| download: | AnyDesk.exe |
| Full analysis: | https://app.any.run/tasks/c0702a31-8539-4450-bb58-6575a15f0958 |
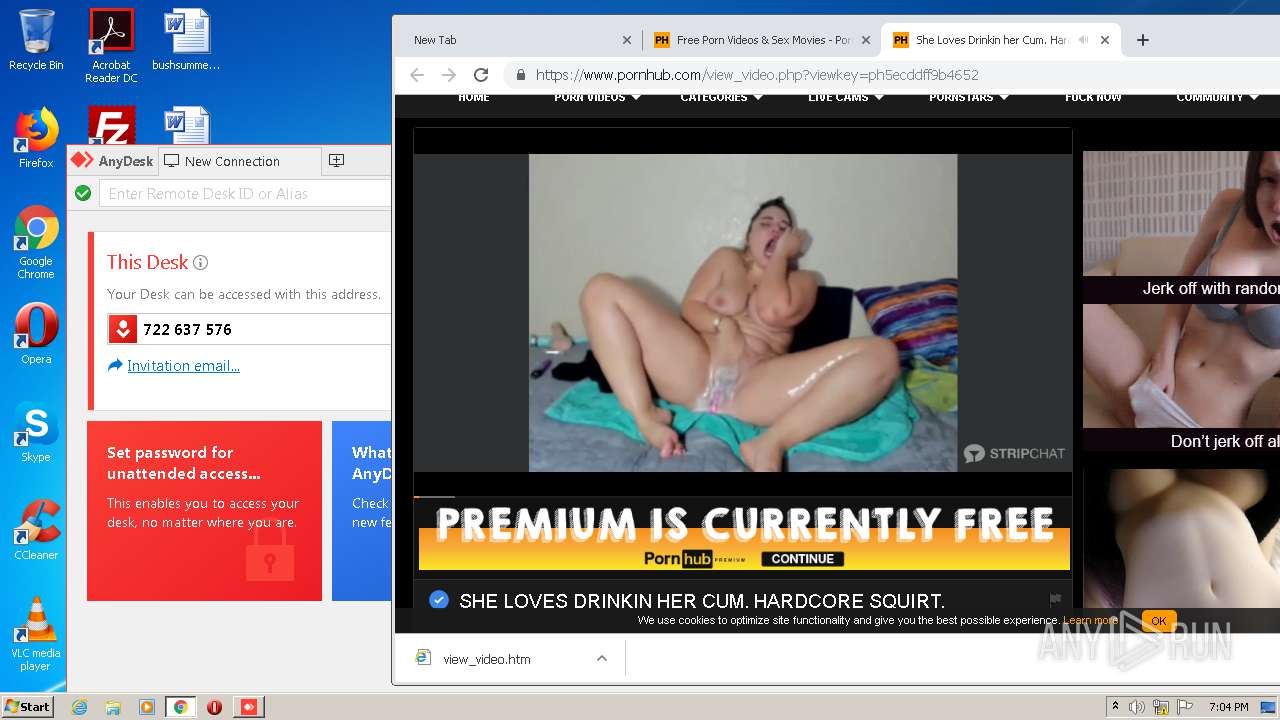
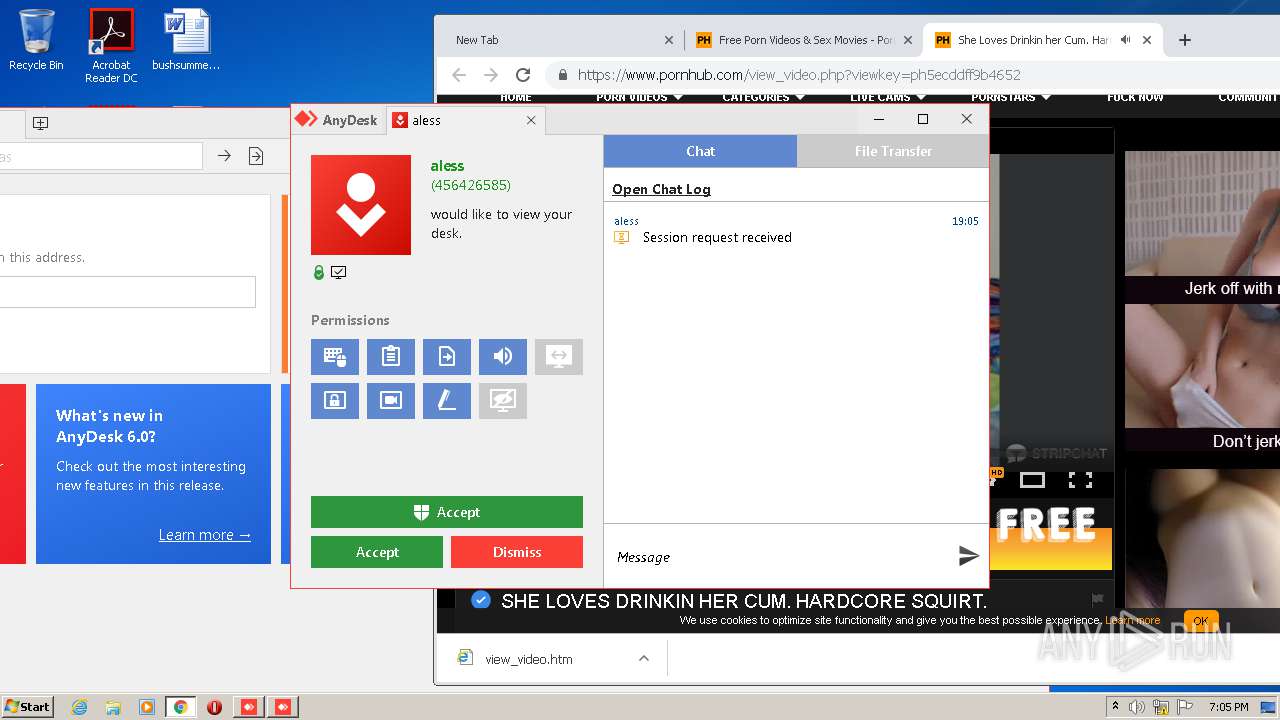
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2020, 18:02:02 |
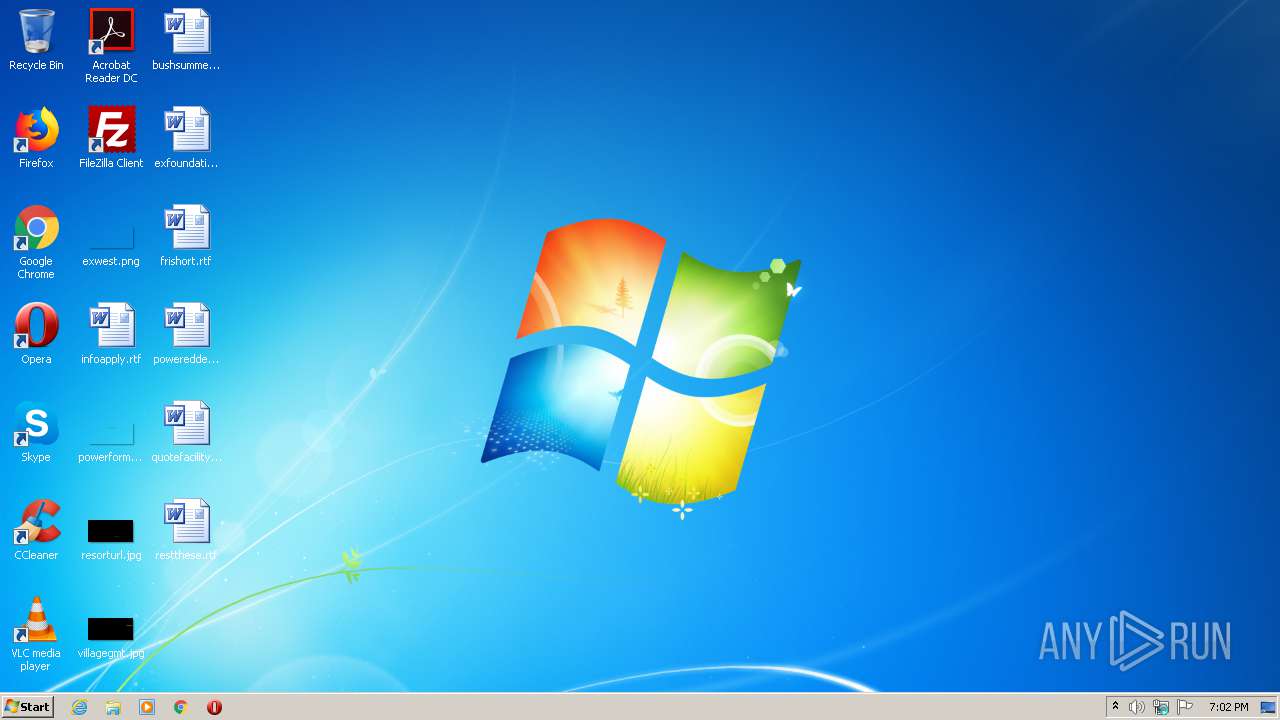
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A4D4C0A0388852421DB53DDCB919F090 |
| SHA1: | 33A8D89A37567C8D3C036FD0B15E1D2F4FC46579 |
| SHA256: | DD7AA730255DA936AF74821FE2E90CBEEC20A06F543F1FABF924D129F526C014 |
| SSDEEP: | 49152:5dqwAtvmTB7H9SHaq0qPykbK+ZDOJaVjJBzXllvLjPgPWy6vQH6/vZhoW6qKmMdi:5Fzzq0aJJDOojBTll/ILmL7oW61HKB |
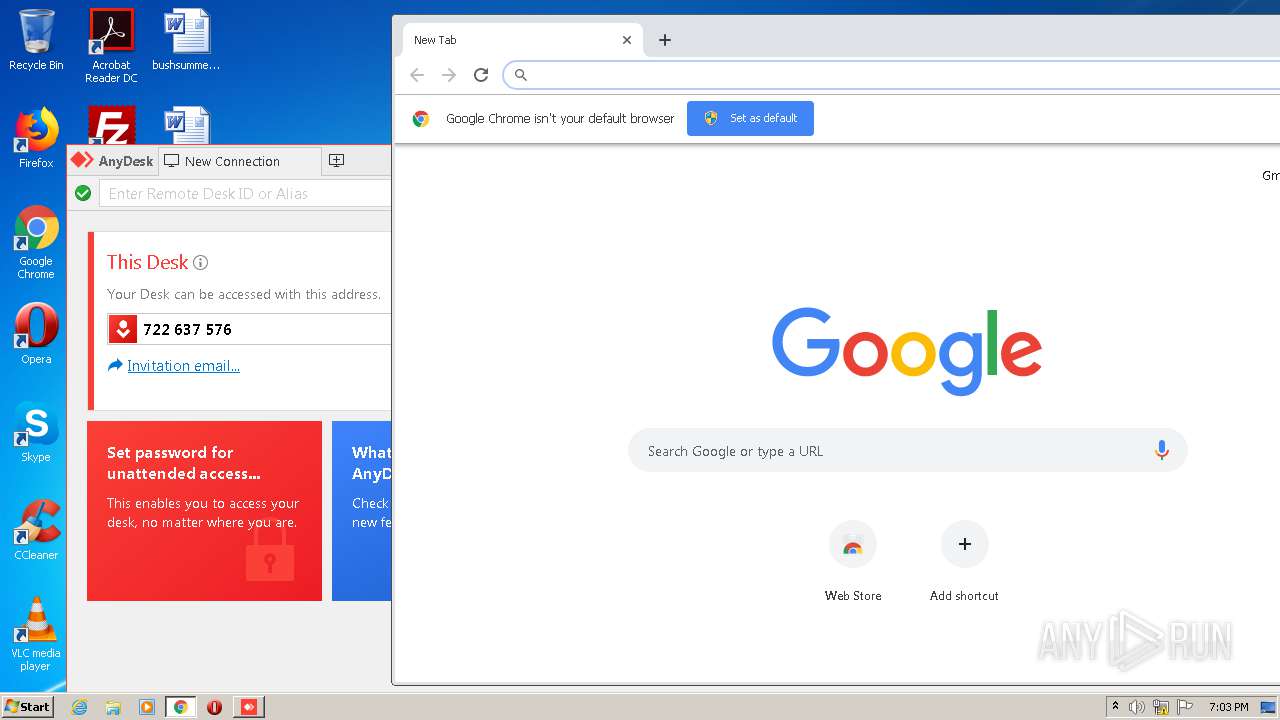
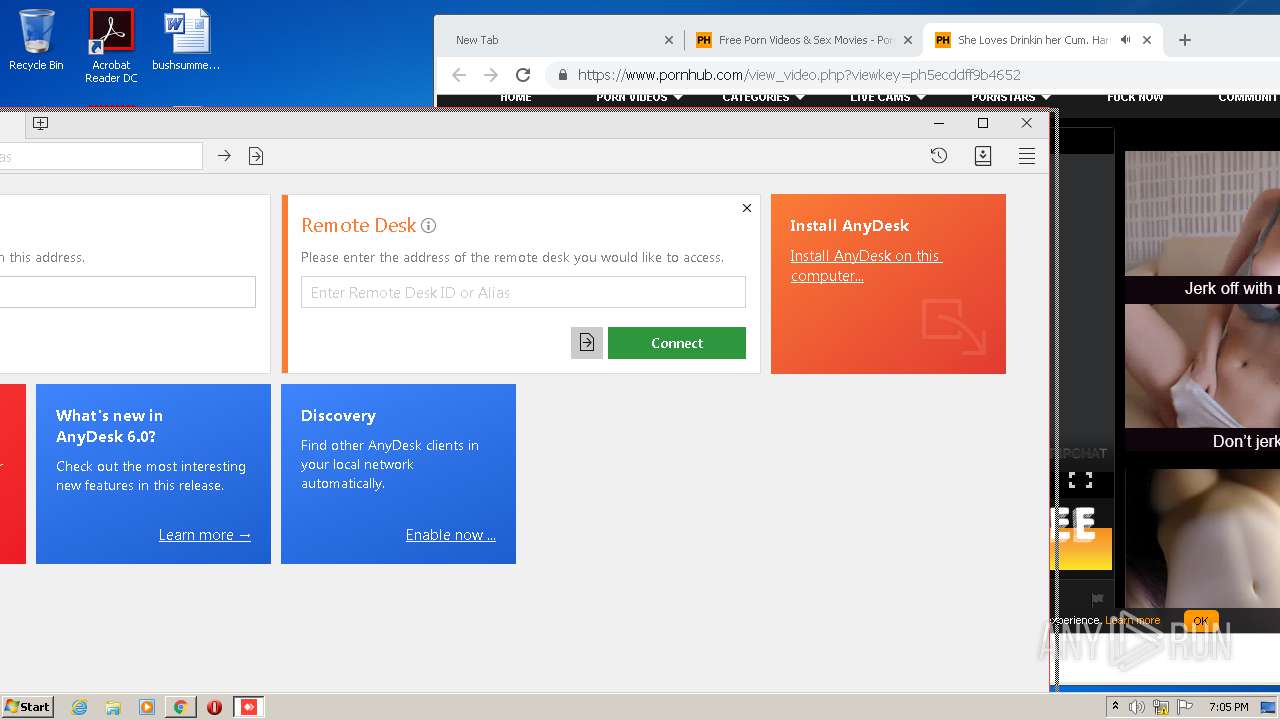
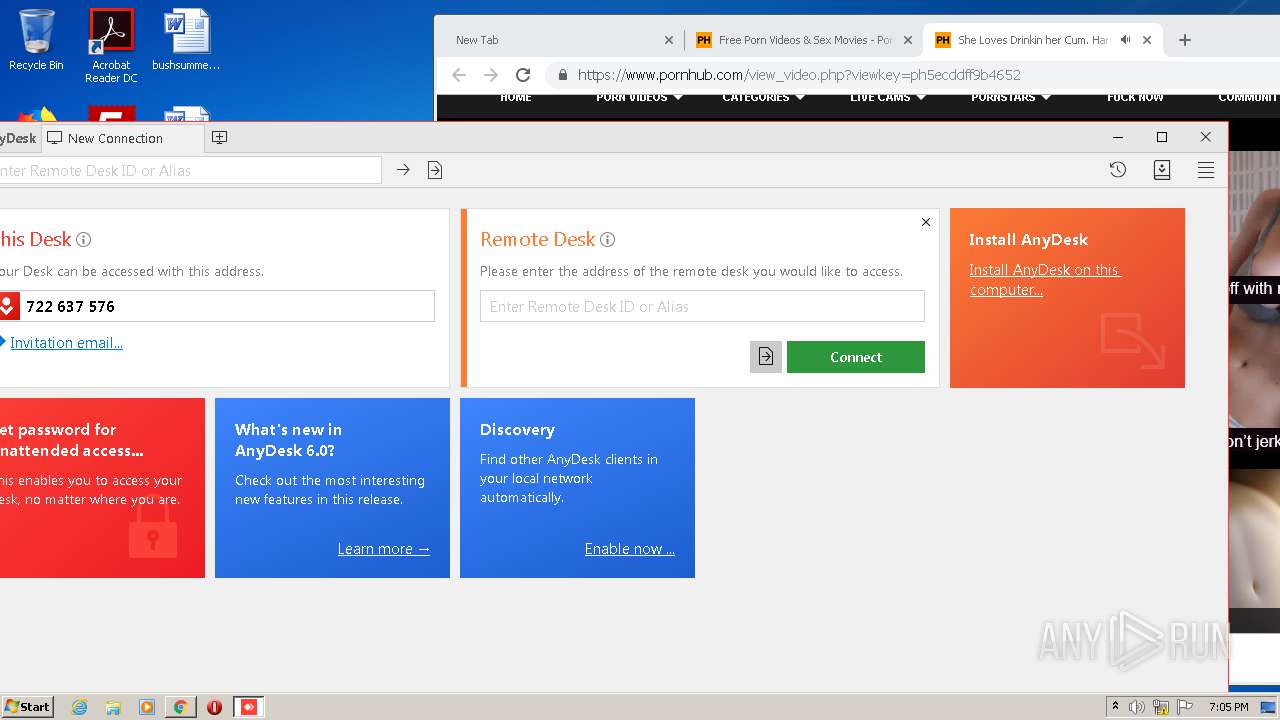
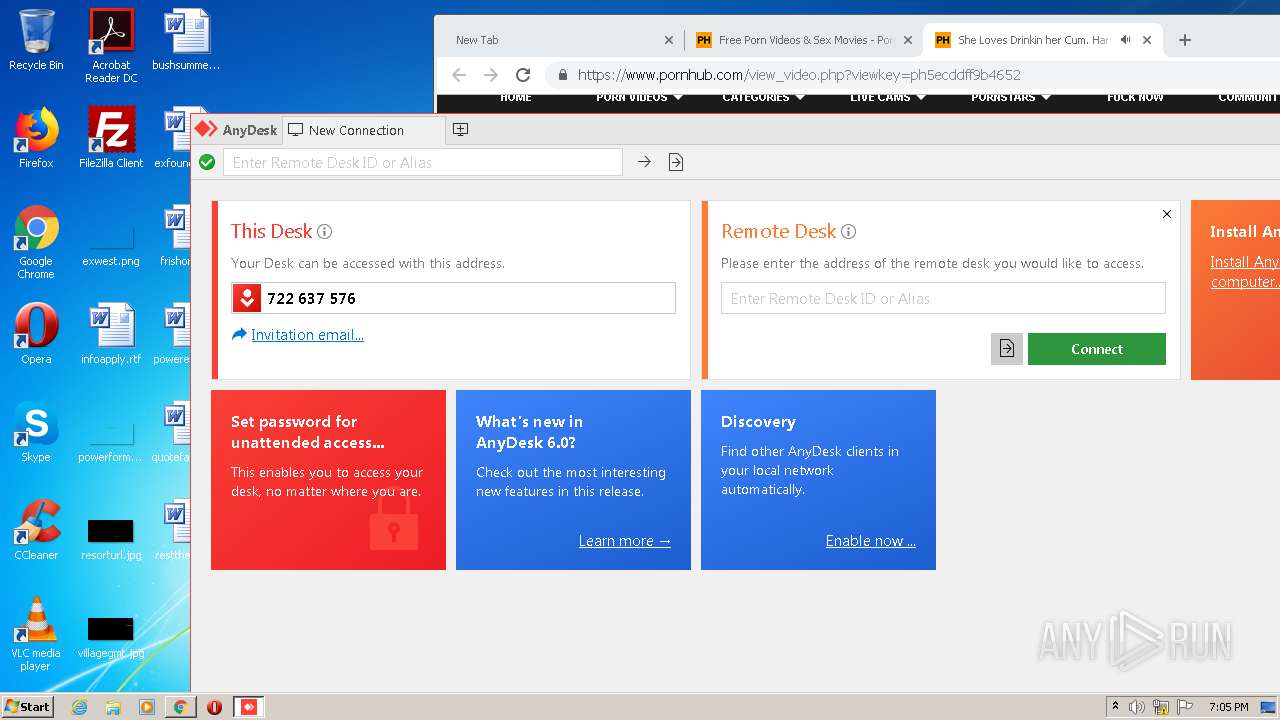
MALICIOUS
Loads dropped or rewritten executable
- AnyDesk.exe (PID: 2428)
- AnyDesk.exe (PID: 2056)
SUSPICIOUS
Application launched itself
- AnyDesk.exe (PID: 2184)
- AnyDesk.exe (PID: 2428)
Creates files in the user directory
- AnyDesk.exe (PID: 2184)
- AnyDesk.exe (PID: 2428)
Executable content was dropped or overwritten
- AnyDesk.exe (PID: 2428)
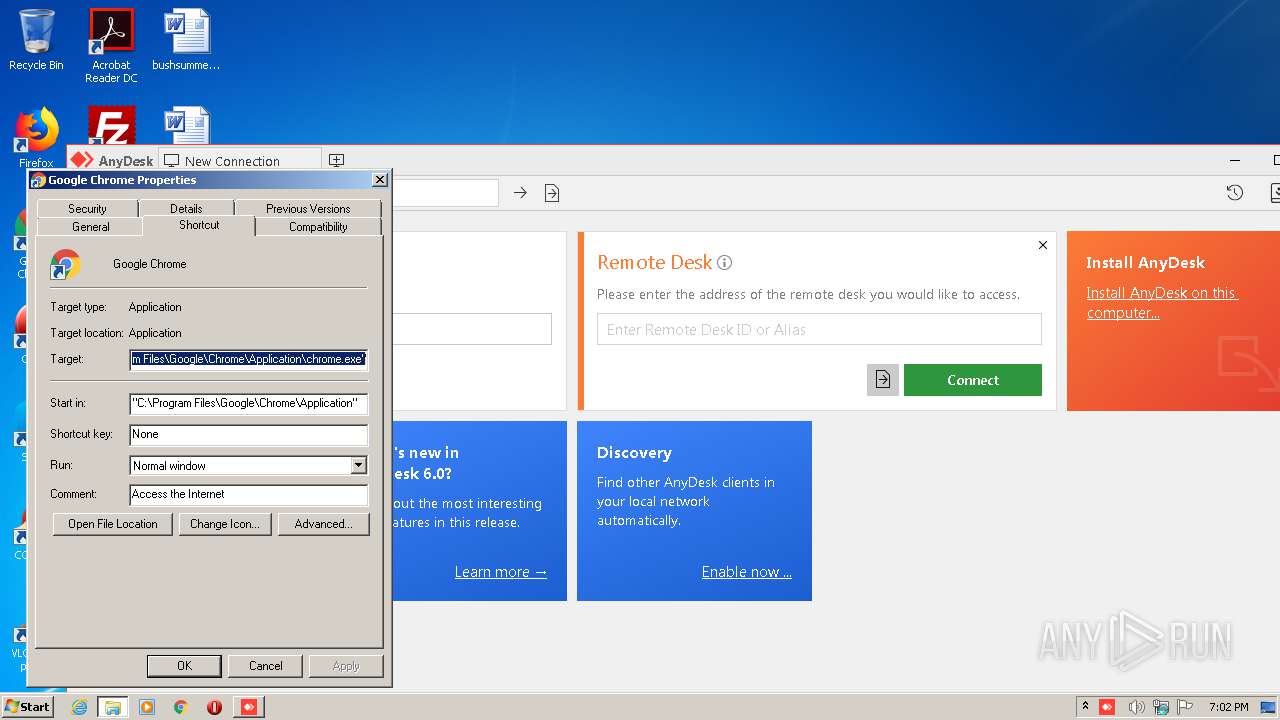
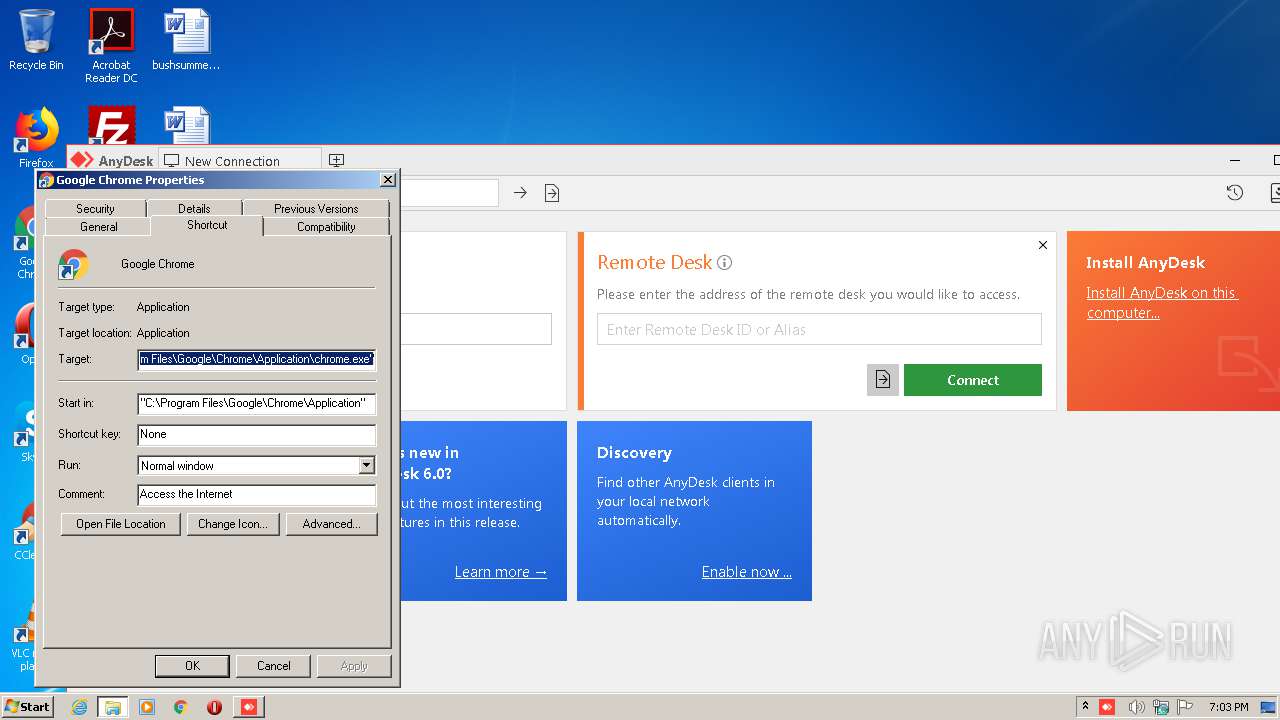
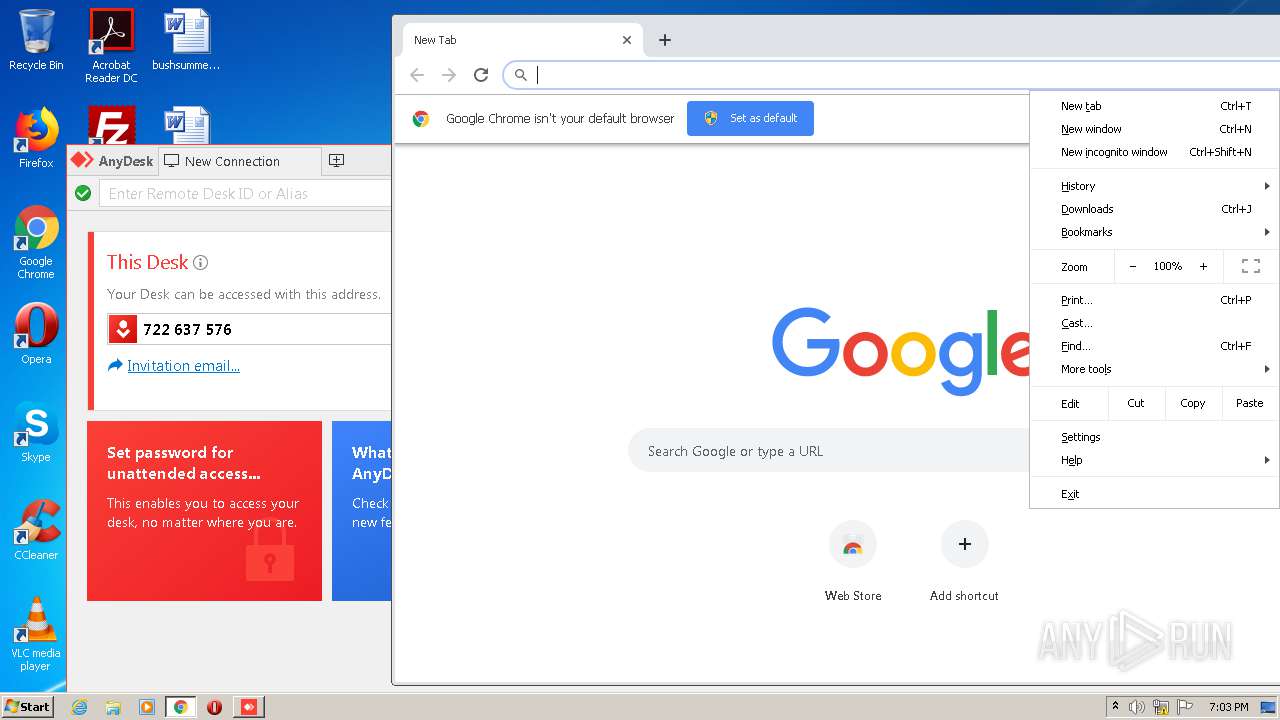
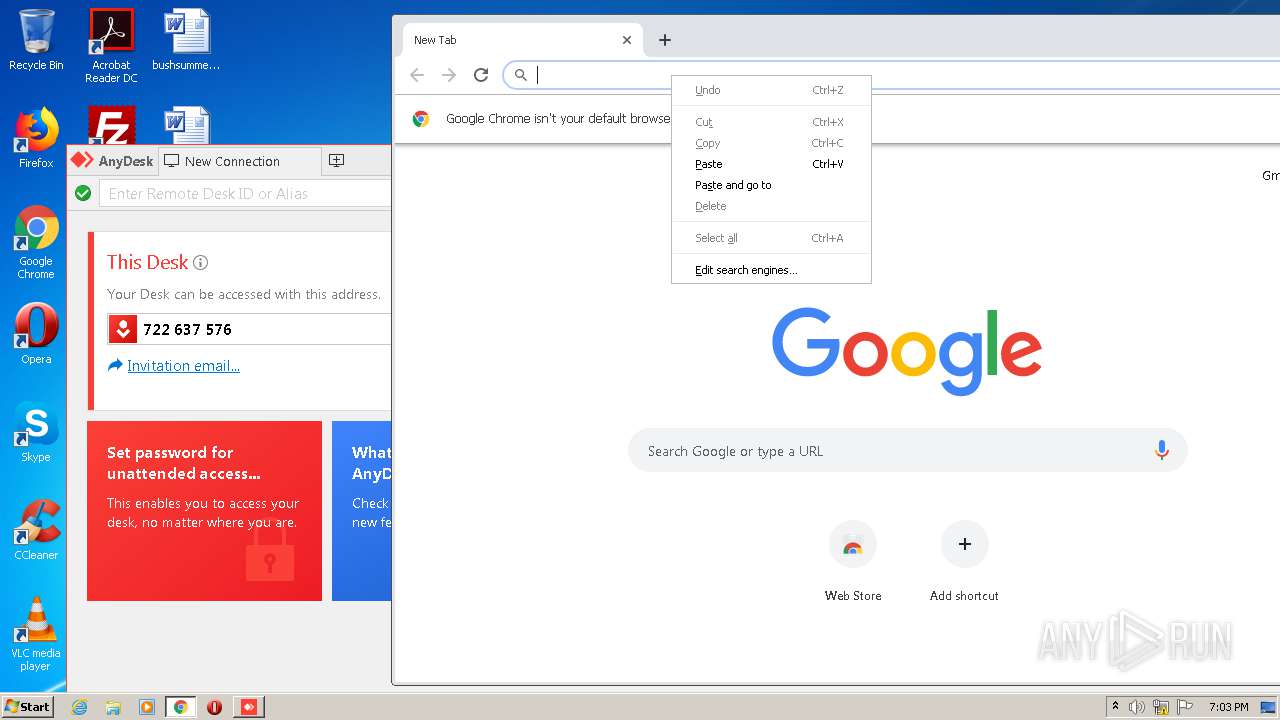
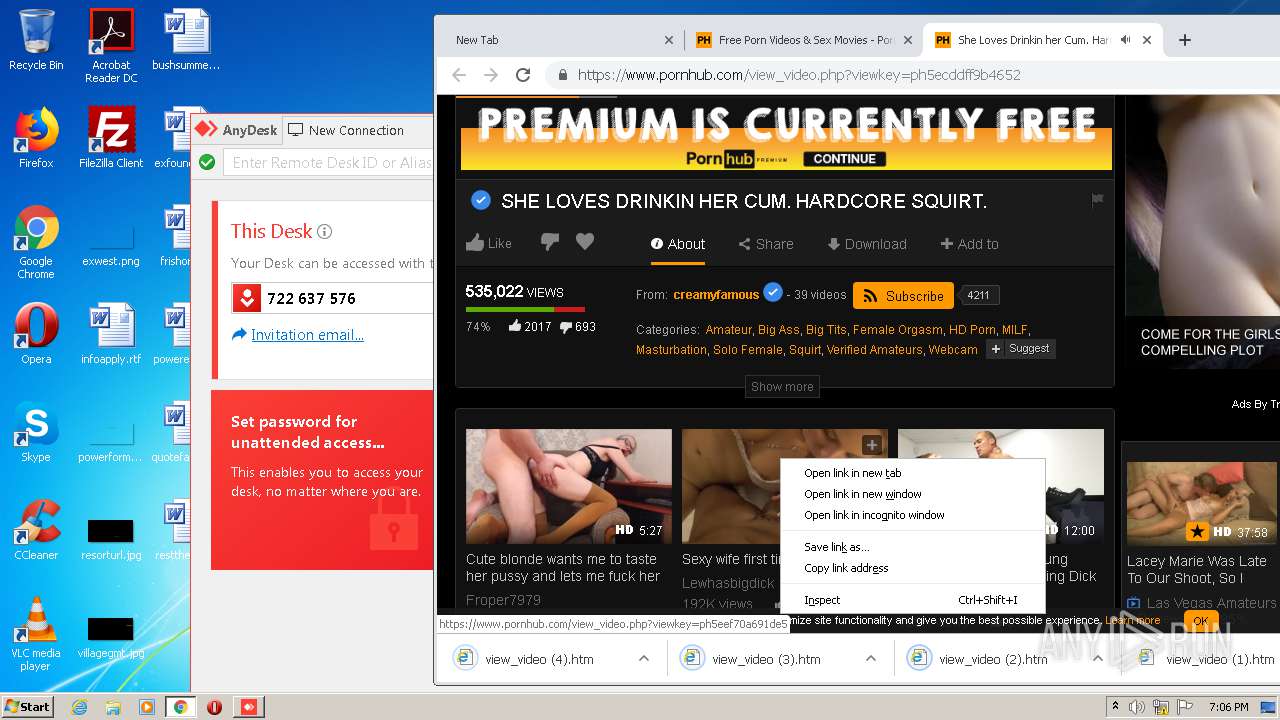
Modifies files in Chrome extension folder
- chrome.exe (PID: 2332)
INFO
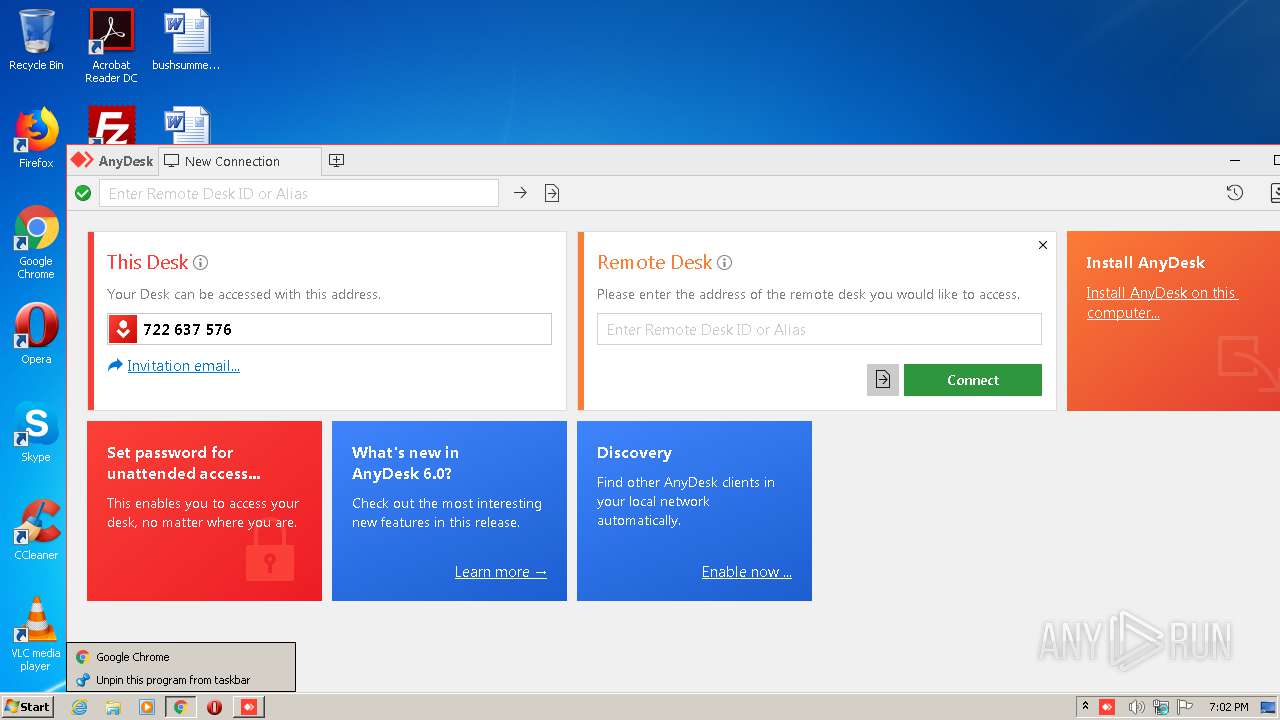
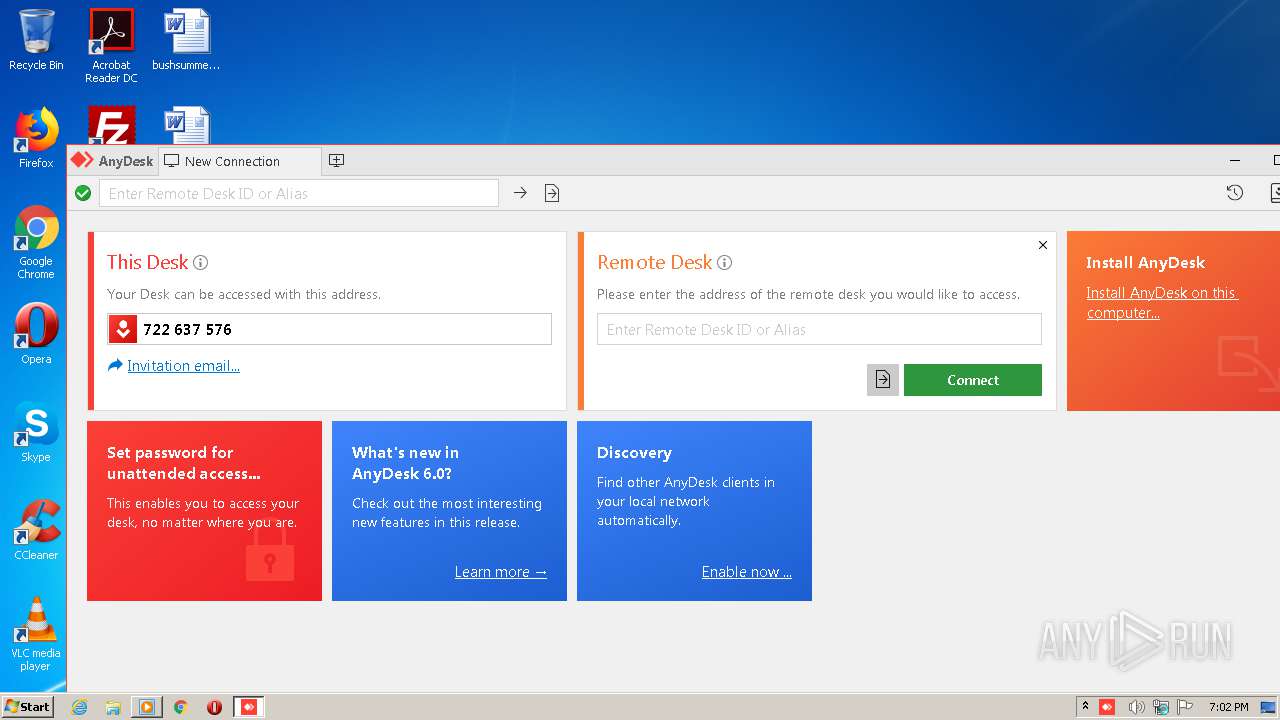
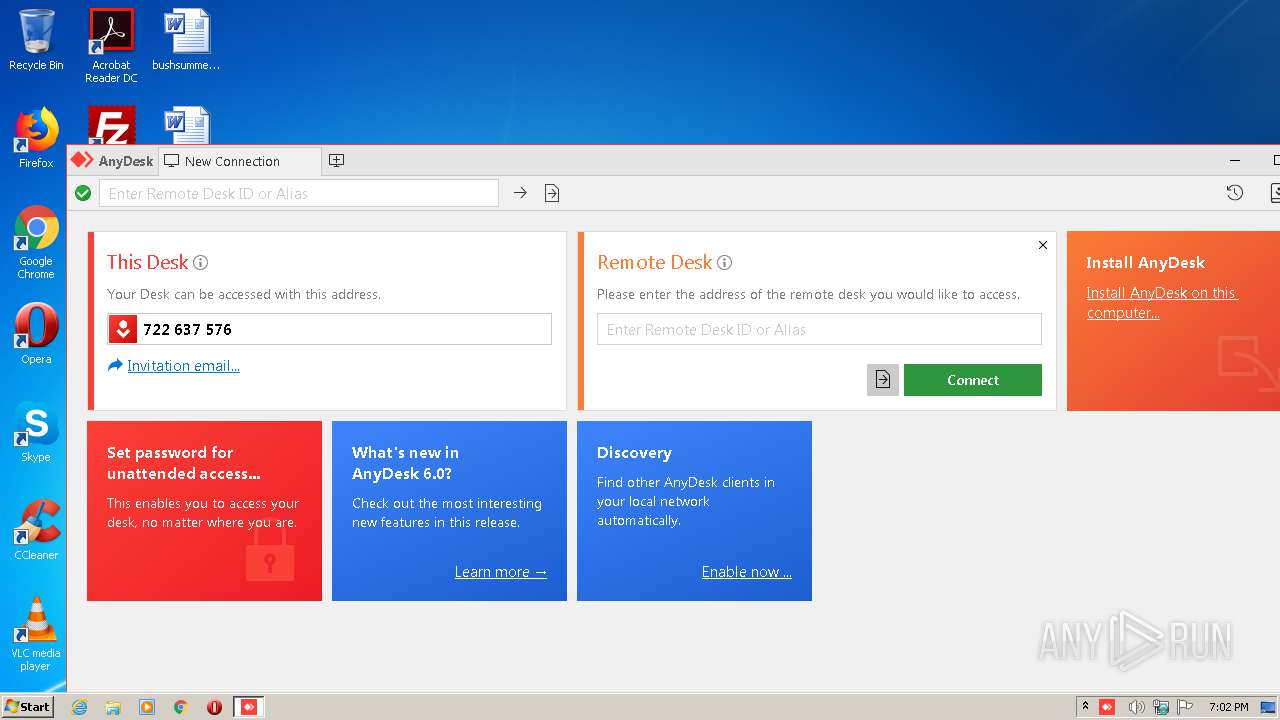
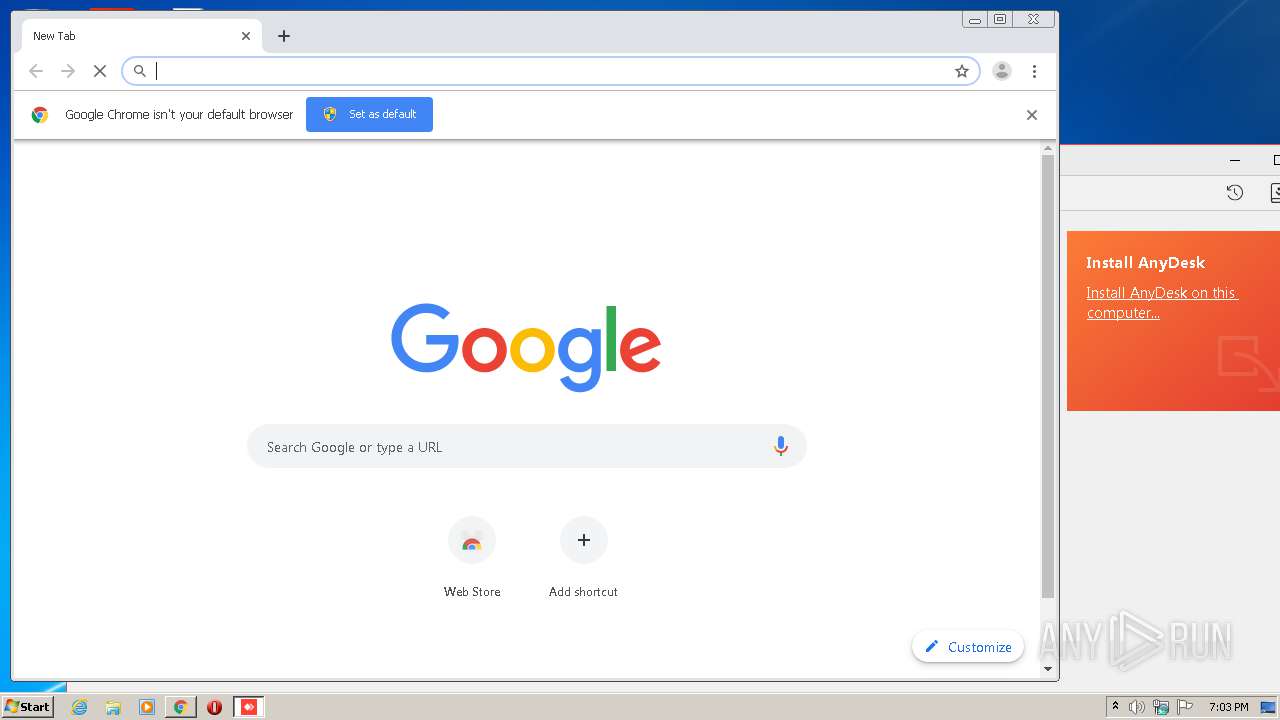
Manual execution by user
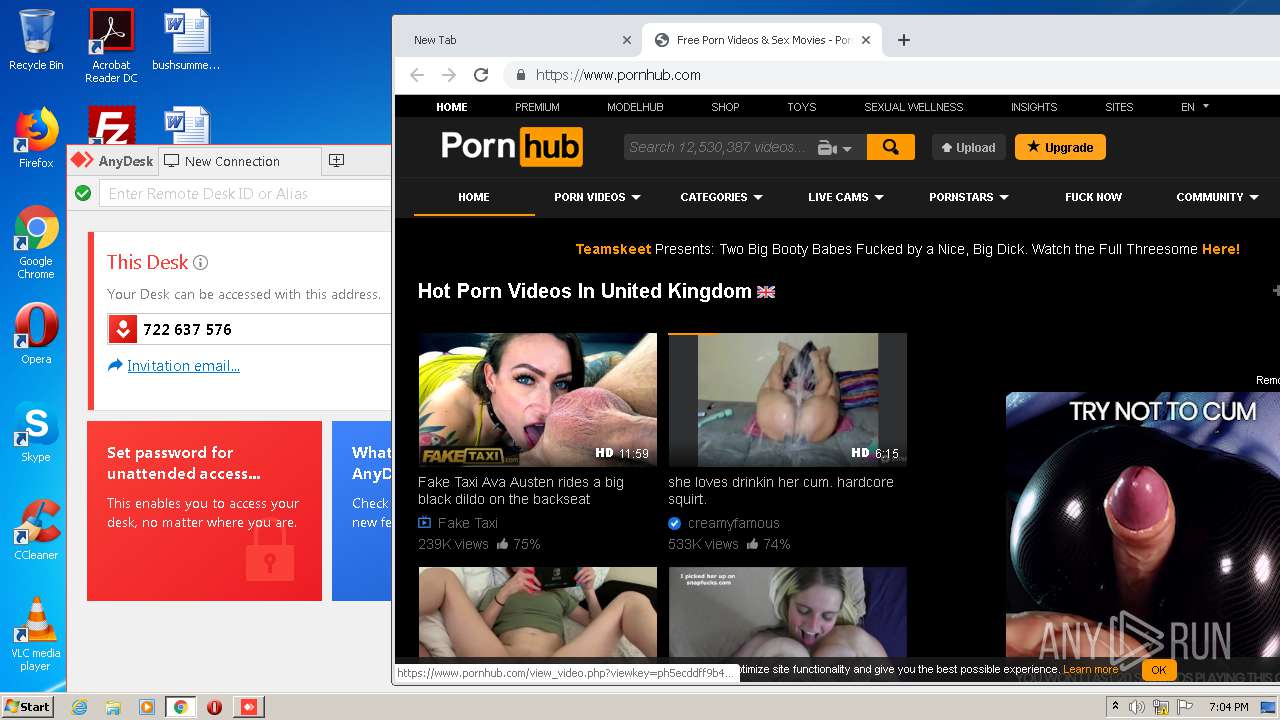
- chrome.exe (PID: 2332)
Application launched itself
- chrome.exe (PID: 2332)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2332)
Reads the hosts file
- chrome.exe (PID: 2332)
- chrome.exe (PID: 852)
Reads Internet Cache Settings
- chrome.exe (PID: 2332)
Reads settings of System Certificates
- chrome.exe (PID: 852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:10 18:01:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 10752 |
| InitializedDataSize: | 3642368 |
| UninitializedDataSize: | 10432000 |
| EntryPoint: | 0x1ce9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.5.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | philandro Software GmbH |
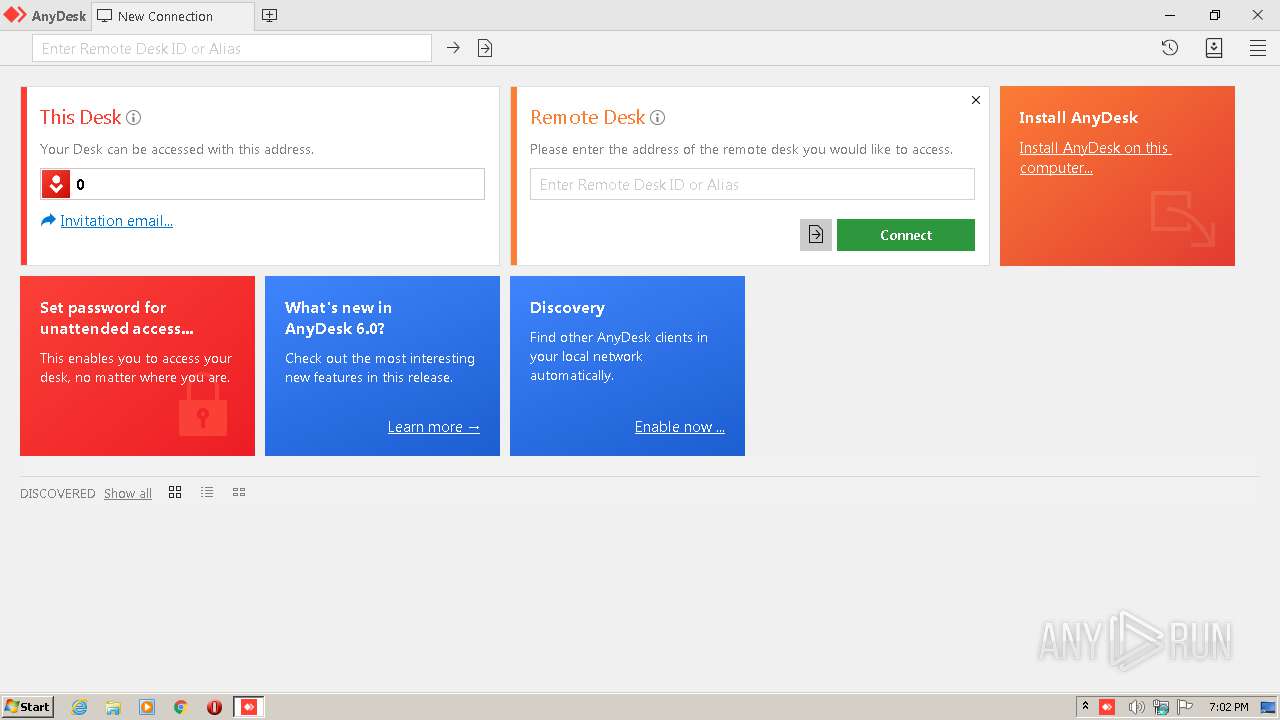
| FileDescription: | AnyDesk |
| FileVersion: | 6.0.5.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 6 |
| LegalCopyright: | (C) 2020 philandro Software GmbH |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jul-2020 16:01:11 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 6.0.5.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 6.0 |
| LegalCopyright: | (C) 2020 philandro Software GmbH |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 10-Jul-2020 16:01:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002835 | 0x00002A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51839 |
.itext | 0x00004000 | 0x009F2E00 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x009F7000 | 0x000002FA | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.63439 |
.data | 0x009F8000 | 0x0037569C | 0x00375400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99995 |
.rsrc | 0x00D6E000 | 0x00003290 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.68396 |
.reloc | 0x00D72000 | 0x00000300 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.18127 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39334 | 1543 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.29968 | 1640 | UNKNOWN | English - United States | RT_ICON |
3 | 3.6735 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 2.73746 | 488 | UNKNOWN | English - United States | RT_ICON |
5 | 3.69265 | 296 | UNKNOWN | English - United States | RT_ICON |
1000 | 2.78538 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
Total processes
84
Monitored processes
45
Malicious processes
1
Suspicious processes
1
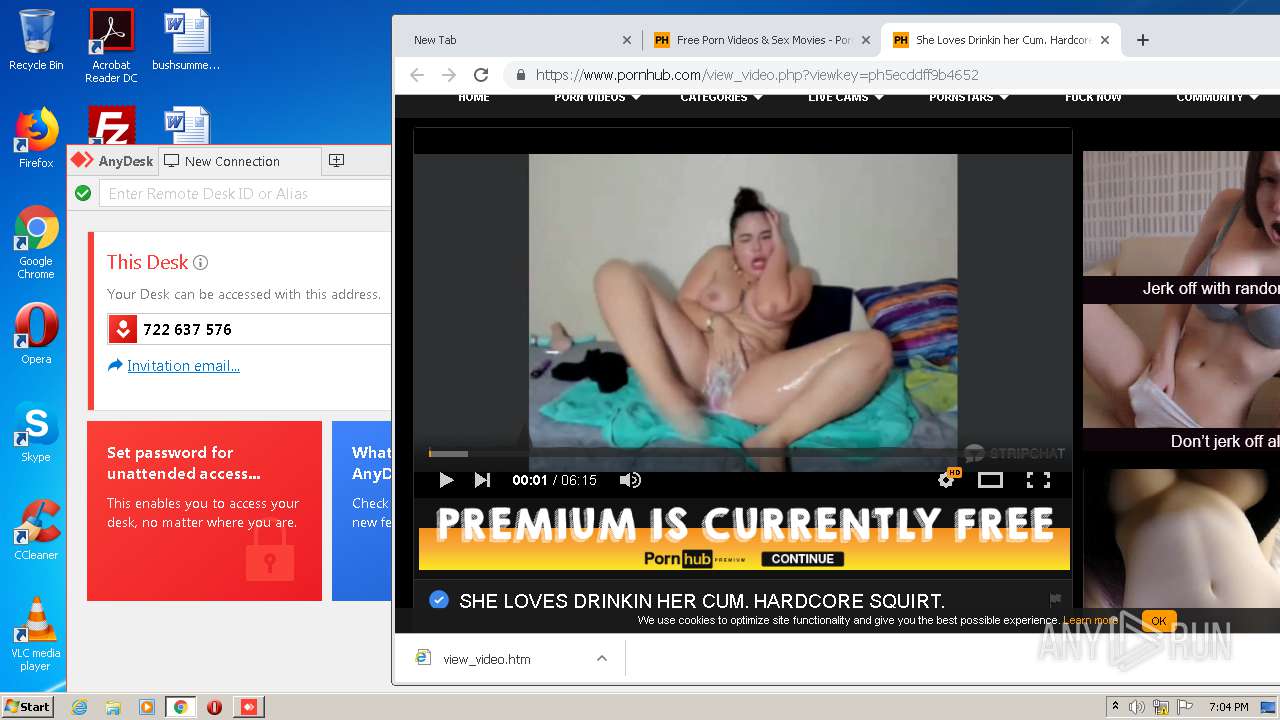
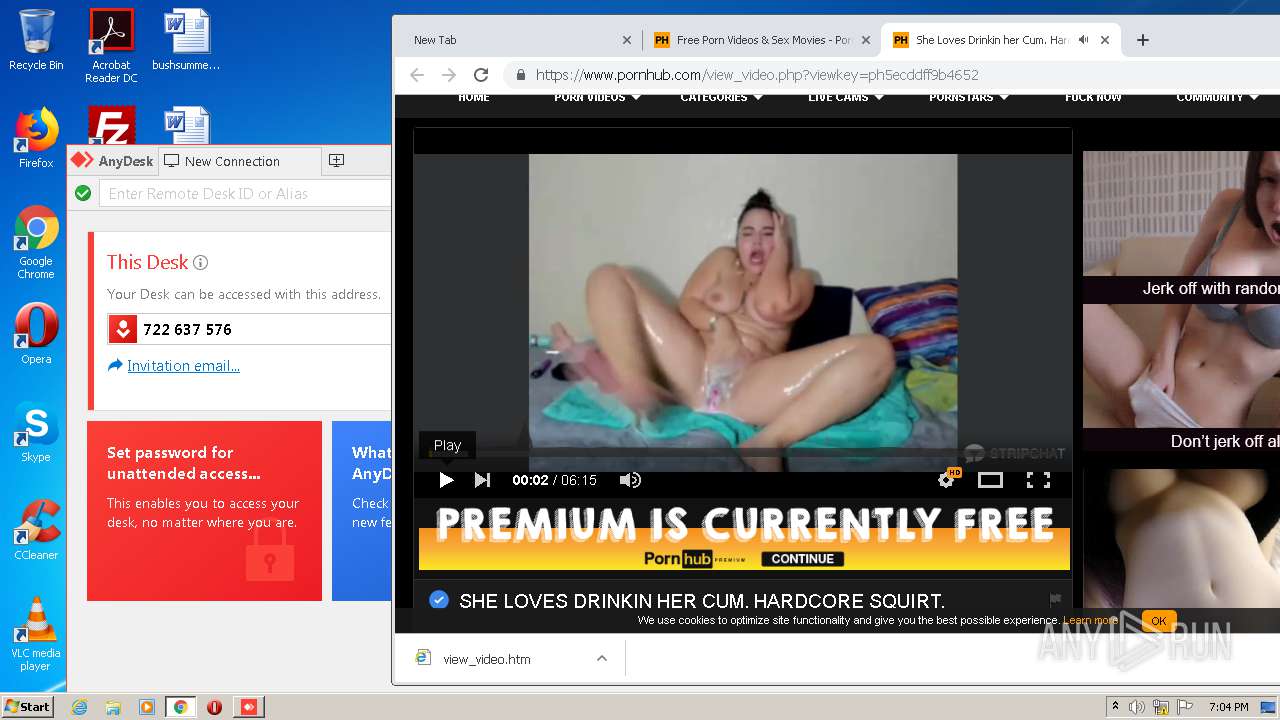
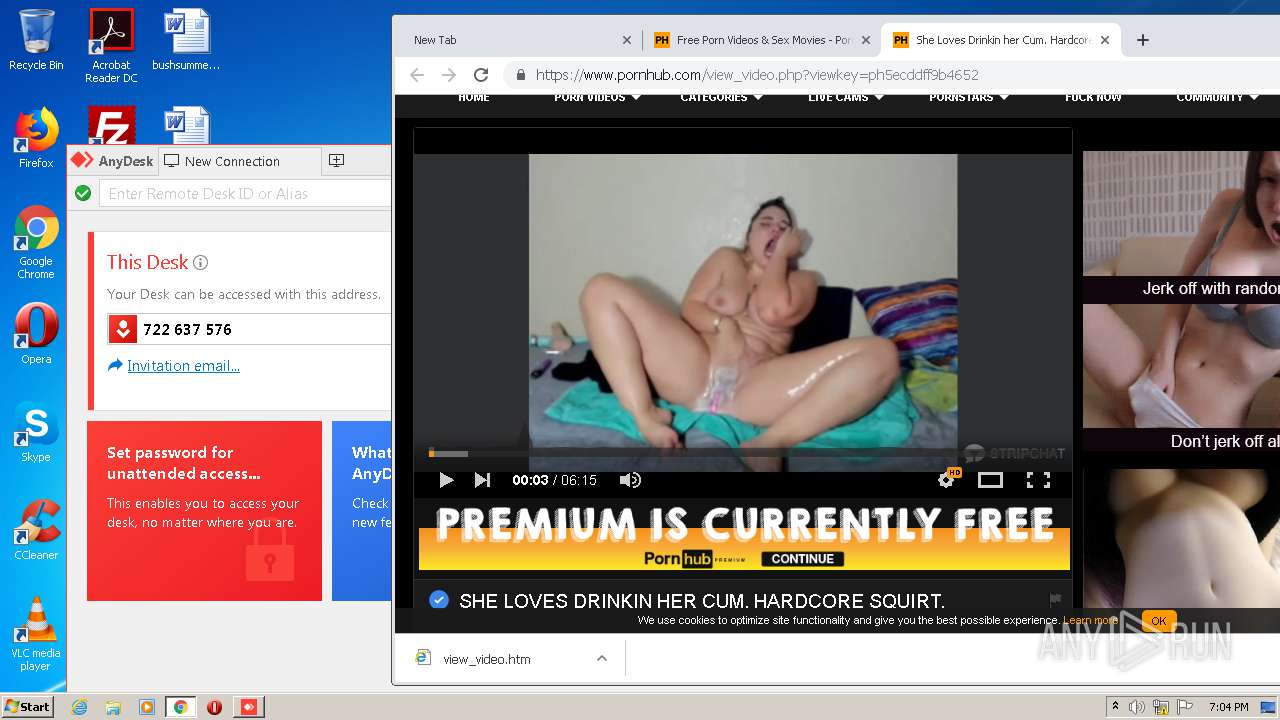
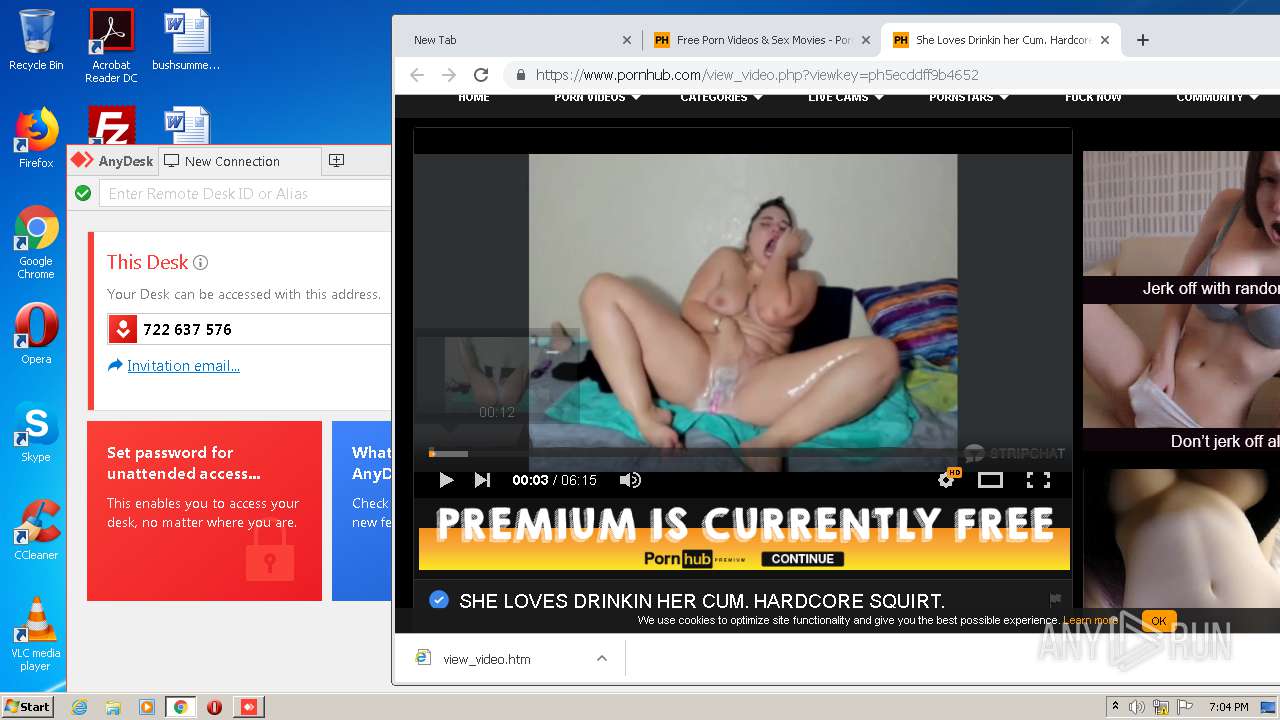
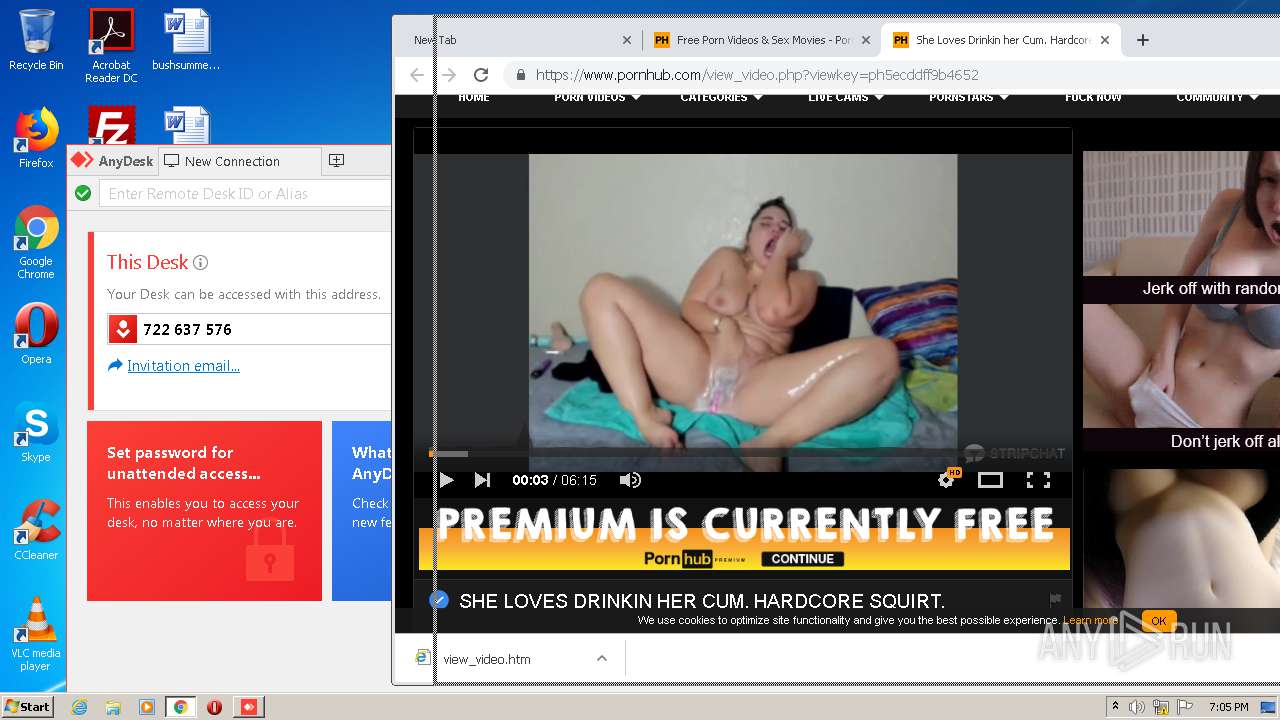
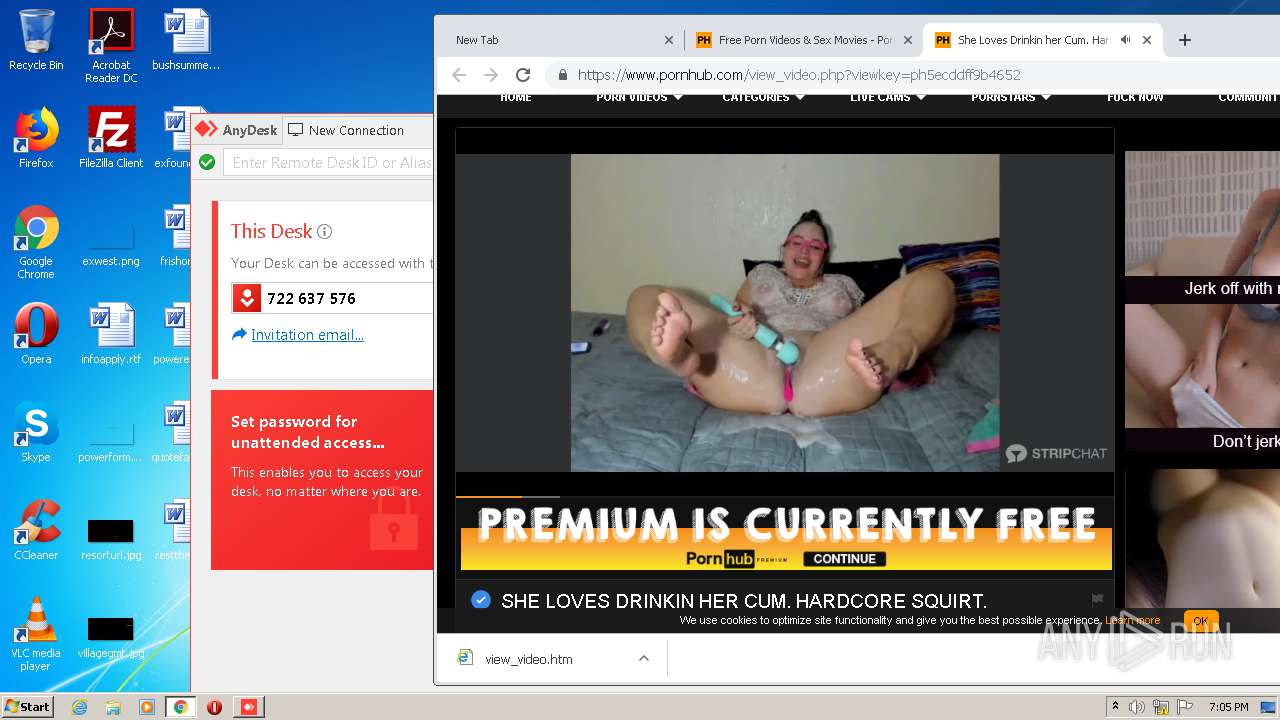
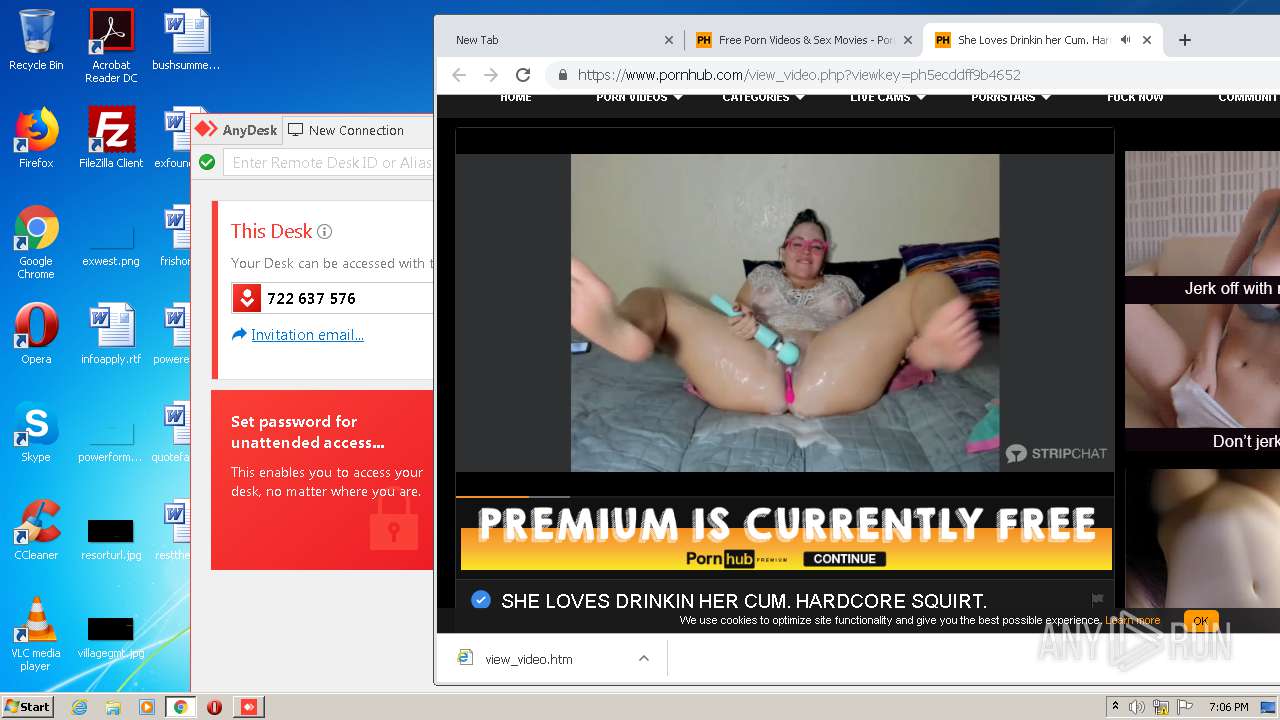
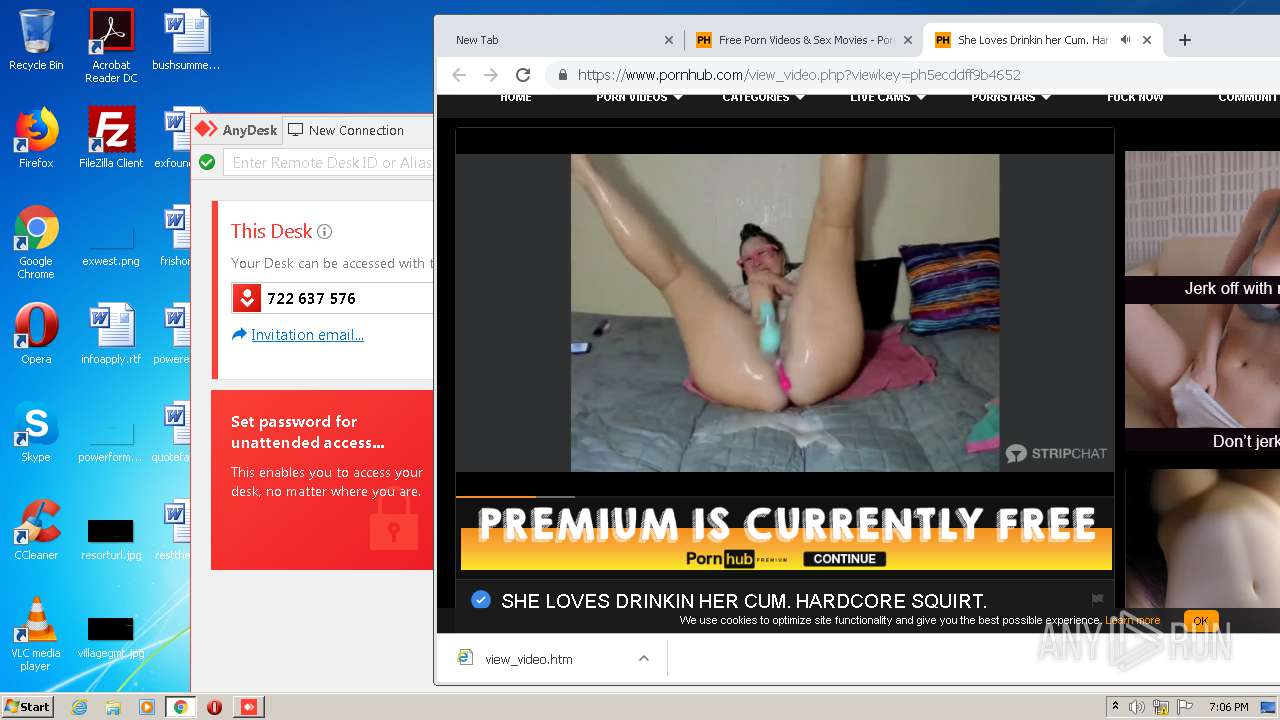
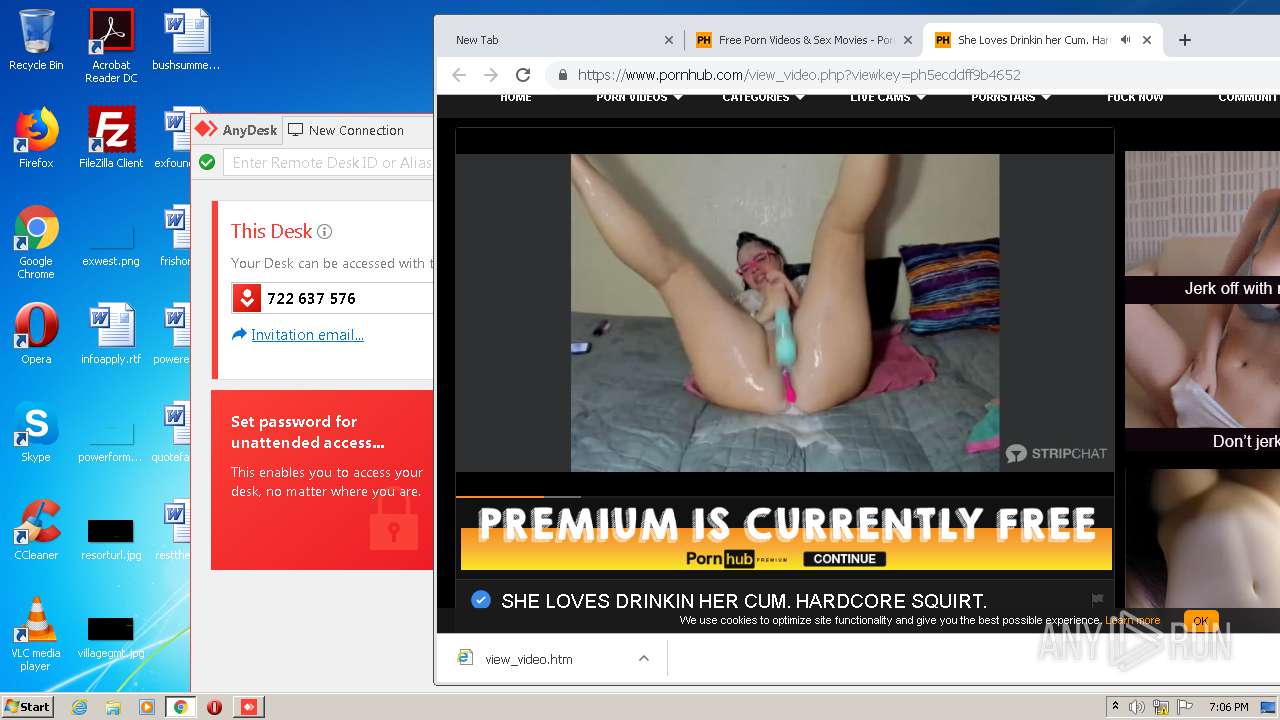
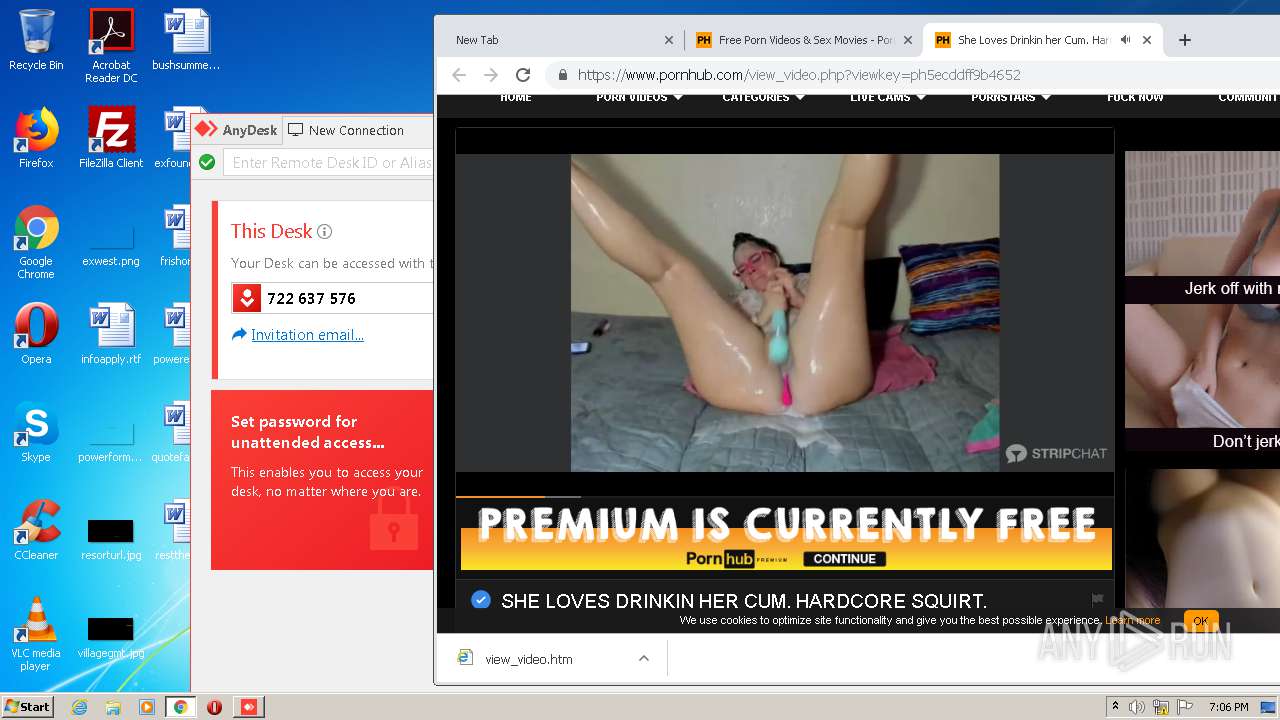
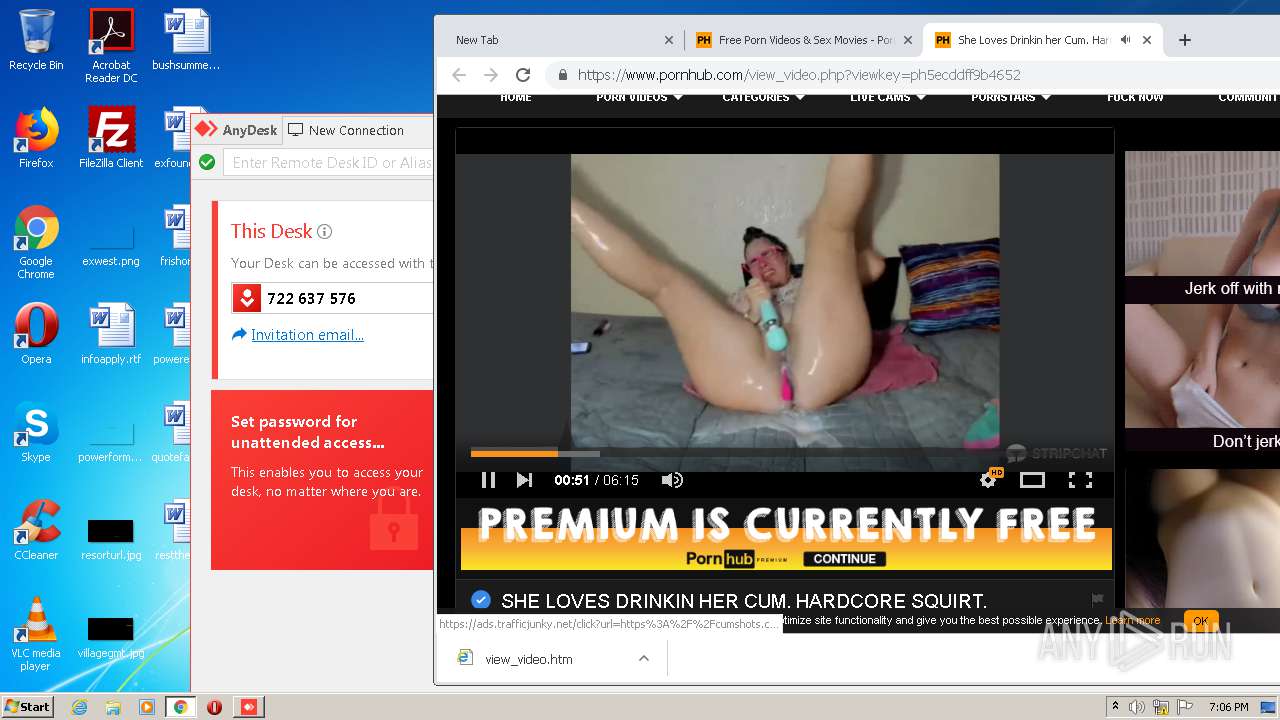
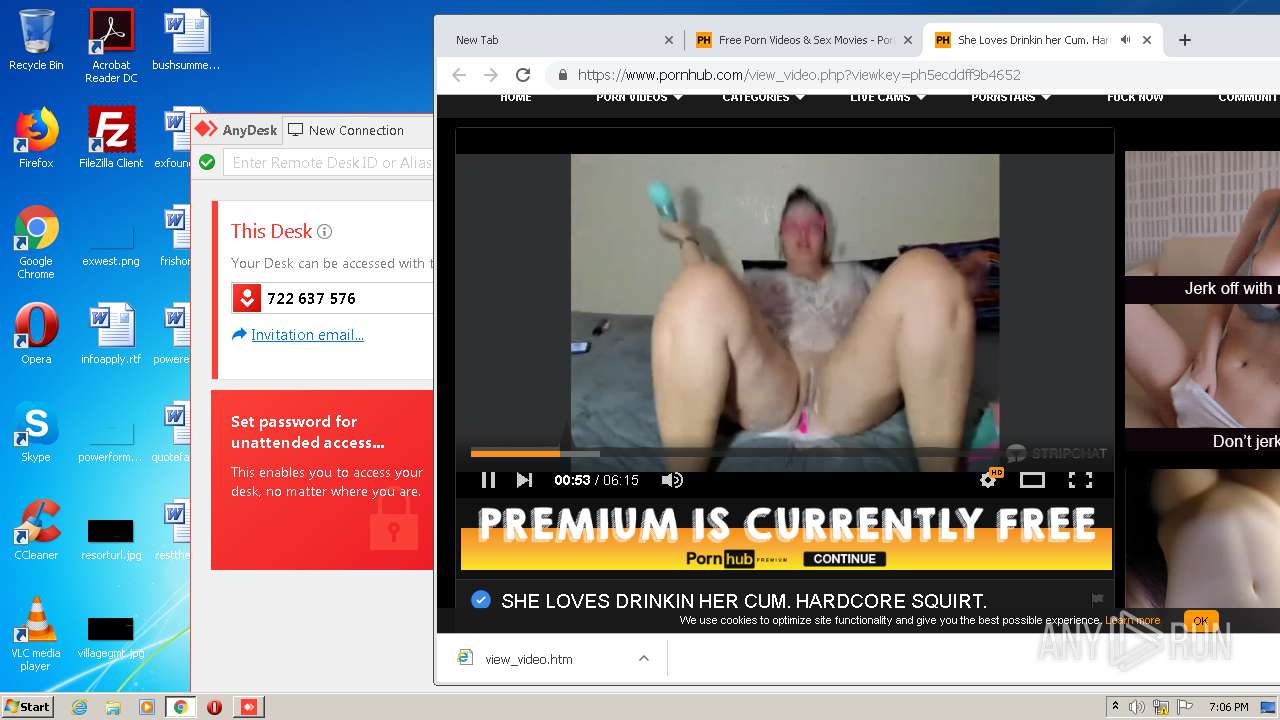
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15223639054716356082 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14565965811266510708 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11333358172419518902 --mojo-platform-channel-handle=1568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14137318328861108324 --mojo-platform-channel-handle=3980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13622154184158799738 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9403234485018692699 --mojo-platform-channel-handle=3144 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=856070184811513344 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12998451164851577992 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7877892109772910403 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,13162365675056076386,14510279206166909581,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10808272459455441998 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 889
Read events
1 778
Write events
106
Delete events
5
Modification events
| (PID) Process: | (2324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2332-13238964186753500 |
Value: 259 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
180
Text files
328
Unknown types
84
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PF0ERBQB7IMAHT9ZEQ0K.temp | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F09FEDB-91C.pma | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f1f9afd1-fe39-4a25-8f89-dd59d427ae1e.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2428 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\system.conf | text | |
MD5:— | SHA256:— | |||
| 2184 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\75fdacd8330bac18.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF115948.TMP | text | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
135
DNS requests
70
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
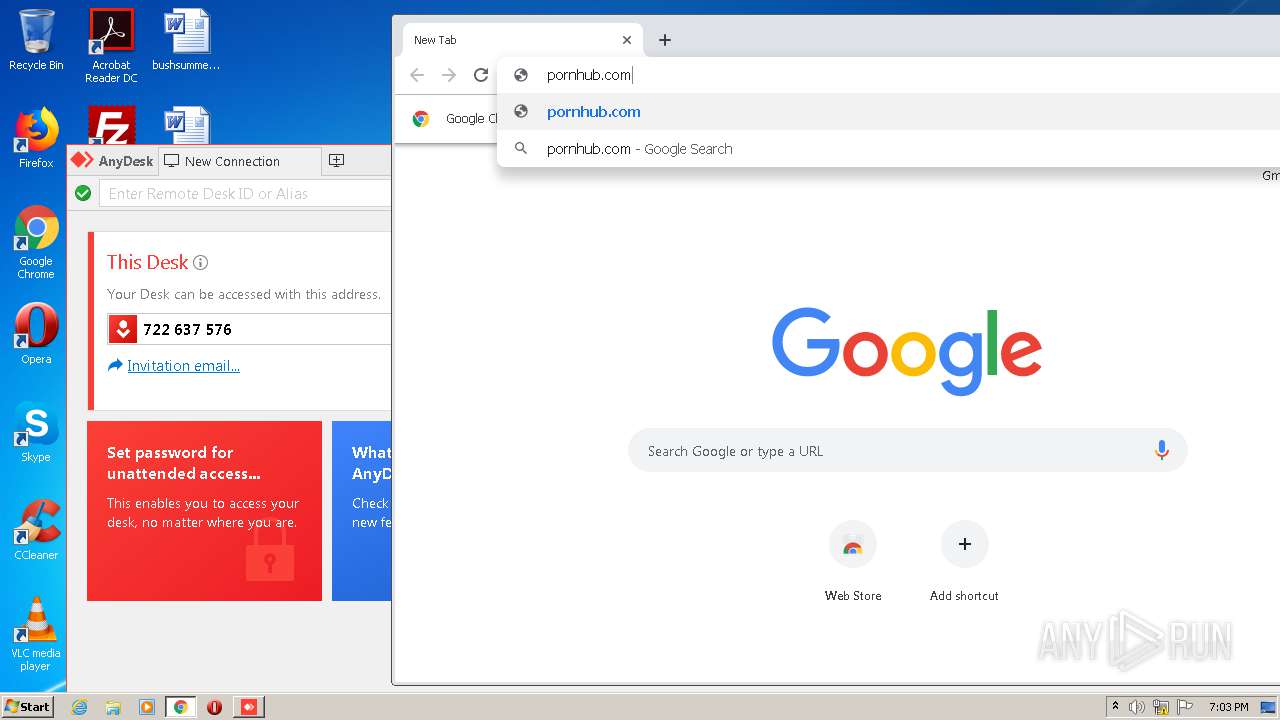
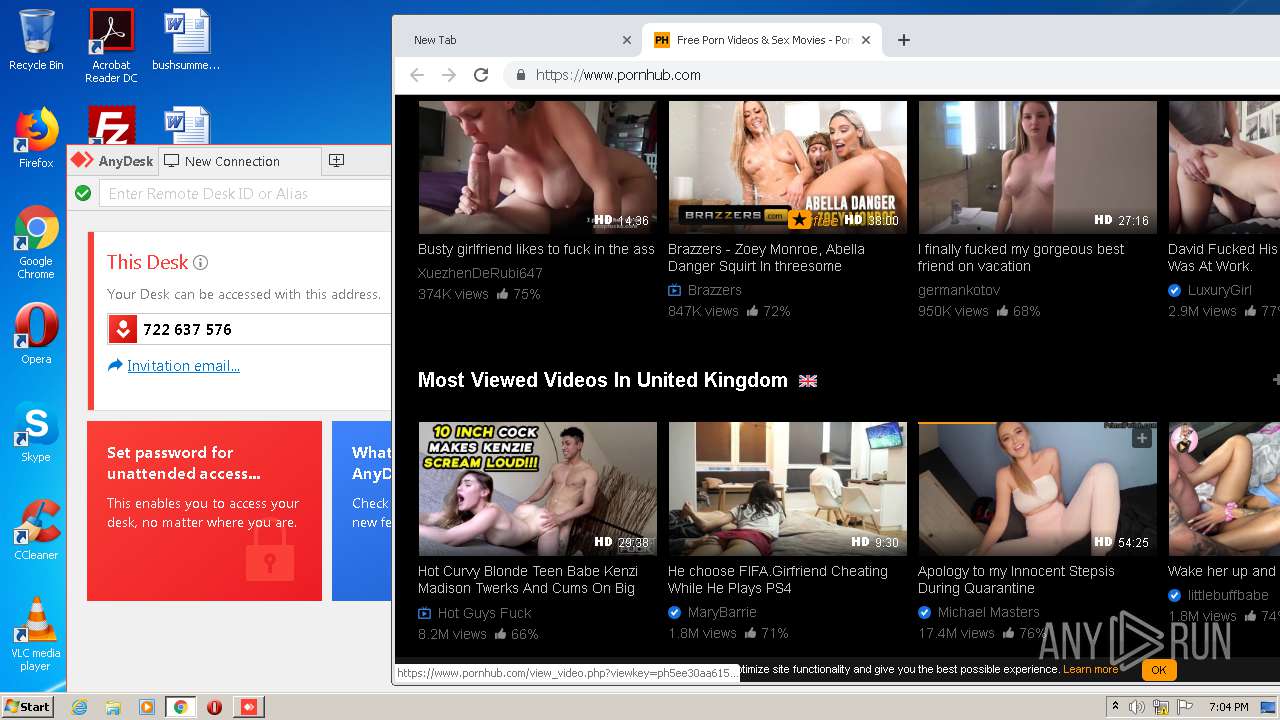
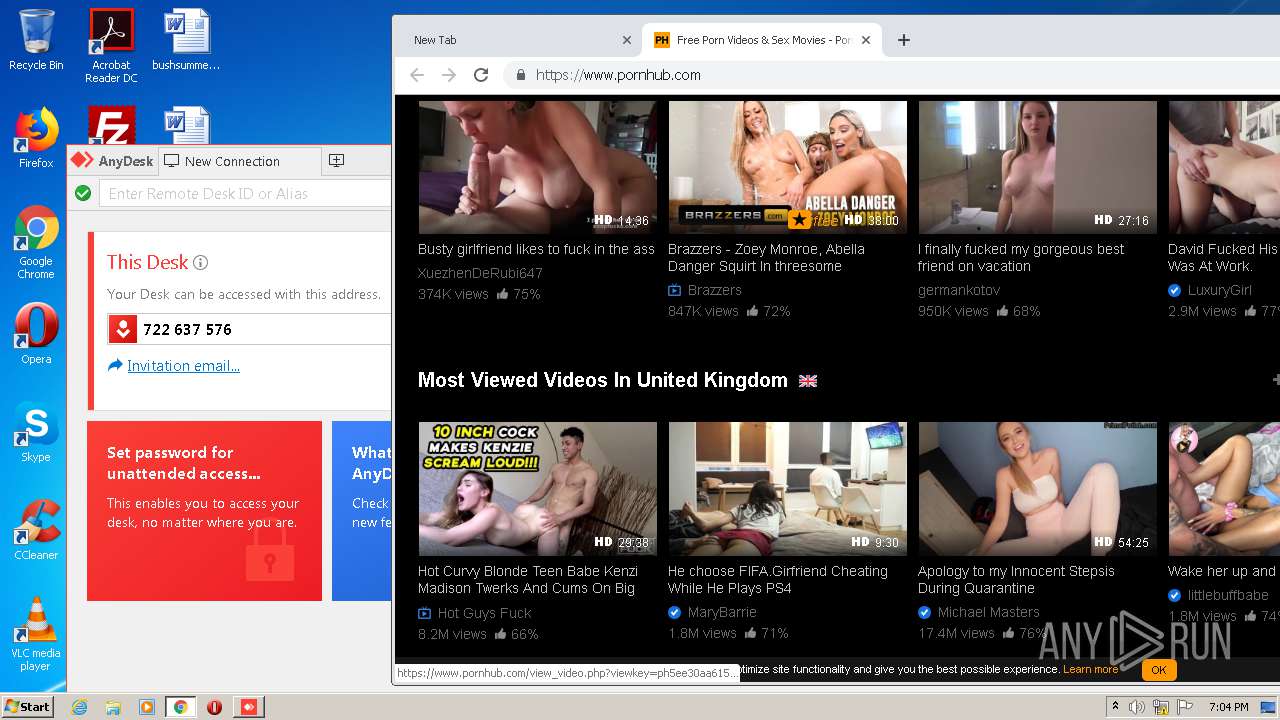
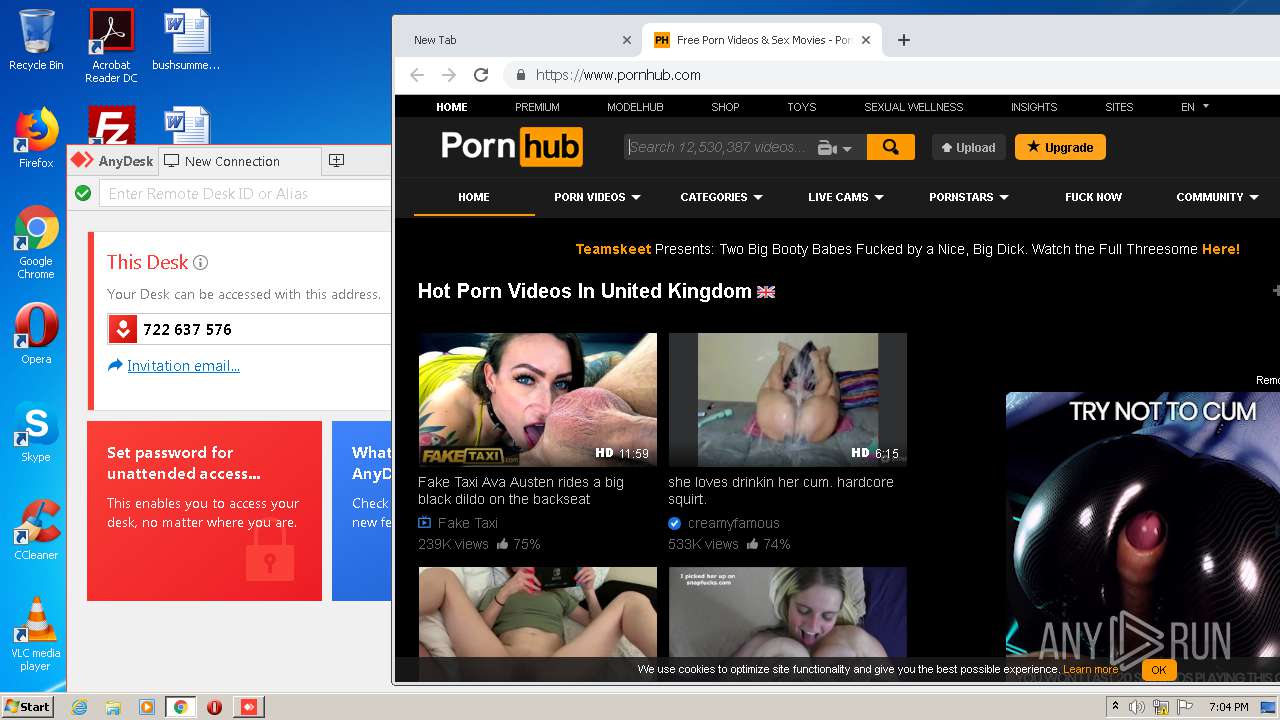
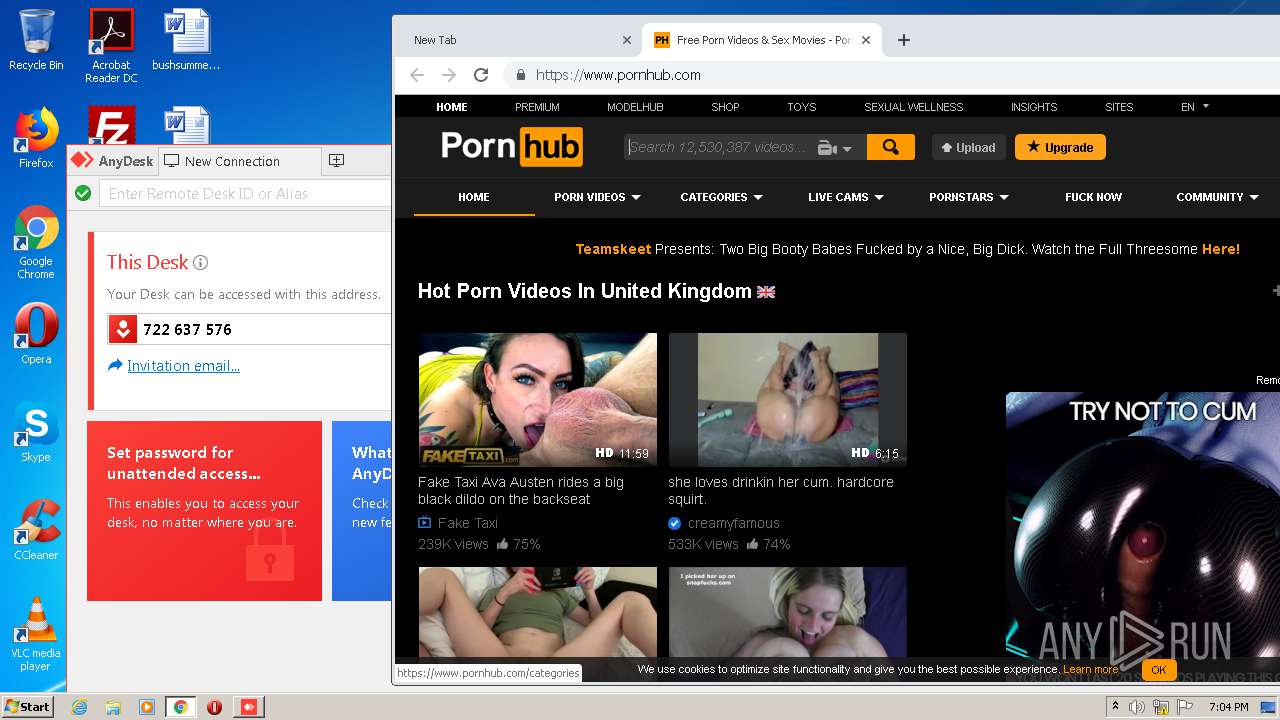
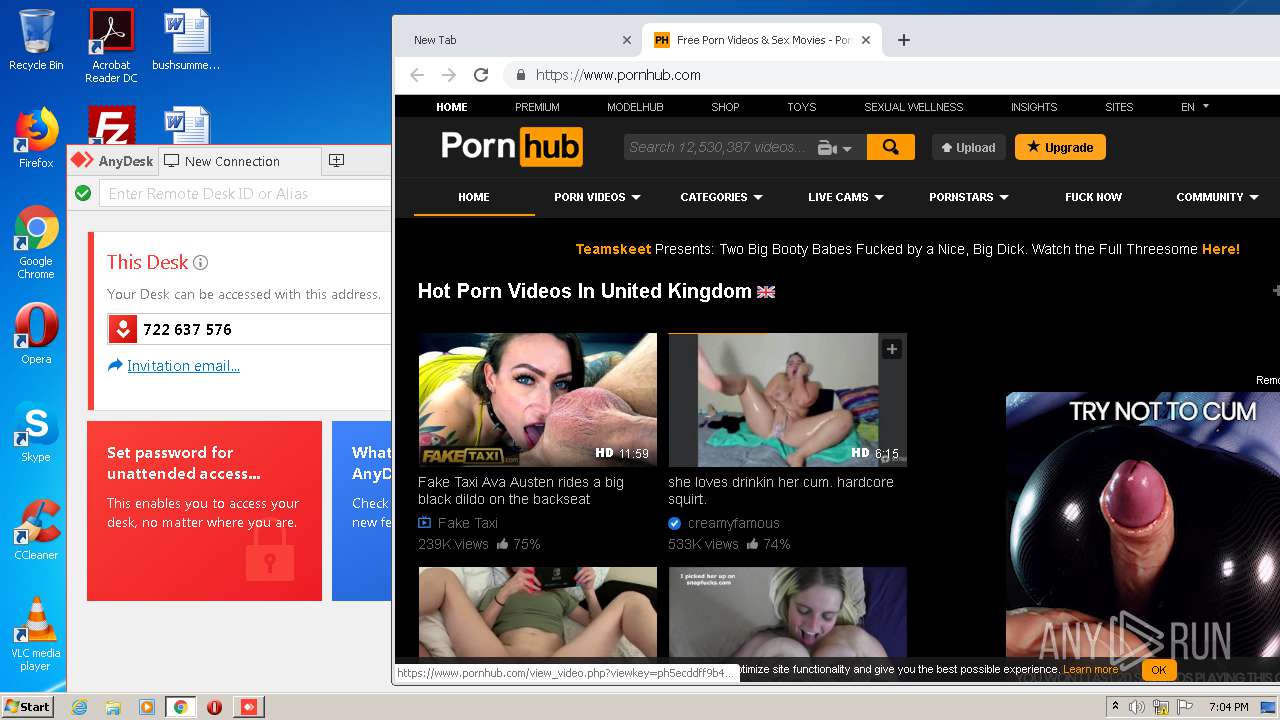
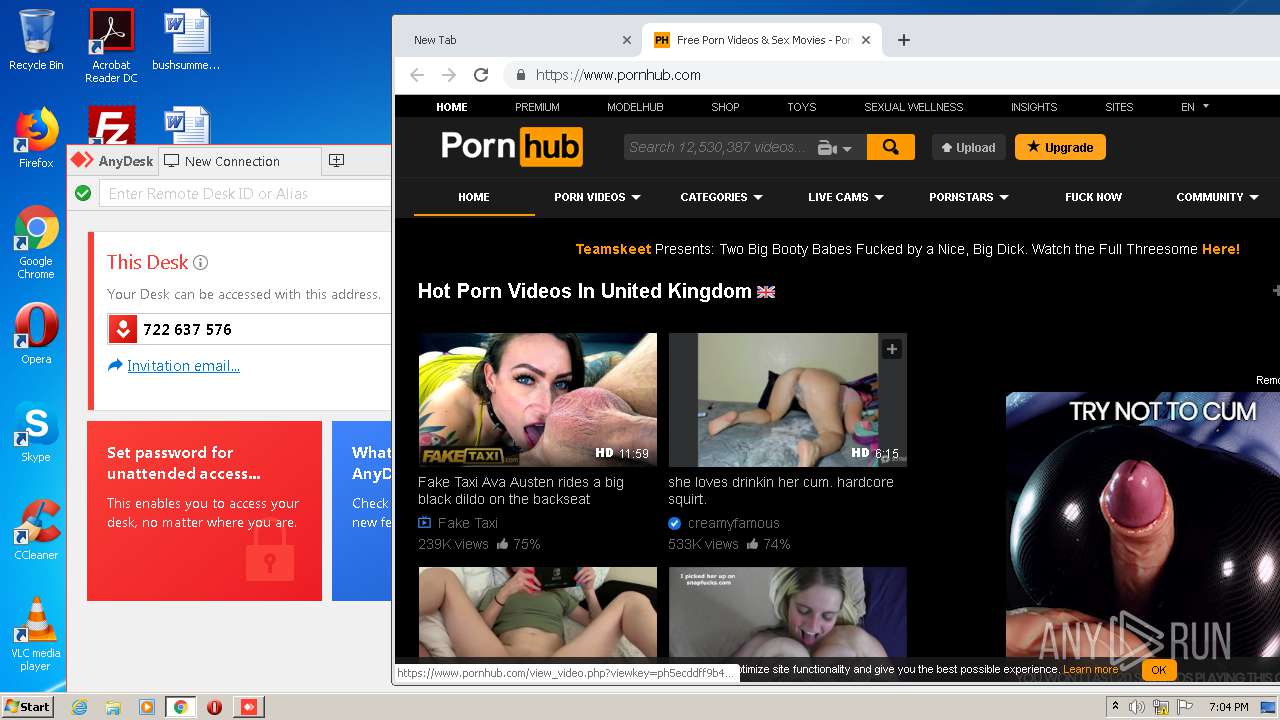
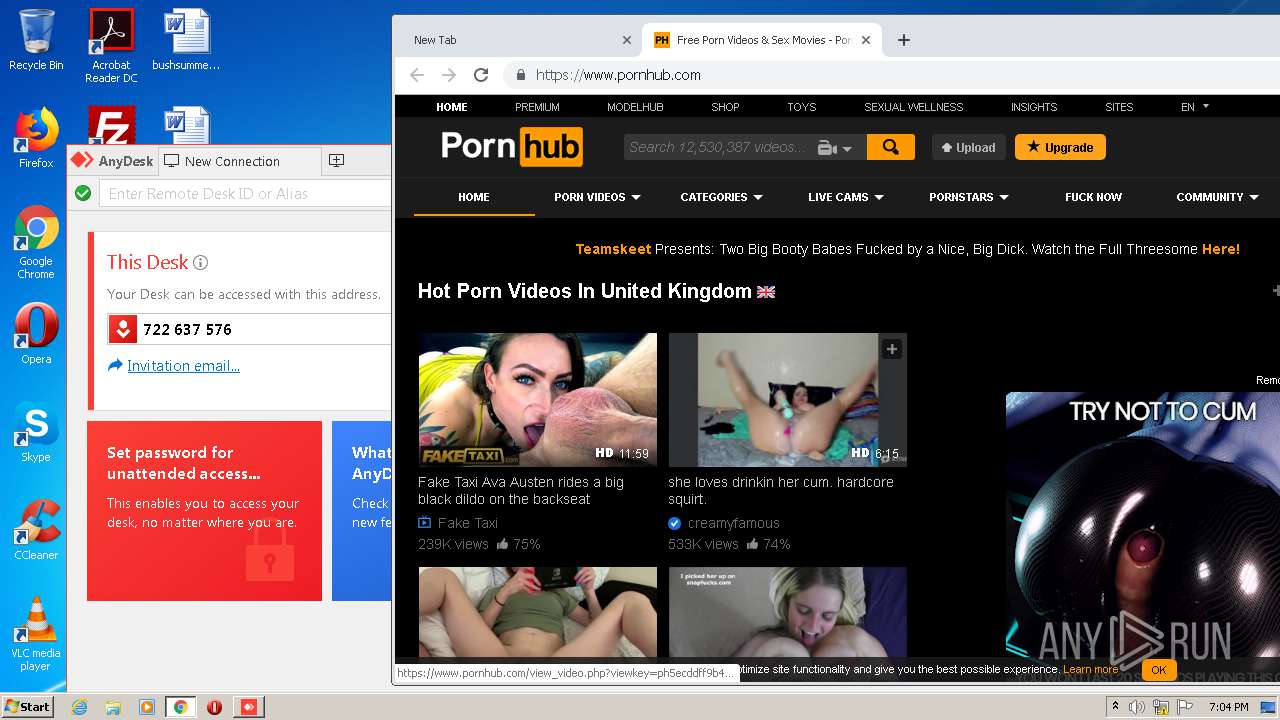
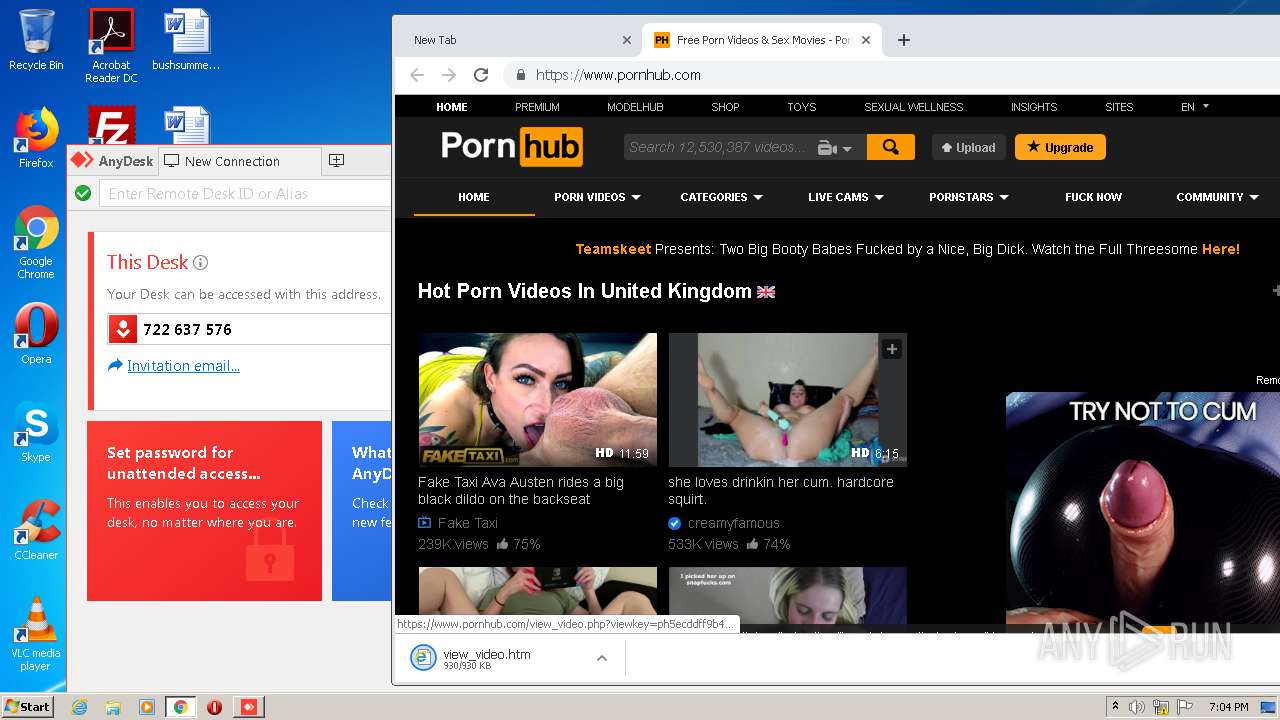
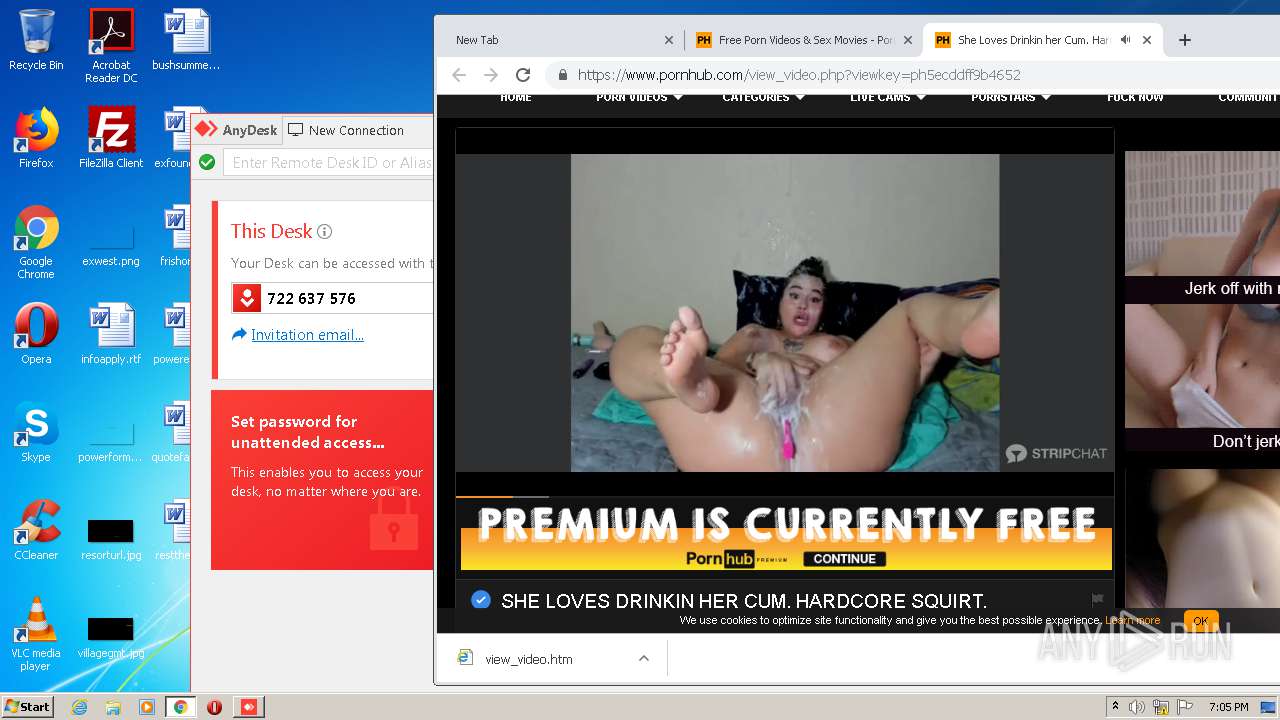
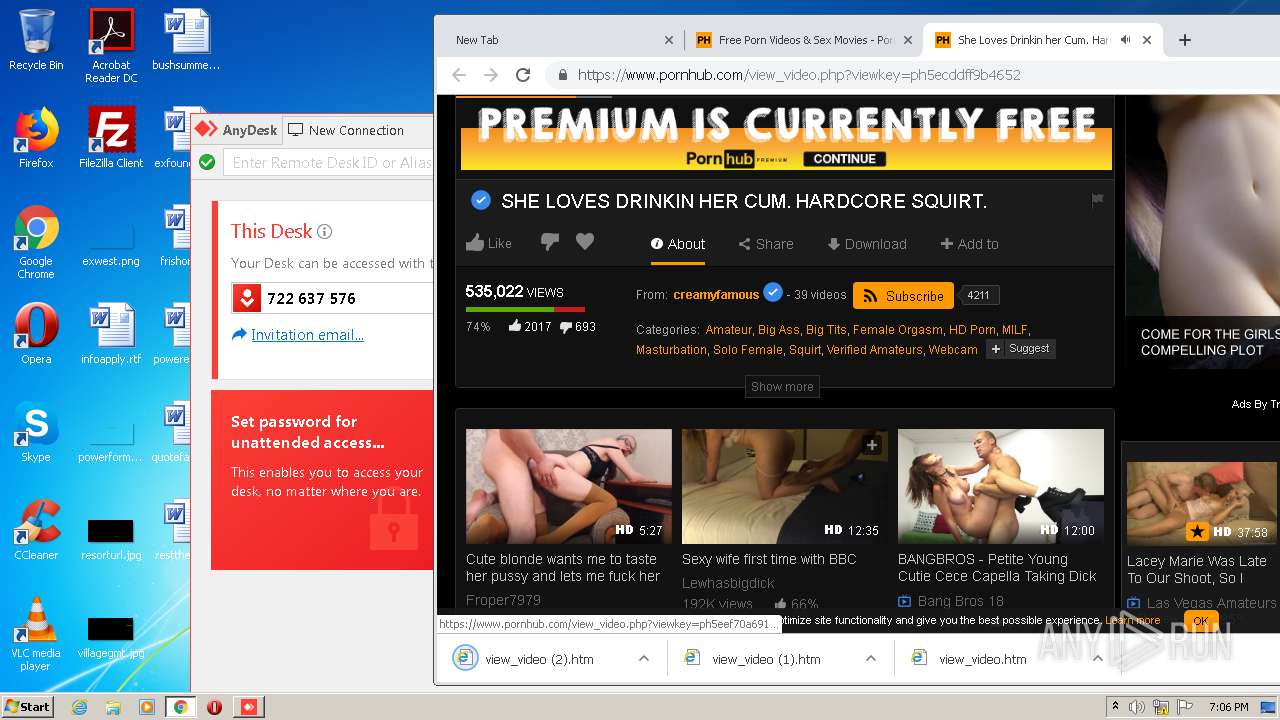
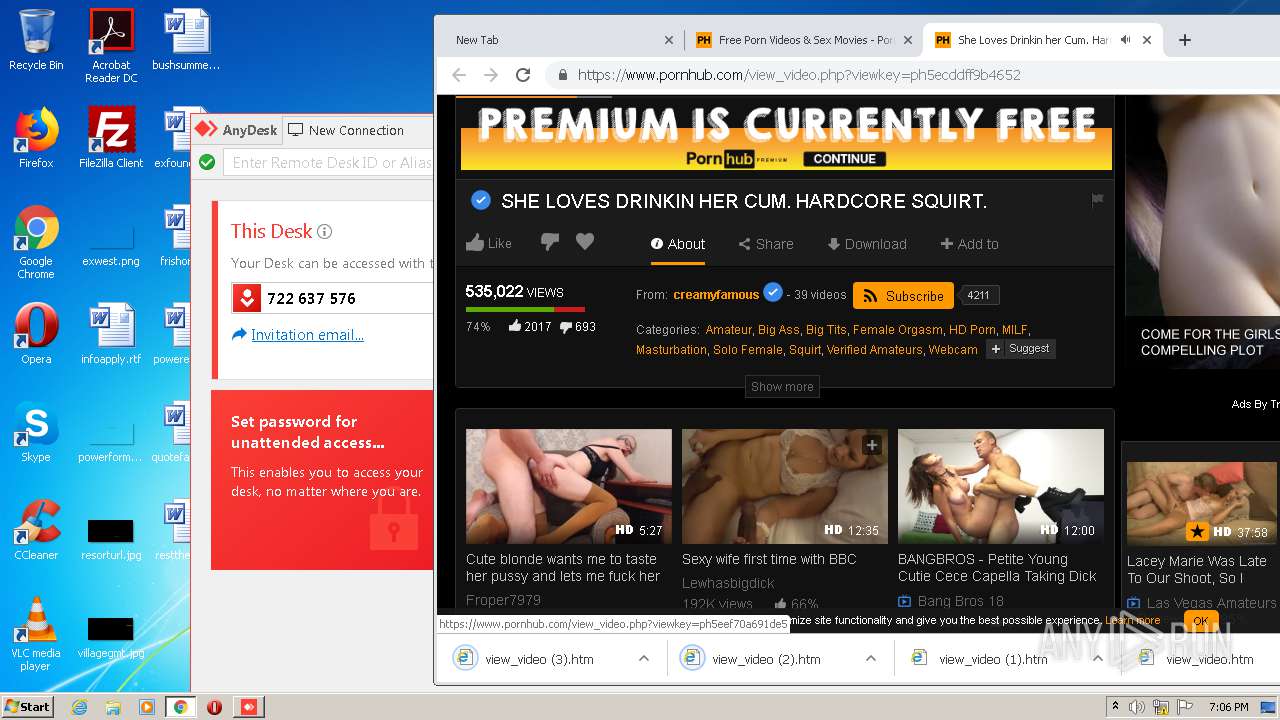
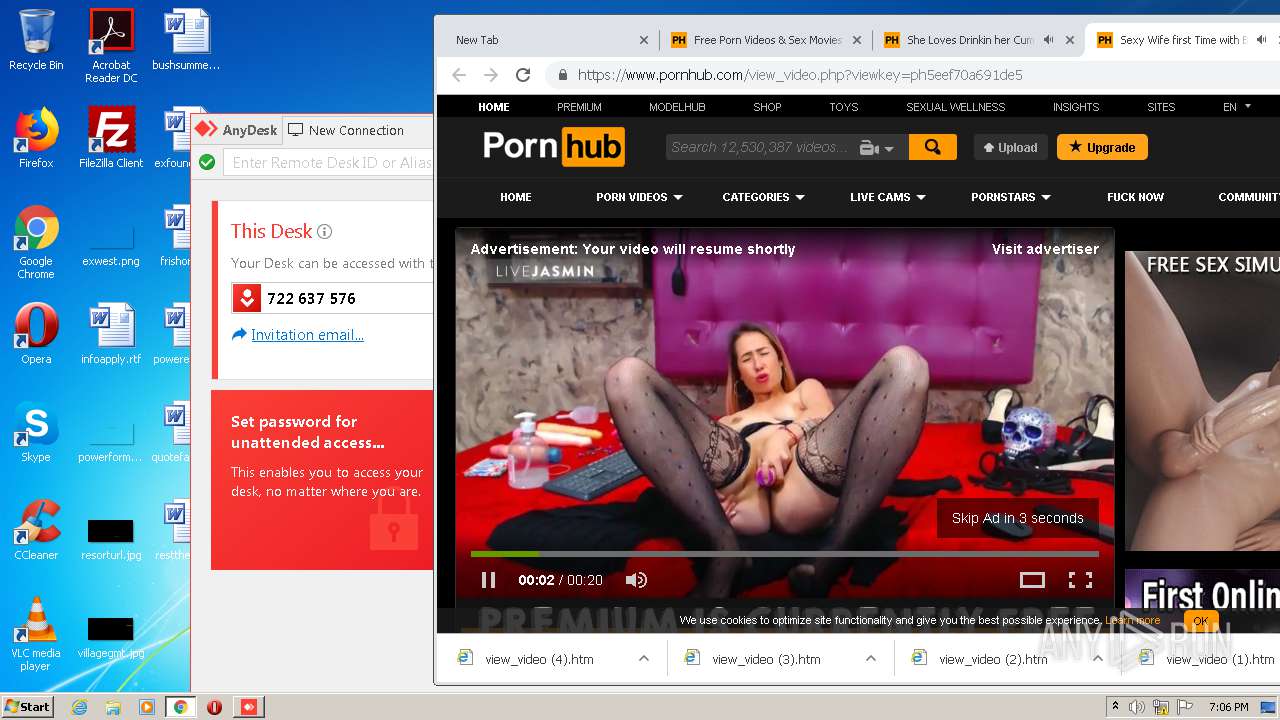
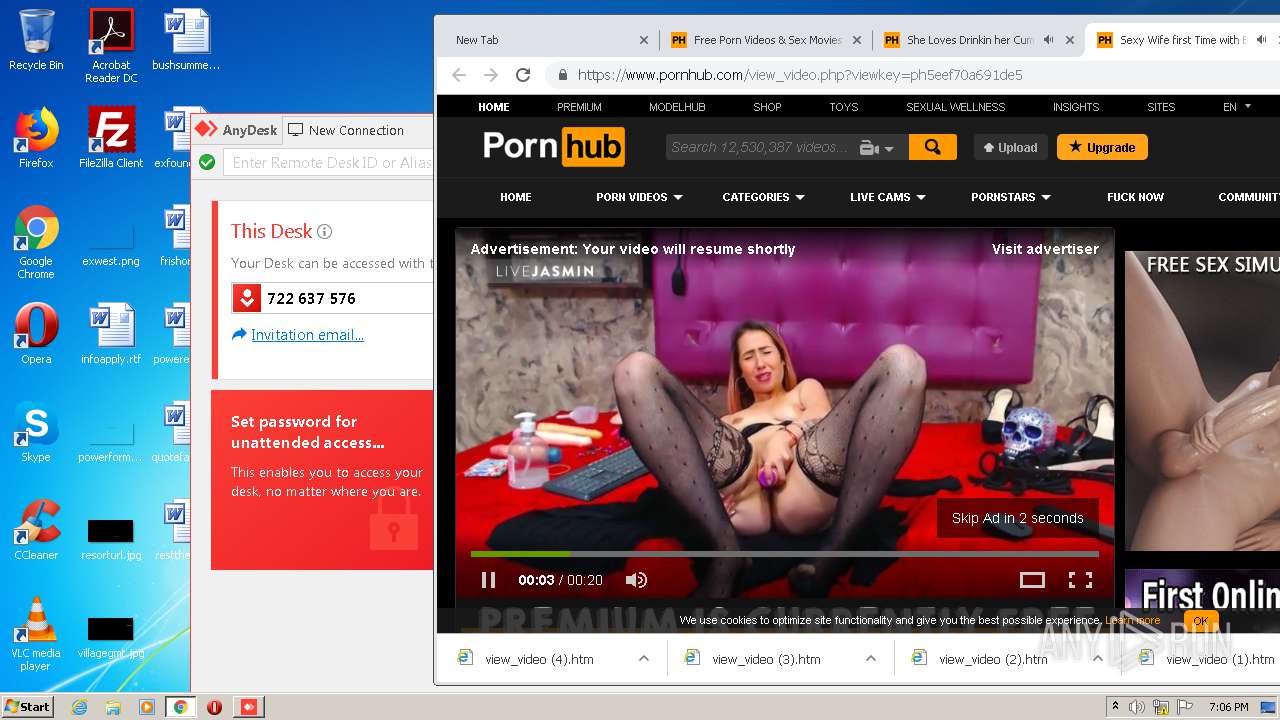
852 | chrome.exe | GET | 301 | 66.254.114.41:80 | http://pornhub.com/ | US | — | — | whitelisted |
2428 | AnyDesk.exe | POST | 204 | 52.17.57.157:80 | http://api.playanext.com/httpapi | IE | — | — | whitelisted |
852 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
852 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
852 | chrome.exe | GET | 200 | 173.194.129.201:80 | http://r4---sn-aigzrn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.217.117.39&mm=28&mn=sn-aigzrn7s&ms=nvh&mt=1594490485&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
852 | chrome.exe | GET | 200 | 74.125.4.216:80 | http://r2---sn-aigzrney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.39&mm=28&mn=sn-aigzrney&ms=nvh&mt=1594490485&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
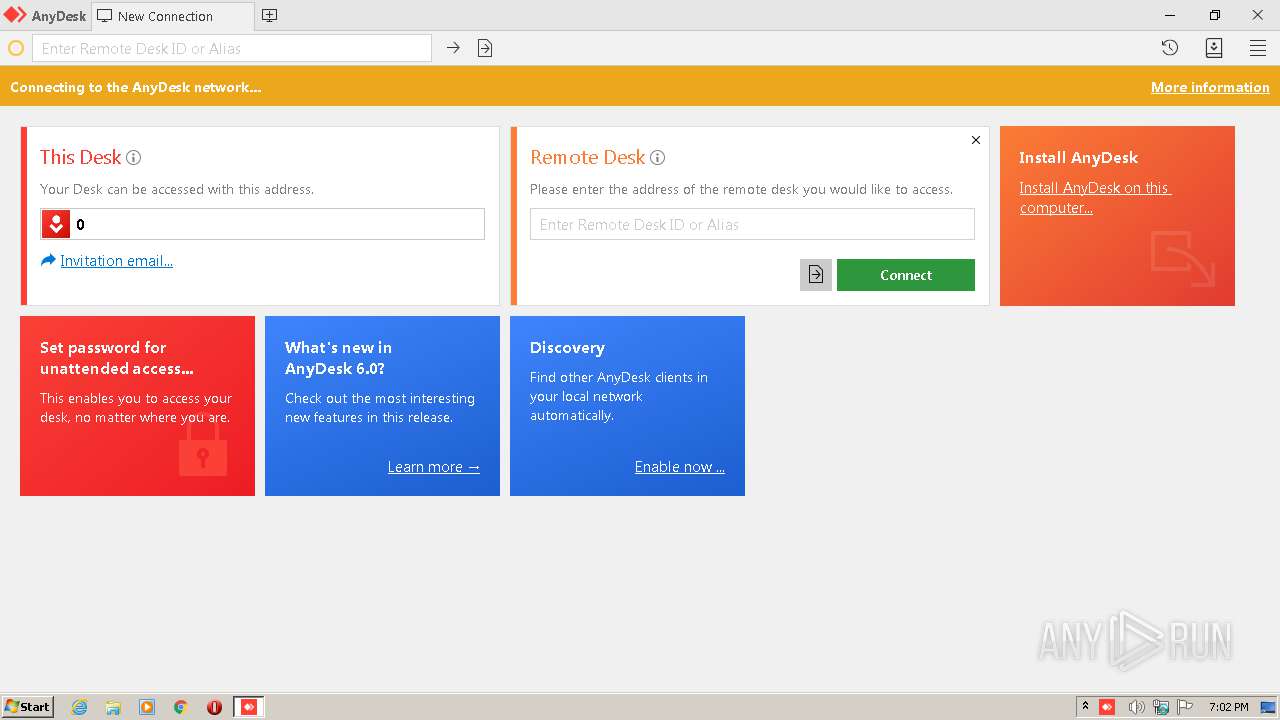
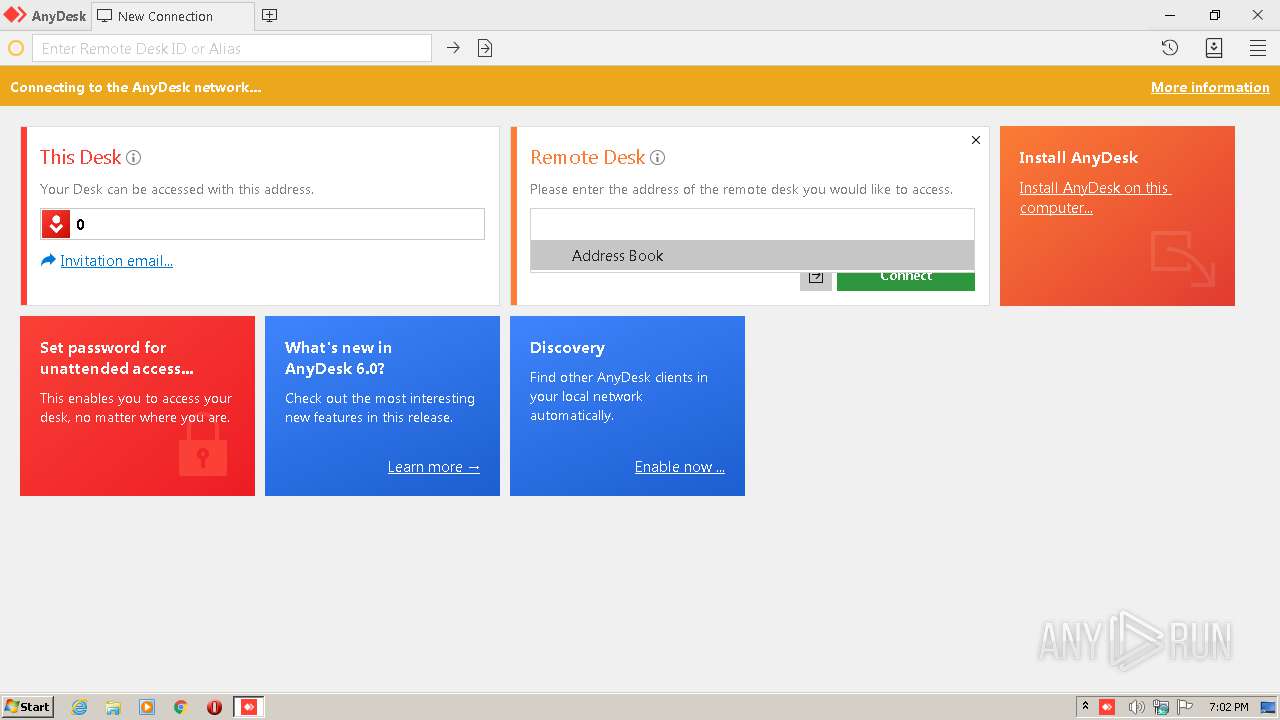
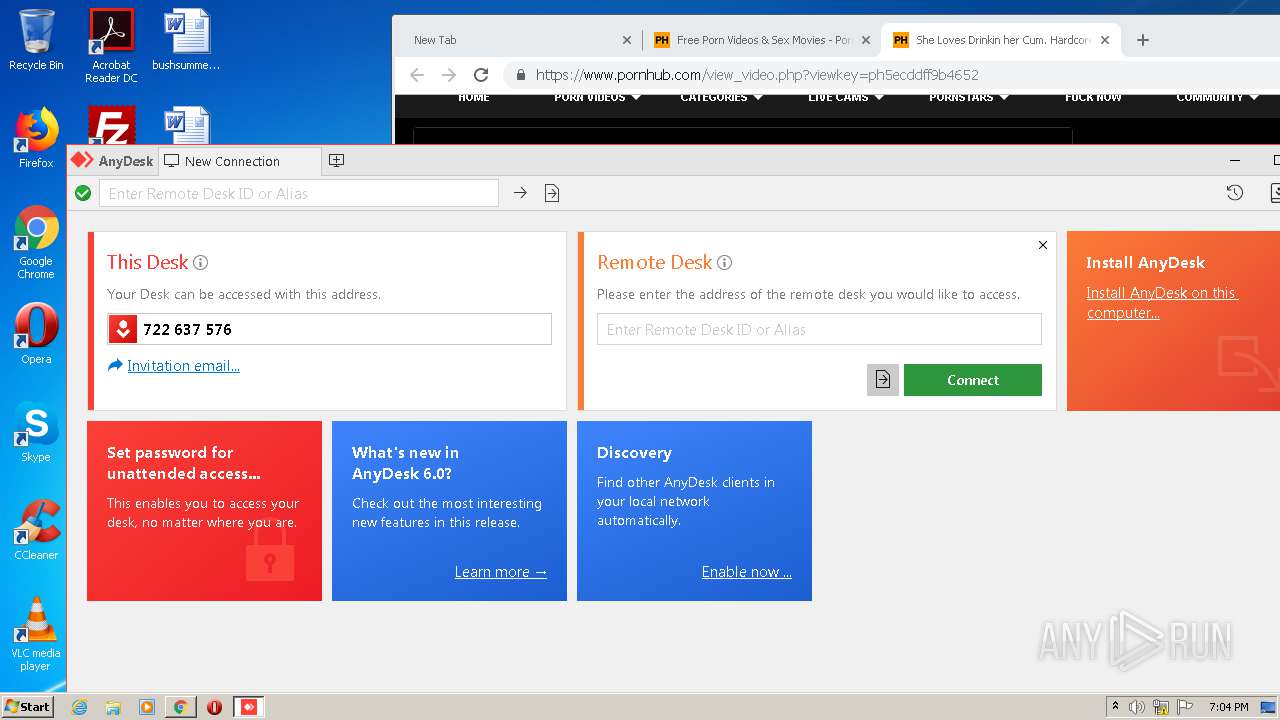
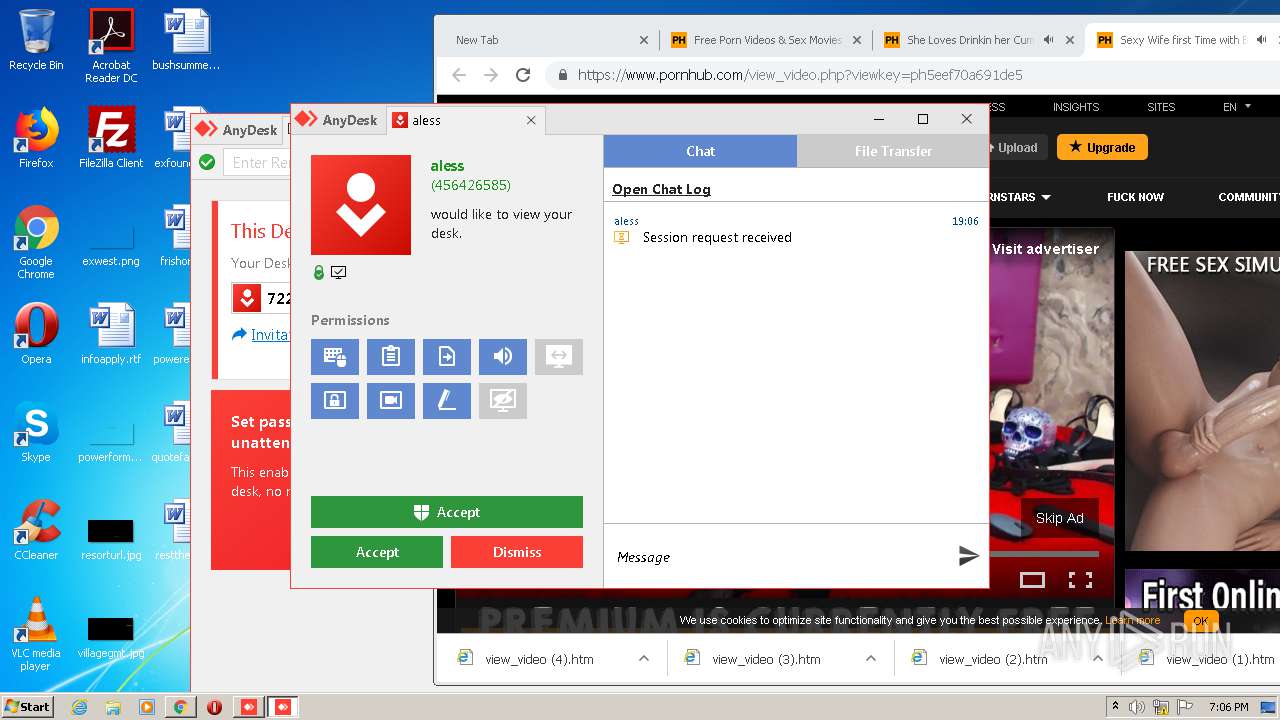
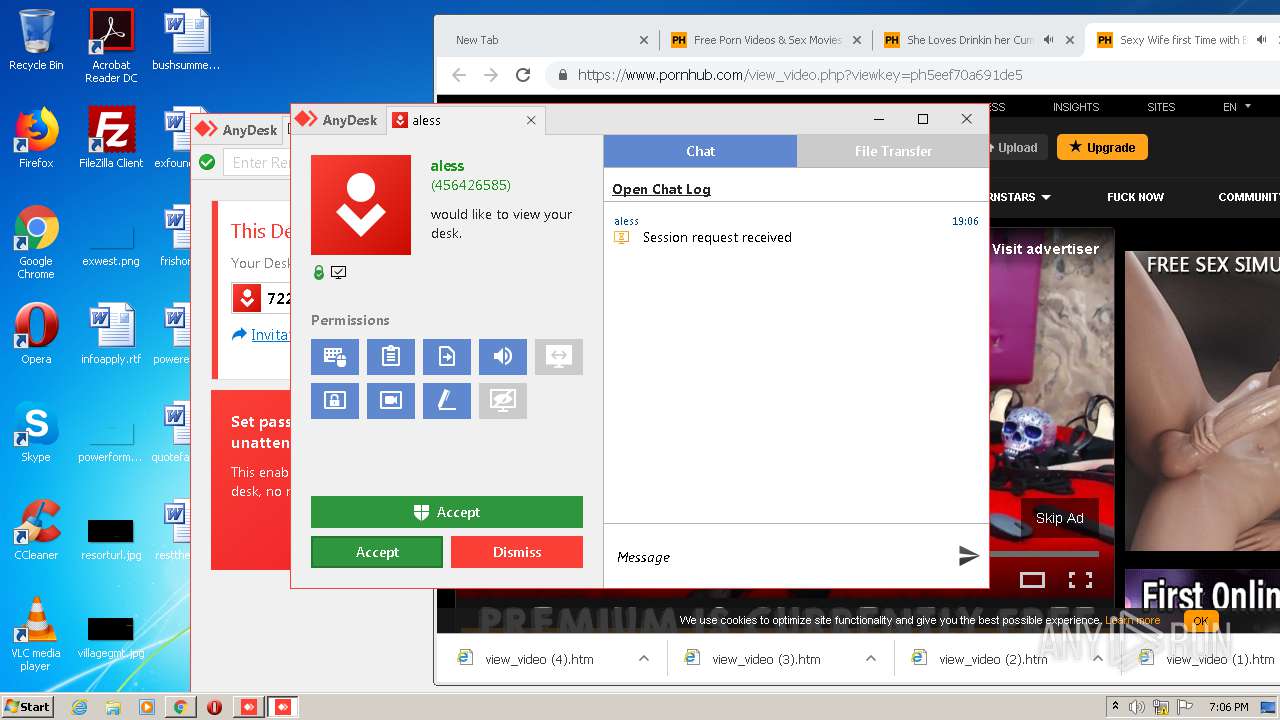
2428 | AnyDesk.exe | 92.223.88.41:443 | boot-01.net.anydesk.com | G-Core Labs S.A. | LU | suspicious |
2428 | AnyDesk.exe | 92.223.88.41:80 | boot-01.net.anydesk.com | G-Core Labs S.A. | LU | suspicious |
2428 | AnyDesk.exe | 136.243.50.29:80 | relay-011e863f.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
2428 | AnyDesk.exe | 116.202.229.59:80 | relay-033a5347.net.anydesk.com | 334,Udyog Vihar | IN | unknown |
2428 | AnyDesk.exe | 52.17.57.157:80 | api.playanext.com | Amazon.com, Inc. | IE | suspicious |
852 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
852 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 172.217.18.163:443 | www.google.ae | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
boot-01.net.anydesk.com |
| whitelisted |
relay-011e863f.net.anydesk.com |
| unknown |
relay-033a5347.net.anydesk.com |
| unknown |
api.playanext.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2428 | AnyDesk.exe | Potential Corporate Privacy Violation | ET POLICY SSL/TLS Certificate Observed (AnyDesk Remote Desktop Software) |
2428 | AnyDesk.exe | Potential Corporate Privacy Violation | ET USER_AGENTS AnyDesk Remote Desktop Software User-Agent |
852 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
852 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
852 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
852 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |