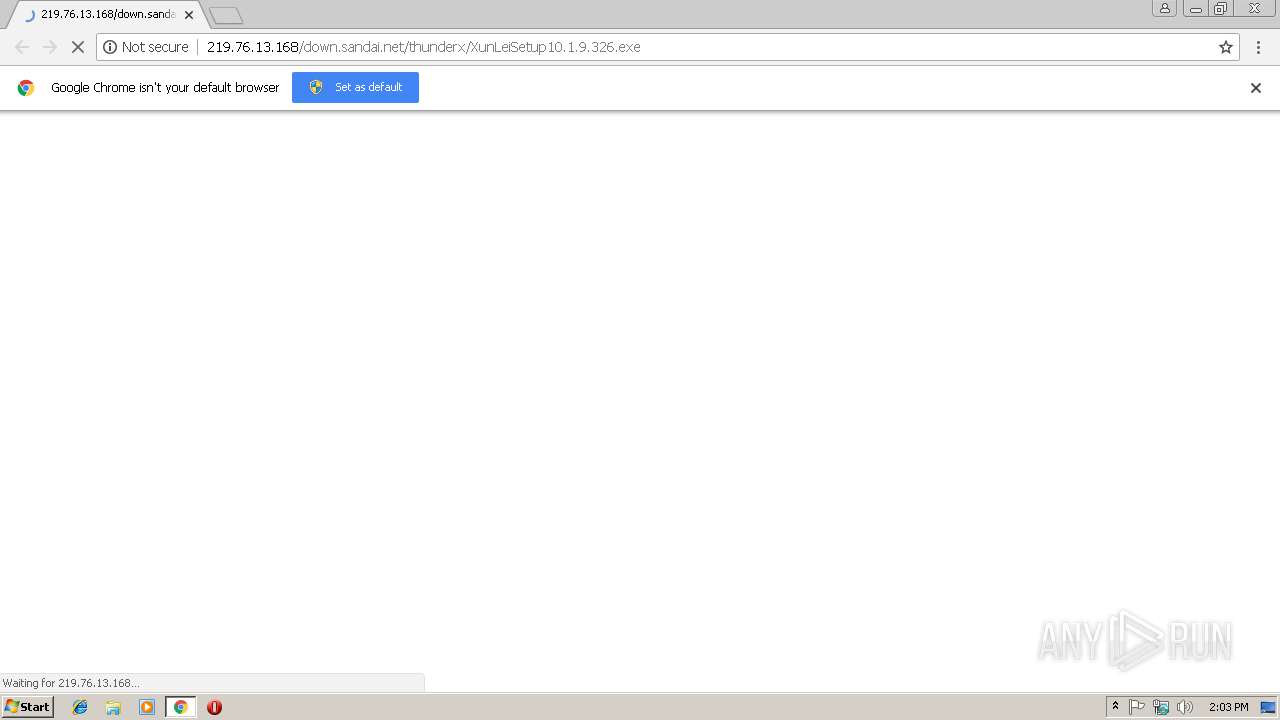
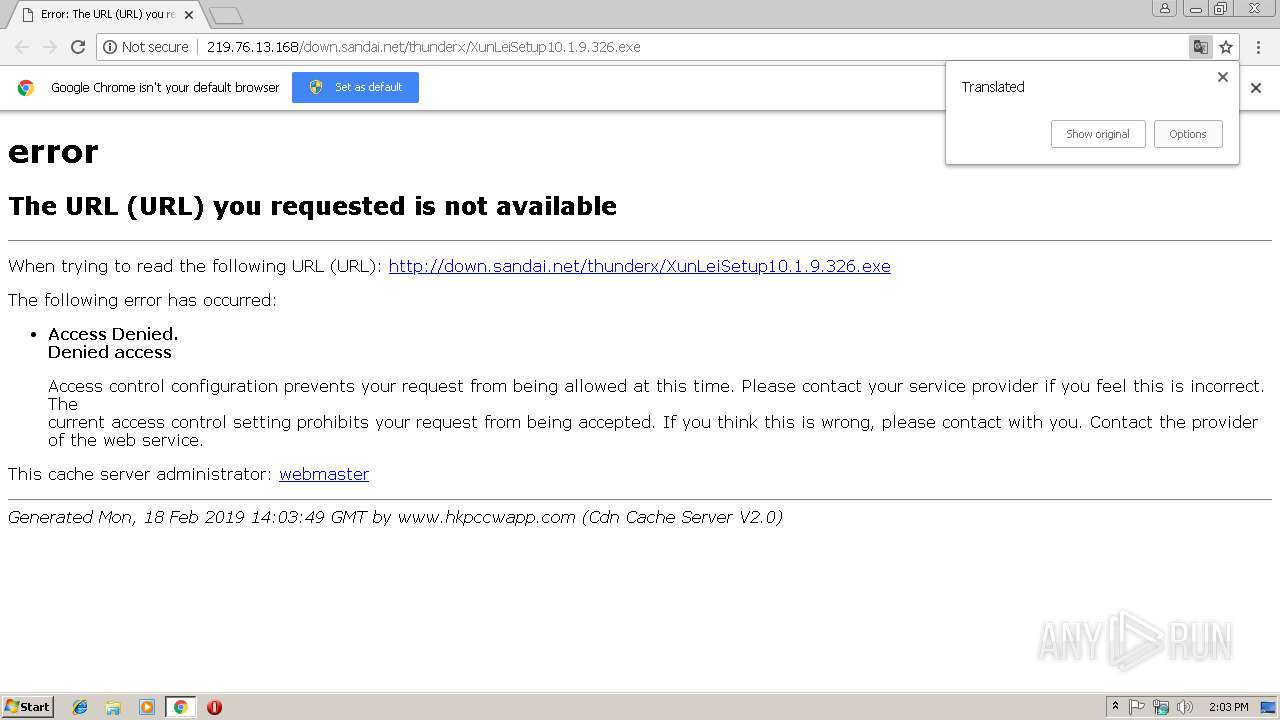
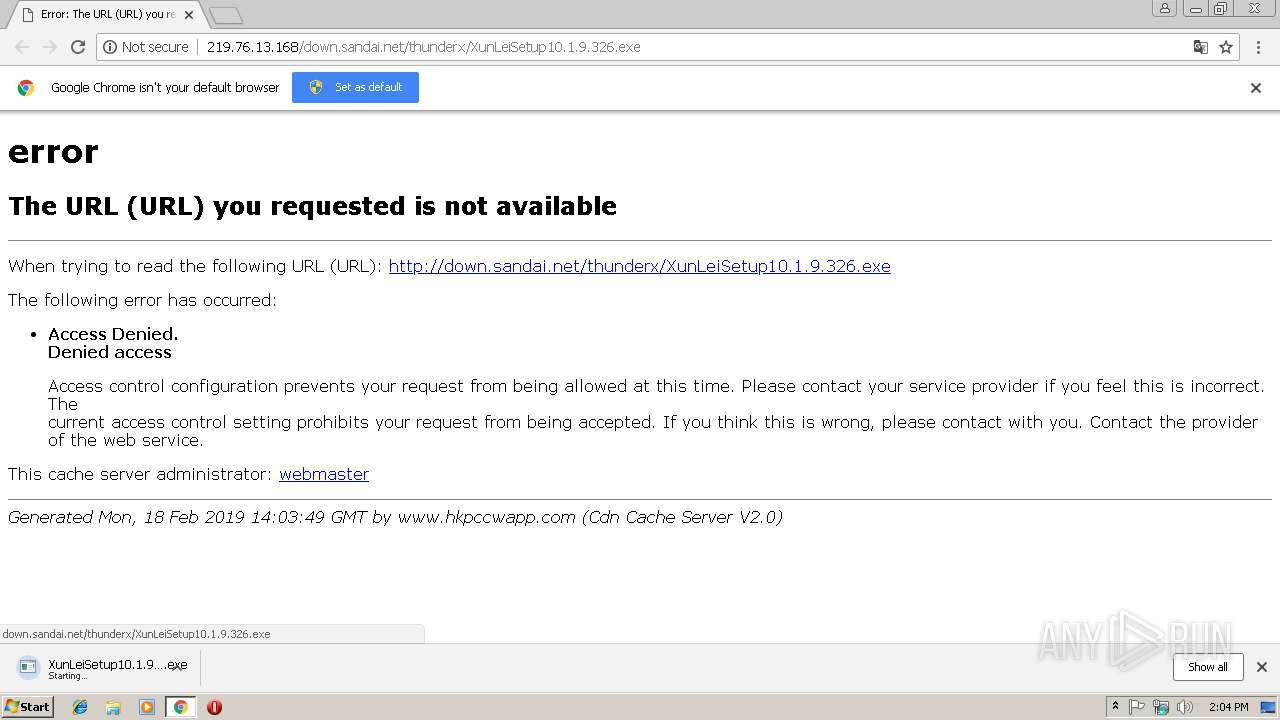
| URL: | http://219.76.13.168/down.sandai.net/thunderx/XunLeiSetup10.1.9.326.exe |
| Full analysis: | https://app.any.run/tasks/48dc871d-24b0-48c8-a85b-d3440c553f59 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 14:03:28 |
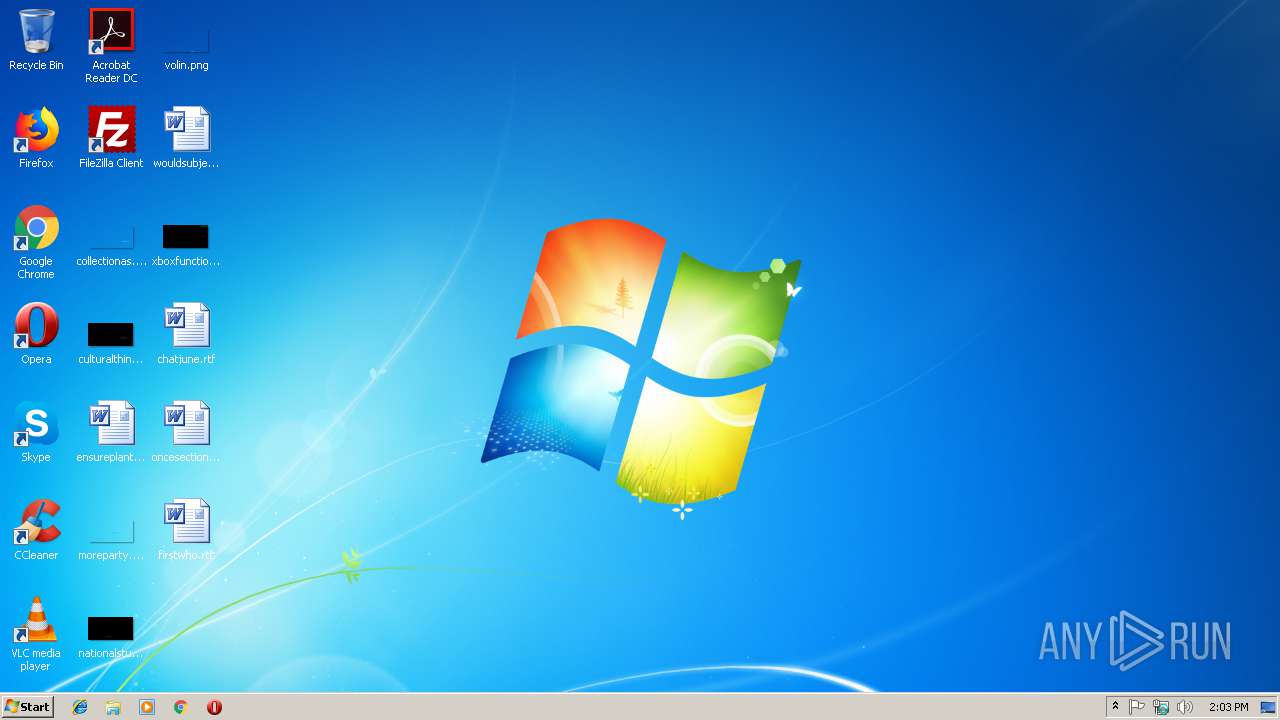
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 05C42E38333BF97F953D369C00DA6004 |
| SHA1: | A7102E0FB2B6C46A904670F49C6F0DAD46AE4950 |
| SHA256: | DDADA6B66D75A8DA28A968B2F4F94AC26ED5E70FD60B80F6F40C216EAA18BC44 |
| SSDEEP: | 3:N1K2kLUWBJLiEjLBNeomQOuUWC:C2CUWBJLnjOom3bWC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2984)
INFO
Application launched itself
- chrome.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=281B95E92C99C37B3E4EB629CE6C546D --mojo-platform-channel-handle=3468 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6AA4547189CEB899010566233BCD4A3F --mojo-platform-channel-handle=2412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --service-pipe-token=DC9C3EDD48FAE28DBEF7029386D5F84E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DC9C3EDD48FAE28DBEF7029386D5F84E --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2D92B89B9E9F67254CF38CEE1F3DDA19 --mojo-platform-channel-handle=832 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2988 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://219.76.13.168/down.sandai.net/thunderx/XunLeiSetup10.1.9.326.exe | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=AB7874DB0980905F0DAEF5FB2388F810 --mojo-platform-channel-handle=512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --service-pipe-token=20778272A85FBDCBA19F728EF5F99BB3 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=20778272A85FBDCBA19F728EF5F99BB3 --renderer-client-id=3 --mojo-platform-channel-handle=2028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f5d00b0,0x6f5d00c0,0x6f5d00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D3D797FED02E1B8EA035C7D742481B03 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
526
Read events
461
Write events
61
Delete events
4
Modification events
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13194972228857500 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2984-13194972228857500 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
1
Suspicious files
21
Text files
68
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ede072e3-d2a2-4532-8fea-2b00d0126c9a.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a8c54251-b5fe-4ea8-afaa-a3e0f832580c.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198b10.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF198b3e.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF198b3e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | chrome.exe | GET | 204 | 172.217.23.142:80 | http://translate.google.com/gen204?nca=te_li&client=te_lib&logld=vTE_20181015_01 | US | — | — | whitelisted |
2984 | chrome.exe | GET | 204 | 172.217.23.142:80 | http://translate.google.com/gen204?sl=zh-CN&tl=en&textlen=18&sp=nmt&ttt=1396&ttl=231&ttf=45&sr=1&nca=te_time&client=te_lib&logld=vTE_20181015_01 | US | — | — | whitelisted |
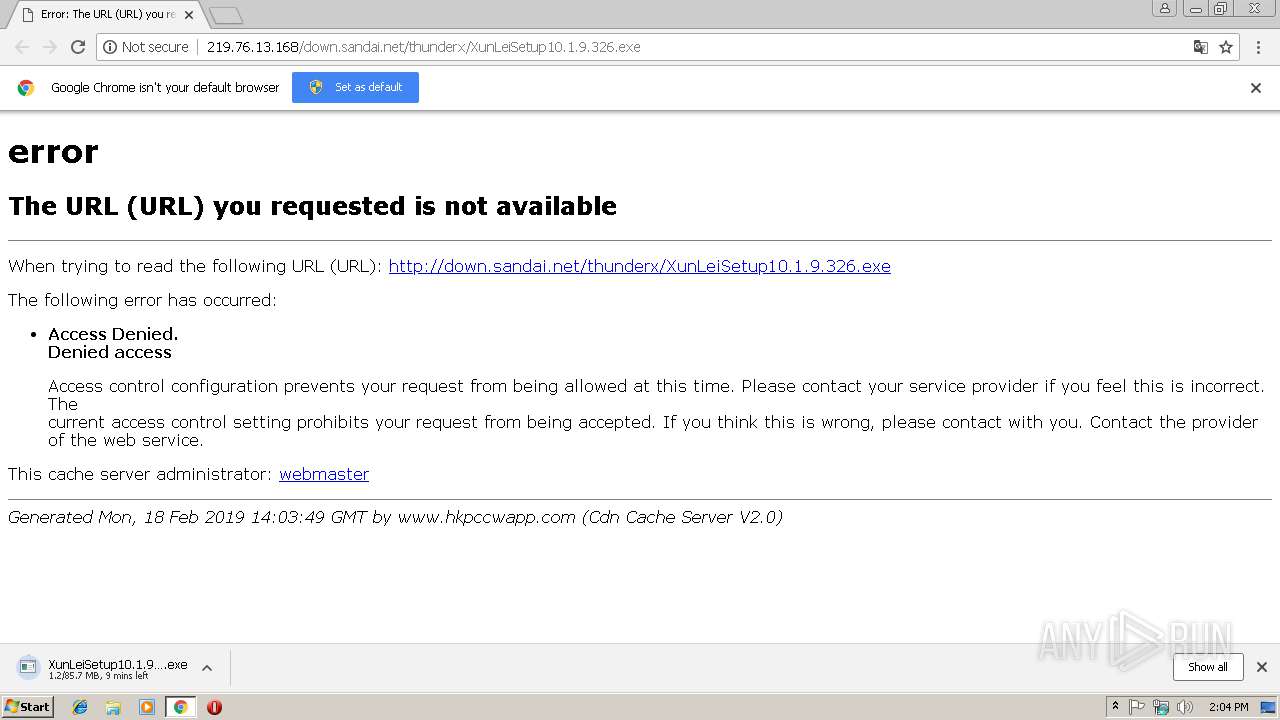
2984 | chrome.exe | GET | — | 119.188.166.184:80 | http://down.sandai.net/thunderx/XunLeiSetup10.1.9.326.exe | CN | — | — | suspicious |
2984 | chrome.exe | GET | 403 | 219.76.13.168:80 | http://219.76.13.168/down.sandai.net/thunderx/XunLeiSetup10.1.9.326.exe | HK | html | 1.16 Kb | suspicious |
2984 | chrome.exe | GET | 403 | 219.76.13.168:80 | http://219.76.13.168/favicon.ico | HK | html | 1.11 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | chrome.exe | 219.76.13.168:80 | — | PCCW Limited | HK | suspicious |
2984 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.23.138:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.23.142:80 | translate.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 119.188.166.184:80 | down.sandai.net | CHINA UNICOM China169 Backbone | CN | suspicious |
2984 | chrome.exe | 216.58.210.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
down.sandai.net |
| suspicious |
translate.googleapis.com |
| whitelisted |
translate.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2984 | chrome.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2984 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |