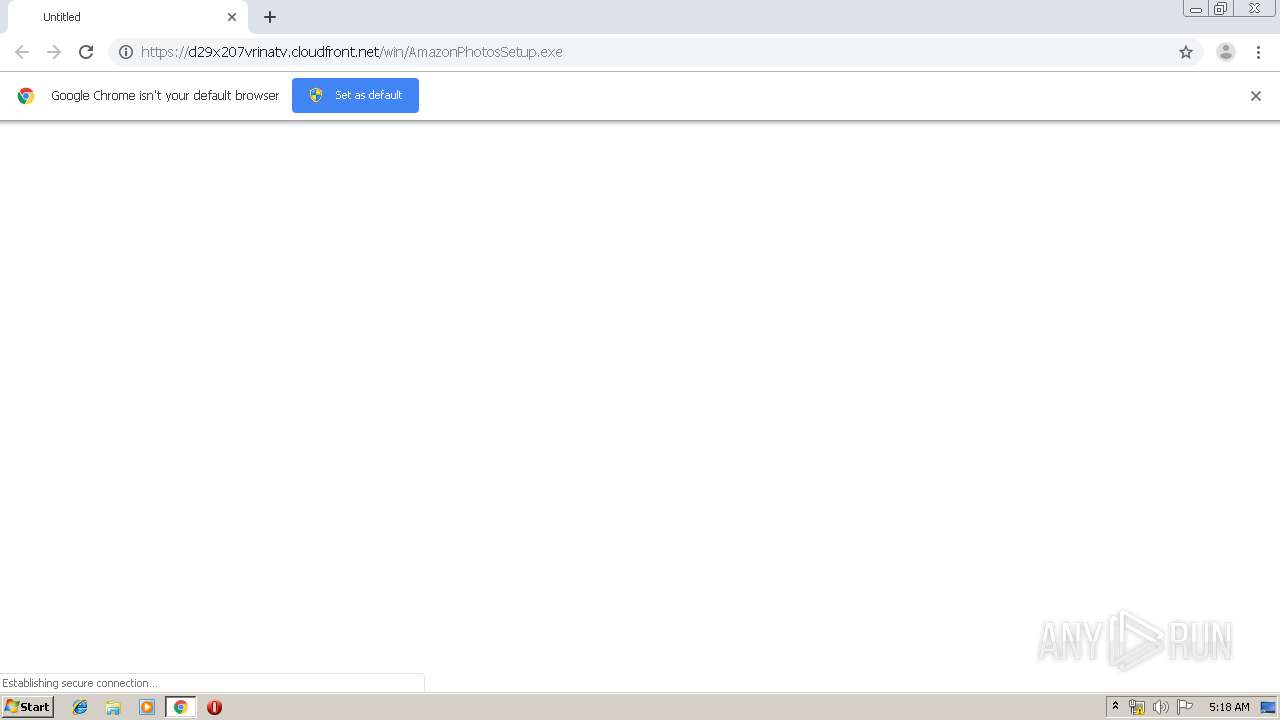
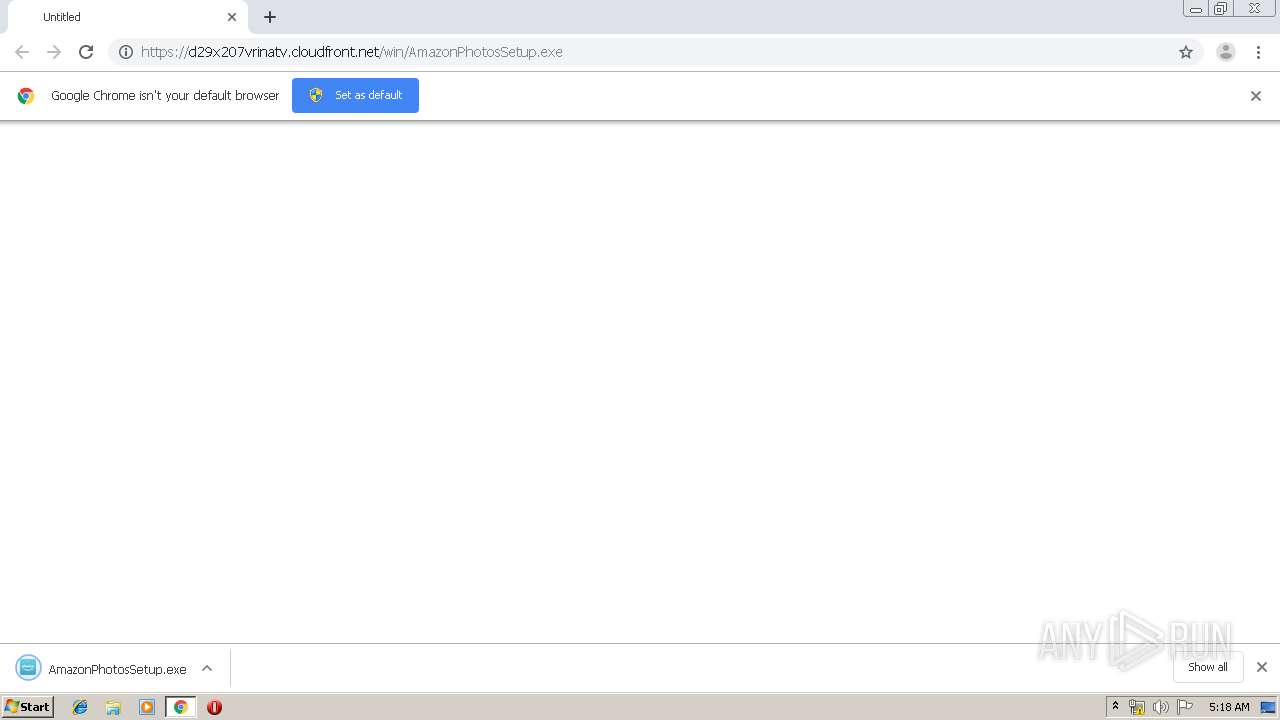
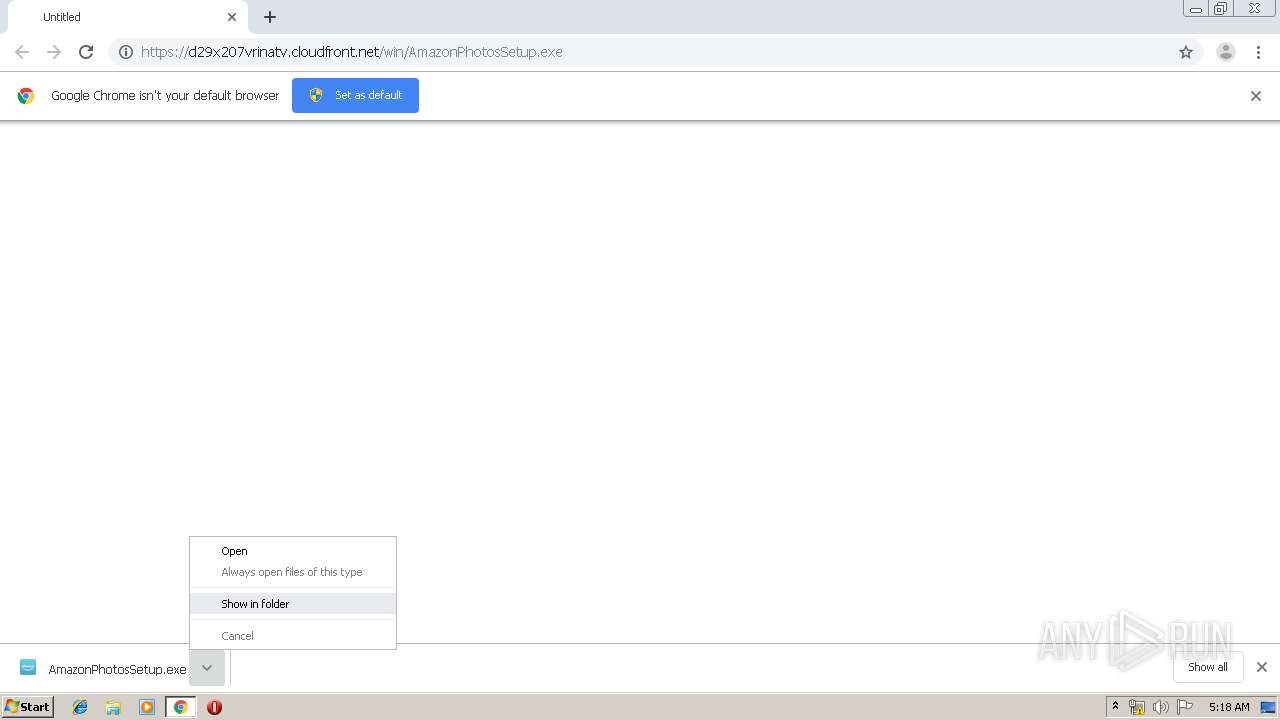
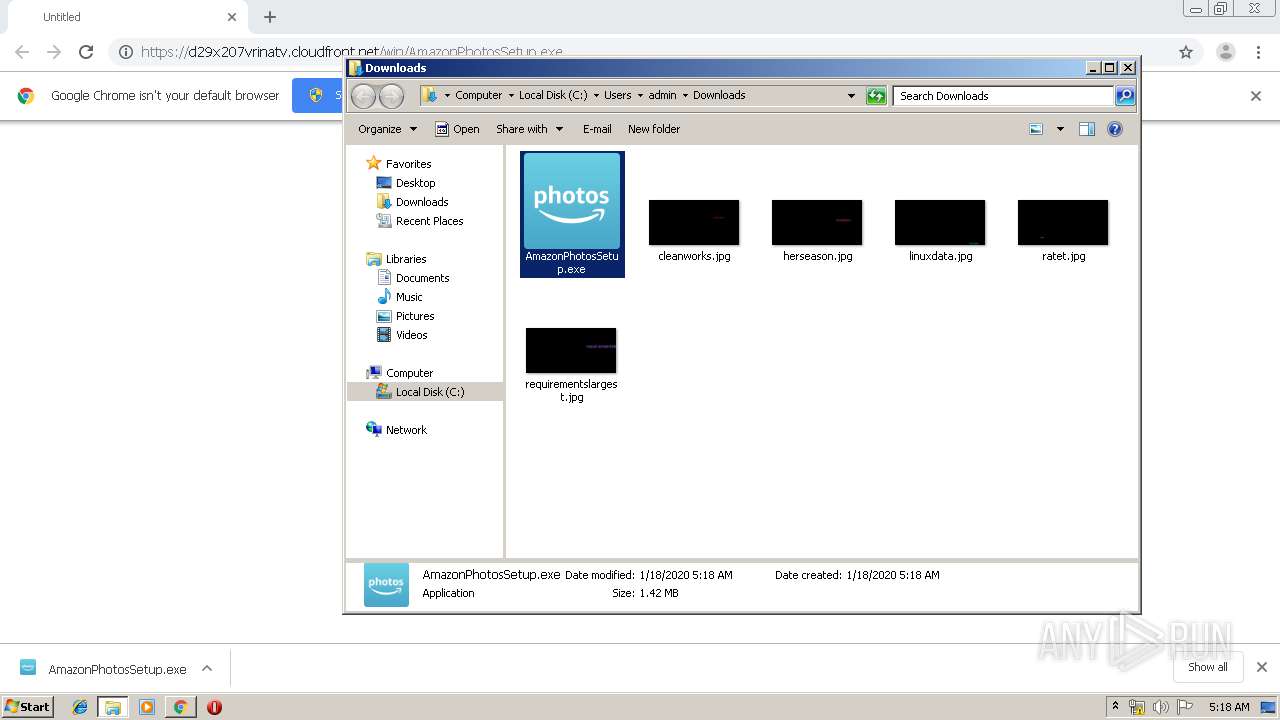
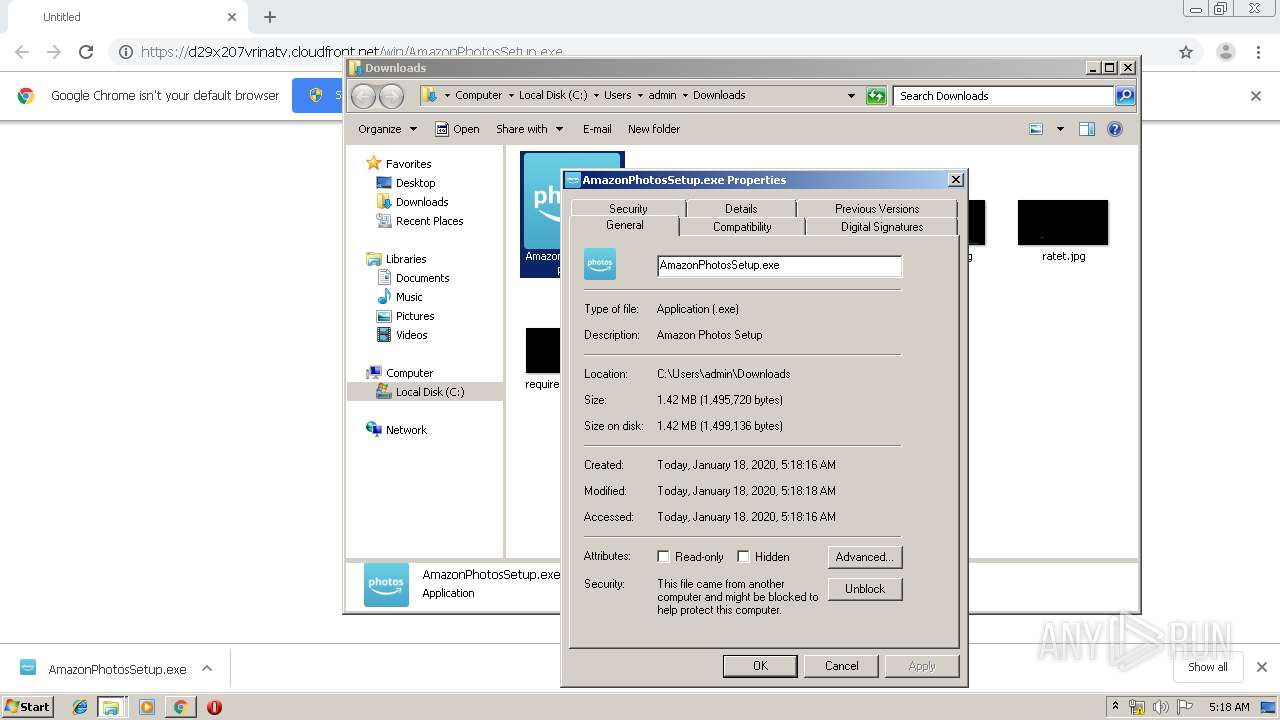
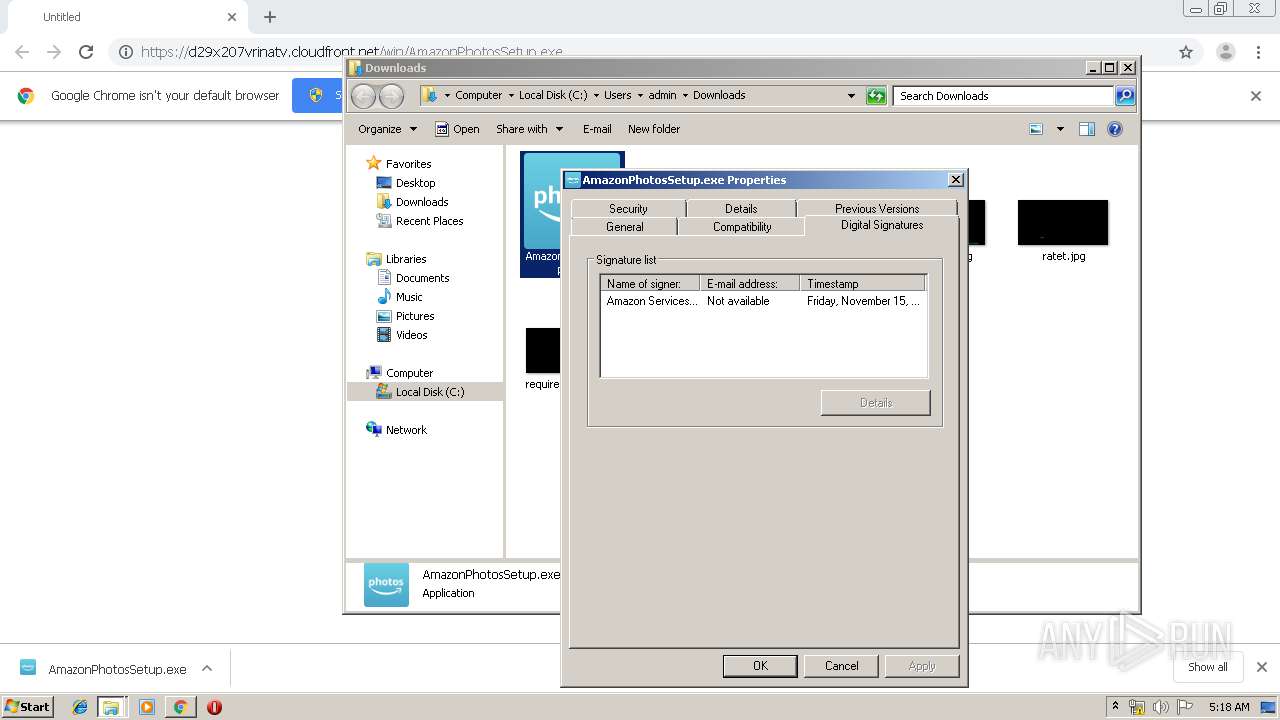
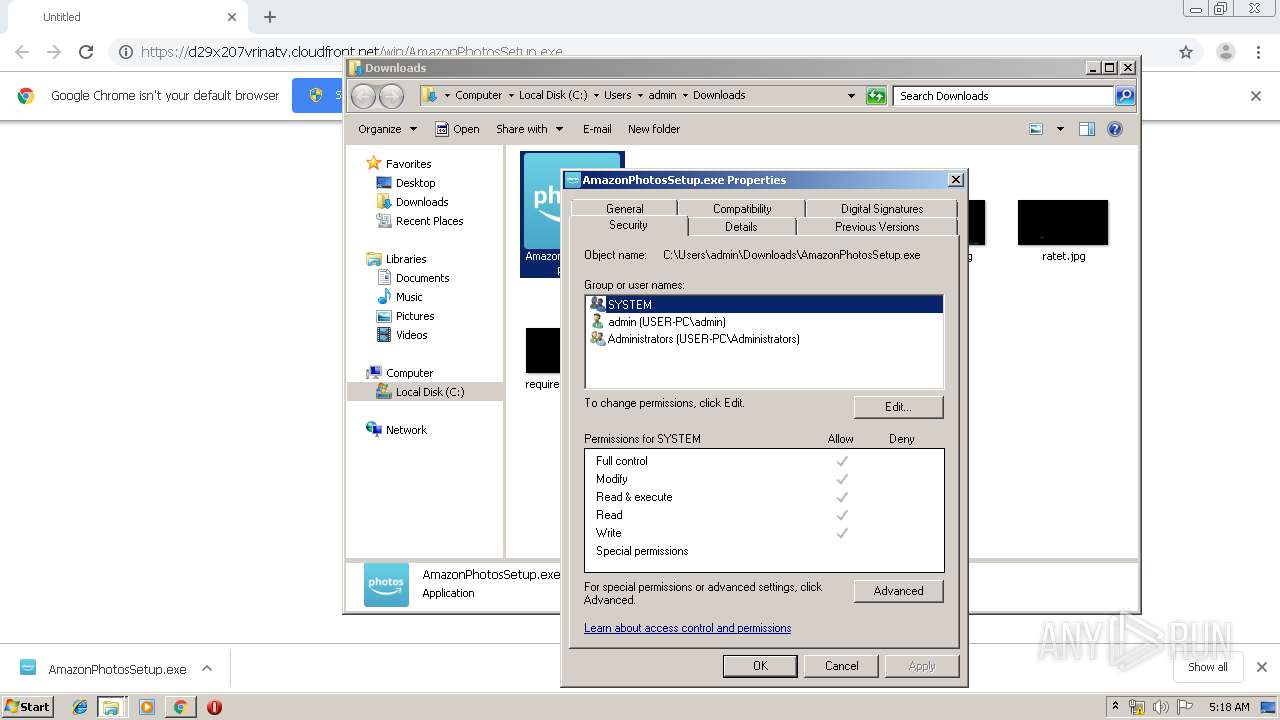
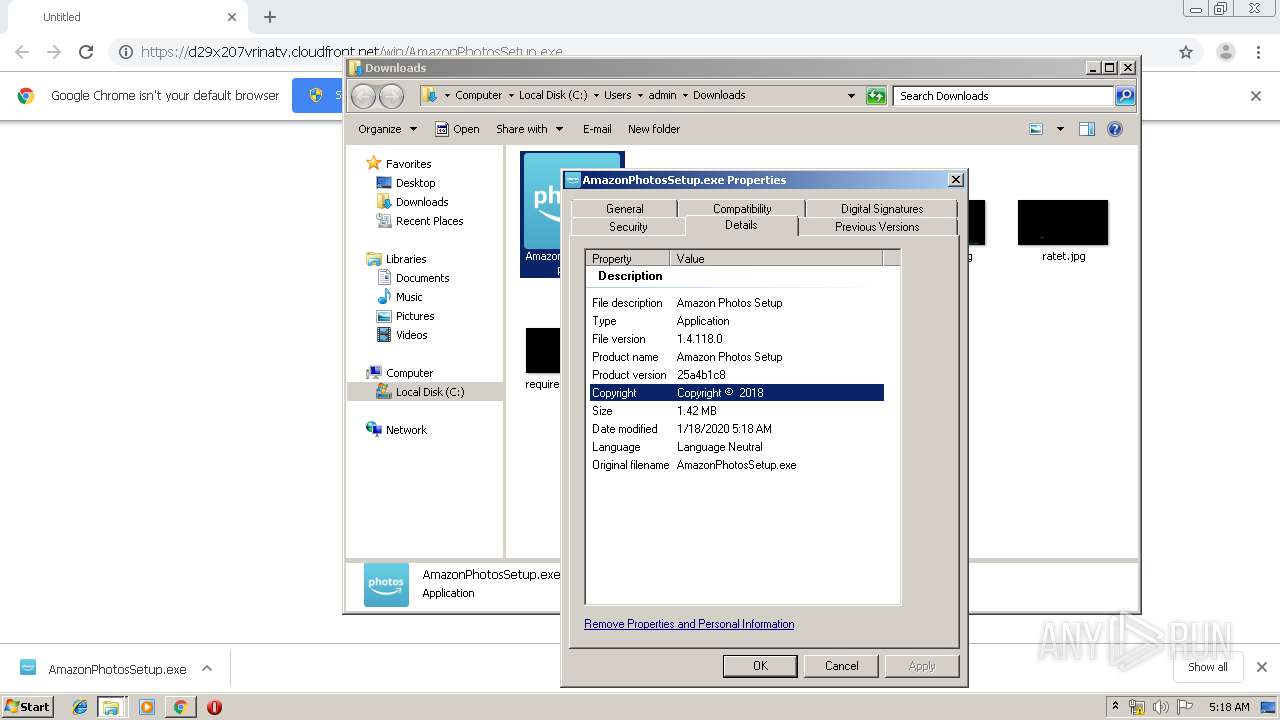
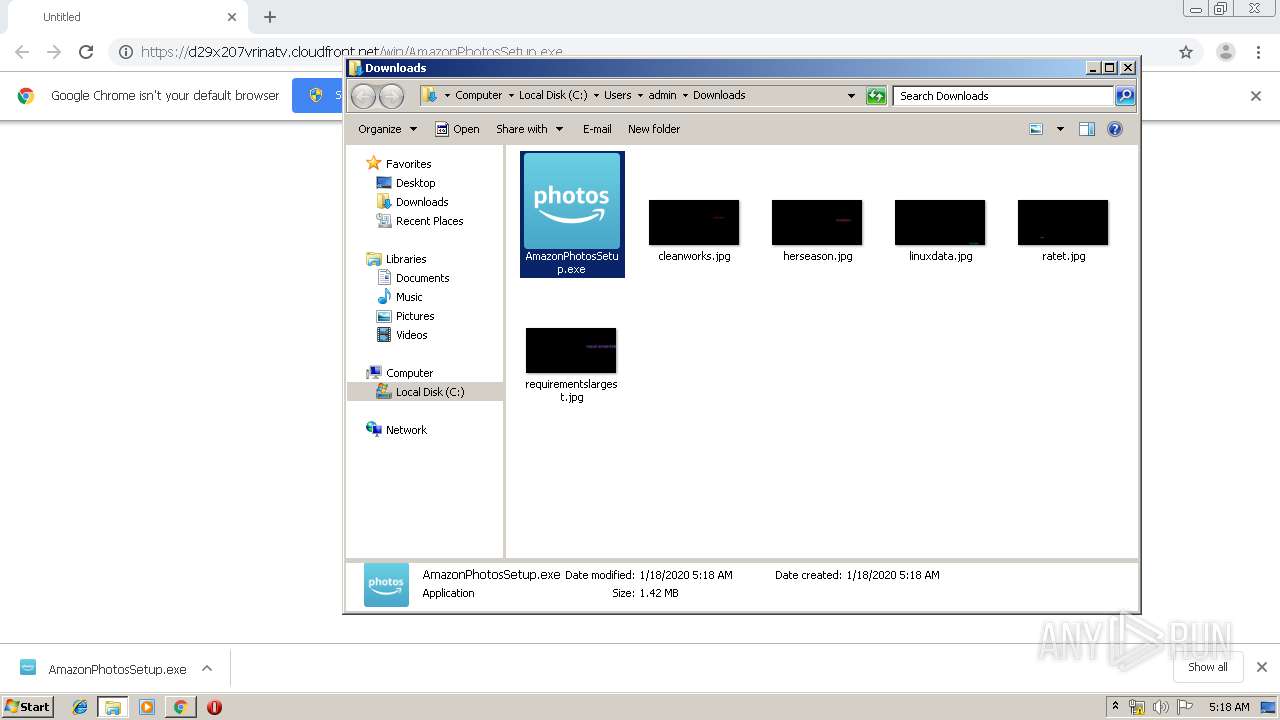
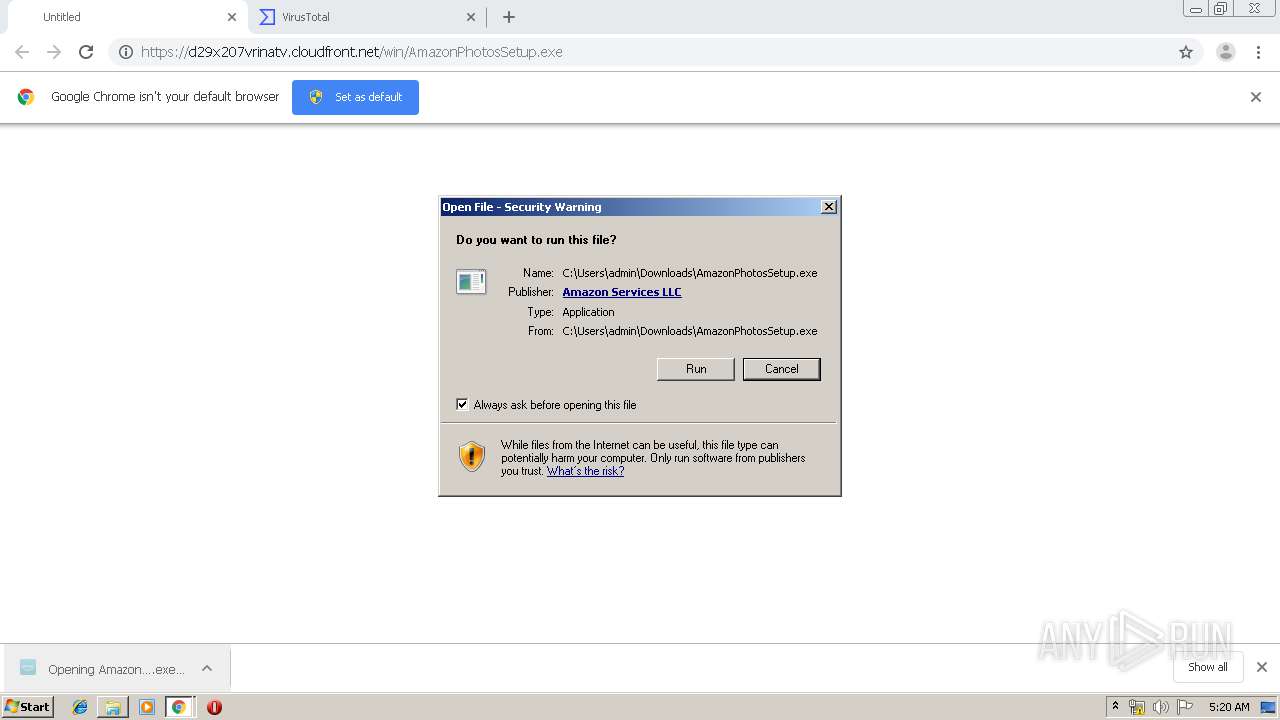
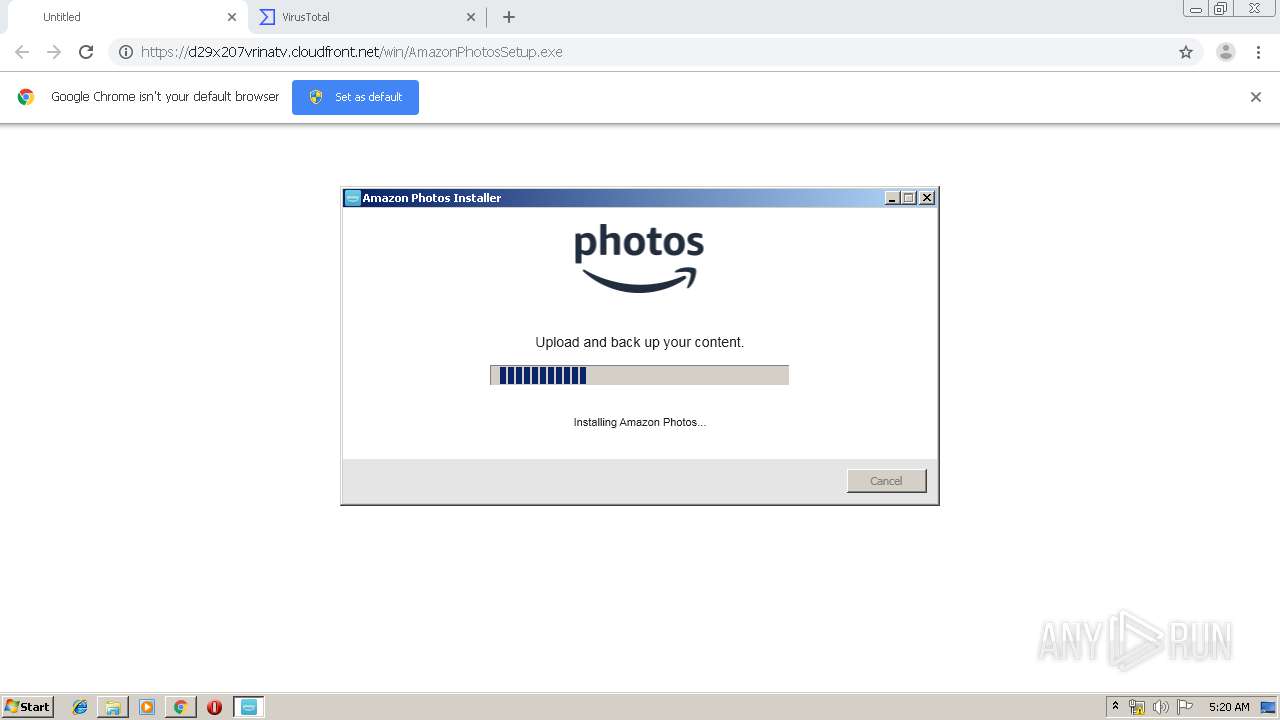
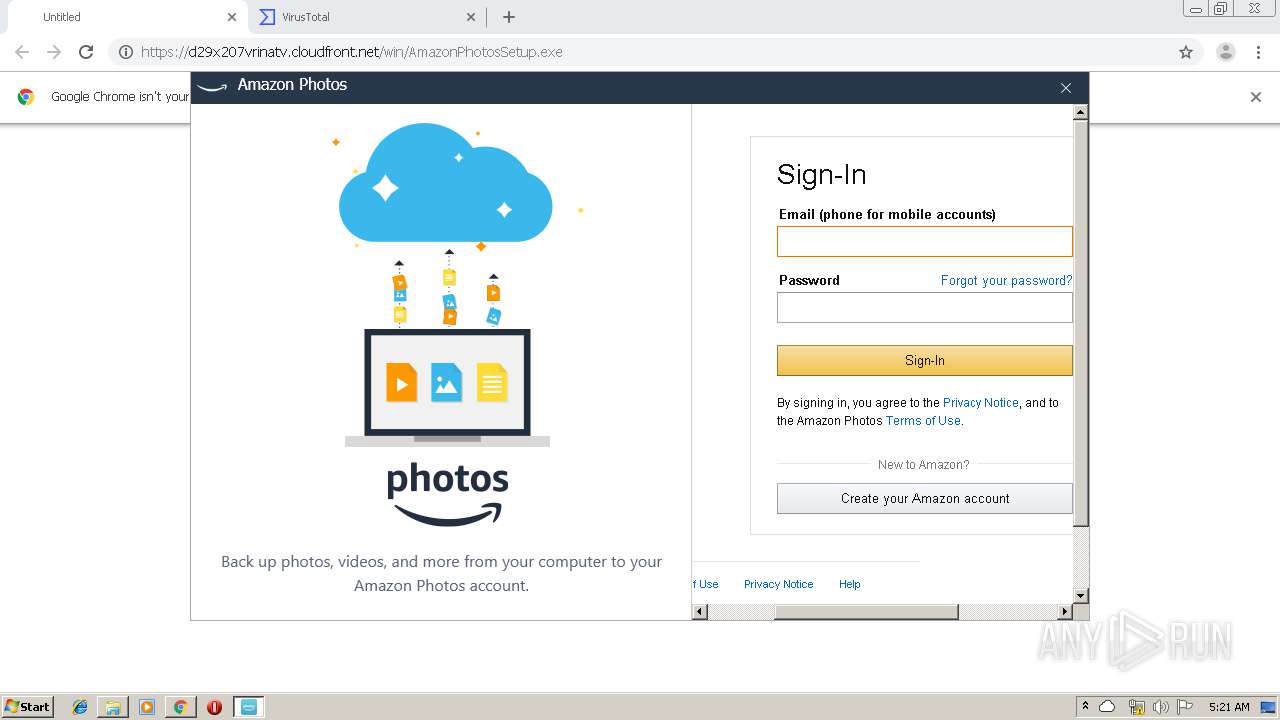
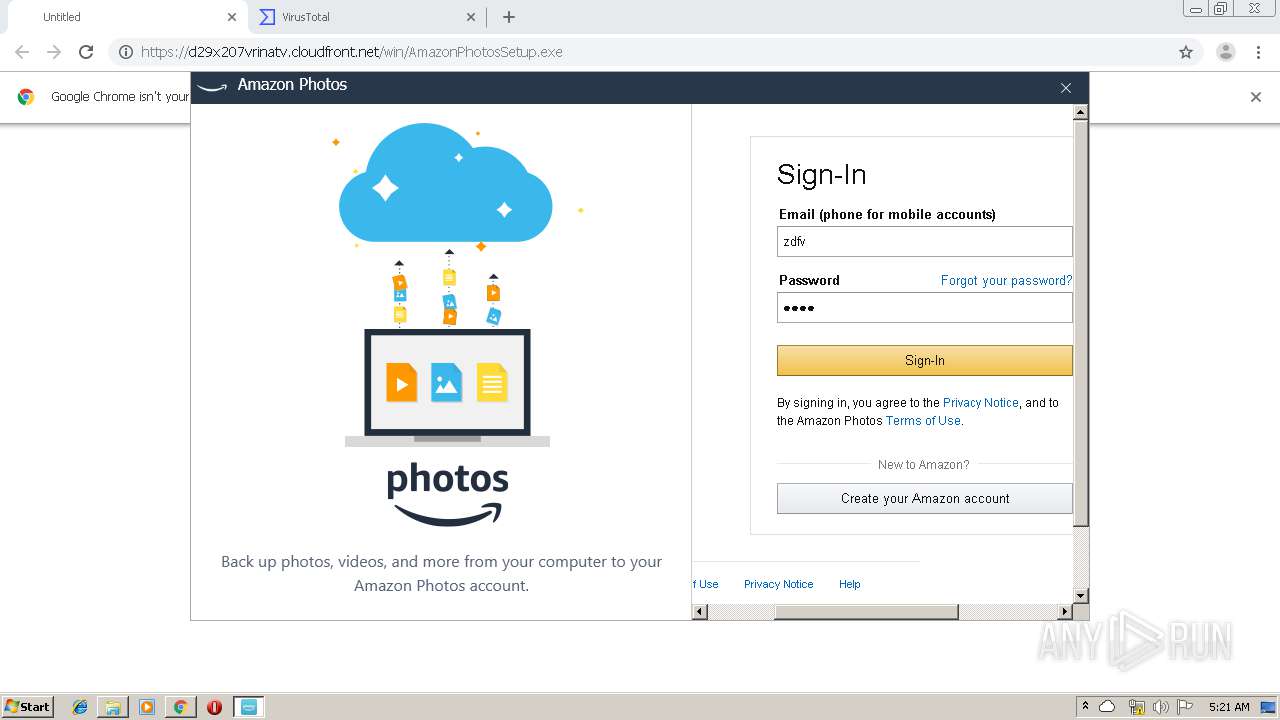
| URL: | https://d29x207vrinatv.cloudfront.net/win/AmazonPhotosSetup.exe |
| Full analysis: | https://app.any.run/tasks/621b9b1f-72bb-475e-81c6-dbc2fc9f239e |
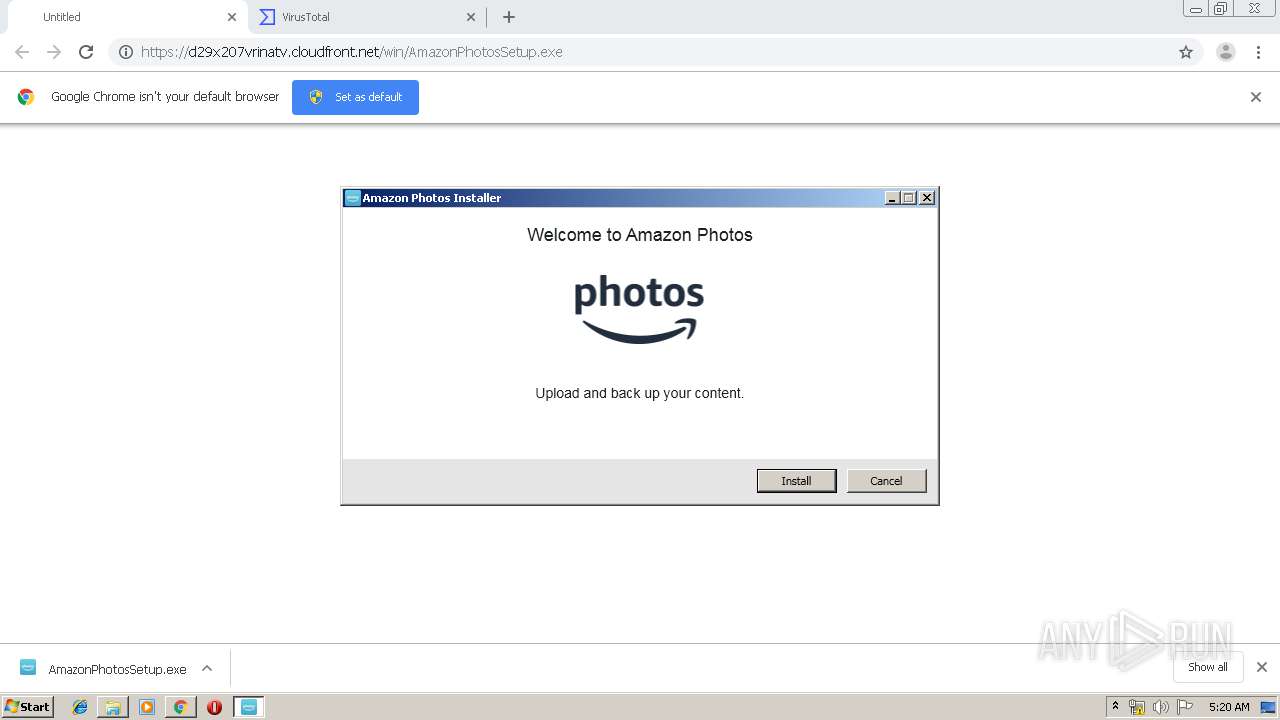
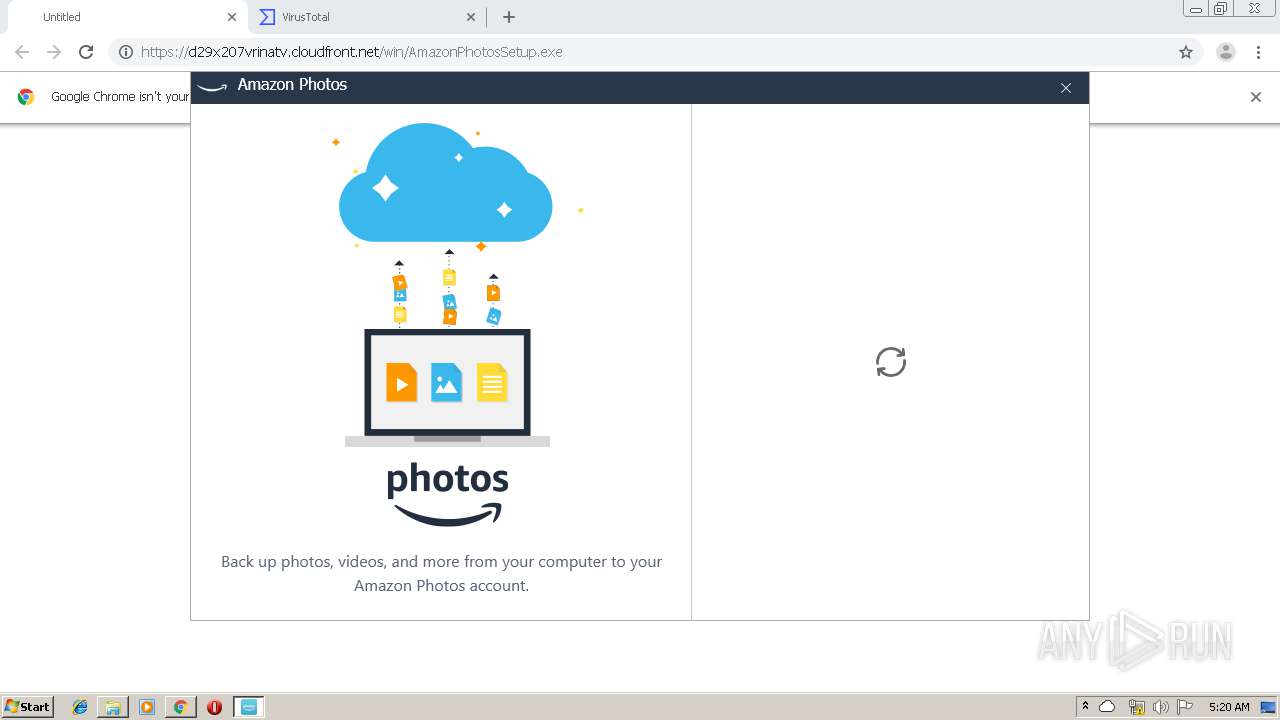
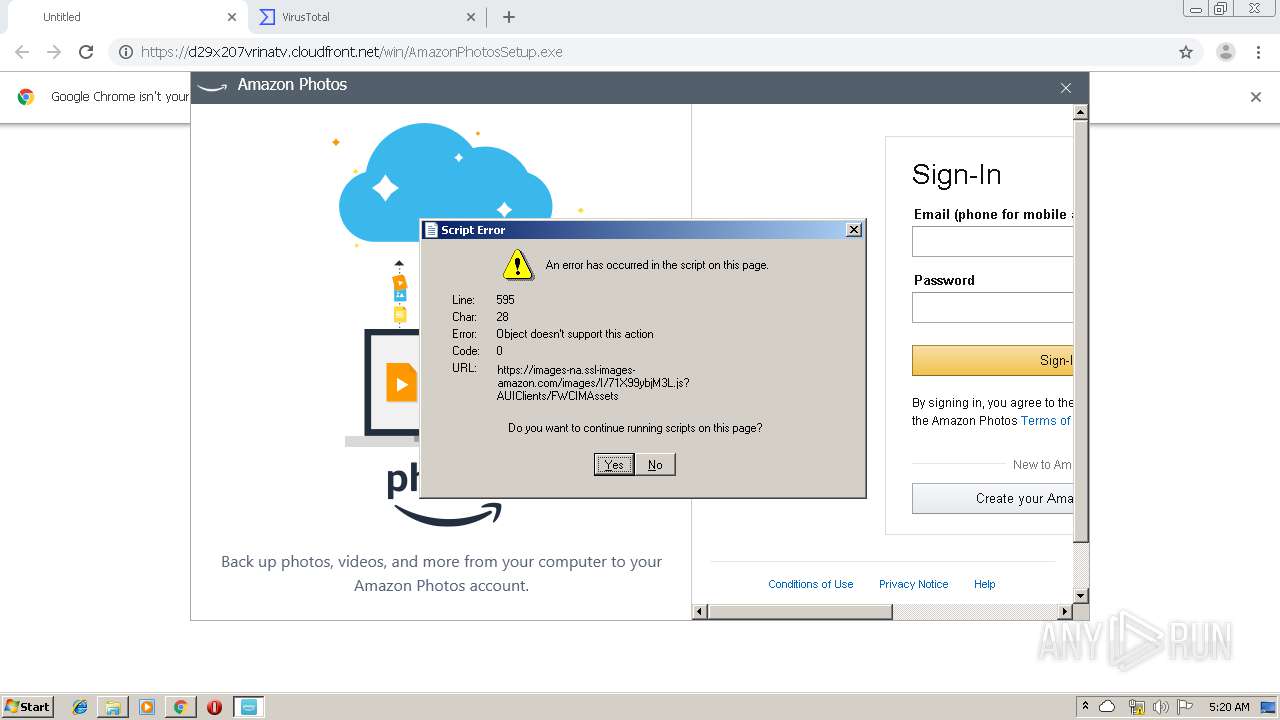
