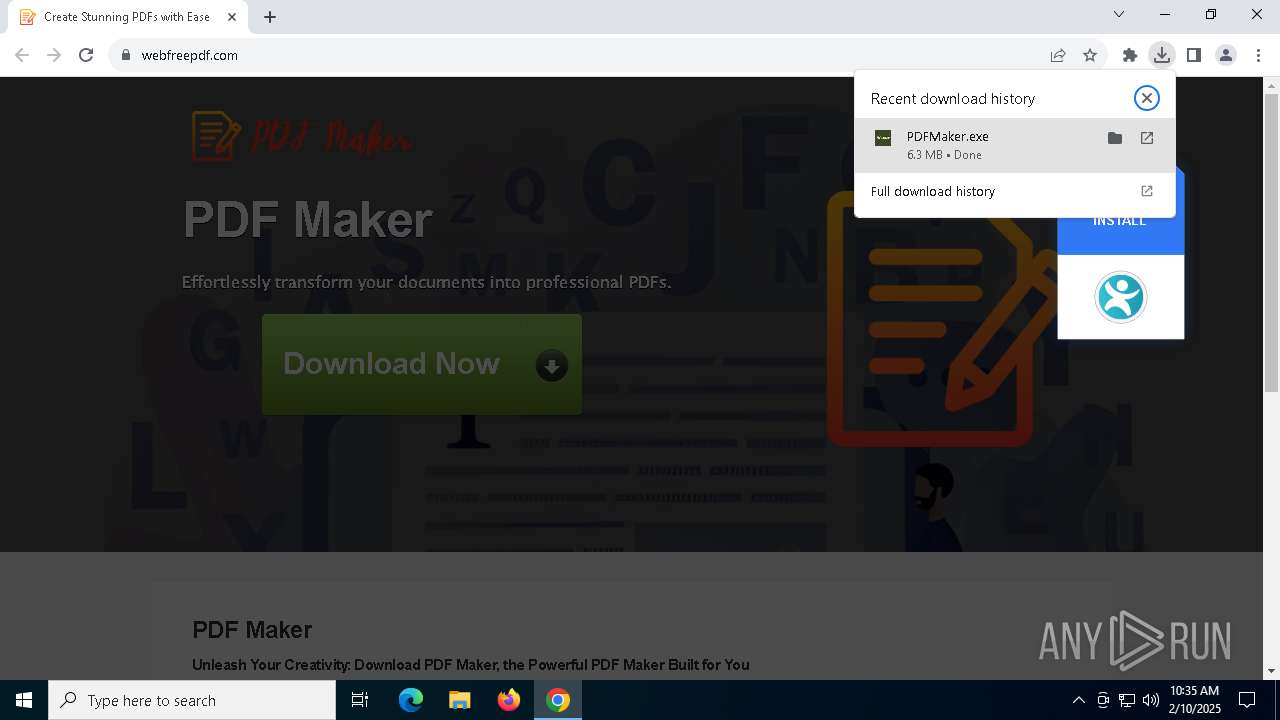
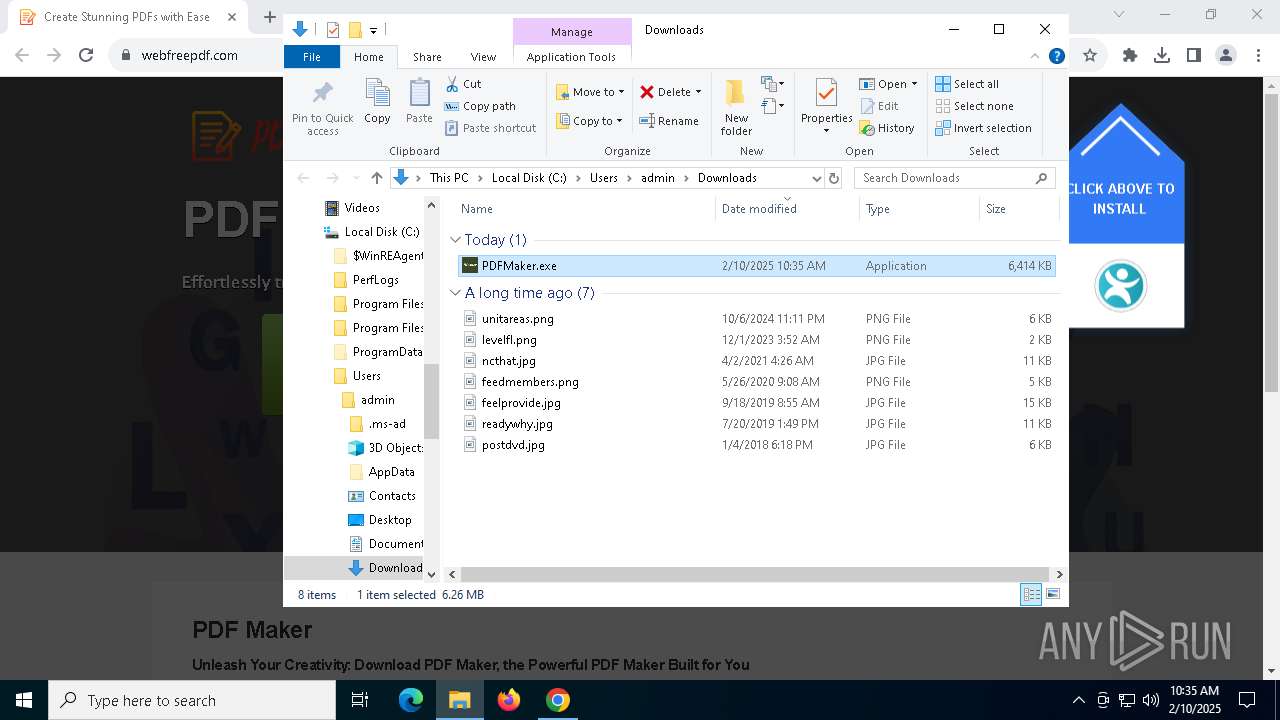
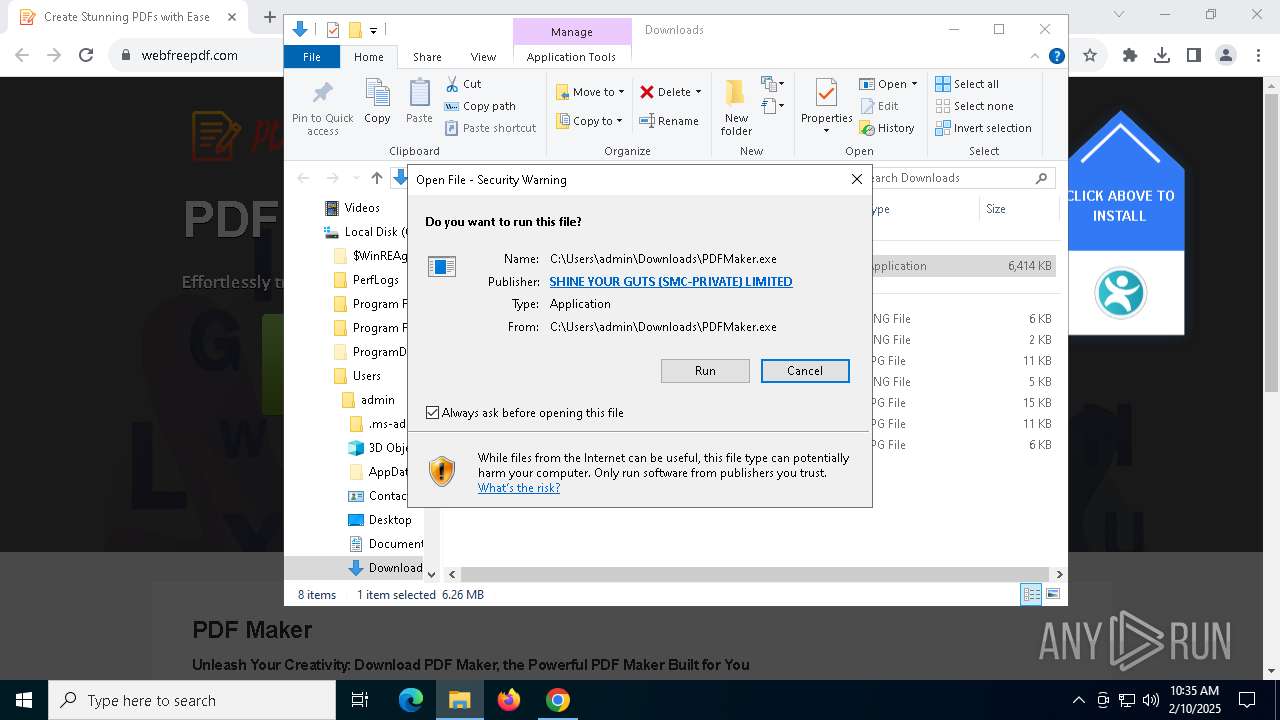
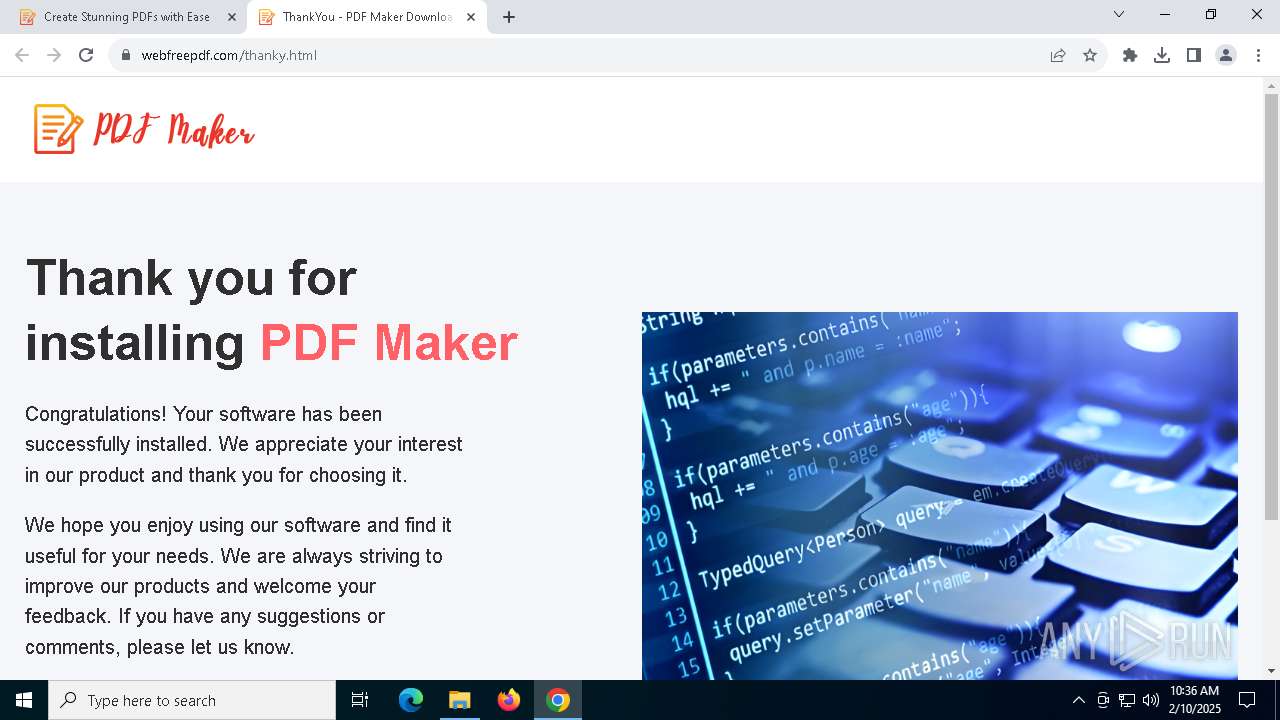
| URL: | webfreepdf.com |
| Full analysis: | https://app.any.run/tasks/eafe66ca-0a5b-4e34-a0ac-6e6a19d2dd86 |
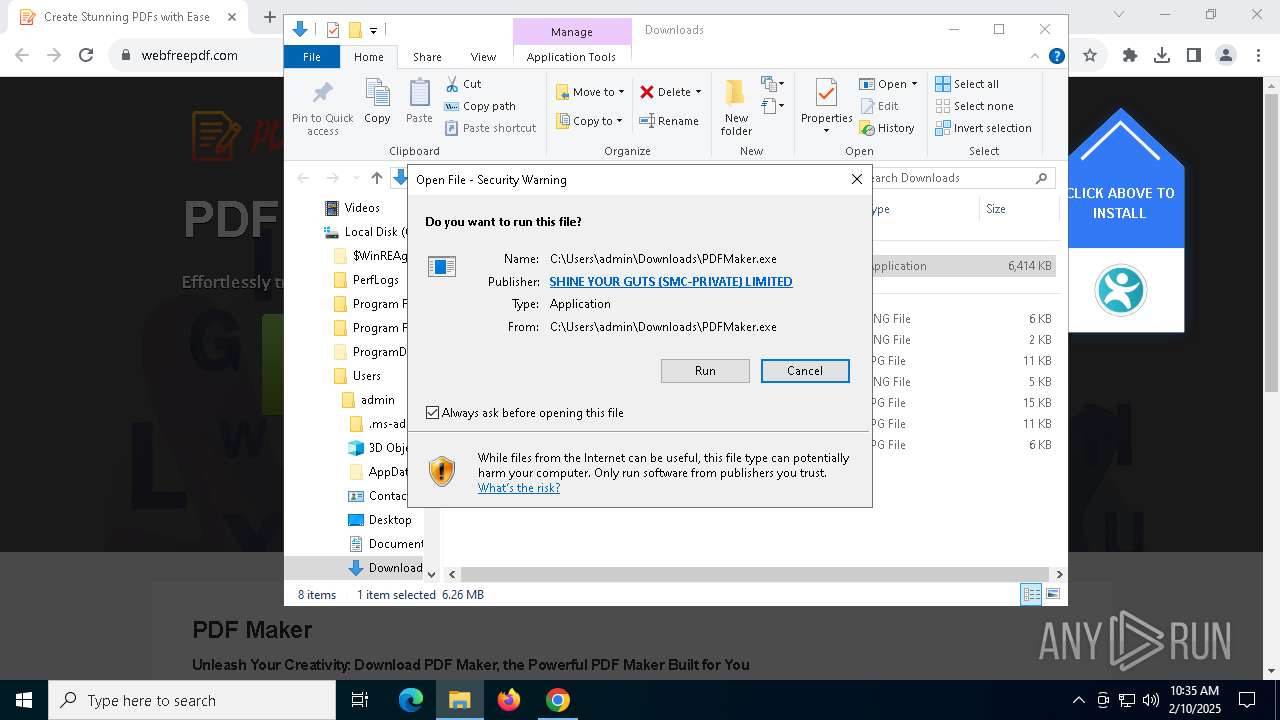
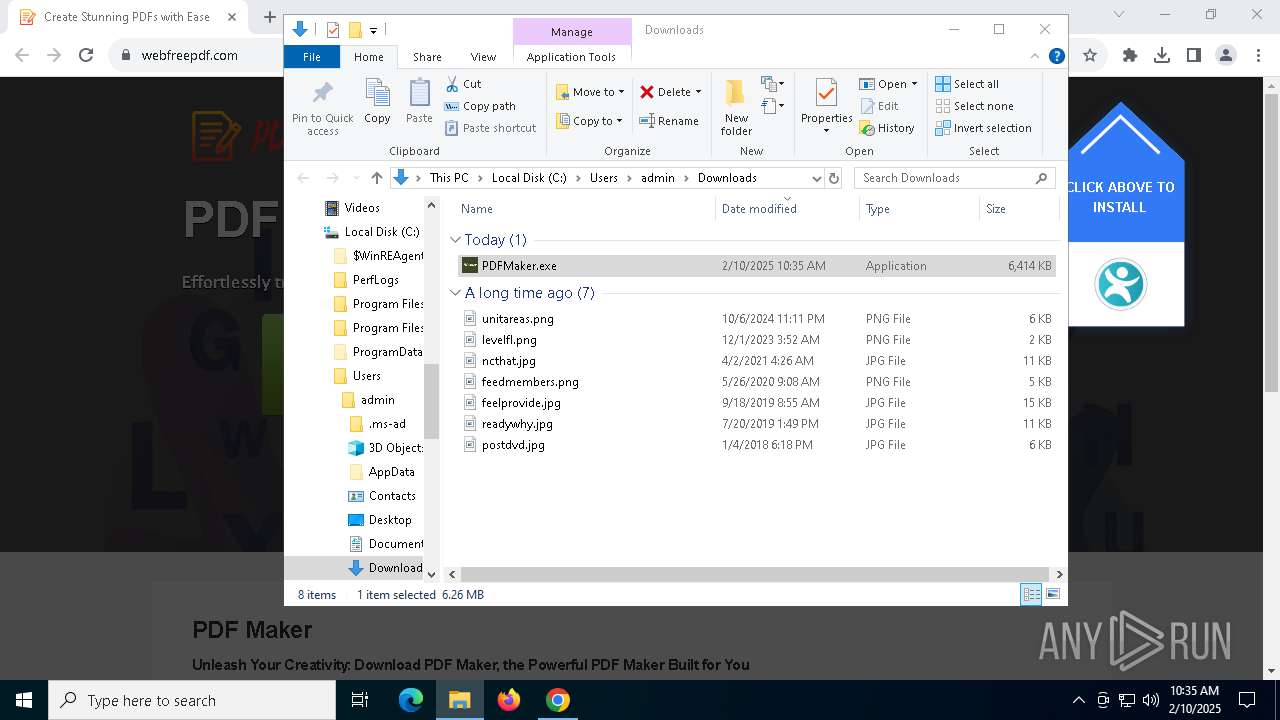
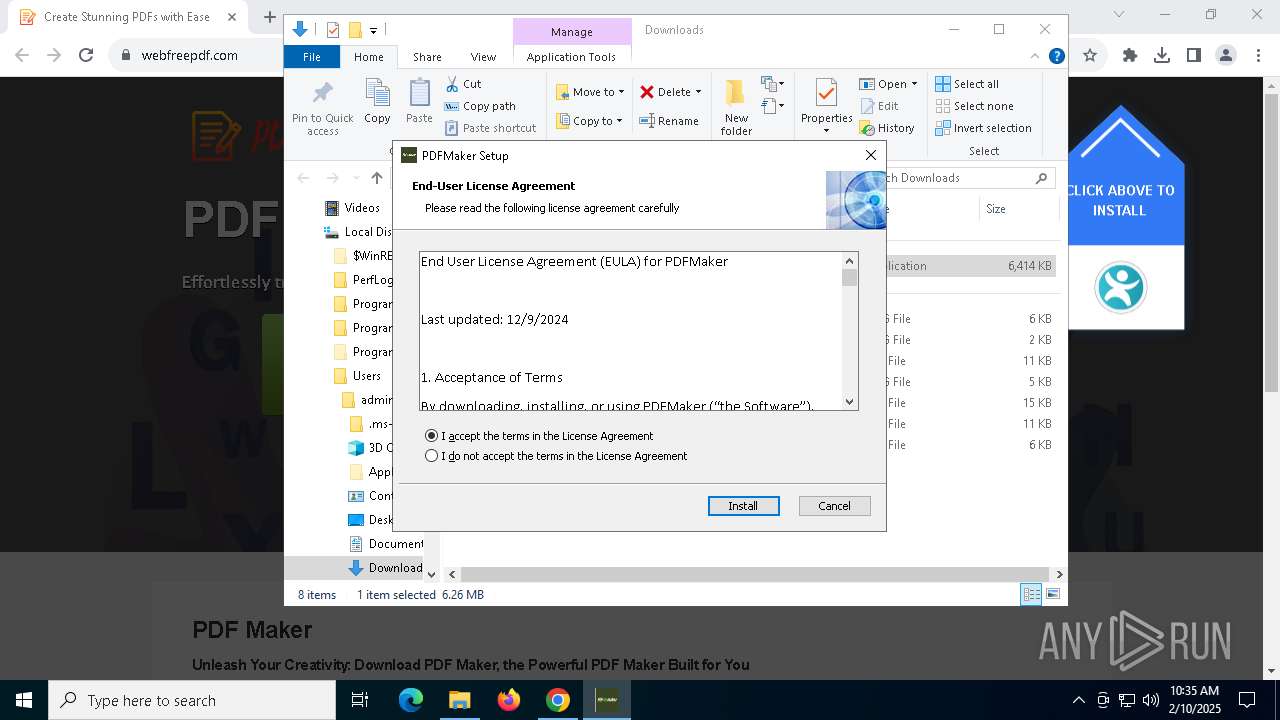
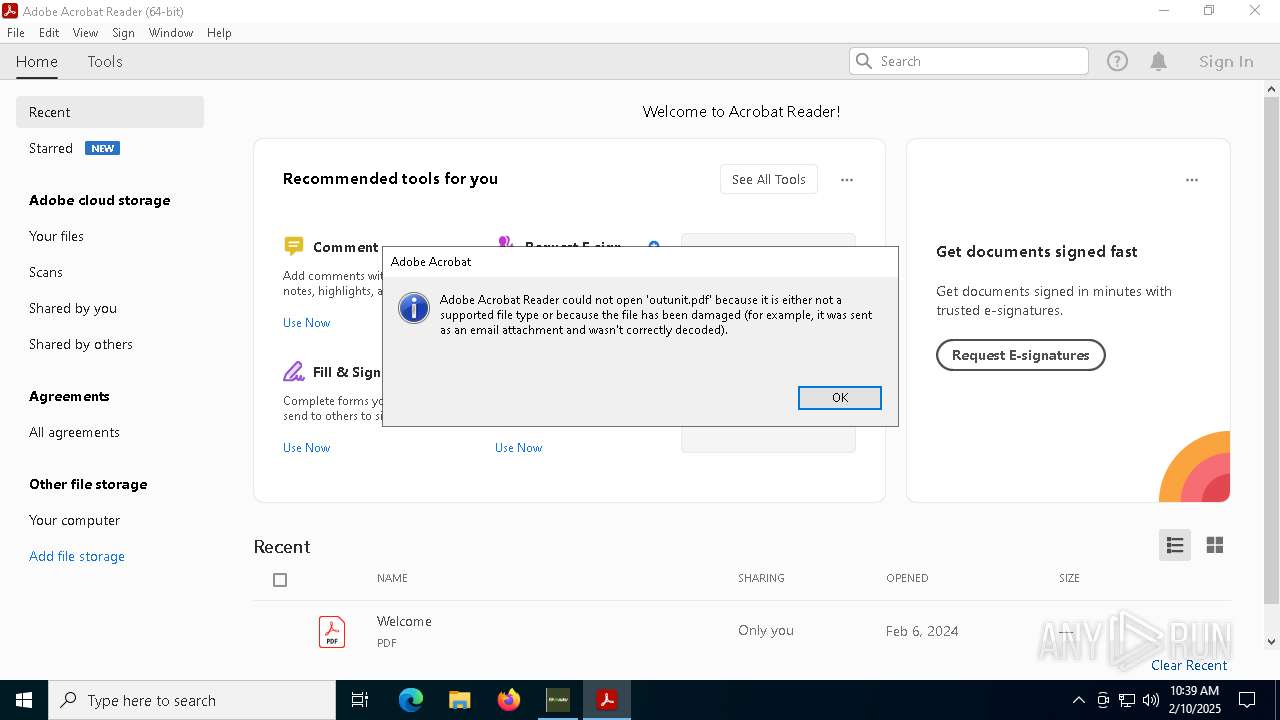
| Verdict: | Malicious activity |
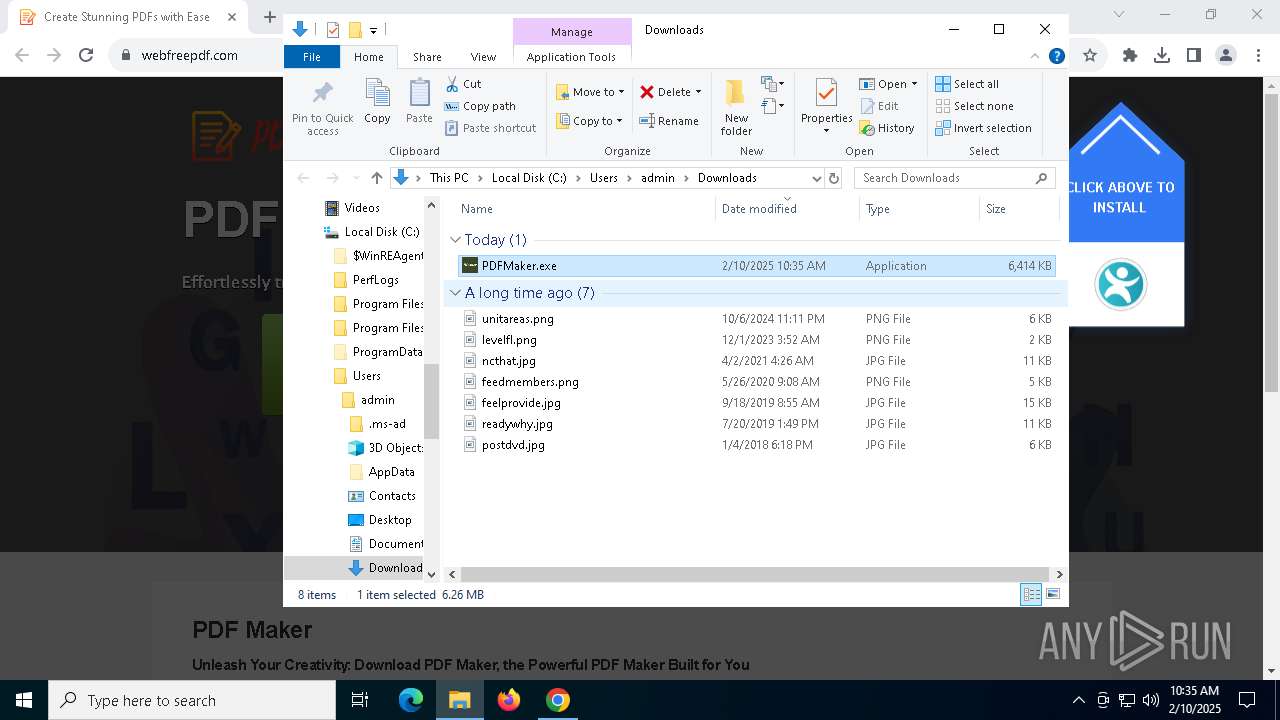
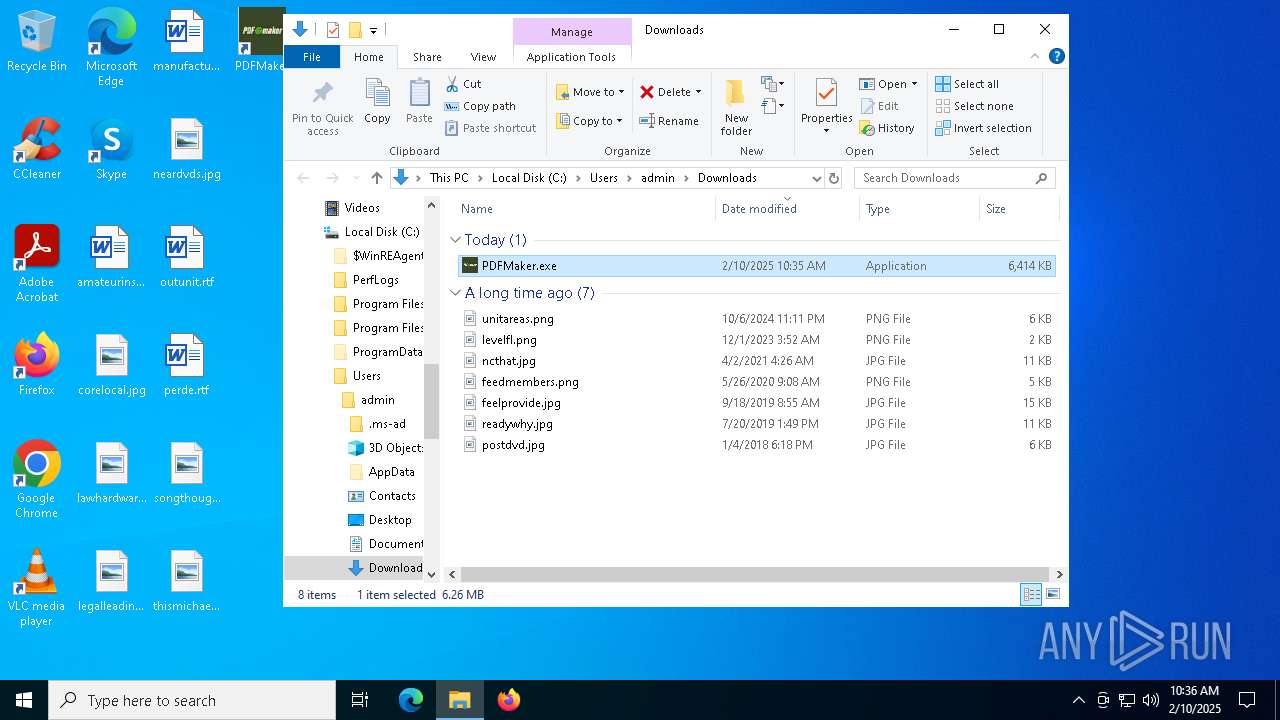
| Analysis date: | February 10, 2025, 10:35:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9ABBFAAA7CB7DFDBABAA8BBE8B3D4797 |
| SHA1: | 0BA5DFECAE7314964067F3DF4243C503358E8681 |
| SHA256: | DDAC230F2EF1A98EF163D3216B1D44D703FD4494A6912473CA989CE91824394D |
| SSDEEP: | 3:pK:pK |
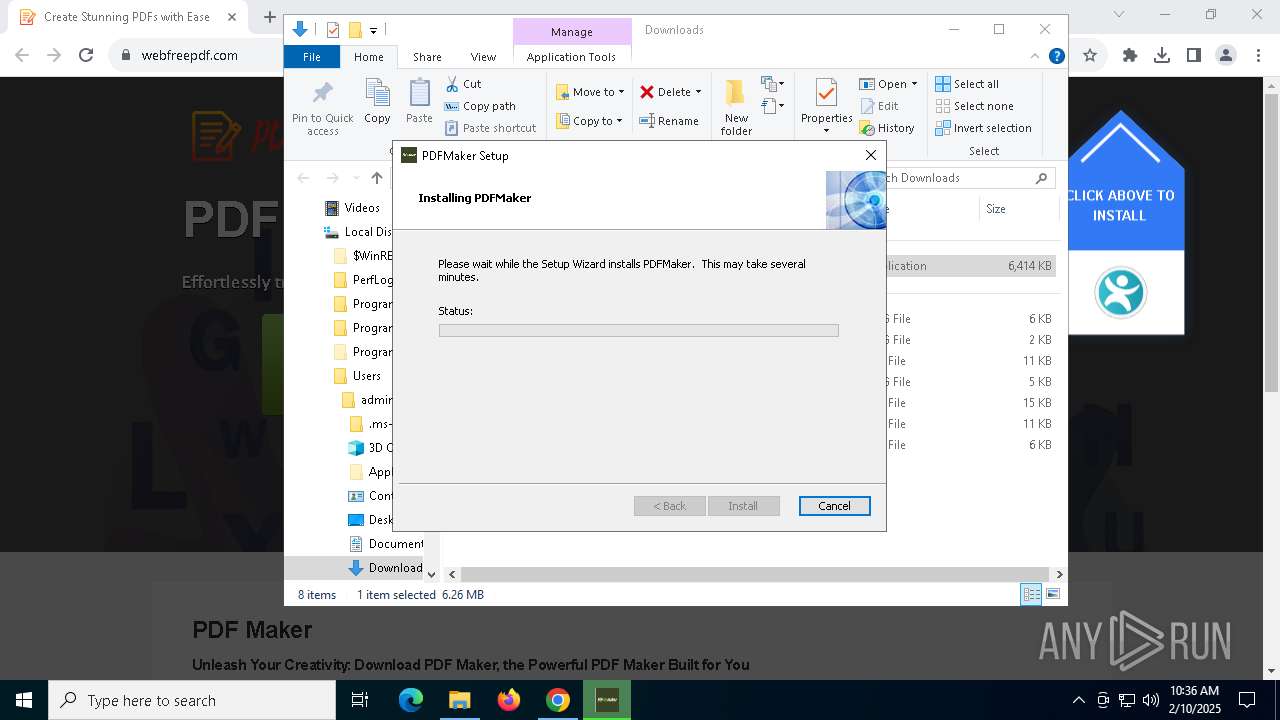
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 7876)
- powershell.exe (PID: 7512)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 7160)
- powershell.exe (PID: 7068)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 3532)
- upd.exe (PID: 4684)
- msiexec.exe (PID: 3416)
- update.exe (PID: 7272)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7512)
- powershell.exe (PID: 7160)
Run PowerShell with an invisible window
- powershell.exe (PID: 7068)
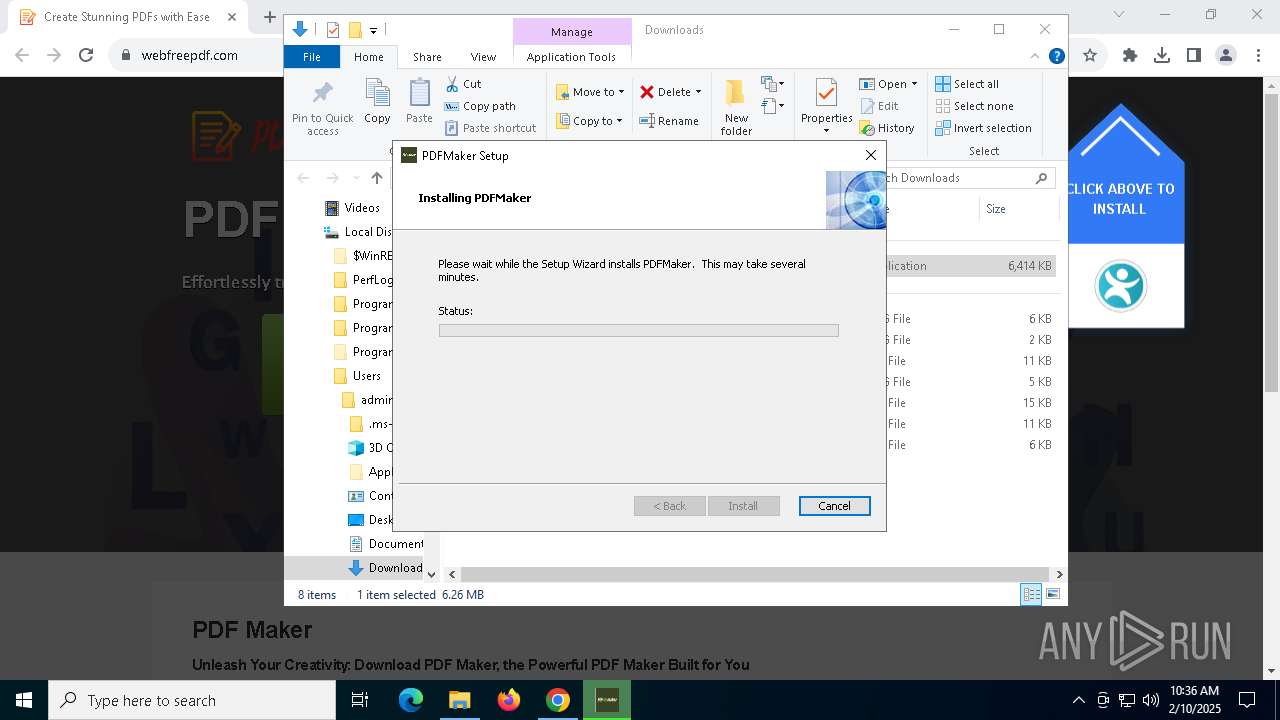
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 4488)
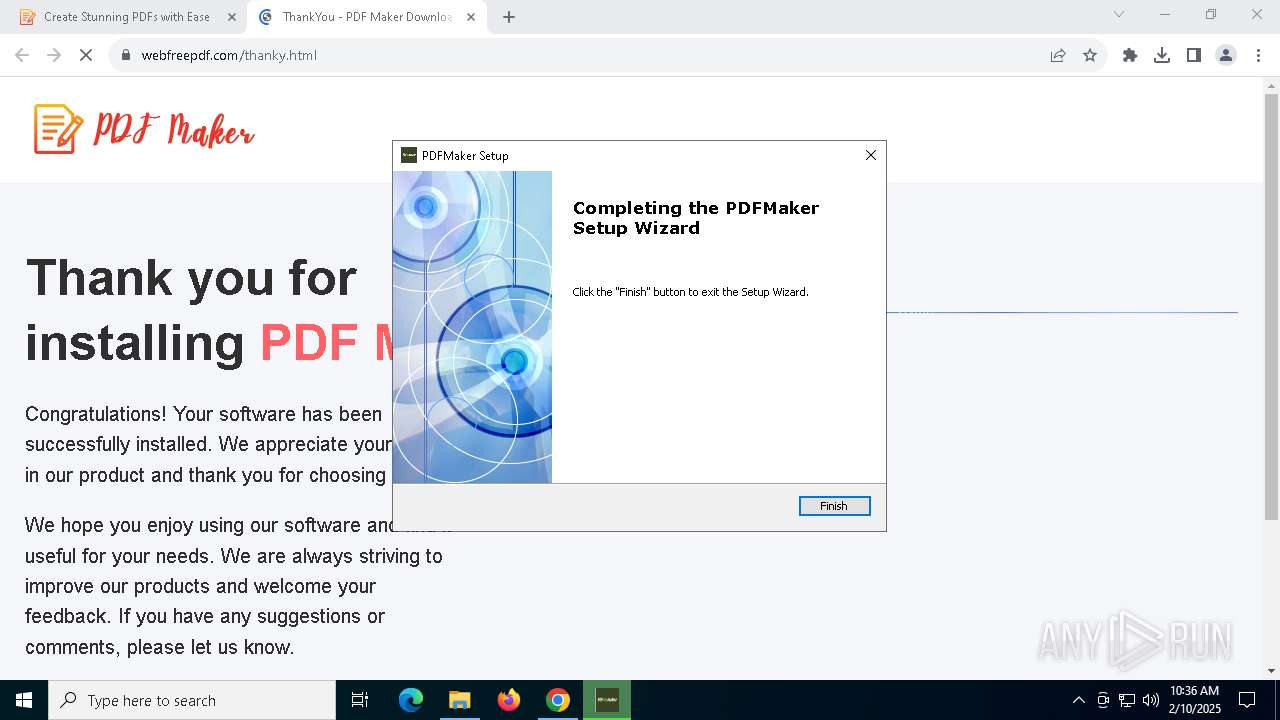
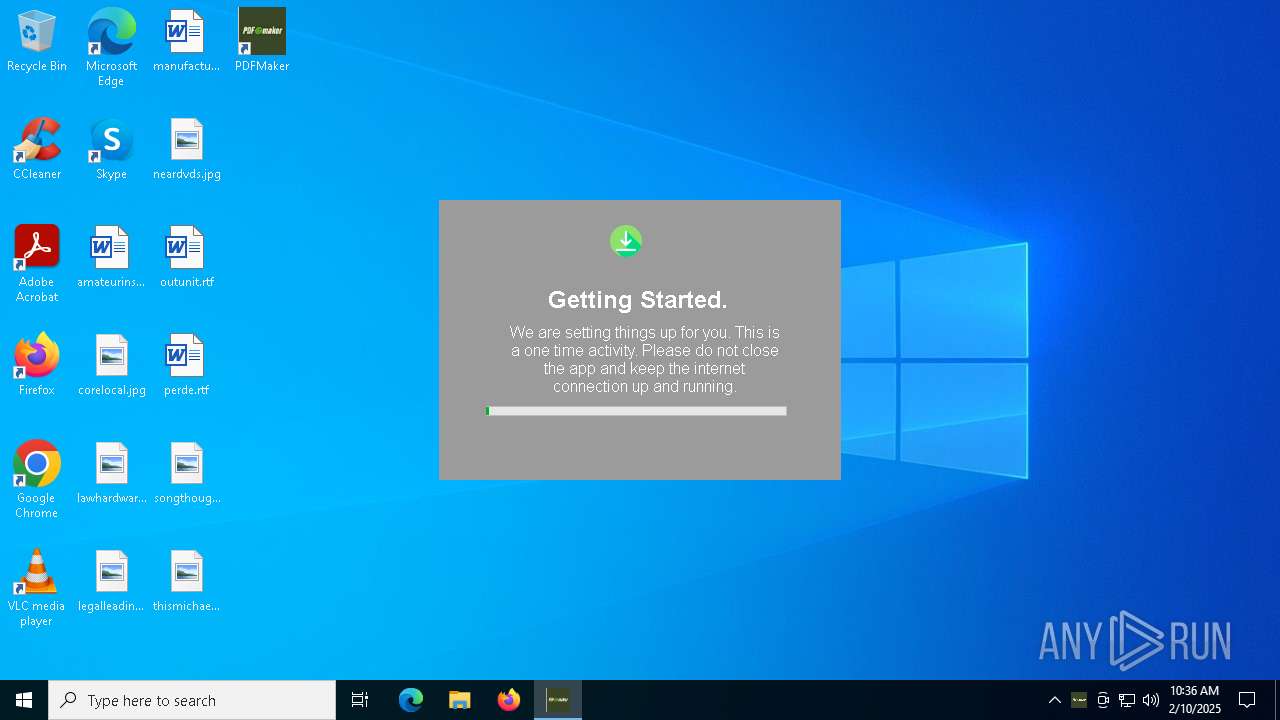
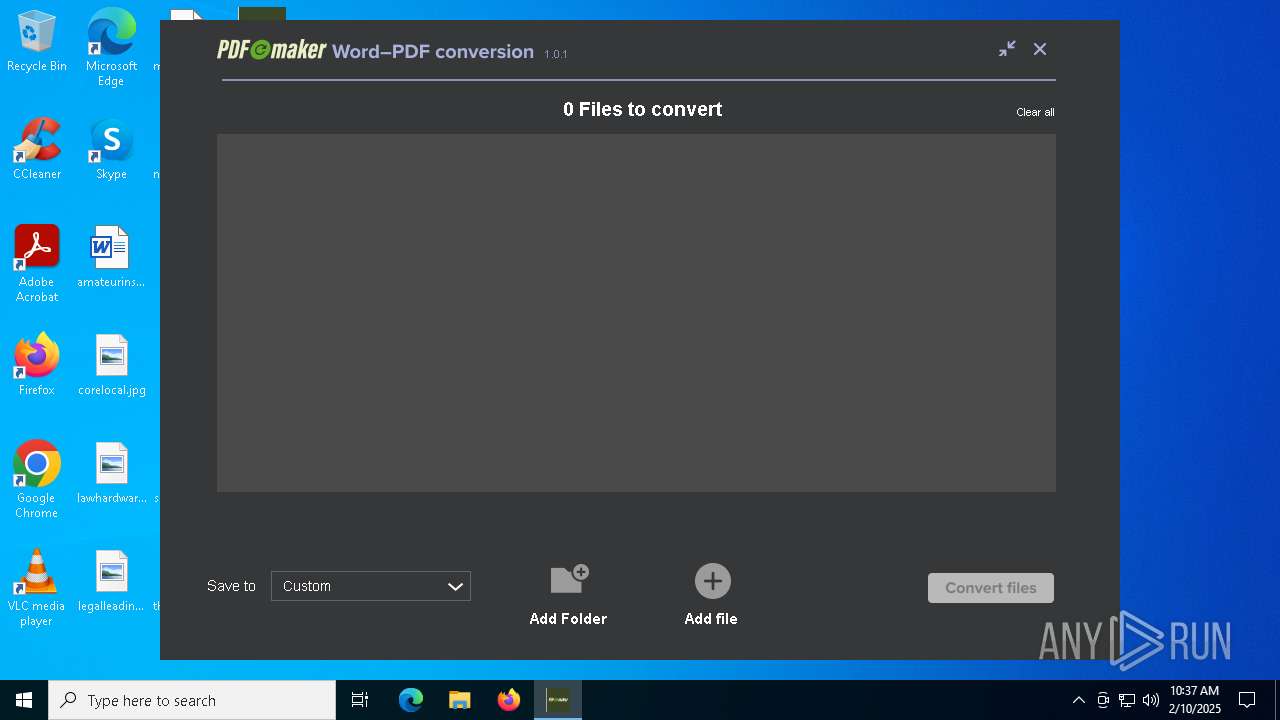
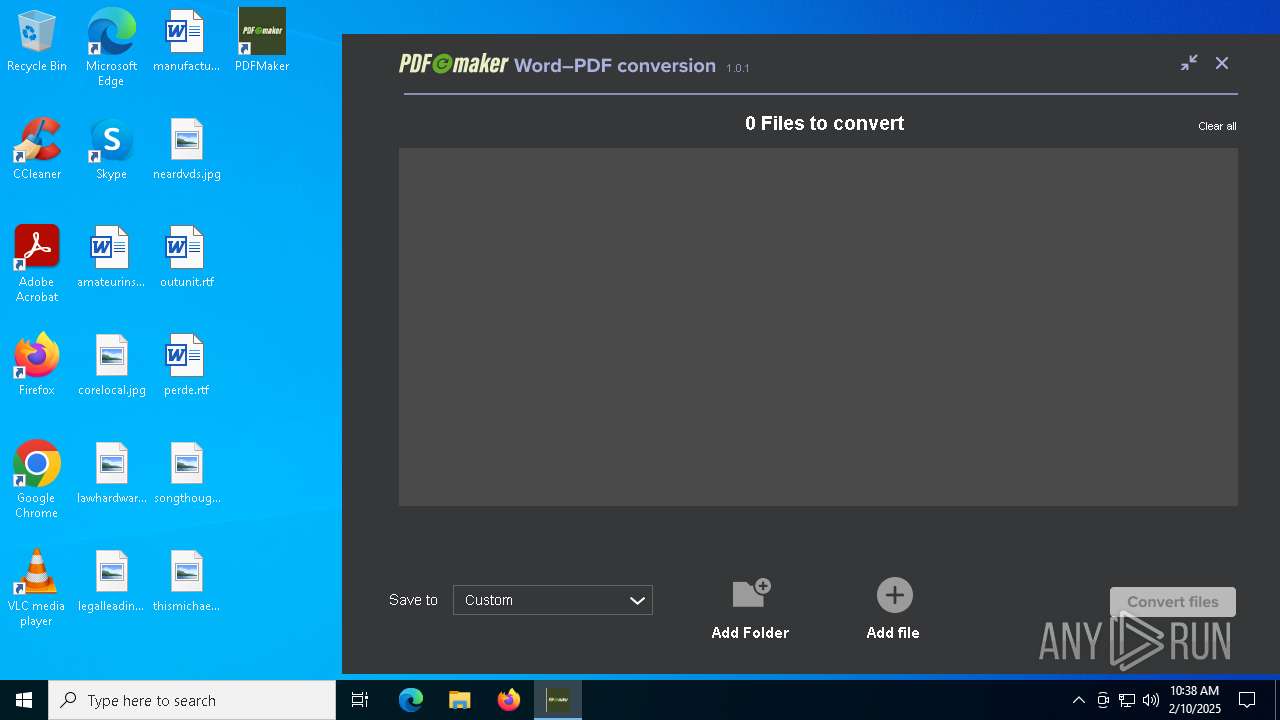
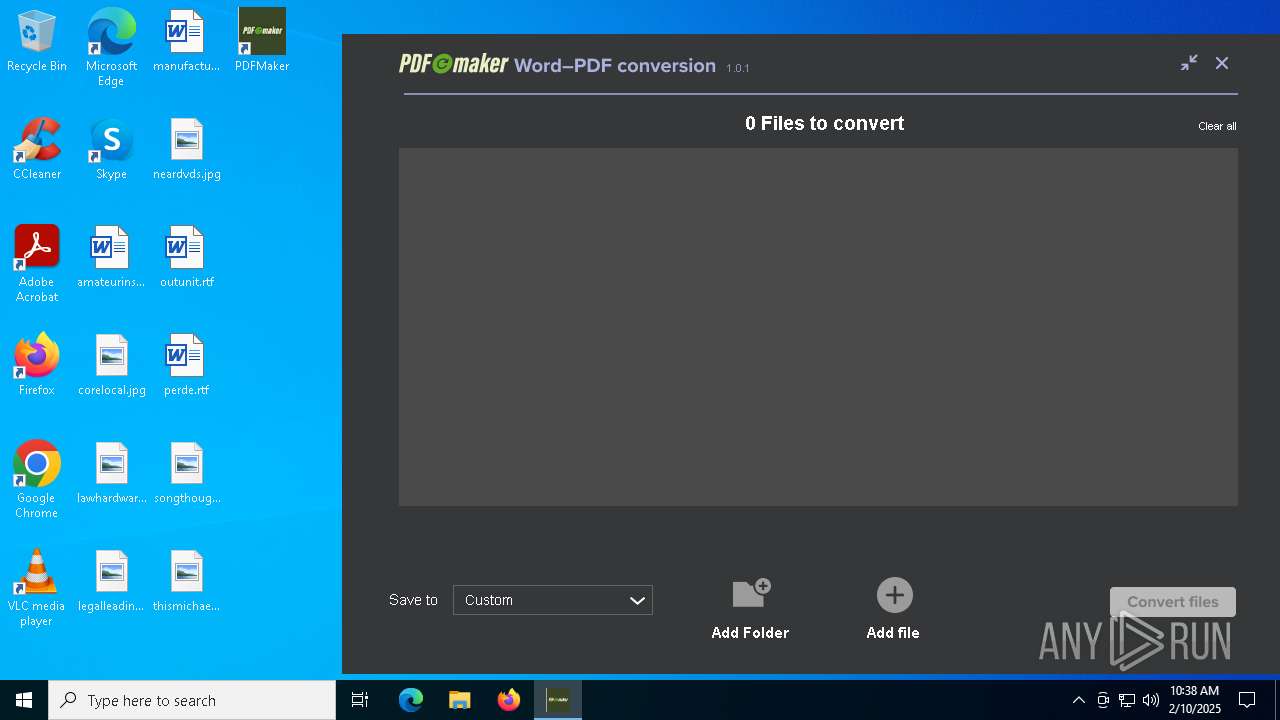
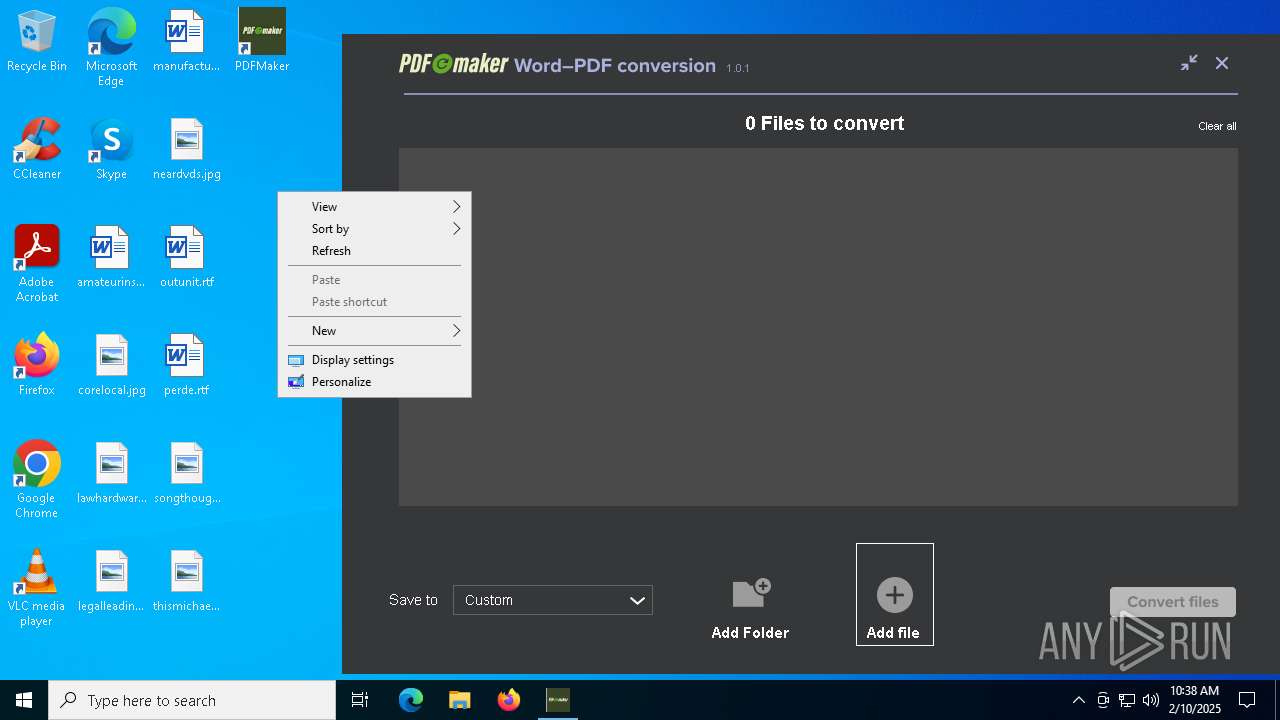
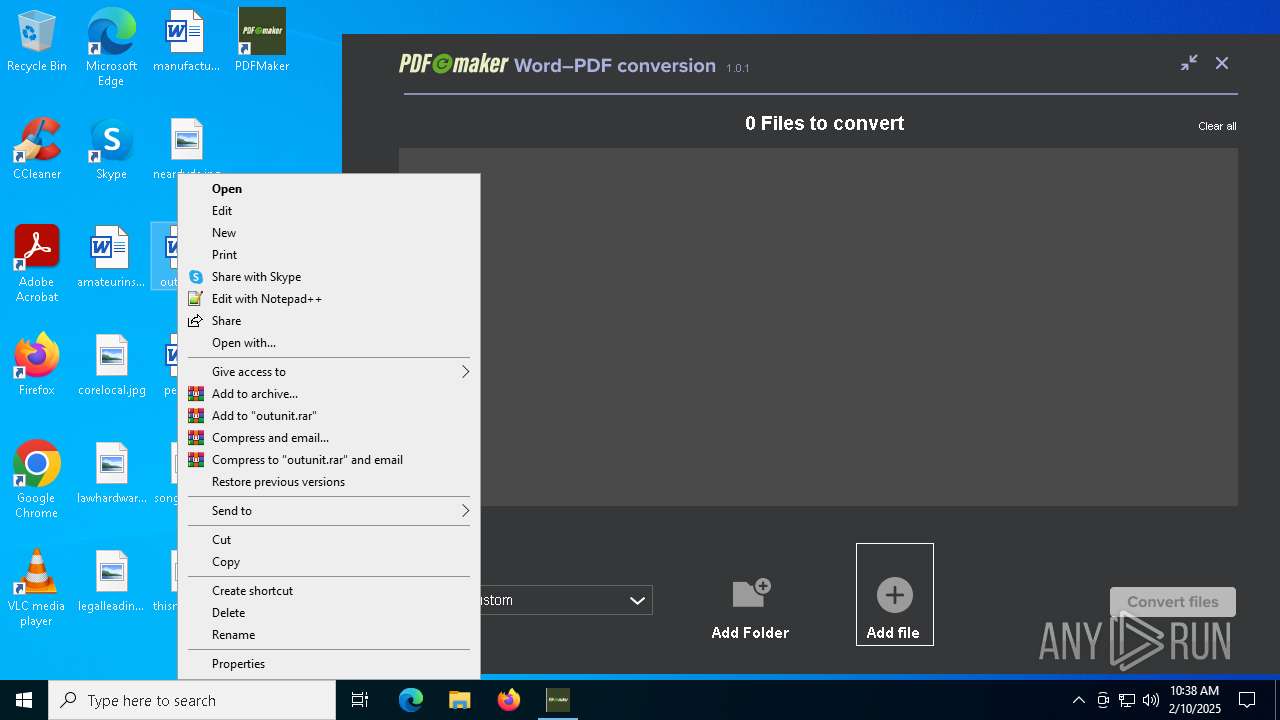
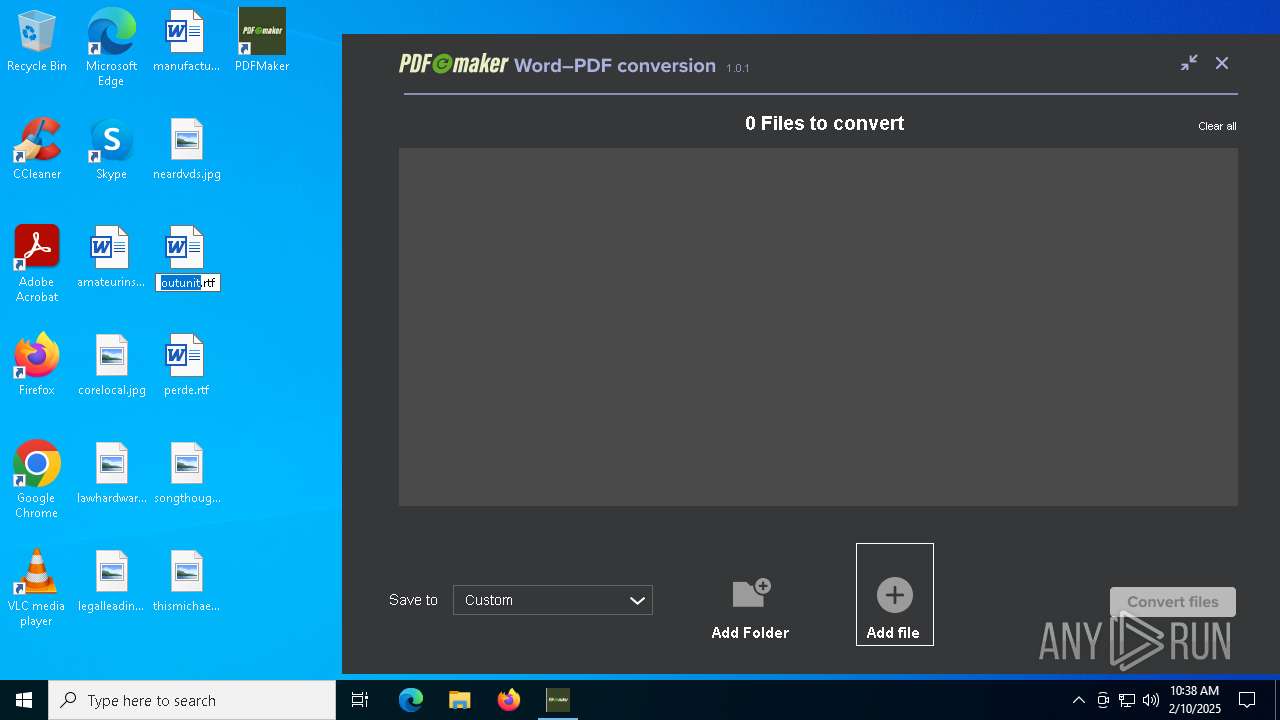
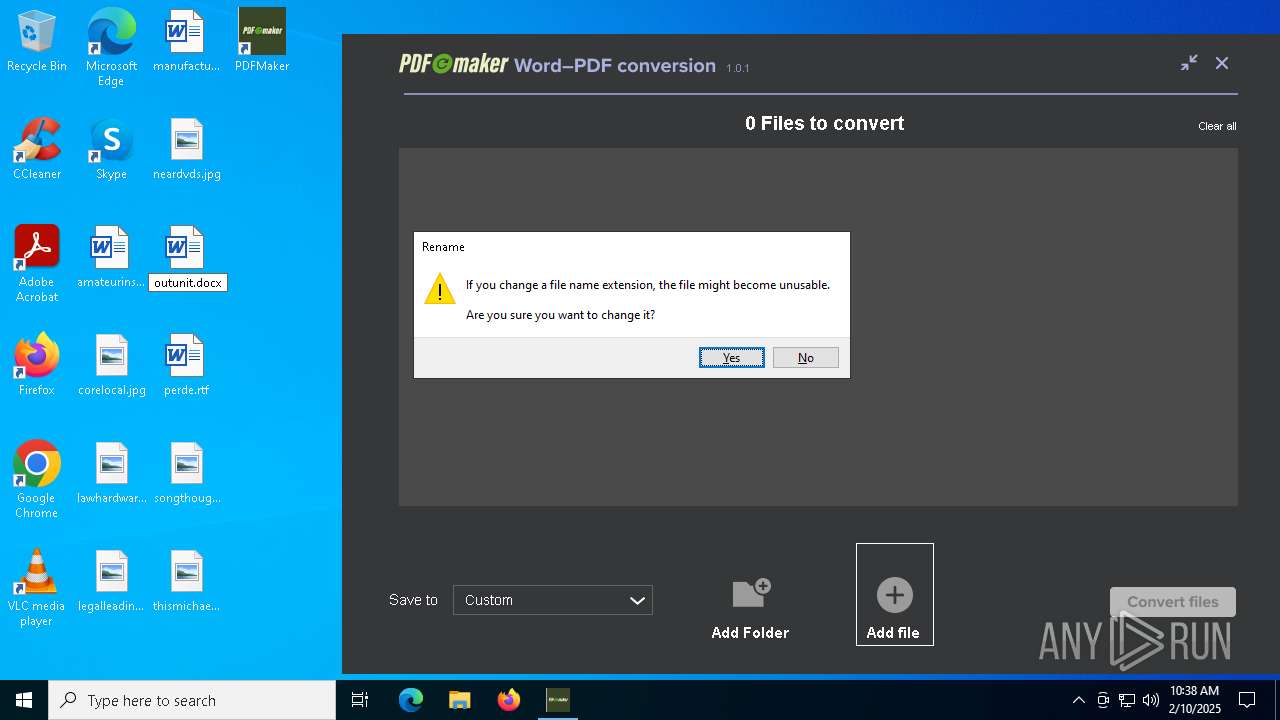
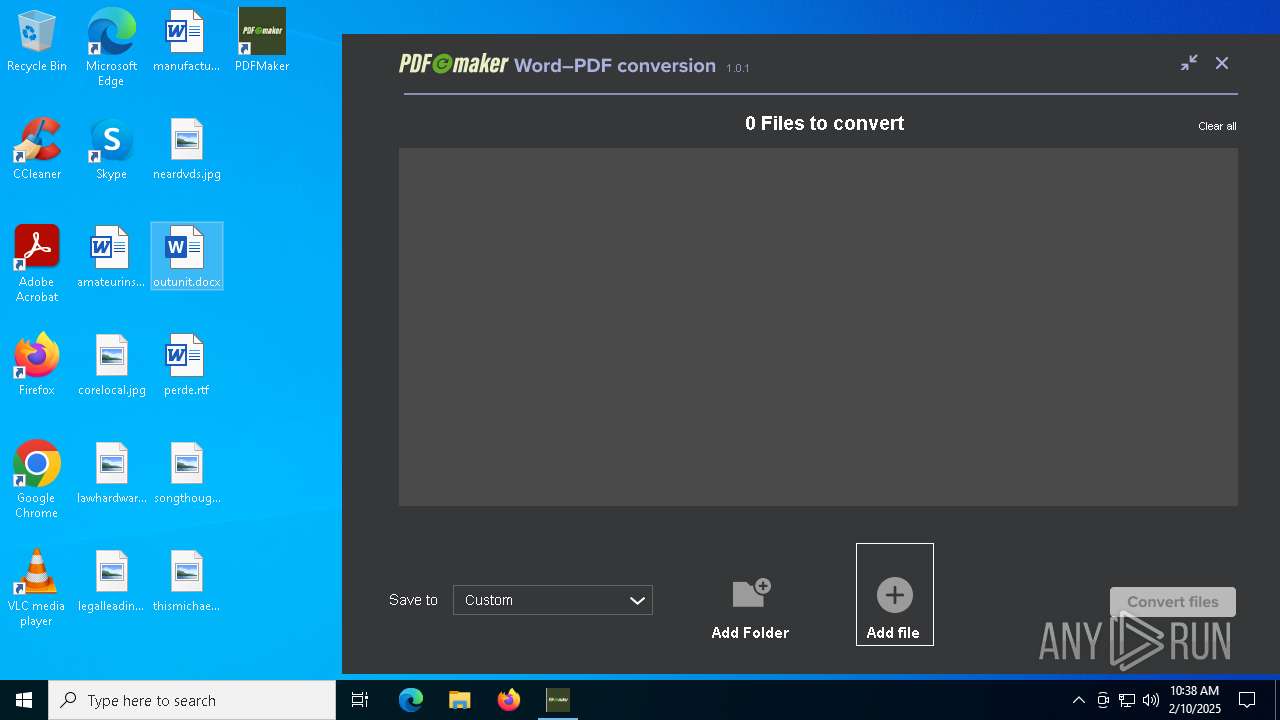
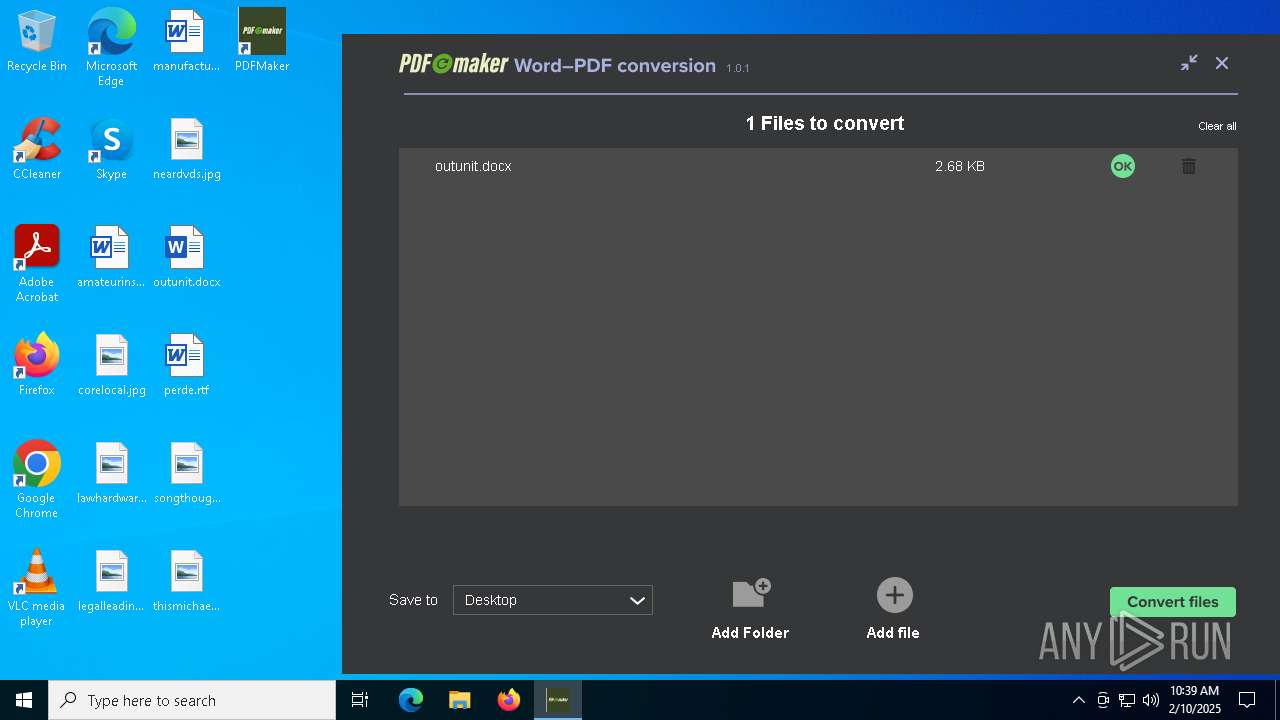
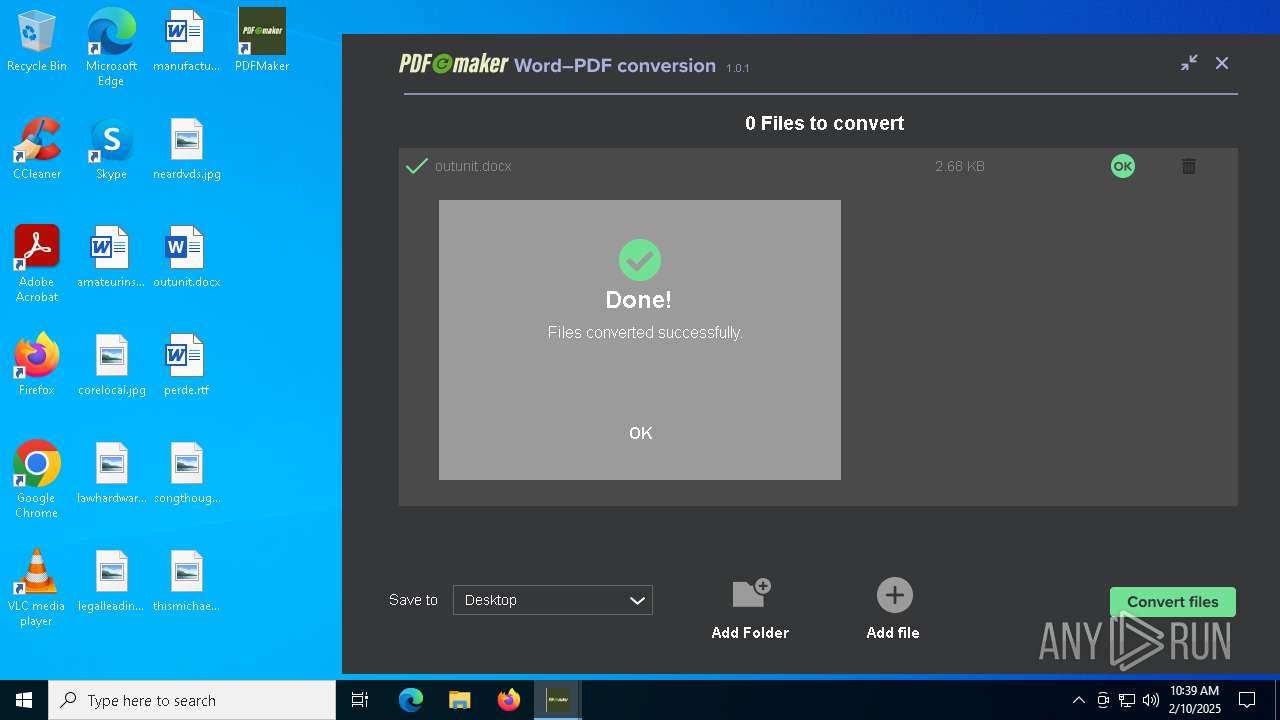
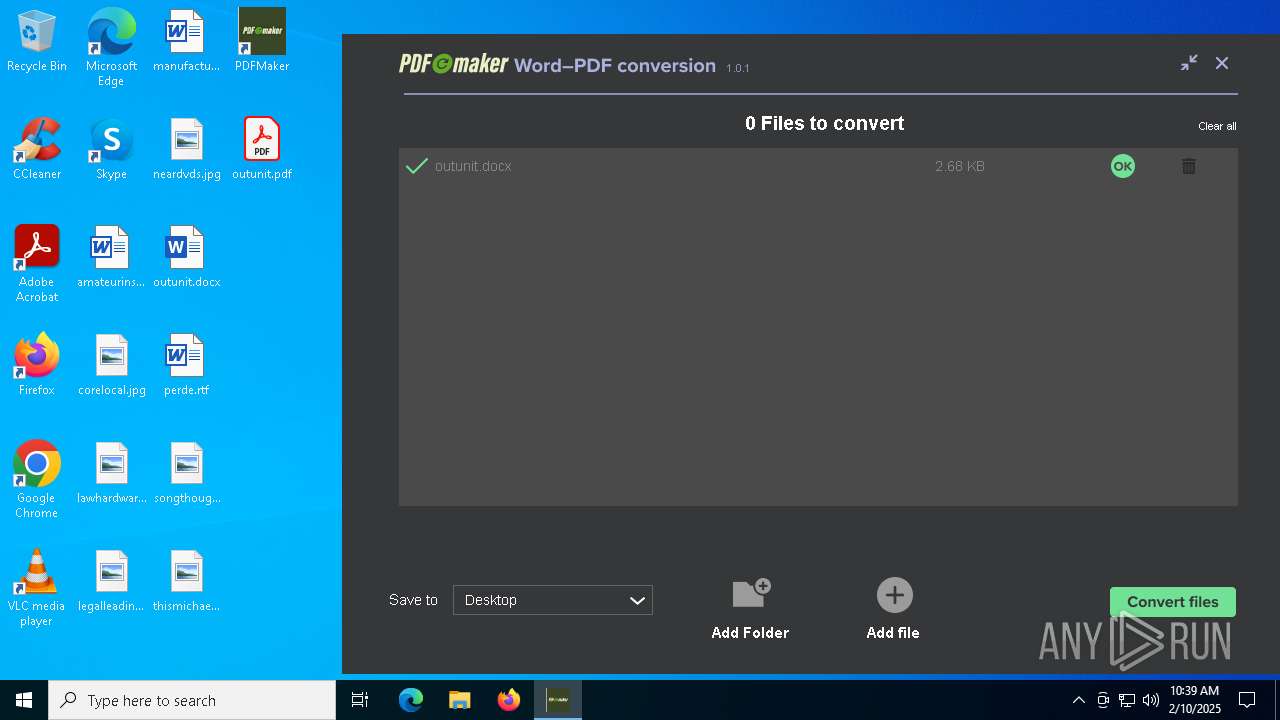
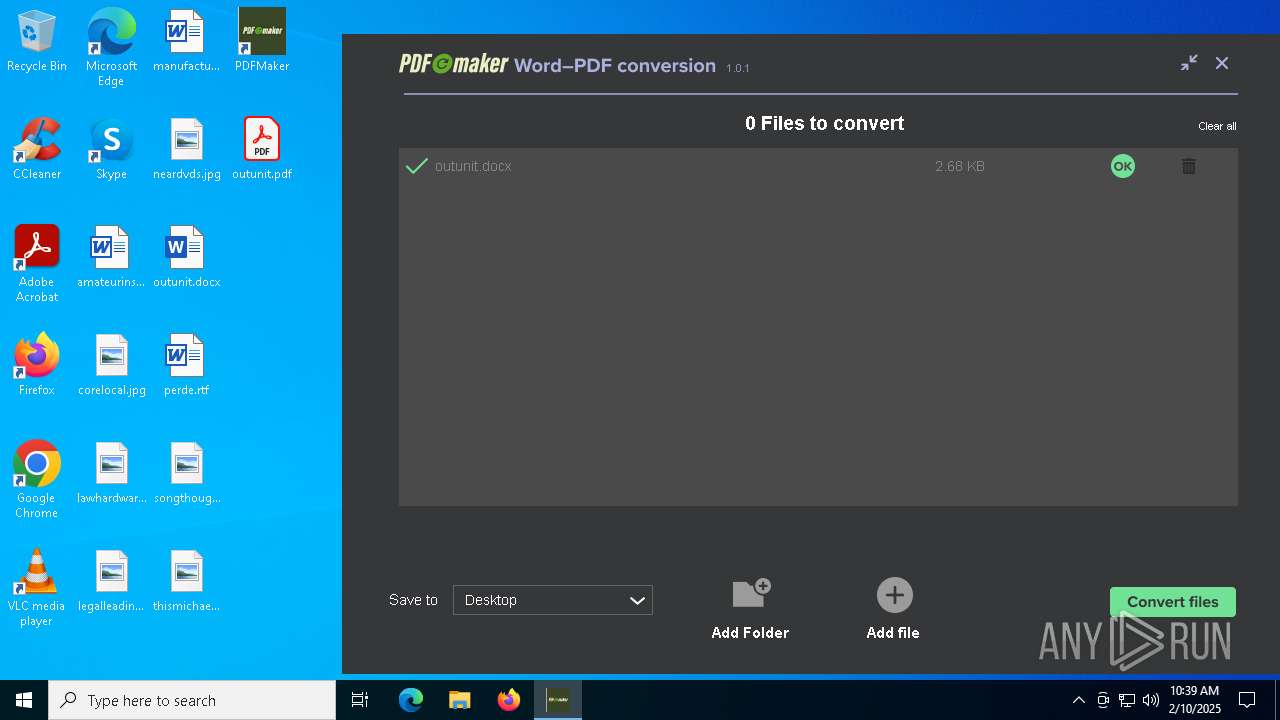
ADVANCEDINSTALLER mutex has been found
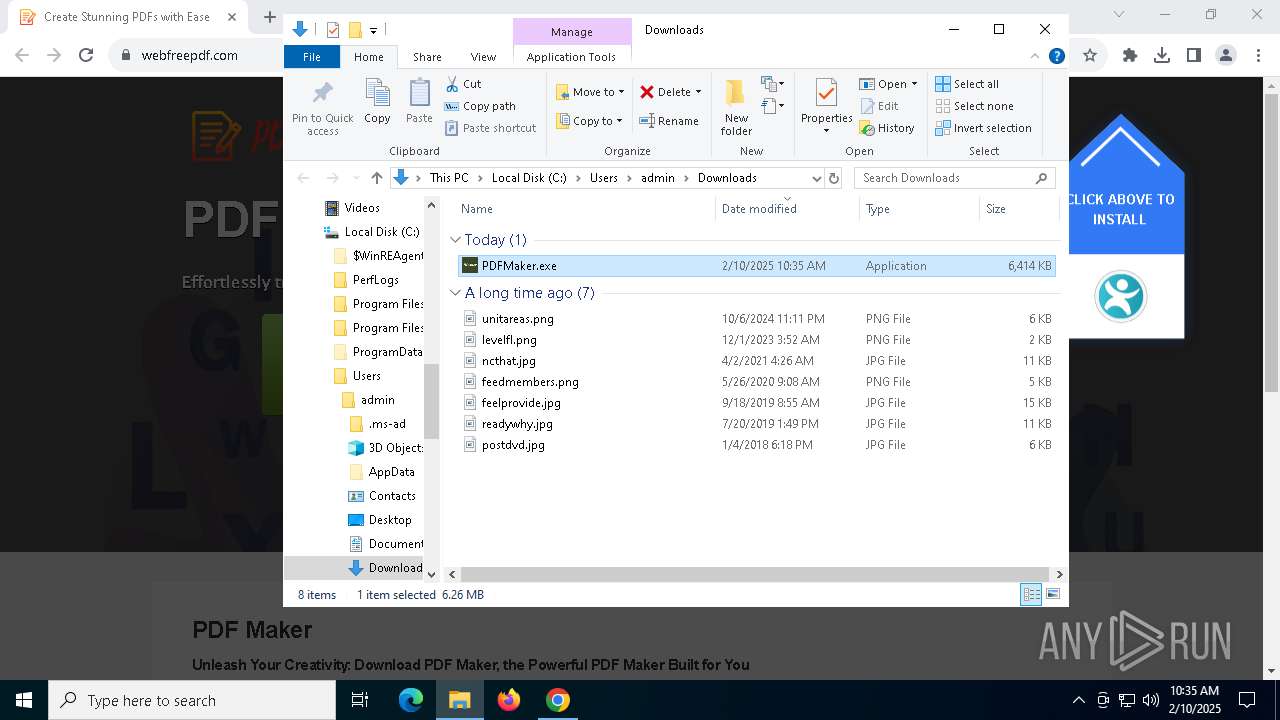
- PDFMaker.exe (PID: 4516)
- PDFMaker-1.0.1.exe (PID: 8120)
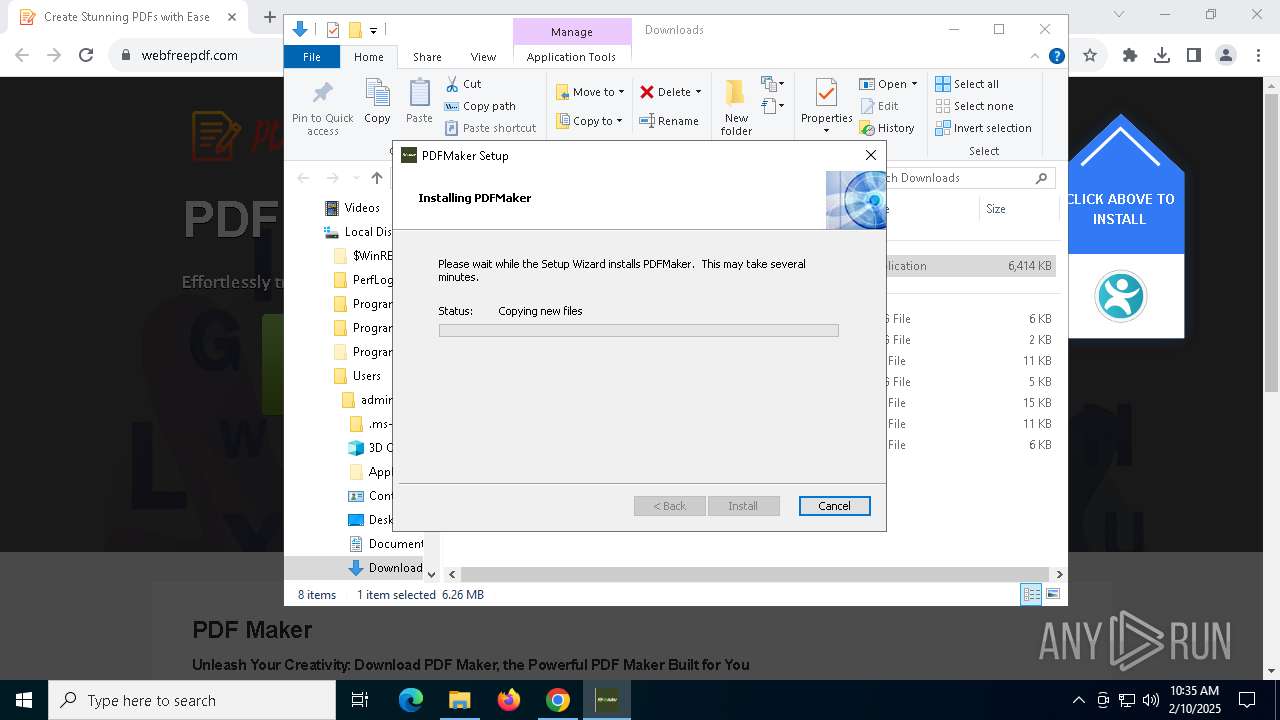
Executable content was dropped or overwritten
- PDFMaker.exe (PID: 4516)
- rundll32.exe (PID: 628)
- rundll32.exe (PID: 524)
- PDFMaker.exe (PID: 6160)
- rundll32.exe (PID: 5340)
- rundll32.exe (PID: 5320)
- PDFMaker.exe (PID: 5872)
- updater.exe (PID: 6176)
- PDFMaker-1.0.1.exe (PID: 8120)
- updater.exe (PID: 7496)
- rundll32.exe (PID: 556)
- rundll32.exe (PID: 3824)
- 7z.exe (PID: 7220)
- decrypt.exe (PID: 7684)
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
- decrypt.exe (PID: 2412)
Reads security settings of Internet Explorer
- PDFMaker.exe (PID: 4516)
- PDFMaker.exe (PID: 6160)
- PDFMaker-1.0.1.exe (PID: 8120)
- updater.exe (PID: 7496)
- PDFMaker.exe (PID: 7624)
Checks Windows Trust Settings
- PDFMaker.exe (PID: 4516)
- msiexec.exe (PID: 5628)
- PDFMaker.exe (PID: 6160)
- PDFMaker-1.0.1.exe (PID: 8120)
- updater.exe (PID: 7496)
Process drops legitimate windows executable
- PDFMaker.exe (PID: 4516)
- PDFMaker.exe (PID: 6160)
- msiexec.exe (PID: 5628)
- PDFMaker.exe (PID: 5872)
- PDFMaker-1.0.1.exe (PID: 8120)
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
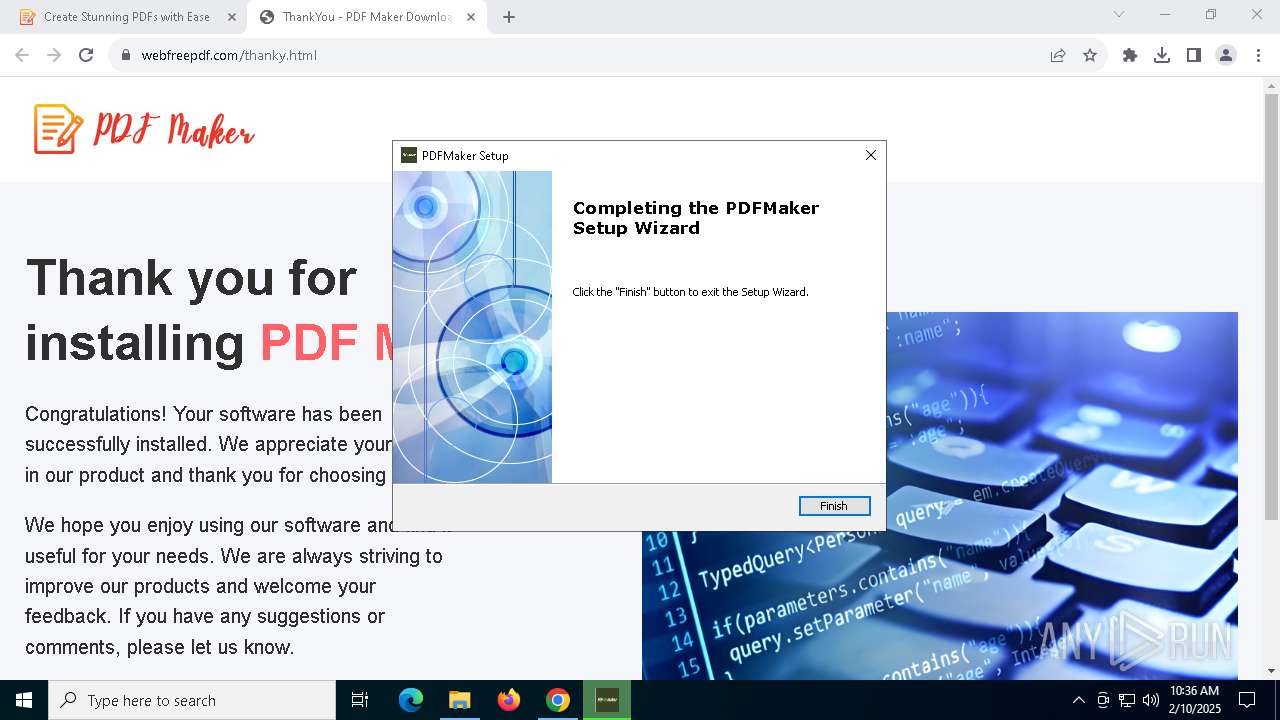
Application launched itself
- PDFMaker.exe (PID: 4516)
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
Reads the Windows owner or organization settings
- PDFMaker.exe (PID: 4516)
- PDFMaker.exe (PID: 6160)
- msiexec.exe (PID: 5628)
The process drops C-runtime libraries
- PDFMaker.exe (PID: 4516)
- msiexec.exe (PID: 5628)
- PDFMaker.exe (PID: 5872)
- PDFMaker-1.0.1.exe (PID: 8120)
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 3532)
- msiexec.exe (PID: 3416)
The process executes Powershell scripts
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 3532)
- upd.exe (PID: 4684)
- msiexec.exe (PID: 3416)
- update.exe (PID: 7272)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 3532)
- msiexec.exe (PID: 3416)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 3532)
- msiexec.exe (PID: 3416)
- upd.exe (PID: 1612)
- update.exe (PID: 7272)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 4132)
- system15627a17808b7546c (PID: 2224)
- upd.exe (PID: 4684)
There is functionality for taking screenshot (YARA)
- PDFMaker.exe (PID: 4516)
- updater.exe (PID: 7496)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 6388)
The process executes via Task Scheduler
- upd.exe (PID: 4684)
Starts itself from another location
- updater.exe (PID: 6176)
Drops 7-zip archiver for unpacking
- PDFMaker-1.0.1.exe (PID: 8120)
- msiexec.exe (PID: 5628)
Base64-obfuscated command line is found
- upd.exe (PID: 1612)
BASE64 encoded PowerShell command has been detected
- upd.exe (PID: 1612)
Hides command output
- cmd.exe (PID: 7544)
- cmd.exe (PID: 4132)
Starts CMD.EXE for commands execution
- decrypt.exe (PID: 7684)
- decrypt.exe (PID: 2412)
- system15627a17808b7546c (PID: 2224)
Starts application with an unusual extension
- powershell.exe (PID: 7824)
- system15627a17808b7546c (PID: 6600)
- powershell.exe (PID: 5912)
- system15627a17808b7546c (PID: 3824)
Loads Python modules
- system15627a17808b7546c (PID: 7596)
- system15627a17808b7546c (PID: 2224)
Starts process via Powershell
- powershell.exe (PID: 7824)
- powershell.exe (PID: 5912)
Process drops python dynamic module
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
Searches for installed software
- system15627a17808b7546c (PID: 2224)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6788)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 7748)
Uses WMIC.EXE
- cmd.exe (PID: 68)
- cmd.exe (PID: 624)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 2572)
INFO
Application launched itself
- chrome.exe (PID: 6592)
- chrome.exe (PID: 8136)
- Acrobat.exe (PID: 7400)
- AcroCEF.exe (PID: 5340)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7876)
- powershell.exe (PID: 4996)
- explorer.exe (PID: 7444)
- powershell.exe (PID: 6388)
- WMIC.exe (PID: 6912)
- WMIC.exe (PID: 6832)
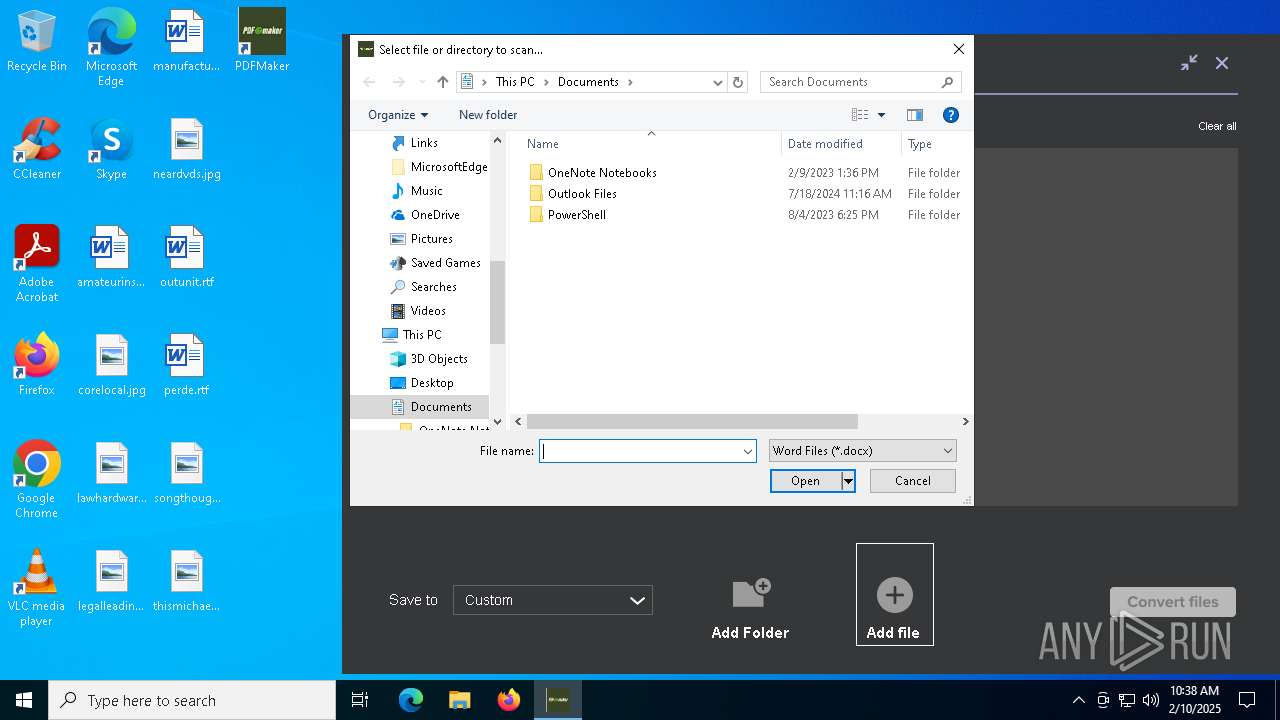
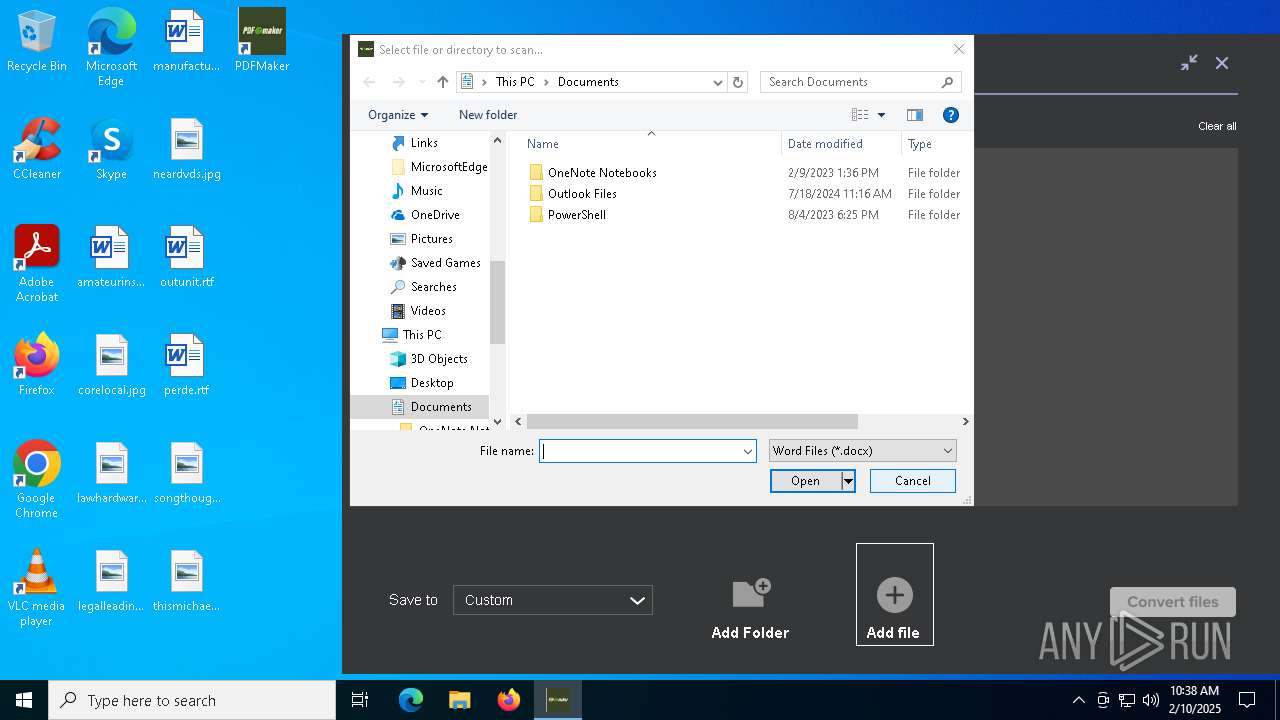
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
- PDFMaker.exe (PID: 4516)
- msiexec.exe (PID: 5628)
- PDFMaker.exe (PID: 5872)
- updater.exe (PID: 6176)
- updater.exe (PID: 7496)
- PDFMaker.exe (PID: 2424)
- PDFMaker-1.0.1.exe (PID: 8120)
The sample compiled with english language support
- chrome.exe (PID: 6592)
- PDFMaker.exe (PID: 4516)
- PDFMaker.exe (PID: 6160)
- msiexec.exe (PID: 5628)
- PDFMaker.exe (PID: 5872)
- updater.exe (PID: 6176)
- PDFMaker-1.0.1.exe (PID: 8120)
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
- updater.exe (PID: 7496)
Executable content was dropped or overwritten
- chrome.exe (PID: 6592)
- msiexec.exe (PID: 5628)
Checks proxy server information
- explorer.exe (PID: 4488)
- rundll32.exe (PID: 524)
- rundll32.exe (PID: 628)
- rundll32.exe (PID: 5340)
- rundll32.exe (PID: 5320)
- powershell.exe (PID: 7512)
- updater.exe (PID: 7496)
- rundll32.exe (PID: 556)
- powershell.exe (PID: 7036)
- powershell.exe (PID: 7160)
- system15627a17808b7546c (PID: 2224)
Reads the computer name
- PDFMaker.exe (PID: 4516)
- msiexec.exe (PID: 5628)
- PDFMaker.exe (PID: 6160)
- msiexec.exe (PID: 3532)
- msiexec.exe (PID: 7424)
- PDFMaker.exe (PID: 5872)
- msiexec.exe (PID: 1216)
- PDFMaker.exe (PID: 2424)
- msiexec.exe (PID: 3416)
- PDFMaker.exe (PID: 7624)
- 7z.exe (PID: 7220)
Checks supported languages
- PDFMaker.exe (PID: 4516)
- PDFMaker.exe (PID: 6160)
- msiexec.exe (PID: 3532)
- msiexec.exe (PID: 5628)
- msiexec.exe (PID: 7424)
- upd.exe (PID: 4684)
- PDFMaker.exe (PID: 5872)
- updater.exe (PID: 6176)
- updater.exe (PID: 7496)
- PDFMaker-1.0.1.exe (PID: 8120)
- msiexec.exe (PID: 1216)
- PDFMaker.exe (PID: 2424)
- msiexec.exe (PID: 3416)
- PDFMaker.exe (PID: 7624)
- upd.exe (PID: 1612)
- 7z.exe (PID: 7220)
- decrypt.exe (PID: 7684)
- java.exe (PID: 7736)
- system15627a17808b7546c (PID: 2224)
Reads Environment values
- PDFMaker.exe (PID: 4516)
- PDFMaker.exe (PID: 6160)
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 3532)
- PDFMaker-1.0.1.exe (PID: 8120)
- msiexec.exe (PID: 3416)
- msiexec.exe (PID: 1216)
Reads the machine GUID from the registry
- PDFMaker.exe (PID: 4516)
- msiexec.exe (PID: 5628)
- PDFMaker.exe (PID: 6160)
- PDFMaker.exe (PID: 5872)
- updater.exe (PID: 7496)
- PDFMaker-1.0.1.exe (PID: 8120)
- PDFMaker.exe (PID: 2424)
- PDFMaker.exe (PID: 7624)
Reads the software policy settings
- PDFMaker.exe (PID: 4516)
- explorer.exe (PID: 4488)
- rundll32.exe (PID: 524)
- PDFMaker.exe (PID: 6160)
- rundll32.exe (PID: 628)
- msiexec.exe (PID: 5628)
- rundll32.exe (PID: 5340)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7876)
- rundll32.exe (PID: 5320)
- powershell.exe (PID: 4996)
- PDFMaker.exe (PID: 5872)
- updater.exe (PID: 7496)
- PDFMaker-1.0.1.exe (PID: 8120)
- rundll32.exe (PID: 556)
- powershell.exe (PID: 6388)
Create files in a temporary directory
- rundll32.exe (PID: 628)
- PDFMaker.exe (PID: 4516)
- rundll32.exe (PID: 524)
- PDFMaker.exe (PID: 6160)
- msiexec.exe (PID: 7424)
- powershell.exe (PID: 7336)
- rundll32.exe (PID: 5340)
- msiexec.exe (PID: 3532)
- powershell.exe (PID: 7876)
- rundll32.exe (PID: 5320)
- powershell.exe (PID: 4996)
- upd.exe (PID: 4684)
- updater.exe (PID: 6176)
- PDFMaker-1.0.1.exe (PID: 8120)
- rundll32.exe (PID: 556)
- msiexec.exe (PID: 3416)
- powershell.exe (PID: 6388)
- rundll32.exe (PID: 3824)
- update.exe (PID: 7272)
- system15627a17808b7546c (PID: 7596)
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
- system15627a17808b7546c (PID: 2224)
Disables trace logs
- rundll32.exe (PID: 628)
- rundll32.exe (PID: 524)
- rundll32.exe (PID: 5340)
- rundll32.exe (PID: 5320)
- PDFMaker.exe (PID: 5872)
- powershell.exe (PID: 7512)
- rundll32.exe (PID: 3824)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 6388)
Creates a software uninstall entry
- msiexec.exe (PID: 5628)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7876)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 7512)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 7036)
- powershell.exe (PID: 7160)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
The executable file from the user directory is run by the Powershell process
- decrypt.exe (PID: 3564)
- decrypt.exe (PID: 7684)
- system15627a17808b7546c (PID: 6600)
- system15627a17808b7546c (PID: 3824)
- decrypt.exe (PID: 2412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
247
Monitored processes
111
Malicious processes
17
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | C:\WINDOWS\system32\cmd.exe /c "wmic datafile where name="C:\\Program Files\\Mozilla Firefox\\firefox.exe" get Version /value" | C:\Windows\SysWOW64\cmd.exe | — | system15627a17808b7546c | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSID2D1.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1299140 777 RequestSender!RequestSender.CustomActions.NextEula | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | powershell.exe "(Get-CimInstance -Namespace root\cimv2 -ClassName Win32_ComputerSystemProduct).UUID" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | system15627a17808b7546c | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | rundll32.exe "C:\WINDOWS\Installer\MSI64CA.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1402046 358 RequestSender!RequestSender.CustomActions.Uninstall | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | C:\WINDOWS\system32\cmd.exe /c "wmic datafile where name="C:\\Program Files (x86)\\Microsoft\\Edge\\Application\\msedge.exe" get Version /value" | C:\Windows\SysWOW64\cmd.exe | — | system15627a17808b7546c | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIC5F9.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1295921 352 RequestSender!RequestSender.CustomActions.Start | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | C:\Windows\syswow64\MsiExec.exe -Embedding 264A16C2AA0E73AE2D53FBBF17C70968 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3492 --field-trial-handle=1836,i,5251696709101645113,14976333477230665594,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\Users\admin\AppData\Roaming\PDFMaker\upd.exe" | C:\Users\admin\AppData\Roaming\PDFMaker\upd.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
187 181
Read events
186 320
Write events
655
Delete events
206
Modification events
| (PID) Process: | (6592) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6592) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6592) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6592) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6592) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000004030A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | Chrome |
Value: 6 | |||
| (PID) Process: | (8044) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000047AEA27FA77BDB01 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
398
Suspicious files
529
Text files
355
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1367c6.TMP | — | |
MD5:— | SHA256:— | |||
| 6592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
100
DNS requests
74
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4520 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 151.101.66.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
4520 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 151.101.66.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDBZxL1hi%2FZHPS2lALw%3D%3D | unknown | — | — | whitelisted |
6344 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1468 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.65.153:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1176 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
webfreepdf.com |
| unknown |
accounts.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6880 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6880 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6880 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6880 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
Process | Message |
|---|---|
updater.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\PDFMaker\PDFMaker\updates\updater.log ) while OLD path is: |
updater.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\PDFMaker\PDFMaker\updates\updater.log ) while OLD path is: |