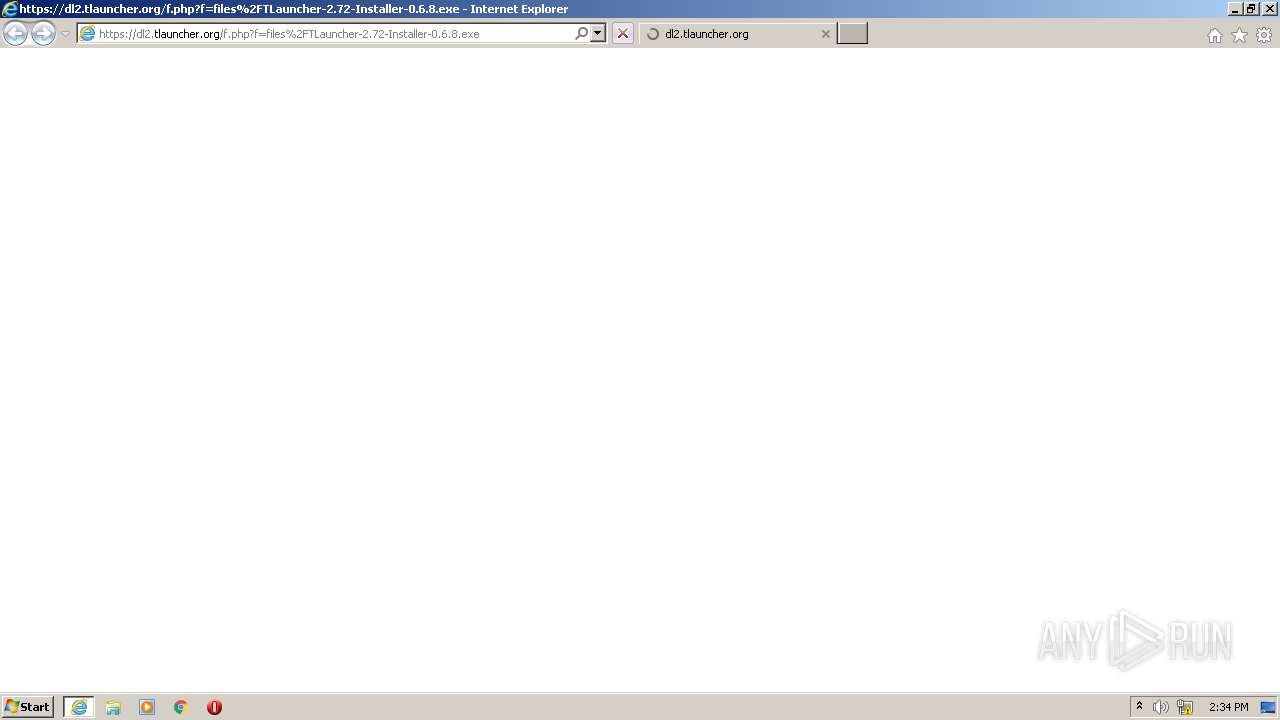
| URL: | https://dl2.tlauncher.org/f.php?f=files%2FTLauncher-2.72-Installer-0.6.8.exe |
| Full analysis: | https://app.any.run/tasks/35e31581-0763-4bcd-9114-1814a286390b |
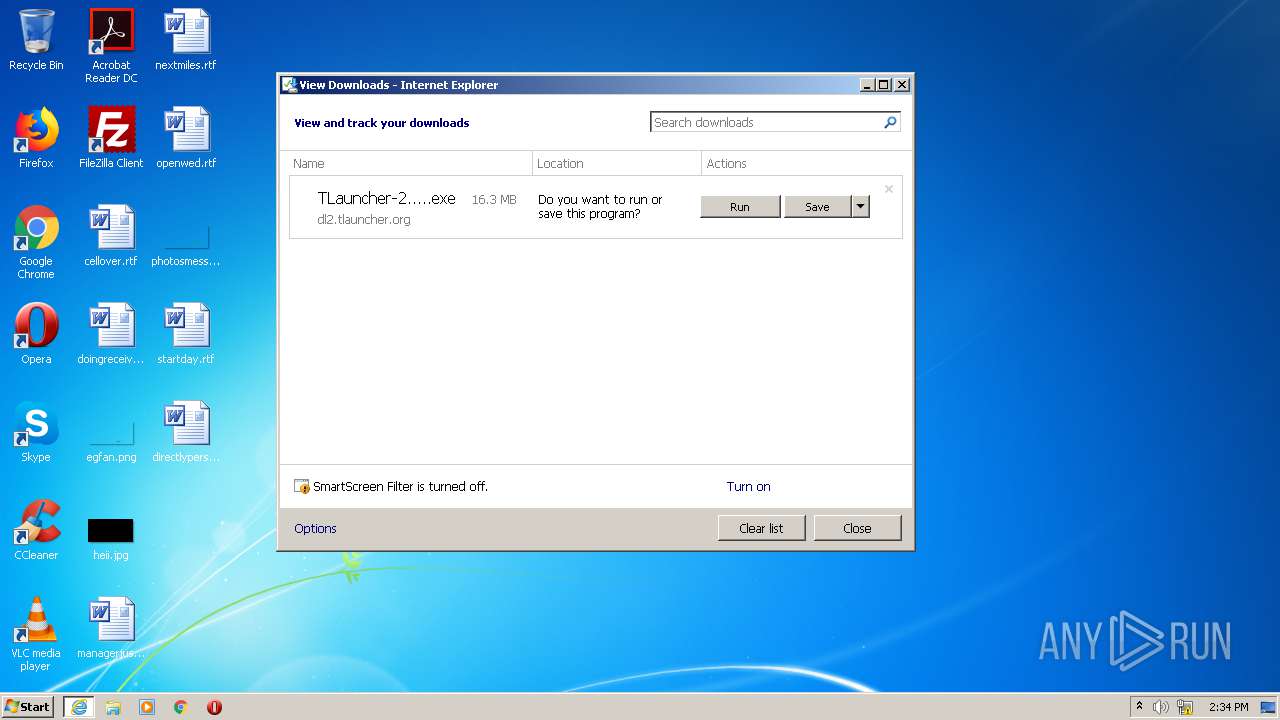
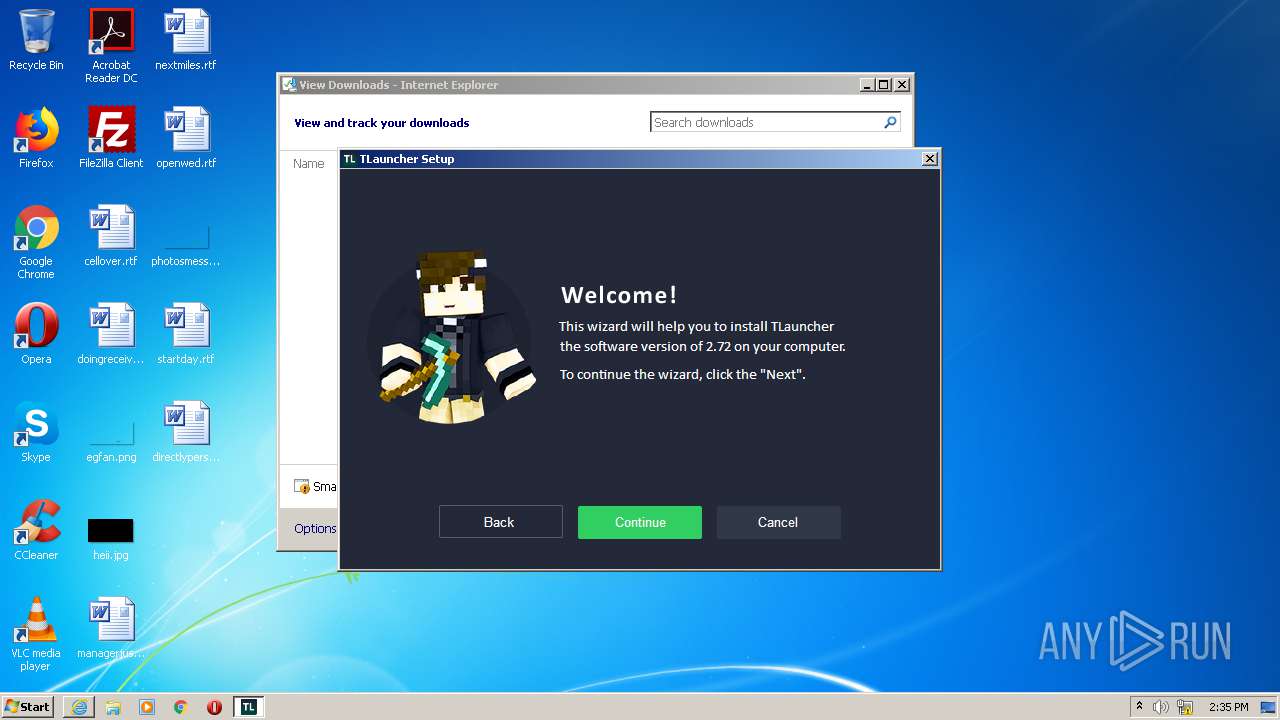
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2020, 14:34:18 |
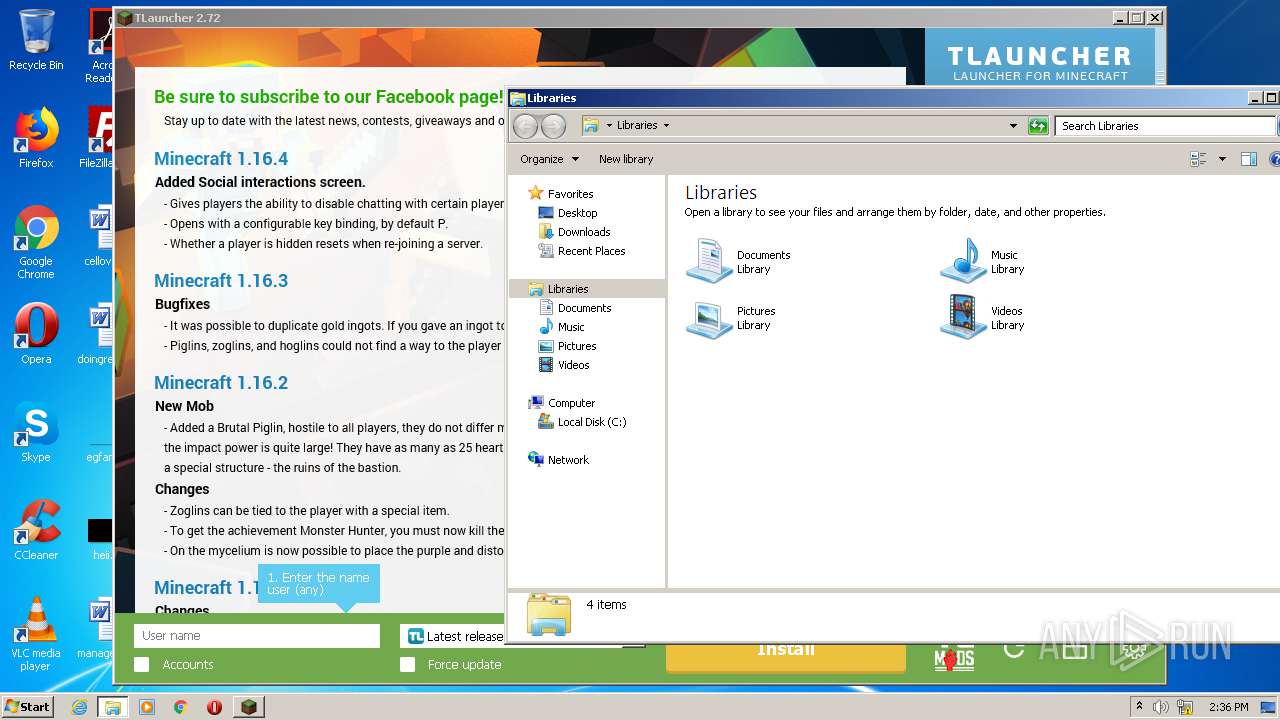
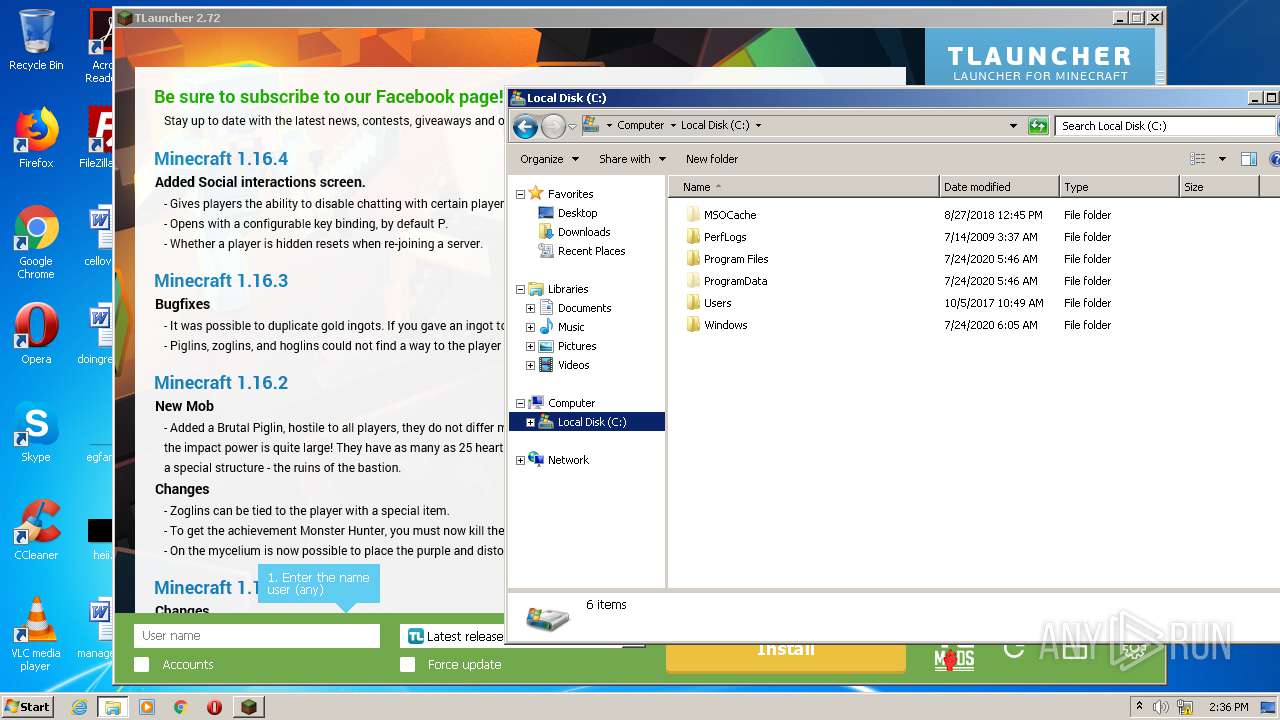
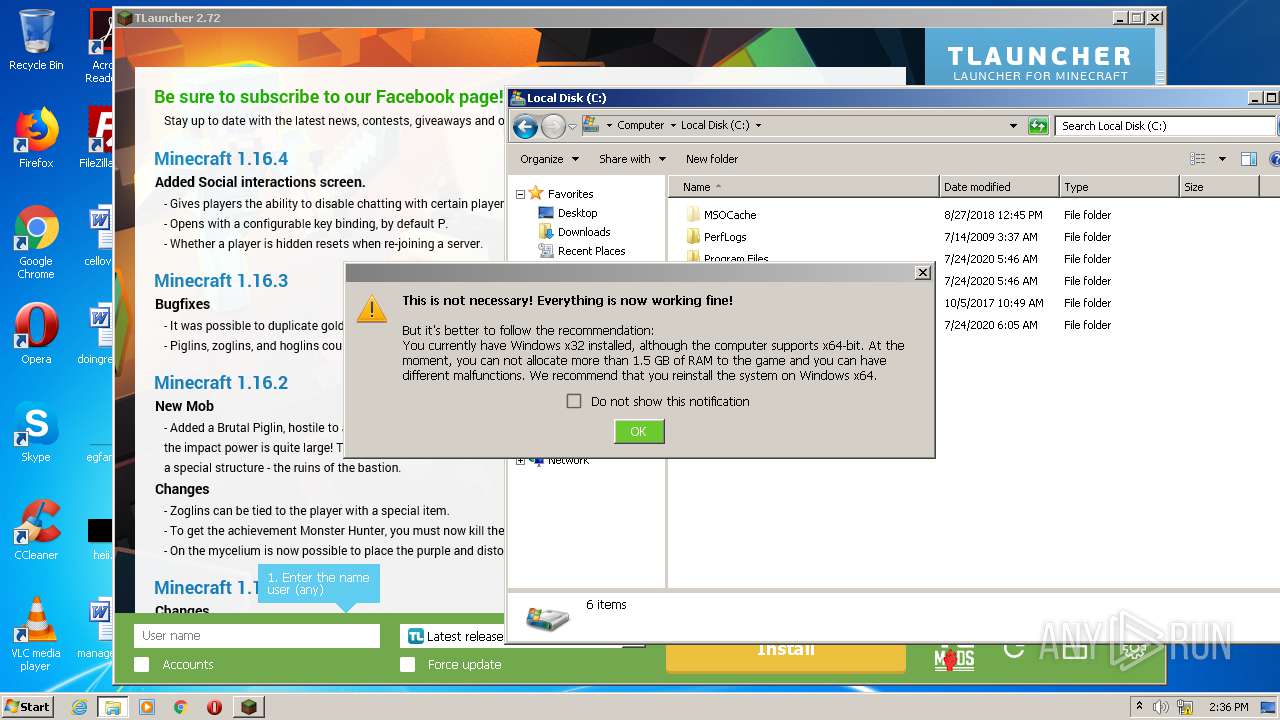
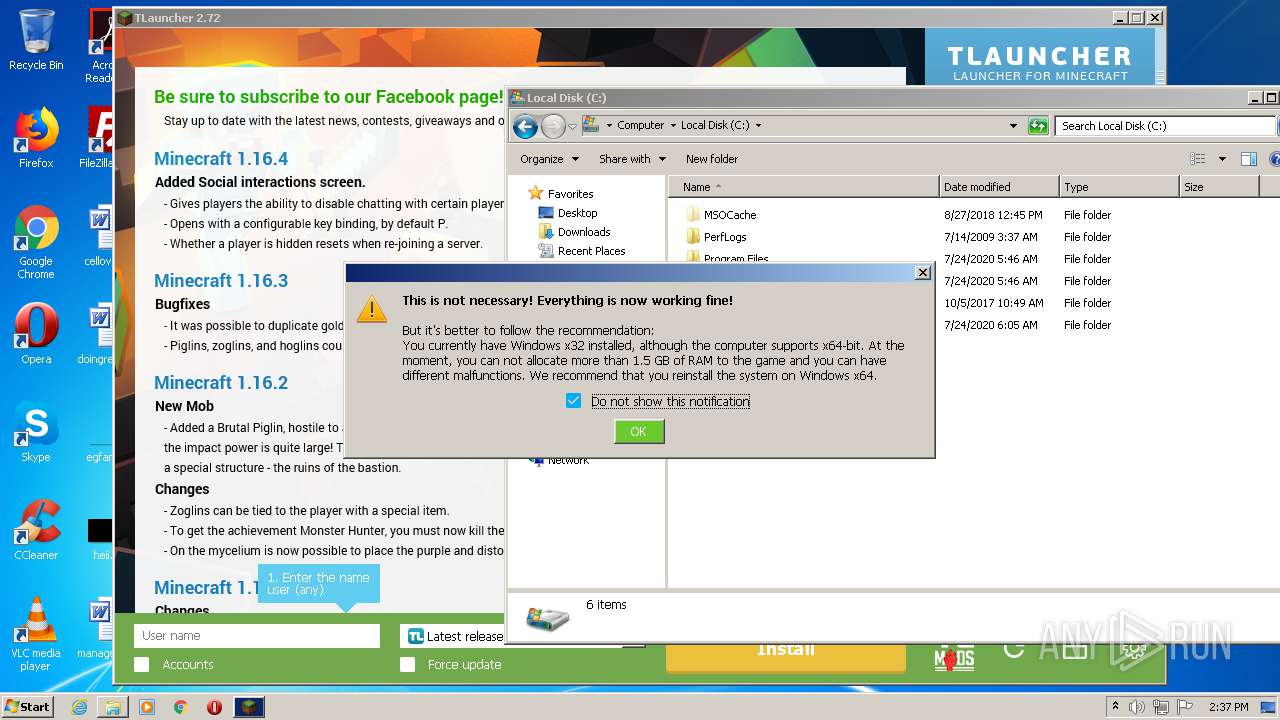
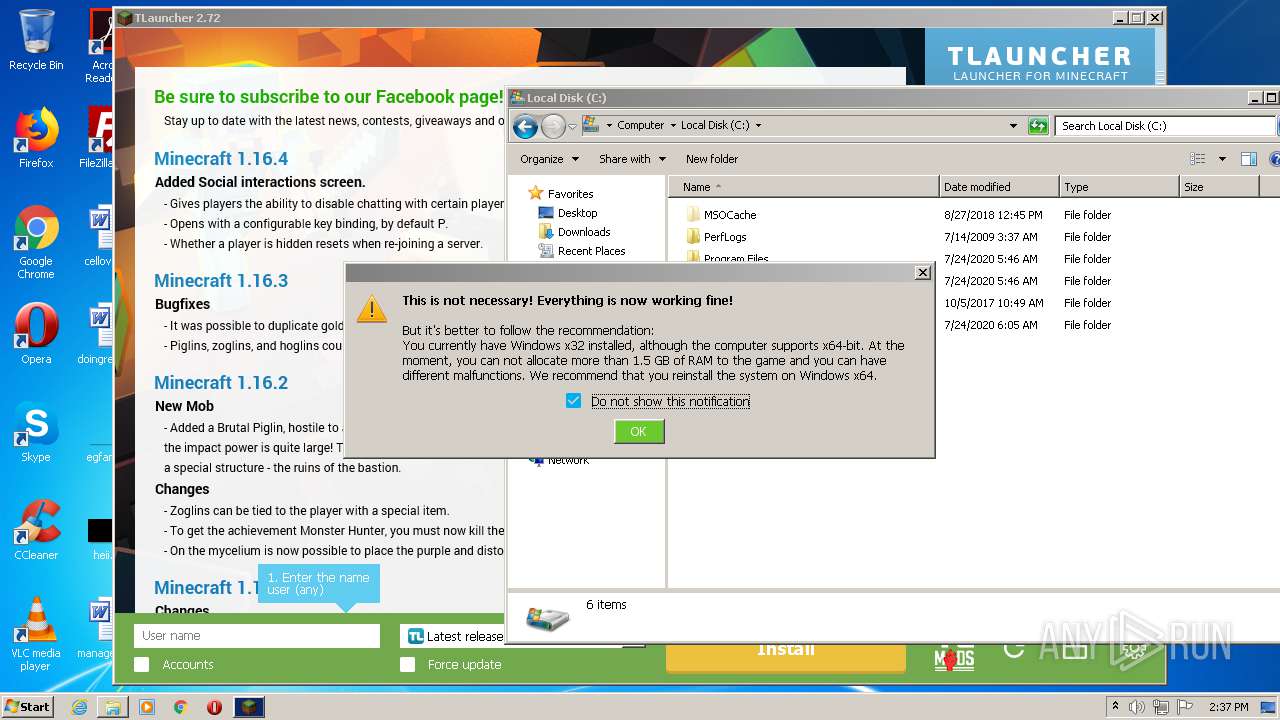
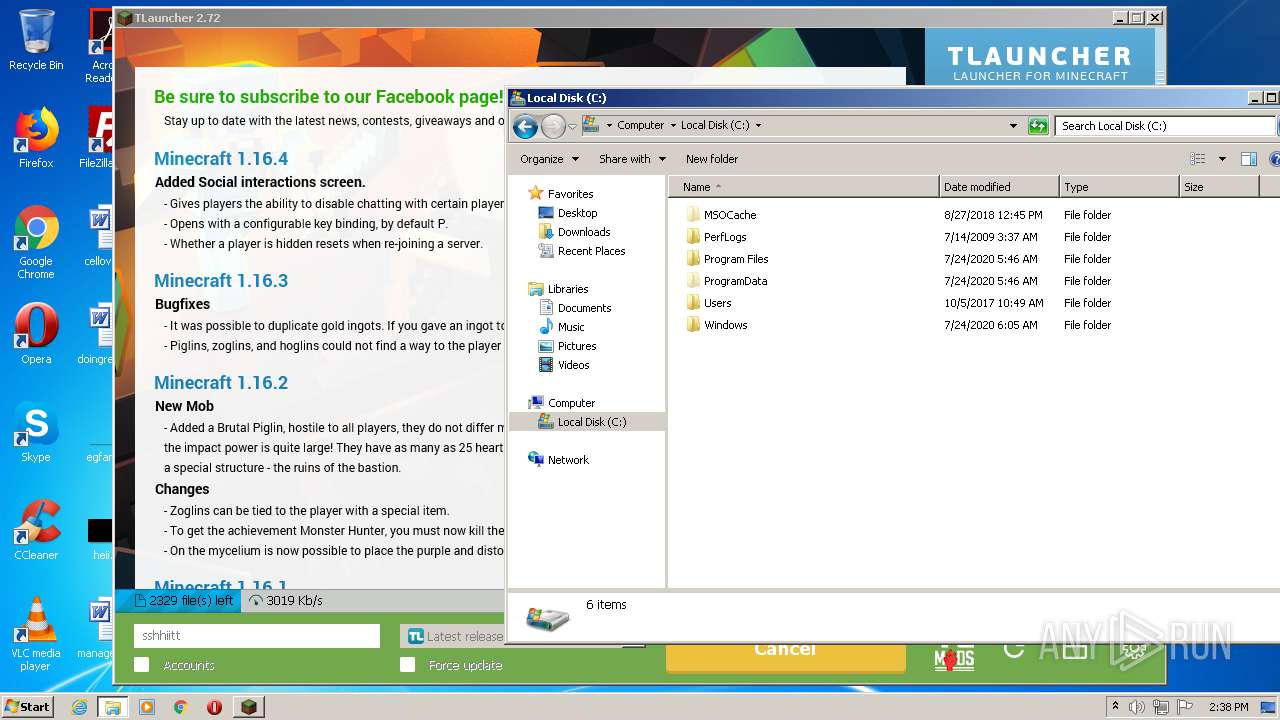
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E9B374554E7036AE4A73305834DAEA7D |
| SHA1: | AEEA5E54FA143BFBE5BFDDCB3D325E78B842466A |
| SHA256: | DD67DEDC8230F2D835022E7488528C74A4D43B05AF3DFCDE72E8F44B389B1002 |
| SSDEEP: | 3:N8R1JVLu5DceHXNCSYjBXIFLdLN:2D/65Dce3xeXuJ |
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 2528)
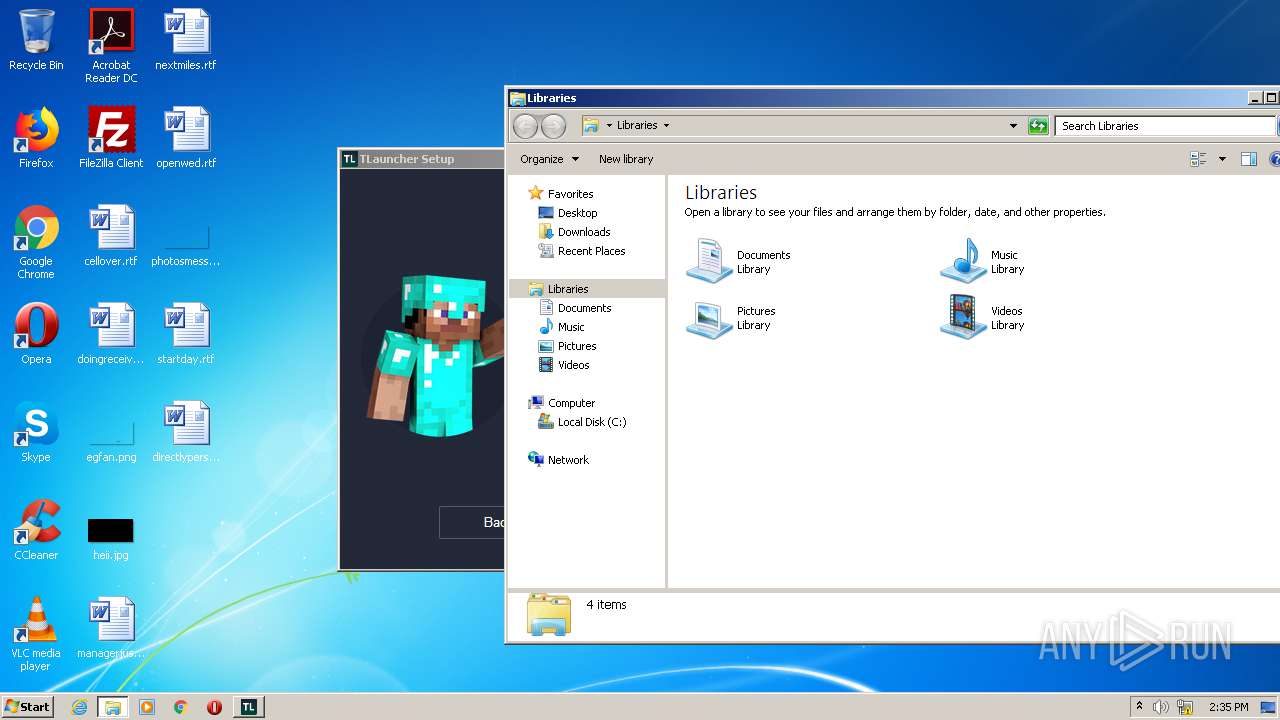
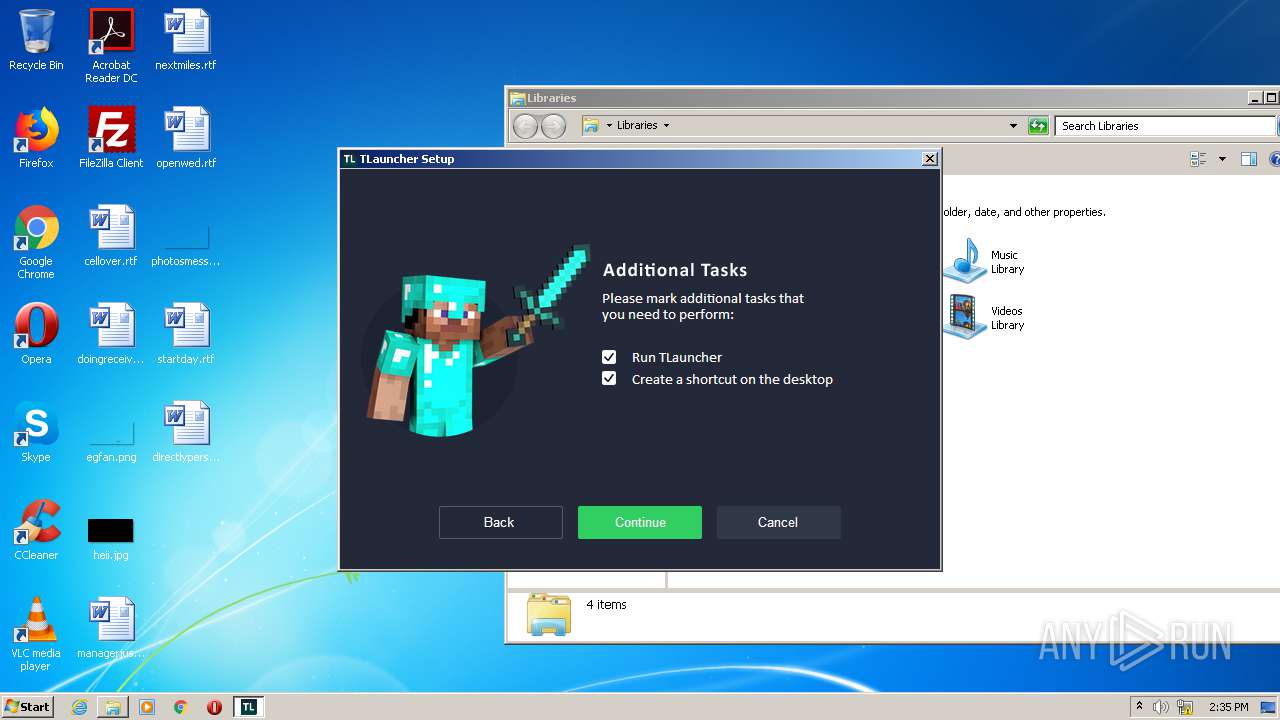
- TLauncher-2.72-Installer-0.6.8.exe (PID: 272)
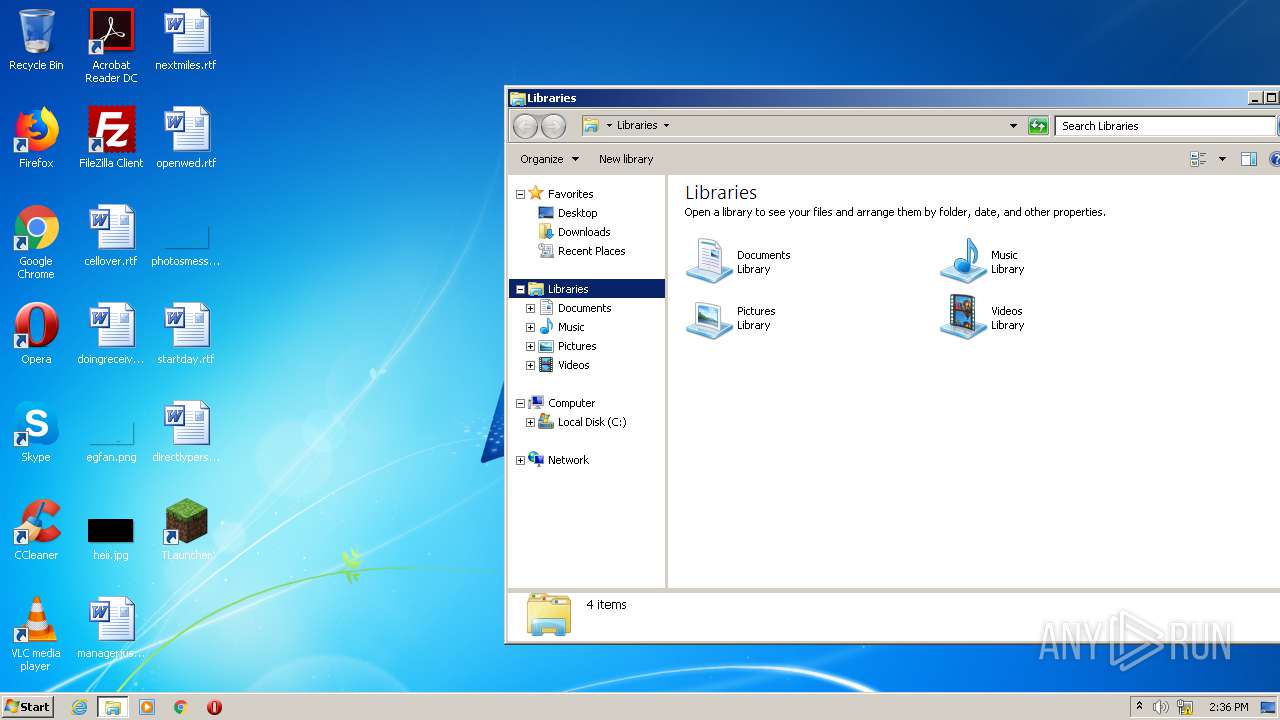
- TLauncher.exe (PID: 520)
Drops executable file immediately after starts
- TLauncher-2.72-Installer-0.6.8.exe (PID: 272)
Loads dropped or rewritten executable
- irsetup.exe (PID: 2528)
SUSPICIOUS
Executable content was dropped or overwritten
- TLauncher-2.72-Installer-0.6.8.exe (PID: 272)
- iexplore.exe (PID: 3220)
- irsetup.exe (PID: 2528)
- iexplore.exe (PID: 3236)
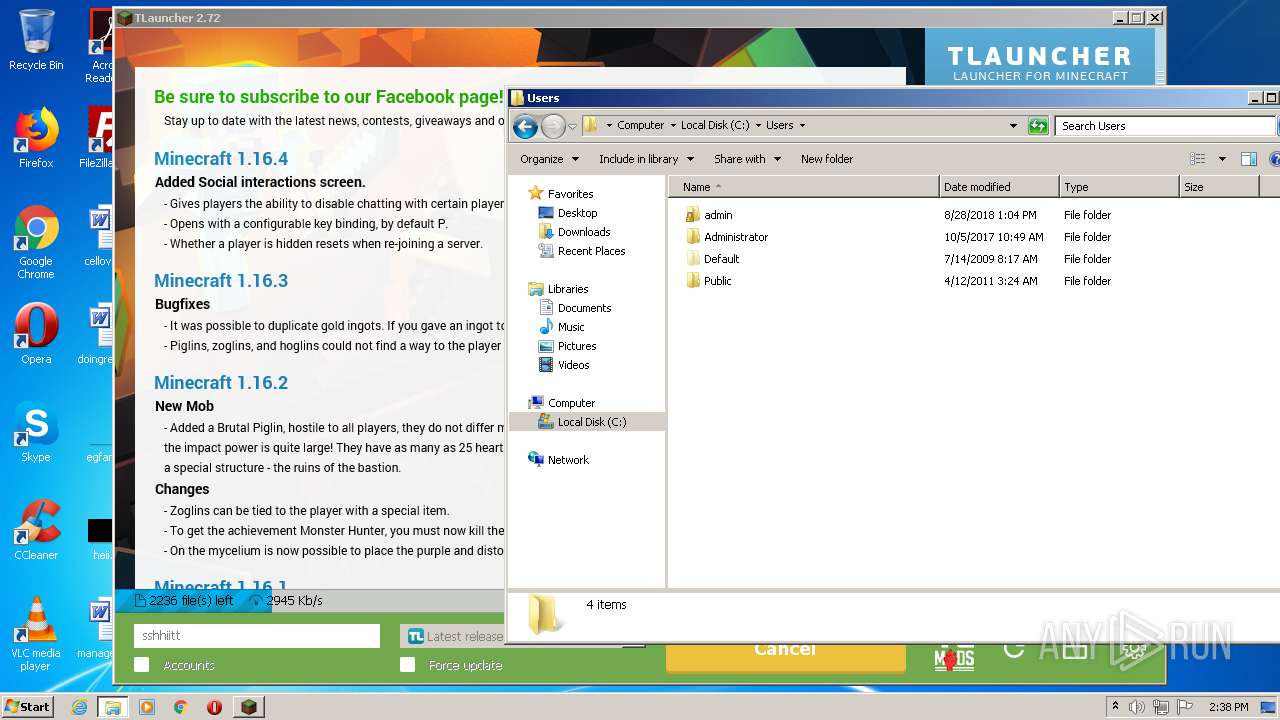
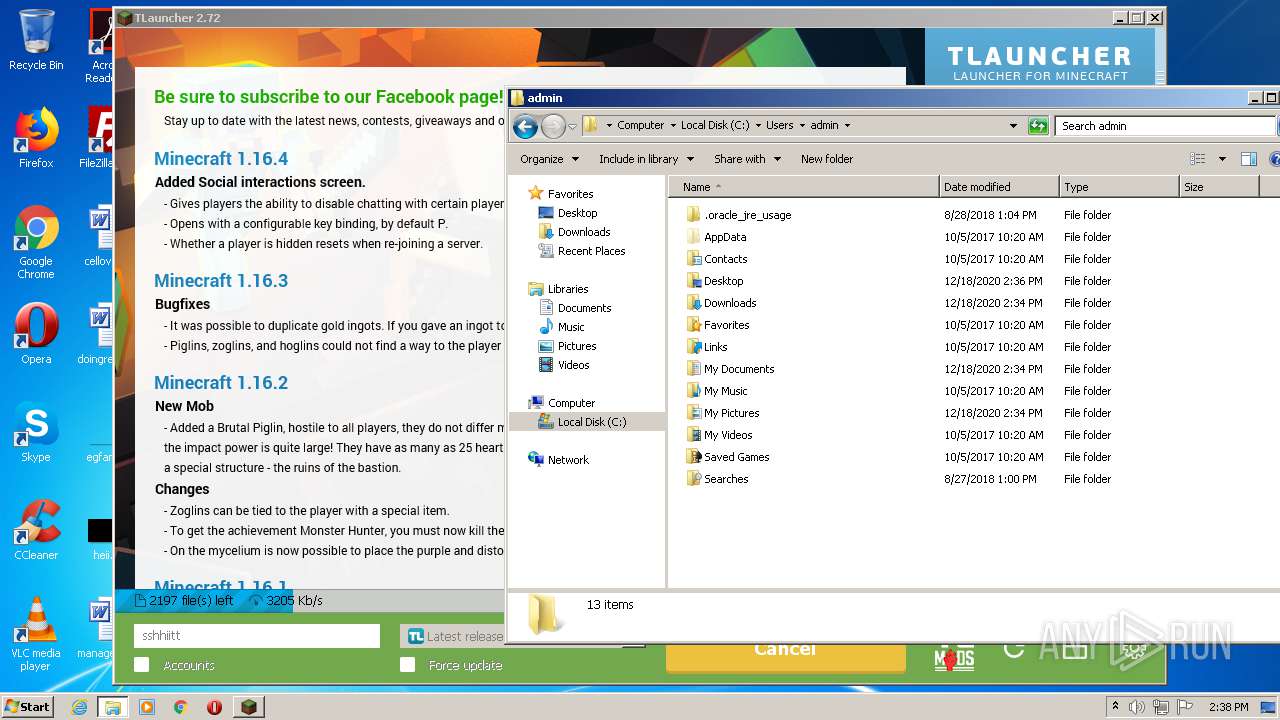
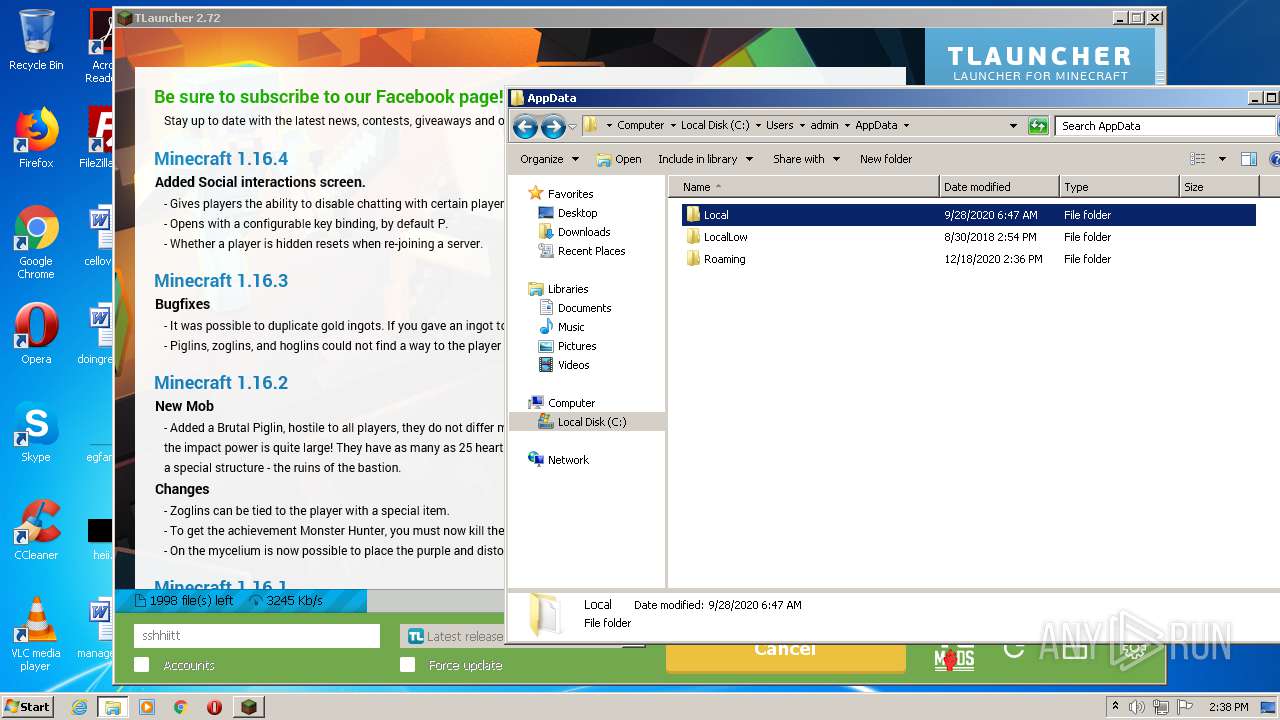
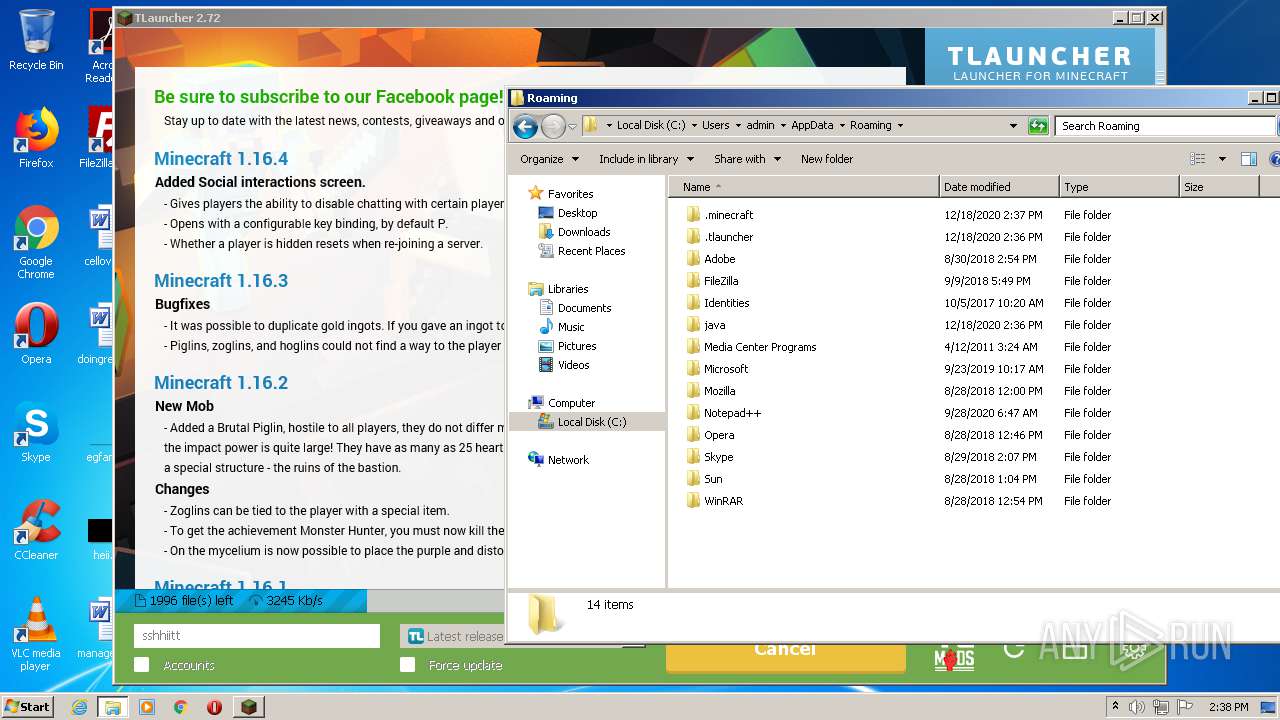
Creates files in the user directory
- irsetup.exe (PID: 2528)
- javaw.exe (PID: 3396)
- dxdiag.exe (PID: 2284)
- javaw.exe (PID: 3300)
Reads internet explorer settings
- irsetup.exe (PID: 2528)
Executes JAVA applets
- TLauncher.exe (PID: 520)
- javaw.exe (PID: 3396)
Starts application with an unusual extension
- cmd.exe (PID: 2356)
- cmd.exe (PID: 2736)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 2832)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 3148)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2356)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2736)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 4020)
Application launched itself
- javaw.exe (PID: 3396)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3396)
- javaw.exe (PID: 3300)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 2832)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 3236)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3236)
Application launched itself
- iexplore.exe (PID: 3236)
Creates files in the user directory
- iexplore.exe (PID: 3220)
Changes settings of System certificates
- iexplore.exe (PID: 3236)
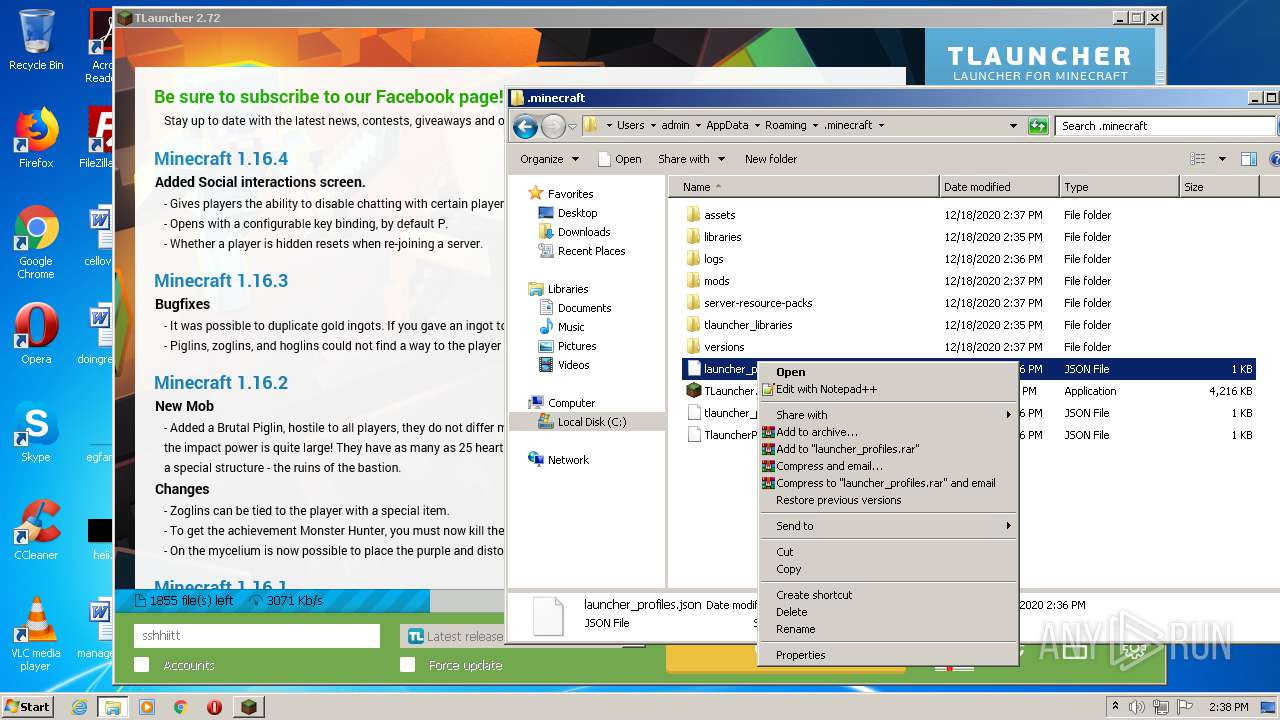
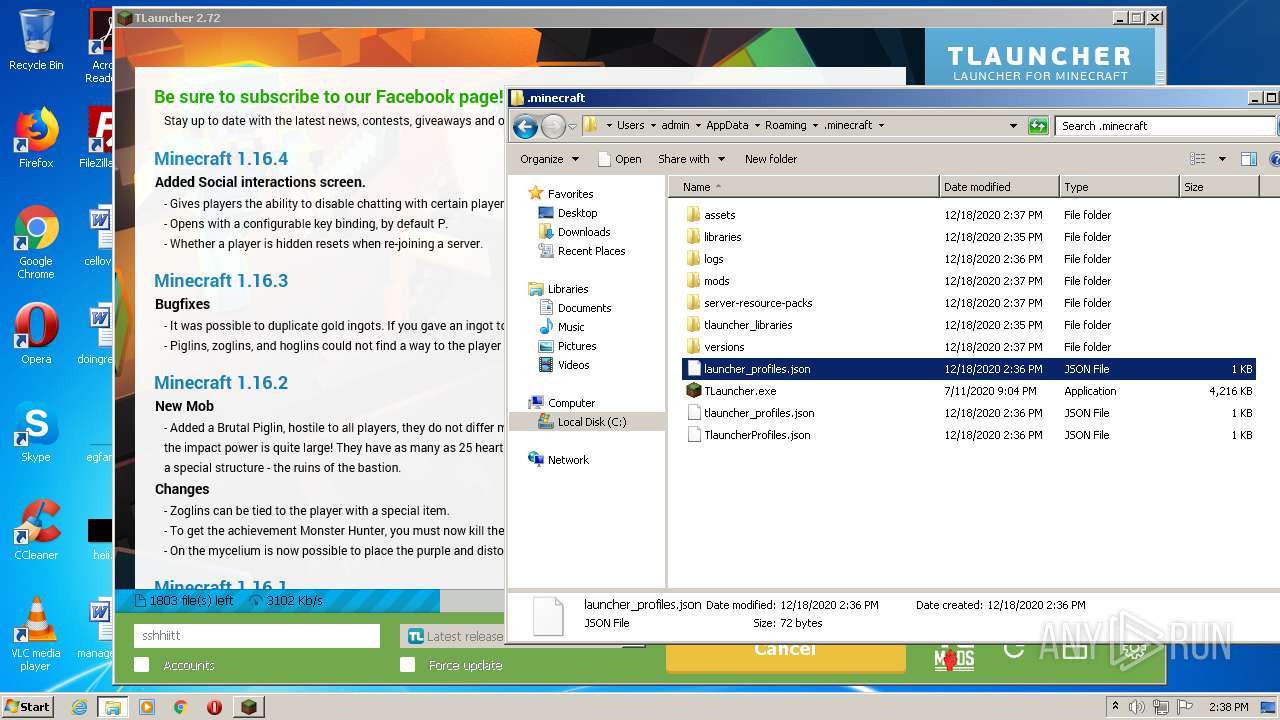
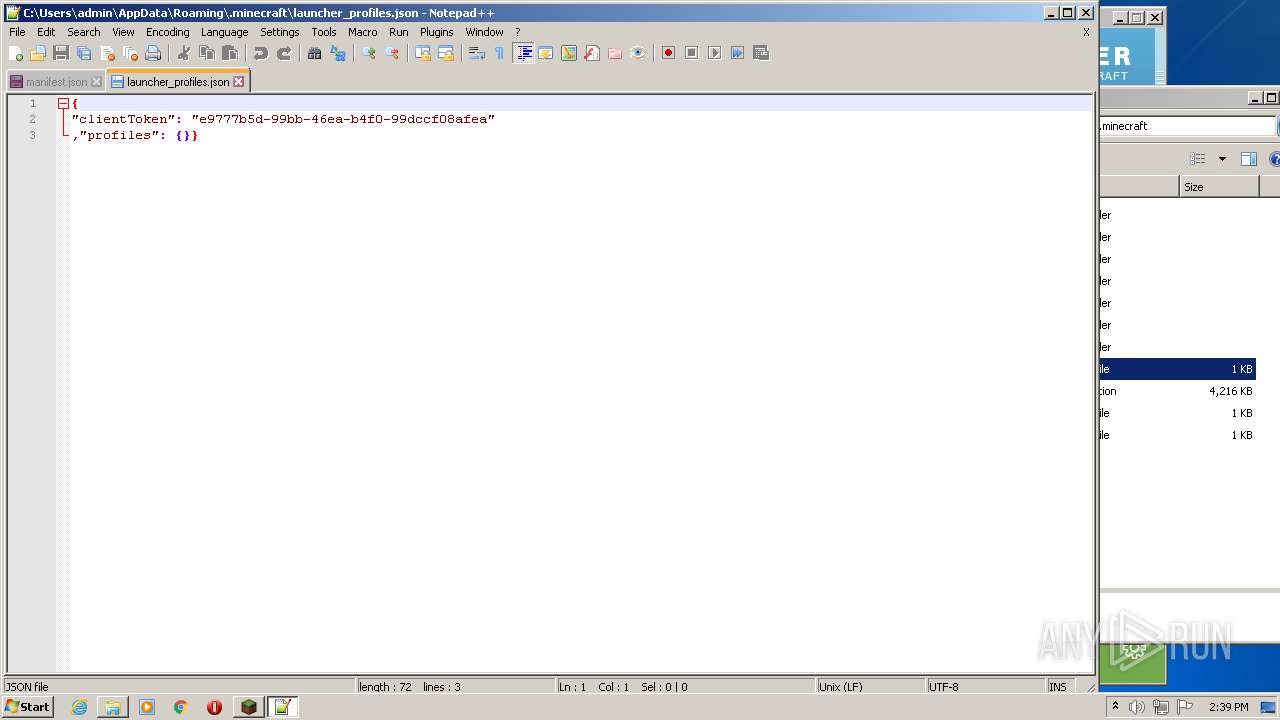
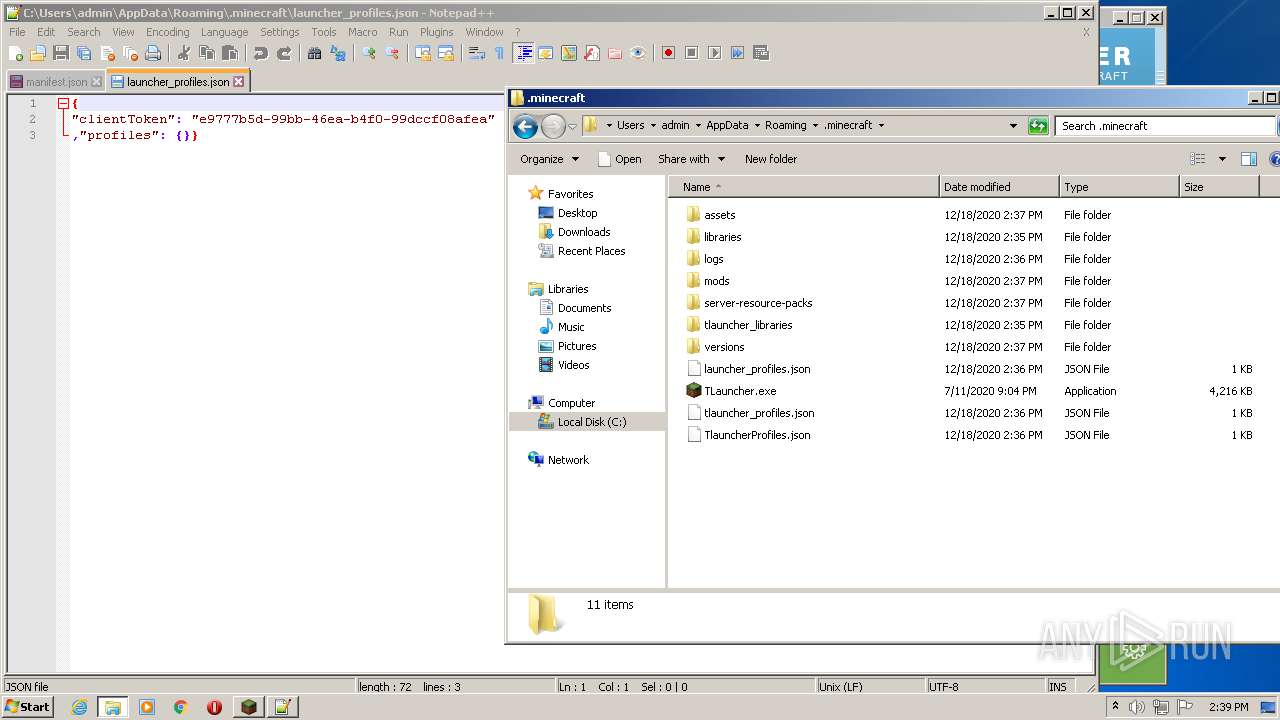
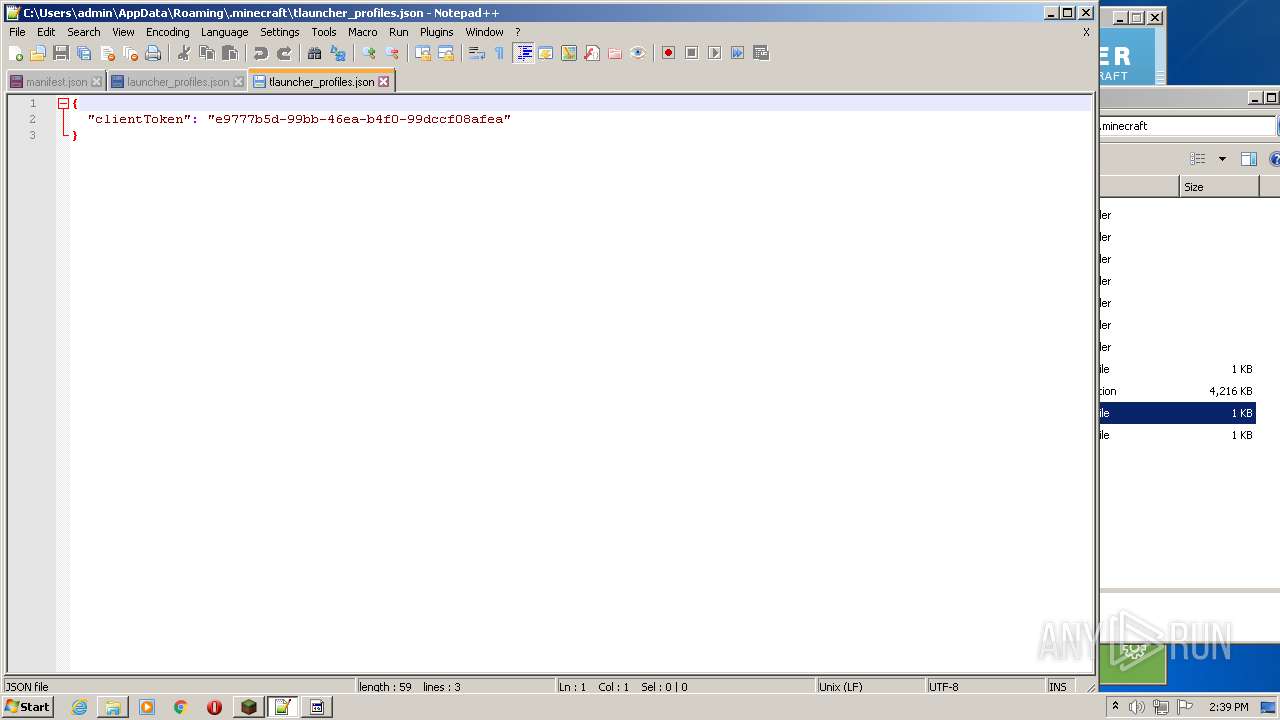
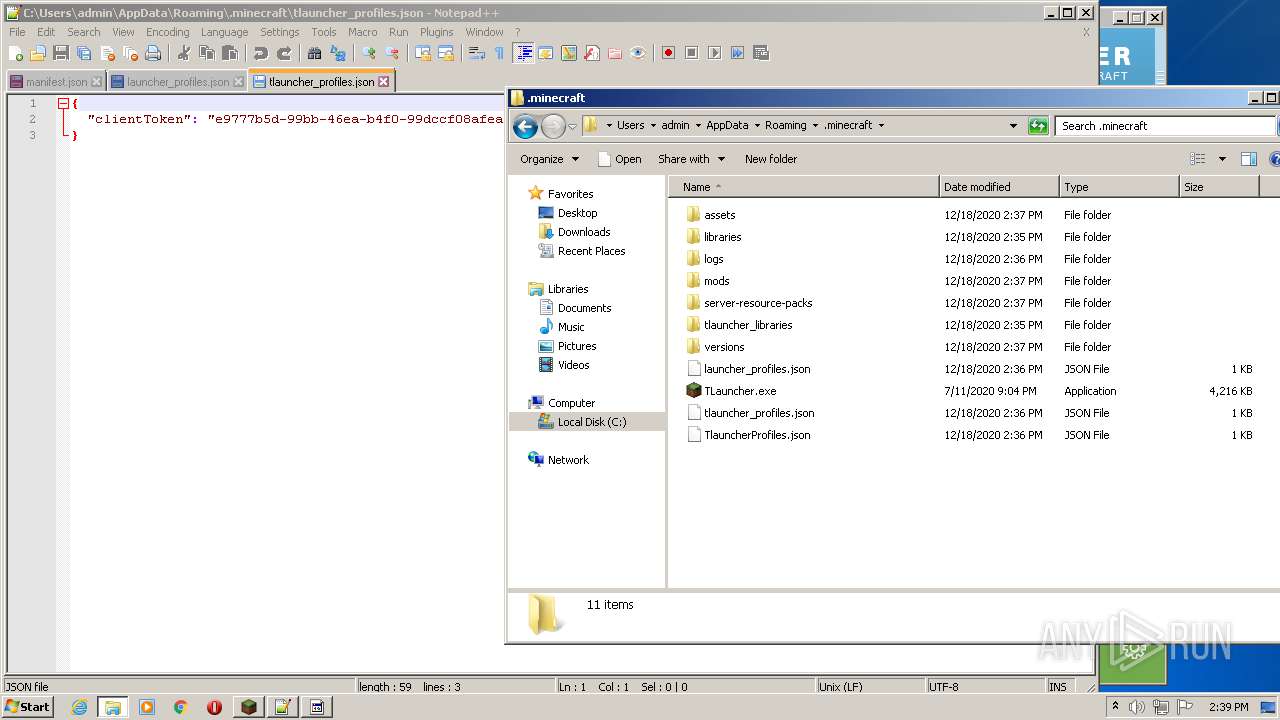
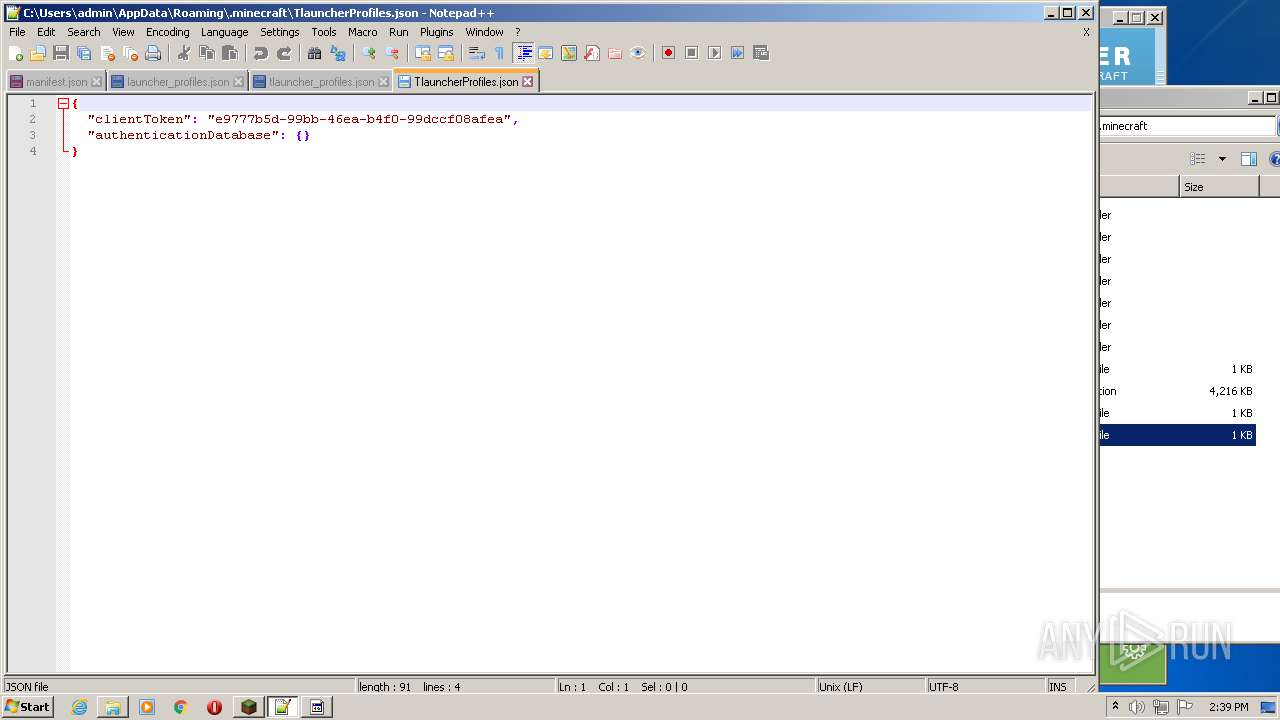
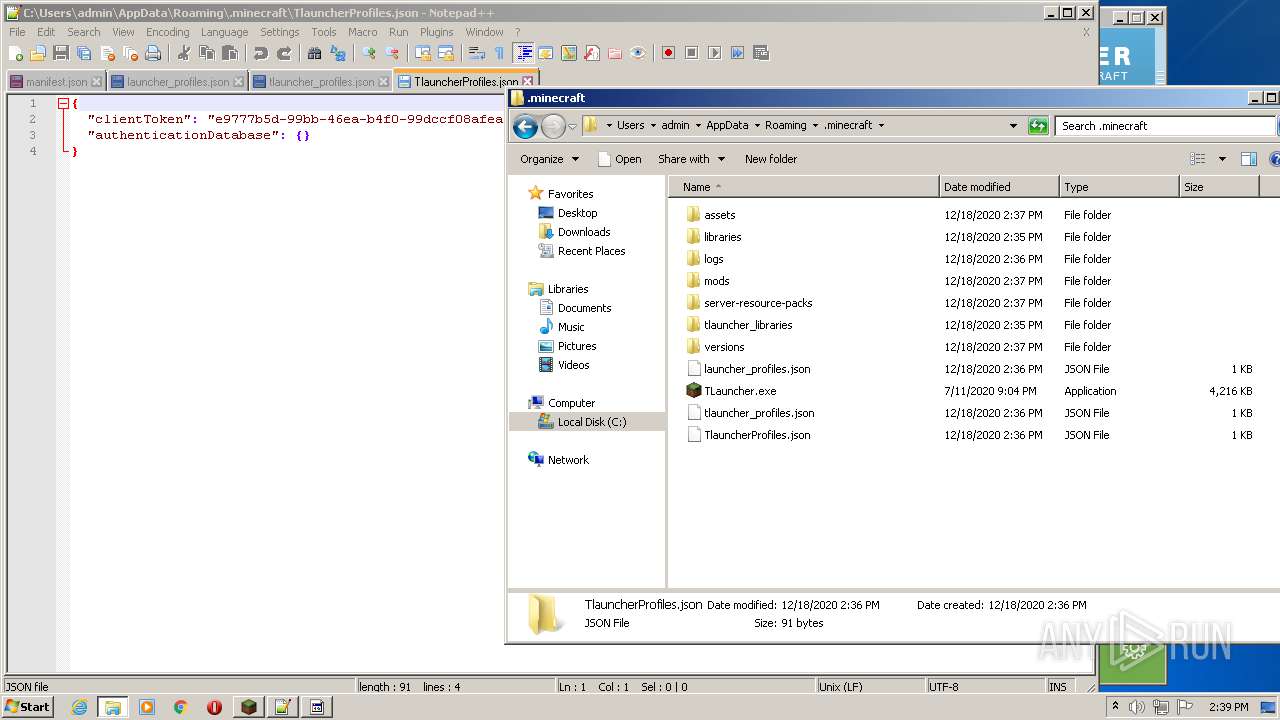
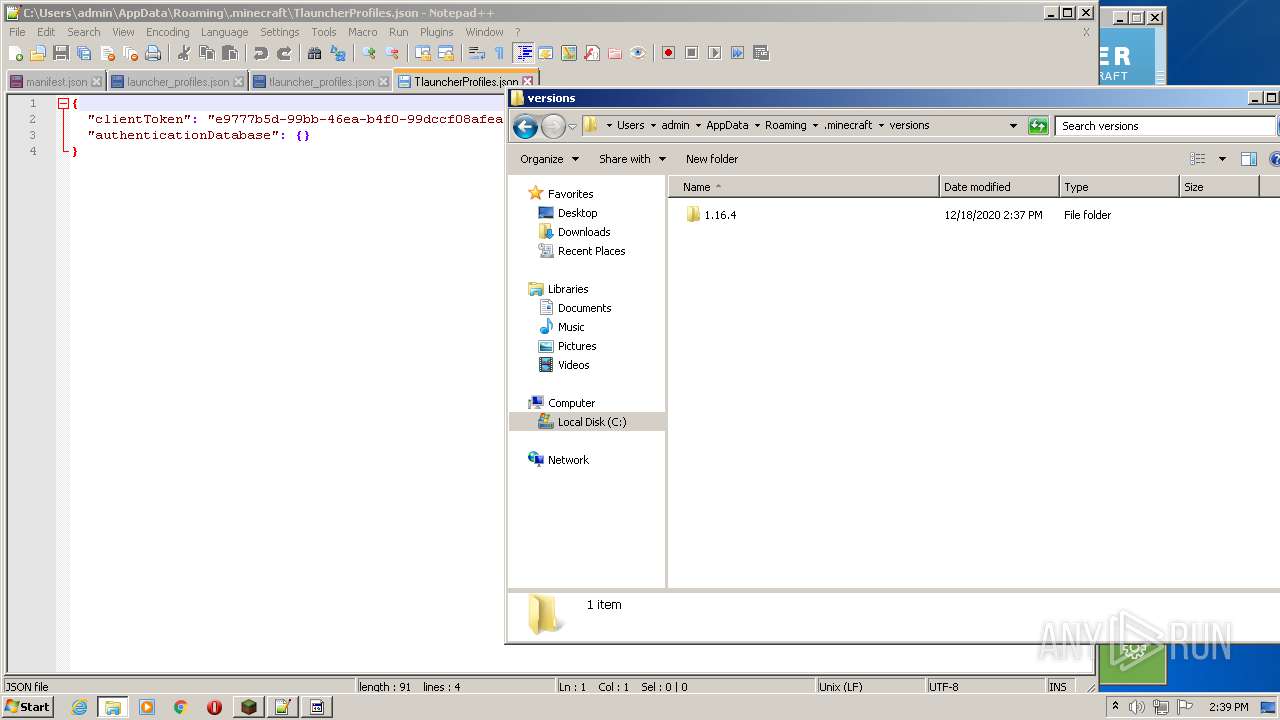
Manual execution by user
- explorer.exe (PID: 2256)
- notepad++.exe (PID: 3284)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3236)
Changes internet zones settings
- iexplore.exe (PID: 3236)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 3300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
31
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | wmic qfe get HotFixID | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
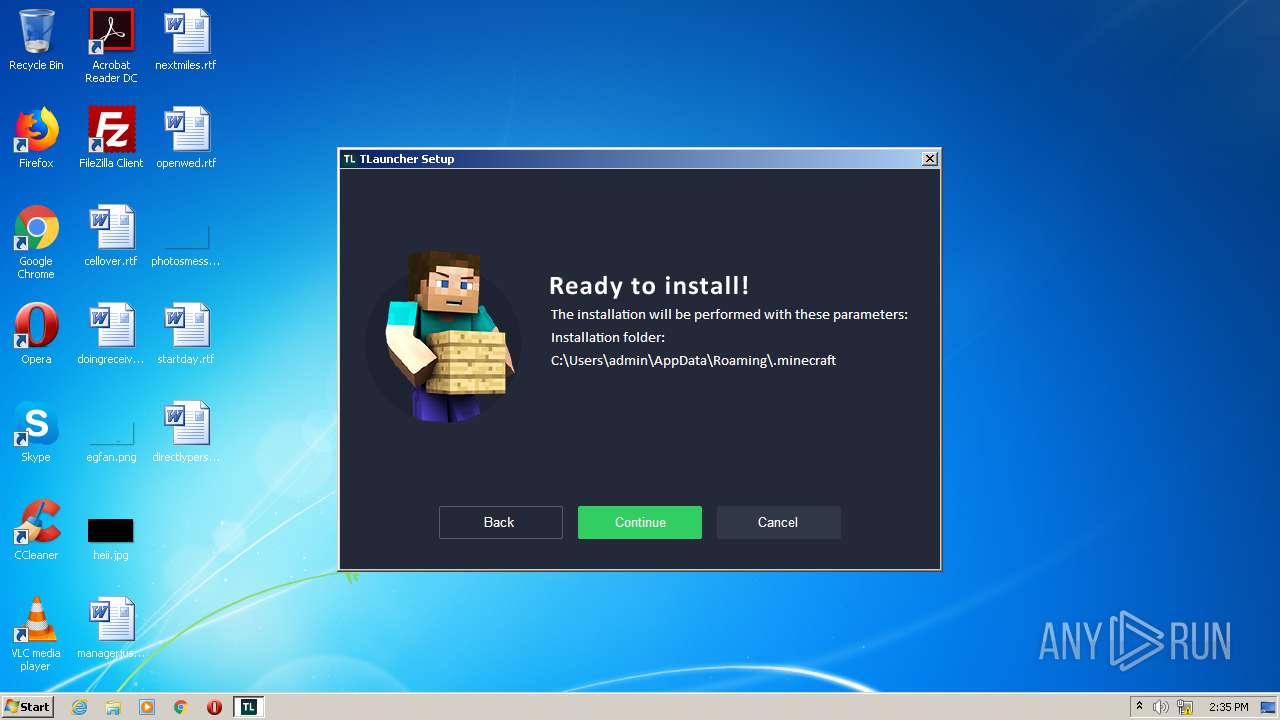
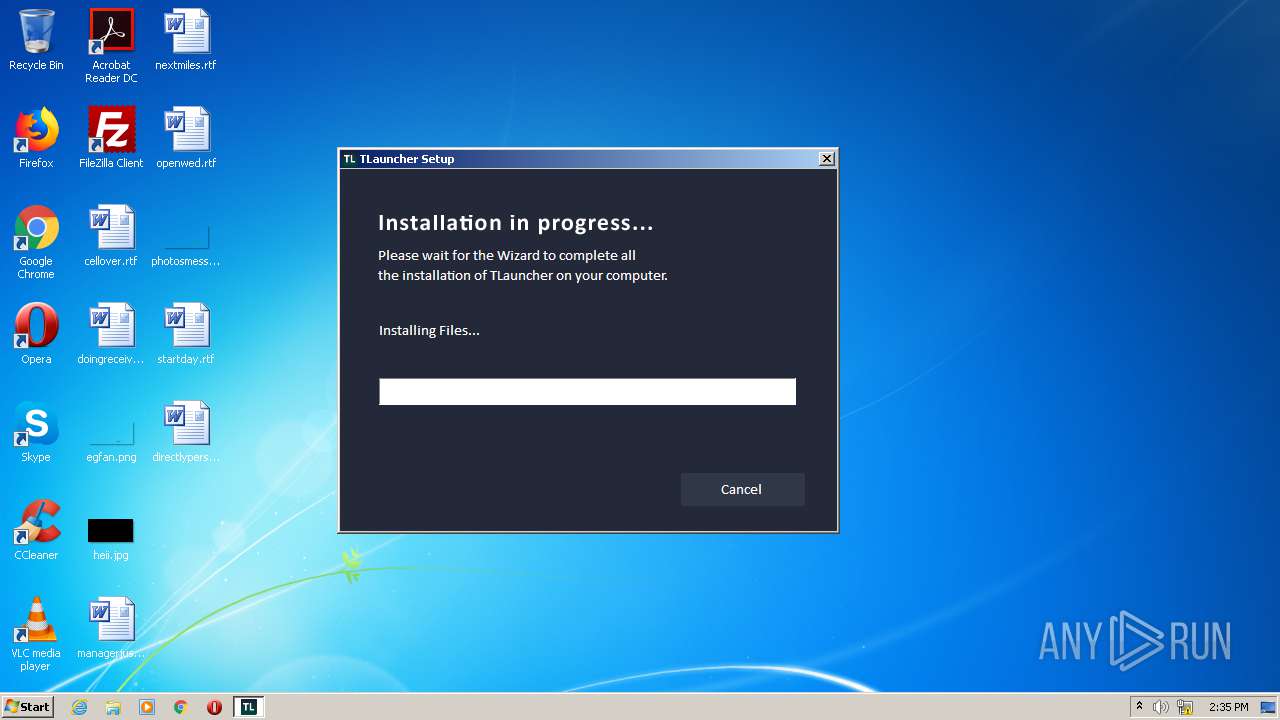
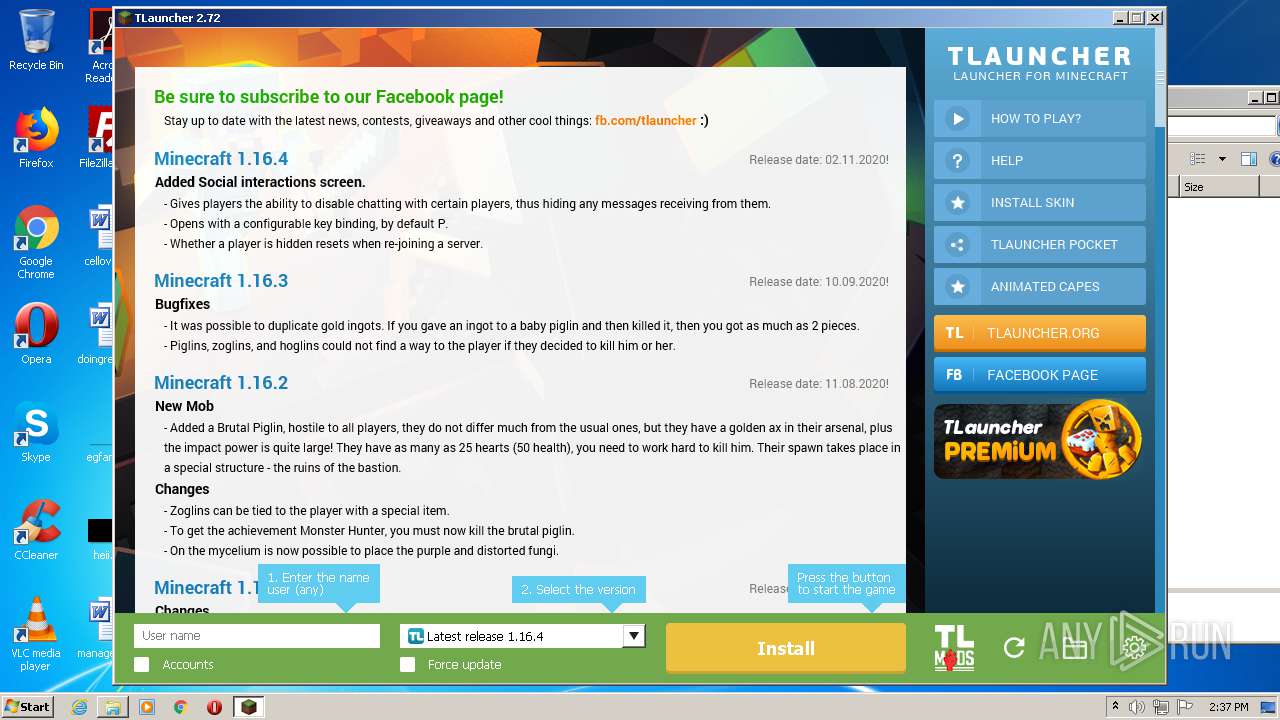
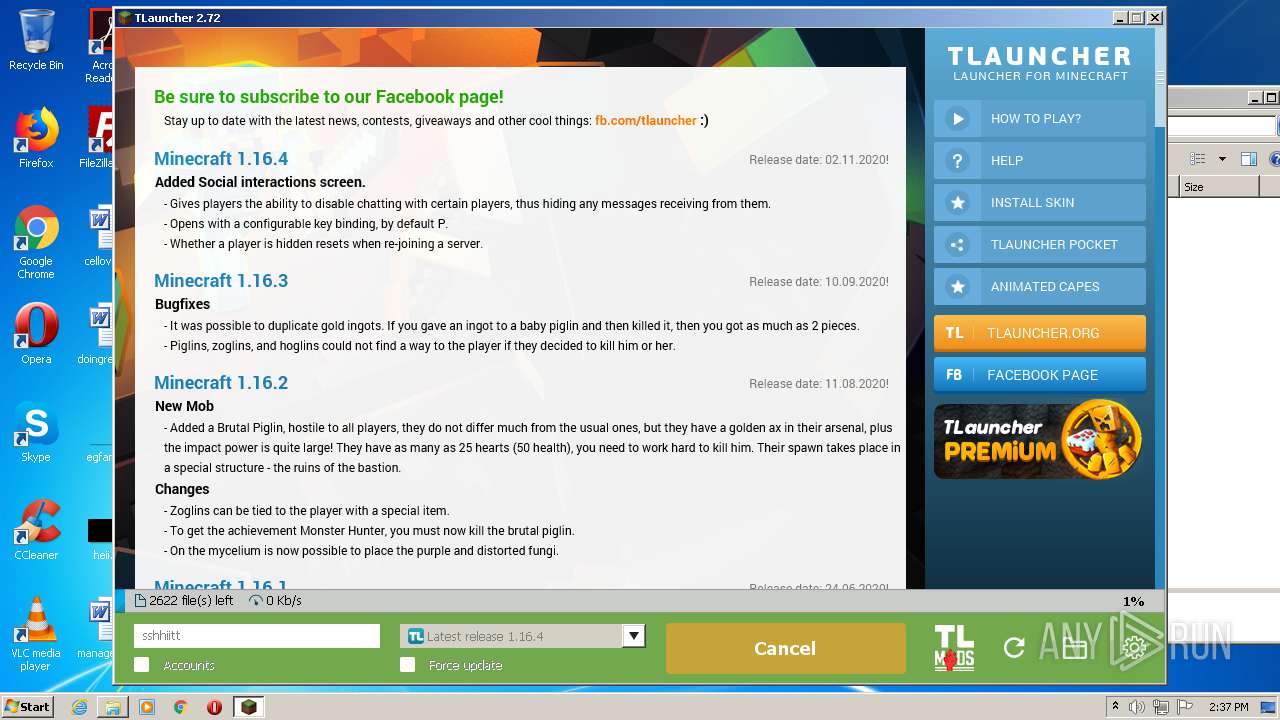
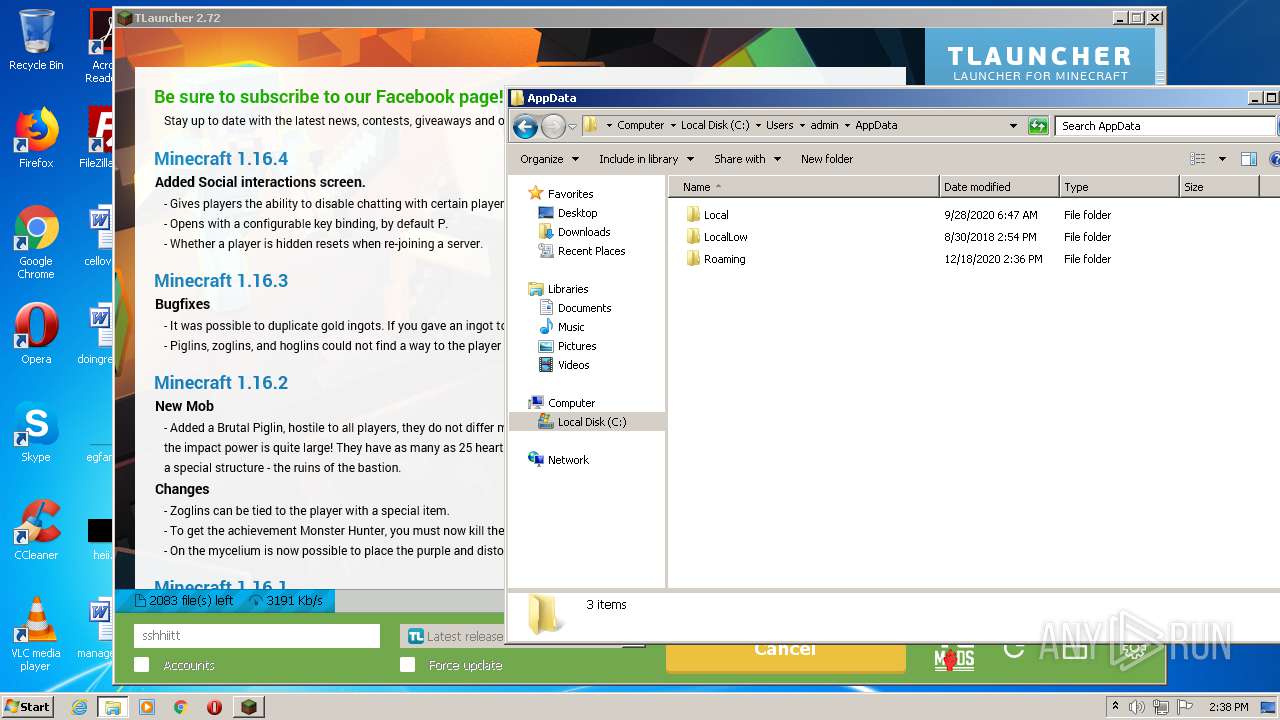
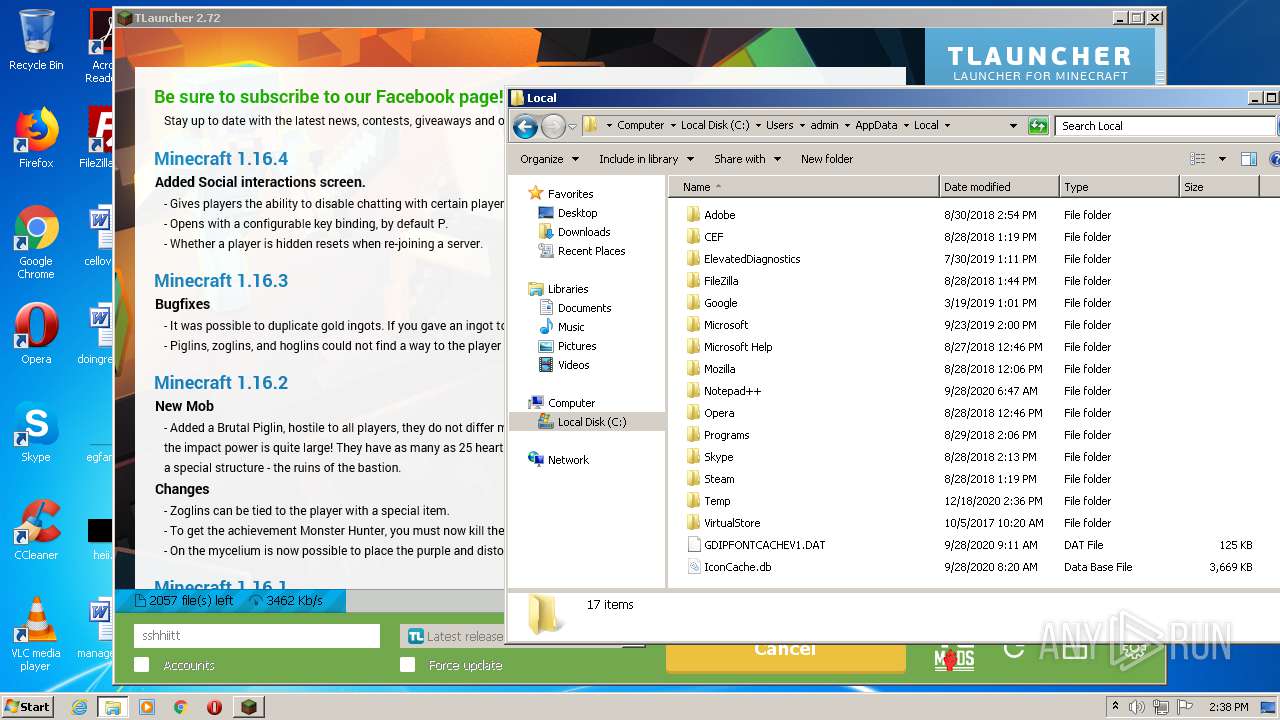
| 272 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\TLauncher-2.72-Installer-0.6.8.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\TLauncher-2.72-Installer-0.6.8.exe | iexplore.exe | ||||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 0 Version: 0.6.8.0 Modules
| |||||||||||||||
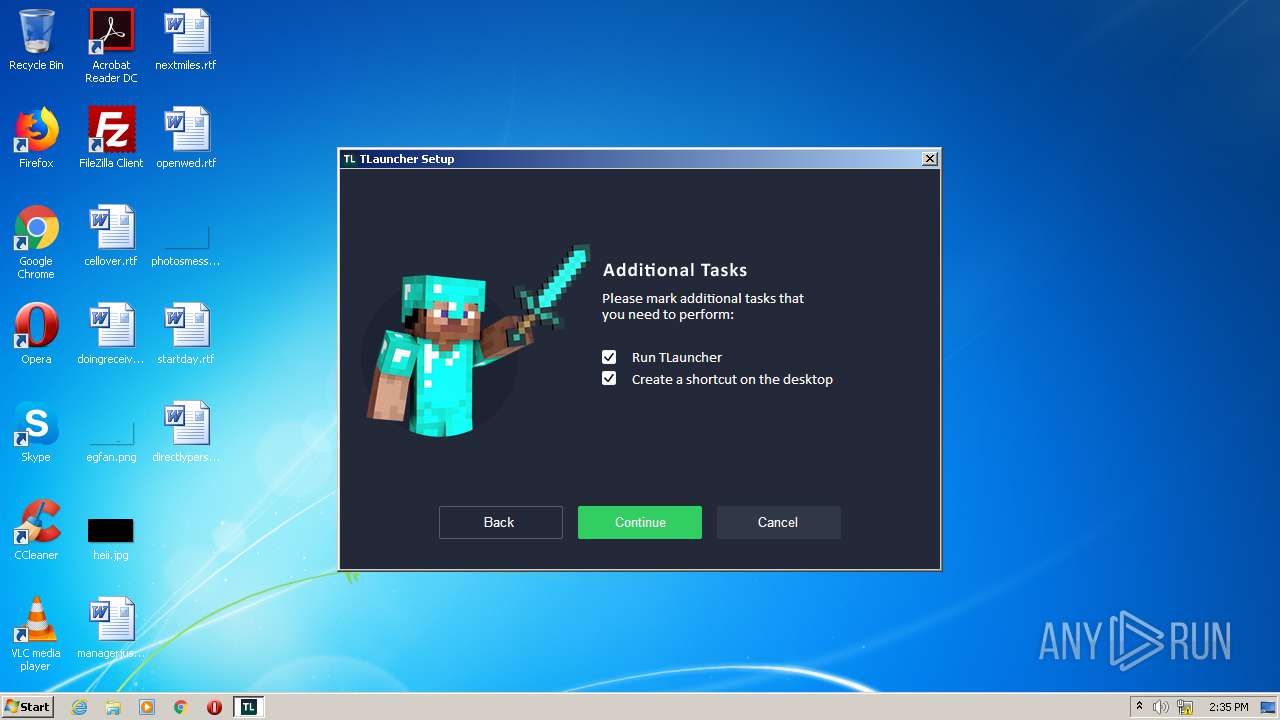
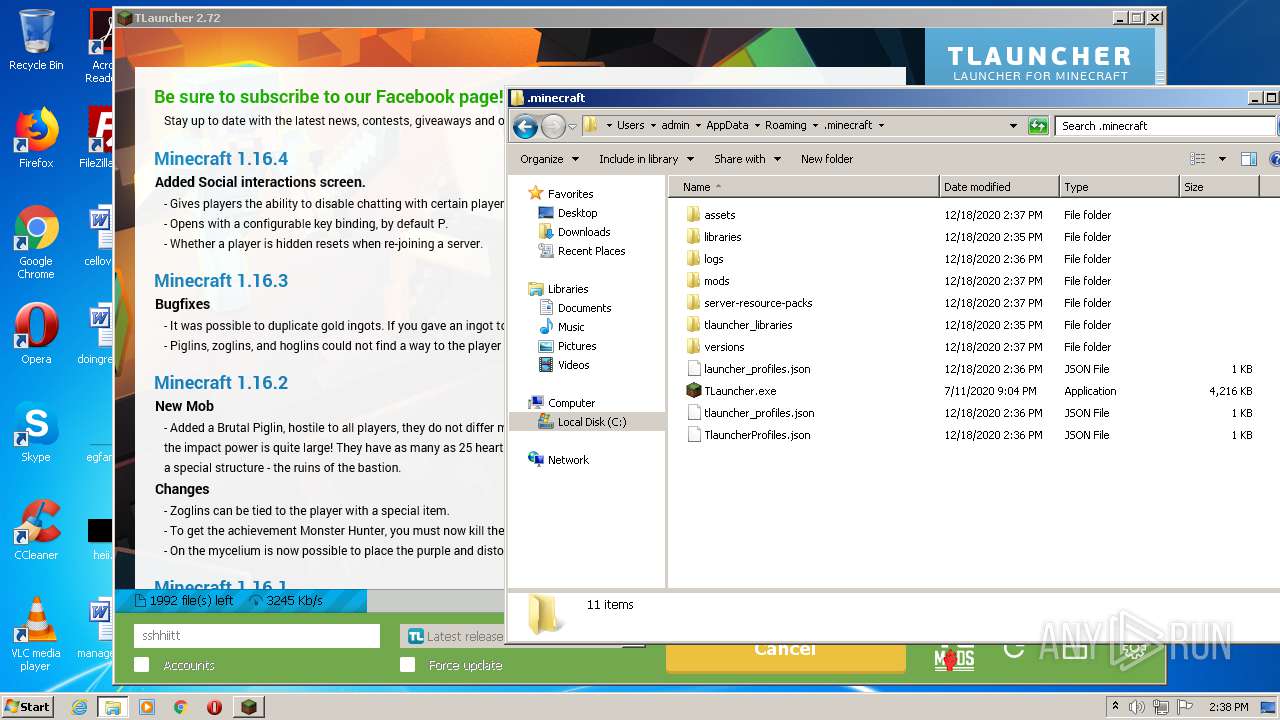
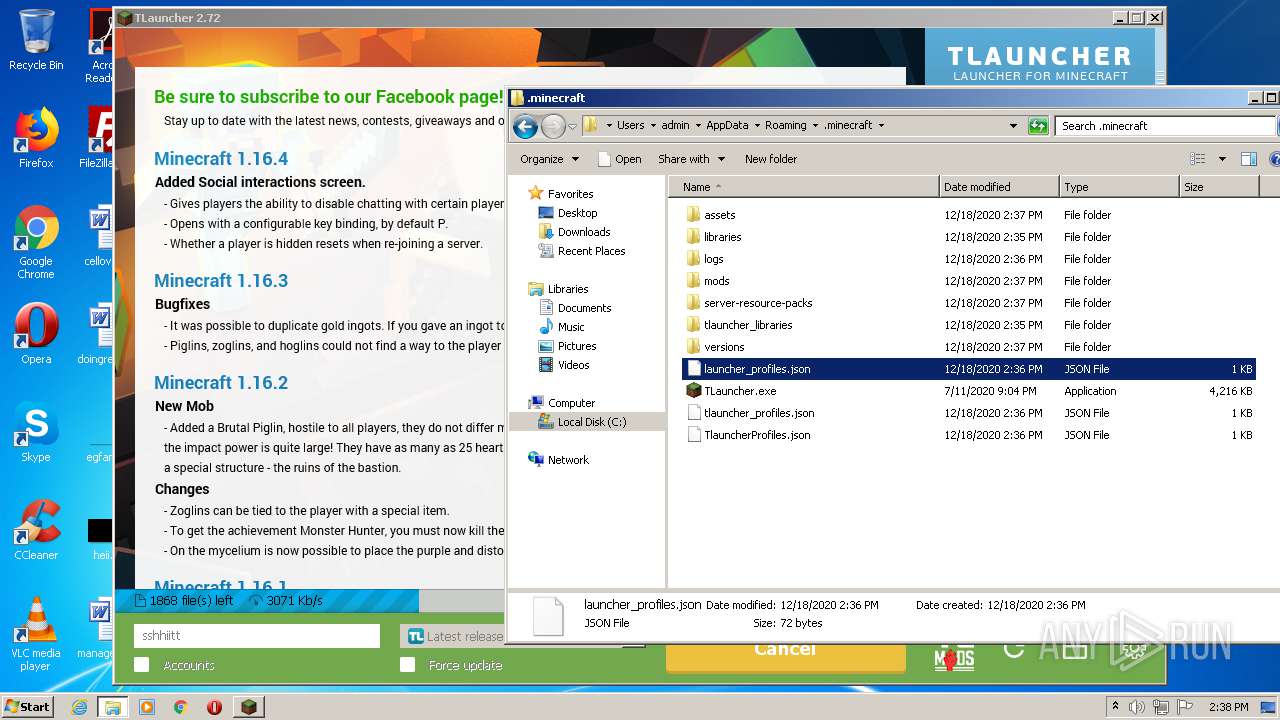
| 520 | "C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe" | C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe | — | irsetup.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Exit code: 0 Version: 2.72 Modules
| |||||||||||||||
| 664 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1684 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1764 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1828 | wmic CPU get NAME | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2256 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 665
Read events
2 399
Write events
247
Delete events
19
Modification events
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4179237988 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30856522 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
12
Suspicious files
37
Text files
360
Unknown types
1 178
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE60A.tmp | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE60B.tmp | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\TLauncher-2.72-Installer-0.6.8.exe.p5u3rt1.partial | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5067346EE7E5E1CC.TMP | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\TLauncher-2.72-Installer-0.6.8.exe.p5u3rt1.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2528 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | der | |
MD5:— | SHA256:— | |||
| 272 | TLauncher-2.72-Installer-0.6.8.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | executable | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\TLauncher-2.72-Installer-0.6.8.exe | executable | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0P168F2D.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 333
TCP/UDP connections
28
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3220 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQCdkaoplkGuEyEAmG5ZINFe | US | der | 472 b | whitelisted |
3220 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3220 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQCdkaoplkGuEyEAmG5ZINFe | US | der | 472 b | whitelisted |
3300 | javaw.exe | GET | 200 | 104.20.87.142:80 | http://repo.tlauncher.org/update/lch/update_2.0.json?version=2.72&client=1124eaa1-dc98-449c-b327-f6a20fb4f1cf | US | text | 7.67 Kb | whitelisted |
3300 | javaw.exe | GET | 200 | 104.20.87.142:80 | http://repo.tlauncher.org/update/downloads/libraries/org/tlauncher/authlib/libraries-1.6.json | US | text | 130 Kb | whitelisted |
3220 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3300 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn4.png | US | image | 205 b | malicious |
3300 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://page.tlauncher.org/update/downloads/configs/client/eng.html | US | html | 16.2 Kb | malicious |
2528 | irsetup.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3300 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn3.png | US | image | 209 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3220 | iexplore.exe | 104.20.86.142:443 | dl2.tlauncher.org | Cloudflare Inc | US | shared |
3220 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2528 | irsetup.exe | 46.4.112.226:443 | advancedrepository.com | Hetzner Online GmbH | DE | malicious |
3300 | javaw.exe | 104.20.86.142:80 | dl2.tlauncher.org | Cloudflare Inc | US | shared |
2528 | irsetup.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
3300 | javaw.exe | 104.20.87.142:80 | dl2.tlauncher.org | Cloudflare Inc | US | shared |
3300 | javaw.exe | 143.204.202.3:80 | resources.download.minecraft.net | — | US | malicious |
3300 | javaw.exe | 104.16.167.35:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3044 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl2.tlauncher.org |
| malicious |
ocsp.comodoca.com |
| whitelisted |
advancedrepository.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
page.tlauncher.org |
| malicious |
repo.tlauncher.org |
| whitelisted |
img.tlauncher.org |
| malicious |
ajax.cloudflare.com |
| whitelisted |
launchermeta.mojang.com |
| whitelisted |
stat.tlrepo.com |
| suspicious |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|