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 05:17:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BE184B13D29EB0ED74615EEC409BF045 |
| SHA1: | 8D63D8BF273A4471D394856C4D45F9D5A0868F95 |
| SHA256: | DD6091CC5839C5260CCB5ACE657620D59421AC951FBE87D4B5BAA91CF86679F8 |
| SSDEEP: | 3:N8P2IKUGJ0l/0C+kI2gYsxAvA:2ONfvRrYs6A |
MALICIOUS
Application was dropped or rewritten from another process
- AmazonPhotosSetup.exe (PID: 3700)
- AmazonPhotosSetupQ.exe (PID: 2880)
- AmazonPhotos.exe (PID: 3976)
Loads dropped or rewritten executable
- AmazonPhotosSetupQ.exe (PID: 2880)
- AmazonPhotos.exe (PID: 3976)
Changes settings of System certificates
- AmazonPhotosSetup.exe (PID: 3700)
Changes the autorun value in the registry
- AmazonPhotosSetupQ.exe (PID: 2880)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3772)
- chrome.exe (PID: 2860)
- AmazonPhotosSetup.exe (PID: 3700)
- AmazonPhotosSetupQ.exe (PID: 2880)
Creates files in the user directory
- AmazonPhotosSetup.exe (PID: 3700)
- AmazonPhotosSetupQ.exe (PID: 2880)
- AmazonPhotos.exe (PID: 3976)
Reads Environment values
- AmazonPhotosSetup.exe (PID: 3700)
- AmazonPhotos.exe (PID: 3976)
Creates files in the program directory
- AmazonPhotosSetup.exe (PID: 3700)
- AmazonPhotos.exe (PID: 3976)
Reads the machine GUID from the registry
- AmazonPhotosSetup.exe (PID: 3700)
Creates a software uninstall entry
- AmazonPhotosSetupQ.exe (PID: 2880)
Changes IE settings (feature browser emulation)
- AmazonPhotosSetupQ.exe (PID: 2880)
Reads Internet Cache Settings
- AmazonPhotos.exe (PID: 3976)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2860)
Reads internet explorer settings
- AmazonPhotos.exe (PID: 3976)
INFO
Reads the hosts file
- chrome.exe (PID: 2860)
- chrome.exe (PID: 3772)
Application launched itself
- chrome.exe (PID: 2860)
Changes settings of System certificates
- chrome.exe (PID: 2860)
Reads Internet Cache Settings
- chrome.exe (PID: 2860)
Reads settings of System Certificates
- AmazonPhotosSetup.exe (PID: 3700)
- AmazonPhotos.exe (PID: 3976)
Dropped object may contain Bitcoin addresses
- AmazonPhotos.exe (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
42
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2888 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7099436024805702564 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11821058747667544923 --mojo-platform-channel-handle=5240 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15288569567426885398 --mojo-platform-channel-handle=4312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16765629293324031303 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8836621701818846505 --mojo-platform-channel-handle=4900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13529491132621843328 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9646769952600989504 --mojo-platform-channel-handle=4256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10984966886704077785 --mojo-platform-channel-handle=5596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7611691410044380720,7881736083991940223,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=634771927416650779 --mojo-platform-channel-handle=5224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 476
Read events
2 180
Write events
290
Delete events
6
Modification events
| (PID) Process: | (272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2860-13223798294200125 |
Value: 259 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2860-13223798294200125 |
Value: 259 | |||
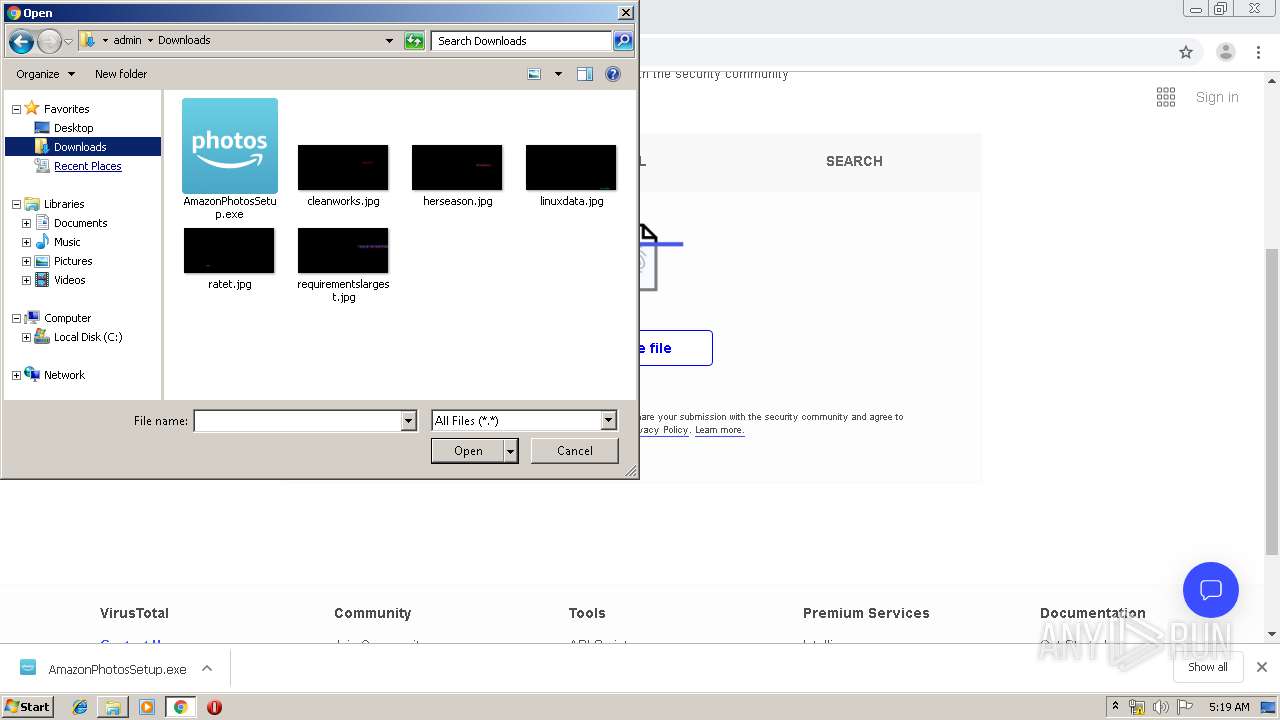
Executable files
157
Suspicious files
73
Text files
341
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f066db2c-59d1-461e-b1c3-67b5a1a8229f.tmp | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF38de59.TMP | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF38def5.TMP | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF38de59.TMP | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
74
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
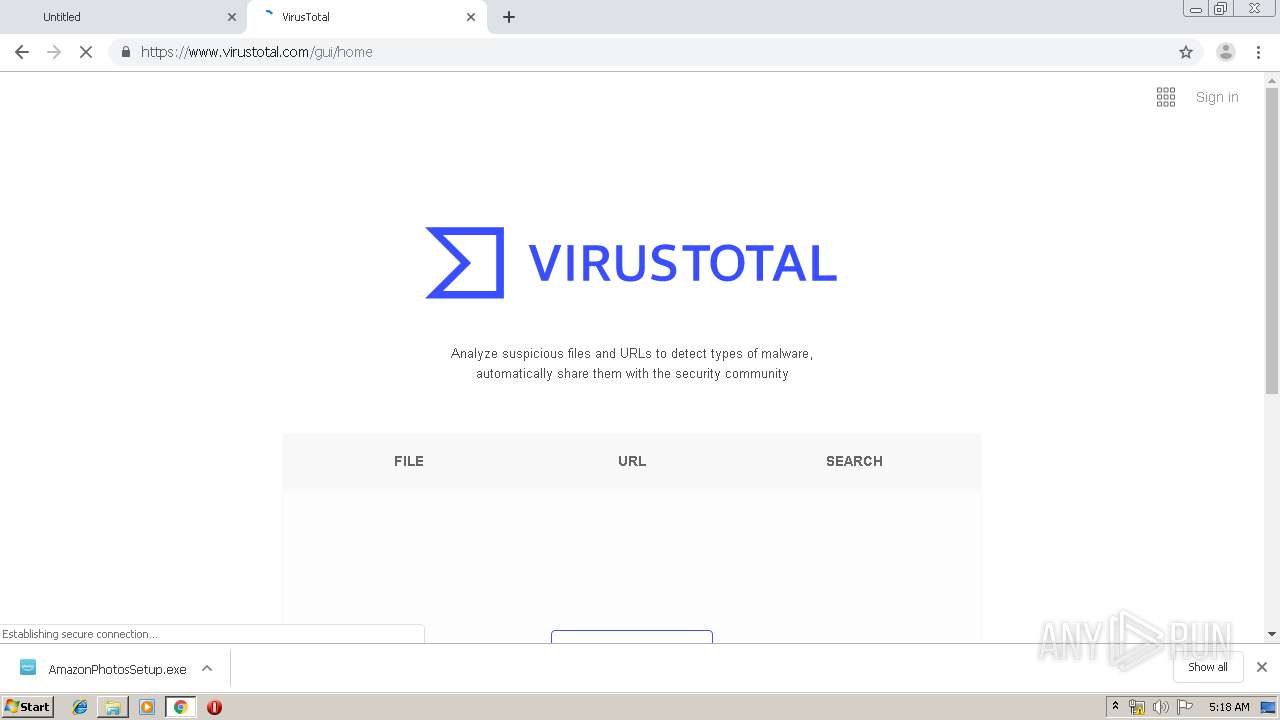
3772 | chrome.exe | GET | 302 | 216.239.34.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3700 | AmazonPhotosSetup.exe | GET | 200 | 23.37.43.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
3700 | AmazonPhotosSetup.exe | POST | 204 | 52.86.11.202:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
3700 | AmazonPhotosSetup.exe | POST | 204 | 52.86.11.202:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
3772 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3700 | AmazonPhotosSetup.exe | POST | 204 | 52.86.11.202:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
3772 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3772 | chrome.exe | GET | 200 | 173.194.183.168:80 | http://r3---sn-aigl6ney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.157.214.134&mm=28&mn=sn-aigl6ney&ms=nvh&mt=1579324814&mv=m&mvi=2&pl=19&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3976 | AmazonPhotos.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
3700 | AmazonPhotosSetup.exe | GET | 200 | 23.37.43.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEDlPLCJizC25K%2F6uIFk78XQ%3D | NL | der | 1.57 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3772 | chrome.exe | 13.35.254.184:443 | d29x207vrinatv.cloudfront.net | — | US | suspicious |
3772 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 216.58.207.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3772 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.22.3:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d29x207vrinatv.cloudfront.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.co.uk |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |