| File name: | Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.uue |
| Full analysis: | https://app.any.run/tasks/0ffd8624-5932-47dd-b7b8-3e4fd7e43a1e |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 06:51:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
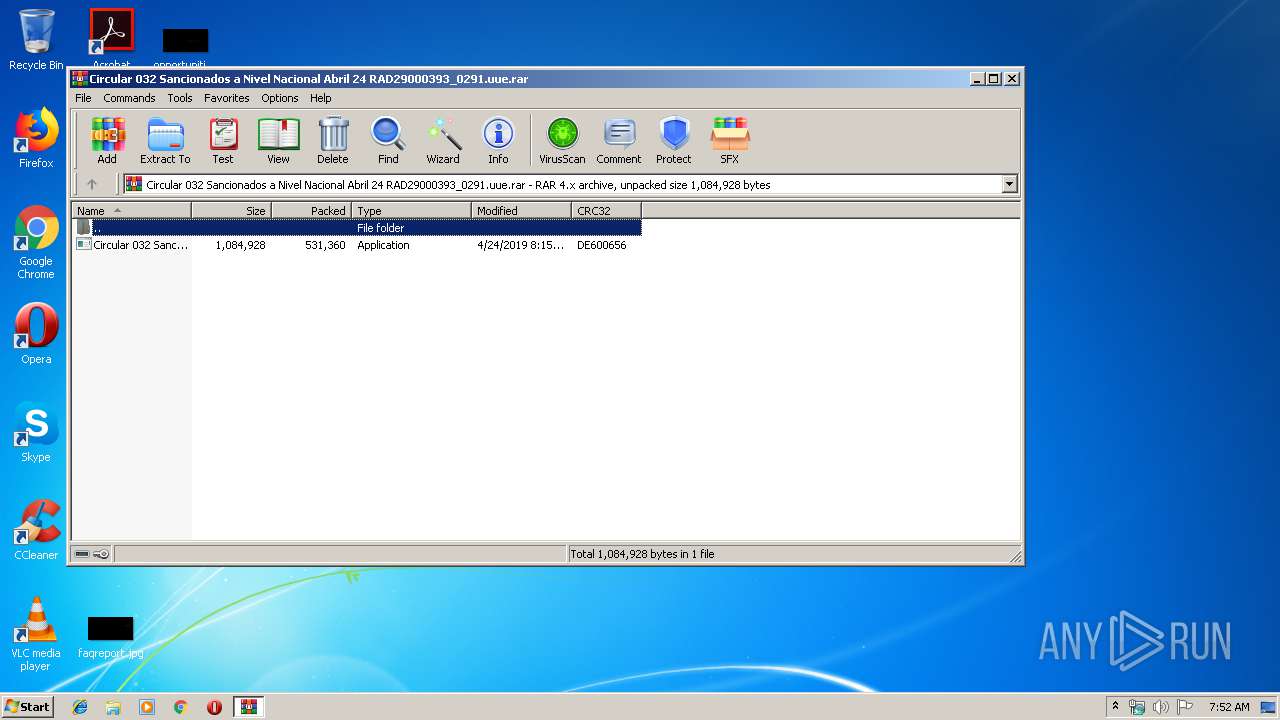
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 12DD8ED13DDE7594D9551A655BAFD169 |
| SHA1: | A8F5211F71DC4B8170DCC40902B0D91A5AF48C92 |
| SHA256: | DD766A3C69BC7E5B384540140EC3F383797AF109D07EA00F9EBFE173CB3863AE |
| SSDEEP: | 12288:RpK1Cc55crUYZH/02h5YEFJjNBbeQ1W51kOfQK222:0Y1c2hVPeQ181pf6 |
MALICIOUS
Application was dropped or rewritten from another process
- Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe (PID: 2612)
Writes to a start menu file
- Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe (PID: 2612)
Changes the autorun value in the registry
- RegAsm.exe (PID: 3692)
SUSPICIOUS
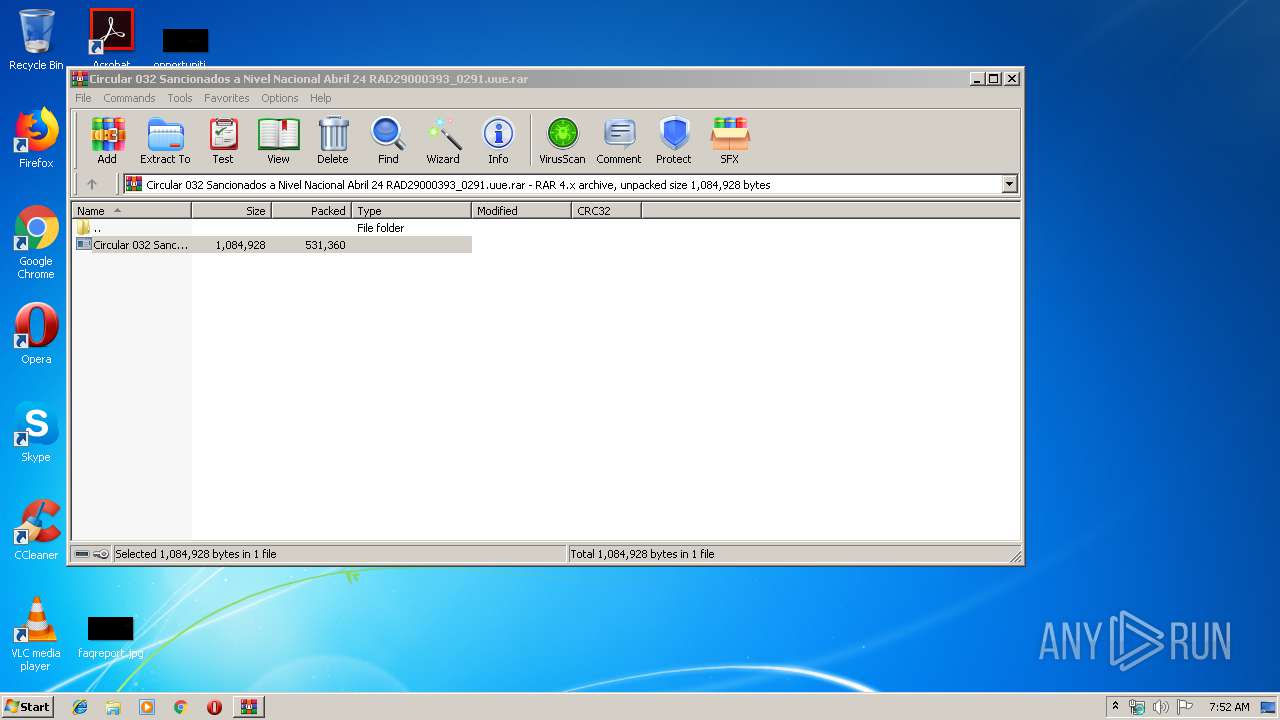
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2952)
- Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe (PID: 2612)
Creates files in the user directory
- Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe (PID: 2612)
INFO
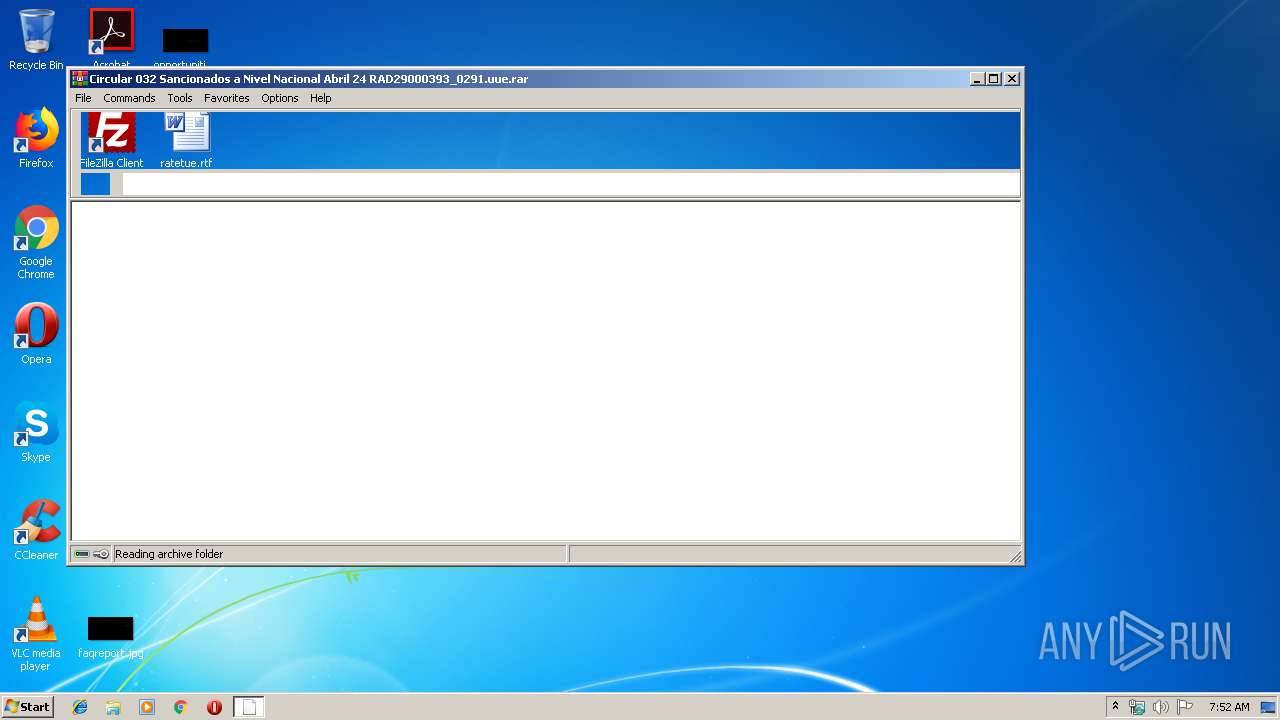
Manual execution by user
- Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 531457 |
|---|---|
| UncompressedSize: | 1084928 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:04:24 08:15:28 |
| PackingMethod: | Normal |
| ArchivedFileName: | Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
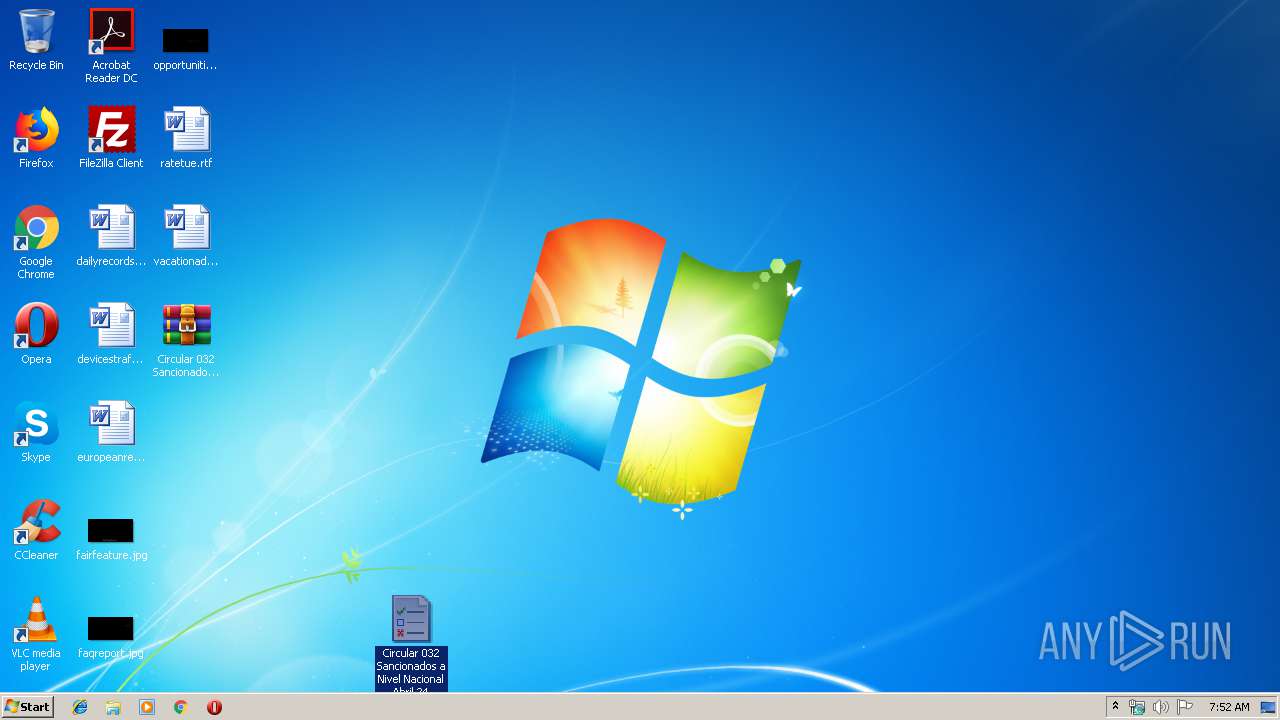
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2612 | "C:\Users\admin\Desktop\Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe" | C:\Users\admin\Desktop\Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe | explorer.exe | ||||||||||||
User: admin Company: hvix64 Integrity Level: MEDIUM Description: RtDCpl64 Exit code: 0 Version: 503.806.715.494 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.uue.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3692 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
640
Read events
329
Write events
311
Delete events
0
Modification events
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.uue.rar | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2612 | Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CredentialUIBroker.url | text | |
MD5:— | SHA256:— | |||
| 2952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2952.24295\Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe | executable | |
MD5:— | SHA256:— | |||
| 2612 | Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe | C:\Users\admin\AppData\Roaming\whoami\CredentialUIBroker.vbs | text | |
MD5:— | SHA256:— | |||
| 2612 | Circular 032 Sancionados a Nivel Nacional Abril 24 RAD29000393_0291.exe | C:\Users\admin\AppData\Roaming\whoami\CompMgmtLauncher.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3692 | RegAsm.exe | 186.85.86.196:1407 | hospisanjose.publicvm.com | Telmex Colombia S.A. | CO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hospisanjose.publicvm.com |
| malicious |
dns.msftncsi.com |
| shared |