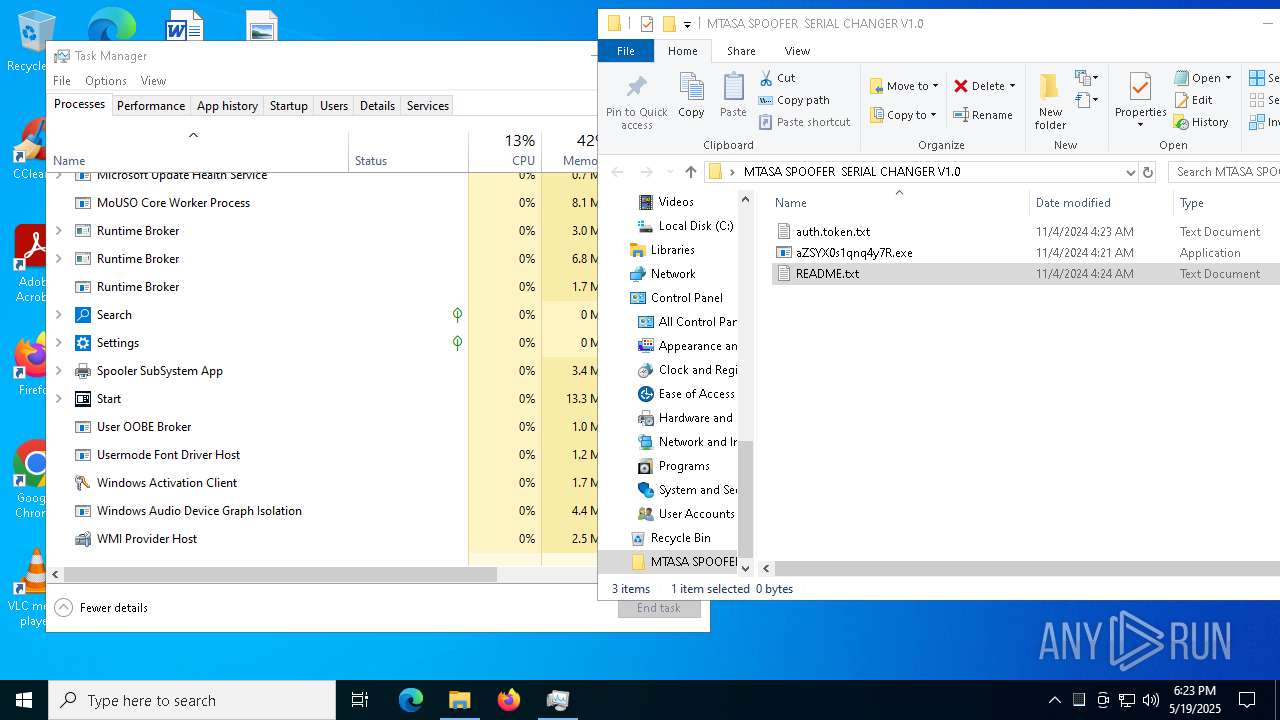
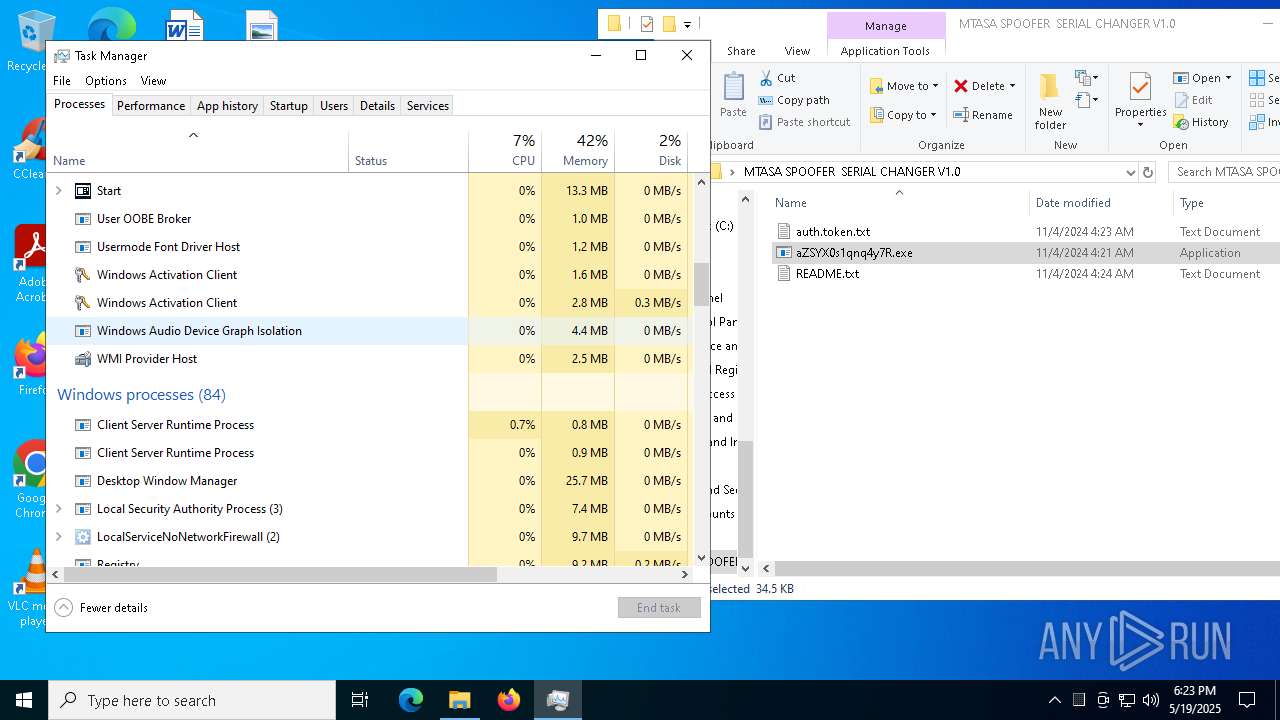
- WinRAR.exe (PID: 7248)
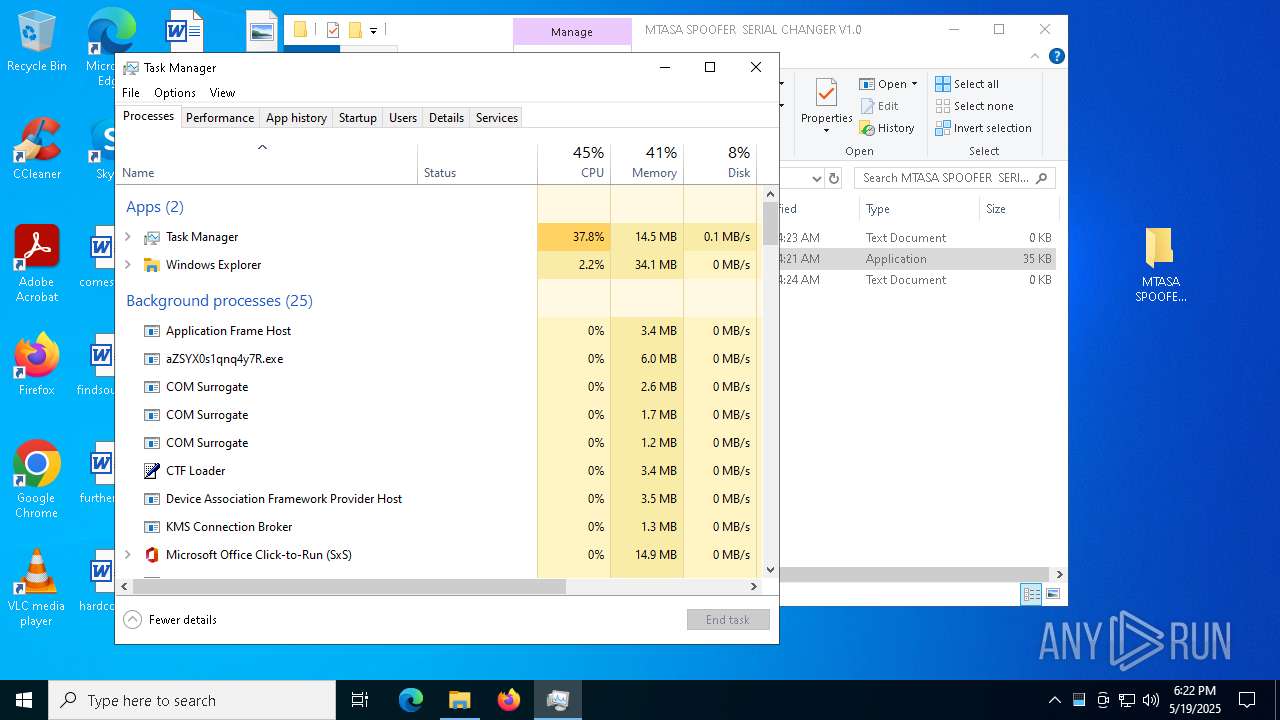
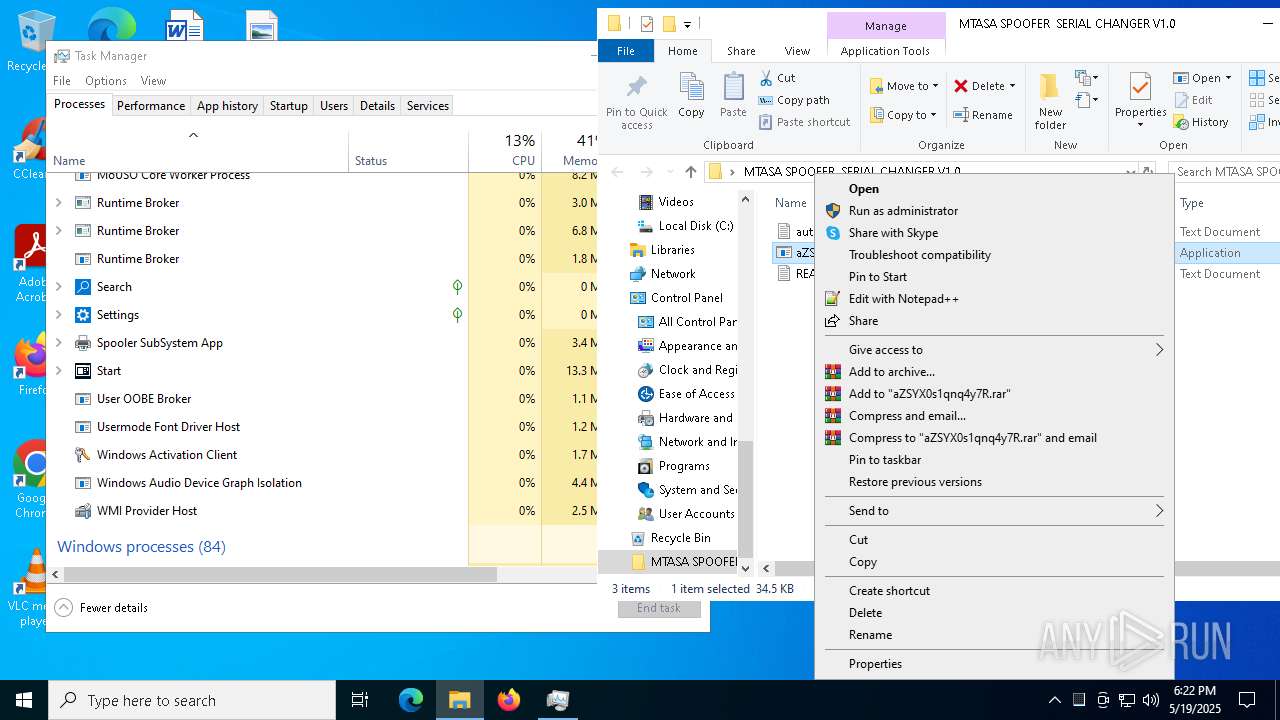
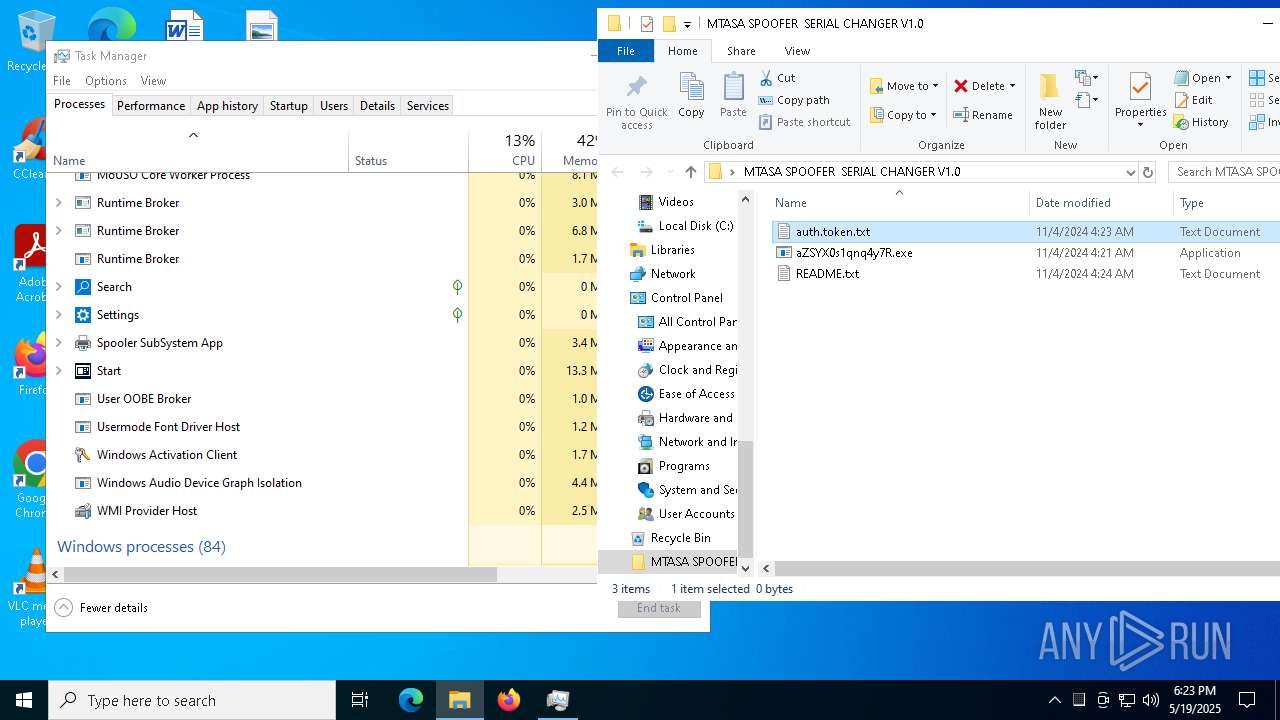
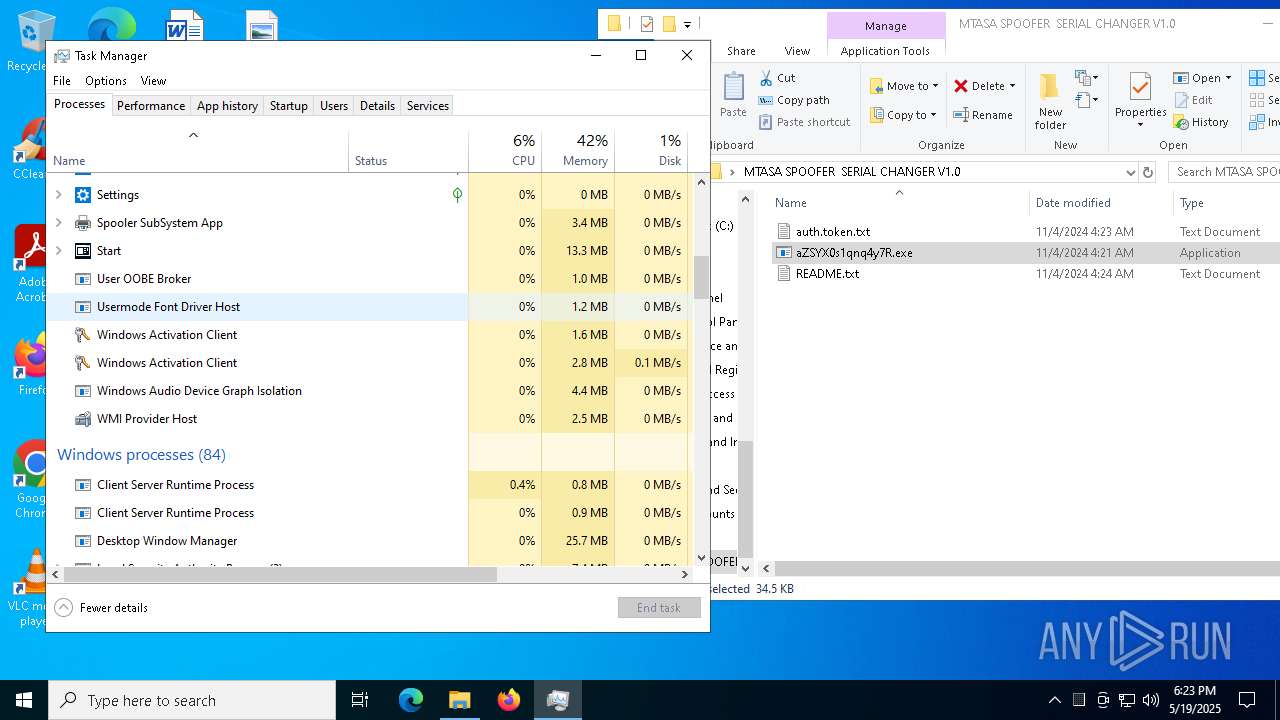
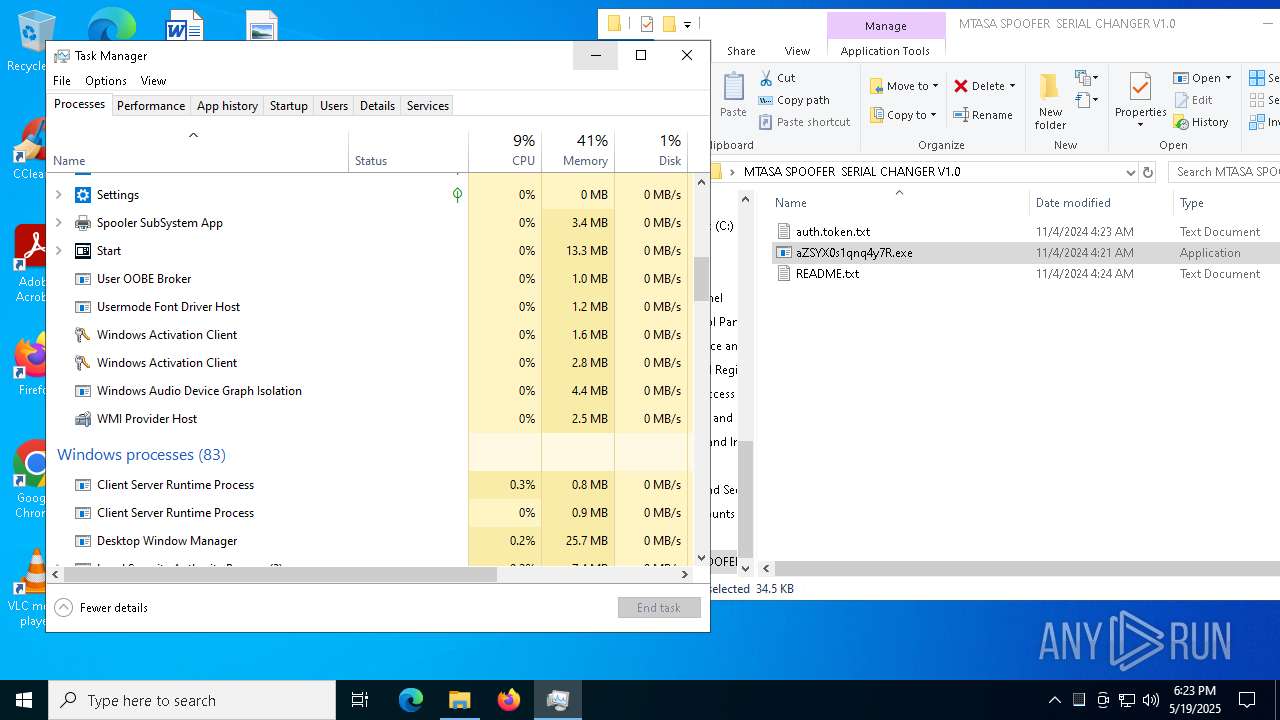
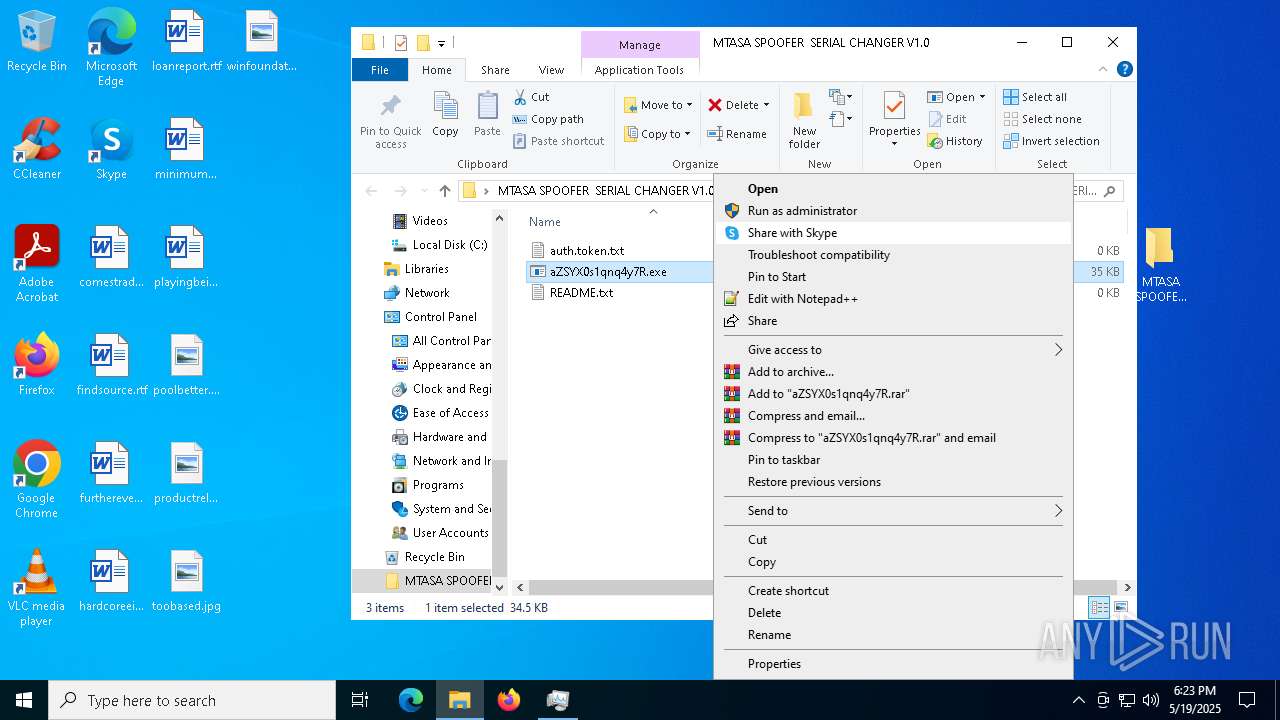
Create files in the Startup directory
- aZSYX0s1qnq4y7R.exe (PID: 8048)
Changes the autorun value in the registry
- aZSYX0s1qnq4y7R.exe (PID: 8048)
XWORM has been detected (YARA)
- aZSYX0s1qnq4y7R.exe (PID: 8048)
SUSPICIOUS
Executable content was dropped or overwritten
- aZSYX0s1qnq4y7R.exe (PID: 8048)
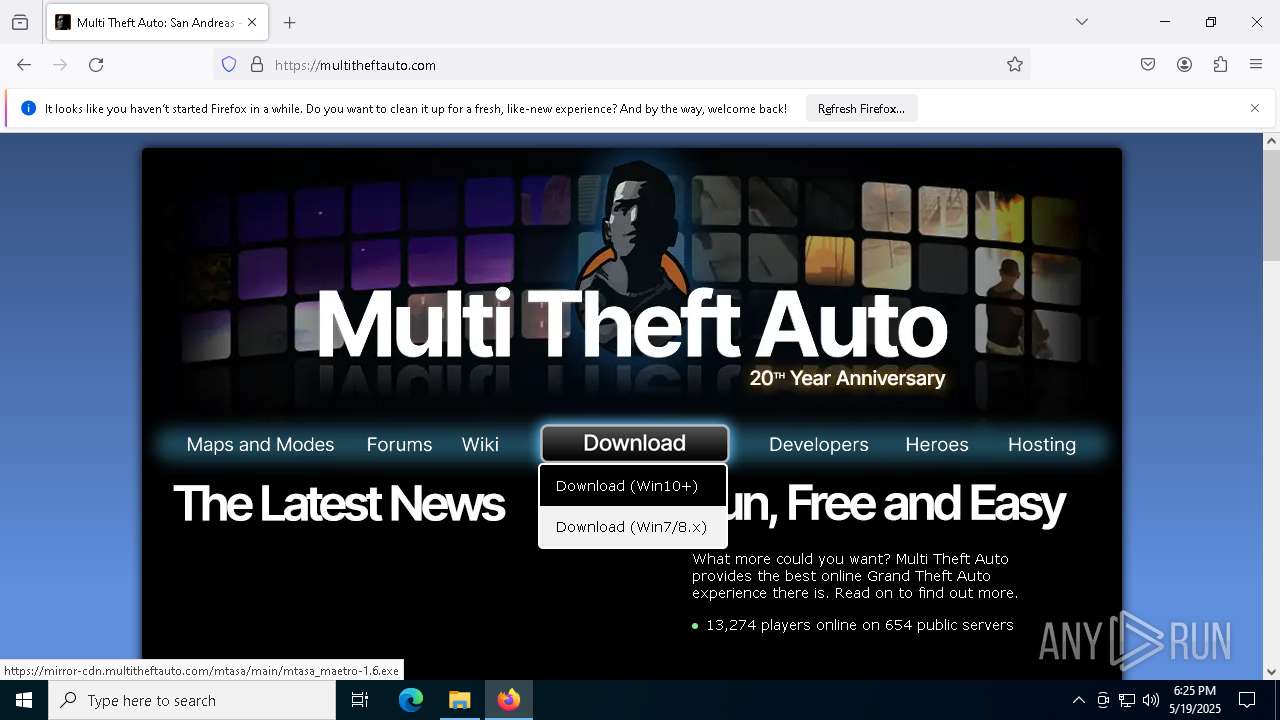
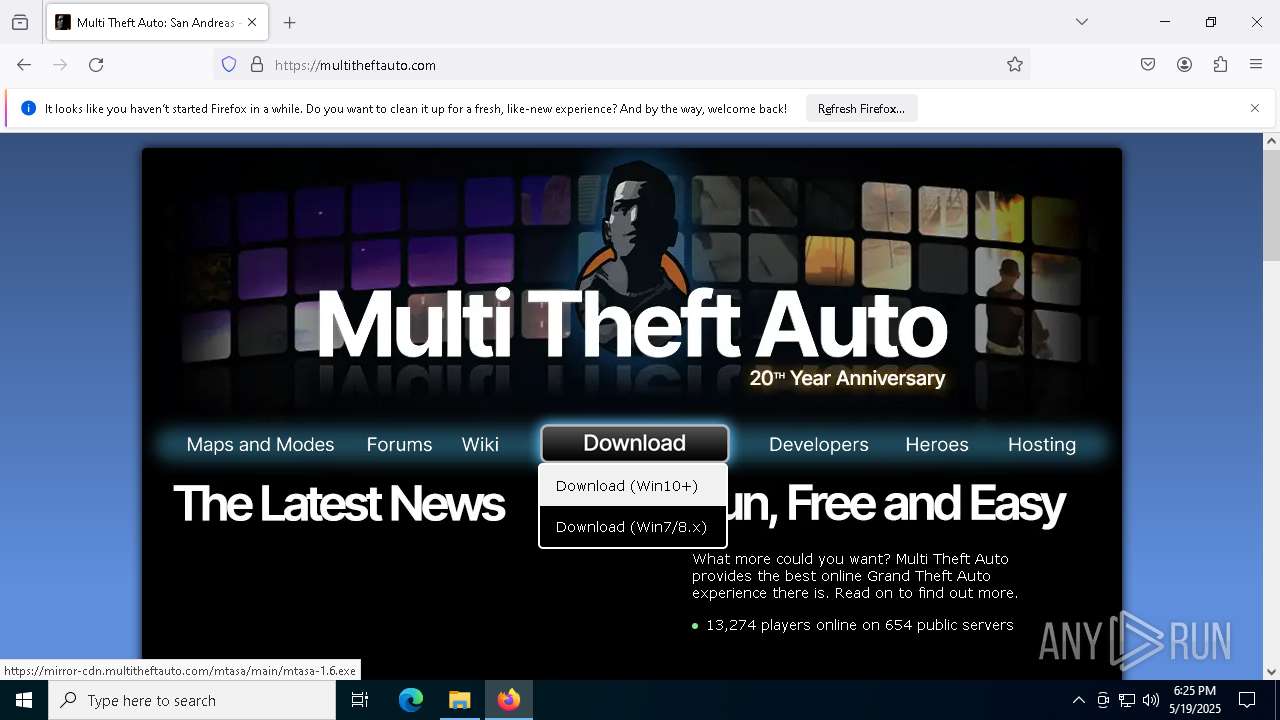
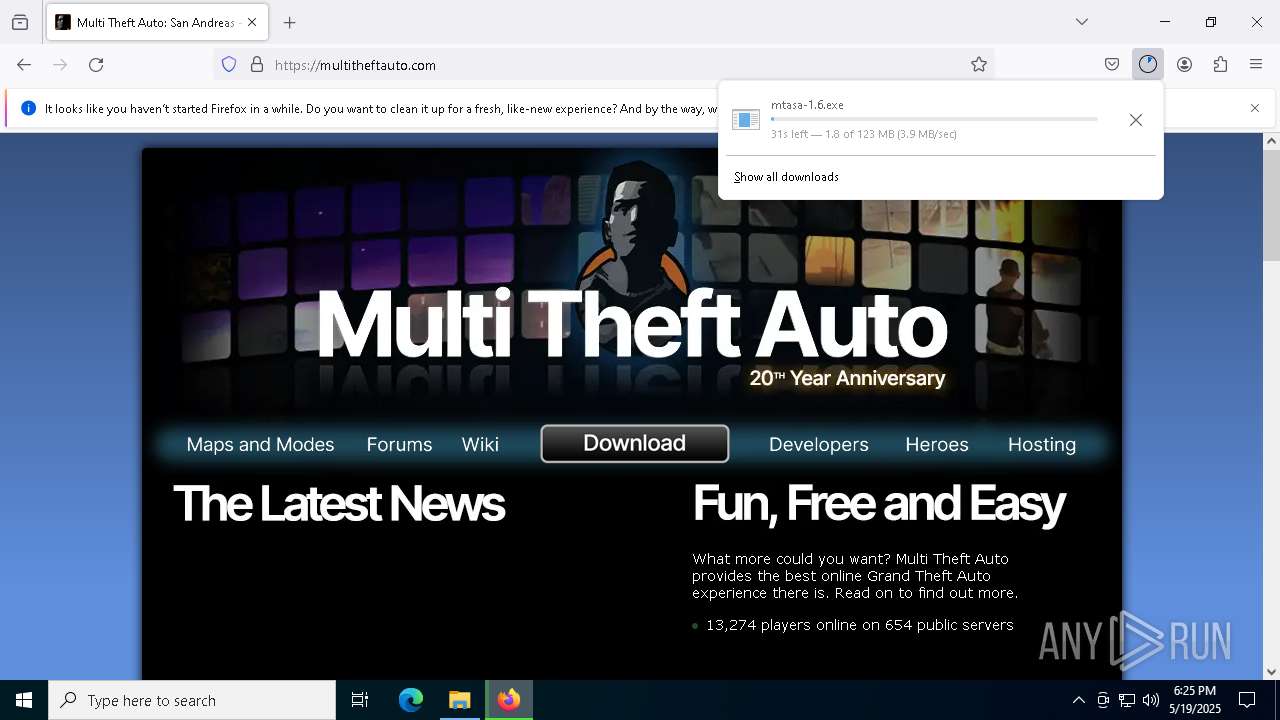
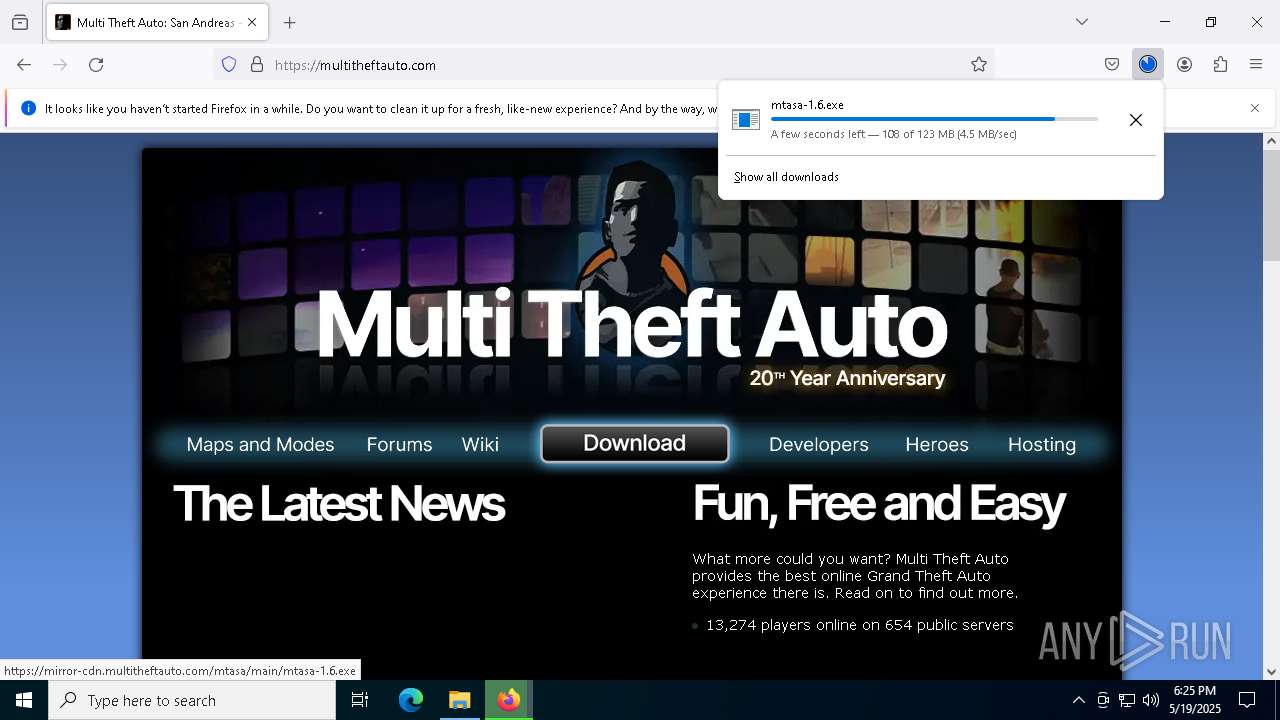
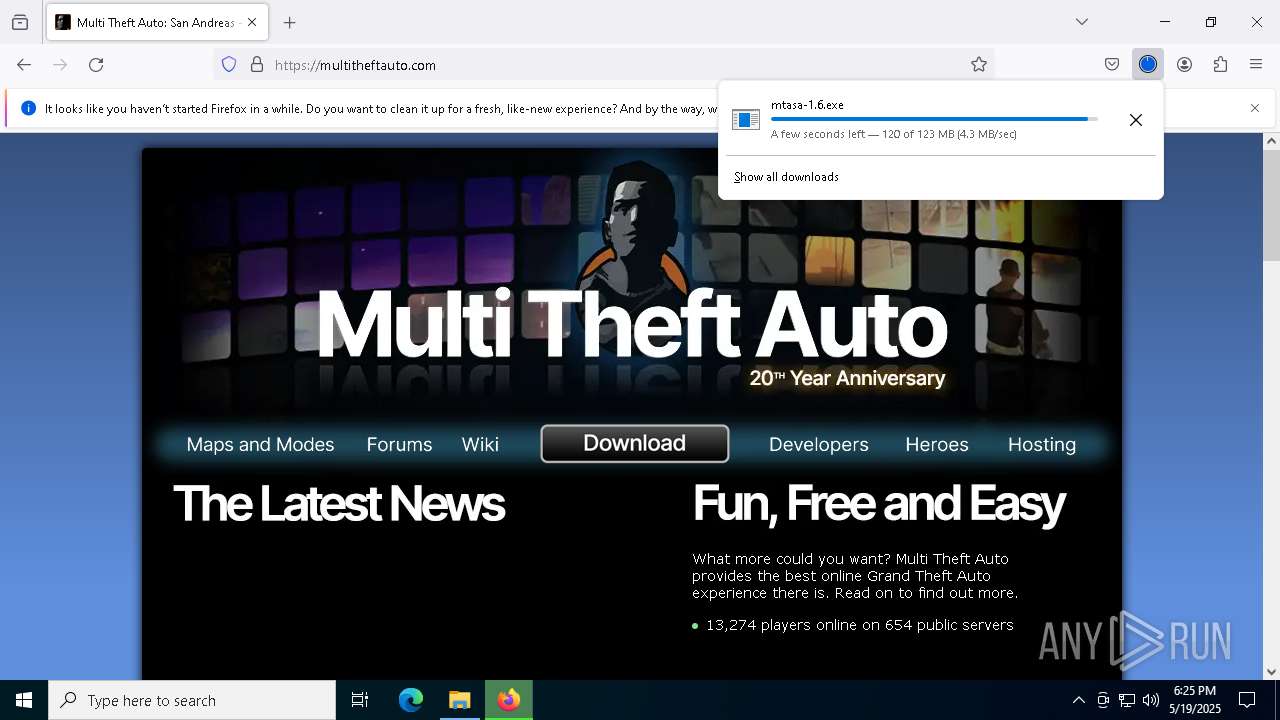
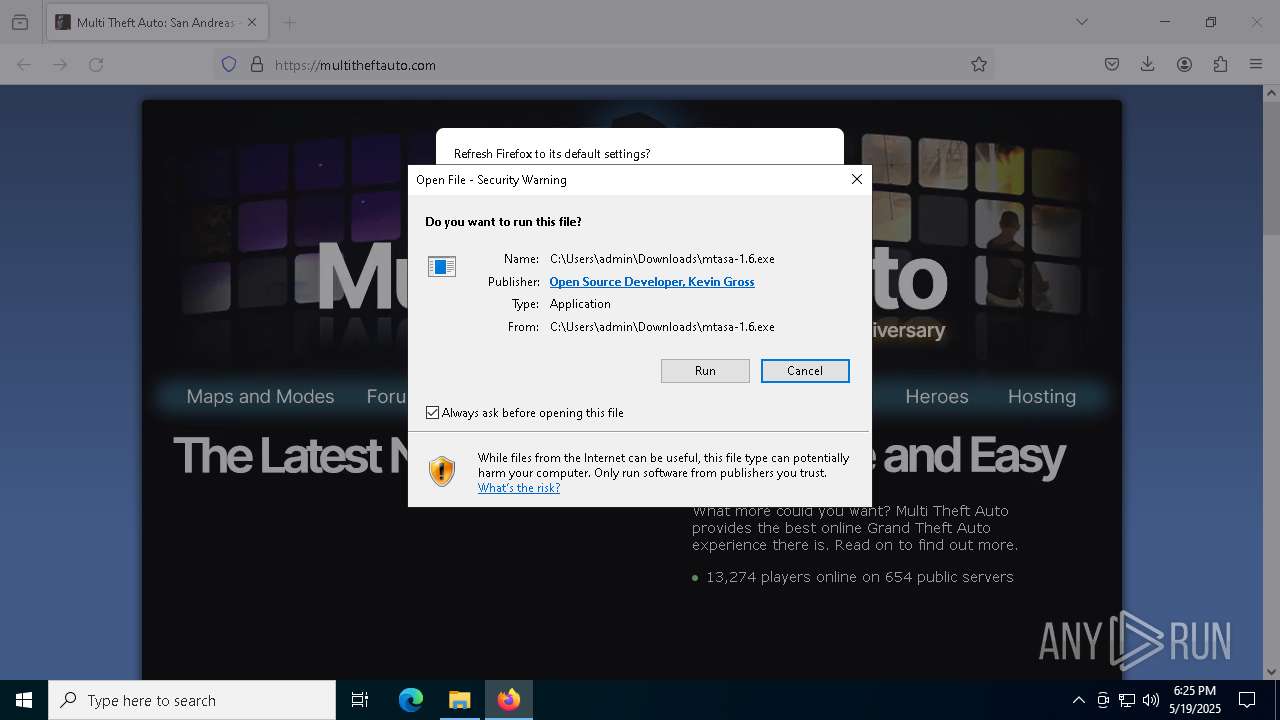
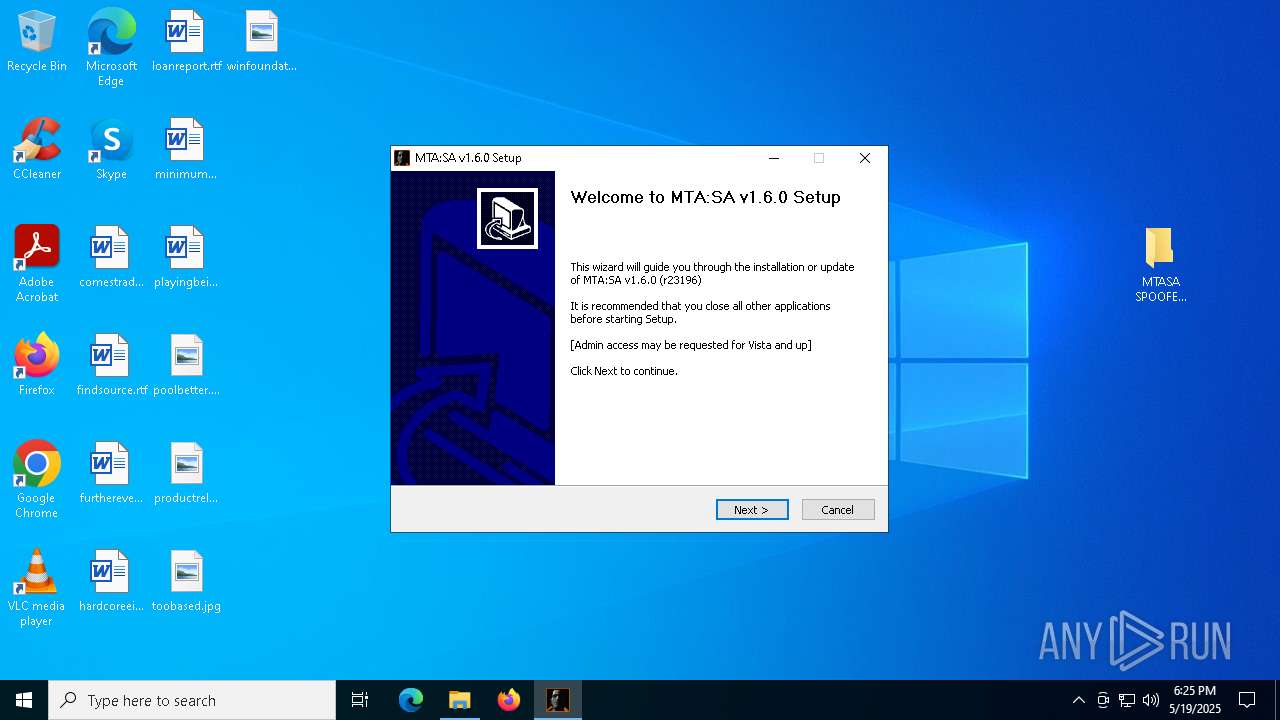
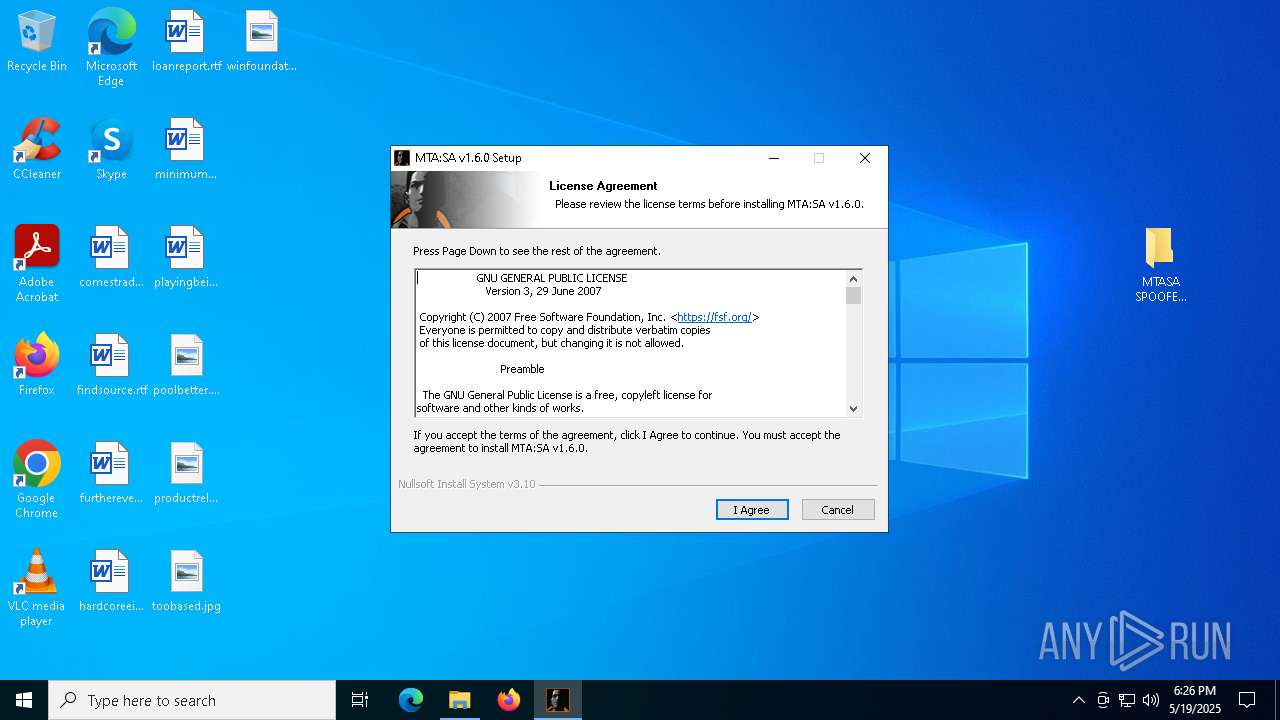
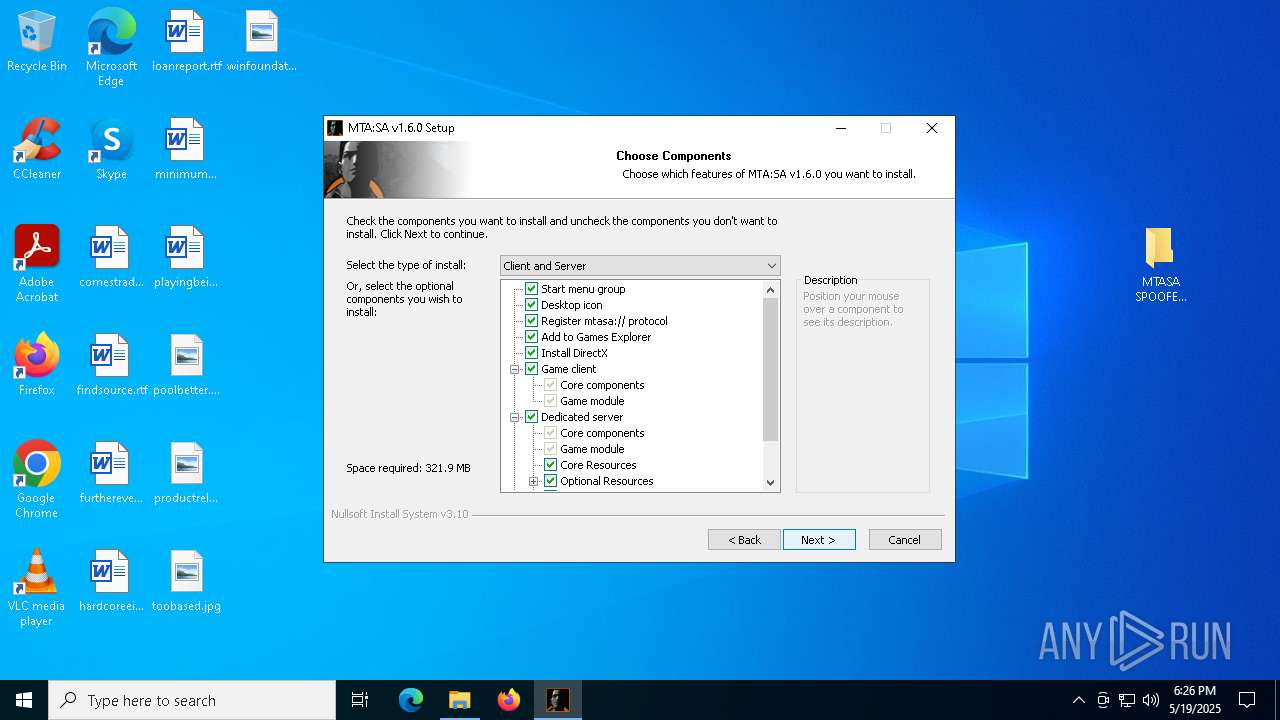
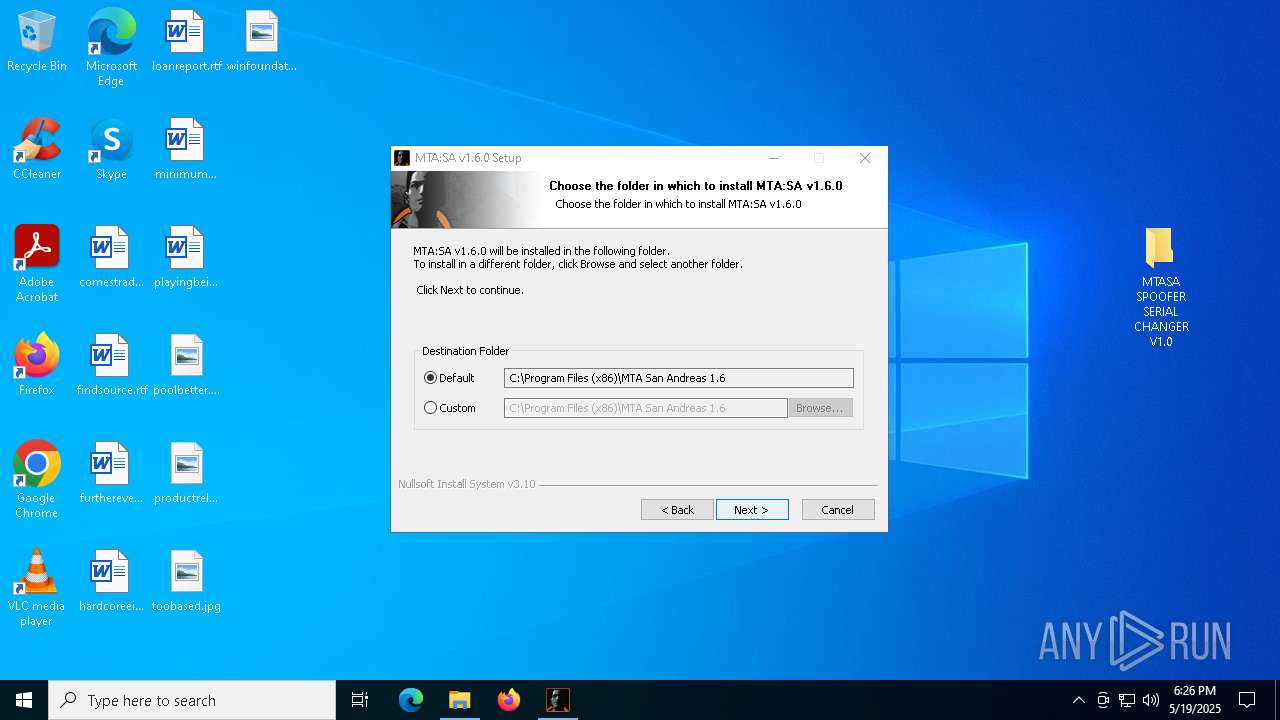
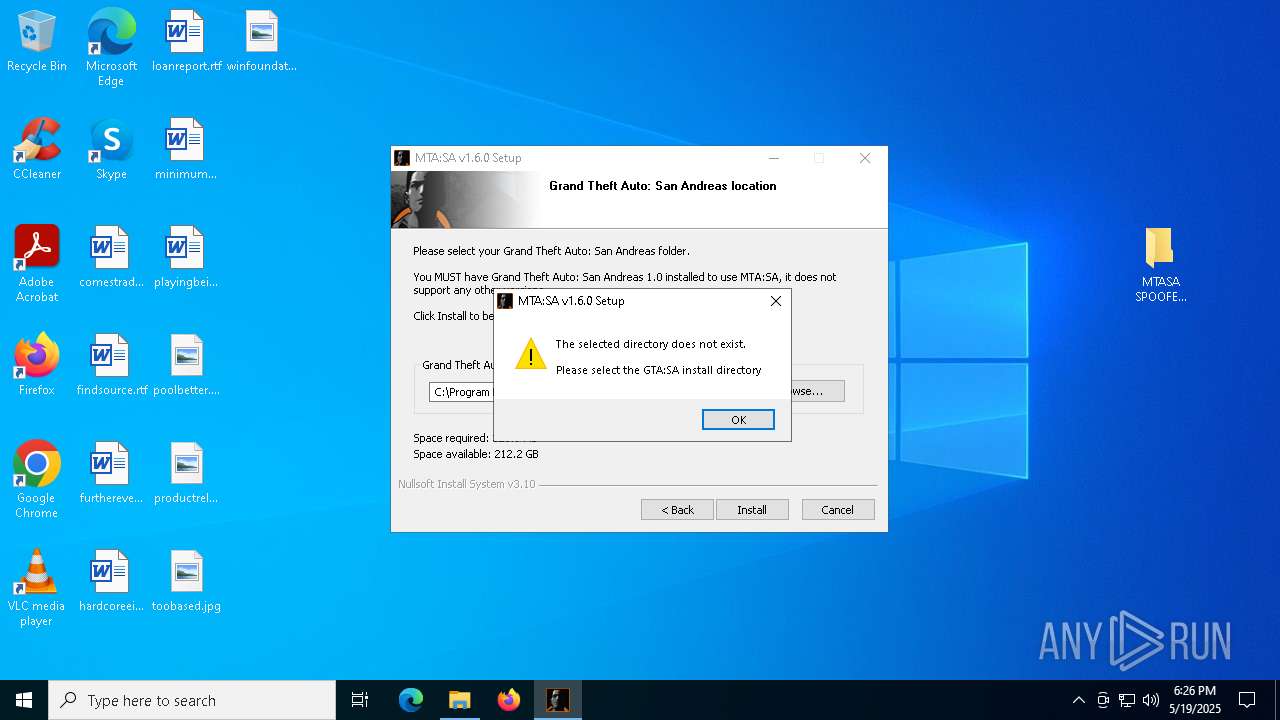
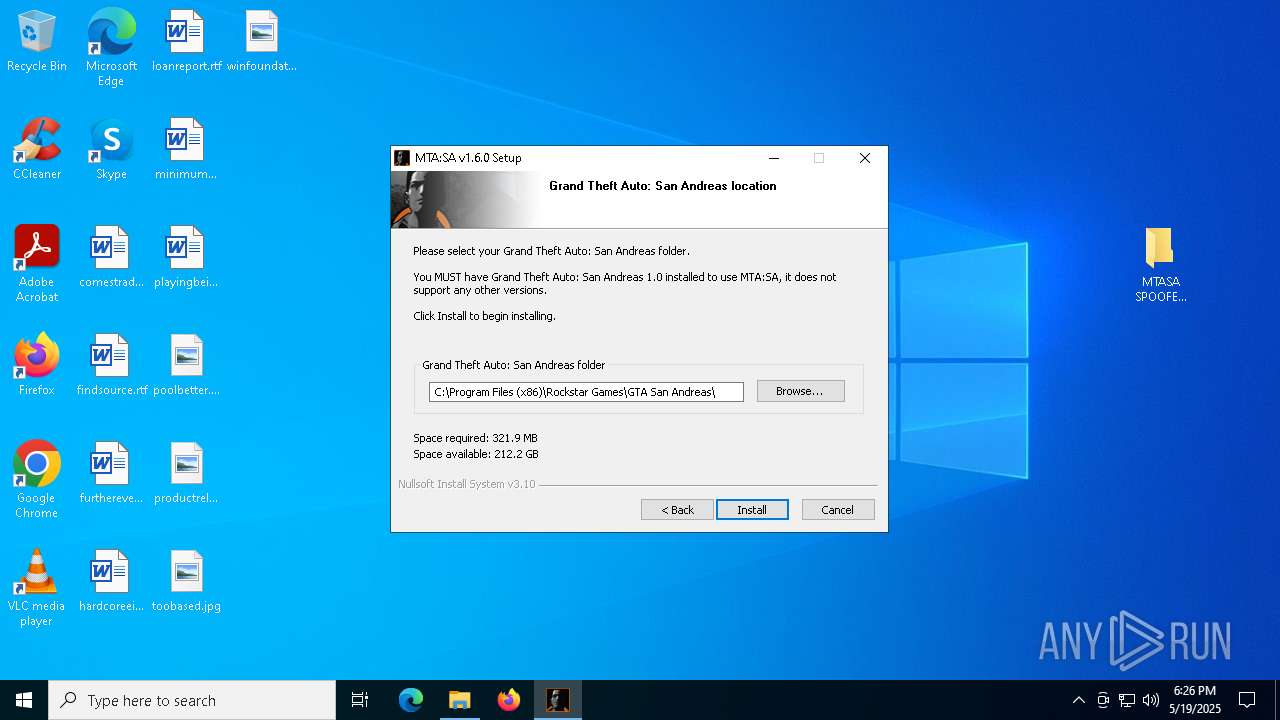
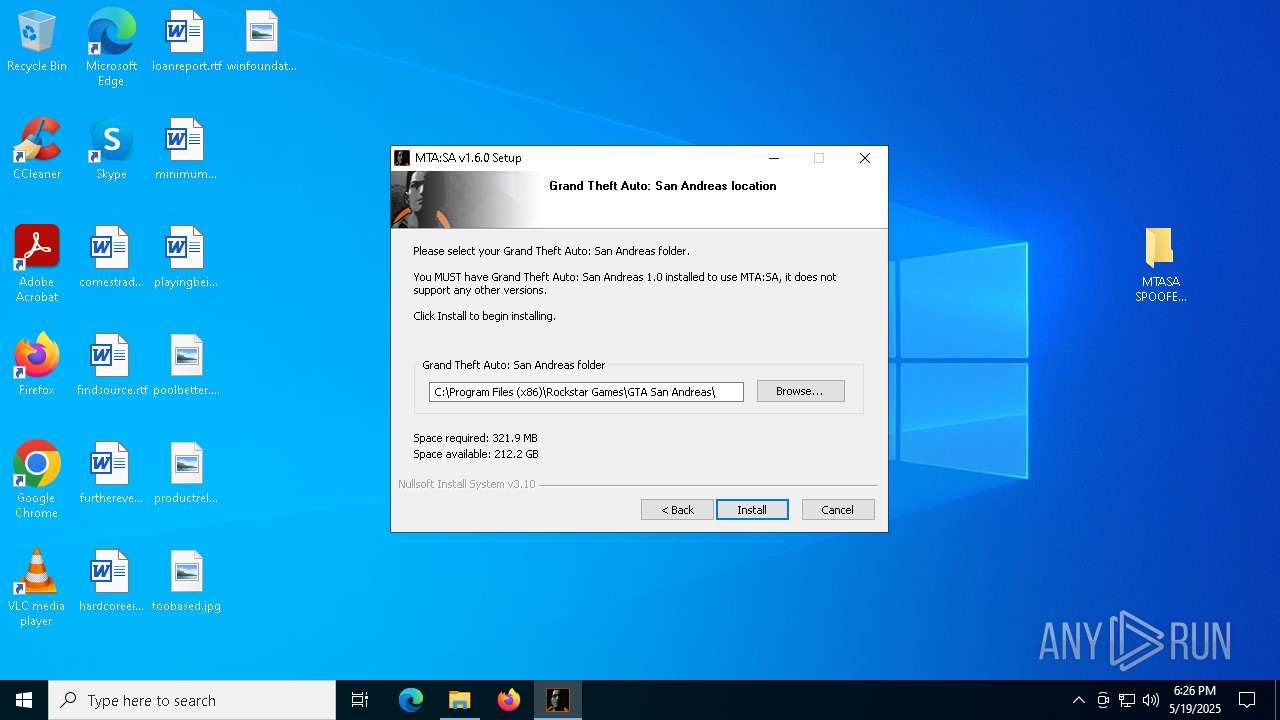
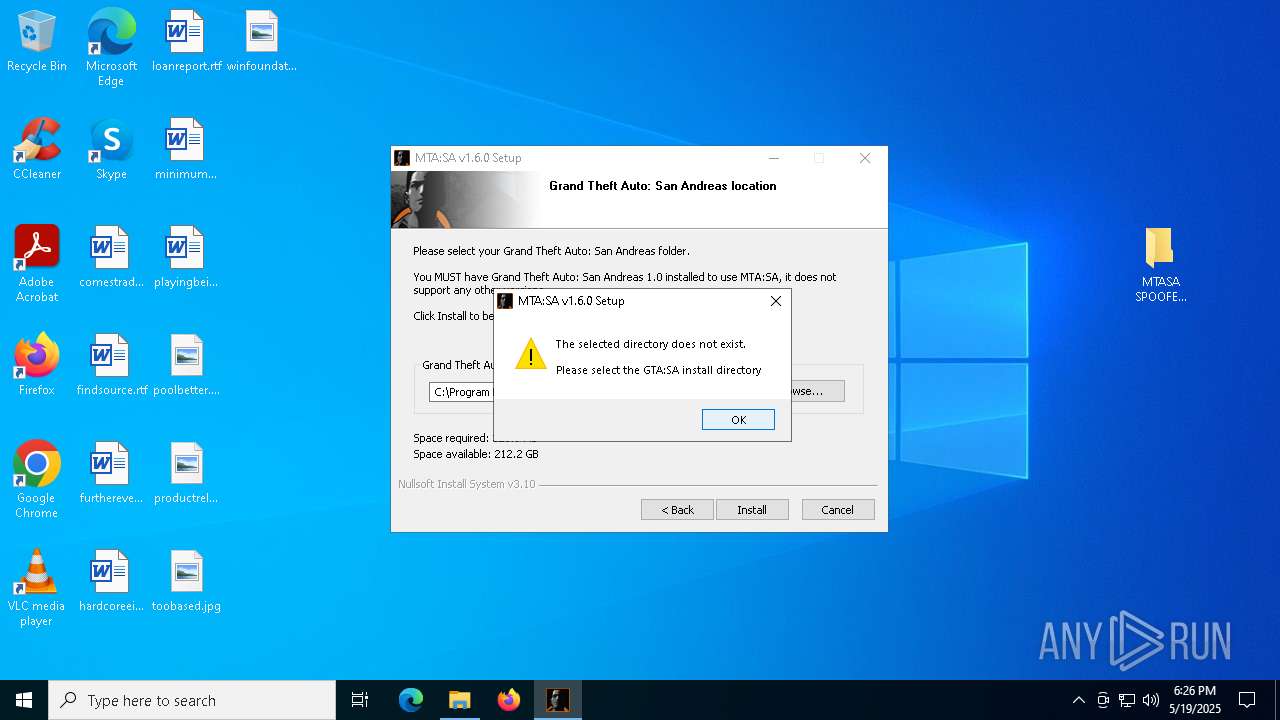
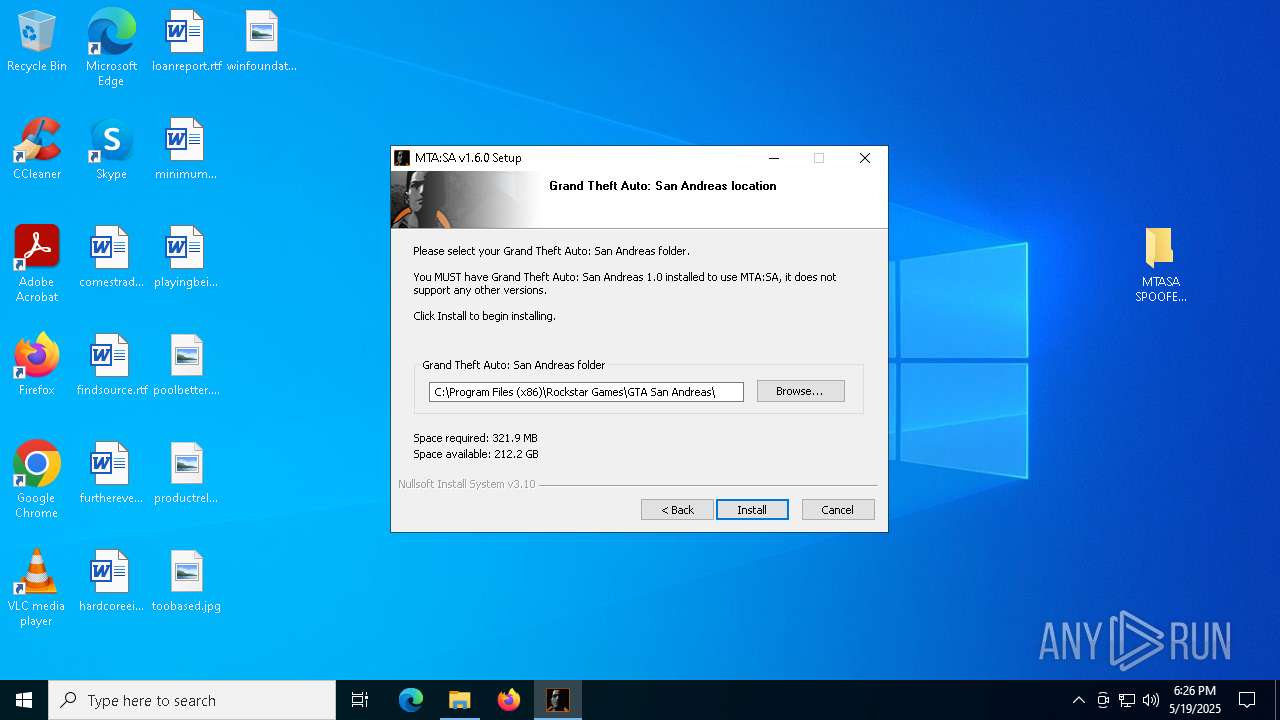
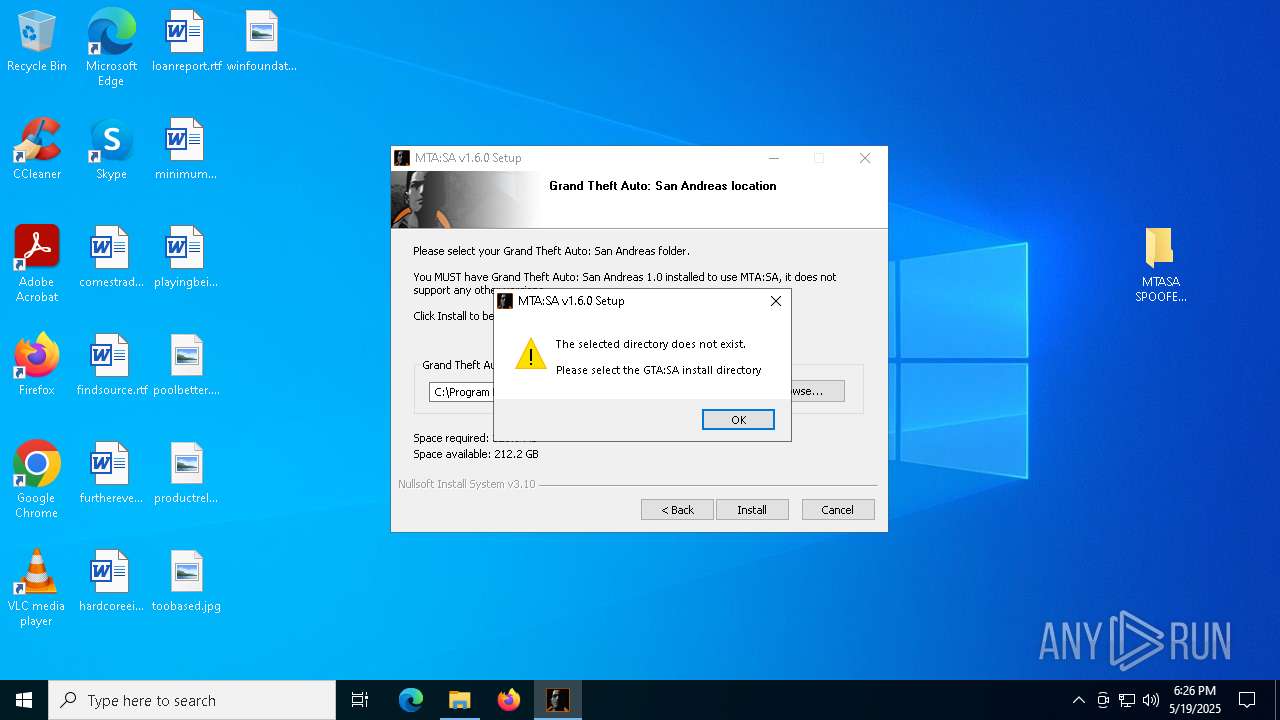
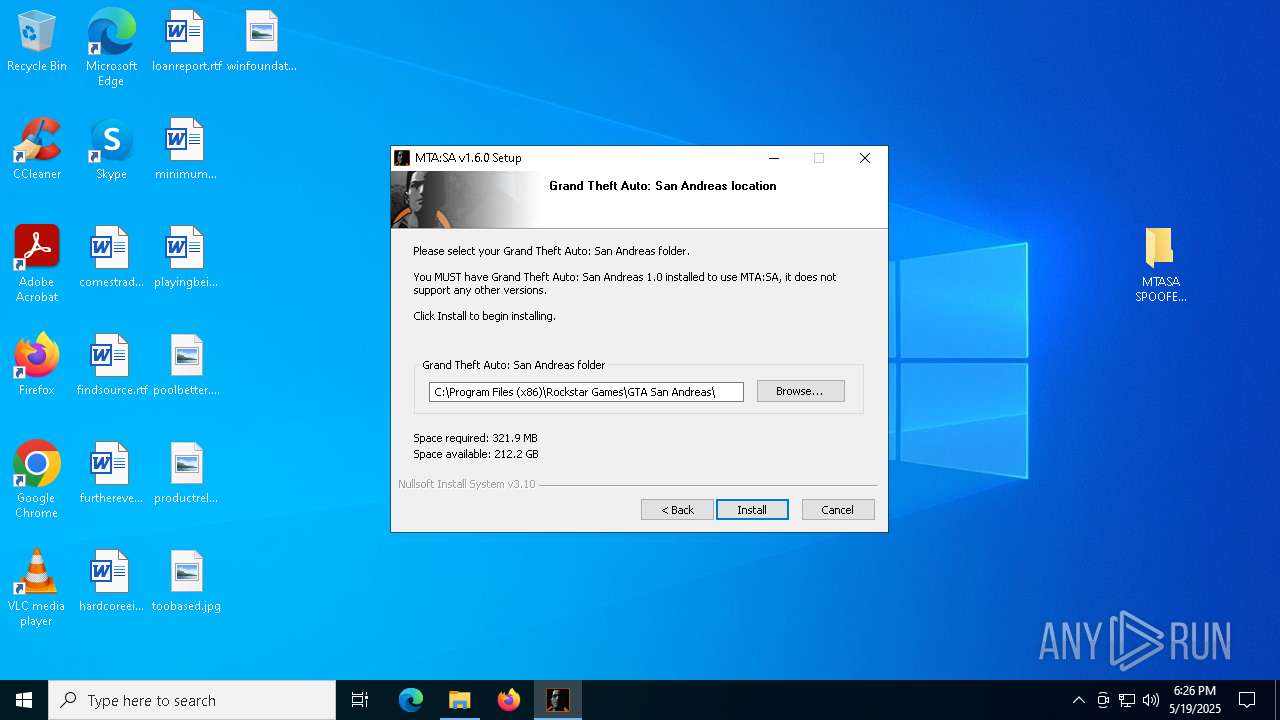
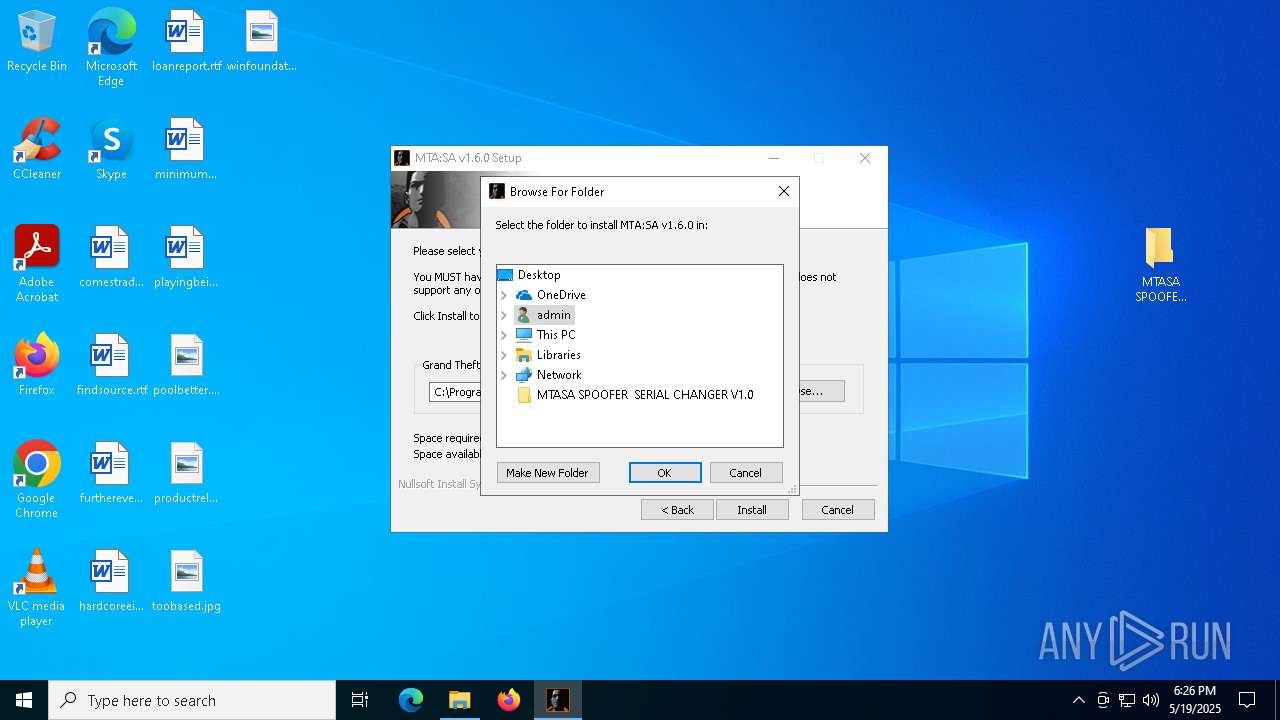
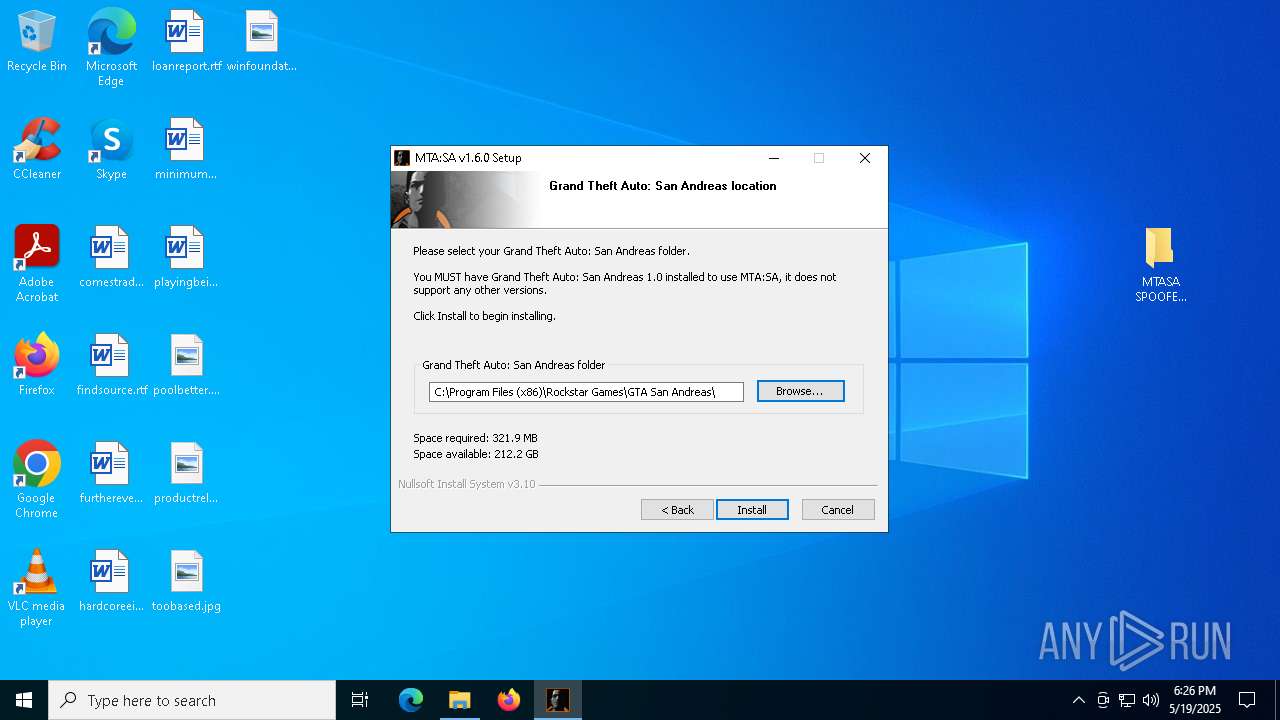
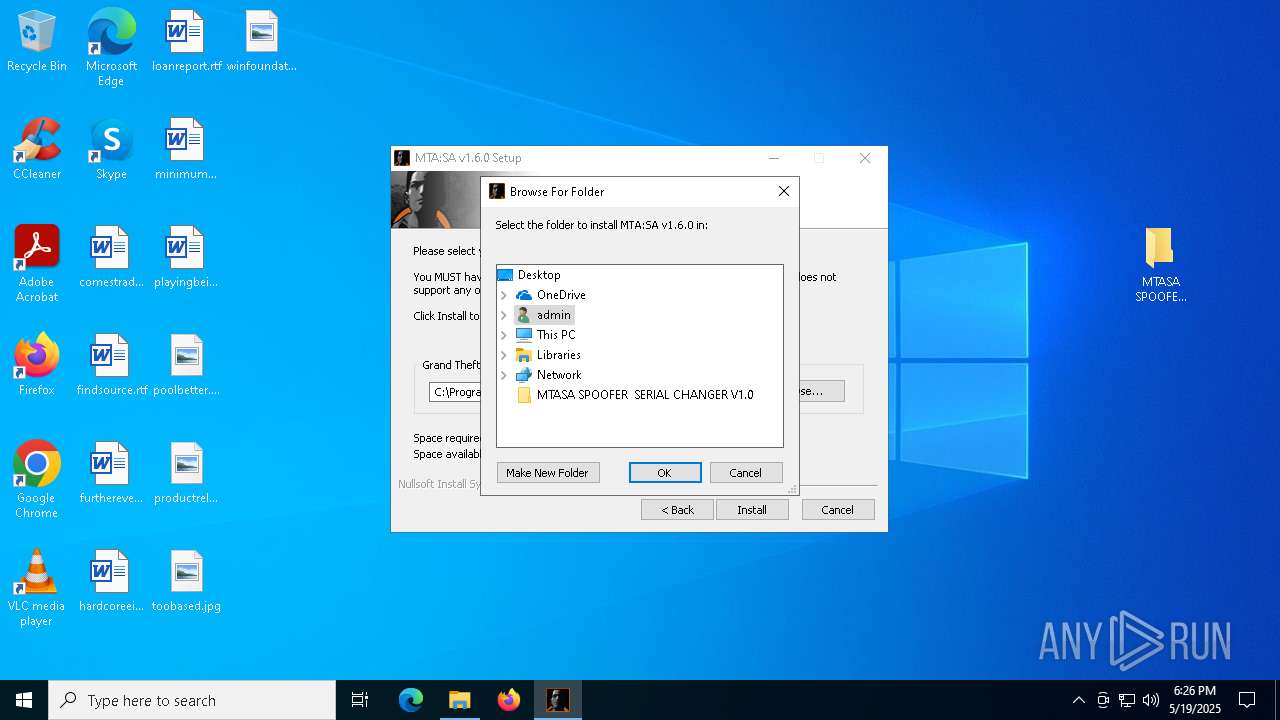
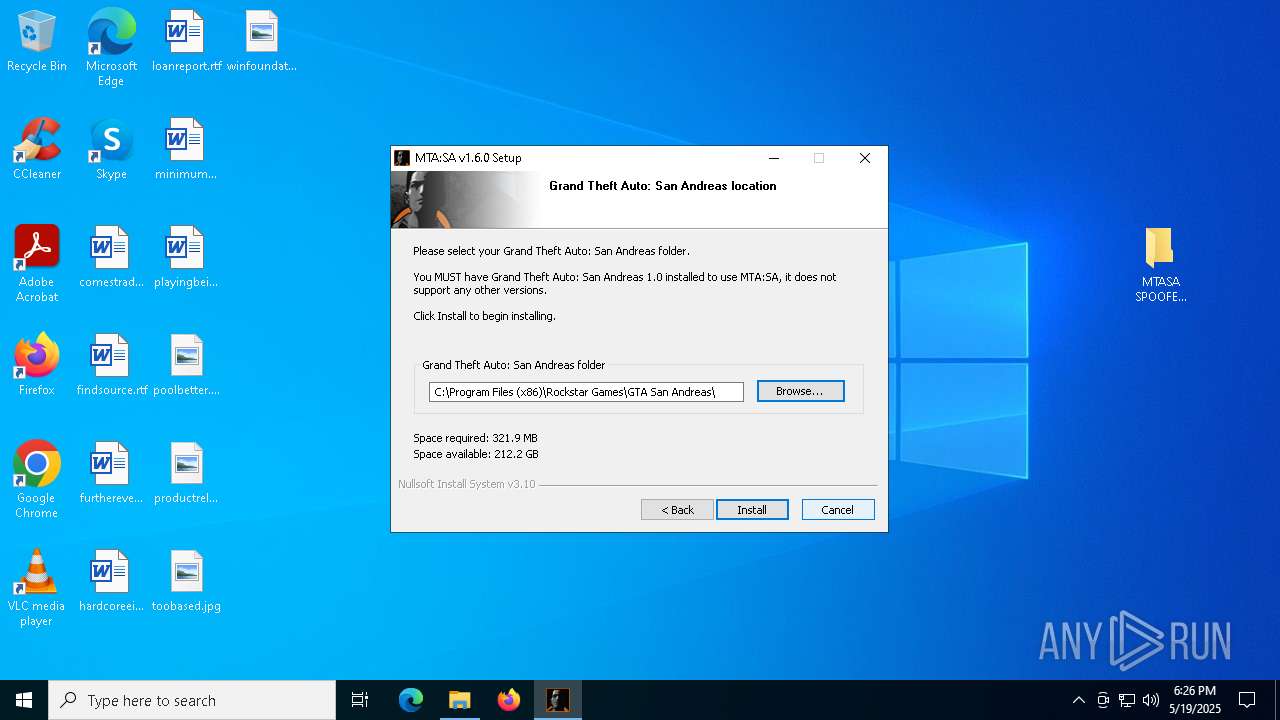
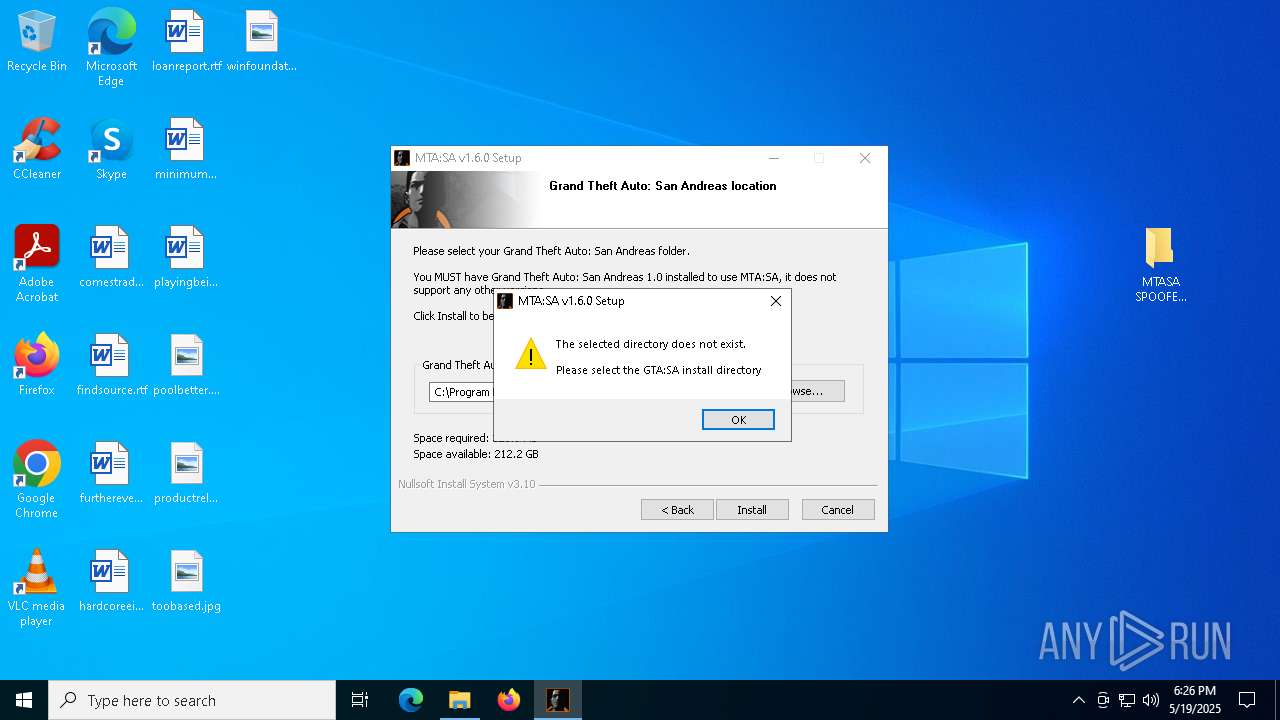
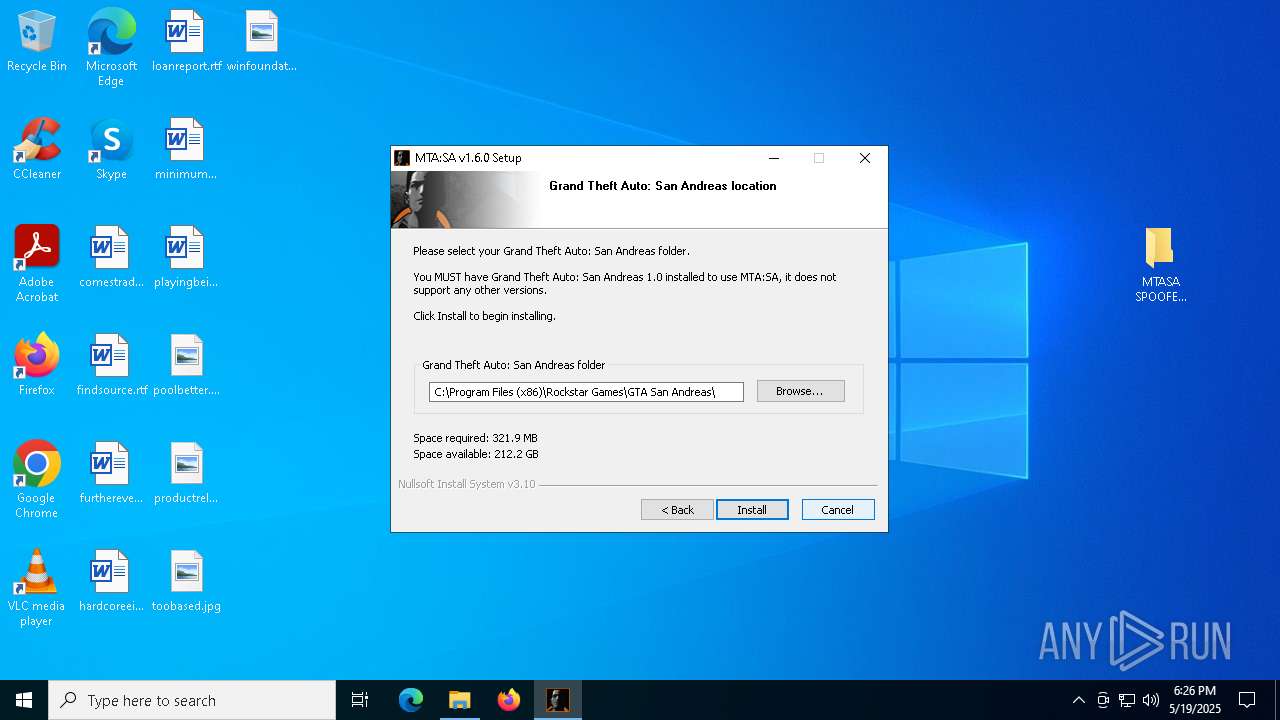
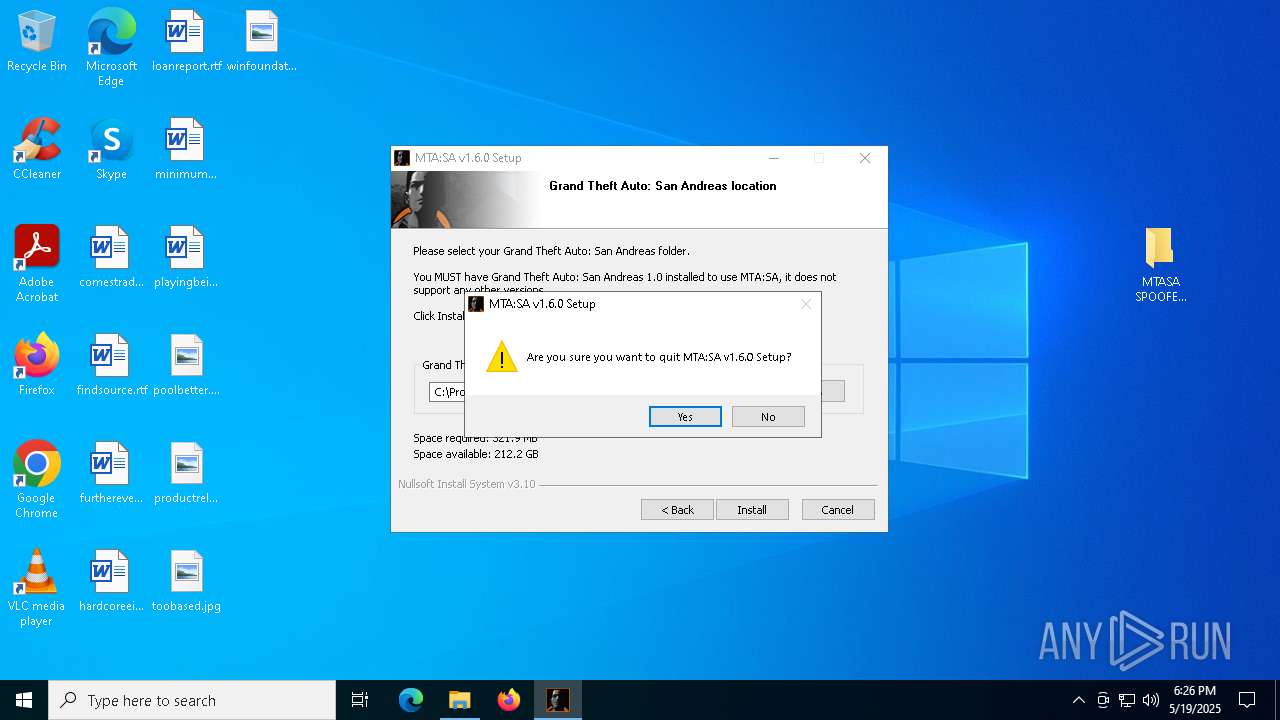
- mtasa-1.6.exe (PID: 7452)
- mtasa-1.6.exe (PID: 4728)
There is functionality for taking screenshot (YARA)
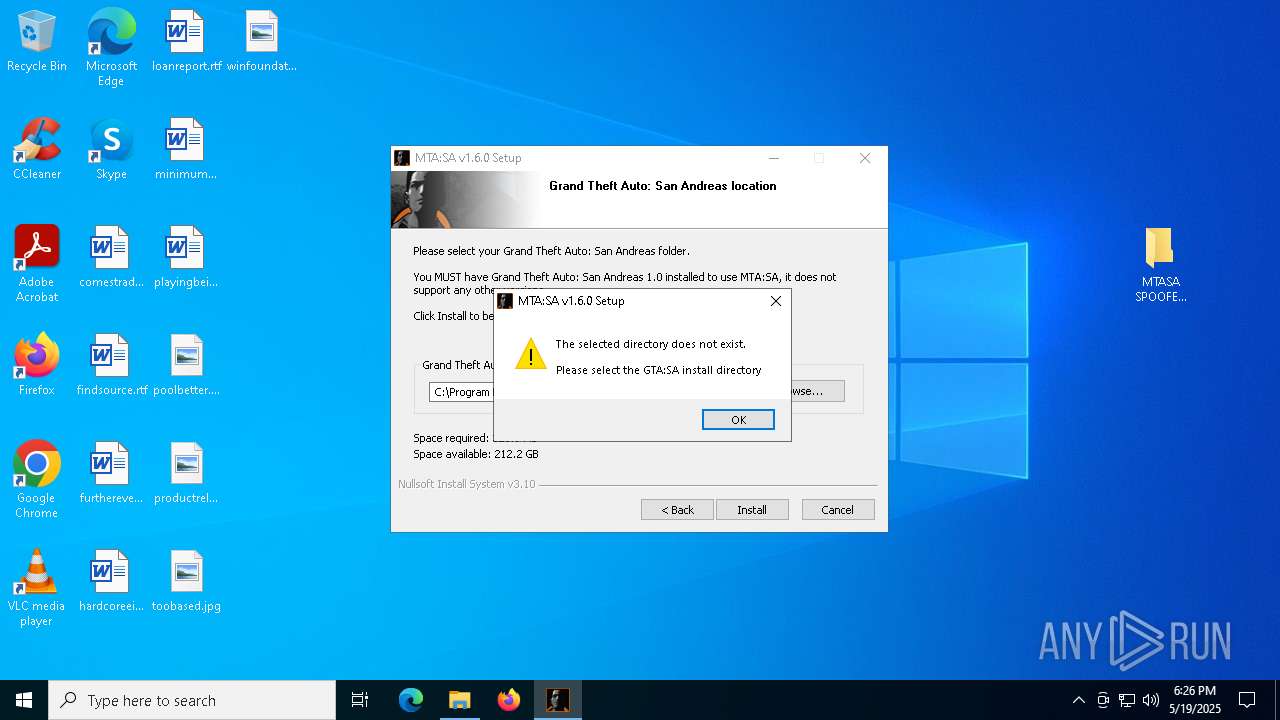
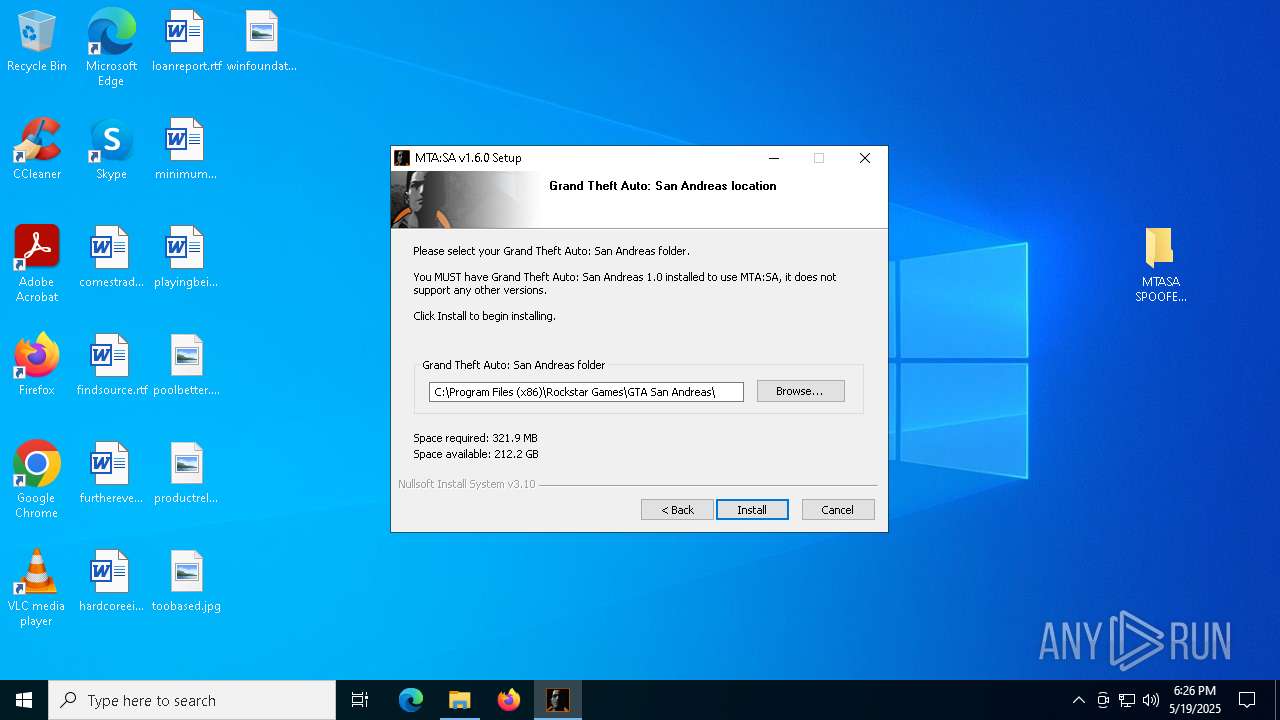
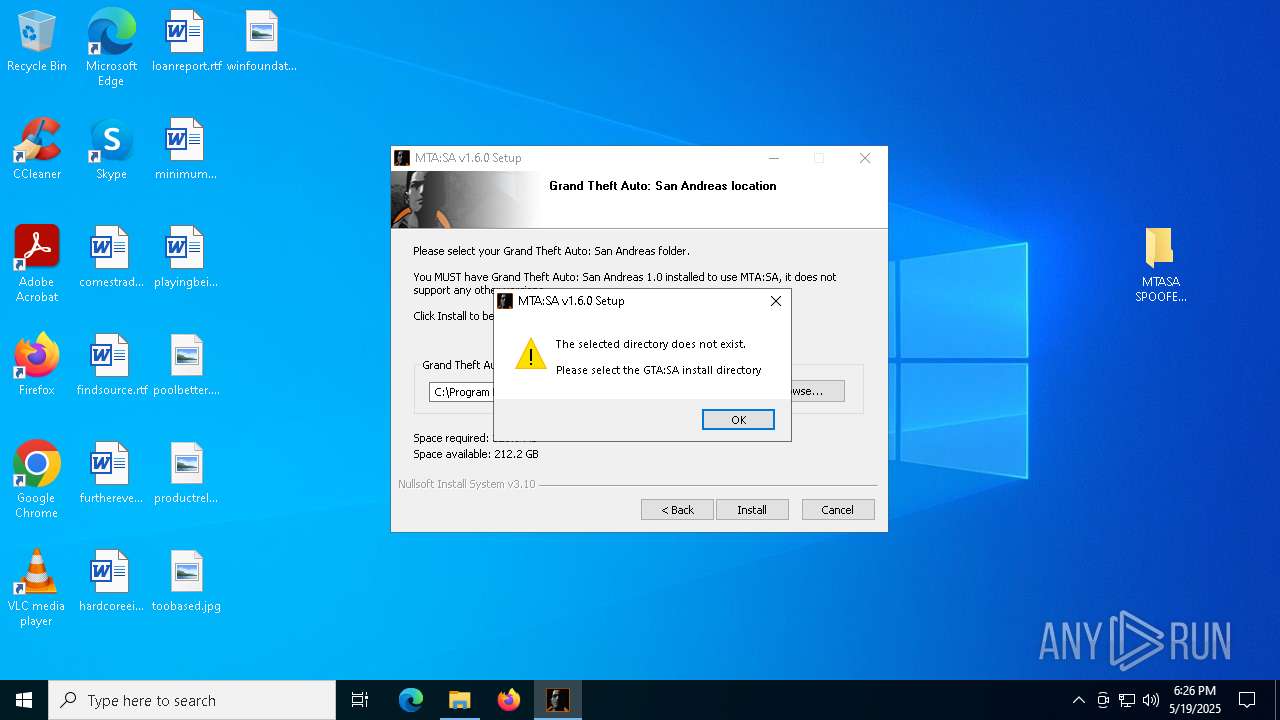
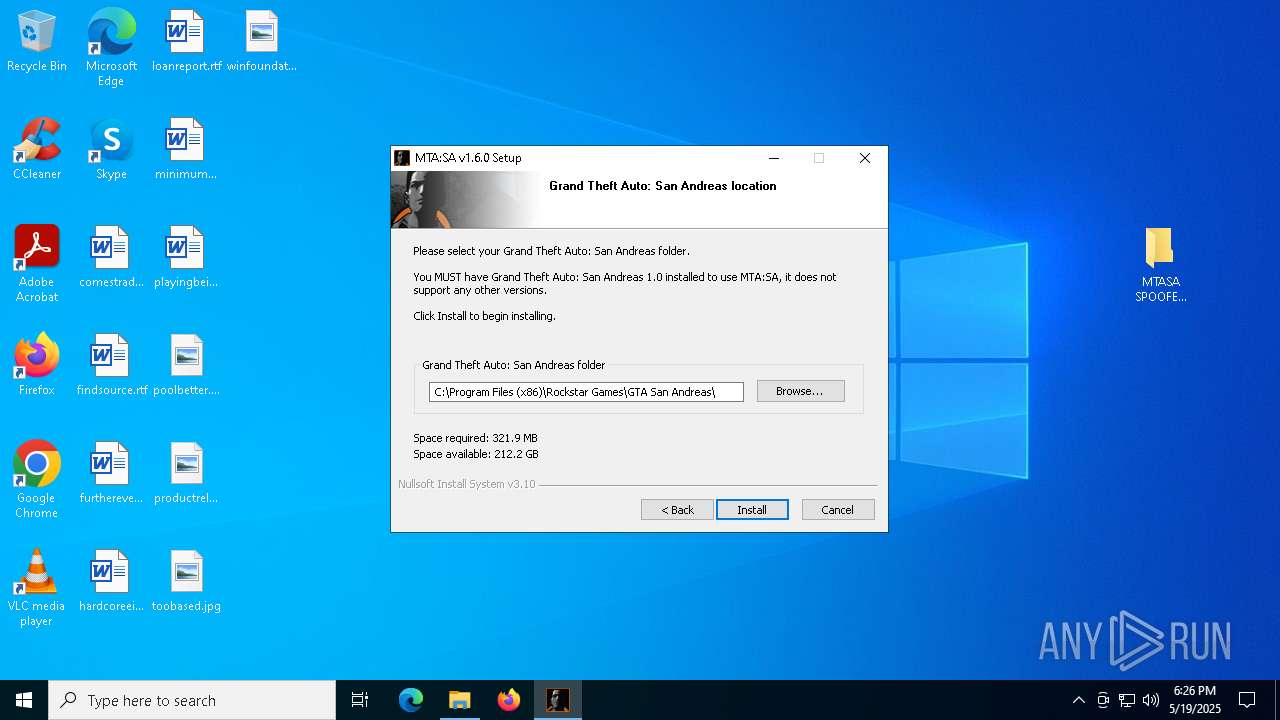
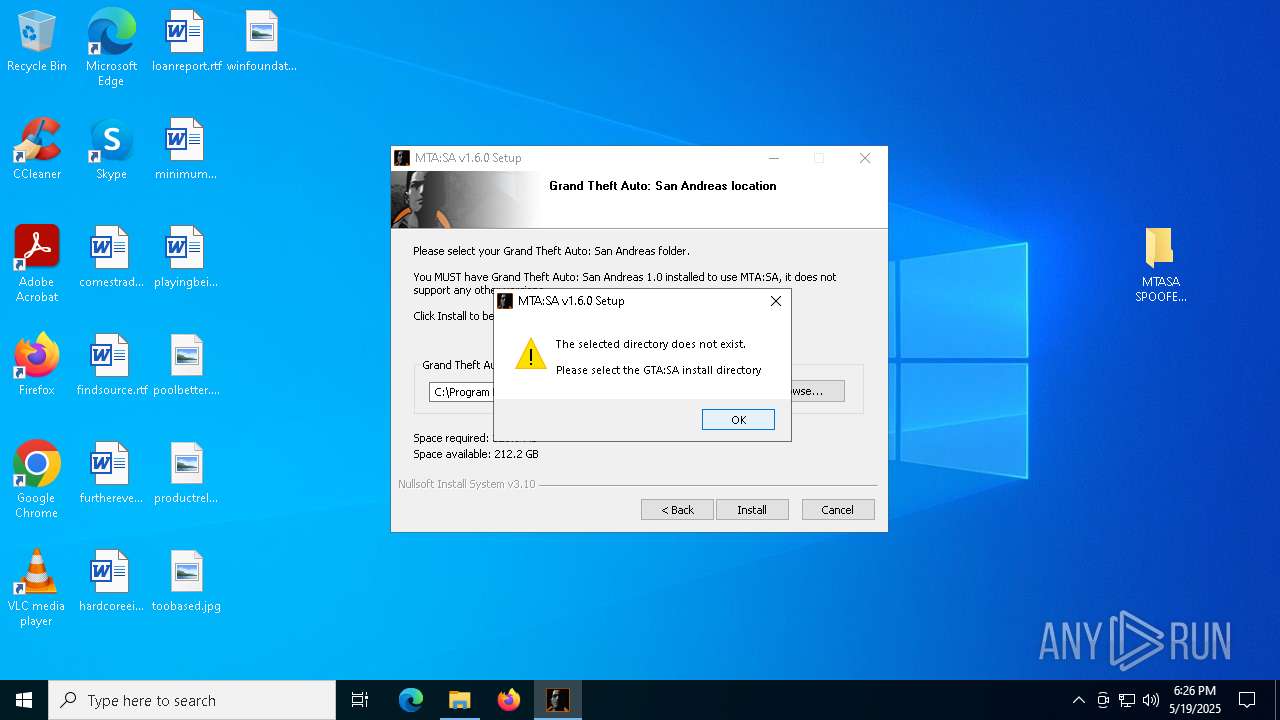
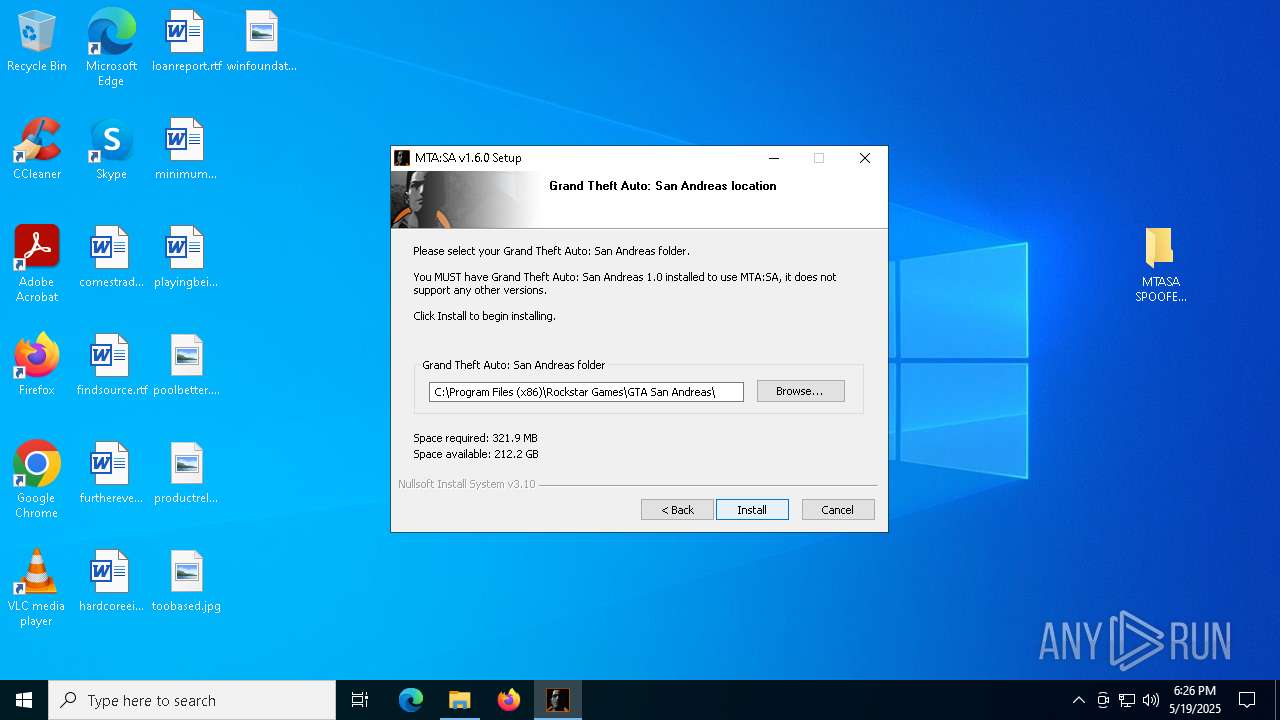
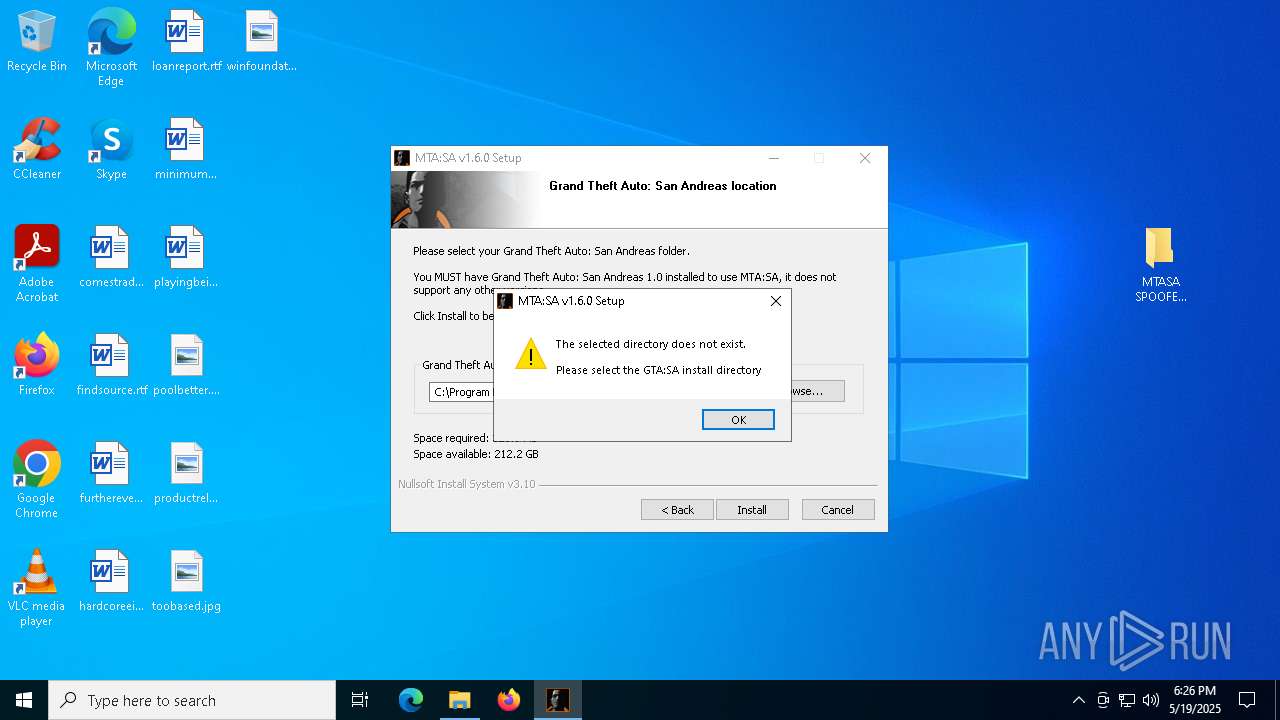
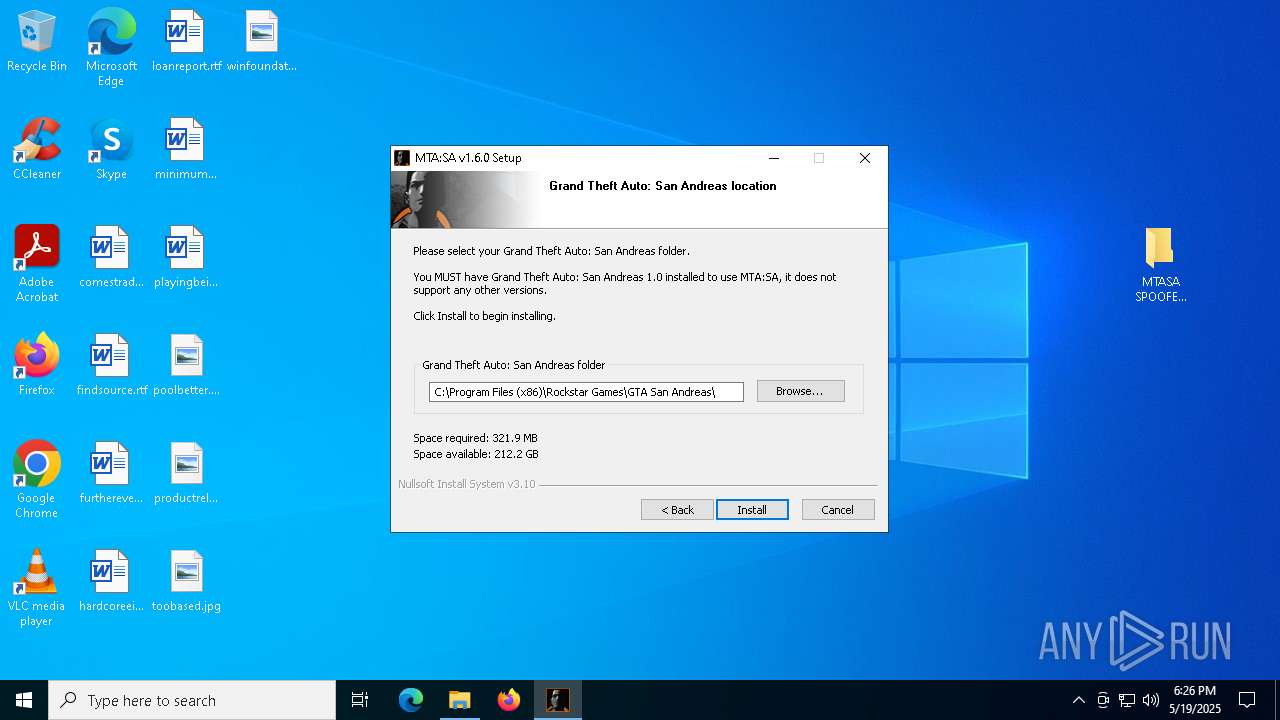
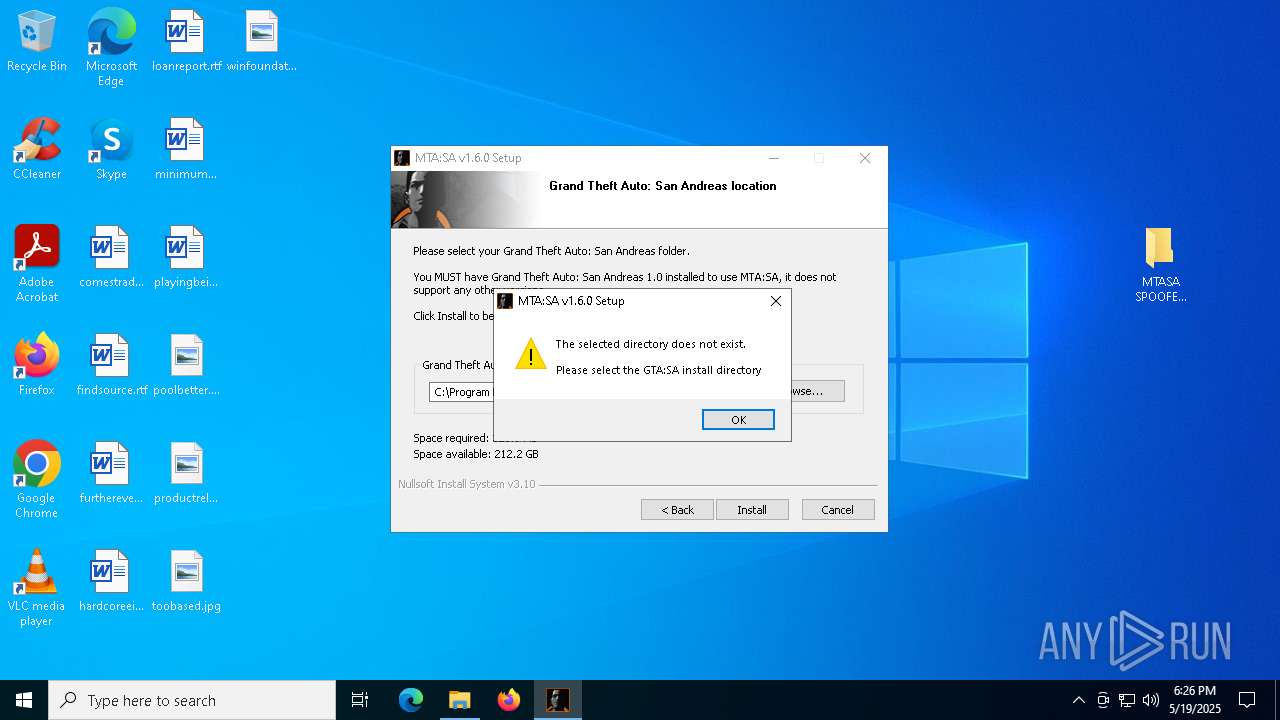
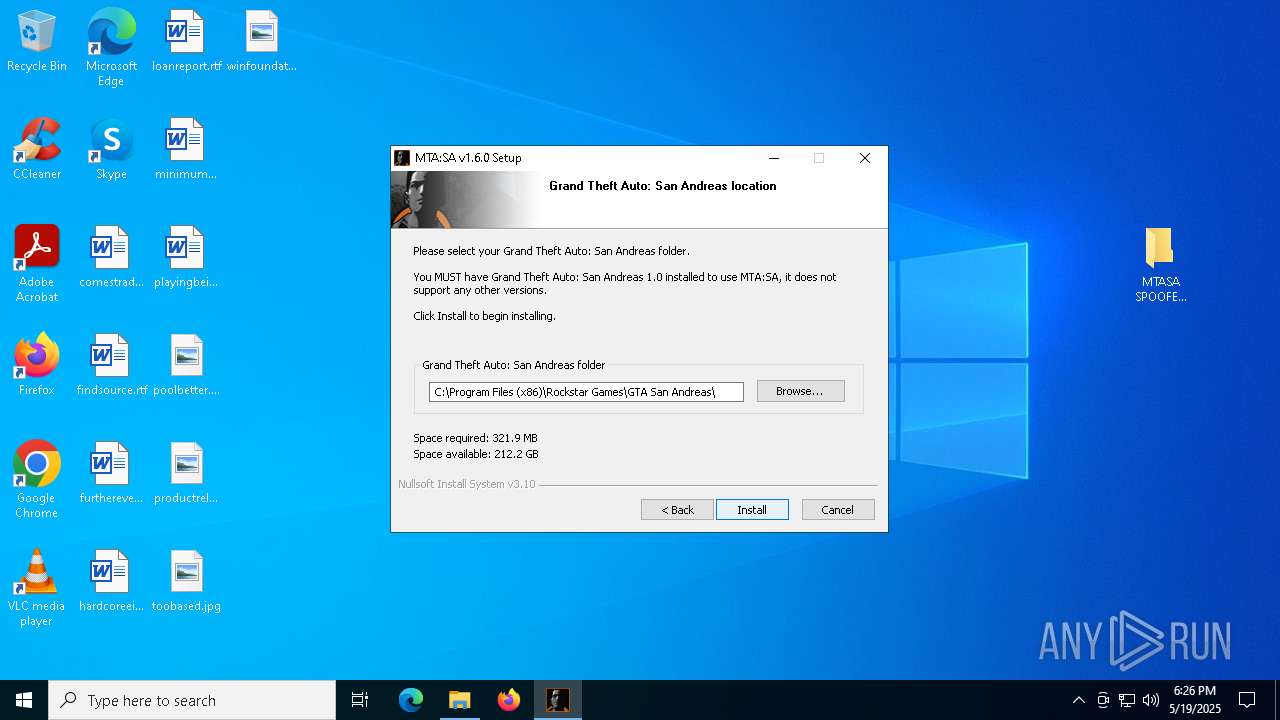
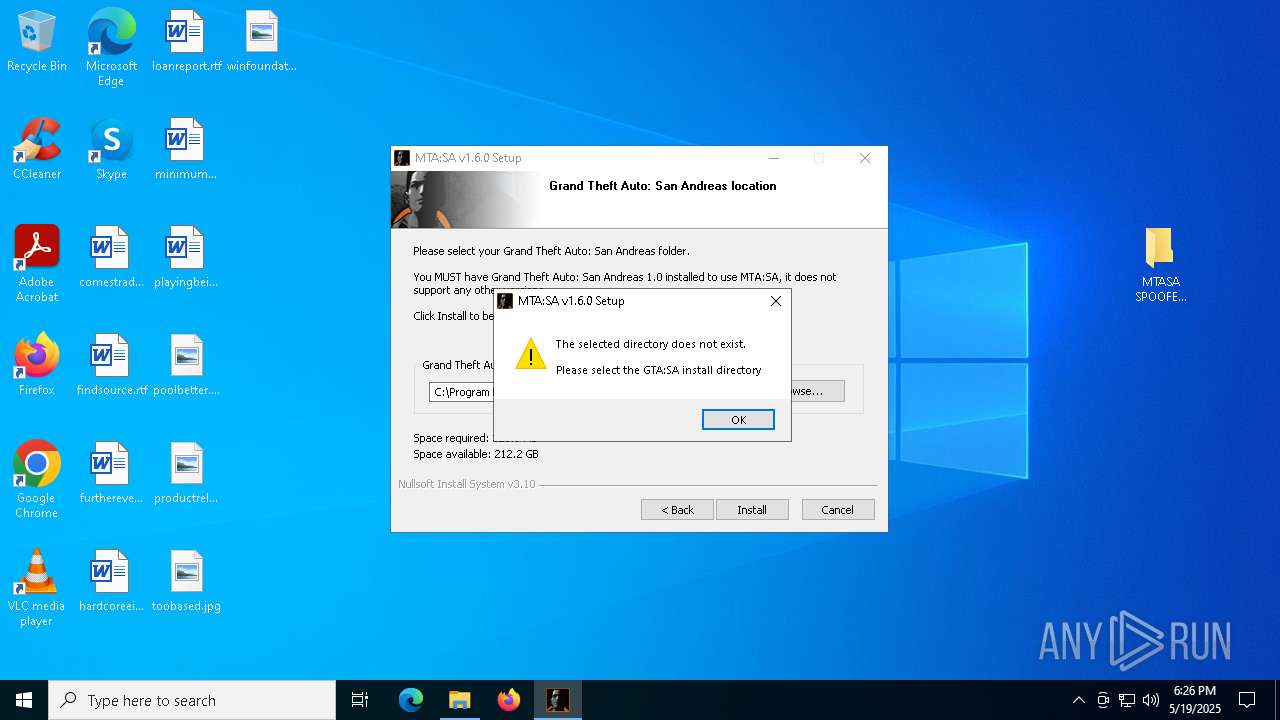
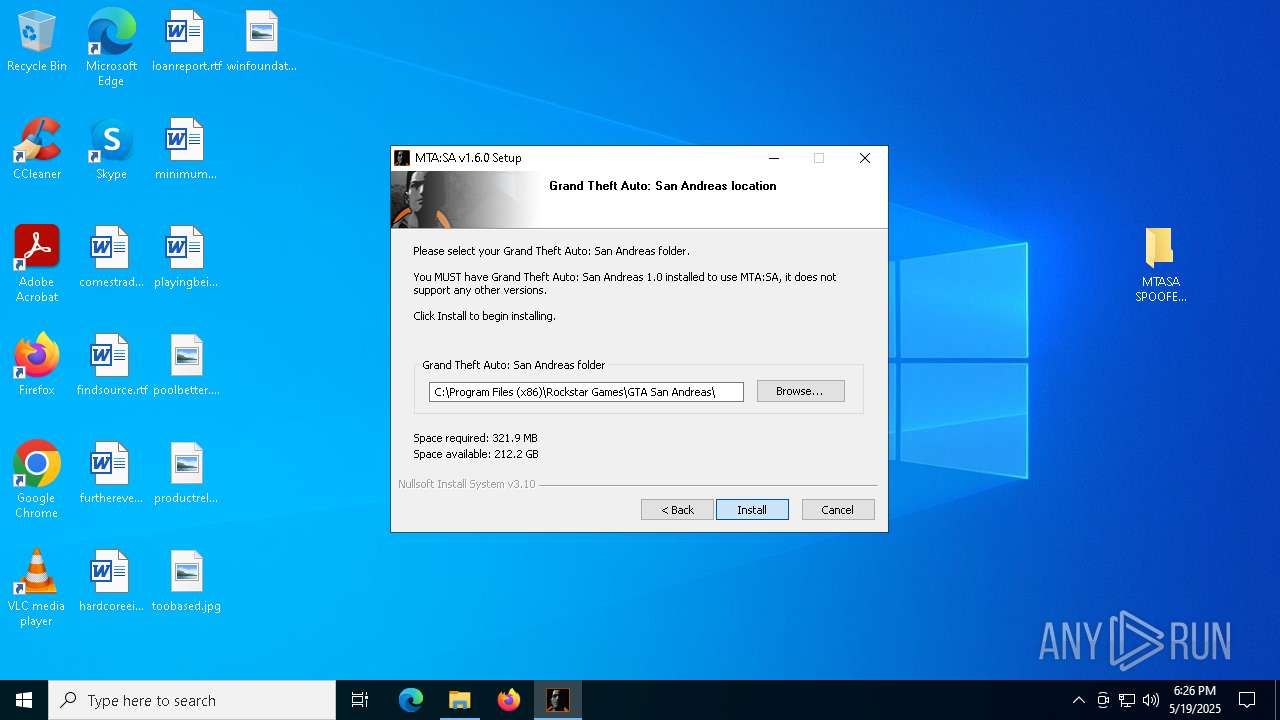
- mtasa-1.6.exe (PID: 7452)
- mtasa-1.6.exe (PID: 4728)
Application launched itself
- mtasa-1.6.exe (PID: 4728)
Malware-specific behavior (creating "System.dll" in Temp)
- mtasa-1.6.exe (PID: 7452)
- mtasa-1.6.exe (PID: 4728)
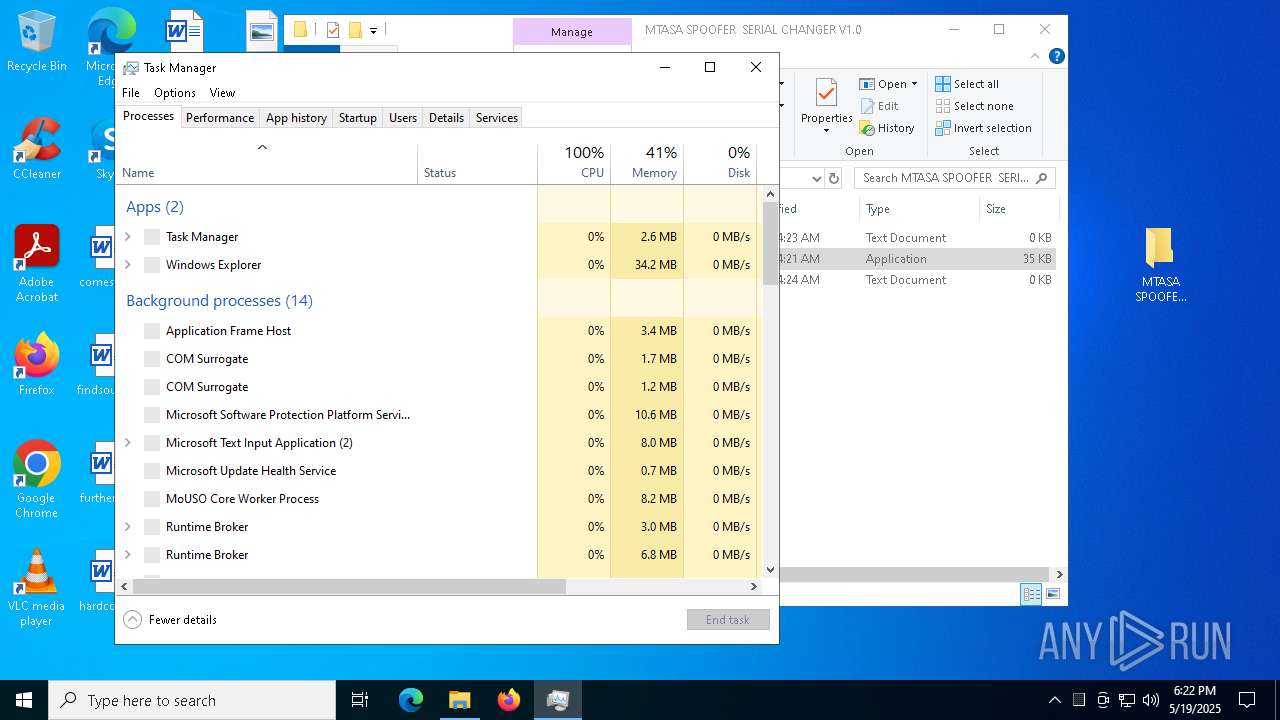
INFO
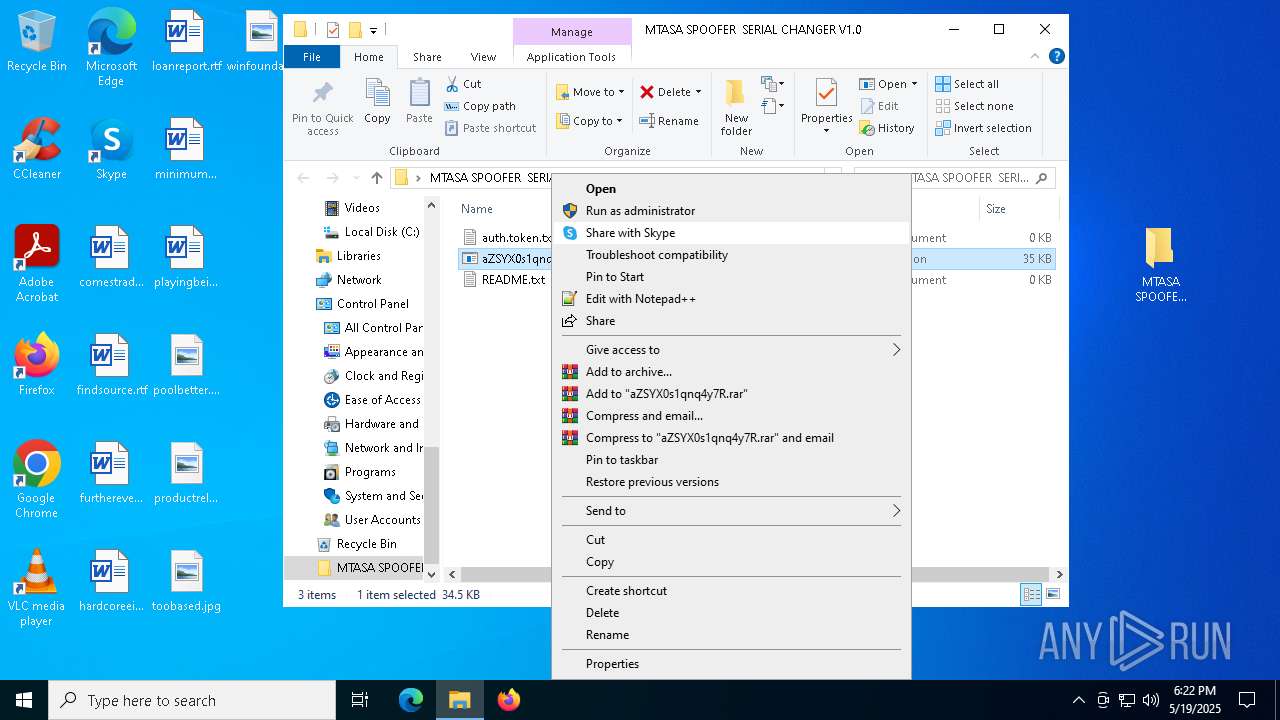
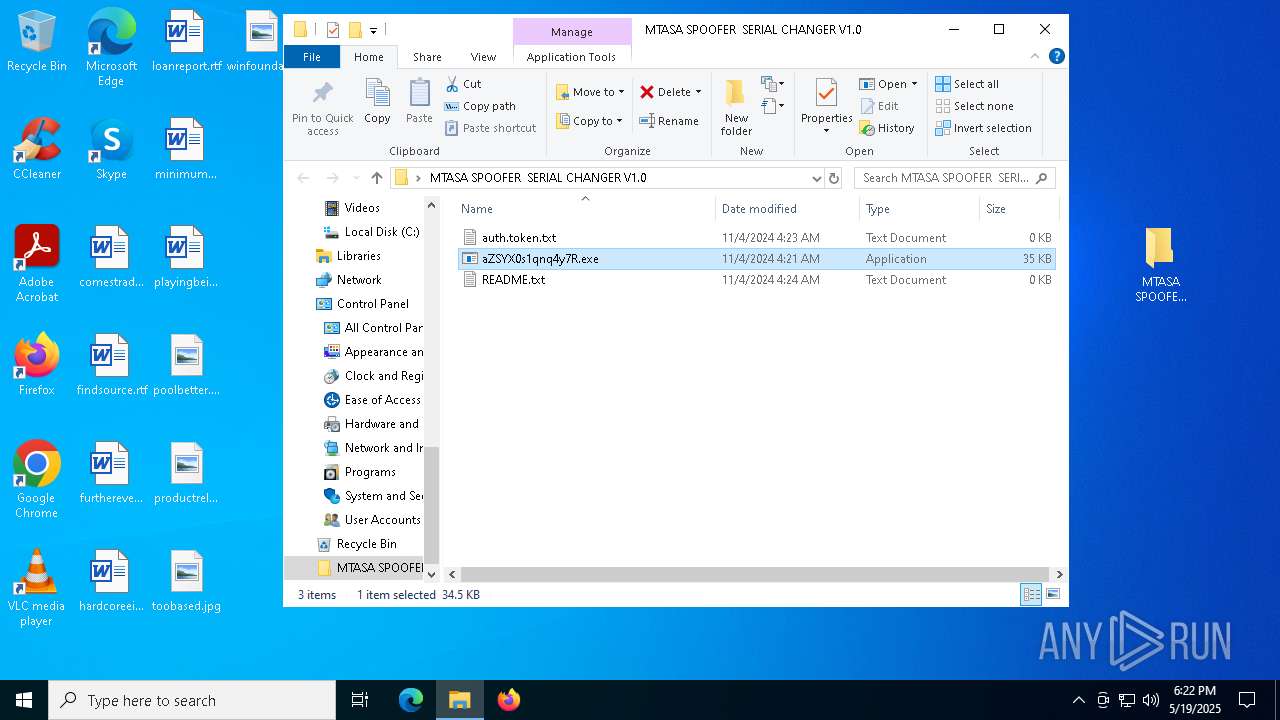
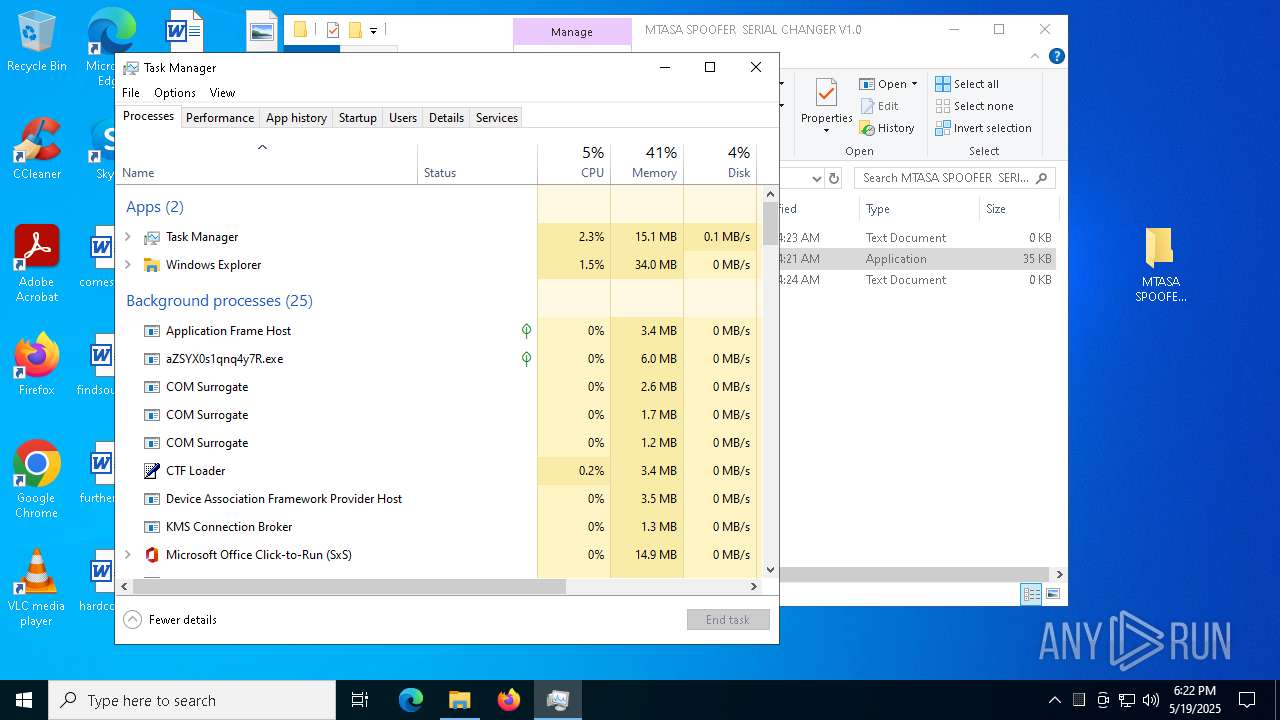
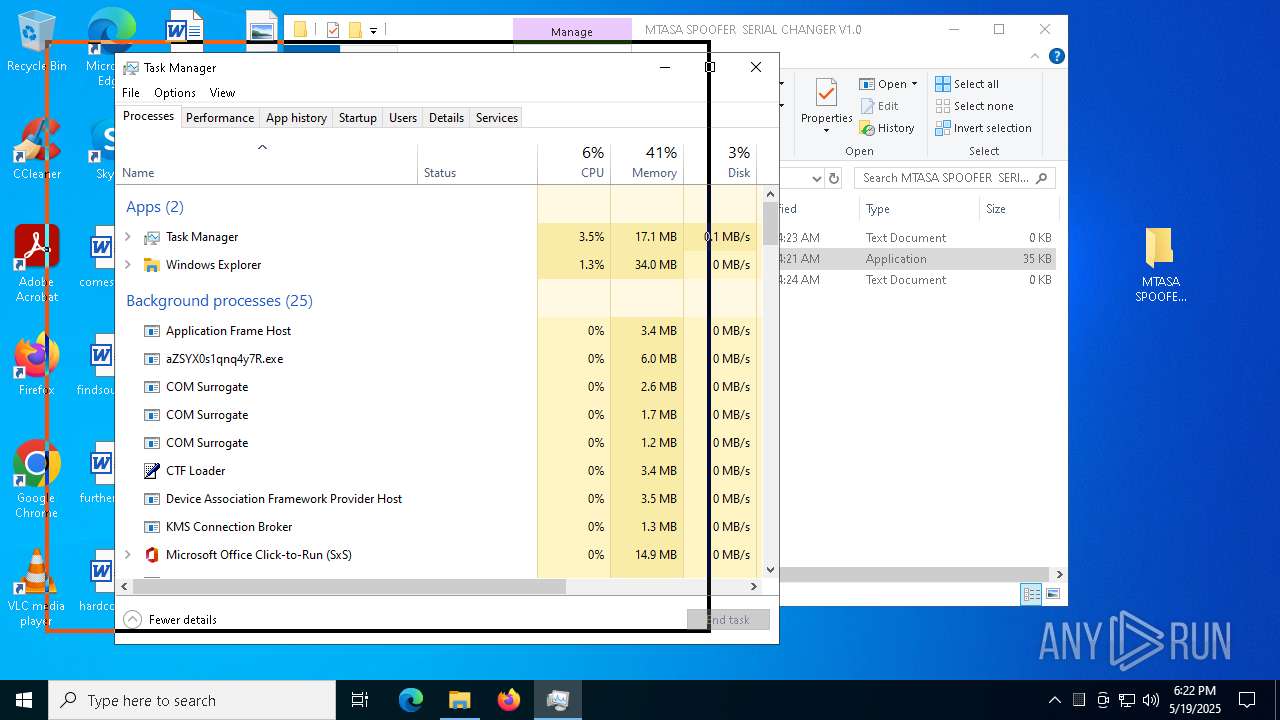
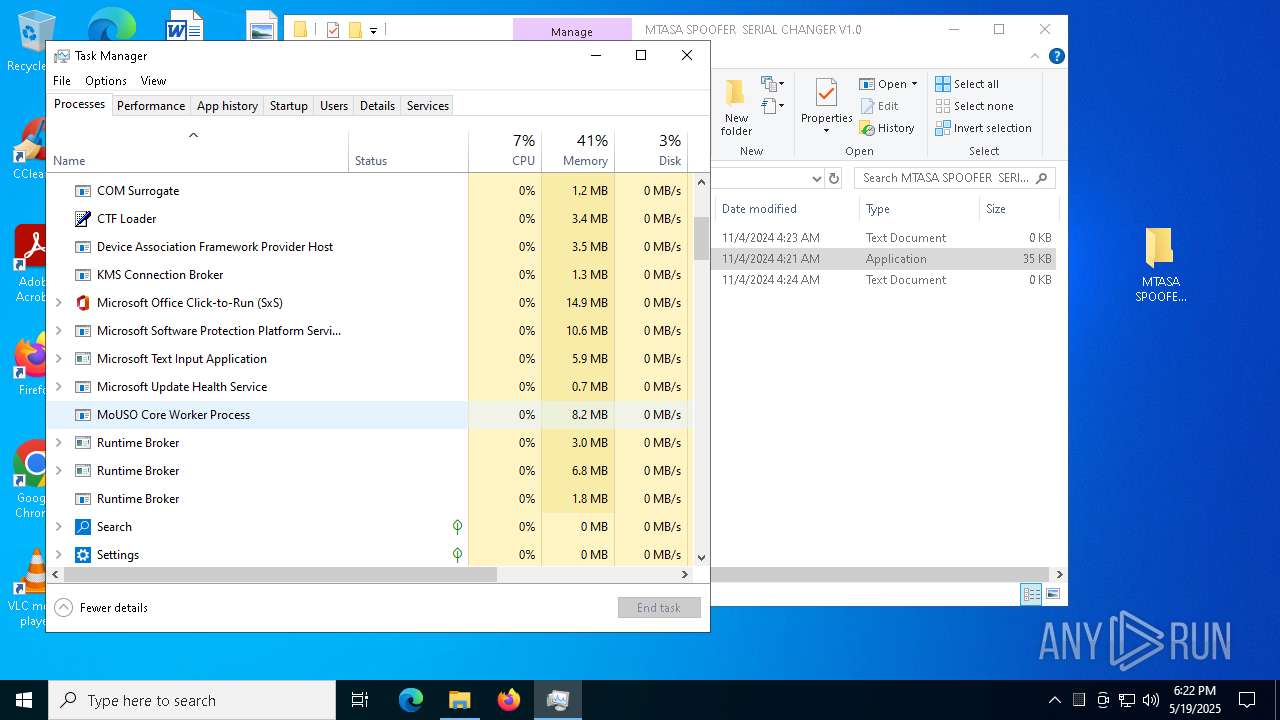
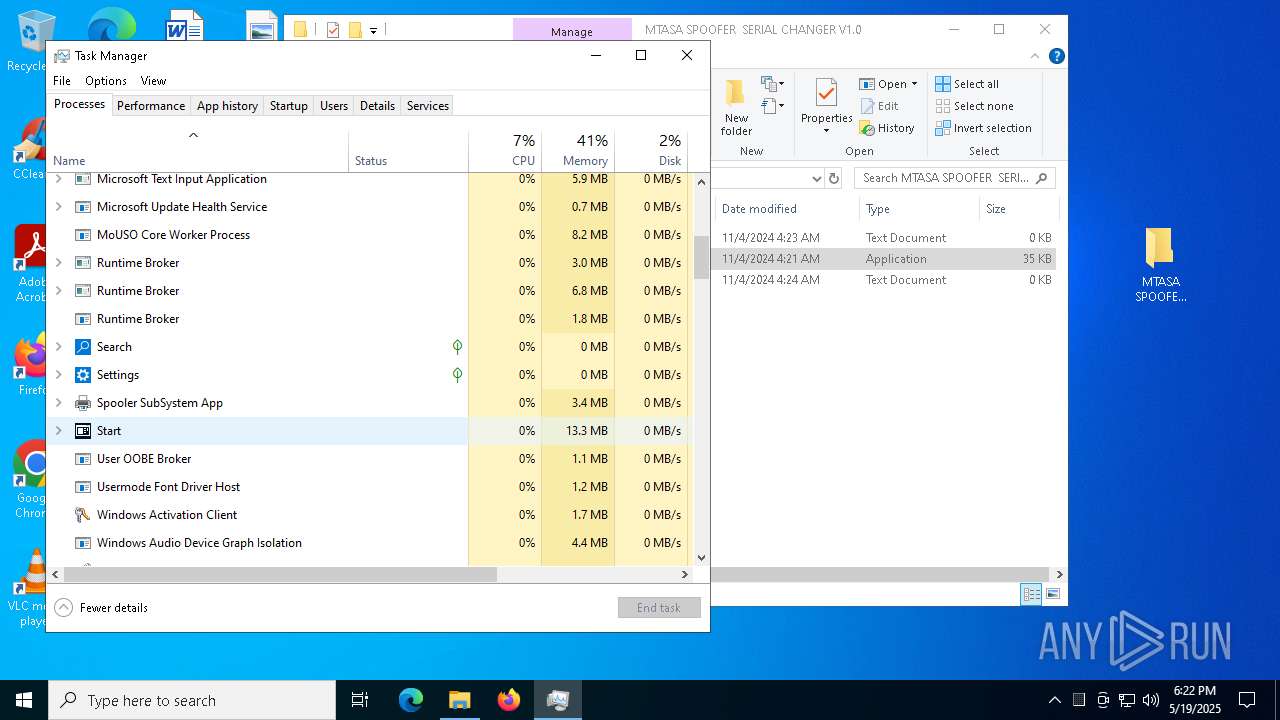
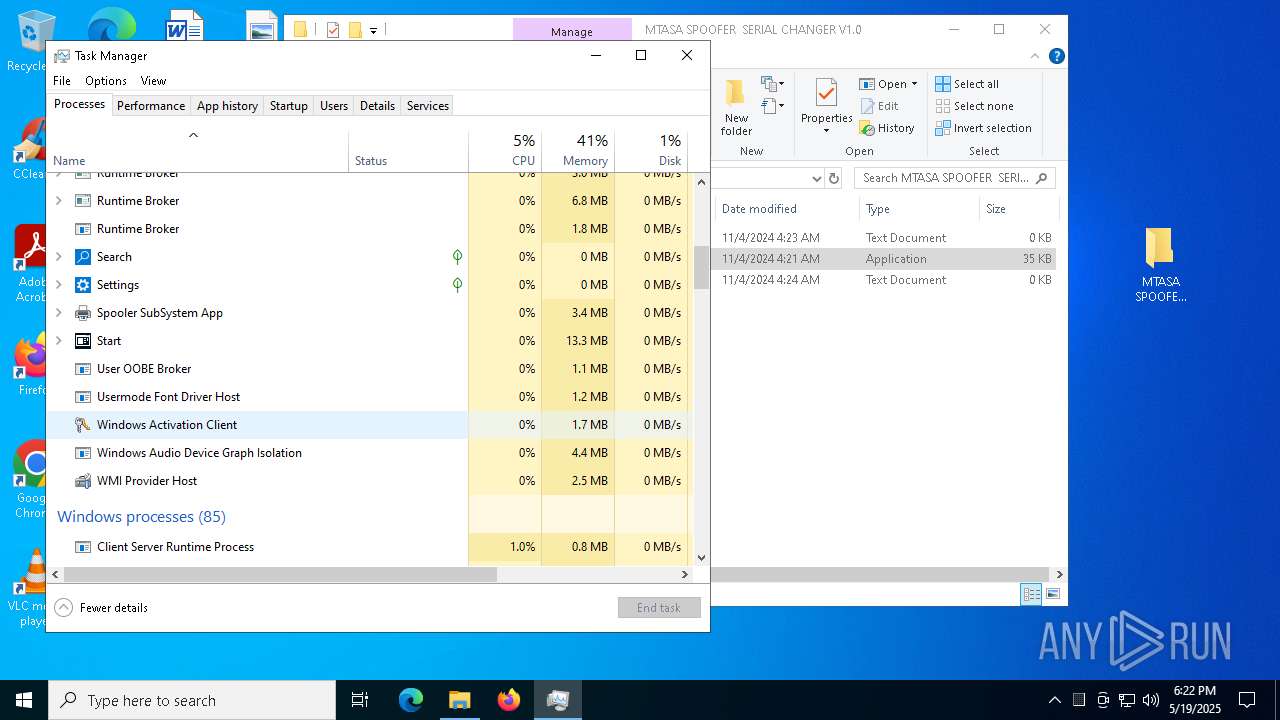
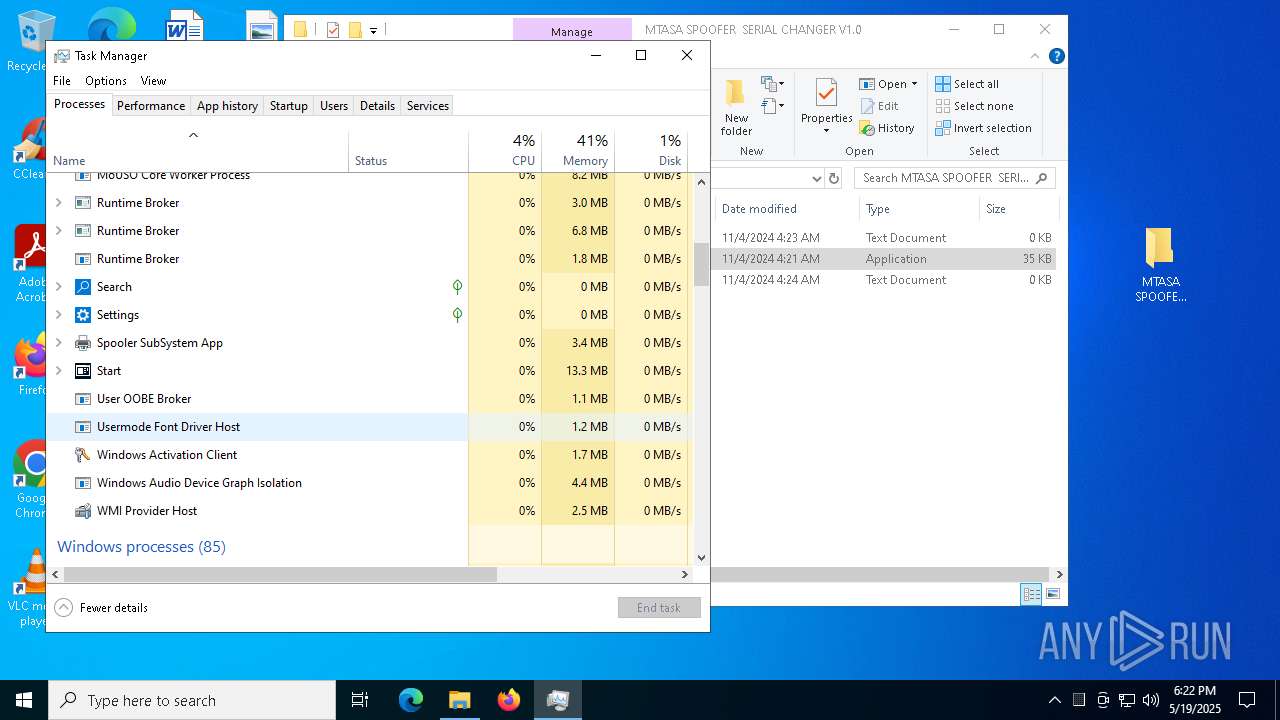
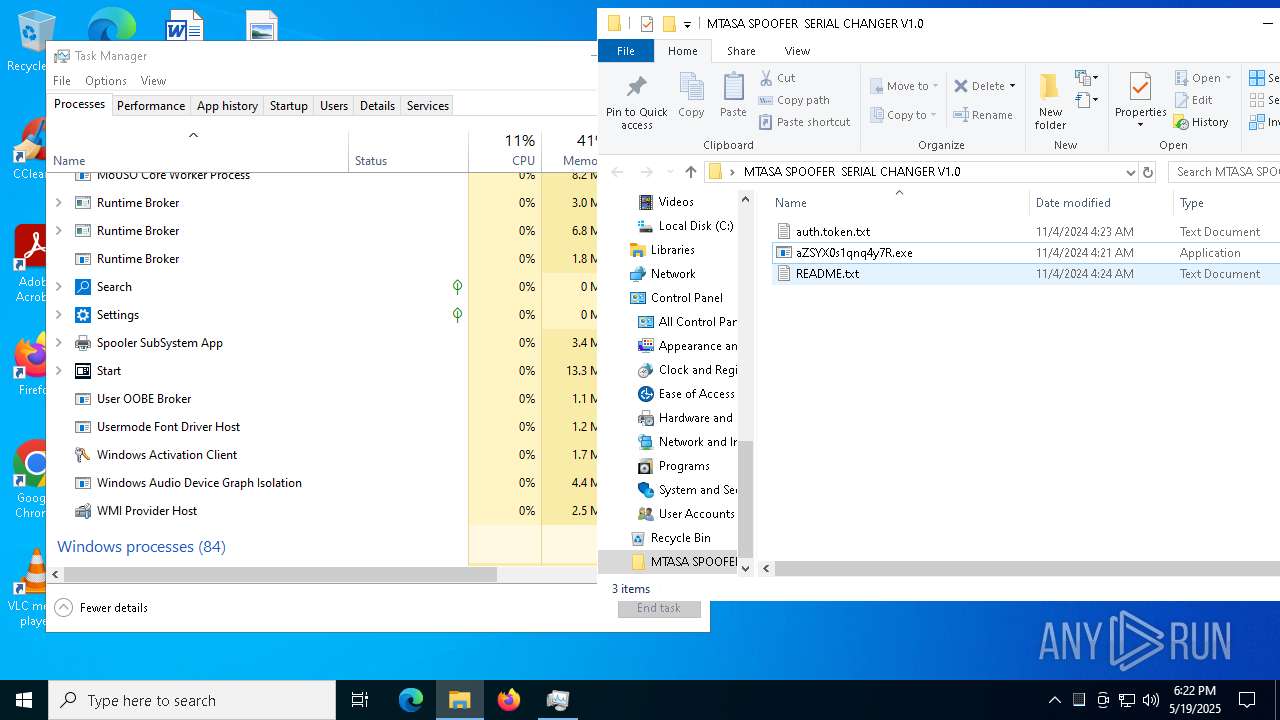
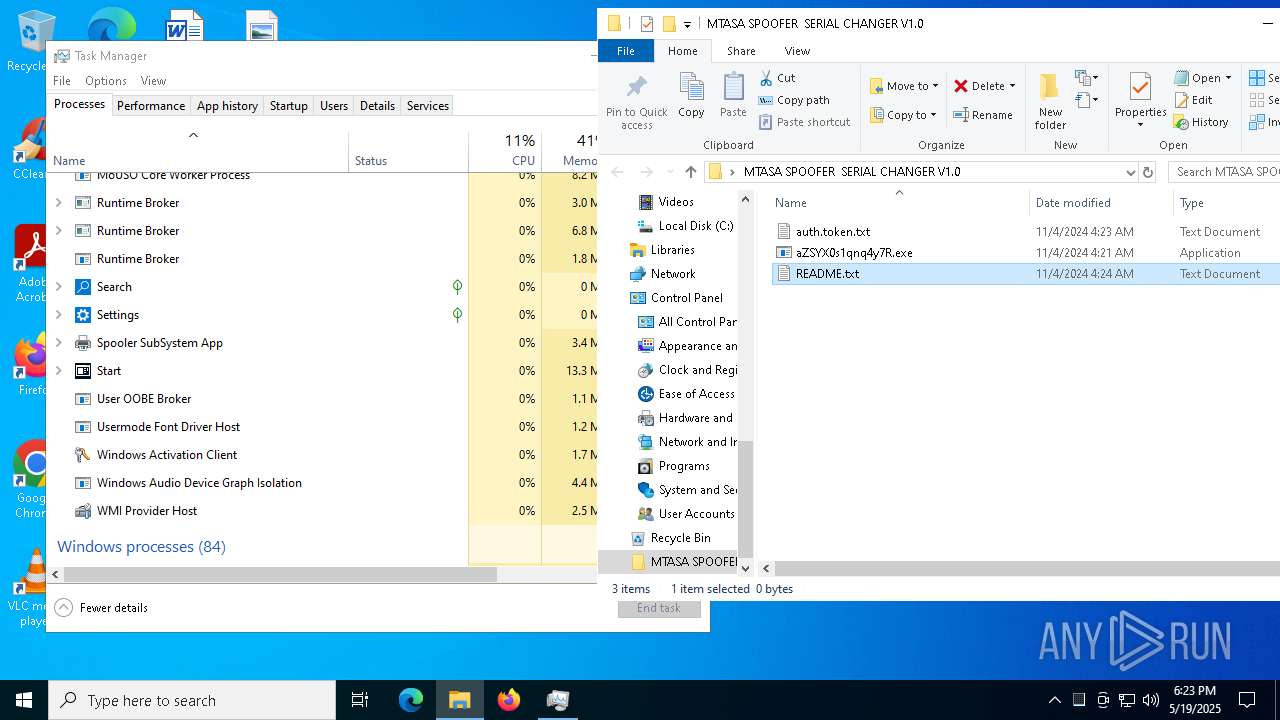
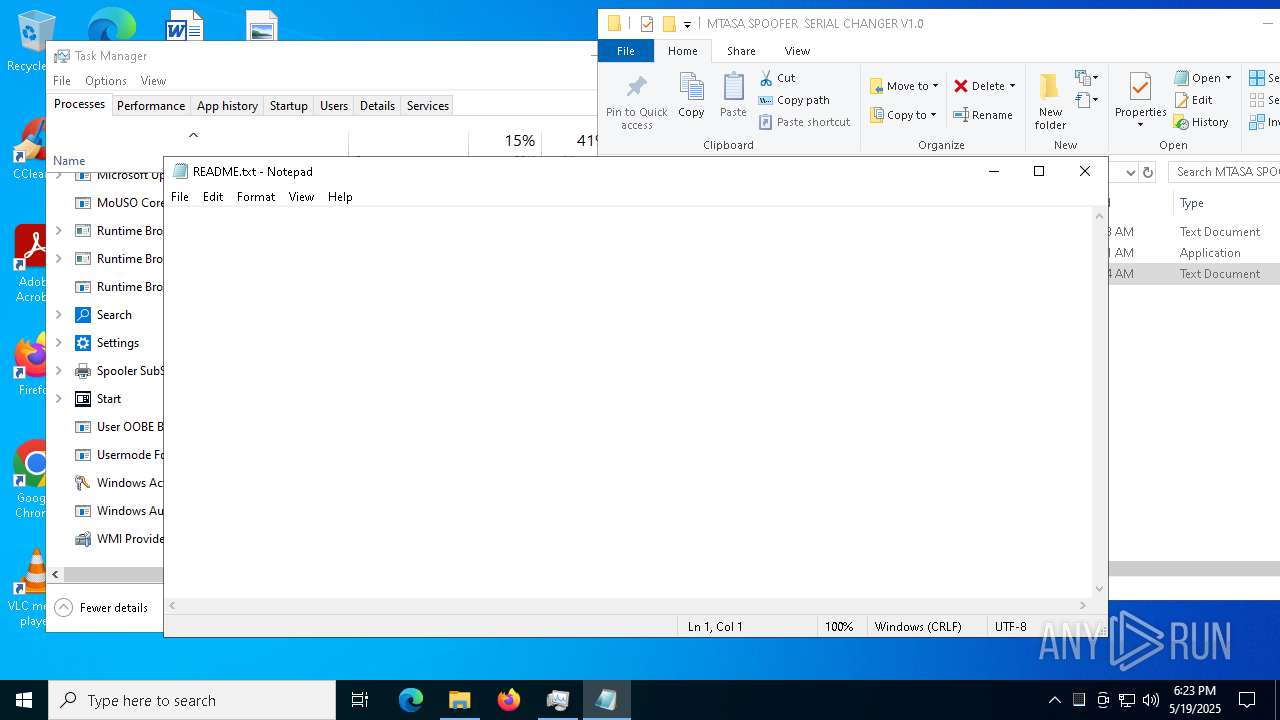
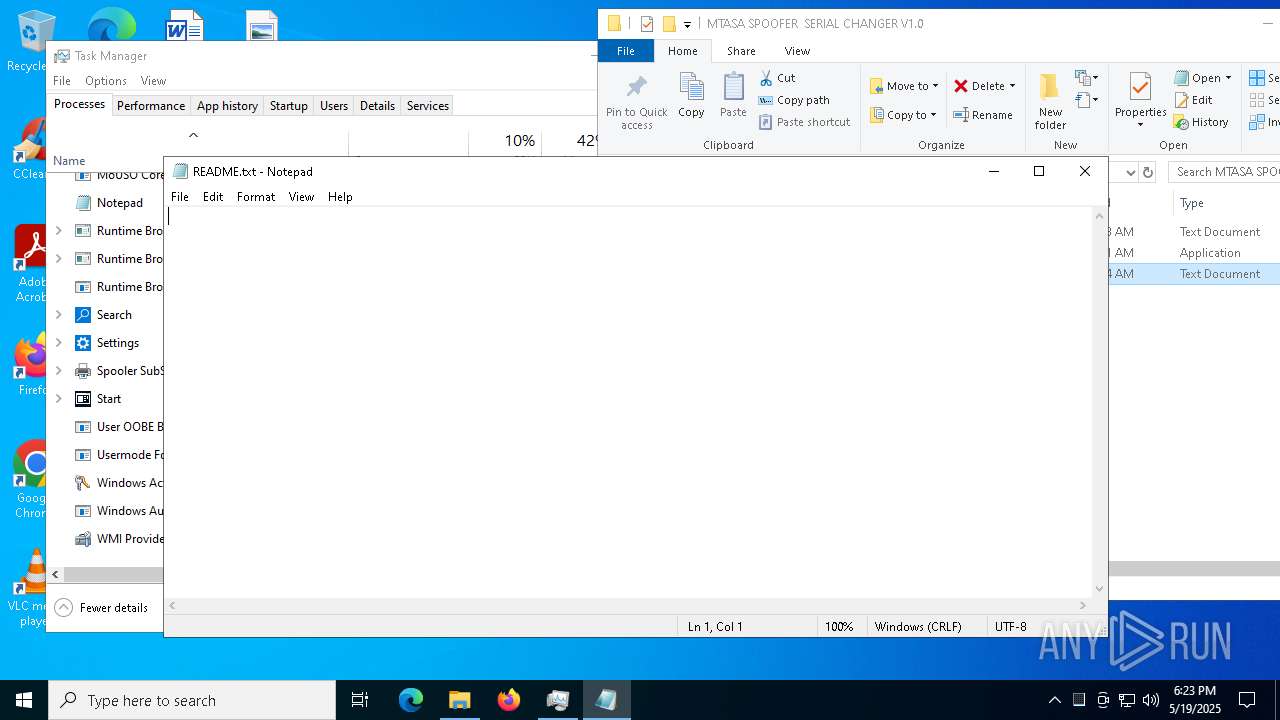
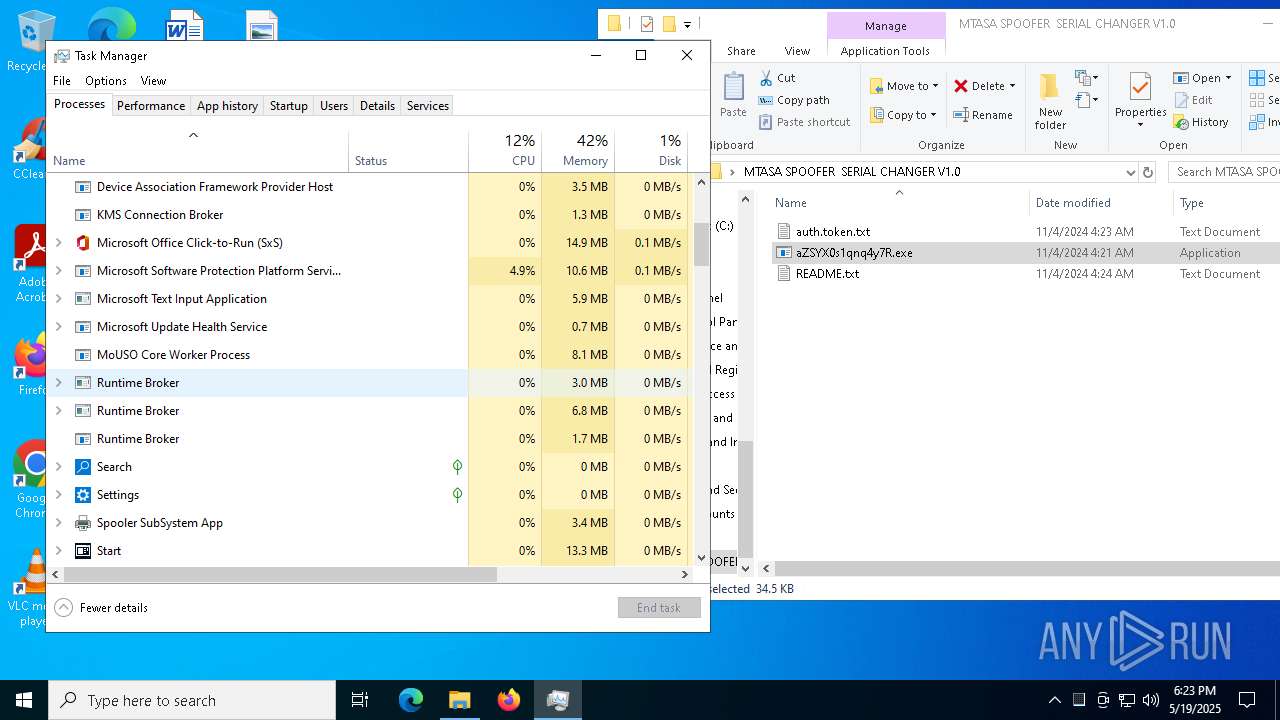
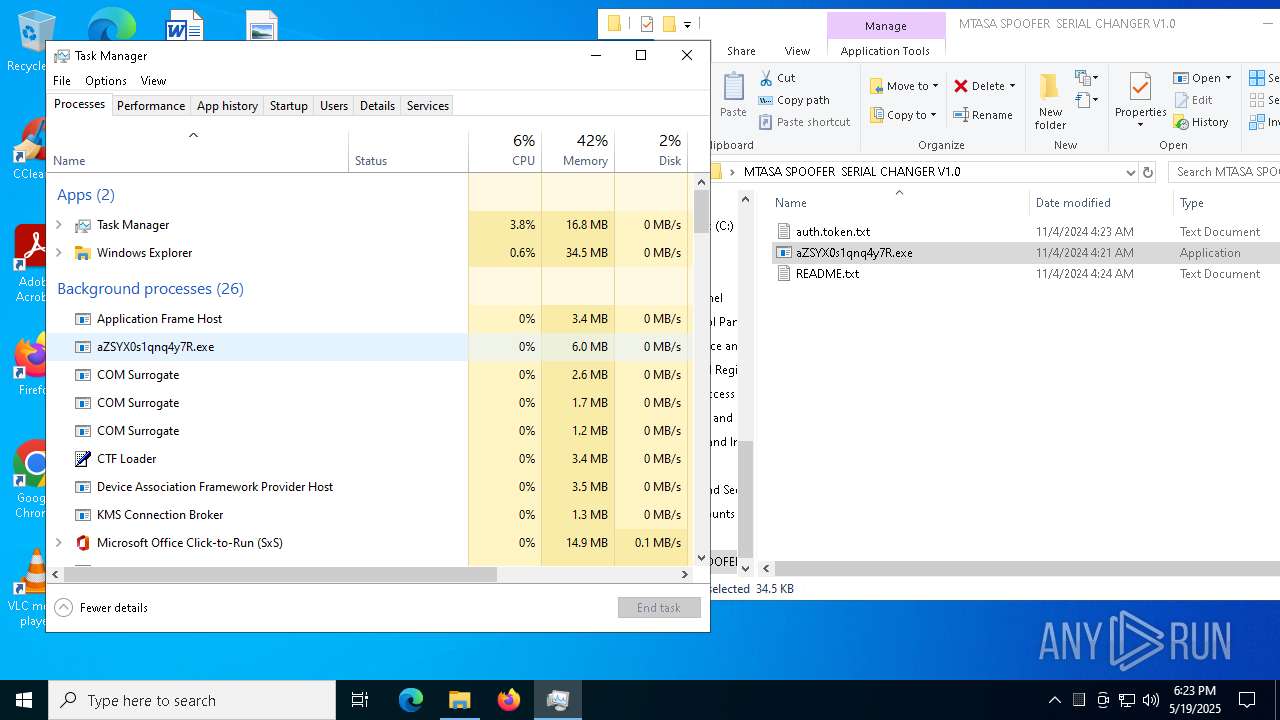
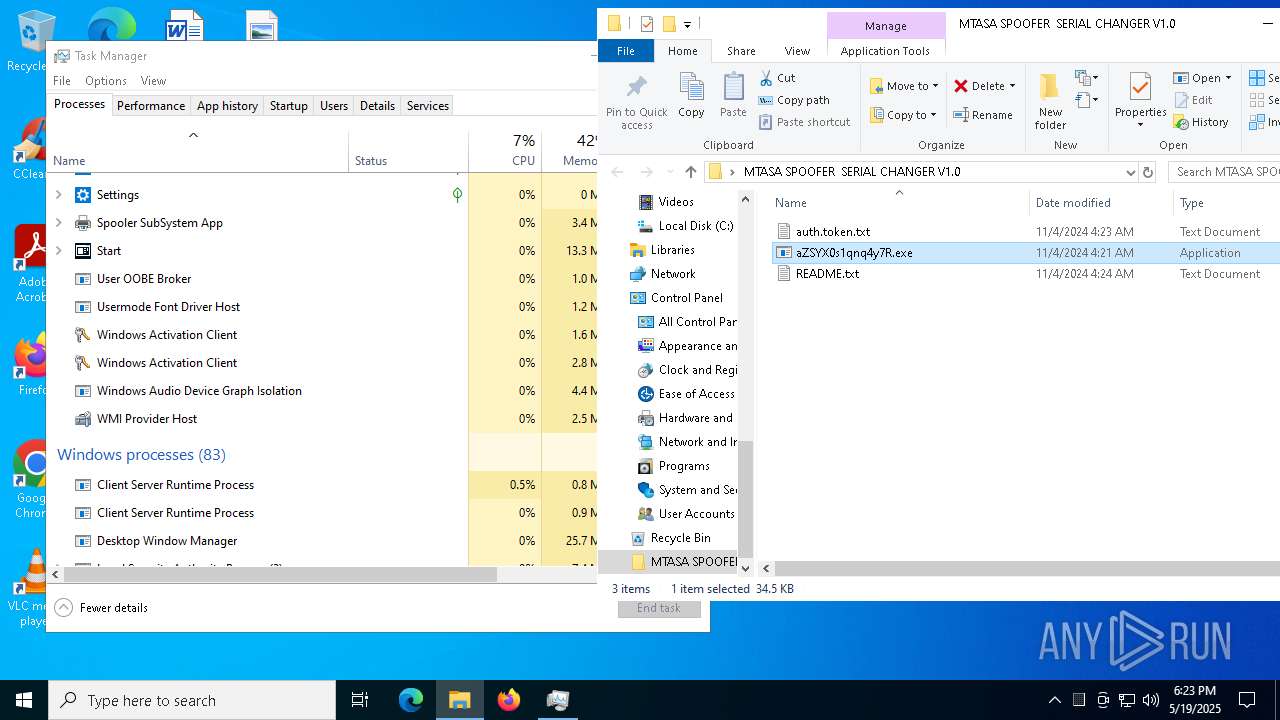
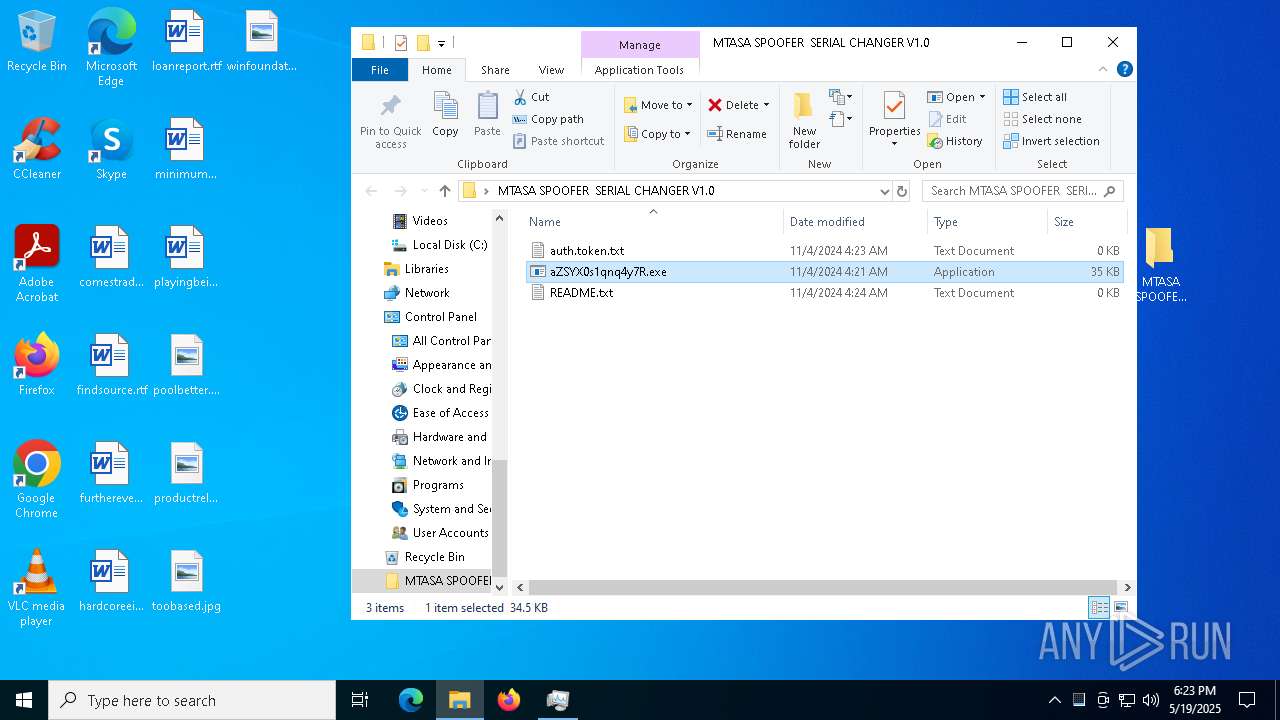
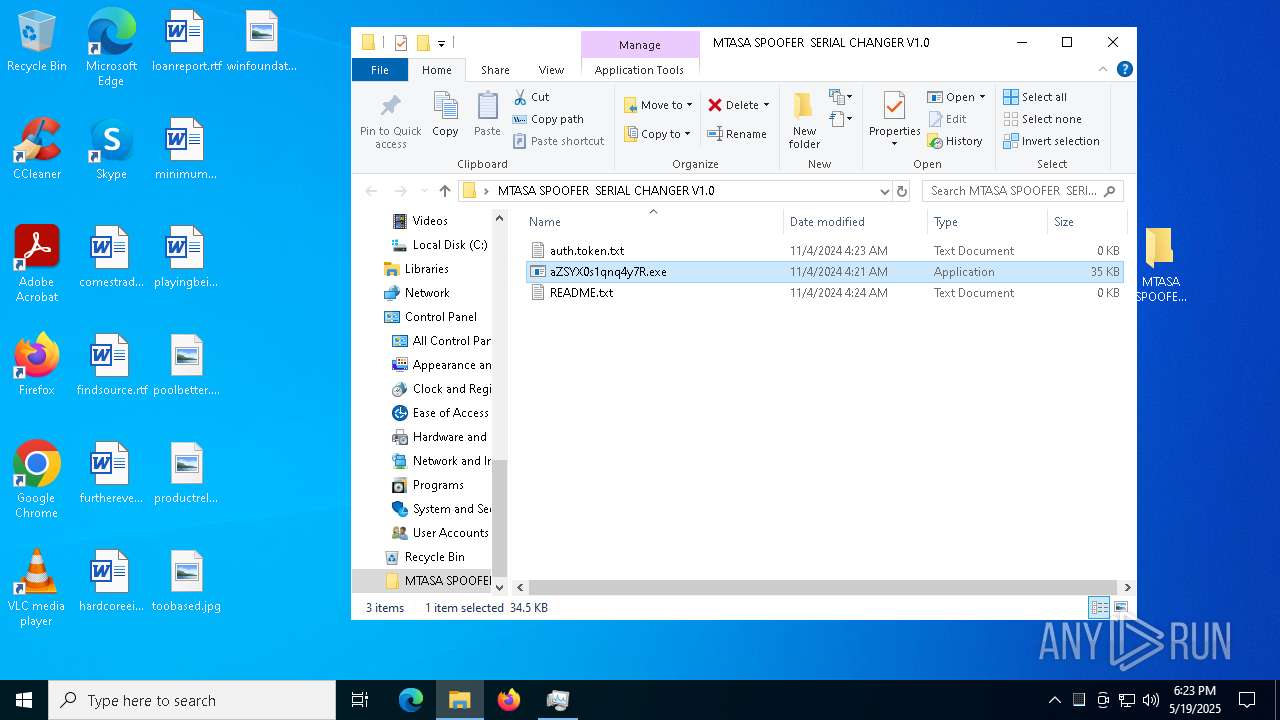
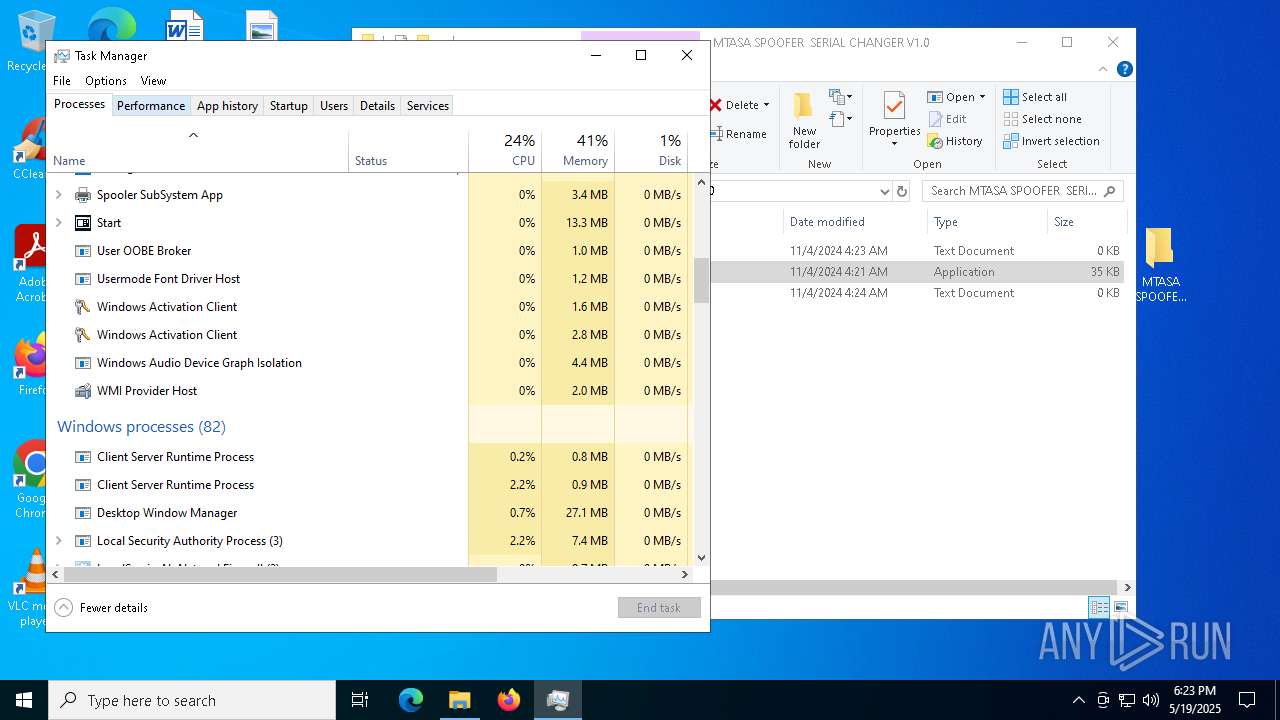
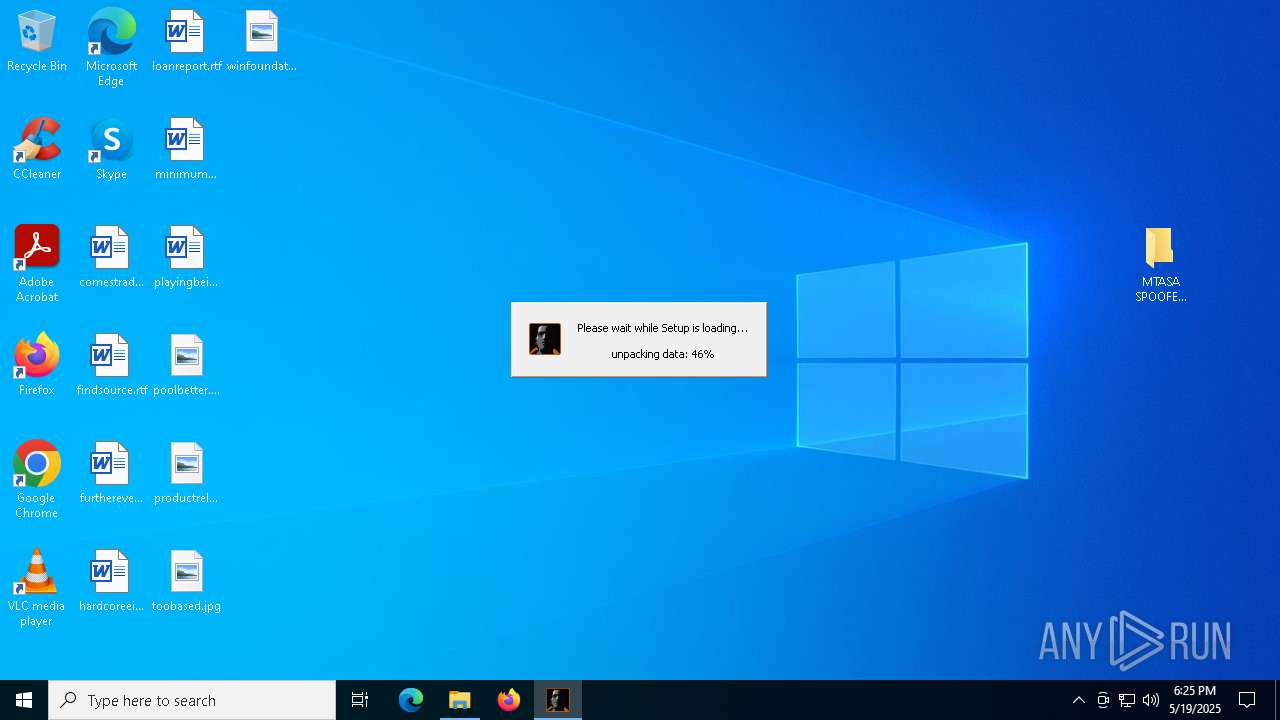
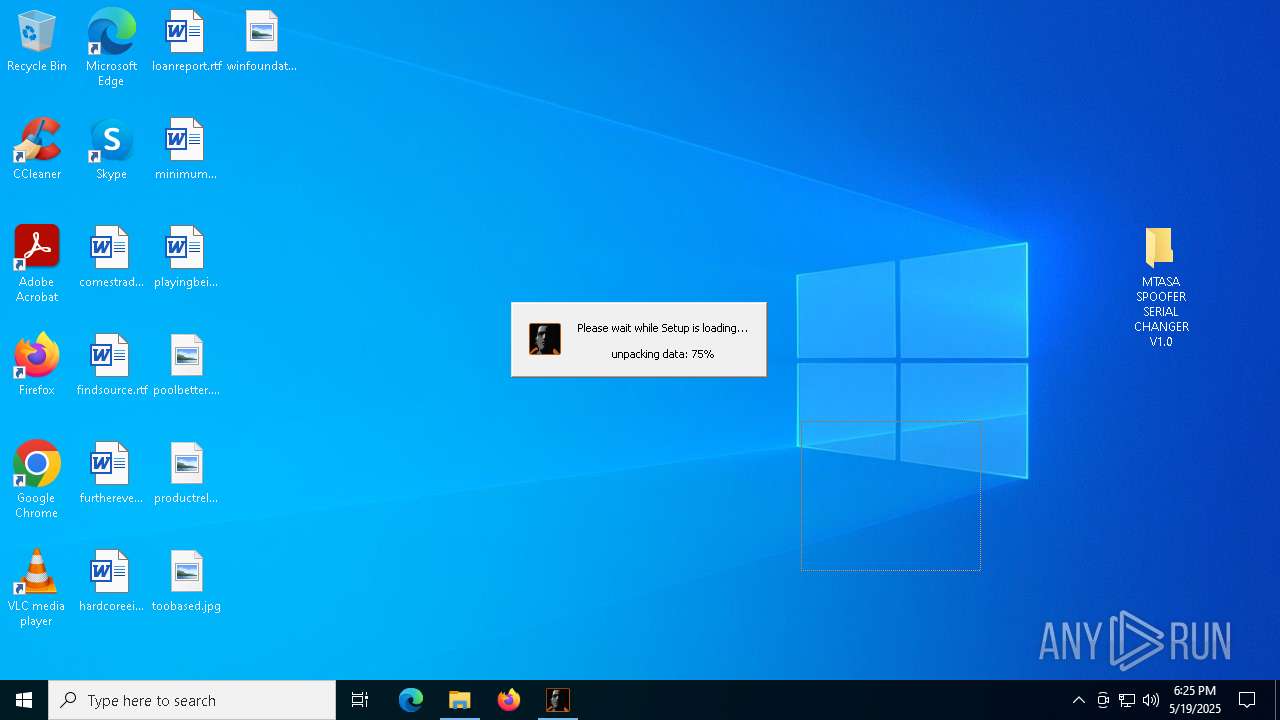
Manual execution by a user
- aZSYX0s1qnq4y7R.exe (PID: 8048)
- Taskmgr.exe (PID: 1184)
- Taskmgr.exe (PID: 5256)
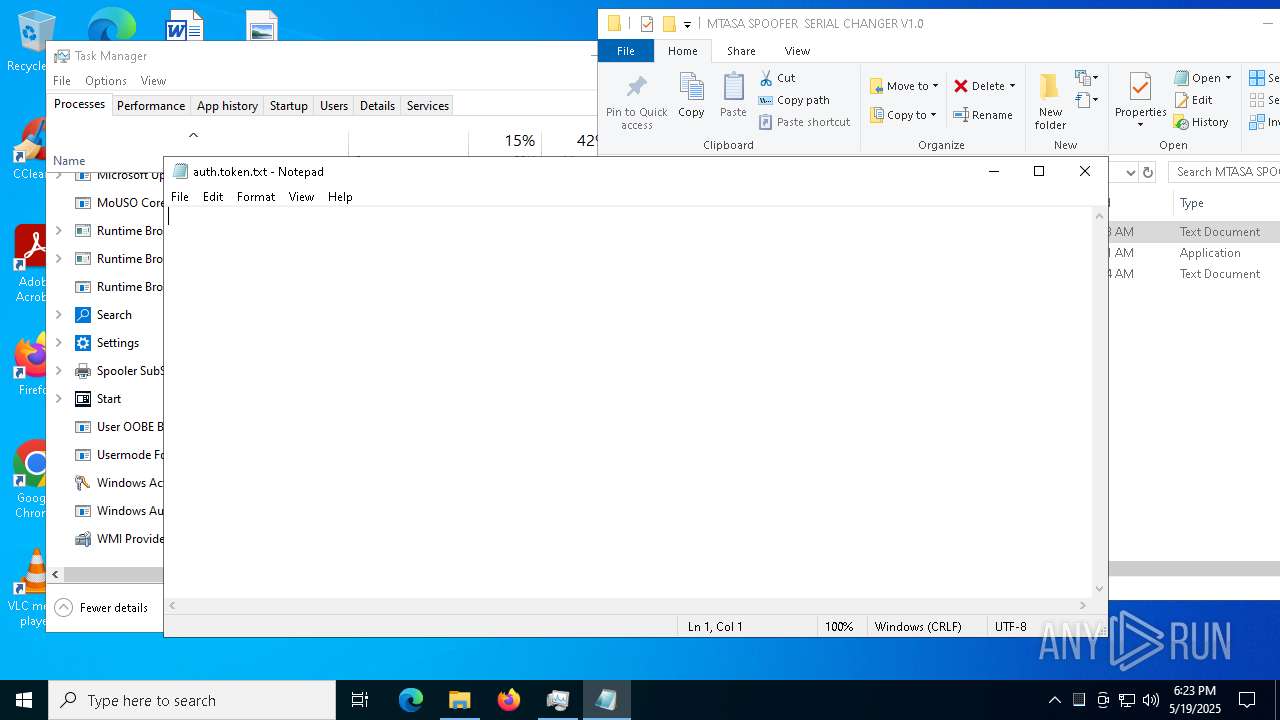
- notepad.exe (PID: 3240)
- notepad.exe (PID: 6184)
- notepad.exe (PID: 7084)
- aZSYX0s1qnq4y7R.exe (PID: 5740)
- aZSYX0s1qnq4y7R.exe (PID: 7396)
- aZSYX0s1qnq4y7R.exe (PID: 4428)
- Taskmgr.exe (PID: 7748)
- Taskmgr.exe (PID: 7608)
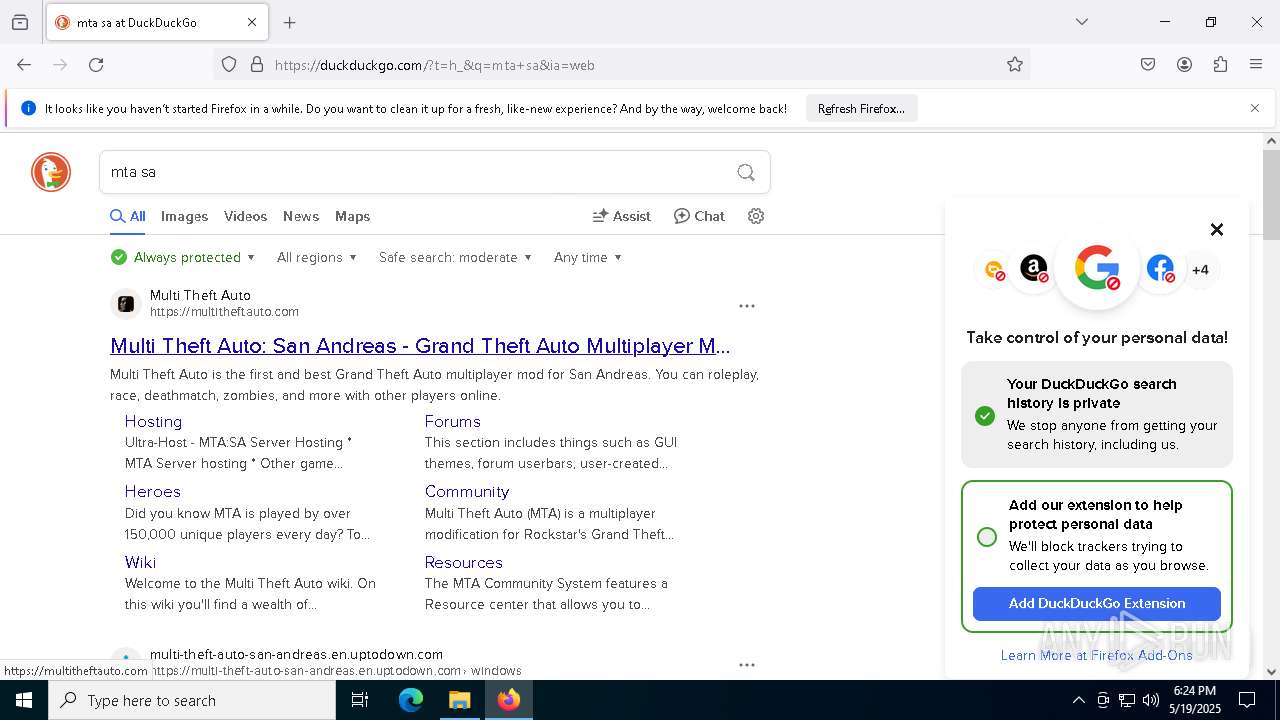
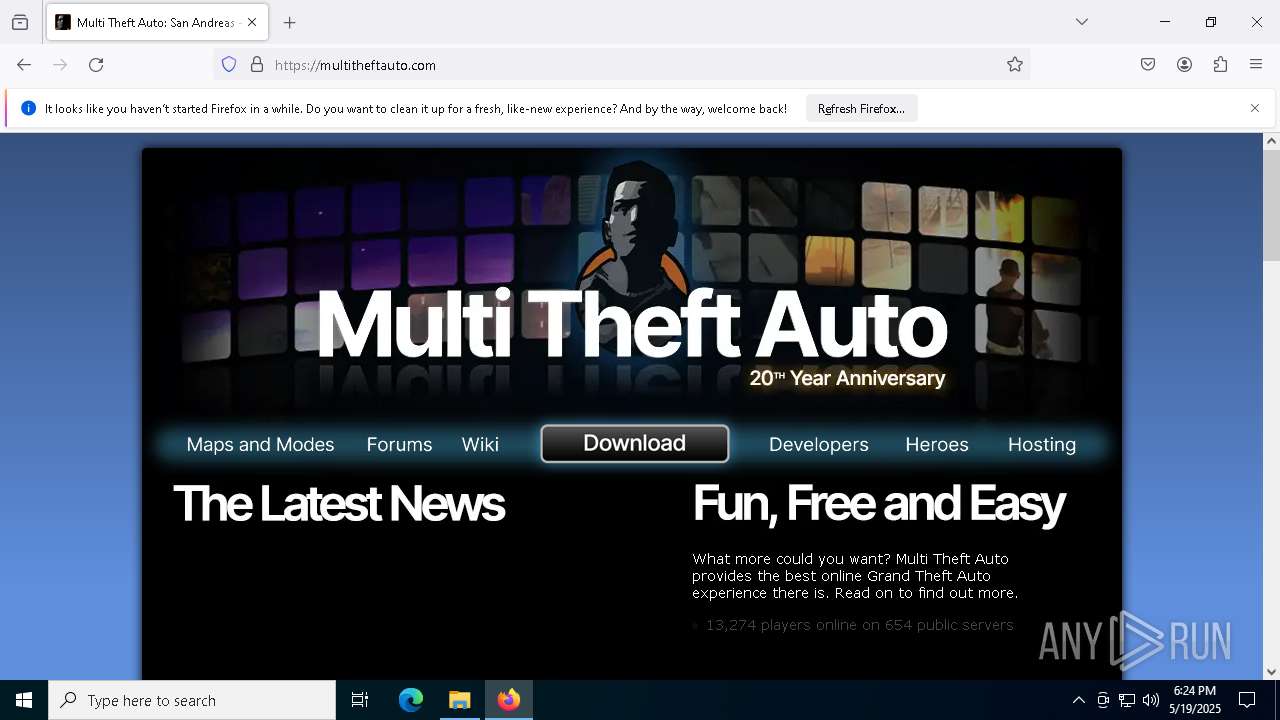
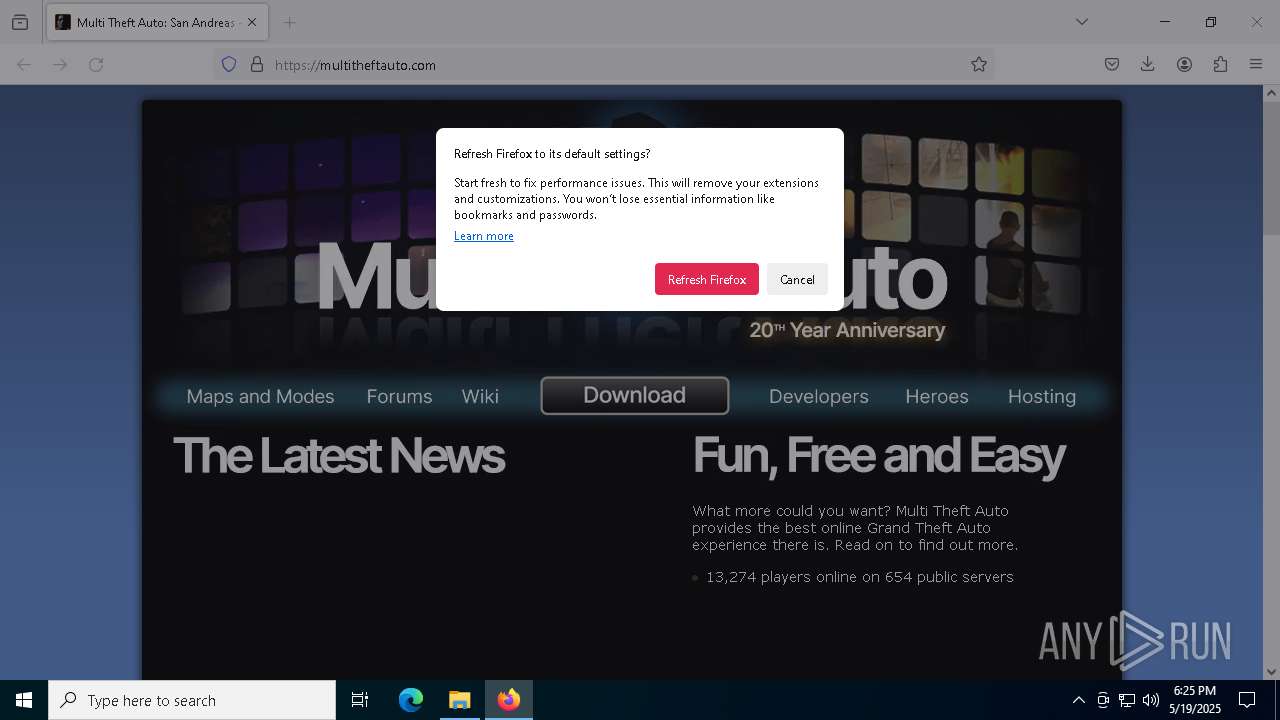
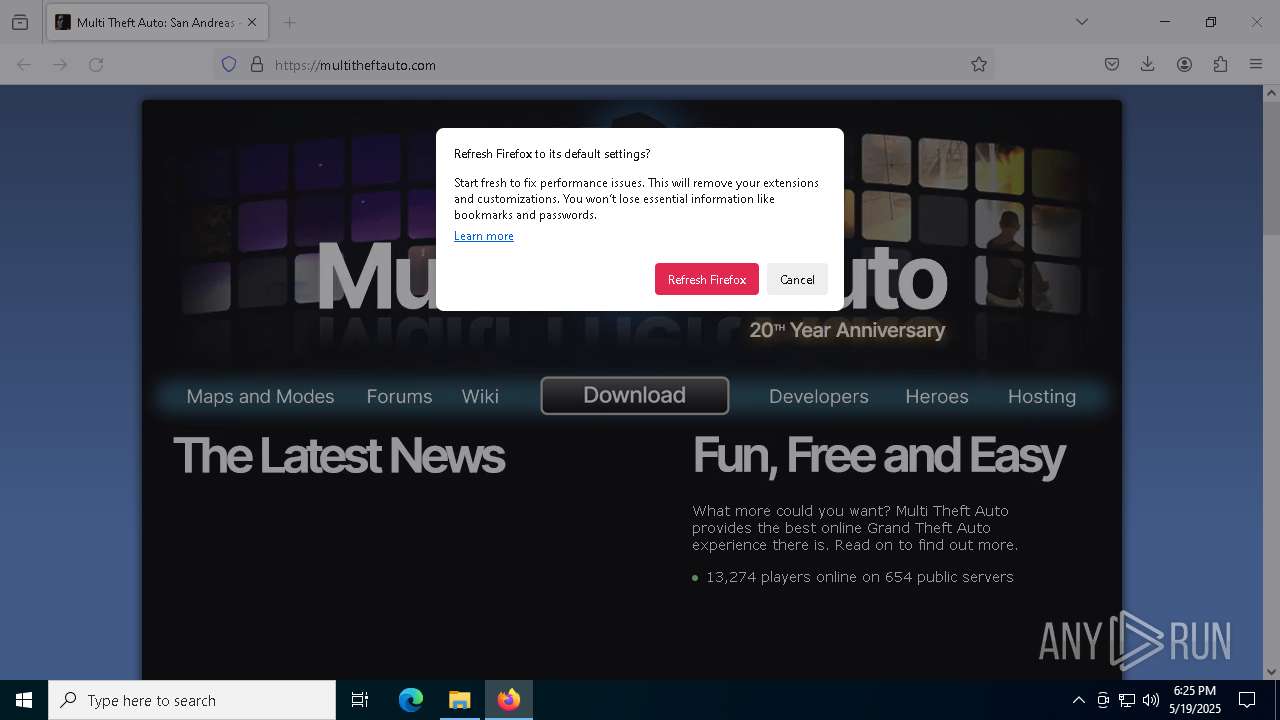
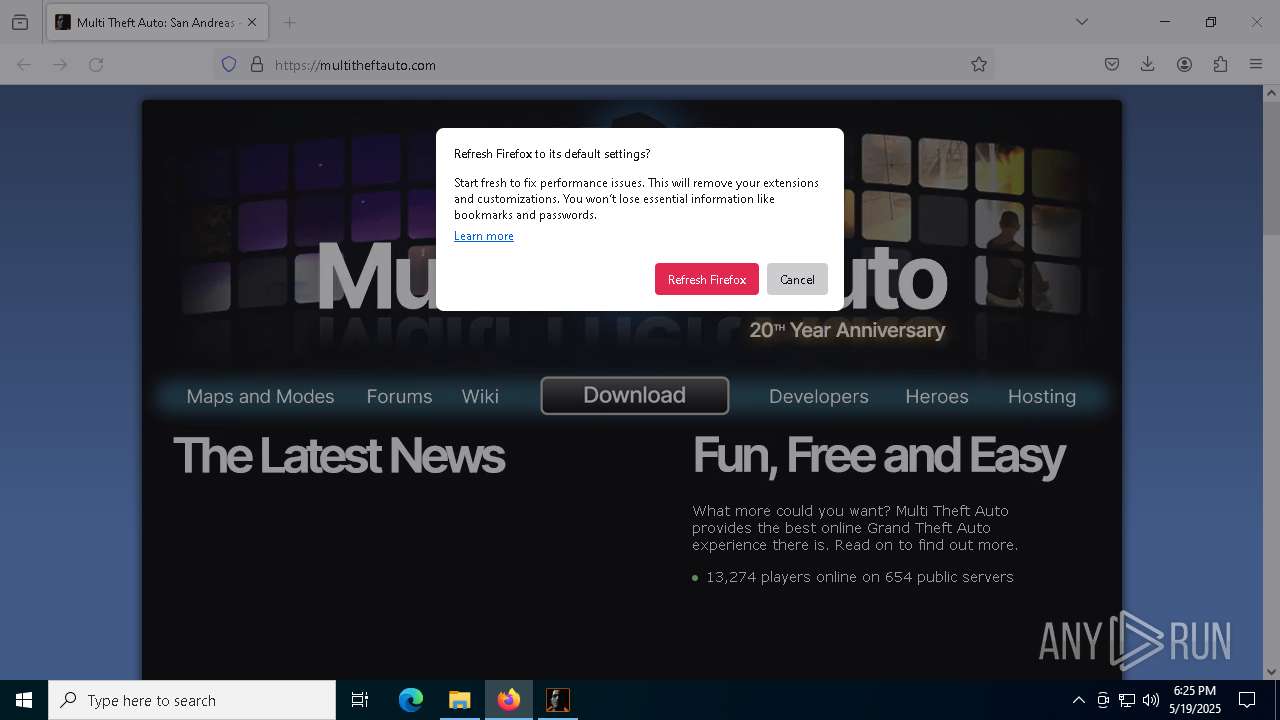
- firefox.exe (PID: 7836)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7248)
- firefox.exe (PID: 7684)
Reads the computer name
- aZSYX0s1qnq4y7R.exe (PID: 8048)
- aZSYX0s1qnq4y7R.exe (PID: 5740)
- aZSYX0s1qnq4y7R.exe (PID: 7396)
- aZSYX0s1qnq4y7R.exe (PID: 4428)
Reads the machine GUID from the registry
- aZSYX0s1qnq4y7R.exe (PID: 8048)
- aZSYX0s1qnq4y7R.exe (PID: 5740)
- aZSYX0s1qnq4y7R.exe (PID: 7396)
- aZSYX0s1qnq4y7R.exe (PID: 4428)
Creates files or folders in the user directory
- aZSYX0s1qnq4y7R.exe (PID: 8048)
Checks supported languages
- aZSYX0s1qnq4y7R.exe (PID: 8048)
- aZSYX0s1qnq4y7R.exe (PID: 7396)
- aZSYX0s1qnq4y7R.exe (PID: 4428)
- aZSYX0s1qnq4y7R.exe (PID: 5740)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 1184)
- notepad.exe (PID: 3240)
- notepad.exe (PID: 7084)
- notepad.exe (PID: 6184)
Reads the software policy settings
- slui.exe (PID: 7452)
The sample compiled with english language support
- firefox.exe (PID: 7684)
- mtasa-1.6.exe (PID: 7452)
- mtasa-1.6.exe (PID: 4728)
Application launched itself
- firefox.exe (PID: 7836)
- firefox.exe (PID: 7684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
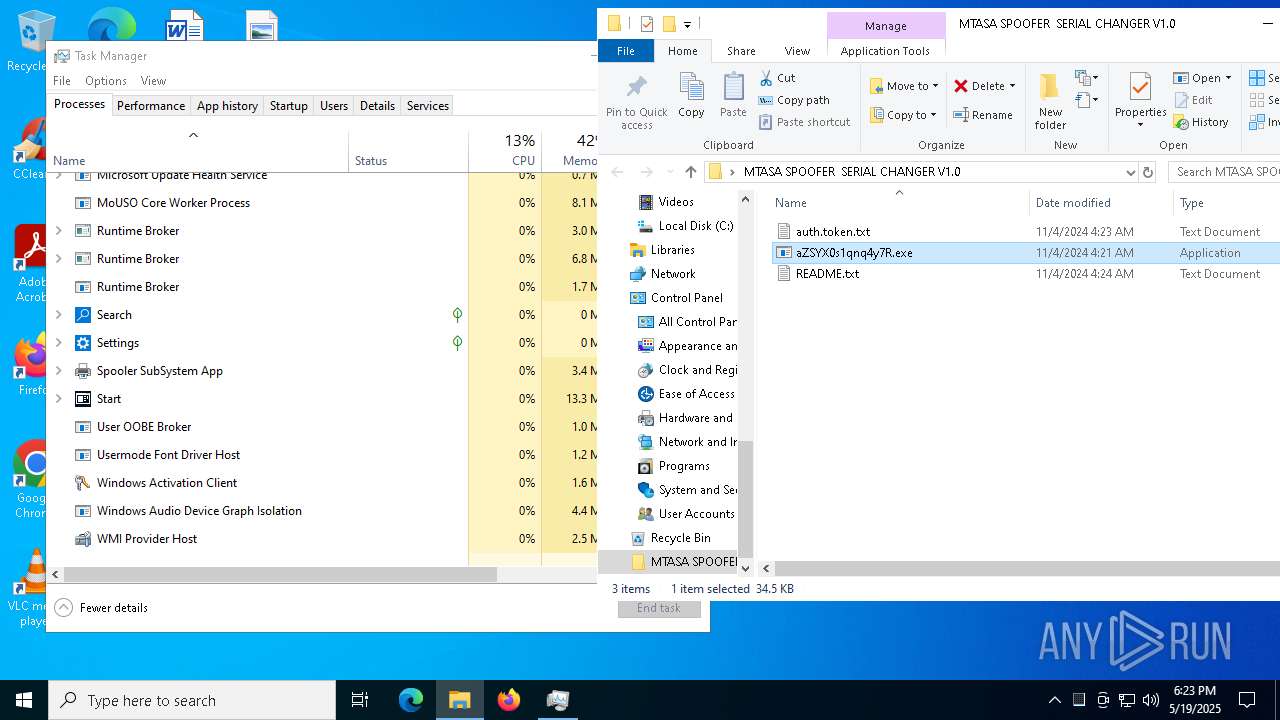
XWorm
(PID) Process(8048) aZSYX0s1qnq4y7R.exe
C2monstr.ddns.net:1177
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.0
Mutexhrrlp3UG4oHVSl9q
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | - |
| UncompressedSize: | - |
| OperatingSystem: | Win32 |
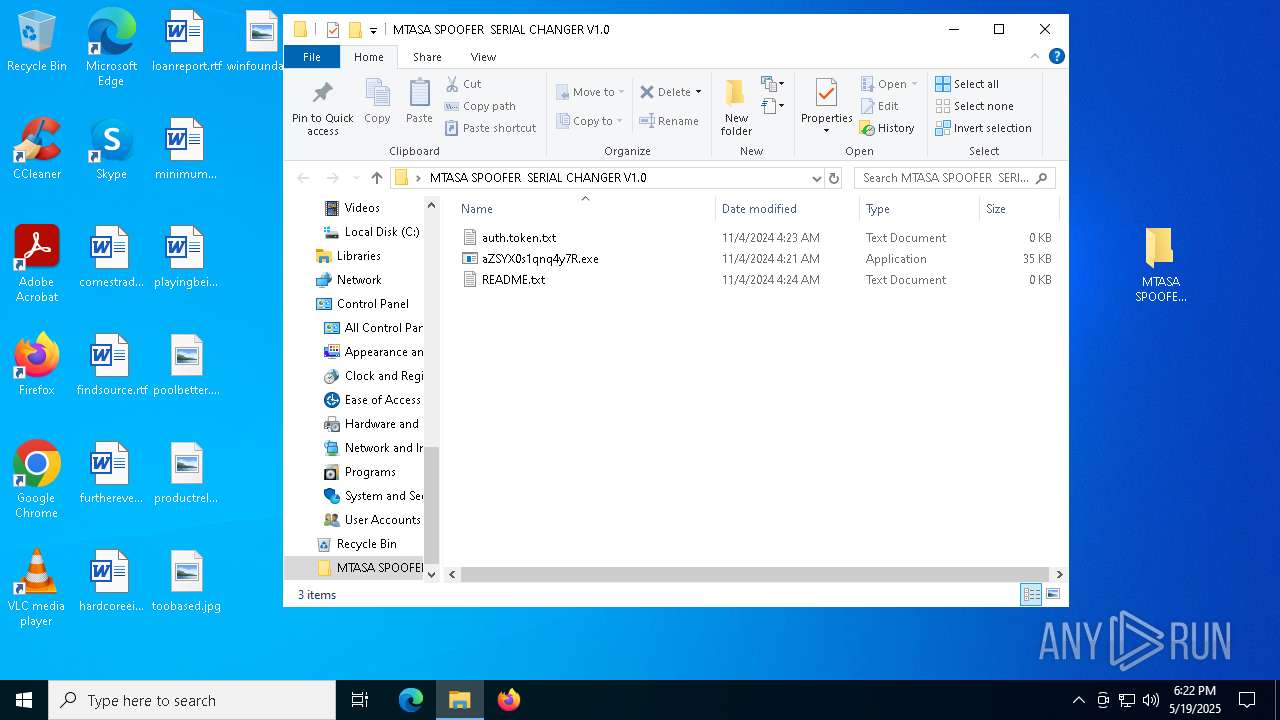
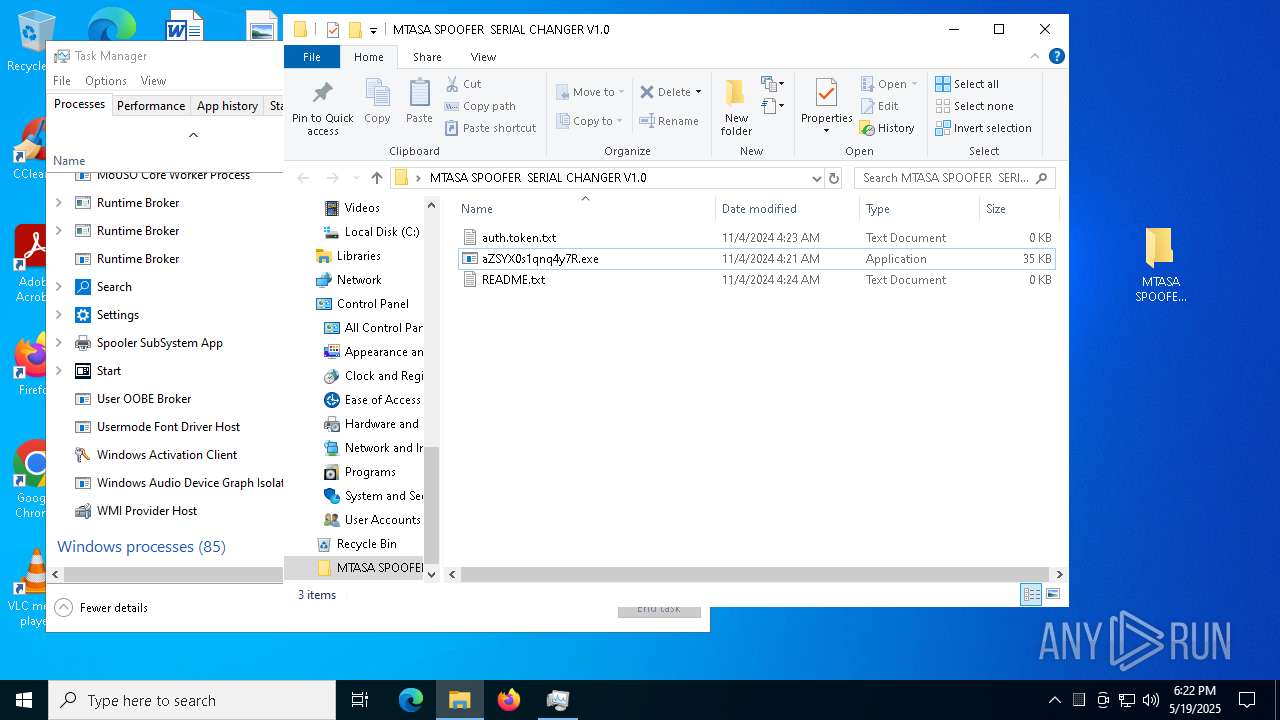
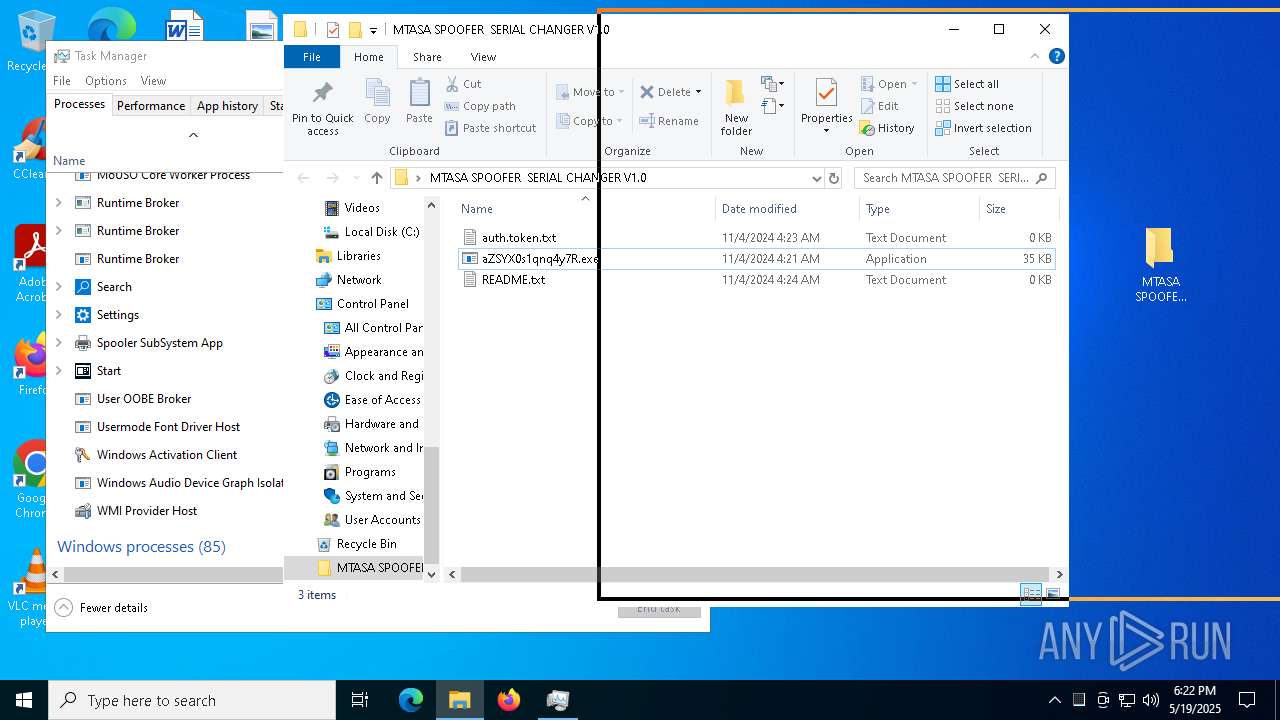
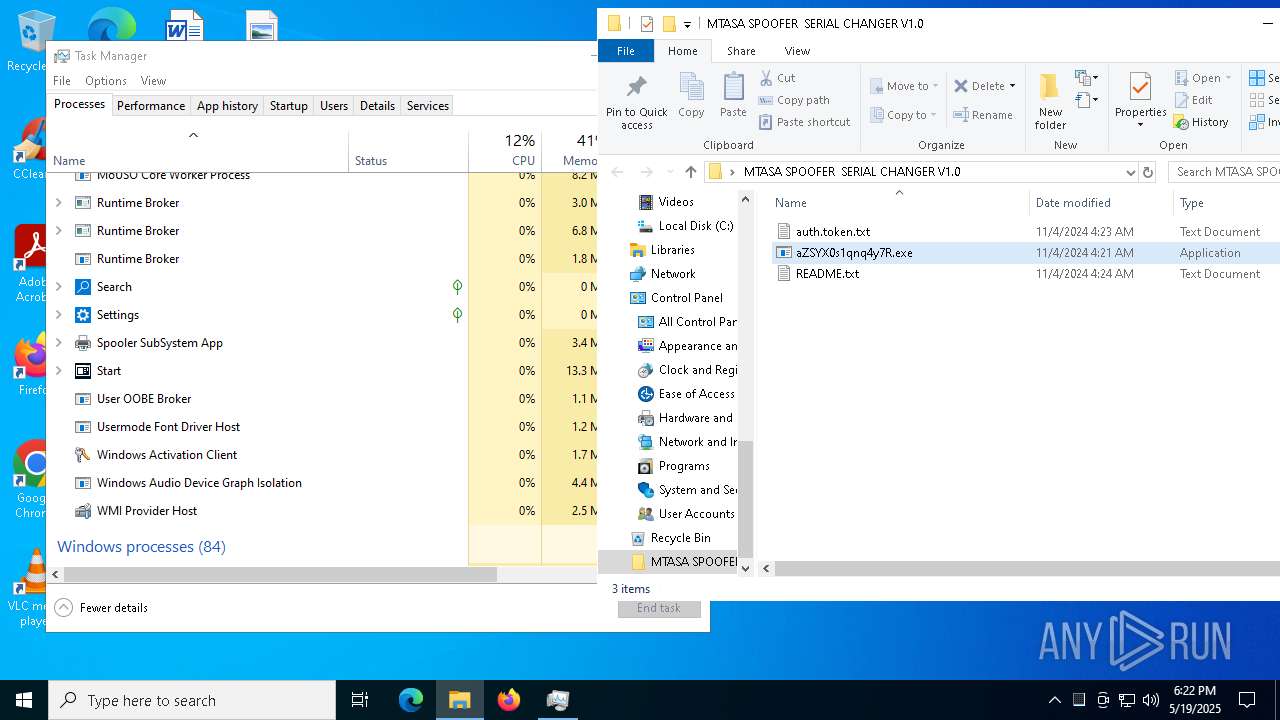
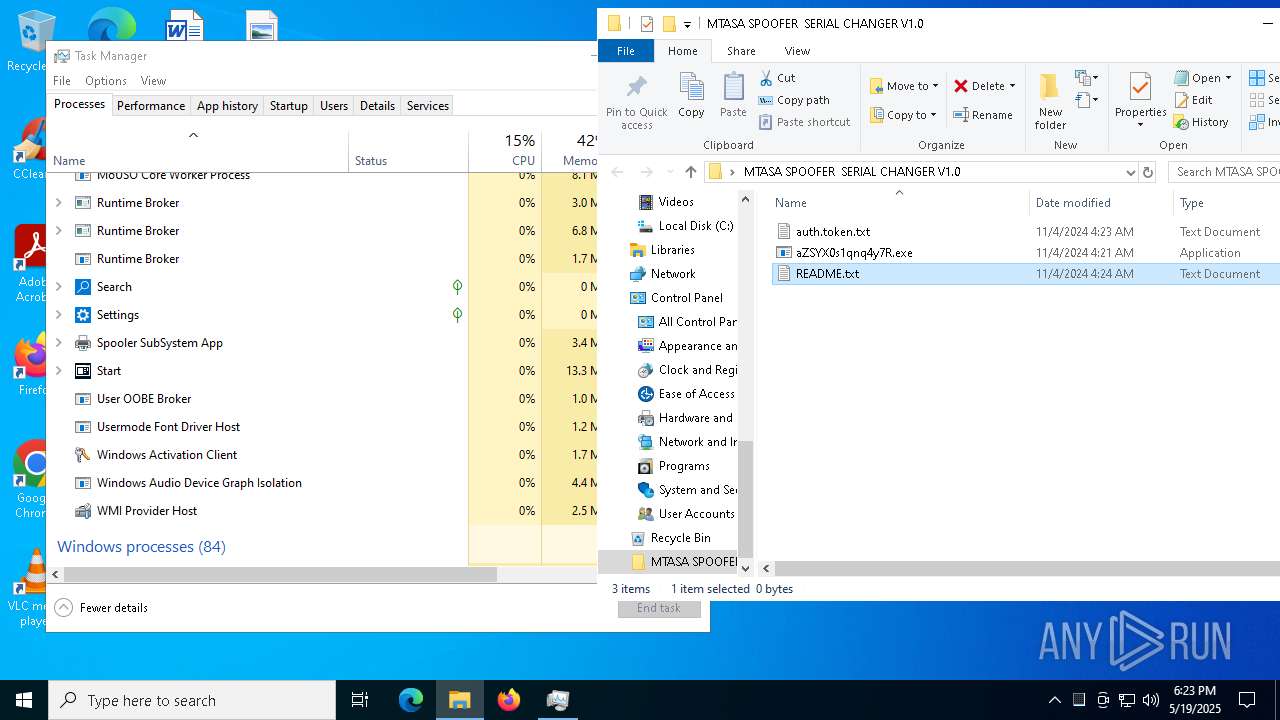
| ArchivedFileName: | MTASA SPOOFER SERIAL CHANGER V1.0/auth.token.txt |
Total processes
172
Monitored processes
33
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5084 -childID 3 -isForBrowser -prefsHandle 4884 -prefMapHandle 5056 -prefsLen 31198 -prefMapSize 244583 -jsInitHandle 1504 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {df4aa608-49d8-4d15-a6b5-fb0159526674} 7684 "\\.\pipe\gecko-crash-server-pipe.7684" 1eae2bdf150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1184 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4328 -childID 2 -isForBrowser -prefsHandle 4320 -prefMapHandle 4316 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1504 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ef13abf5-2cb9-493c-baae-6c85445d91ed} 7684 "\\.\pipe\gecko-crash-server-pipe.7684" 1eade7654d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6096 -childID 9 -isForBrowser -prefsHandle 5856 -prefMapHandle 4776 -prefsLen 31600 -prefMapSize 244583 -jsInitHandle 1504 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c04cbabc-9207-4ed5-8823-009e9e3b2216} 7684 "\\.\pipe\gecko-crash-server-pipe.7684" 1eae39d1850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4968 -childID 4 -isForBrowser -prefsHandle 4960 -prefMapHandle 4920 -prefsLen 31198 -prefMapSize 244583 -jsInitHandle 1504 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {8395ec96-c0cf-46ea-a21a-3e861fa7a12c} 7684 "\\.\pipe\gecko-crash-server-pipe.7684" 1eae2bdf4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2140 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {72e5f06d-31b0-444b-8104-550f26c674fc} 7684 "\\.\pipe\gecko-crash-server-pipe.7684" 1eacb081710 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3240 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\MTASA SPOOFER SERIAL CHANGER V1.0\README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4792 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4928 -prefMapHandle 4300 -prefsLen 36642 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {99097e56-f1e0-4e9d-97a2-b6d60a58bc25} 7684 "\\.\pipe\gecko-crash-server-pipe.7684" 1eae0f4b510 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 4012 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5204 -childID 5 -isForBrowser -prefsHandle 5212 -prefMapHandle 5216 -prefsLen 31198 -prefMapSize 244583 -jsInitHandle 1504 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {bd4a27cf-44a6-4001-b728-3489f3b060d9} 7684 "\\.\pipe\gecko-crash-server-pipe.7684" 1eae2bdf850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
25 178
Read events
25 150
Write events
27
Delete events
1
Modification events
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MTASA_SPOOFER__SERIAL_CHANGER_V1.0.rar | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
18
Suspicious files
222
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7248.24930\MTASA SPOOFER SERIAL CHANGER V1.0\aZSYX0s1qnq4y7R.exe | executable | |
MD5:081EE30547B13150C01909B0BD20C106 | SHA256:4380D2BBE9F643E4CB096C64E63A743D58D655BA4A93993128FF56ED0BABE265 | |||
| 1184 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 7684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:103A13DCA599A55AD50545878C9A357B | SHA256:394B1228690DB9BA401D179907FD881B030A501F6681108466FC132D1B39E19A | |||
| 8048 | aZSYX0s1qnq4y7R.exe | C:\Users\admin\AppData\Roaming\RuntimeBroker.exe | executable | |
MD5:081EE30547B13150C01909B0BD20C106 | SHA256:4380D2BBE9F643E4CB096C64E63A743D58D655BA4A93993128FF56ED0BABE265 | |||
| 7684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:17DEF2EC7C4DFBA148F680E9E95B3DAC | SHA256:64296D3B8D473FD2D1A30AC1D2F69543D801BD55ED54CF0B4E3F9D75BD0BB172 | |||
| 7684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 8048 | aZSYX0s1qnq4y7R.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\RuntimeBroker.lnk | binary | |
MD5:5D609B538C8B9F06812E01FD64CF2126 | SHA256:B06ABADB5673F2653624FBBD943C337E40C059E1ECF1903DA19F738064D5DB32 | |||
| 7684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
133
DNS requests
160
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7684 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7684 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7684 | firefox.exe | POST | 200 | 2.16.168.117:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7684 | firefox.exe | POST | 200 | 2.16.168.117:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7684 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
976 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
monstr.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |