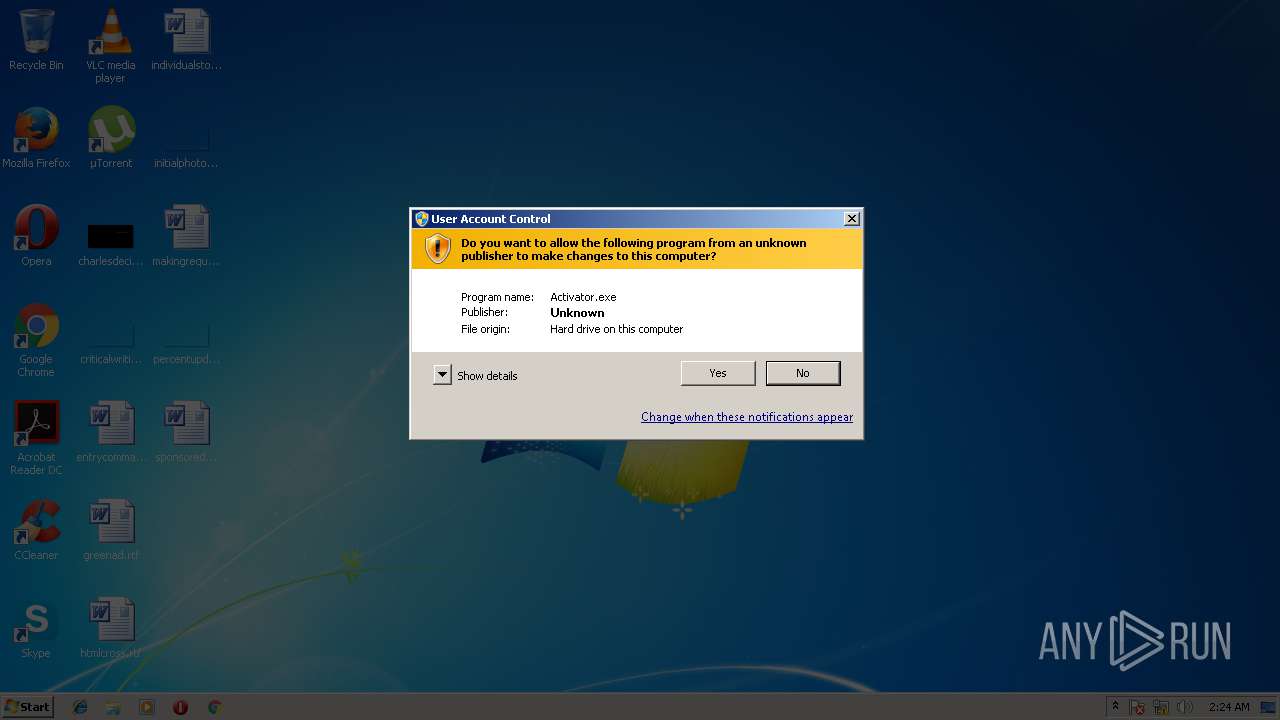
| File name: | Activator.exe |
| Full analysis: | https://app.any.run/tasks/6404cd32-8a09-4c24-874a-835532a84efd |
| Verdict: | No threats detected |
| Analysis date: | March 18, 2018, 02:24:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 063E6D3B5C4C8A35D0A12BD6D25176F9 |
| SHA1: | 203DF188A8922CB75AD6BBB5232C40B9DCEB8BFF |
| SHA256: | DDA1582FCDF7355BB64D7029F6C8C92F7768D93FA5F8921AF38D63A1BEBF5E3F |
| SSDEEP: | 12288:l+Qz1ml4GzNM2zcUs0wdaE8UrJac8dqVH6sA5fUrvvD8GaWdeA7X2zSrmm1eMNom:lmlZMuxs1f538sA5crYGaWcmX5feHq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in the system directory
- Activator.exe (PID: 2720)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:04:20 14:16:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 647168 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | 1204224 |
| EntryPoint: | 0x1c3870 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
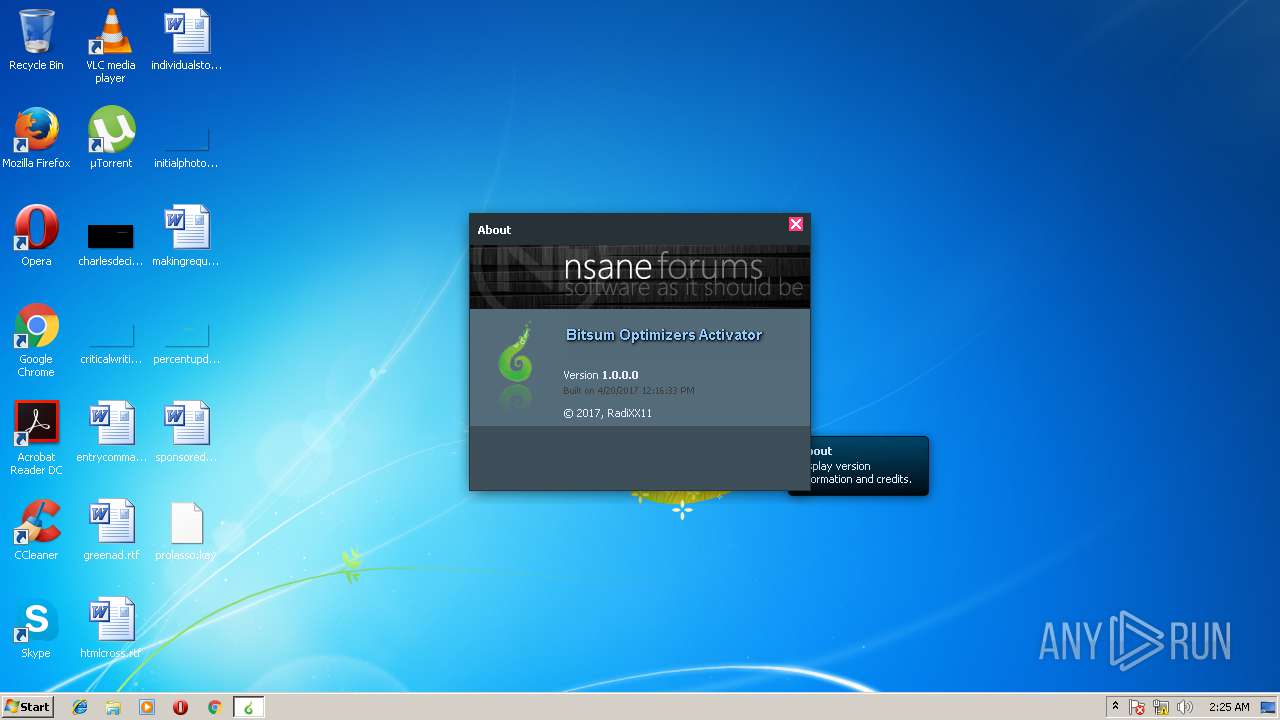
| CompanyName: | RadiXX11 |
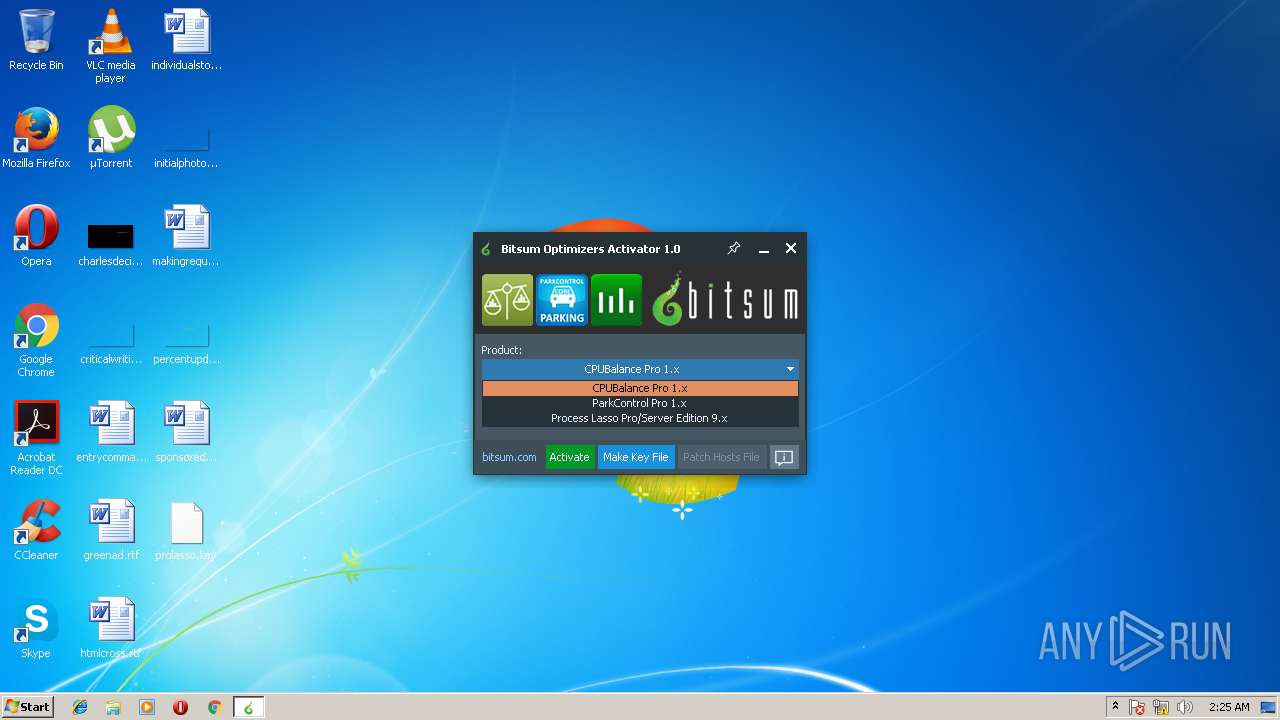
| FileDescription: | Activator for Bitsum CPU optimizers |
| FileVersion: | 1.0.0.0 |
| InternalName: | Activator.exe |
| LegalCopyright: | © 2017, RadiXX11 |
| LegalTrademarks: | - |
| OriginalFileName: | Activator.exe |
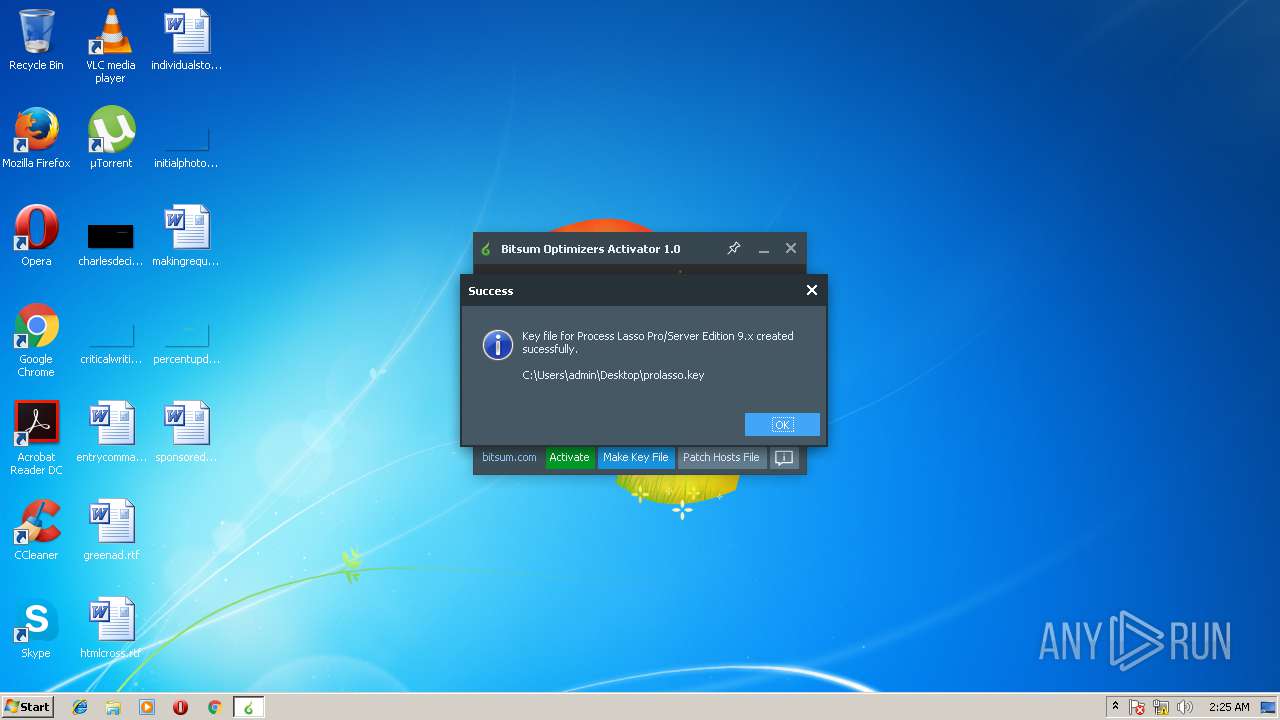
| ProductName: | Bitsum Optimizers Activator |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Apr-2017 12:16:33 |
| Detected languages: |
|
| CompanyName: | RadiXX11 |
| FileDescription: | Activator for Bitsum CPU optimizers |
| FileVersion: | 1.0.0.0 |
| InternalName: | Activator.exe |
| LegalCopyright: | © 2017, RadiXX11 |
| LegalTrademarks: | - |
| OriginalFilename: | Activator.exe |
| ProductName: | Bitsum Optimizers Activator |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Apr-2017 12:16:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00126000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.text | 0x00127000 | 0x0009E000 | 0x0009D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99944 |
.rsrc | 0x001C5000 | 0x0000E000 | 0x0000D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.84898 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91364 | 1847 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.71337 | 3752 | UNKNOWN | Spanish - Argentina | RT_ICON |
3 | 4.17944 | 2216 | UNKNOWN | Spanish - Argentina | RT_ICON |
4 | 4.34239 | 1384 | UNKNOWN | Spanish - Argentina | RT_ICON |
5 | 2.73137 | 16936 | UNKNOWN | Spanish - Argentina | RT_ICON |
6 | 3.90473 | 9640 | UNKNOWN | Spanish - Argentina | RT_ICON |
7 | 4.42289 | 4264 | UNKNOWN | Spanish - Argentina | RT_ICON |
8 | 5.32706 | 1128 | UNKNOWN | Spanish - Argentina | RT_ICON |
3682 | 6.09003 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
3683 | 6.82981 | 170 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
IMAGEHLP.DLL |
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
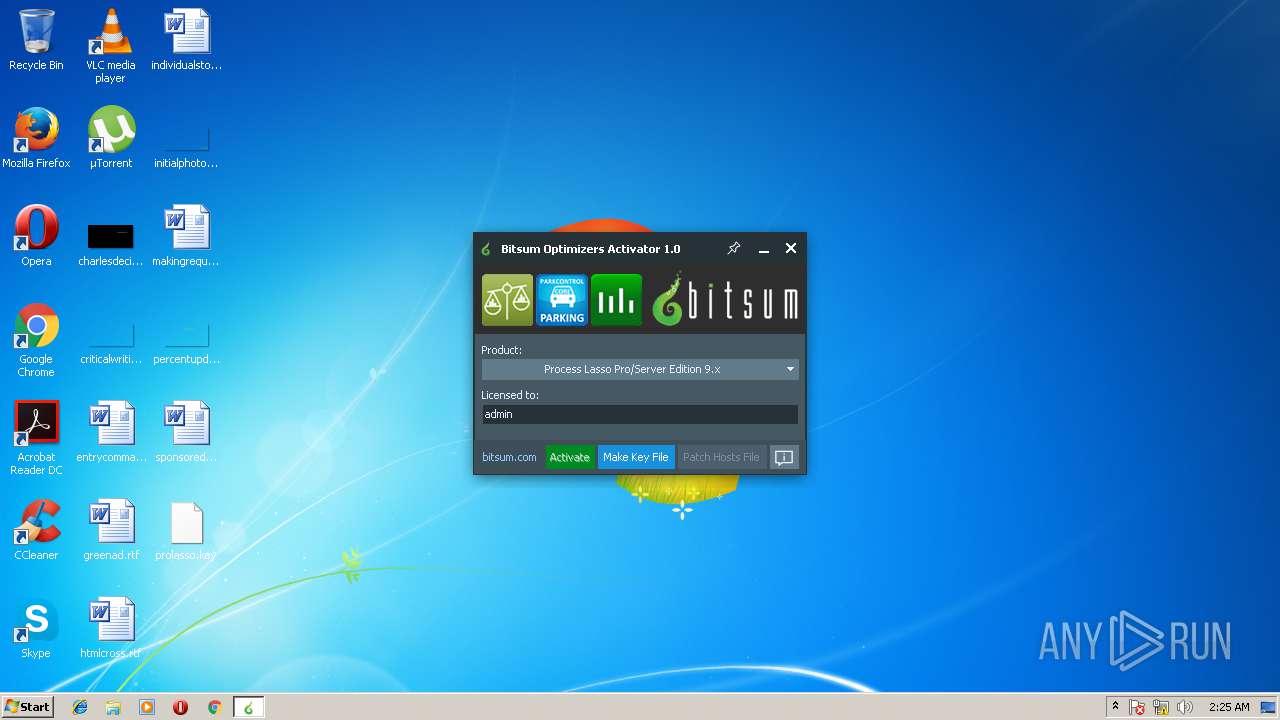
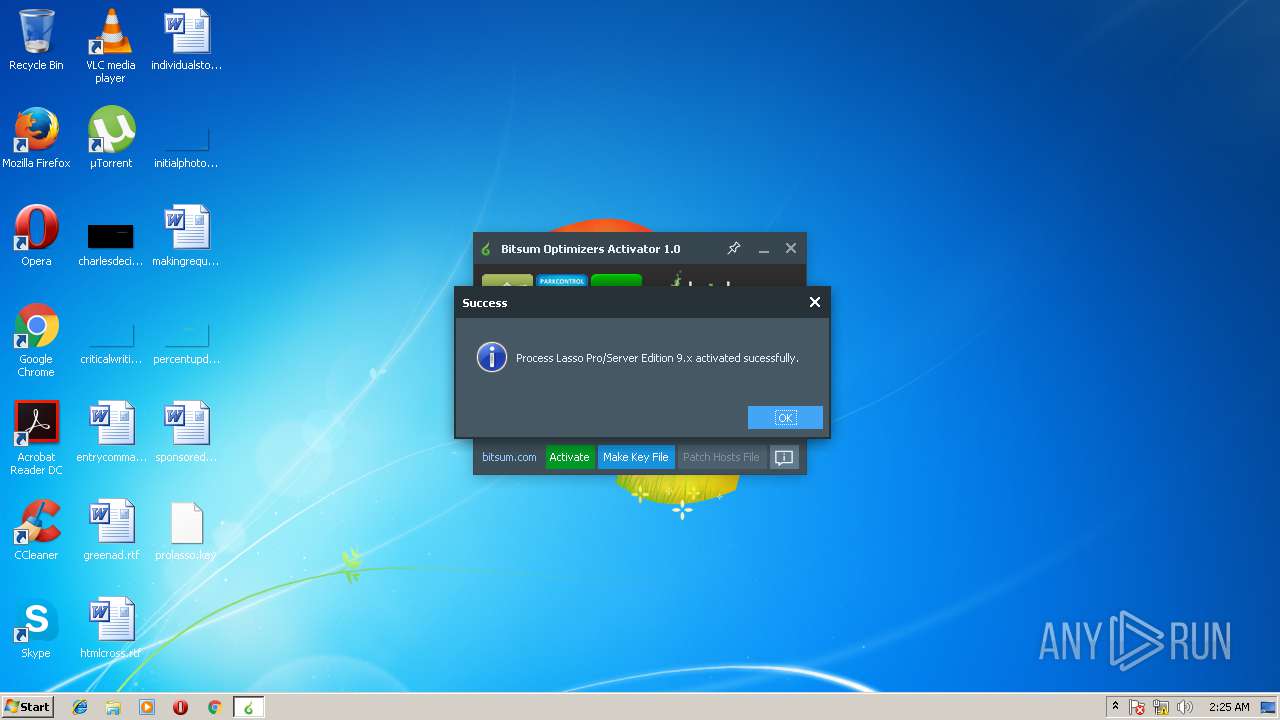
| 2720 | "C:\Users\admin\Downloads\Activator.exe" | C:\Users\admin\Downloads\Activator.exe | explorer.exe | ||||||||||||
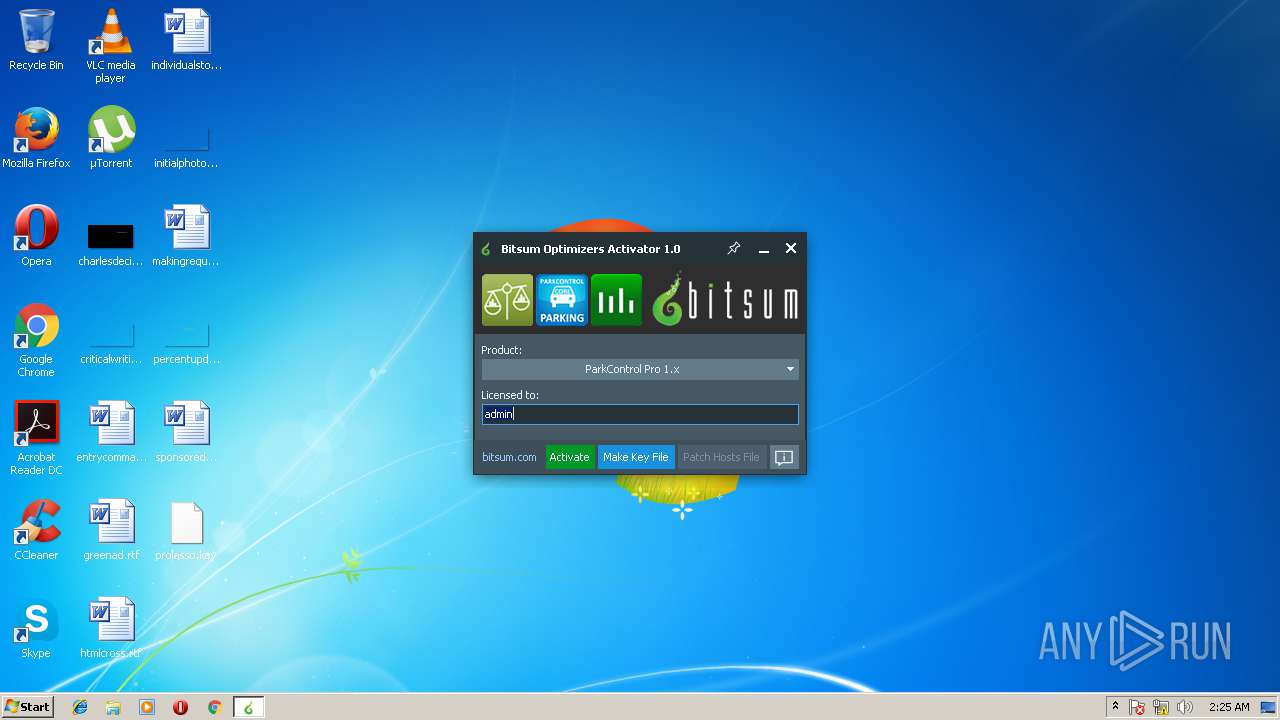
User: admin Company: RadiXX11 Integrity Level: HIGH Description: Activator for Bitsum CPU optimizers Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\Downloads\Activator.exe" | C:\Users\admin\Downloads\Activator.exe | — | explorer.exe | |||||||||||
User: admin Company: RadiXX11 Integrity Level: MEDIUM Description: Activator for Bitsum CPU optimizers Exit code: 3221226540 Version: 1.0.0.0 | |||||||||||||||
Total events
417
Read events
395
Write events
22
Delete events
0
Modification events
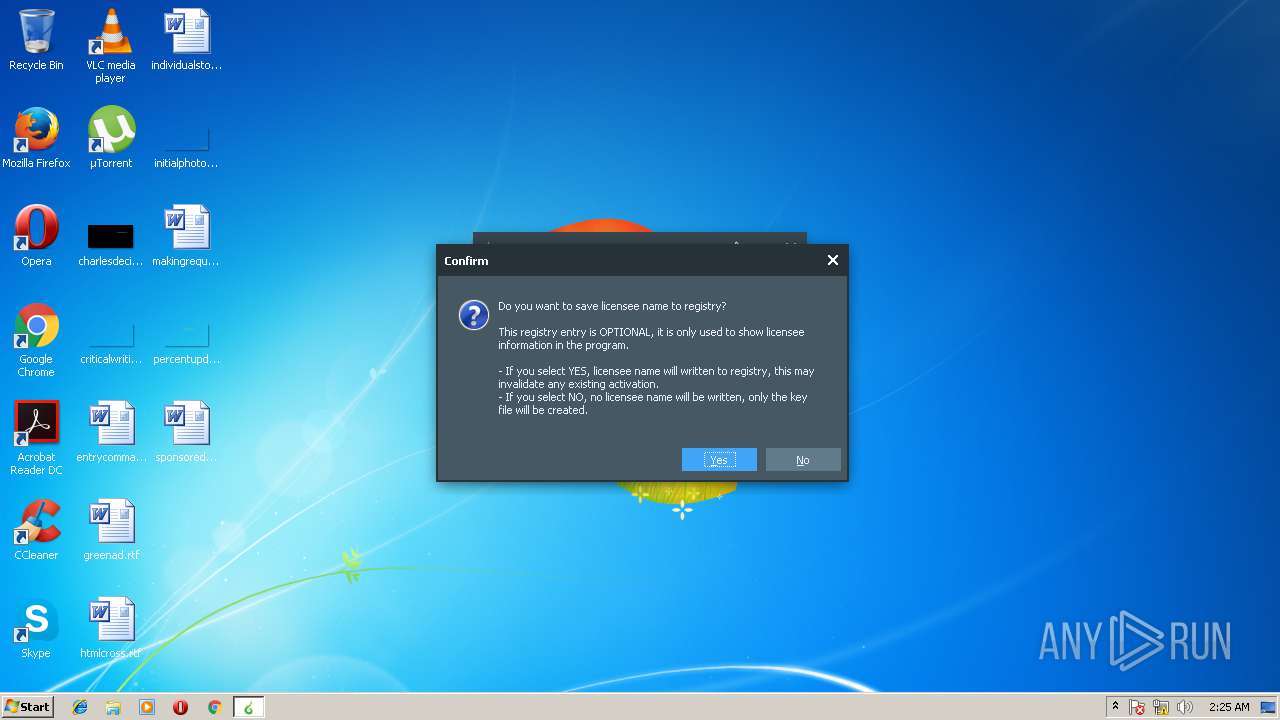
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_CURRENT_USER\Software\ProcessLasso |
| Operation: | write | Name: | LicensedTo |
Value: admin | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ProcessLasso |
| Operation: | write | Name: | LicensedTo |
Value: admin | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_CURRENT_USER\Software\ProcessLasso |
| Operation: | write | Name: | EDD |
Value: 1 | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_CURRENT_USER\Software\ProcessLasso |
| Operation: | write | Name: | ValidCPU |
Value: 1 | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_CURRENT_USER\Software\ProcessLasso |
| Operation: | write | Name: | ea |
Value: 1 | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_CURRENT_USER\Software\ProcessLasso |
| Operation: | write | Name: | ViewState |
Value: AB488EF6A69C86CC | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_CURRENT_USER\Software\ProcessLasso |
| Operation: | write | Name: | CacheTag |
Value: A025D2644756F55F | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ProcessLasso |
| Operation: | write | Name: | EDD |
Value: 1 | |||
| (PID) Process: | (2720) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ProcessLasso |
| Operation: | write | Name: | ValidCPU |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
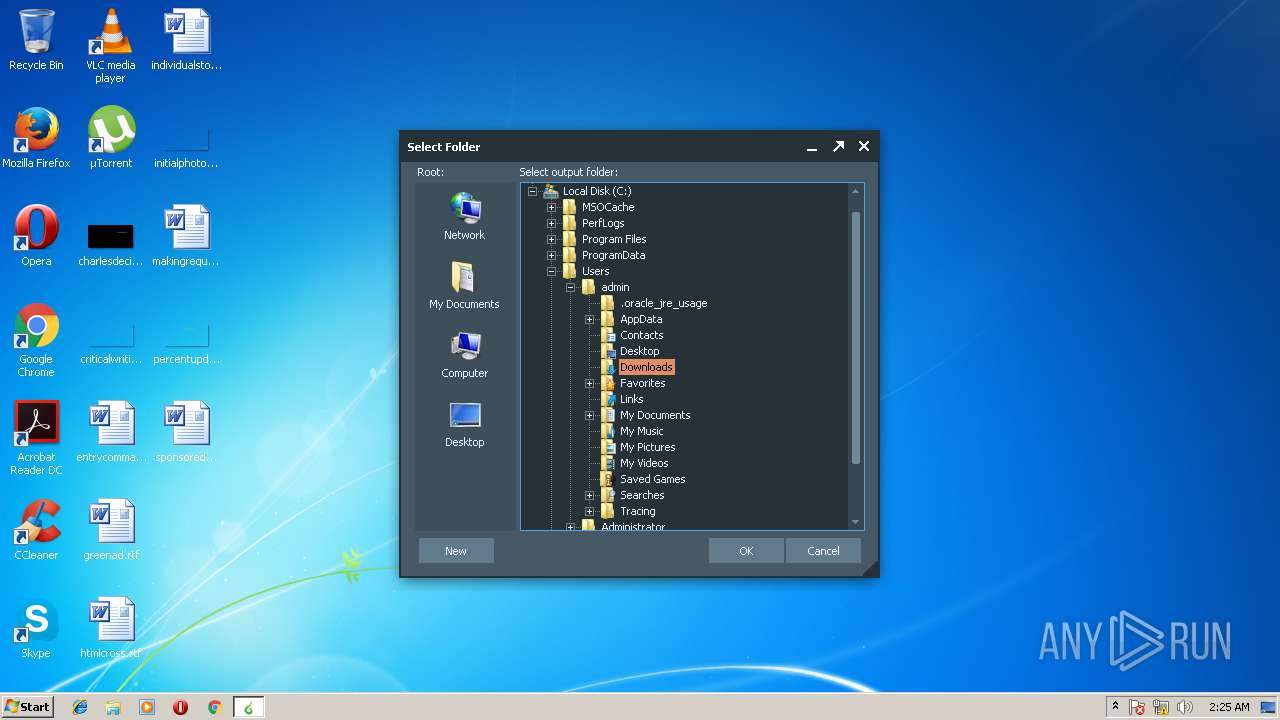
| 2720 | Activator.exe | C:\Windows\system32\drivers\etc\hosts | text | |
MD5:279F7F8F71600DEA60A07250C3BCC4CD | SHA256:6A6E46D145E4669E6A9284DAA56B5E286374BABAC9BA64D2473CCEE01C7BA377 | |||
| 2720 | Activator.exe | C:\Users\admin\Desktop\prolasso.key | binary | |
MD5:422411B13506374E17967CB5BDA59467 | SHA256:ABAE0F95ABEBC2F3B10D6D4C103C7E17E0A5638E62AF56A259160E6008035A00 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report