| File name: | dangerousrat.bat |
| Full analysis: | https://app.any.run/tasks/a0d29a58-00be-49af-810f-b578cb6c462e |
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2024, 12:01:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (1408), with CRLF line terminators |
| MD5: | D627A23F3F4CF579F35752BA42BDCCB2 |
| SHA1: | 429640980A93AB3D5EEE2ABD5C846803065C742E |
| SHA256: | DDA2C5D7B91D7BB0BF7EA4811C3914D90B3AA4DB667E4ABFE8A09BF1612139D1 |
| SSDEEP: | 48:ixPtKfEpDOzW8Ii0vXIrZ6OhBKIDN9Laxv5pJ1pjKwzDH:48AigMZxOwhax3J1vDH |
MALICIOUS
No malicious indicators.SUSPICIOUS
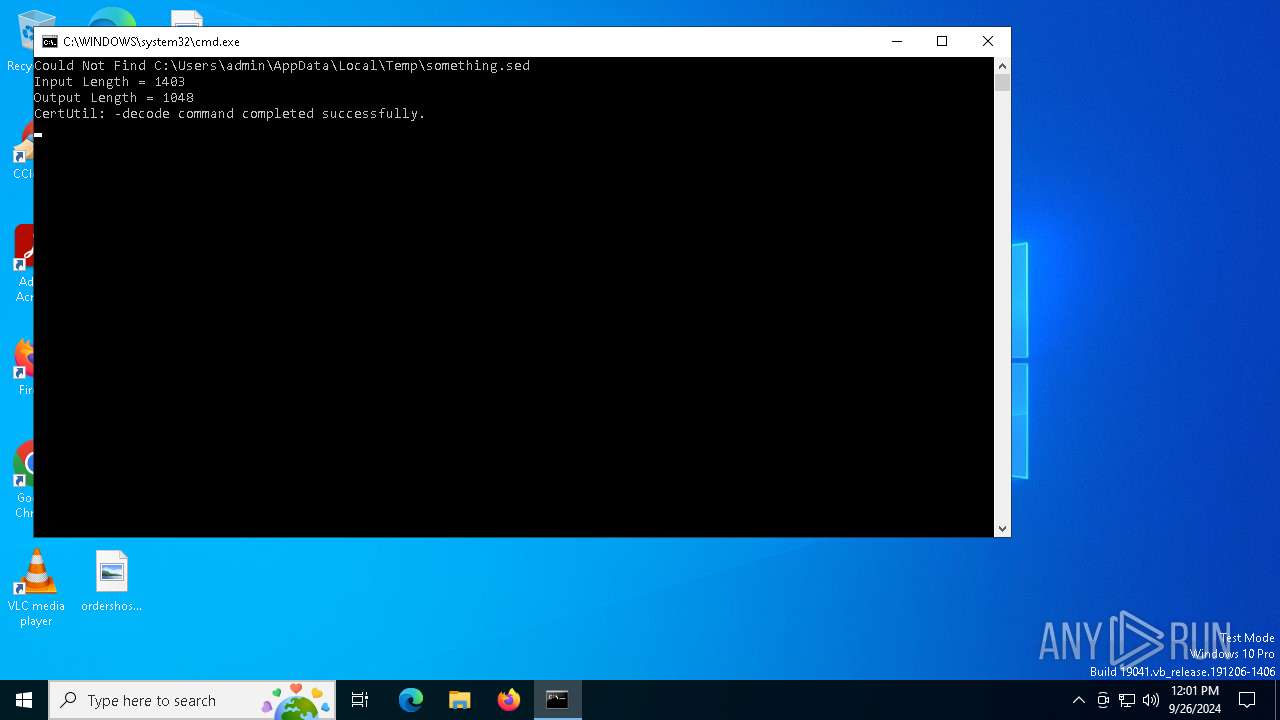
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 5996)
Process drops legitimate windows executable
- iexpress.exe (PID: 2464)
- Google Chrome.exe (PID: 6640)
- rat[1].exe (PID: 5364)
Creates file in the systems drive root
- iexpress.exe (PID: 2464)
Executable content was dropped or overwritten
- iexpress.exe (PID: 2464)
- Google Chrome.exe (PID: 6640)
- IMEWDBLD.EXE (PID: 6356)
- rat[1].exe (PID: 5364)
Starts a Microsoft application from unusual location
- Google Chrome.exe (PID: 6640)
- charmap.exe (PID: 2648)
The executable file from the user directory is run by the CMD process
- Google Chrome.exe (PID: 6640)
- rat[1].exe (PID: 5364)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7076)
- Google Chrome.exe (PID: 6640)
Application launched itself
- cmd.exe (PID: 7076)
- rat[1].exe (PID: 5364)
The process drops C-runtime libraries
- rat[1].exe (PID: 5364)
Process drops python dynamic module
- rat[1].exe (PID: 5364)
INFO
Create files in a temporary directory
- certutil.exe (PID: 6988)
- makecab.exe (PID: 2204)
- iexpress.exe (PID: 2464)
- Google Chrome.exe (PID: 6640)
Checks supported languages
- makecab.exe (PID: 2204)
- Google Chrome.exe (PID: 6640)
Reads security settings of Internet Explorer
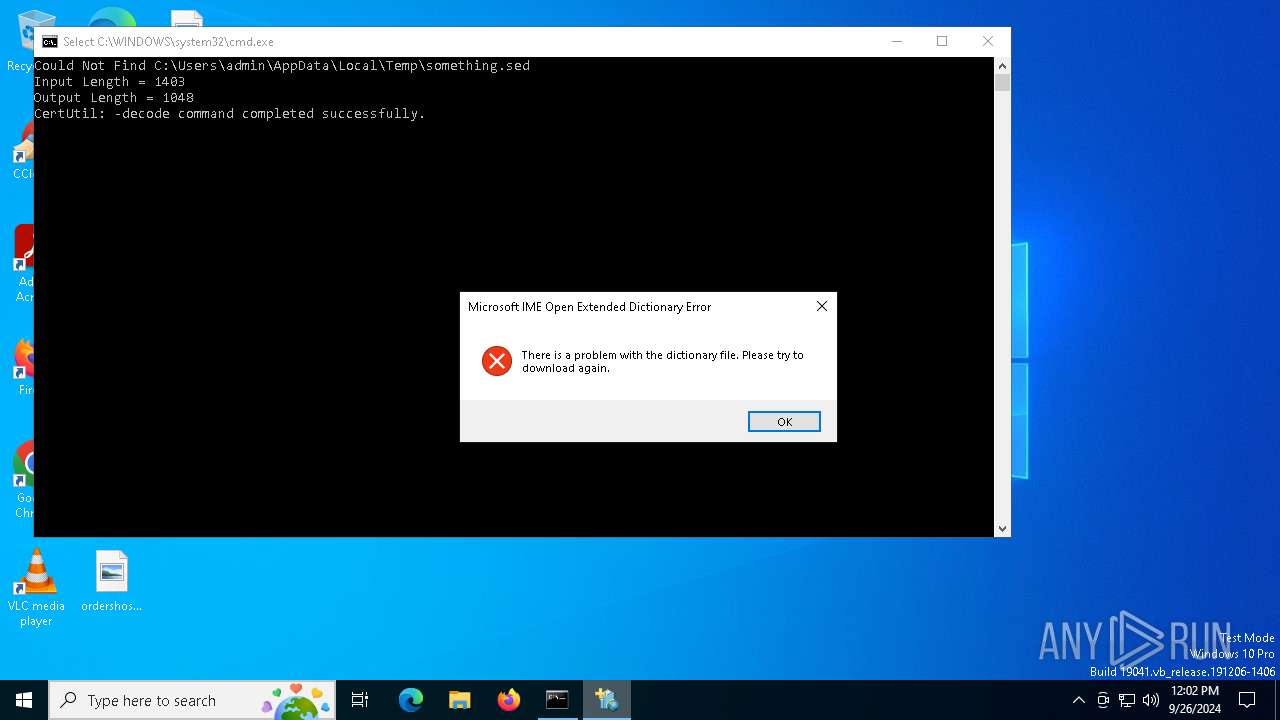
- IMEWDBLD.EXE (PID: 6356)
Reads the software policy settings
- IMEWDBLD.EXE (PID: 6356)
Checks proxy server information
- IMEWDBLD.EXE (PID: 6356)
Creates files or folders in the user directory
- IMEWDBLD.EXE (PID: 6356)
Attempting to use instant messaging service
- rat[1].exe (PID: 4364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
143
Monitored processes
15
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | makecab.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2204 | C:\WINDOWS\system32\makecab.exe /f "~Google Chrome.DDF" | C:\Windows\System32\makecab.exe | — | iexpress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | C:\WINDOWS\system32\cmd.exe /c where /r C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache rat* | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | iexpress /N /Q /M something.sed | C:\Windows\System32\iexpress.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Wizard Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2608 | where /r C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache rat* | C:\Windows\System32\where.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\charmap.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\charmap.exe | — | Google Chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Character Map Exit code: 0 Version: 5.2.3668.0 Modules
| |||||||||||||||
| 3908 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4364 | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\rat[1].exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\rat[1].exe | rat[1].exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5364 | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\rat[1].exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\rat[1].exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
4 146
Read events
4 143
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6356) IMEWDBLD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6356) IMEWDBLD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6356) IMEWDBLD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
79
Suspicious files
250
Text files
32
Unknown types
358
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | makecab.exe | C:\Users\admin\AppData\Local\Temp\~Google Chrome.CAB | compressed | |
MD5:234696B64E2C7FECCE262DA12C61F3A9 | SHA256:B1B156EE65670A6699B34C89A3B4E253B8EDFB08F27EDE552D97B1B74C8A271E | |||
| 2204 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2204_9 | binary | |
MD5:A0E1423082C66DDE9C77036B042071F1 | SHA256:7AEC934E6E31FE456F081AAA41EFD6093806AE5319A58CFEC439A63B65A257EF | |||
| 2204 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2204_7 | binary | |
MD5:3E64955147F863411FE004B372D02865 | SHA256:BB395D23CF649E1053BF26488D05FC356A0E1DE708DA54A25238899B993B779F | |||
| 2204 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2204_5 | binary | |
MD5:BE29C76C617035A7BD035540FE8E0BA7 | SHA256:BBDE42221164E43EEE8E4C5C964B2DEC8A37B6866A077BB9BB2E6EED0398133E | |||
| 2464 | iexpress.exe | C:\Users\admin\AppData\Local\Temp\~Google Chrome.DDF | binary | |
MD5:CB6066C66B6EB1447B44CA903A882C7F | SHA256:3C8872032A0889E68C605409B506FAD6BDE756C8269052B787B8A04316702F71 | |||
| 2204 | makecab.exe | C:\Users\admin\AppData\Local\Temp\inf_2204_3 | text | |
MD5:32ABDF61816CC3D7AA9BFDA23511DD97 | SHA256:B607389F9BF040CD3C405DFA69226D3BC9D60B36E3D3283E2C2BE6AA2DDE359A | |||
| 2204 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2204_6 | binary | |
MD5:B69FB6EC480083D4D3FECDEB619EA251 | SHA256:80DBDCDF73B254990DE3D10AA2205AB39590F6E39C13F42FD67C5A3E15D64A76 | |||
| 6988 | certutil.exe | C:\Users\admin\AppData\Local\Temp\something.sed | text | |
MD5:533454065E607003114010212717510F | SHA256:9E0EED92B6764EE27D8725F4DD5AAC89615568E22EB80C996D03D073C04731B7 | |||
| 2204 | makecab.exe | C:\Users\admin\AppData\Local\Temp\~Google Chrome_LAYOUT.INF | binary | |
MD5:4C6305D199ED53A66067D549E6293072 | SHA256:80F9783D1F42130D06581BC7BAC3BF043877BED8247F176B329D4C394B05BC7E | |||
| 6356 | IMEWDBLD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | der | |
MD5:B337DBF2F187B5760F247A06589E6494 | SHA256:DBD11560FA60418C37222289A0FEE1852D7C3589B7E40DD7155785D3B4C8875B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
36
DNS requests
15
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6424 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6424 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6008 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6356 | IMEWDBLD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6008 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3004 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6356 | IMEWDBLD.EXE | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
6356 | IMEWDBLD.EXE | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2932 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2932 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
discord.com |
| whitelisted |
gateway.discord.gg |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
4364 | rat[1].exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |