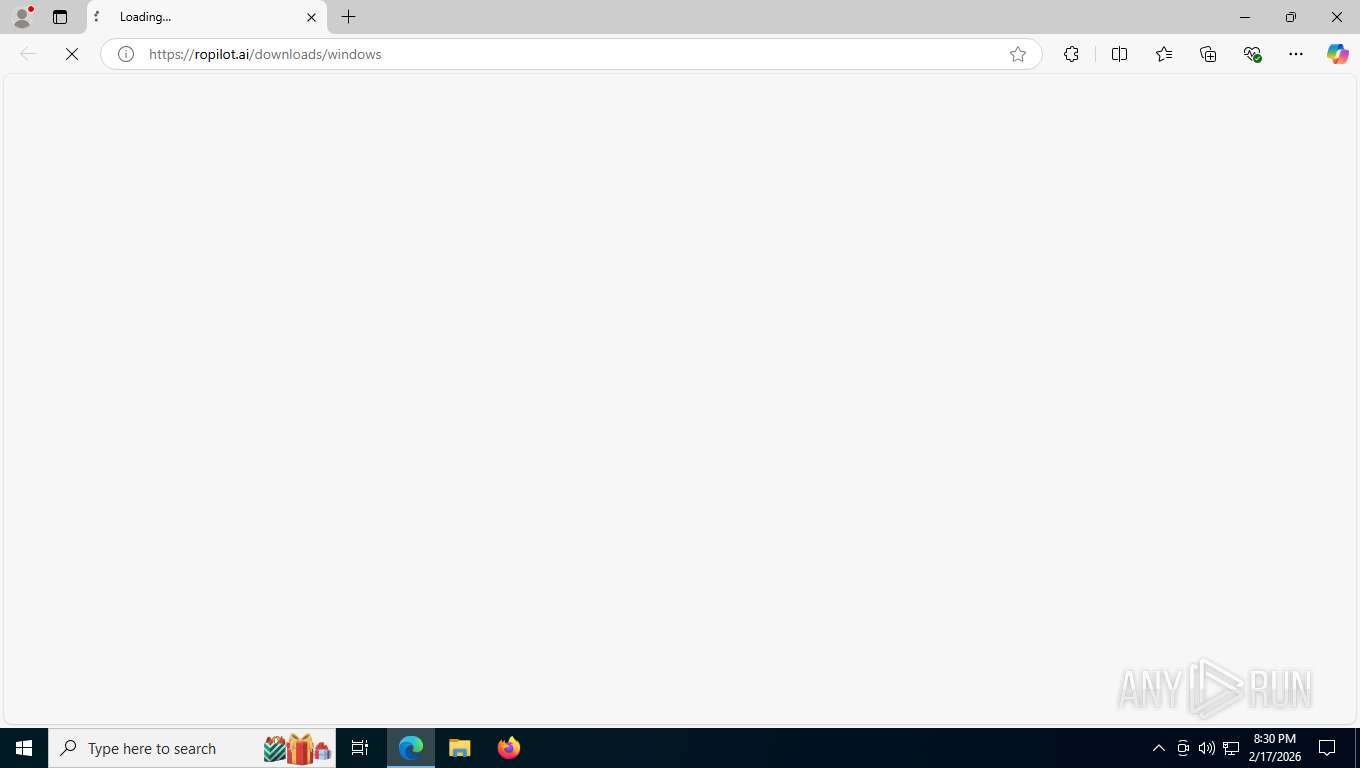
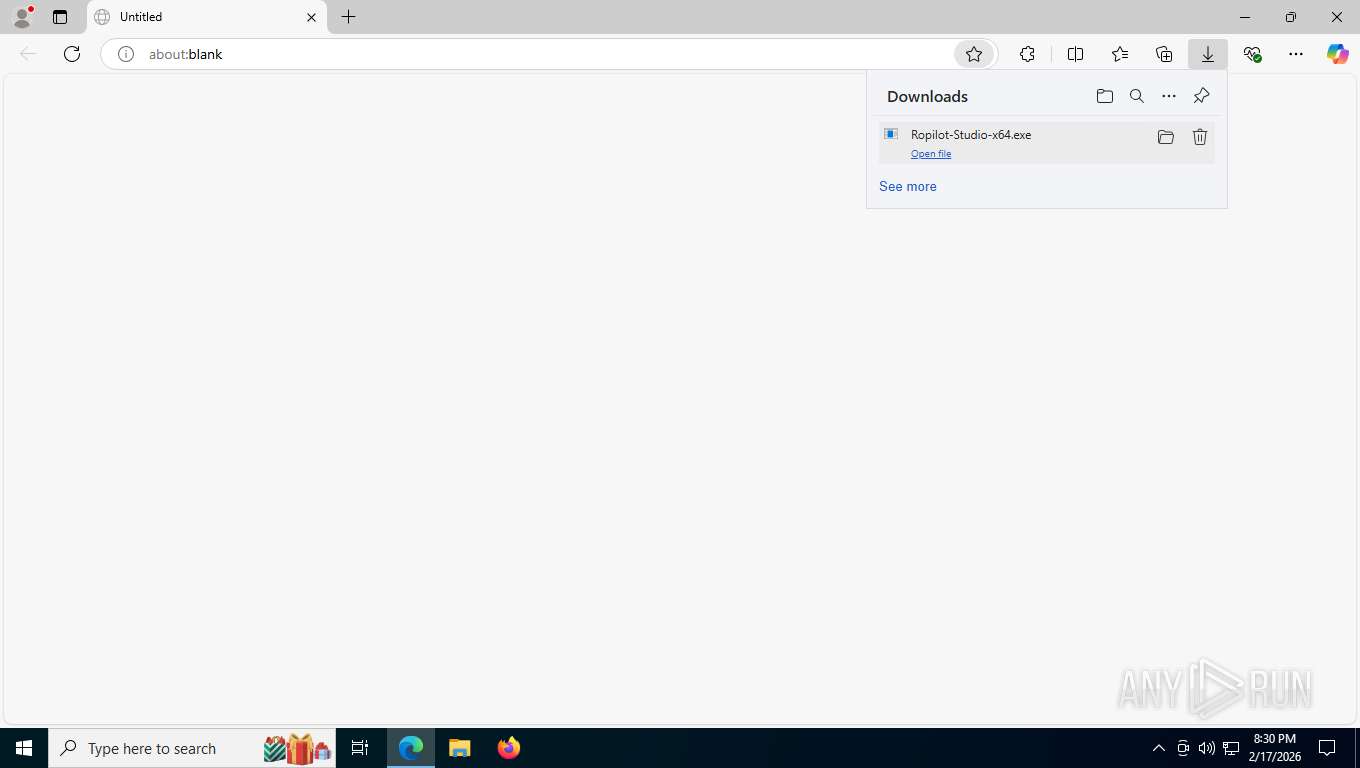
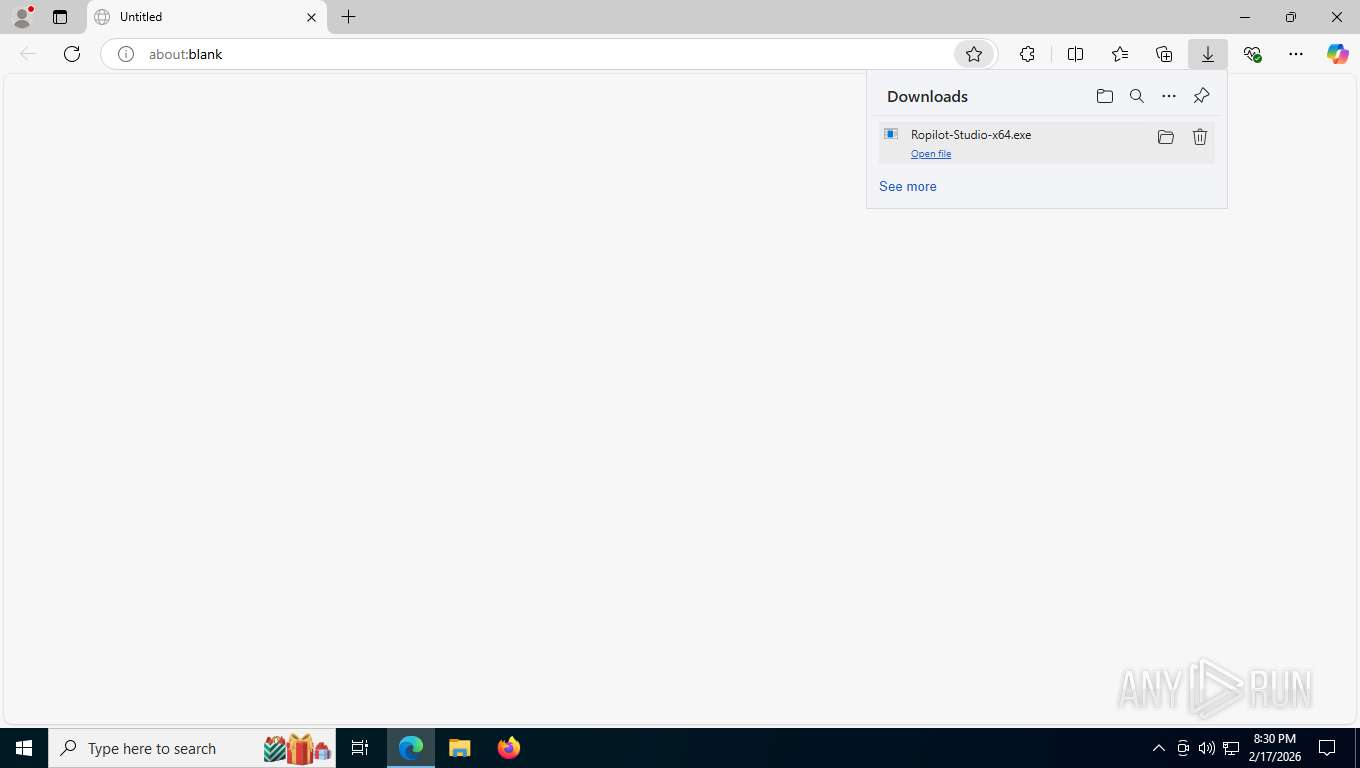
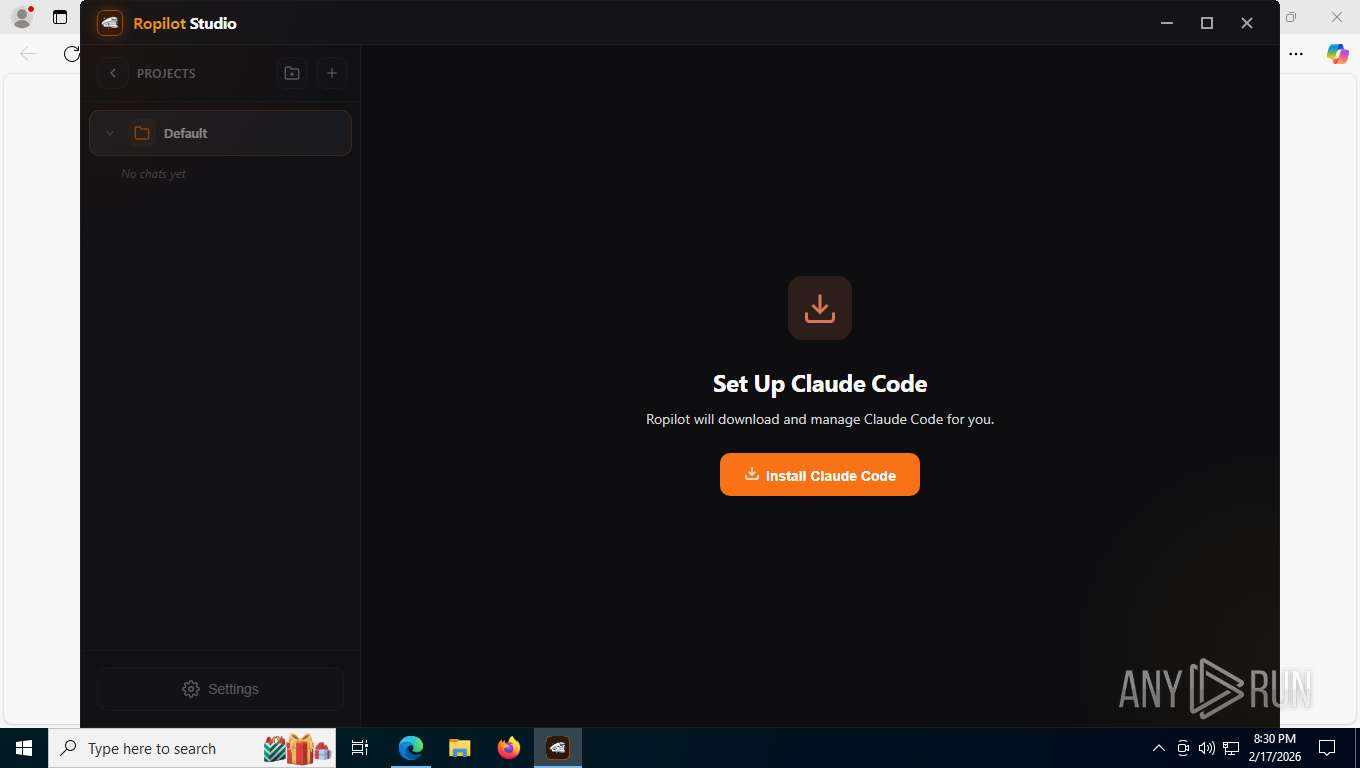
| URL: | https://ropilot.ai/downloads/windows |
| Full analysis: | https://app.any.run/tasks/244eb79c-e015-45a3-b27c-781ace9b6566 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2026, 01:29:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B65C99BE759CE2327487DD51ABDA134D |
| SHA1: | AC295C1863FEDE5E25EF1656DE91DF08FDFE553B |
| SHA256: | DDA2B58F56B73260BBFC165433EF9079E5782A41D41358ECD38313EF6DAE8203 |
| SSDEEP: | 3:N8MIKnSLJ4K/1Kl:2bKaIl |
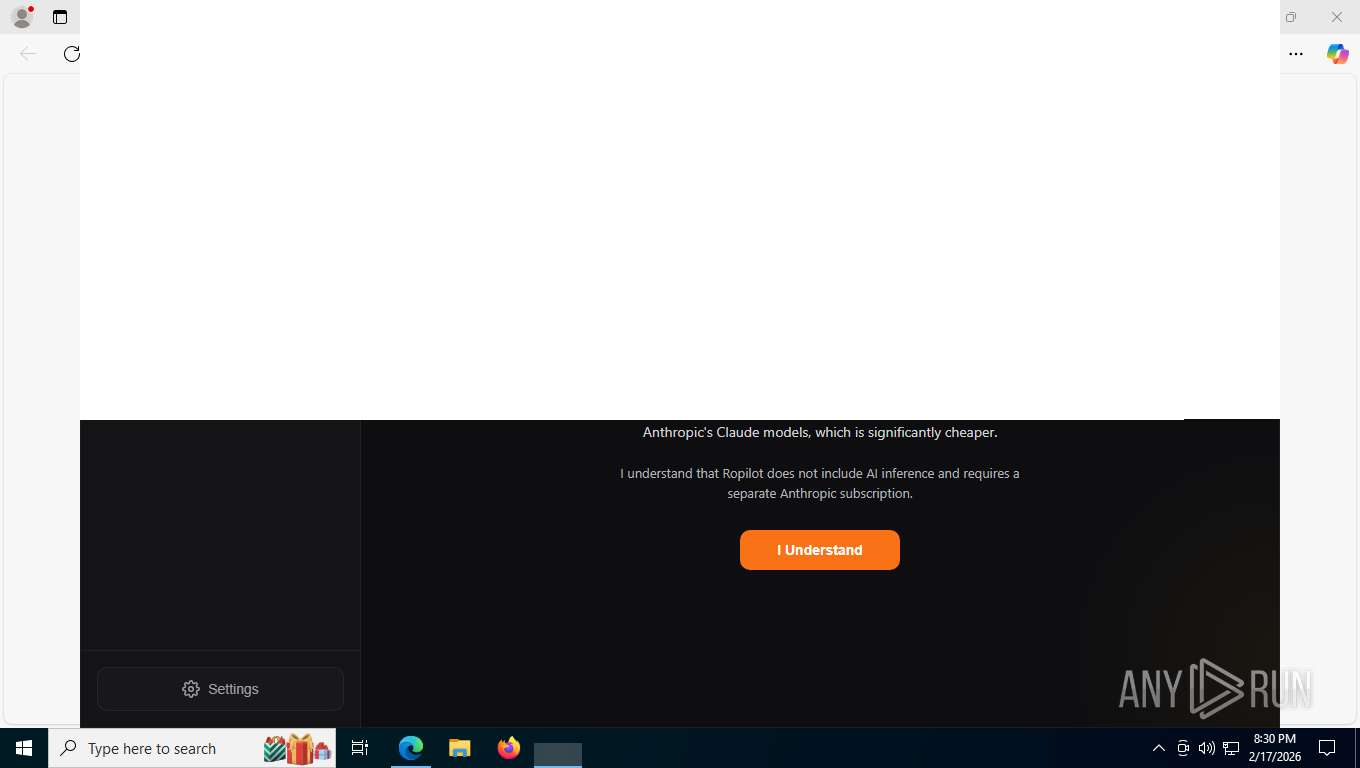
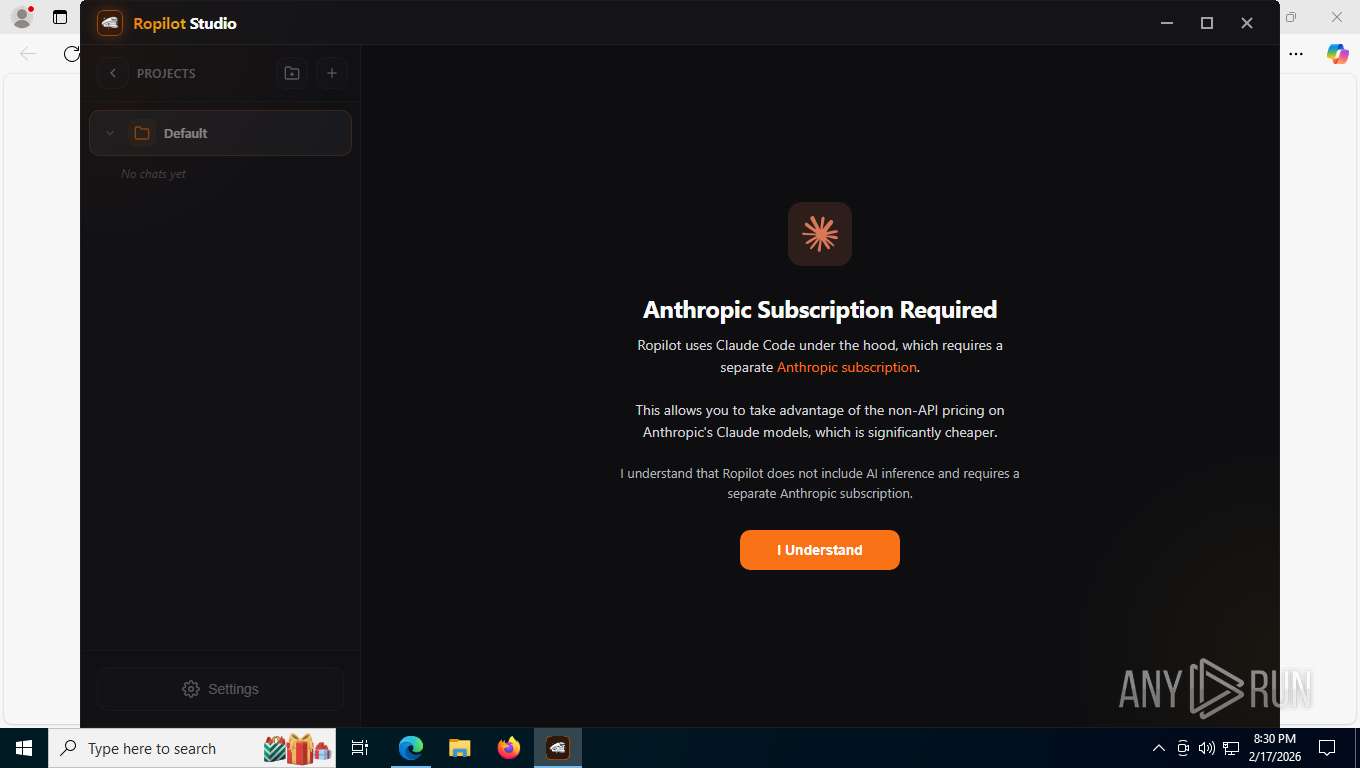
MALICIOUS
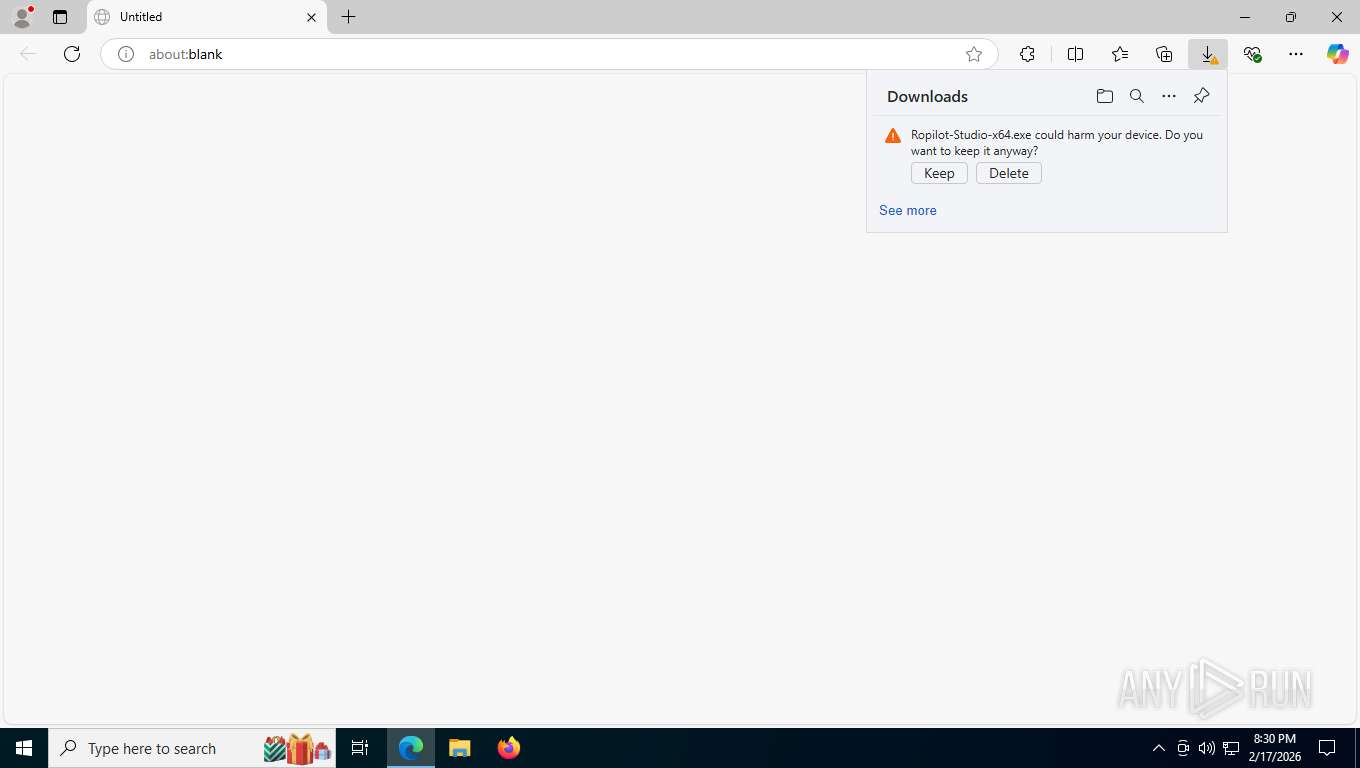
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6424)
SUSPICIOUS
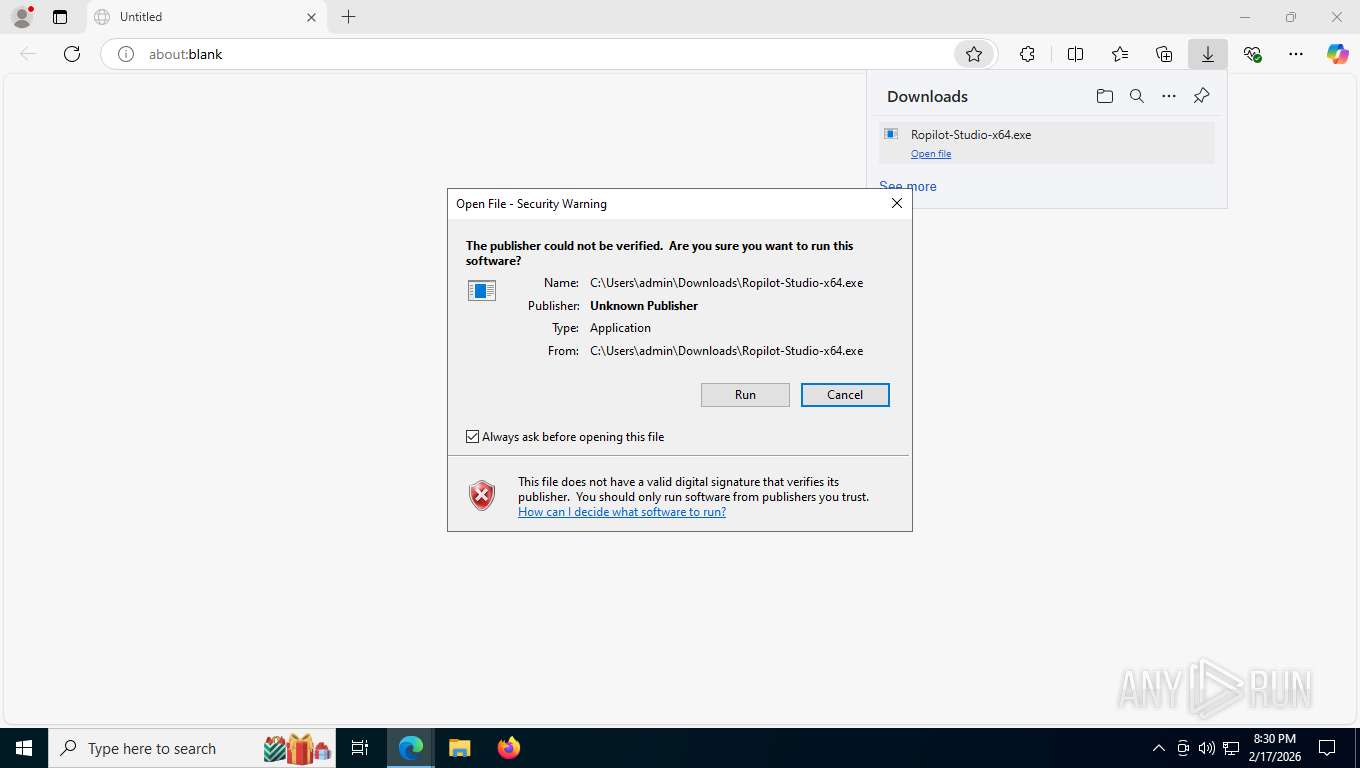
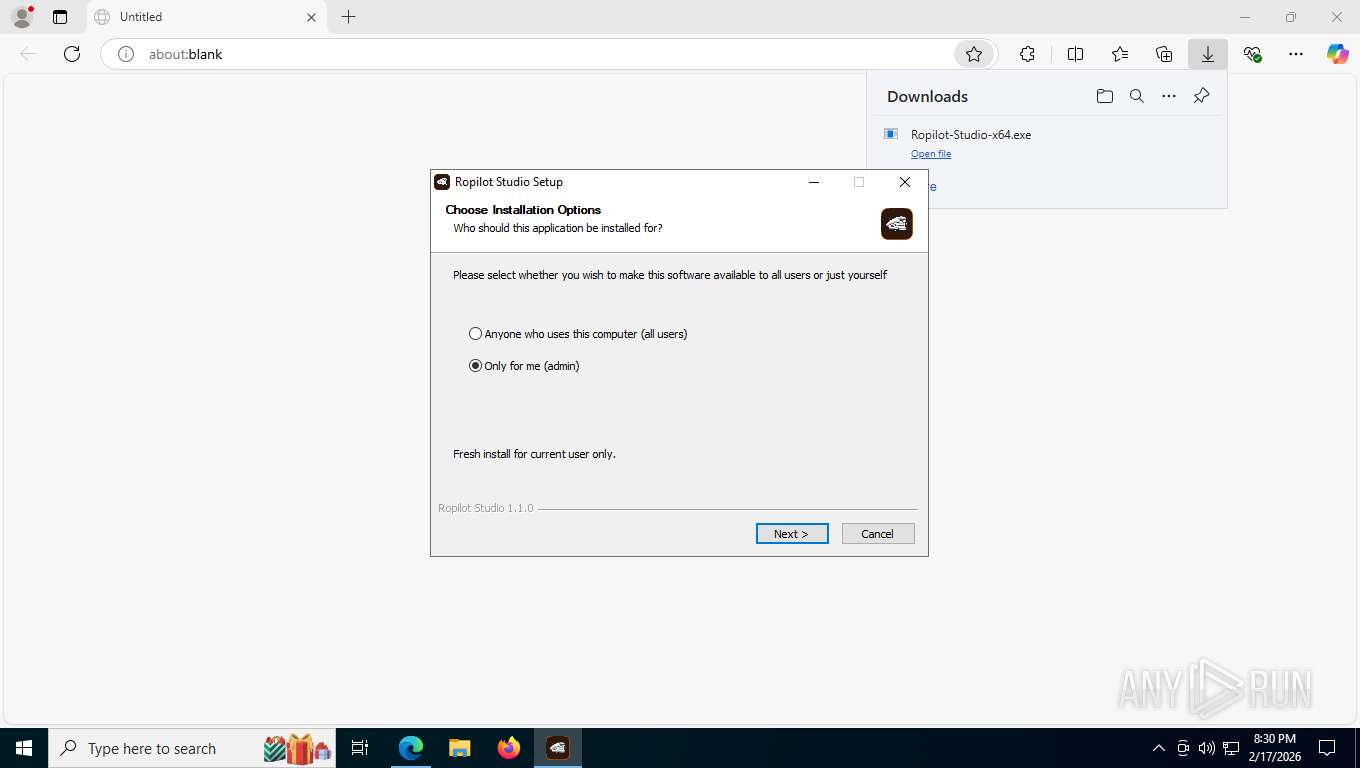
The process creates files with name similar to system file names
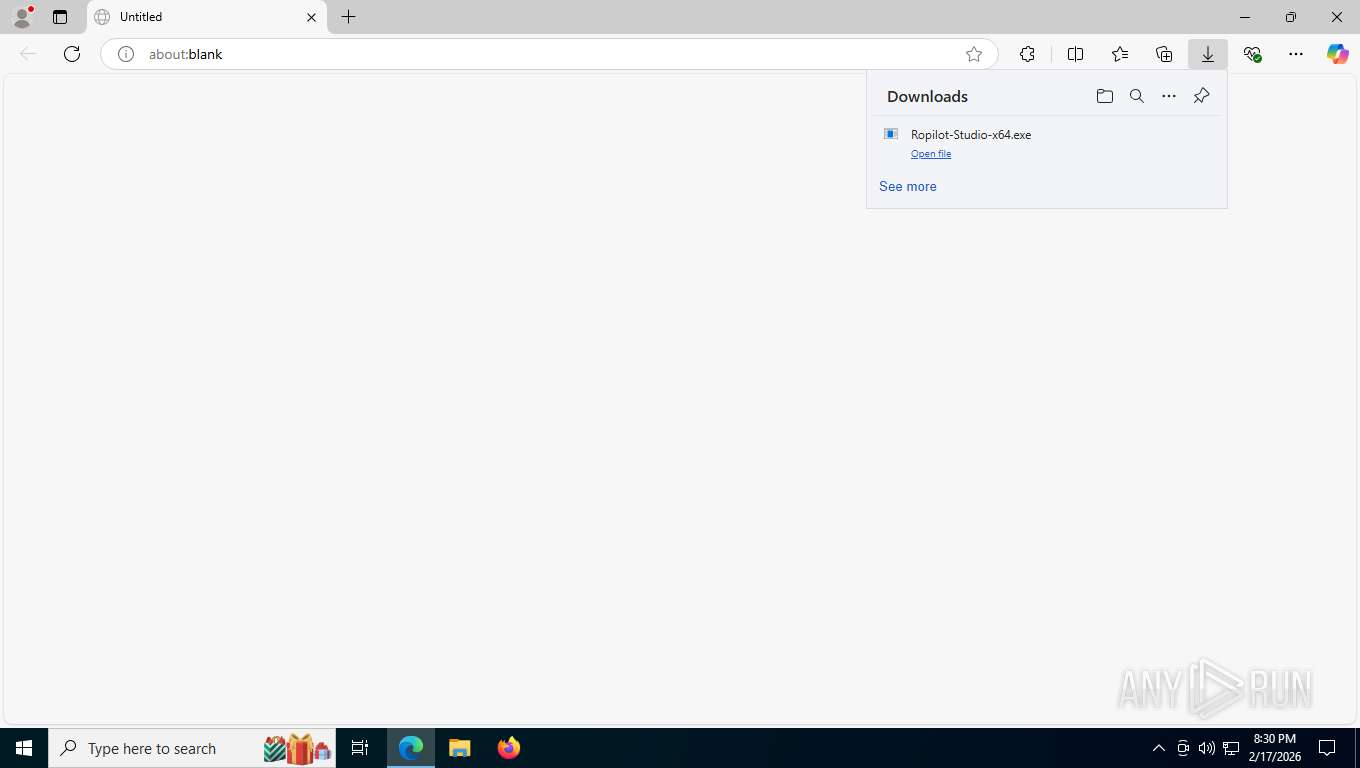
- Ropilot-Studio-x64.exe (PID: 8580)
Malware-specific behavior (creating "System.dll" in Temp)
- Ropilot-Studio-x64.exe (PID: 8580)
Executable content was dropped or overwritten
- Ropilot-Studio-x64.exe (PID: 8580)
- Ropilot Studio.exe (PID: 2232)
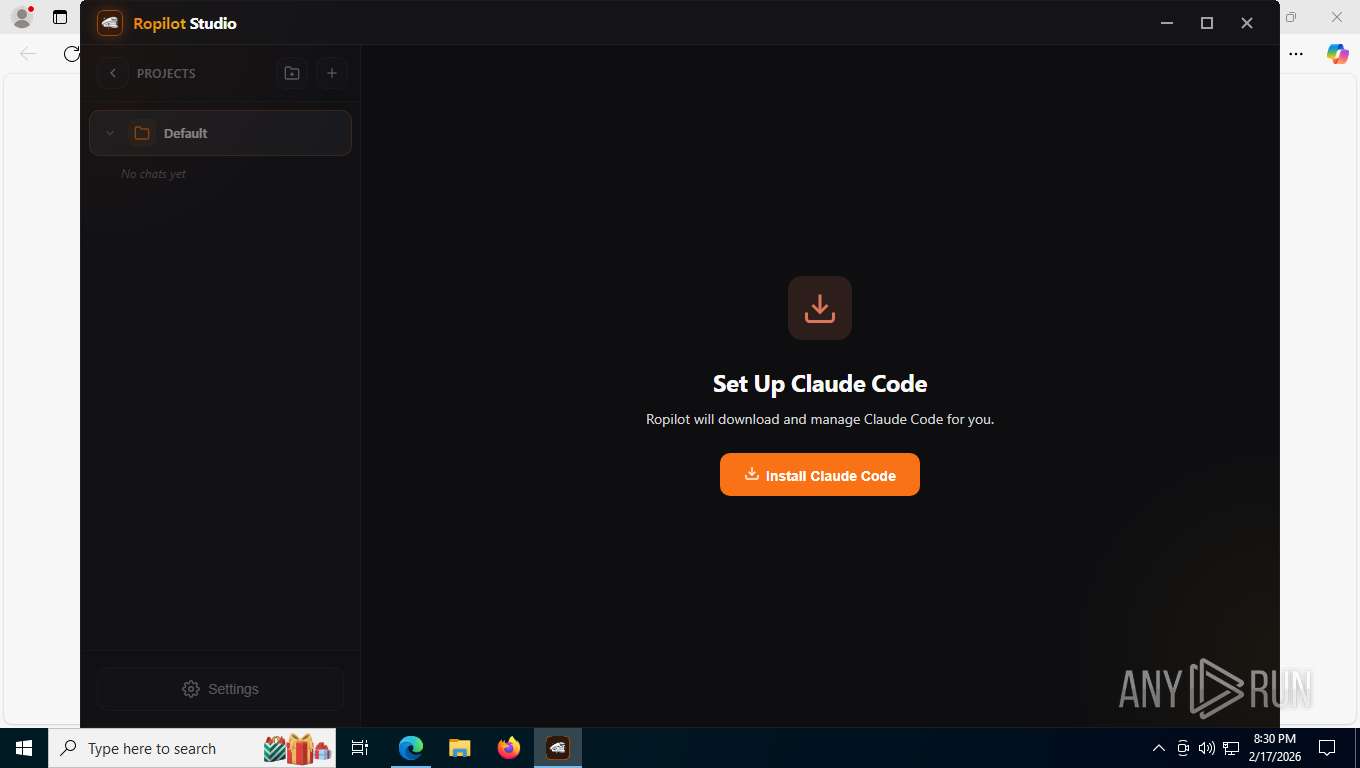
Drops 7-zip archiver for unpacking
- Ropilot-Studio-x64.exe (PID: 8580)
Process drops legitimate windows executable
- Ropilot-Studio-x64.exe (PID: 8580)
Starts CMD.EXE for commands execution
- Ropilot Studio.exe (PID: 2232)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8404)
Application launched itself
- Ropilot Studio.exe (PID: 2232)
The executable file from the user directory is run by the CMD process
- ropilot-infra.exe (PID: 8556)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 8196)
Application launched itself
- msedge.exe (PID: 8196)
Reads Environment values
- identity_helper.exe (PID: 4200)
- Ropilot Studio.exe (PID: 2232)
Checks supported languages
- identity_helper.exe (PID: 4200)
- Ropilot-Studio-x64.exe (PID: 8580)
- Ropilot Studio.exe (PID: 2232)
- Ropilot Studio.exe (PID: 5044)
- Ropilot Studio.exe (PID: 7736)
- ropilot-infra.exe (PID: 8556)
- Ropilot Studio.exe (PID: 2288)
The sample compiled with english language support
- msedge.exe (PID: 8196)
- Ropilot-Studio-x64.exe (PID: 8580)
Reads the computer name
- identity_helper.exe (PID: 4200)
- Ropilot-Studio-x64.exe (PID: 8580)
- Ropilot Studio.exe (PID: 2232)
- Ropilot Studio.exe (PID: 5044)
- Ropilot Studio.exe (PID: 7736)
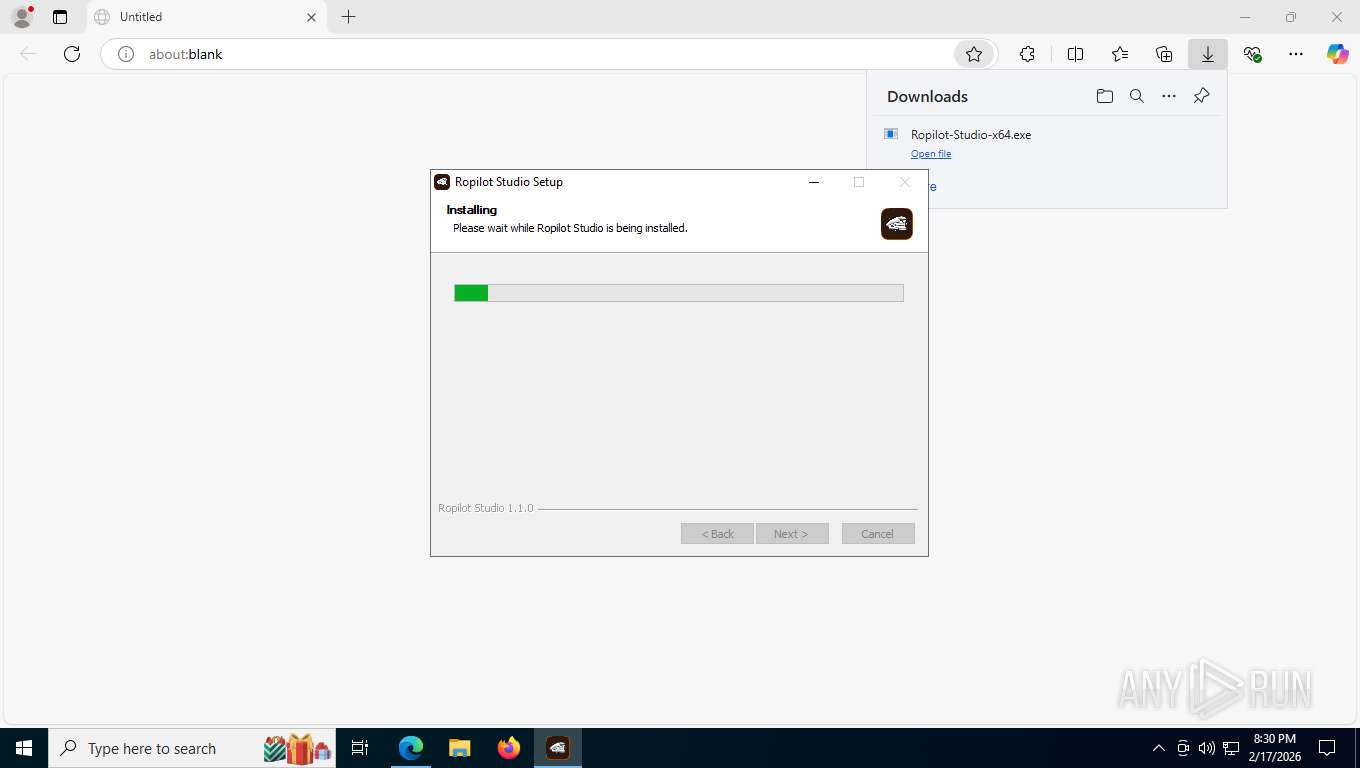
Create files in a temporary directory
- Ropilot-Studio-x64.exe (PID: 8580)
- Ropilot Studio.exe (PID: 2232)
Reads security settings of Internet Explorer
- Ropilot-Studio-x64.exe (PID: 8580)
Creates files or folders in the user directory
- Ropilot-Studio-x64.exe (PID: 8580)
- Ropilot Studio.exe (PID: 2232)
- ropilot-infra.exe (PID: 8556)
- Ropilot Studio.exe (PID: 7736)
Creates a software uninstall entry
- Ropilot-Studio-x64.exe (PID: 8580)
There is functionality for taking screenshot (YARA)
- Ropilot-Studio-x64.exe (PID: 8580)
Reads product name
- Ropilot Studio.exe (PID: 2232)
Reads the machine GUID from the registry
- Ropilot Studio.exe (PID: 2232)
Drops script file
- Ropilot Studio.exe (PID: 2232)
- ropilot-infra.exe (PID: 8556)
Checks proxy server information
- Ropilot Studio.exe (PID: 2232)
Manual execution by a user
- Ropilot Studio.exe (PID: 2232)
Drops encrypted JS script (Microsoft Script Encoder)
- ropilot-infra.exe (PID: 8556)
Process checks computer location settings
- Ropilot Studio.exe (PID: 2232)
- Ropilot Studio.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
187
Monitored processes
39
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5688,i,13507282532721019289,3682779891870933328,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5680 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1784 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2760,i,13507282532721019289,3682779891870933328,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2528 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Ropilot Studio.exe" | C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Ropilot Studio.exe | explorer.exe | ||||||||||||
User: admin Company: Ropilot Integrity Level: MEDIUM Description: Ropilot Studio Version: 1.1.0 Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Ropilot Studio.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\ropilot" --app-path="C:\Users\admin\AppData\Local\Programs\Ropilot Studio\resources\app.asar" --enable-sandbox --first-renderer-process --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=3052 --field-trial-handle=1368,i,2261968962708415798,18103830100299441303,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Ropilot Studio.exe | — | Ropilot Studio.exe | |||||||||||
User: admin Company: Ropilot Integrity Level: LOW Description: Ropilot Studio Version: 1.1.0 Modules
| |||||||||||||||
| 2424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7052,i,13507282532721019289,3682779891870933328,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=3840,i,13507282532721019289,3682779891870933328,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4304 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6688,i,13507282532721019289,3682779891870933328,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7196 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4200 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6476,i,13507282532721019289,3682779891870933328,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6532 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffd6f4cf208,0x7ffd6f4cf214,0x7ffd6f4cf220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
3 327
Read events
3 296
Write events
13
Delete events
18
Modification events
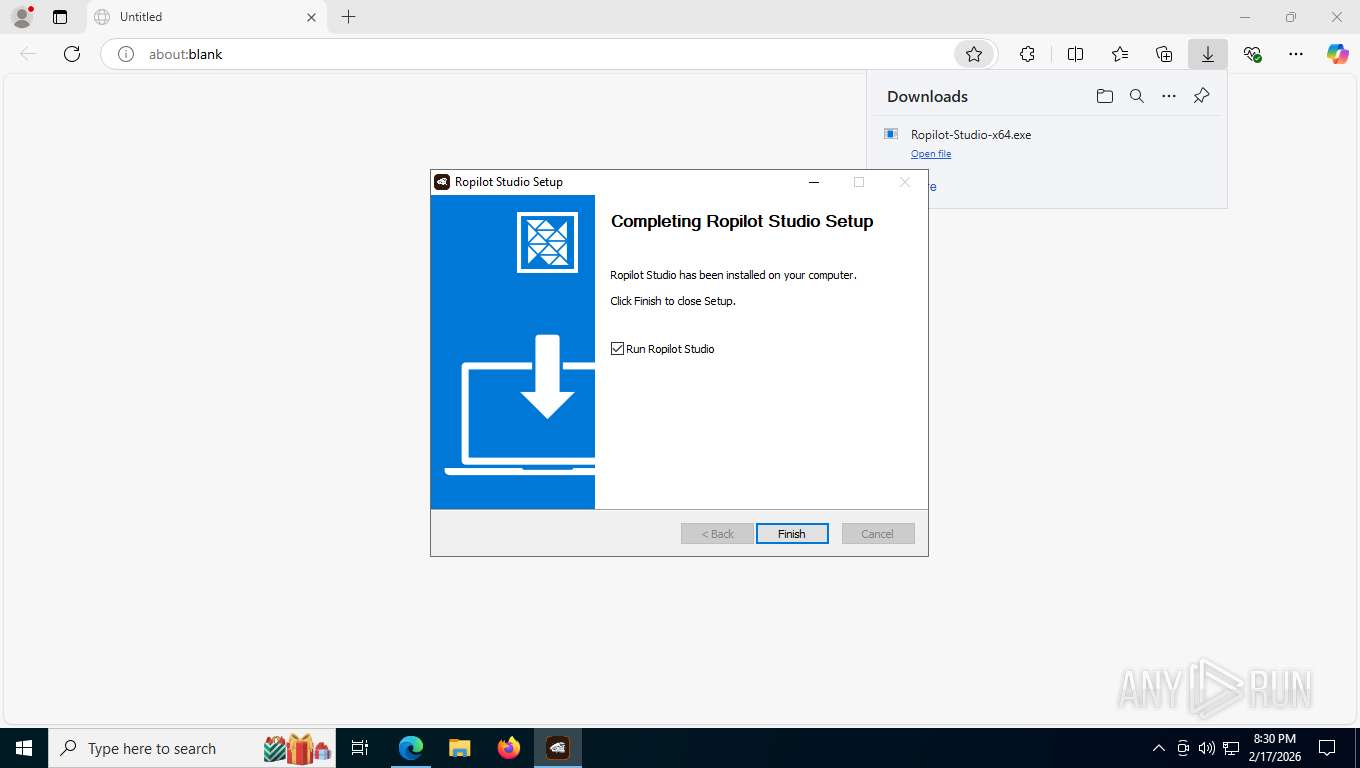
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\Ropilot Studio | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | ShortcutName |
Value: Ropilot Studio | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | DisplayName |
Value: Ropilot Studio 1.1.0 | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Uninstall Ropilot Studio.exe" /currentuser | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Uninstall Ropilot Studio.exe" /currentuser /S | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.1.0 | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Ropilot Studio.exe,0 | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | Publisher |
Value: Ropilot | |||
| (PID) Process: | (8580) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
28
Suspicious files
163
Text files
93
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e538c.TMP | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e539c.TMP | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e53ac.TMP | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e53ac.TMP | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e53ac.TMP | — | |
MD5:— | SHA256:— | |||
| 8196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
67
DNS requests
47
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6424 | msedge.exe | GET | 302 | 172.67.160.128:443 | https://ropilot.ai/downloads/windows | US | — | — | unknown |
6424 | msedge.exe | GET | 200 | 172.67.160.128:443 | https://ropilot.ai/downloads/Ropilot-Studio-x64.exe | US | — | — | unknown |
6424 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
6424 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:N8oqBaZoqYKz2TUZxpFxtZtY2ZDV5Rl9LODXYMjom_4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 98 b | whitelisted |
6424 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | binary | 295 b | whitelisted |
6424 | msedge.exe | GET | 200 | 52.123.243.194:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.30 Kb | whitelisted |
6424 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
6424 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | binary | 25 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8680 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.32:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 92.123.104.60:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 92.123.104.32:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8176 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ropilot.ai |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6424 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (.ropilot .ai) |
6424 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
6424 | msedge.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
7736 | Ropilot Studio.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7736 | Ropilot Studio.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |