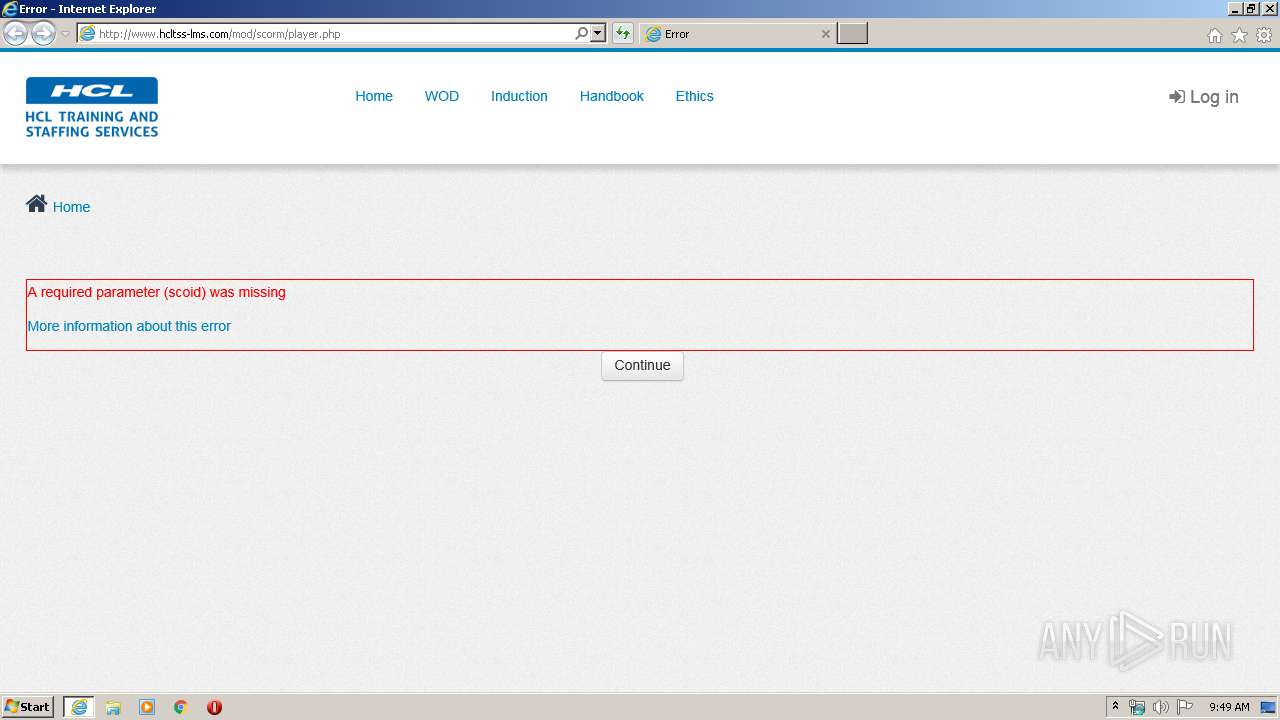
| URL: | http://www.hcltss-lms.com/mod/scorm/player.php |
| Full analysis: | https://app.any.run/tasks/3f295334-373f-4b5c-ab1a-4fc017a38303 |
| Verdict: | No threats detected |
| Analysis date: | March 19, 2020, 09:49:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3D3CB32323D429B421572FE9FFD1B054 |
| SHA1: | BD78B500769ABA39B13679EE71D011831403B91B |
| SHA256: | DDA75FB7E41D2C95F086F312F8D6343C76DD4DCBDC60AE1A4B178E5CED578C75 |
| SSDEEP: | 3:N1KJS4QyGK3IBB8gbV:Cc4UK4BBTbV |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 3792)
Reads Internet Cache Settings
- iexplore.exe (PID: 2892)
- iexplore.exe (PID: 3792)
Application launched itself
- iexplore.exe (PID: 2892)
Changes internet zones settings
- iexplore.exe (PID: 2892)
Reads settings of System Certificates
- iexplore.exe (PID: 2892)
Changes settings of System certificates
- iexplore.exe (PID: 2892)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2892 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.hcltss-lms.com/mod/scorm/player.php | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2892 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 859
Read events
911
Write events
3 981
Delete events
1 967
Modification events
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3455643052 | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30801363 | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
31
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\styles[1].php | text | |
MD5:1FAD5A10F03FB2AE7F8986AFADD7A925 | SHA256:4E02EB7B6C5B0631014629E793092CC8A3748BDAF5DF939B5943C10CC636C4A2 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\combo[1] | text | |
MD5:5104022419D198B2FCB2237735786E34 | SHA256:9C5FC167EC66FE7ADFC7919A7B8FF630E9C7250980D5C0C489818B273BB8AE61 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\requirejs[1].php | text | |
MD5:4046892CFBA87B64EB2E78B59A7100BD | SHA256:51260055CD284F0BFF9BC87C1A5857938CE289609592D4905D3ECC45597CFB45 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\javascript[1].php | html | |
MD5:99D0FBEE5B8B56B46155F8887EF2EB59 | SHA256:D43449E21297219118EA75F7C4882C6A052BB8512672768A6E7F756F453AD169 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\PNG%20Logo[1].png | image | |
MD5:FC542825D83B24325066F57C4AC3F5D8 | SHA256:198A908D0D0A4EB0D2CD7D6307AF2923423555C99E475B9CEA45988612E45406 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\javascript[1].php | text | |
MD5:1AC2C29ECC0F8716020855452601D3AC | SHA256:152E615FB1CFA6BF4B22769502CB1AF2EF966A14B46774D9FDA6F2EF1695F6CF | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\javascript[1].php | text | |
MD5:46CF363ABB901D163AC9A1A2F8BCD149 | SHA256:A837F7B0A01A3D3CDFEBB04DE2A0AD7C52113B3DA0F718EFC45899CCE9F318C0 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\fontawesome-webfont[1].eot | eot | |
MD5:F7C2B4B747B1A225EB8DEE034134A1B0 | SHA256:CBB644D0EE730EA57DD5FBAE35EF5BA4A41D57A254A6B1215DE5C9FF8A321C2D | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery-1.12.1.min[1].js | text | |
MD5:1D244CB043BE8157F0050CE9E45C9EF2 | SHA256:2359D383BF2D4AB65EBF7923BDF74CE40E4093F6E58251B395A64034B3C39772 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
15
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/image.php/hclt/theme/1583309937/login-bg1 | IN | image | 316 Kb | unknown |
3792 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/image.php/hclt/core/1583309937/help | IN | image | 691 b | unknown |
3792 | iexplore.exe | POST | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/lib/ajax/service.php?sesskey=07x5mXPROM | IN | text | 253 b | unknown |
3792 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/styles.php/hclt/1583309937/all | IN | text | 140 Kb | unknown |
2892 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/image.php/hclt/theme/1583309937/favicon | IN | image | 339 b | unknown |
3792 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/font.php/hclt/theme/1583309937/bebasneue_regular-webfont.eot | IN | eot | 17.4 Kb | unknown |
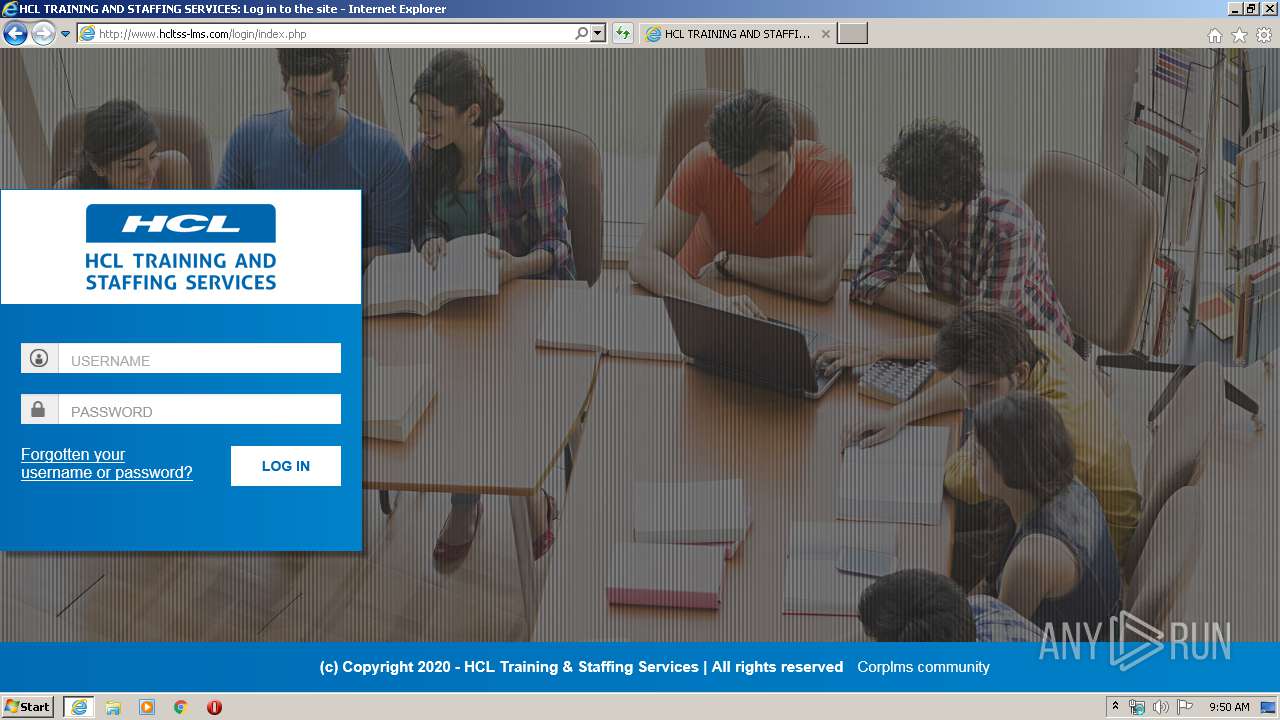
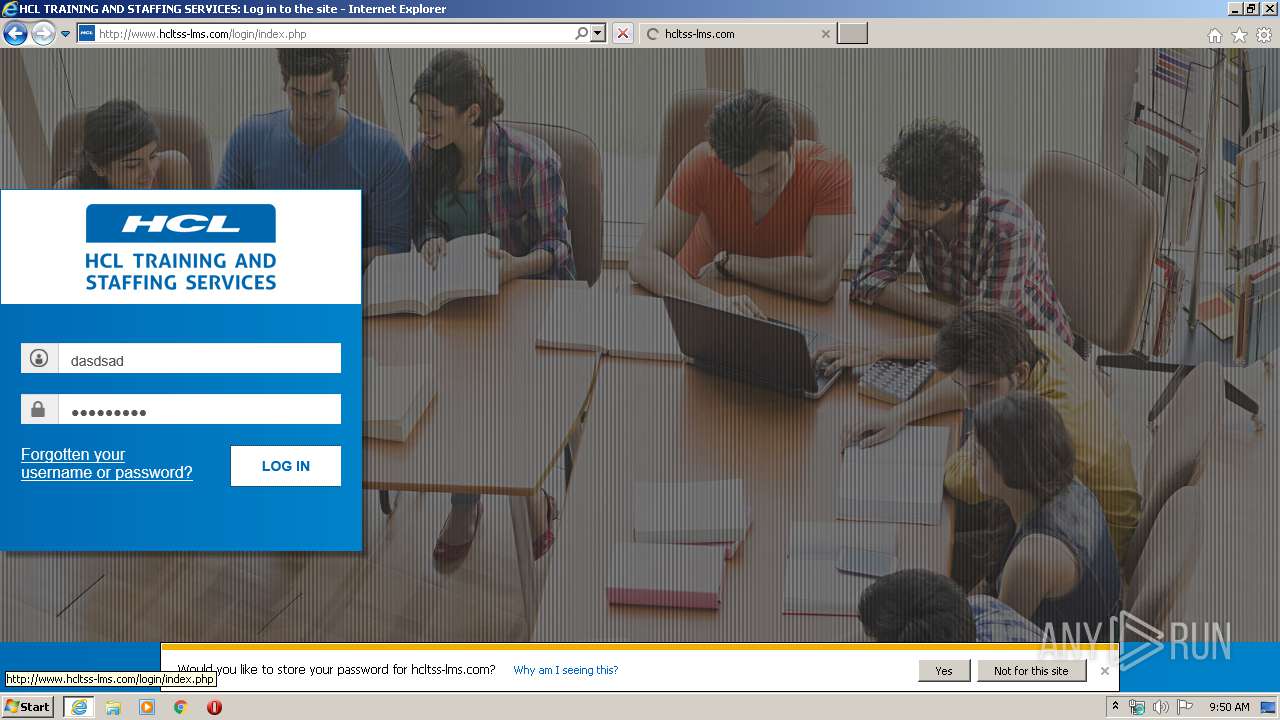
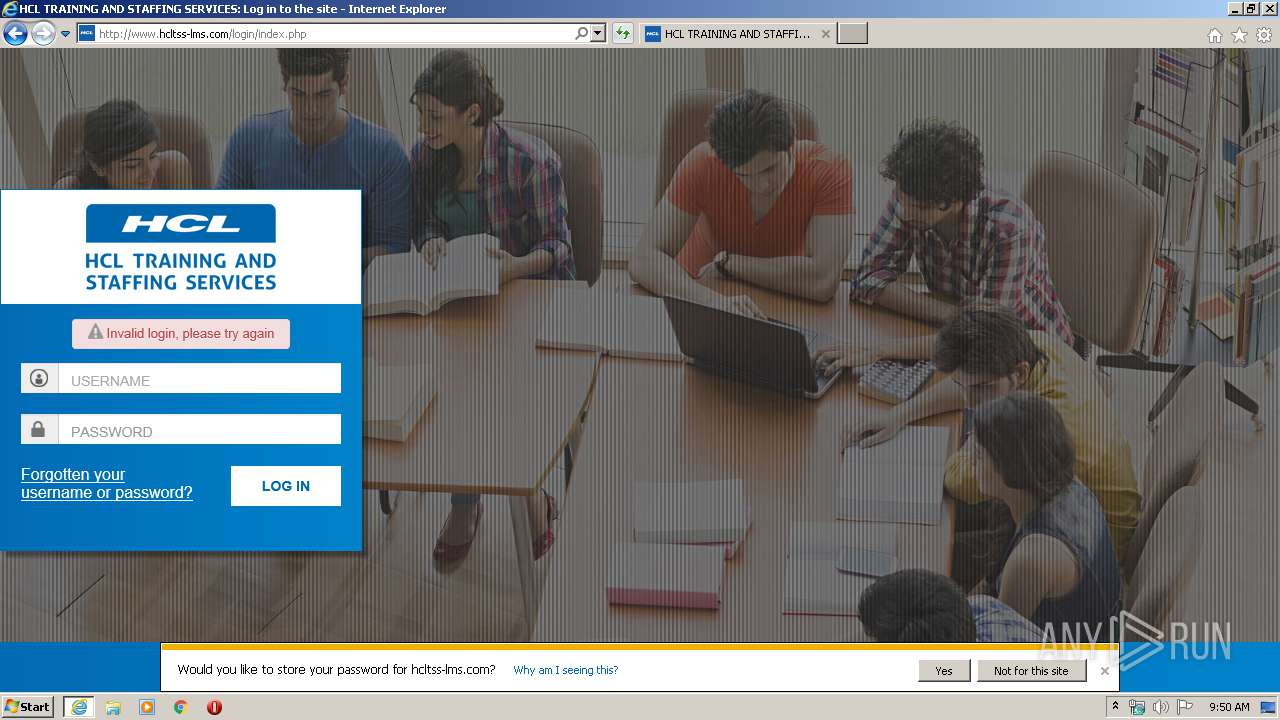
3792 | iexplore.exe | POST | 303 | 13.71.121.15:80 | http://www.hcltss-lms.com/login/index.php | IN | html | 439 b | unknown |
3792 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/jquery.php/core/ui-1.11.4/jquery-ui.min.js | IN | text | 62.3 Kb | unknown |
3792 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/jquery.php/core/ui-1.11.4/theme/smoothness/jquery-ui.min.css | IN | text | 7.20 Kb | unknown |
3792 | iexplore.exe | GET | 200 | 13.71.121.15:80 | http://www.hcltss-lms.com/theme/javascript.php/hclt/1583309937/footer | IN | text | 38.3 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 13.71.121.15:80 | www.hcltss-lms.com | Microsoft Corporation | IN | unknown |
2892 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3792 | iexplore.exe | 209.197.3.15:80 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 13.71.121.15:80 | www.hcltss-lms.com | Microsoft Corporation | IN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hcltss-lms.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |